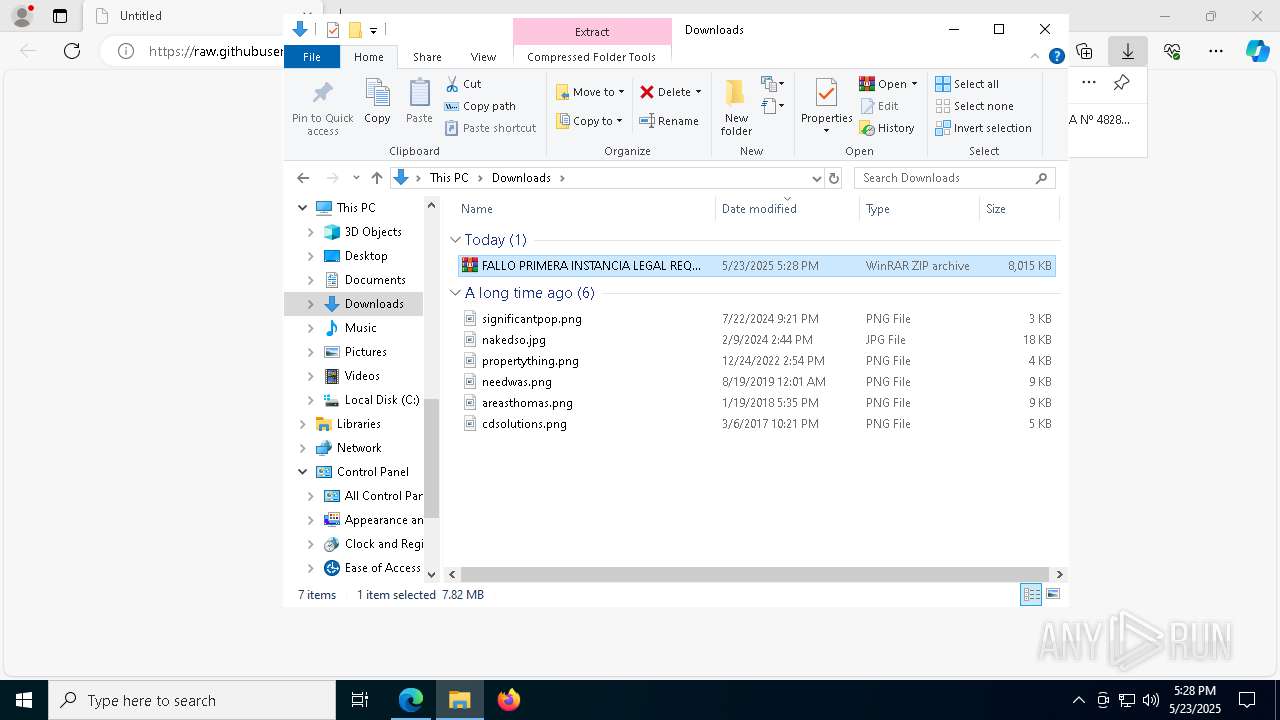
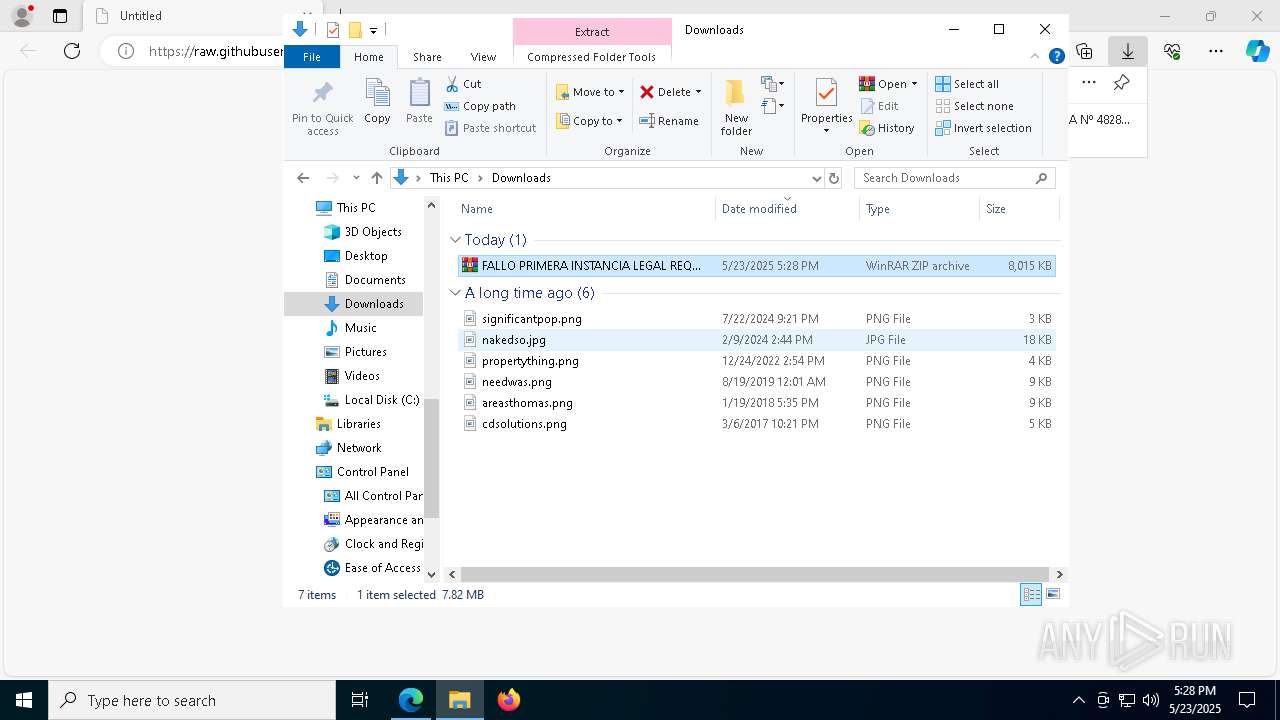
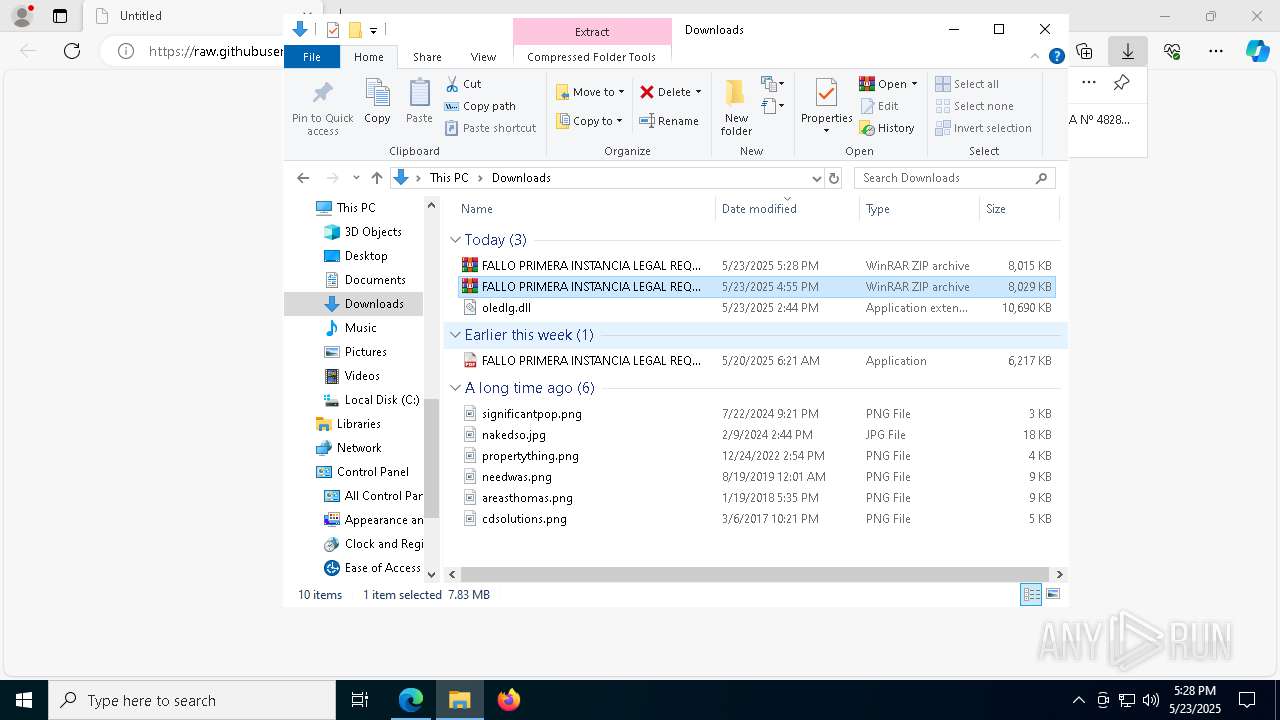
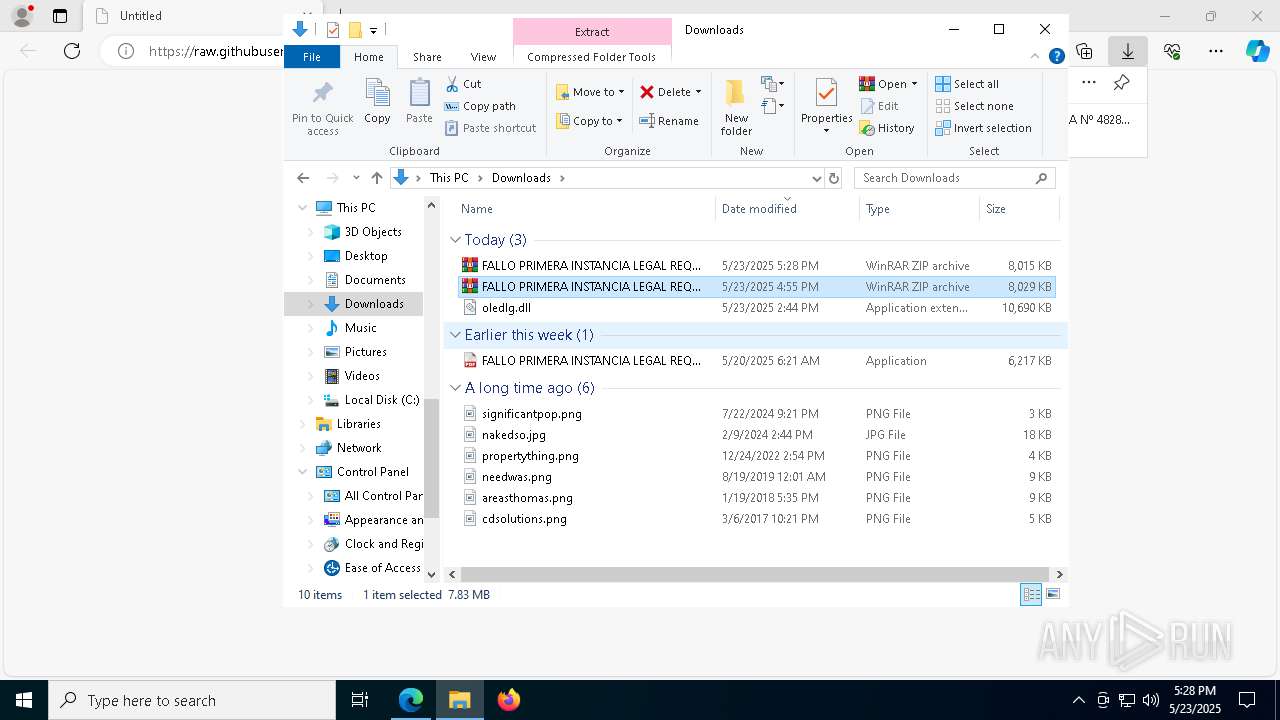
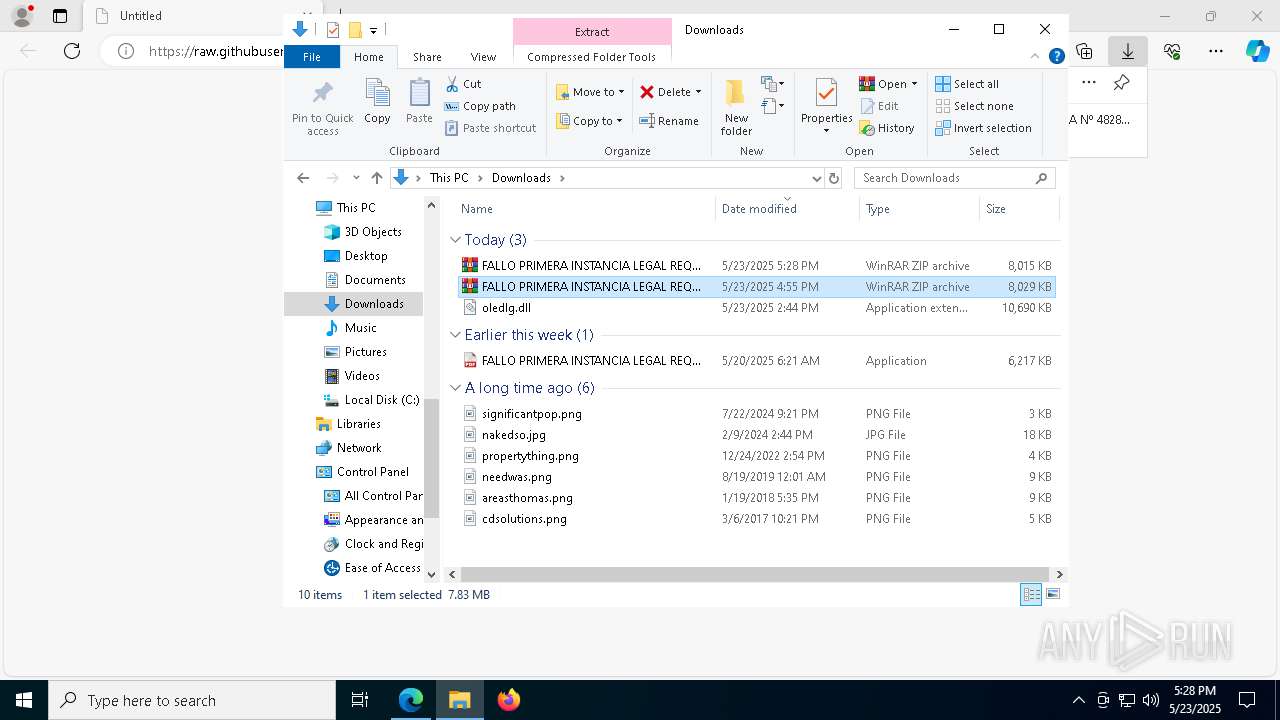
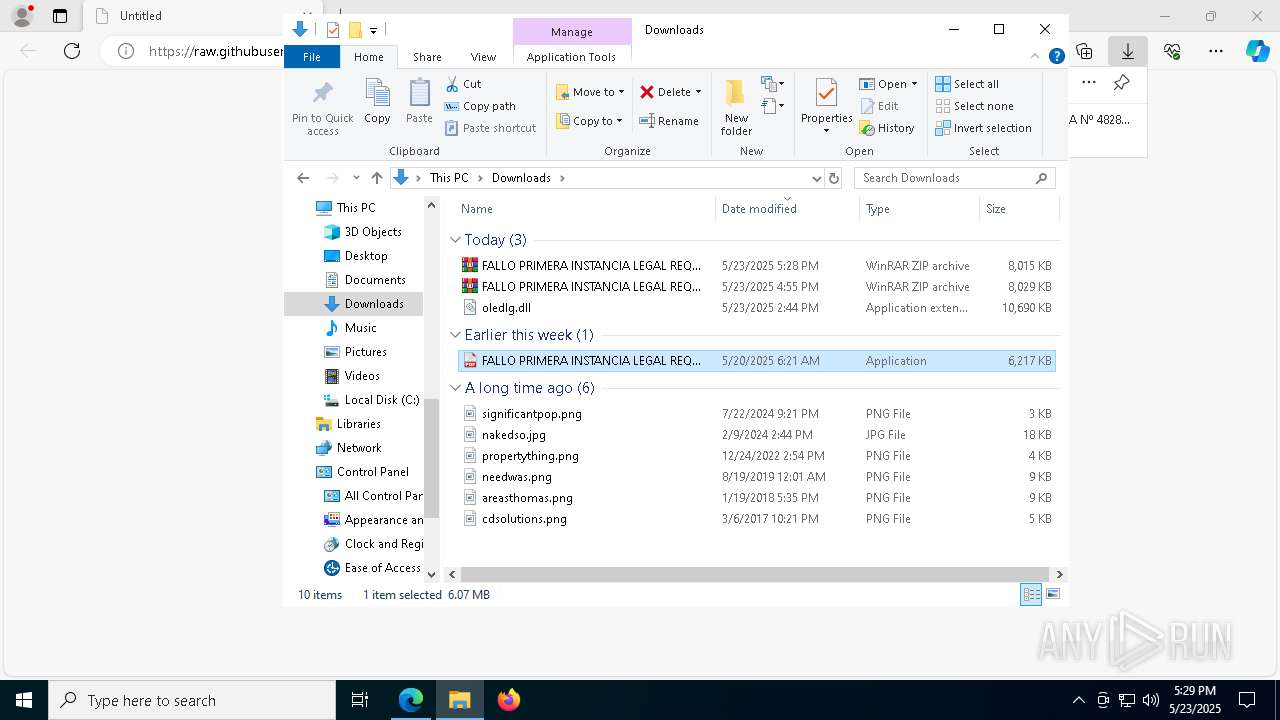
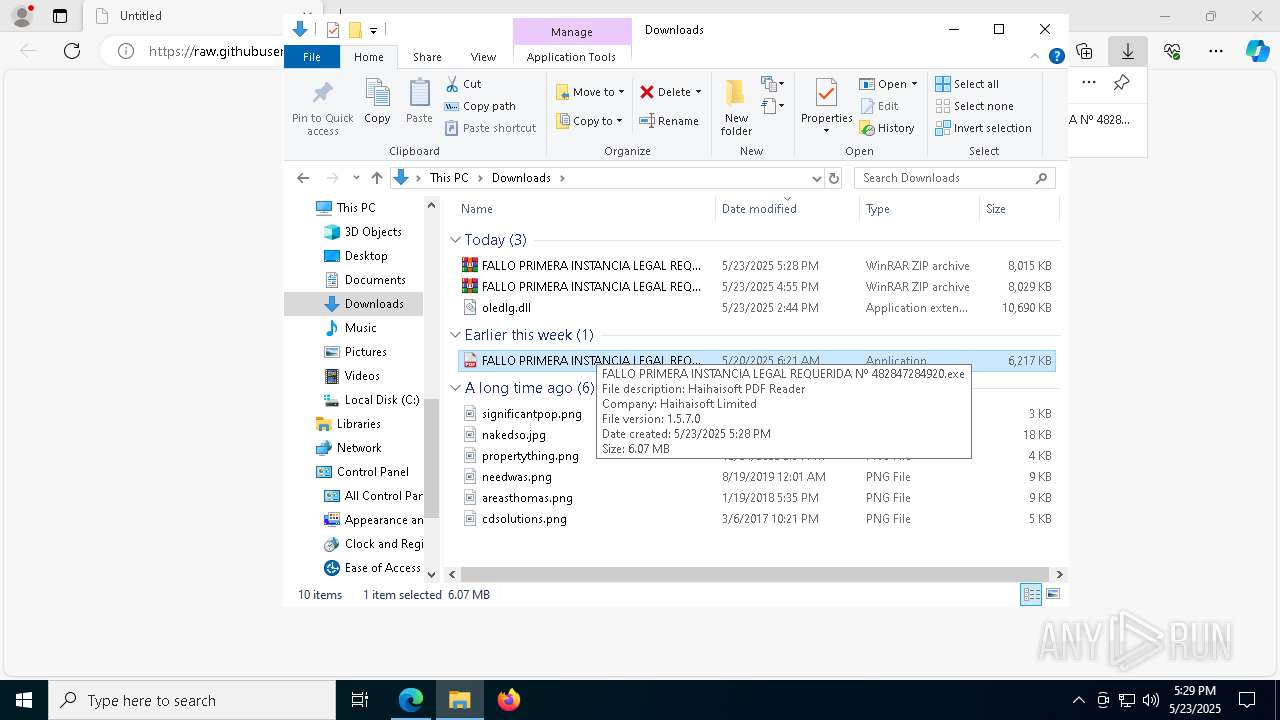
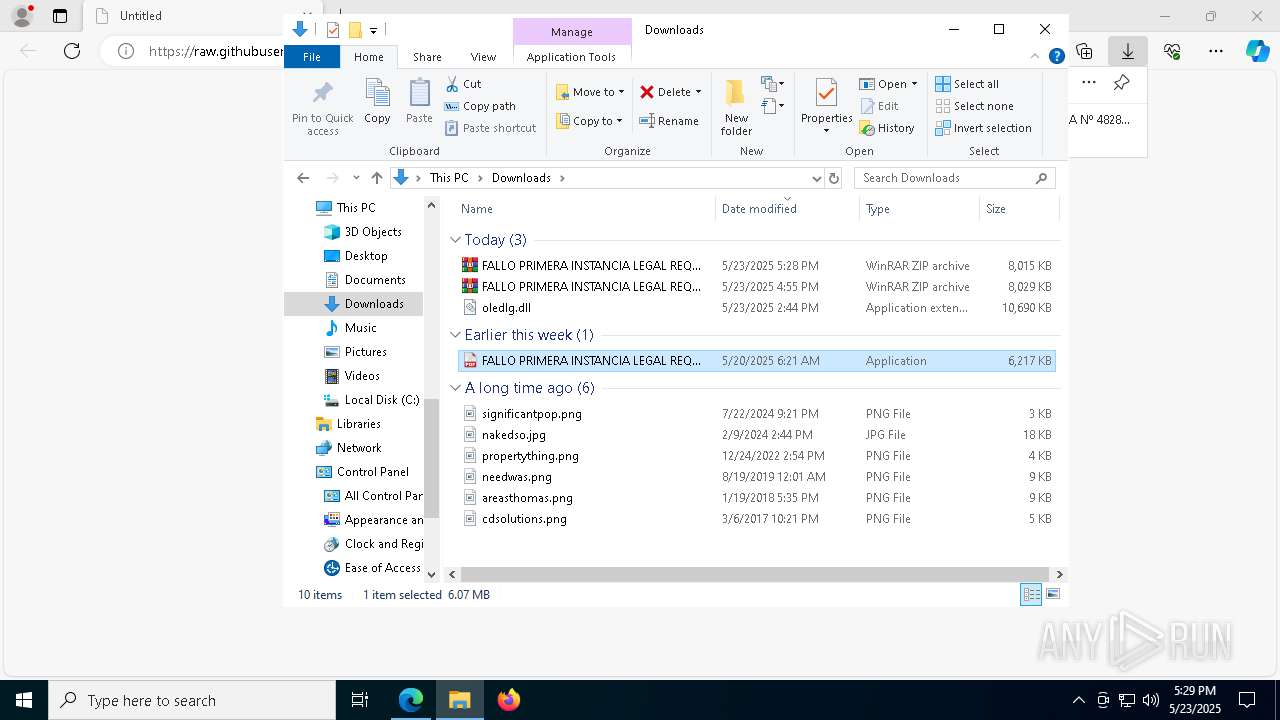
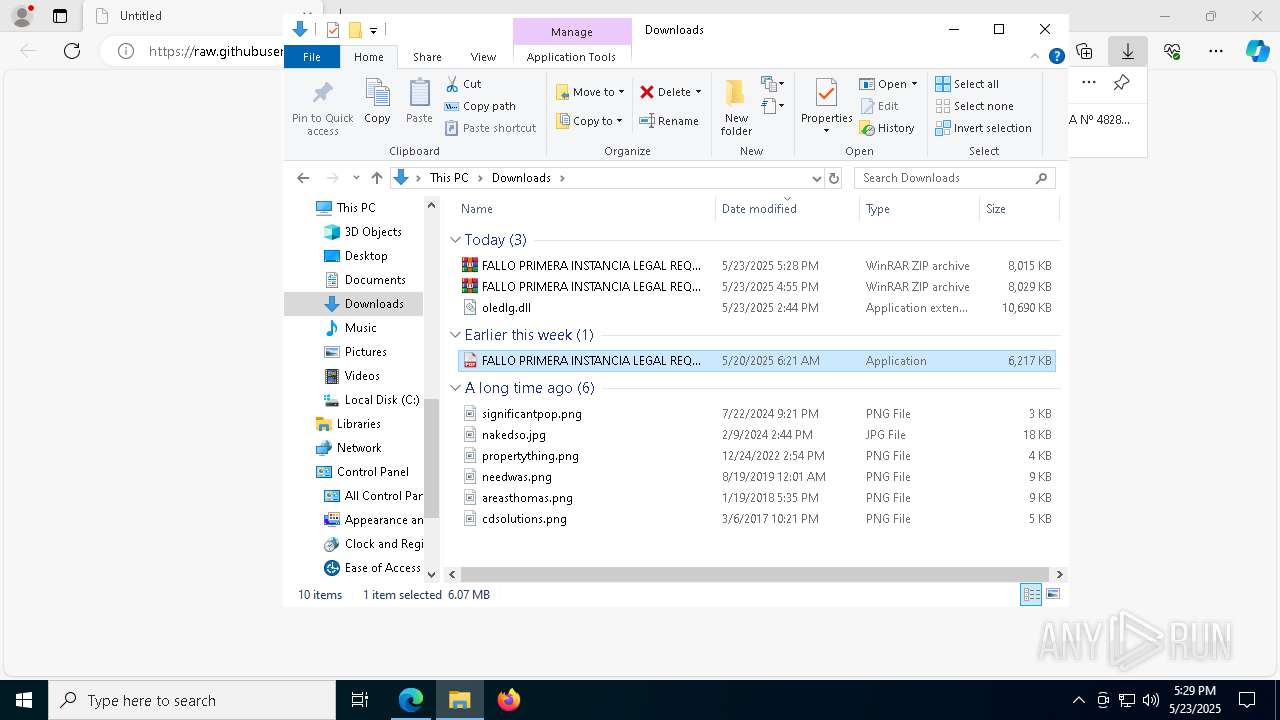
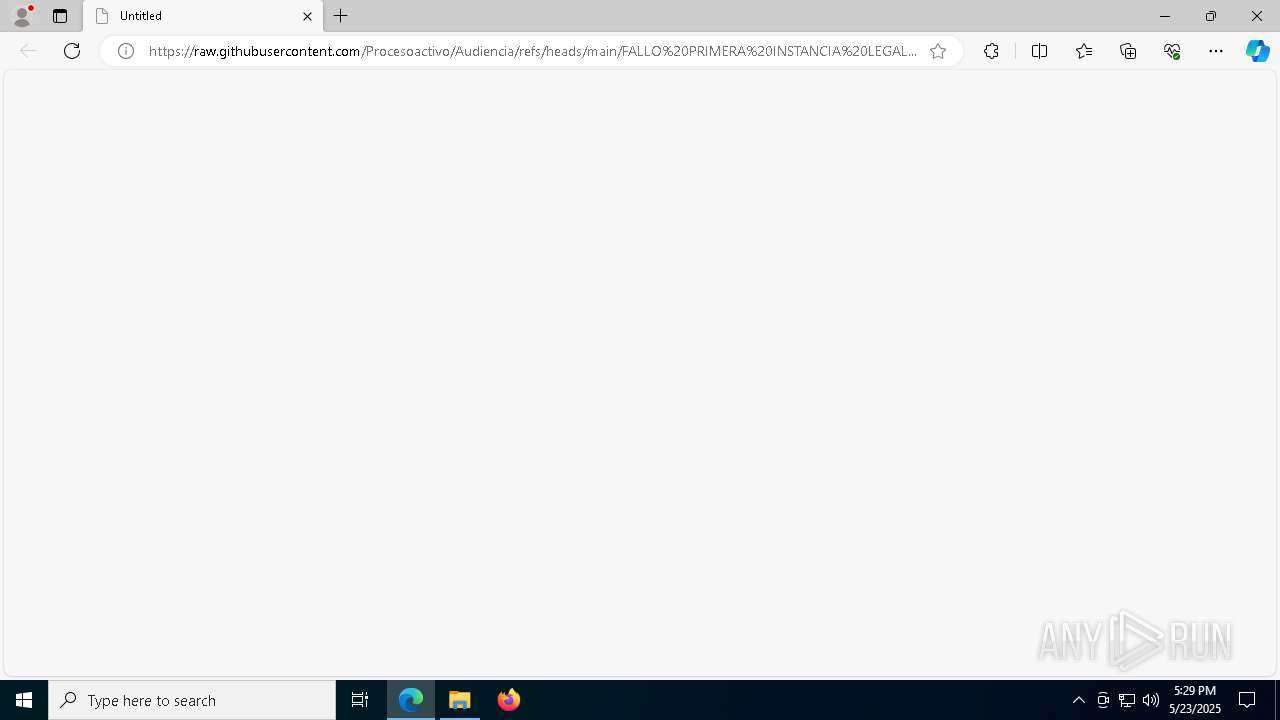
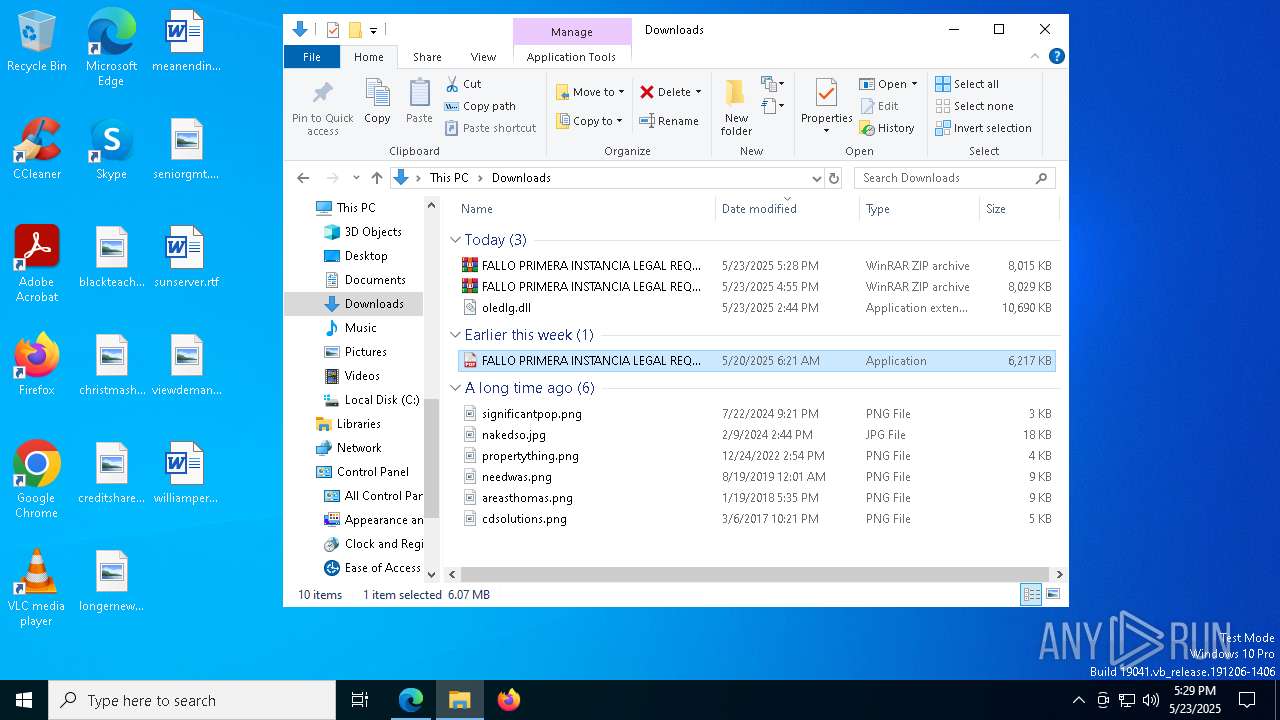
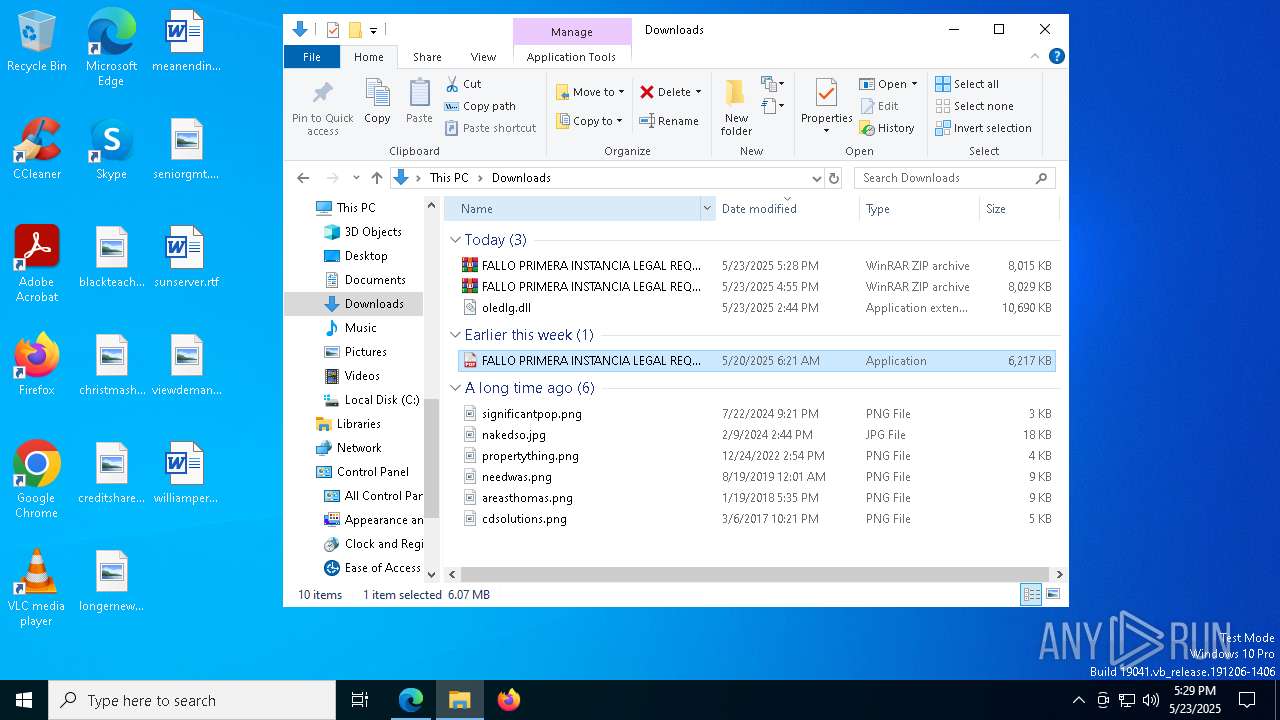
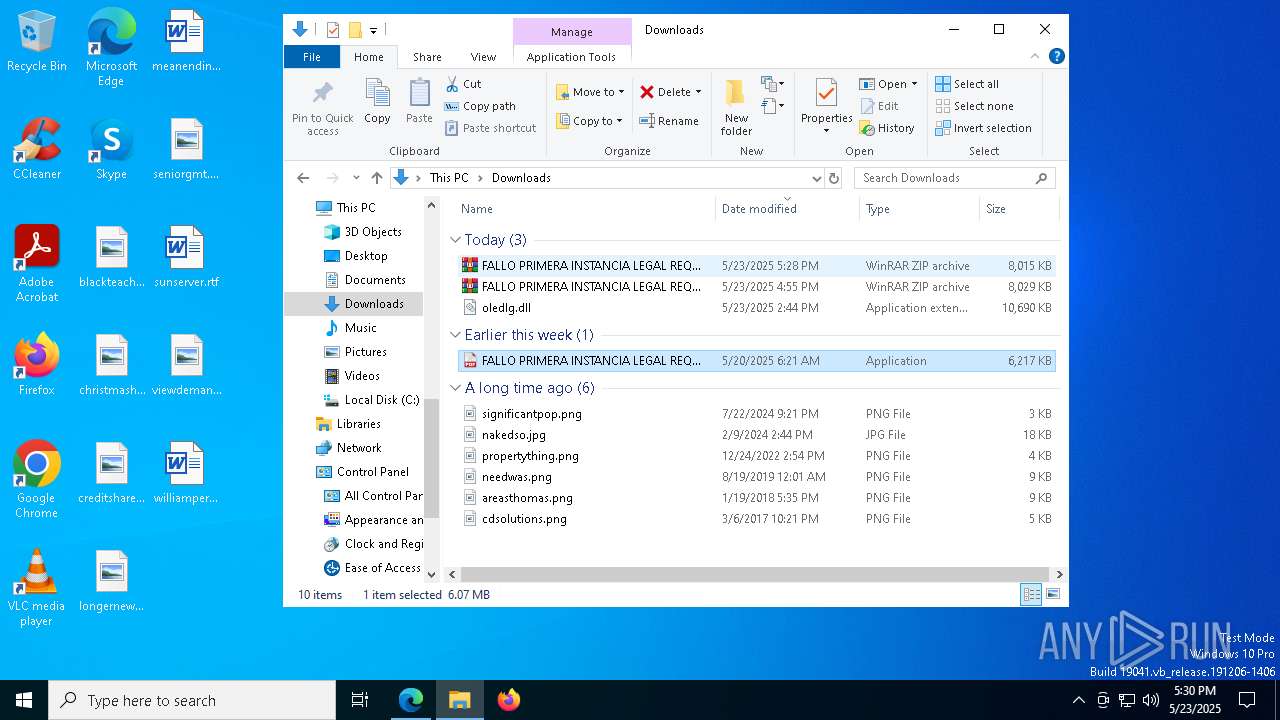
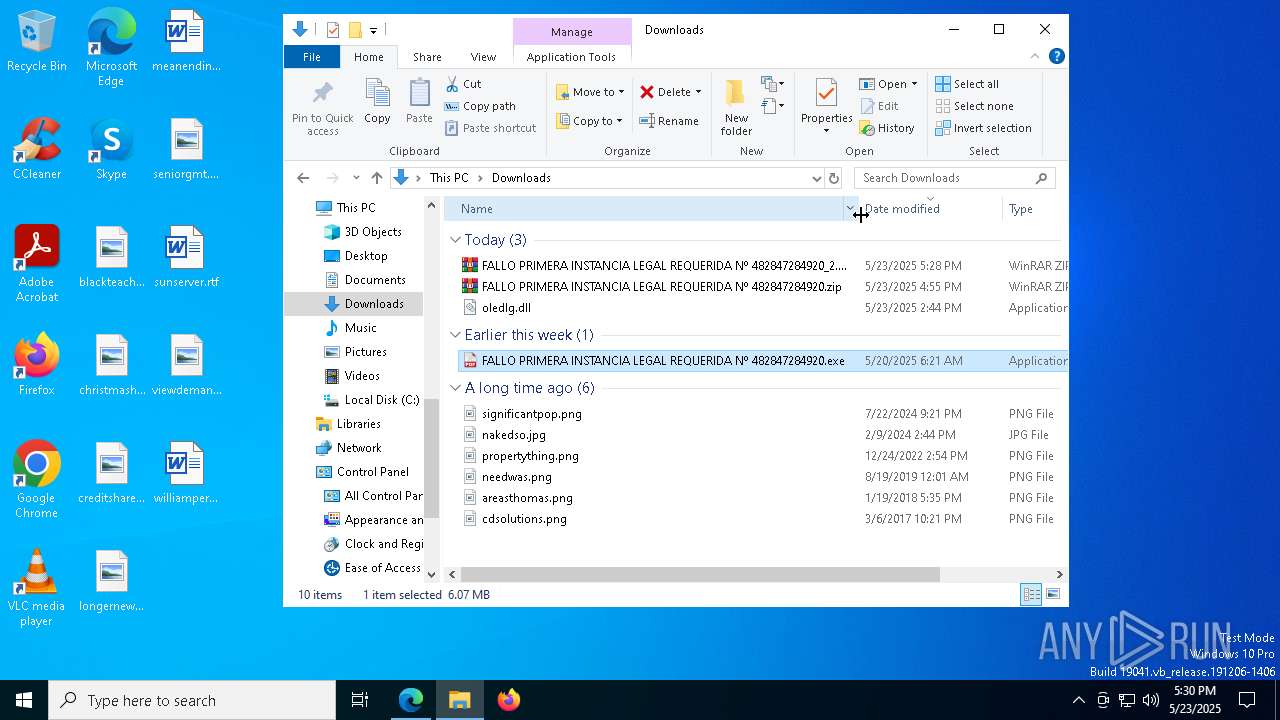
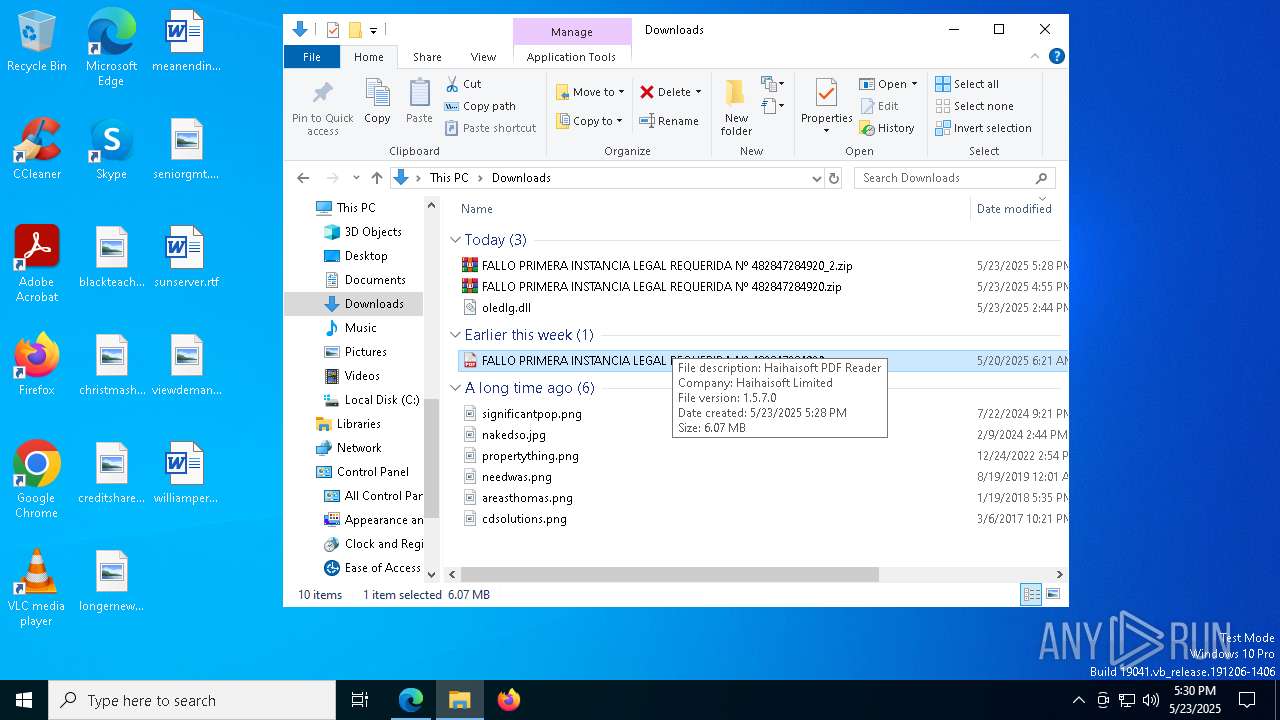
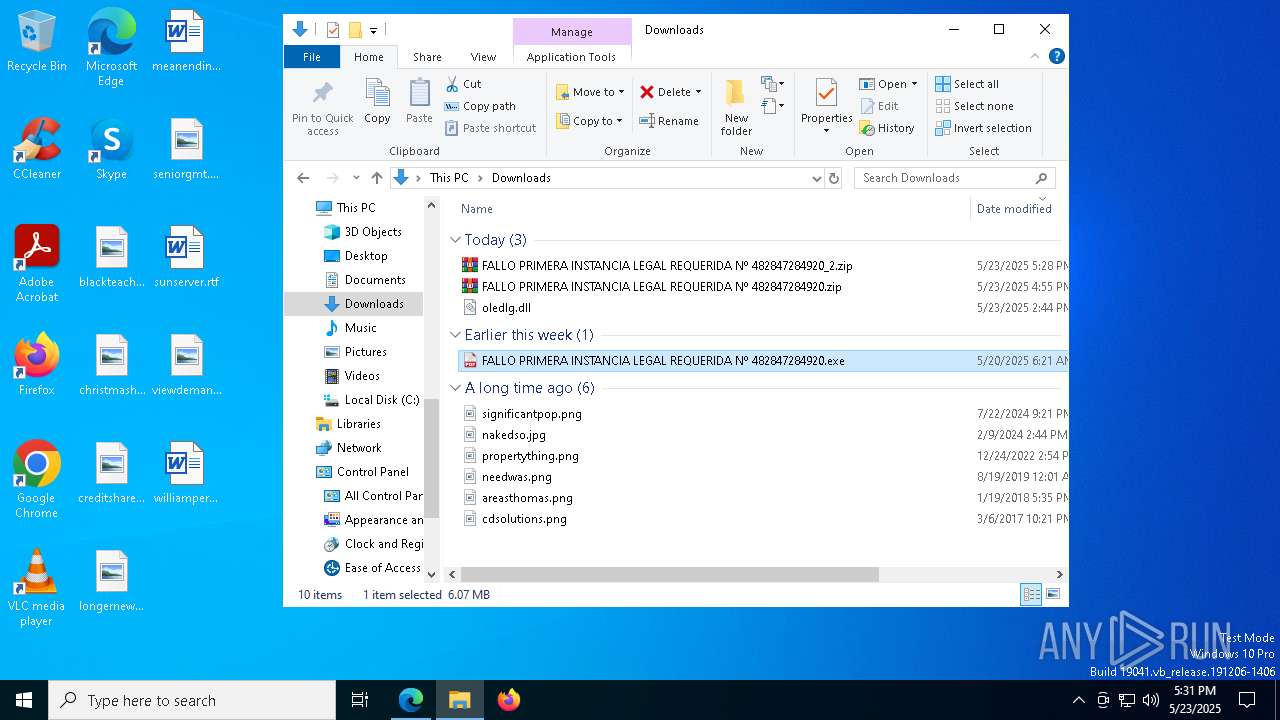
| URL: | https://raw.githubusercontent.com/Procesoactivo/Audiencia/refs/heads/main/FALLO%20PRIMERA%20INSTANCIA%20LEGAL%20REQUERIDA%20N%C2%BA%20482847284920_2.zip |
| Full analysis: | https://app.any.run/tasks/84c28f61-09a6-46fb-8b1c-2f58f93c39e5 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 23, 2025, 17:28:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1B48FA656255E0F3B7B66B9B2A673BAA |
| SHA1: | BBD285349C65C607B30DB0CAEEBF5D1BF0C4D542 |
| SHA256: | 8F71488AC06A91A7C2F86F8D9EF89005EB4F0E5674FD47689AF9557F0FEF6AEA |
| SSDEEP: | 3:N8SGfALtGTGAWKvqGs9gKWoLNK4XV9sVJXGrLkAsa8tDXnG3ipLkV:2FMGqAWKCY1oLNKe9AtDXGypLkV |
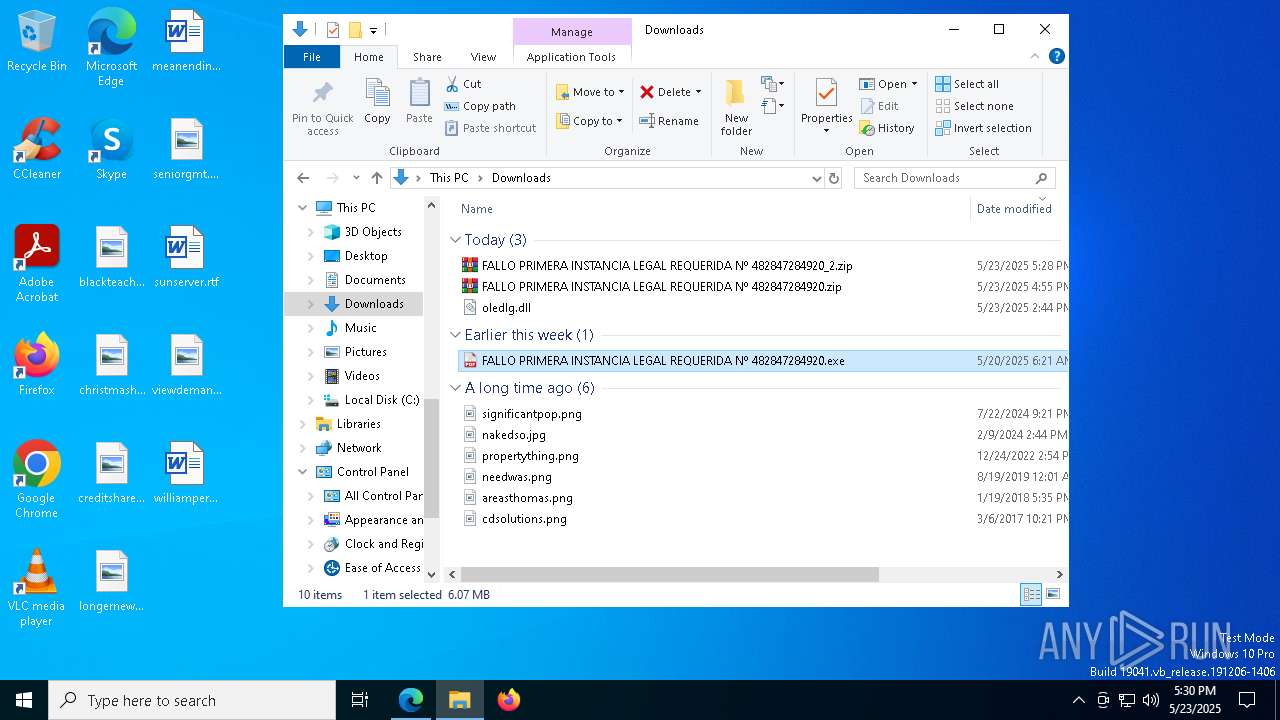
MALICIOUS
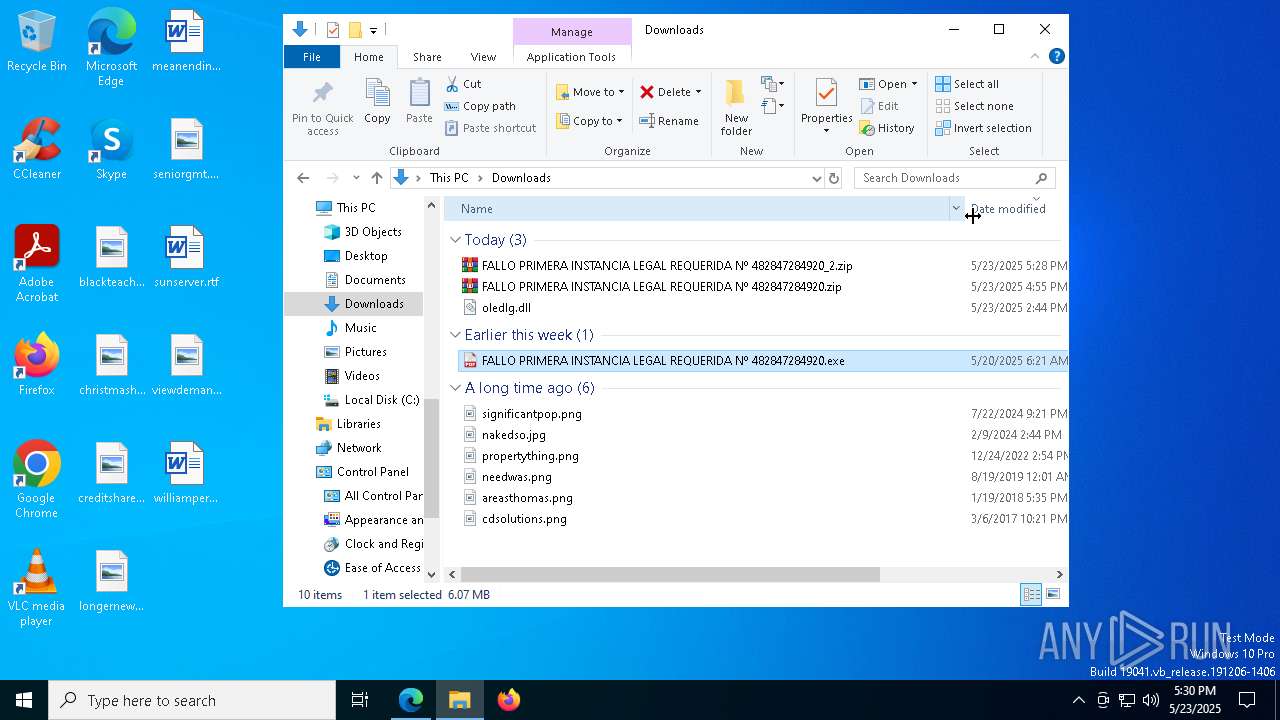
Starts Visual C# compiler
