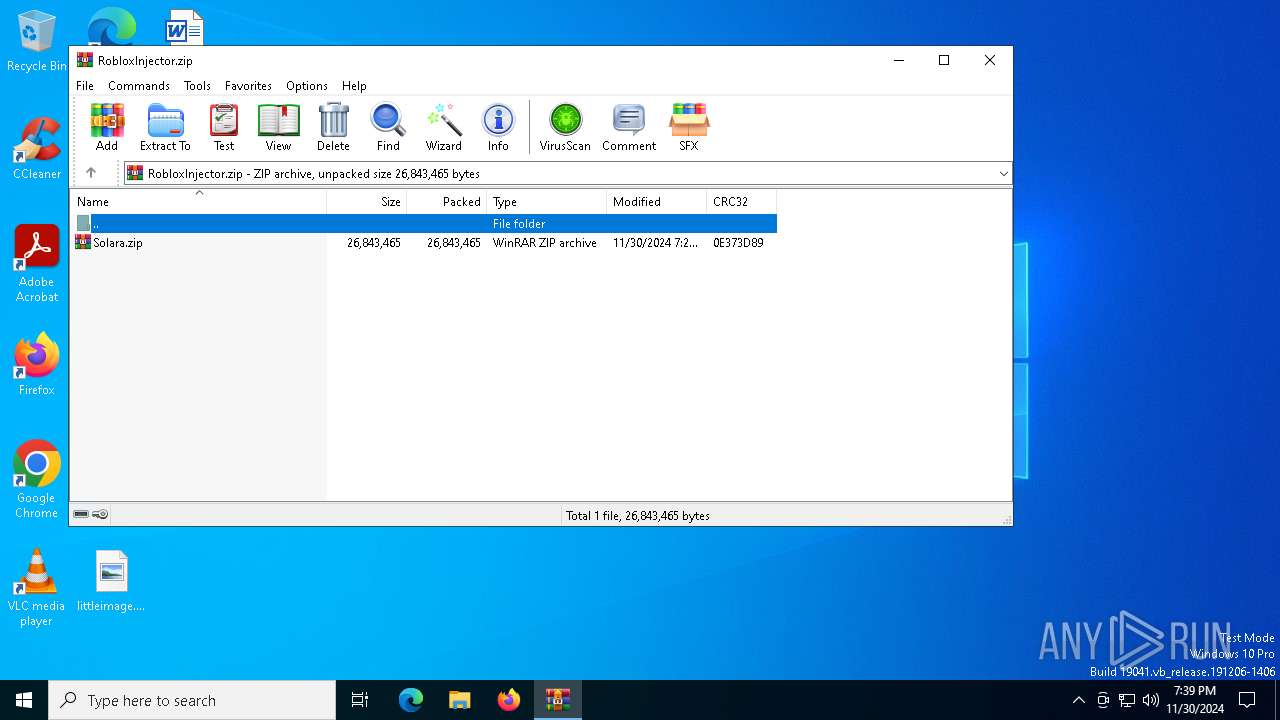
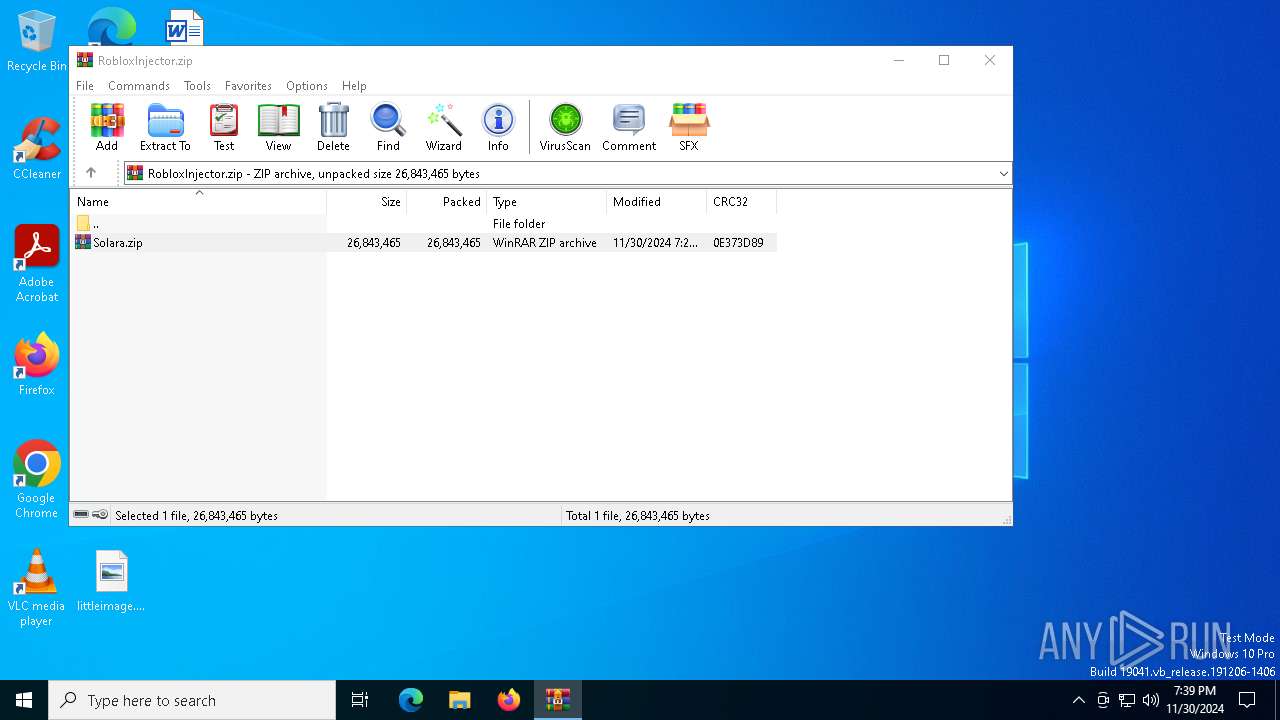
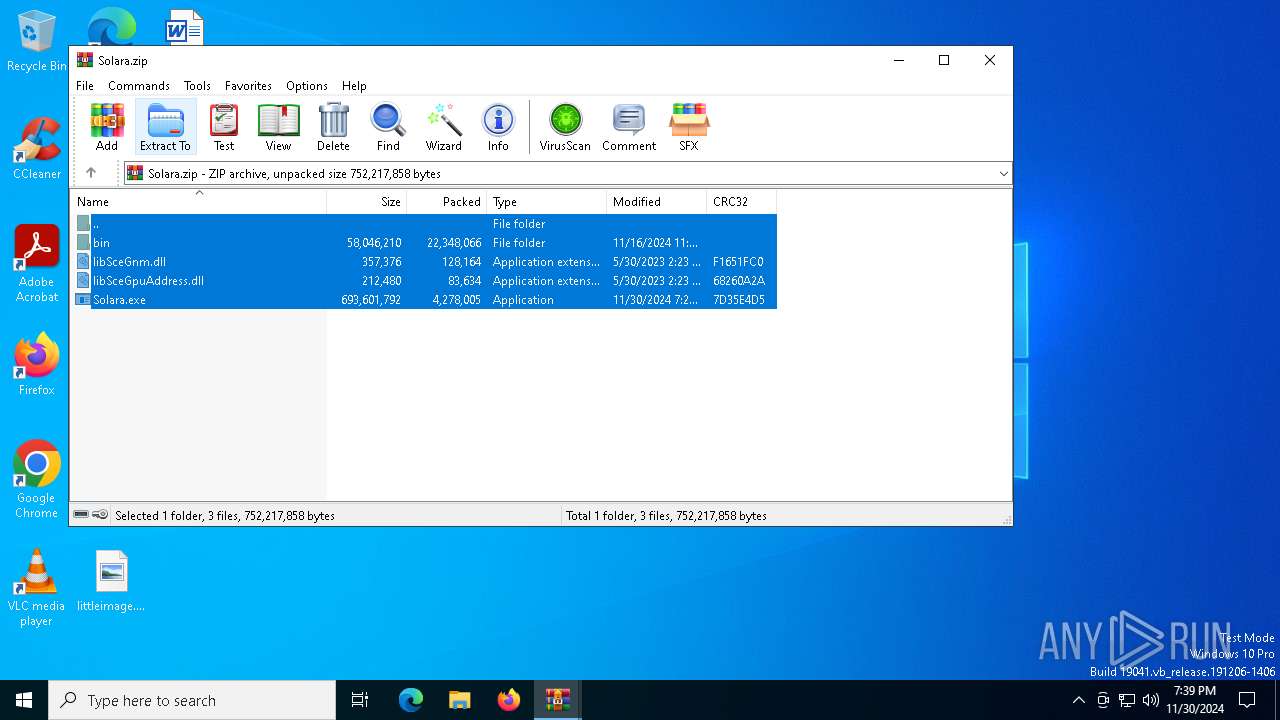
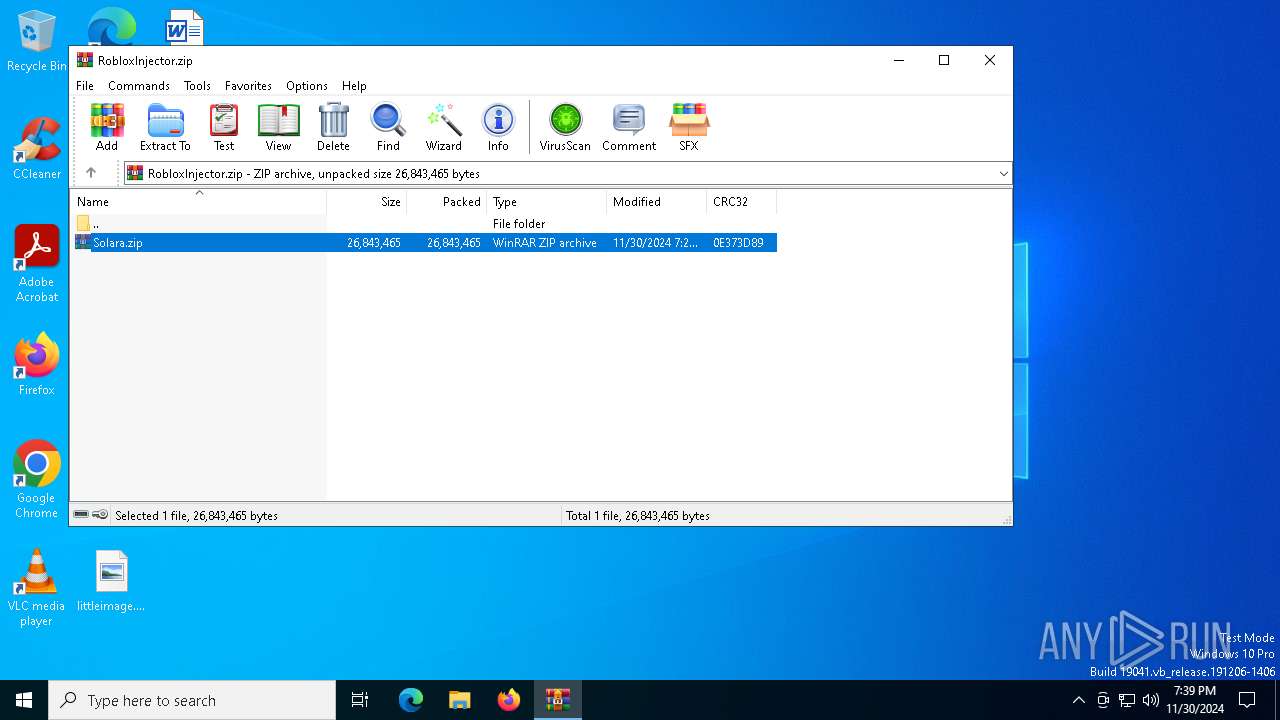
| download: | /bow16nelson/Solara-Executor-Roblox/releases/download/Enjoy!/RobloxInjector.zip |
| Full analysis: | https://app.any.run/tasks/9a2d490b-4952-4ace-a4ac-253ab4d06dd0 |
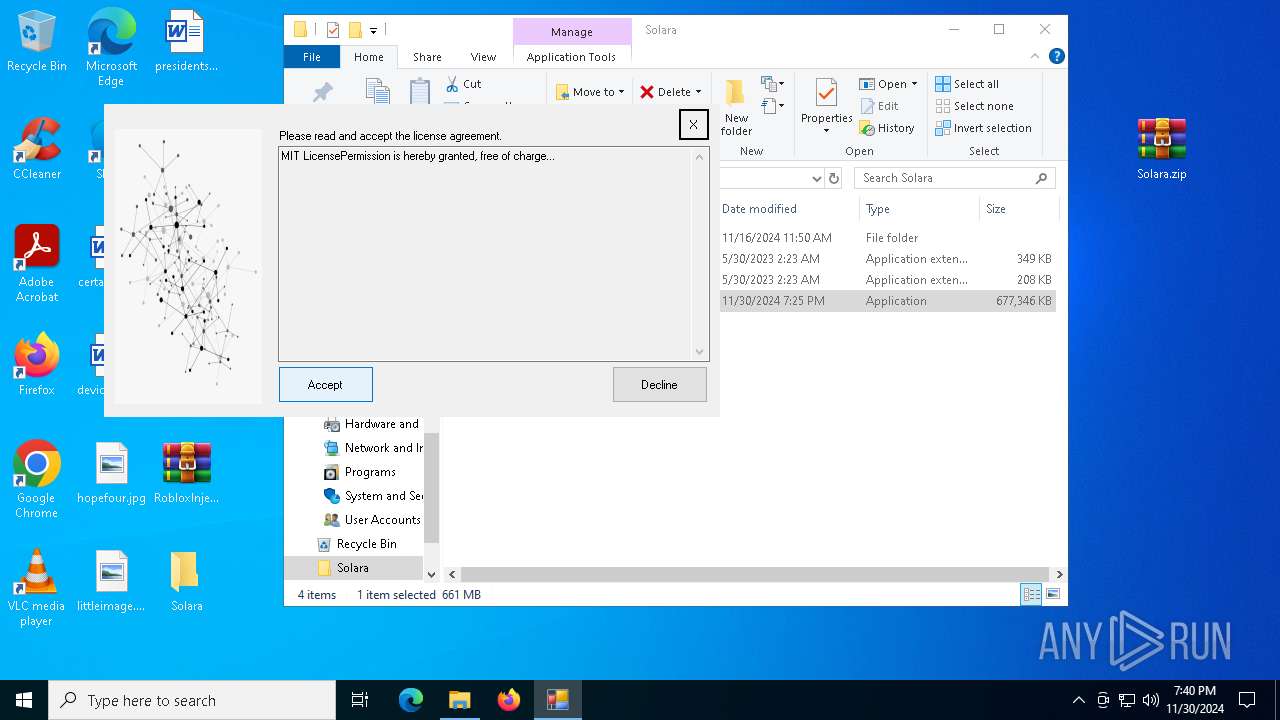
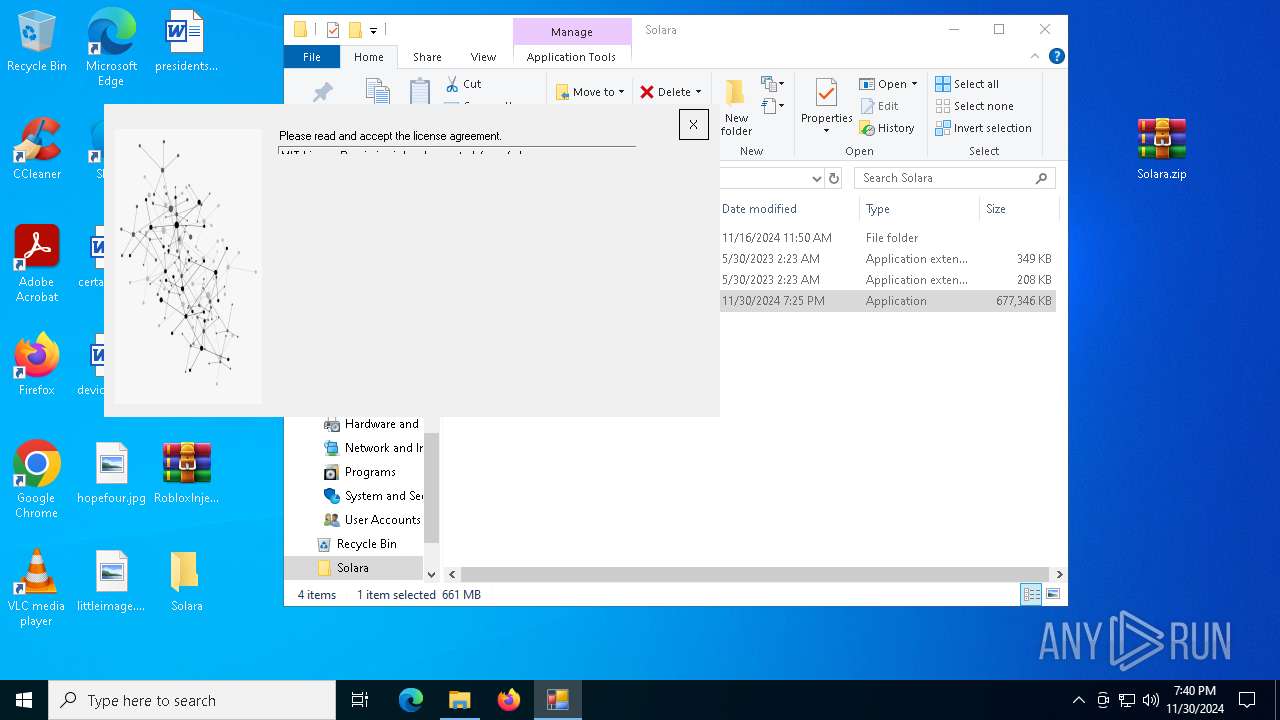
| Verdict: | Malicious activity |
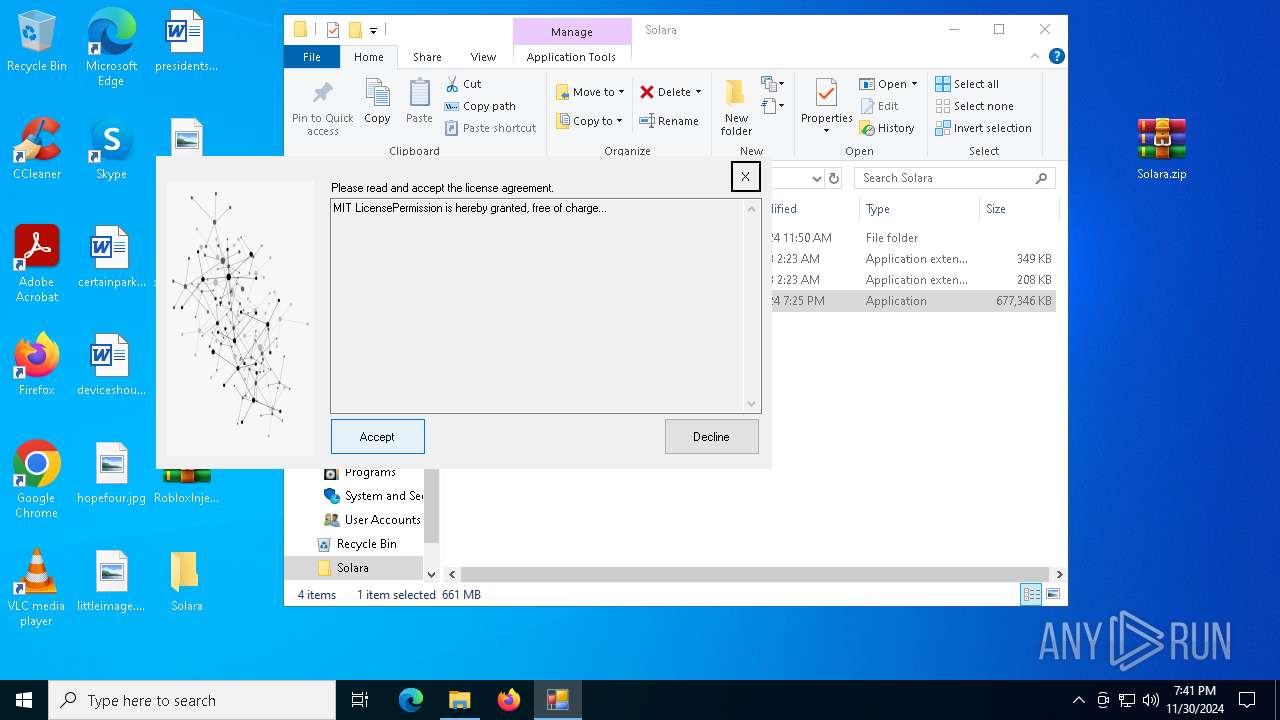
| Threats: | Meduza Stealer is an information-stealing malware primarily targeting Windows systems, designed to harvest sensitive data such as login credentials, browsing histories, cookies, cryptocurrency wallets, and password manager data. It has advanced anti-detection mechanisms, allowing it to evade many antivirus programs. The malware is distributed through various means, including phishing emails and malicious links. It’s marketed on underground forums and Telegram channels. |
| Analysis date: | November 30, 2024, 19:39:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 5A2CDBCC82C80A5181618C40844F0766 |
| SHA1: | E8F8439D49EF5AF776271685191B665F20554A30 |
| SHA256: | 8FAD9CED8EEF4B980C51ECA9F5B2B1095B69DE9DFE204592CA99782102169C37 |
