| File name: | Order Details_pdf.exe |
| Full analysis: | https://app.any.run/tasks/59a77eab-4ae6-4a41-ae8a-04afc7f94cfb |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | November 02, 2022, 13:22:31 |
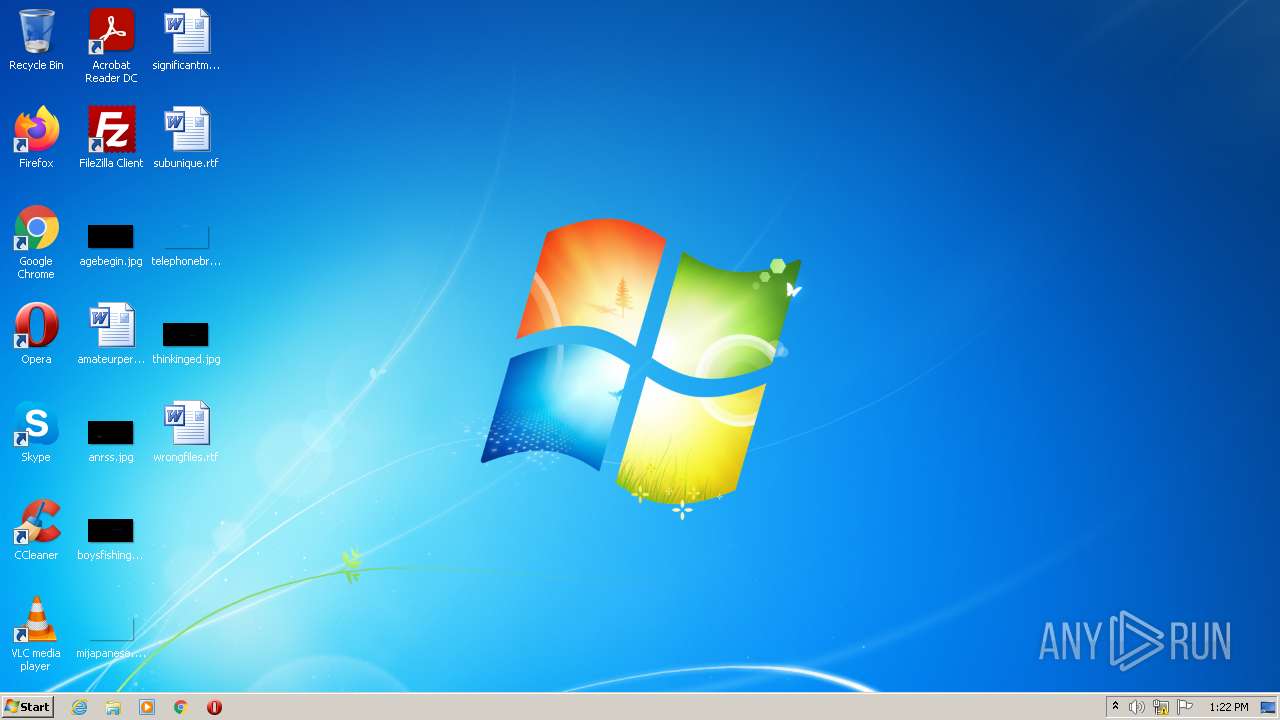
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 1894F40C29A6F1B93D214DF0698AEA22 |
| SHA1: | 29CF18B38FF329547CA9FF16DD16DB0DE6E6BDAC |
| SHA256: | 90260ACEB18D9538C91EC8739DFE72B7DBBDA8A060BDB9308AD1BDB5C2A56884 |
| SSDEEP: | 12288:kG0vouHH1J+00hr3ITAsGq65TLw4+wUfhJzv5HtF150:kGu18N3ITpIP+lv9b1 |
MALICIOUS
FORMBOOK detected by memory dumps
- wlanext.exe (PID: 2516)
Formbook is detected
- Explorer.EXE (PID: 1100)
FORMBOOK was detected
- Explorer.EXE (PID: 1100)
Connects to the CnC server
- Explorer.EXE (PID: 1100)
SUSPICIOUS
Application launched itself
- Order Details_pdf.exe (PID: 3260)
Starts CMD.EXE for commands execution
- wlanext.exe (PID: 2516)
INFO
Reads the machine GUID from the registry
- Order Details_pdf.exe (PID: 3260)
Checks supported languages
- Order Details_pdf.exe (PID: 3260)
- Order Details_pdf.exe (PID: 2064)
Reads the computer name
- Order Details_pdf.exe (PID: 3260)
- Order Details_pdf.exe (PID: 2064)
Process checks LSA protection
- Order Details_pdf.exe (PID: 3260)
Manual execution by user
- wlanext.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Formbook
(PID) Process(2516) wlanext.exe
C2www.klix.icu/d10a/�
Decoys and strings (143)USERNAME
LOCALAPPDATA
USERPROFILE
APPDATA
TEMP
ProgramFiles
CommonProgramFiles
ALLUSERSPROFILE
/c copy "
/c del "
\Run
\Policies
\Explorer
\Registry\User
\Registry\Machine
\SOFTWARE\Microsoft\Windows\CurrentVersion
Office\15.0\Outlook\Profiles\Outlook\
NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\
\SOFTWARE\Mozilla\Mozilla
\Mozilla
Username:
Password:
formSubmitURL
usernameField
encryptedUsername
encryptedPassword
\logins.json
\signons.sqlite
\Microsoft\Vault\
SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins
\Google\Chrome\User Data\Default\Login Data
SELECT origin_url, username_value, password_value FROM logins
.exe
.com
.scr
.pif
.cmd
.bat
ms
win
gdi
mfc
vga
igfx
user
help
config
update
regsvc
chkdsk
systray
audiodg
certmgr
autochk
taskhost
colorcpl
services
IconCache
ThumbCache
Cookies
SeDebugPrivilege
SeShutdownPrivilege
\BaseNamedObjects
config.php
POST
HTTP/1.1
Host:
Connection: close
Content-Length:
Cache-Control: no-cache
Origin: http://
User-Agent: Mozilla Firefox/4.0
Content-Type: application/x-www-form-urlencoded
Accept: */*
Referer: http://
Accept-Language: en-US
Accept-Encoding: gzip, deflate
dat=
f-start
tprgamesslot.com
1wautomarketing.shop
jnfc.bar
reelestate.info
coolvenead.buzz
am2pmconstruction.com
casasbh-digital.com
kmzu.info
magabestonline.com
evdirect.net
utaxi.app
gamemakr.tech
klsxofficial.com
qfaw.mom
bwchosting.com
joseli.xyz
carnelianintimates.com
manarnews.site
axacpe.click
pinupmeals.click
libraryetherealprocess.xyz
tinchap-nganhang.biz
insurancestrategy.agency
dirty-cobra.com
charee.shop
buycheap-cialisonline.net
piecepty.xyz
indocan.info
goldenkeywholesale.com
goremtnbuilders.com
viberteacher.net
s3change.com
moony00tsnft.xyz
gnhousing.com
nasigoreng.online
xraytoys.online
52127.top
tariboamandanigltd.com
nmckyiqsi.top
97238.vip
hsgtw.xyz
jeron.top
animusclothes.com
overhound.xyz
colombiabusca.store
hh42.shop
amb978.club
sec-28082672co.info
youla-secure.ltd
mfaoil-solar.net
marketingyourbrand.dev
larosewashington.site
js-design.info
hkkwmhwv.site