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 6372)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7524)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3268)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 5508)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7260)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7324)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3180)
ASYNCRAT has been detected (YARA)
- csc.exe (PID: 1228)
ASYNCRAT has been detected (SURICATA)
- csc.exe (PID: 1228)
Bypass execution policy to execute commands
- powershell.exe (PID: 7992)
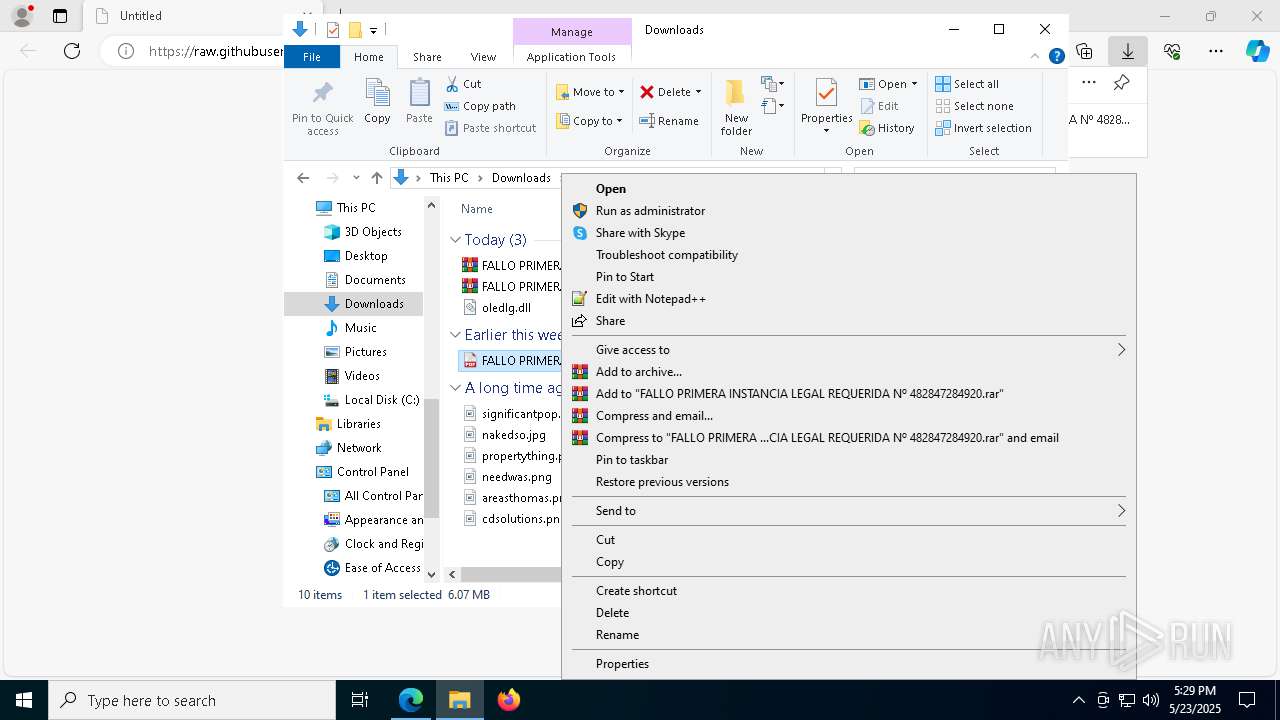
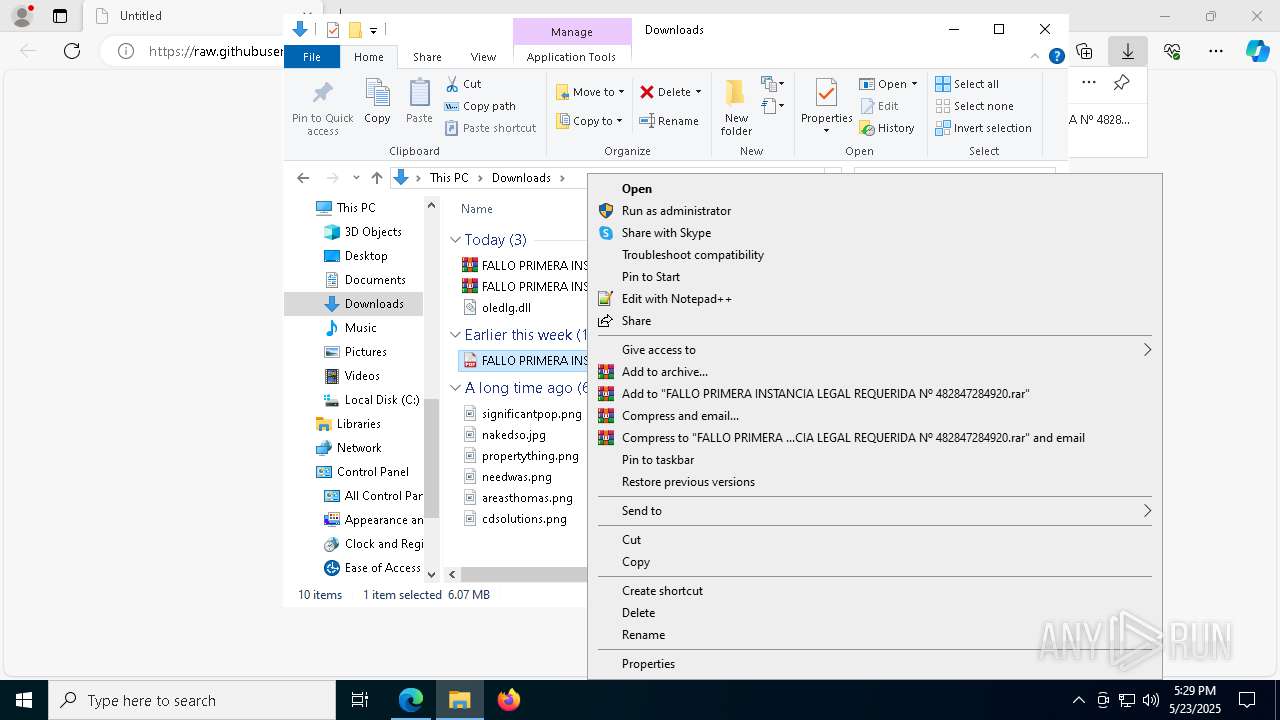
Executing a file with an untrusted certificate
- NanoGa.exe (PID: 1388)
- XPFix.exe (PID: 7180)
HIJACKLOADER has been detected (YARA)
- Cac_M64.exe (PID: 2652)
REMCOS has been detected (YARA)
- NanoGa.exe (PID: 1388)
REMCOS has been detected (SURICATA)
- NanoGa.exe (PID: 1388)
Connects to the CnC server
- NanoGa.exe (PID: 1388)
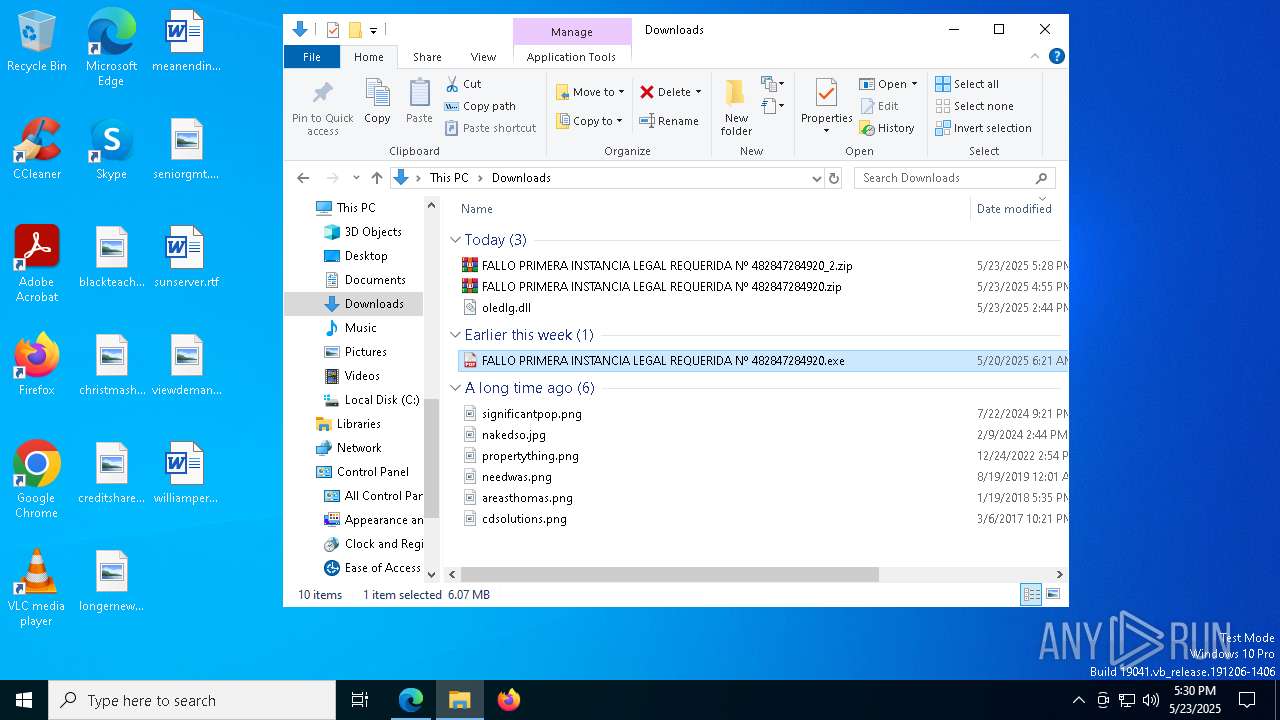
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 6372)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7524)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 5508)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3268)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7260)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7324)
- NanoGa.exe (PID: 1388)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3180)
Contacting a server suspected of hosting an CnC
- csc.exe (PID: 1228)
- NanoGa.exe (PID: 1388)
Connects to unusual port
