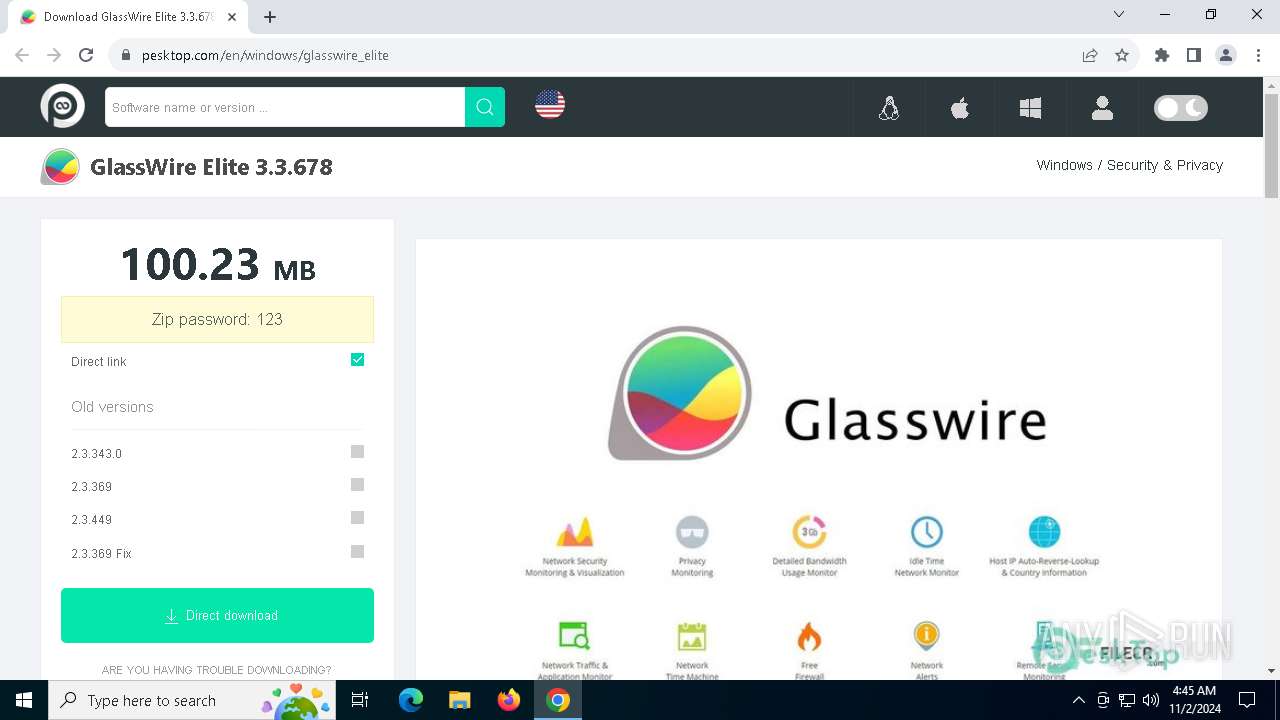
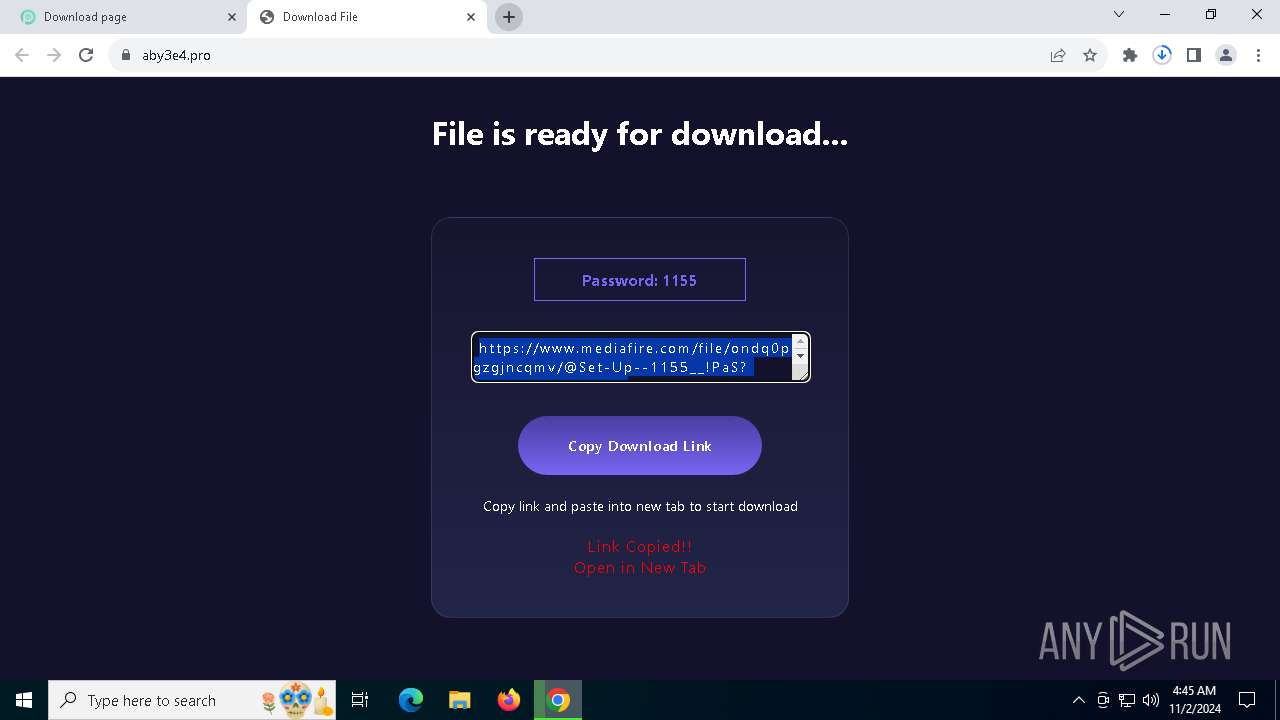
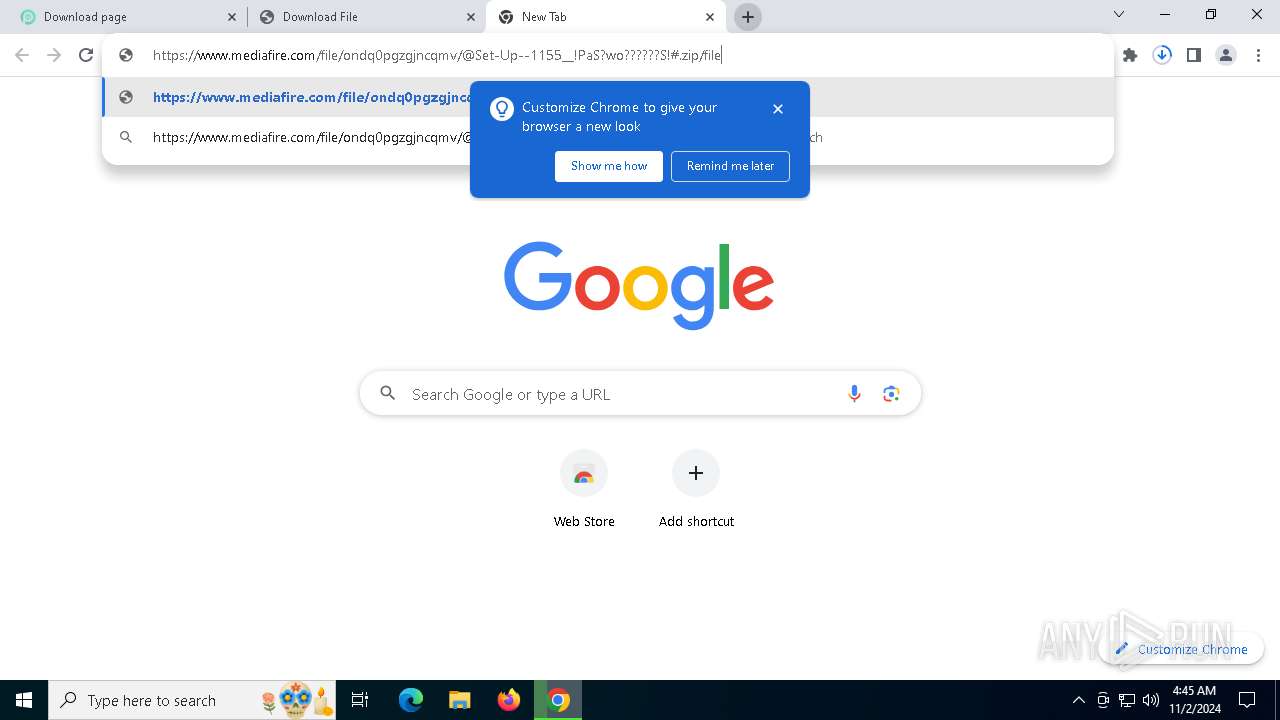
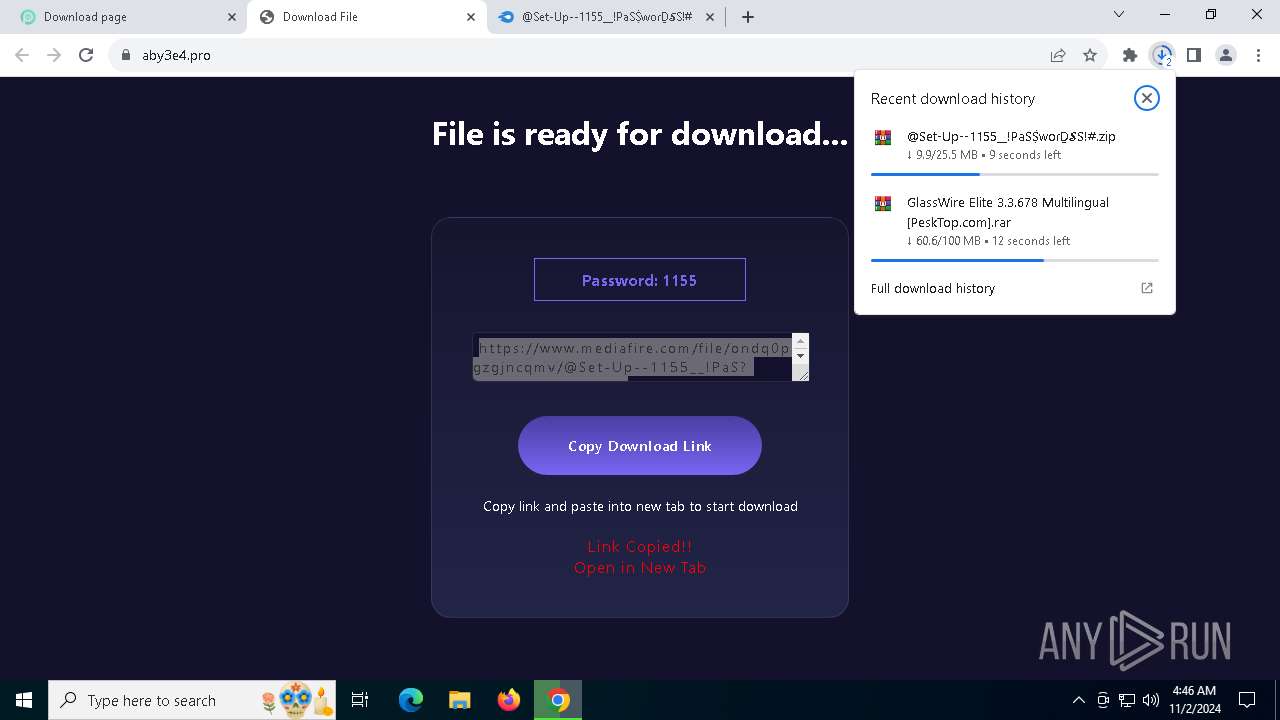
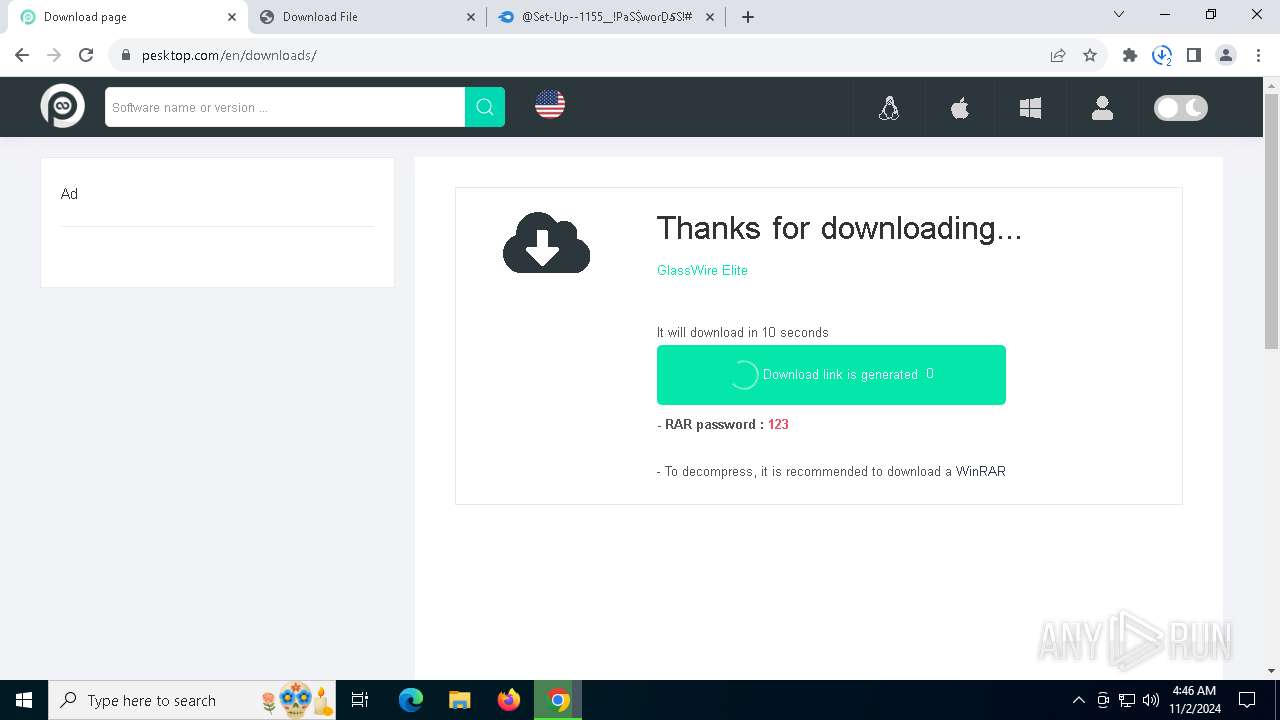
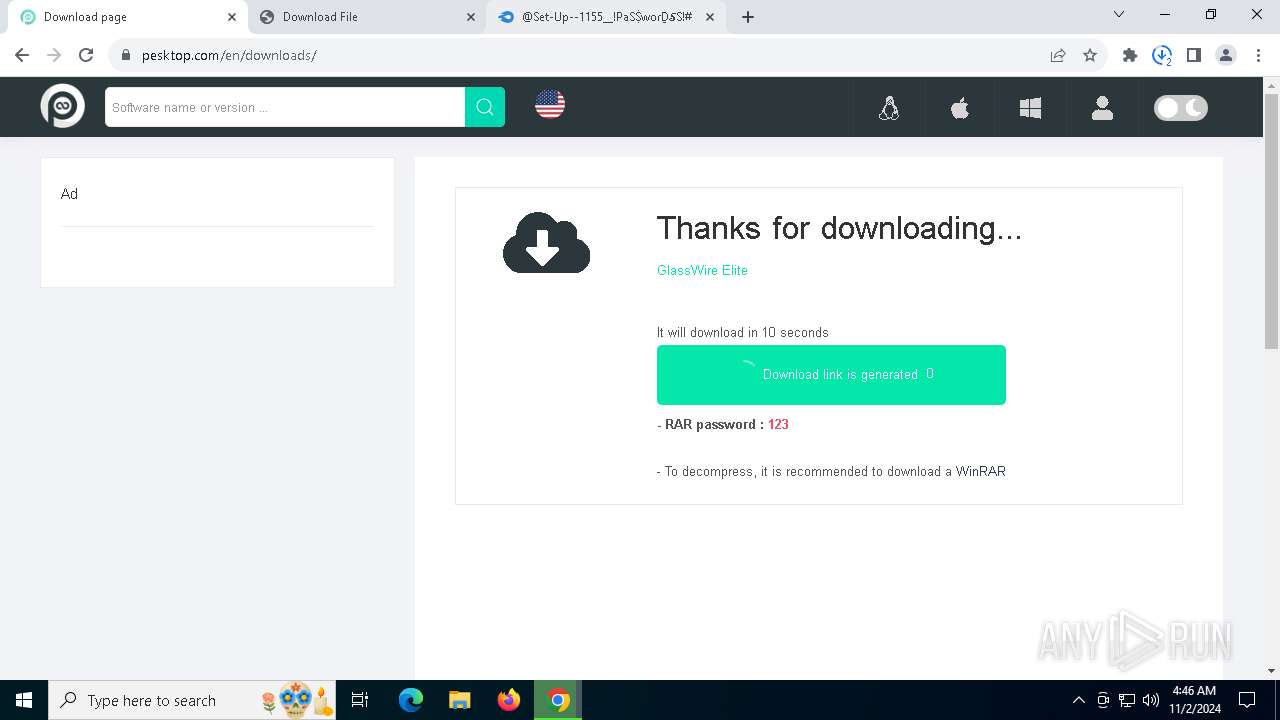
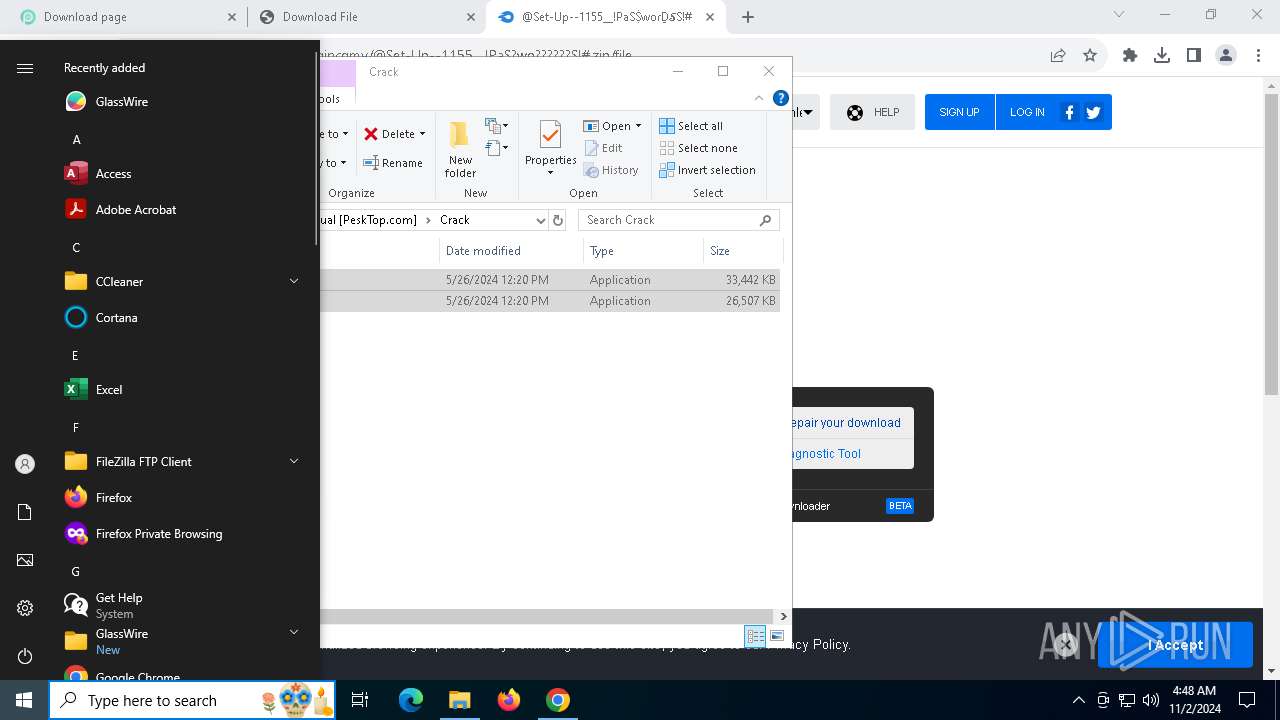
| URL: | https://pesktop.com/en/windows/glasswire_elite |
| Full analysis: | https://app.any.run/tasks/cca7aaf5-d965-4a58-9f7d-f373a389cdcd |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
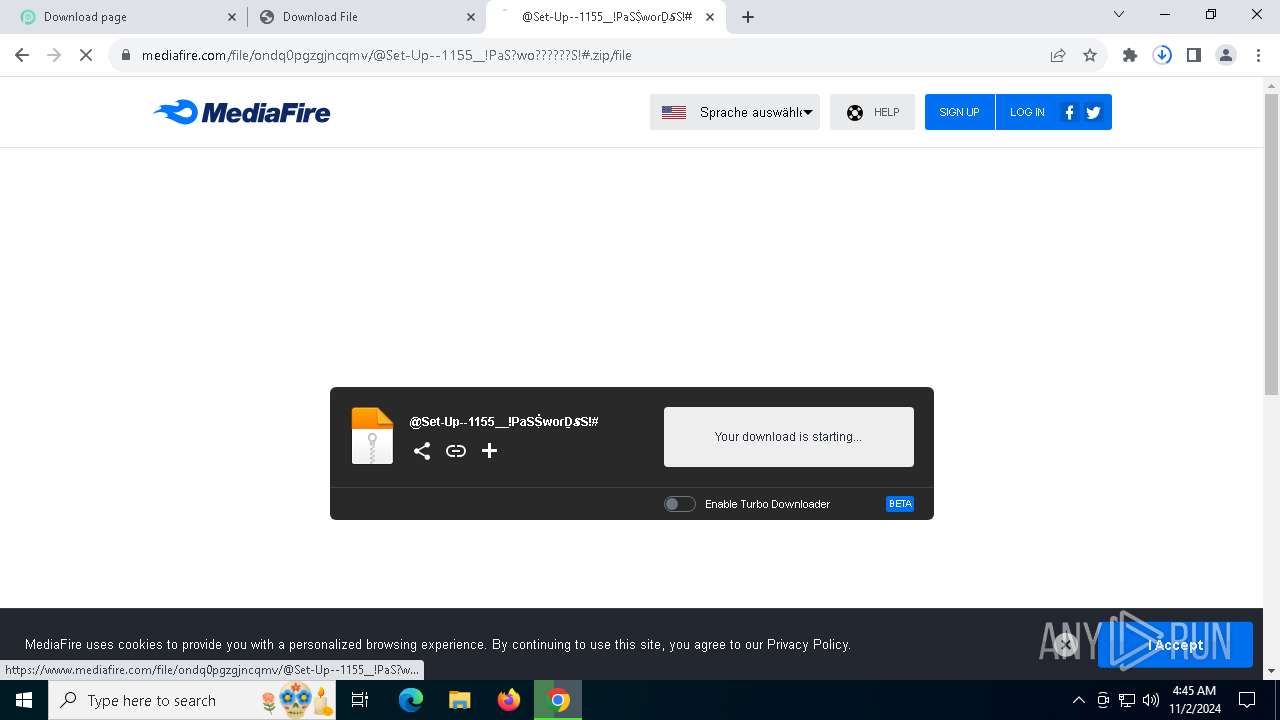
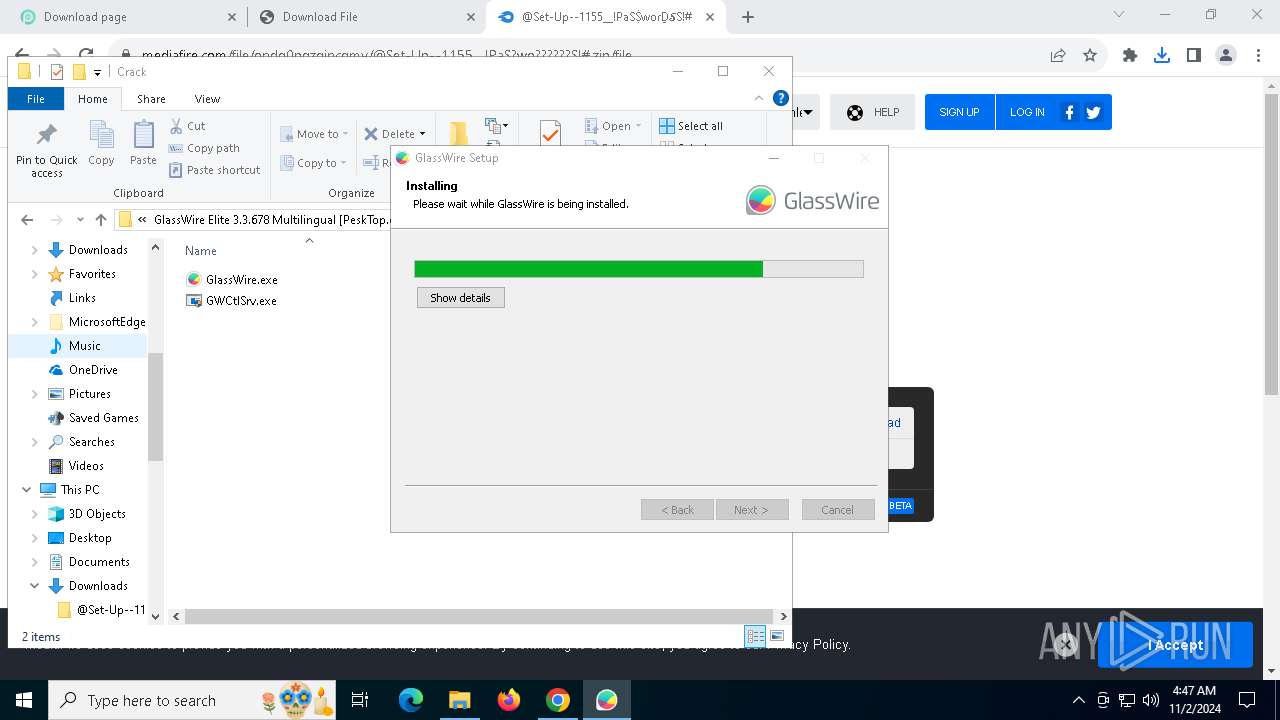
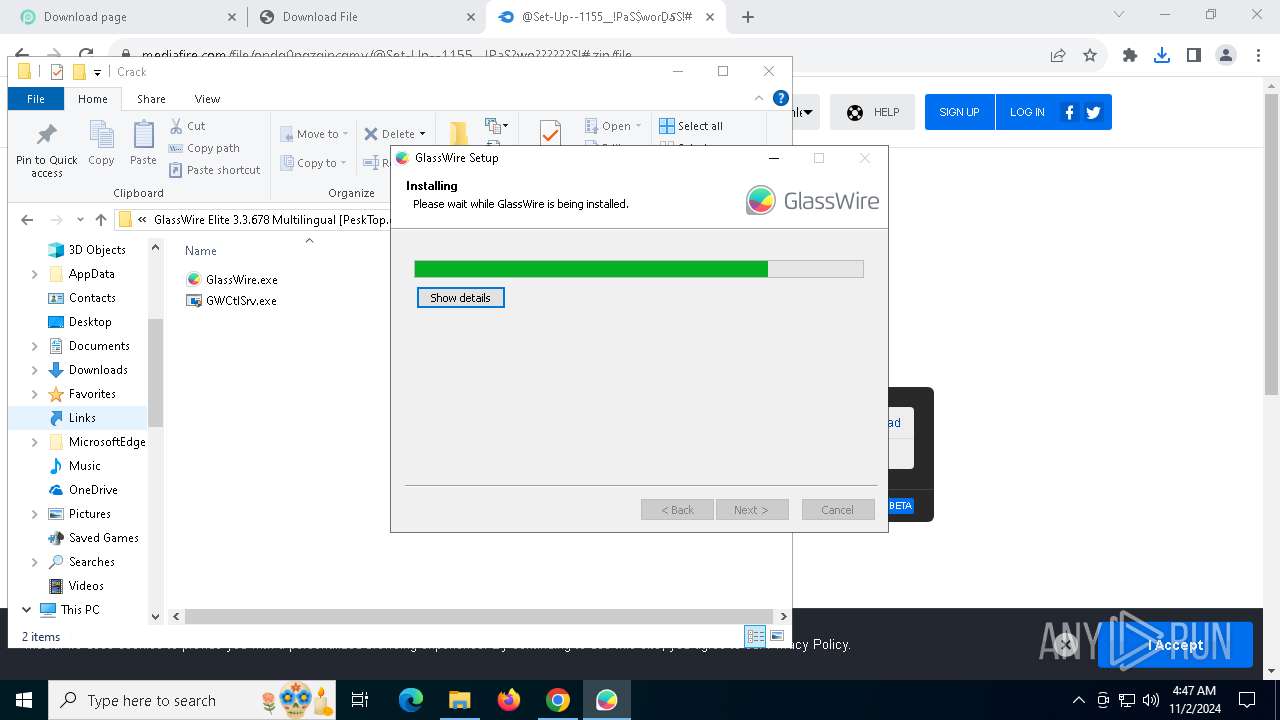
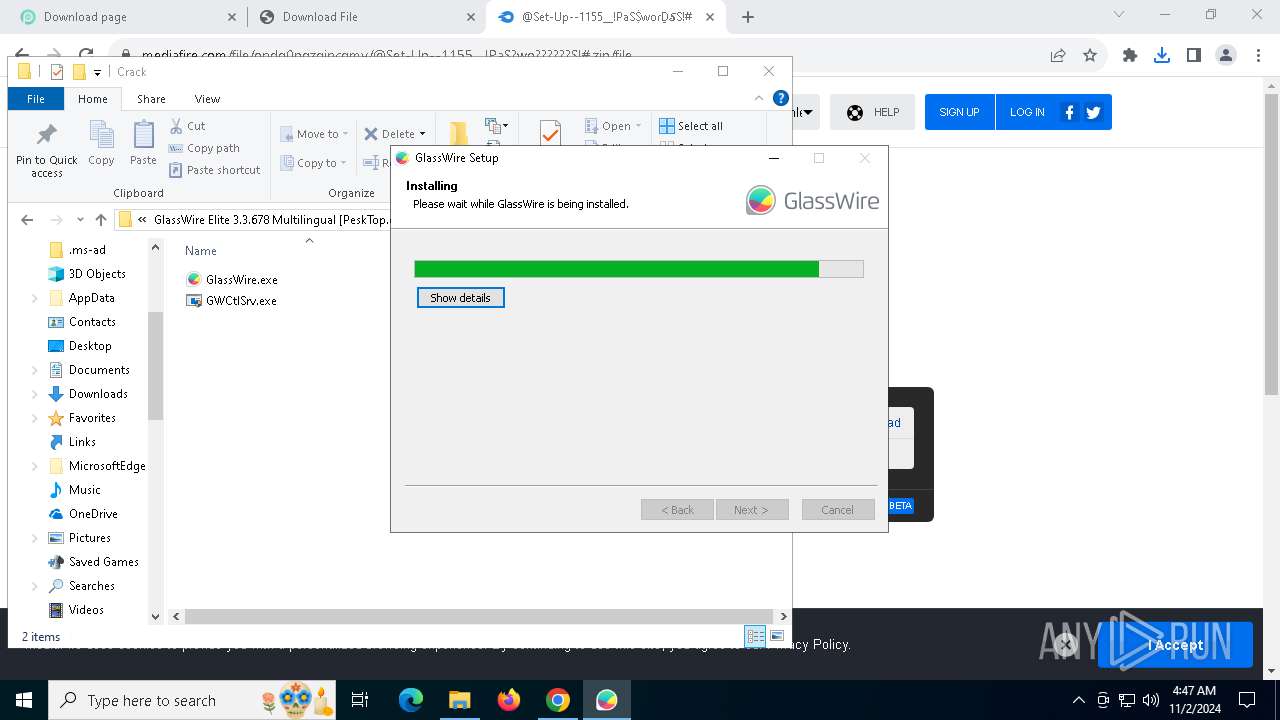
| Analysis date: | November 02, 2024, 04:45:24 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7D304E1AD7462DA9F9FBBF92D1E4A5D0 |
| SHA1: | 2250312085B6F180E339BF60796C7DBD188AB7E0 |
| SHA256: | 8F38A4AAB10AC0C80DD36744686DA6F8F5D9BF91C3417566D706EA4E1AF5FF04 |
| SSDEEP: | 3:N8EiVLKKFSML8XJefUV:2E2LKKF/L8XJefUV |
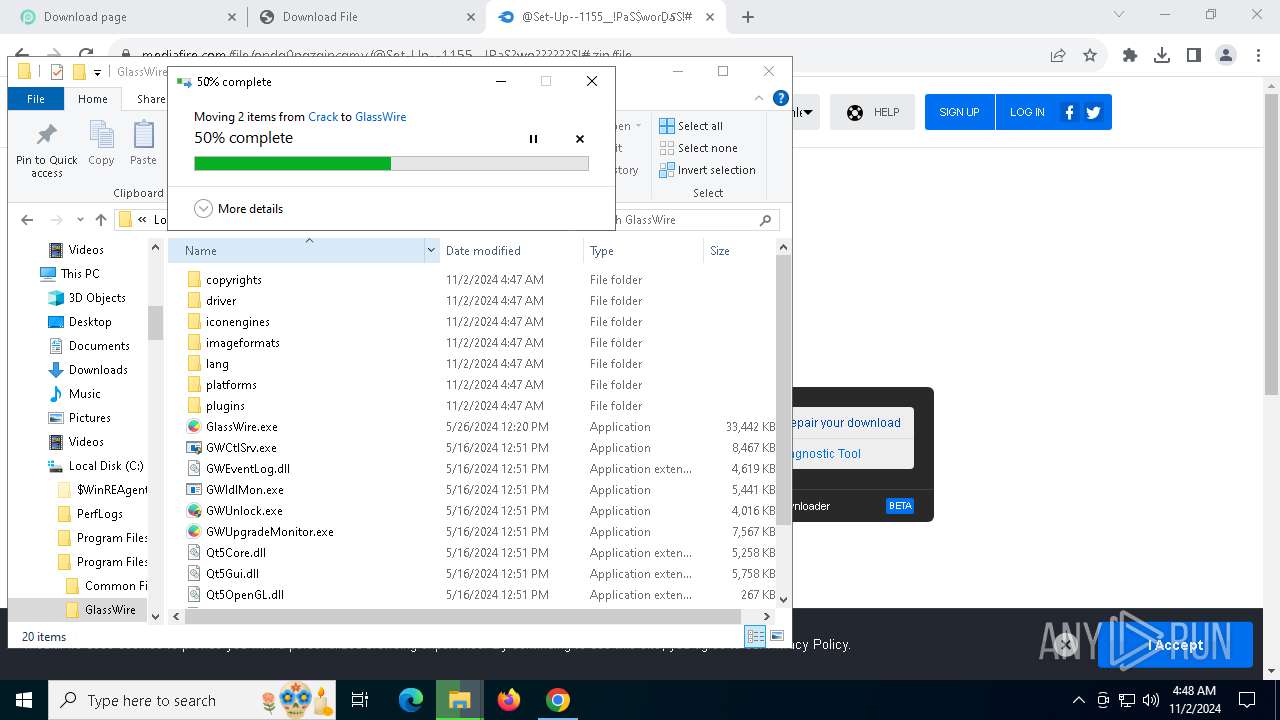
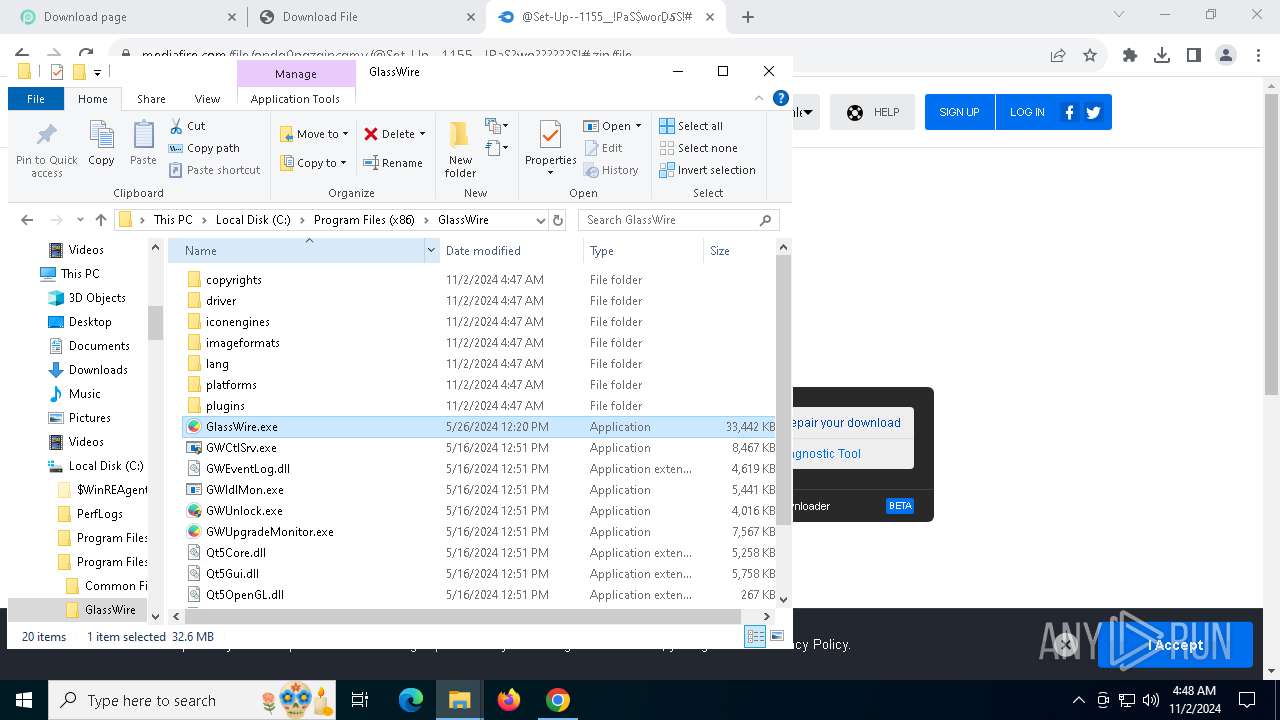
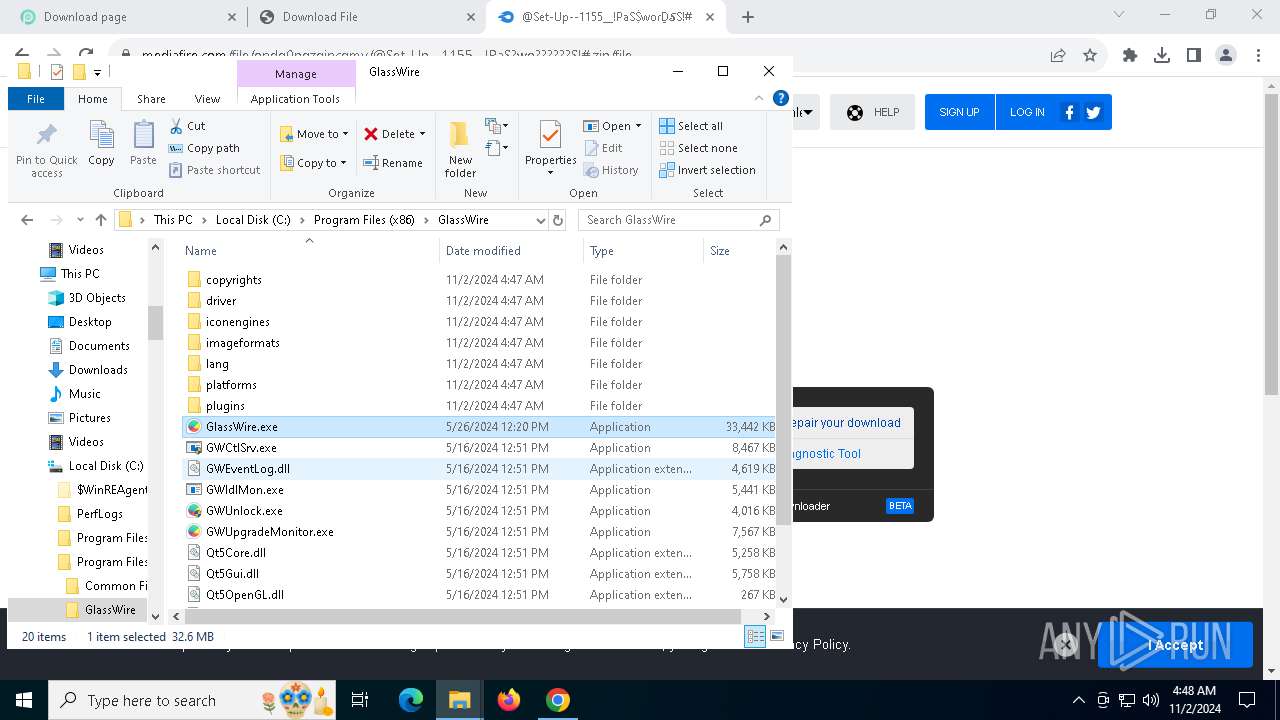
MALICIOUS
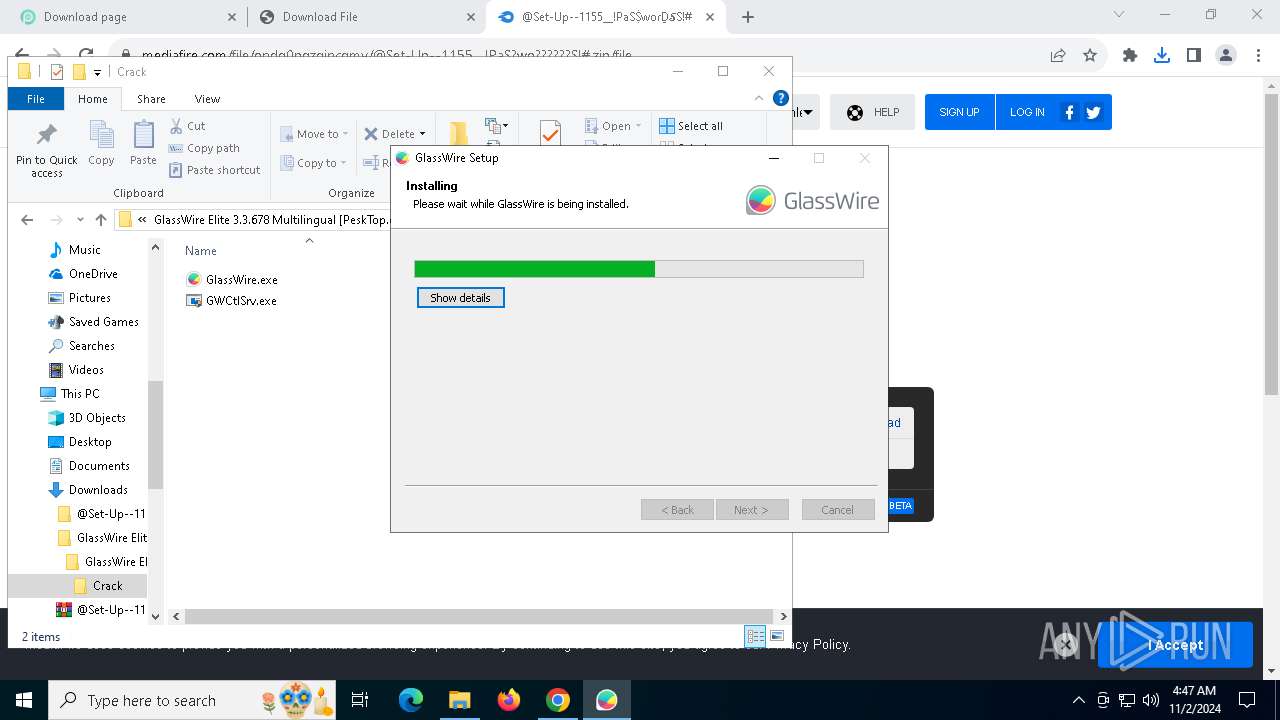
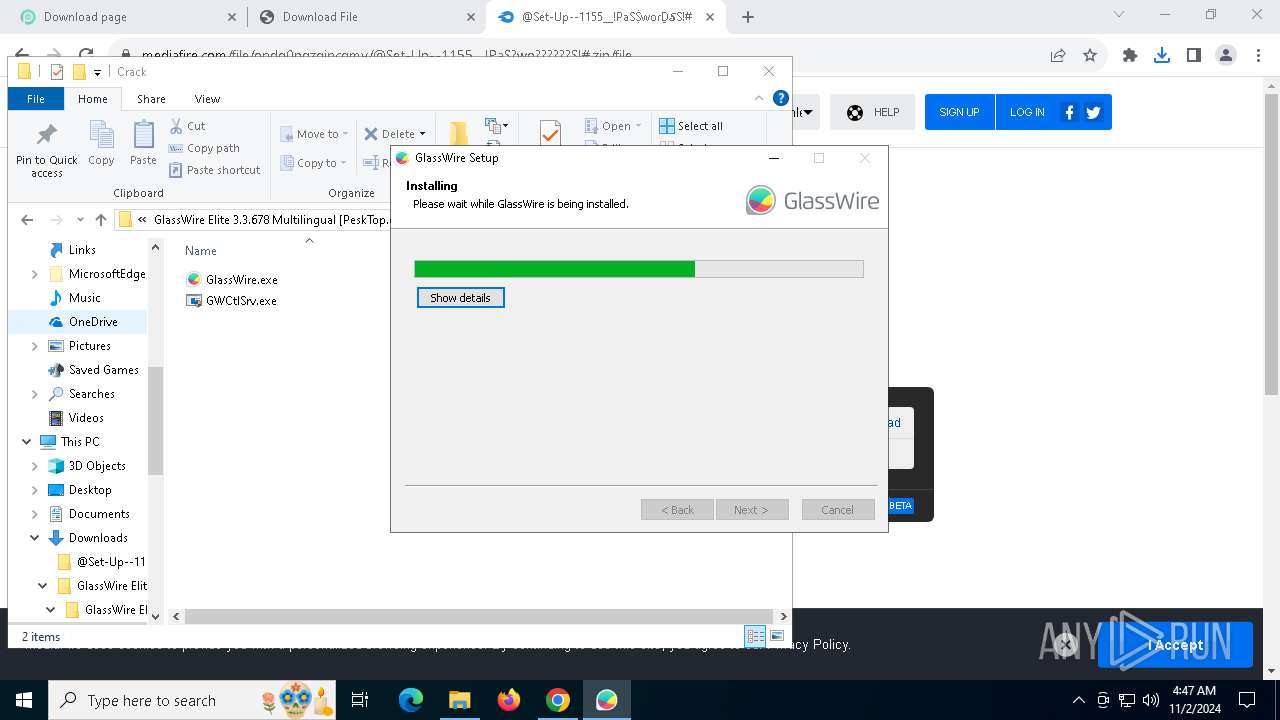
Starts NET.EXE for service management
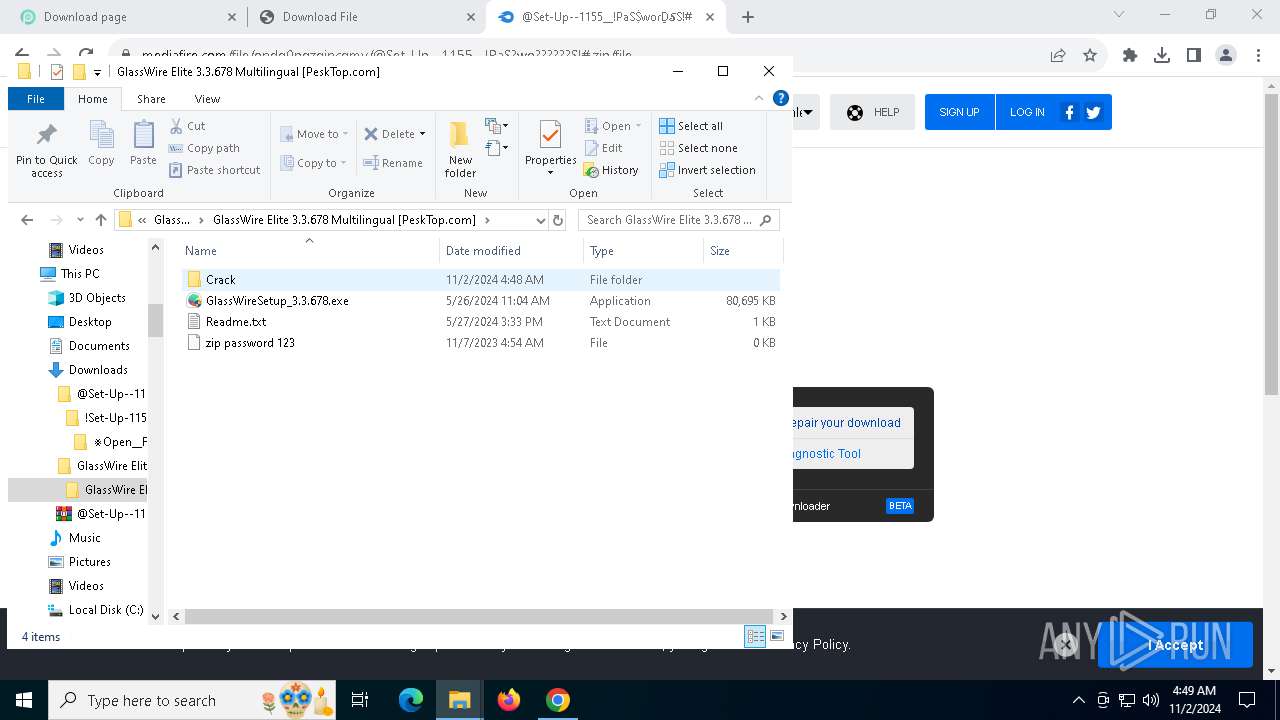
- GlassWireSetup_3.3.678.exe (PID: 4352)
- net.exe (PID: 6448)
Changes powershell execution policy (Bypass)
- AutoIt3.exe (PID: 6500)
Bypass execution policy to execute commands
- powershell.exe (PID: 7788)
SUSPICIOUS
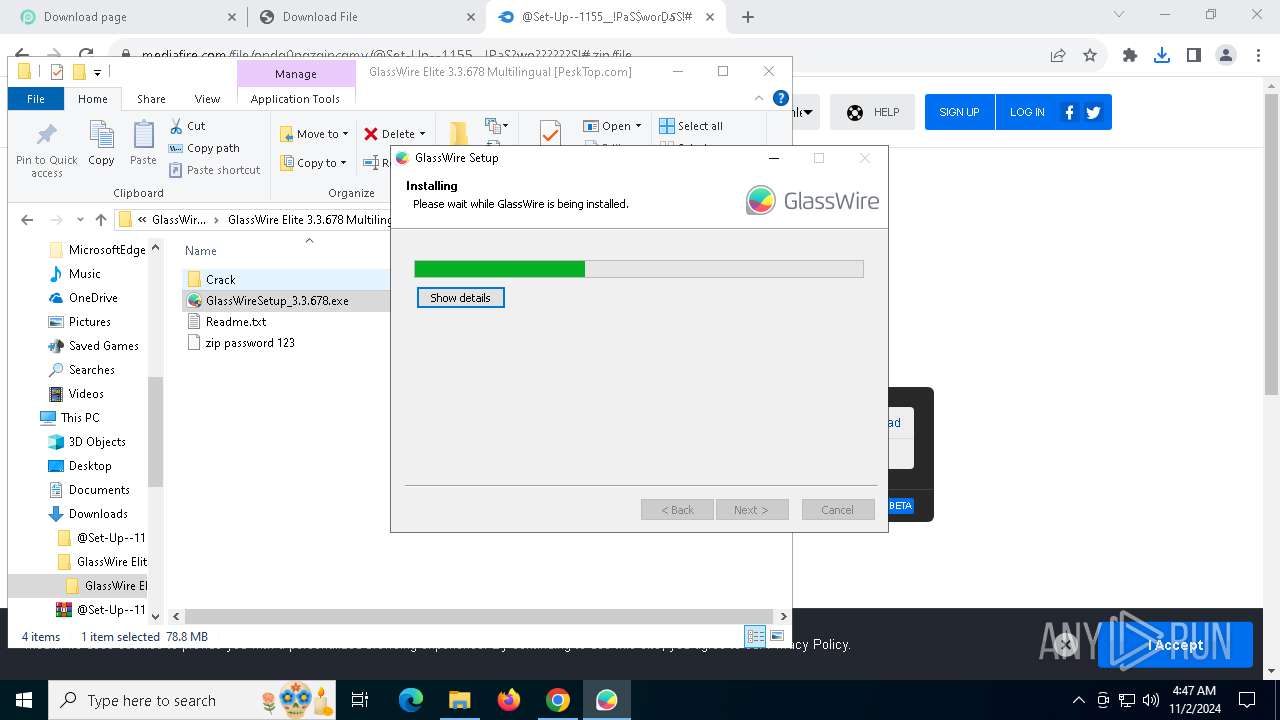
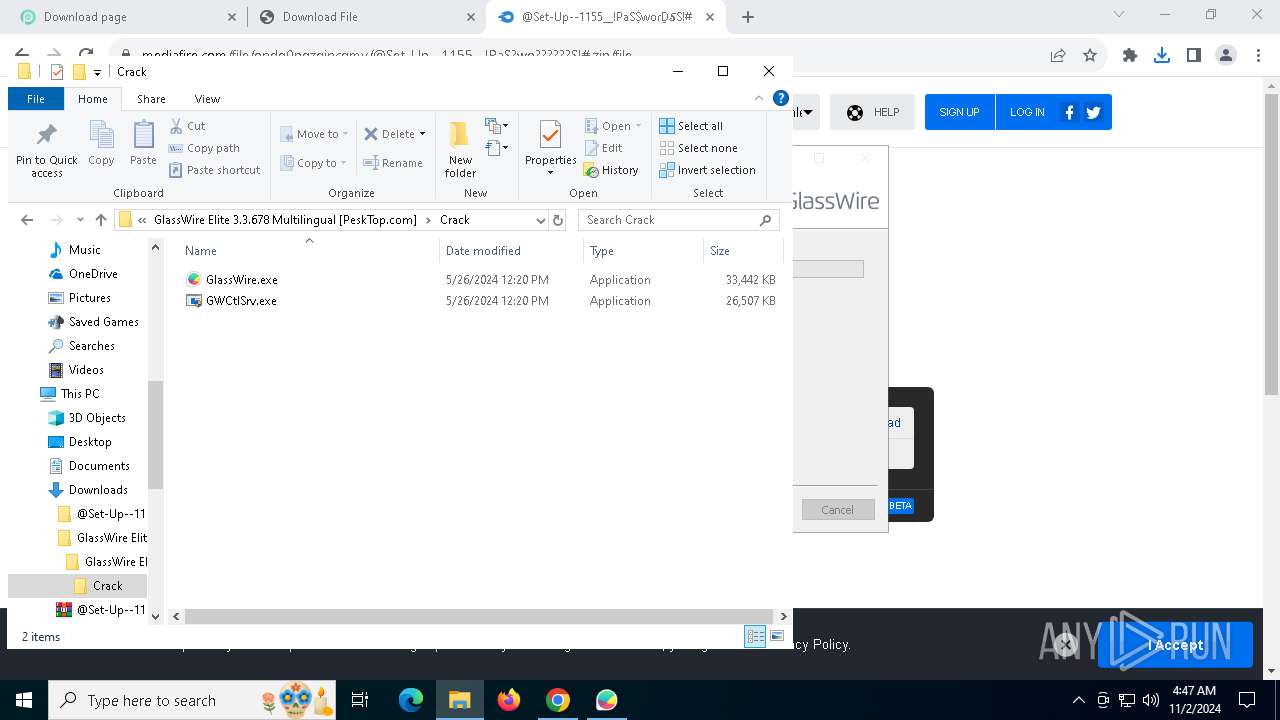
