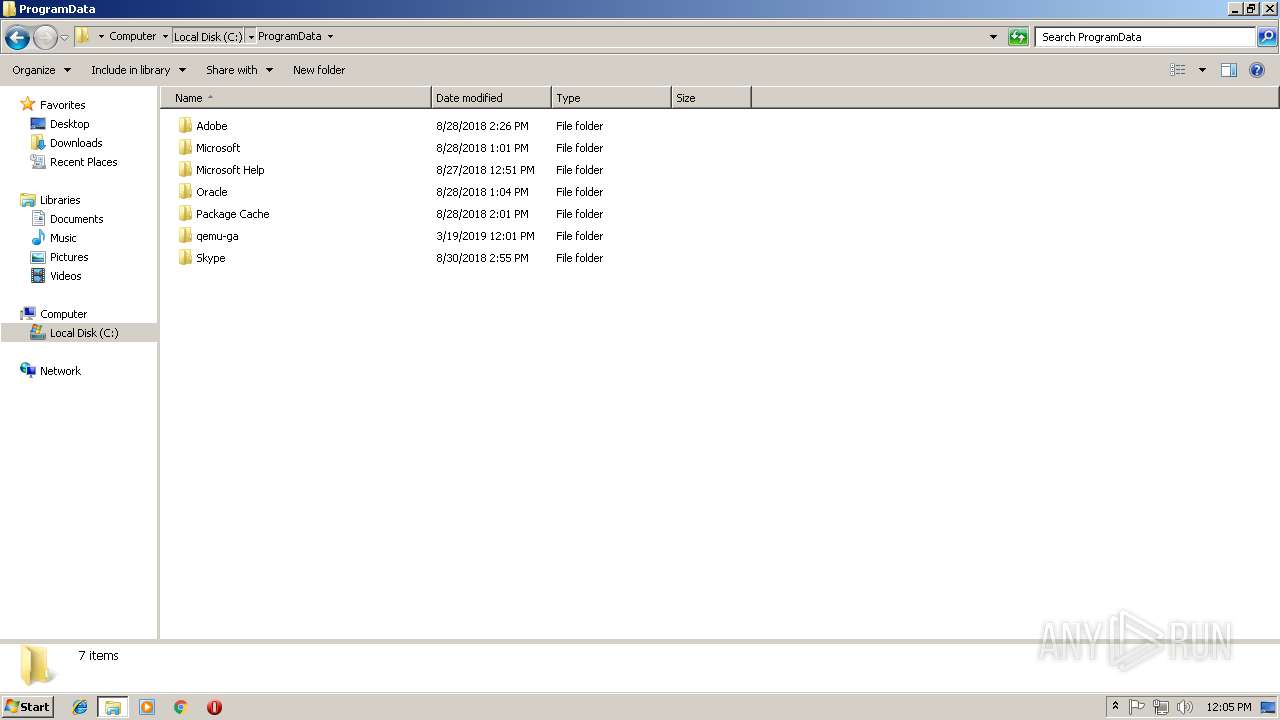
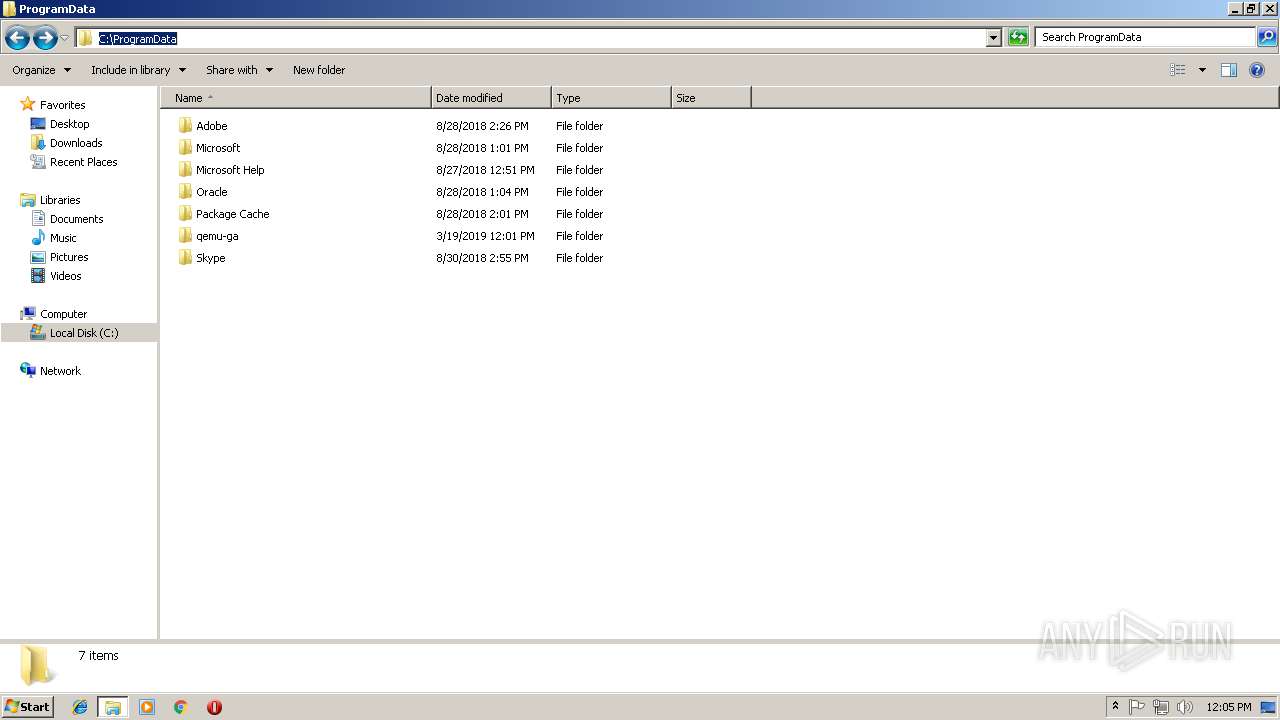
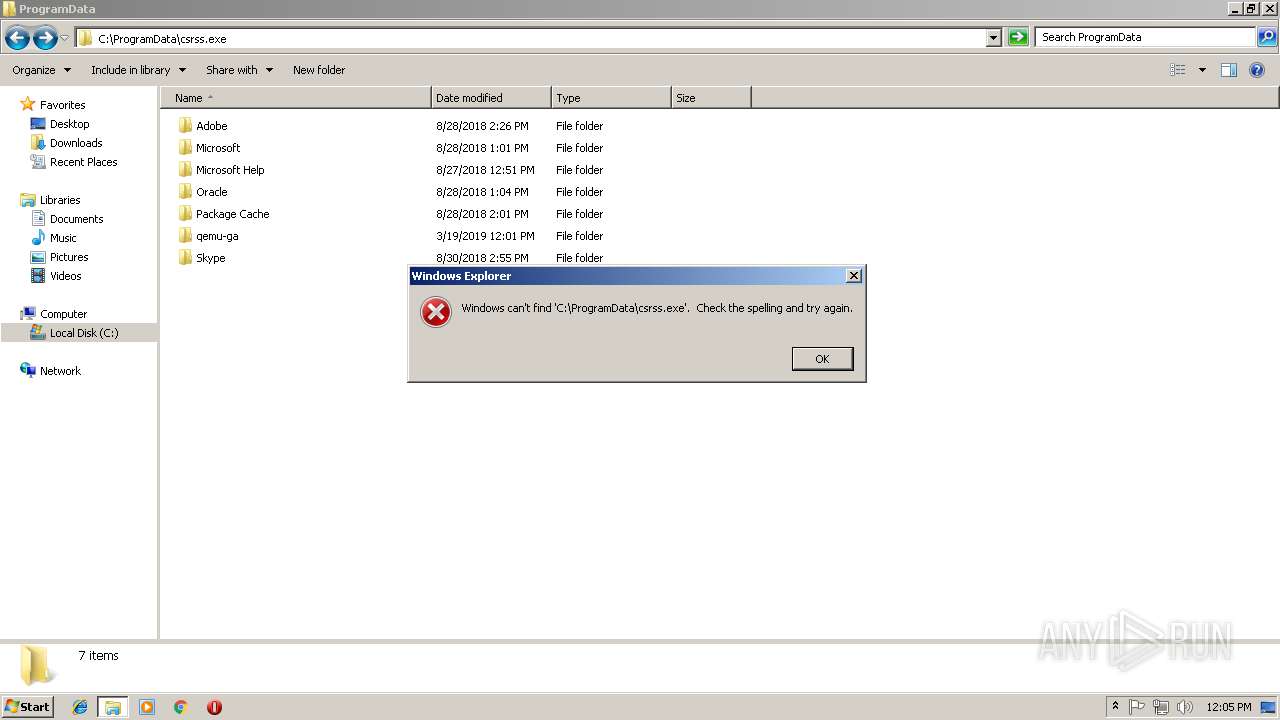
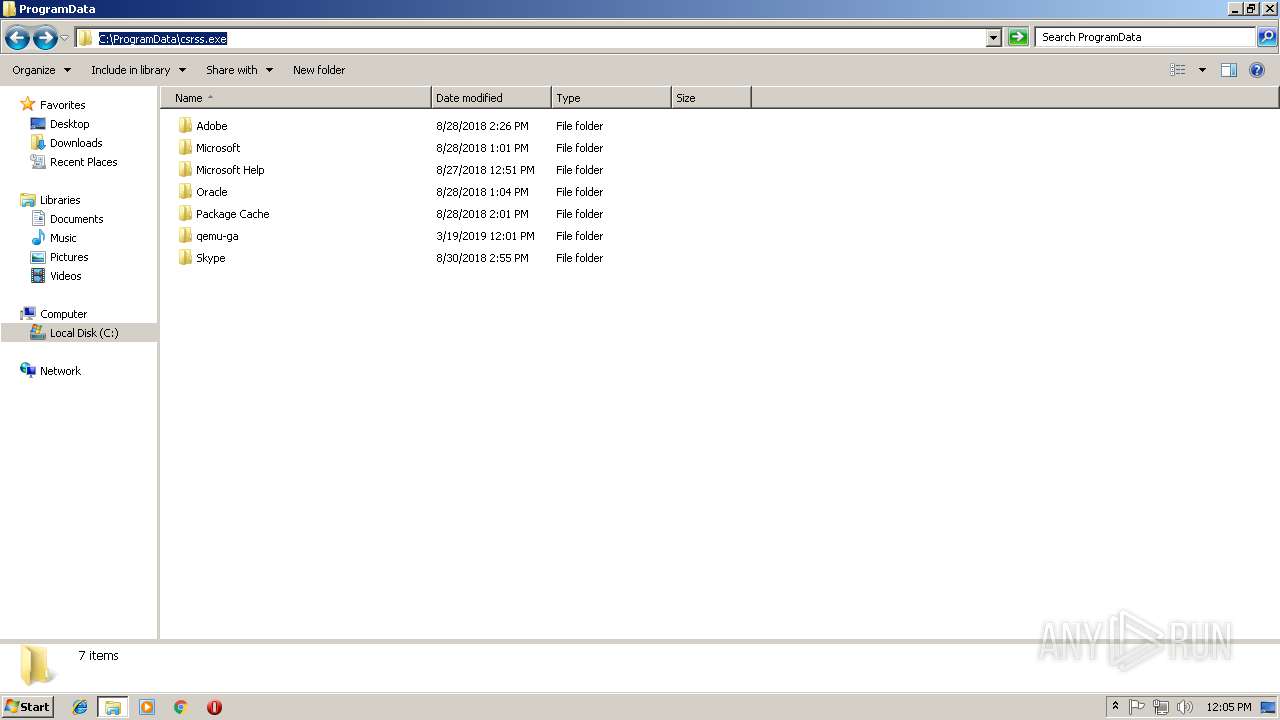
| File name: | C:\ProgramData\Windows\csrss.exe |
| Full analysis: | https://app.any.run/tasks/38bea059-b202-4650-8d27-9c8ed113d856 |
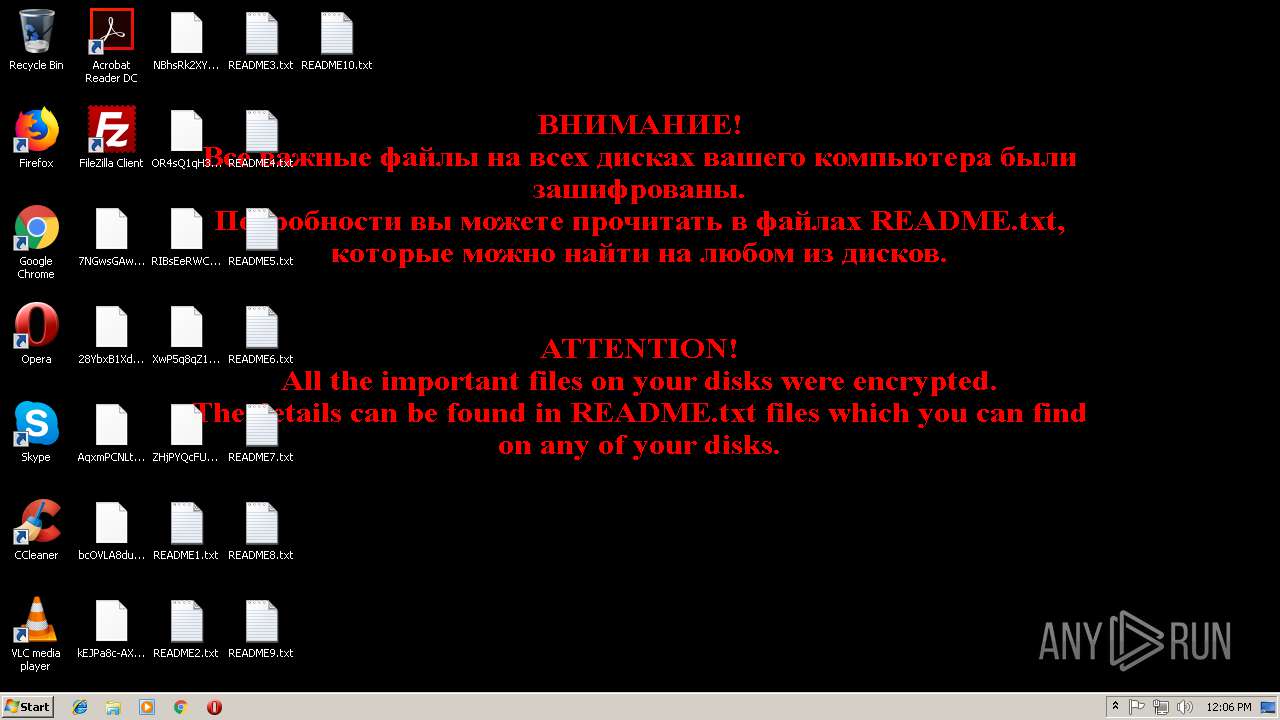
| Verdict: | Malicious activity |
| Threats: | Ransomware is a type of malicious software that locks users out of their system or data using different methods to force them to pay a ransom. Most often, such programs encrypt files on an infected machine and demand a fee to be paid in exchange for the decryption key. Additionally, such programs can be used to steal sensitive information from the compromised computer and even conduct DDoS attacks against affected organizations to pressure them into paying. |
| Analysis date: | March 19, 2019, 12:01:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B82B82BEB62AC4EB418482D9BCB517C2 |
| SHA1: | 3FCBF6EE4A4C917F985ACC78A7B1C05374992E20 |
| SHA256: | 90333748EE4E4C42BBC72B4317AFAF62CA23FF018B356FB0B92CAC1648B1144D |
| SSDEEP: | 24576:6Dbt4YcxdNDjJQqRTE0cZLx4bcWS5PcQV3D14EAKXtRutF3dF7D:61yDNXS2T+4c9cQVxnXtIr3T |
MALICIOUS
Deletes shadow copies
- csrss.exe (PID: 3532)
Runs app for hidden code execution
- csrss.exe (PID: 3532)
Changes the autorun value in the registry