- csc.exe (PID: 1228)
- NanoGa.exe (PID: 1388)
Executes application which crashes
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 6372)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7524)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3268)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 5508)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7260)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7324)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3180)
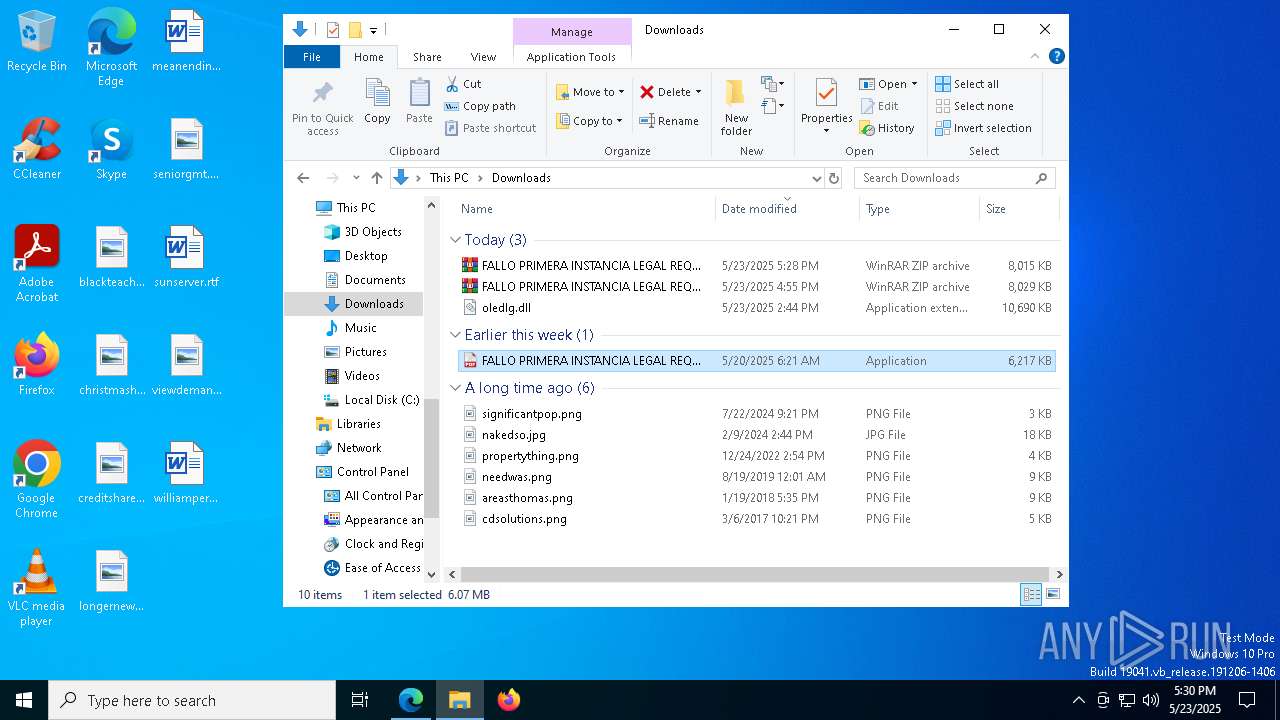
Executable content was dropped or overwritten
- csc.exe (PID: 1228)
- WinZIP.EXE (PID: 7036)
- Cac_M64.exe (PID: 3016)
- Cac_M64.exe (PID: 2652)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 536)
Process drops legitimate windows executable
- csc.exe (PID: 1228)
Starts CMD.EXE for commands execution
- csc.exe (PID: 1228)
Starts process via Powershell
- powershell.exe (PID: 7992)
Starts a Microsoft application from unusual location
- WinZIP.EXE (PID: 7036)
Starts itself from another location
- Cac_M64.exe (PID: 3016)
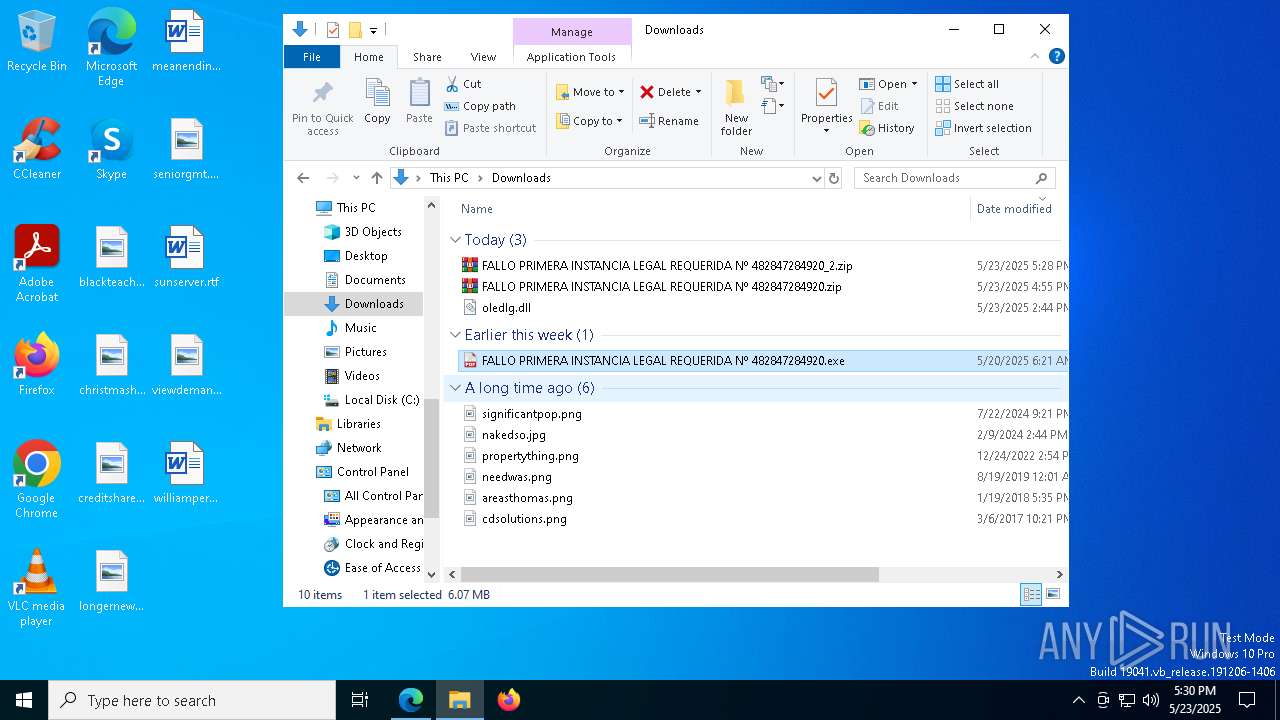
INFO
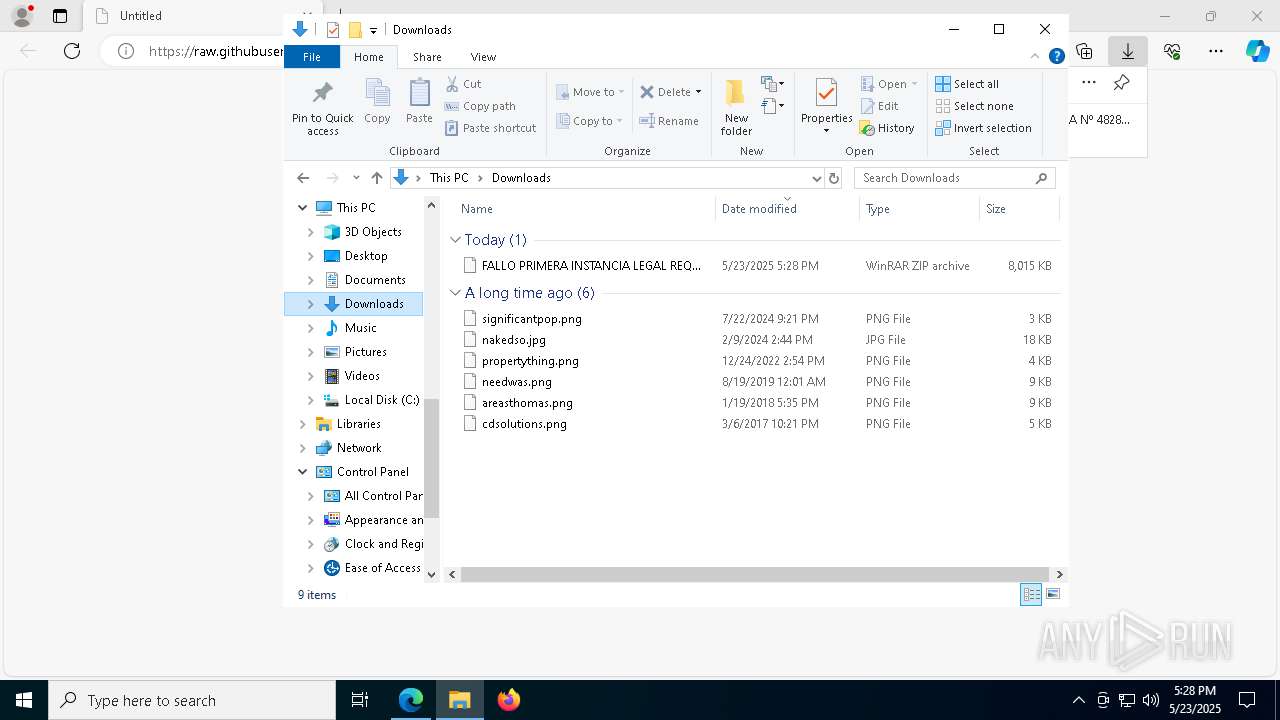
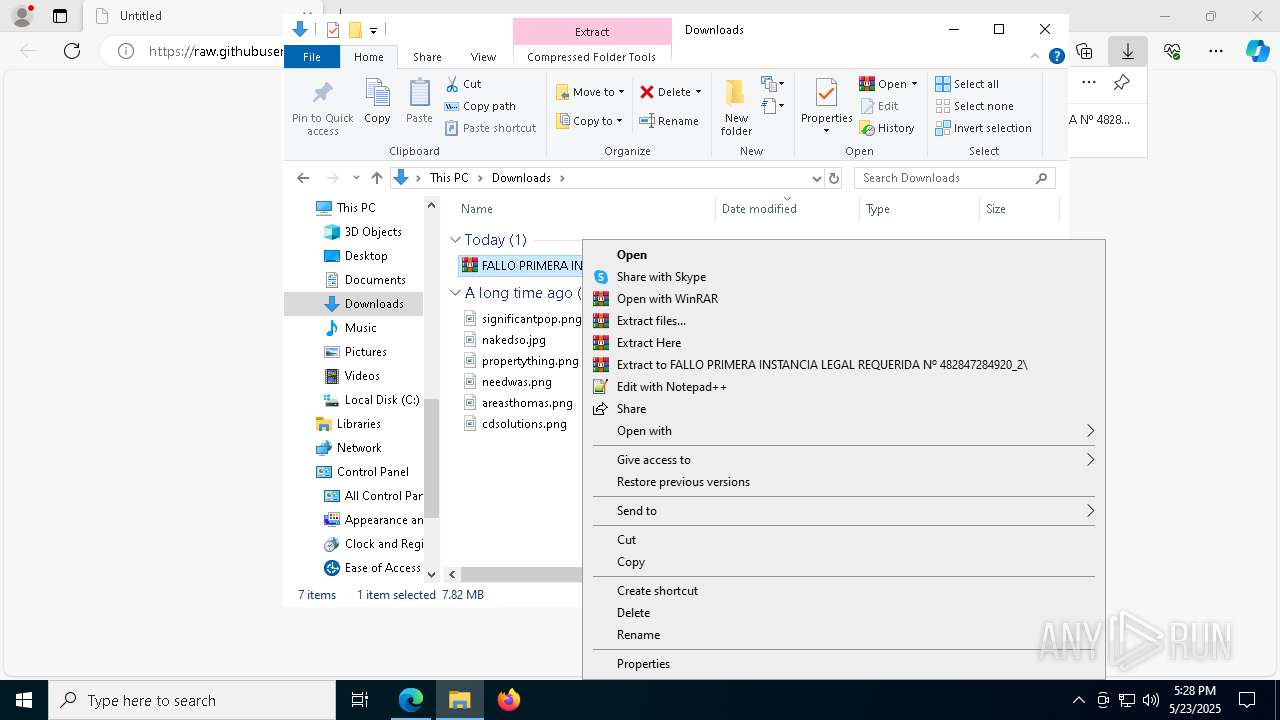
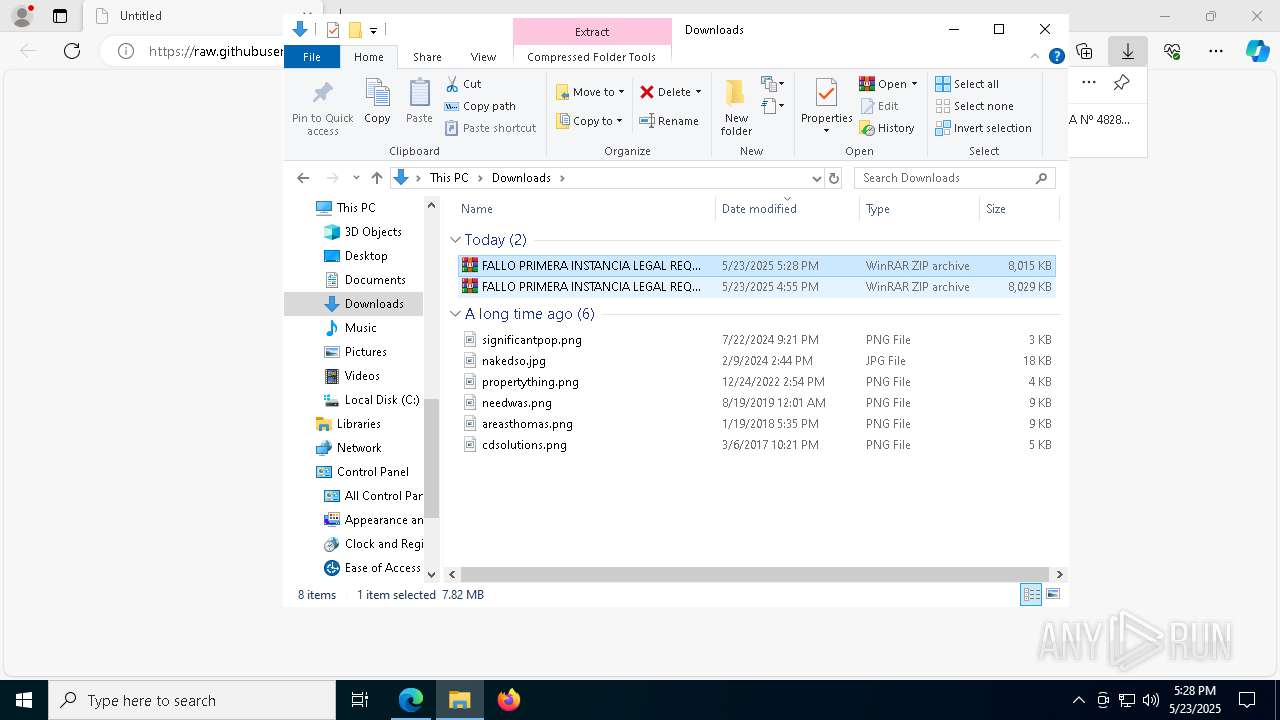
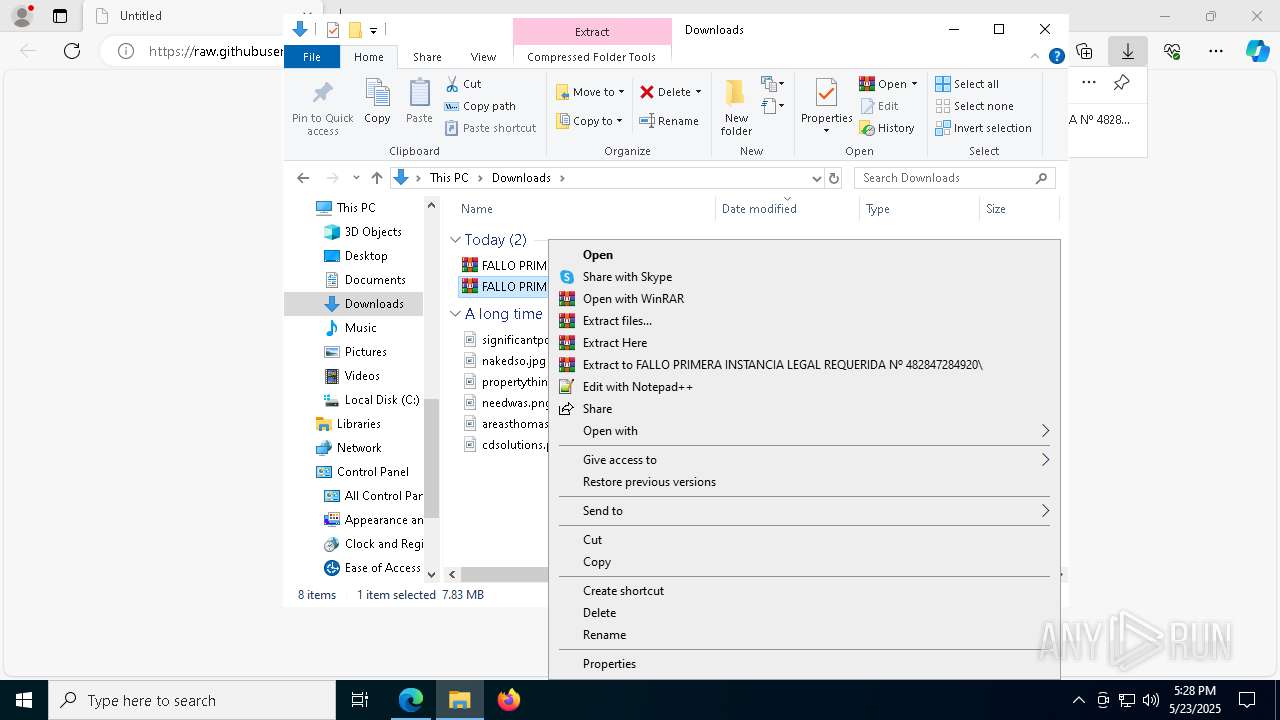
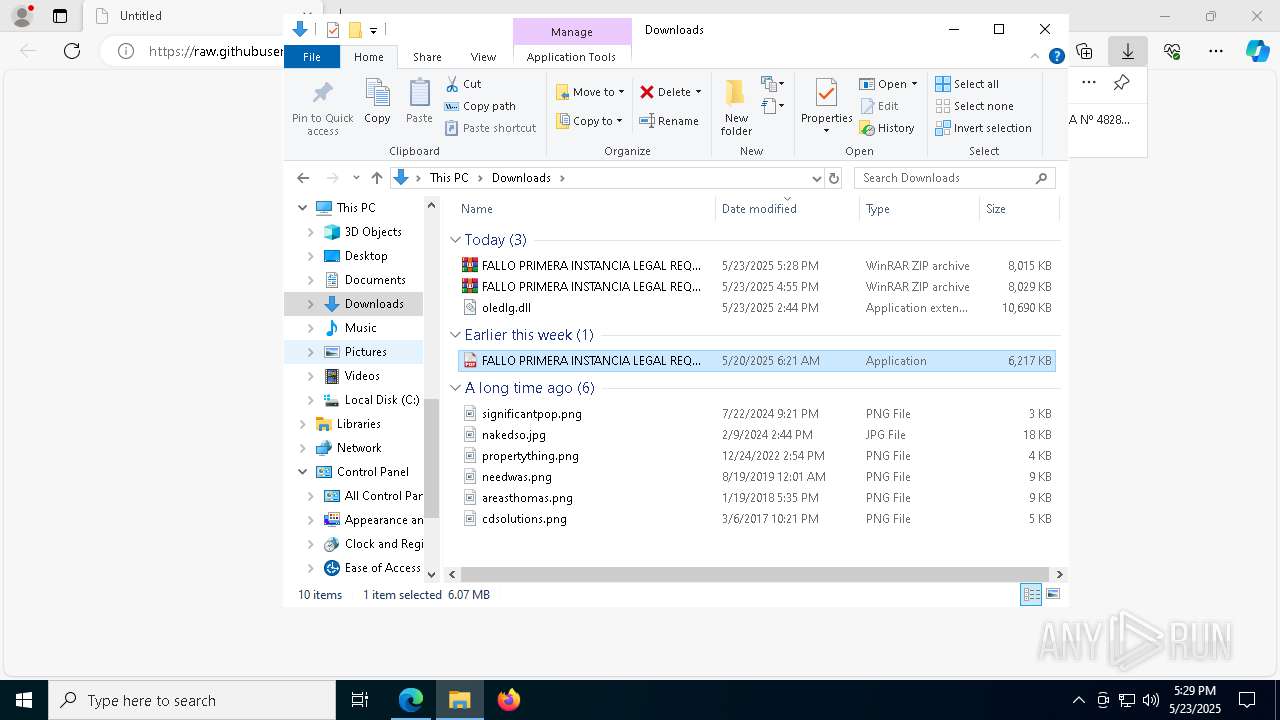
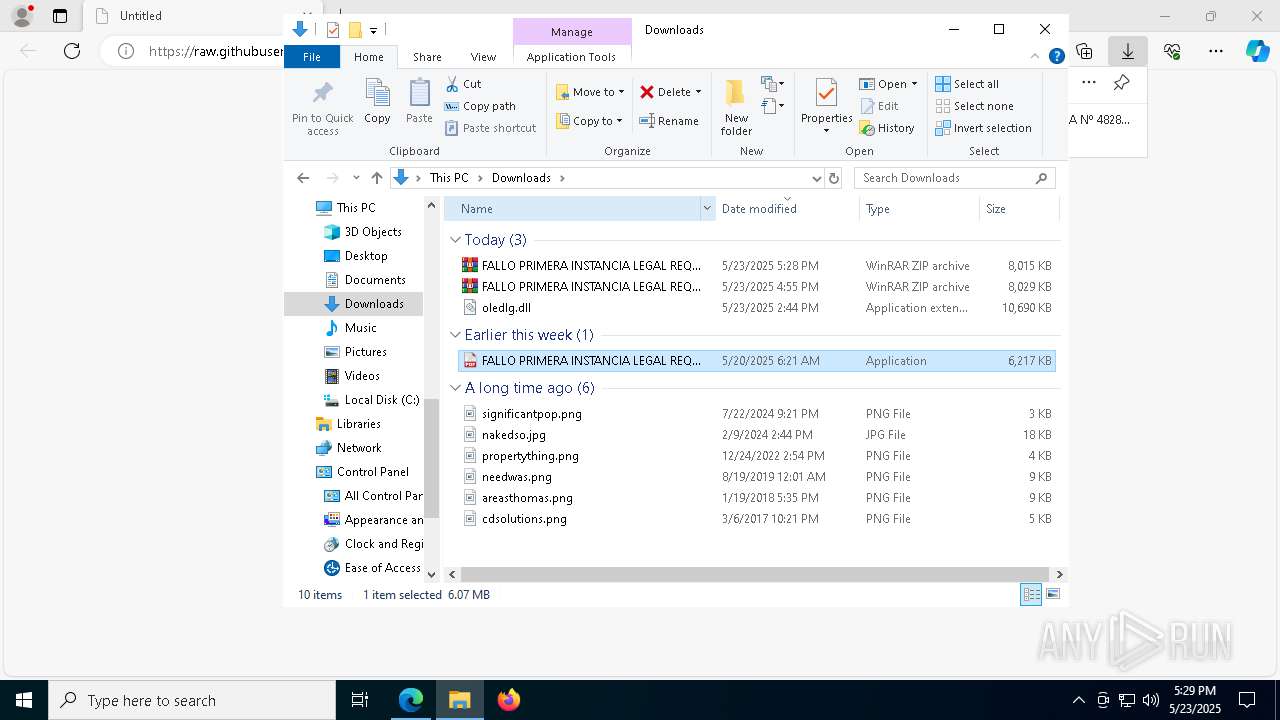
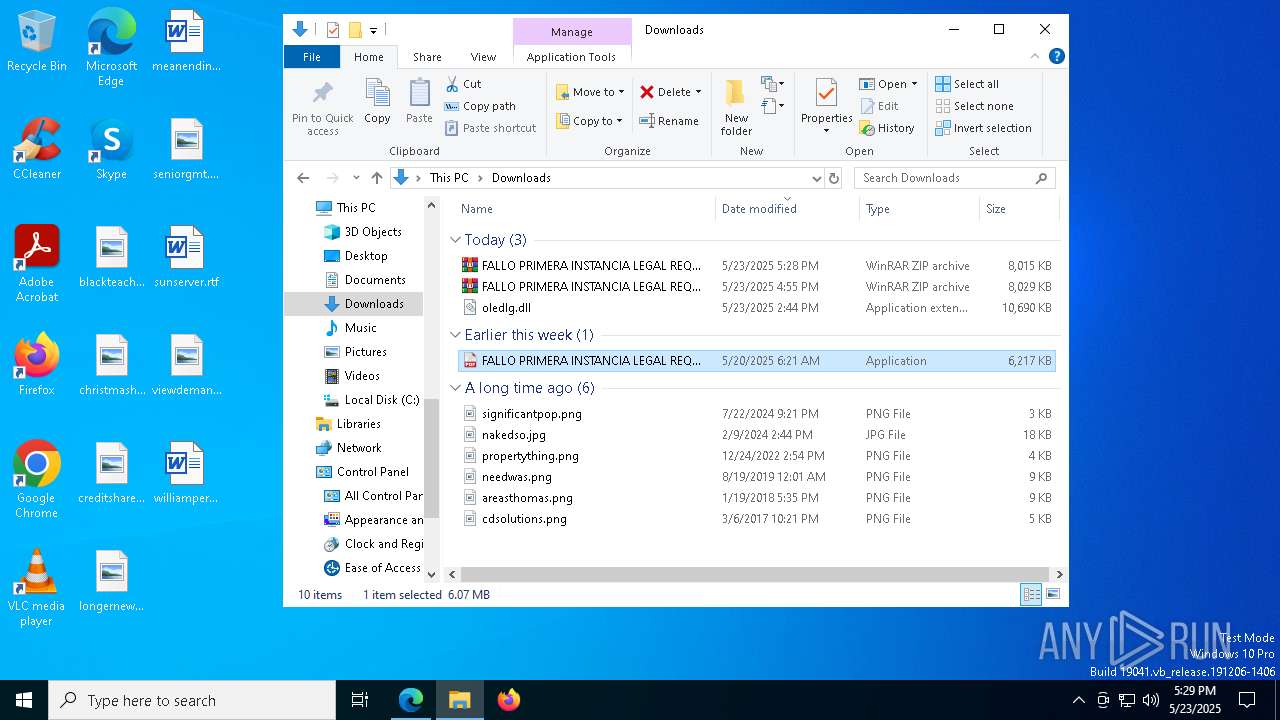
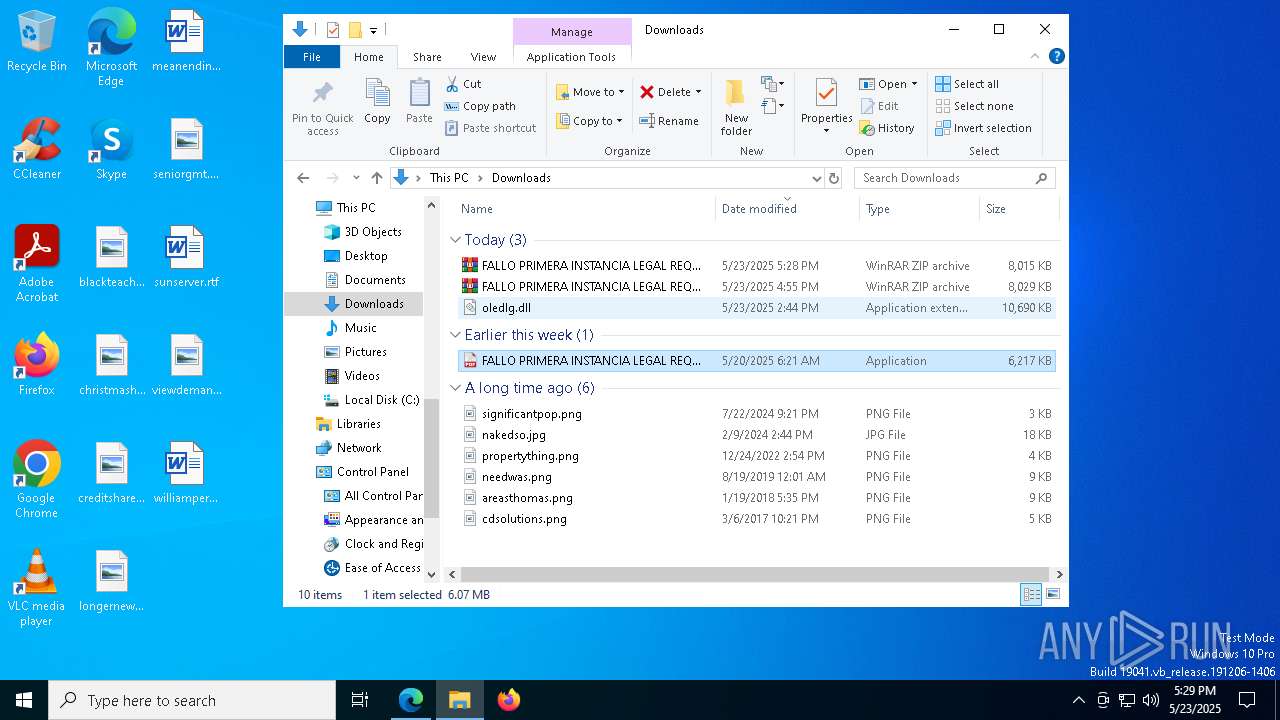
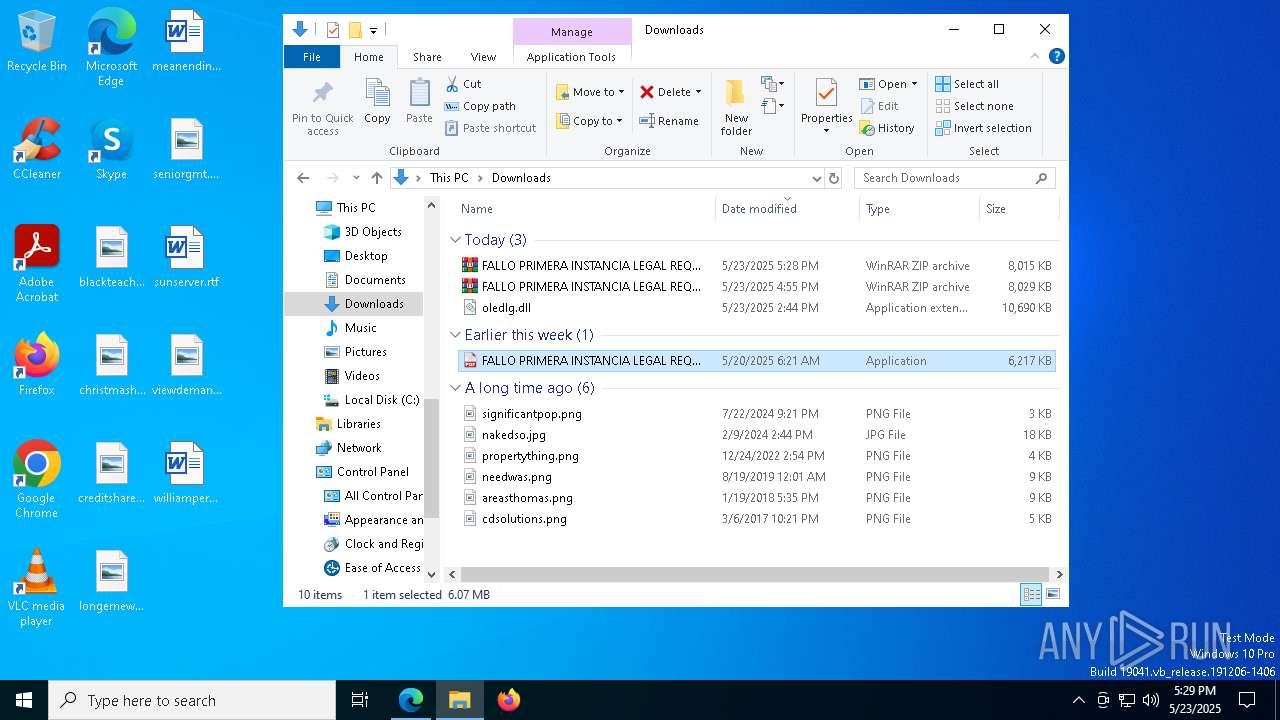
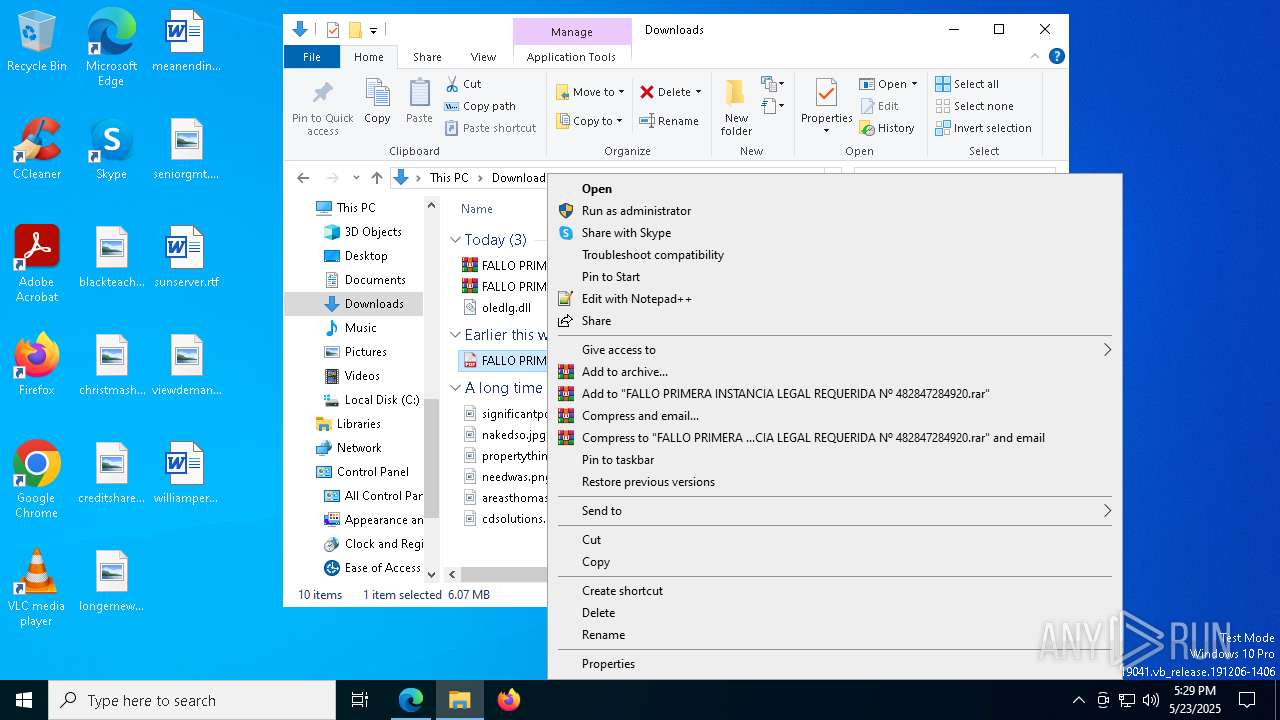