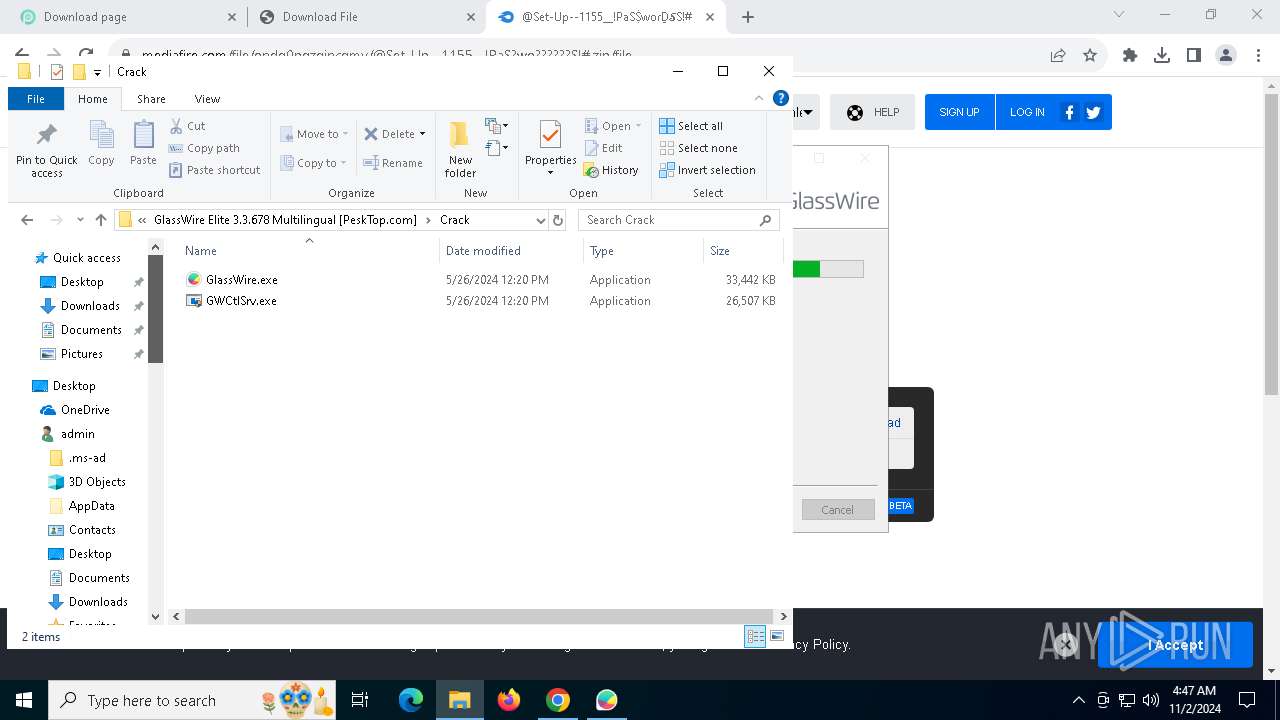
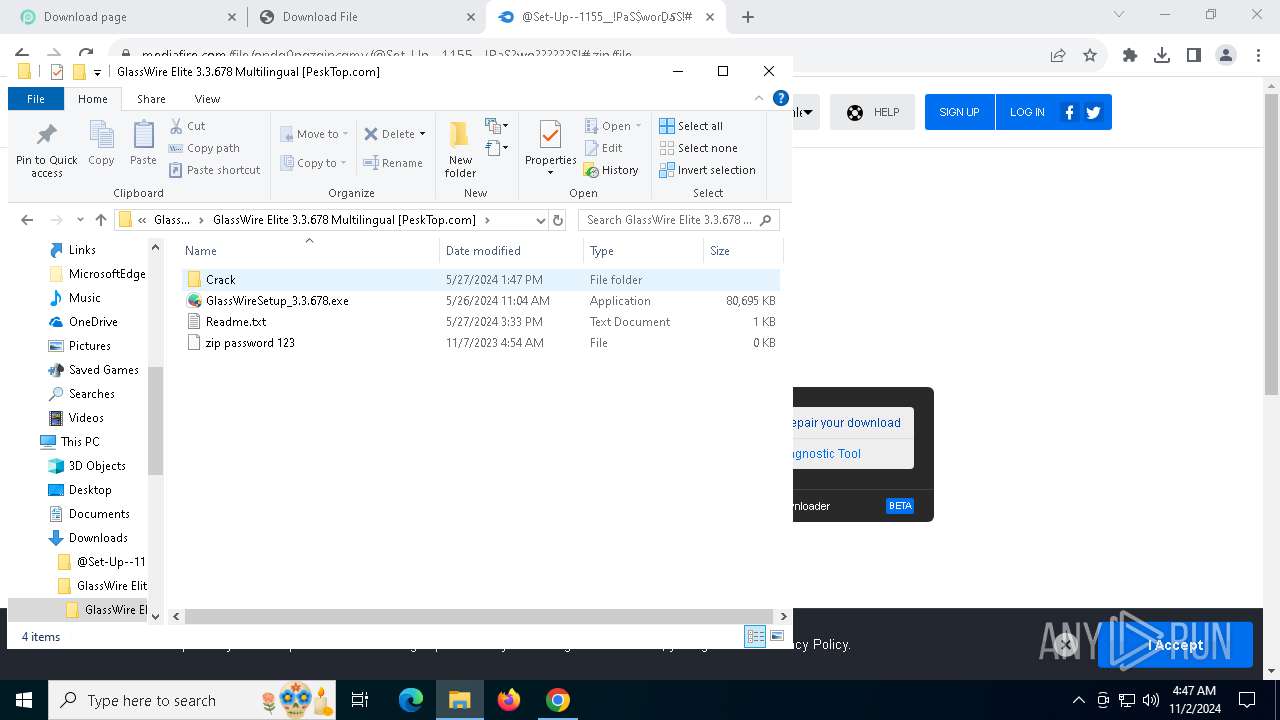
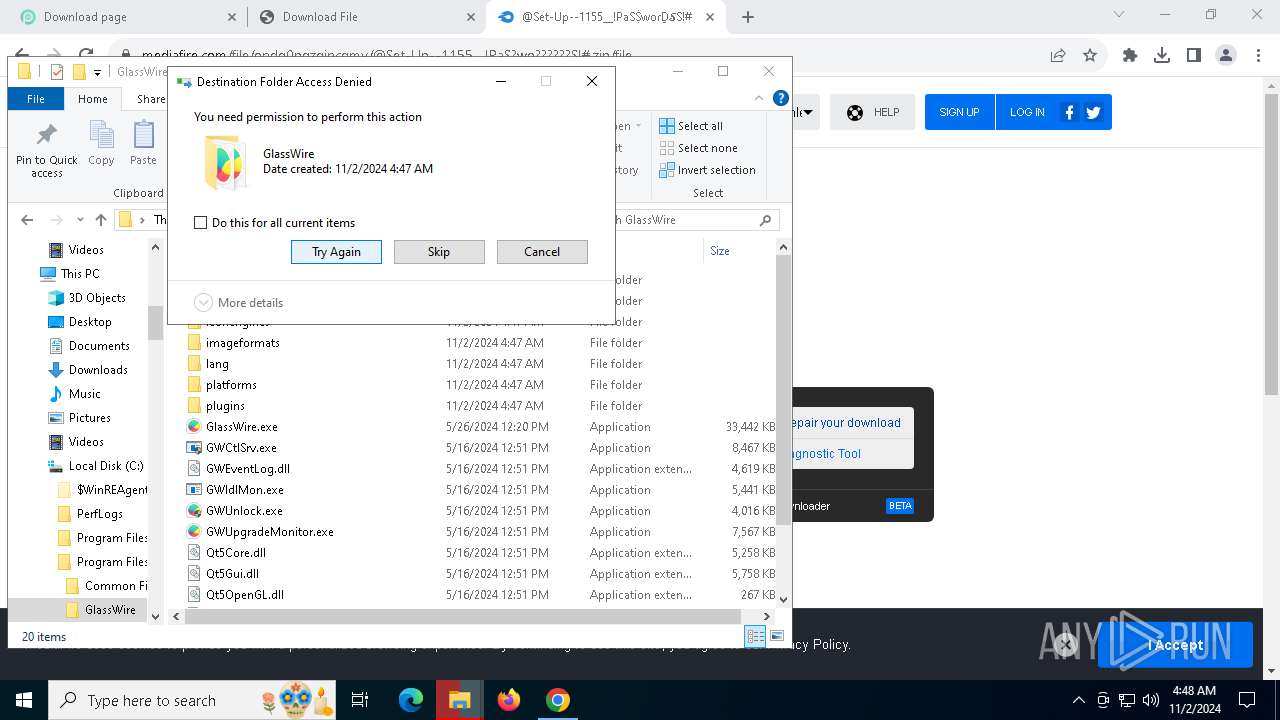
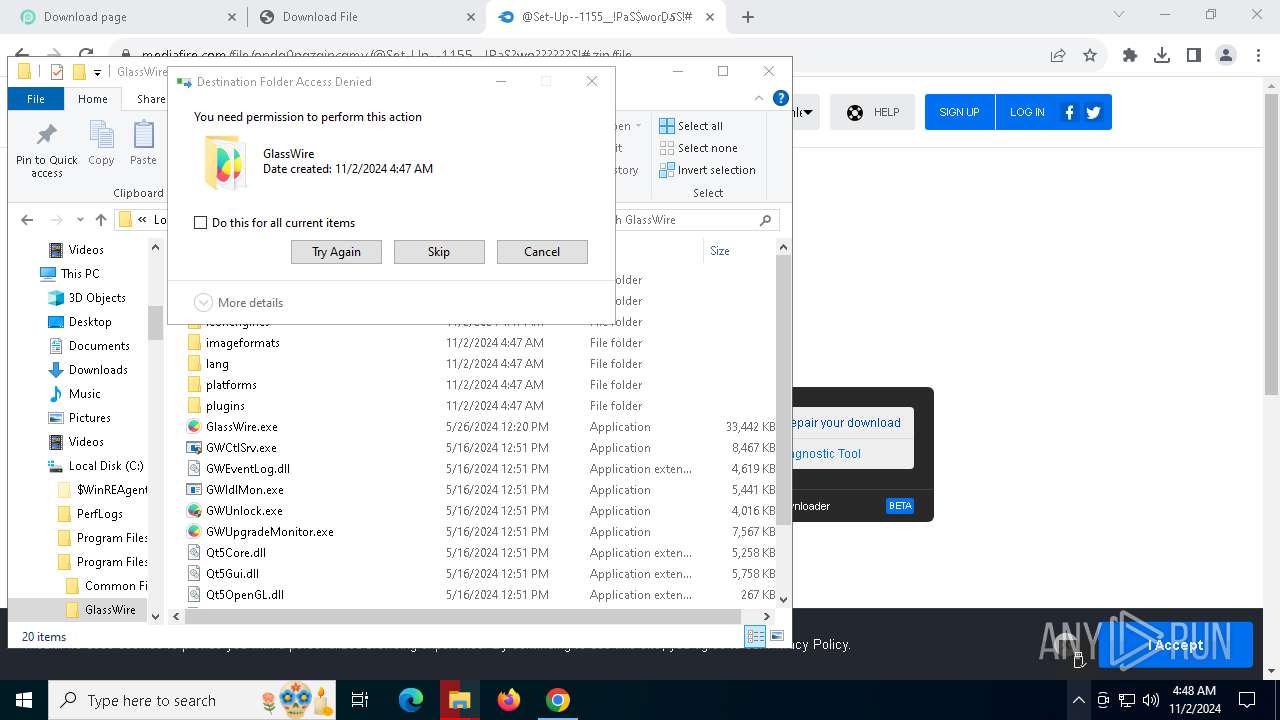
Malware-specific behavior (creating "System.dll" in Temp)
- GlassWireSetup_3.3.678.exe (PID: 4352)
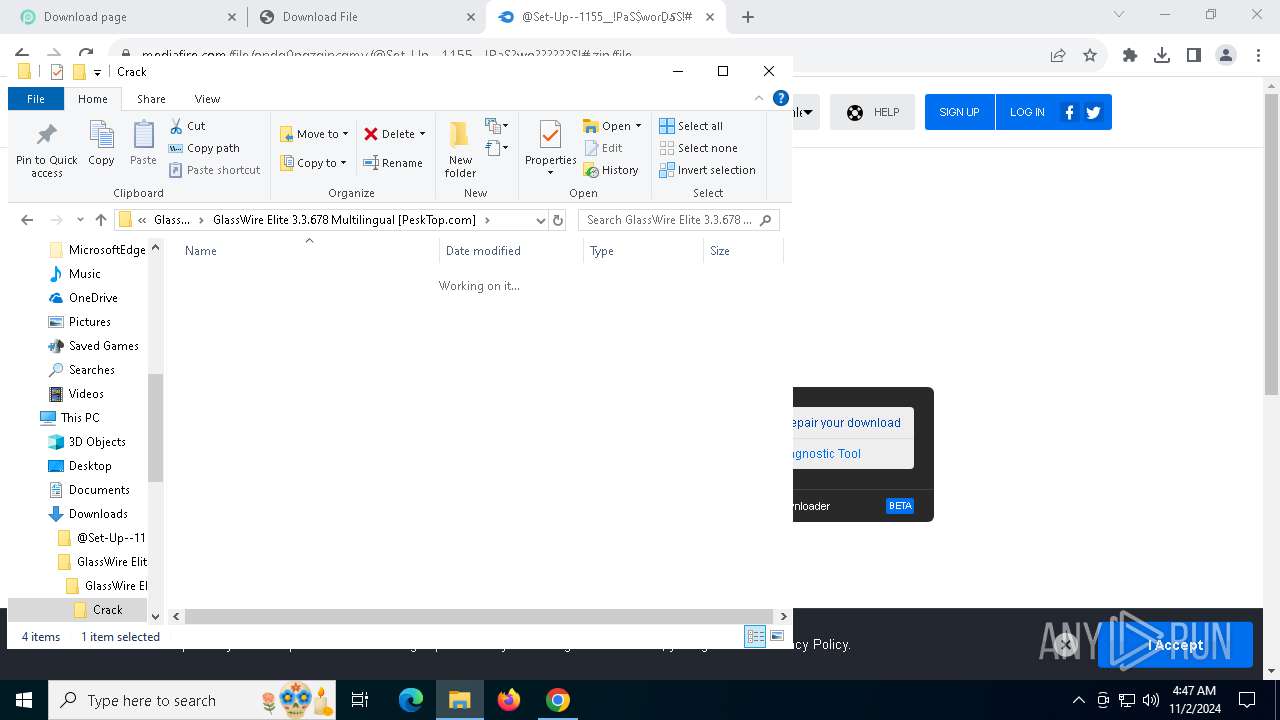
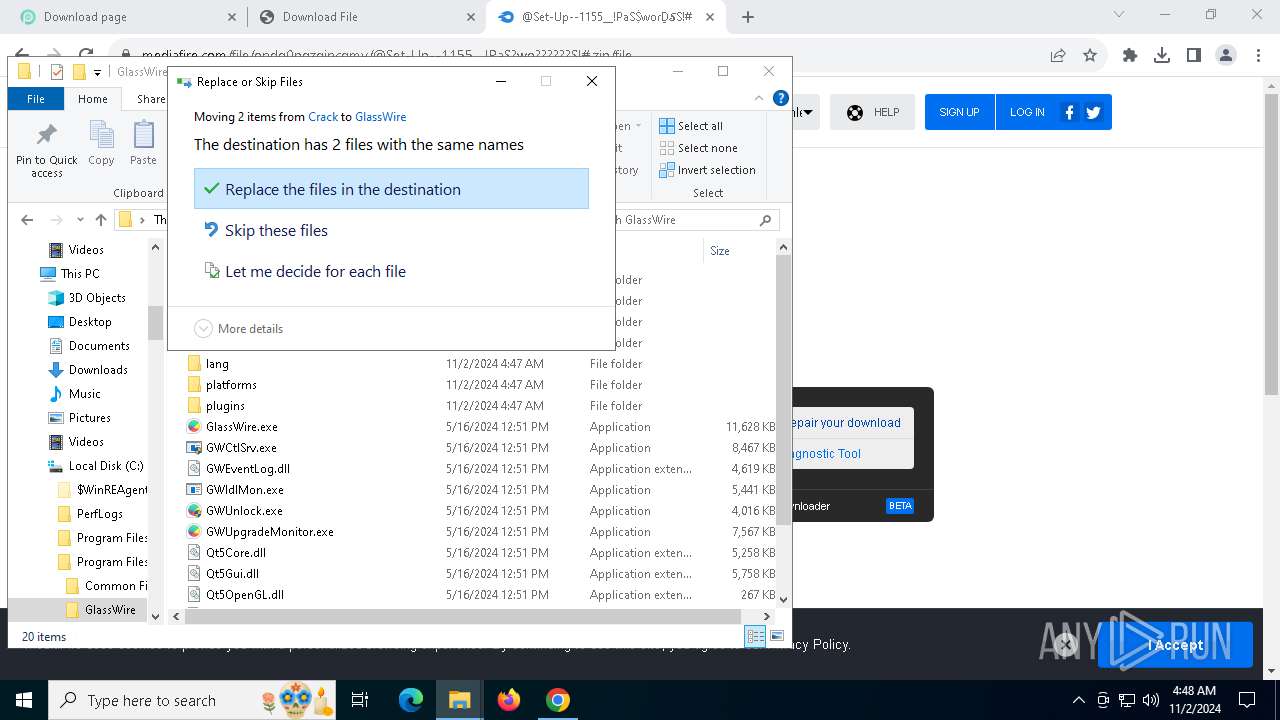
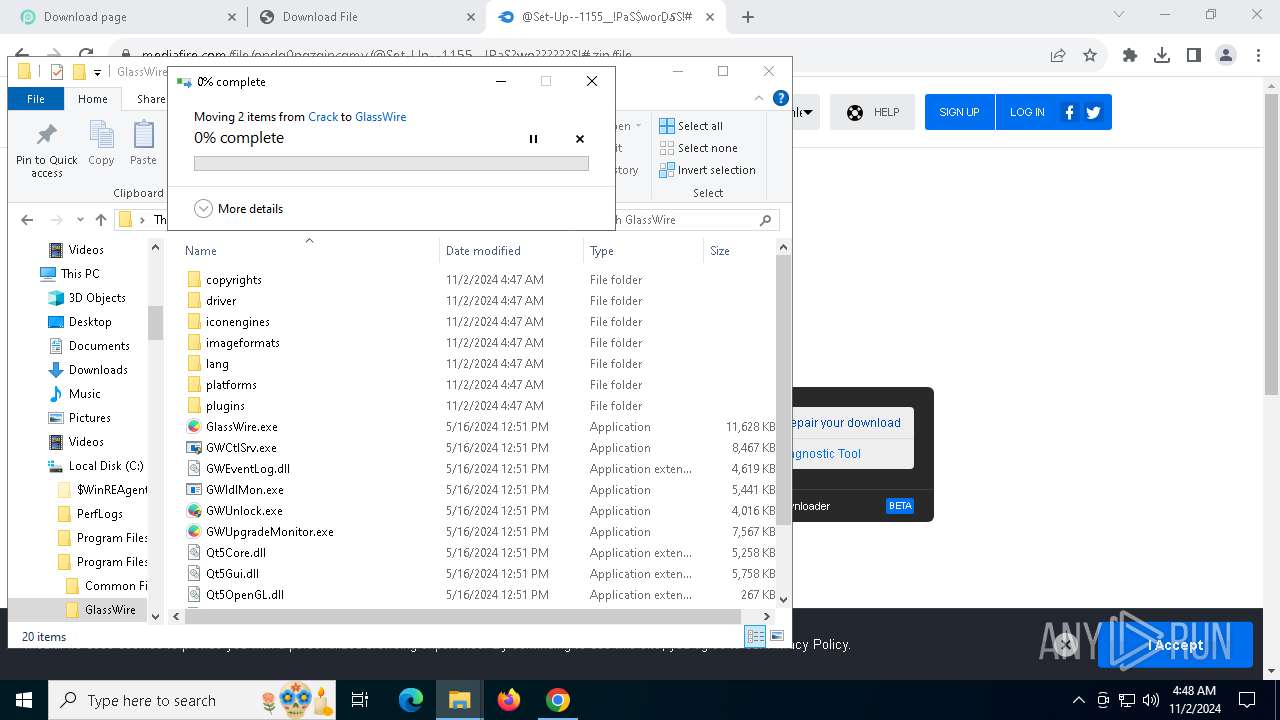
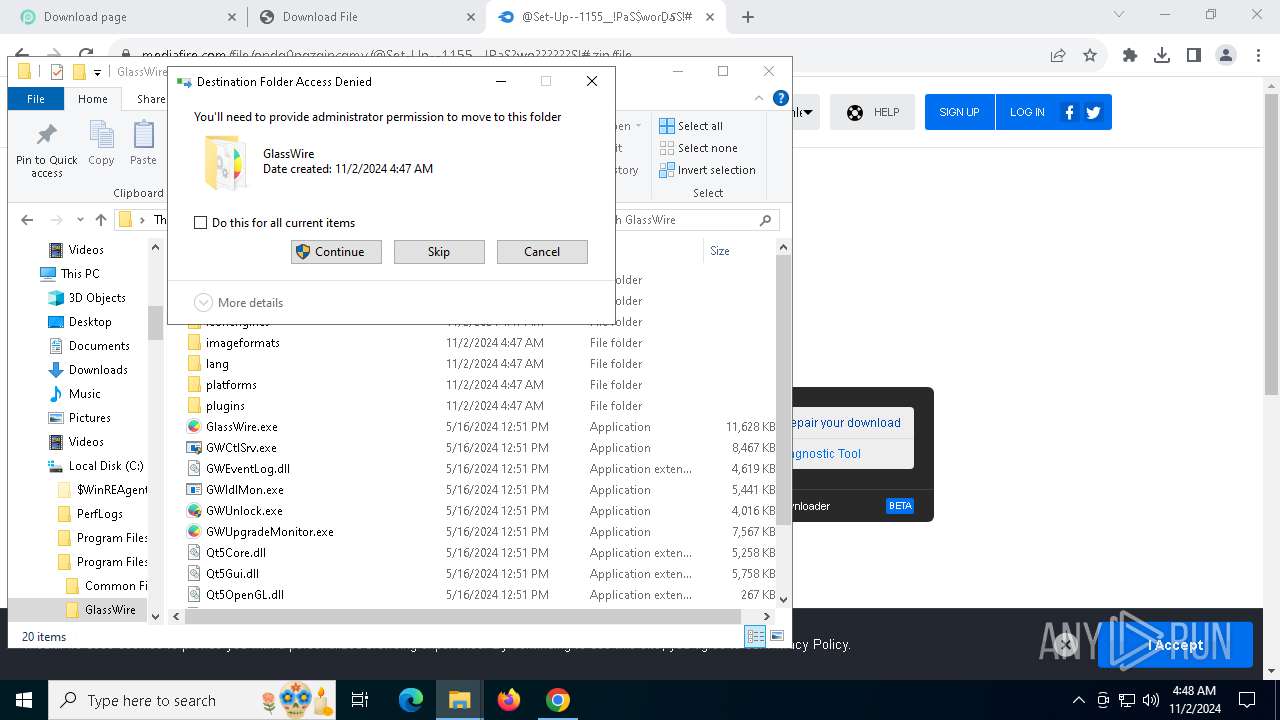
Executable content was dropped or overwritten
- GlassWireSetup_3.3.678.exe (PID: 4352)
- vc_redist.x86.exe (PID: 6232)
- vc_redist.x86.exe (PID: 7284)
- rundll32.exe (PID: 8140)
- AutoIt3.exe (PID: 6500)
- Setup.exe (PID: 8152)
- more.com (PID: 7460)
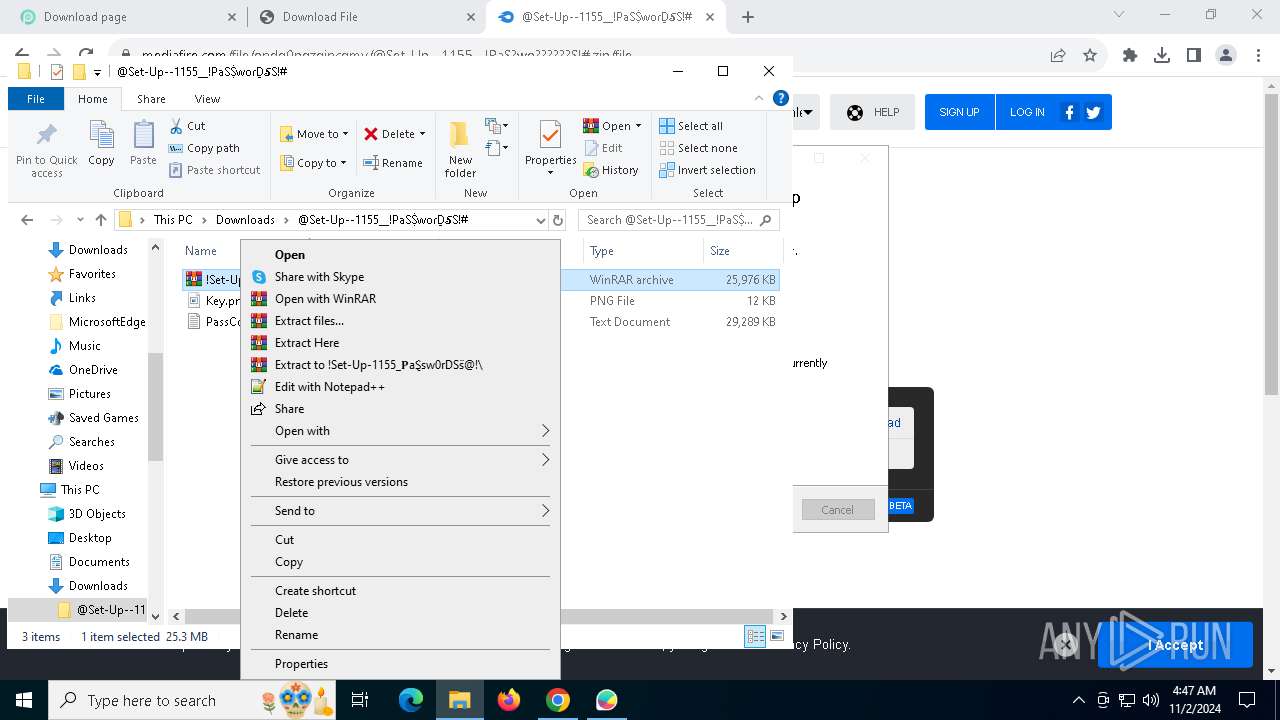
Process drops legitimate windows executable
- GlassWireSetup_3.3.678.exe (PID: 4352)
- vc_redist.x86.exe (PID: 6232)
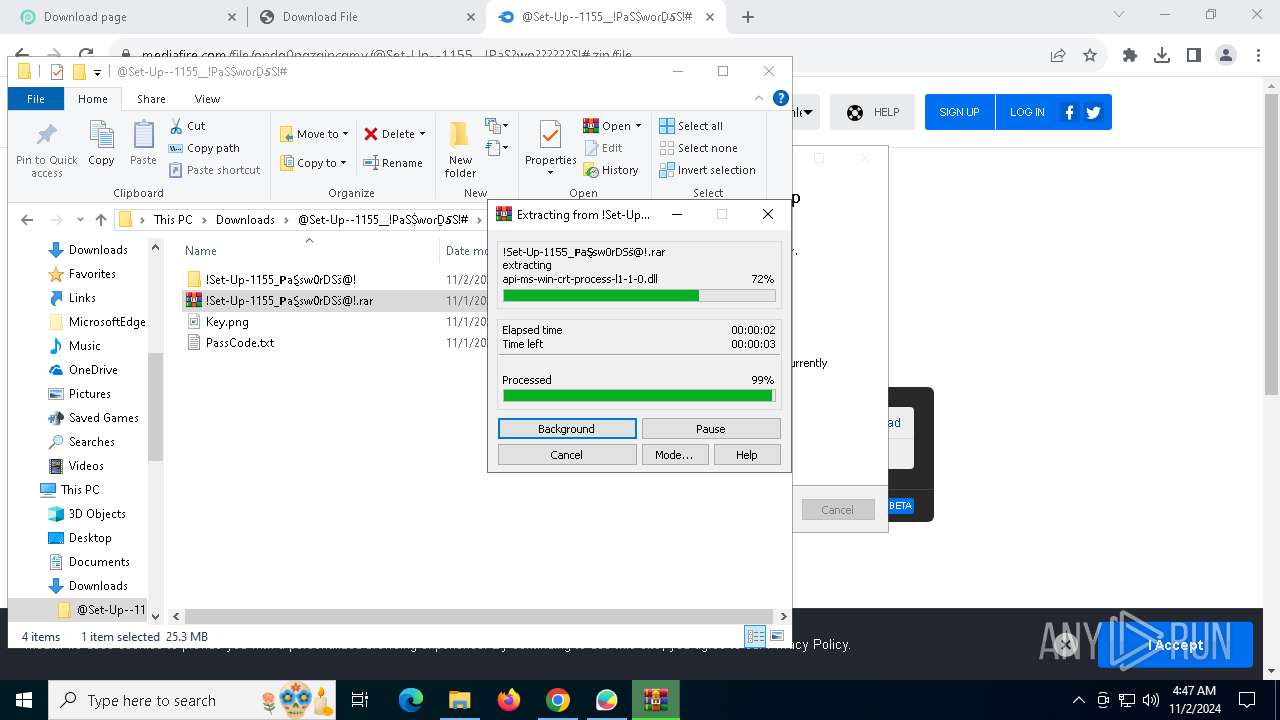
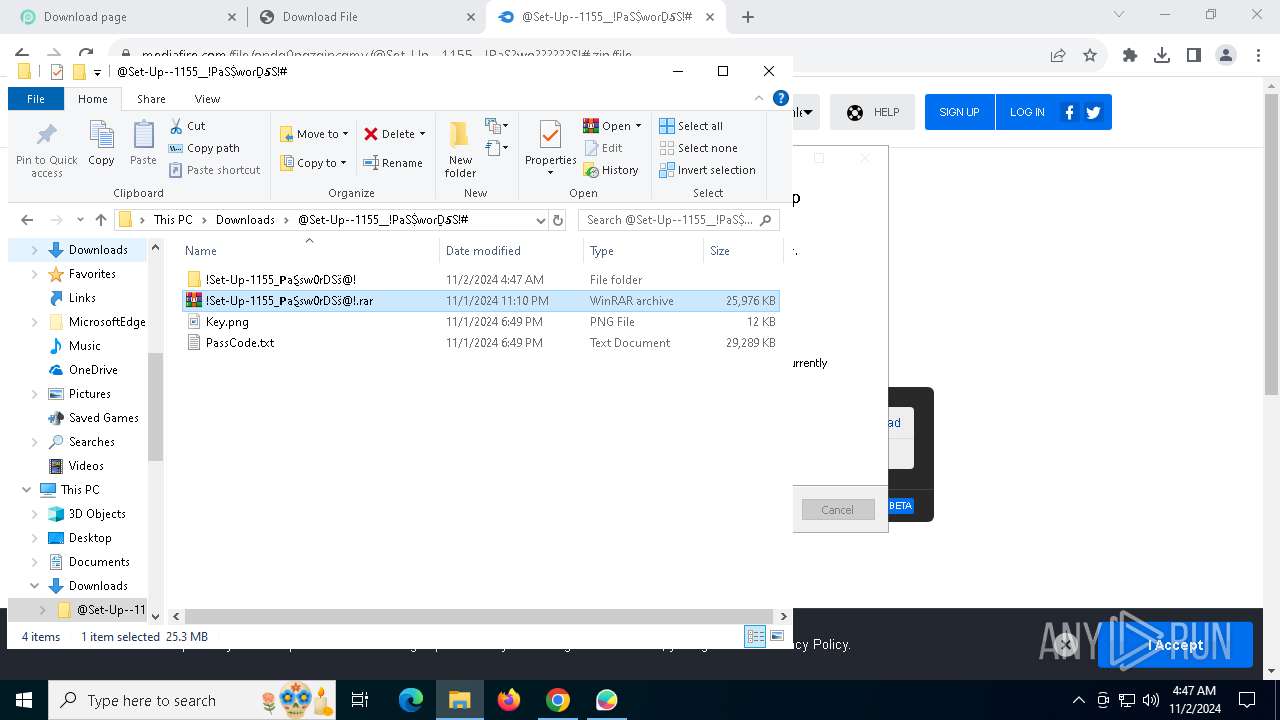
- WinRAR.exe (PID: 6792)
Starts a Microsoft application from unusual location
- vc_redist.x86.exe (PID: 6232)
- vc_redist.x86.exe (PID: 7284)
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- GlassWireSetup_3.3.678.exe (PID: 4352)
- wevtutil.exe (PID: 4700)
Drops a system driver (possible attempt to evade defenses)
- GlassWireSetup_3.3.678.exe (PID: 4352)
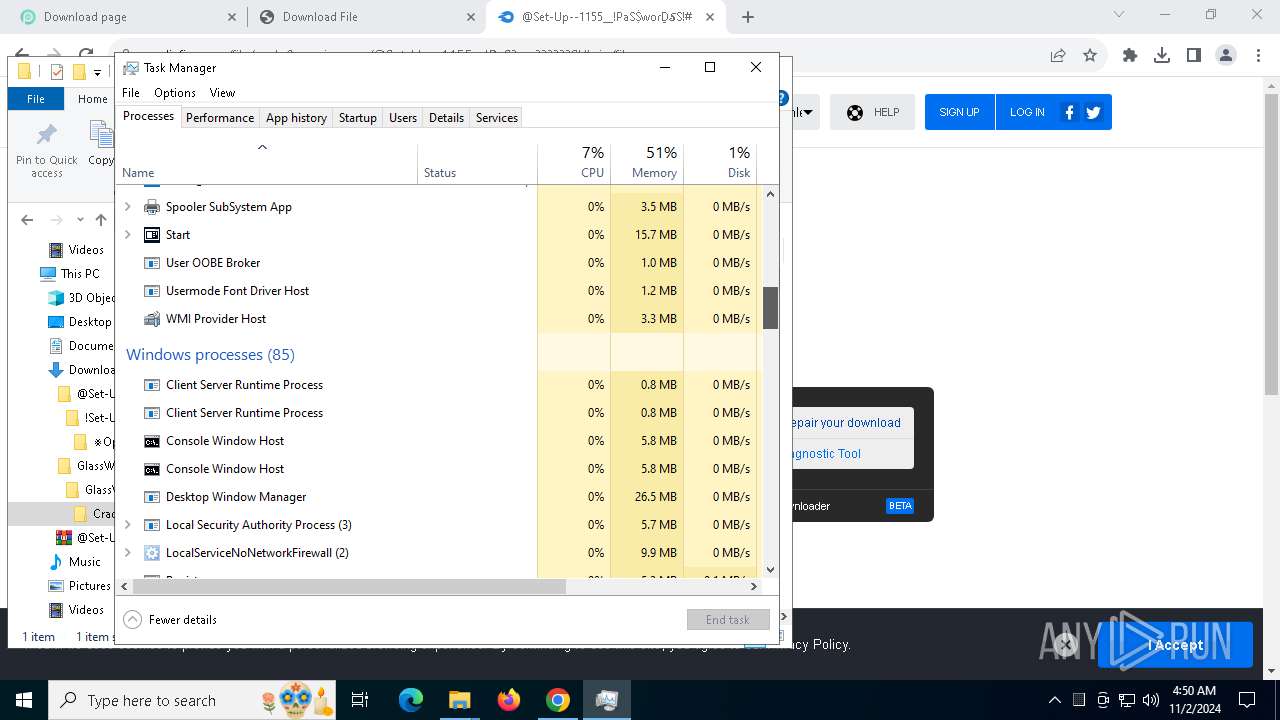
Uses RUNDLL32.EXE to load library
- GlassWireSetup_3.3.678.exe (PID: 4352)
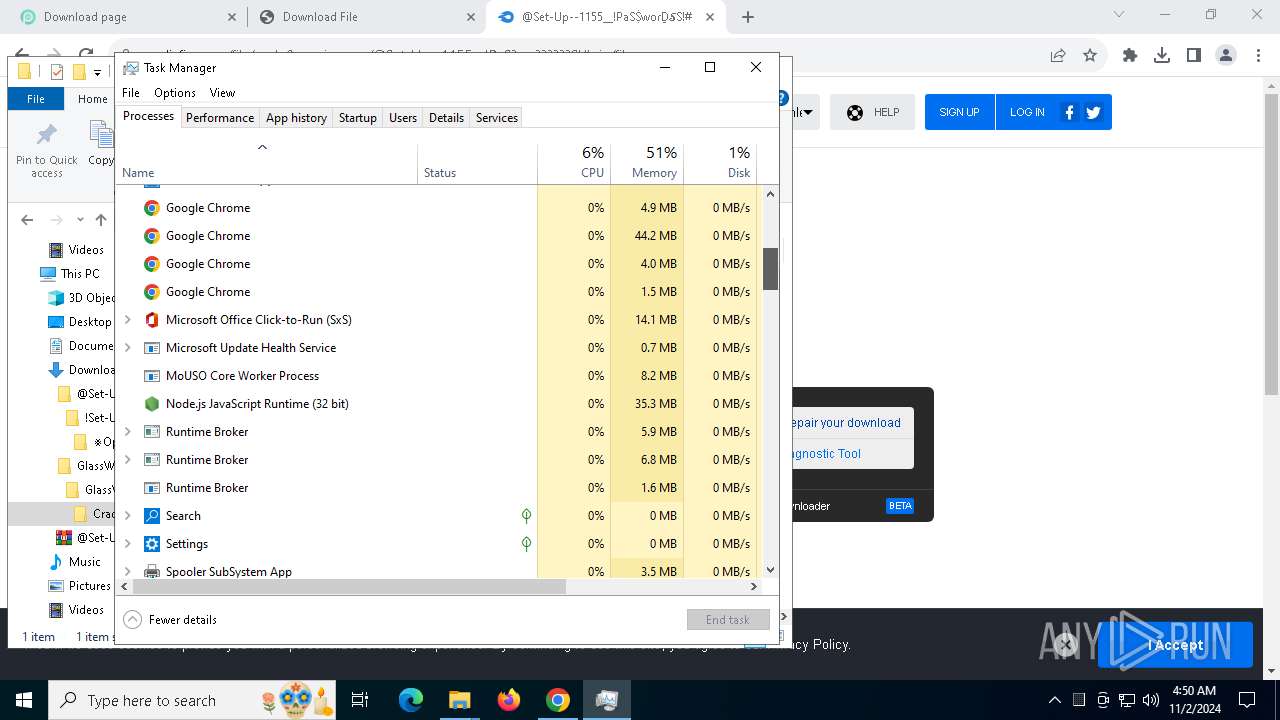
The process executes Powershell scripts
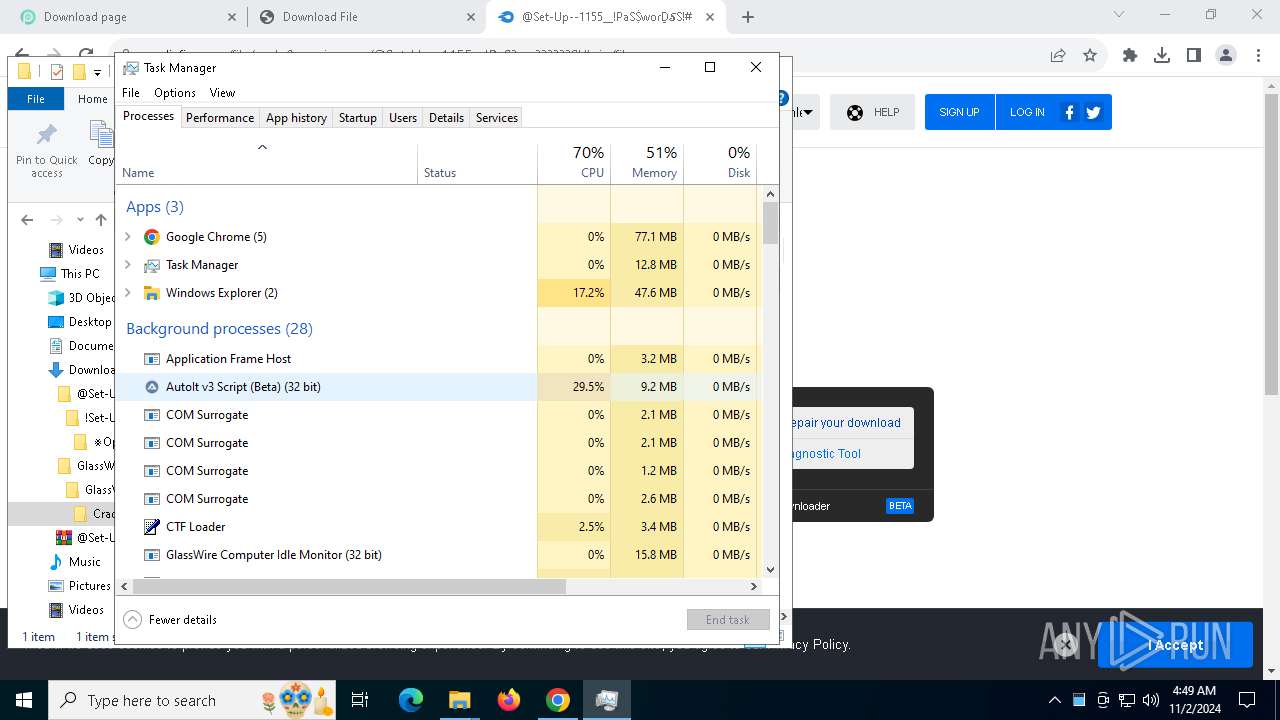
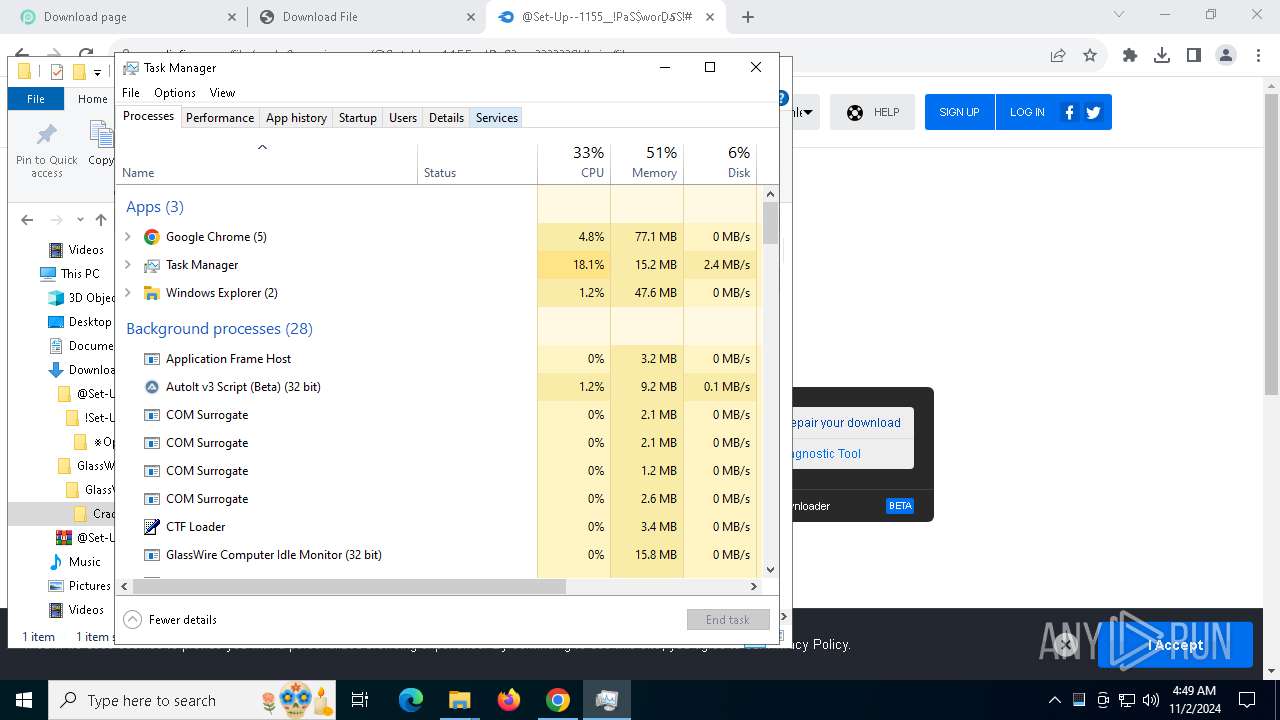
