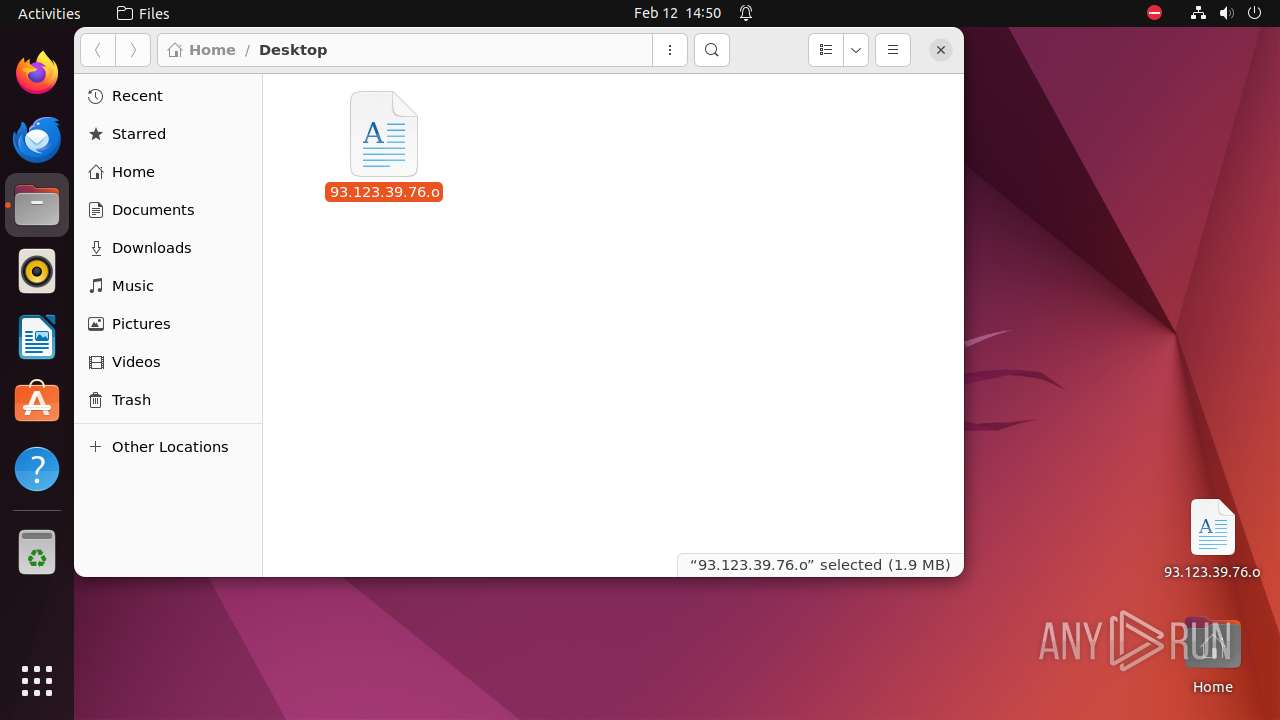
| File name: | 93.123.39.76 |
| Full analysis: | https://app.any.run/tasks/8d3c4e95-5949-46b2-b81f-fc80b205c079 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
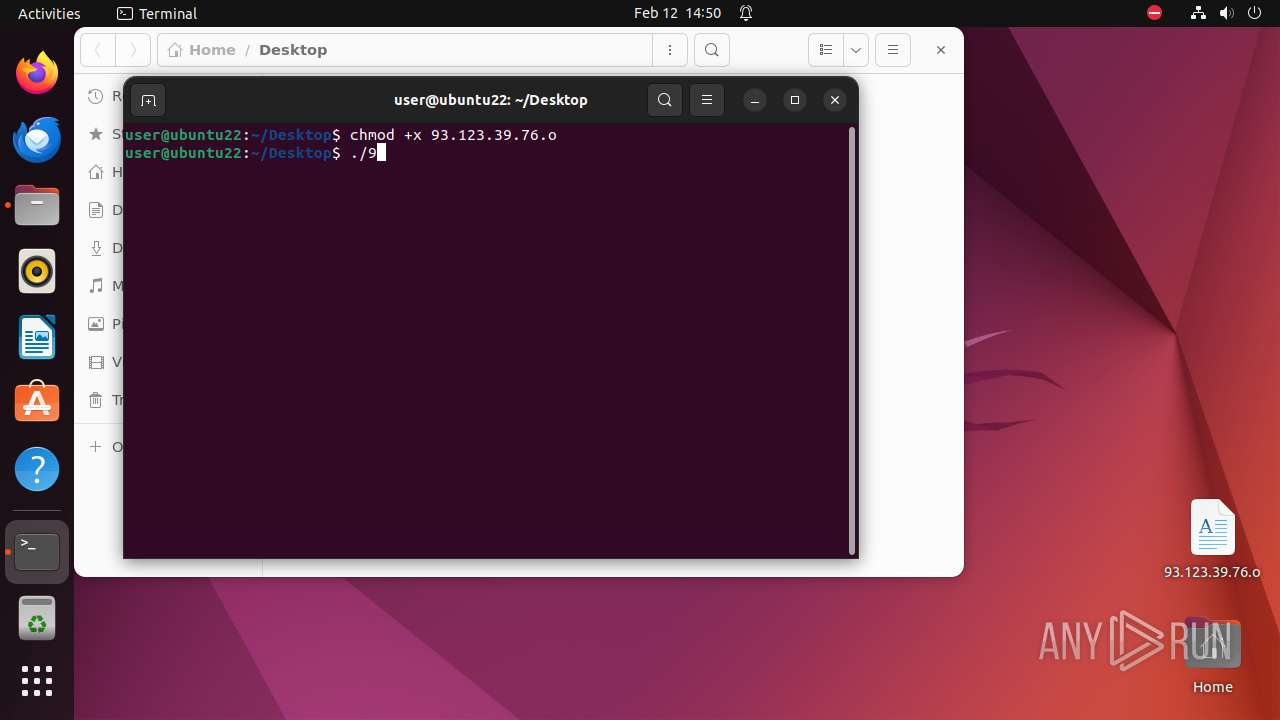
| Analysis date: | February 12, 2024, 14:50:24 |
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MIME: | application/x-sharedlib |
| File info: | ELF 64-bit LSB shared object, x86-64, version 1 (SYSV), statically linked, no section header |
| MD5: | A0EB024CB13B9C02849BA0729F2E5B1B |
| SHA1: | 0F6EAB3F3CFE650F138B03A9B21A325846F99181 |
| SHA256: | 8DAD514C01CE5564C635629F624BB0818FBD27D030BF74027B394B0CA8F673CD |
| SSDEEP: | 98304:pKgiKrfzJld3eUddCZ4m+punPnRIXBoeUdiSuZ4EFY/ALTBgoP+73qPrdtdO+524:+uCi |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks DMI information (probably VM detection)
- systemd-hostnamed (PID: 7959)
- 93.123.39.76.o (PID: 7994)
- udevadm (PID: 8005)
Executes commands using command-line interpreter
- gnome-terminal-server (PID: 7966)
- 93.123.39.76.o (PID: 7995)
Checks list of the CPUs
- 93.123.39.76.o (PID: 7994)
Reads /proc/mounts (likely used to find writable filesystems)
- 93.123.39.76.o (PID: 7994)
Checks active cgroups controllers (like CPU time, system memory, network bandwidth)
- 93.123.39.76.o (PID: 7994)
Checks the online status of NUMA nodes
- 93.123.39.76.o (PID: 7994)
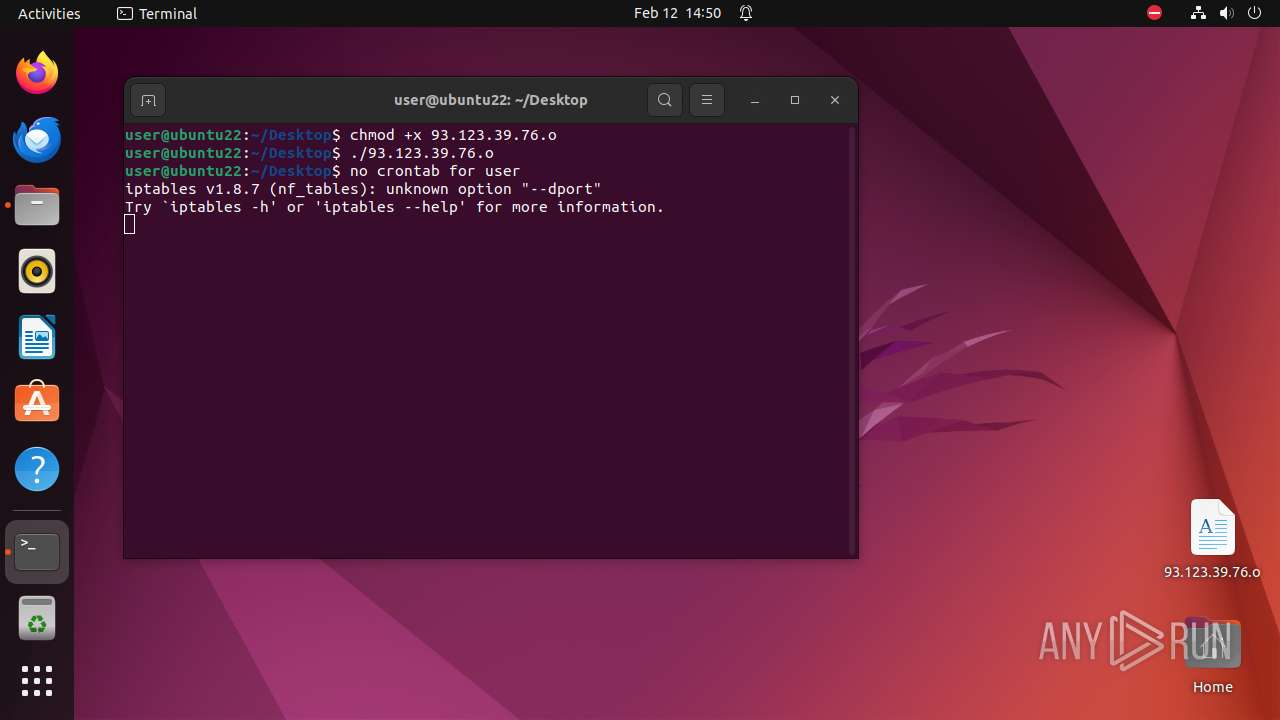
Modifies Cron jobs
- sh (PID: 7999)
INFO
Manipulating modules (likely to execute programs on system boot)
- modprobe (PID: 8004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Shared object file |
| CPUType: | AMD x86-64 |
Total processes
245
Monitored processes
27
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 7938 | /bin/sh -c "DISPLAY=:0 sudo -iu user nautilus \"/home/user/Desktop/93\.123\.39\.76\.o\" " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 7966 | ||||
| 7939 | sudo -iu user nautilus /home/user/Desktop/93.123.39.76.o | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN Exit code: 7966 | ||||
| 7940 | nautilus /home/user/Desktop/93.123.39.76.o | /usr/bin/nautilus | — | sudo |
User: user Integrity Level: UNKNOWN Exit code: 7966 | ||||
| 7941 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | nautilus |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7959 | /lib/systemd/systemd-hostnamed | /lib/systemd/systemd-hostnamed | — | systemd |
User: root Integrity Level: UNKNOWN Exit code: 7994 | ||||
| 7966 | /usr/libexec/gnome-terminal-server | /usr/libexec/gnome-terminal-server | — | systemd |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7984 | bash | /bin/bash | — | gnome-terminal-server |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 7985 | /bin/sh /usr/bin/lesspipe | /usr/bin/lesspipe | — | bash |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
| 7986 | basename /usr/bin/lesspipe | /usr/bin/basename | — | lesspipe |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
| 7987 | /bin/sh /usr/bin/lesspipe | /usr/bin/dash | — | lesspipe |
User: user Integrity Level: UNKNOWN Exit code: 496 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7940 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-wal | — | |
MD5:— | SHA256:— | |||
| 7940 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm | — | |
MD5:— | SHA256:— | |||
| 7940 | nautilus | /home/user/.local/share/nautilus/tags/.meta.isrunning | — | |
MD5:— | SHA256:— | |||
| 8001 | crontab | /var/spool/cron/crontabs/tmp.hr1fr5 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
13
DNS requests
13
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 185.125.188.58:443 | https://api.snapcraft.io/api/v1/snaps/auth/nonces | unknown | — | 54 b | unknown |
— | — | GET | 200 | 156.146.33.137:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | text | 1.50 Mb | unknown |
— | — | GET | 200 | 212.102.56.182:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | text | 1.50 Mb | unknown |
— | — | POST | 200 | 185.125.188.59:443 | https://api.snapcraft.io/api/v1/snaps/auth/sessions | unknown | — | — | unknown |
— | — | GET | 200 | 156.146.33.137:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | text | 1.50 Mb | unknown |
— | — | GET | 200 | 195.181.170.19:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | text | 1.50 Mb | unknown |
— | — | POST | 200 | 185.125.188.58:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | tss | 36.9 Kb | unknown |
— | — | GET | 200 | 156.146.33.137:443 | https://odrs.gnome.org/1.0/reviews/api/ratings | unknown | text | 1.50 Mb | unknown |
— | — | POST | 200 | 185.125.188.59:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | tss | 36.9 Kb | unknown |
— | — | POST | 200 | 185.125.188.55:443 | https://api.snapcraft.io/v2/snaps/refresh | unknown | tss | 36.9 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 212.102.56.179:443 | — | Datacamp Limited | DE | unknown |
— | — | 195.181.170.18:443 | — | Datacamp Limited | DE | unknown |
— | — | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 45.95.147.236:43782 | cnc.ohuyal.xyz | Alsycon B.V. | NL | unknown |
— | — | 141.94.96.195:443 | pool.supportxmr.com | OVH SAS | FR | unknown |
— | — | 141.94.96.71:443 | pool.supportxmr.com | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
74.100.168.192.in-addr.arpa |
| unknown |
api.snapcraft.io |
| unknown |
cnc.ohuyal.xyz |
| unknown |
pool.supportxmr.com |
| unknown |
pool-fr.supportxmr.com |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Crypto Currency Mining Activity Detected | ET MALWARE CoinMiner Domain in DNS Lookup (pool .supportxmr .com) |
— | — | Crypto Currency Mining Activity Detected | ET MALWARE CoinMiner Domain in DNS Lookup (pool .supportxmr .com) |