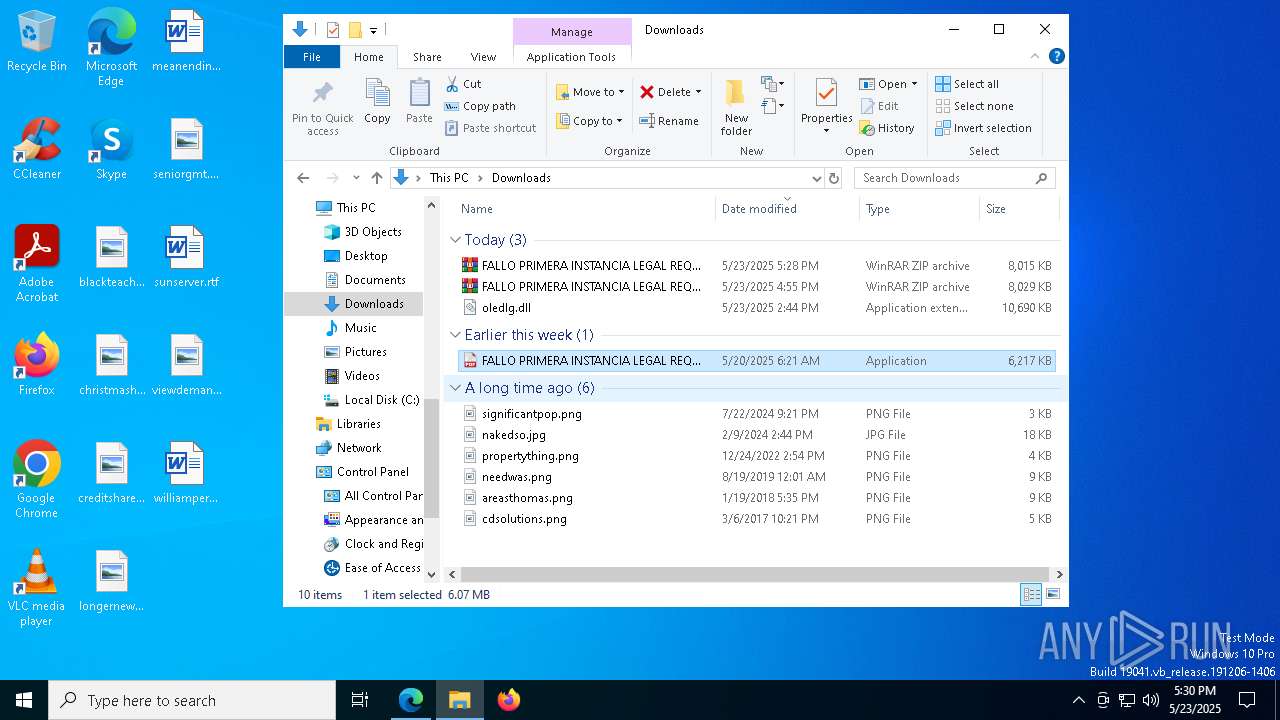
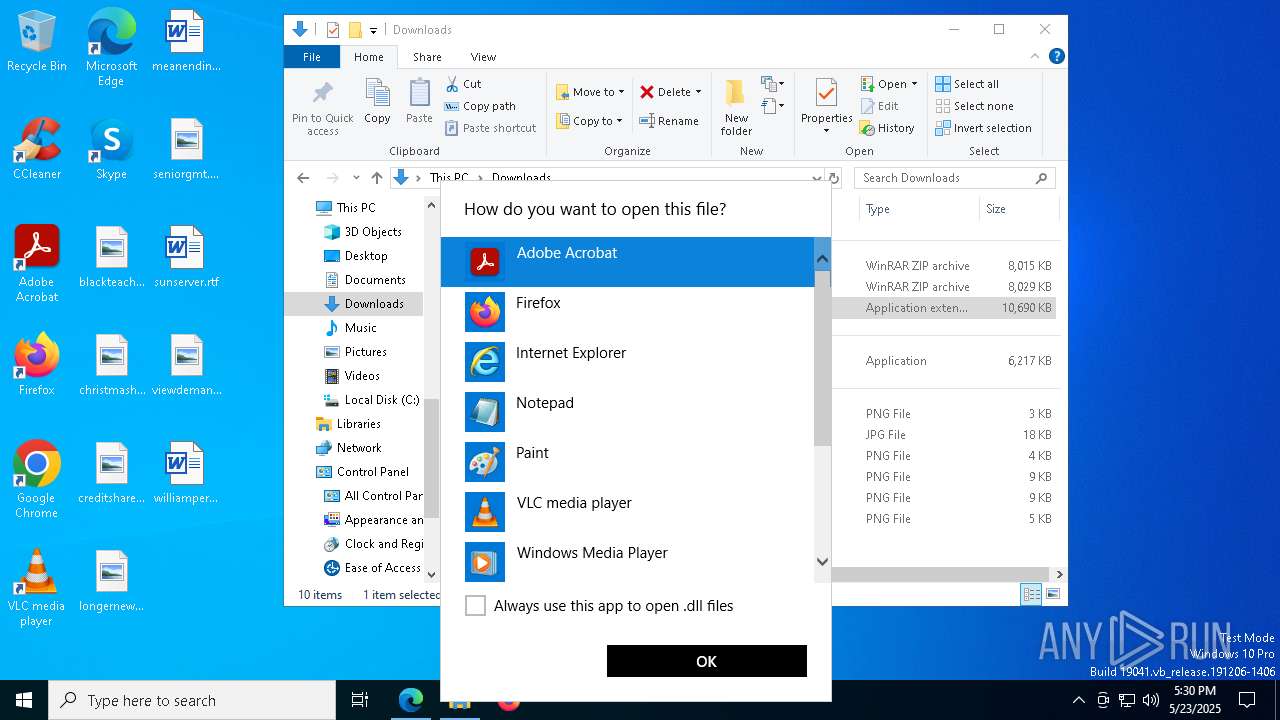
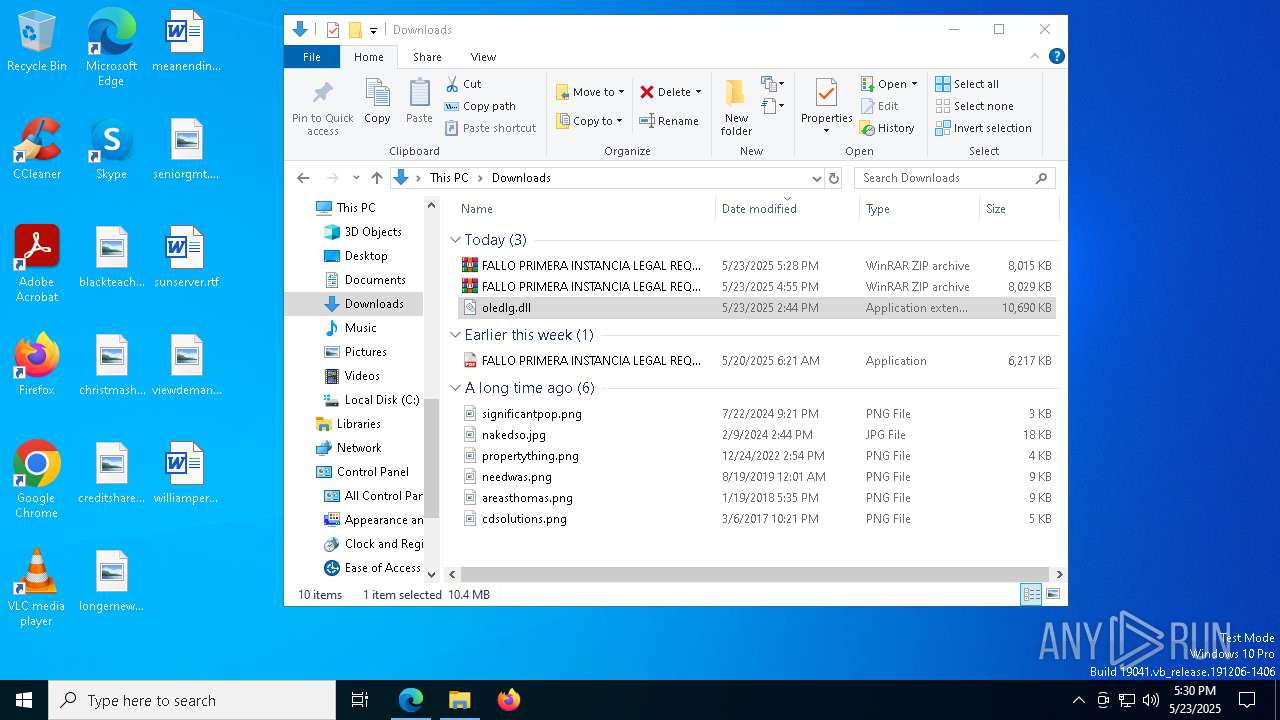
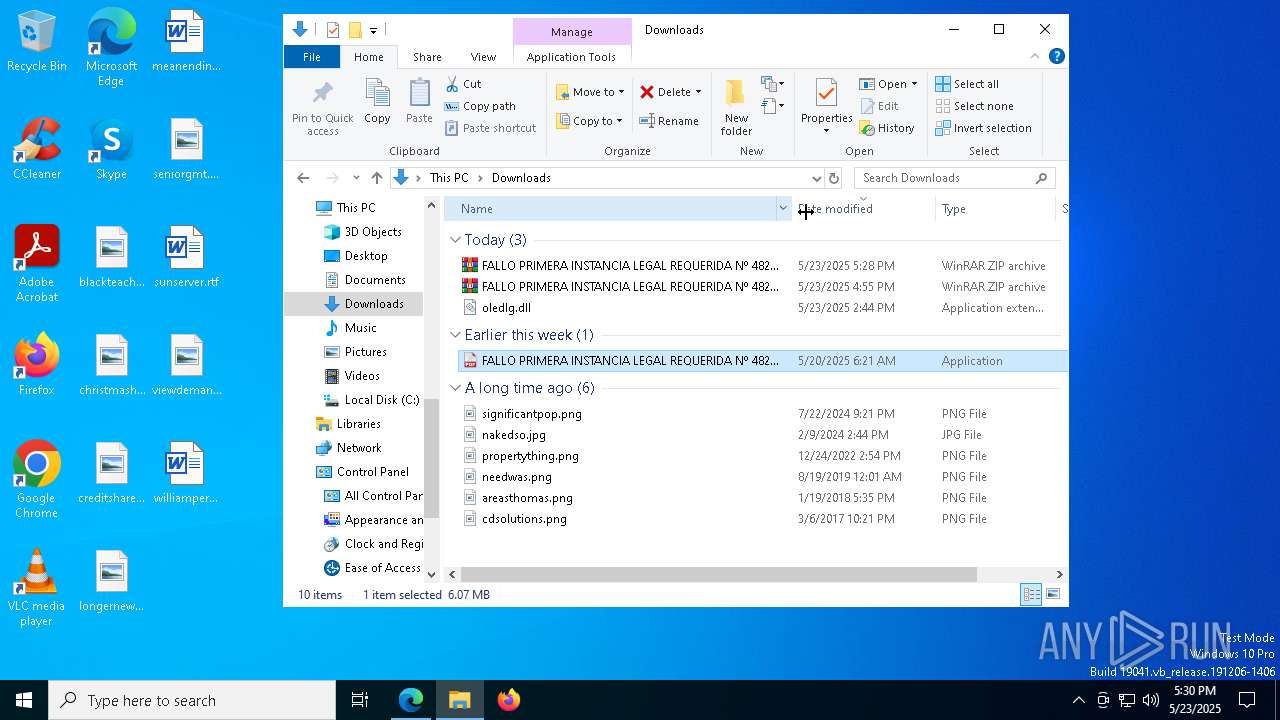
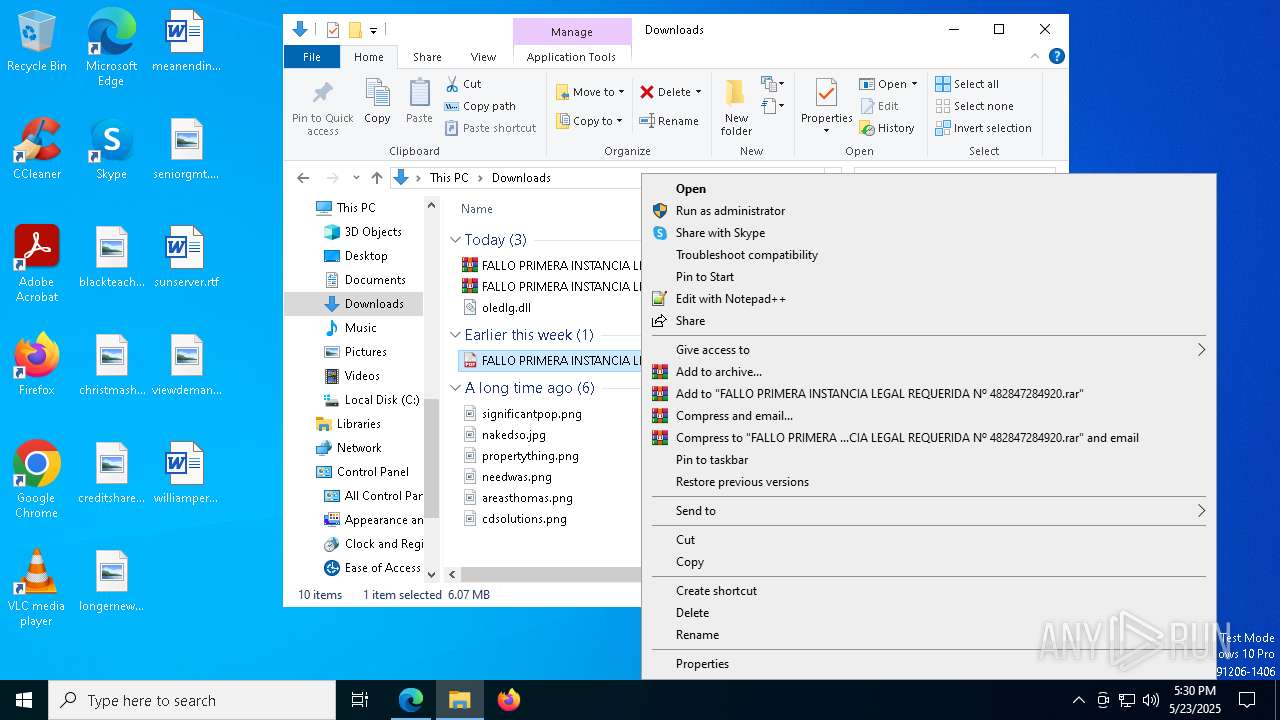
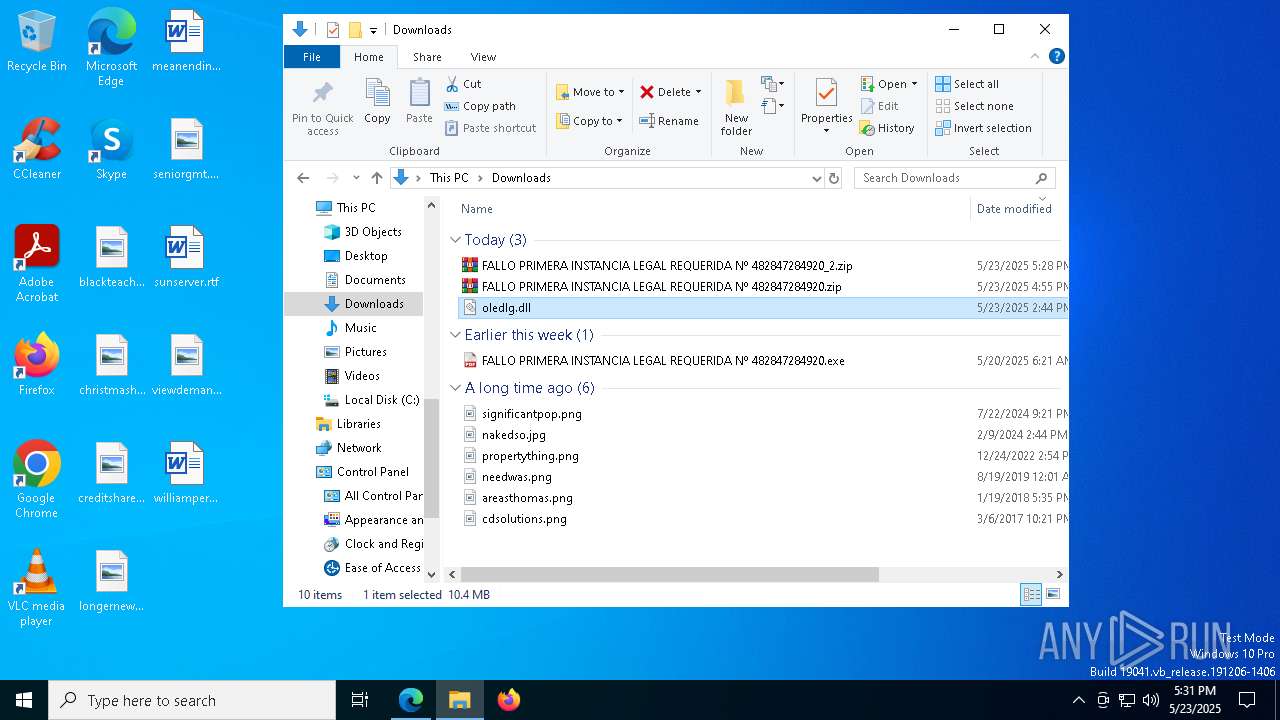
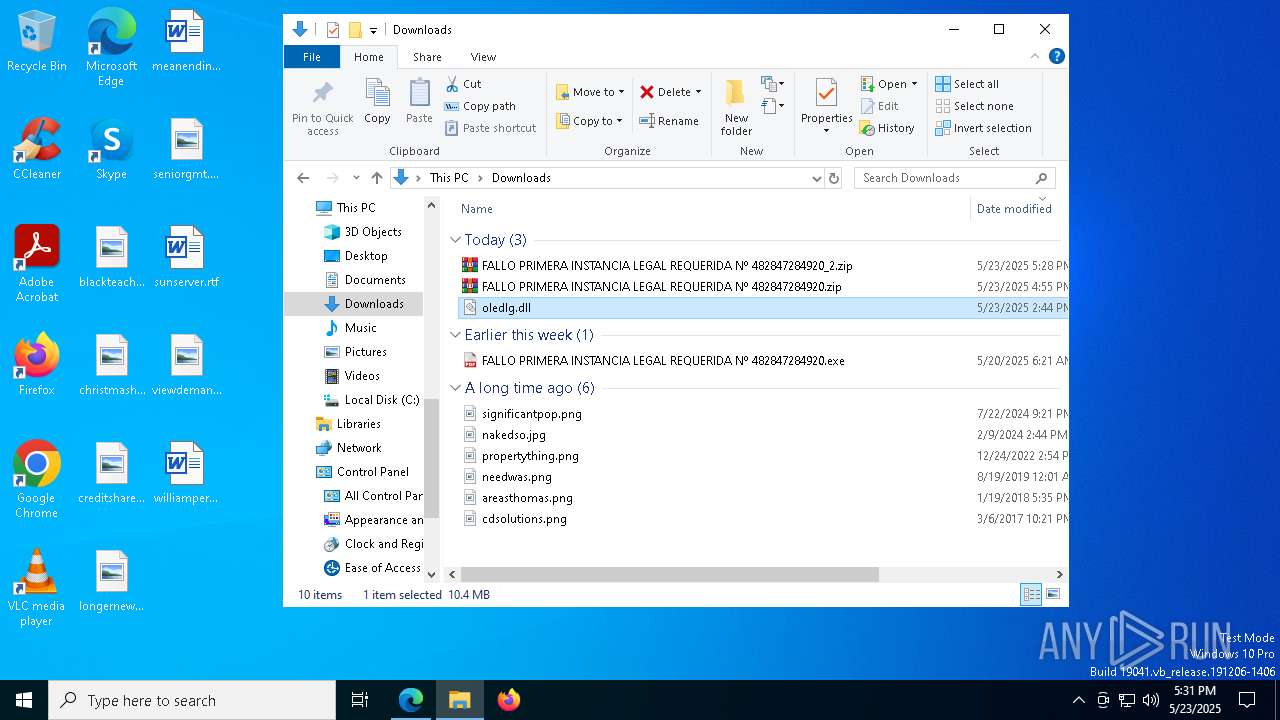
Manual execution by a user
- WinRAR.exe (PID: 6476)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3268)
- WinRAR.exe (PID: 2908)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7524)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 5508)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7260)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7324)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3180)
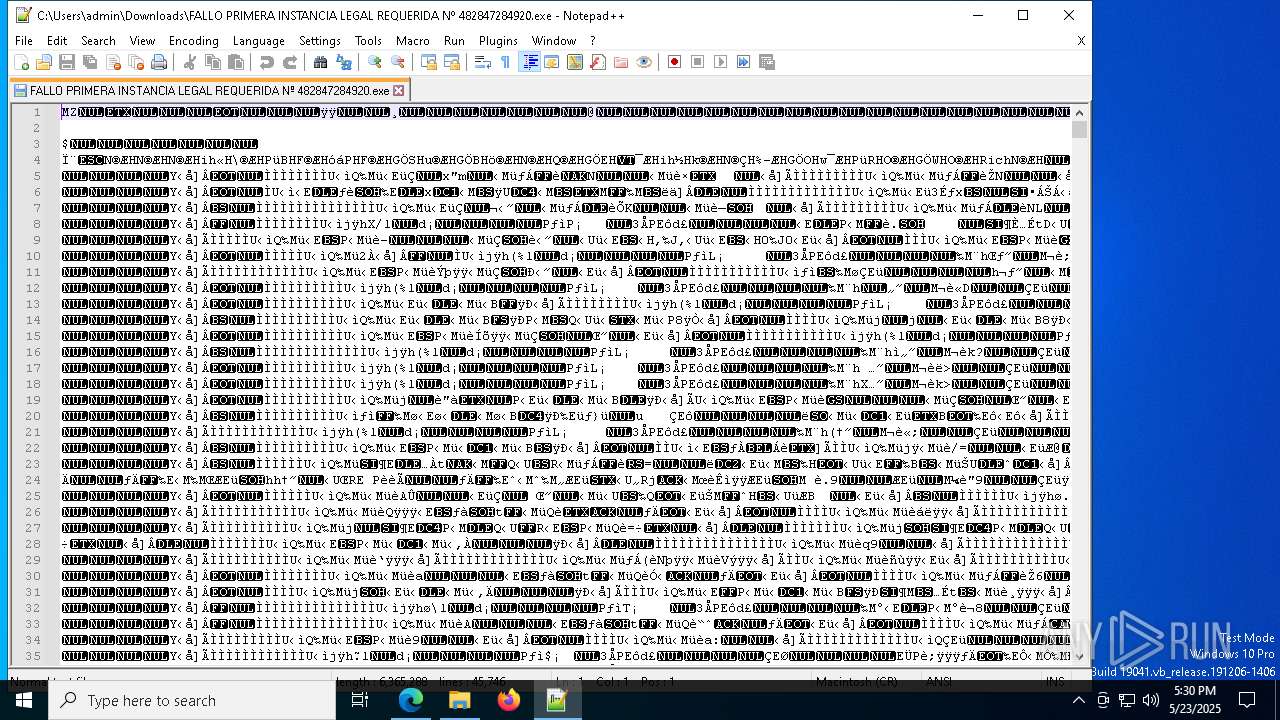
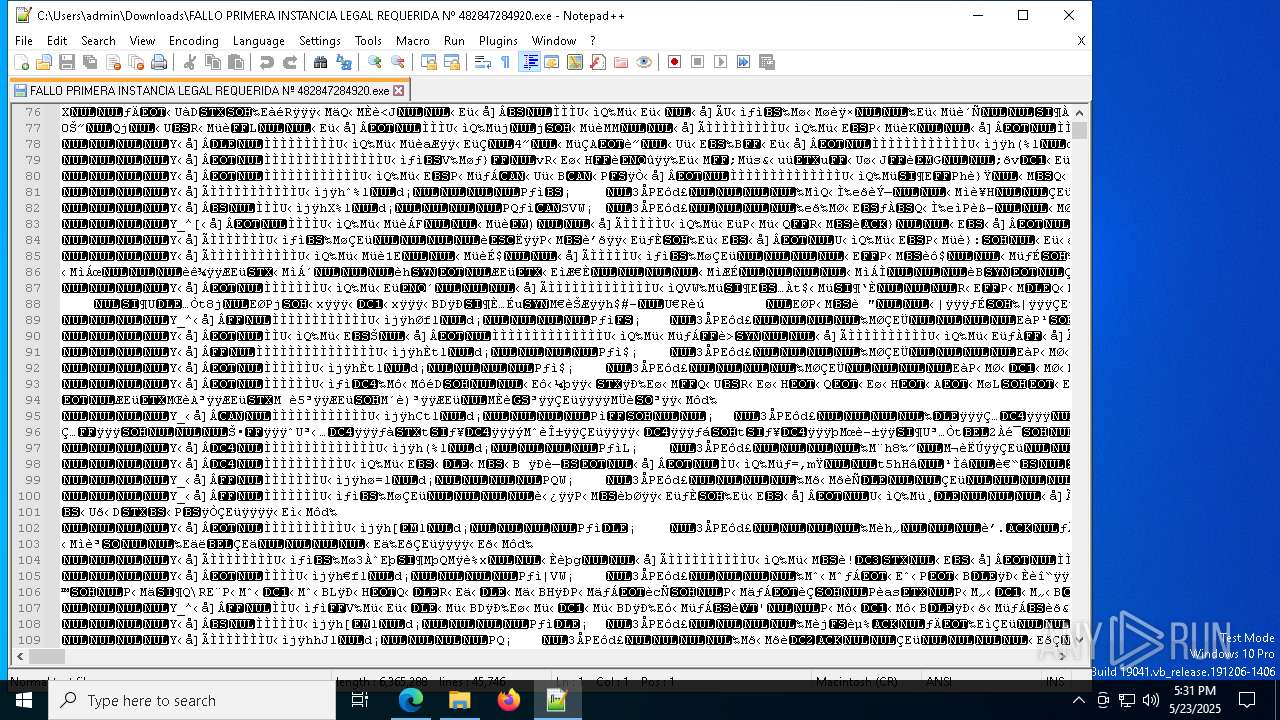
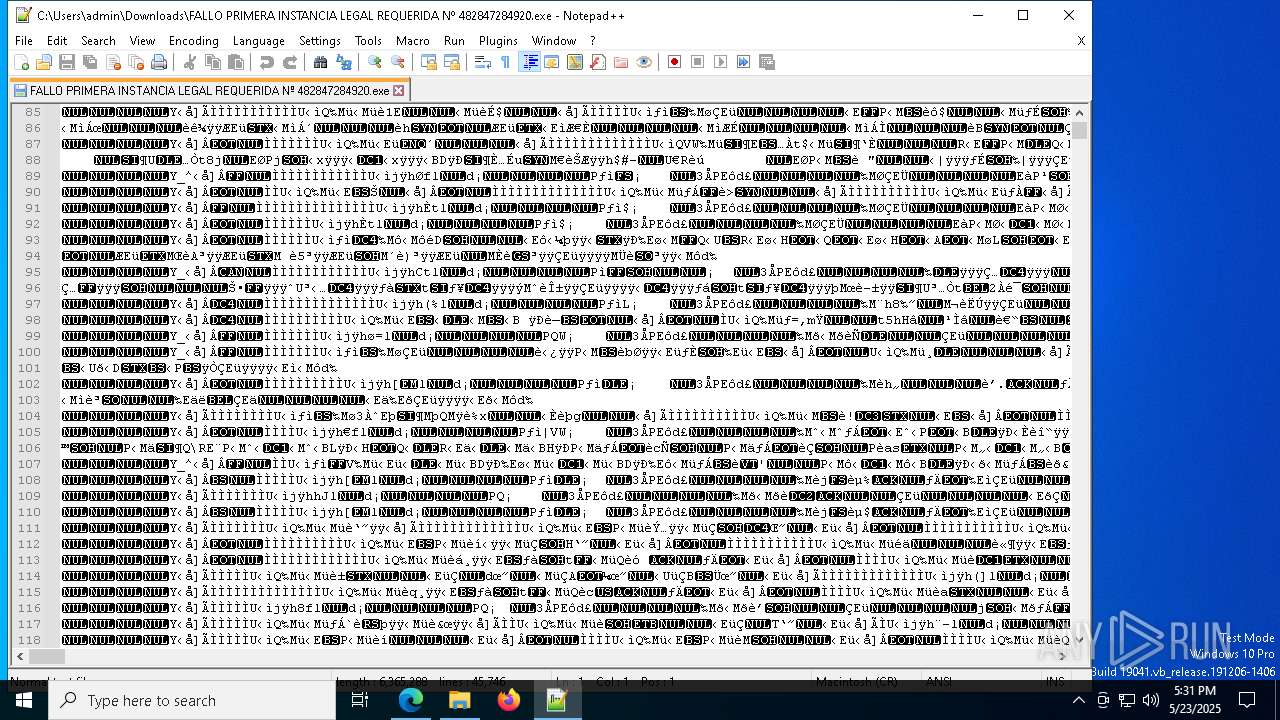
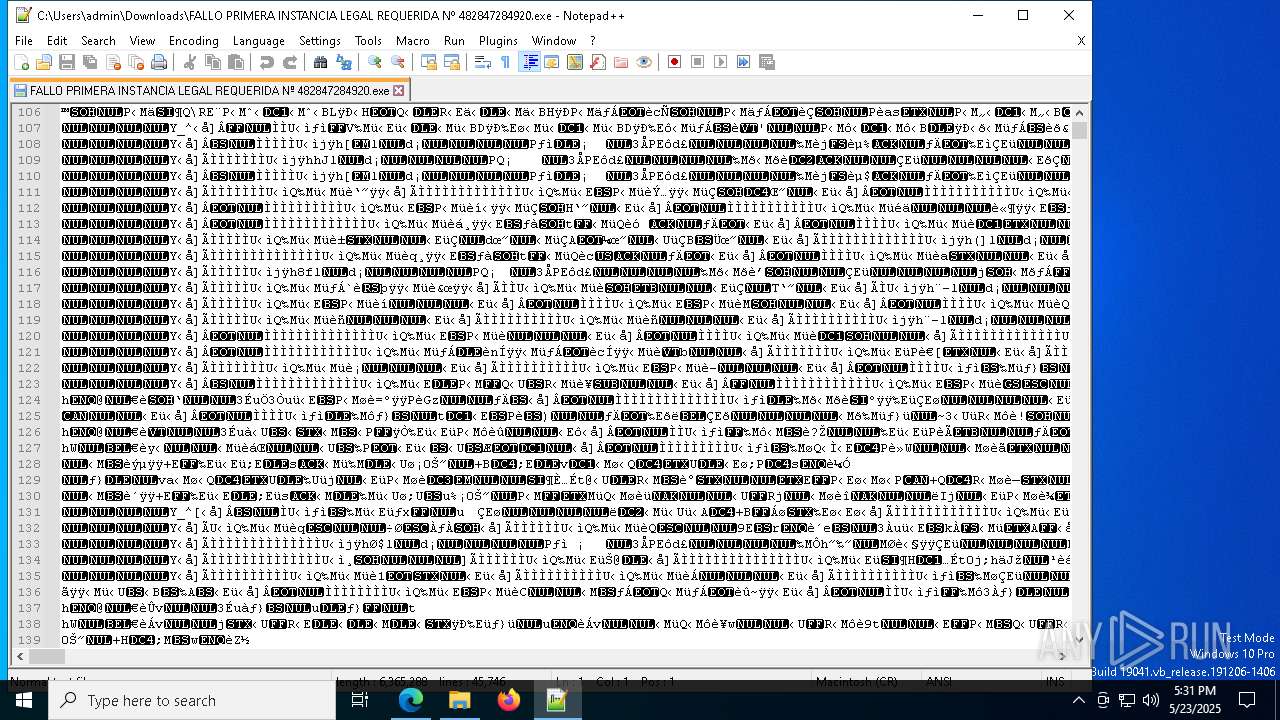
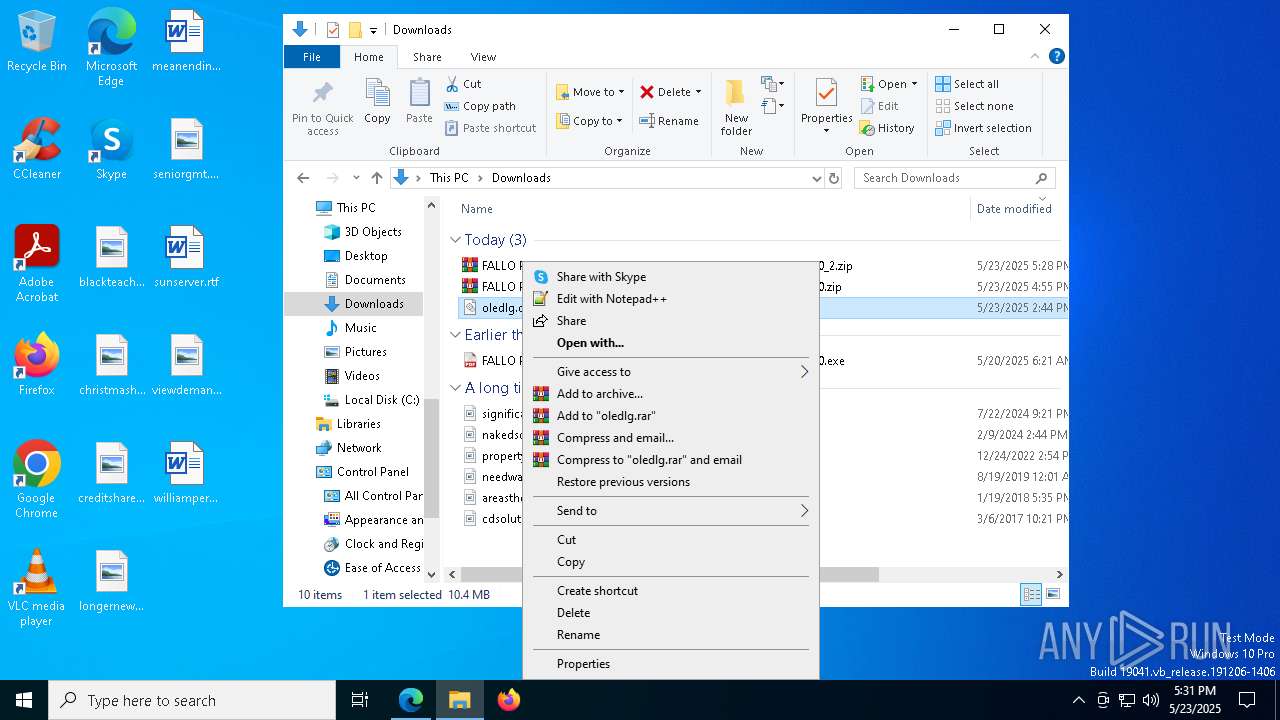
- notepad++.exe (PID: 7972)
- notepad++.exe (PID: 1168)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 6372)
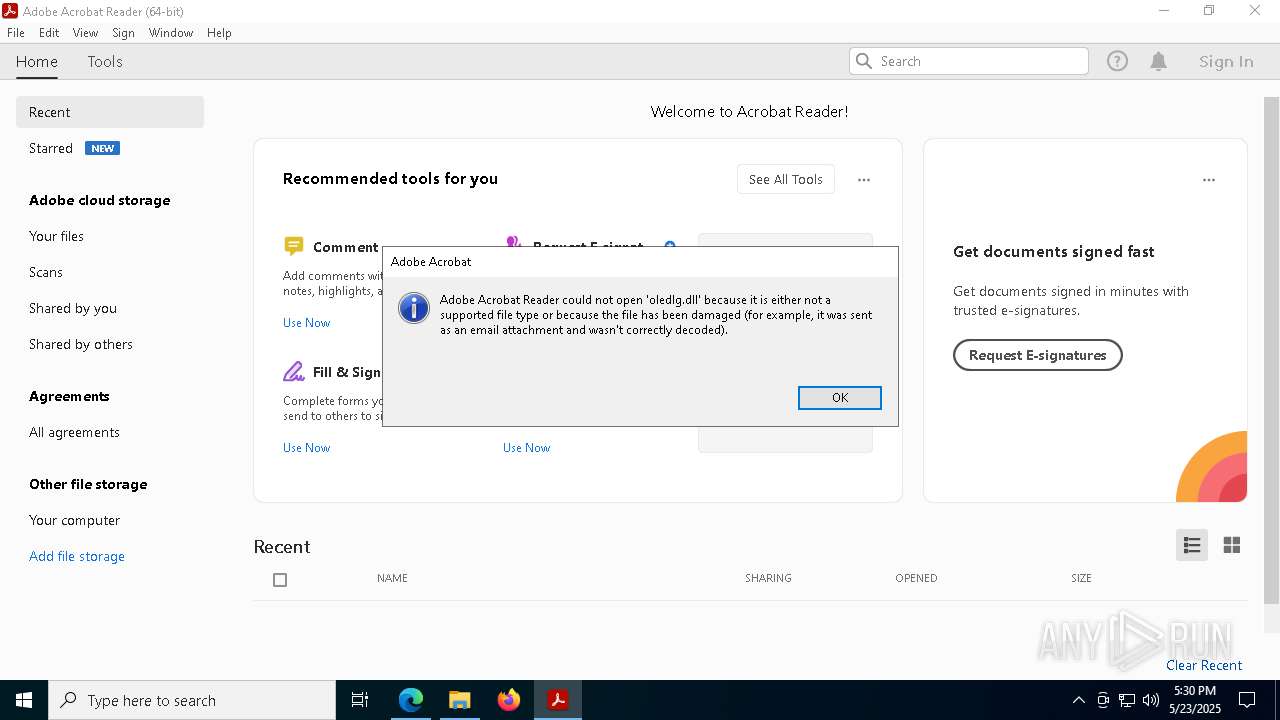
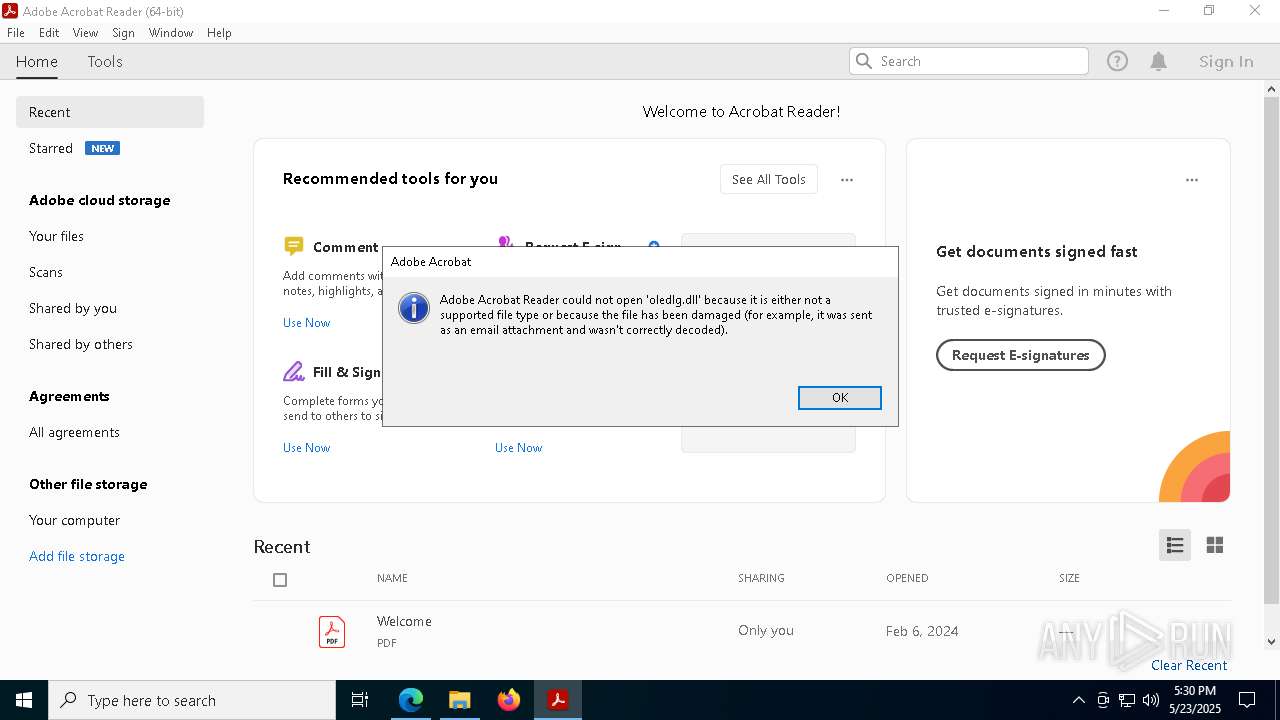
Application launched itself
- msedge.exe (PID: 7480)
- Acrobat.exe (PID: 5428)
- AcroCEF.exe (PID: 7232)
Checks supported languages
- identity_helper.exe (PID: 2320)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 6372)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 7524)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 3268)
- FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe (PID: 5508)