- AutoIt3.exe (PID: 6500)
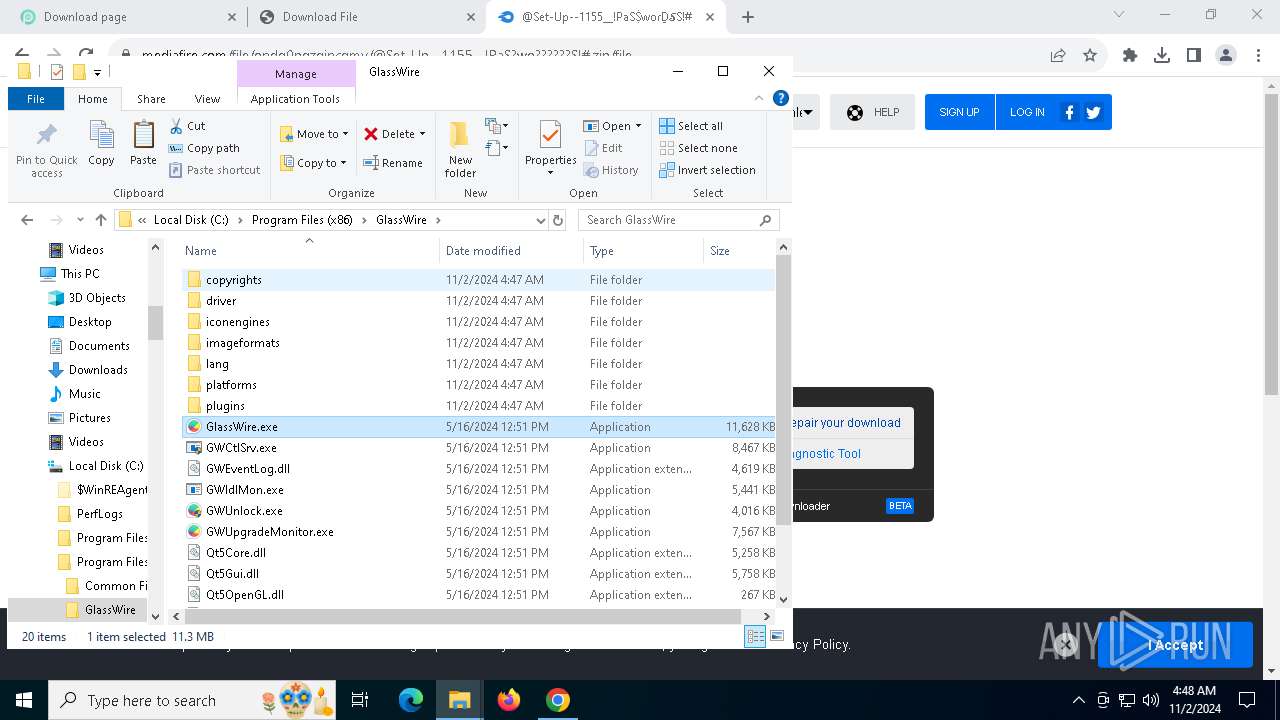
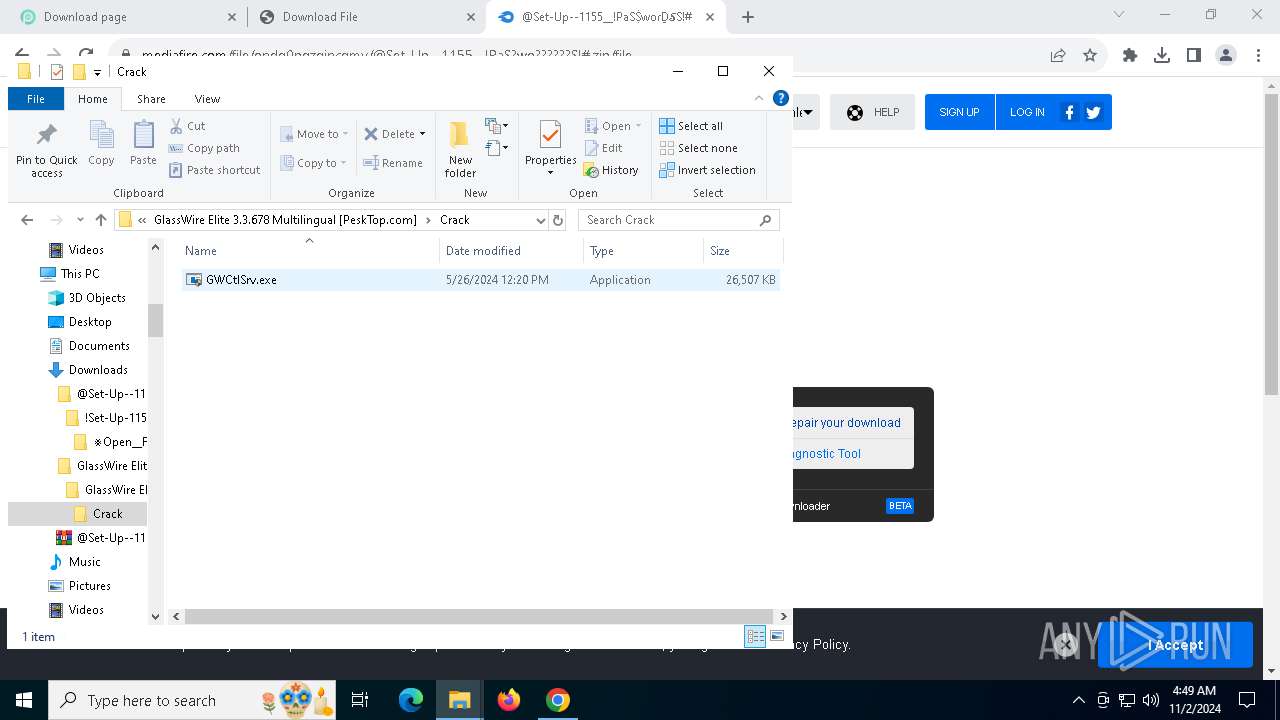
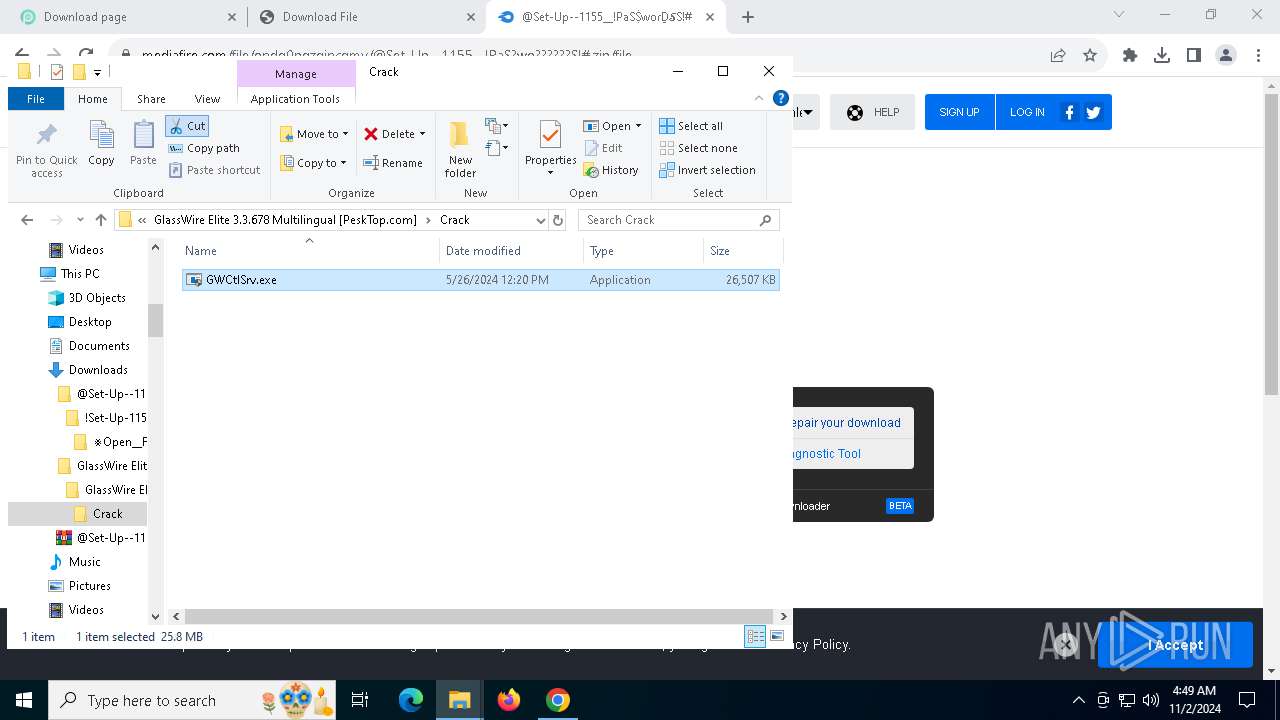
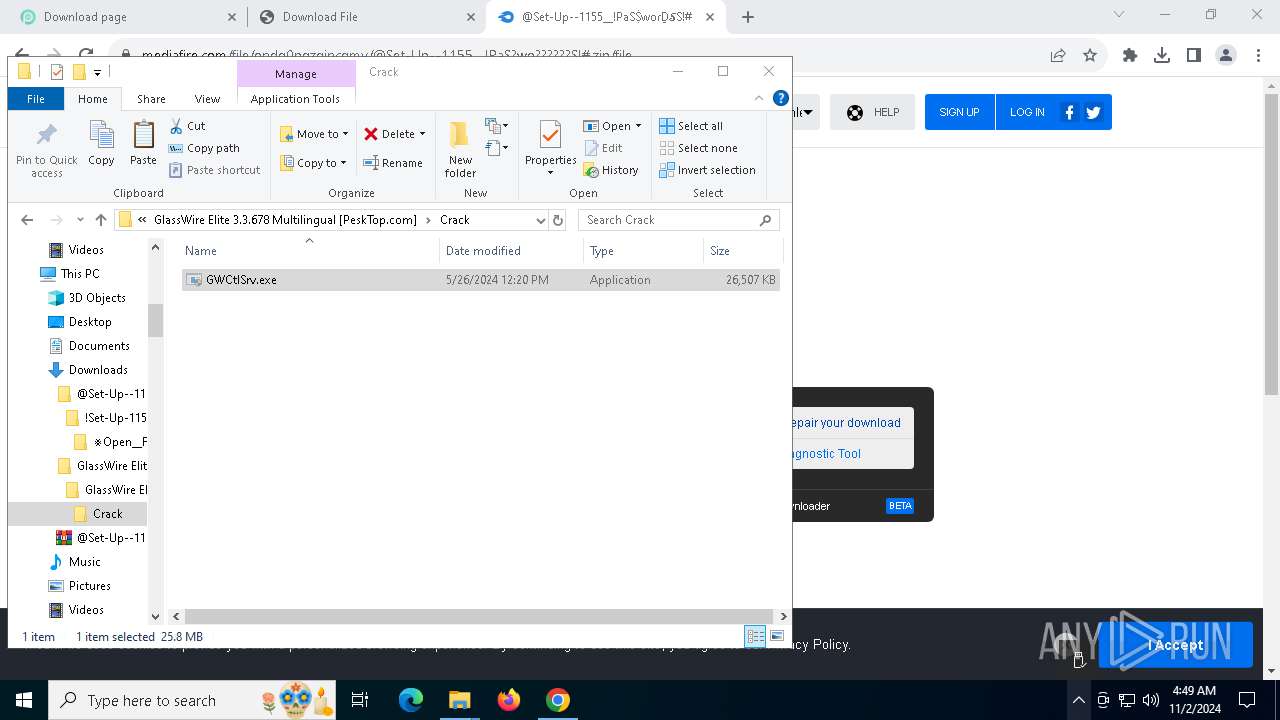
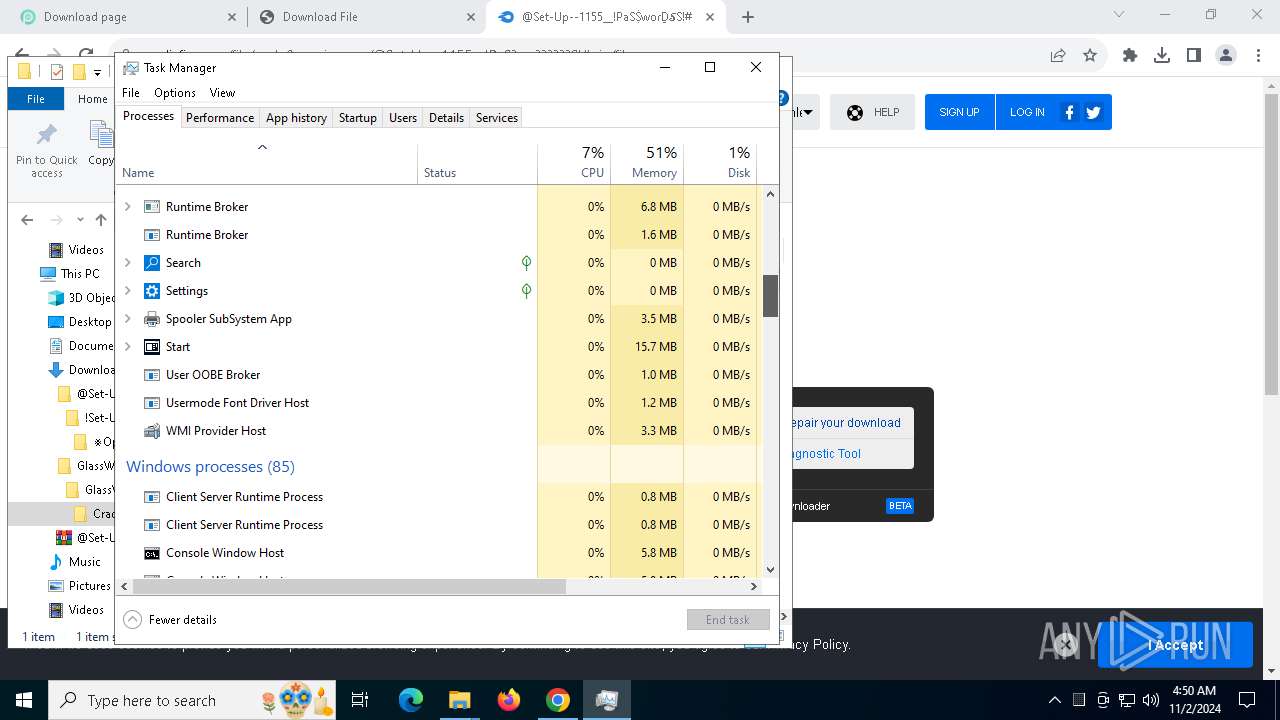
Executes as Windows Service
- GWCtlSrv.exe (PID: 6496)
Starts application with an unusual extension
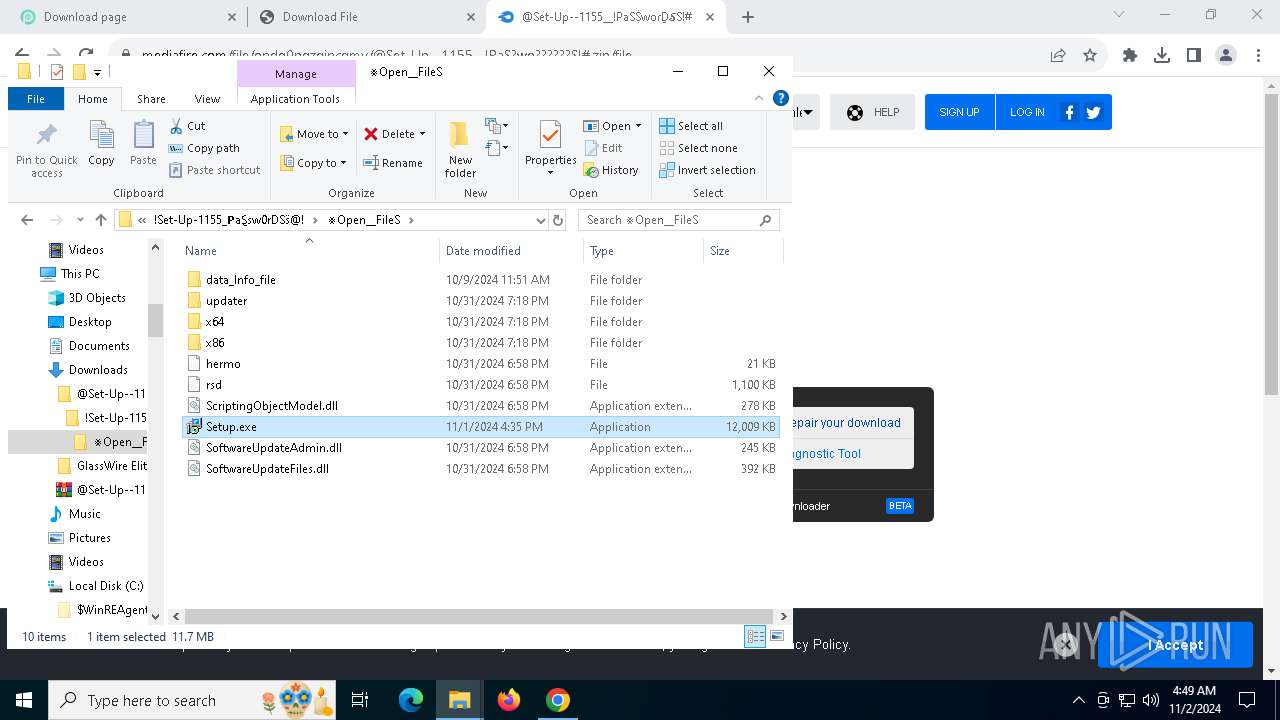
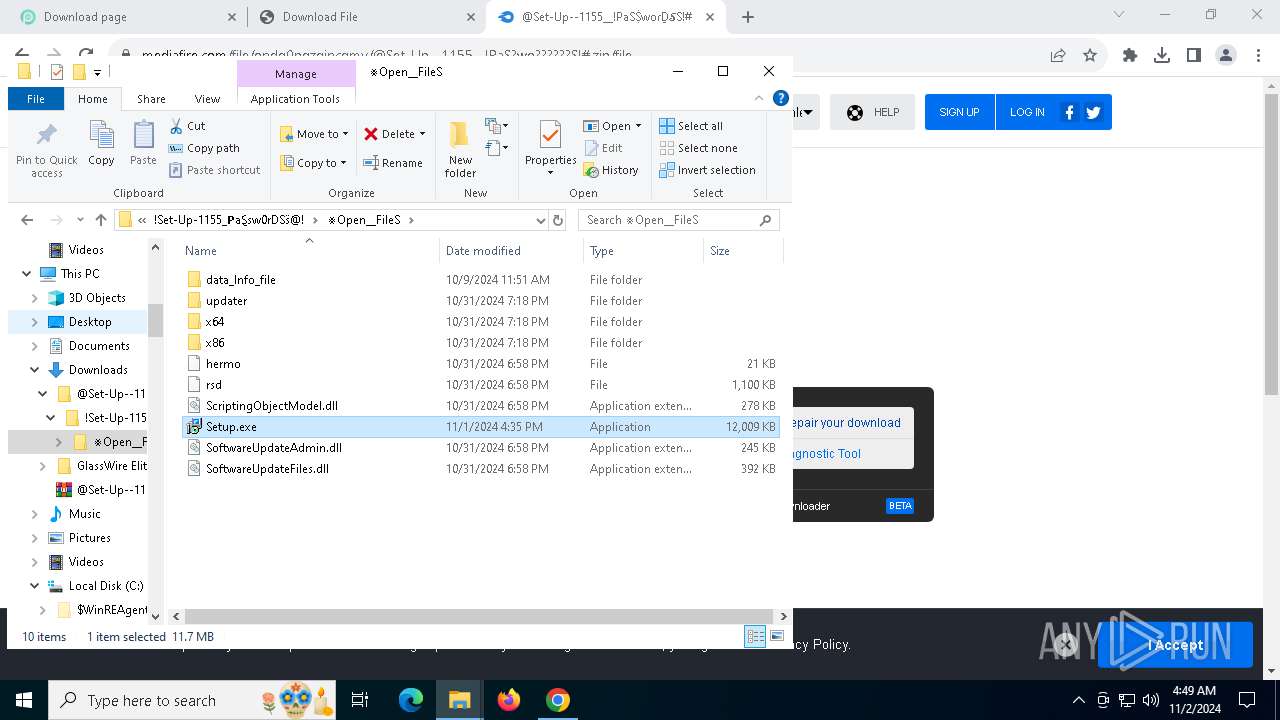
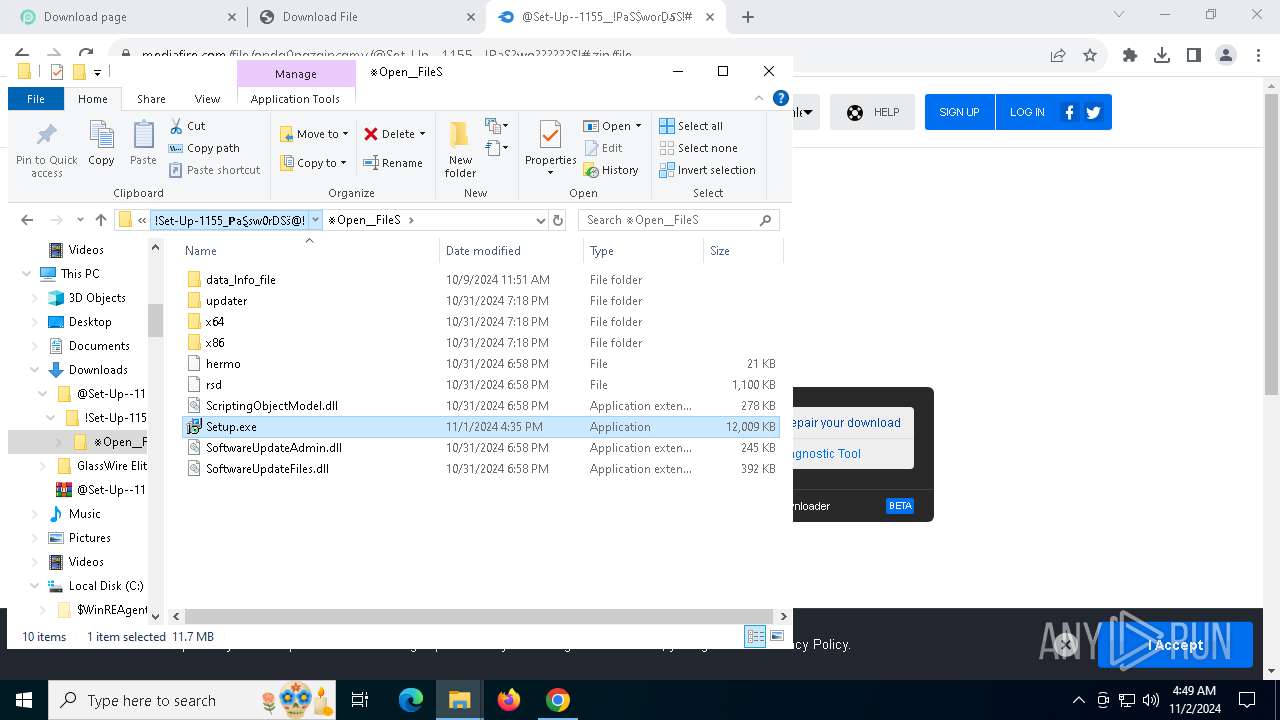
- Setup.exe (PID: 8152)
Node.exe was dropped
- AutoIt3.exe (PID: 6500)
Starts POWERSHELL.EXE for commands execution
- AutoIt3.exe (PID: 6500)
Starts itself from another location
- AutoIt3.exe (PID: 6500)
INFO
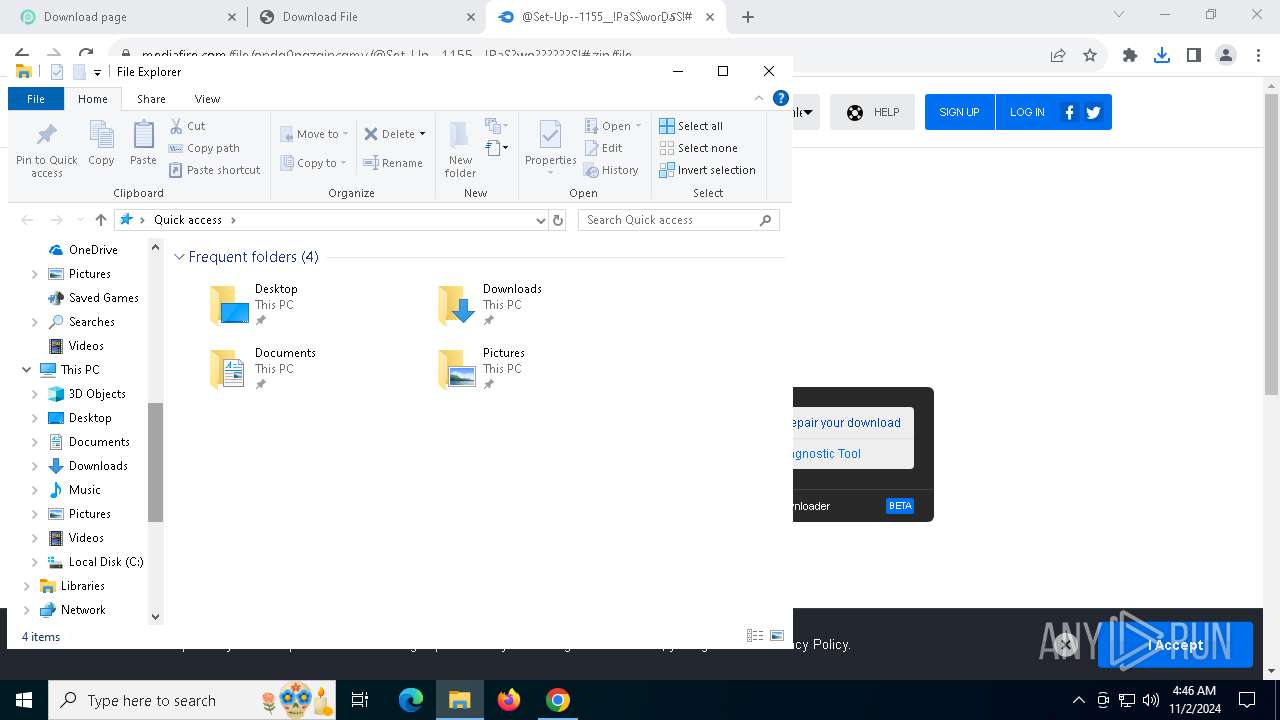
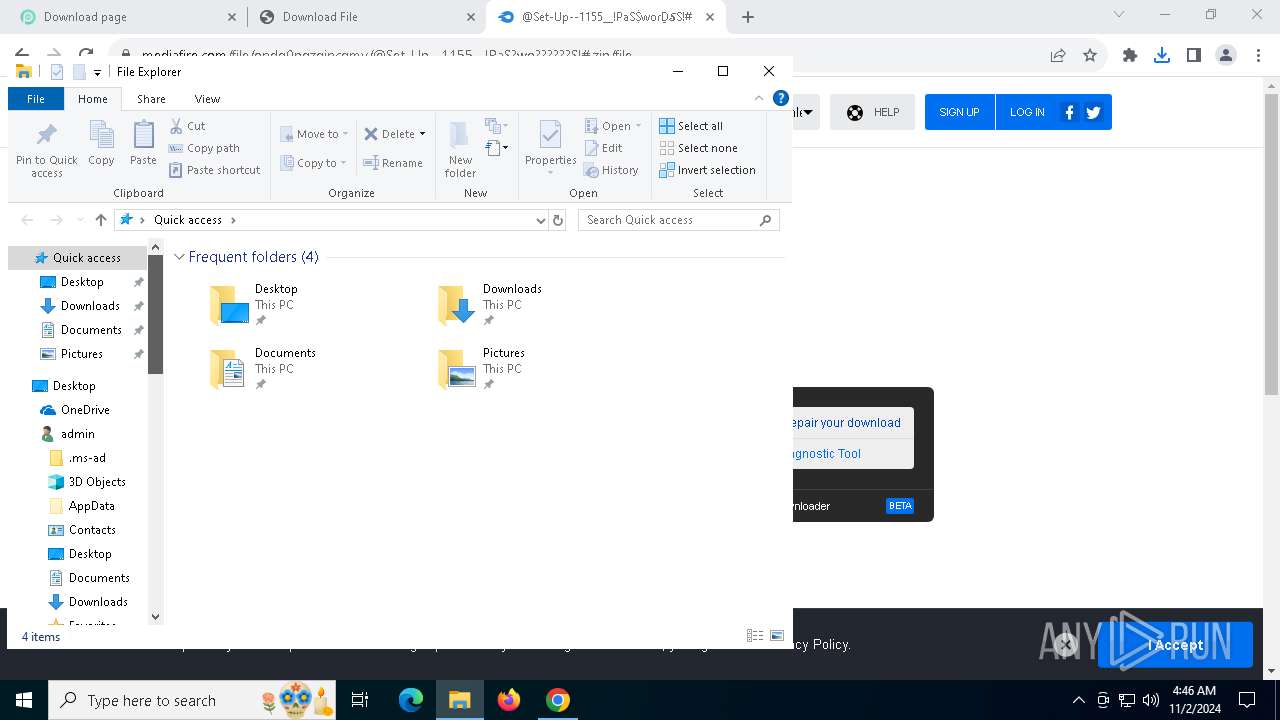
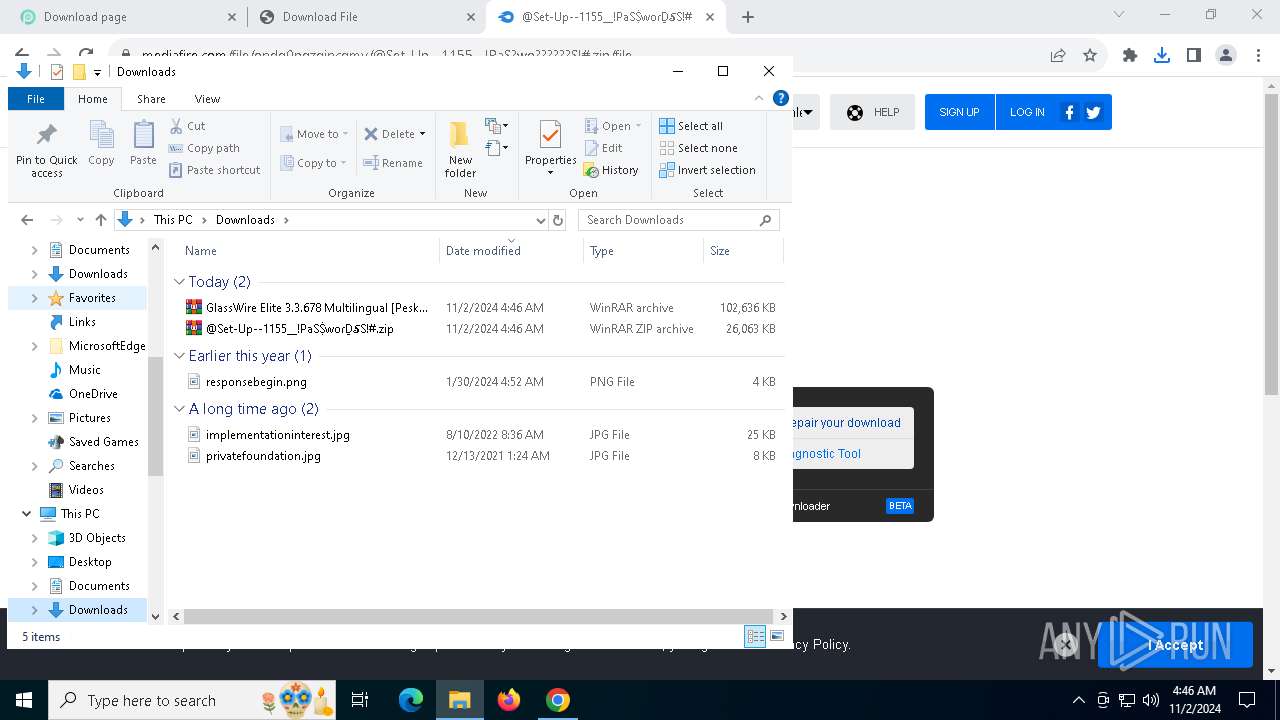
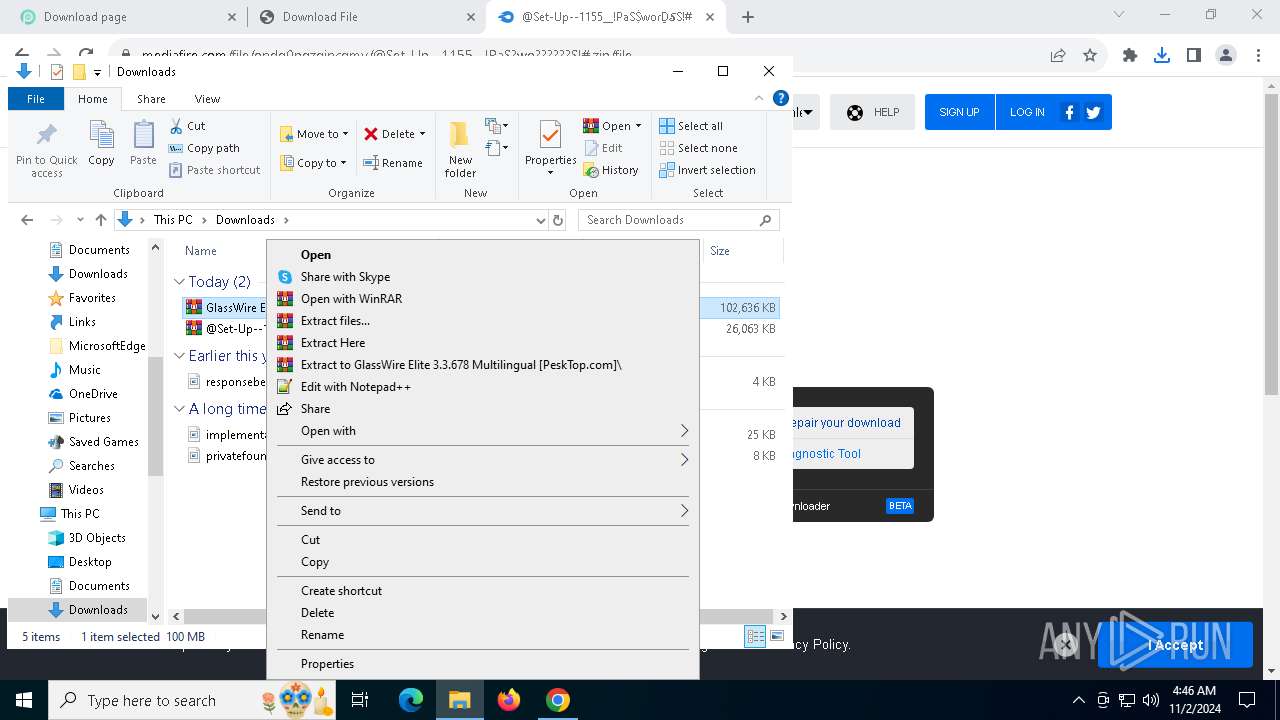
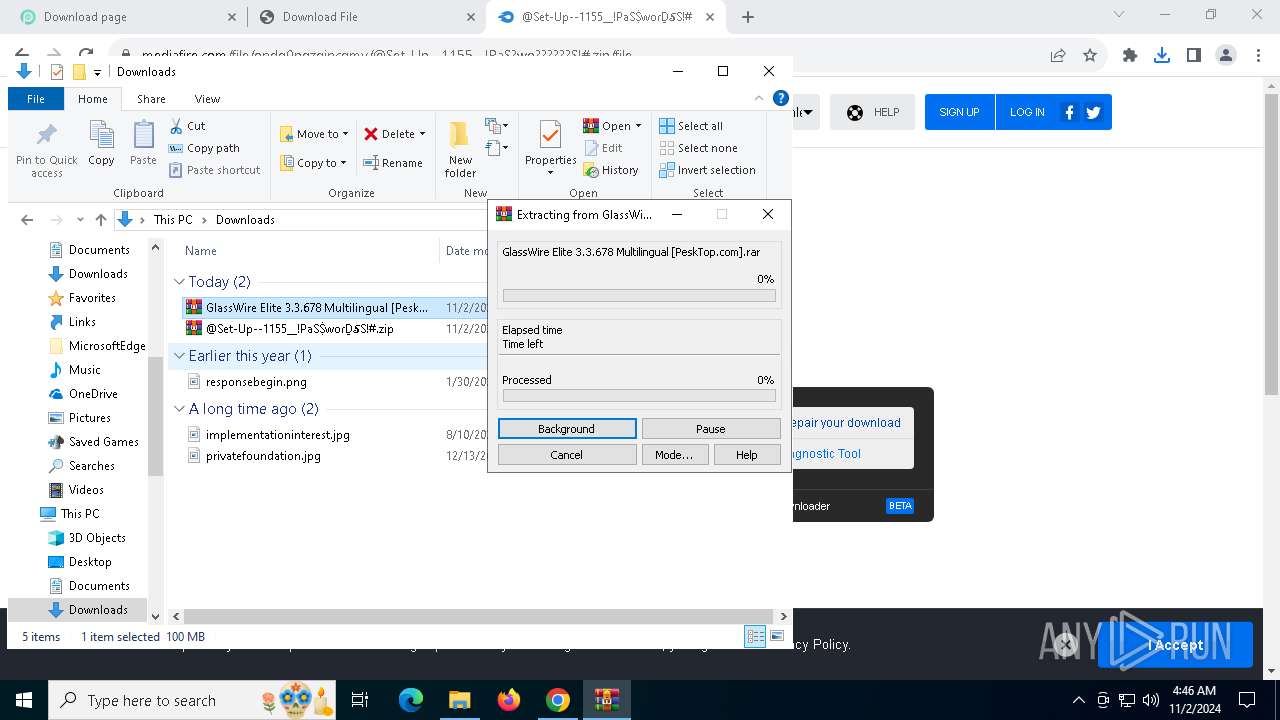
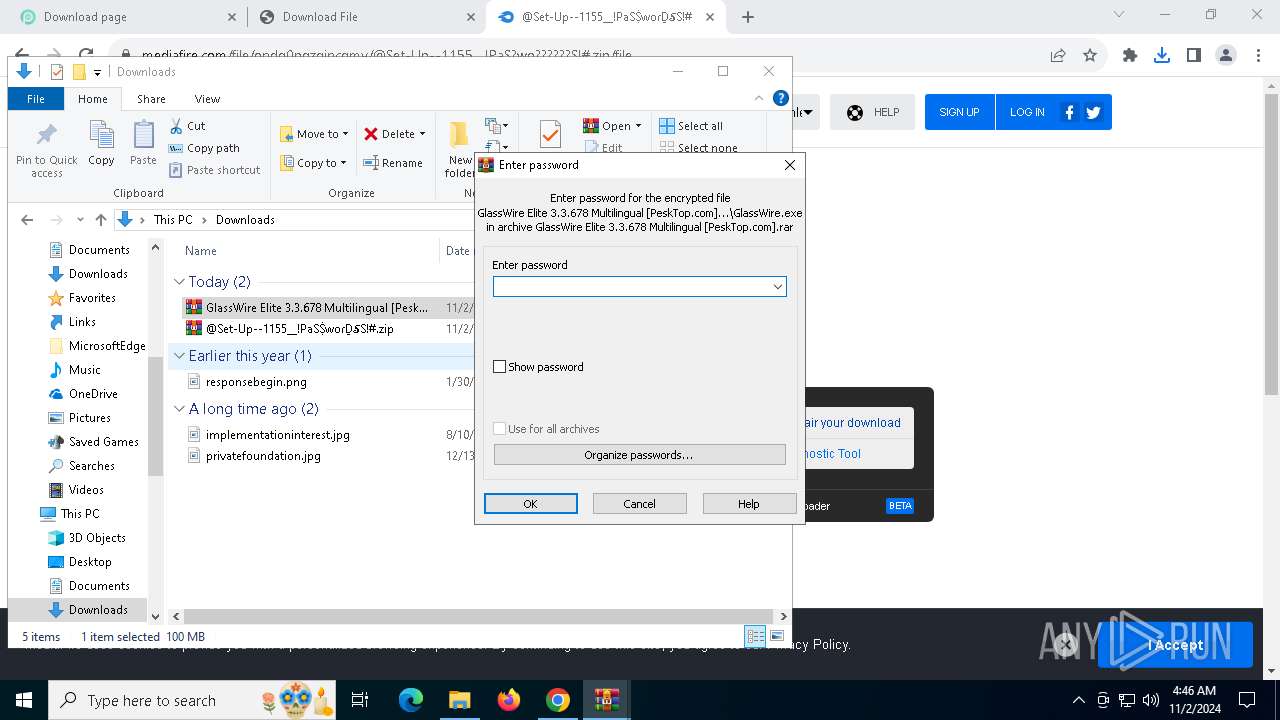
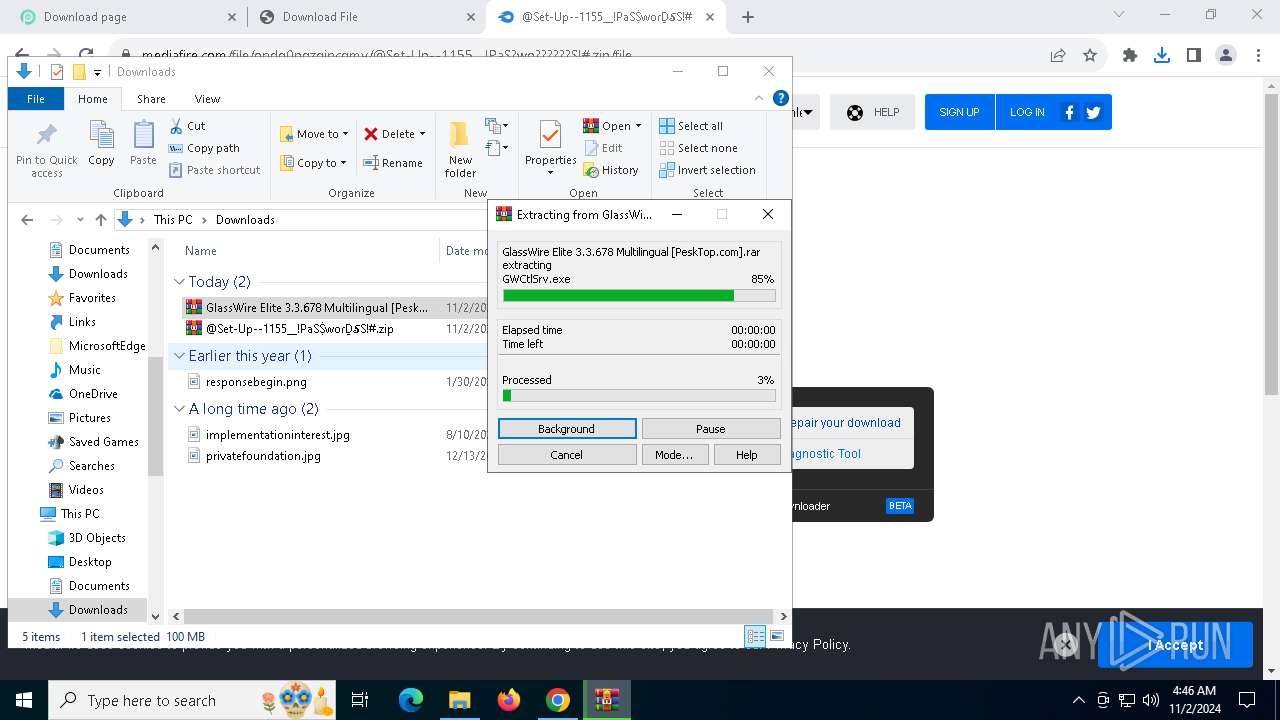
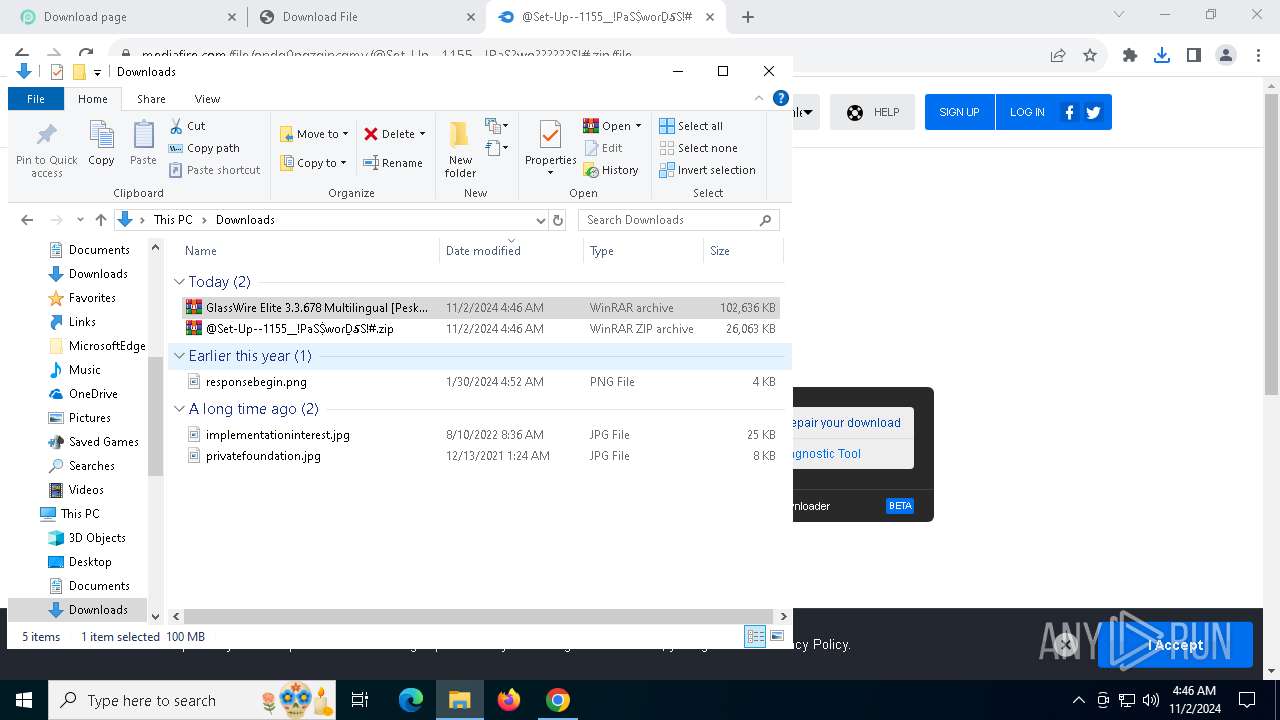
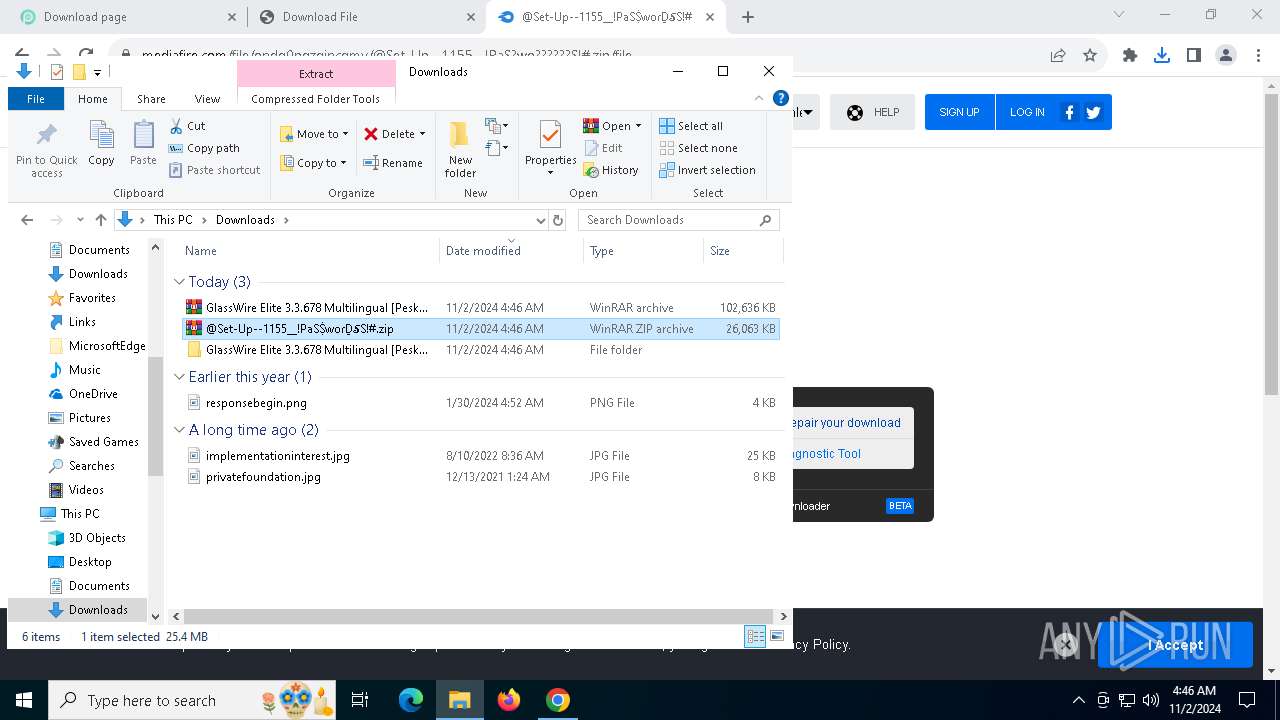
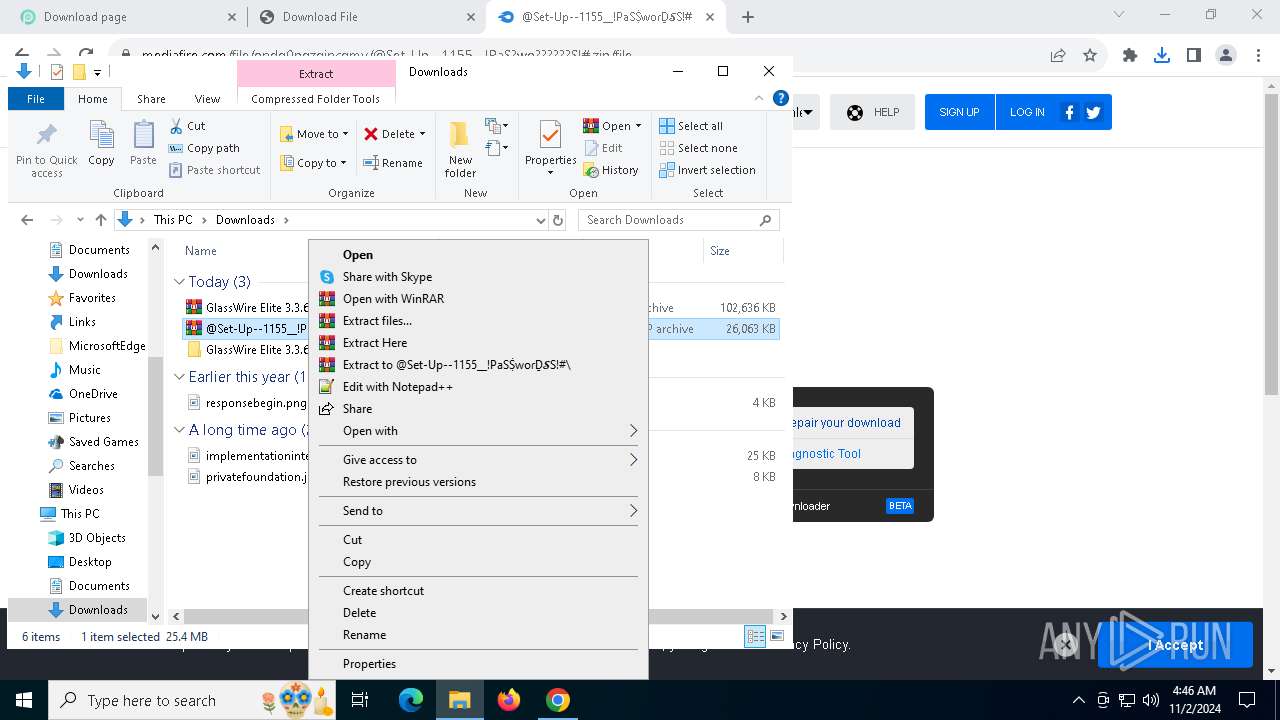
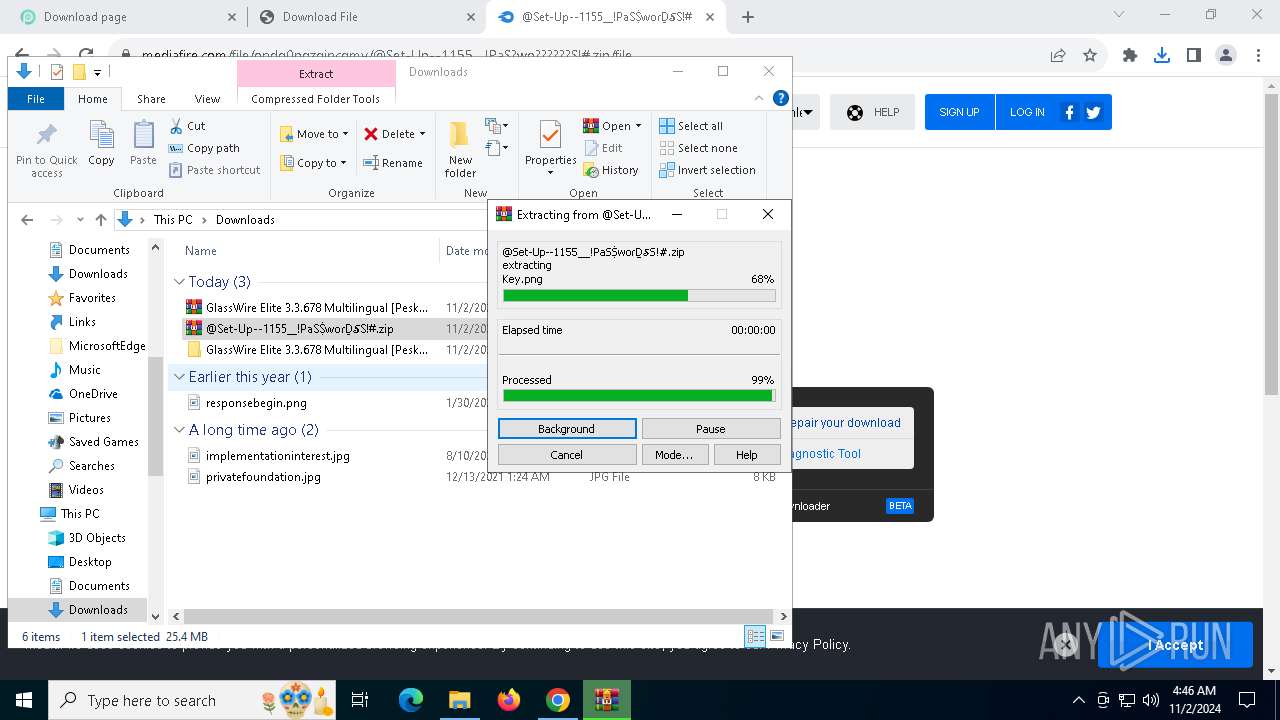
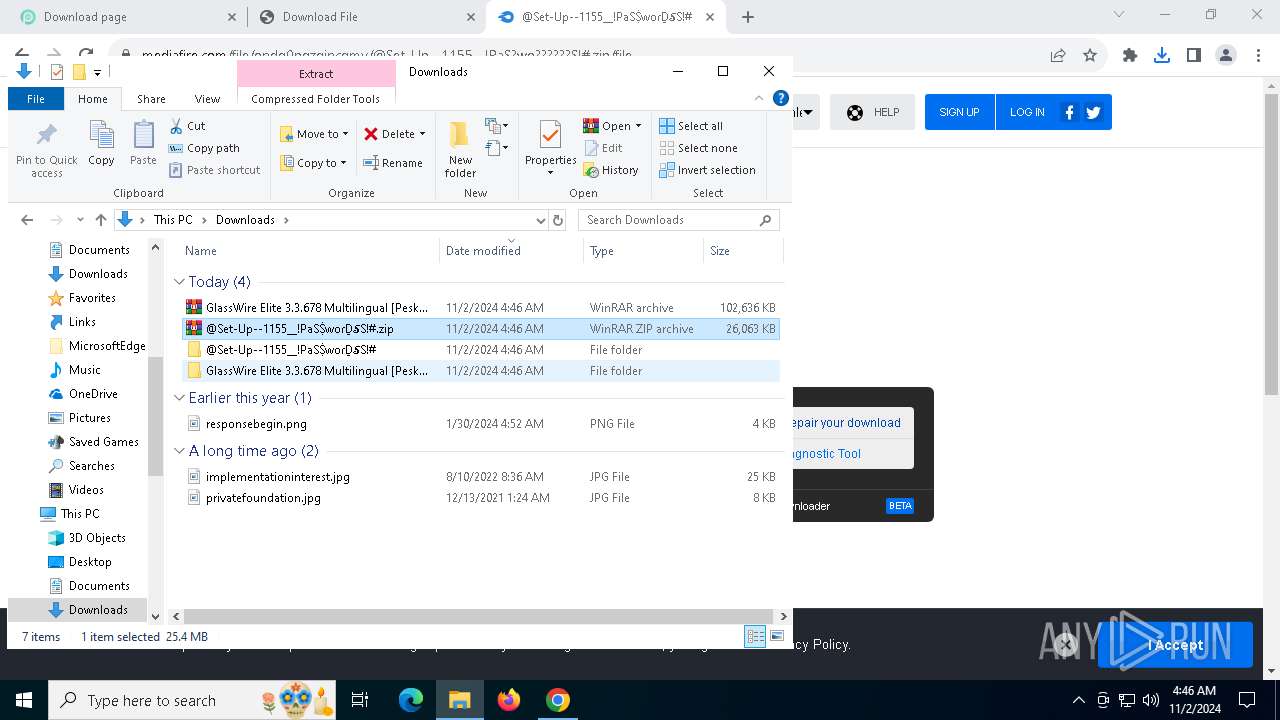
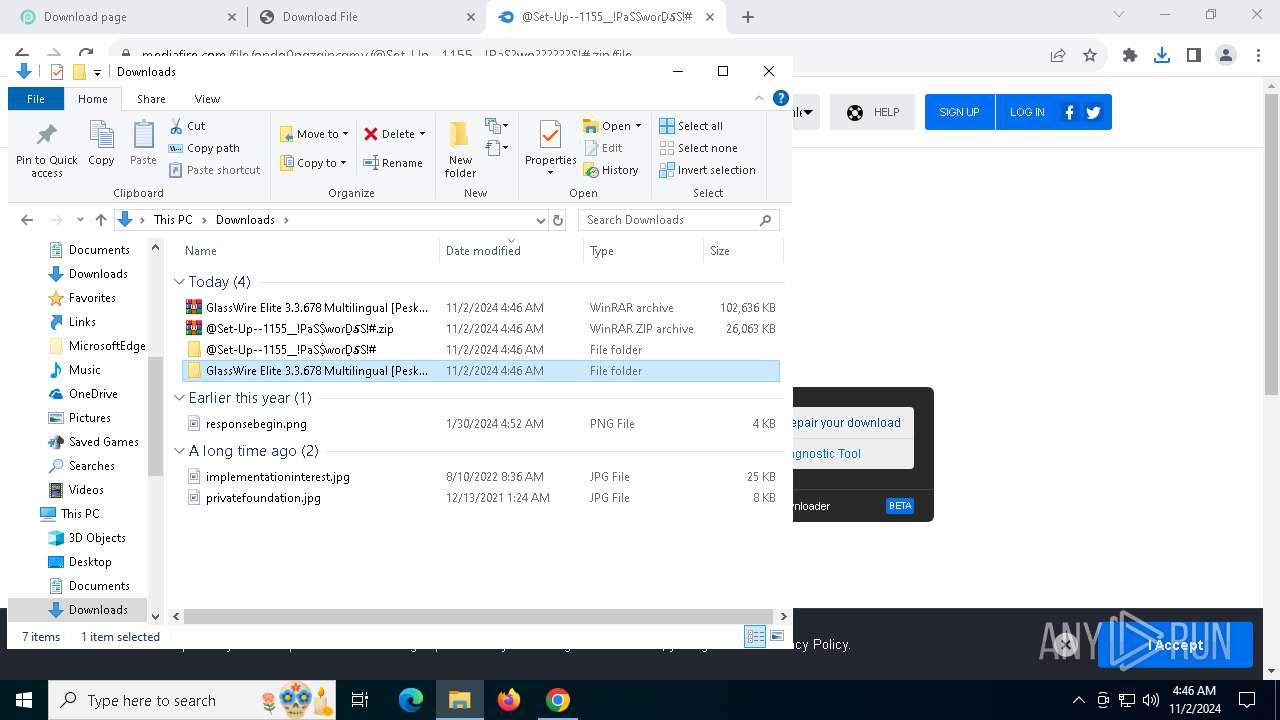
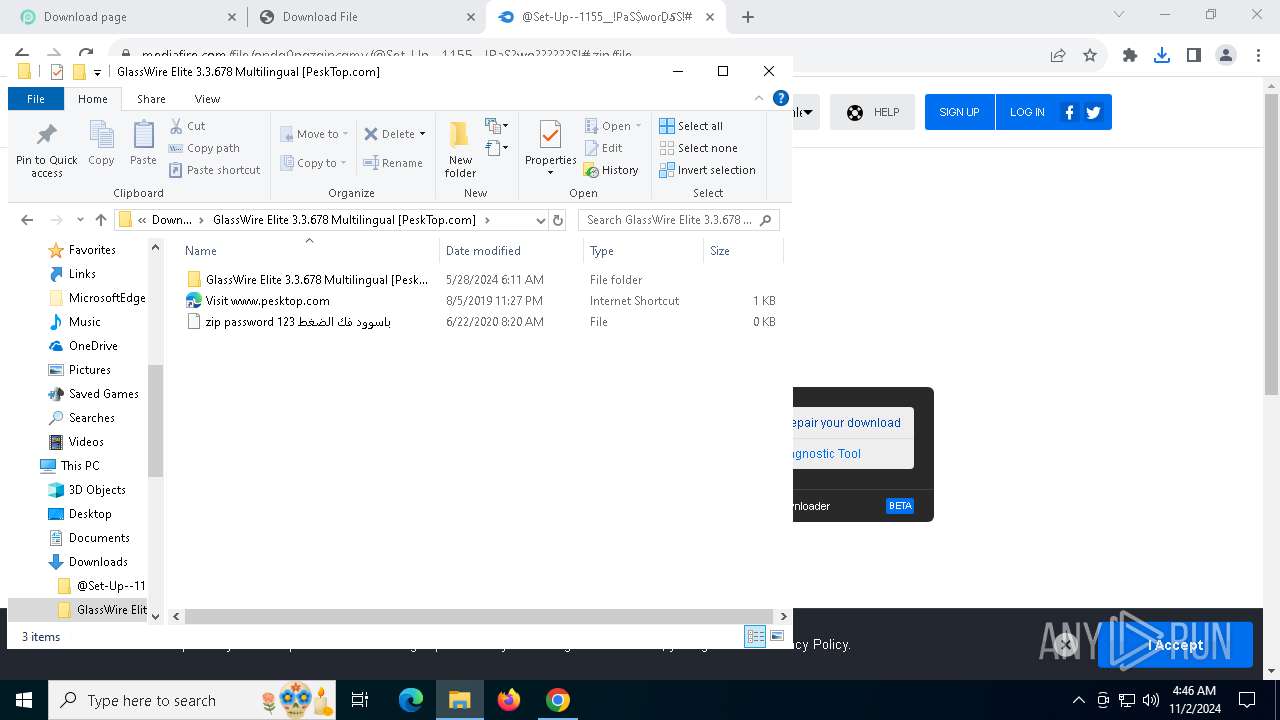
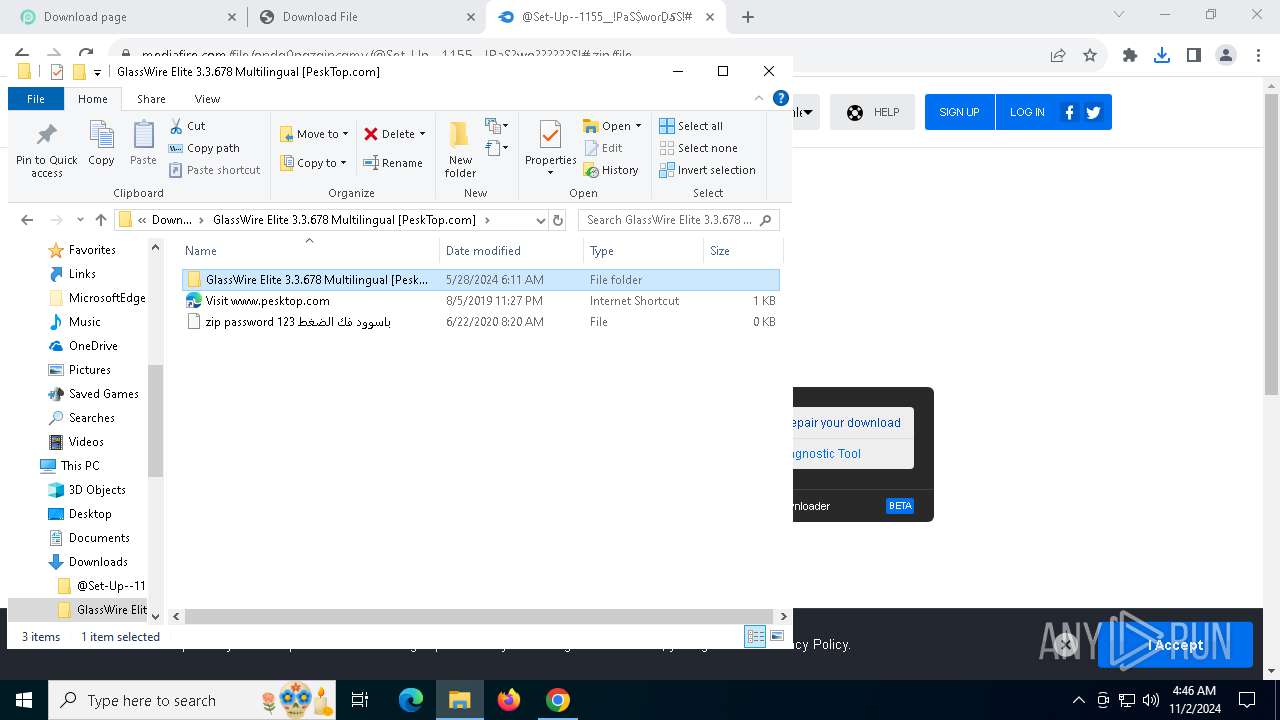
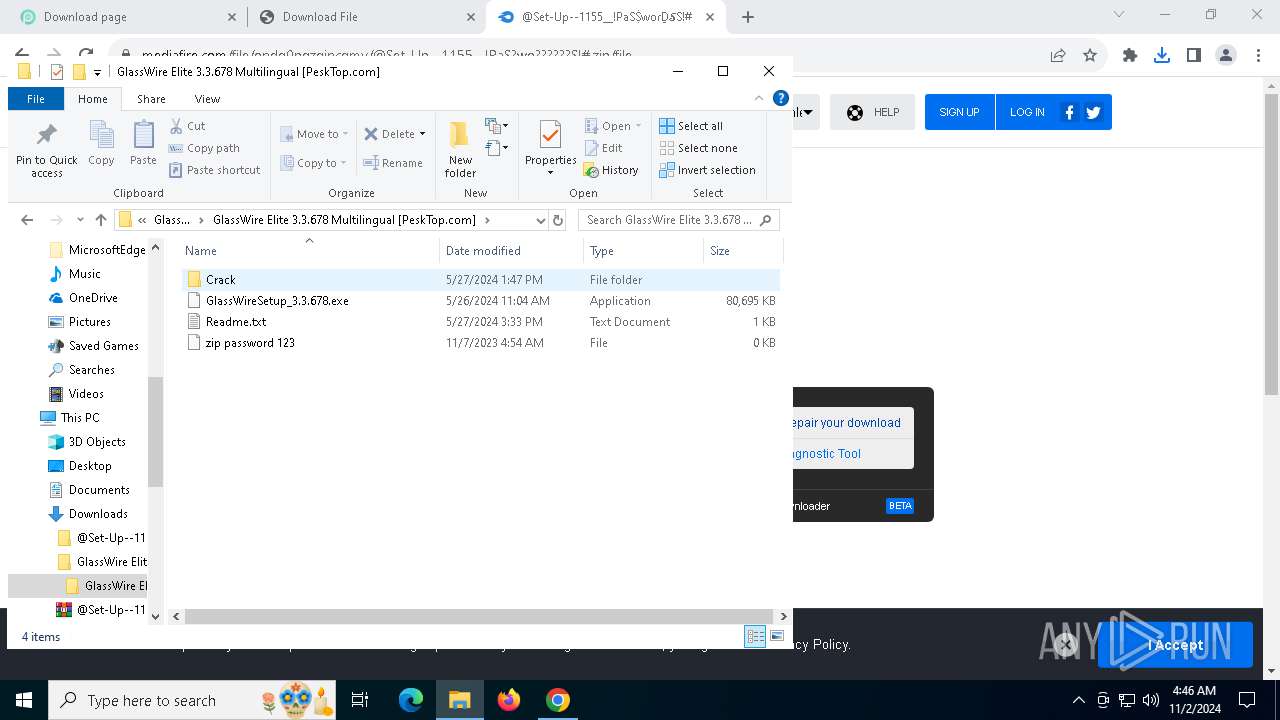
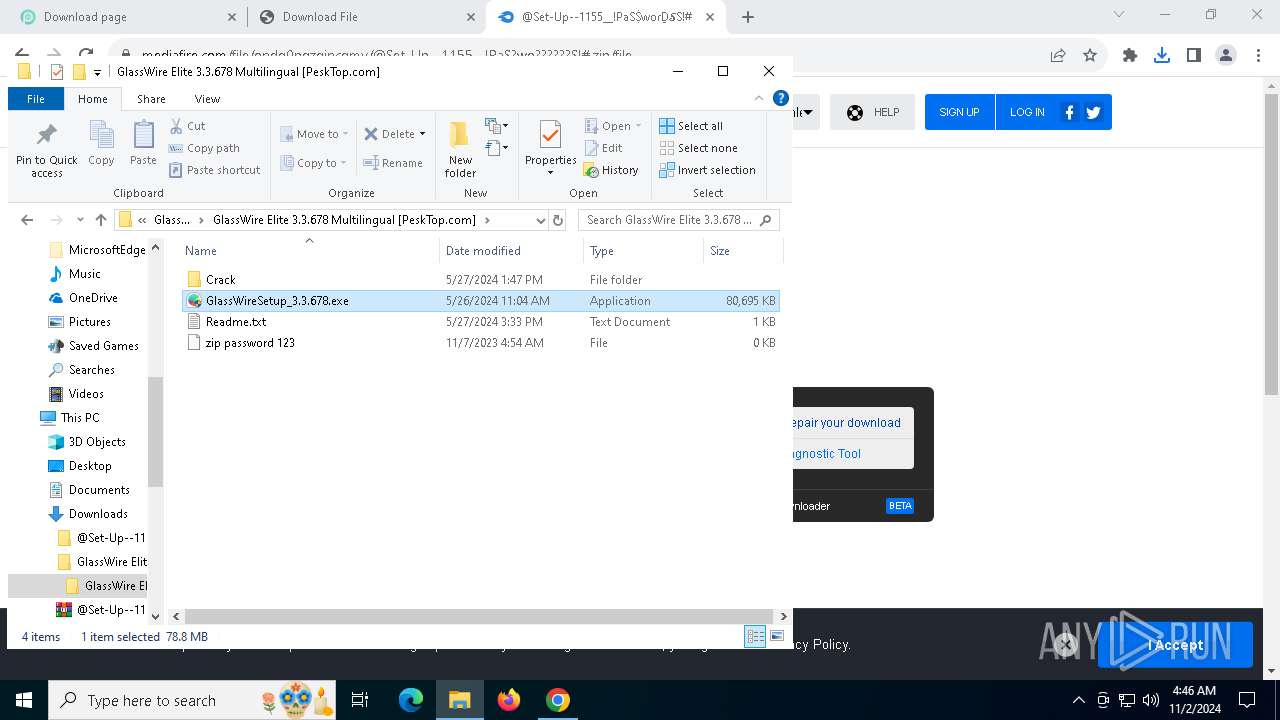
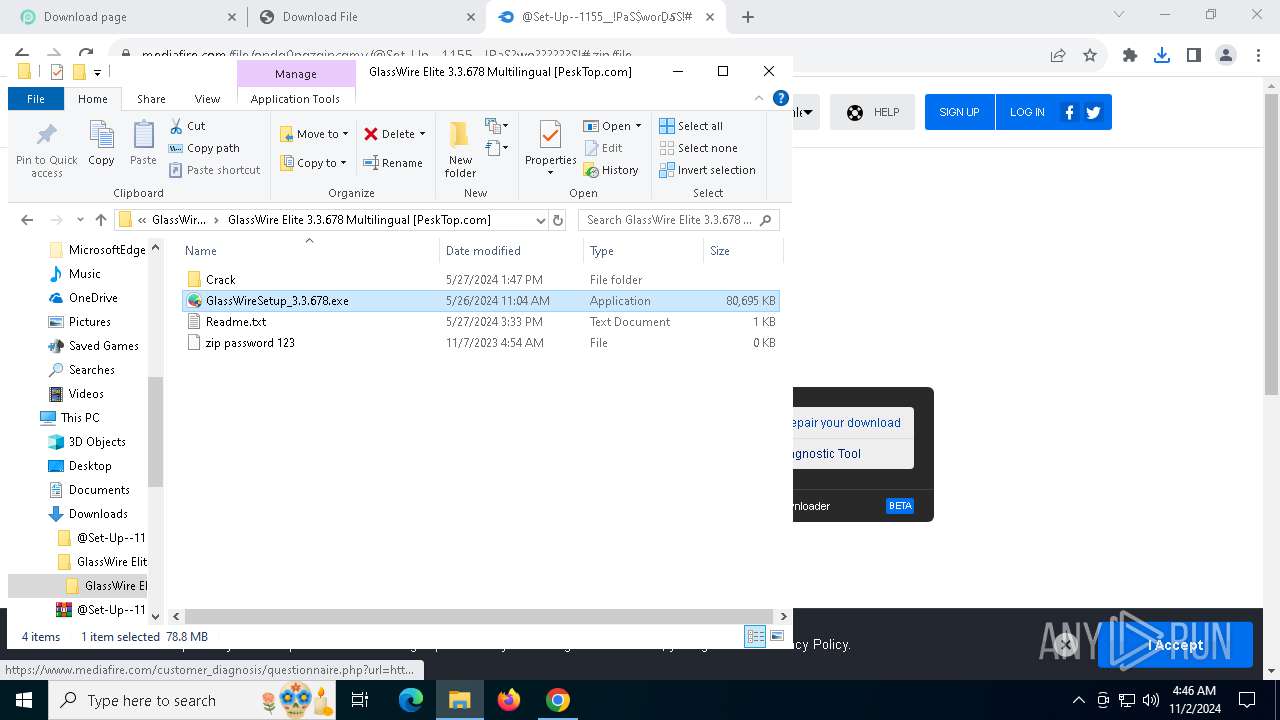
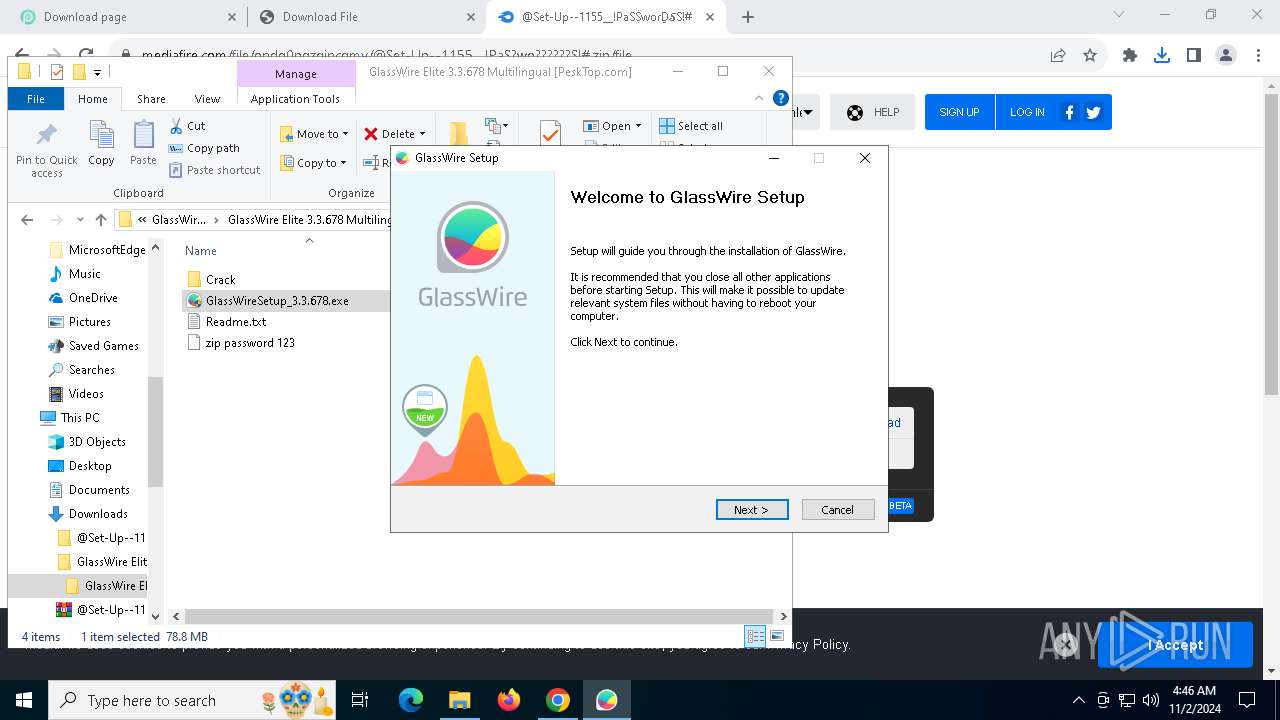
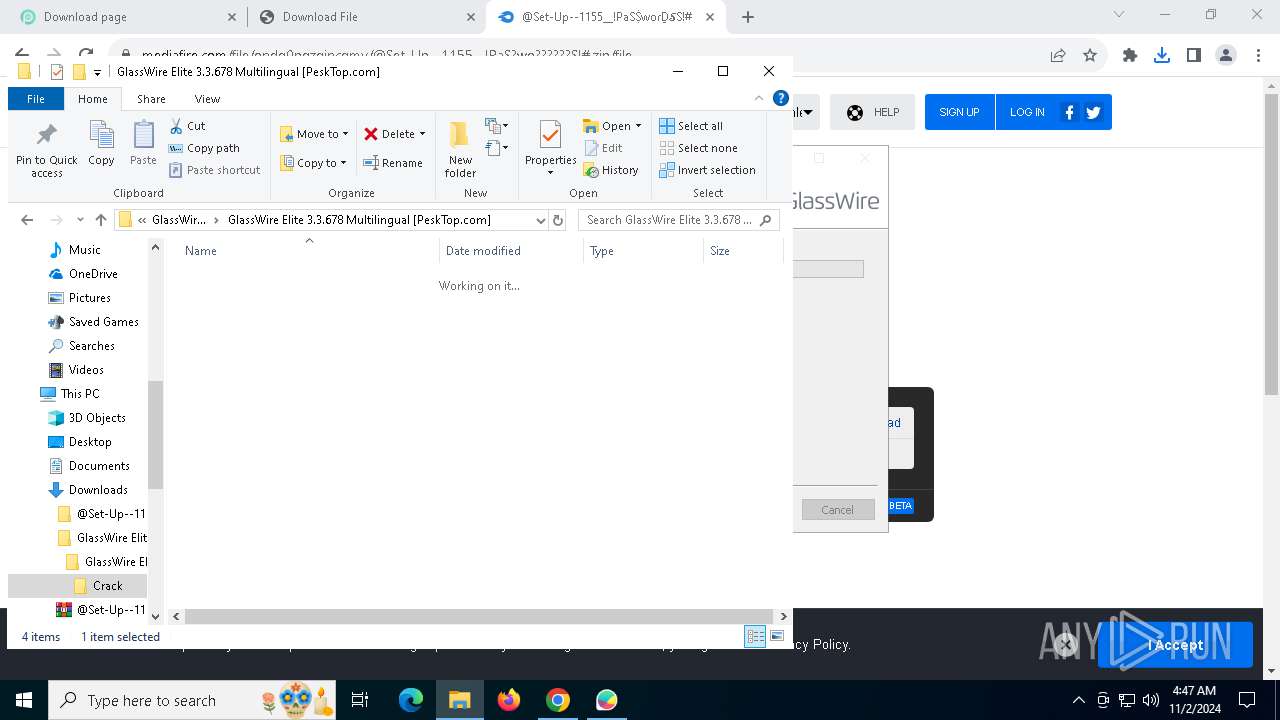
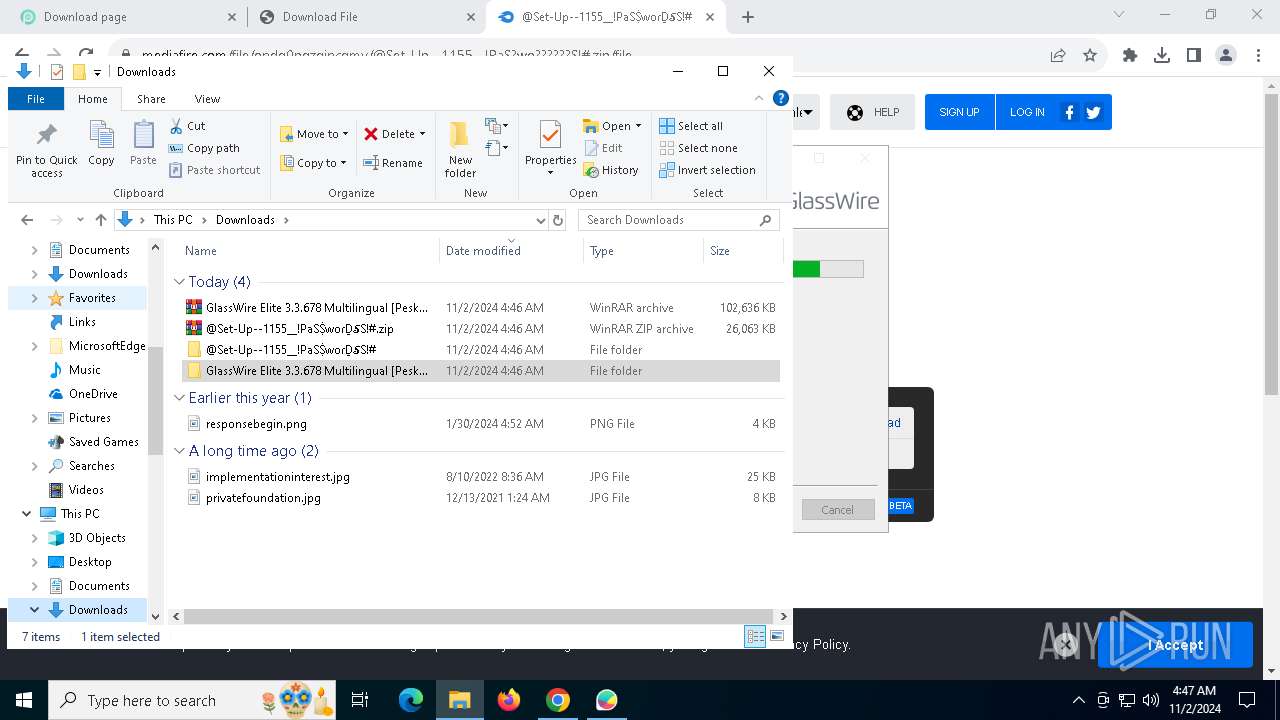