- csrss.exe (PID: 3532)
TROLDESH was detected
- csrss.exe (PID: 3532)
Dropped file may contain instructions of ransomware
- csrss.exe (PID: 3532)
Actions looks like stealing of personal data
- csrss.exe (PID: 3532)
Modifies files in Chrome extension folder
- csrss.exe (PID: 3532)
SUSPICIOUS
Connects to unusual port
- csrss.exe (PID: 3532)
Starts CMD.EXE for commands execution
- csrss.exe (PID: 3532)
Starts application with an unusual extension
- cmd.exe (PID: 3712)
Creates files in the user directory
- csrss.exe (PID: 3532)
Executable content was dropped or overwritten
- csrss.exe (PID: 3532)
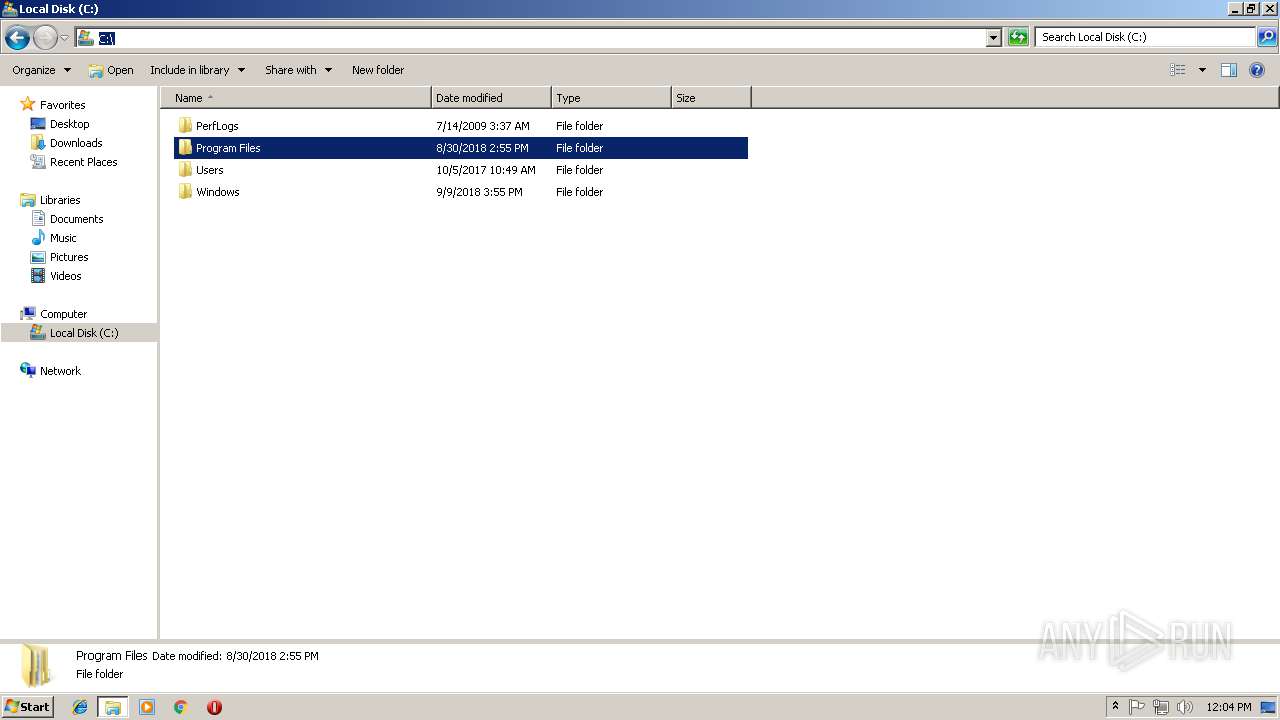
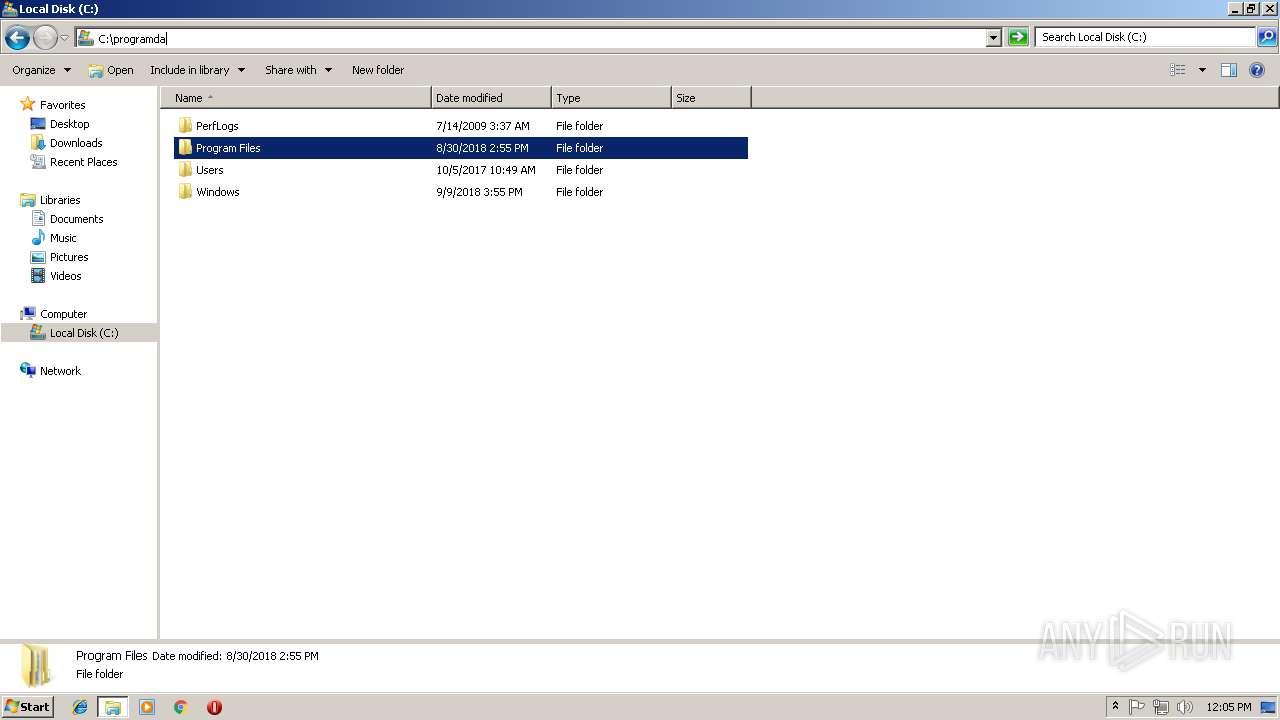
Creates files in the program directory
- csrss.exe (PID: 3532)
Checks for external IP
- csrss.exe (PID: 3532)
Creates files like Ransomware instruction
- csrss.exe (PID: 3532)
INFO
Dropped object may contain TOR URL's
- csrss.exe (PID: 3532)
Dropped object may contain Bitcoin addresses
- csrss.exe (PID: 3532)
Dropped object may contain URL to Tor Browser
- csrss.exe (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:03:19 00:10:42+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1123328 |
| InitializedDataSize: | 42496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f20 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.40.20 |