- csc.exe (PID: 1228)
The sample compiled with english language support
- msedge.exe (PID: 7736)
- msedge.exe (PID: 7480)
- WinRAR.exe (PID: 6476)
- WinRAR.exe (PID: 2908)
- csc.exe (PID: 1228)
- WinZIP.EXE (PID: 7036)
- Cac_M64.exe (PID: 3016)
- Cac_M64.exe (PID: 2652)
- msedge.exe (PID: 1452)
Reads the computer name
- identity_helper.exe (PID: 2320)
- csc.exe (PID: 1228)
Reads Environment values
- identity_helper.exe (PID: 2320)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2908)
- msedge.exe (PID: 1452)
Reads the machine GUID from the registry
- csc.exe (PID: 1228)
The executable file from the user directory is run by the Powershell process
- WinZIP.EXE (PID: 7036)
The sample compiled with chinese language support
- Cac_M64.exe (PID: 2652)
Reads the software policy settings
- slui.exe (PID: 7376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
233
Monitored processes
87
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3784 --field-trial-handle=2436,i,12109398838511899335,511989790616114272,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 536 | "C:\Windows\System32\cmd.exe" /c start /b powershell –ExecutionPolicy Bypass Start-Process -FilePath '"C:\Users\admin\AppData\Local\Temp\WinZIP.EXE"' & exit | C:\Windows\SysWOW64\cmd.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4356 --field-trial-handle=2436,i,12109398838511899335,511989790616114272,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
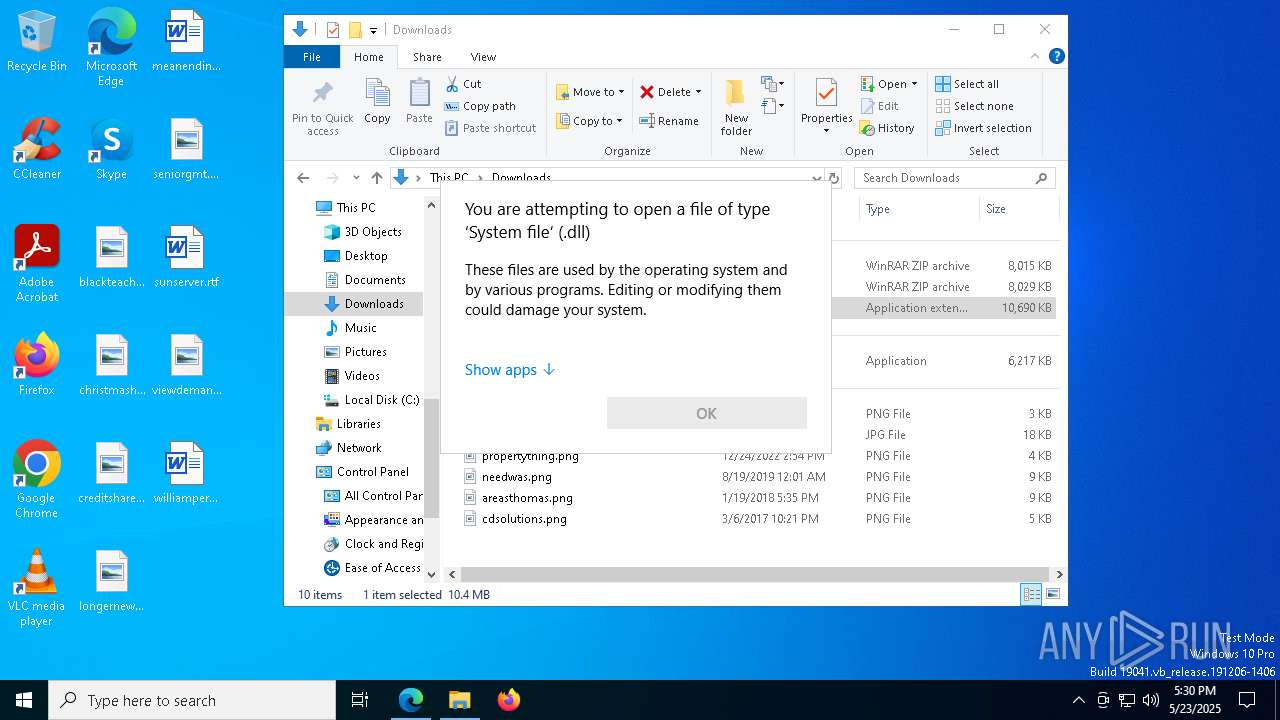