| SSDEEP: | 196608:NslLlXJl2geFA3NIg0gjWKQyLIwdk4wUfU0X+IJ28q2jK/NoEmy9p87B:WkgCgzKwiJUf9+mJqkSSy9O7B |
MALICIOUS
Steals credentials from Web Browsers
- installer.exe (PID: 6332)
MEDUZASTEALER has been detected (SURICATA)
- installer.exe (PID: 6332)
Actions looks like stealing of personal data
- installer.exe (PID: 6332)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 6812)
- WinRAR.exe (PID: 7156)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6812)
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Application launched itself
- WinRAR.exe (PID: 6812)
The process creates files with name similar to system file names
- WinRAR.exe (PID: 7156)
Checks Windows Trust Settings
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
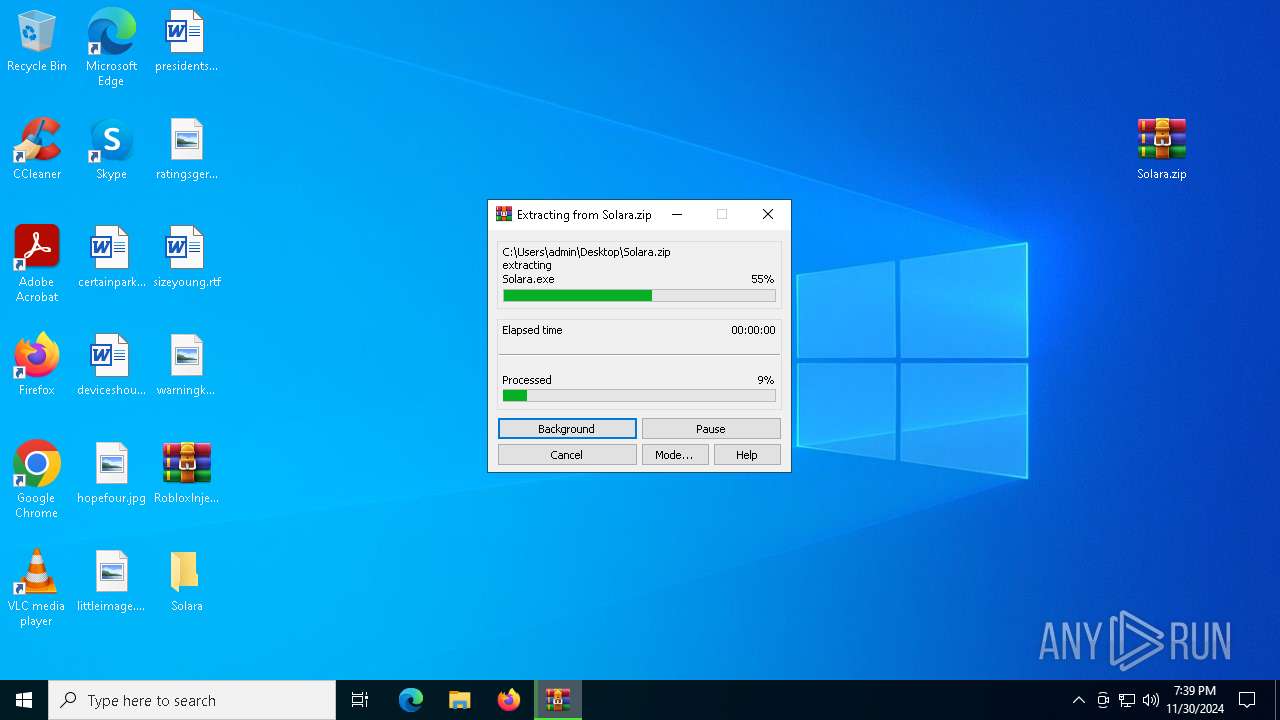
Executable content was dropped or overwritten
- Solara.exe (PID: 2452)
Searches for installed software
- installer.exe (PID: 6332)
Reads the date of Windows installation
- Solara.exe (PID: 2452)
Checks for external IP
- installer.exe (PID: 6332)
Connects to unusual port
- installer.exe (PID: 6332)
The process connected to a server suspected of theft
- installer.exe (PID: 6332)
INFO
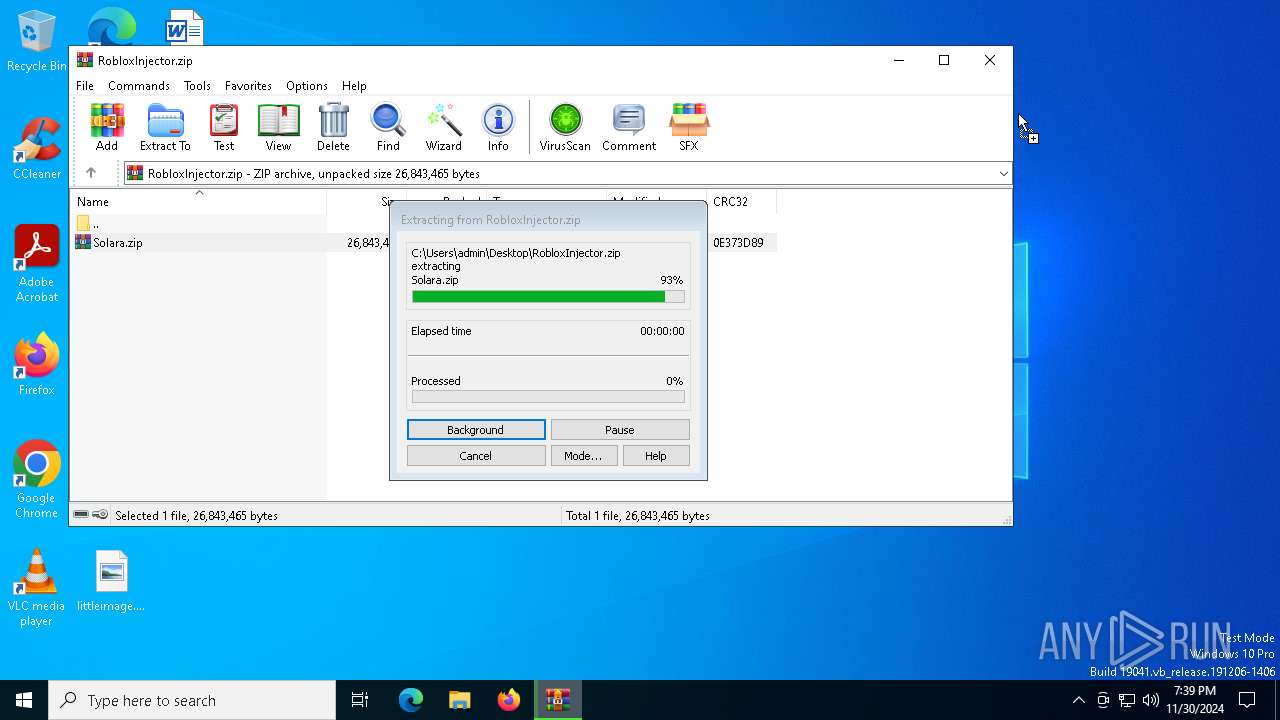
The process uses the downloaded file
- WinRAR.exe (PID: 6812)
- WinRAR.exe (PID: 7156)
- Solara.exe (PID: 2452)
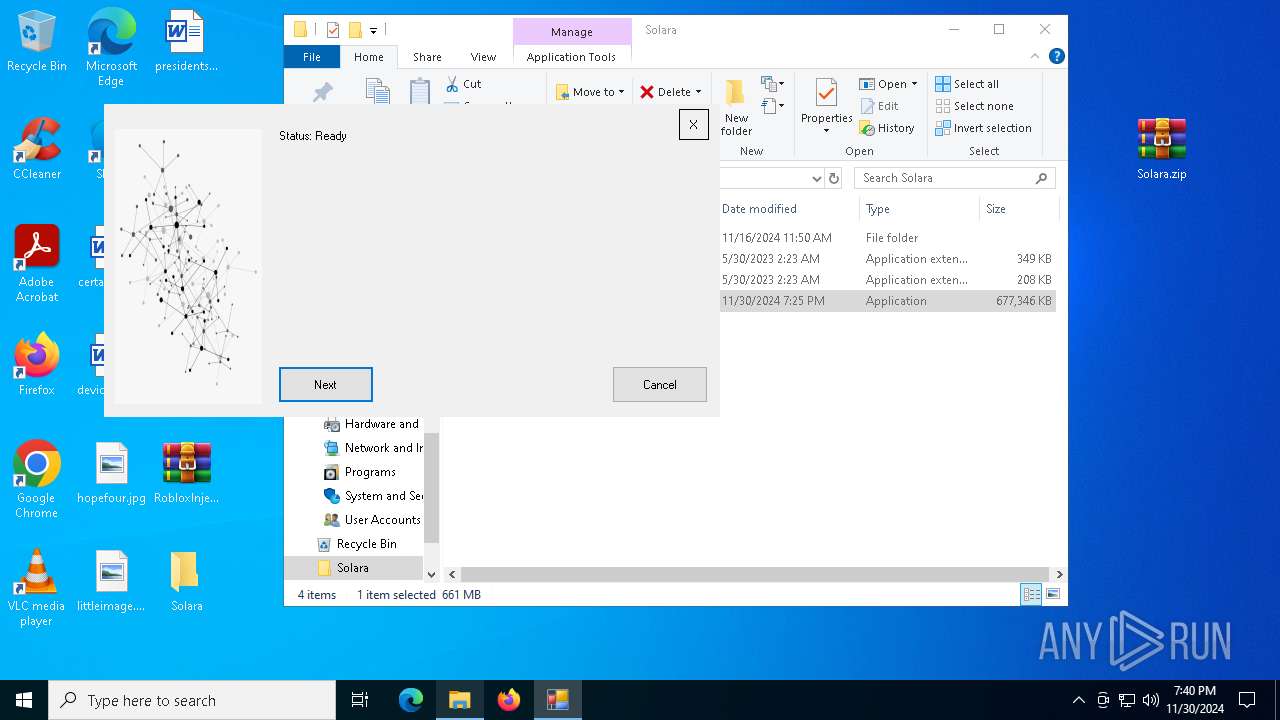
