| File name: | Setup.exe |
| Full analysis: | https://app.any.run/tasks/0d127f0b-a620-43f0-8fcb-67afbfa92c2f |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | November 01, 2024, 20:12:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 12 sections |
| MD5: | 59D5751D980FAE8A556E53A4282C69ED |
| SHA1: | C10BFFAF031D58E0DC895B659BC5B2D06DE12A17 |
| SHA256: | 8F1454E8928042BF6EEADD9FFDB524A27DD9CFB10208090C02F97D5768237D53 |
| SSDEEP: | 98304:SLsb5ssVi/yyrJdOJzvbJXk2d7TzhDa2/9LbW80/WZqn1XV0neai4M3hk4t56udK:1IjV3NY |
MALICIOUS
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
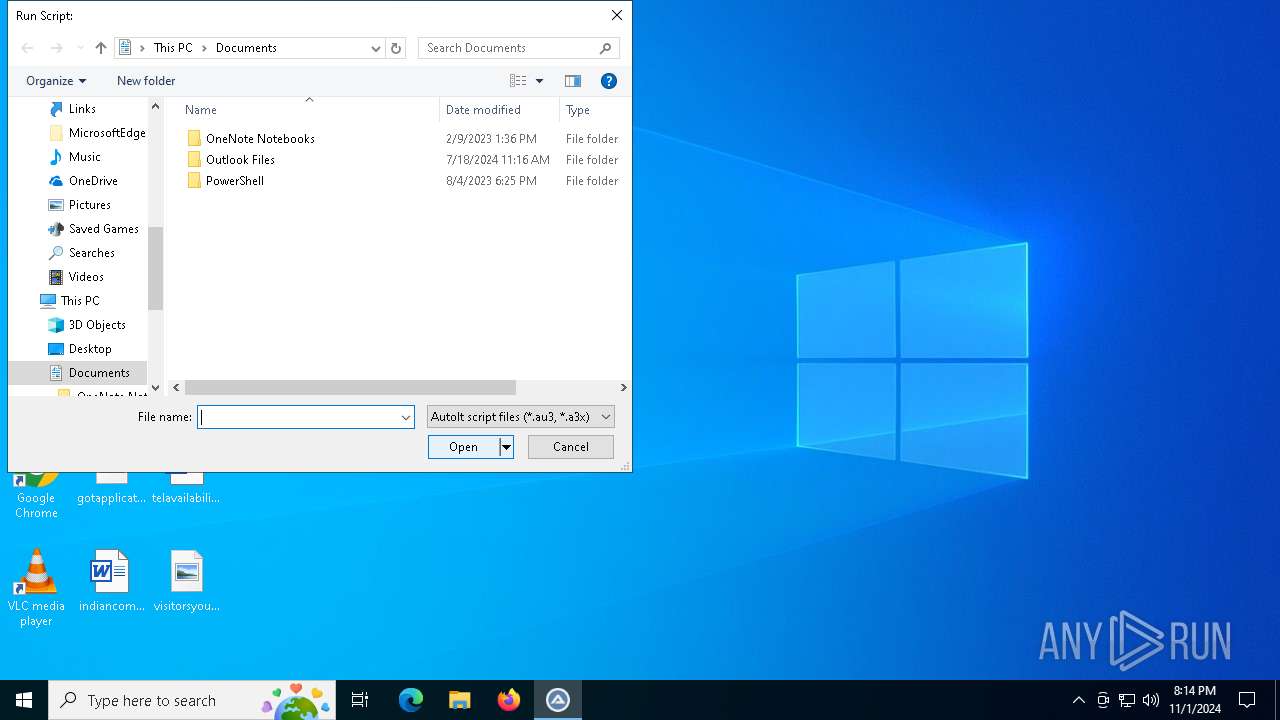
Bypass execution policy to execute commands
- powershell.exe (PID: 5920)
Changes powershell execution policy (Bypass)
- AutoIt3.exe (PID: 6168)
Stealers network behavior
- svchost.exe (PID: 2172)
Connects to the CnC server
- explorer.exe (PID: 7016)
AMADEY has been detected (SURICATA)
- explorer.exe (PID: 7016)
SUSPICIOUS
Checks for Java to be installed
- nc.exe (PID: 6508)
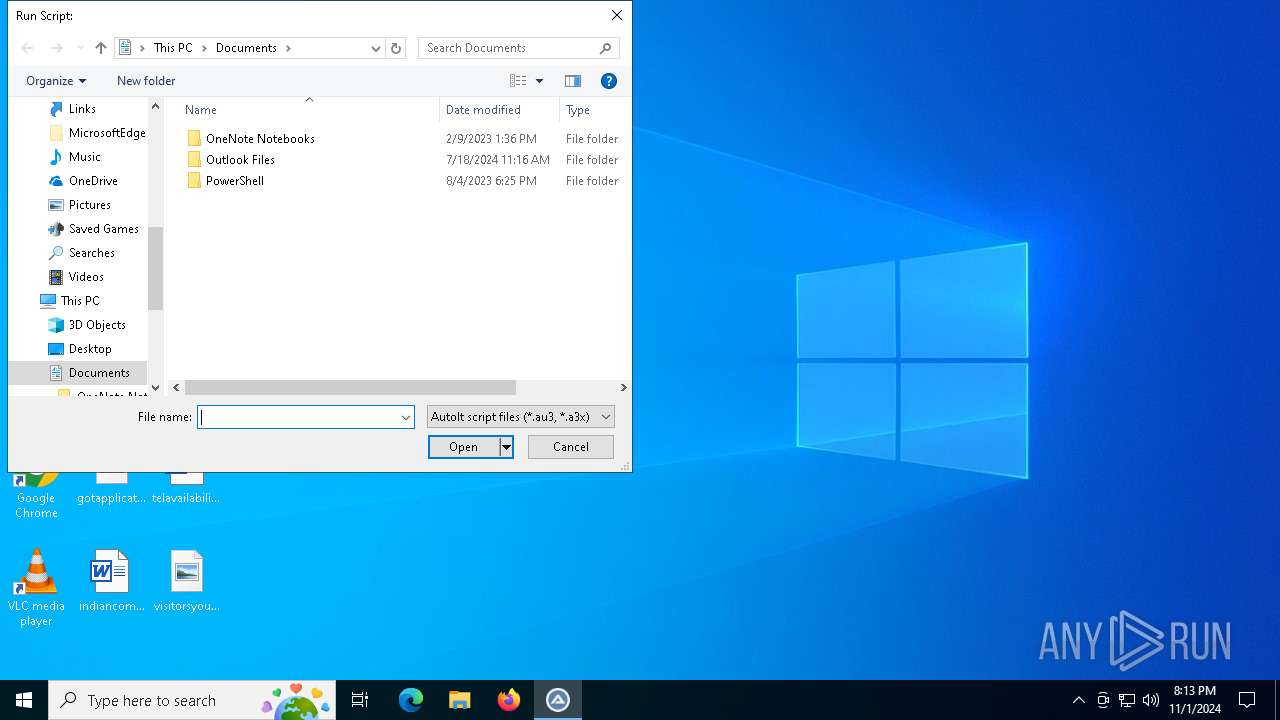
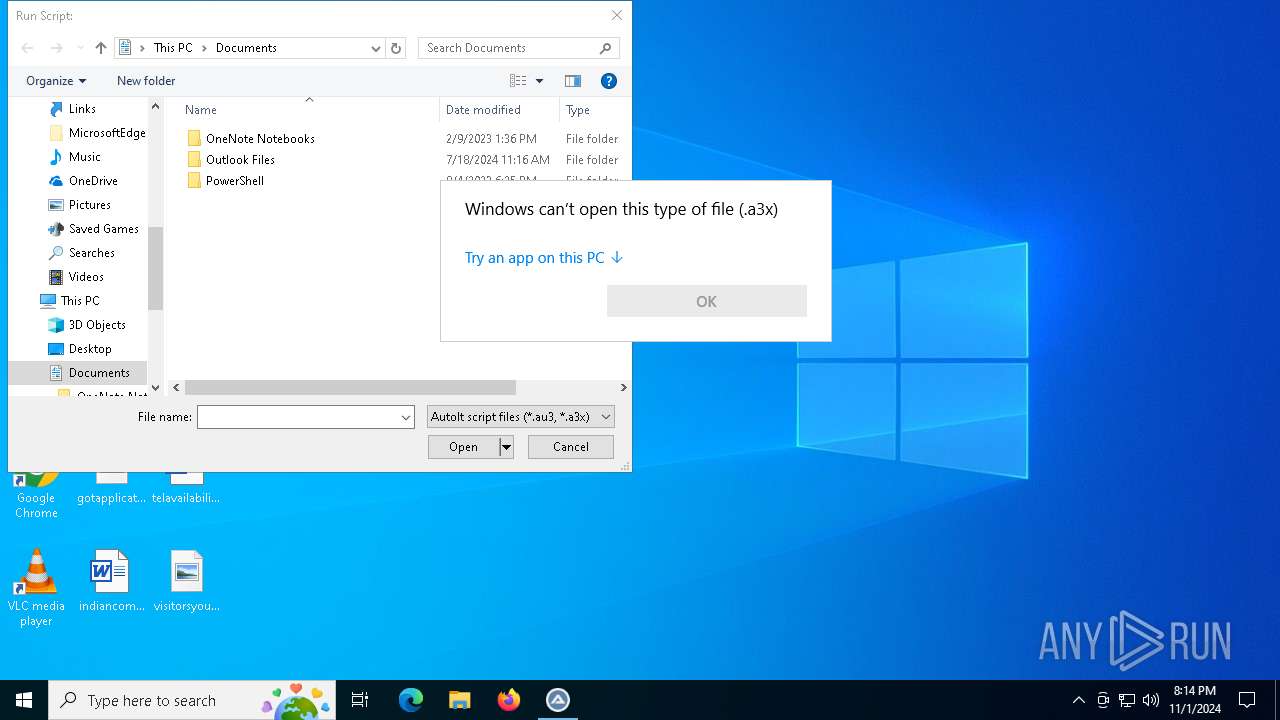
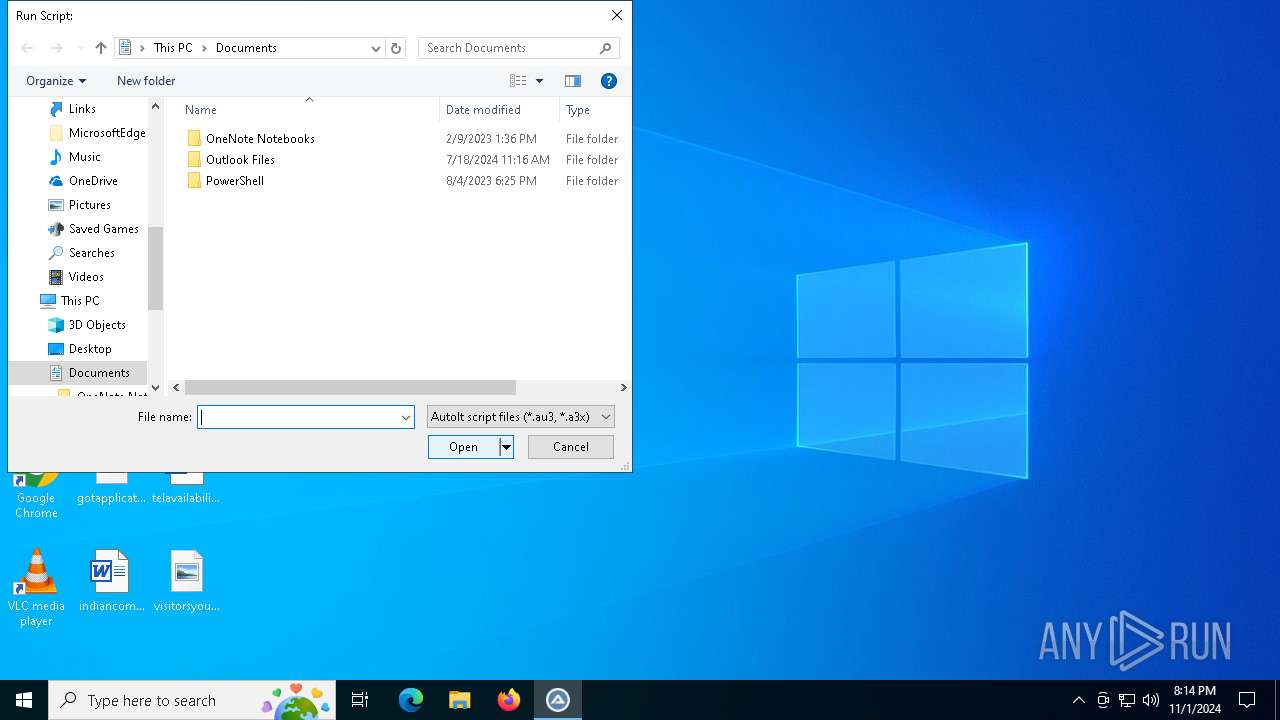
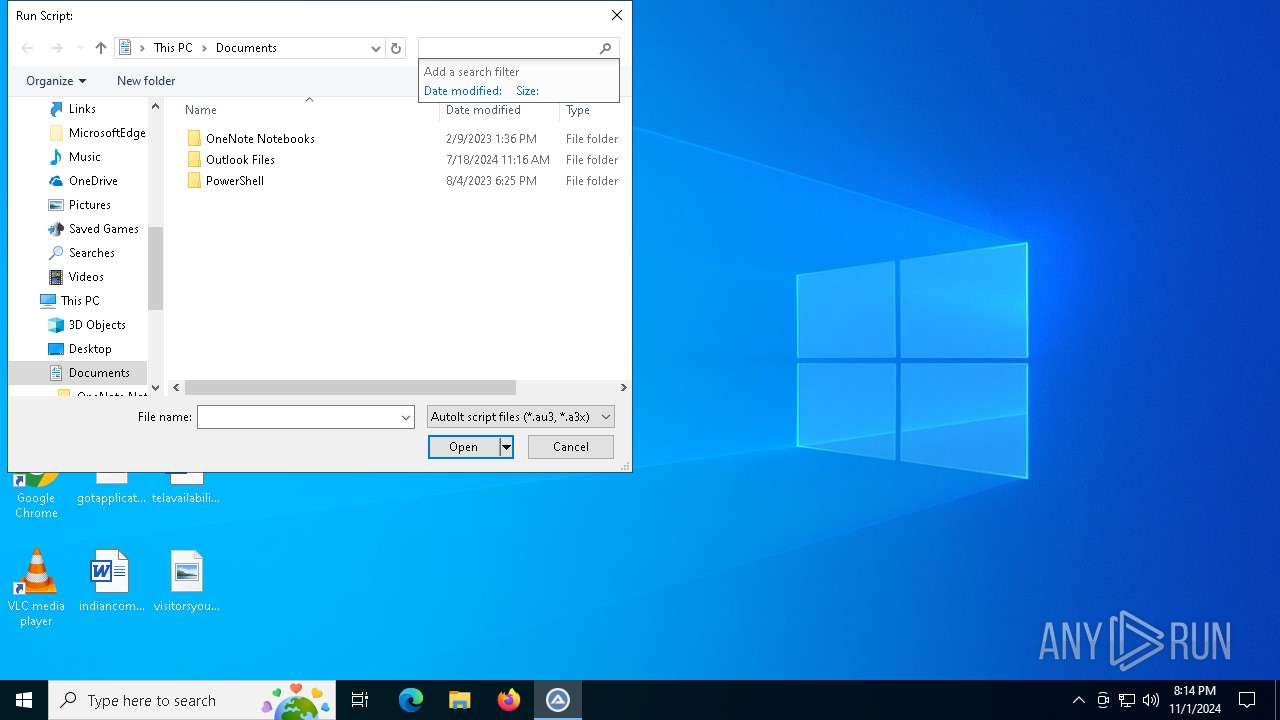
Starts application with an unusual extension
- Setup.exe (PID: 6548)
Executable content was dropped or overwritten
- Setup.exe (PID: 6548)
- AutoIt3.exe (PID: 6168)
- more.com (PID: 7088)
- AutoIt3.exe (PID: 5792)
There is functionality for communication over UDP network (YARA)
- Setup.exe (PID: 6548)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2172)
- explorer.exe (PID: 7016)
Node.exe was dropped
- AutoIt3.exe (PID: 6168)
