| File name: | GM2SC_random.exe |
| Full analysis: | https://app.any.run/tasks/c7fec258-5432-4d13-b493-6ae5861f665e |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | January 18, 2025, 17:19:17 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 7 sections |
| MD5: | FA93EE30BA0FF259954673B85347CF2E |
| SHA1: | A1EA1E175E4585FCB0345EF5A00D4B047384DD73 |
| SHA256: | 8E04D767B94A24732BE0868059F2D2FD09B86E73FAEF0C753E8AA6B604630CED |
| SSDEEP: | 98304:Il4fERgKGmsltDOVCcYDeDIT48QWJ8dpt1HDfrHtj9azvT1K83HyB63s3xsJT6Ho:pOp |
MALICIOUS
AMADEY mutex has been found
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- axplong.exe (PID: 4420)
- skotes.exe (PID: 7220)
- ITM0U1Z0EXRLGHCZOSI.exe (PID: 3260)
- axplong.exe (PID: 2736)
- skotes.exe (PID: 6376)
Connects to the CnC server
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- svchost.exe (PID: 2192)
- skotes.exe (PID: 2076)
- 021949f0ac.exe (PID: 6296)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
AMADEY has been detected (SURICATA)
- axplong.exe (PID: 4244)
- skotes.exe (PID: 2076)
StealC has been detected
- aeb8a77c3e.exe (PID: 5464)
- 021949f0ac.exe (PID: 6296)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
Changes the autorun value in the registry
- axplong.exe (PID: 4244)
- skotes.exe (PID: 2076)
STEALC has been detected (SURICATA)
- aeb8a77c3e.exe (PID: 5464)
- 021949f0ac.exe (PID: 6296)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
AMADEY has been detected (YARA)
- axplong.exe (PID: 4244)
- skotes.exe (PID: 2076)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2192)
- f2560da6b4.exe (PID: 7812)
Actions looks like stealing of personal data
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- f2560da6b4.exe (PID: 7812)
- 84d8863aac.exe (PID: 6844)
LUMMA mutex has been found
- 54d9e0f2b2.exe (PID: 4512)
- c2a795d497.exe (PID: 6076)
- f2560da6b4.exe (PID: 7812)
- 84d8863aac.exe (PID: 6844)
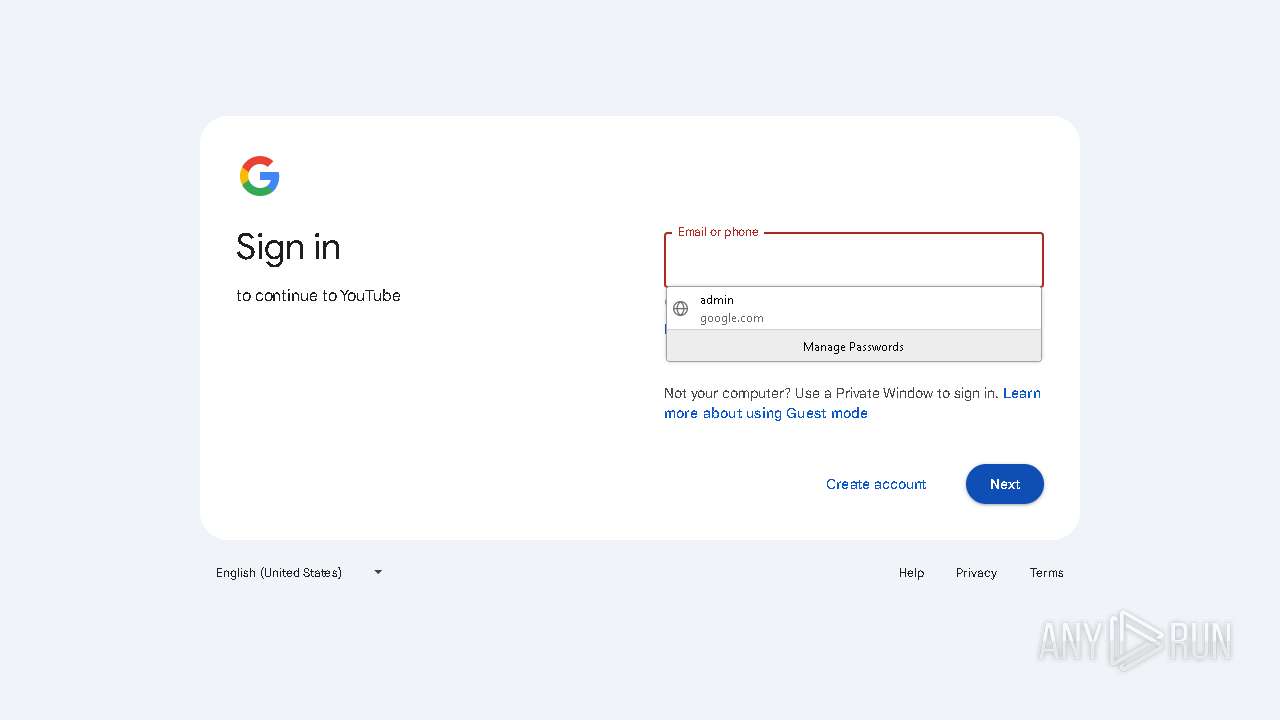
Steals credentials from Web Browsers
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- f2560da6b4.exe (PID: 7812)
- 84d8863aac.exe (PID: 6844)
Possible tool for stealing has been detected
- firefox.exe (PID: 7088)
- 03c656ca1f.exe (PID: 6448)
GCLEANER has been detected (SURICATA)
- 969778179c.exe (PID: 848)
LUMMA has been detected (YARA)
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
Bypass execution policy to execute commands
- powershell.exe (PID: 7896)
Changes powershell execution policy (Bypass)
- c2a795d497.exe (PID: 6076)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7024)
Run PowerShell with an invisible window
- powershell.exe (PID: 3696)
Request from PowerShell that ran from MSHTA.EXE
- powershell.exe (PID: 3696)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 3696)
Disables Windows Defender
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
Executing a file with an untrusted certificate
- eda85f68f1.exe (PID: 8160)
- servicebrowserv5.exe (PID: 5092)
Changes the Windows auto-update feature
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
SUSPICIOUS
Reads the BIOS version
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- 969778179c.exe (PID: 848)
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- 021949f0ac.exe (PID: 6296)
- skotes.exe (PID: 7220)
- axplong.exe (PID: 4420)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- ITM0U1Z0EXRLGHCZOSI.exe (PID: 3260)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
- skotes.exe (PID: 6376)
- axplong.exe (PID: 2736)