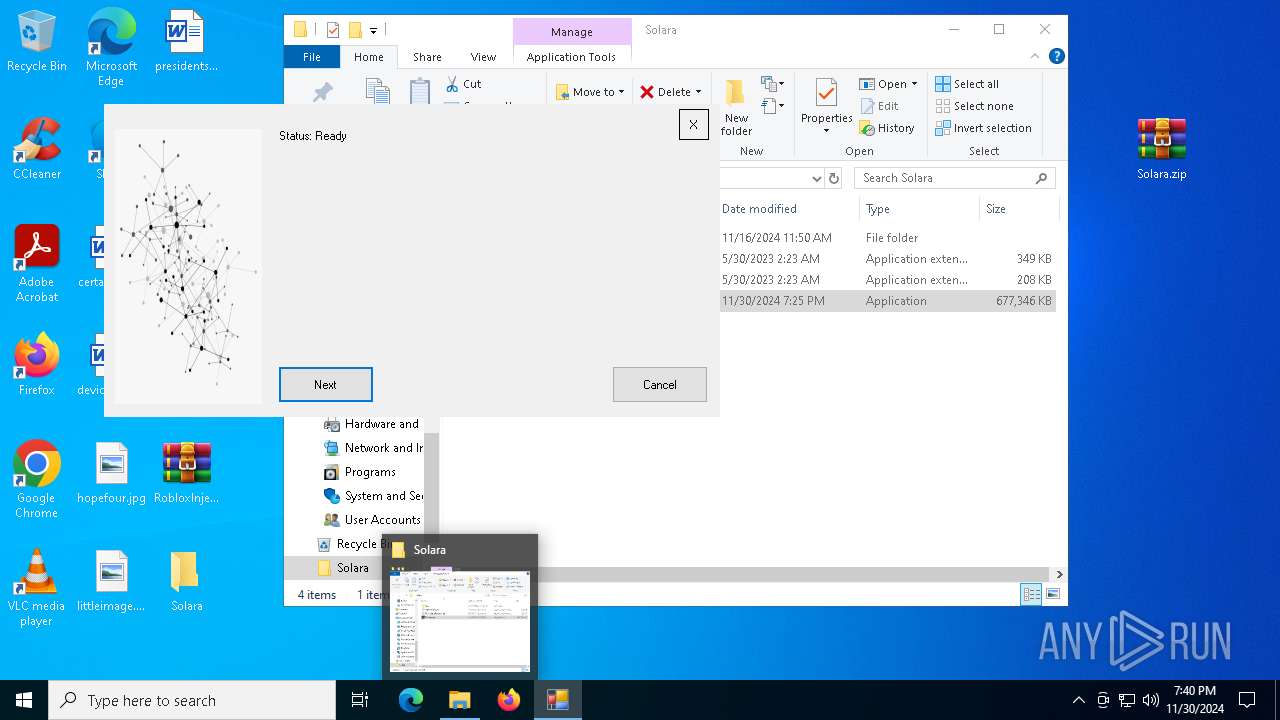
Manual execution by a user
- WinRAR.exe (PID: 7156)
- Solara.exe (PID: 2452)
- Solara.exe (PID: 520)
- Solara.exe (PID: 6936)
- Solara.exe (PID: 7120)
- Solara.exe (PID: 6256)
- Solara.exe (PID: 5432)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7156)
Checks supported languages
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Reads the computer name
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Create files in a temporary directory
- Solara.exe (PID: 2452)
Reads Environment values
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Disables trace logs
- Solara.exe (PID: 2452)
Checks proxy server information
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Reads the machine GUID from the registry
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Reads the software policy settings
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Process checks computer location settings
- Solara.exe (PID: 2452)
- installer.exe (PID: 6332)
Reads product name
- installer.exe (PID: 6332)
Reads the time zone
- installer.exe (PID: 6332)
Creates files or folders in the user directory
- installer.exe (PID: 6332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:11:30 22:28:28 |
| ZipCRC: | 0x0e373d89 |
| ZipCompressedSize: | 26843465 |
