| download: | wifi_bruter.exe |
| Full analysis: | https://app.any.run/tasks/b1c80f7d-93e9-4937-ac5e-8ad5cdec2a5c |
| Verdict: | Malicious activity |
| Threats: | Orcus is a modular Remote Access Trojan with some unusual functions. This RAT enables attackers to create plugins using a custom development library and offers a robust core feature set that makes it one of the most dangerous malicious programs in its class. |
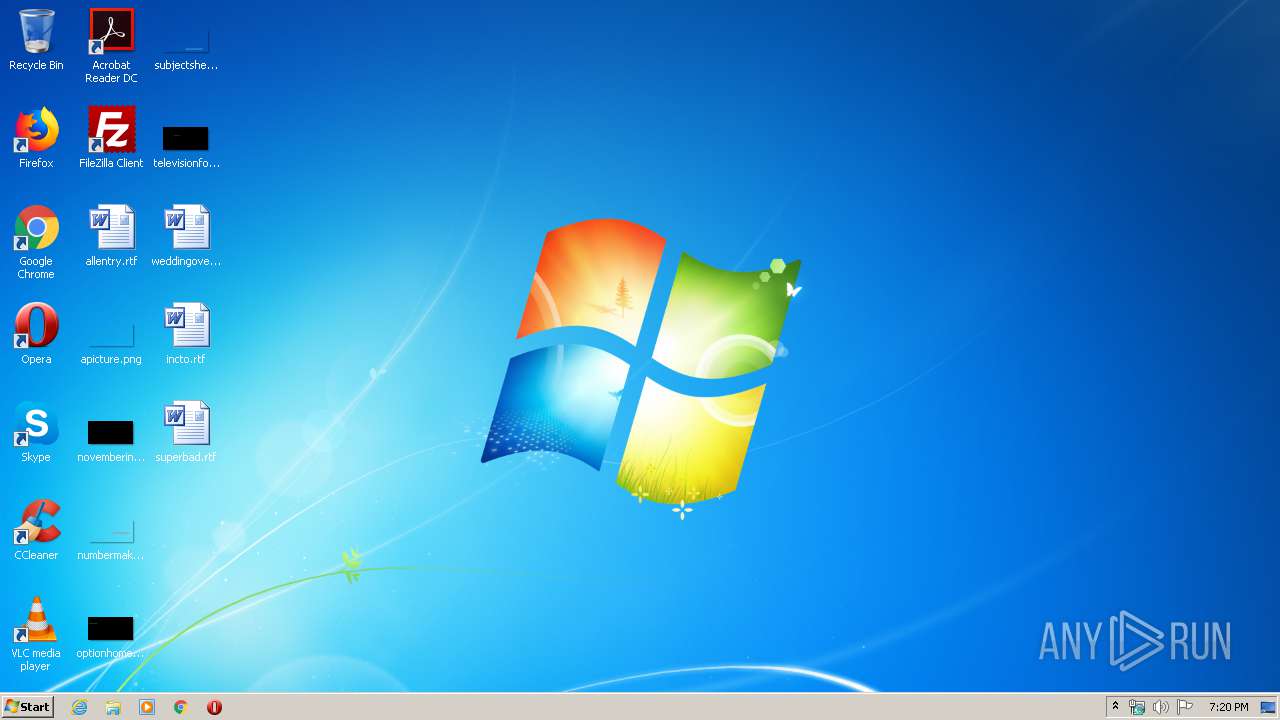
| Analysis date: | May 30, 2020, 18:20:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 00123F651A0FB54F2C91BD04F6F010B4 |
| SHA1: | 66CF37BD3DB0C0EDE8125537217CB829E14E2B70 |
| SHA256: | 8EB8BEE836574E96DCE964208C1E29F1D5F9843B2AC6CDD545FD537FE2557FBB |
| SSDEEP: | 6144:Xxw25wUHB2BcfpqvSxUBx5YCFL5gwoyLXXMzDJI:hp5wUHBNfpqvtqCFuULb |
MALICIOUS
Loads dropped or rewritten executable
- wifi_bruter.exe (PID: 2928)
Actions looks like stealing of personal data
- wifi_bruter.exe (PID: 2928)
ORCUS was detected
- wifi_bruter.exe (PID: 2928)
SUSPICIOUS
Creates files in the program directory
- wifi_bruter.exe (PID: 2928)
Reads Environment values
- wifi_bruter.exe (PID: 2928)
Reads the Windows organization settings
- wifi_bruter.exe (PID: 2928)
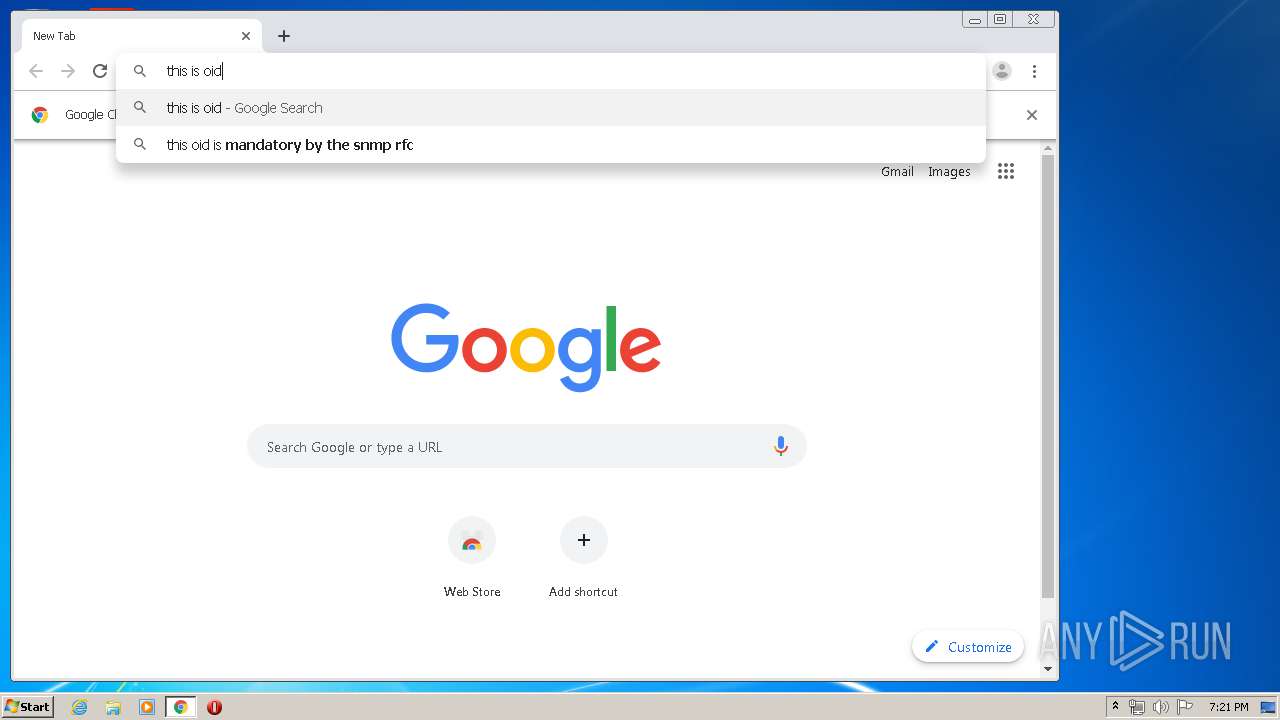
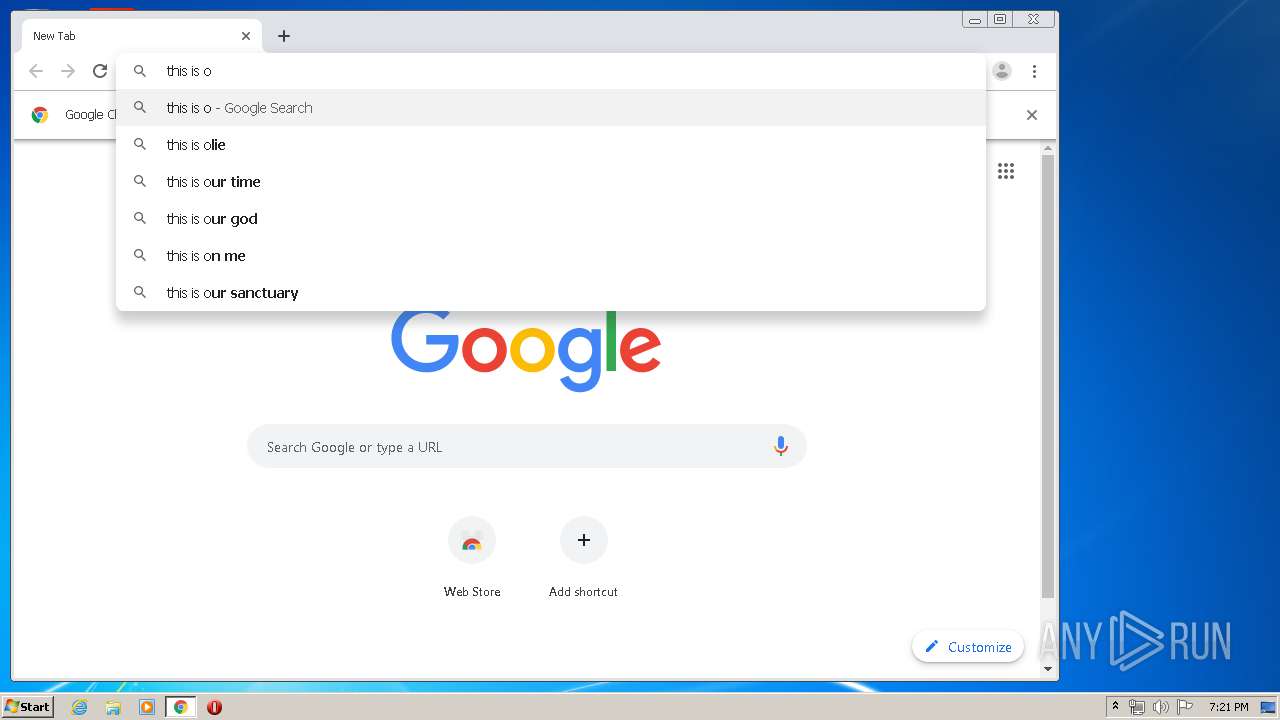
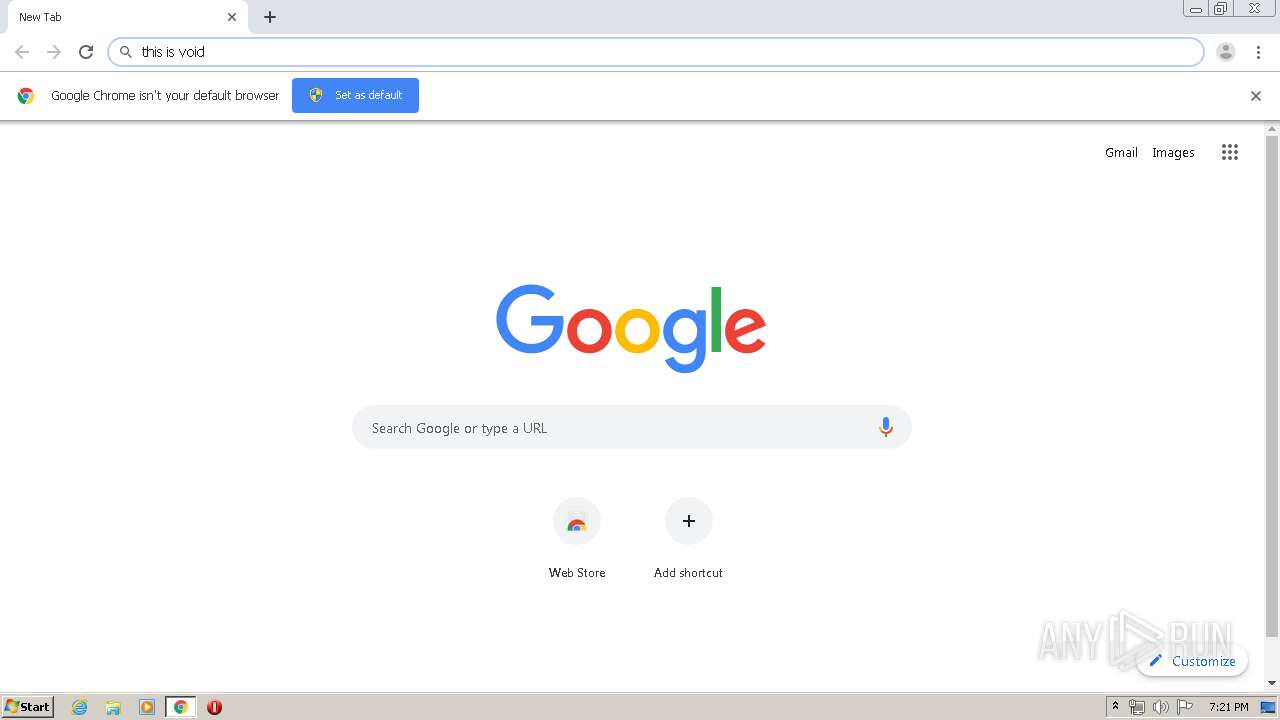
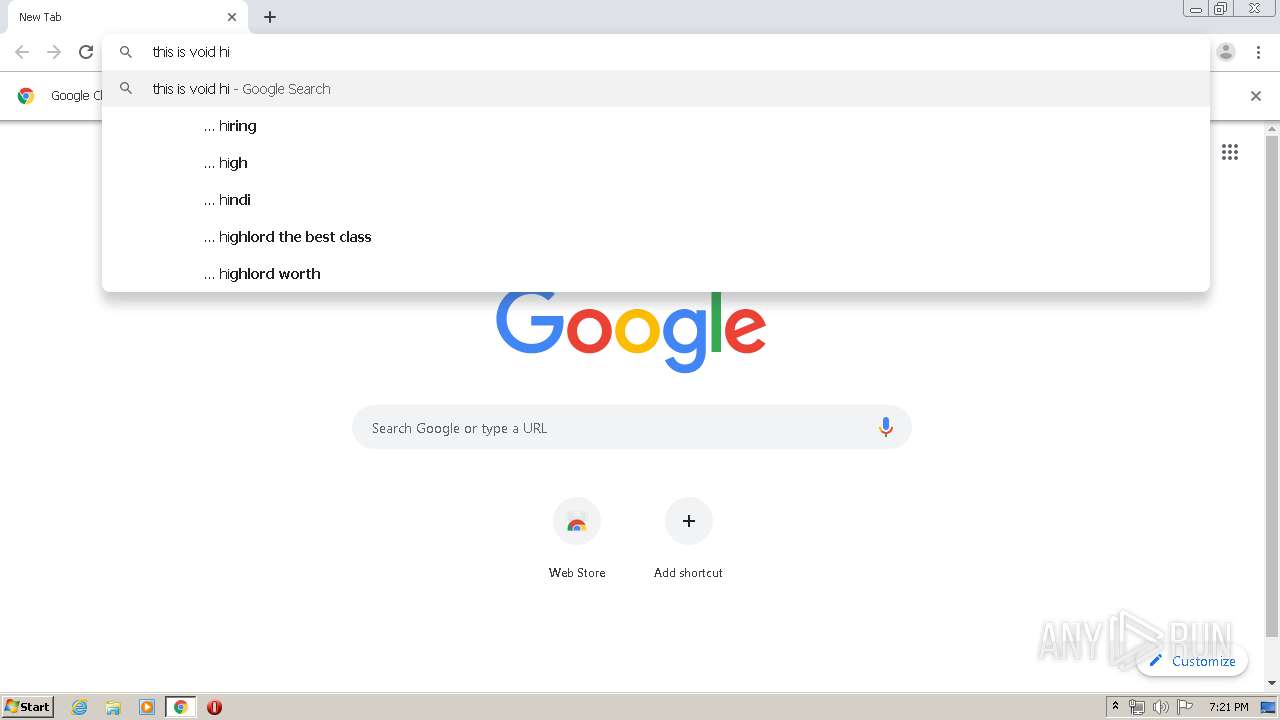
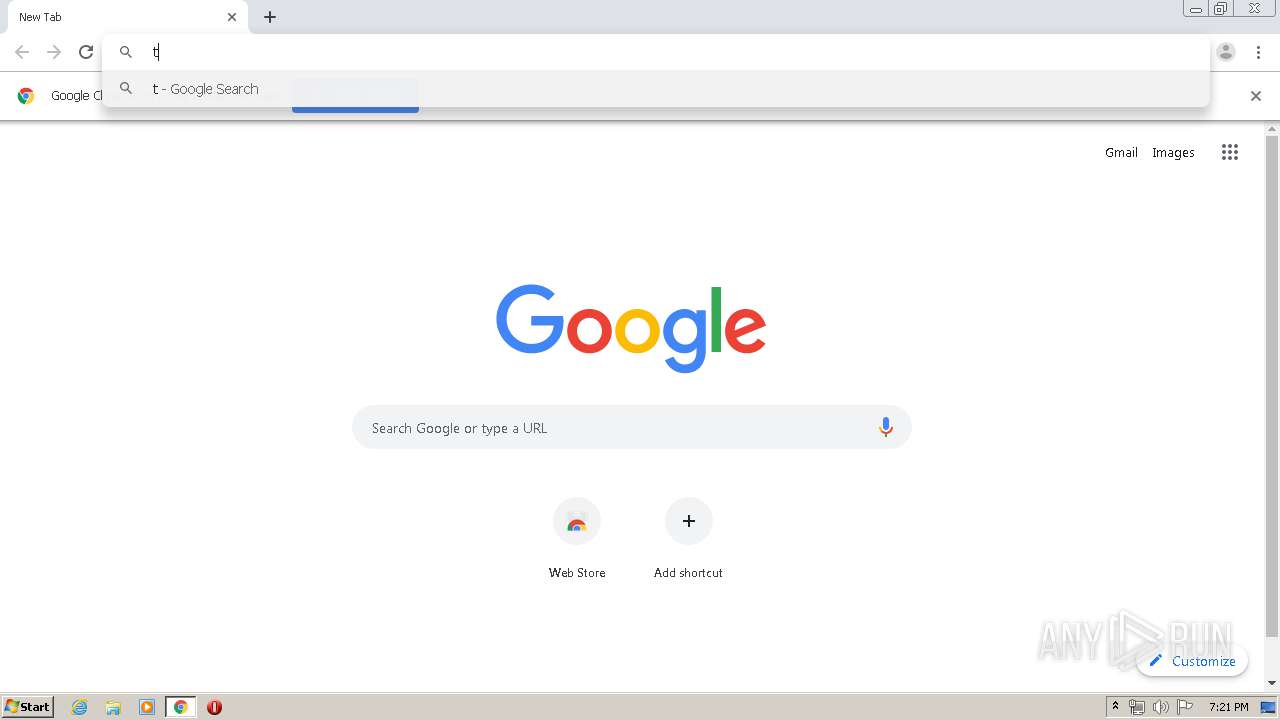
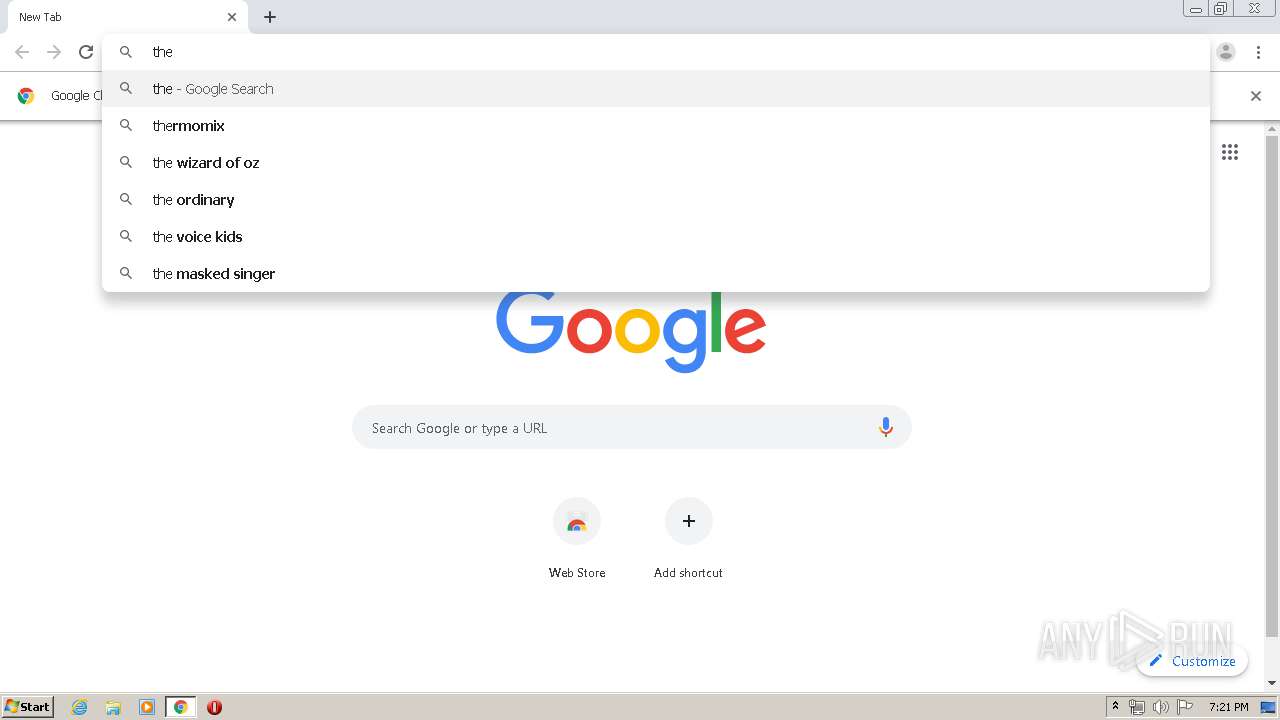
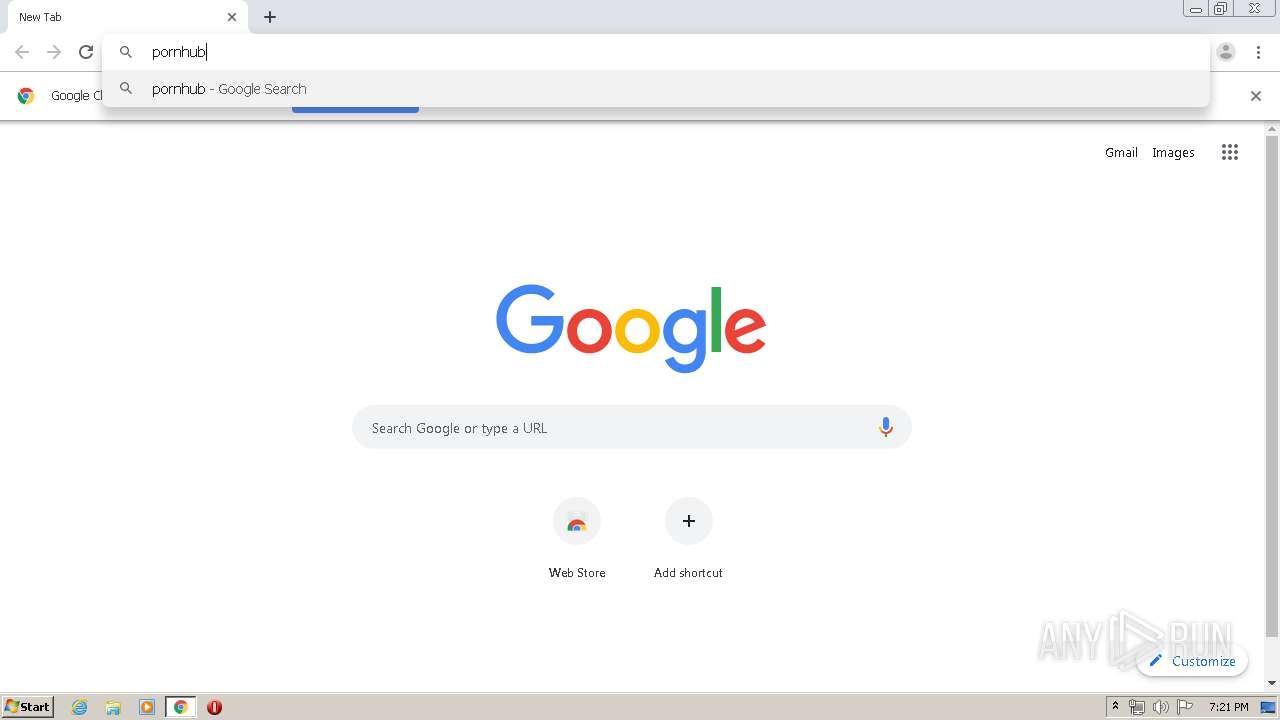
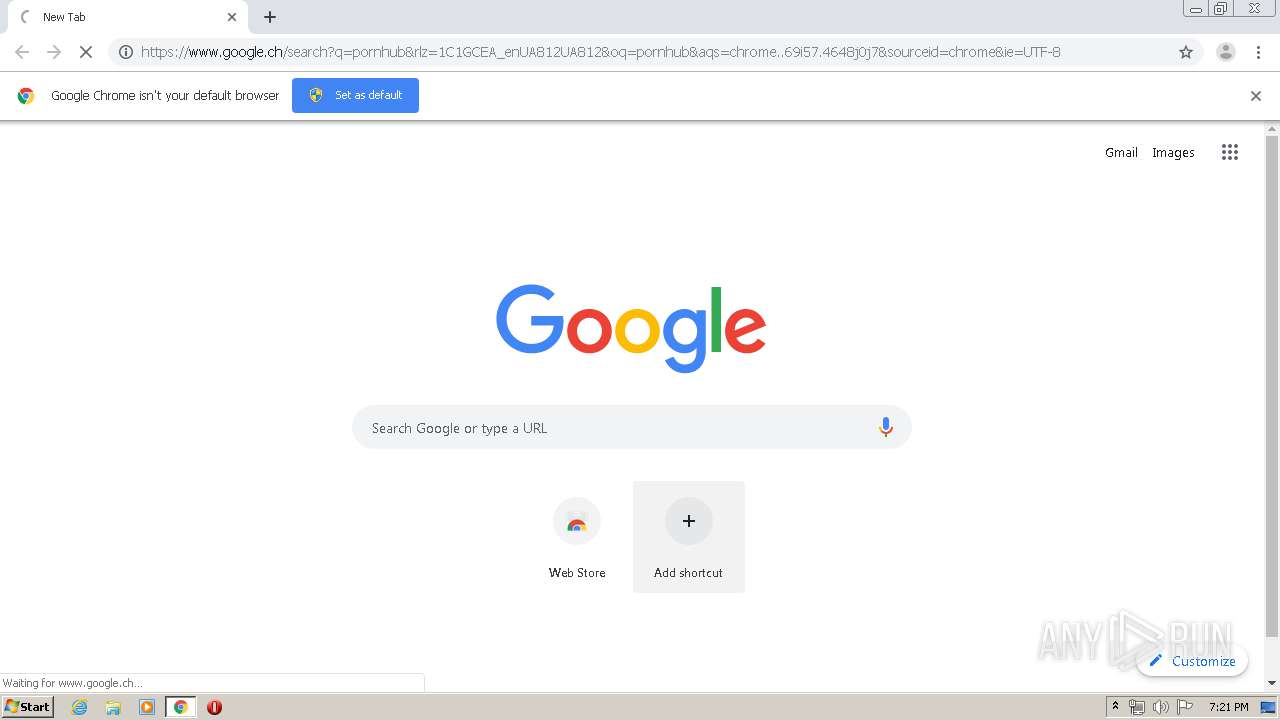
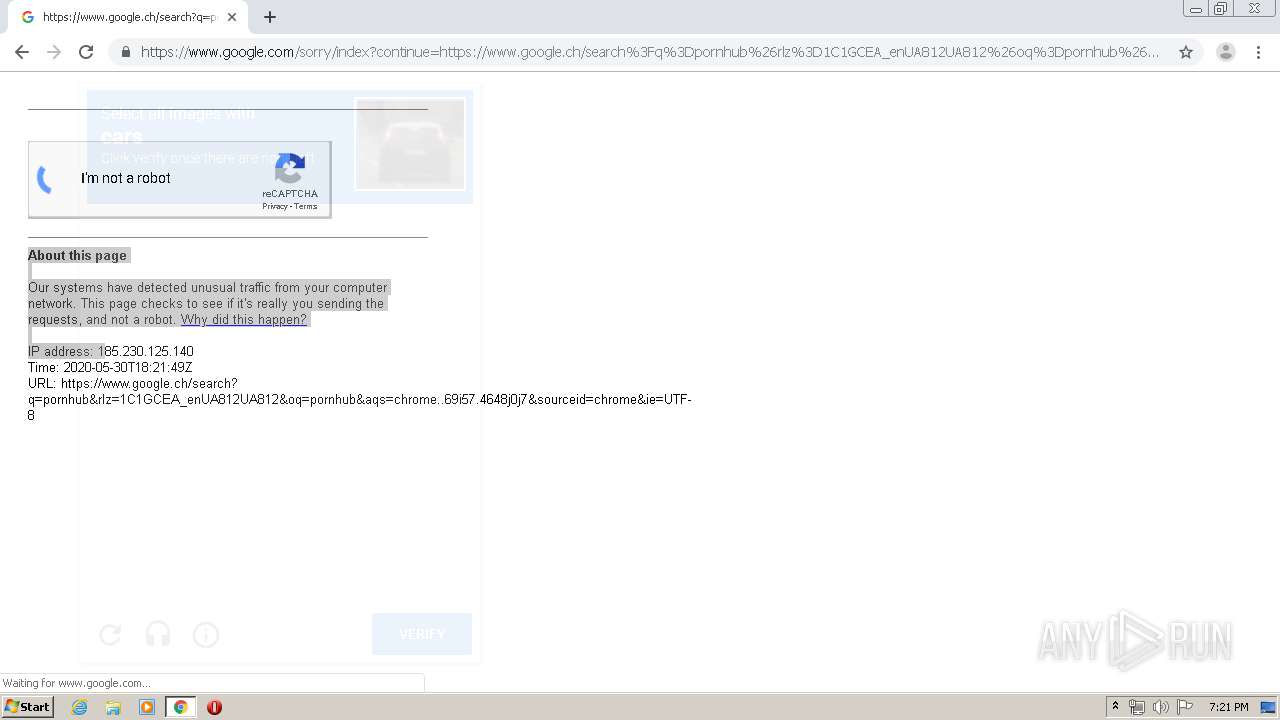
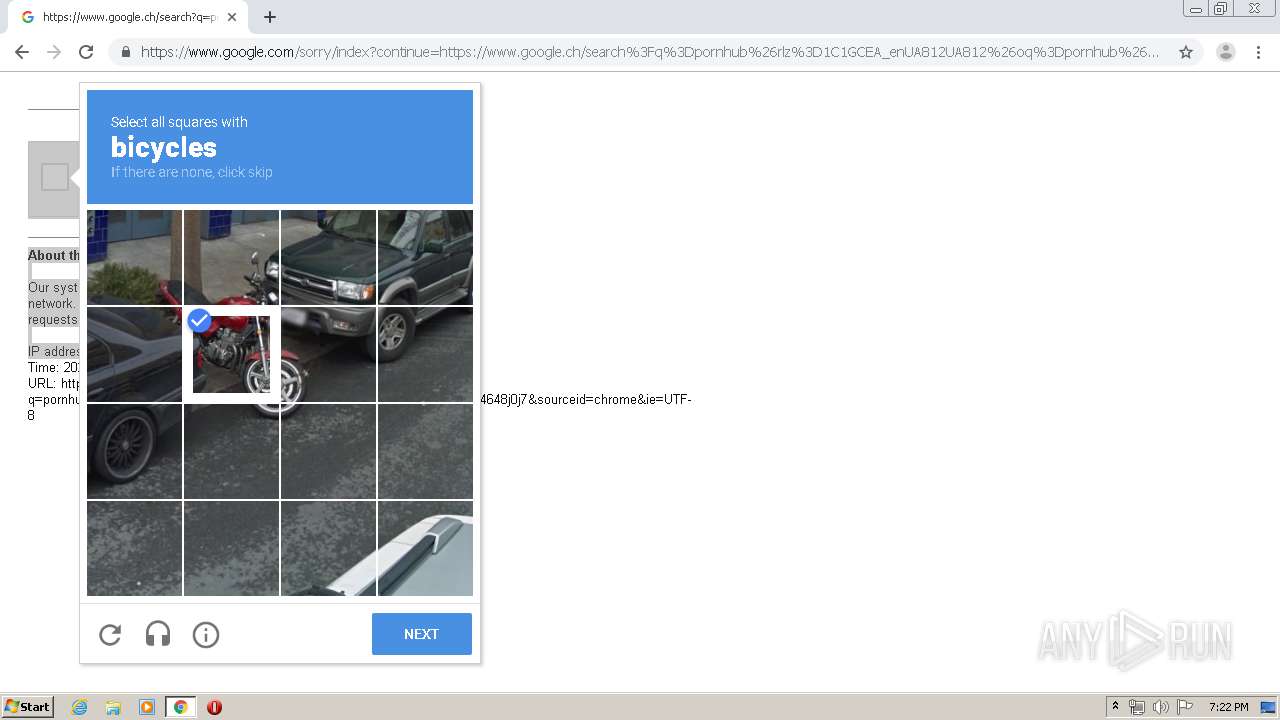
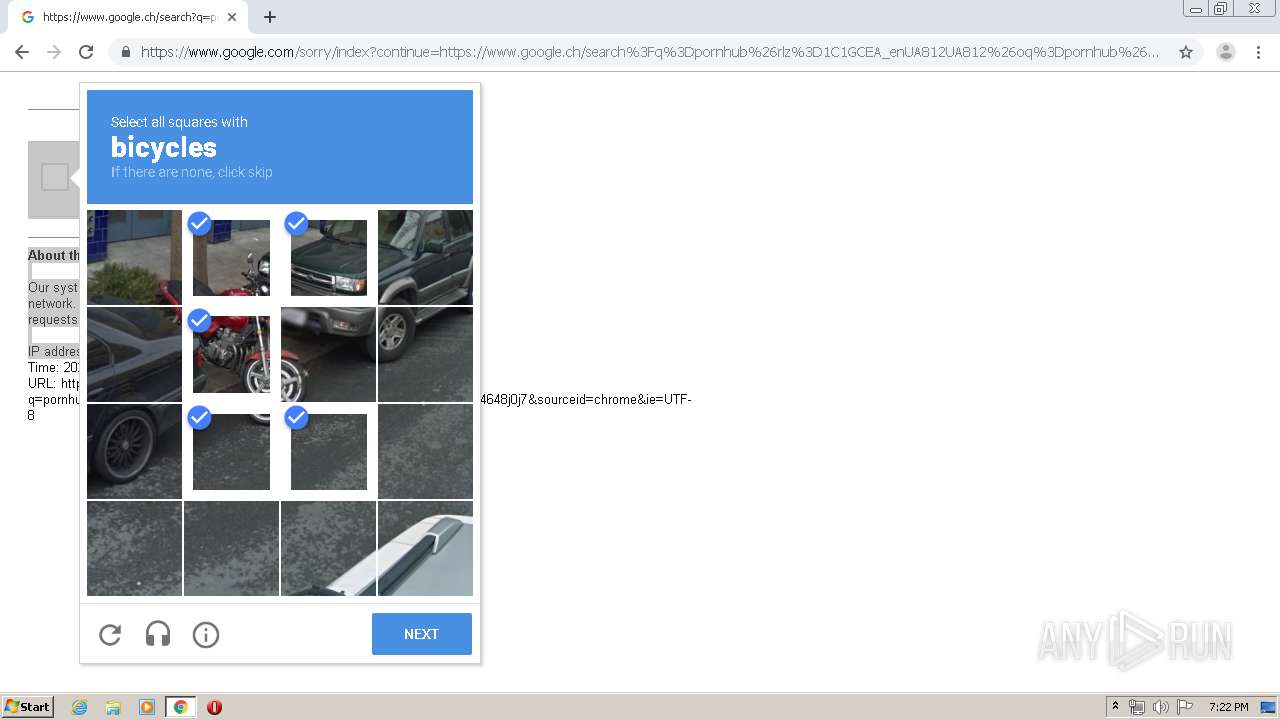
Modifies files in Chrome extension folder
- chrome.exe (PID: 2412)
Reads Windows owner or organization settings
- wifi_bruter.exe (PID: 2928)
Creates files in the user directory
- wifi_bruter.exe (PID: 2928)
Executable content was dropped or overwritten
- wifi_bruter.exe (PID: 2928)
Searches for installed software
- wifi_bruter.exe (PID: 2928)
INFO
Manual execution by user
- chrome.exe (PID: 2412)
Reads the hosts file
- chrome.exe (PID: 2412)
- chrome.exe (PID: 3984)
Application launched itself
- chrome.exe (PID: 2412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (45.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (19.2) |
| .exe | | | Win64 Executable (generic) (17) |
| .scr | | | Windows screen saver (8) |
| .dll | | | Win32 Dynamic Link Library (generic) (4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:05:30 20:07:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 228864 |
| InitializedDataSize: | 167424 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x39cae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.100.100.100 |
| ProductVersionNumber: | 5.100.100.100 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Microsoft ® Windows Based Script Host |
| CompanyName: | Microsoft ® Windows Script Host |
| FileDescription: | wscript.exe |
| FileVersion: | 5.100.100.100 |
| InternalName: | wifichecker.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | wifichecker.exe |
| ProductName: | Microsoft Corporation |
| ProductVersion: | 5.100.100.100 |
| AssemblyVersion: | 5.100.100.100 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-May-2020 18:07:52 |
| Comments: | Microsoft ® Windows Based Script Host |
| CompanyName: | Microsoft ® Windows Script Host |
| FileDescription: | wscript.exe |
| FileVersion: | 5.100.100.100 |
| InternalName: | wifichecker.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | wifichecker.exe |
| ProductName: | Microsoft Corporation |
| ProductVersion: | 5.100.100.100 |
| Assembly Version: | 5.100.100.100 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 30-May-2020 18:07:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00037CB4 | 0x00037E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.92897 |
.sdata | 0x0003A000 | 0x00000938 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.64599 |
.rsrc | 0x0003C000 | 0x00028098 | 0x00028200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.32759 |
.reloc | 0x00066000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.48549 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.54237 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.70862 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 3.20708 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 3.99194 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.02487 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.58416 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.67041 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 3.0879 | 118 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
71
Monitored processes
33
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13621807277712833155 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8556892221601910480 --mojo-platform-channel-handle=3956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6a31a9d0,0x6a31a9e0,0x6a31a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3384 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6461509225178105694 --mojo-platform-channel-handle=4388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13797804197339210665 --mojo-platform-channel-handle=3904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4754037997903331486 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13312272733871033504 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11140927898306616224 --mojo-platform-channel-handle=4216 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8974124996711952044,1184521135712739327,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=277118248922093463 --mojo-platform-channel-handle=3272 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 593
Read events
2 465
Write events
123
Delete events
5
Modification events
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_CLASSES_ROOT\CID\{7A007200-4800-2B00-2F00-4C0058005200} |
| Operation: | write | Name: | 1 |
Value: FHGDvYnqWHZyQU2tchcug8n/b+HCaKShadCyf9ZrFvQhwzrGYLQQLfIX9AJnNEScH6e5igDjtSTedOsPTMQsOieFYP8hwk/joRm5prj40F3dmtYd1PfEzkGsiaRrvtYLJePfUH+u8SOvggacHGIXK5NAkFsOzEEoe/lyBKiYJRIB+45Cdz2DexVw+1xCLRJmpuGr0U6n7ZodjoK1fYJj6dk1uWjd0XCXFVcKX3BrFuZtx53HqYN1NoqklkDAUUCB/4utX3v9T6pTg+q8wlqha9yK+vggu57CjBmQrtCOffsxS3yTKasnMWXJN4nD3Tog8Wau9tXGnKEAK7UtAcxnKqmgsDhBdXjc75sShUK2XSTHq/CME/jKpRa4x53jxWgyb/ByDrRusS+deOPqf+5d9iTl/sYQyK942GkNFOosnHXI1URdYCBuQ65lOmrg+u5LR5bvXO38GPHBBbJ2z4Umcqdl/6OWmiAr0O7RhjT/Usos0cXNg+BB15tBnUNRCool9QcOaWFZjcqt/e/czcIvH/PAPo6sfMhnGqmnf/5+Nl8CjJieiDLBKiMoqhPn0yckPKIiyH4L+Nrq6Yci/rW2teZ5iQqKzyDcddk6KVCXmveqb6SB4rM1SuuoPaFr/MSTQDdHVHKtya5vBhaXU+NDW70BJ2m0alYcbnI/uo532ges+2Flq8gPsrx+3iNh70UX | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_CLASSES_ROOT\CID\{47007900-7000-7400-4700-630041006C00} |
| Operation: | write | Name: | 1 |
Value: og0JhaZldMvHTu29bwcBMy9SQe0ql5jQhffP8/7/QlQX9qr7Hjq2xhpPvFOqML4otjuZc9U36DSQIza3BncjPa6fqoPUyHigHUcFTDPF/ljuRHoNmEX8sKfHb4Jf1riRwAvKjKT0nUNa49w5iUW4zBWCVT5xerJhfPoznsJOjdqPIk6cdxntEcyr+Vcyajr8 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2928) wifi_bruter.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wifi_bruter_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
14
Suspicious files
35
Text files
294
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\CabF815.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\TarF816.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\CabF836.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\TarF837.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\Cab642.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\Tar643.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\Cab1E41.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\Tar1E42.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\Cab1EA1.tmp | — | |
MD5:— | SHA256:— | |||
| 2928 | wifi_bruter.exe | C:\Users\admin\AppData\Local\Temp\Tar1EA2.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
29
DNS requests
22
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3984 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
3984 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 526 b | whitelisted |
3984 | chrome.exe | GET | 200 | 74.125.173.166:80 | http://r1---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjY5QUFXTEQwc2RPVXhRY3picjhxblh1dw/7619.603.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Qx&mip=185.230.125.140&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1590862751&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 816 Kb | whitelisted |
3984 | chrome.exe | GET | 200 | 74.125.173.170:80 | http://r5---sn-1gieen7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.230.125.140&mm=28&mn=sn-1gieen7e&ms=nvh&mt=1590862751&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2928 | wifi_bruter.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2928 | wifi_bruter.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
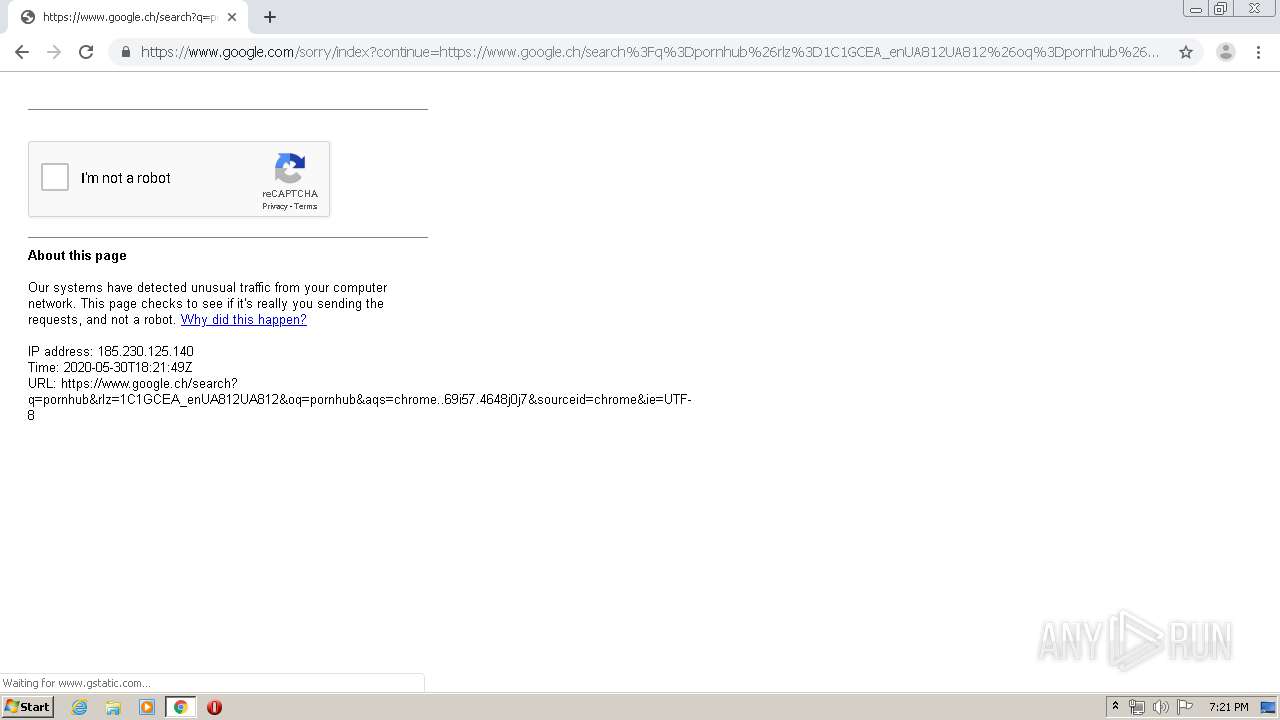
3984 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.16.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 216.58.207.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3984 | chrome.exe | 172.217.22.78:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2928 | wifi_bruter.exe | 3.13.191.225:11638 | 0.tcp.ngrok.io | — | US | malicious |
2928 | wifi_bruter.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
cdn.discordapp.com |
| shared |
0.tcp.ngrok.io |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY DNS Query to a *.ngrok domain (ngrok.io) |
2928 | wifi_bruter.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) |
2928 | wifi_bruter.exe | A Network Trojan was detected | MALWARE [PTsecurity] Malicious SSL connection (Orcus RAT) |
2 ETPRO signatures available at the full report