Executable content was dropped or overwritten
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- 969778179c.exe (PID: 848)
- vx72NG3gHzoM.exe (PID: 7948)
- vx72NG3gHzoM.tmp (PID: 7968)
- mobilemediaplayer5.exe (PID: 8116)
- 54d9e0f2b2.exe (PID: 4512)
- powershell.exe (PID: 3696)
- eda85f68f1.exe (PID: 8160)
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
- cmd.exe (PID: 7772)
Starts itself from another location
- GM2SC_random.exe (PID: 3140)
- 571439c8b1.exe (PID: 3208)
- Adobe QT32 Server.exe (PID: 7012)
Reads security settings of Internet Explorer
- axplong.exe (PID: 4244)
- GM2SC_random.exe (PID: 3140)
- aeb8a77c3e.exe (PID: 5464)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- 021949f0ac.exe (PID: 6296)
- fef09d218e.exe (PID: 6876)
- 969778179c.exe (PID: 848)
- mobilemediaplayer5.exe (PID: 8116)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
Contacting a server suspected of hosting an CnC
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- skotes.exe (PID: 2076)
- svchost.exe (PID: 2192)
- 021949f0ac.exe (PID: 6296)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
Process requests binary or script from the Internet
- axplong.exe (PID: 4244)
- skotes.exe (PID: 2076)
- 54d9e0f2b2.exe (PID: 4512)
- powershell.exe (PID: 3696)
Potential Corporate Privacy Violation
- axplong.exe (PID: 4244)
- skotes.exe (PID: 2076)
- 969778179c.exe (PID: 848)
- 54d9e0f2b2.exe (PID: 4512)
- powershell.exe (PID: 3696)
Connects to the server without a host name
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- skotes.exe (PID: 2076)
- 021949f0ac.exe (PID: 6296)
- 969778179c.exe (PID: 848)
- 54d9e0f2b2.exe (PID: 4512)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- powershell.exe (PID: 3696)
Windows Defender mutex has been found
- aeb8a77c3e.exe (PID: 5464)
- 021949f0ac.exe (PID: 6296)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
Searches for installed software
- 54d9e0f2b2.exe (PID: 4512)
- f2560da6b4.exe (PID: 7812)
- 84d8863aac.exe (PID: 6844)
Uses TASKKILL.EXE to kill Browsers
- 03c656ca1f.exe (PID: 6448)
Uses TASKKILL.EXE to kill process
- 03c656ca1f.exe (PID: 6448)
Starts CMD.EXE for commands execution
- fef09d218e.exe (PID: 6876)
- cmd.exe (PID: 7024)
- Adobe QT32 Server.exe (PID: 4872)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7024)
Executing commands from a ".bat" file
- fef09d218e.exe (PID: 6876)
Application launched itself
- cmd.exe (PID: 7024)
- f2560da6b4.exe (PID: 7736)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6324)
- cmd.exe (PID: 8148)
- mobilemediaplayer5.exe (PID: 8116)
- c2a795d497.exe (PID: 6076)
- cmd.exe (PID: 8132)
- mshta.exe (PID: 1620)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 6324)
- cmd.exe (PID: 8148)
- cmd.exe (PID: 8132)
Executes application which crashes
- f2560da6b4.exe (PID: 7736)
- 969778179c.exe (PID: 848)
Reads the Windows owner or organization settings
- vx72NG3gHzoM.tmp (PID: 7968)
- eda85f68f1.tmp (PID: 8144)
Process drops legitimate windows executable
- vx72NG3gHzoM.tmp (PID: 7968)
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
The process drops C-runtime libraries
- vx72NG3gHzoM.tmp (PID: 7968)
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
The process executes via Task Scheduler
- skotes.exe (PID: 7220)
- axplong.exe (PID: 4420)
- skotes.exe (PID: 6376)
- axplong.exe (PID: 2736)
The process executes Powershell scripts
- c2a795d497.exe (PID: 6076)
Probably download files using WebClient
- mshta.exe (PID: 1620)
Manipulates environment variables