The process executes Powershell scripts
- AutoIt3.exe (PID: 6168)
Starts POWERSHELL.EXE for commands execution
- AutoIt3.exe (PID: 6168)
Starts itself from another location
- AutoIt3.exe (PID: 6168)
Connects to unusual port
- MicrosoftEdgeUpdateCore.exe (PID: 2364)
INFO
Checks supported languages
- Setup.exe (PID: 6548)
- nc.exe (PID: 6508)
Creates files or folders in the user directory
- Setup.exe (PID: 6548)
Create files in a temporary directory
- Setup.exe (PID: 6548)
- nc.exe (PID: 6508)
Creates files in the program directory
- nc.exe (PID: 6508)
Manual execution by a user
- OpenWith.exe (PID: 6636)
- AutoIt3.exe (PID: 6340)
Reads the computer name
- Setup.exe (PID: 6548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:03:18 14:54:00+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 7553536 |
| InitializedDataSize: | 4730368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x734e6c |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.7.775 |
| ProductVersionNumber: | 5.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Jan Fiala |
| FileDescription: | Text editor |
| FileVersion: | 5.0.7.775 |
| InternalName: | PSPad editor |
| LegalCopyright: | Jan Fiala (2001) |
| LegalTrademarks: | Jan Fiala (2001) |
| OriginalFileName: | PSPad.exe |
| ProductName: | PSPad editor |
| ProductVersion: | 5 |
| Comments: | General freeware text editor |
| ProgramID: | com.embarcadero.PSPad |
Total processes
142
Monitored processes
18
