| File name: | CrackSoftware.exe |
| Full analysis: | https://app.any.run/tasks/3c7c85dd-98f4-4eb1-838e-be986a7c622a |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | May 15, 2025, 12:58:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 7D3173723E130D5EF87A234E8B6B525A |
| SHA1: | B2B16F2954DC1E7EDE3B7C49400FAB6104198CE9 |
| SHA256: | 8F53789C4E0E06032BCF0B3DA0643B187AD8F1D60BFA2091E2A2A249BE596154 |
| SSDEEP: | 98304:eJDPe5JhSUrIVOOOv+5A+9ZmnlvoRri2VNjGb4YzBTmwTC0e9cusK9NI6iyHp2Ia:DkPQ9 |
MALICIOUS
ASYNCRAT has been detected (YARA)
- CrackSoftware.exe (PID: 7616)
SUSPICIOUS
Reads security settings of Internet Explorer
- CrackSoftware.exe (PID: 7616)
- MyExeFile.exe (PID: 8088)
Executable content was dropped or overwritten
- CrackSoftware.exe (PID: 7616)
Reads the BIOS version
- MyExeFile.exe (PID: 8088)
Connects to unusual port
- CrackSoftware.exe (PID: 7616)
INFO
Checks supported languages
- CrackSoftware.exe (PID: 7616)
- MyExeFile.exe (PID: 8088)
Create files in a temporary directory
- CrackSoftware.exe (PID: 7616)
Reads the computer name
- CrackSoftware.exe (PID: 7616)
- MyExeFile.exe (PID: 8088)
Reads the machine GUID from the registry
- CrackSoftware.exe (PID: 7616)
- MyExeFile.exe (PID: 8088)
Disables trace logs
- CrackSoftware.exe (PID: 7616)
Creates files or folders in the user directory
- CrackSoftware.exe (PID: 7616)
- MyExeFile.exe (PID: 8088)
Checks proxy server information
- CrackSoftware.exe (PID: 7616)
- MyExeFile.exe (PID: 8088)
Process checks computer location settings
- CrackSoftware.exe (PID: 7616)
Process checks whether UAC notifications are on
- MyExeFile.exe (PID: 8088)
Reads CPU info
- MyExeFile.exe (PID: 8088)
Compiled with Borland Delphi (YARA)
- CrackSoftware.exe (PID: 7616)
Reads the software policy settings
- MyExeFile.exe (PID: 8088)
Creates files in the program directory
- MyExeFile.exe (PID: 8088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
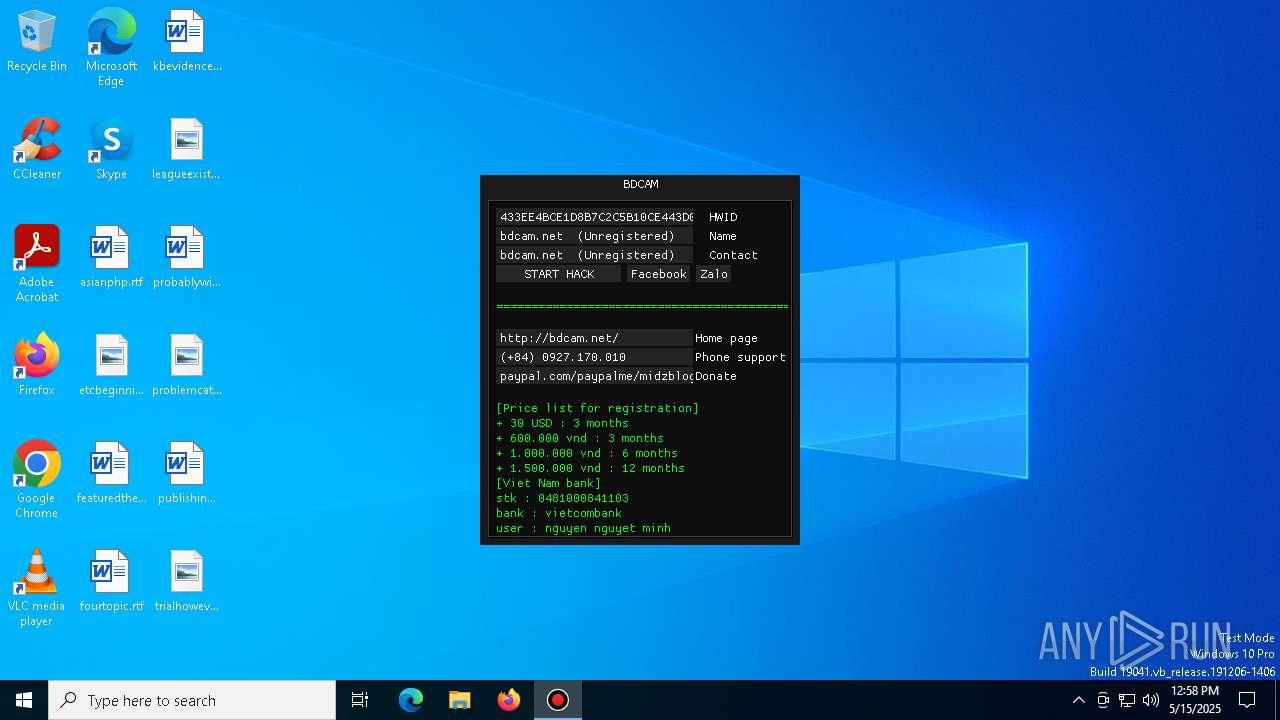
AsyncRat
(PID) Process(7616) CrackSoftware.exe
C2 (1)206.206.77.63
Ports (3)6606
7707
8808
Version0.5.8
BotnetFree1
Options
AutoRunfalse
MutexKw6rtGd3h9UZ
InstallFolder%AppData%
BSoDtrue
AntiVMtrue
Certificates
Cert1MIIE5jCCAs6gAwIBAgIQAM2HoLVRRIDi1g2hfnnn7TANBgkqhkiG9w0BAQ0FADAUMRIwEAYDVQQDDAlRTCBTZXJ2ZXIwIBcNMjUwNTA0MTczMDE2WhgPOTk5OTEyMzEyMzU5NTlaMBQxEjAQBgNVBAMMCVFMIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKPm9cMAneGWF3gsiX45rXDar/l3mV+vb3fEuUr1hFmPDJUKGOX6fAJhEQH6c+SF7iG8Yx8Twa52NtbBiuKv2TqLPVZV...
Server_SignatureL0WAP2wJ/8pe4YY033iBJWmMW6GuQ6KFU8/IT7001sF5aXj5yLMmxb2KgcWhVgPvBkj0vT+71rSsSnC6WWMvbv3M3lQEjODxQog6rbpY48Hk1zX+augACXLs4uSo19+89Lu8c+ONtLgSKiuSDacjJ1tSrOKu3WjPL0MJzhadThOuB+6M5fRYESjqwVGRCZPBgwzxYXCeq1yapfHSmsKdhvm1oFNSo4OzsC26/Hf6Eu1lO2USjwjdp1+1nEa4S6Dj23eENgnGU7V5Ou0reWOtUwaWY11xln9KjwkOQteU3iAi...