- powershell.exe (PID: 3696)
Found IP address in command line
- powershell.exe (PID: 3696)
Starts process via Powershell
- powershell.exe (PID: 3696)
Connects to unusual port
- 93e4adf5bd.exe (PID: 1520)
The process creates files with name similar to system file names
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
The executable file from the user directory is run by the CMD process
- servicebrowserv5.exe (PID: 5092)
Detected use of alternative data streams (AltDS)
- servicebrowserv5.exe (PID: 5092)
Connects to SMTP port
- servicebrowserv5.exe (PID: 5092)
INFO
Sends debugging messages
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- 969778179c.exe (PID: 848)
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- 021949f0ac.exe (PID: 6296)
- axplong.exe (PID: 4420)
- skotes.exe (PID: 7220)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- ITM0U1Z0EXRLGHCZOSI.exe (PID: 3260)
- skotes.exe (PID: 6376)
- axplong.exe (PID: 2736)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
Checks supported languages
- GM2SC_random.exe (PID: 3140)
- aeb8a77c3e.exe (PID: 5464)
- axplong.exe (PID: 4244)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- 969778179c.exe (PID: 848)
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- 021949f0ac.exe (PID: 6296)
- 03c656ca1f.exe (PID: 6448)
- fef09d218e.exe (PID: 6876)
- f2560da6b4.exe (PID: 7736)
- f2560da6b4.exe (PID: 7812)
- vx72NG3gHzoM.exe (PID: 7948)
- vx72NG3gHzoM.tmp (PID: 7968)
- skotes.exe (PID: 7220)
- mobilemediaplayer5.exe (PID: 8116)
- axplong.exe (PID: 4420)
- hVShs8C8lF7jd.exe (PID: 6808)
- 84d8863aac.exe (PID: 6844)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- ITM0U1Z0EXRLGHCZOSI.exe (PID: 3260)
- b57652dbdc.exe (PID: 6600)
- 93e4adf5bd.exe (PID: 1520)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
- eda85f68f1.exe (PID: 8160)
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
- Adobe QT32 Server.exe (PID: 4872)
- axplong.exe (PID: 2736)
- servicebrowserv5.exe (PID: 5092)
- skotes.exe (PID: 6376)
Reads the computer name
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- skotes.exe (PID: 2076)
- c2a795d497.exe (PID: 6076)
- 571439c8b1.exe (PID: 3208)
- 54d9e0f2b2.exe (PID: 4512)
- 021949f0ac.exe (PID: 6296)
- 03c656ca1f.exe (PID: 6448)
- fef09d218e.exe (PID: 6876)
- 969778179c.exe (PID: 848)
- f2560da6b4.exe (PID: 7736)
- f2560da6b4.exe (PID: 7812)
- vx72NG3gHzoM.tmp (PID: 7968)
- mobilemediaplayer5.exe (PID: 8116)
- hVShs8C8lF7jd.exe (PID: 6808)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
- 93e4adf5bd.exe (PID: 1520)
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
- Adobe QT32 Server.exe (PID: 4872)
- servicebrowserv5.exe (PID: 5092)
- 84d8863aac.exe (PID: 6844)
Create files in a temporary directory
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- fef09d218e.exe (PID: 6876)
- vx72NG3gHzoM.exe (PID: 7948)
- vx72NG3gHzoM.tmp (PID: 7968)
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- 969778179c.exe (PID: 848)
- eda85f68f1.exe (PID: 8160)
- Adobe QT32 Server.exe (PID: 4872)
- eda85f68f1.tmp (PID: 8144)
Process checks computer location settings
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- fef09d218e.exe (PID: 6876)
- mobilemediaplayer5.exe (PID: 8116)
The process uses the downloaded file
- GM2SC_random.exe (PID: 3140)
- axplong.exe (PID: 4244)
- 571439c8b1.exe (PID: 3208)
- skotes.exe (PID: 2076)
- fef09d218e.exe (PID: 6876)
- mobilemediaplayer5.exe (PID: 8116)
- mshta.exe (PID: 1620)