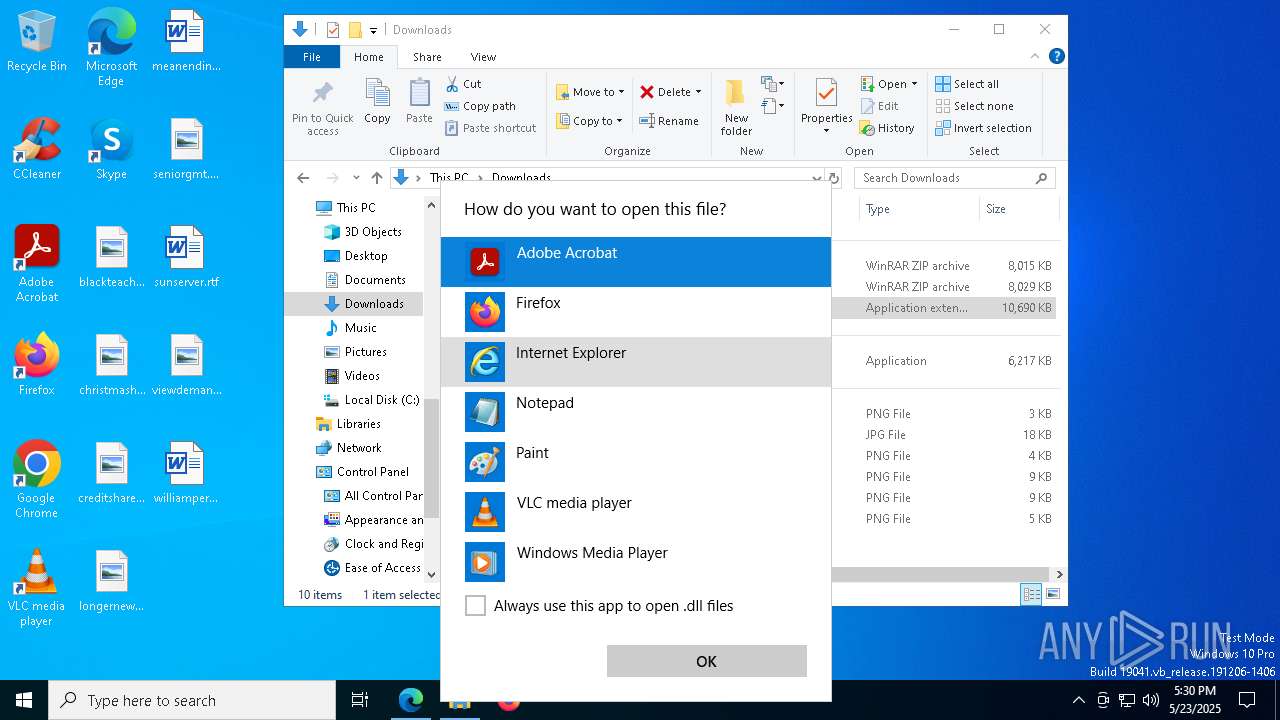
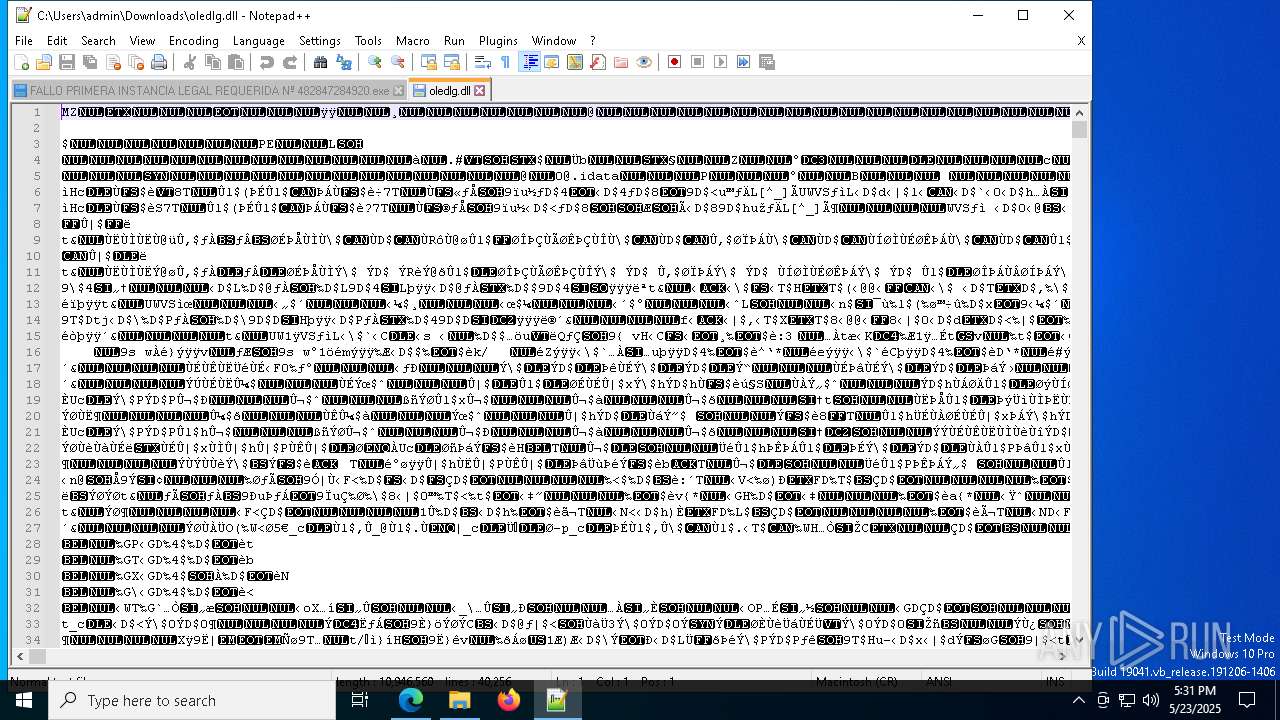
| 1168 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Downloads\oledlg.dll" | C:\Program Files\Notepad++\notepad++.exe | — | explorer.exe | |||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Version: 7.91 Modules
| |||||||||||||||
| 1228 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5384 --field-trial-handle=2436,i,12109398838511899335,511989790616114272,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1312 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | — | FALLO PRIMERA INSTANCIA LEGAL REQUERIDA Nº 482847284920.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1388 | C:\Users\admin\AppData\Local\NanoGa.exe | C:\Users\admin\AppData\Local\NanoGa.exe | Cac_M64.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.4.7.0 Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=5392 --field-trial-handle=2436,i,12109398838511899335,511989790616114272,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
36 991
Read events
36 788
Write events
184
Delete events
19
Modification events
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2A00B73467942F00 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 52A8C03467942F00 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3C2BC4A5-C2AC-4292-9BBF-404586E778C1} | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262982 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {64170931-CF56-4C6A-83D9-9273CE4D89A2} | |||