| ZipUncompressedSize: | 26843465 |
| ZipFileName: | Solara.zip |
Total processes
138
Monitored processes
11
Malicious processes
2
Suspicious processes
2
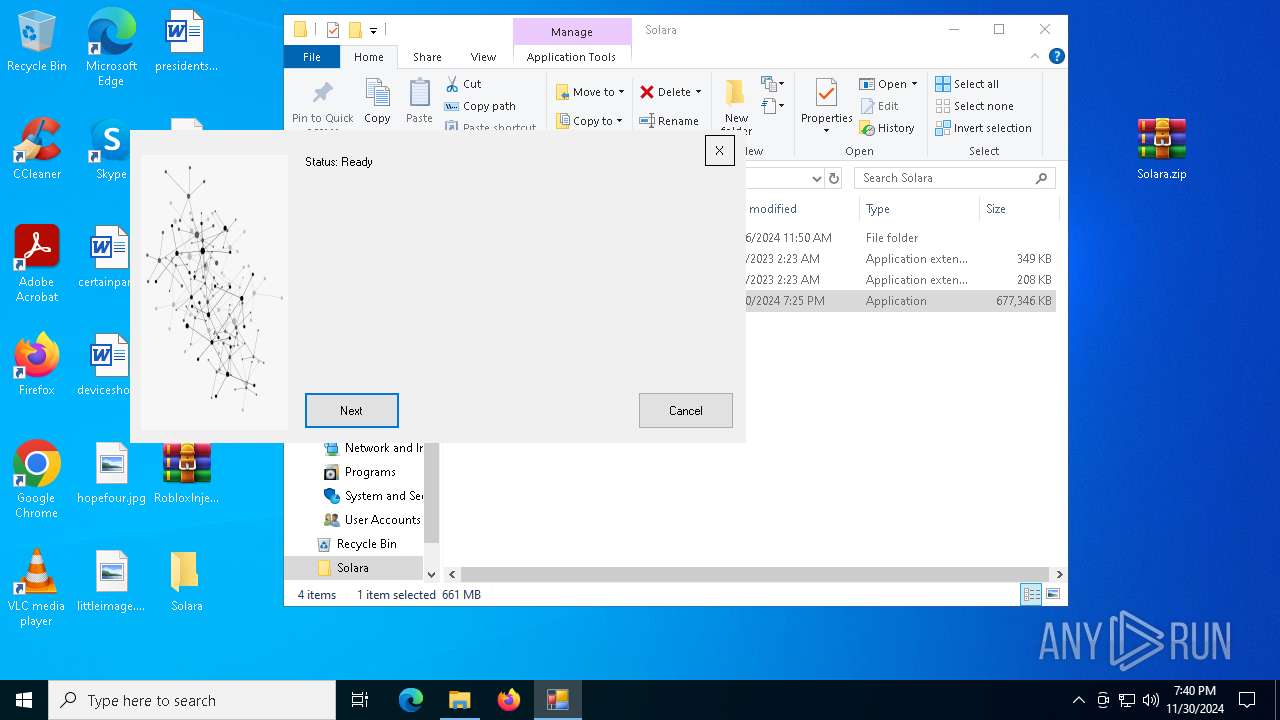
Behavior graph
Click at the process to see the details
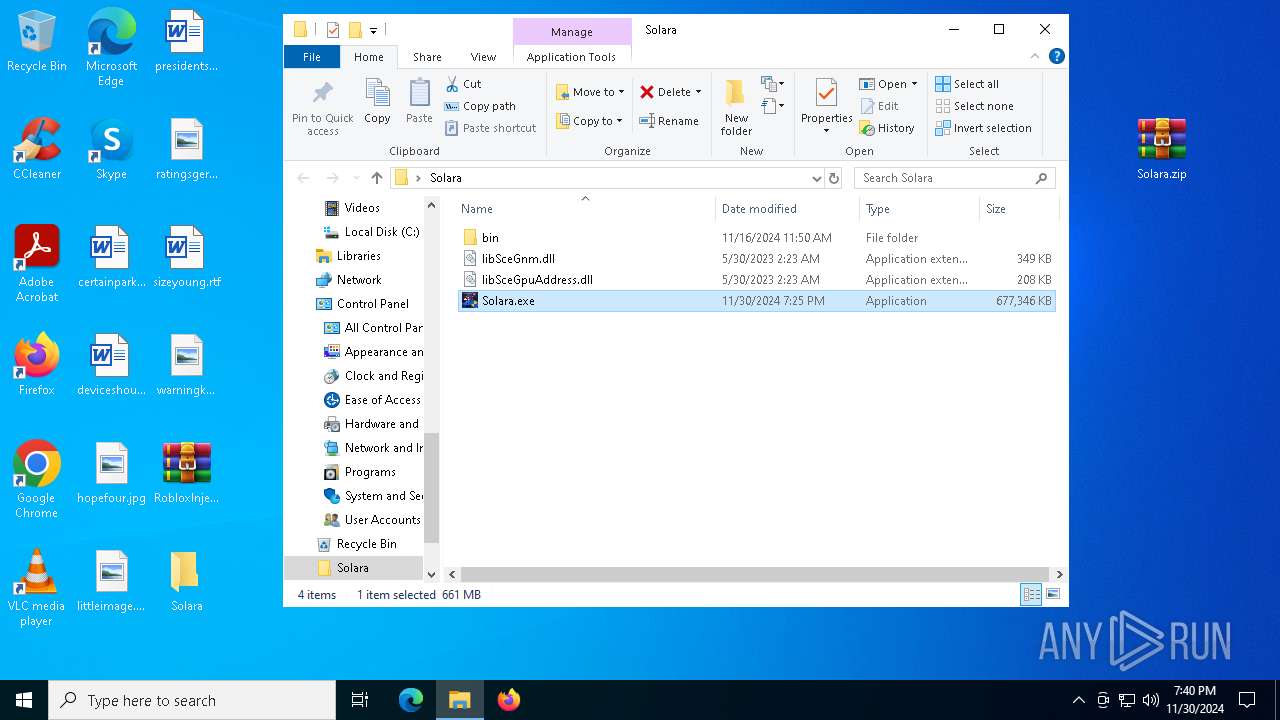
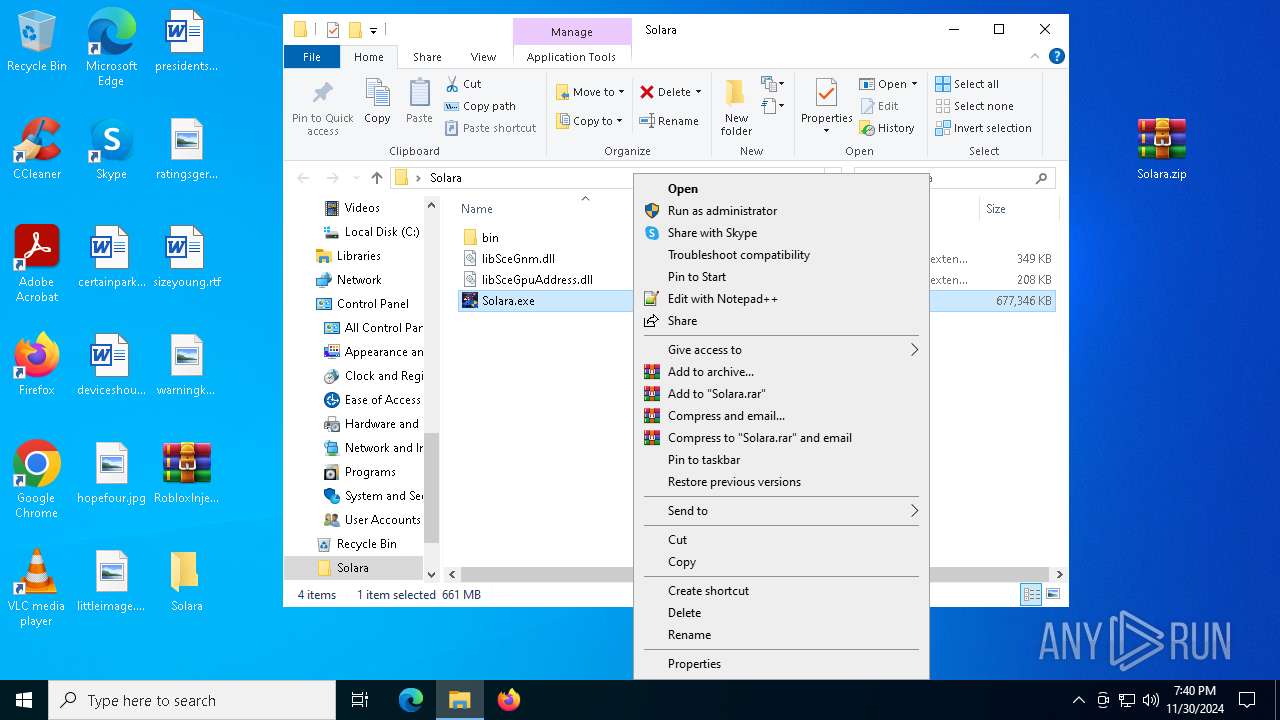
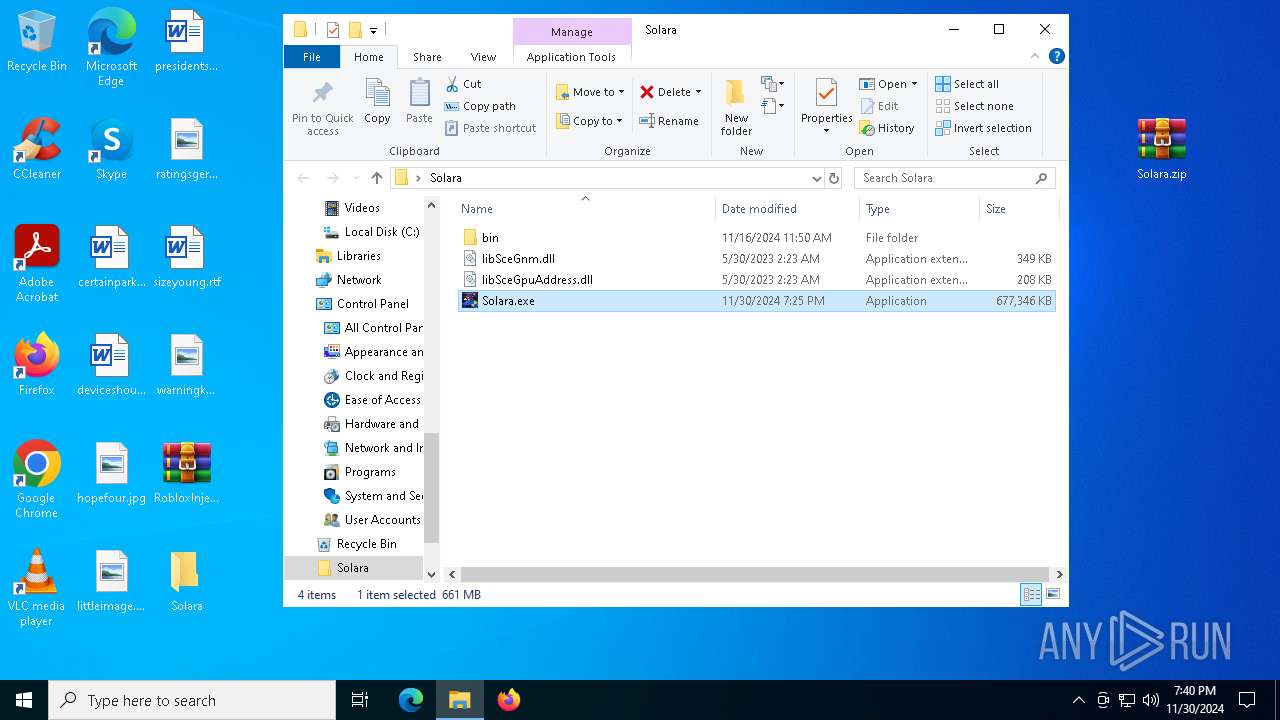
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
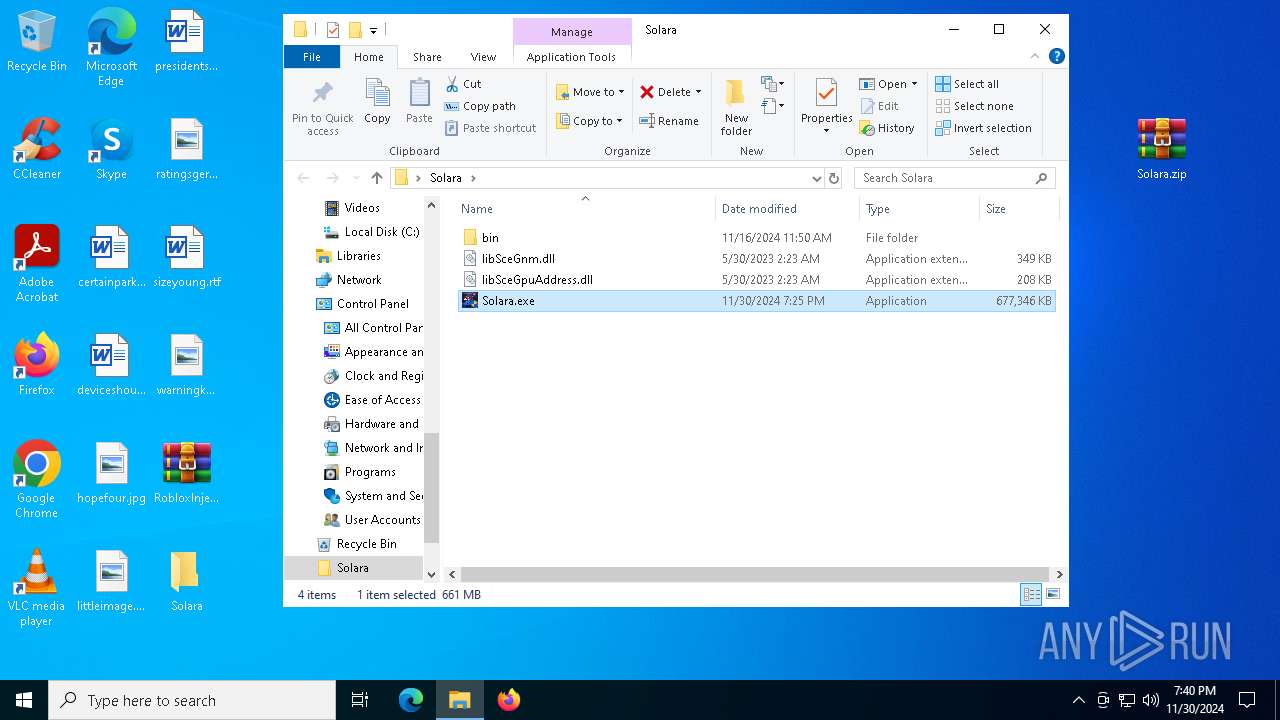
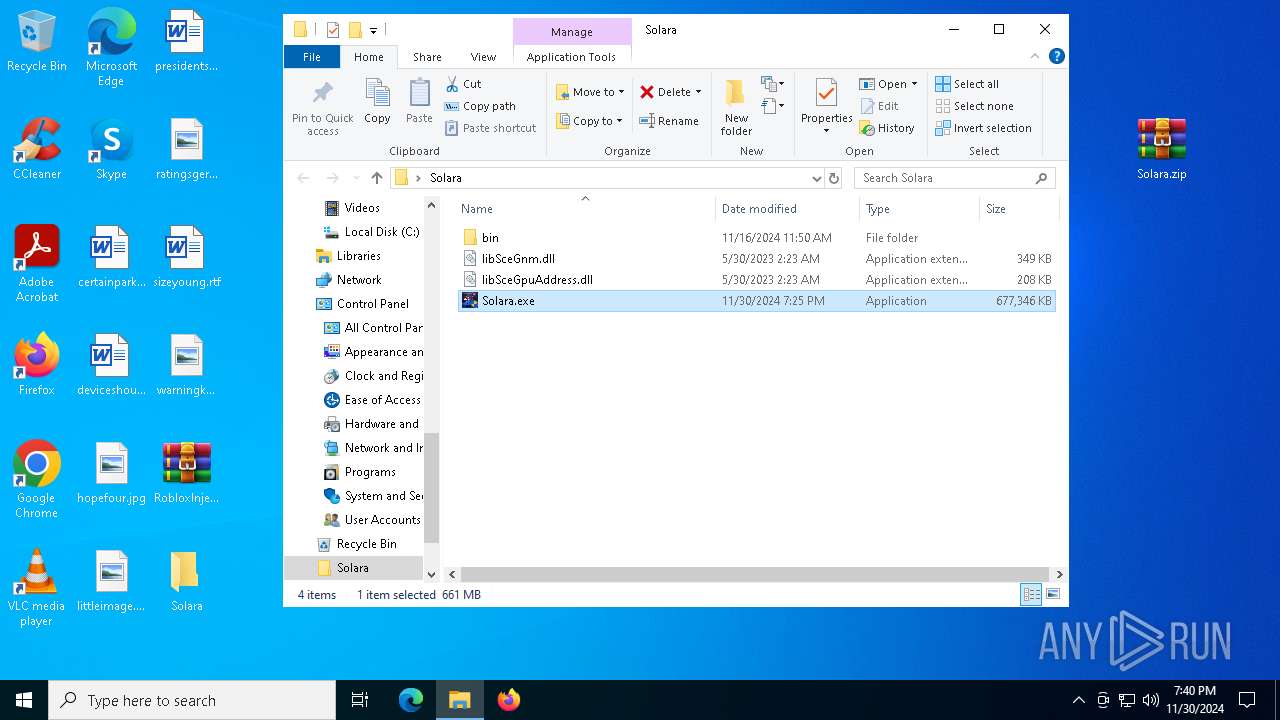
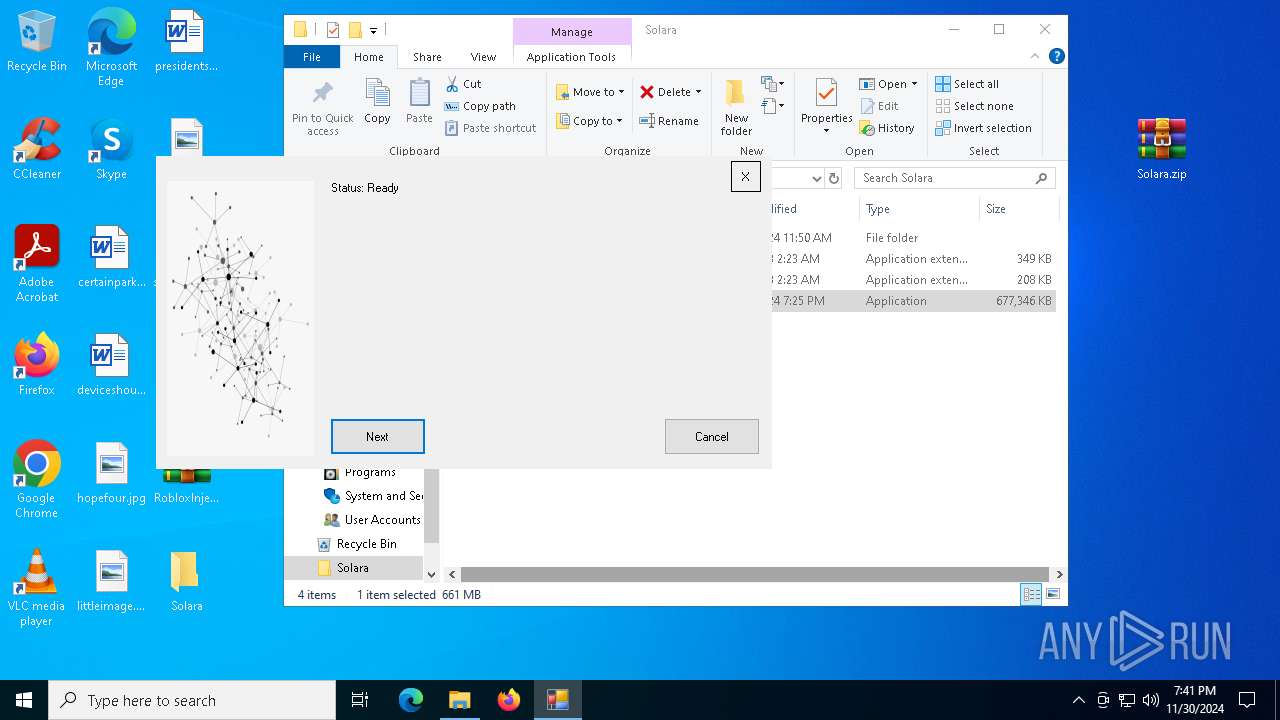
| 520 | "C:\Users\admin\Desktop\Solara\Solara.exe" | C:\Users\admin\Desktop\Solara\Solara.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AdventureHub Exit code: 3221226540 Version: 3.2.1.0 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\Desktop\Solara\Solara.exe" | C:\Users\admin\Desktop\Solara\Solara.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AdventureHub Exit code: 0 Version: 3.2.1.0 Modules
| |||||||||||||||
| 4672 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5432 | "C:\Users\admin\Desktop\Solara\Solara.exe" | C:\Users\admin\Desktop\Solara\Solara.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AdventureHub Exit code: 0 Version: 3.2.1.0 Modules
| |||||||||||||||