- powershell.exe (PID: 3696)
Checks proxy server information
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- skotes.exe (PID: 2076)
- 021949f0ac.exe (PID: 6296)
- 969778179c.exe (PID: 848)
- WerFault.exe (PID: 7920)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- powershell.exe (PID: 3696)
- WerFault.exe (PID: 3288)
Creates files or folders in the user directory
- axplong.exe (PID: 4244)
- aeb8a77c3e.exe (PID: 5464)
- skotes.exe (PID: 2076)
- 021949f0ac.exe (PID: 6296)
- 969778179c.exe (PID: 848)
- vx72NG3gHzoM.tmp (PID: 7968)
- WerFault.exe (PID: 7920)
- 6IVKF7BMMT9QKW7O.exe (PID: 5872)
- WerFault.exe (PID: 3288)
- Adobe QT32 Server.exe (PID: 7012)
The sample compiled with czech language support
- axplong.exe (PID: 4244)
Themida protector has been detected
- axplong.exe (PID: 4244)
- skotes.exe (PID: 2076)
- 969778179c.exe (PID: 848)
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
Reads the software policy settings
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- f2560da6b4.exe (PID: 7812)
- WerFault.exe (PID: 7920)
- WerFault.exe (PID: 3288)
- 84d8863aac.exe (PID: 6844)
Reads the machine GUID from the registry
- c2a795d497.exe (PID: 6076)
- 54d9e0f2b2.exe (PID: 4512)
- 969778179c.exe (PID: 848)
- f2560da6b4.exe (PID: 7812)
- 93e4adf5bd.exe (PID: 1520)
- 84d8863aac.exe (PID: 6844)
The sample compiled with english language support
- skotes.exe (PID: 2076)
- vx72NG3gHzoM.tmp (PID: 7968)
- mobilemediaplayer5.exe (PID: 8116)
- eda85f68f1.tmp (PID: 8144)
- Adobe QT32 Server.exe (PID: 7012)
- cmd.exe (PID: 7772)
Application launched itself
- firefox.exe (PID: 7088)
- firefox.exe (PID: 7140)
The sample compiled with russian language support
- vx72NG3gHzoM.tmp (PID: 7968)
Reads mouse settings
- 03c656ca1f.exe (PID: 6448)
Creates a software uninstall entry
- vx72NG3gHzoM.tmp (PID: 7968)
Creates files in the program directory
- mobilemediaplayer5.exe (PID: 8116)
Reads Internet Explorer settings
- mshta.exe (PID: 1620)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7896)
Disables trace logs
- powershell.exe (PID: 3696)
The executable file from the user directory is run by the Powershell process
- 483d2fa8a0d53818306efeb32d3.exe (PID: 6288)
Reads Environment values
- 93e4adf5bd.exe (PID: 1520)
Changes the registry key values via Powershell
- mobilemediaplayer5.exe (PID: 8116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:25 12:10:38+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.24 |
| CodeSize: | 321024 |
| InitializedDataSize: | 104960 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4be000 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
198
Monitored processes
78
Malicious processes
33
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 848 | "C:\Users\admin\AppData\Local\Temp\1014395001\969778179c.exe" | C:\Users\admin\AppData\Local\Temp\1014395001\969778179c.exe | axplong.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226505 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Temp\1045990001\93e4adf5bd.exe" | C:\Users\admin\AppData\Local\Temp\1045990001\93e4adf5bd.exe | skotes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 6.0.5 Modules
| |||||||||||||||