imandkrstore.com
94kv.com
cryptocurrency.haus
zabloudil.website
583535.xyz
businesscapitaladvisor.site
ky9466.com
iklepas.com
seamossexpress.store
bydglobal.online
f-end
Modules (42)kernel32.dll
advapi32.dll
ws2_32.dll
svchost.exe
msiexec.exe
wuauclt.exe
lsass.exe
wlanext.exe
msg.exe
lsm.exe
dwm.exe
help.exe
chkdsk.exe
cmmon32.exe
nbtstat.exe
spoolsv.exe
rdpclip.exe
control.exe
taskhost.exe
rundll32.exe
systray.exe
audiodg.exe
wininit.exe
services.exe
autochk.exe
autoconv.exe
autofmt.exe
cmstp.exe
colorcpl.exe
cscript.exe
explorer.exe
WWAHost.exe
ipconfig.exe
msdt.exe
mstsc.exe
NAPSTAT.EXE
netsh.exe
NETSTAT.EXE
raserver.exe
wscript.exe
wuapp.exe
cmd.exe
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2022-Nov-02 01:24:37 |
| Comments: | - |
| CompanyName: | Microsoft |
| FileDescription: | MyTraceListener |
| FileVersion: | 1.0.0.0 |
| InternalName: | kJiSG.exe |
| LegalCopyright: | Copyright © Microsoft 2011 |
| LegalTrademarks: | - |
| OriginalFilename: | kJiSG.exe |
| ProductName: | MyTraceListener |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2022-Nov-02 01:24:37 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 501140 | 501248 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95398 |
.rsrc | 516096 | 6052 | 6144 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.95162 |
.reloc | 524288 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.55973 | 4392 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 1.51664 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 3.31374 | 840 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#3) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
37
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1100 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2064 | "C:\Users\admin\AppData\Local\Temp\Order Details_pdf.exe" | C:\Users\admin\AppData\Local\Temp\Order Details_pdf.exe | — | Order Details_pdf.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: MyTraceListener Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2516 | "C:\Windows\System32\wlanext.exe" | C:\Windows\System32\wlanext.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wireless LAN 802.11 Extensibility Framework Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
Formbook(PID) Process(2516) wlanext.exe C2www.klix.icu/d10a/� Decoys and strings (143)USERNAME LOCALAPPDATA USERPROFILE APPDATA TEMP ProgramFiles CommonProgramFiles ALLUSERSPROFILE /c copy " /c del " \Run \Policies \Explorer \Registry\User \Registry\Machine \SOFTWARE\Microsoft\Windows\CurrentVersion Office\15.0\Outlook\Profiles\Outlook\ NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\ \SOFTWARE\Mozilla\Mozilla \Mozilla Username: Password: formSubmitURL usernameField encryptedUsername encryptedPassword \logins.json \signons.sqlite \Microsoft\Vault\ SELECT encryptedUsername, encryptedPassword, formSubmitURL FROM moz_logins \Google\Chrome\User Data\Default\Login Data SELECT origin_url, username_value, password_value FROM logins .exe .com .scr .pif .cmd .bat ms win gdi mfc vga igfx user help config update regsvc chkdsk systray audiodg certmgr autochk taskhost colorcpl services IconCache ThumbCache Cookies SeDebugPrivilege SeShutdownPrivilege \BaseNamedObjects config.php POST HTTP/1.1 Host: Connection: close Content-Length: Cache-Control: no-cache Origin: http:// User-Agent: Mozilla Firefox/4.0 Content-Type: application/x-www-form-urlencoded Accept: */* Referer: http:// Accept-Language: en-US Accept-Encoding: gzip, deflate