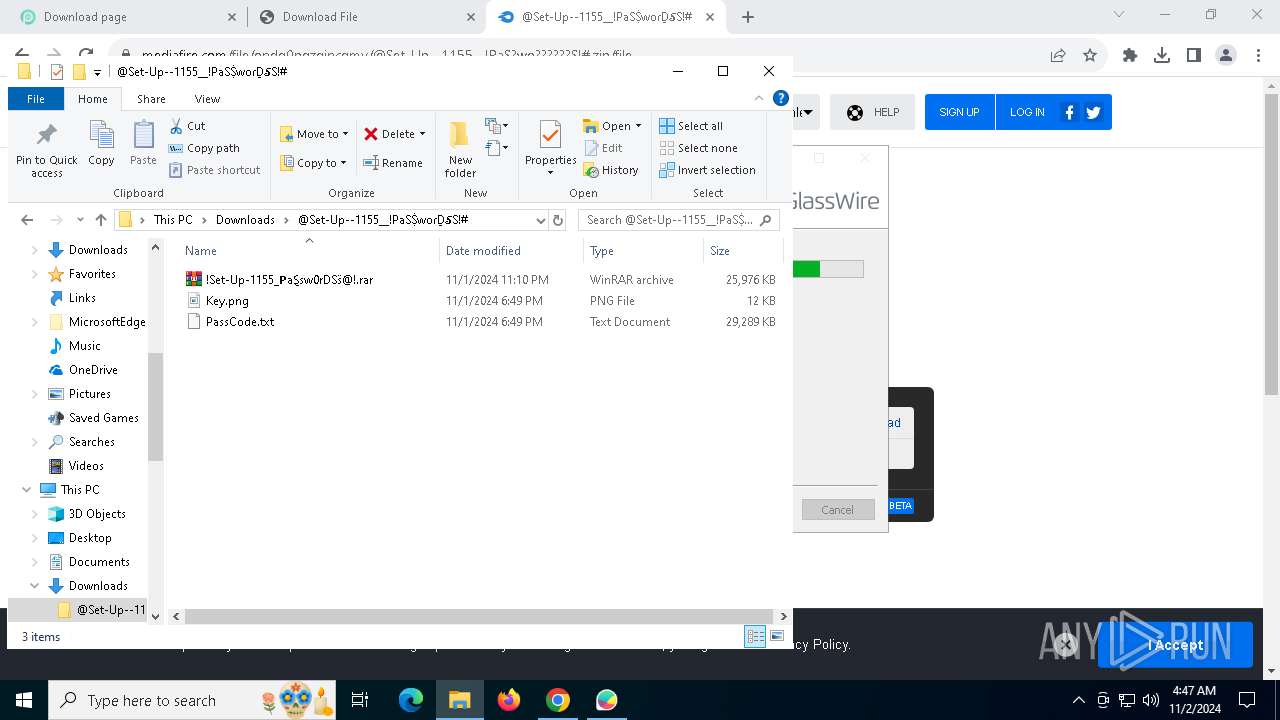
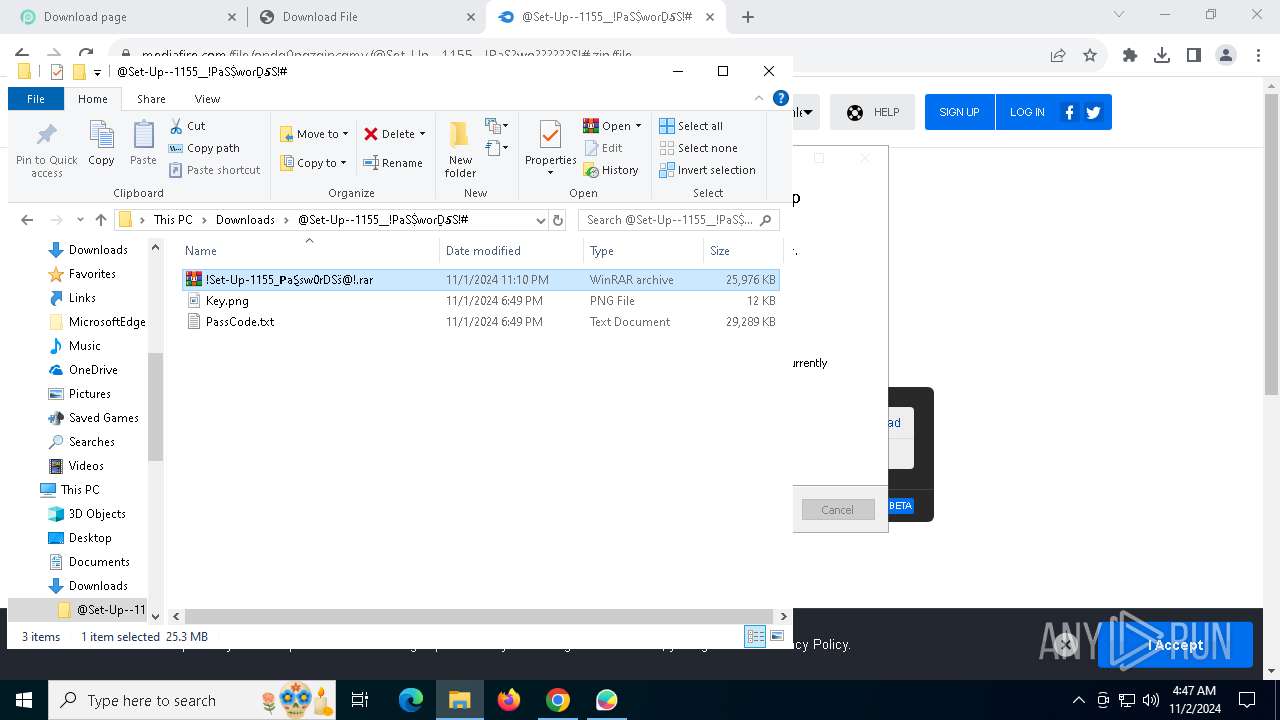
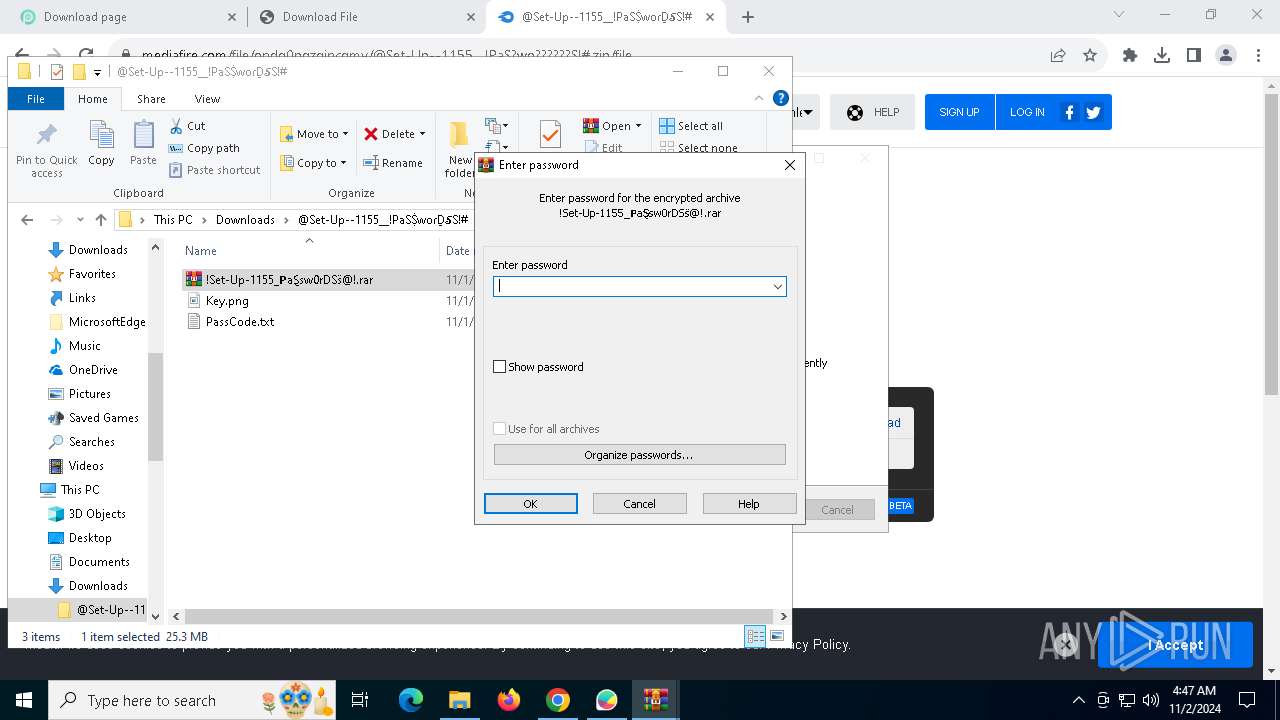
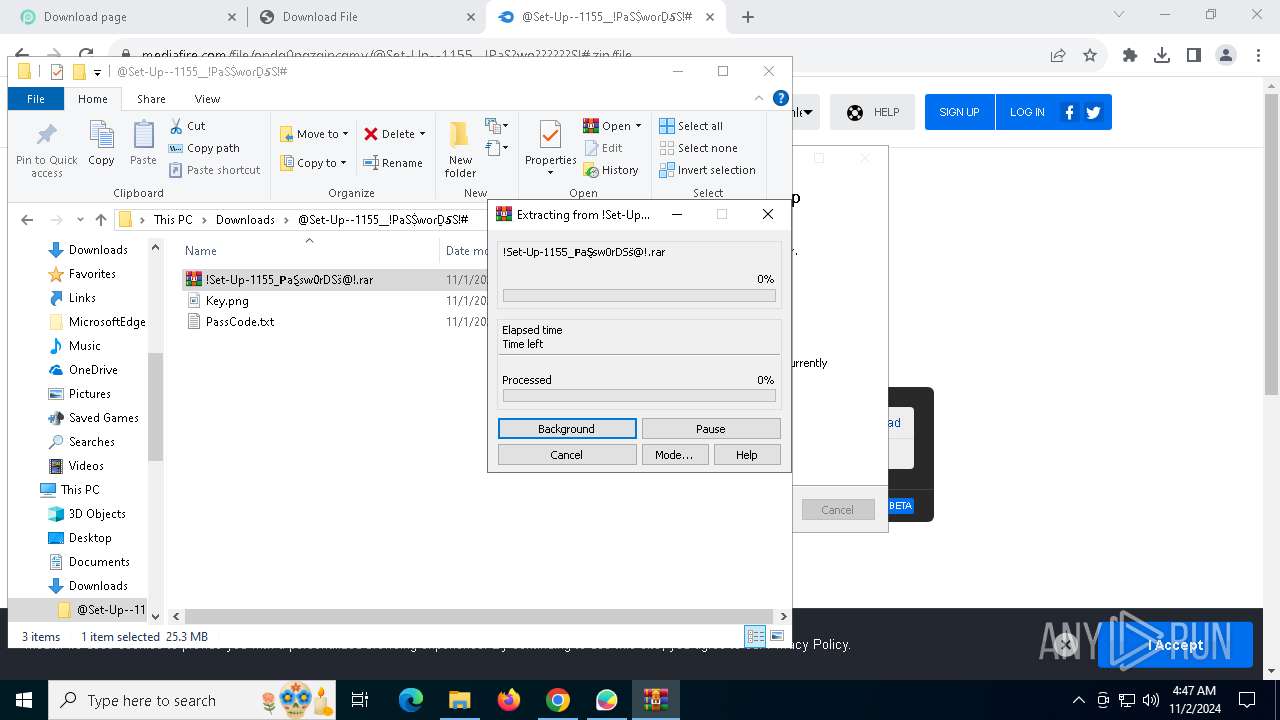
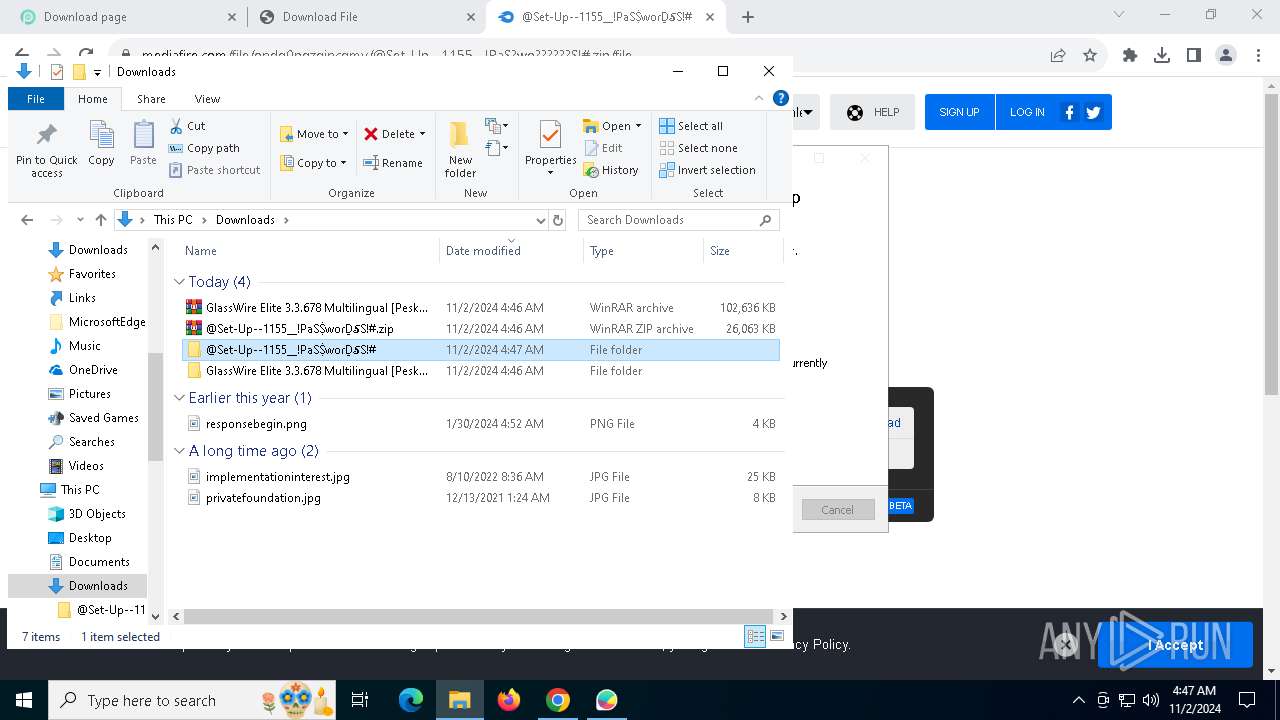
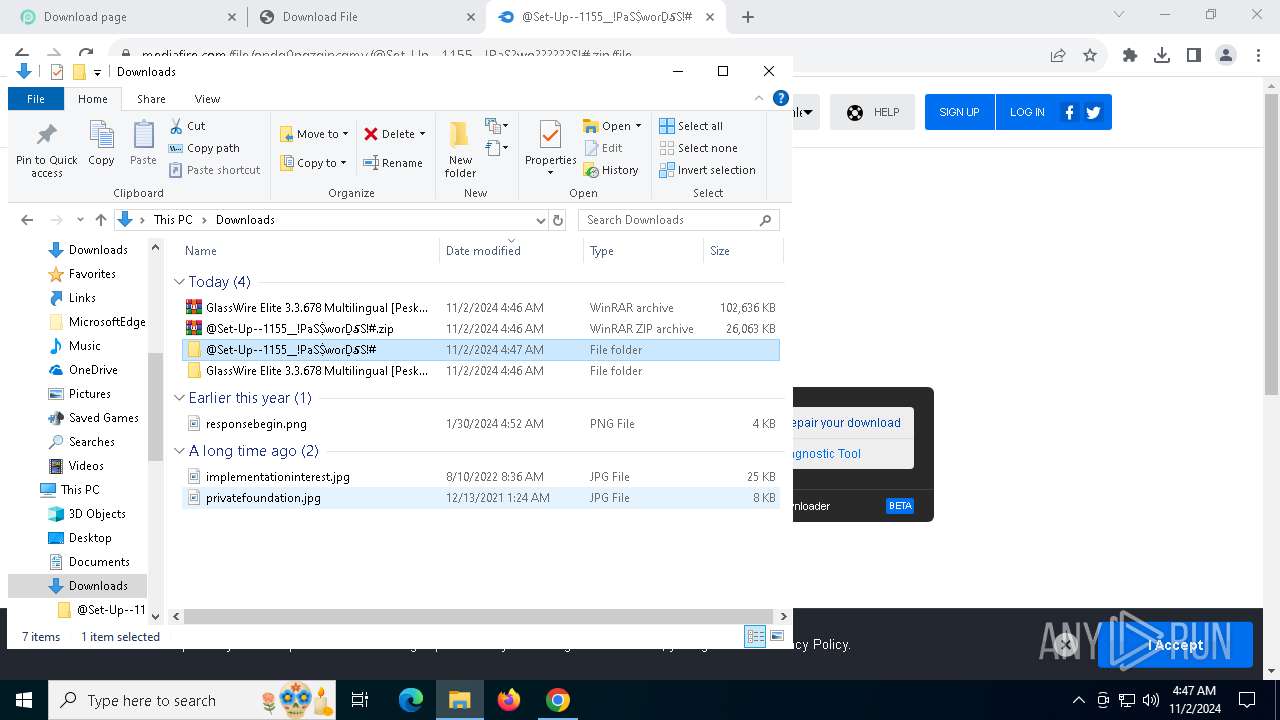
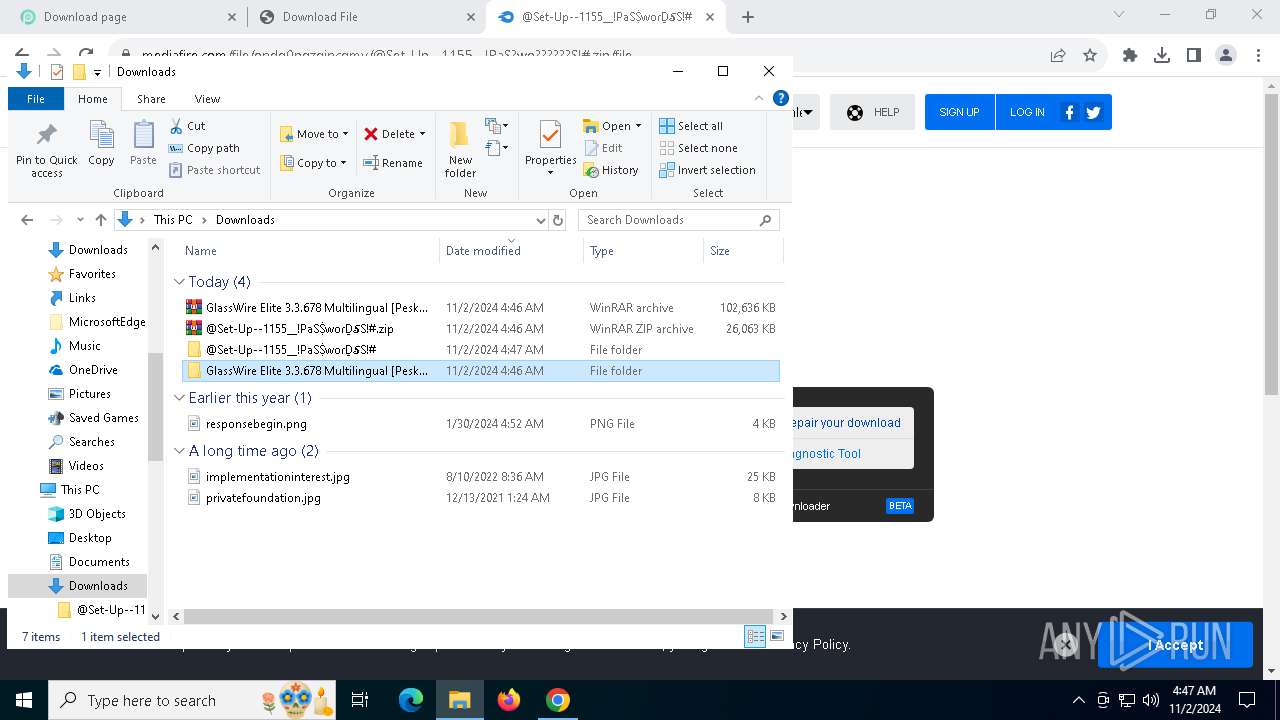
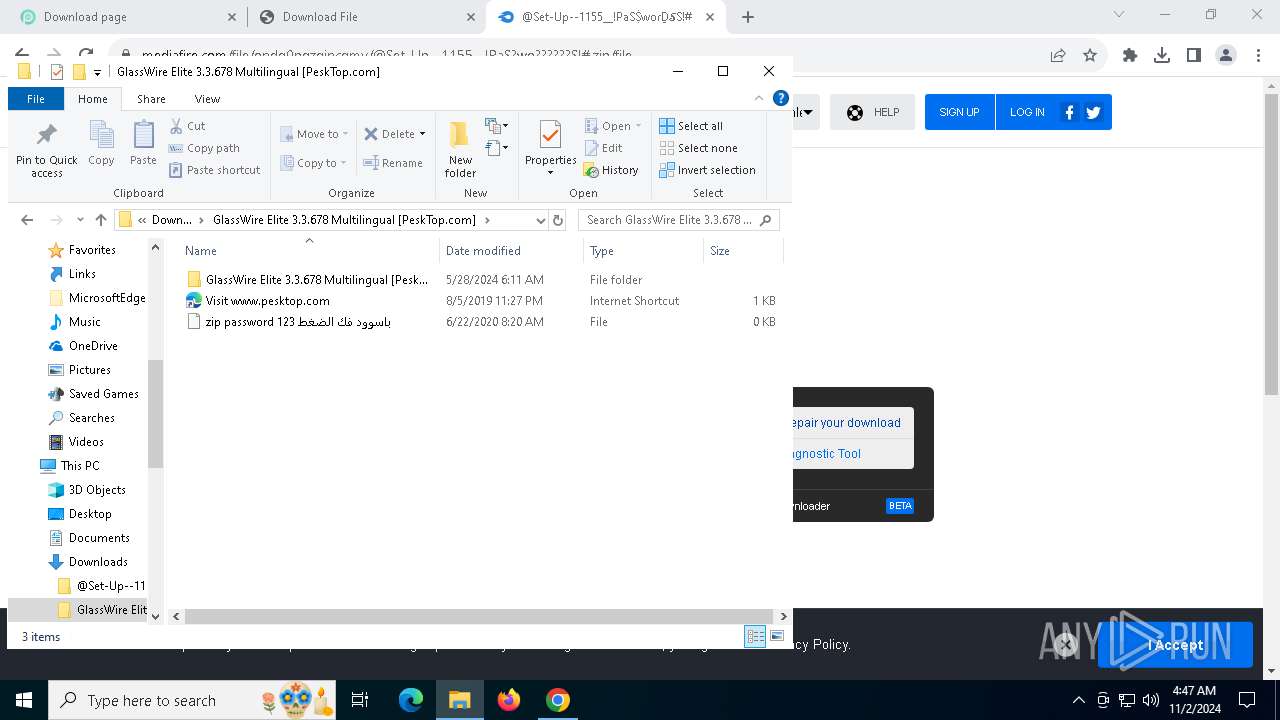
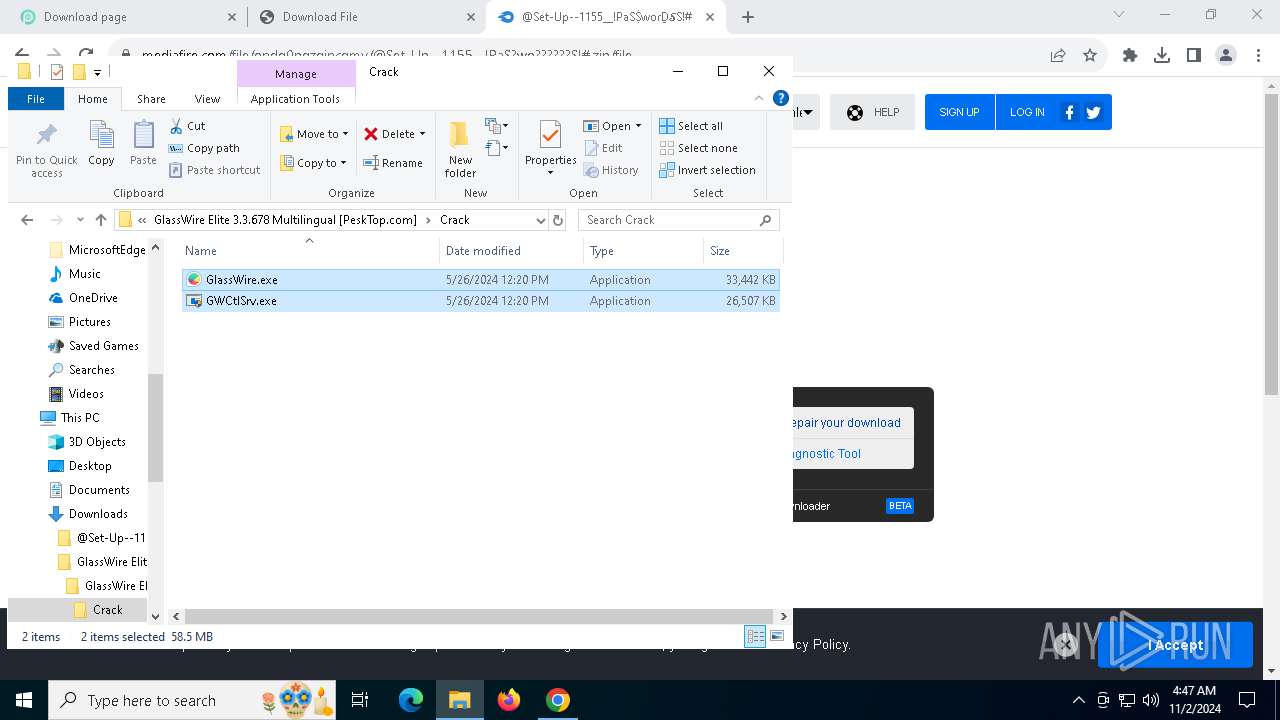
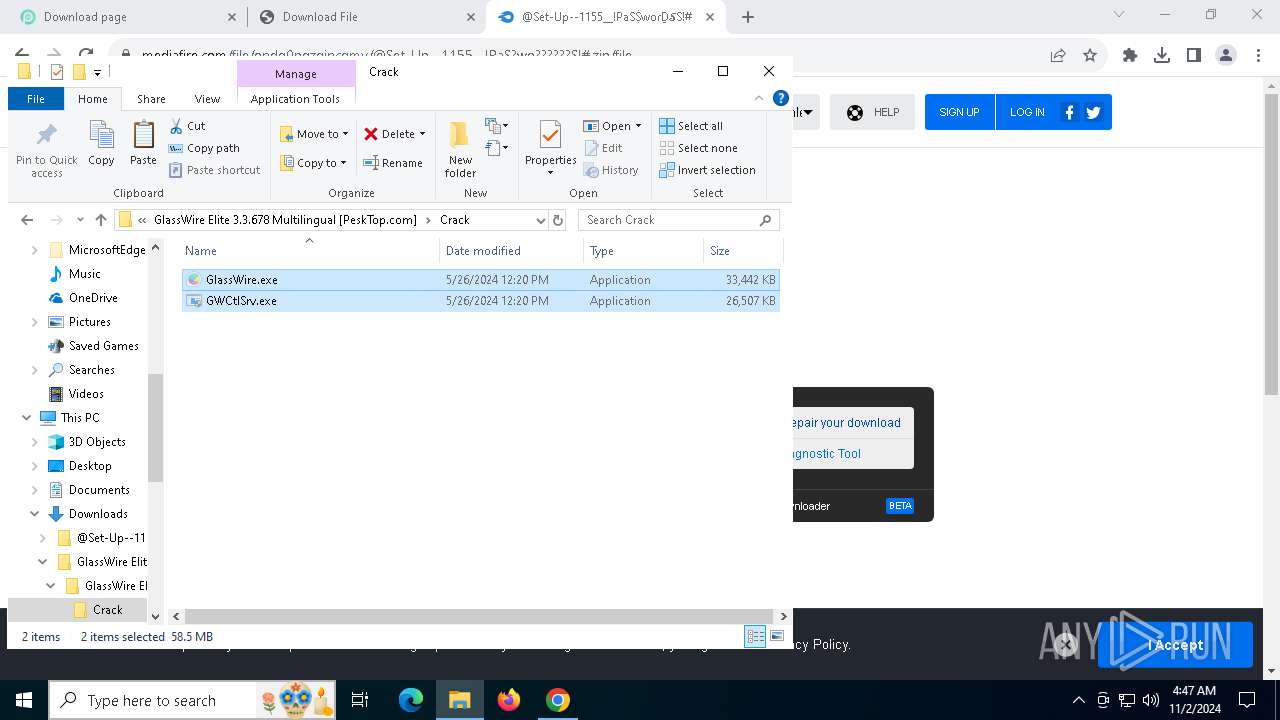
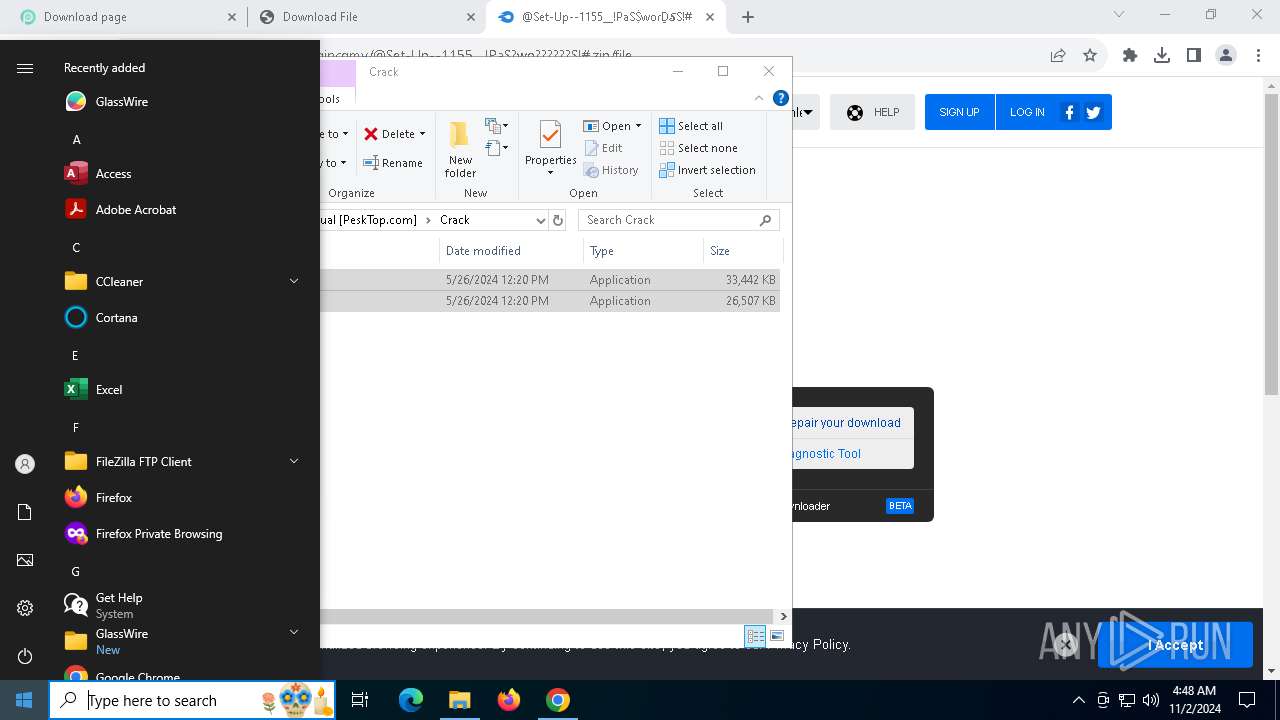
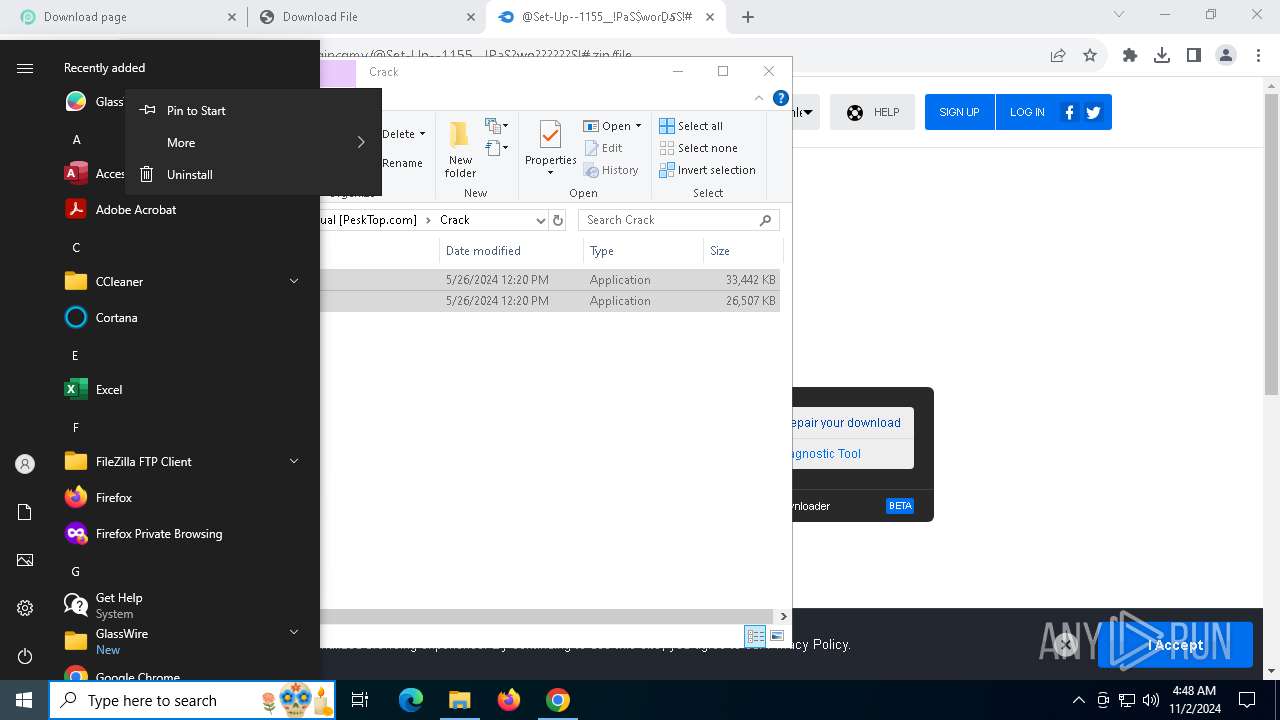
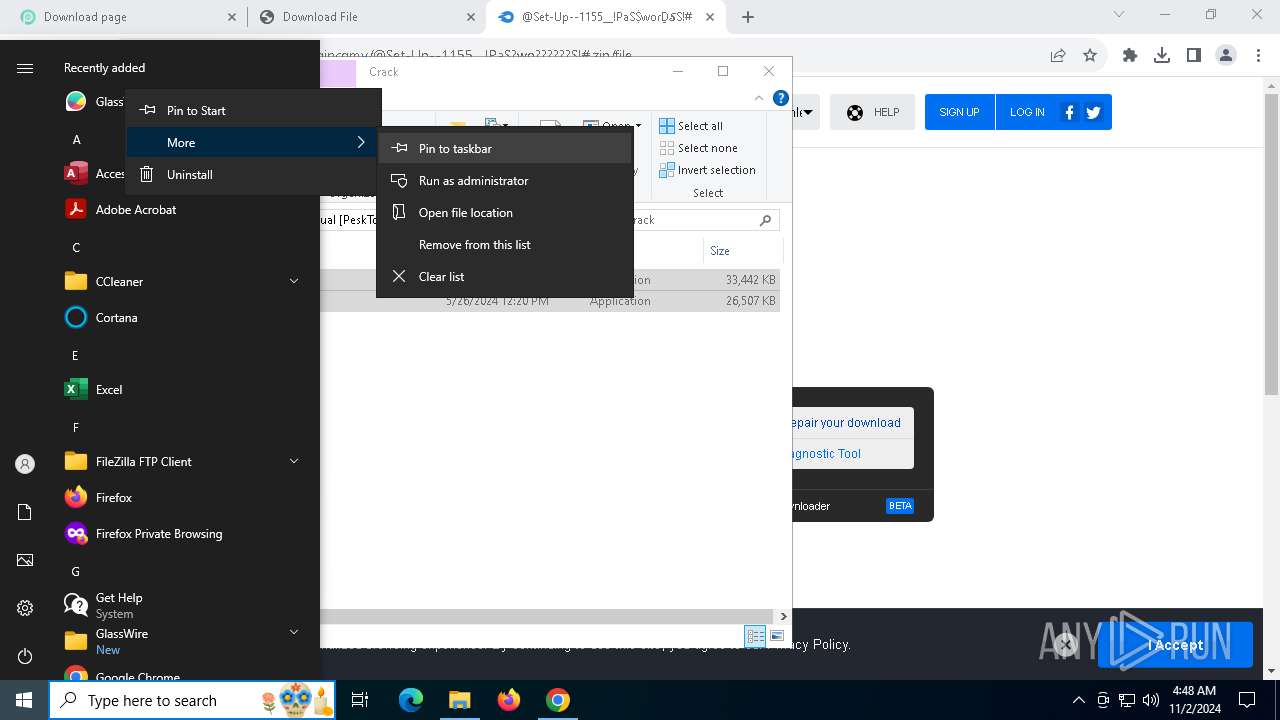
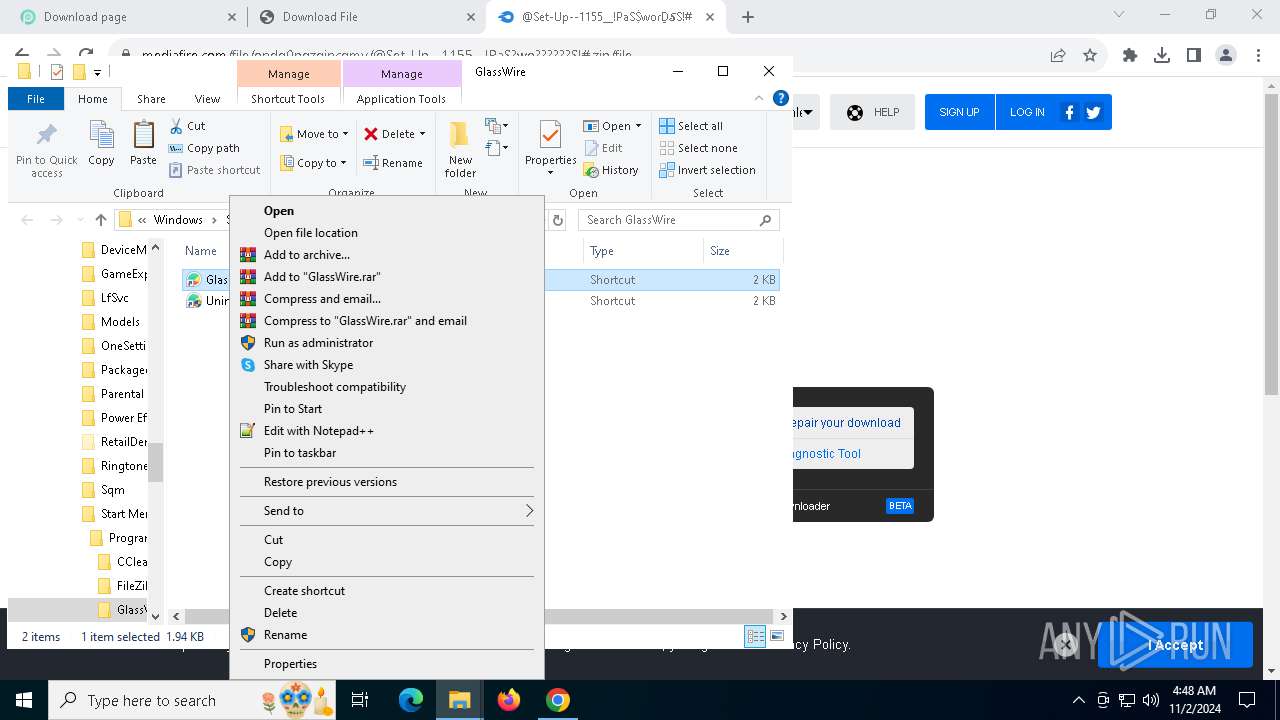
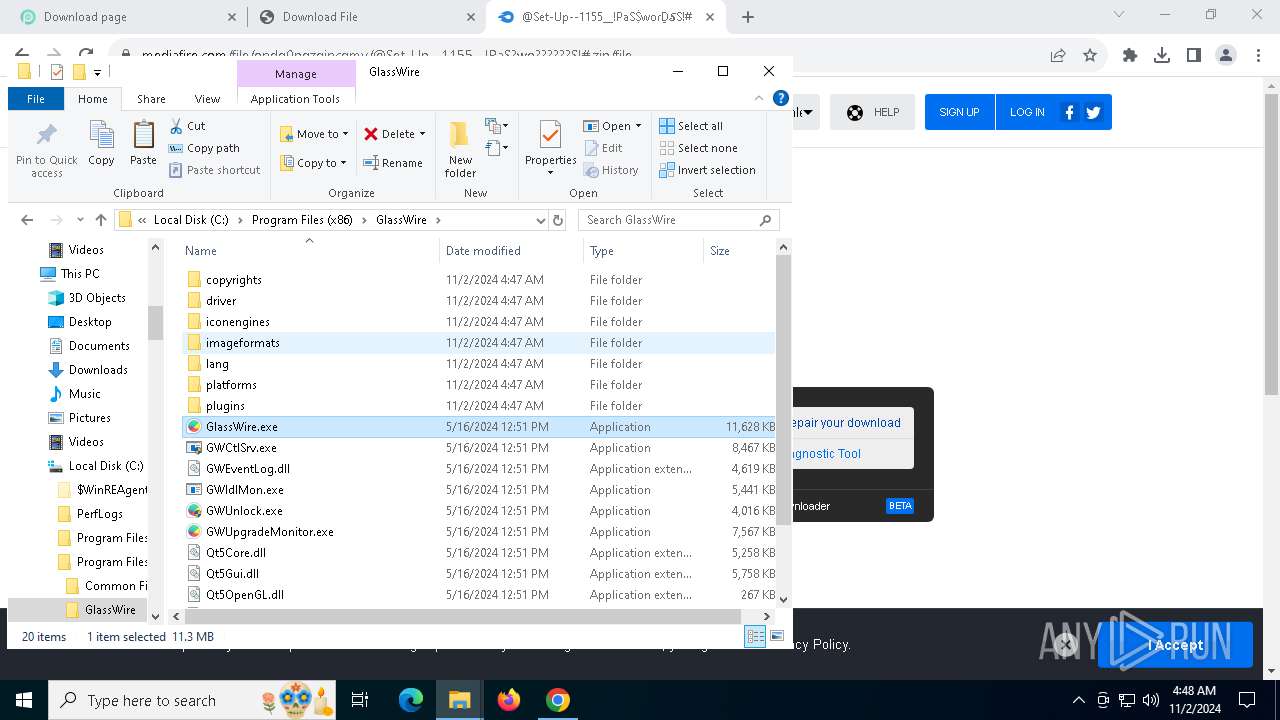
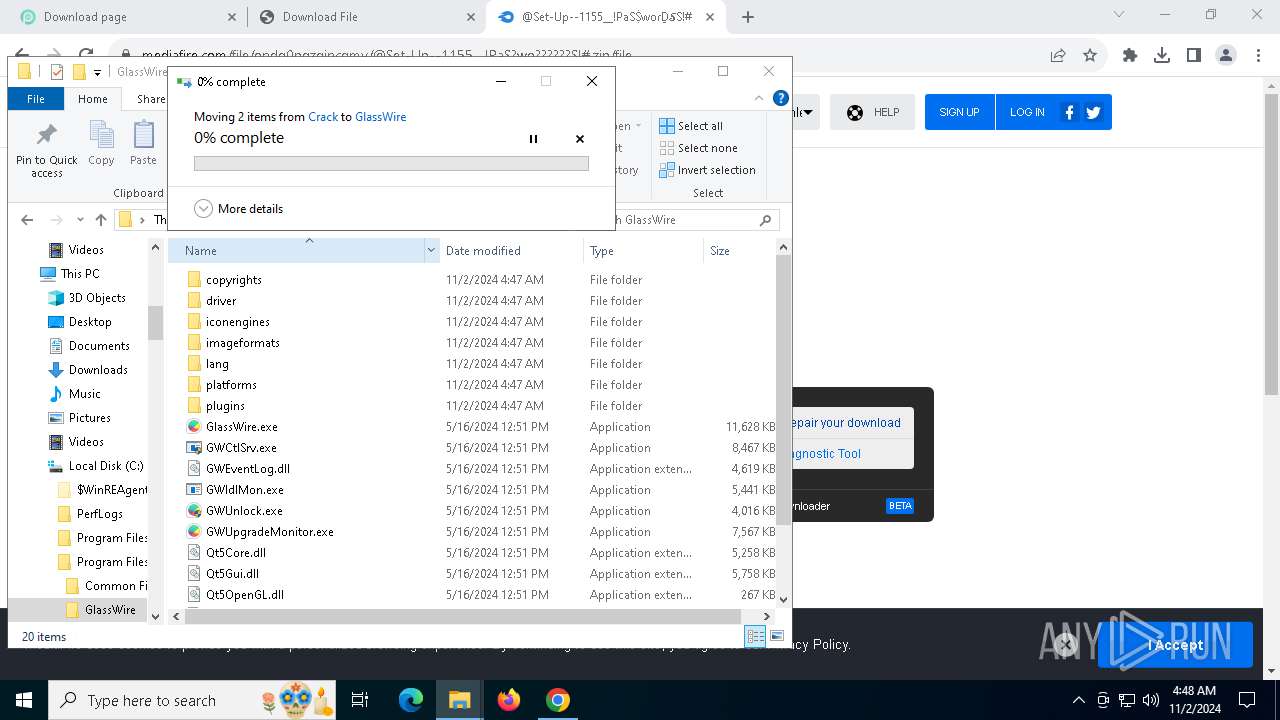
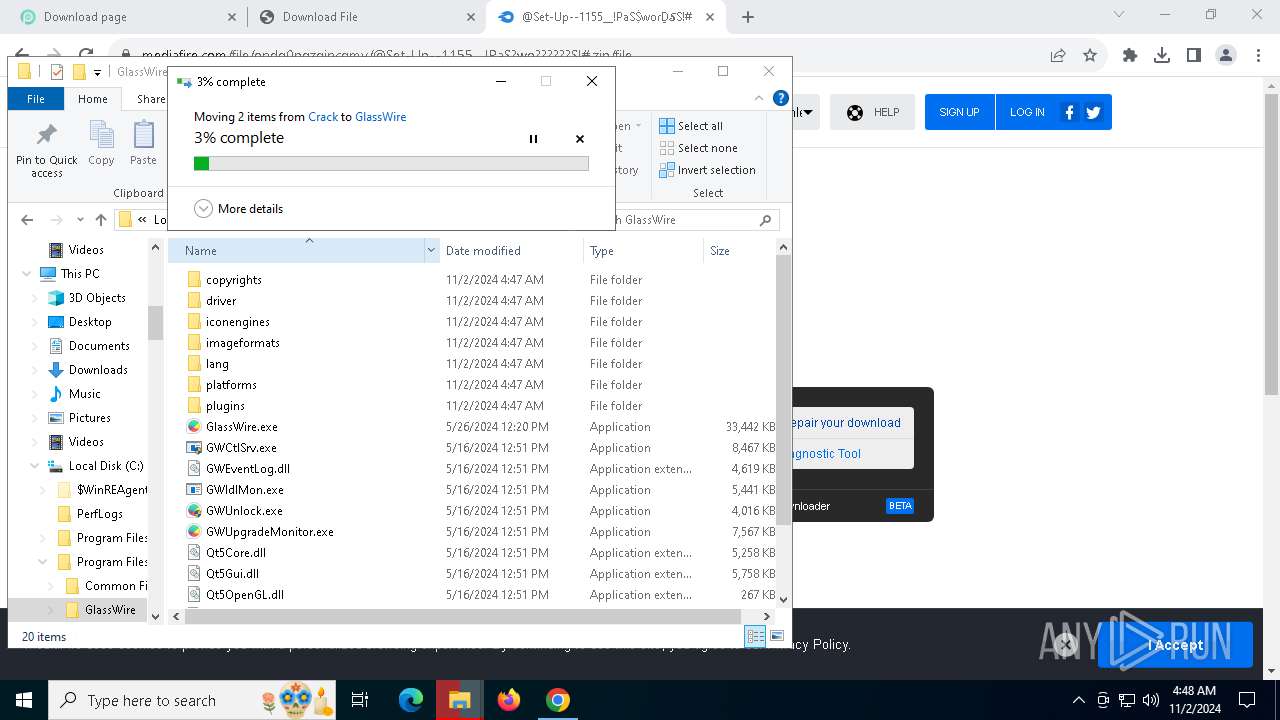
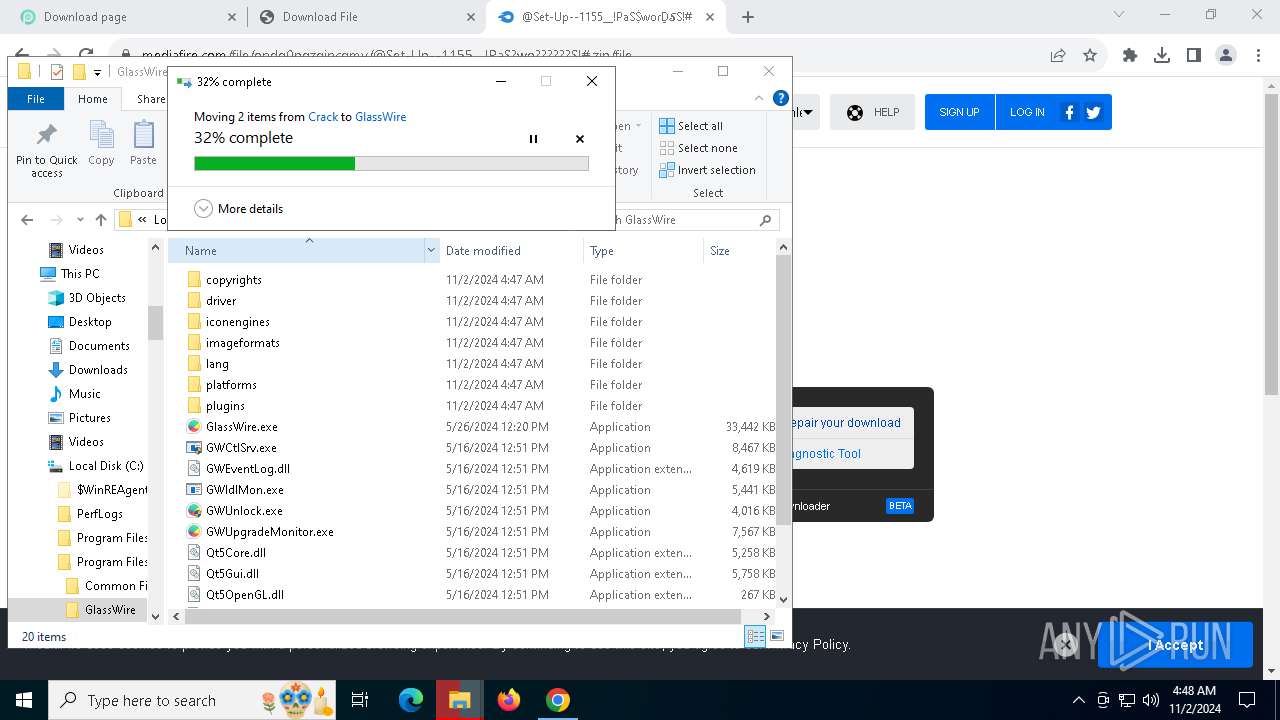
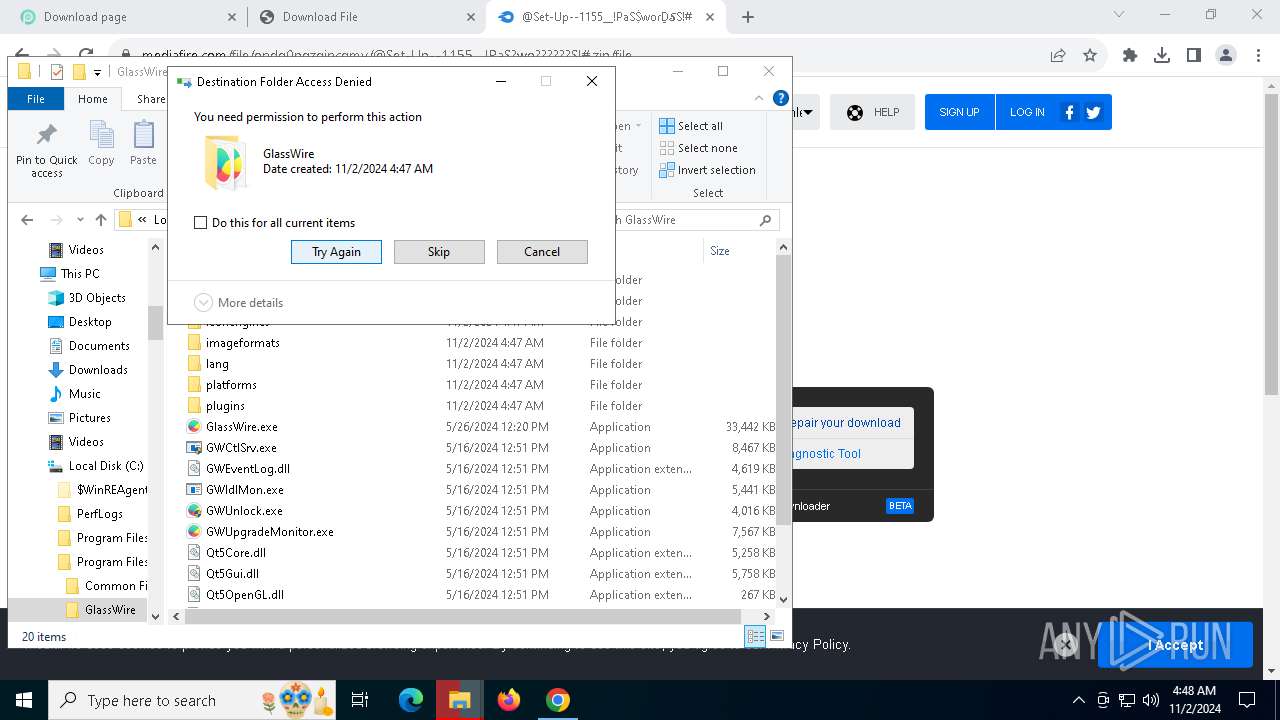
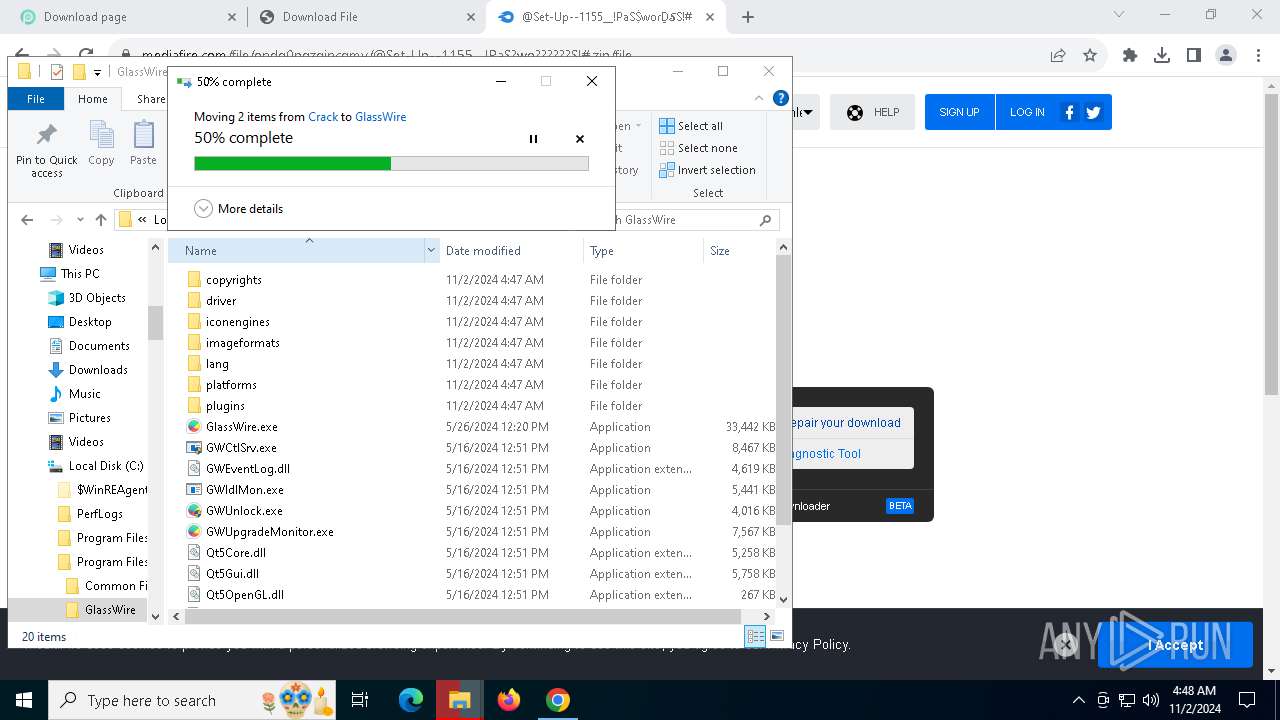
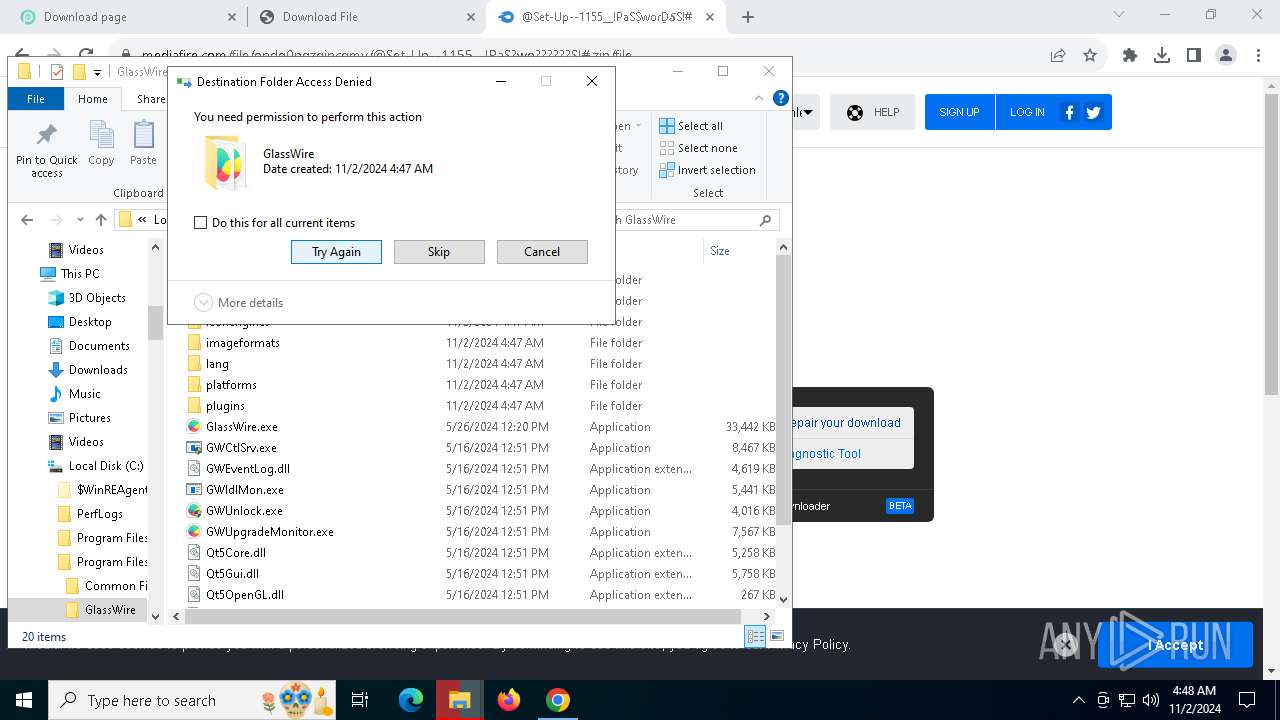
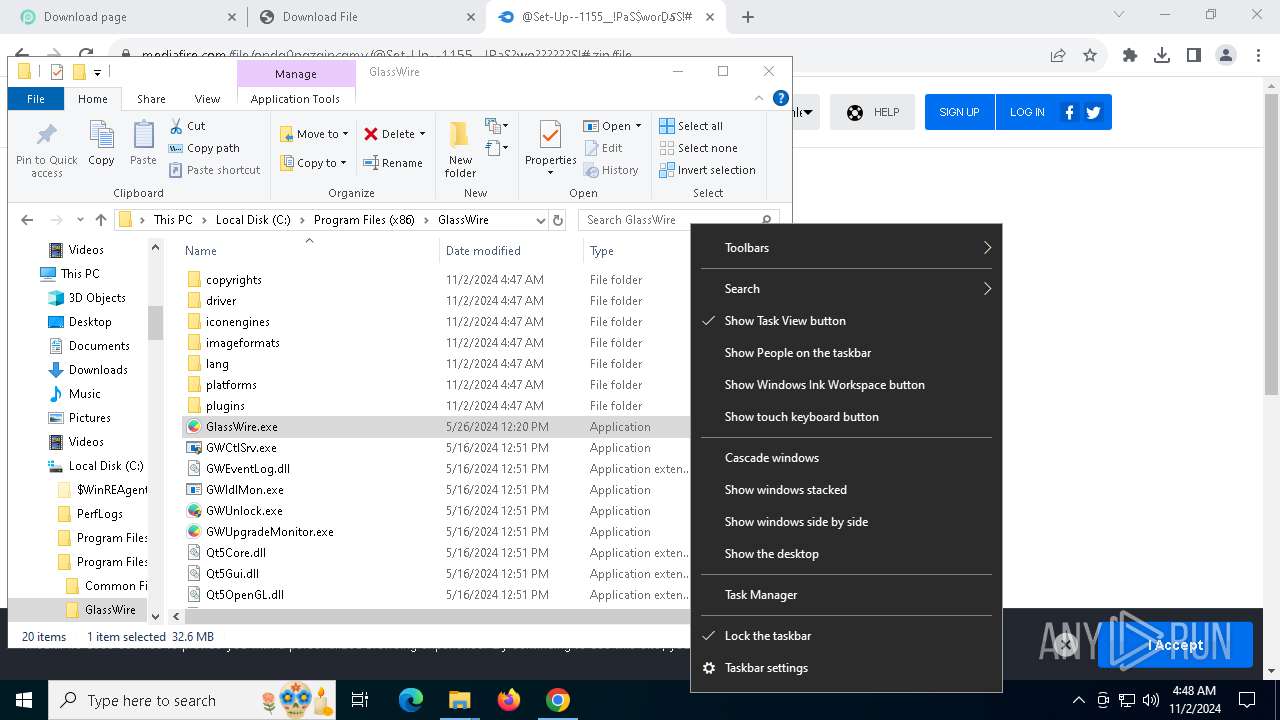
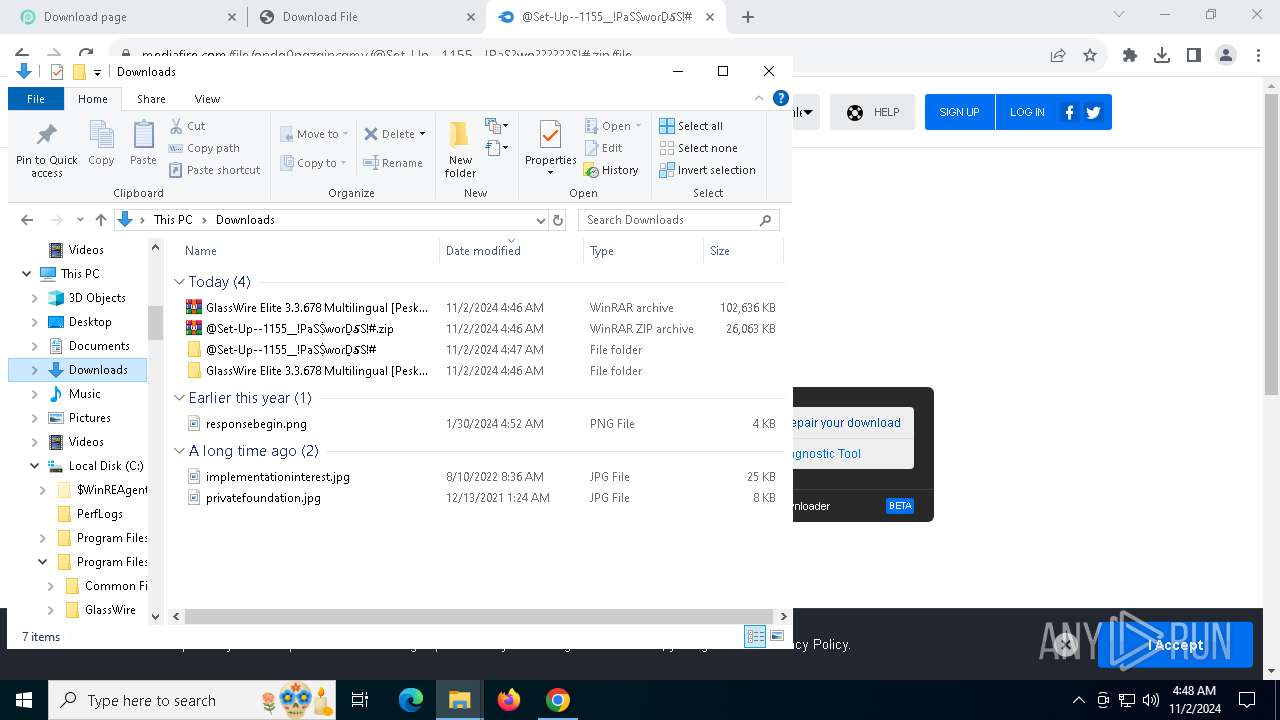
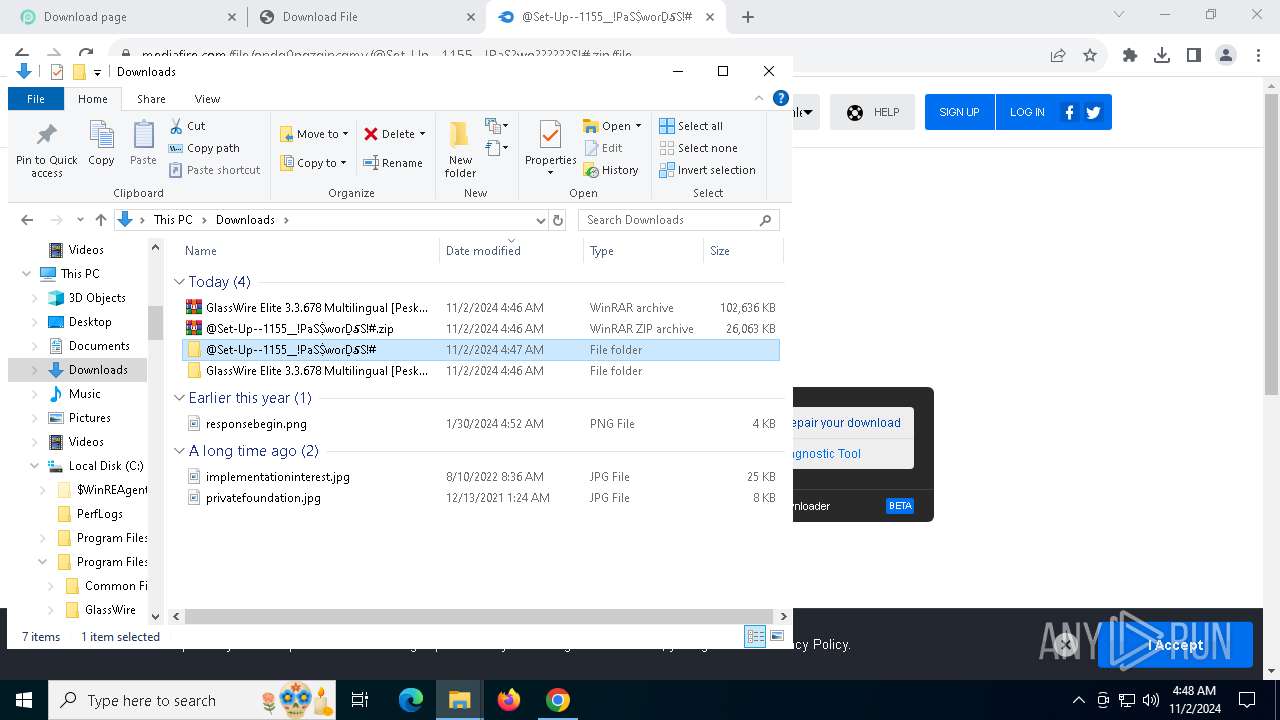
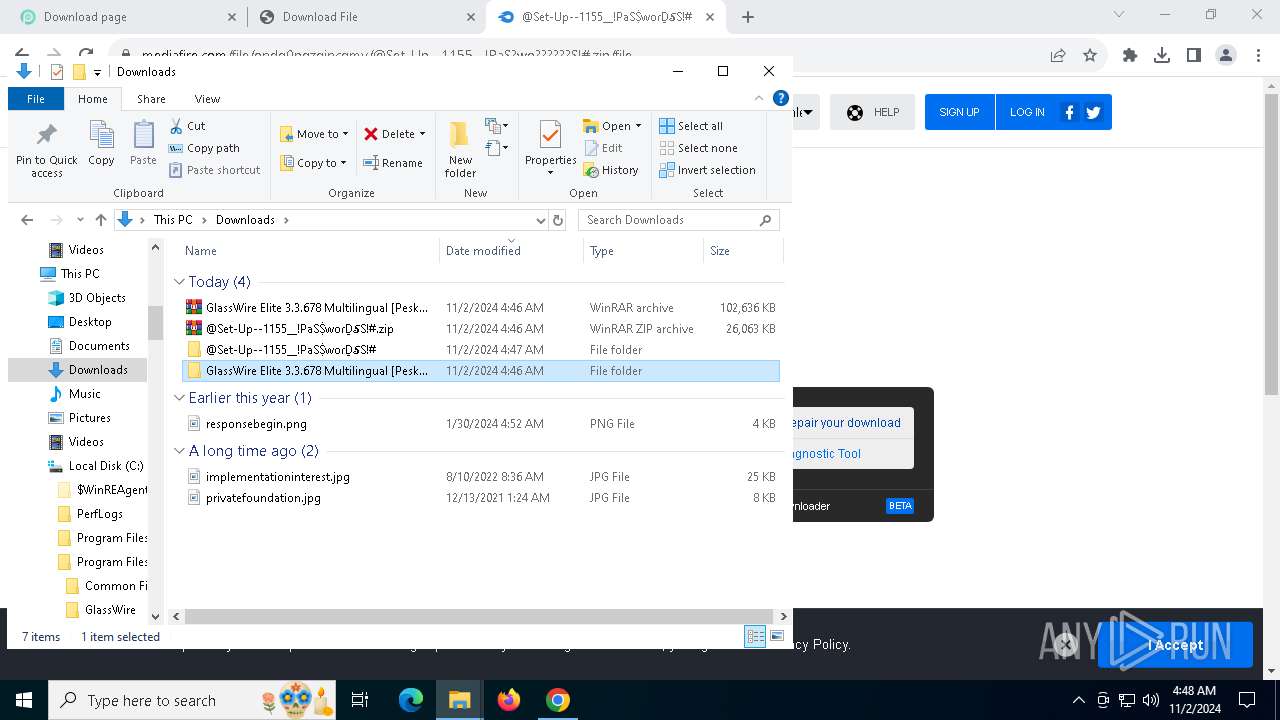
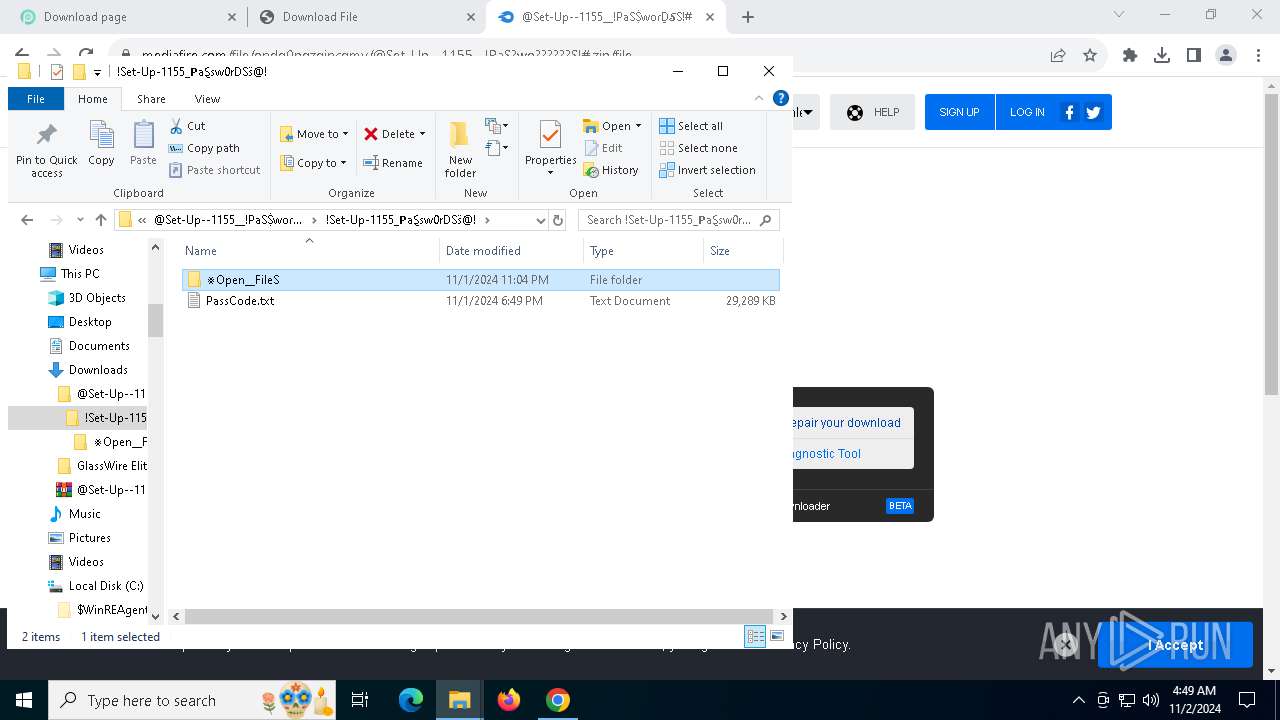
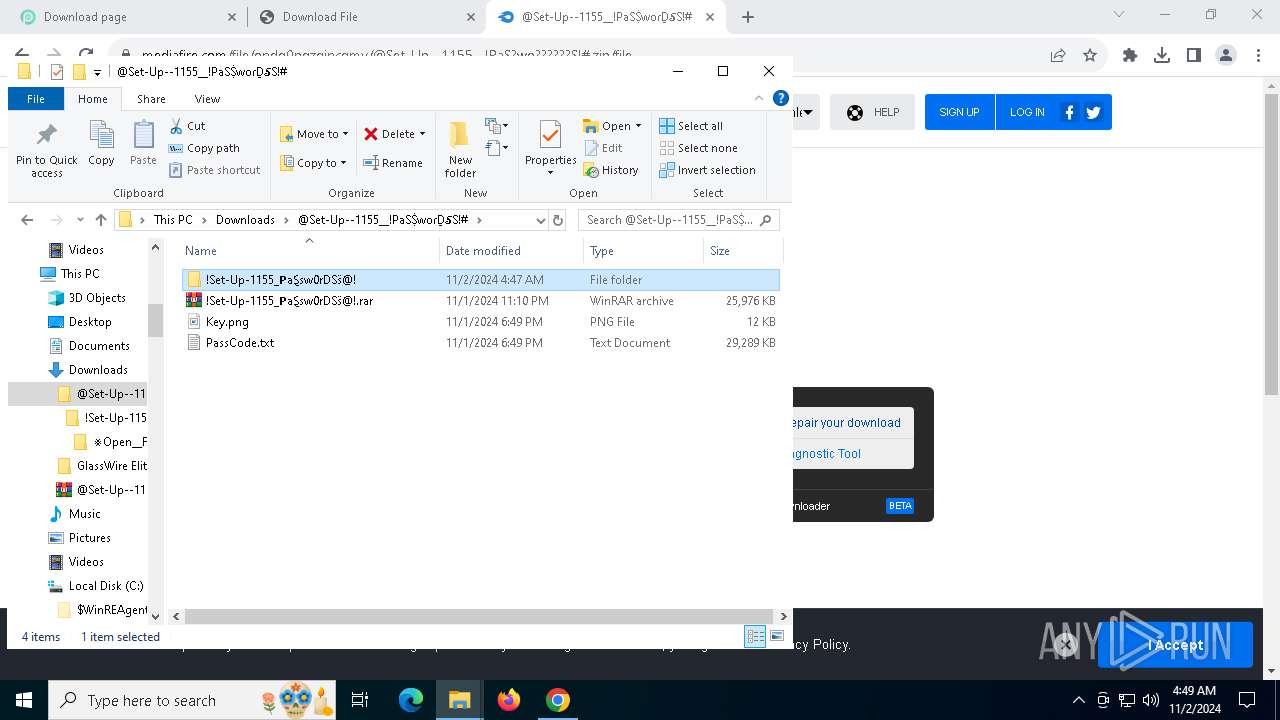
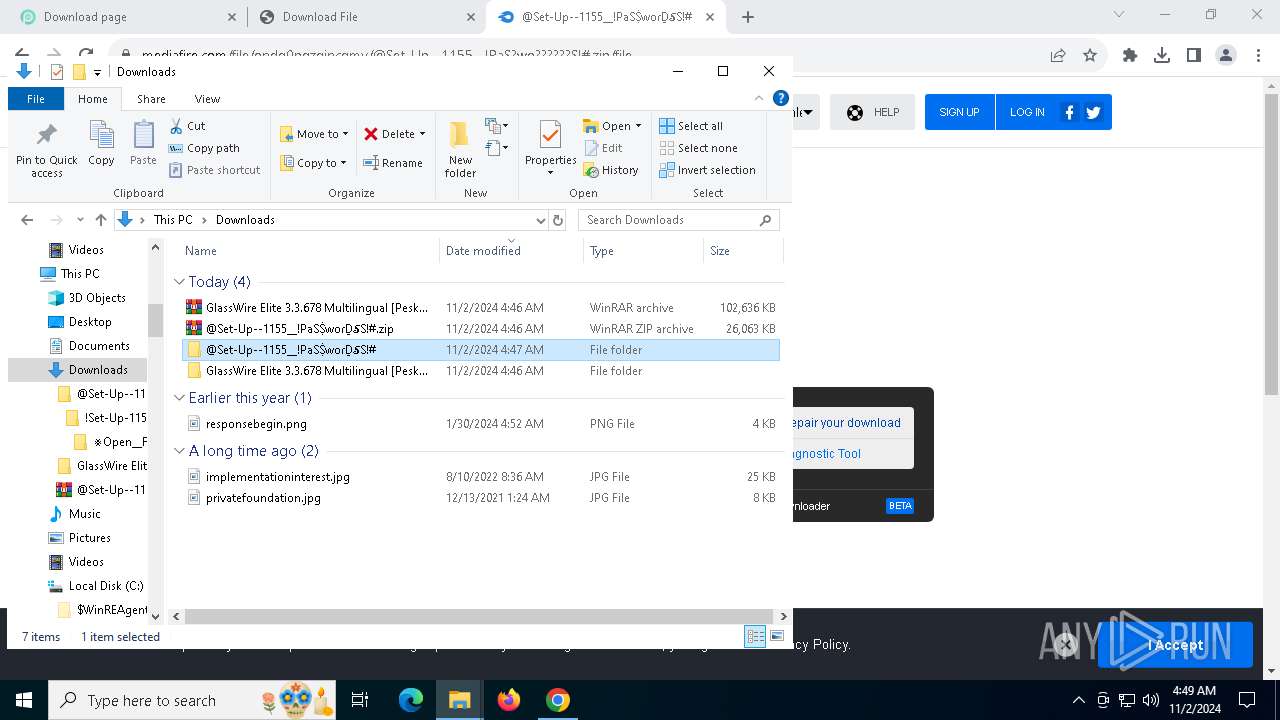
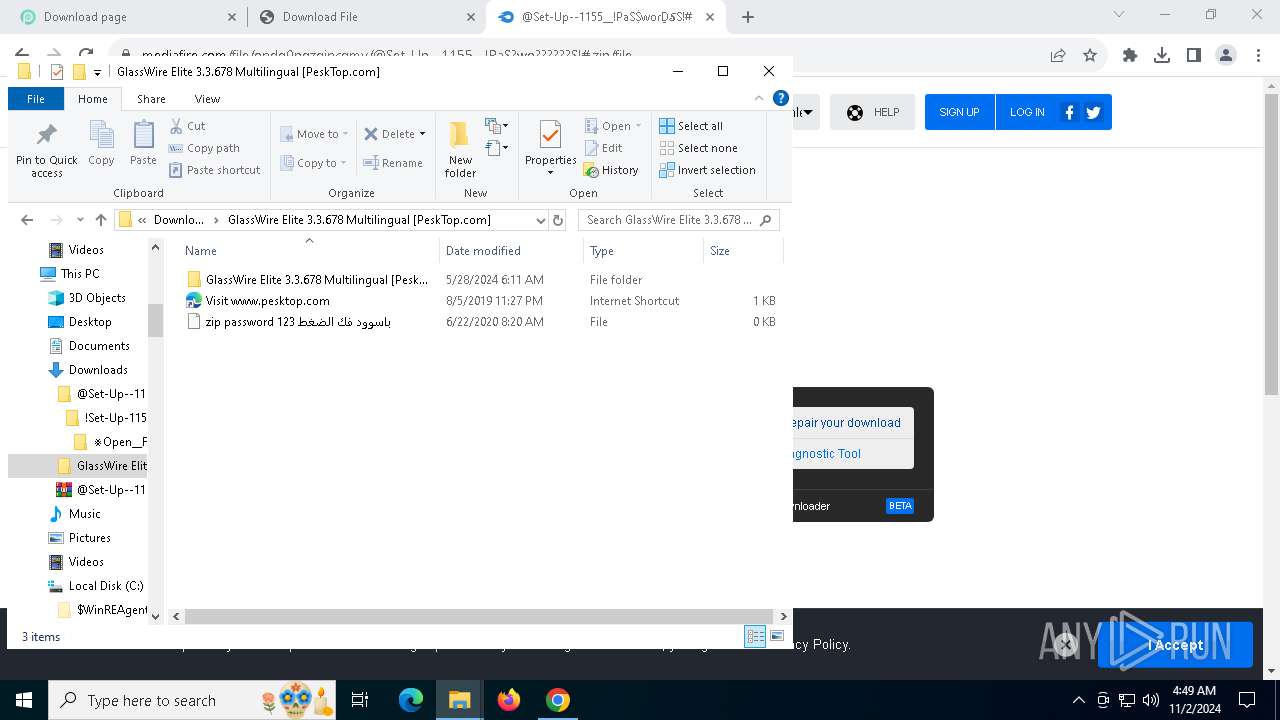
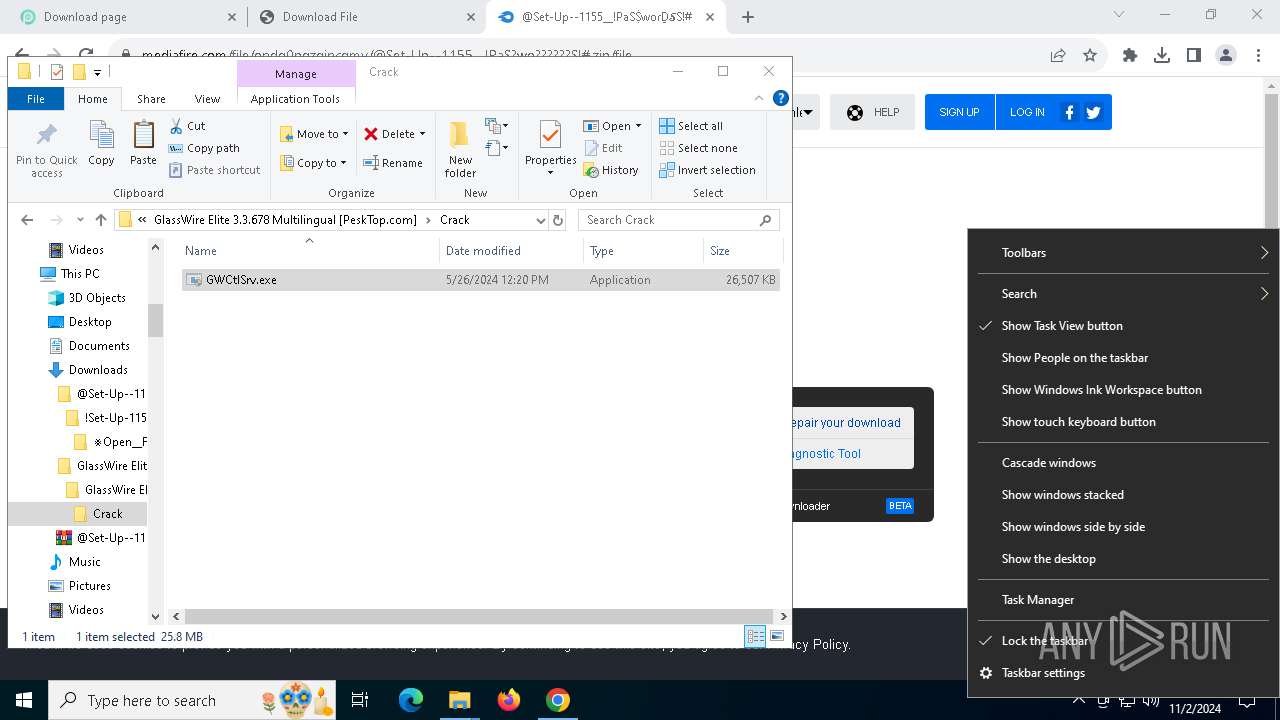
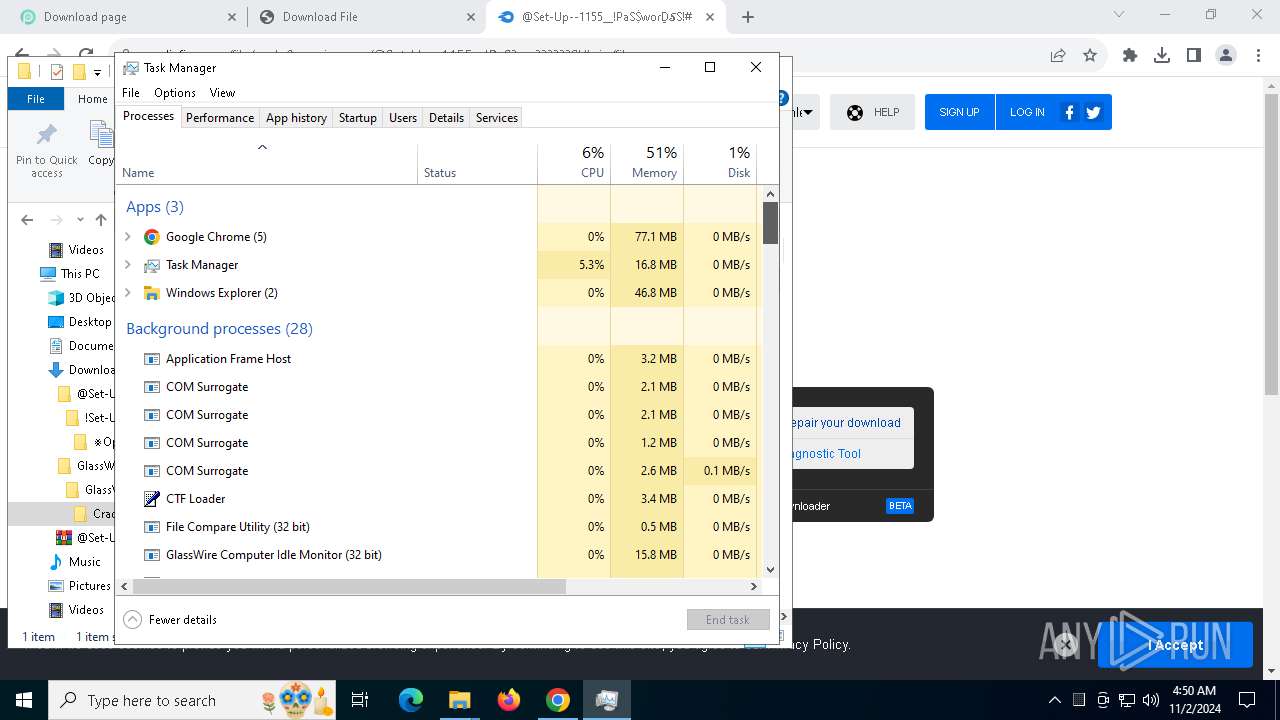
Manual execution by a user
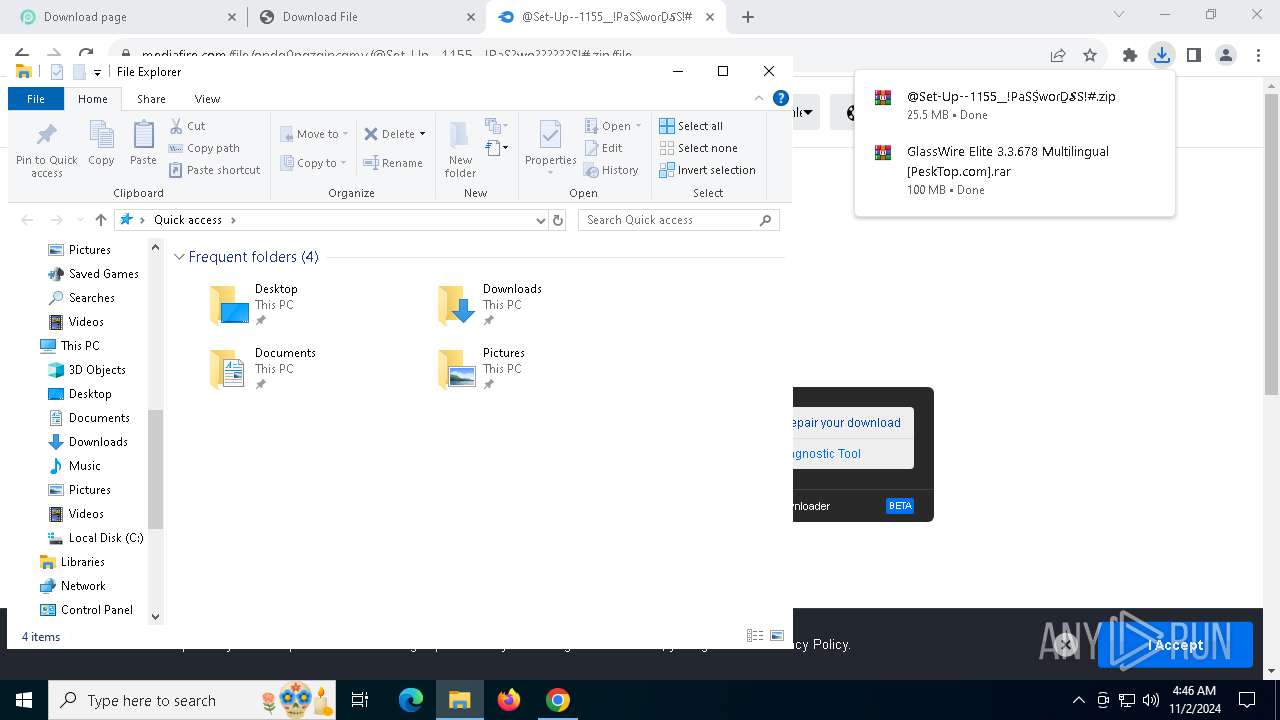
- WinRAR.exe (PID: 7800)
- WinRAR.exe (PID: 2684)
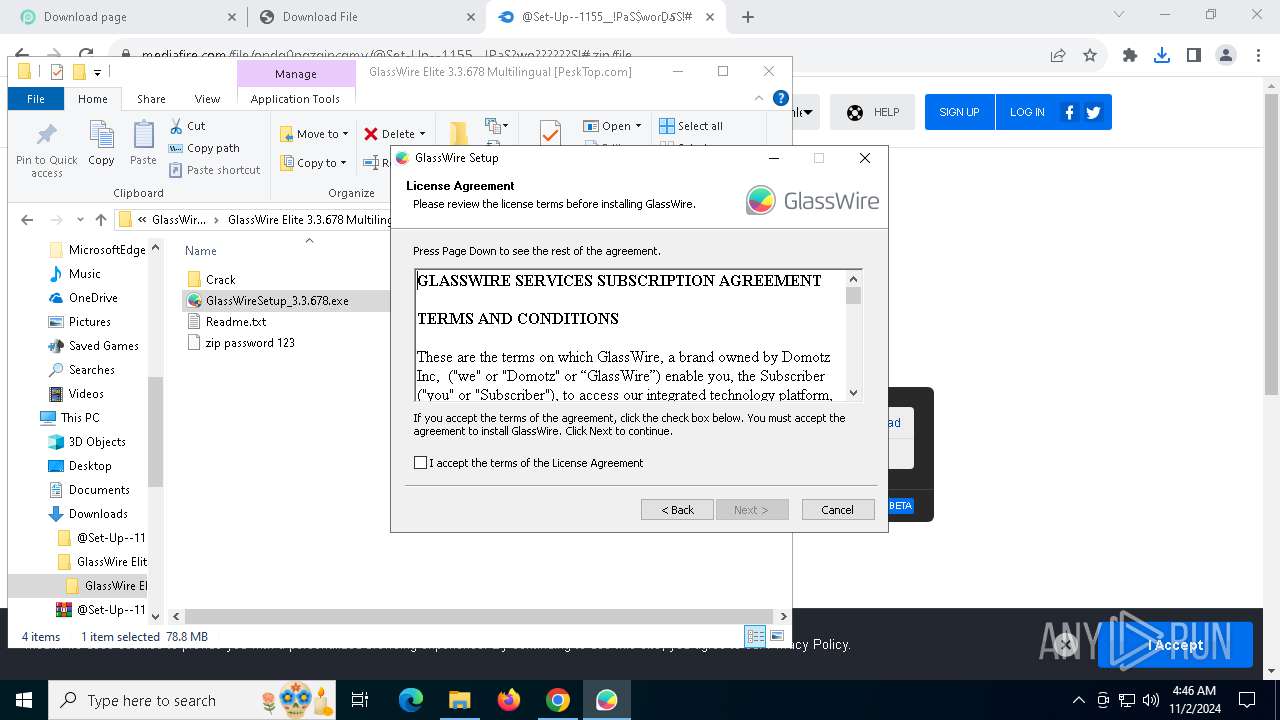
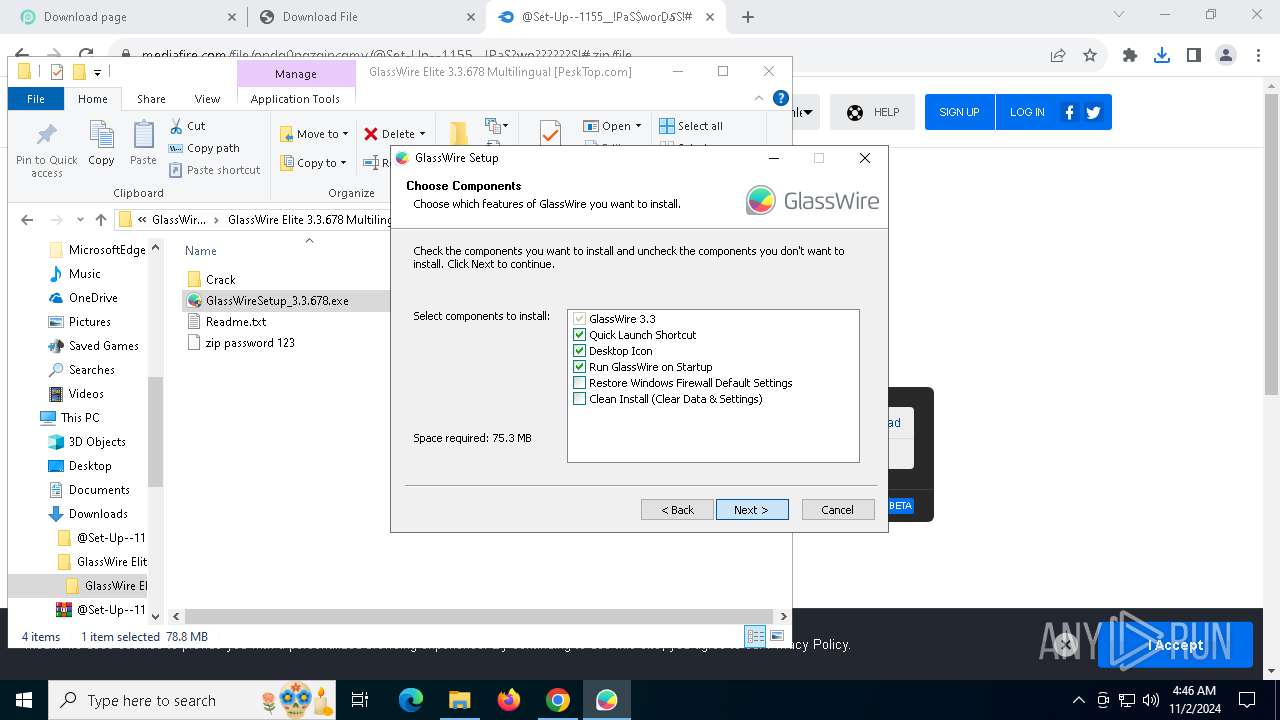
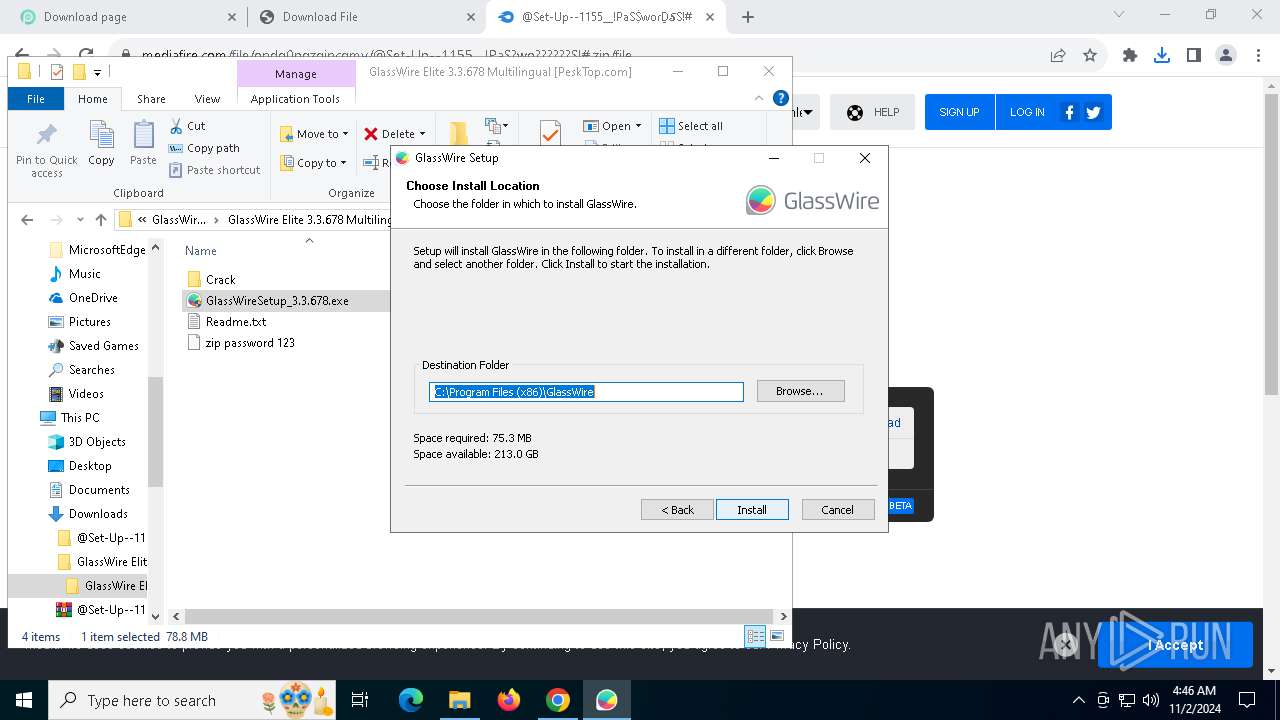
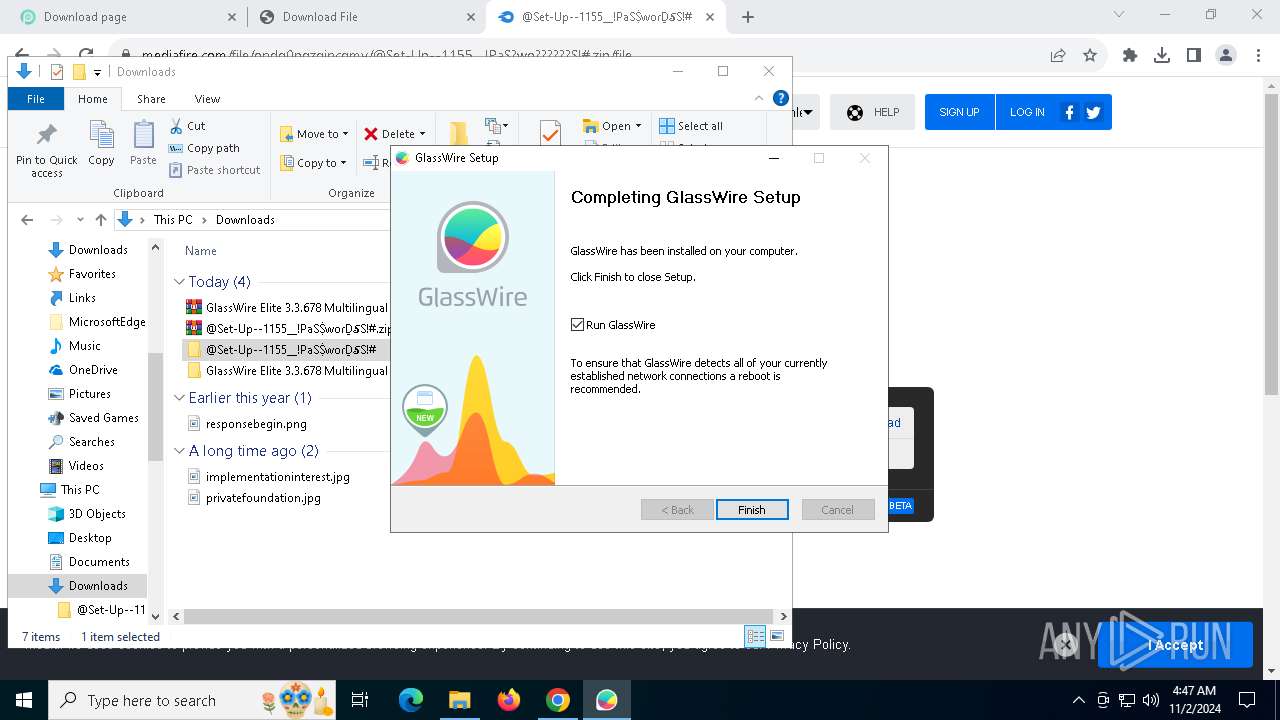