| 1620 | mshta "C:\Temp\u192xgeym.hta" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe" | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | 571439c8b1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2736 | "C:\Users\admin\AppData\Local\Temp\44111dbc49\axplong.exe" | C:\Users\admin\AppData\Local\Temp\44111dbc49\axplong.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 3140 | "C:\Users\admin\Desktop\GM2SC_random.exe" | C:\Users\admin\Desktop\GM2SC_random.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\AppData\Local\Temp\1014394001\571439c8b1.exe" | C:\Users\admin\AppData\Local\Temp\1014394001\571439c8b1.exe | axplong.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Temp\ITM0U1Z0EXRLGHCZOSI.exe" | C:\Users\admin\AppData\Local\Temp\ITM0U1Z0EXRLGHCZOSI.exe | 54d9e0f2b2.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3288 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 848 -s 1772 | C:\Windows\SysWOW64\WerFault.exe | 969778179c.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
75 285
Read events
75 222
Write events
59
Delete events
4
Modification events
| (PID) Process: | (4244) axplong.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4244) axplong.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4244) axplong.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4244) axplong.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | aeb8a77c3e.exe |
Value: C:\Users\admin\AppData\Local\Temp\1014393001\aeb8a77c3e.exe | |||
| (PID) Process: | (5464) aeb8a77c3e.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5464) aeb8a77c3e.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5464) aeb8a77c3e.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4244) axplong.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | 571439c8b1.exe |
Value: C:\Users\admin\AppData\Local\Temp\1014394001\571439c8b1.exe | |||
| (PID) Process: | (2076) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2076) skotes.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
103
Suspicious files
177
Text files
75
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4244 | axplong.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\random[1].exe | executable | |
MD5:7047309D142EB601BB0C8B2C949FC40B | SHA256:4F5964F723A825E1DBB6884AA47A5D7DD01D6241DB1A40E33836B1964F24EAB6 | |||
| 3208 | 571439c8b1.exe | C:\Users\admin\AppData\Local\Temp\abc3bc1985\skotes.exe | executable | |
MD5:2C780BD0B93D85AFBAD23124CF8994C2 | SHA256:96A1EEA0F525785429D36CFF82916E54227BE6A3750796E05D594E952A213EC2 | |||
| 2076 | skotes.exe | C:\Users\admin\AppData\Local\Temp\1045984001\021949f0ac.exe | executable | |
MD5:CFED3795B5DF45BBD48F493175331240 | SHA256:F2A959CAED0D99D3FF313F6C7F70A8752D8BC2DBFDA56EA577596FFADD980E67 | |||
| 7140 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4244 | axplong.exe | C:\Users\admin\AppData\Local\Temp\1014395001\969778179c.exe | executable | |
MD5:7047309D142EB601BB0C8B2C949FC40B | SHA256:4F5964F723A825E1DBB6884AA47A5D7DD01D6241DB1A40E33836B1964F24EAB6 | |||
| 2076 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\random[2].exe | executable | |
MD5:084D3CCD05F099092487D5CB20F9FBDB | SHA256:C9ADF6CDFF87BC44F5E5581FCE762D86D073969D9638AD6ABD5A7426845F6584 | |||
| 4244 | axplong.exe | C:\Users\admin\AppData\Local\Temp\1014394001\571439c8b1.exe | executable | |
MD5:2C780BD0B93D85AFBAD23124CF8994C2 | SHA256:96A1EEA0F525785429D36CFF82916E54227BE6A3750796E05D594E952A213EC2 | |||
| 4244 | axplong.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\random[2].exe | executable | |
MD5:8C98F00647FCF80B28C982C2D02D2C80 | SHA256:5064A5D432B8AA2C46752D5D680BB56AC1A0C100330226FC7C66BB3B87AC91B1 | |||
| 2076 | skotes.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\random[2].exe | executable | |