Keys
AES4da4f707cefca472038c47c402c61bd5ef4a12a57b108f09bc75541d9d570c65
Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.6) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:05:11 03:50:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 6691840 |
| InitializedDataSize: | 3072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x663b0e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.19041.1766 |
| ProductVersionNumber: | 6.2.19041.1766 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Microsoft Corporation |
| FileDescription: | XblGameSave Standby Task |
| FileVersion: | 6.2.19041.1766 |
| InternalName: | XblGameSave Standby Task |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| LegalTrademarks: | - |
| OriginalFileName: | XblGameSave Standby Task |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.2.19041.1766 |
| AssemblyVersion: | 6.2.19041.1766 |
Total processes
132
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7500 | "C:\Users\admin\Downloads\CrackSoftware.exe" | C:\Users\admin\Downloads\CrackSoftware.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: XblGameSave Standby Task Exit code: 3221226540 Version: 6.2.19041.1766 Modules
| |||||||||||||||
| 7616 | "C:\Users\admin\Downloads\CrackSoftware.exe" | C:\Users\admin\Downloads\CrackSoftware.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: XblGameSave Standby Task Version: 6.2.19041.1766 Modules
AsyncRat(PID) Process(7616) CrackSoftware.exe C2 (1)206.206.77.63 Ports (3)6606 7707 8808 Version0.5.8 BotnetFree1 Options AutoRunfalse MutexKw6rtGd3h9UZ InstallFolder%AppData% BSoDtrue AntiVMtrue Certificates Cert1MIIE5jCCAs6gAwIBAgIQAM2HoLVRRIDi1g2hfnnn7TANBgkqhkiG9w0BAQ0FADAUMRIwEAYDVQQDDAlRTCBTZXJ2ZXIwIBcNMjUwNTA0MTczMDE2WhgPOTk5OTEyMzEyMzU5NTlaMBQxEjAQBgNVBAMMCVFMIFNlcnZlcjCCAiIwDQYJKoZIhvcNAQEBBQADggIPADCCAgoCggIBAKPm9cMAneGWF3gsiX45rXDar/l3mV+vb3fEuUr1hFmPDJUKGOX6fAJhEQH6c+SF7iG8Yx8Twa52NtbBiuKv2TqLPVZV... Server_SignatureL0WAP2wJ/8pe4YY033iBJWmMW6GuQ6KFU8/IT7001sF5aXj5yLMmxb2KgcWhVgPvBkj0vT+71rSsSnC6WWMvbv3M3lQEjODxQog6rbpY48Hk1zX+augACXLs4uSo19+89Lu8c+ONtLgSKiuSDacjJ1tSrOKu3WjPL0MJzhadThOuB+6M5fRYESjqwVGRCZPBgwzxYXCeq1yapfHSmsKdhvm1oFNSo4OzsC26/Hf6Eu1lO2USjwjdp1+1nEa4S6Dj23eENgnGU7V5Ou0reWOtUwaWY11xln9KjwkOQteU3iAi... Keys AES4da4f707cefca472038c47c402c61bd5ef4a12a57b108f09bc75541d9d570c65 Saltbfeb1e56fbcd973bb219022430a57843003d5644d21e62b9d4f180e7e6c33941 | |||||||||||||||
| 8088 | "C:\Users\admin\AppData\Local\Temp\MyExeFile.exe" | C:\Users\admin\AppData\Local\Temp\MyExeFile.exe | — | CrackSoftware.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
3 301
Read events
3 281
Write events
20
Delete events
0
Modification events
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7616) CrackSoftware.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\CrackSoftware_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