| ProductVersionNumber: | 7.0.40.20 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Oracle Corporation |
| FileDescription: | Java(TM) Platform SE binary |
| FileVersion: | 7.0.40.20 |
| FullVersion: | 1.7.0_04-b20 |
| InternalName: | kinit |
| LegalCopyright: | Copyright © 2012 |
| OriginalFileName: | kinit.exe |
| ProductName: | Java(TM) Platform SE 7 U4 |
| ProductVersion: | 7.0.40.20 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Mar-2019 23:10:42 |
| Detected languages: |
|
| CompanyName: | Oracle Corporation |
| FileDescription: | Java(TM) Platform SE binary |
| FileVersion: | 7.0.40.20 |
| Full Version: | 1.7.0_04-b20 |
| InternalName: | kinit |
| LegalCopyright: | Copyright © 2012 |
| OriginalFilename: | kinit.exe |
| ProductName: | Java(TM) Platform SE 7 U4 |
| ProductVersion: | 7.0.40.20 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Mar-2019 23:10:42 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001122B1 | 0x00112400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.97007 |
.rdata | 0x00114000 | 0x000094A0 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.36523 |
.data | 0x0011E000 | 0x0000058C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.66374 |
.rsrc | 0x0011F000 | 0x000E8948 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.74115 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.43701 | 816 | UNKNOWN | UNKNOWN | RT_VERSION |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