MD5:C7973E44BF12EFC64100C761EF3978EB | SHA256:423E9F7892E7929955DCB8F97FF0F29F2255AF24BC5E6F753A3DCE8DBF7F582B | |||
| 3208 | 571439c8b1.exe | C:\Windows\Tasks\skotes.job | binary | |
MD5:A818706E6AA133F7883744D684D72300 | SHA256:0721B1E5FB4605E1561D625FF4A7C7EA92C98642DFAA4F54E10C2BFDBF37F426 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
218
TCP/UDP connections
166
DNS requests
153
Threats
96
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4244 | axplong.exe | POST | 200 | 185.215.113.16:80 | http://185.215.113.16/Jo89Ku7d/index.php | unknown | — | — | malicious |
4244 | axplong.exe | POST | 200 | 185.215.113.16:80 | http://185.215.113.16/Jo89Ku7d/index.php | unknown | — | — | malicious |
4244 | axplong.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/mine/random.exe | unknown | — | — | malicious |
4244 | axplong.exe | GET | 200 | 185.215.113.16:80 | http://185.215.113.16/steam/random.exe | unknown | — | — | malicious |
4244 | axplong.exe | POST | 200 | 185.215.113.16:80 | http://185.215.113.16/Jo89Ku7d/index.php | unknown | — | — | malicious |
5464 | aeb8a77c3e.exe | GET | 200 | 185.215.113.206:80 | http://185.215.113.206/ | unknown | — | — | malicious |
4244 | axplong.exe | POST | 200 | 185.215.113.16:80 | http://185.215.113.16/Jo89Ku7d/index.php | unknown | — | — | malicious |
5464 | aeb8a77c3e.exe | POST | 200 | 185.215.113.206:80 | http://185.215.113.206/c4becf79229cb002.php | unknown | — | — | malicious |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.86.251.16:443 | — | Akamai International B.V. | DE | unknown |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4244 | axplong.exe | 185.215.113.16:80 | — | 1337team Limited | SC | malicious |
4712 | MoUsoCoreWorker.exe | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3976 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
tawdrydadysz.icu |
| unknown |
nearycrepso.shop |
| malicious |
abruptyopsn.shop |
| malicious |
wholersorie.shop |
| malicious |
framekgirus.shop |
| malicious |
tirepublicerj.shop |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4244 | axplong.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
4244 | axplong.exe | Malware Command and Control Activity Detected | BOTNET [ANY.RUN] Amadey HTTP POST Request (st=s) |
4244 | axplong.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
4244 | axplong.exe | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
4244 | axplong.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
4244 | axplong.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
4244 | axplong.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
4244 | axplong.exe | A Network Trojan was detected | ET MALWARE Win32/Amadey Host Fingerprint Exfil (POST) M2 |
5464 | aeb8a77c3e.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 33 |
5464 | aeb8a77c3e.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Stealc HTTP POST Request |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
GM2SC_random.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
axplong.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
aeb8a77c3e.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
571439c8b1.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
969778179c.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
c2a795d497.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
54d9e0f2b2.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
021949f0ac.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
skotes.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|