- GlassWireSetup_3.3.678.exe (PID: 1344)
- GlassWireSetup_3.3.678.exe (PID: 4352)
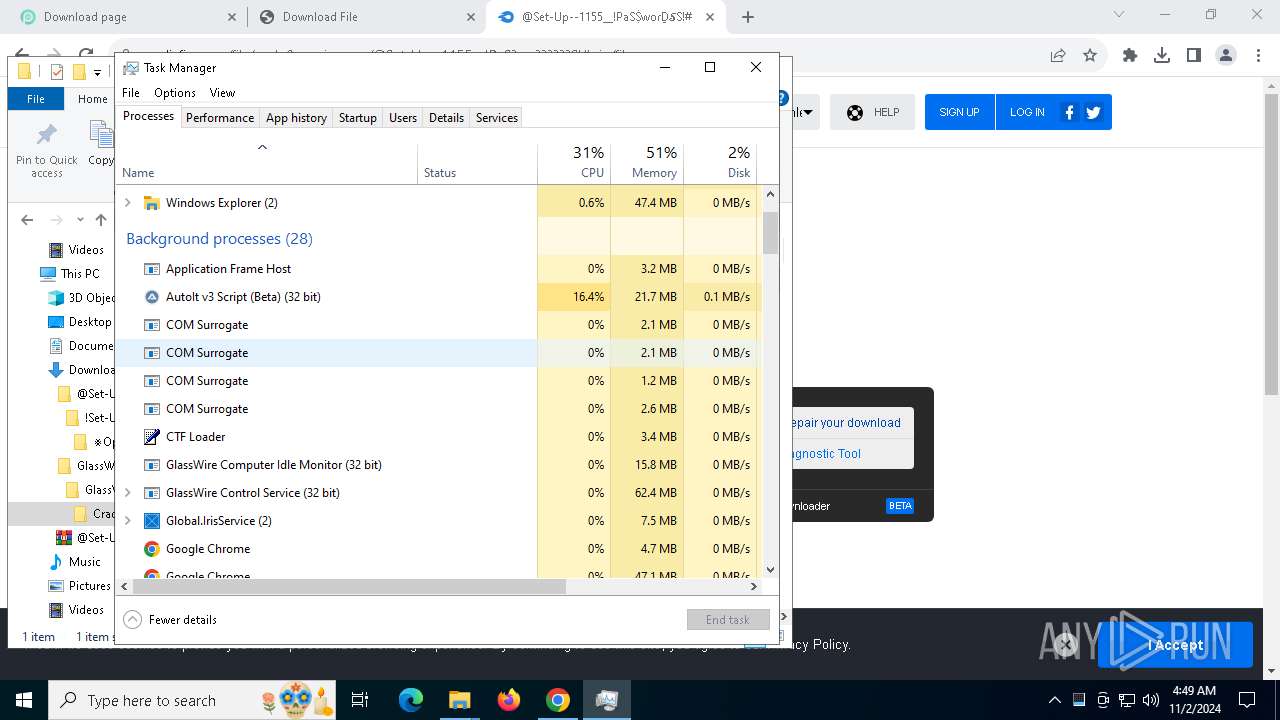
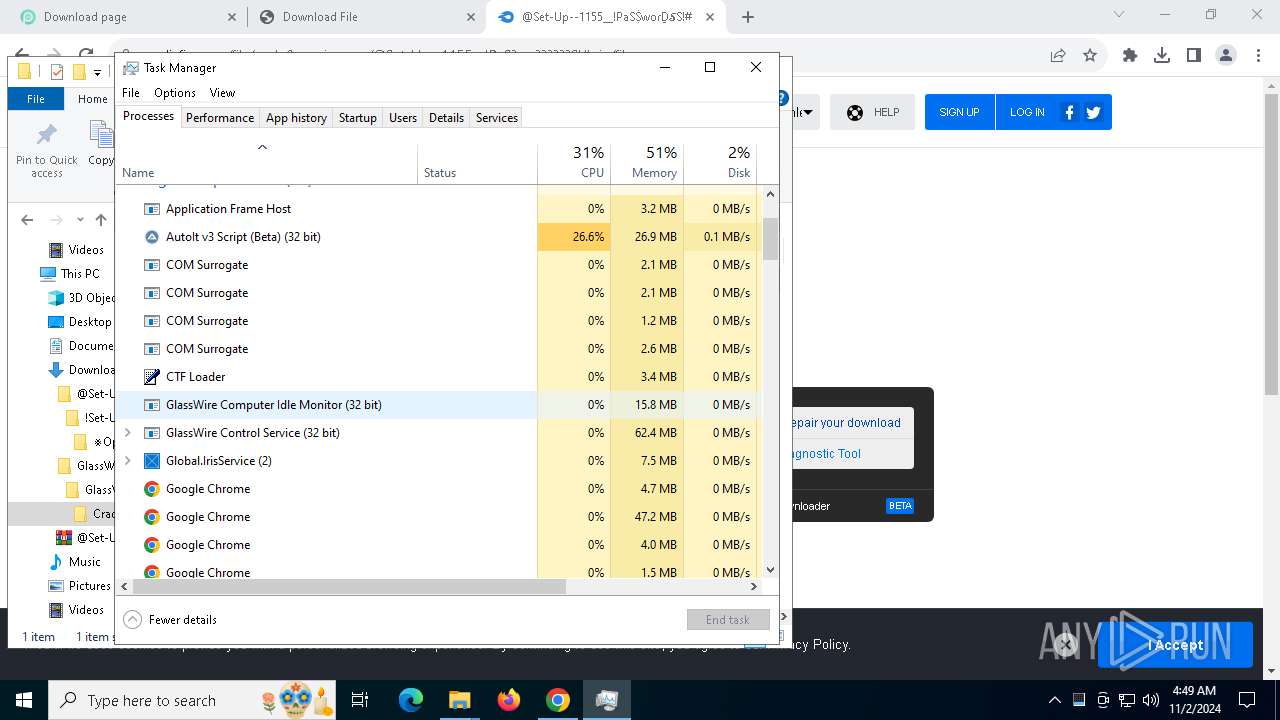
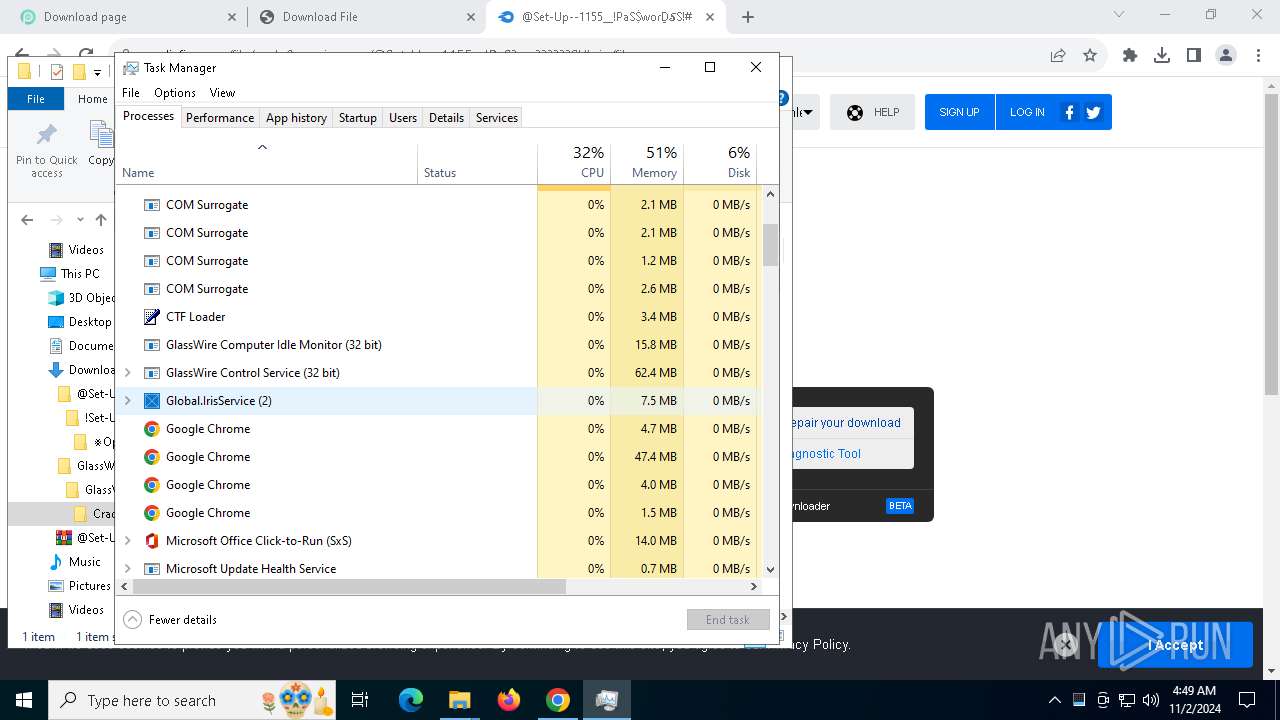
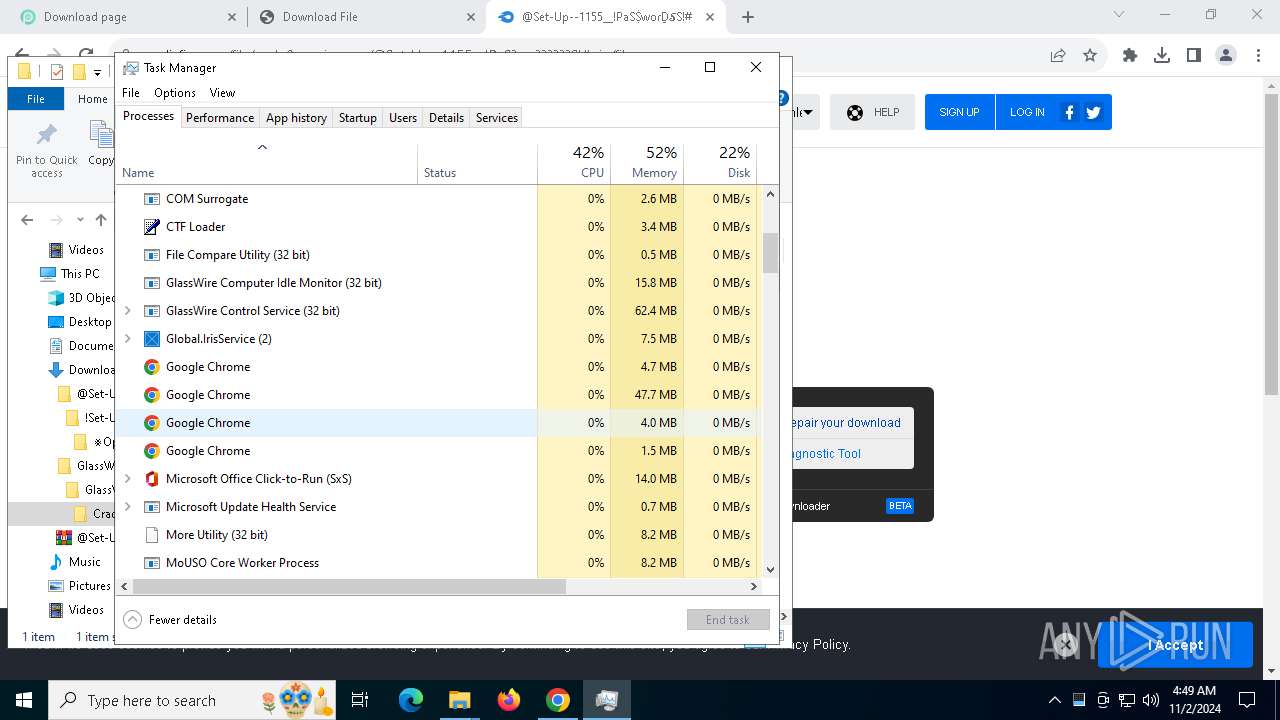
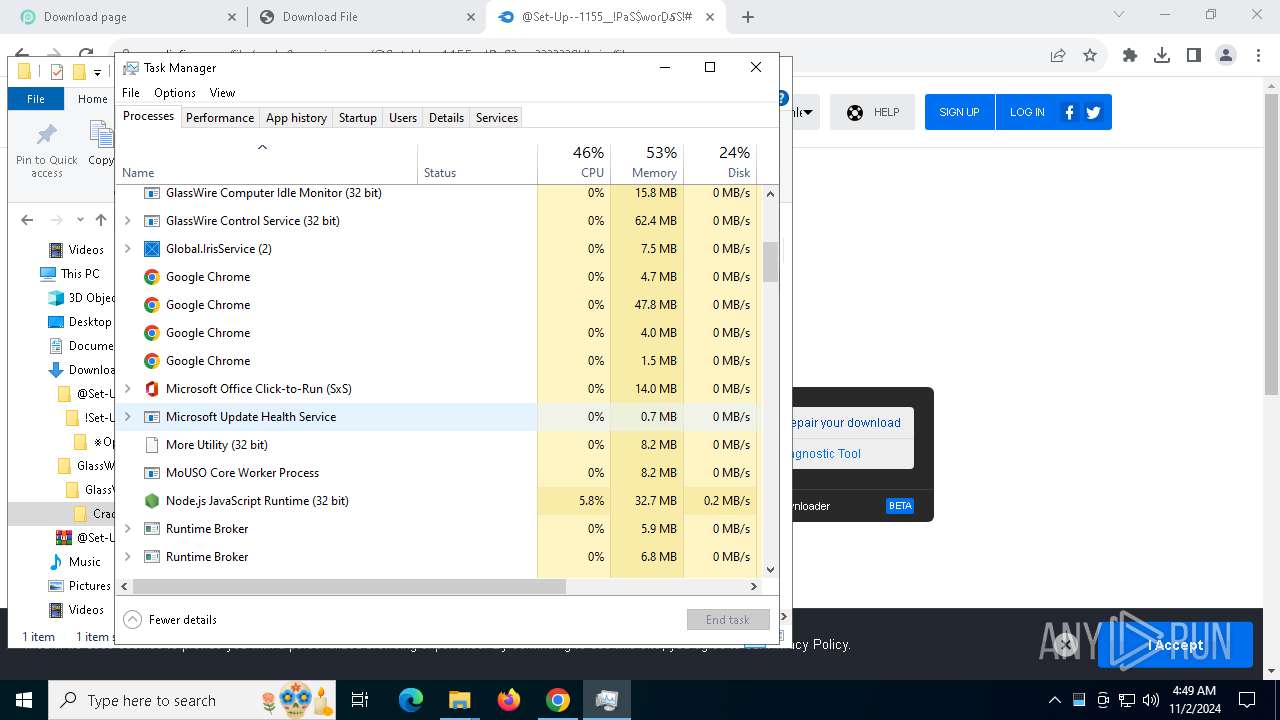
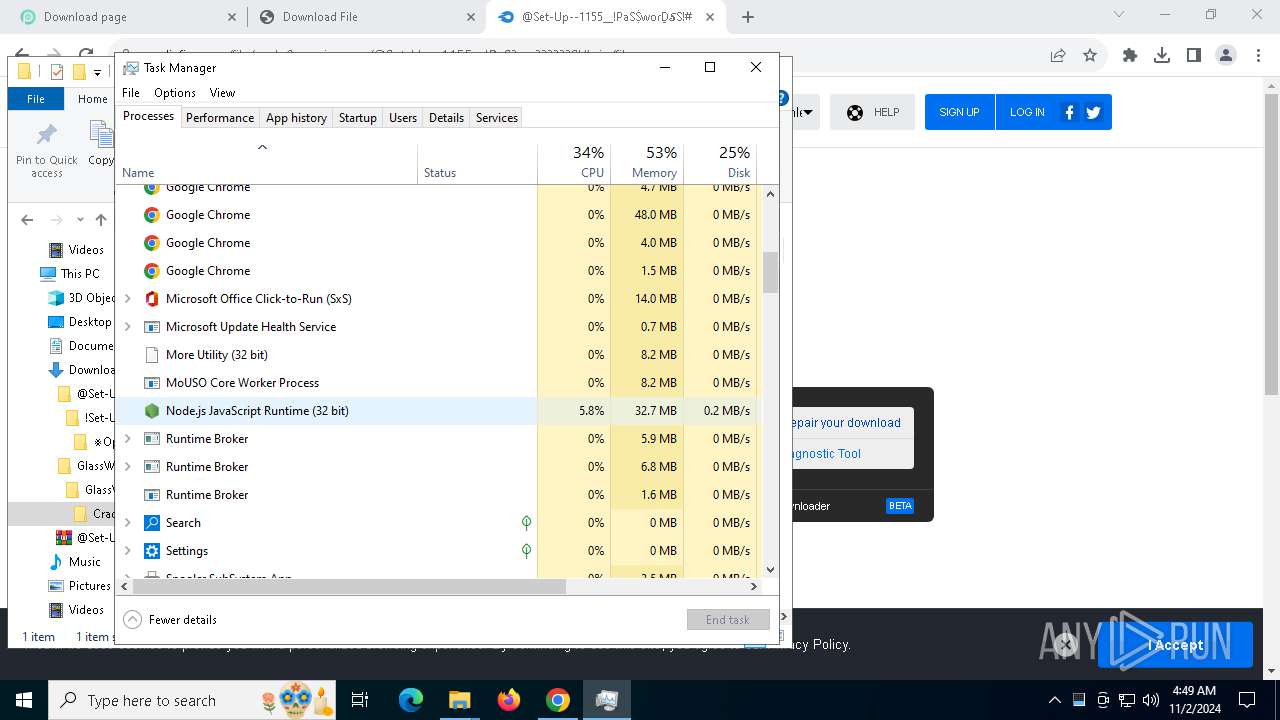
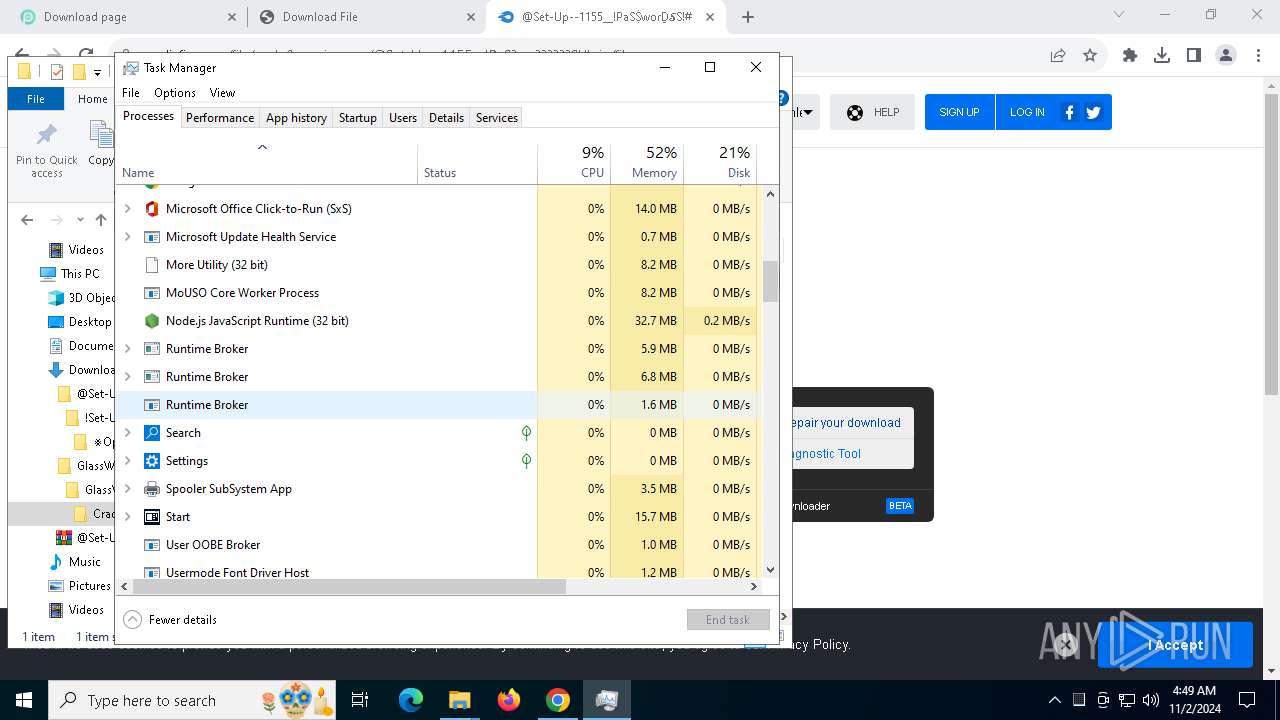
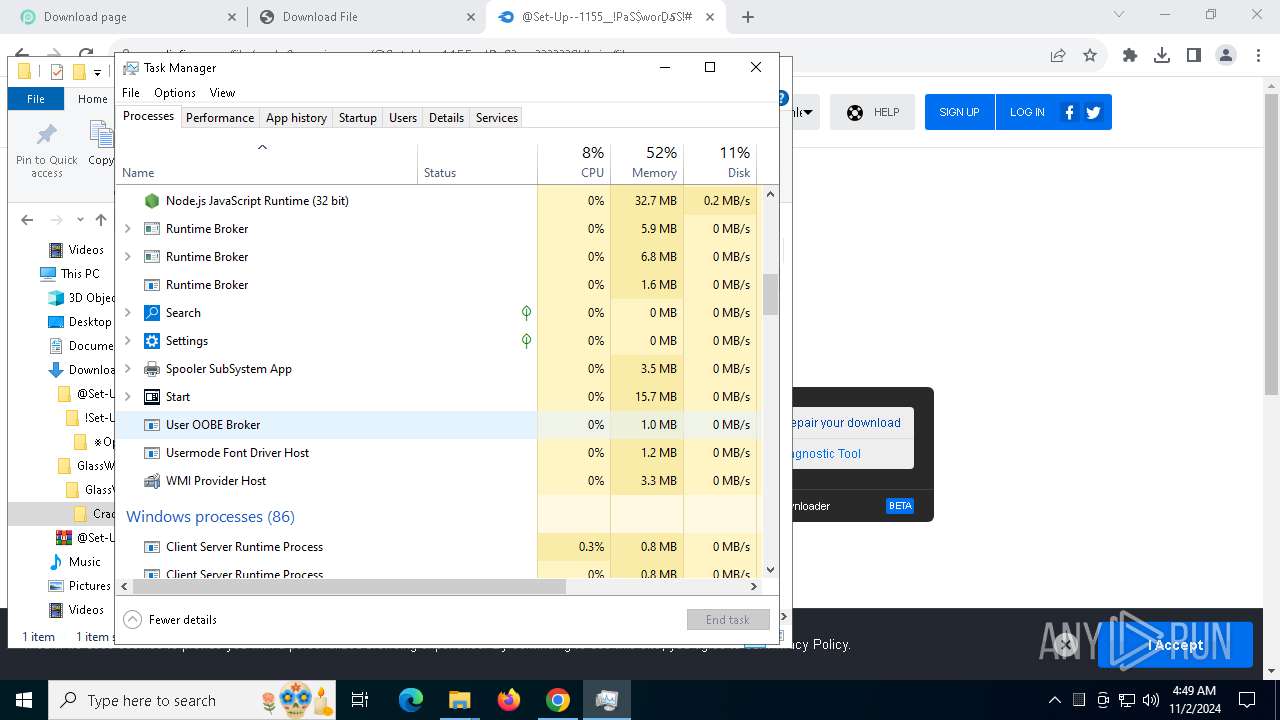
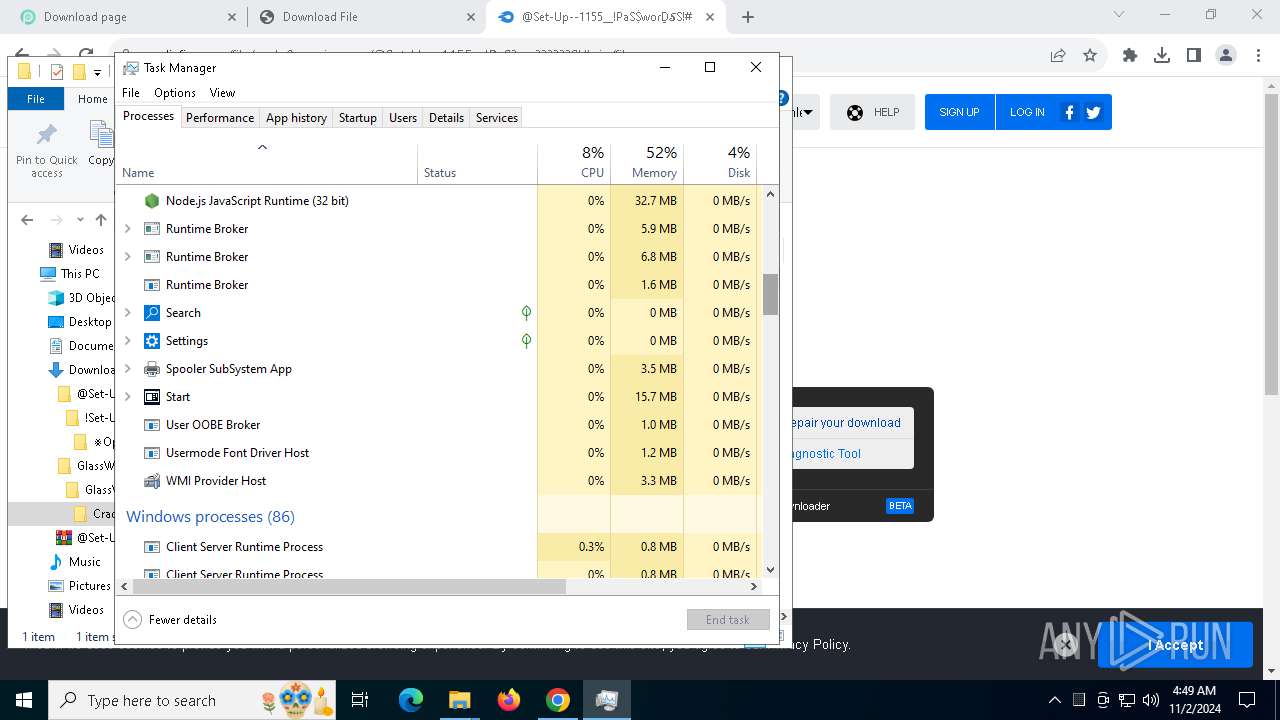
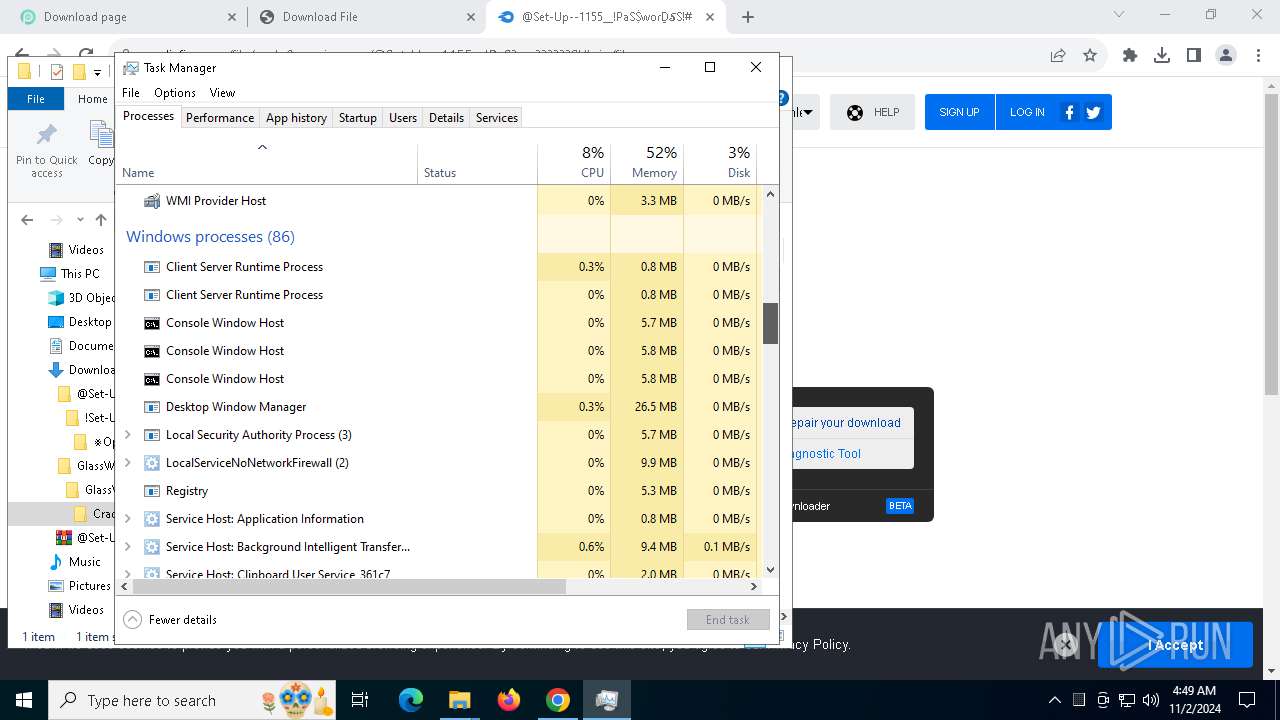
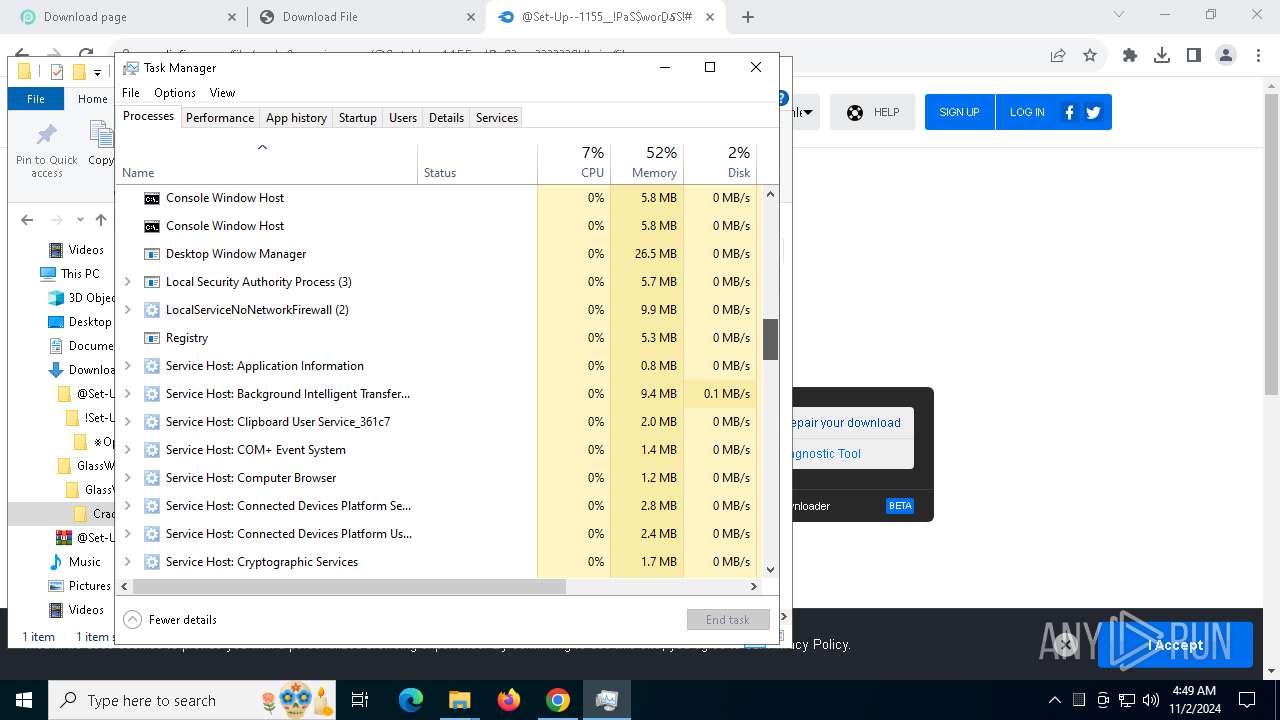
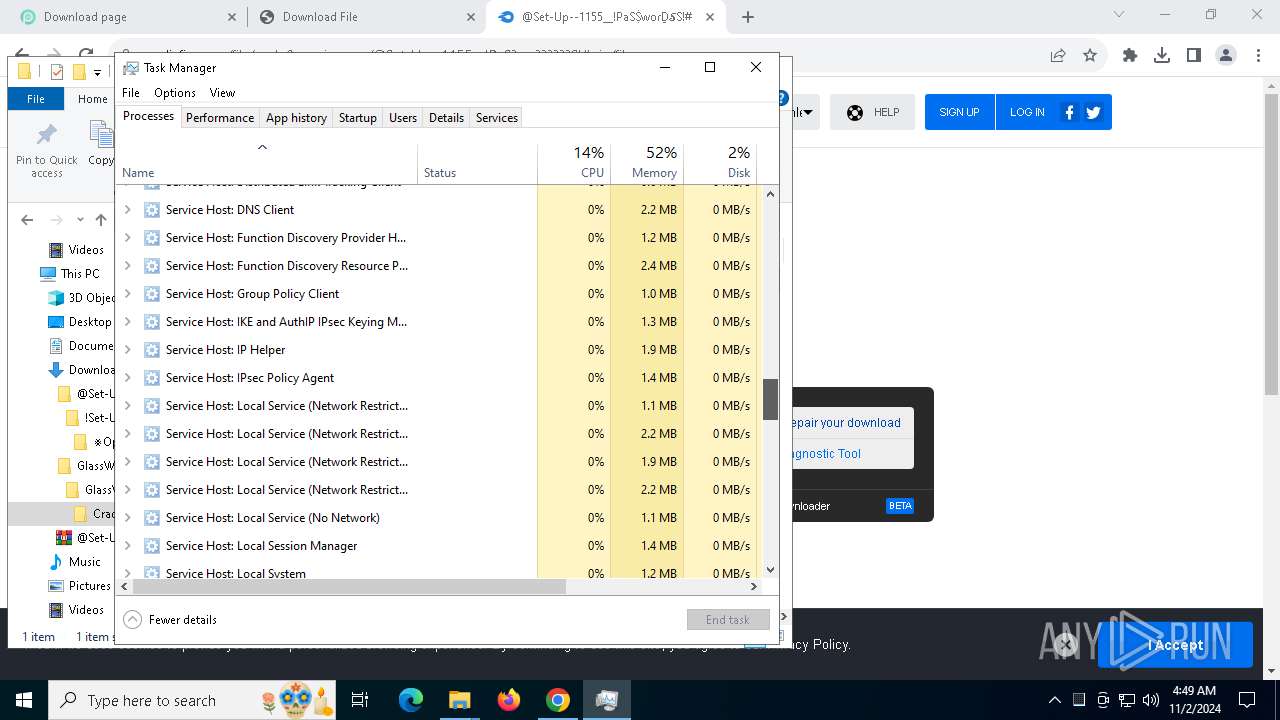
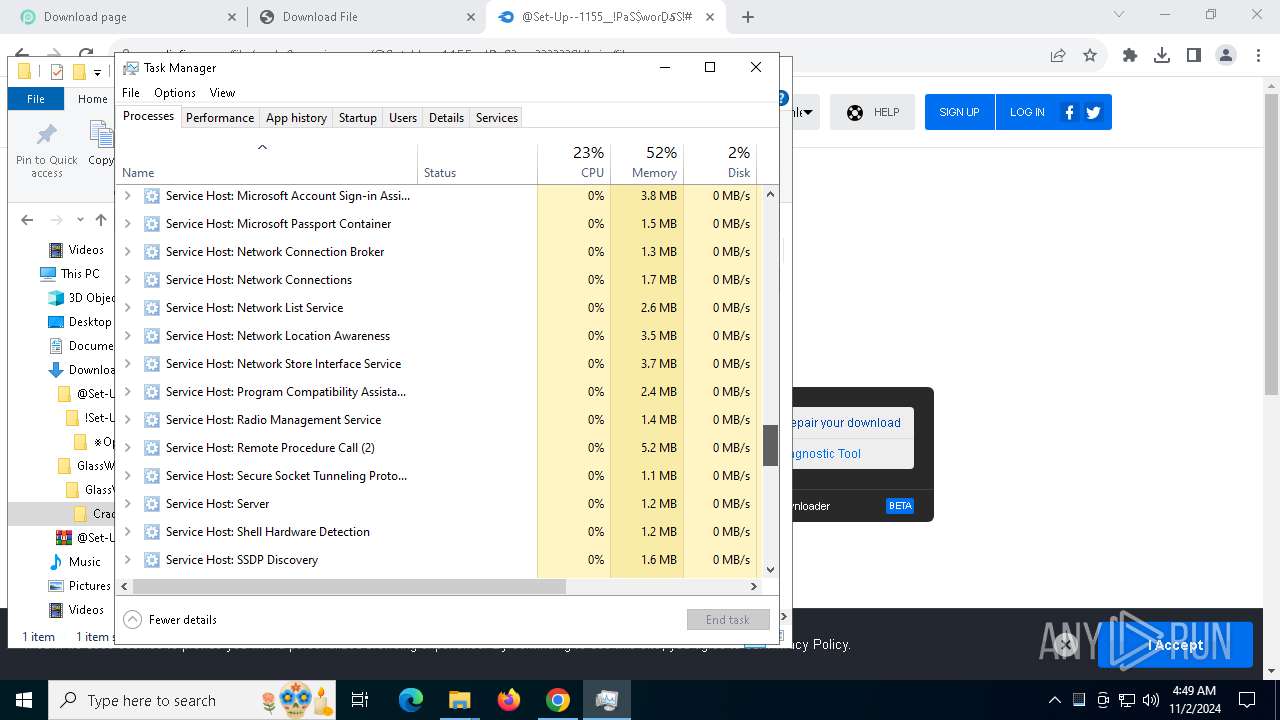
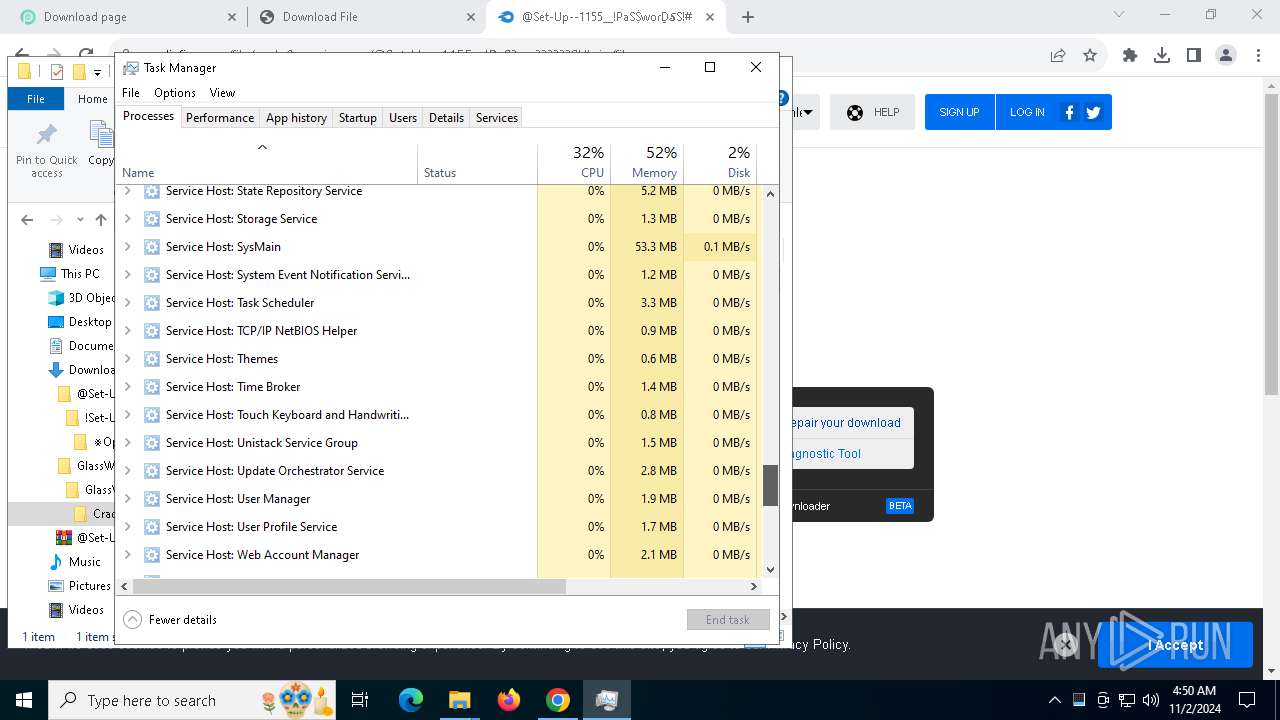
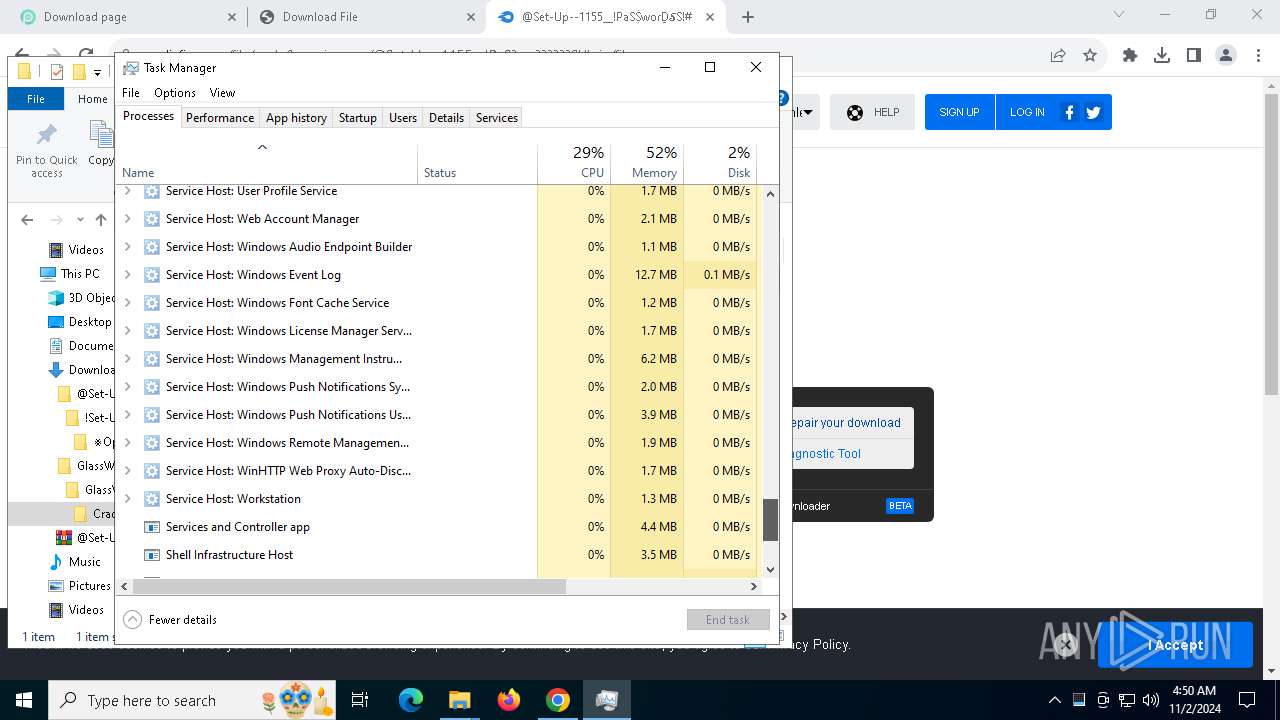
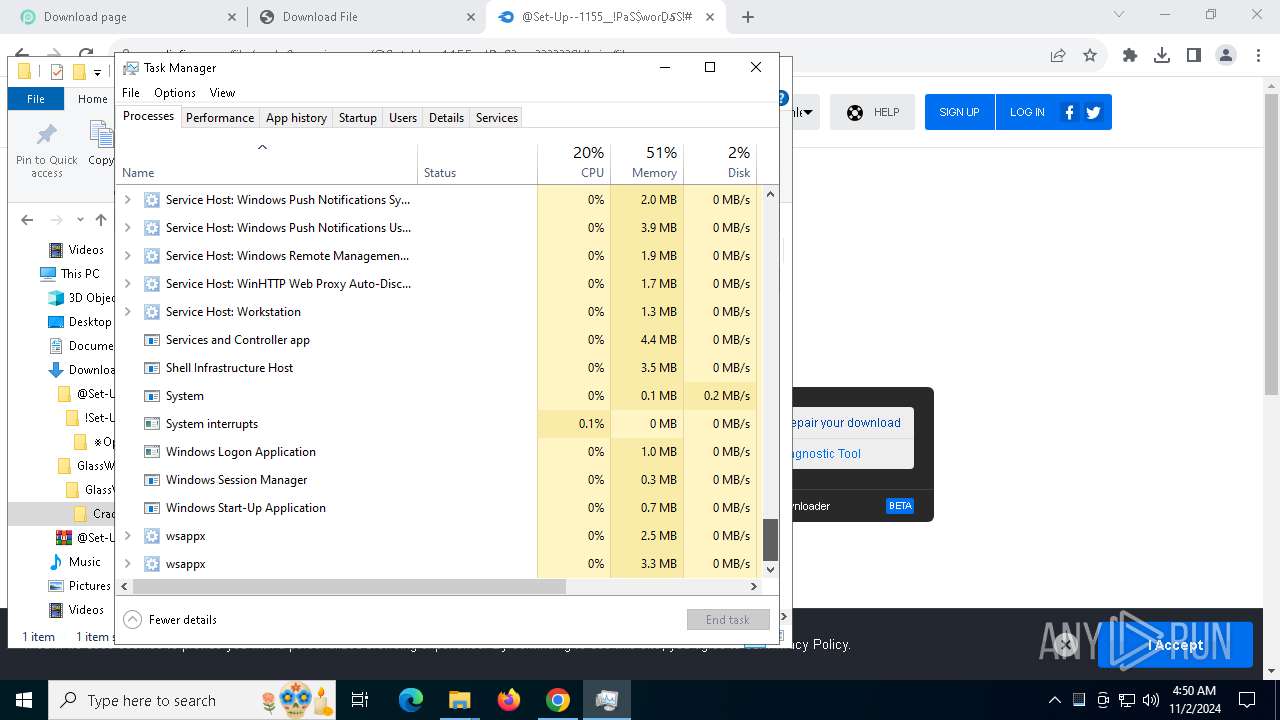
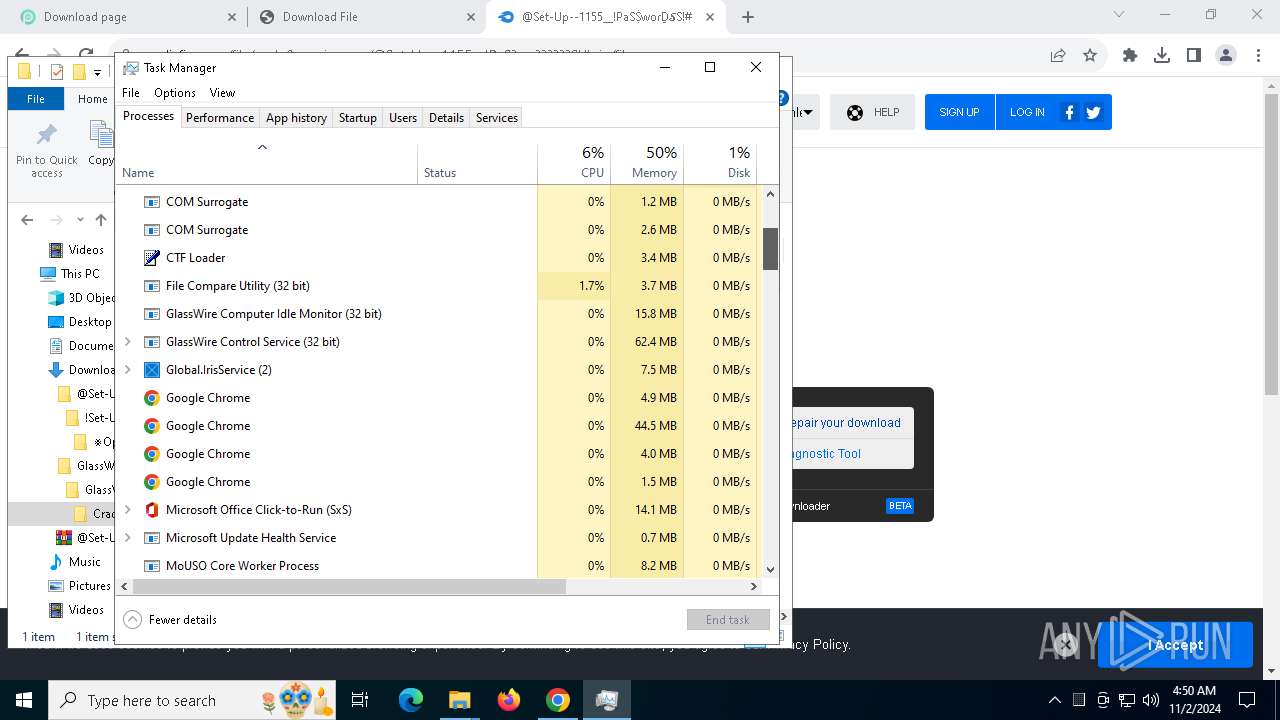
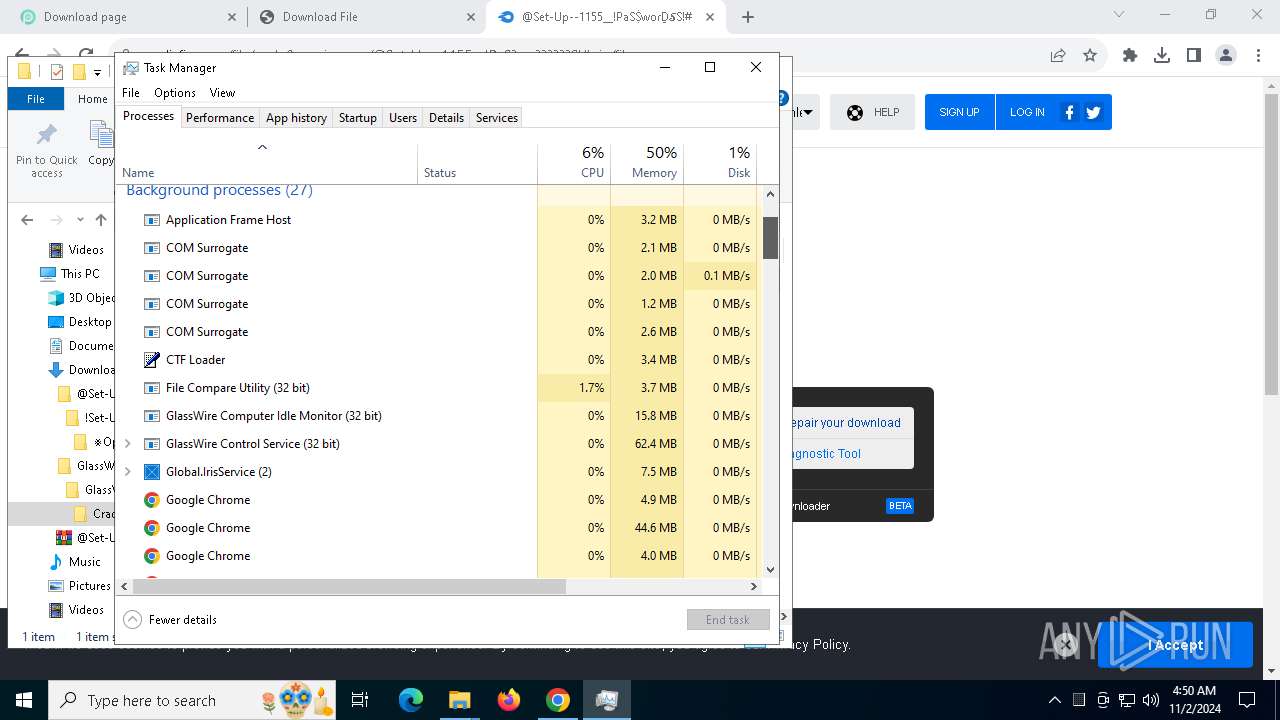
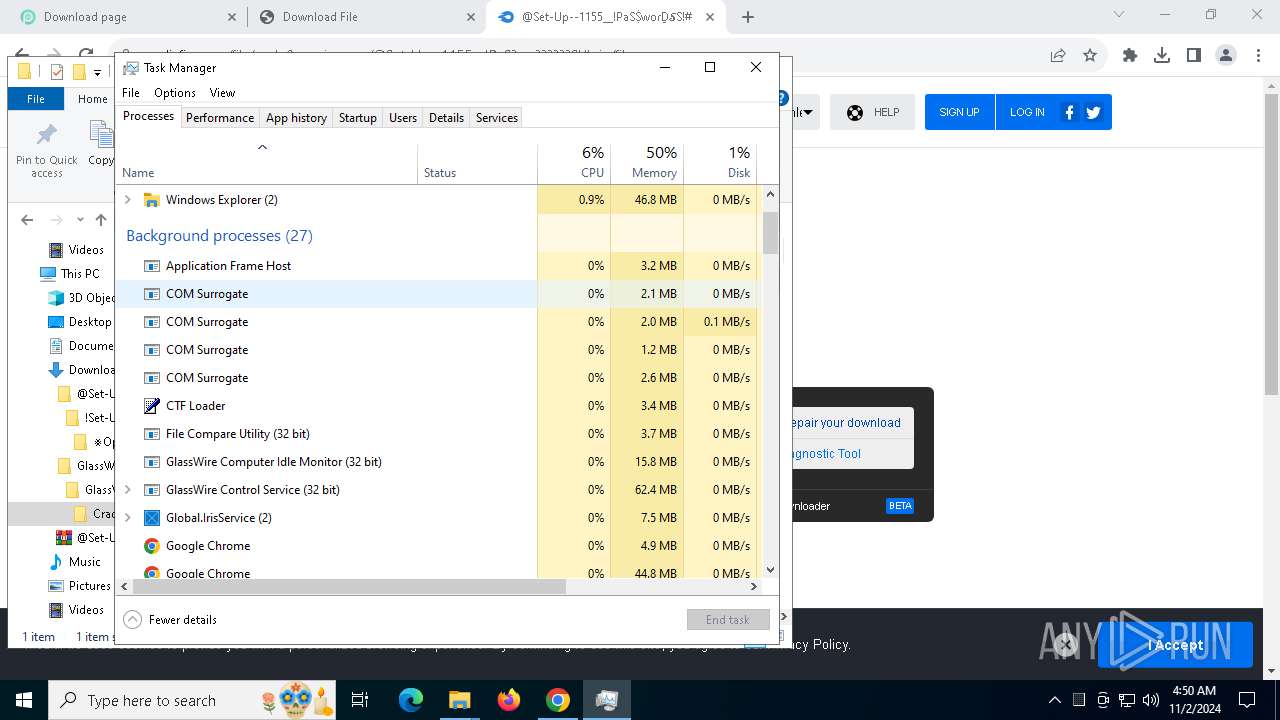
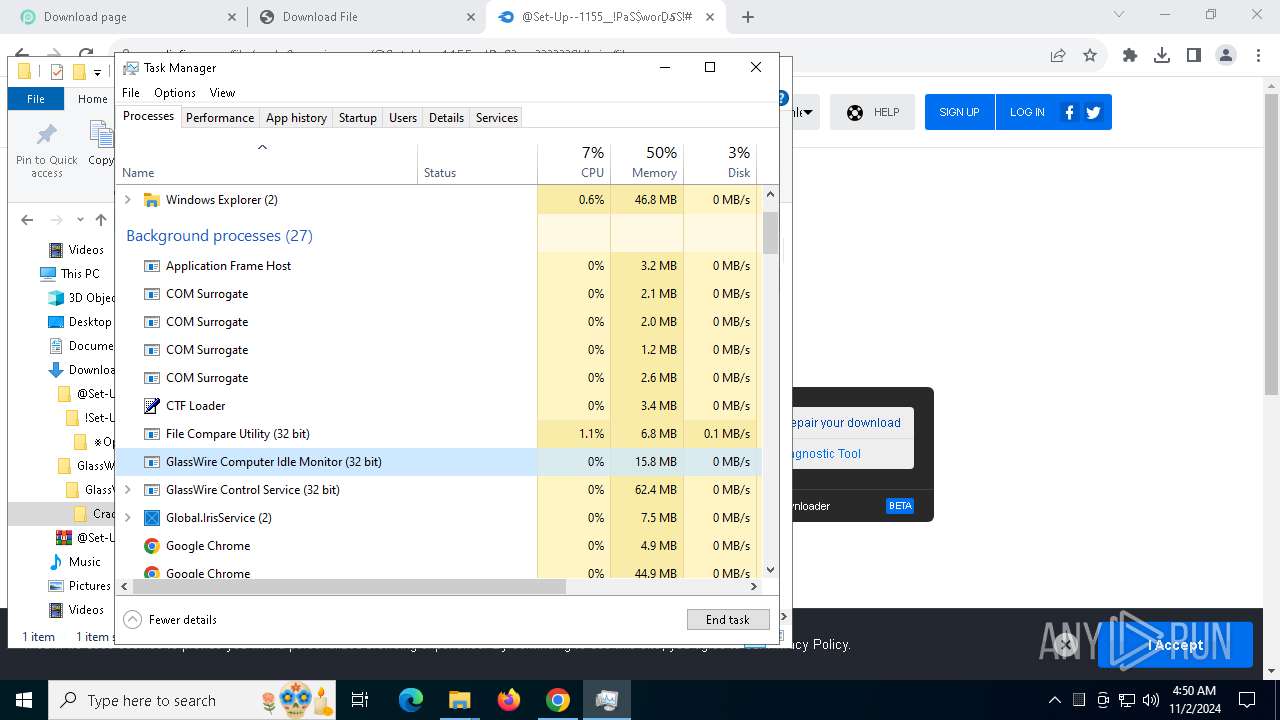
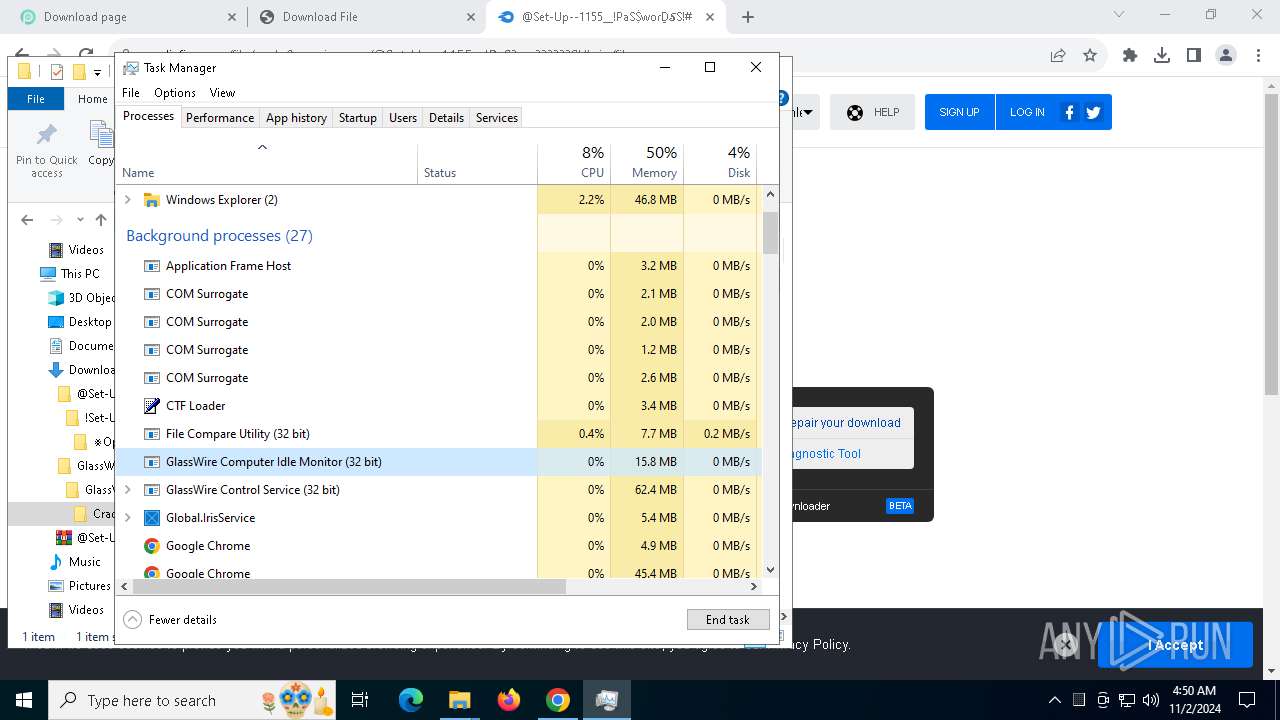
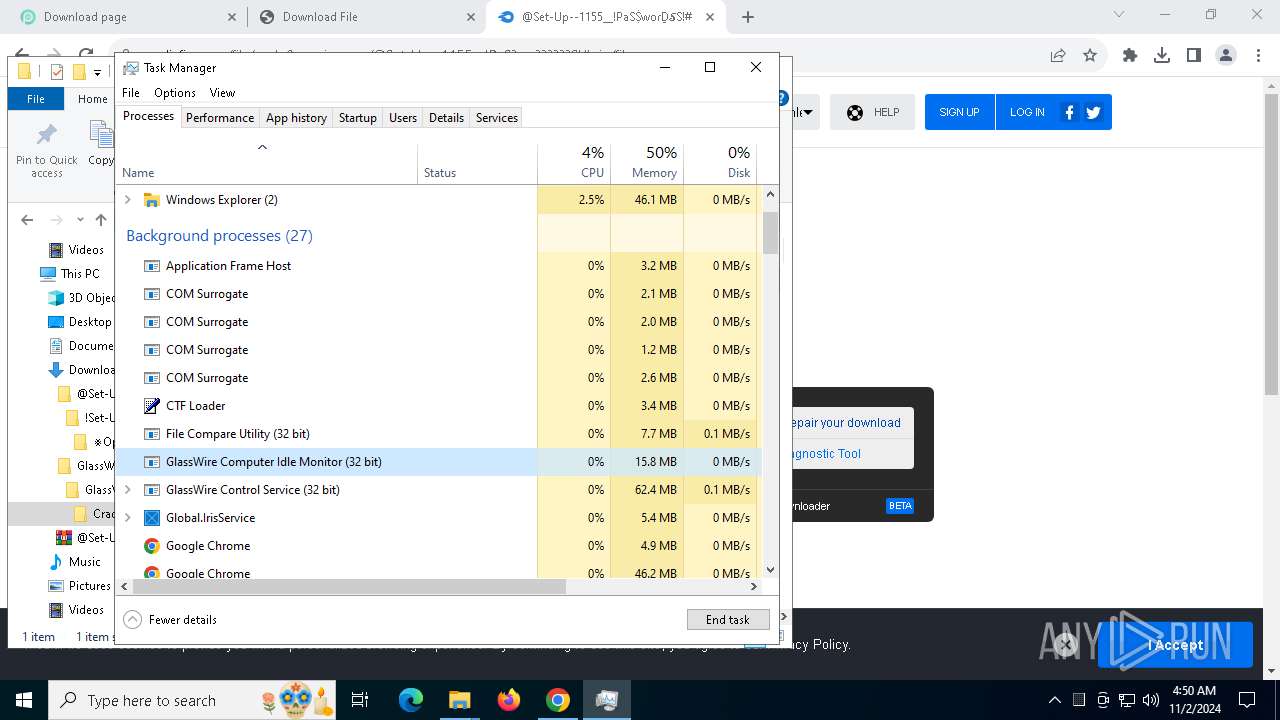
- Taskmgr.exe (PID: 7880)
- Taskmgr.exe (PID: 6668)
- WinRAR.exe (PID: 6792)
- Setup.exe (PID: 8152)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7800)
- chrome.exe (PID: 7396)
- WinRAR.exe (PID: 6792)
Application launched itself
- chrome.exe (PID: 5328)
Themida protector has been detected
- GlassWireSetup_3.3.678.exe (PID: 4352)
- GWCtlSrv.exe (PID: 6496)
- GWIdlMon.exe (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
230
Monitored processes
80