| (PID) Process: | (7200) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000076F4071108CCDB01 | |||
| (PID) Process: | (7480) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8D17E93467942F00 | |||
Executable files
19
Suspicious files
241
Text files
86
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a8c5.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a8f4.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a8f4.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a8d4.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a932.TMP | — | |
MD5:— | SHA256:— | |||
| 7480 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
56
DNS requests
67
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1052 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6156 | svchost.exe | HEAD | 200 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305662&P2=404&P3=2&P4=jZKvpbL%2fAH5Ro1GqmXZtIIxTXa8TFPGGXQpugCgSfwcr3PWvYzroFhp8hVisi0v3zJARiITp1yoG4iujMotaZg%3d%3d | unknown | — | — | whitelisted |
1052 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6156 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305662&P2=404&P3=2&P4=jZKvpbL%2fAH5Ro1GqmXZtIIxTXa8TFPGGXQpugCgSfwcr3PWvYzroFhp8hVisi0v3zJARiITp1yoG4iujMotaZg%3d%3d | unknown | — | — | whitelisted |
6156 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305662&P2=404&P3=2&P4=jZKvpbL%2fAH5Ro1GqmXZtIIxTXa8TFPGGXQpugCgSfwcr3PWvYzroFhp8hVisi0v3zJARiITp1yoG4iujMotaZg%3d%3d | unknown | — | — | whitelisted |