dat= f-start tprgamesslot.com 1wautomarketing.shop jnfc.bar reelestate.info coolvenead.buzz am2pmconstruction.com casasbh-digital.com kmzu.info magabestonline.com evdirect.net utaxi.app gamemakr.tech klsxofficial.com qfaw.mom bwchosting.com joseli.xyz carnelianintimates.com manarnews.site axacpe.click pinupmeals.click libraryetherealprocess.xyz tinchap-nganhang.biz insurancestrategy.agency dirty-cobra.com charee.shop buycheap-cialisonline.net piecepty.xyz indocan.info goldenkeywholesale.com goremtnbuilders.com viberteacher.net s3change.com moony00tsnft.xyz gnhousing.com nasigoreng.online xraytoys.online 52127.top tariboamandanigltd.com nmckyiqsi.top 97238.vip hsgtw.xyz jeron.top animusclothes.com overhound.xyz colombiabusca.store hh42.shop amb978.club sec-28082672co.info youla-secure.ltd mfaoil-solar.net marketingyourbrand.dev larosewashington.site js-design.info hkkwmhwv.site imandkrstore.com 94kv.com cryptocurrency.haus zabloudil.website 583535.xyz businesscapitaladvisor.site ky9466.com iklepas.com seamossexpress.store bydglobal.online f-end Modules (42)kernel32.dll advapi32.dll ws2_32.dll svchost.exe msiexec.exe wuauclt.exe lsass.exe wlanext.exe msg.exe lsm.exe dwm.exe help.exe chkdsk.exe cmmon32.exe nbtstat.exe spoolsv.exe rdpclip.exe control.exe taskhost.exe rundll32.exe systray.exe audiodg.exe wininit.exe services.exe autochk.exe autoconv.exe autofmt.exe cmstp.exe colorcpl.exe cscript.exe explorer.exe WWAHost.exe ipconfig.exe msdt.exe mstsc.exe NAPSTAT.EXE netsh.exe NETSTAT.EXE raserver.exe wscript.exe wuapp.exe cmd.exe | |||||||||||||||
| 3192 | /c del "C:\Users\admin\AppData\Local\Temp\Order Details_pdf.exe" | C:\Windows\System32\cmd.exe | — | wlanext.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\Order Details_pdf.exe" | C:\Users\admin\AppData\Local\Temp\Order Details_pdf.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: MyTraceListener Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
108
Read events
108
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
8
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1100 | Explorer.EXE | GET | 403 | 34.149.198.43:80 | http://www.94kv.com/d10a/?uHlP7BMX=RvVjxIMyBfoAw6PAKNepAjoRrZYbkIvZdwiZIms2/YWDi9lqfYhimwtyTcy83ZqWxdac/g==&BZl=7notQhB | US | html | 300 b | malicious |
1100 | Explorer.EXE | GET | 404 | 109.68.33.25:80 | http://www.am2pmconstruction.com/d10a/?uHlP7BMX=JsKbbAjBq0takqQODXNBQ49io7/mGeZLb6l4pnnVO+r76ci7i4yB5S+Iy39gcAH6LkxJSQ==&BZl=7notQhB | GB | html | 1.22 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 109.68.33.25:80 | www.am2pmconstruction.com | Host Europe GmbH | GB | malicious |
1100 | Explorer.EXE | 34.149.198.43:80 | www.94kv.com | GOOGLE | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.coolvenead.buzz |
| unknown |
dns.msftncsi.com |
| shared |
www.am2pmconstruction.com |
| malicious |
www.94kv.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1100 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1100 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1100 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1100 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1100 | Explorer.EXE | Generic Protocol Command Decode | SURICATA HTTP Unexpected Request body |
1100 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1100 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |
1100 | Explorer.EXE | A Network Trojan was detected | ET TROJAN FormBook CnC Checkin (GET) |