| 6256 | "C:\Users\admin\Desktop\Solara\Solara.exe" | C:\Users\admin\Desktop\Solara\Solara.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AdventureHub Exit code: 3221226540 Version: 3.2.1.0 Modules
| |||||||||||||||
| 6332 | "C:\Users\admin\AppData\Local\Temp\installer.exe" | C:\Users\admin\AppData\Local\Temp\installer.exe | Solara.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6812 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\RobloxInjector.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 6936 | "C:\Users\admin\Desktop\Solara\Solara.exe" | C:\Users\admin\Desktop\Solara\Solara.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AdventureHub Exit code: 3221226540 Version: 3.2.1.0 Modules
| |||||||||||||||
| 7012 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa6812.37929\Solara.zip | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7120 | "C:\Users\admin\Desktop\Solara\Solara.exe" | C:\Users\admin\Desktop\Solara\Solara.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AdventureHub Exit code: 0 Version: 3.2.1.0 Modules
| |||||||||||||||
Total events
12 092
Read events
12 038
Write events
54
Delete events
0
Modification events
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\RobloxInjector.zip | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6812) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7012) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
28
Suspicious files
8
Text files
6
Unknown types
0
Dropped files
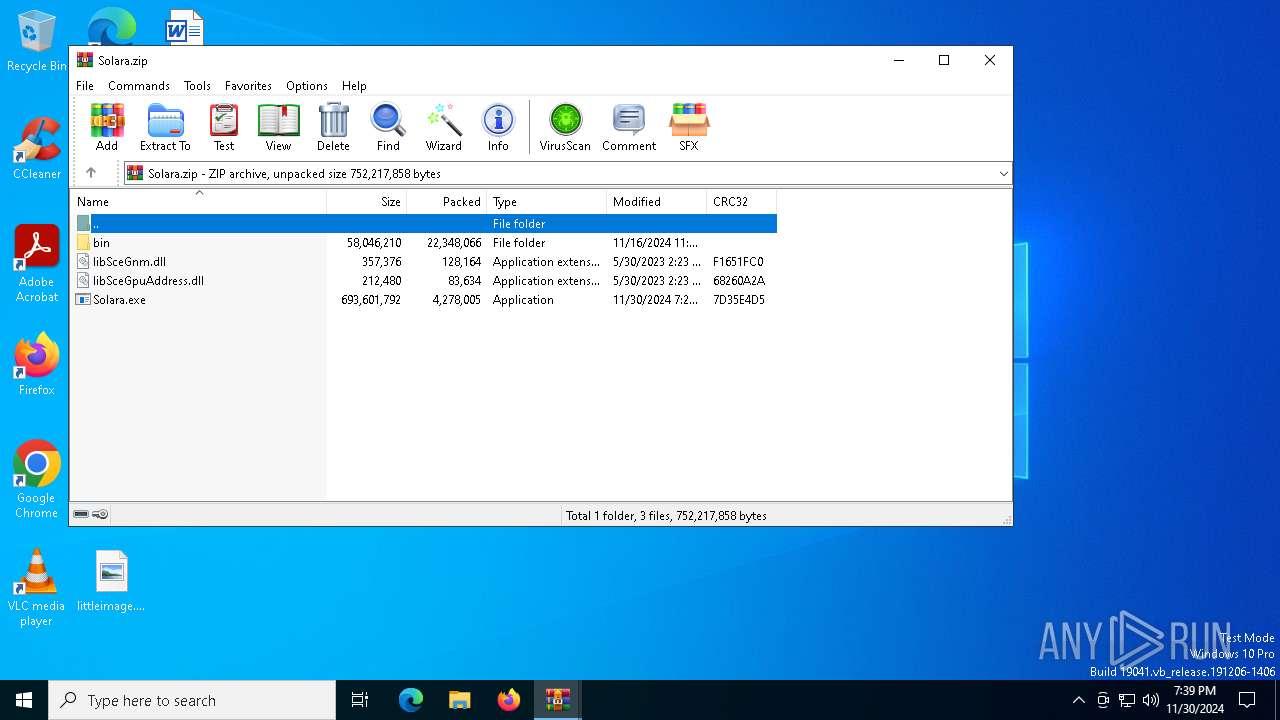
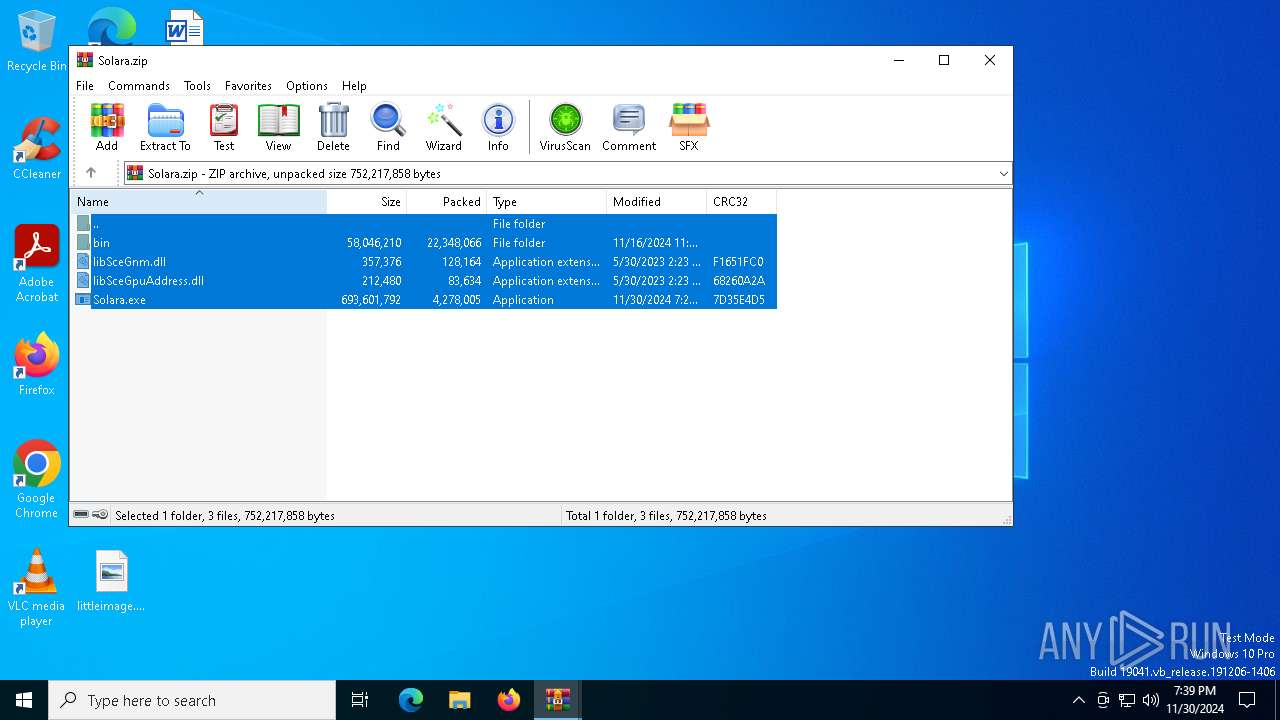
PID | Process | Filename | Type | |
|---|---|---|---|---|
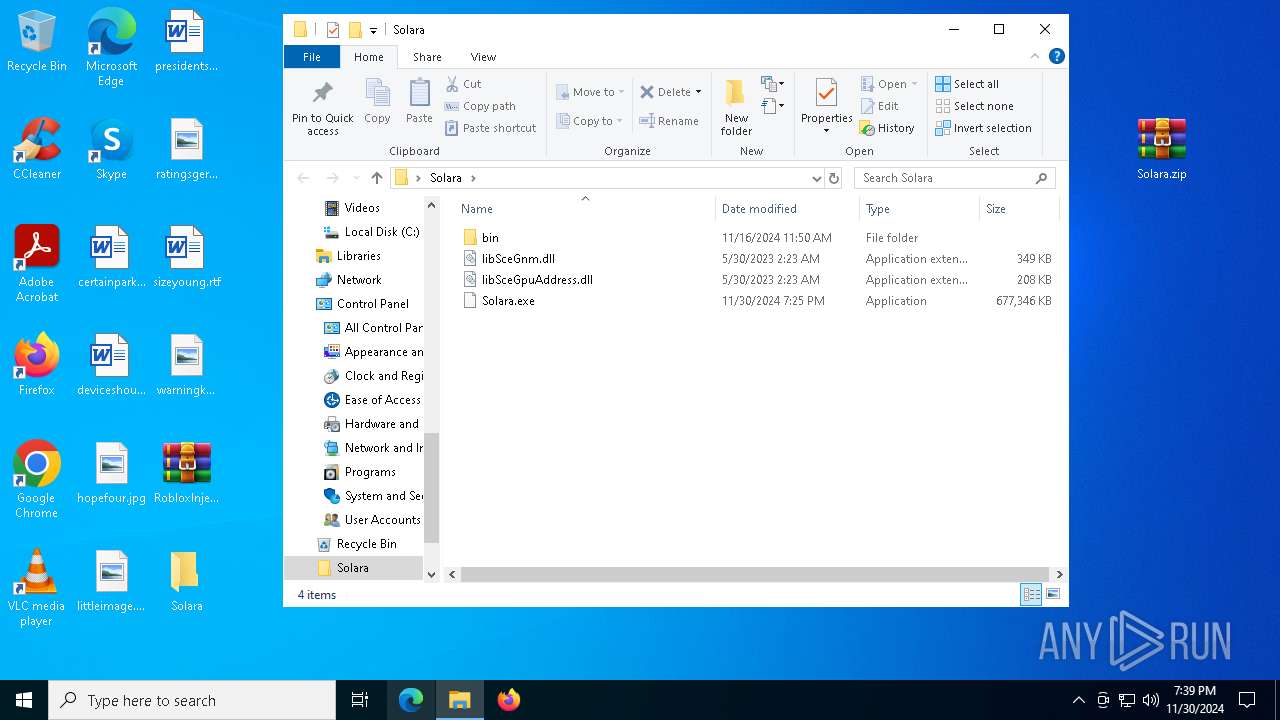
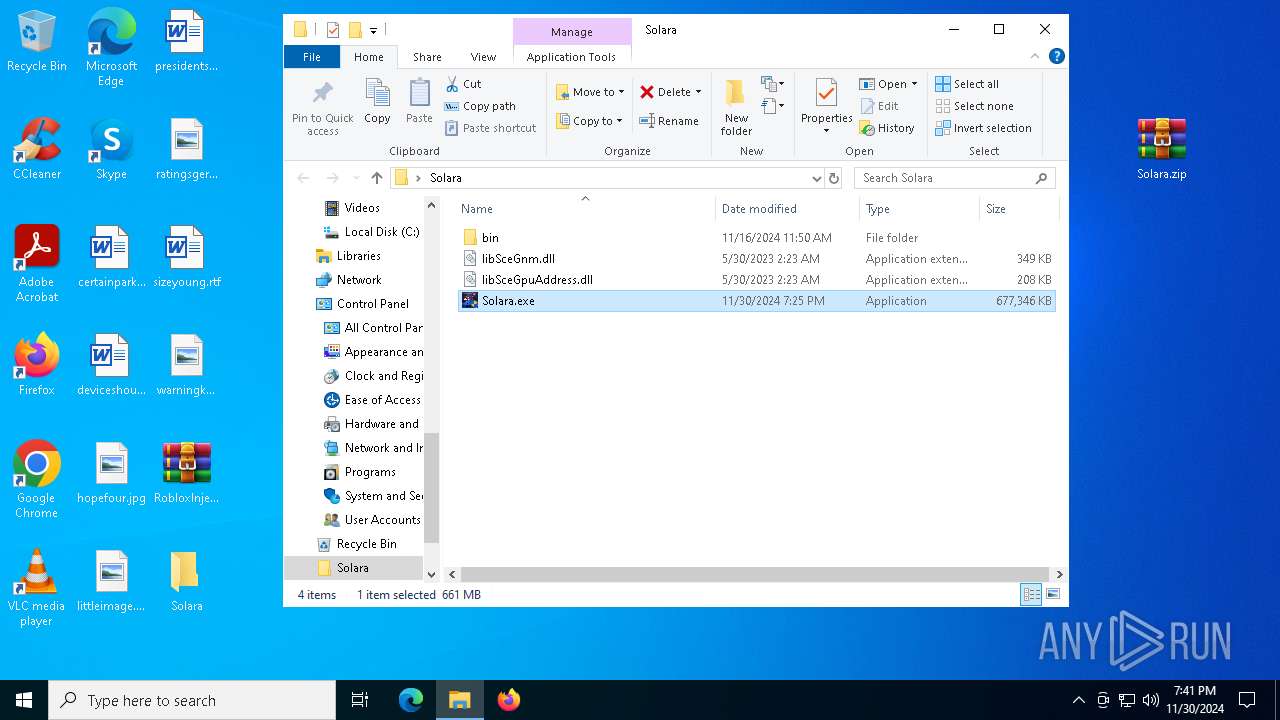
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\Solara.exe | — | |
MD5:— | SHA256:— | |||
| 6812 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6812.37929\Solara.zip | compressed | |
MD5:3E763A5B9164FA6B1764F86374171245 | SHA256:21E11E00B7ED809BDF765AD1F334FD0BA3AB2DE94CCAAA358EFDC6D6FCC40AD4 | |||
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\libSceGpuAddress.dll | executable | |
MD5:E1F0BBDB0DEB8DFE138A8DC92227E00F | SHA256:E99F1F208AFCB5186C9B27CEE362A6525CF2808F1905CB306302AB2D97817357 | |||
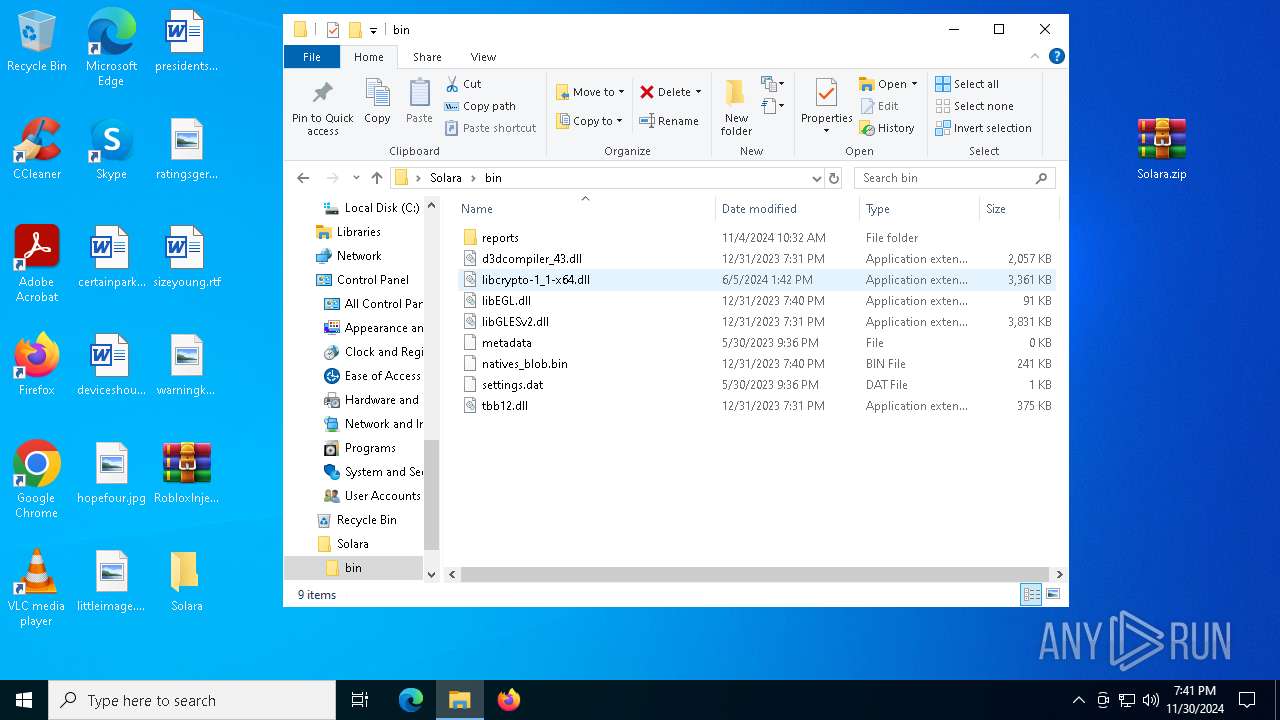
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\bin\reports\amd_ags_x64.dll | executable | |
MD5:C69E3E05BF240D7762286833E39C9029 | SHA256:2449E8339E0F031BC4F954398F5917B8EB5A2D20C32D4688A083D5DD9F637AB8 | |||
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\bin\natives_blob.bin | binary | |
MD5:94855C31F6C24656A6D67CEAE0B04CCA | SHA256:20210A0E530832A0267D584015EECB331C2AC0D841FAF7B36FEB9D326C32C113 | |||