6156 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305662&P2=404&P3=2&P4=jZKvpbL%2fAH5Ro1GqmXZtIIxTXa8TFPGGXQpugCgSfwcr3PWvYzroFhp8hVisi0v3zJARiITp1yoG4iujMotaZg%3d%3d | unknown | — | — | whitelisted |
6156 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305662&P2=404&P3=2&P4=jZKvpbL%2fAH5Ro1GqmXZtIIxTXa8TFPGGXQpugCgSfwcr3PWvYzroFhp8hVisi0v3zJARiITp1yoG4iujMotaZg%3d%3d | unknown | — | — | whitelisted |
6156 | svchost.exe | GET | 206 | 208.89.74.31:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1748305662&P2=404&P3=2&P4=jZKvpbL%2fAH5Ro1GqmXZtIIxTXa8TFPGGXQpugCgSfwcr3PWvYzroFhp8hVisi0v3zJARiITp1yoG4iujMotaZg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6476 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7480 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7736 | msedge.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
7736 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7736 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7736 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7736 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7736 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1228 | csc.exe | Domain Observed Used for C2 Detected | REMOTE [ANY.RUN] AsyncRAT SSL certificate |
1228 | csc.exe | A Network Trojan was detected | ET MALWARE Observed Malicious SSL Cert (Various RAT) |
1228 | csc.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Malicious SSL Cert (AsyncRAT) |
1228 | csc.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |