| File name: | 617724eae420e5972f88066ba4c9eb9a24772176.xls |
| Full analysis: | https://app.any.run/tasks/156c9447-61de-40e6-bdfc-bec6d828a3b9 |
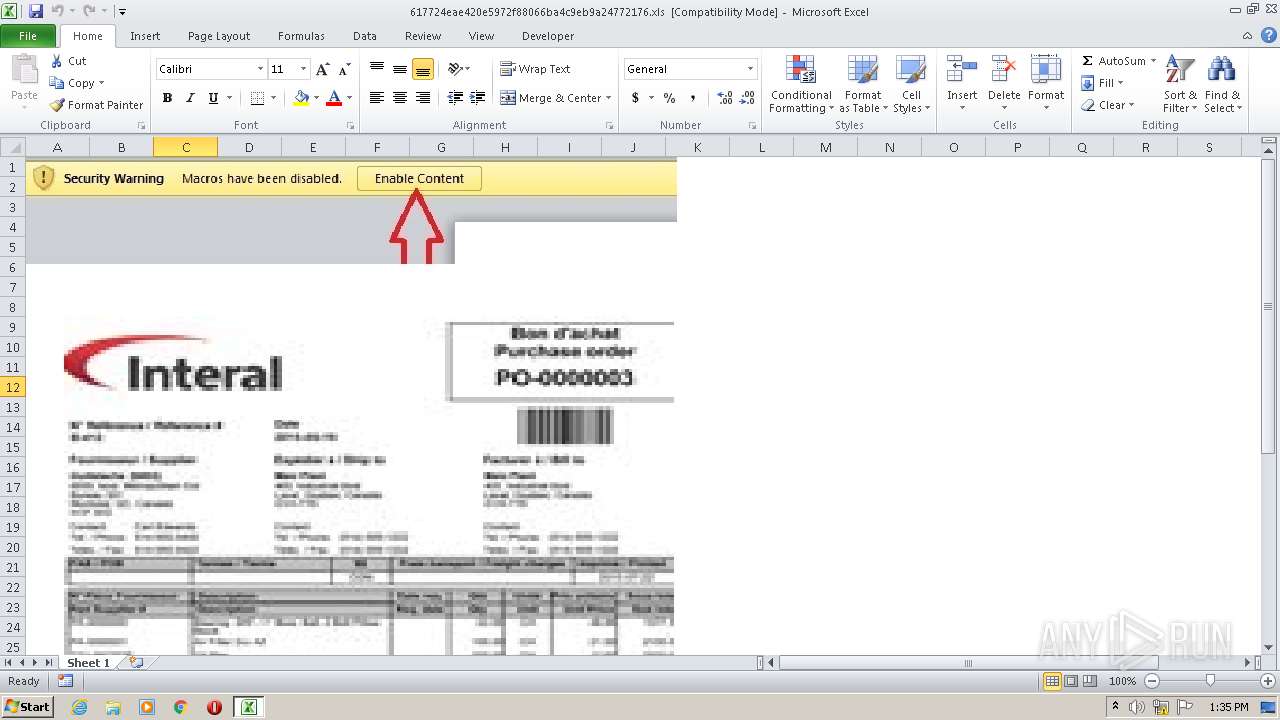
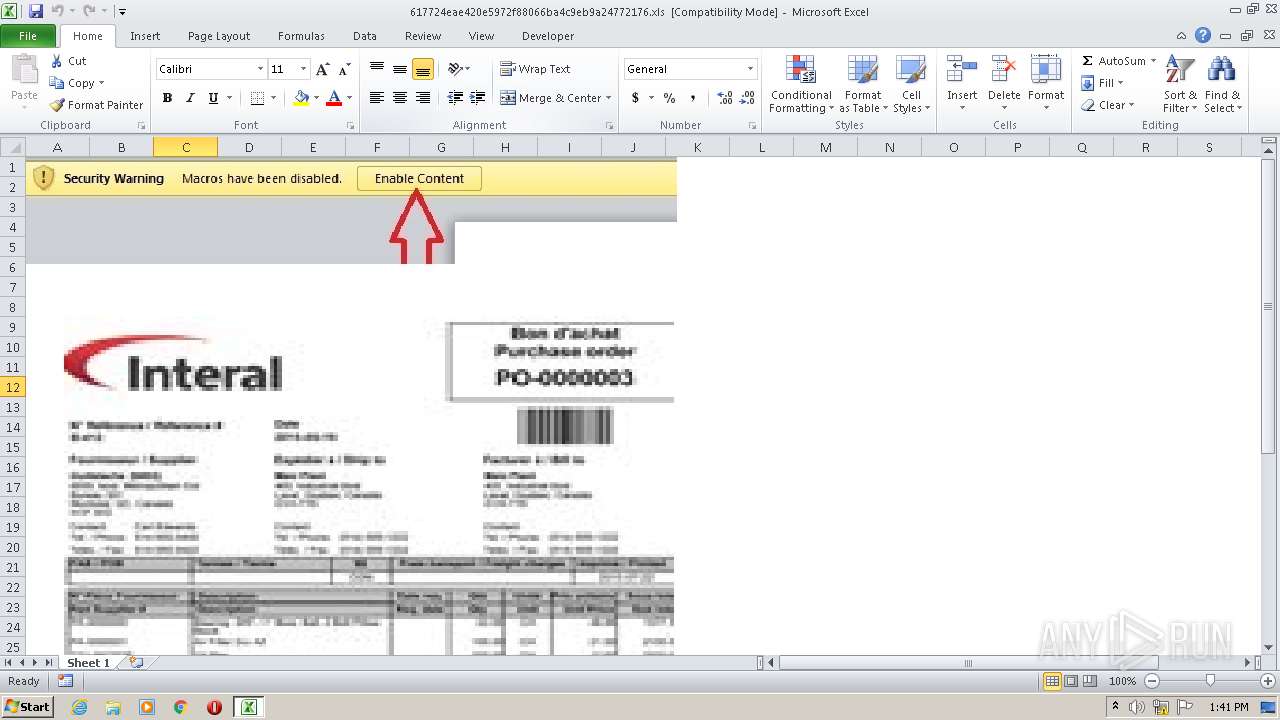
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | September 30, 2020, 12:35:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: DELL, Last Saved By: DELL, Create Time/Date: Wed Sep 30 09:35:34 2020, Last Saved Time/Date: Wed Sep 30 09:35:34 2020, Security: 0 |
| MD5: | 68D49604D2AF422137883BBE175597C9 |
| SHA1: | 617724EAE420E5972F88066BA4C9EB9A24772176 |
| SHA256: | 8F0B57FFEBABF29670832449B17EB4B76E9C9D4ACC7D79A34547CF641521BBB5 |
| SSDEEP: | 6144:Pk3hOdsylKlgryzc4bNhZF+E+W2kn08u0keNXFL318Aeu3bjbAOiOEc8ICtLtBDI:Qu03NXB31lf7jnEnIgLt |
MALICIOUS
Changes the autorun value in the registry
- reg.exe (PID: 1736)
- msdt.exe (PID: 2560)
Application was dropped or rewritten from another process
- osign.exe (PID: 1700)
- AddInProcess32.exe (PID: 1544)
- ezotrtxrfh52th.exe (PID: 1100)
- svchost32.exe (PID: 3984)
Loads dropped or rewritten executable
- osign.exe (PID: 1700)
- msdt.exe (PID: 2560)
- svchost32.exe (PID: 3984)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 2628)
Connects to CnC server
- explorer.exe (PID: 352)
Actions looks like stealing of personal data
- msdt.exe (PID: 2560)
FORMBOOK was detected
- explorer.exe (PID: 352)
- msdt.exe (PID: 2560)
- Firefox.exe (PID: 3132)
Stealing of credential data
- cmd.exe (PID: 724)
- msdt.exe (PID: 2560)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2628)
SUSPICIOUS
Creates files in the user directory
- explorer.exe (PID: 352)
- msdt.exe (PID: 2560)
Starts itself from another location
- svchost32.exe (PID: 3984)
Starts CMD.EXE for commands execution
- msdt.exe (PID: 2560)
- svchost32.exe (PID: 3984)
Loads DLL from Mozilla Firefox
- msdt.exe (PID: 2560)
Executable content was dropped or overwritten
- explorer.exe (PID: 352)
- msdt.exe (PID: 2560)
- DllHost.exe (PID: 3320)
- svchost32.exe (PID: 3984)
Executed via COM
- DllHost.exe (PID: 3320)
Creates files in the program directory
- DllHost.exe (PID: 3320)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2152)
INFO
Starts Microsoft Office Application
- explorer.exe (PID: 352)
Reads the hosts file
- msdt.exe (PID: 2560)
Manual execution by user
- msdt.exe (PID: 2560)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2628)
Creates files in the user directory
- EXCEL.EXE (PID: 2628)
- Firefox.exe (PID: 3132)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (48) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (39.2) |
EXIF
FlashPix
| Author: | DELL |
|---|---|
| LastModifiedBy: | DELL |
| CreateDate: | 2020:09:30 08:35:34 |
| ModifyDate: | 2020:09:30 08:35:34 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | Sheet 1 |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 31 |
| CompObjUserType: | Microsoft Excel 2003 Worksheet |
Total processes
54
Monitored processes
13
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 724 | /c copy "C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data" "C:\Users\admin\AppData\Local\Temp\DB1" /V | C:\Windows\System32\cmd.exe | msdt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Hrzu8y8\ezotrtxrfh52th.exe" | C:\Program Files\Hrzu8y8\ezotrtxrfh52th.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 1 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1544 | "C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe" | C:\Users\admin\AppData\Local\Temp\AddInProcess32.exe | — | osign.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: AddInProcess.exe Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
| 1700 | "C:\Users\admin\osign.exe" | C:\Users\admin\osign.exe | — | svchost32.exe | |||||||||||
User: admin Company: r;24a,#0f5s]u Integrity Level: MEDIUM Description: u,78r&]5zx(1*6do_0)4t Exit code: 0 Version: 1.1.2.2 Modules
| |||||||||||||||
| 1736 | REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /f /v sobm /t REG_SZ /d C:\Windows\system32\pcalua.exe" -a C:\Users\admin\osign.exe" | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "cmd.exe" /c REG ADD HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run /f /v sobm /t REG_SZ /d C:\Windows\system32\pcalua.exe" -a C:\Users\admin\osign.exe" | C:\Windows\system32\cmd.exe | — | svchost32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2560 | "C:\Windows\System32\msdt.exe" | C:\Windows\System32\msdt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | msdt.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
Total events
3 150
Read events
3 043
Write events
94
Delete events
13
Modification events
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 4'h |
Value: 34276800440A0000010000000000000000000000 | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2628) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
8
Suspicious files
81
Text files
3
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2628 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR7734.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2628 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\617724eae420e5972f88066ba4c9eb9a24772176.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2628 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\DFI-6059[1].jpg | executable | |
MD5:— | SHA256:— | |||
| 2628 | EXCEL.EXE | C:\Users\Public\svchost32.exe | executable | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\617724eae420e5972f88066ba4c9eb9a24772176.xls.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2628 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 352 | explorer.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms | automaticdestinations-ms | |
MD5:— | SHA256:— | |||
| 2560 | msdt.exe | C:\Users\admin\AppData\Local\Temp\ehd07bmx.zip | compressed | |
MD5:— | SHA256:— | |||
| 2560 | msdt.exe | C:\Users\admin\AppData\Roaming\556PN550\556logrg.ini | binary | |
MD5:— | SHA256:— | |||
| 3984 | svchost32.exe | C:\Users\admin\osign.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
33
DNS requests
17
Threats
73
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | explorer.exe | GET | 200 | 217.70.184.50:80 | http://www.duplex-id.com/dmr/?cx4=JqX3llDj5zrEJKAr/heZ/yuNYEc2LyTvyN69LG/zeKg7yqdKQXyOgjofEK3QvXdz4KAd2A==&Tj=Cp8LjLB | FR | html | 2.45 Kb | malicious |
352 | explorer.exe | GET | 200 | 63.250.45.230:80 | http://www.funpexw.com/dmr/?cx4=S8hjfYTpkybpMc1fzCwJp/QhNeFvwwQCO/UiWBJtQ/7unD0KpHd2F8yPB6G75RTZf3U29Q==&Tj=Cp8LjLB | US | binary | 323 Kb | malicious |
352 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.sunlivetv.com/dmr/ | US | — | — | malicious |
352 | explorer.exe | POST | — | 63.250.45.230:80 | http://www.funpexw.com/dmr/ | US | — | — | malicious |
352 | explorer.exe | POST | 404 | 63.250.45.230:80 | http://www.funpexw.com/dmr/ | US | html | 292 b | malicious |
352 | explorer.exe | GET | 302 | 23.20.239.12:80 | http://www.sunlivetv.com/dmr/?cx4=27Olka01VUixcY2UgpwcBLXd1vSzo9aGad1vOsMZAm0IpJpBeNadkUyisDhAIQj3S+LC8A==&Tj=Cp8LjLB | US | html | 185 b | malicious |
352 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.sunlivetv.com/dmr/ | US | — | — | malicious |
352 | explorer.exe | POST | 404 | 63.250.45.230:80 | http://www.funpexw.com/dmr/ | US | html | 292 b | malicious |
352 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.sunlivetv.com/dmr/ | US | — | — | malicious |
352 | explorer.exe | POST | — | 23.20.239.12:80 | http://www.sunlivetv.com/dmr/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2628 | EXCEL.EXE | 185.33.85.52:80 | — | — | GB | malicious |
352 | explorer.exe | 217.70.184.50:80 | www.duplex-id.com | GANDI SAS | FR | malicious |
352 | explorer.exe | 23.20.239.12:80 | www.sunlivetv.com | Amazon.com, Inc. | US | shared |
352 | explorer.exe | 63.250.45.230:80 | www.funpexw.com | Frontline Data Services, Inc | US | malicious |
352 | explorer.exe | 195.110.124.154:80 | www.boredofbooze.com | Register.it SpA | IT | malicious |
352 | explorer.exe | 34.102.136.180:80 | www.shiltawi.com | — | US | whitelisted |
352 | explorer.exe | 185.225.208.56:80 | www.aracaju.online | — | — | malicious |
— | — | 34.102.136.180:80 | www.shiltawi.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.diptya.net |
| unknown |
www.dhzzyy.net |
| malicious |
www.rooster-money.com |
| unknown |
www.swiyke.download |
| unknown |
www.duplex-id.com |
| malicious |
www.bestsmokeapp.com |
| unknown |
www.hotelsitaly.online |
| unknown |
www.siyahmaske.win |
| unknown |
www.funpexw.com |
| malicious |
www.imagingnetworkri.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2628 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
2628 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
2628 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
2628 | EXCEL.EXE | A Network Trojan was detected | ET TROJAN JS/WSF Downloader Dec 08 2016 M4 |
2628 | EXCEL.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |
2628 | EXCEL.EXE | A Network Trojan was detected | AV POLICY EXE or DLL in HTTP Image Content Inbound - Likely Malicious |
2628 | EXCEL.EXE | Misc activity | SUSPICIOUS [PTsecurity] PE as Image Content type mismatch |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
352 | explorer.exe | A Network Trojan was detected | SPYWARE [PTsecurity] FormBook |
24 ETPRO signatures available at the full report