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1396 | C:\WINDOWS\SysWOW64\comp.exe | C:\Windows\SysWOW64\comp.exe | — | SOMBUCBXDNEIW603EYVR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Compare Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2364 | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | C:\Program Files (x86)\Microsoft\EdgeUpdate\1.3.185.17\MicrosoftEdgeUpdateCore.exe | AutoIt3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.185.17 Modules
| |||||||||||||||
| 4128 | "C:\Users\admin\AppData\Local\Temp\SOMBUCBXDNEIW603EYVR.exe" | C:\Users\admin\AppData\Local\Temp\SOMBUCBXDNEIW603EYVR.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 1 Version: 18.13.0 Modules
| |||||||||||||||
| 5584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | comp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5792 | "C:\Users\admin\AppData\Local\Temp\MMMUTI\AutoIt3.exe" "C:\Users\admin\AppData\Local\Temp\MMMUTI\Flaring.a3x" | C:\Users\admin\AppData\Local\Temp\MMMUTI\AutoIt3.exe | AutoIt3.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 1 Modules
| |||||||||||||||
| 5920 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | icacls.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5920 | powershell -exec bypass -f "C:\Users\admin\AppData\Local\Temp\XGRPLO5OPDSUC4HOB5G.ps1" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | AutoIt3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5948 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | more.com | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6044 | C:\WINDOWS\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | nc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 224
Read events
16 202
Write events
22
Delete events
0
Modification events
| (PID) Process: | (6548) Setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\PSPad |
| Operation: | write | Name: | Ready5 |
Value: 0 | |||
| (PID) Process: | (5792) AutoIt3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | afbkfee |
Value: "C:\keadbfa\AutoIt3.exe" C:\keadbfa\afbkfee.a3x | |||
| (PID) Process: | (6340) AutoIt3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (6340) AutoIt3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0400000000000000030000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (6340) AutoIt3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 040000000000000005000000020000000100000003000000FFFFFFFF | |||
| (PID) Process: | (6340) AutoIt3.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\119\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Documents | |||
| (PID) Process: | (6340) AutoIt3.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 96 | |||
| (PID) Process: | (7016) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7016) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7016) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
5
Suspicious files
4
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7088 | more.com | C:\Users\admin\AppData\Local\Temp\dynqilhkiyqxyo | — | |
MD5:— | SHA256:— | |||
| 6168 | AutoIt3.exe | C:\Users\admin\AppData\Local\Temp\MMMUTI\Flaring.a3x | — | |
MD5:— | SHA256:— | |||
| 5792 | AutoIt3.exe | C:\keadbfa\afbkfee.a3x | — | |
MD5:— | SHA256:— | |||
| 1396 | comp.exe | C:\Users\admin\AppData\Local\Temp\bkjj | — | |
MD5:— | SHA256:— | |||