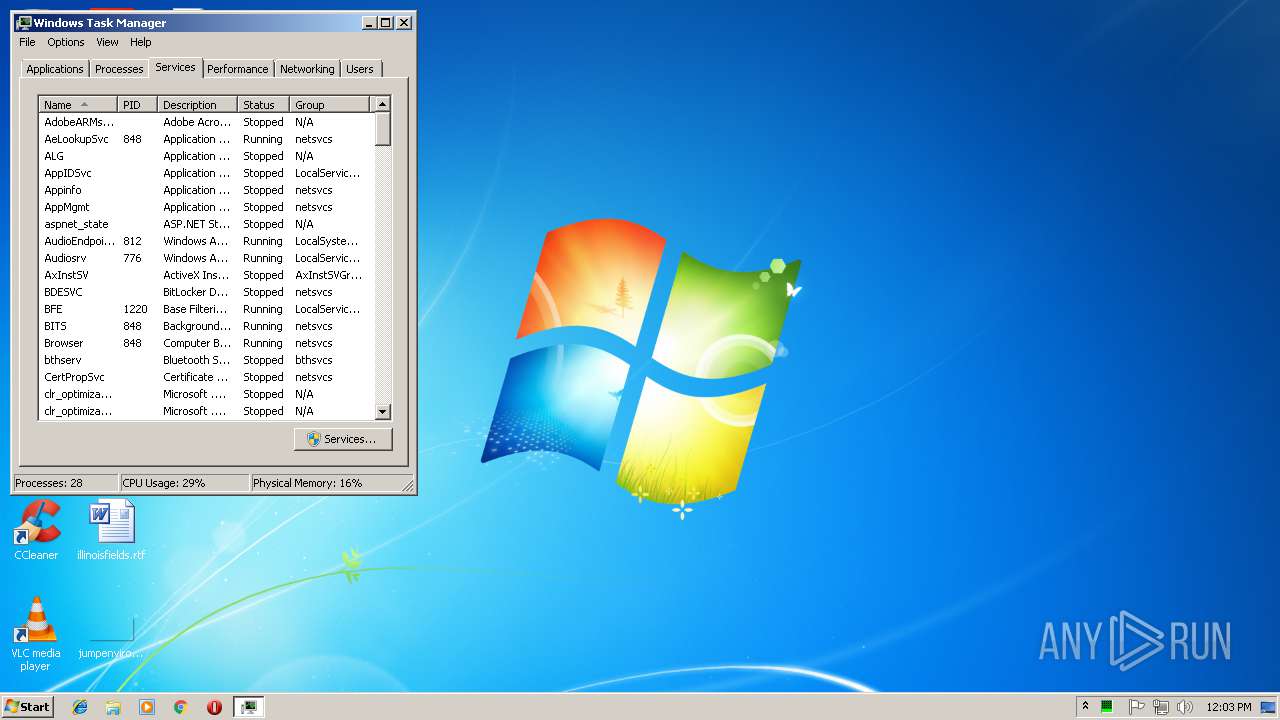
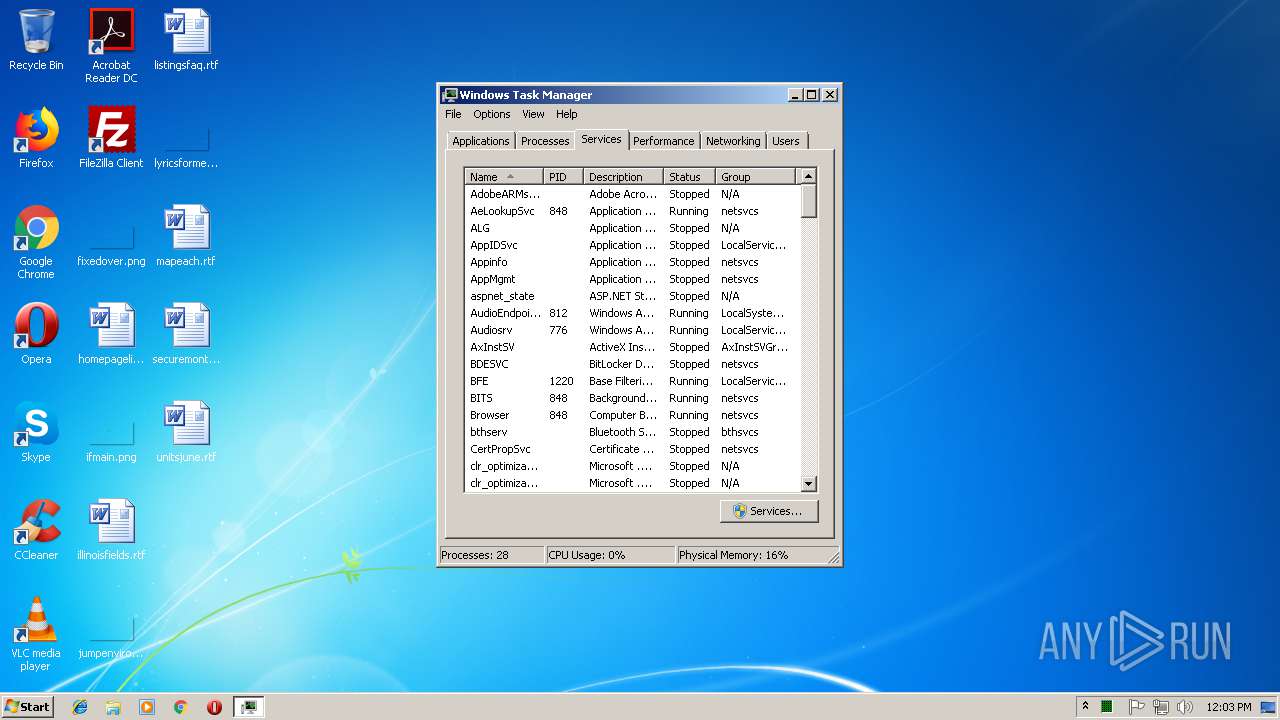
Total processes
47
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | chcp | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2456 | "C:\Windows\system32\vssadmin.exe" Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | csrss.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | C:\Windows\system32\vssadmin.exe List Shadows | C:\Windows\system32\vssadmin.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3400 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\AppData\Local\Temp\csrss.exe" | C:\Users\admin\AppData\Local\Temp\csrss.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 7.0.40.20 Modules
| |||||||||||||||
| 3712 | C:\Windows\system32\cmd.exe | C:\Windows\system32\cmd.exe | — | csrss.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
150
Read events
126
Write events
24
Delete events
0
Modification events
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xi |
Value: 906D0F2E2F604F839E04 | |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Client Server Runtime Subsystem |
Value: "C:\ProgramData\Windows\csrss.exe" | |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xVersion |
Value: 4.0.0.1 | |||
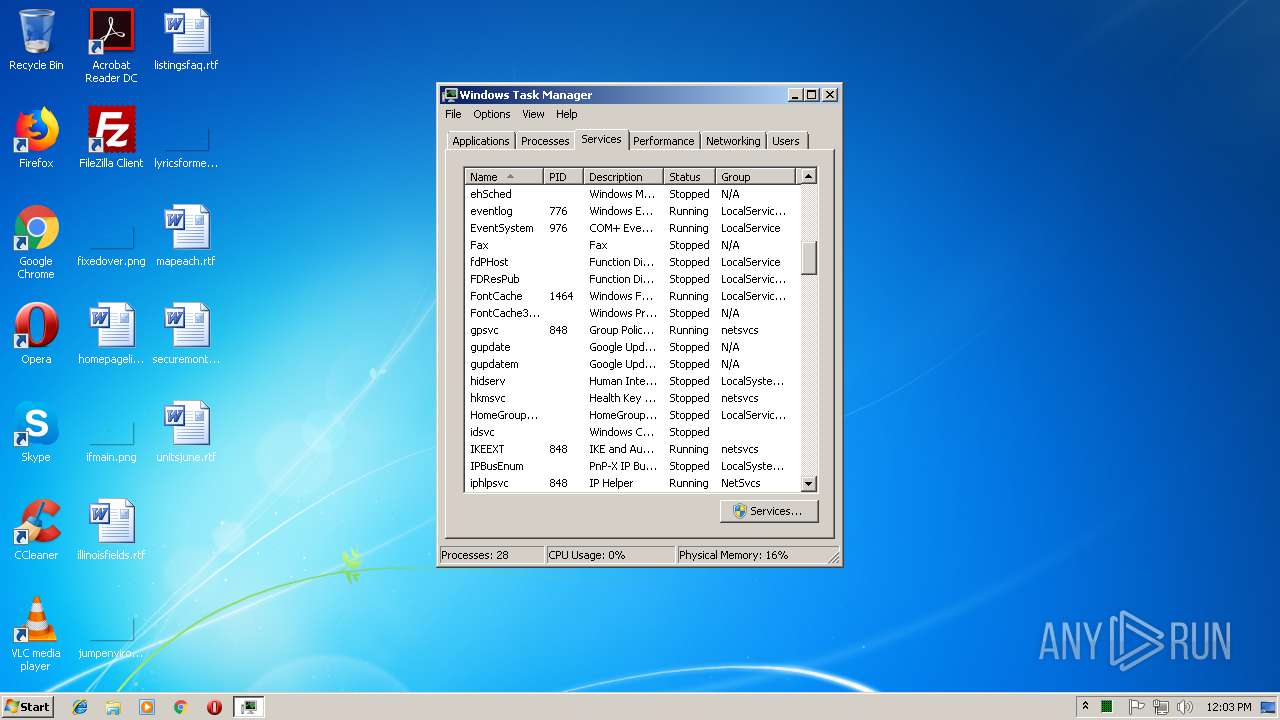
| (PID) Process: | (2408) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | UsrColumnSettings |