| 6812 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6812.38887\Solara.zip | compressed | |
MD5:3E763A5B9164FA6B1764F86374171245 | SHA256:21E11E00B7ED809BDF765AD1F334FD0BA3AB2DE94CCAAA358EFDC6D6FCC40AD4 | |||
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\bin\libcrypto-1_1-x64.dll | executable | |
MD5:3390D76A13973BD46B512BF257C171C8 | SHA256:DEB034588EF43DB62809CC2C599374894BF7FEF5DF990DA6EAAA0674FBEC0301 | |||
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\bin\d3dcompiler_43.dll | executable | |
MD5:1C9B45E87528B8BB8CFA884EA0099A85 | SHA256:2F23182EC6F4889397AC4BF03D62536136C5BDBA825C7D2C4EF08C827F3A8A1C | |||
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\bin\libEGL.dll | executable | |
MD5:50C717AB7624384B2B2D8A953263BEB2 | SHA256:63580999B8210315B664E7742B6D4F59E587D20B4D0826072A5EF311C6F25B74 | |||
| 7156 | WinRAR.exe | C:\Users\admin\Desktop\Solara\bin\libGLESv2.dll | executable | |
MD5:DD3F55559CA3EB1A89E7D696C8C5DE53 | SHA256:99F261FA5A69DD2B3BD6192AAF72A0D9F88D769A311FAC87963658A7573EC669 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
43
DNS requests
23
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6508 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
3620 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6332 | installer.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/gsr1.crl | US | binary | 1.70 Kb | whitelisted |
3620 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
6332 | installer.exe | GET | 200 | 142.250.186.35:80 | http://c.pki.goog/r/r4.crl | US | binary | 436 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
440 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.32.134:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6332 | installer.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2192 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
6332 | installer.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
6332 | installer.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Meduza Stealer Exfiltration M1 |
6332 | installer.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Meduza Stealer Exfiltration M1 |
6332 | installer.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Meduza Stealer |
6332 | installer.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Meduza Stealer |
6332 | installer.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
6332 | installer.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |
6332 | installer.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Possible Meduza Stealer Exfiltration (TCP) |