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5328 --field-trial-handle=1900,i,9565522037400538390,4009902699980203155,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 860 | C:\Users\admin\AppData\Roaming\Local\IRGQFYSAZDPSEYIFVHSO\nc.exe | C:\Users\admin\AppData\Roaming\Local\IRGQFYSAZDPSEYIFVHSO\nc.exe | — | Setup.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.3810.9 | |||||||||||||||
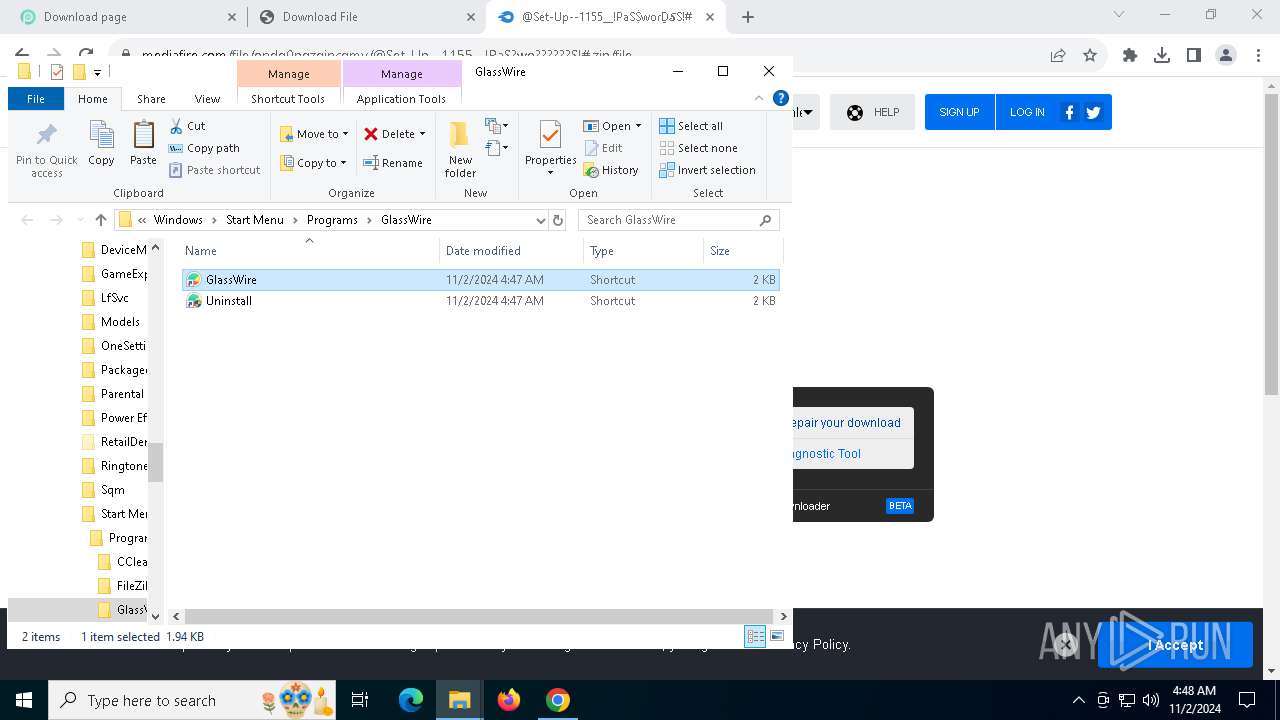
| 916 | "C:\Program Files (x86)\GlassWire/GWIdlMon.exe" --auth-cookie=3712385107 --server-port=20000 | C:\Program Files (x86)\GlassWire\GWIdlMon.exe | GWCtlSrv.exe | ||||||||||||
User: admin Company: GlassWire Integrity Level: MEDIUM Description: GlassWire Computer Idle Monitor Exit code: 1 Version: 3.3.678.0 | |||||||||||||||
| 1084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | wevtutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\WINDOWS\system32\wevtutil.exe" im "C:\Users\admin\AppData\Local\Temp\nsfEB30.tmp\eventlog.man" /rf:"C:\Program Files (x86)\GlassWire\GWEventLog.dll" /mf:"C:\Program Files (x86)\GlassWire\GWEventLog.dll" /fromwow64 | C:\Windows\System32\wevtutil.exe | — | wevtutil.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Eventing Command Line Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
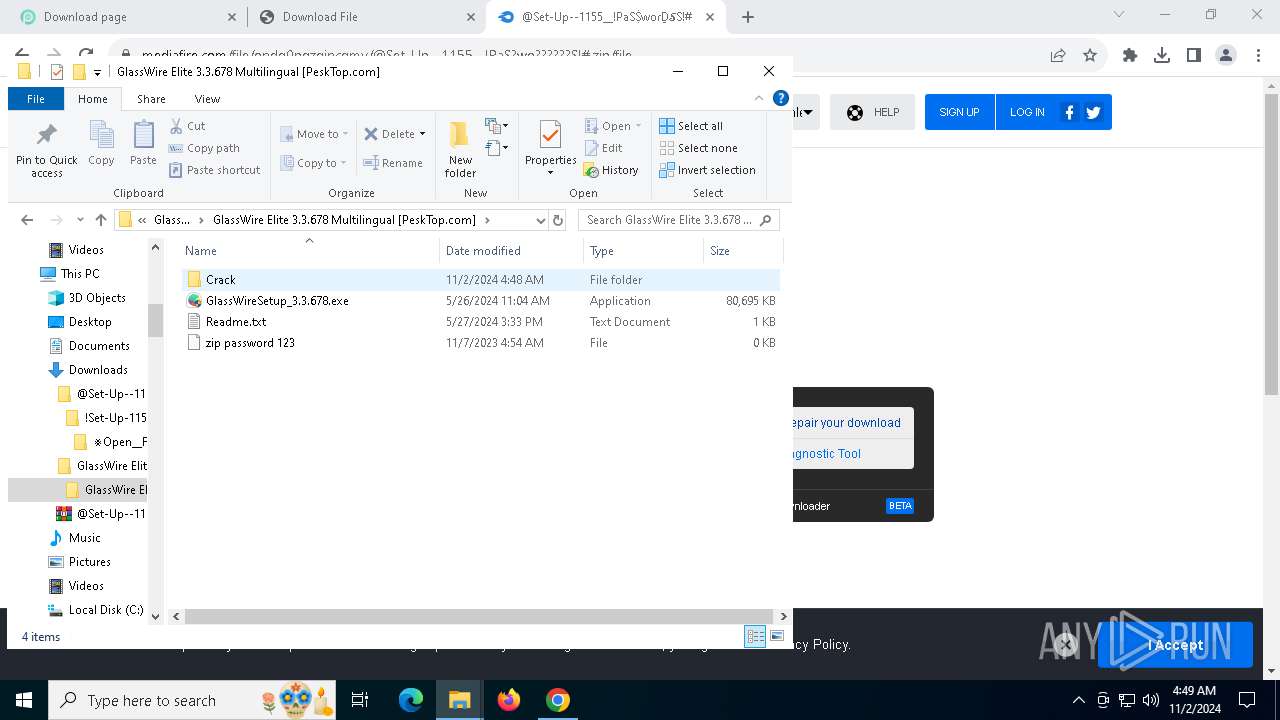
| 1344 | "C:\Users\admin\Downloads\GlassWire Elite 3.3.678 Multilingual [PeskTop.com]\GlassWire Elite 3.3.678 Multilingual [PeskTop.com]\GlassWireSetup_3.3.678.exe" | C:\Users\admin\Downloads\GlassWire Elite 3.3.678 Multilingual [PeskTop.com]\GlassWire Elite 3.3.678 Multilingual [PeskTop.com]\GlassWireSetup_3.3.678.exe | — | explorer.exe | |||||||||||
User: admin Company: GlassWire Integrity Level: MEDIUM Description: GlassWire Setup Exit code: 3221226540 Version: 3,3,678,0 Modules
| |||||||||||||||
| 1376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5740 --field-trial-handle=1900,i,9565522037400538390,4009902699980203155,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
Total events
23 805
Read events
23 630
Write events
127
Delete events
48
Modification events
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (5328) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1F |
Value: 1 | |||
| (PID) Process: | (7980) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000009408325E22CDB01 | |||
Executable files
77
Suspicious files
250
Text files
479
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF8c06a.TMP | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8c06a.TMP | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8c07a.TMP | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8c07a.TMP | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8c07a.TMP | — | |
MD5:— | SHA256:— | |||
| 5328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
146
DNS requests
136
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | BR | binary | 973 b | whitelisted |
6944 | svchost.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
7448 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | — | — | whitelisted |
1204 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
7652 | SIHClient.exe | GET | 200 | 23.32.185.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | BR | binary | 408 b | whitelisted |
7448 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | binary | 1.09 Kb | whitelisted |
7448 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | binary | 1.94 Kb | whitelisted |
7448 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | binary | 4.00 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1428 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5328 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6716 | chrome.exe | 172.67.69.186:443 | pesktop.com | CLOUDFLARENET | US | suspicious |
6716 | chrome.exe | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pesktop.com |
| unknown |
accounts.google.com |
| whitelisted |
analytics.pesktop.com |
| unknown |
yvjskep4.click |
| unknown |
static.cloudflareinsights.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6716 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6716 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
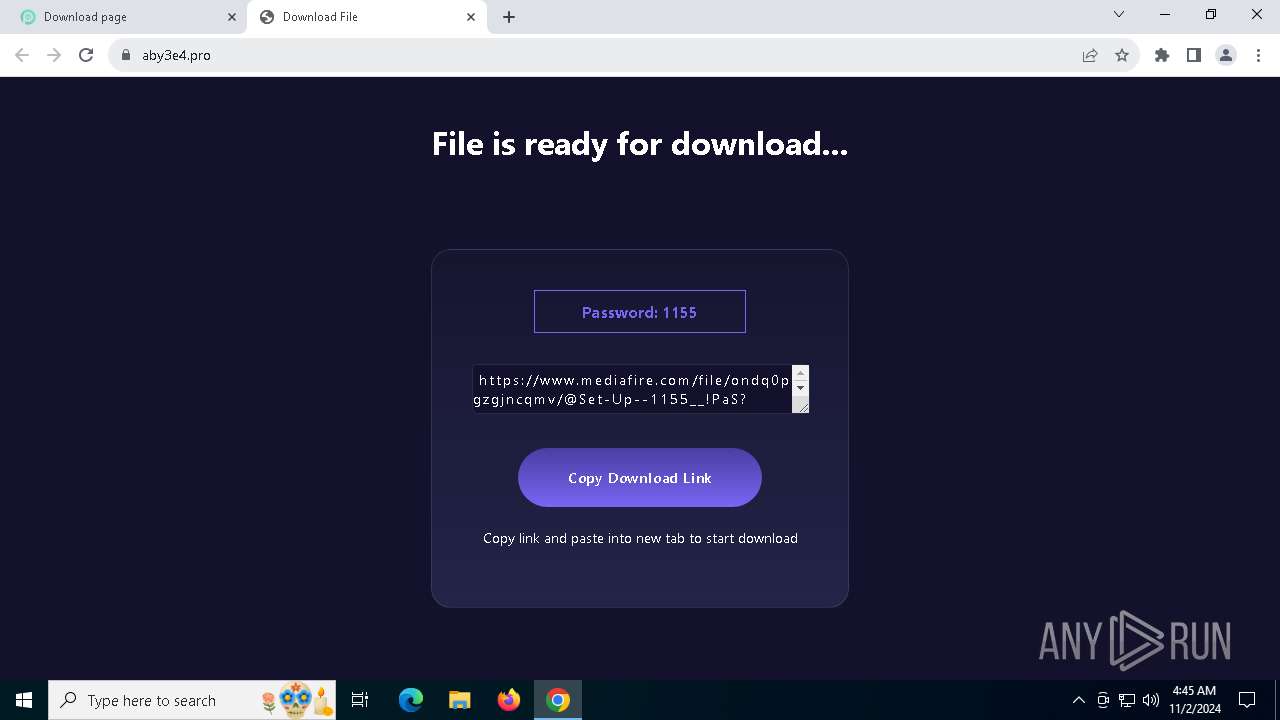
6716 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
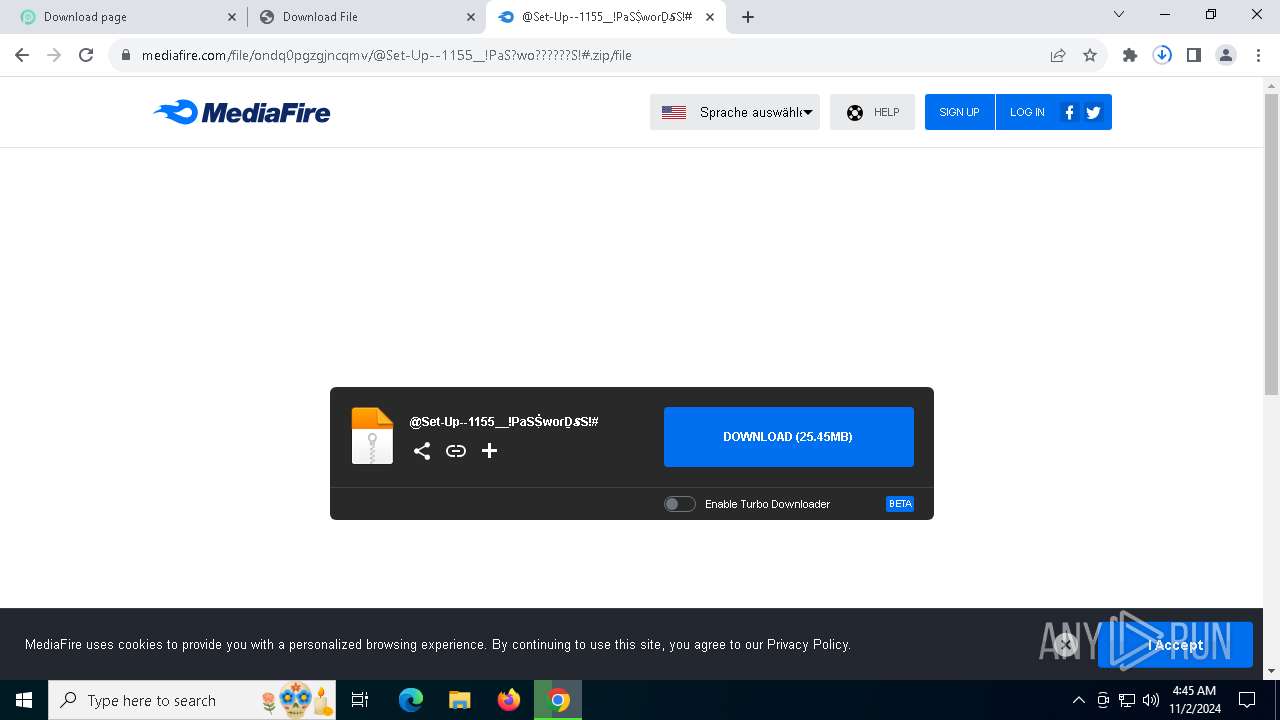
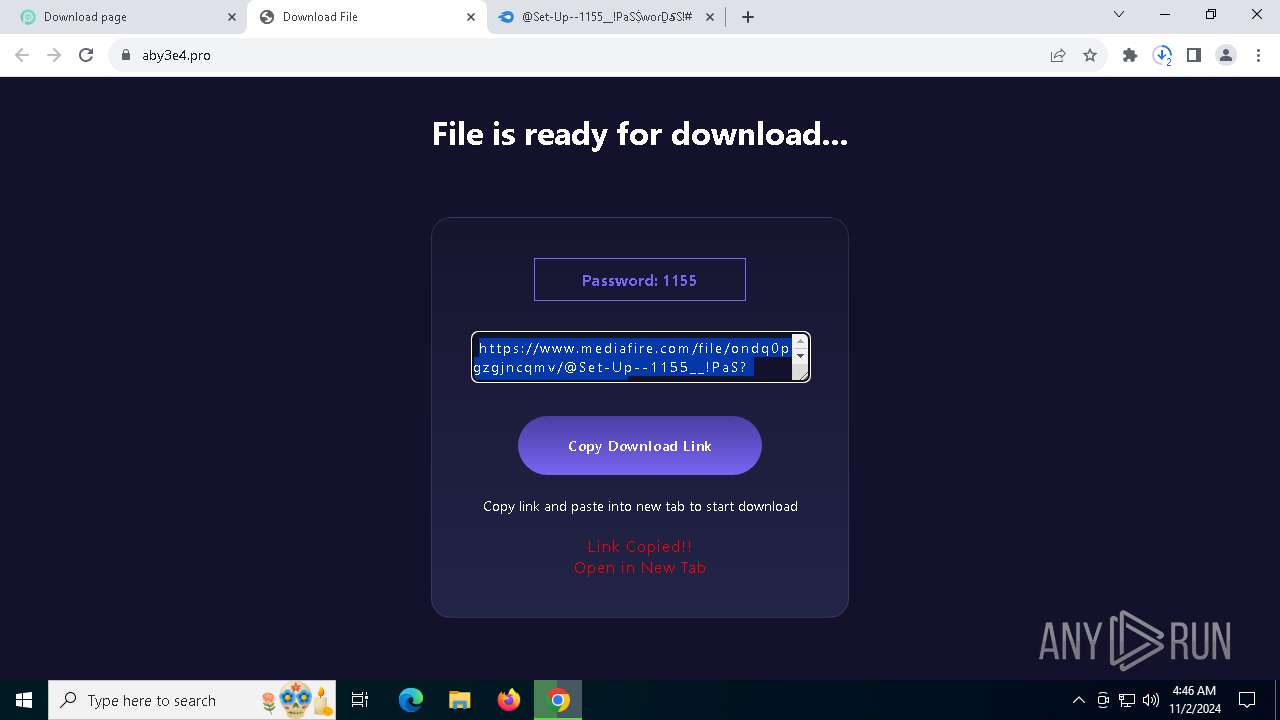
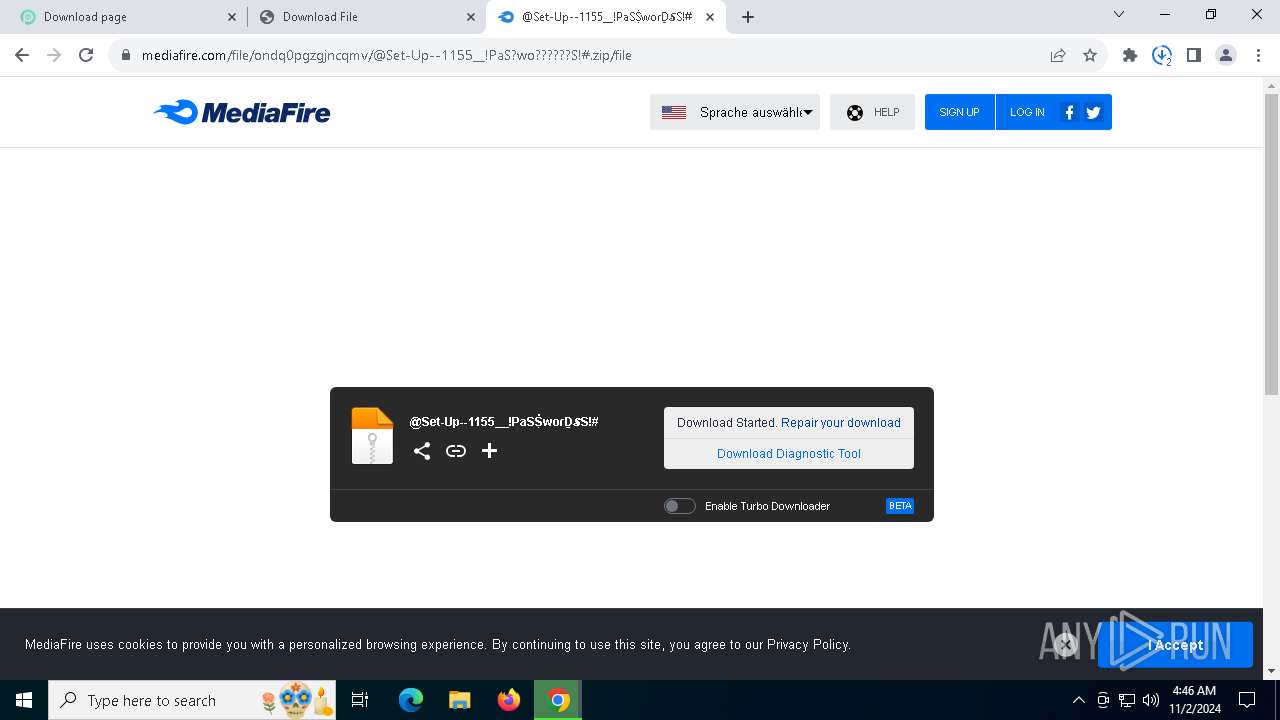
6716 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6716 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6716 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6716 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6716 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6716 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (creative-habitat .shop) |