Value: 1C0C0000340400000000000050000000010000001D0C0000350400000000000023000000010000001E0C000036040000000000003C000000010000001F0C000039040000000000004E00000001000000200C000037040000000000004E00000001000000 | |||
| (PID) Process: | (2408) taskmgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 30030000E80300000100000001000000B4010000520000004C030000380200000200000001000000000000000000000001000000000000000100000000000000000000000200000004000000090000001D000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000009C00000040000000210000004600000052000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0000000002000000010000000300000004000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0500000000000000FFFFFFFF00000000020000000300000004000000FFFFFFFF00000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF000000000000010000000200000003000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF0400000000000000FFFFFFFF00000000FFFFFFFF4F00000028000000500000003400000050000000000000000100000002000000030000000400000000000000FFFFFFFF43000000000000000000000001000000 | |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xmail |
Value: 1 | |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xmode |
Value: 0 | |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xpk |
Value: -----BEGIN PUBLIC KEY-----
MIIBojANBgkqhkiG9w0BAQEFAAOCAY8AMIIBigKCAYEA8mn4F2LJ2xbiQ2U0nRya
c1tR+wN6CcLUa3lCLO+4Hj4gGGvPGugPV/9l2cAkeQZahnqlgKG51eaFO1UYdmPs
zyNfi9qlgFndoFL8XsxFHJ4C9BqqlIpD15pglgrubqX0lZGlI27dXh4bu3fA9zrI
ULugLryqMmIId6MDIY2WalR+7Vpq8ATM6VN1/+CKBDEcdHeWsNScgxtKOVa20E60
qOWxzdUoCeMHgMr+Q8kzPQzreyejLbBZL9cXTxstXJVsA64ge/G71oZlLU7j2Ujp
EHkXR4G0I5QBEQu62K0R+cz3FqxP6CN6Pm1MJb8XHkU54FYsVsLsk5nasUMUZ9Uq
5ikgVEO65k7bgwi9nGZsyDlWDOwbGuSRreLAVKeCDiO2jfSBOTH16gIyT9rE7UDj
6SRe2guJhe2sqwXpwgmTJsWffQmzg5vQwWrL4UXUASCWvtODBBTq8jGom9T5Aet/
gsLcsM1ozqI961wp6RZPO1WluzsxvpDT4bCJmc5D6dp/AgMBAAE=
-----END PUBLIC KEY-----
| |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xstate |
Value: 3 | |||
| (PID) Process: | (3532) csrss.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\System32\Configuration |
| Operation: | write | Name: | xcnt |
Value: 0 | |||
Executable files
1
Suspicious files
1 096
Text files
43
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | csrss.exe | C:\Users\admin\AppData\Local\Temp\6893A5D897\state.tmp | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\admin\AppData\Local\Temp\6893A5D897\unverified-microdesc-consensus.tmp | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\admin\AppData\Local\Temp\6893A5D897\cached-certs.tmp | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\admin\AppData\Local\Temp\6893A5D897\cached-microdesc-consensus.tmp | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\Public\Videos\Sample Videos\Wildlife.wmv | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\Public\Videos\Sample Videos\MDiMr-UzwwMDpl02YT7SP2h0dIl7wNtJVu2stJUcpMA=.906D0F2E2F604F839E04.crypted000007 | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\Public\Pictures\Sample Pictures\Tulips.jpg | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\Public\Pictures\Sample Pictures\Penguins.jpg | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\Public\Pictures\Sample Pictures\Lighthouse.jpg | — | |
MD5:— | SHA256:— | |||
| 3532 | csrss.exe | C:\Users\Public\Pictures\Sample Pictures\Koala.jpg | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
18
DNS requests
2
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 200 | 104.18.35.131:80 | http://whatsmyip.net/ | US | html | 7.35 Kb | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
3532 | csrss.exe | GET | 403 | 104.16.155.36:80 | http://whatismyipaddress.com/ | US | text | 100 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3532 | csrss.exe | 76.73.17.194:9090 | — | Cogent Communications | US | malicious |
3532 | csrss.exe | 128.31.0.39:9101 | — | Massachusetts Institute of Technology | US | malicious |
3532 | csrss.exe | 208.83.223.34:80 | — | Applied Operations, LLC | US | malicious |
3532 | csrss.exe | 171.25.193.9:80 | — | Foreningen for digitala fri- och rattigheter | SE | malicious |
3532 | csrss.exe | 85.25.213.211:80 | — | Host Europe GmbH | DE | suspicious |
3532 | csrss.exe | 163.172.53.201:443 | — | Online S.a.s. | FR | malicious |
3532 | csrss.exe | 188.118.153.20:9001 | — | EWE-Tel GmbH | DE | suspicious |
3532 | csrss.exe | 104.16.155.36:80 | whatismyipaddress.com | Cloudflare Inc | US | shared |
3532 | csrss.exe | 104.18.35.131:80 | whatsmyip.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
whatismyipaddress.com |
| shared |
whatsmyip.net |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3532 | csrss.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
3532 | csrss.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
3532 | csrss.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 184 |
3532 | csrss.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
3532 | csrss.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
3532 | csrss.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 649 |
3532 | csrss.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 178 |
3532 | csrss.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
3532 | csrss.exe | Misc activity | ET POLICY TLS possible TOR SSL traffic |
3532 | csrss.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] TOR SSL connection |
23 ETPRO signatures available at the full report