| 6548 | Setup.exe | C:\Users\admin\AppData\Local\Temp\7af05ebf | image | |
MD5:531404FDD35D8845745187F514197A0A | SHA256:3CE25C1DC8B43579E9239DC26BFB8C8E5D368636EB9F8817C5D96B03065F9A07 | |||
| 6548 | Setup.exe | C:\Users\admin\AppData\Roaming\Local\IRGQFYSAZDPSEYIFVHSO\nc.exe | executable | |
MD5:7FB44C5BCA4226D8AAB7398E836807A2 | SHA256:A64EAD73C06470BC5C84CFC231B0723D70D29FEC7D385A268BE2C590DC5EB1EF | |||
| 6548 | Setup.exe | C:\Users\admin\AppData\Local\Temp\7b23133b | binary | |
MD5:CC3D521B77887E8F1AF175FAB6987619 | SHA256:83CF24F60FC8EDFC136FA4A8BC329FF7EF609165A4F84EB244F9740FFD207279 | |||
| 6508 | nc.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:A43641AA54505E9F20EB321B692DD734 | SHA256:E4A467F61CA952D6107C8EF33B2953DEF20902720536BC45E7B9CB60DE132B9D | |||
| 1396 | comp.exe | C:\Windows\Tasks\ServiceHub Controller.job | binary | |
MD5:FCC97A36D1B6E9D24BAEFD941A1AB22B | SHA256:7526B16458F1DF82600FF0B738F98507F80D944A50004A5083C93327F3A3BA47 | |||
| 6168 | AutoIt3.exe | C:\Users\admin\AppData\Local\Temp\SOMBUCBXDNEIW603EYVR.exe | executable | |
MD5:C52C721E095A91BB0D589DD0206D5F3D | SHA256:331F38A2128E273AC865BE7C6722D4107EBF0CC77A5ABD46965492DBAD0FADF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
39
DNS requests
16
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | RUXIMICS.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7016 | explorer.exe | POST | 200 | 104.21.23.211:80 | http://moviecentral-petparade.com/g9jvjfd73/index.php | unknown | — | — | malicious |
1764 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 172.67.183.102:443 | https://proggresinvj.cyou/api | unknown | text | 17.0 Kb | malicious |
— | — | POST | 200 | 104.21.32.51:443 | https://proggresinvj.cyou/api | unknown | text | 40 b | malicious |
— | — | POST | 200 | 104.21.32.51:443 | https://proggresinvj.cyou/api | unknown | text | 2 b | malicious |
— | — | POST | 200 | 104.21.32.51:443 | https://proggresinvj.cyou/api | unknown | text | 40 b | malicious |
— | — | POST | 200 | 172.67.183.102:443 | https://proggresinvj.cyou/api | unknown | text | 40 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1764 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1764 | RUXIMICS.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1764 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
proggresinvj.cyou |
| malicious |
cdn4.creative-habitat.shop |
| unknown |
rentry.co |
| unknown |
cdn2.creative-habitat.shop |
| unknown |
steamcommunity.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer Related Activity |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer CnC Host Checkin |
— | — | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer Related Activity M2 |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer CnC Host Checkin |
— | — | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Exfiltration |
— | — | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Exfiltration |
— | — | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
— | — | A Network Trojan was detected | ET MALWARE Lumma Stealer CnC Host Checkin |
2172 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (creative-habitat .shop) |
5 ETPRO signatures available at the full report