14
Text files
46
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7616 | CrackSoftware.exe | C:\MU\Aida.png | image | |
MD5:EC943AFD0B61FA187041D96E4FB1CA76 | SHA256:0DAA51199EACC356FAB666BF802DC5A767B6E91935483939FDF1AB72965BF8DE | |||
| 7616 | CrackSoftware.exe | C:\MU\BalgassRefuge.png | image | |
MD5:0A951863D40B38180BAAF839FAC74DA8 | SHA256:CBEBF3D5F1FC34B8B6200E2226D714793FB19E335865FC0DD13A57609C88B4EF | |||
| 7616 | CrackSoftware.exe | C:\MU\Doppelganger4.png | image | |
MD5:262EC182C2DD8644ECF9495B3022B738 | SHA256:F4487F089CC7B498FFD362B781970F1AFE372BB3D8B7B4C41B4CF4696019F75A | |||
| 7616 | CrackSoftware.exe | C:\MU\ChaosCastle.png | image | |
MD5:0E16CE45CFAD9F1884BDFABF082CCBA2 | SHA256:A23D617559CEDE640908EA82BBDF7B3CB22D5B41C5F4F41561EEC2411118906A | |||
| 7616 | CrackSoftware.exe | C:\MU\Devias.png | image | |
MD5:FB140E82EB7891B83D8EFCD75E16A72A | SHA256:30A55165F4D4B9AA1882DE29AEE7DB0CA1814A335D1F11C4E2A128FC1C67490E | |||
| 7616 | CrackSoftware.exe | C:\MU\DuelArena.png | image | |
MD5:5F3765A786FC8F01FD7BD2AAB6611109 | SHA256:48389941D2EB297C207906C513B45321E7DFA68EBC301F8C881979C9C9D0E58F | |||
| 7616 | CrackSoftware.exe | C:\MU\Exile.png | image | |
MD5:A6AC624A5EF875CCFEA303EAB97E7DEC | SHA256:FAC0F8A018A074D565FD7C9332DBD1AF72D9BD7DA47A1BA723AD8D007997038F | |||
| 7616 | CrackSoftware.exe | C:\MU\Doppelganger2.png | image | |
MD5:15962699ADC3B6B43B14F87D451346E7 | SHA256:19C773879939762AB2965005A2E0C2E720140BD0D15E030CEF2D3B31078F0398 | |||
| 7616 | CrackSoftware.exe | C:\MU\Crywolf.png | image | |
MD5:AC89AB927C61EA4BB993E20ED61B8631 | SHA256:1CDADB93BA052A4F5391EE7A6E6DF451C97E3B3F5C9610CE9B2822A70CFAD975 | |||
| 7616 | CrackSoftware.exe | C:\MU\Dungeon.png | image | |
MD5:F541B7C60D9270C44C6386F7787BBACC | SHA256:9FD3DDFAB7BFDC5BB52A8337BBE5CEC3A7760596A953CE8F5CC7EDFC603B503A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
33
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.218.209.163:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7616 | CrackSoftware.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
7616 | CrackSoftware.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7616 | CrackSoftware.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
7616 | CrackSoftware.exe | GET | 404 | 14.225.204.125:80 | http://bdcam.net/NEW/NEW.php | unknown | — | — | malicious |
7616 | CrackSoftware.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCrZoa1YnvoBZaCEzAShkn1 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.218.209.163:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
811092dcc98648d790a1730d08245b4b.monitor-eqatec.com |
| unknown |
bdcam.net |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |