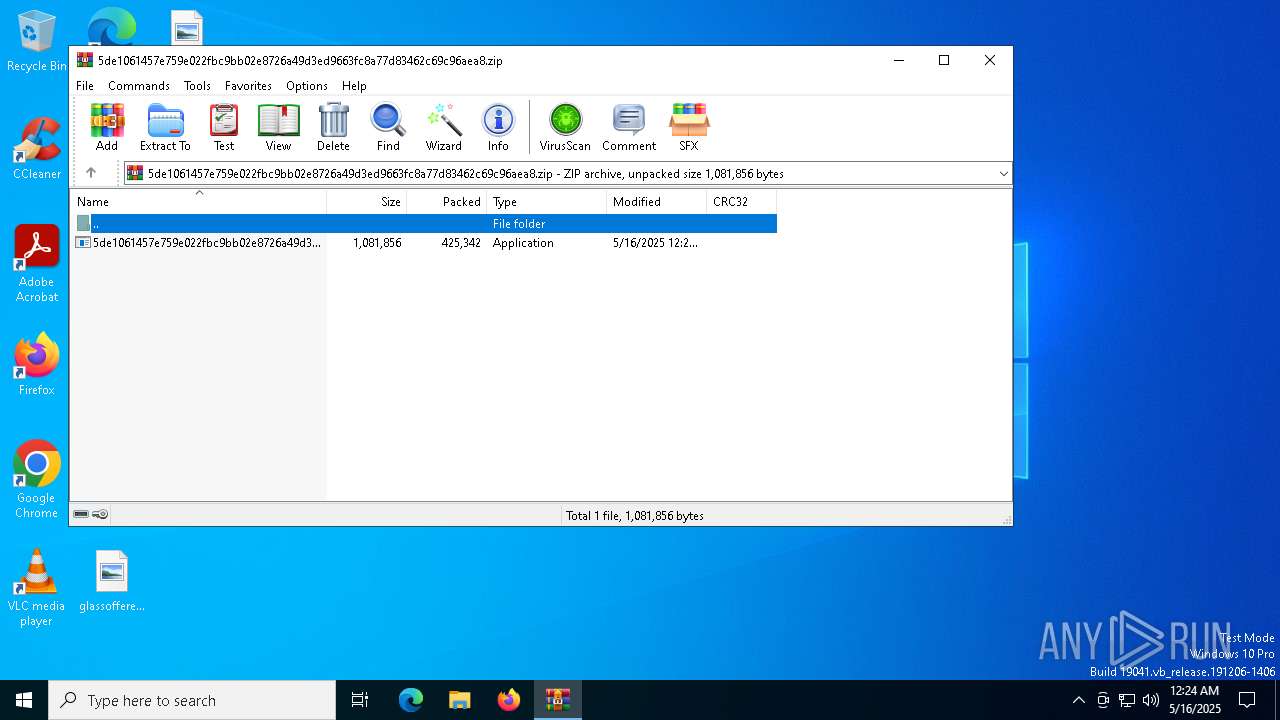
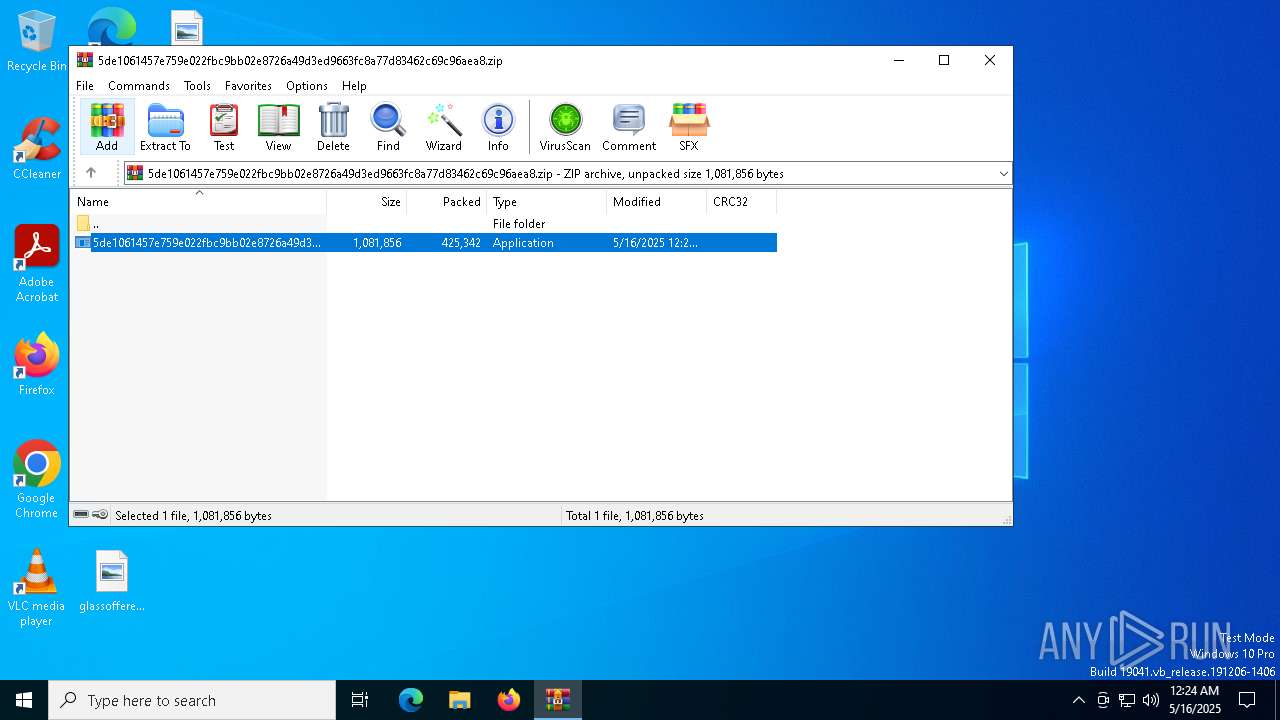
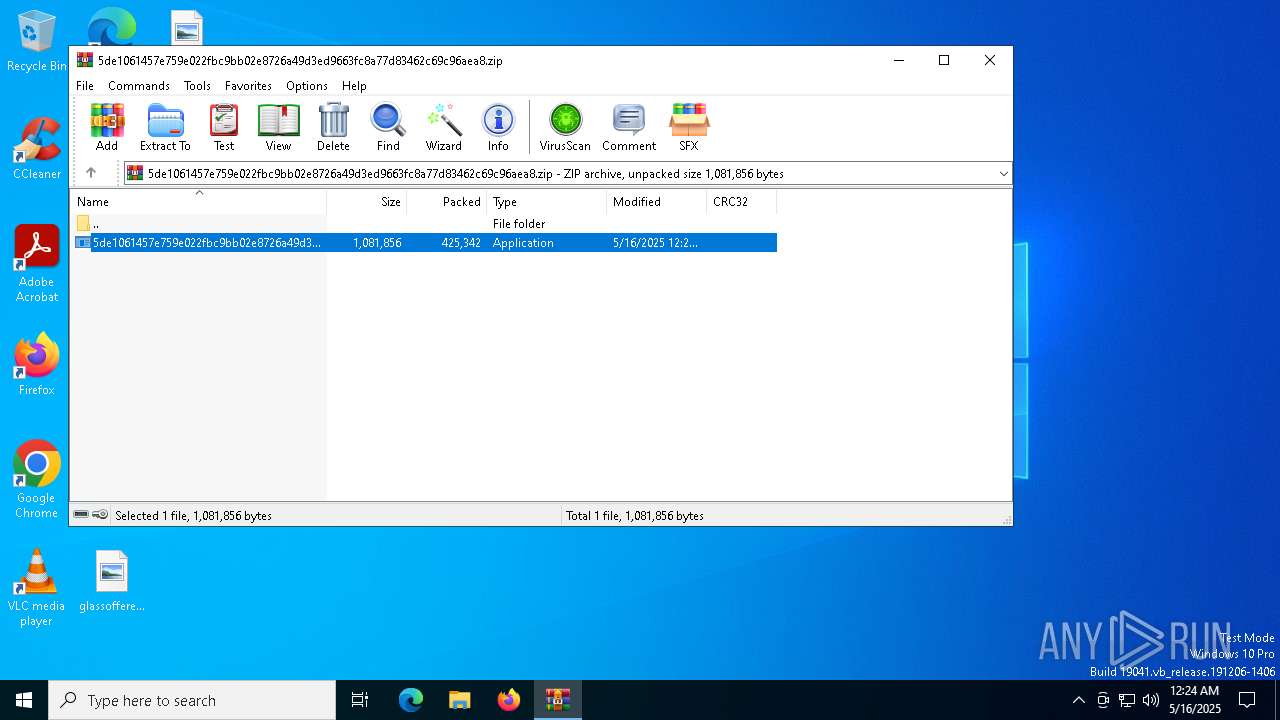
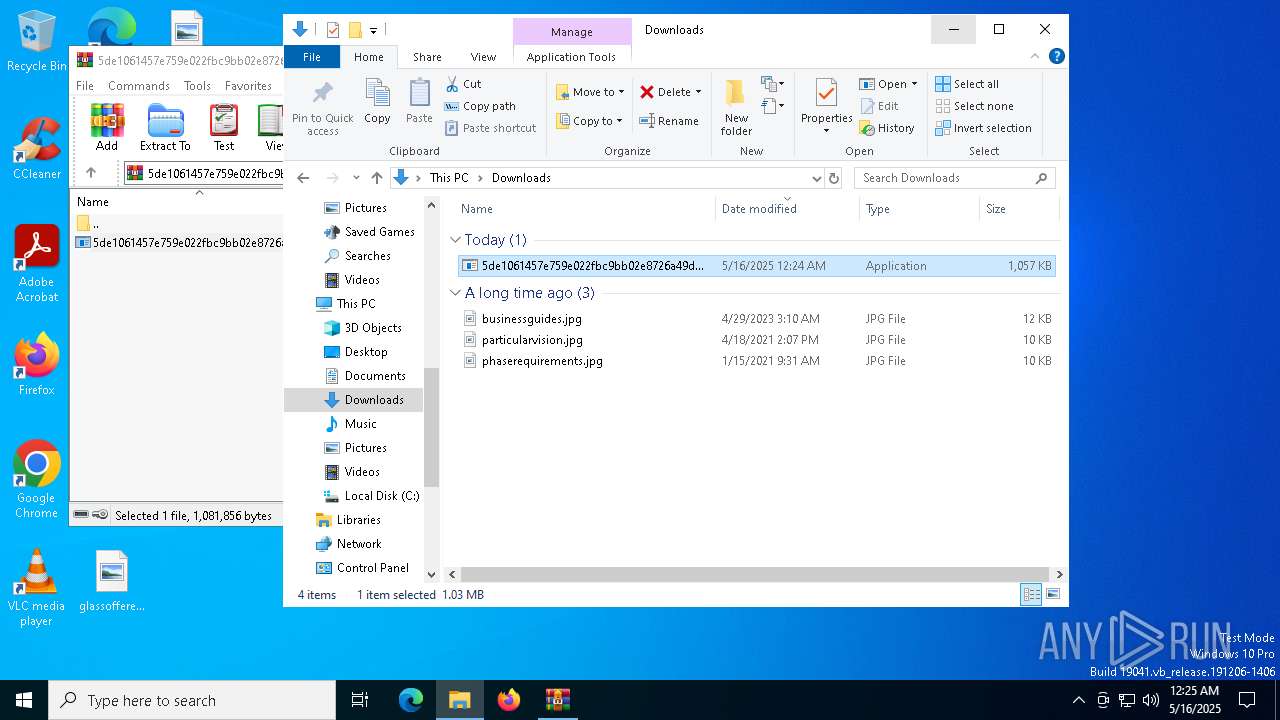
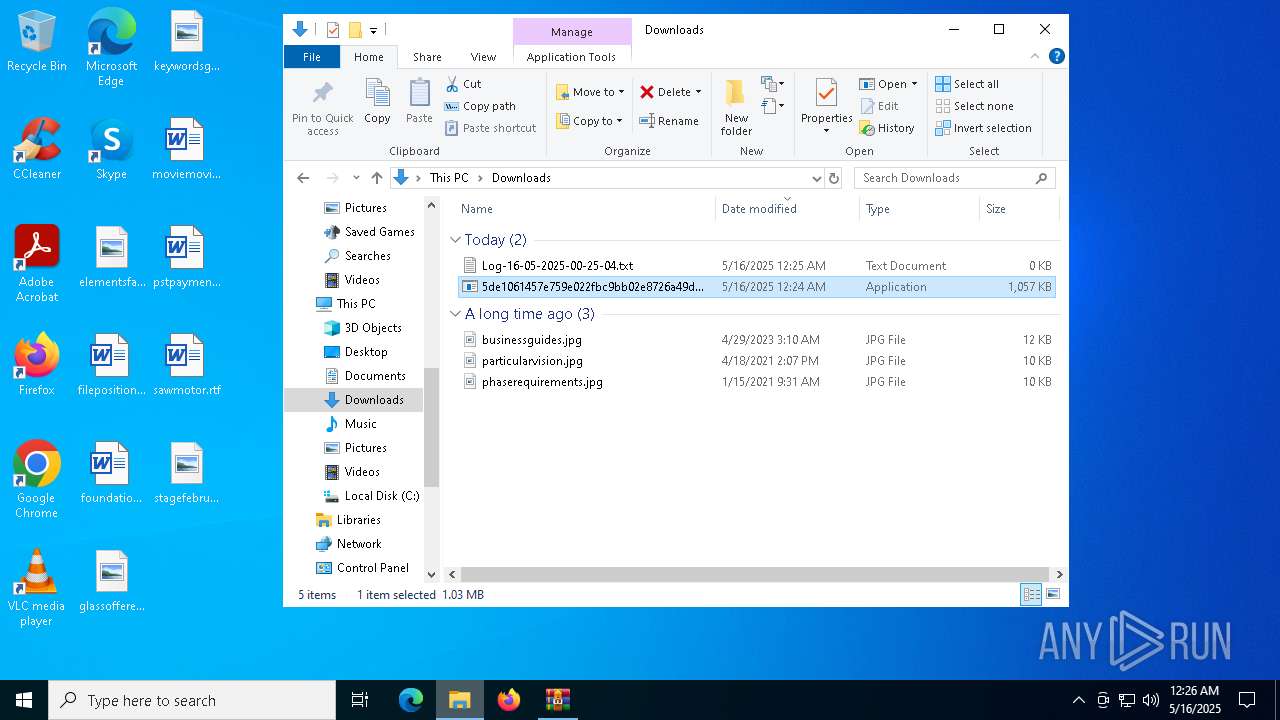
| File name: | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.zip |
| Full analysis: | https://app.any.run/tasks/cd27c422-7656-45d9-8d8a-1acd6a0b81e7 |
| Verdict: | Malicious activity |
| Threats: | Akira Ransomware emerged in March 2023 and compromised over 250 organizations by January 2024 with approximately $42 million in ransom payments. It employs double extortion tactics exfiltrating data before encryption and threatening to publish it on a dedicated website. |
| Analysis date: | May 16, 2025, 00:24:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
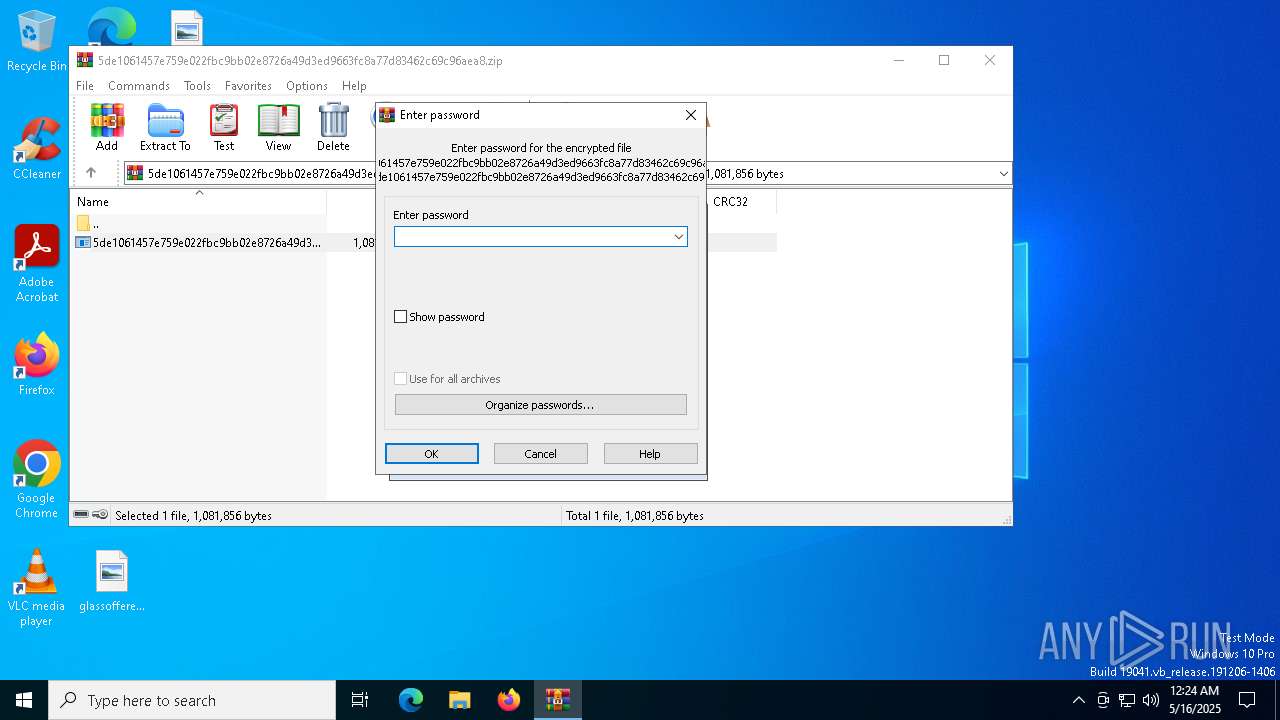
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 805E8C9B1D6210E369B499758B25EAED |
| SHA1: | E01FEFCCF0026F7D9AF3F21AD43CD421E5340D4C |
| SHA256: | 8E3321318790833998D7737A93727774FF68357FAE54F23BF5AF46CA29BAA977 |
| SSDEEP: | 12288:866RbQDv/+GpmP1GTOzSEBBjEHCp9+YDEX9QQp6yTU:866RcDv/+GpmP0TOzjBIHCjbDEX9QQpa |
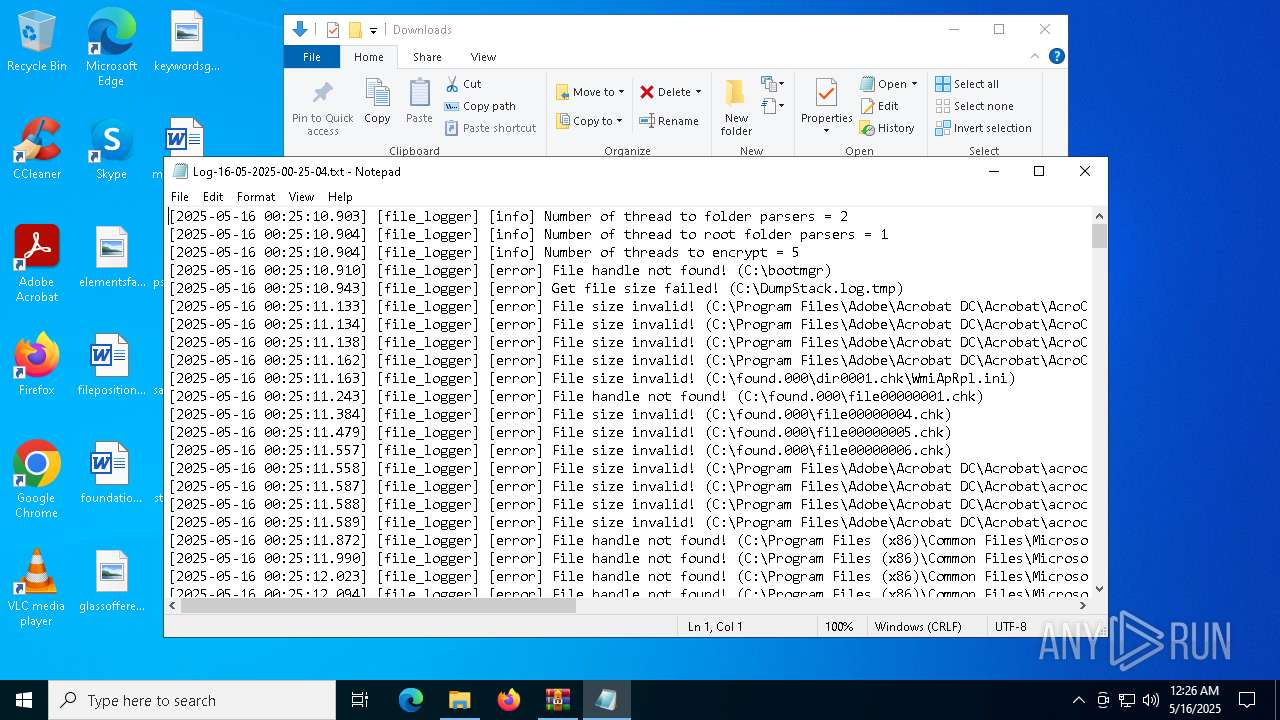
MALICIOUS
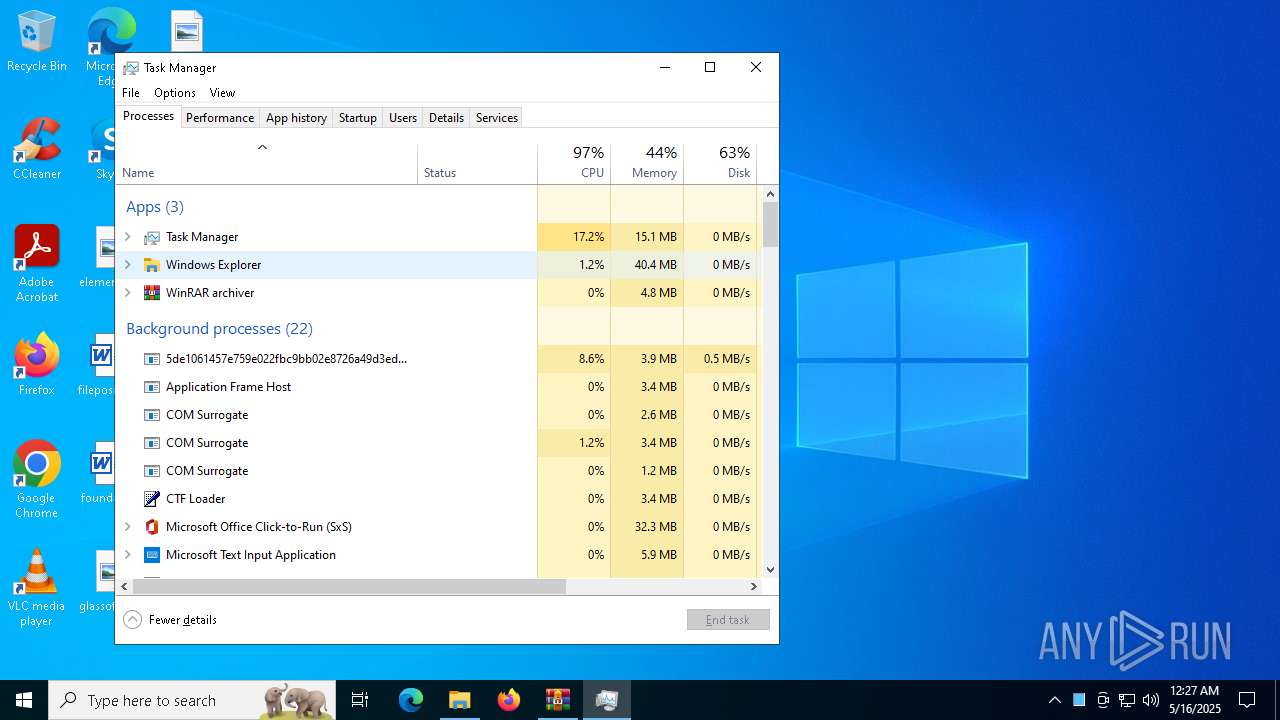
RANSOMWARE has been found (auto)
- WinRAR.exe (PID: 1512)
AKIRA has been detected (YARA)
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
AKIRA has been detected
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
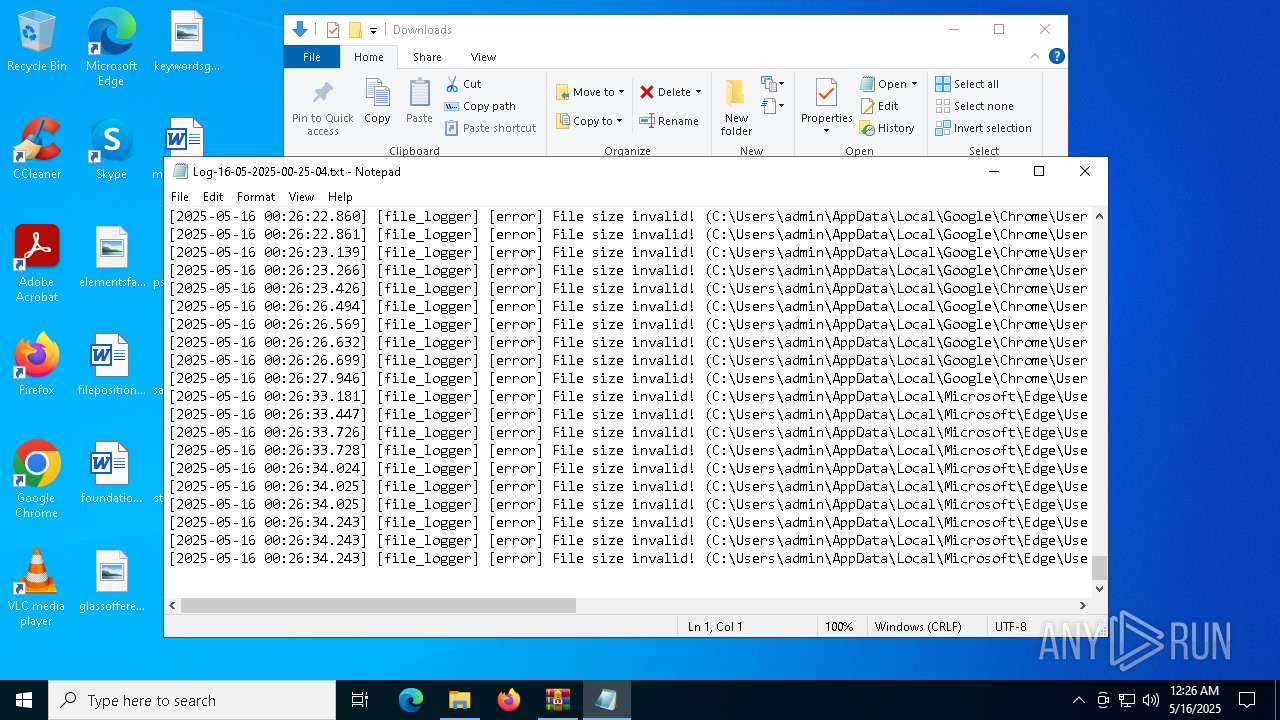
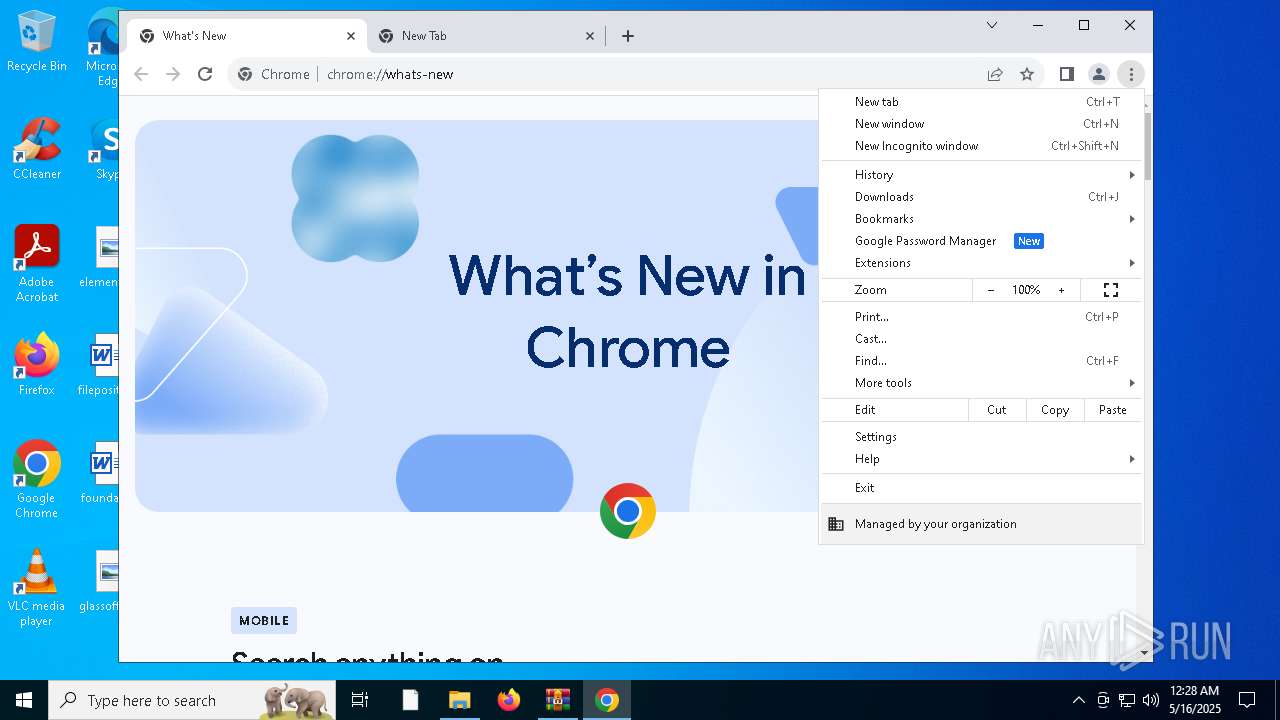
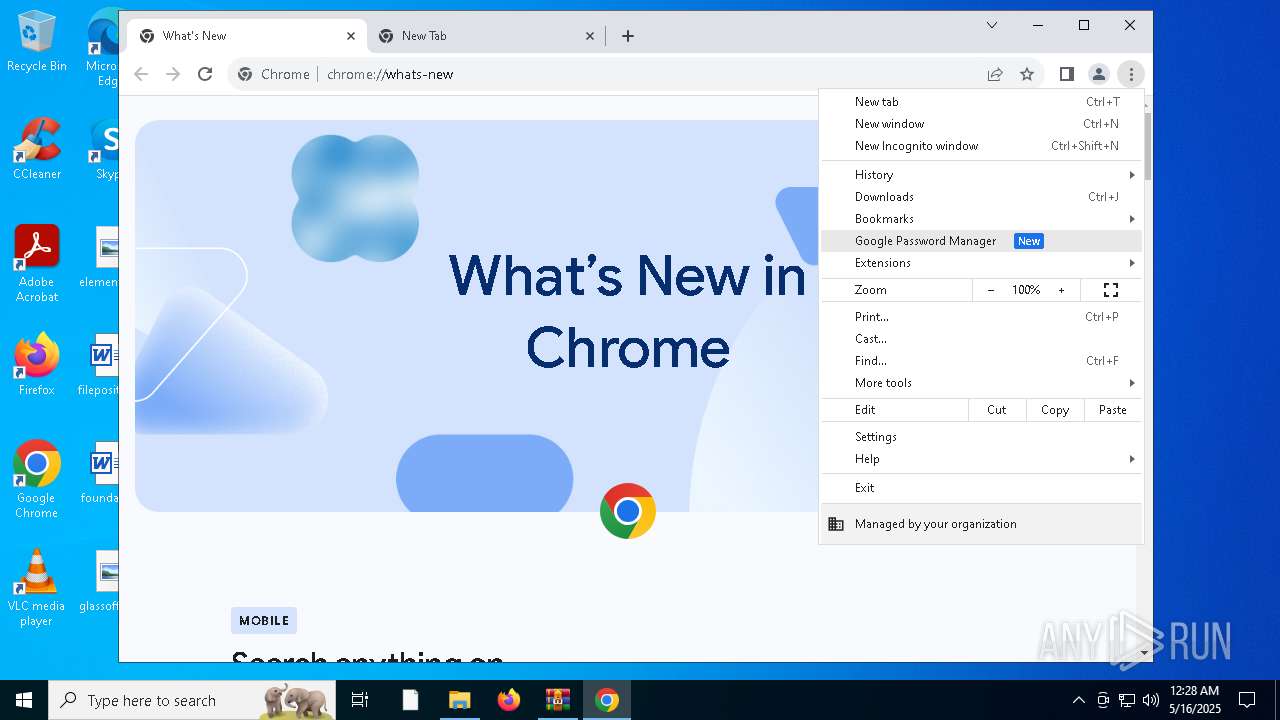
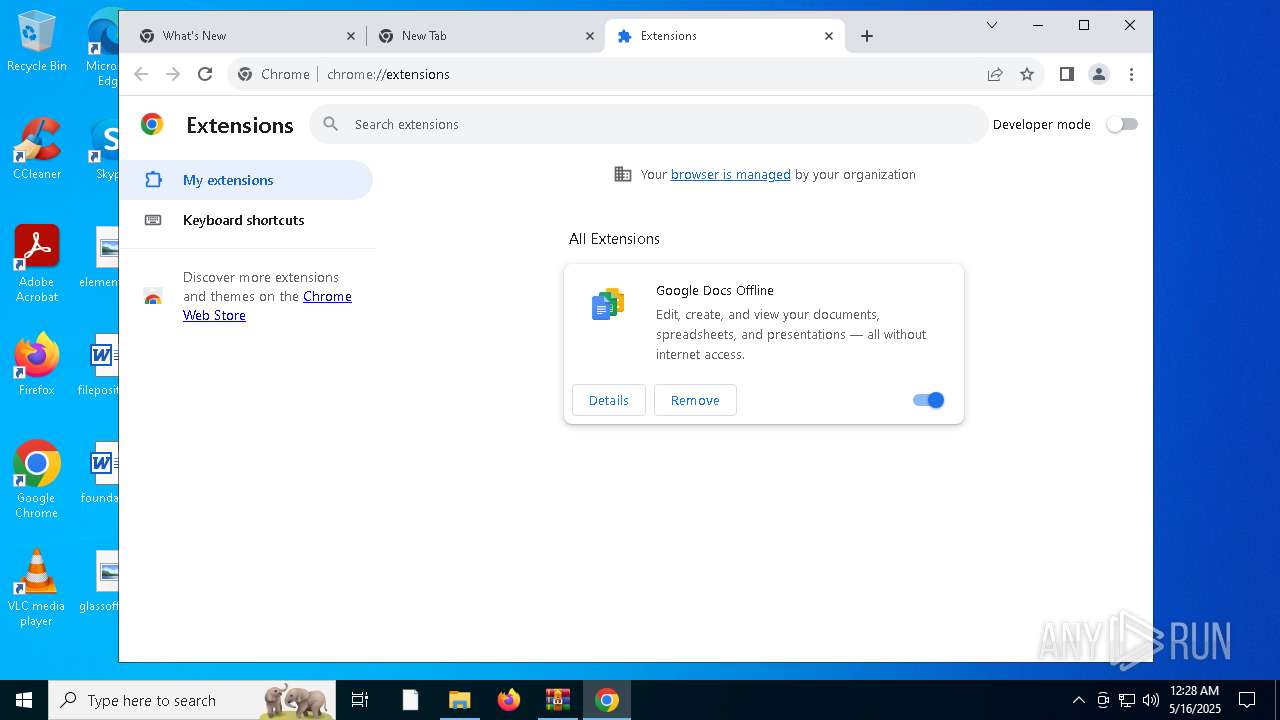
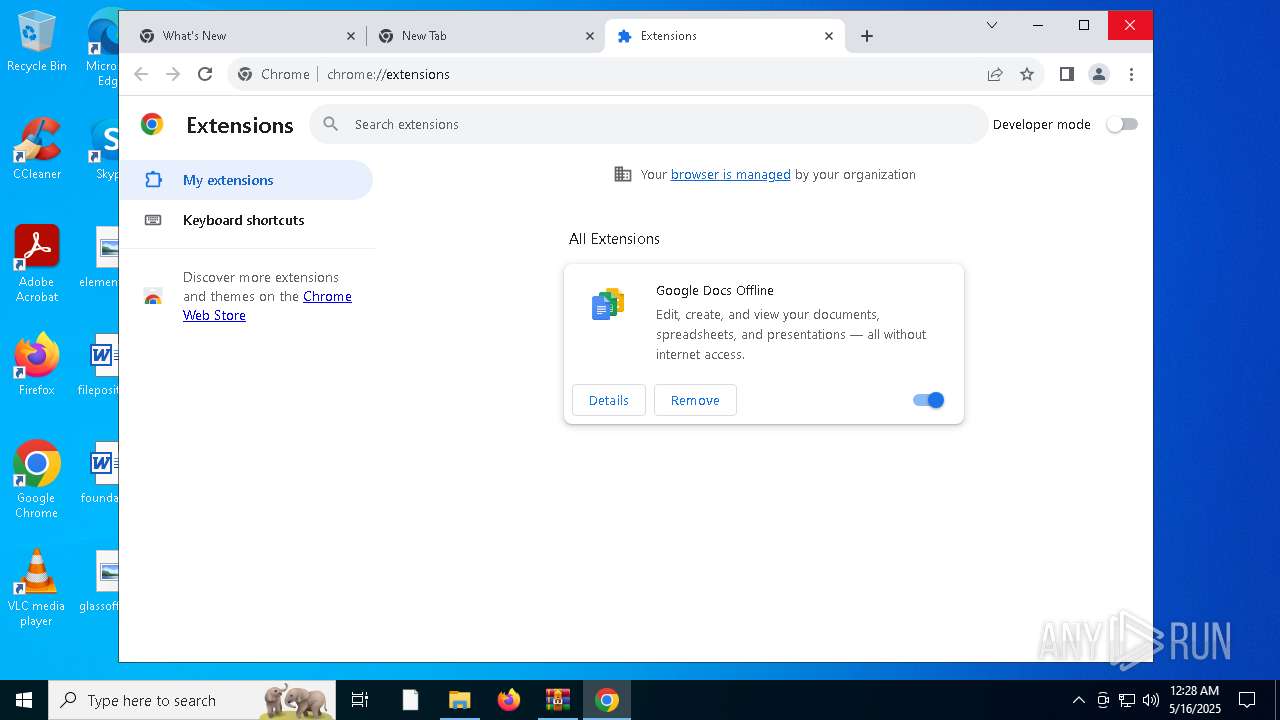
Modifies files in the Chrome extension folder
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
RANSOMWARE has been detected
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 8056)
- powershell.exe (PID: 4728)
Executes as Windows Service
- VSSVC.exe (PID: 6032)
Creates file in the systems drive root
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
Write to the desktop.ini file (may be used to cloak folders)
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
INFO
Checks supported languages
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
Reads the computer name
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
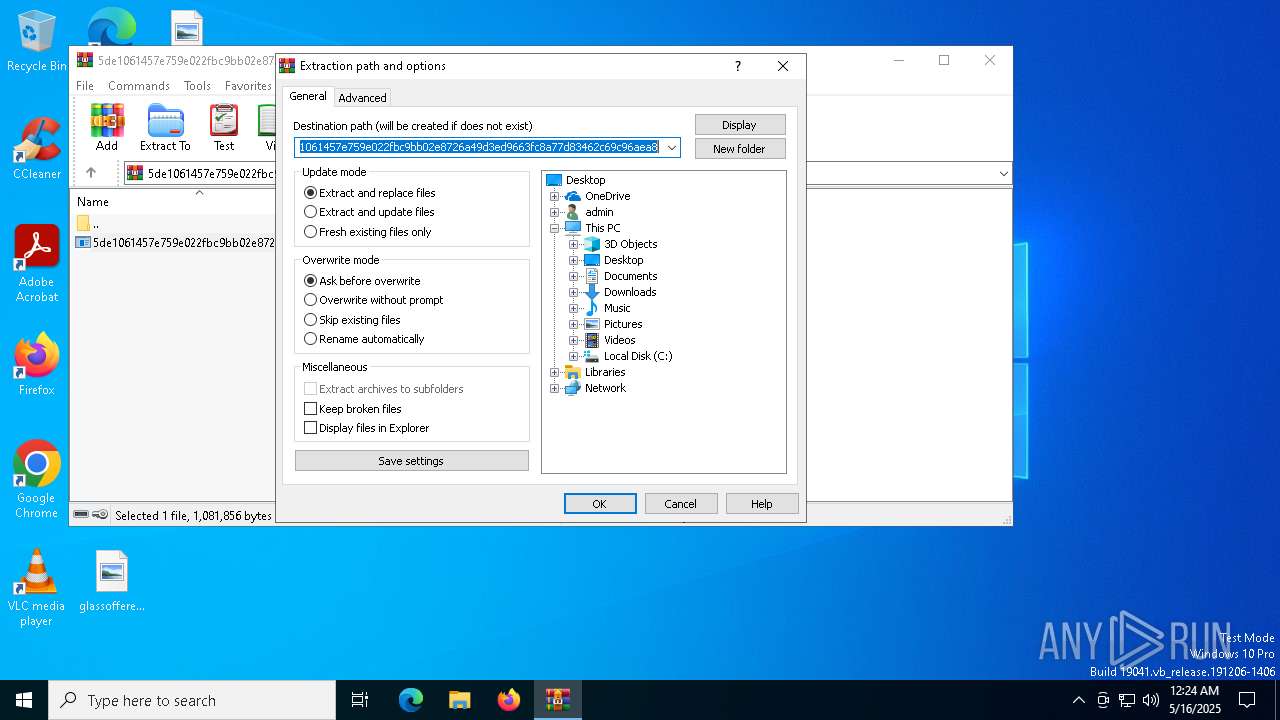
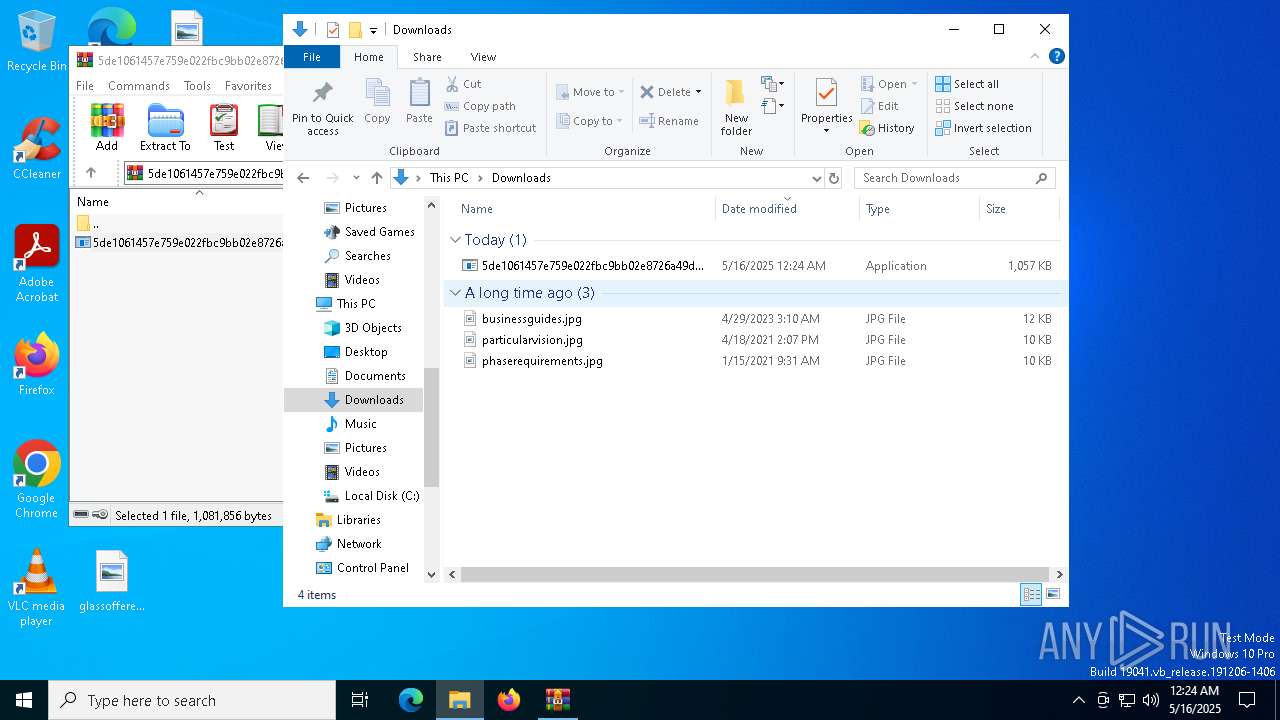
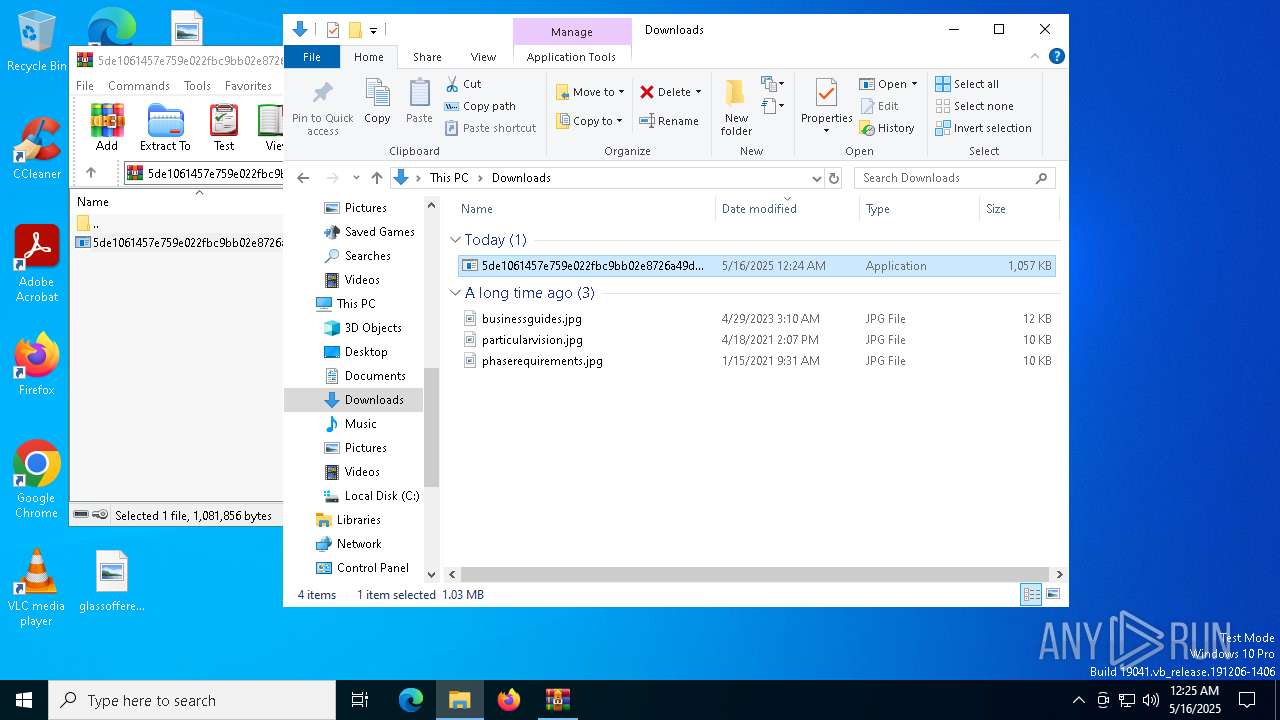
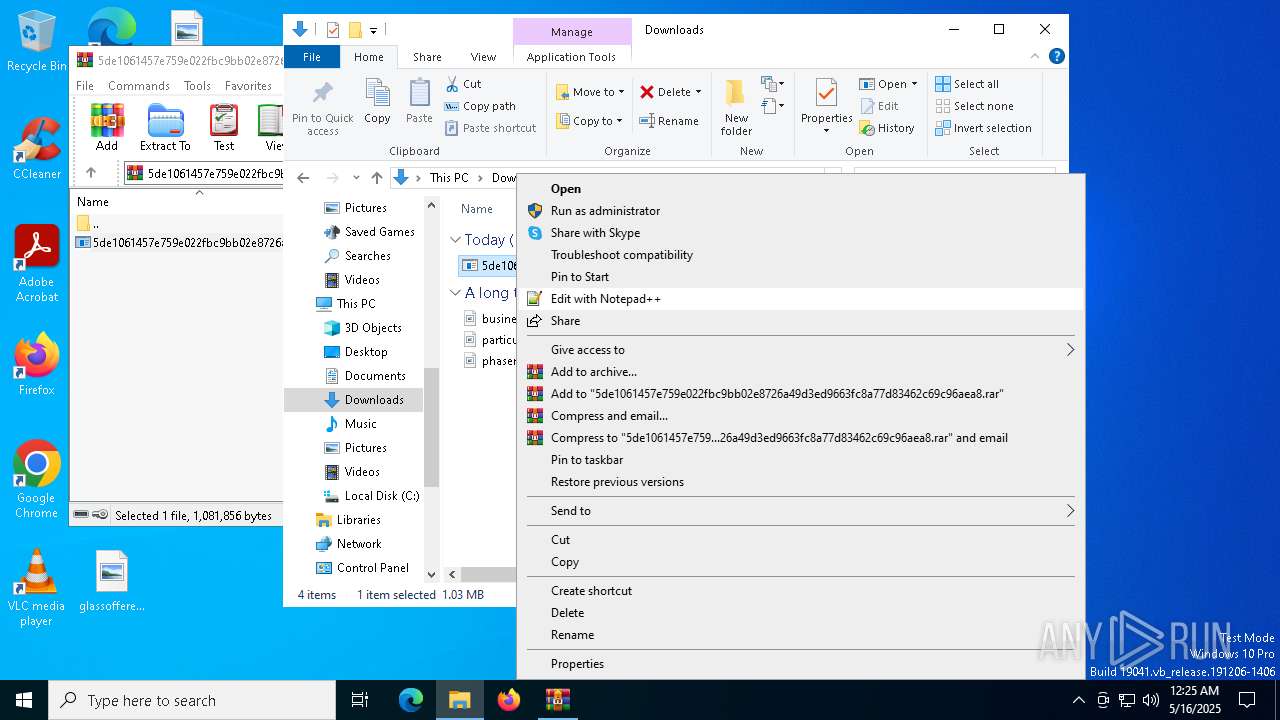
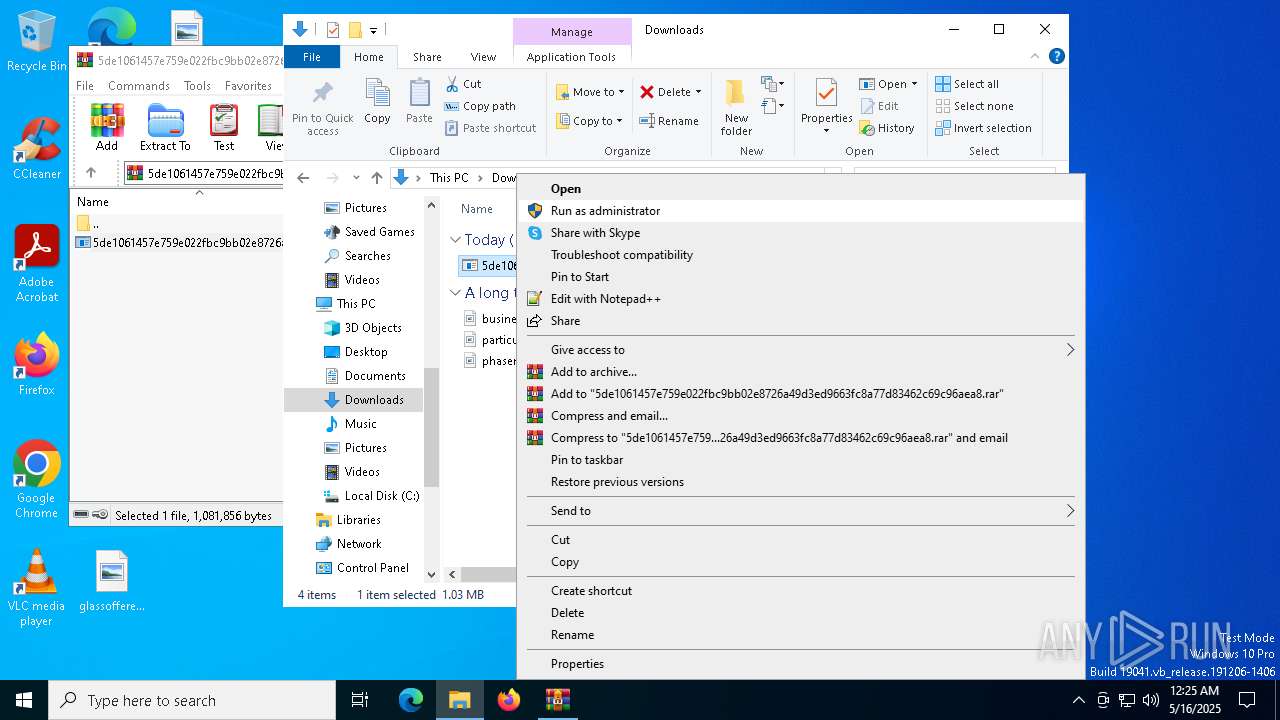
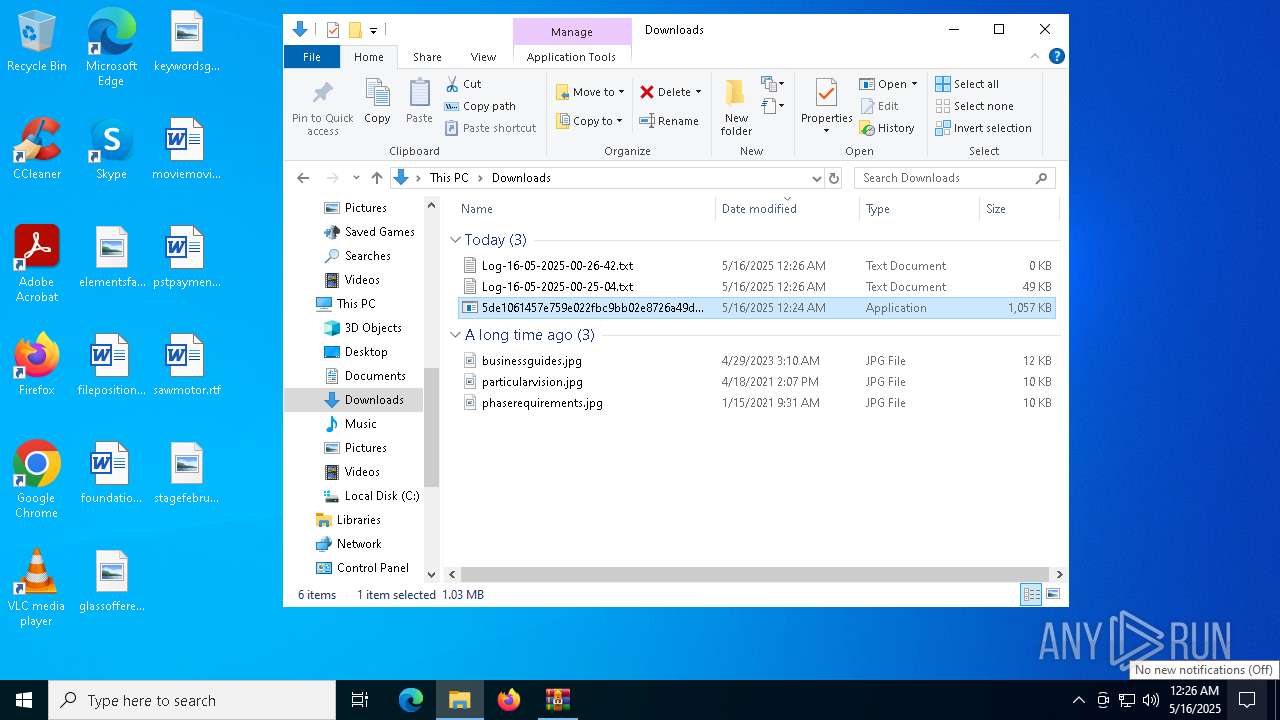
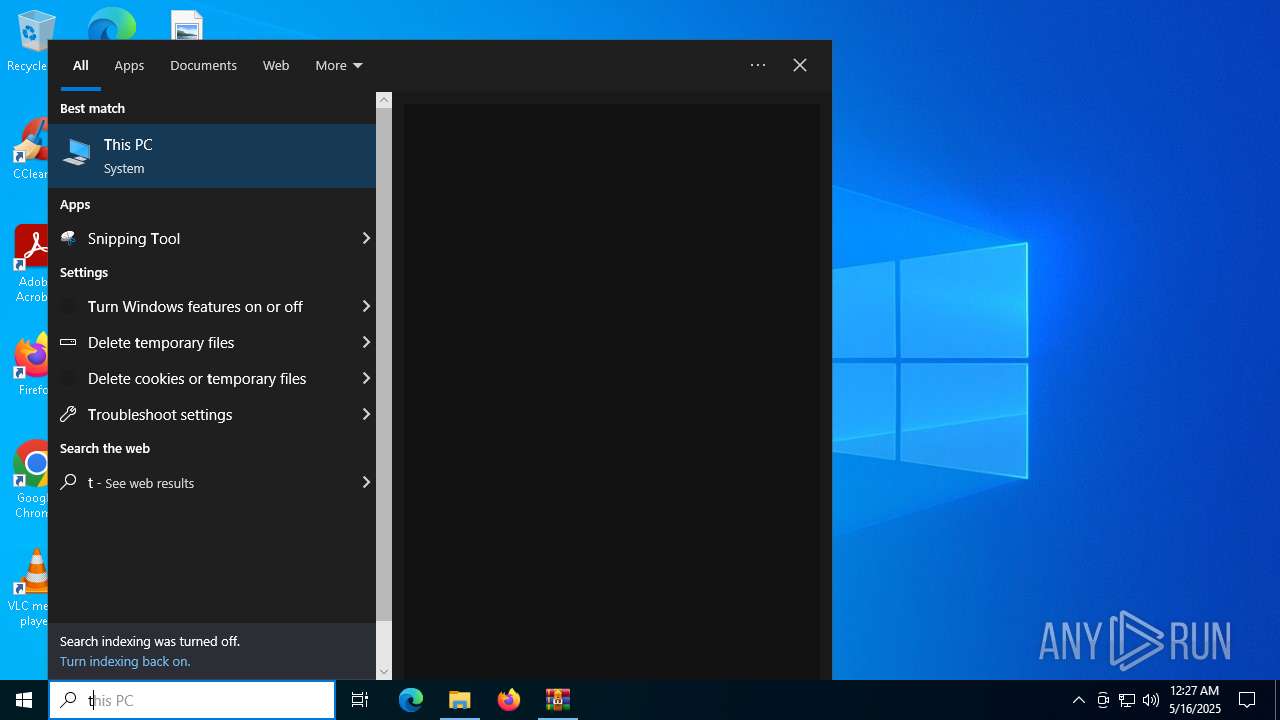
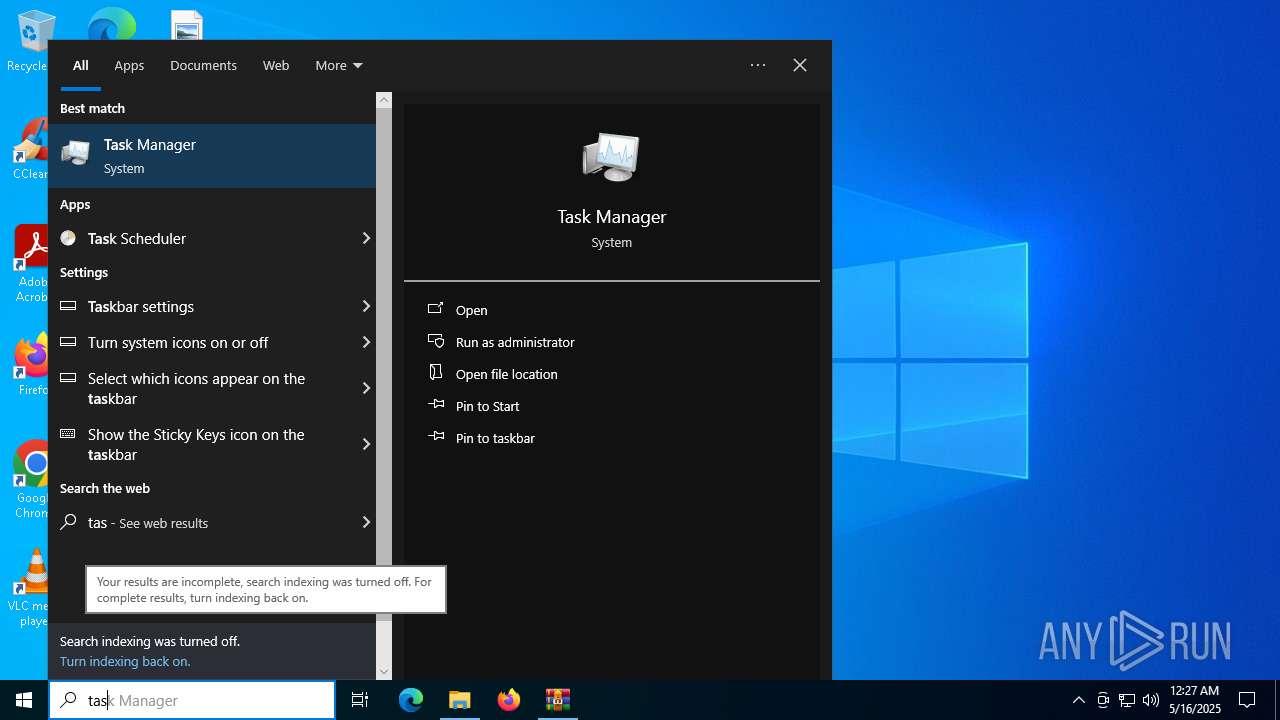
Manual execution by a user
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 7948)
- Taskmgr.exe (PID: 5364)
- chrome.exe (PID: 6016)
- Taskmgr.exe (PID: 1852)
- WINWORD.EXE (PID: 7288)
- notepad.exe (PID: 7928)
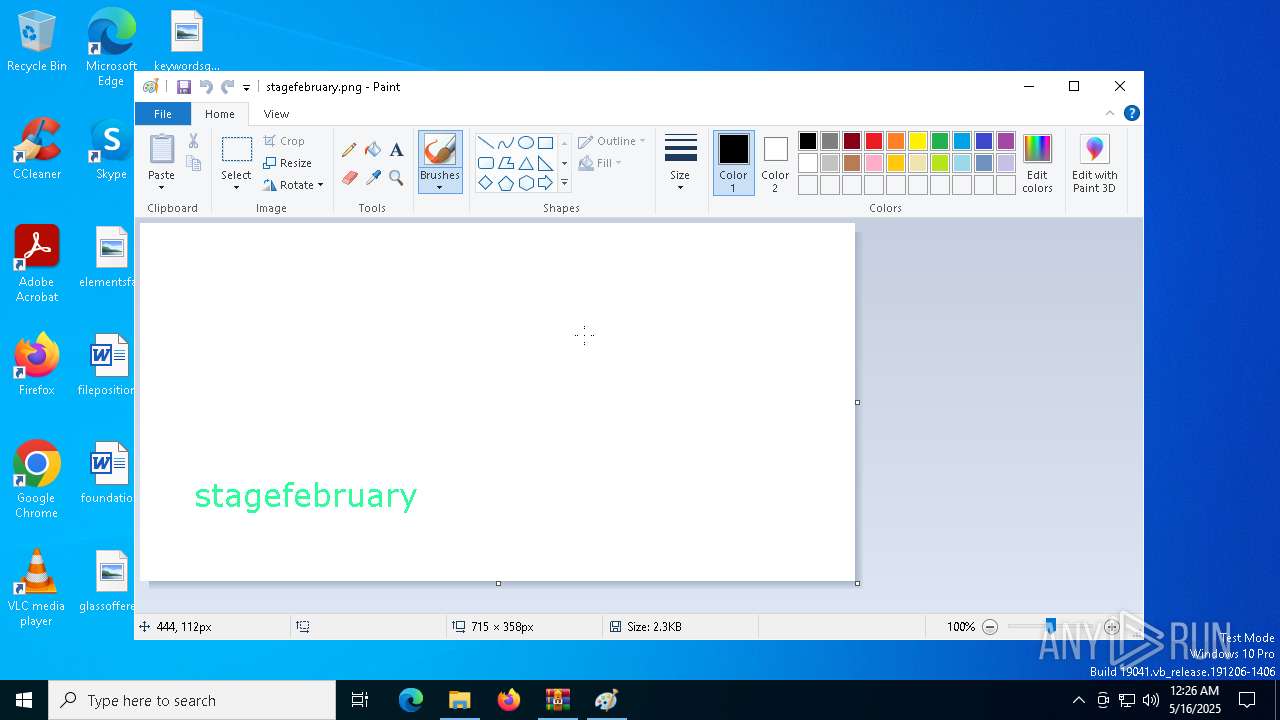
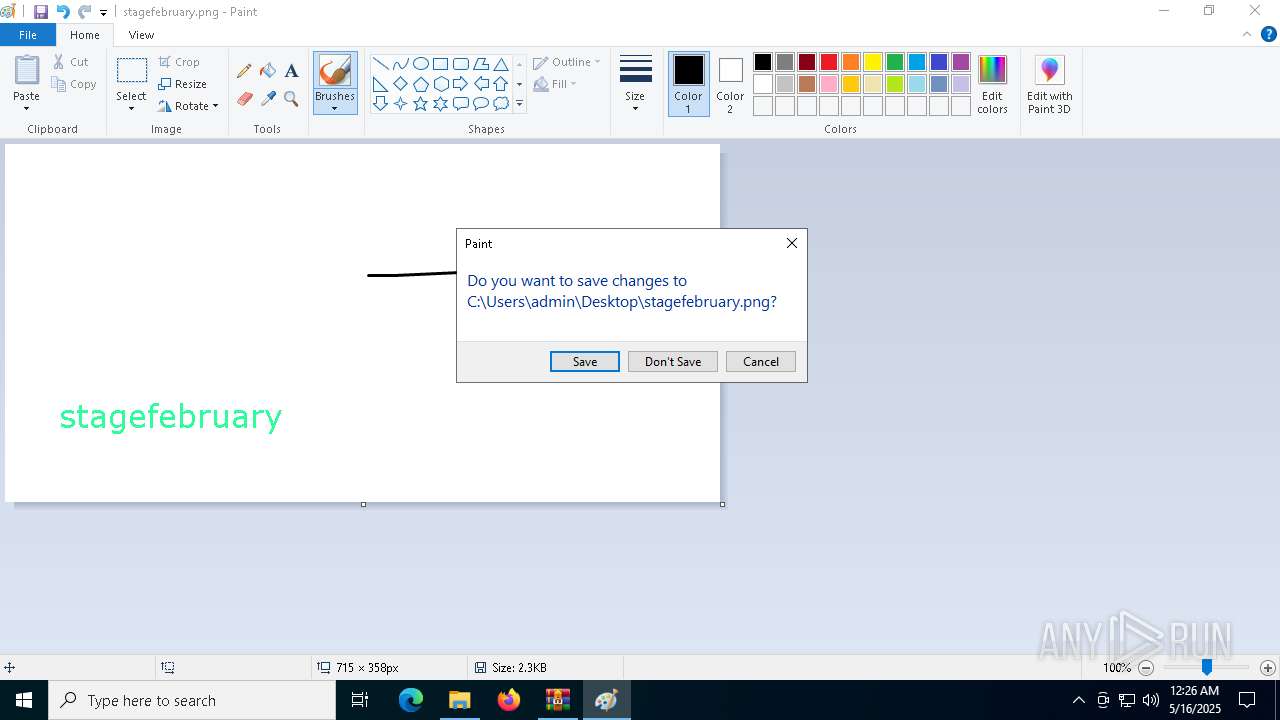
- mspaint.exe (PID: 6240)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8056)
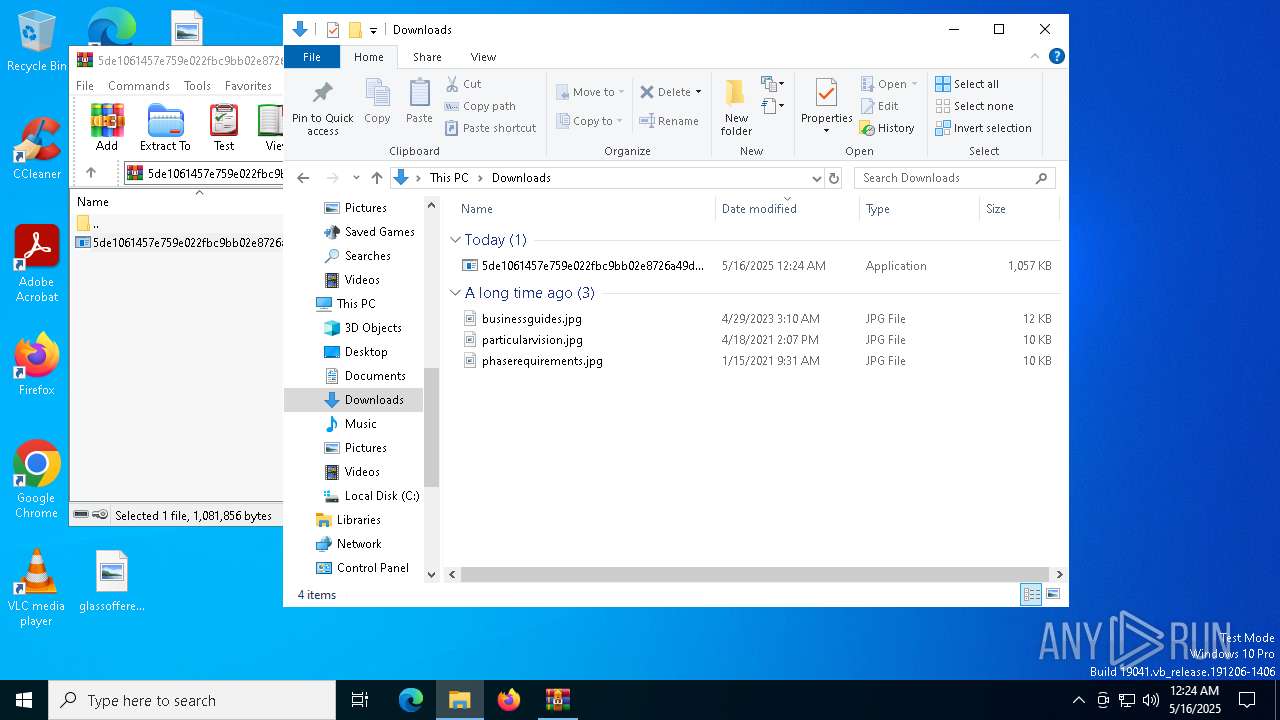
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1512)
Creates files in the program directory
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
Reads the software policy settings
- slui.exe (PID: 7236)
Creates files or folders in the user directory
- 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe (PID: 8016)
Application launched itself
- chrome.exe (PID: 6016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
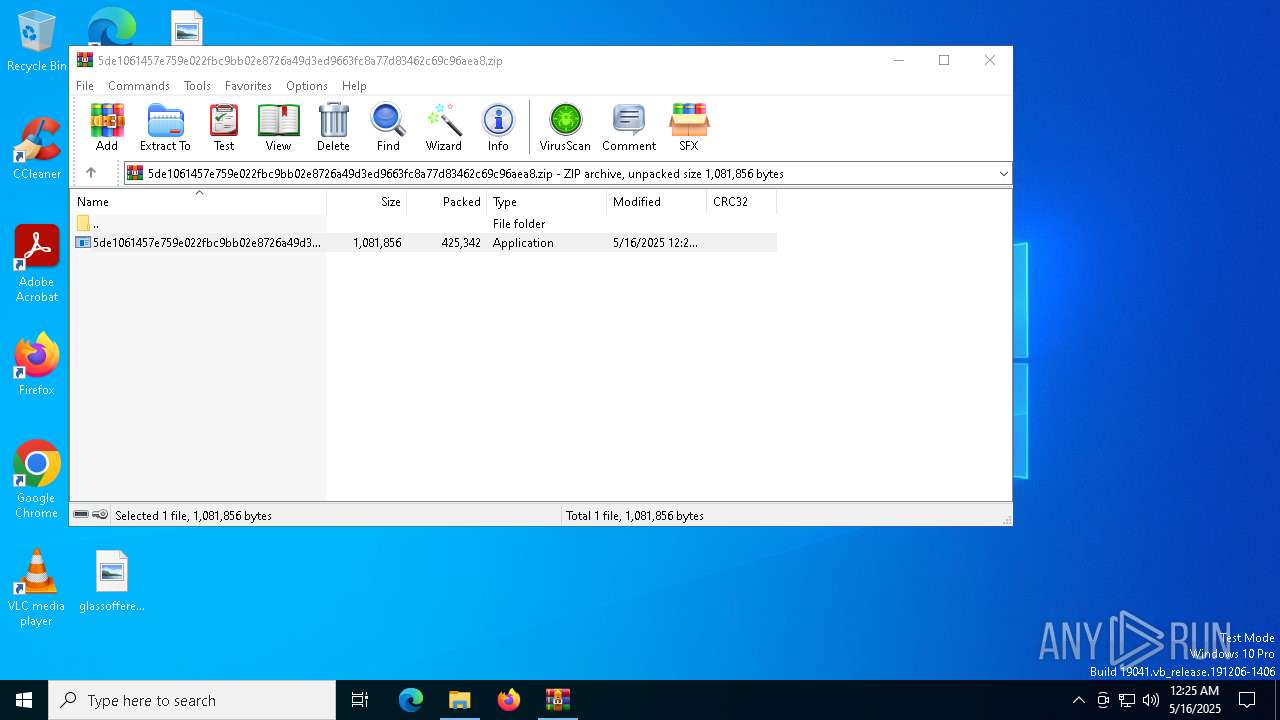
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:16 00:24:00 |
| ZipCRC: | 0xae94f7c9 |
| ZipCompressedSize: | 425342 |
| ZipUncompressedSize: | 1081856 |
| ZipFileName: | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe |
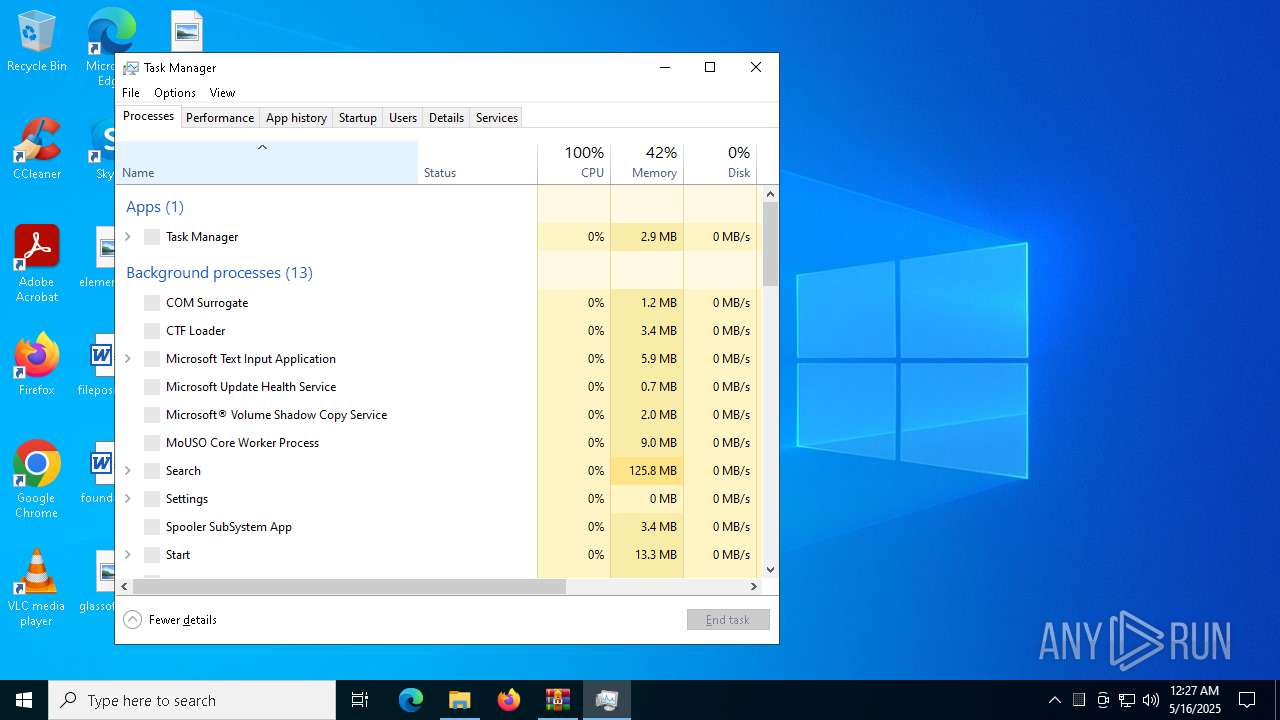
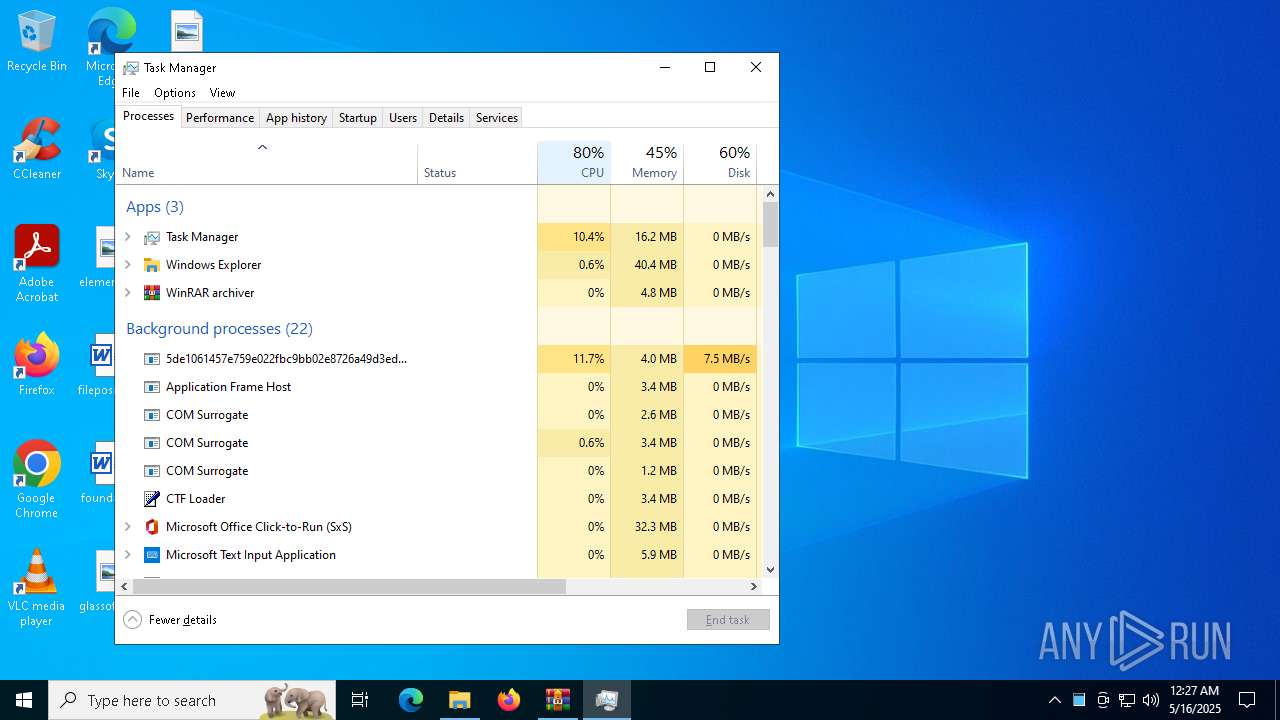
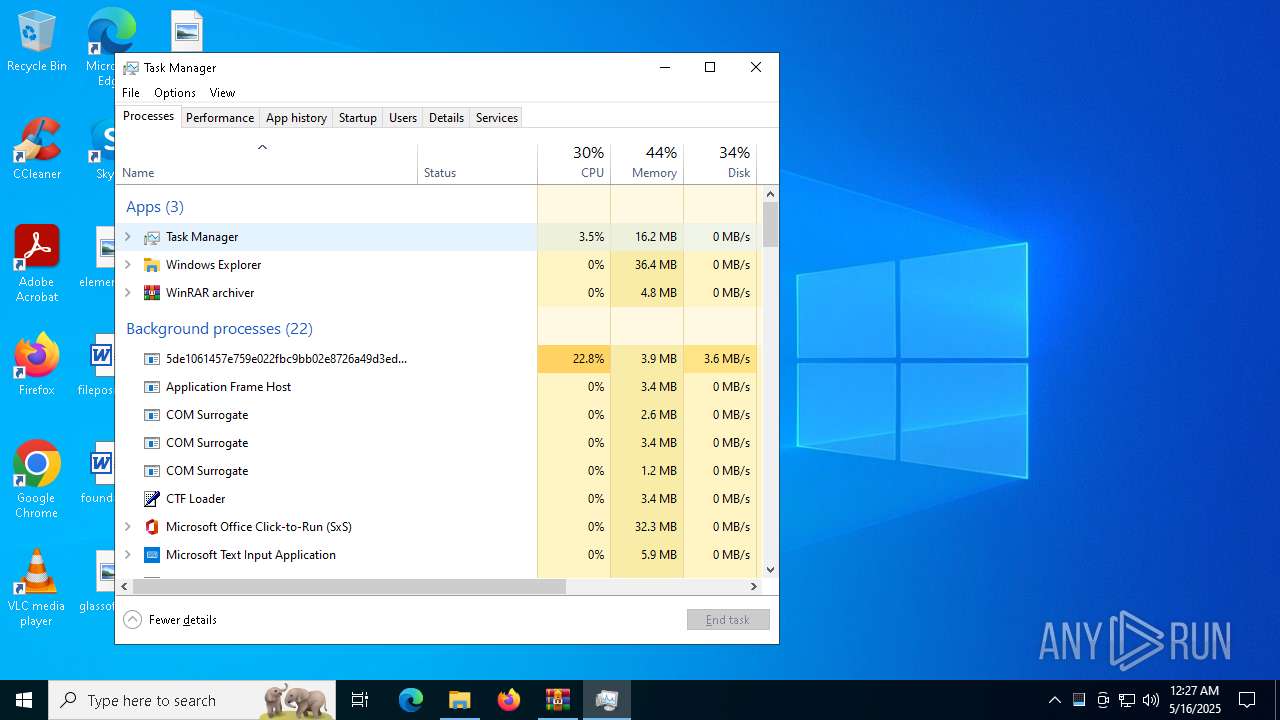
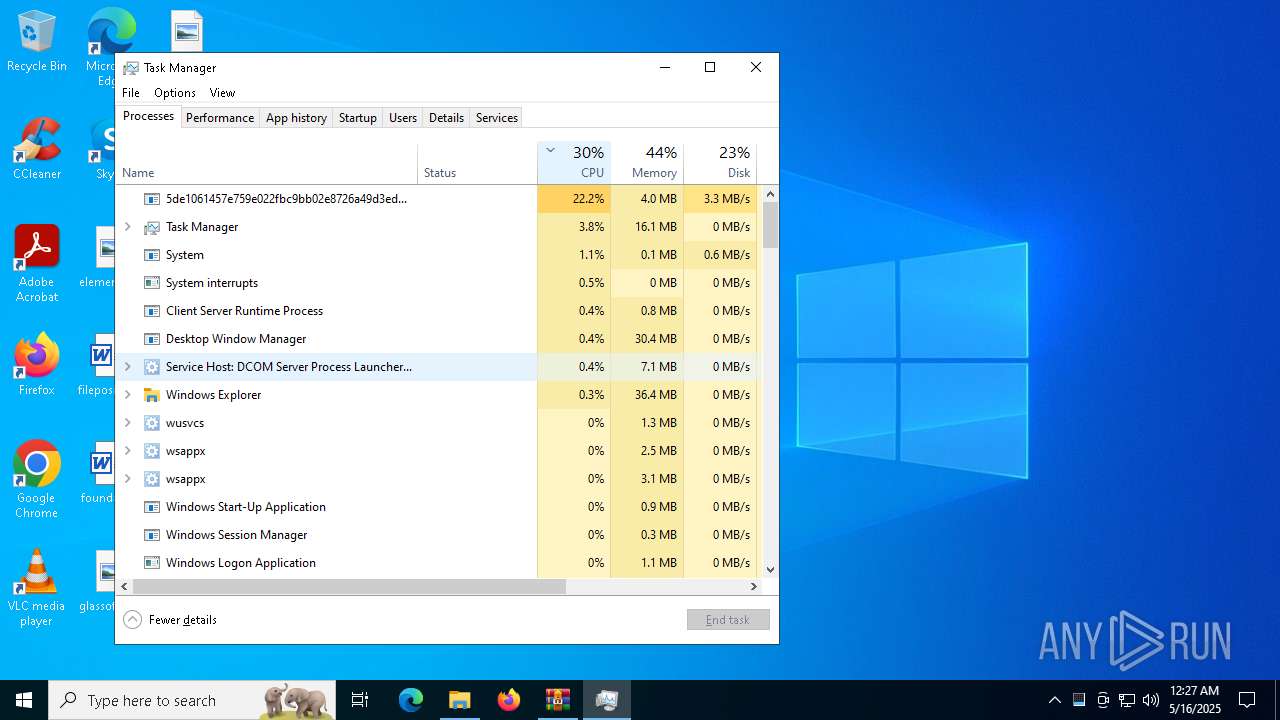
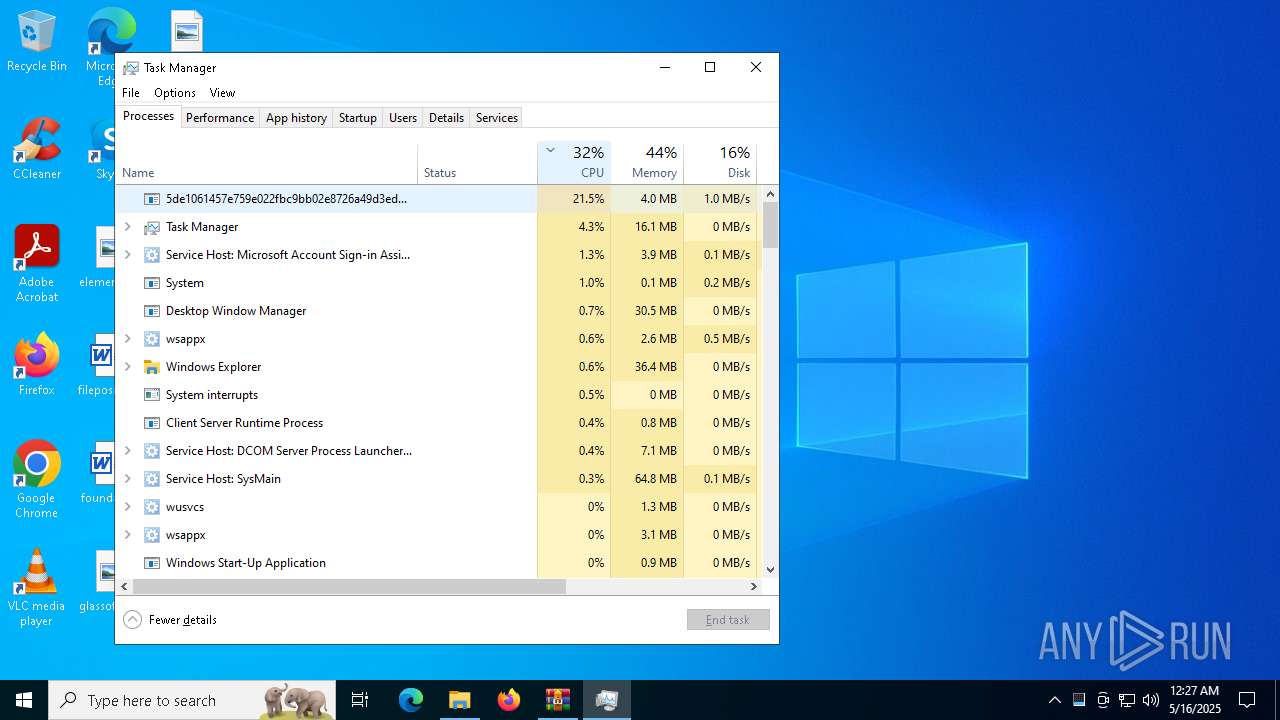
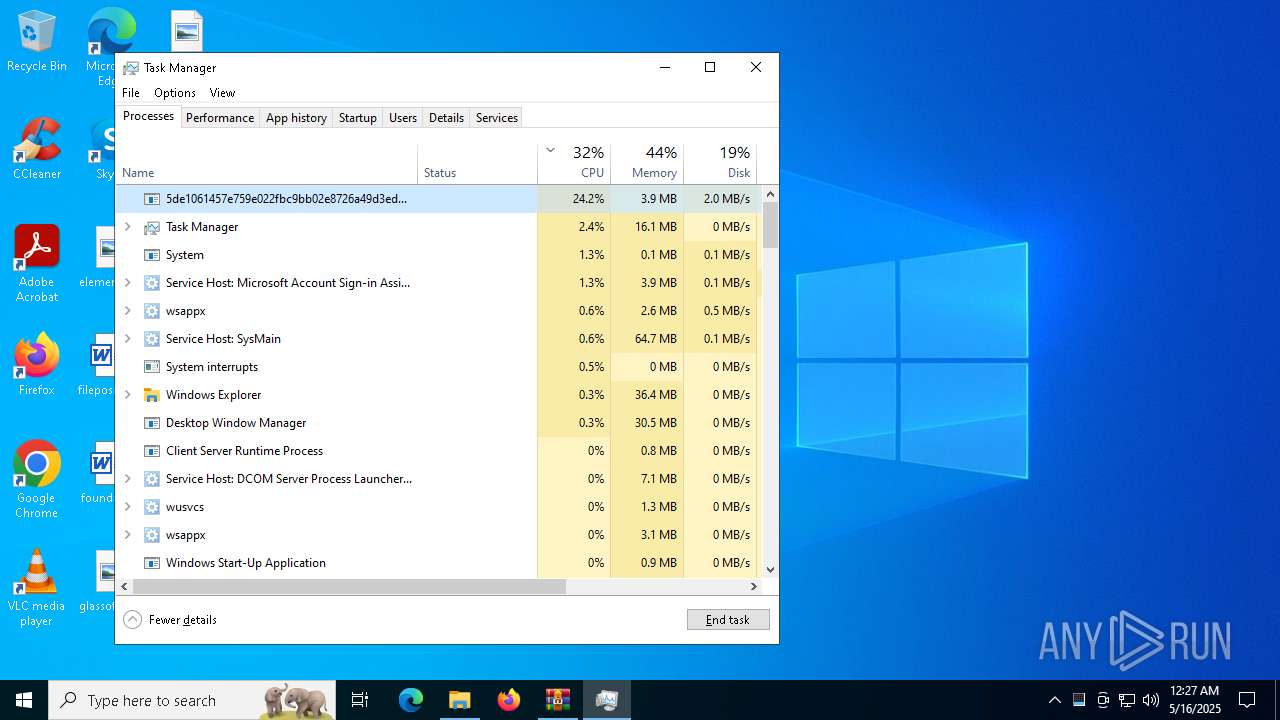
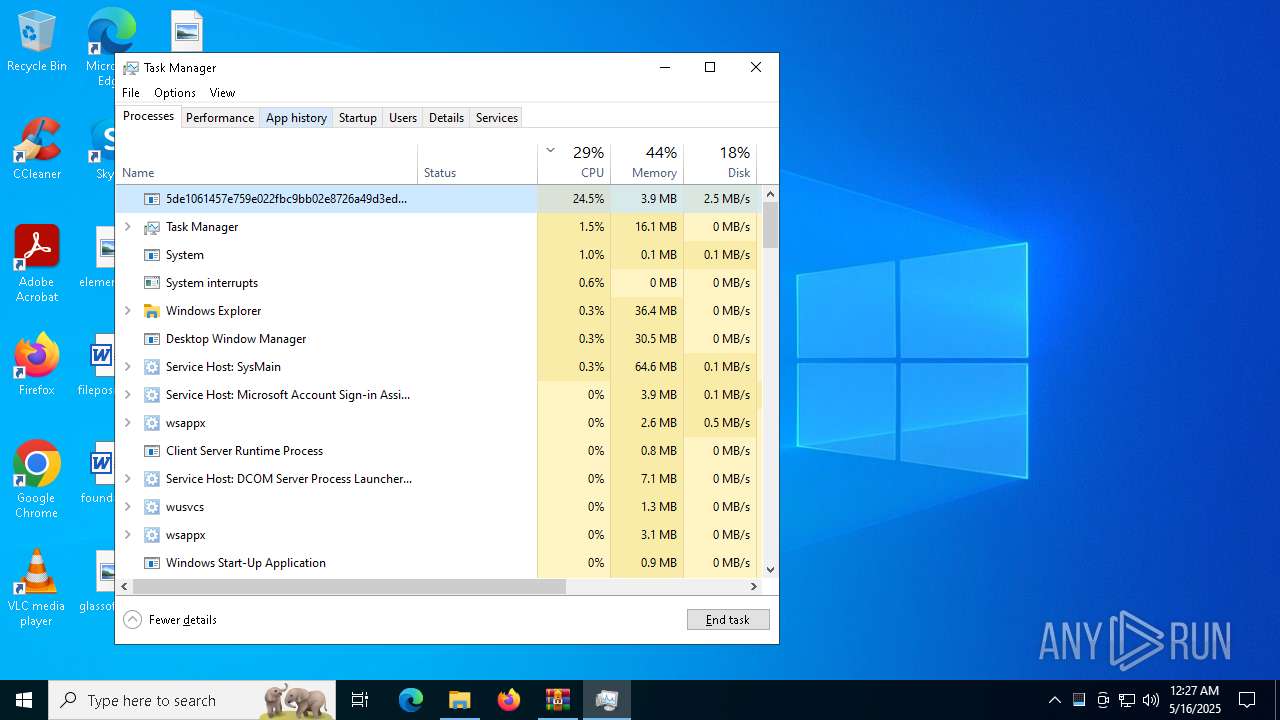
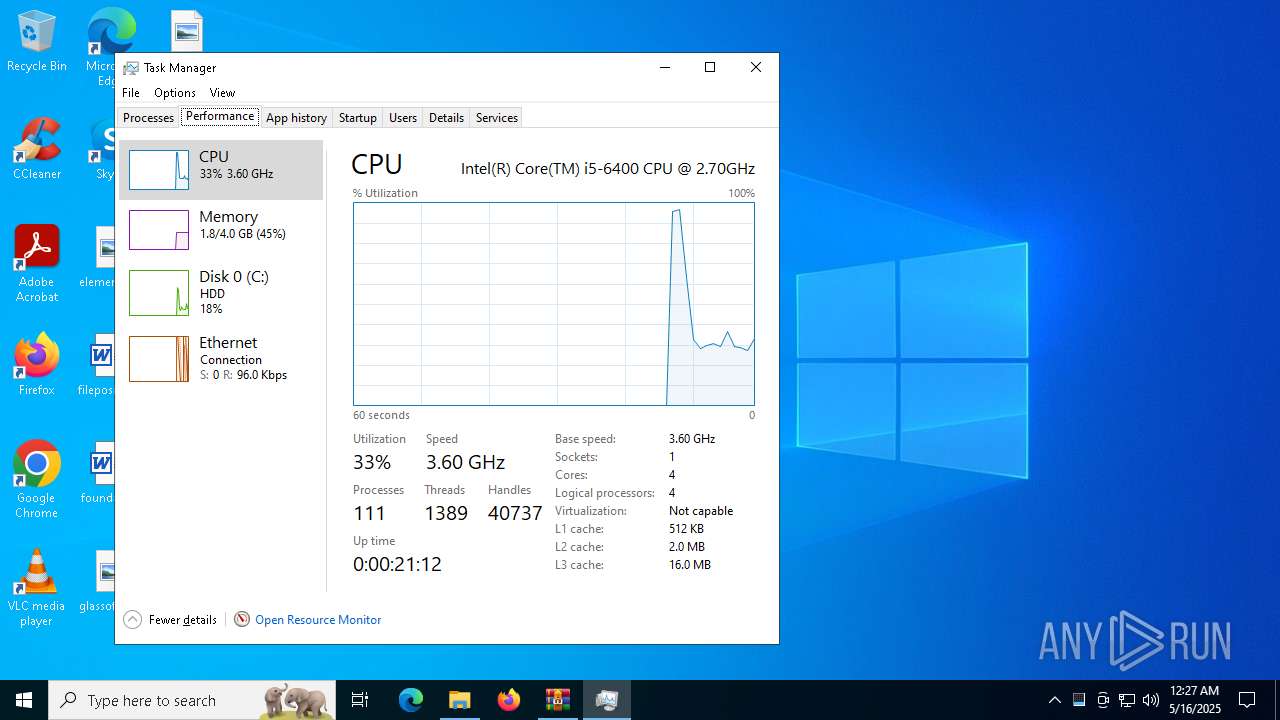
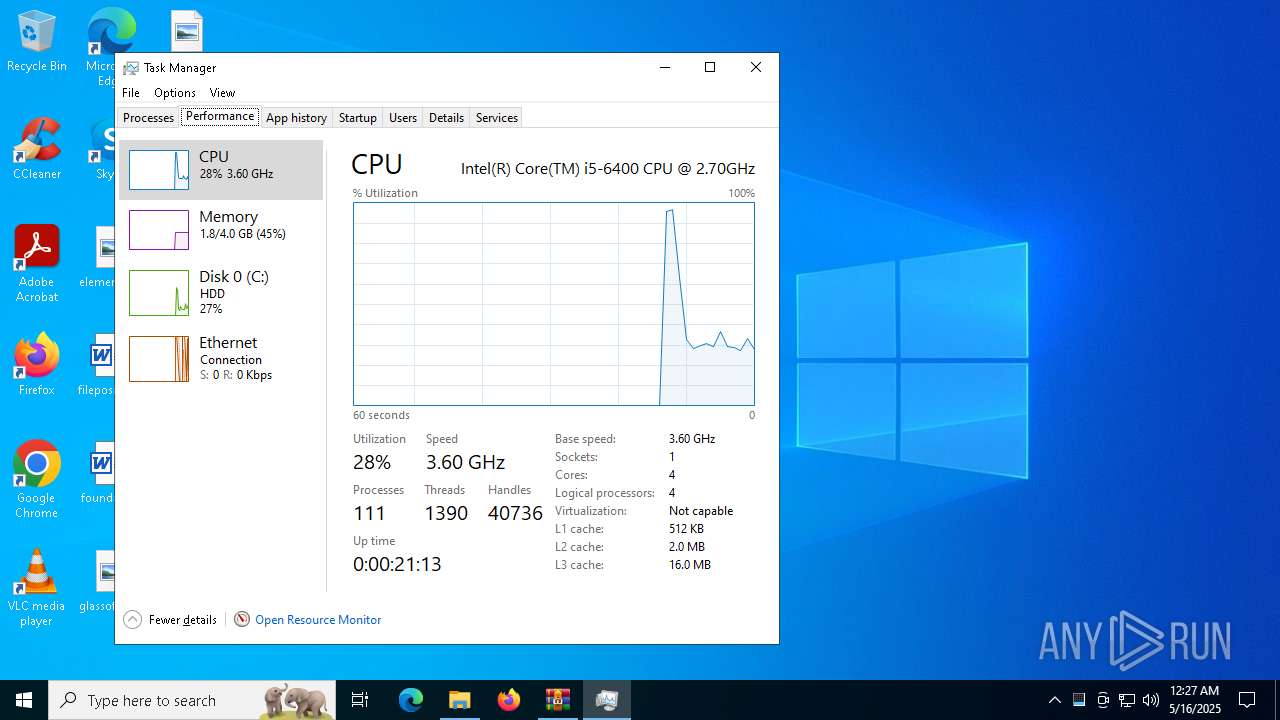
Total processes
200
Monitored processes
52
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5192 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6340 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=6076 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6072 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=23 --mojo-platform-channel-handle=6280 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4836 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
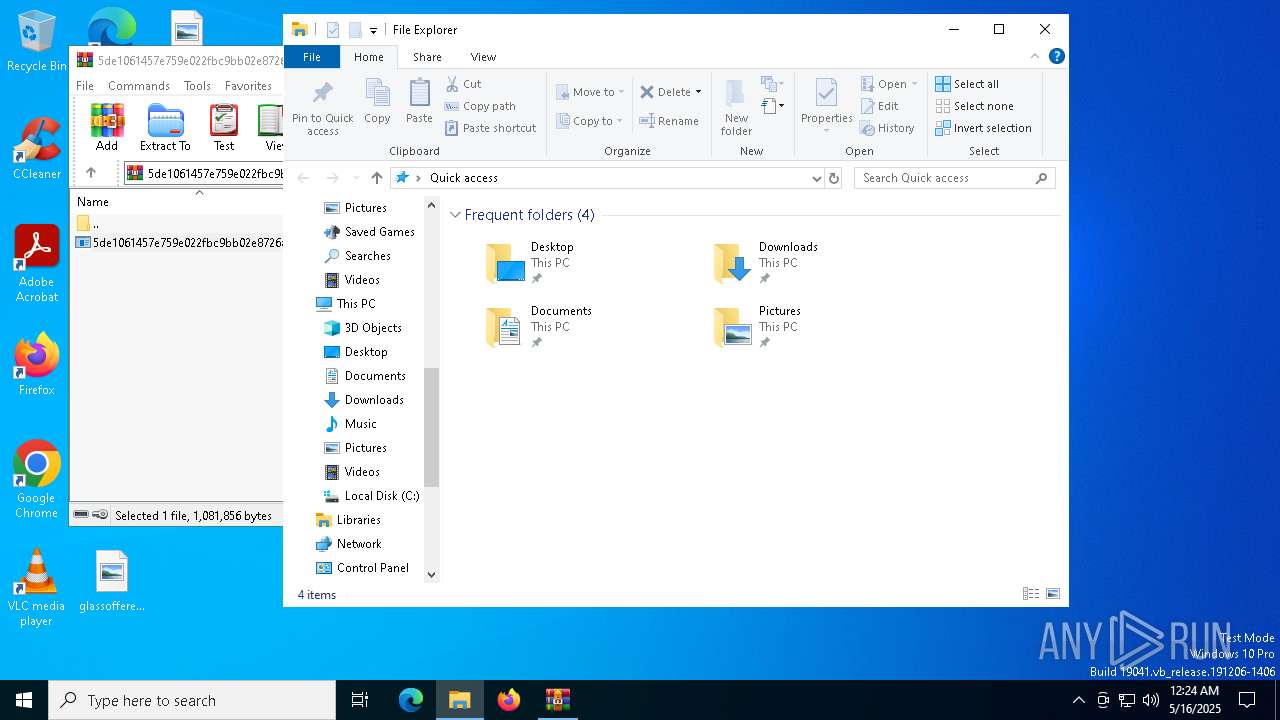
| 1512 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
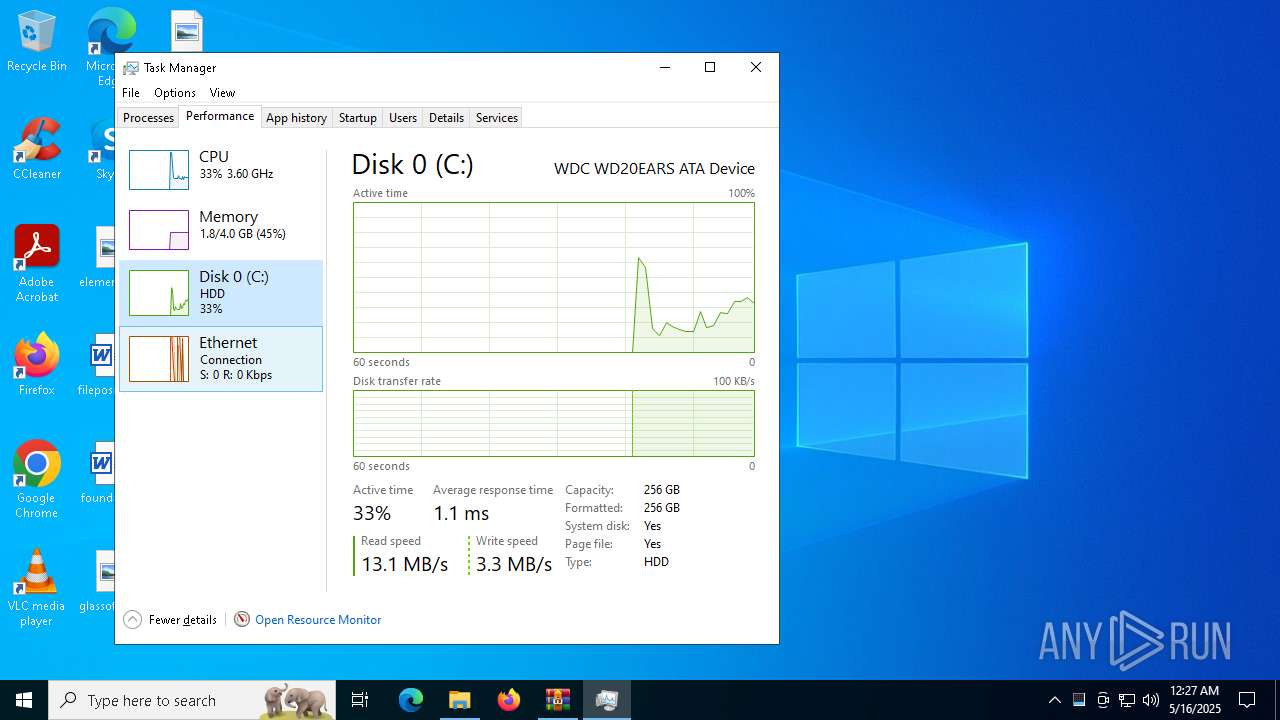
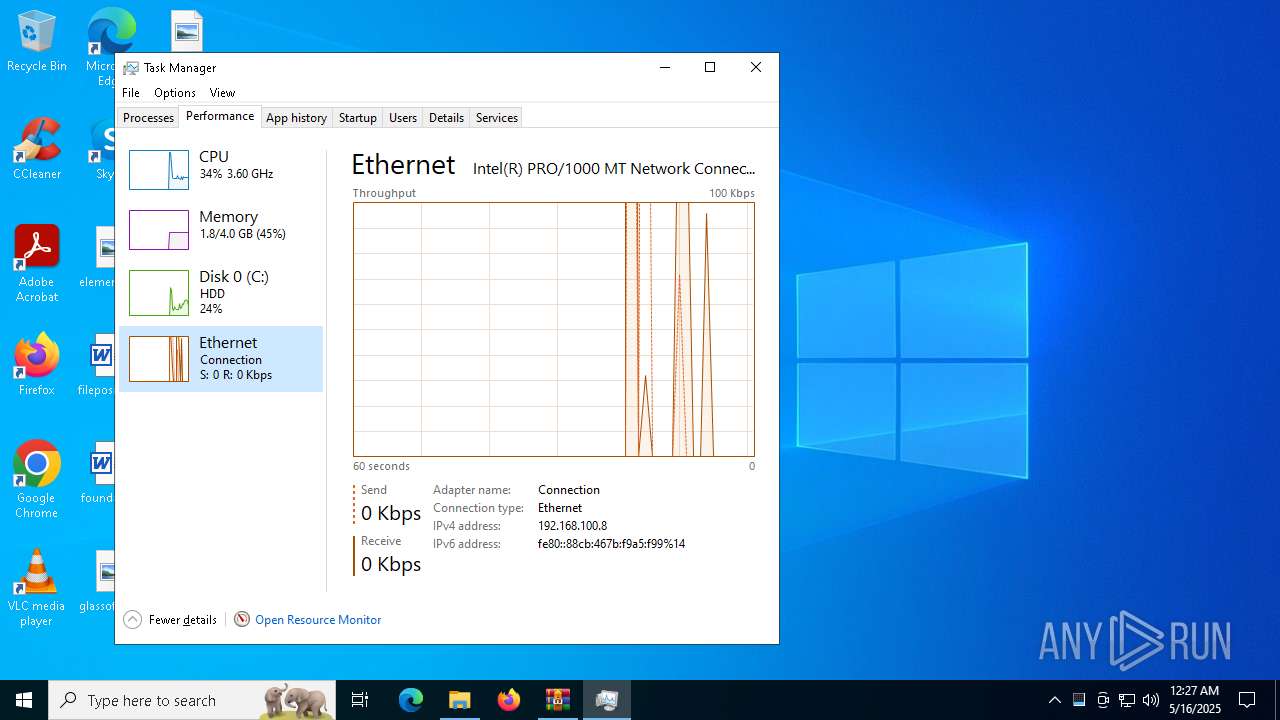
| 1852 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2344 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6088 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3312 --field-trial-handle=1072,i,4935076978249257247,15111812266429779907,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
26 200
Read events
25 777
Write events
365
Delete events
58
Modification events
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.zip | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (1512) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
33
Suspicious files
7 761
Text files
2 721
Unknown types
0
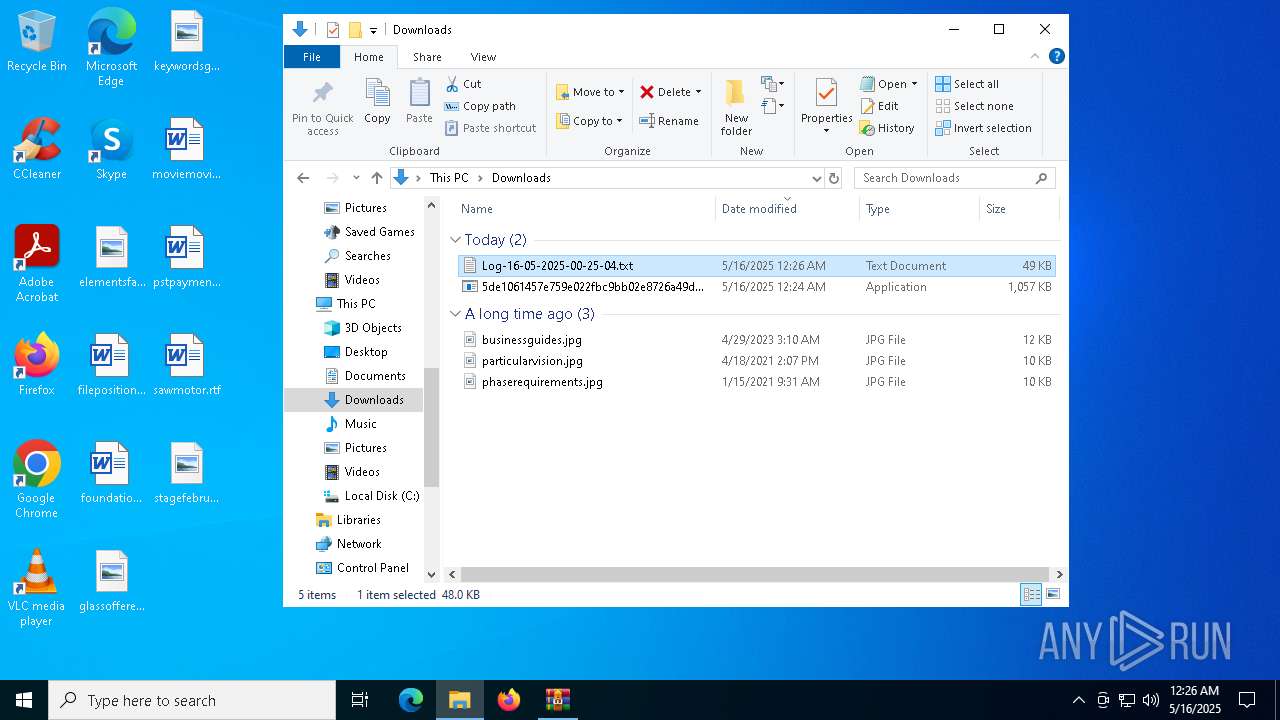
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8016 | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | C:\$WinREAgent\akira_readme.txt | text | |
MD5:6482B5984CC2F0012B452E6BA5D92635 | SHA256:4E0E4FB4266250EBF7F646C6EEFF934491E25D2722CAA1D6FE099D3E50913A57 | |||
| 1512 | WinRAR.exe | C:\Users\admin\Downloads\5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | executable | |
MD5:433DEEDF1091C8EA24E0EBAABFB240FF | SHA256:5DE1061457E759E022FBC9BB02E8726A49D3ED9663FC8A77D83462C69C96AEA8 | |||
| 8056 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pw0oaodm.1pl.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8016 | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | C:\akira_readme.txt | text | |
MD5:6482B5984CC2F0012B452E6BA5D92635 | SHA256:4E0E4FB4266250EBF7F646C6EEFF934491E25D2722CAA1D6FE099D3E50913A57 | |||
| 8056 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_elgj3gx3.5q0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8016 | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | C:\$WinREAgent\Scratch\akira_readme.txt | text | |
MD5:6482B5984CC2F0012B452E6BA5D92635 | SHA256:4E0E4FB4266250EBF7F646C6EEFF934491E25D2722CAA1D6FE099D3E50913A57 | |||
| 8016 | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | C:\$WinREAgent\Backup\location.txt.akira | binary | |
MD5:41D4966C8B3F3DEE2F49E2506E9B30A7 | SHA256:1CB0CEB4334CA13D432CA3A27014CF62D60B43B667E92BD16D886C60A81C13F9 | |||
| 8016 | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | C:\$WinREAgent\Backup\ReAgent.xml.akira | binary | |
MD5:DBD5553D56DC083A4C4DD7547D03394B | SHA256:0FC4A3E1EB39514076AD1185C7742C4B16172331983CAB3DA9F1EFFE694DE157 | |||
| 8016 | 5de1061457e759e022fbc9bb02e8726a49d3ed9663fc8a77d83462c69c96aea8.exe | C:\$WinREAgent\Backup\akira_readme.txt | text | |
MD5:6482B5984CC2F0012B452E6BA5D92635 | SHA256:4E0E4FB4266250EBF7F646C6EEFF934491E25D2722CAA1D6FE099D3E50913A57 | |||
| 8056 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:62F103838726389CA5D213D308A43463 | SHA256:6556F9971E7F98F00838F39F91541EC5CD16931C6CFAC5DB8086729BEDE86C33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
74
DNS requests
73
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7784 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7288 | WINWORD.EXE | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7484 | chrome.exe | GET | 302 | 142.250.186.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7484 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7484 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |