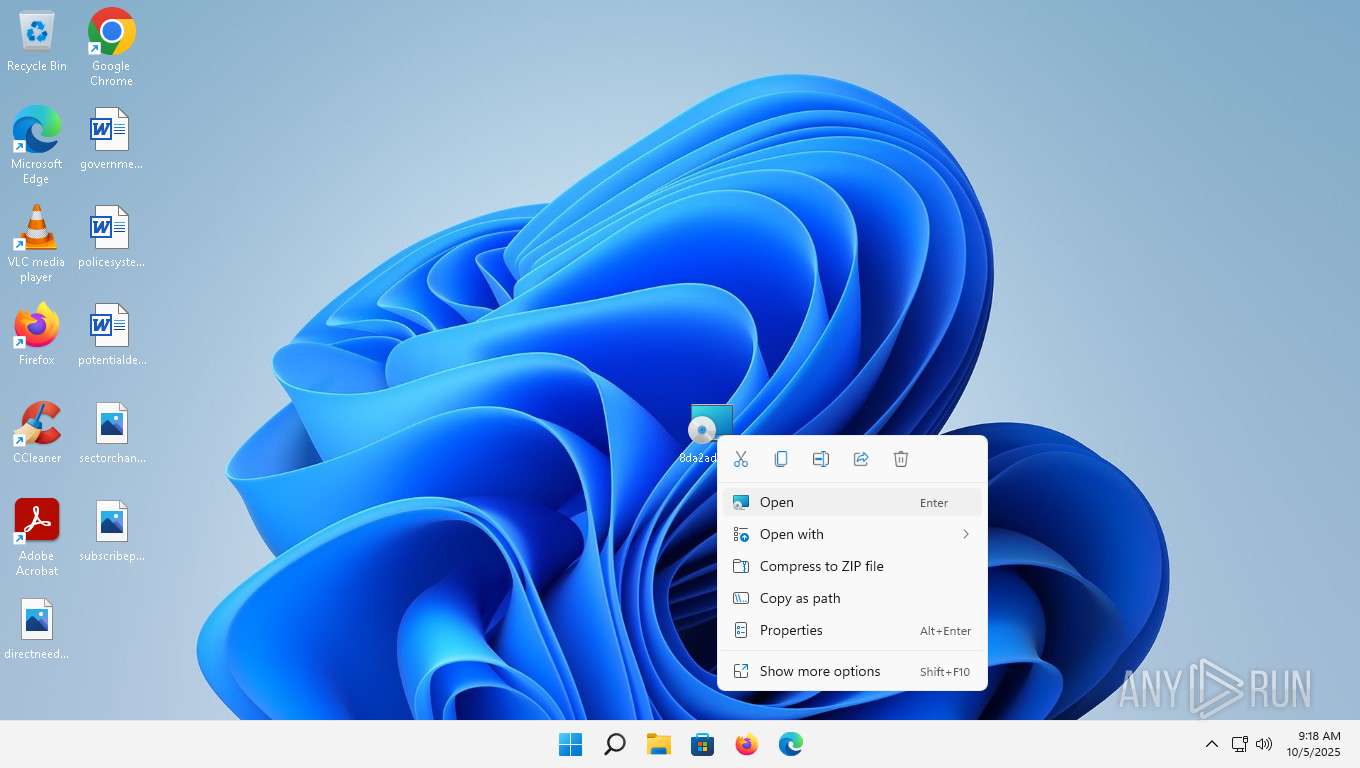
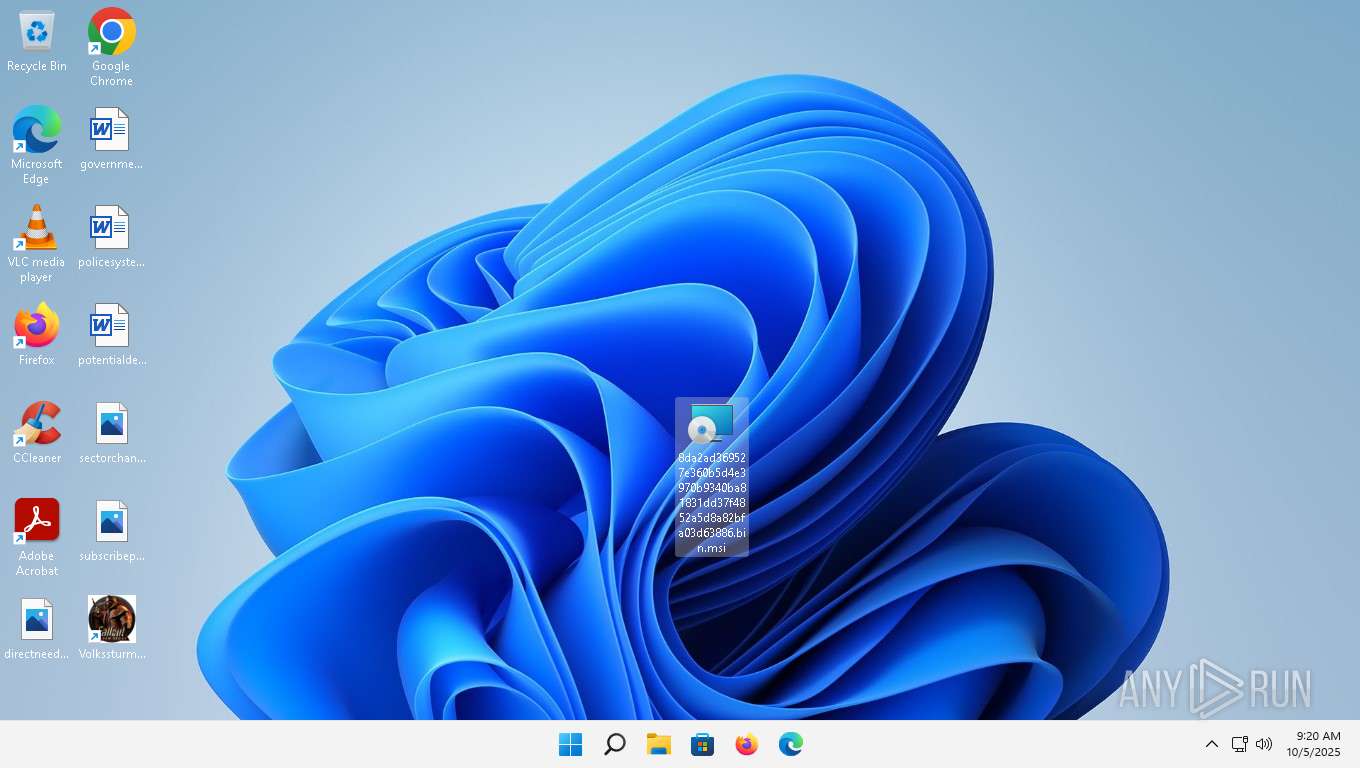
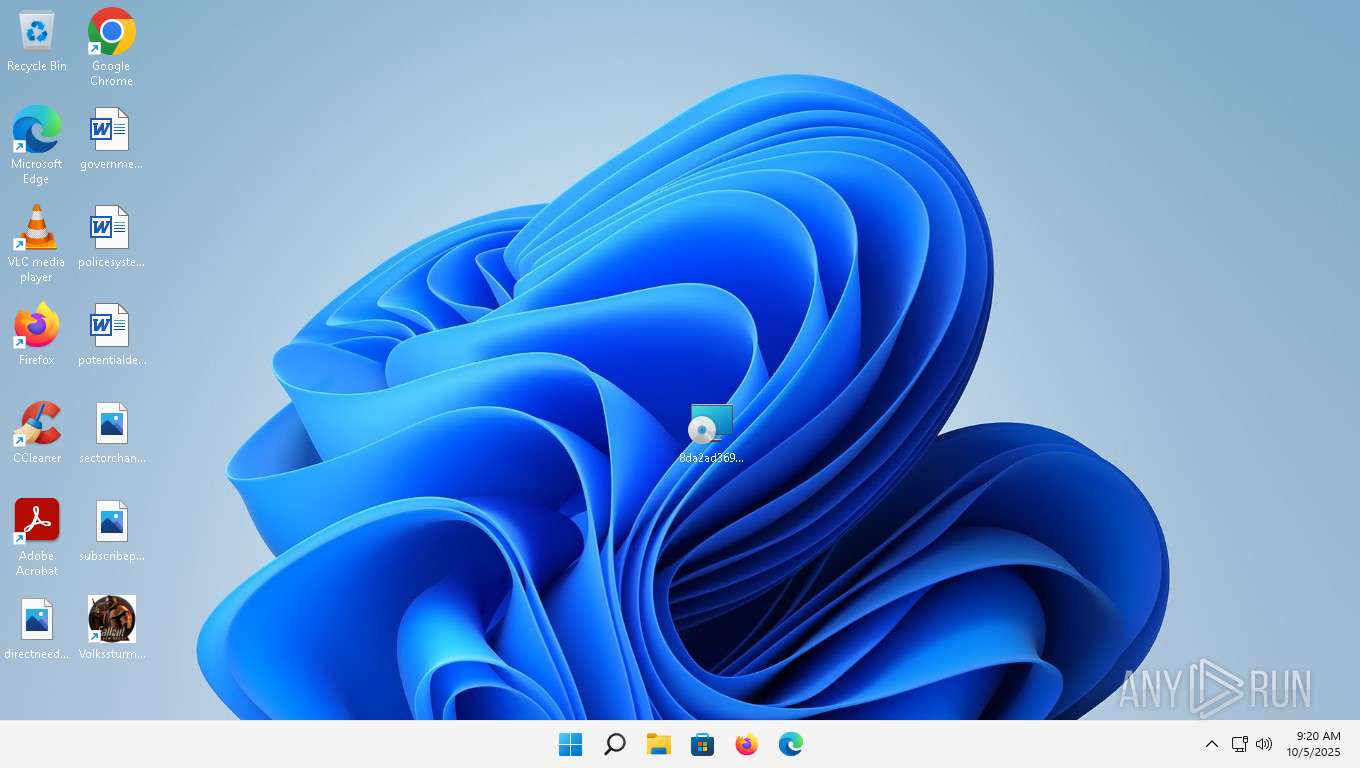
| File name: | 8da2ad369527e360b5d4e3970b9340ba81831dd37f4852a5d8a82bfa03d63886.bin |
| Full analysis: | https://app.any.run/tasks/cdb63936-fae1-4751-ad35-b12a3e17fa6b |
| Verdict: | Malicious activity |
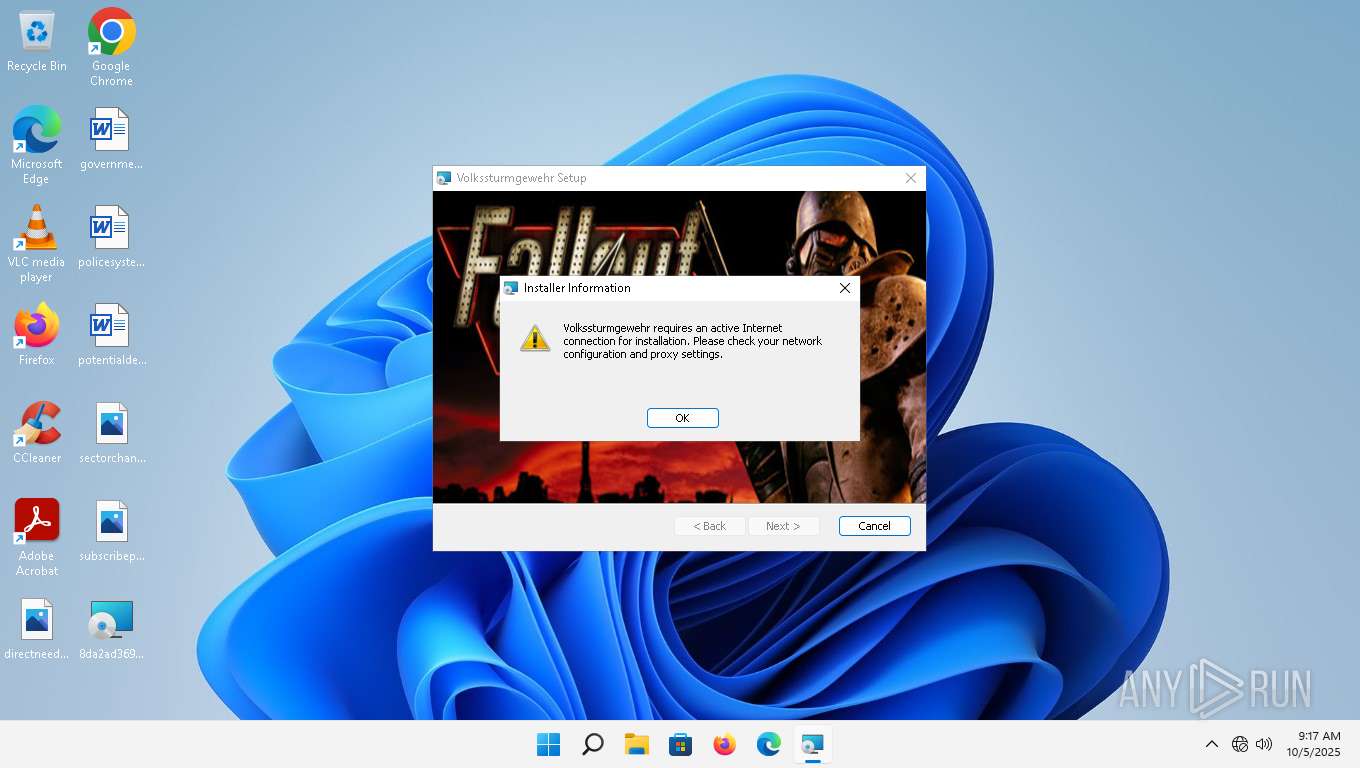
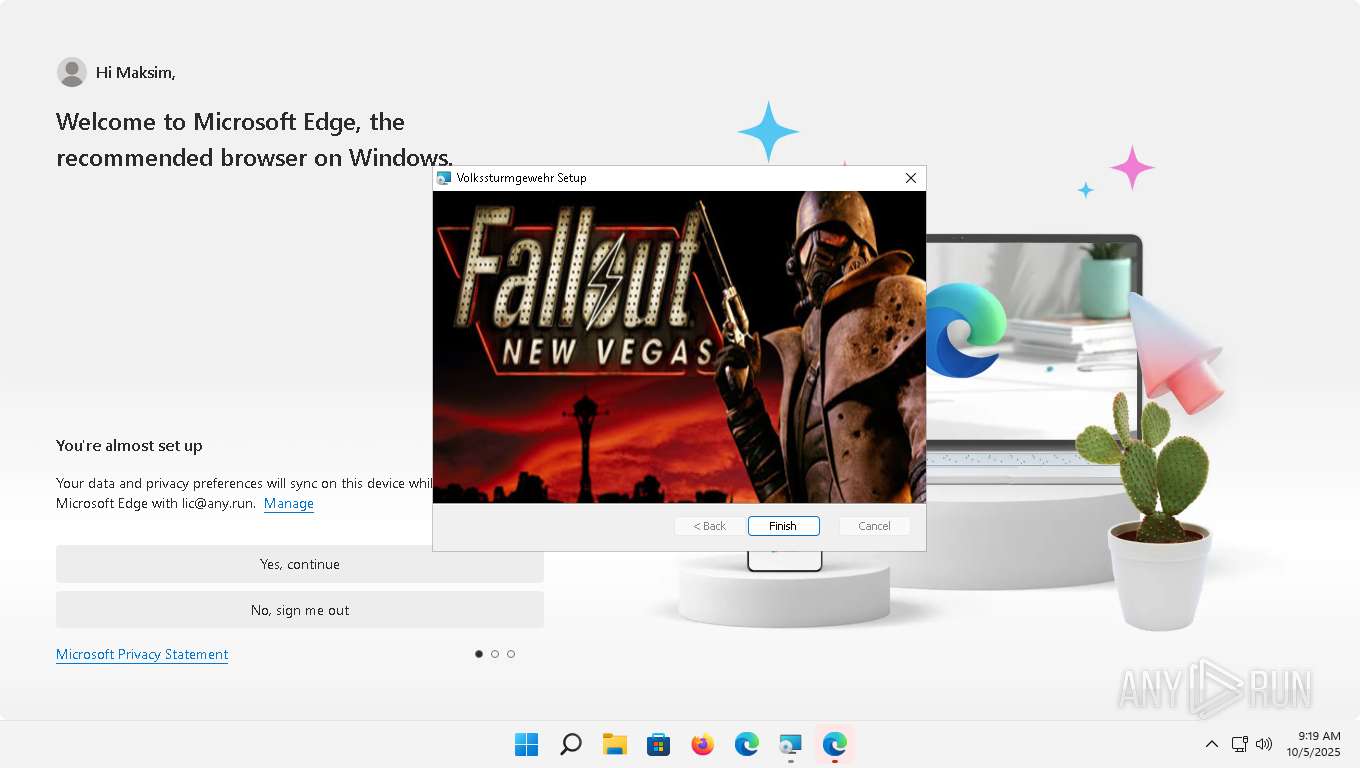
| Threats: | The Arechclient2 malware is a sophisticated .NET-based Remote Access Trojan (RAT) that collects sensitive information, such as browser credentials, from infected computers. It employs various stealth techniques, including Base64 encoding to obscure its code and the ability to pause activities to evade automated security tools. The malware also can adjust Windows Defender settings and uses code injection to manipulate legitimate processes. |
| Analysis date: | October 05, 2025, 09:17:42 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
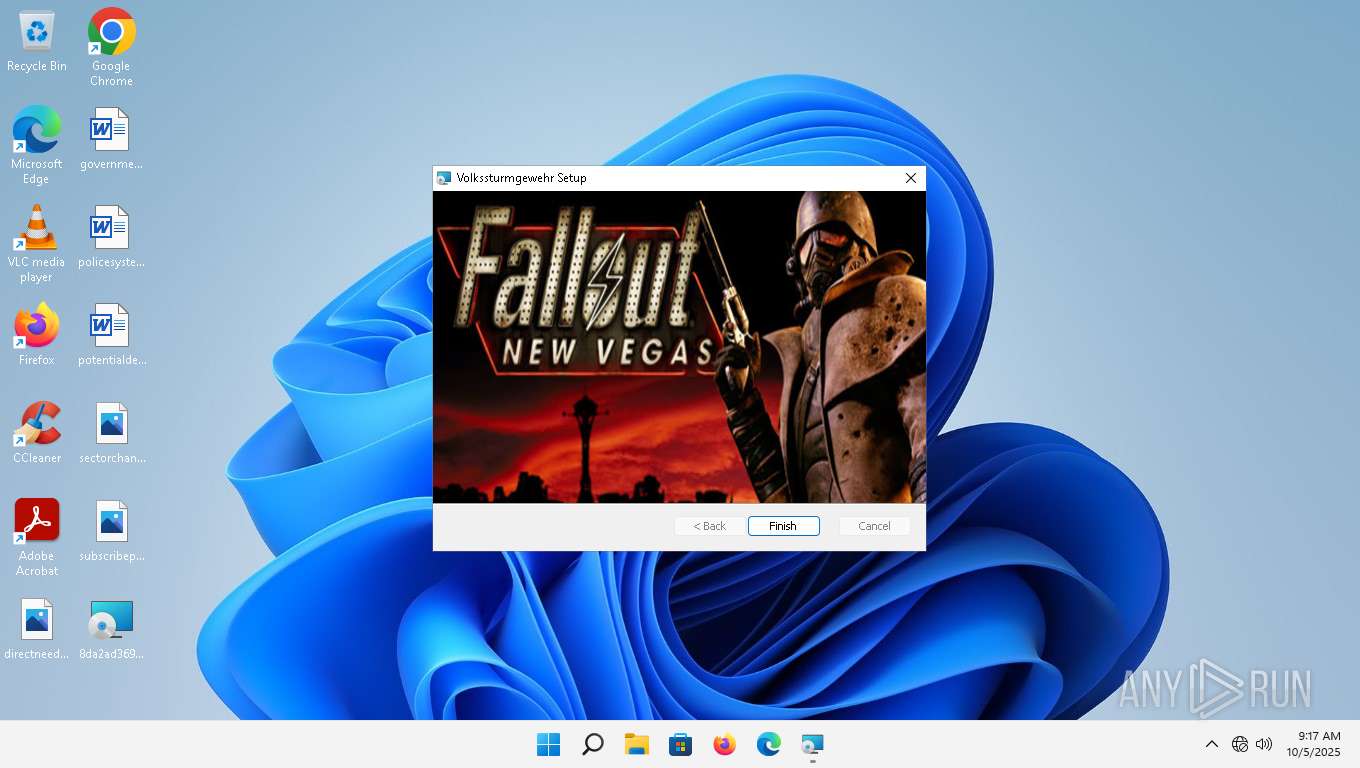
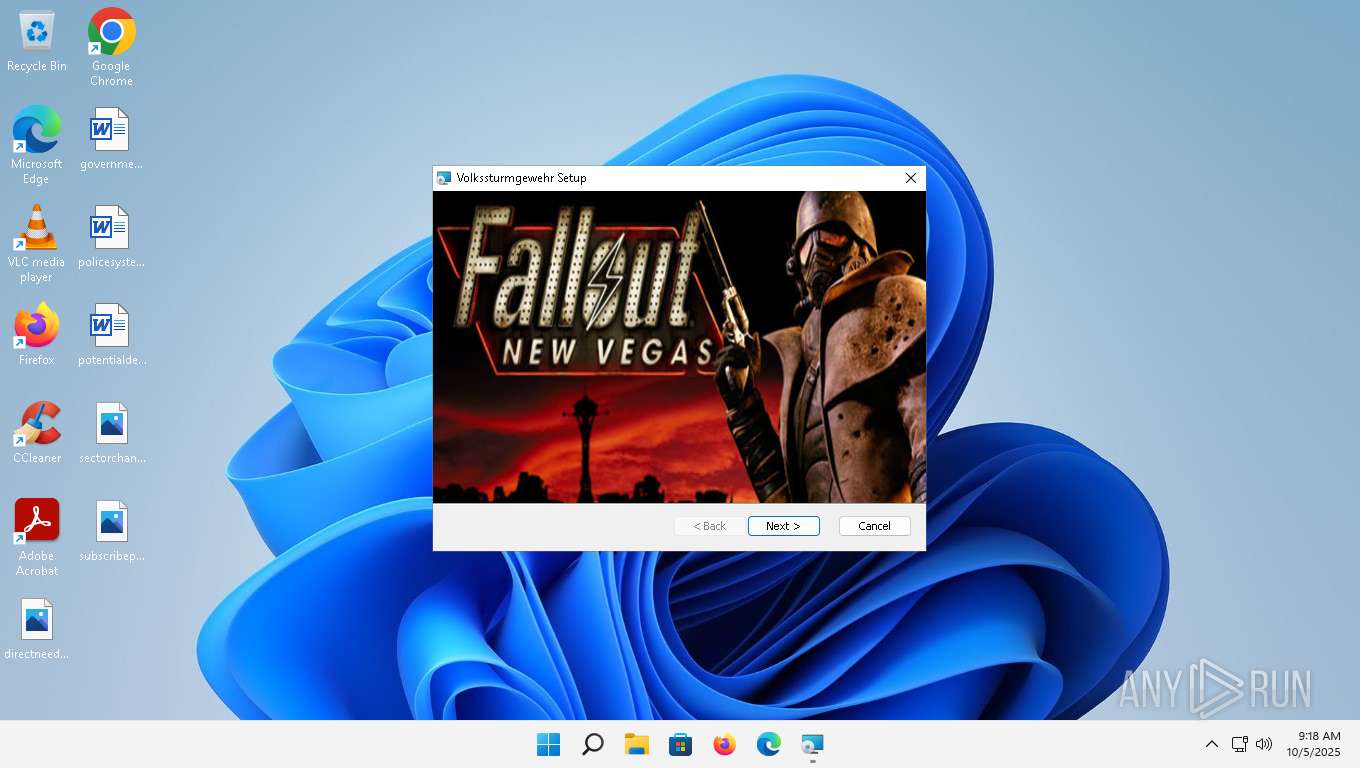
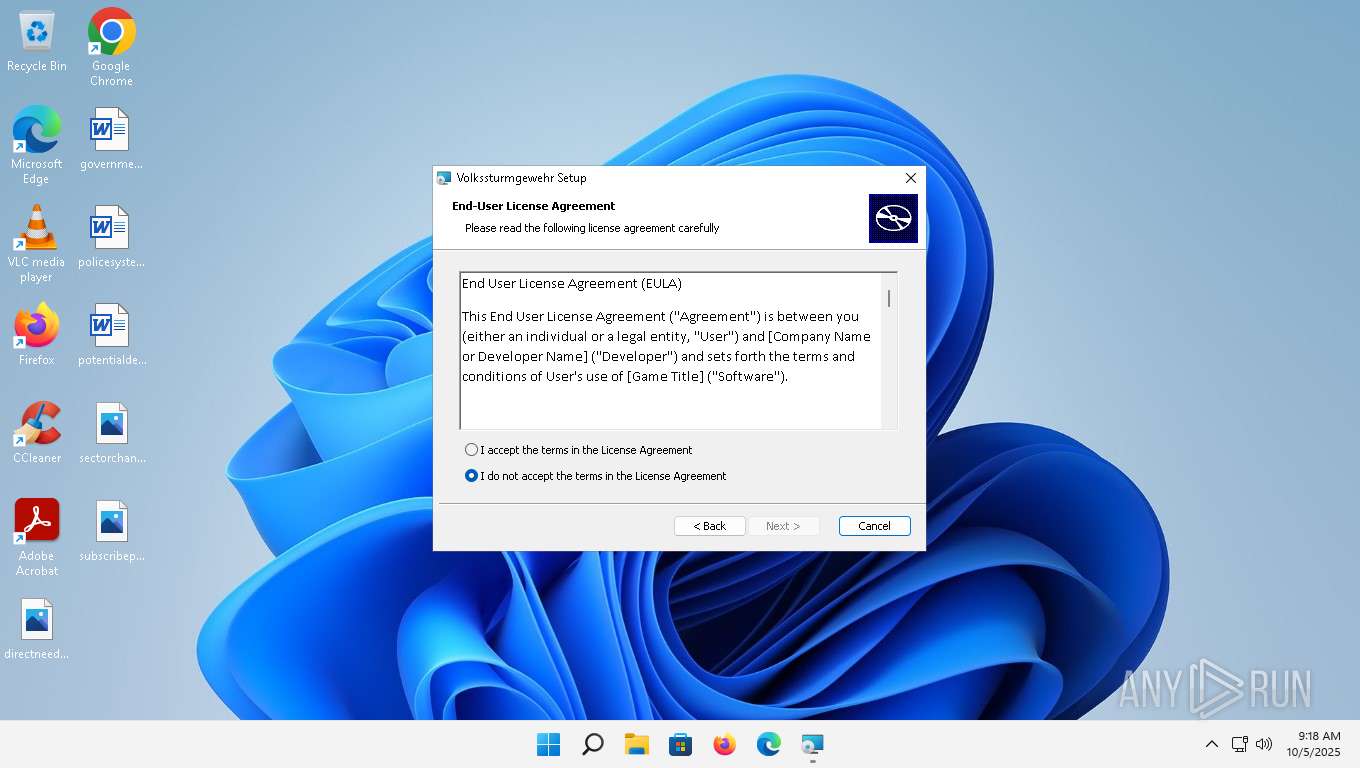
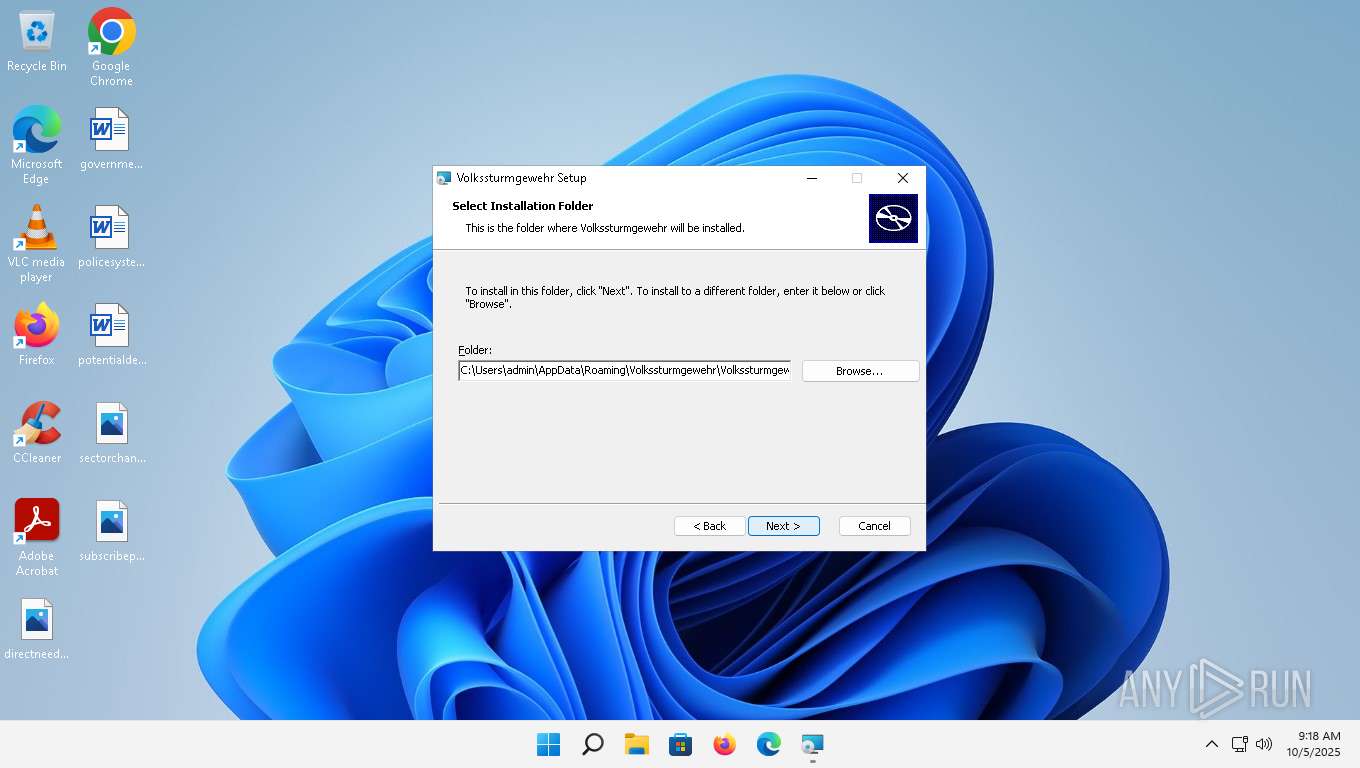
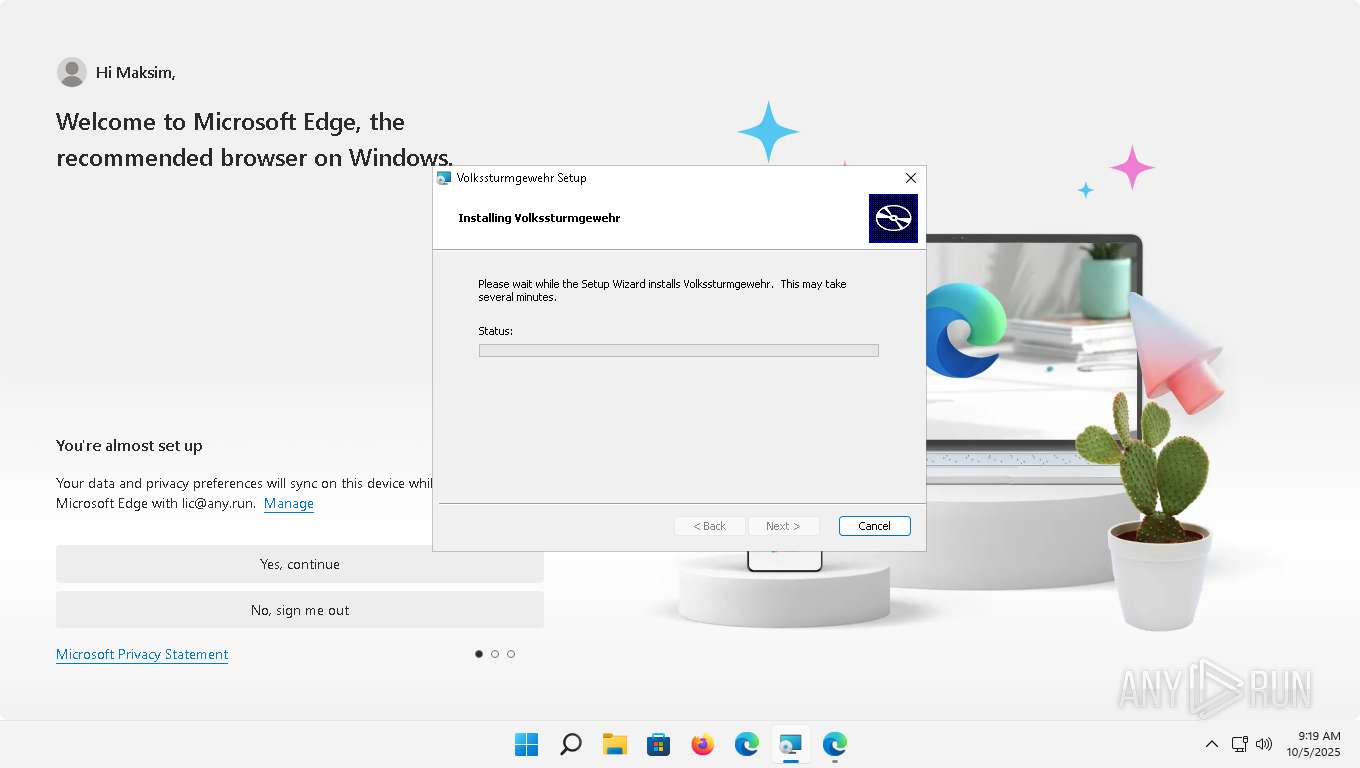
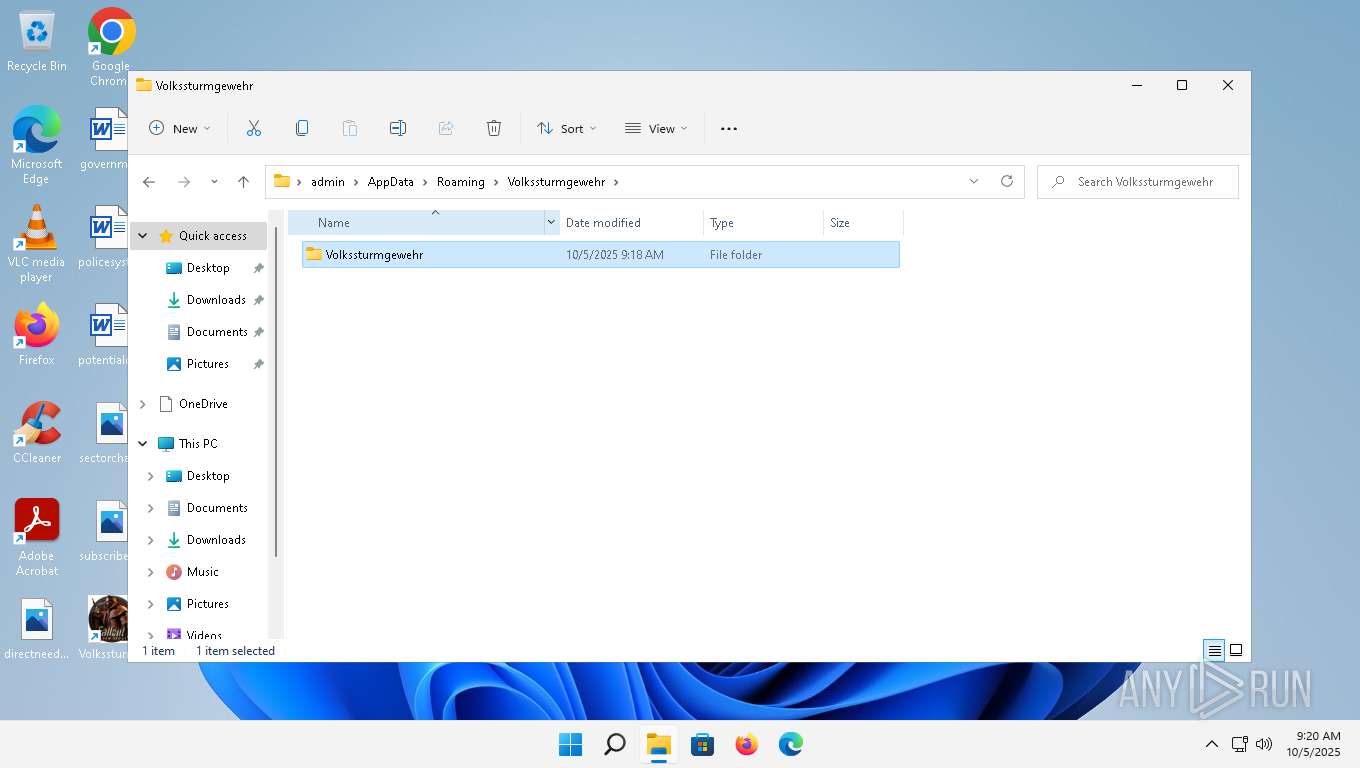
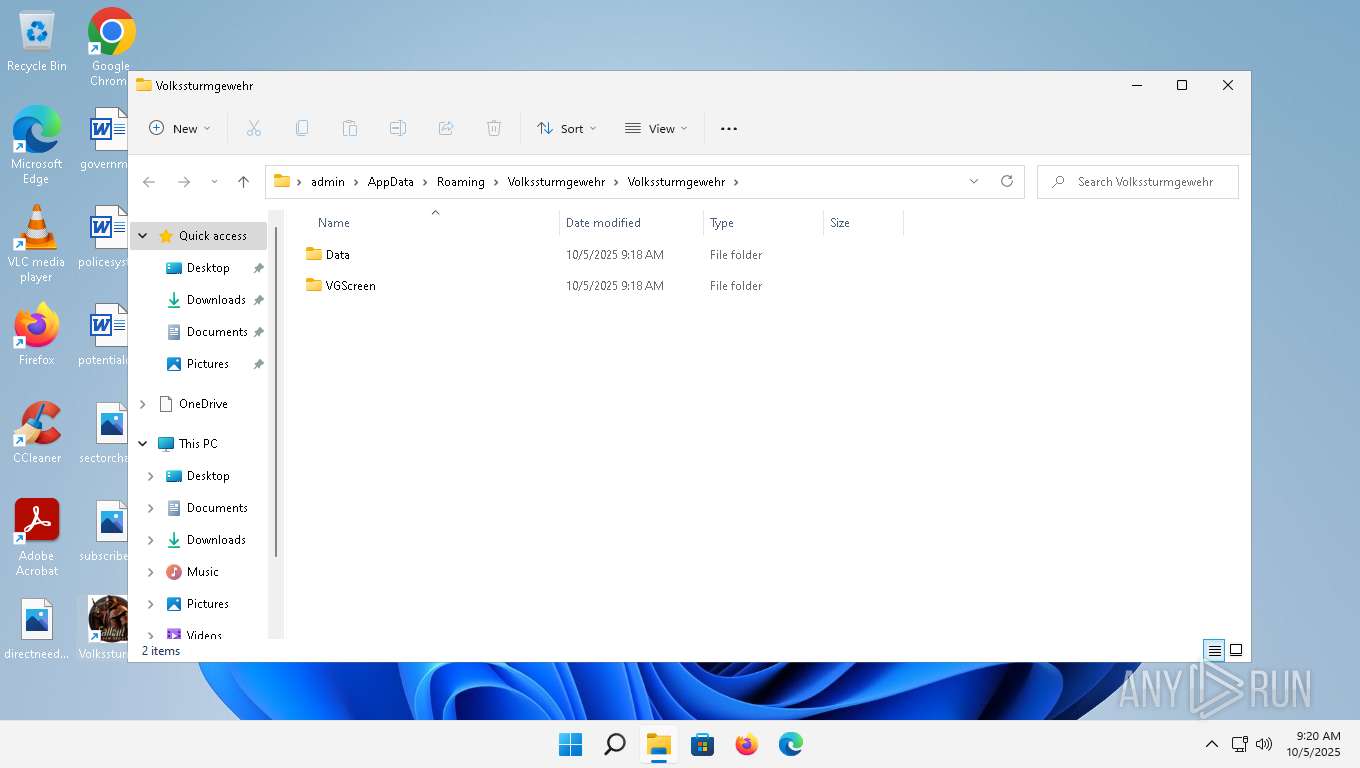
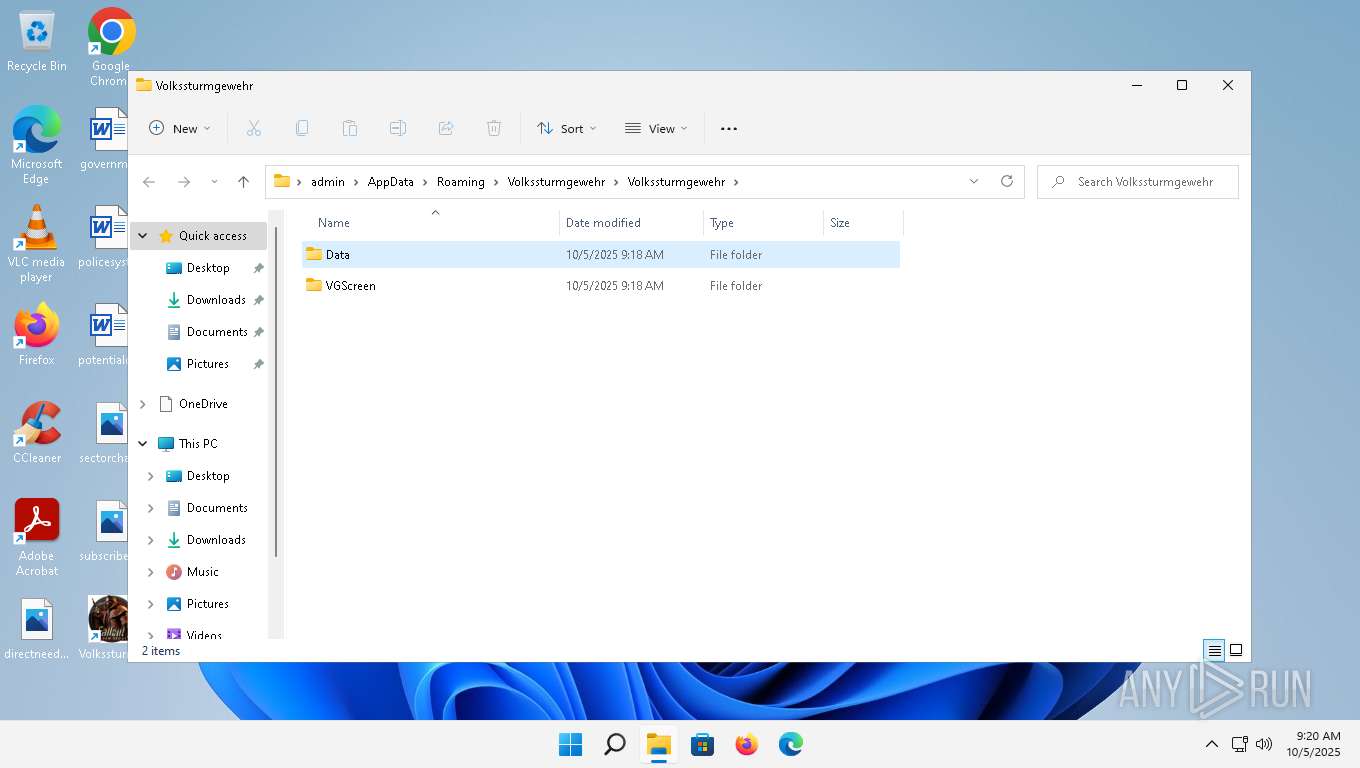
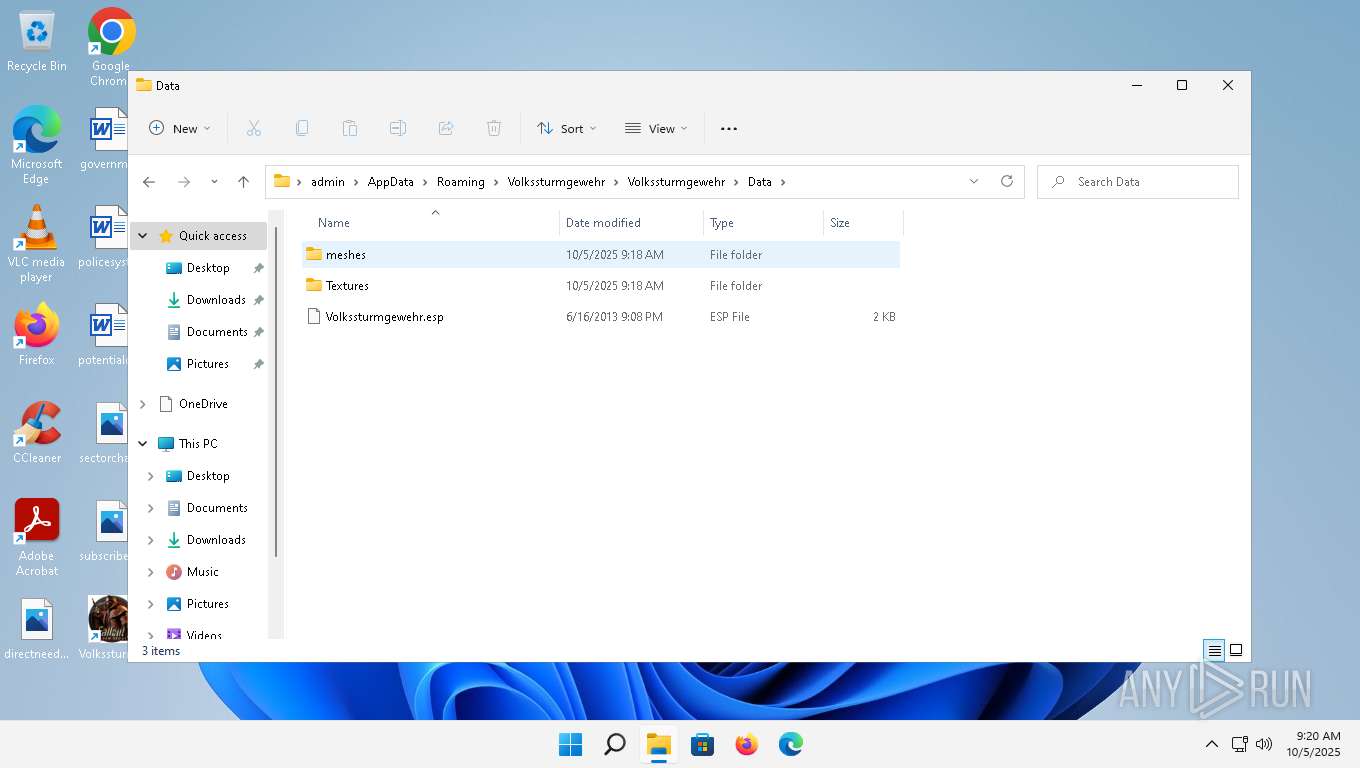
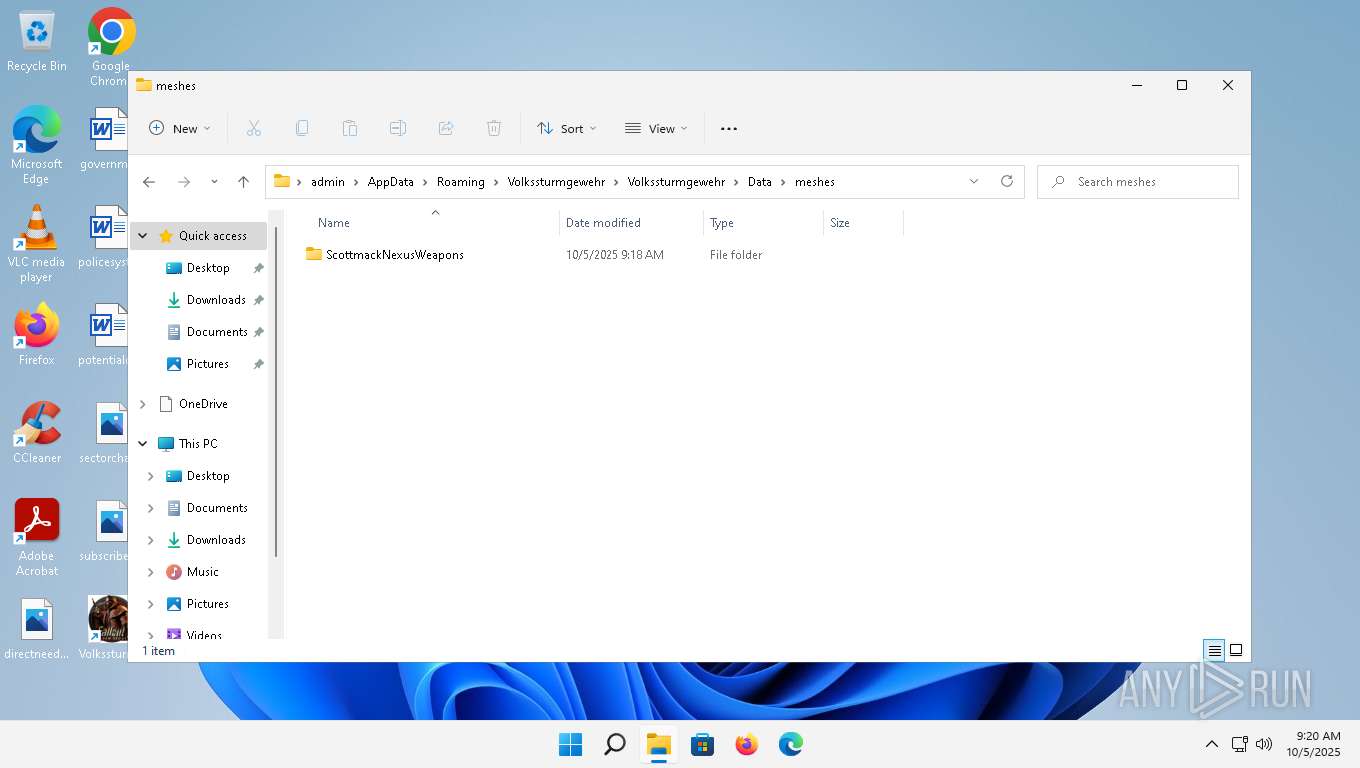
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Security: 0, Code page: 1252, Revision Number: {4A957CDA-9AC1-4F19-A68A-50517FCF9C9C}, Number of Words: 2, Subject: Volkssturmgewehr, Author: Volkssturmgewehr, Name of Creating Application: Advanced Installer 17.1.2 build 64c1c160, Template: ;1033, Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | FD23BD0DA41640D4CDB1B8B4FE0213E1 |
| SHA1: | 1664A8090D8203642179ECDB6AF9822F74B9A18F |
| SHA256: | 8DA2AD369527E360B5D4E3970B9340BA81831DD37F4852A5D8A82BFA03D63886 |
| SSDEEP: | 98304:V1Cenc79K7a6iCB3YdtTvHIFGbM/QDcyJBy9K98qSXFRf8wtb13PjY58r+8mNn4S:NDpFG1+32vAH25GsNFDxhMA |
MALICIOUS
Changes settings of System certificates
- msiexec.exe (PID: 1872)
Bypass execution policy to execute commands
- powershell.exe (PID: 1664)
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 3932)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 1664)
Dynamically loads an assembly (POWERSHELL)
- rundll32.exe (PID: 6784)
Actions looks like stealing of personal data
- MOrchestrator.exe (PID: 7236)
- rundll32.exe (PID: 6784)
ARECHCLIENT2 has been detected (SURICATA)
- MOrchestrator.exe (PID: 7236)
Steals credentials from Web Browsers
- rundll32.exe (PID: 6784)
- MOrchestrator.exe (PID: 7236)
HIJACKLOADER has been detected (YARA)
- MOrchestrator.exe (PID: 7236)
SUSPICIOUS
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3732)
- msiexec.exe (PID: 5780)
- chrmstp.exe (PID: 7876)
- cookie_exporter.exe (PID: 5400)
- cookie_exporter.exe (PID: 6500)
- cookie_exporter.exe (PID: 9944)
Reads the date of Windows installation
- msiexec.exe (PID: 3732)
- chrmstp.exe (PID: 7876)
Adds/modifies Windows certificates
- msiexec.exe (PID: 1872)
Reads the Internet Settings
- msiexec.exe (PID: 3732)
- msiexec.exe (PID: 6156)
- msiexec.exe (PID: 5780)
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
- cookie_exporter.exe (PID: 6500)
- cookie_exporter.exe (PID: 5400)
- MOrchestrator.exe (PID: 7236)
- ShellExperienceHost.exe (PID: 8260)
- cookie_exporter.exe (PID: 9944)
Application launched itself
- msiexec.exe (PID: 3732)
- msiexec.exe (PID: 5780)
- chrmstp.exe (PID: 7652)
- chrmstp.exe (PID: 7876)
- setup.exe (PID: 8424)
- setup.exe (PID: 8532)
- setup.exe (PID: 9280)
- setup.exe (PID: 9584)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3836)
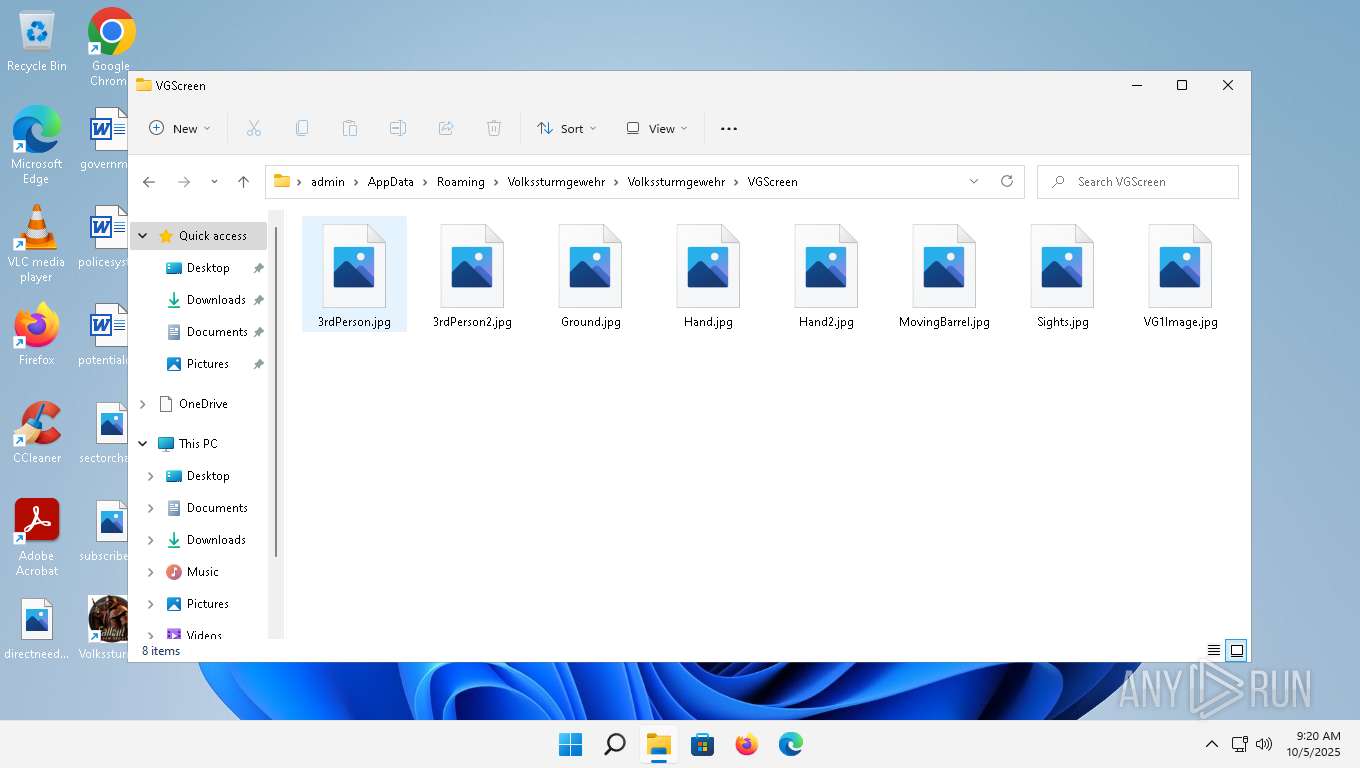
There is functionality for taking screenshot (YARA)
- dllhost.exe (PID: 2916)
The process executes Powershell scripts
- msiexec.exe (PID: 3932)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 1108)
- msiexec.exe (PID: 3932)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 3932)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1664)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 3932)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 1664)
Reads settings of System Certificates
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
Executable content was dropped or overwritten
- powershell.exe (PID: 1664)
- SuSwitch64.exe (PID: 6536)
- SuSwitch64.exe (PID: 6872)
Enumerates operating system information (Win32_OperatingSystem) (SCRIPT)
- powershell.exe (PID: 1664)
The process drops C-runtime libraries
- powershell.exe (PID: 1664)
- SuSwitch64.exe (PID: 6536)
Process drops legitimate windows executable
- SuSwitch64.exe (PID: 6536)
Starts itself from another location
- SuSwitch64.exe (PID: 6536)
The process executes via Task Scheduler
- rundll32.exe (PID: 6784)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 3932)
Starts CMD.EXE for commands execution
- SuSwitch64.exe (PID: 6872)
Searches for installed software
- MOrchestrator.exe (PID: 7236)
Connects to unusual port
- MOrchestrator.exe (PID: 7236)
Loads DLL from Mozilla Firefox
- rundll32.exe (PID: 6784)
The process creates files with name similar to system file names
- rundll32.exe (PID: 6784)
- powershell.exe (PID: 1664)
Possibly patching Antimalware Scan Interface function (YARA)
- MOrchestrator.exe (PID: 7236)
INFO
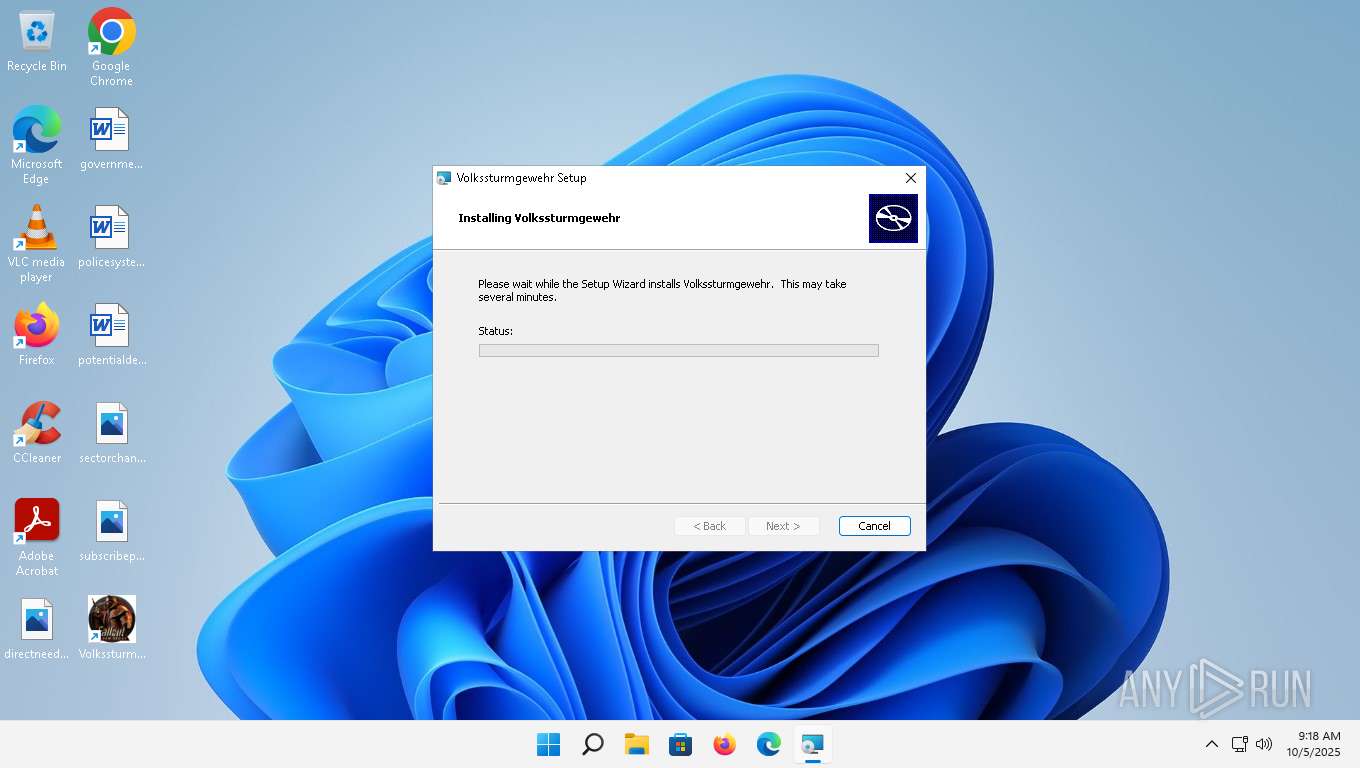
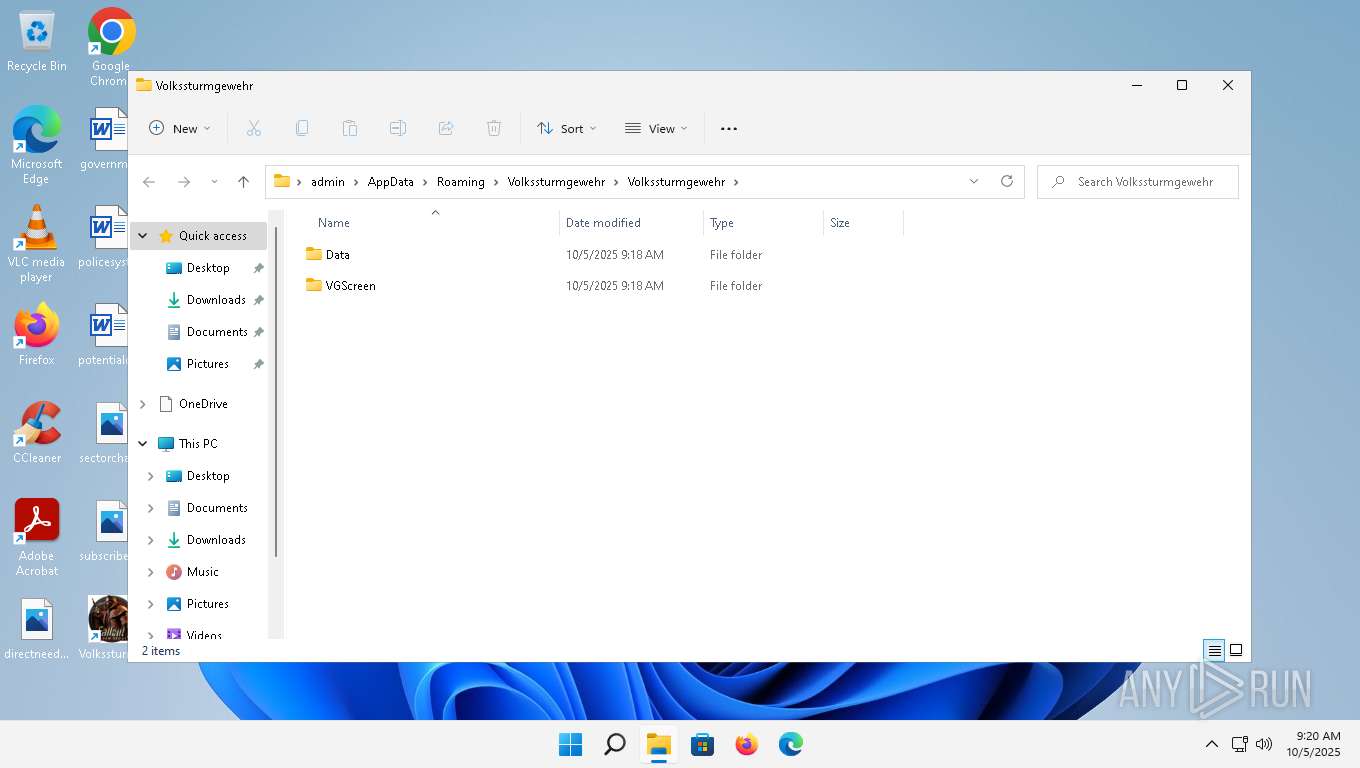
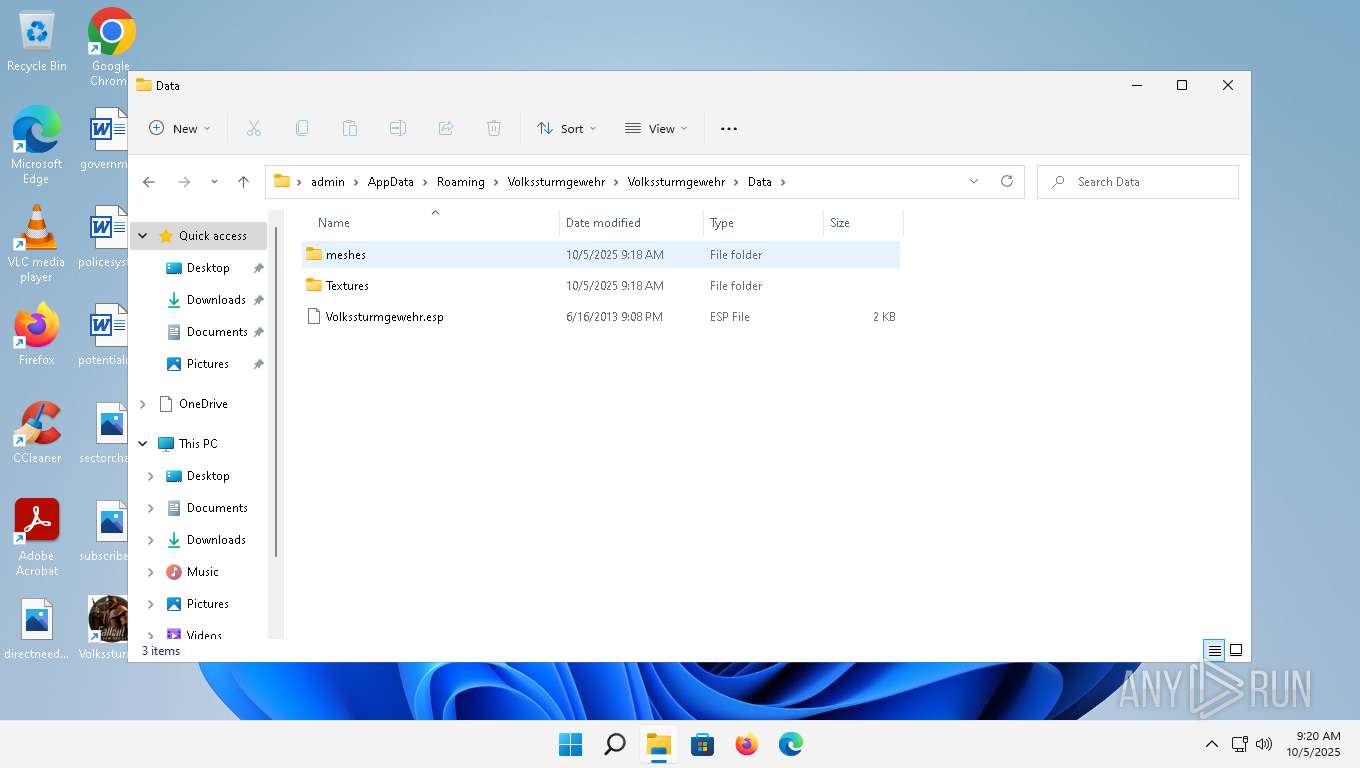
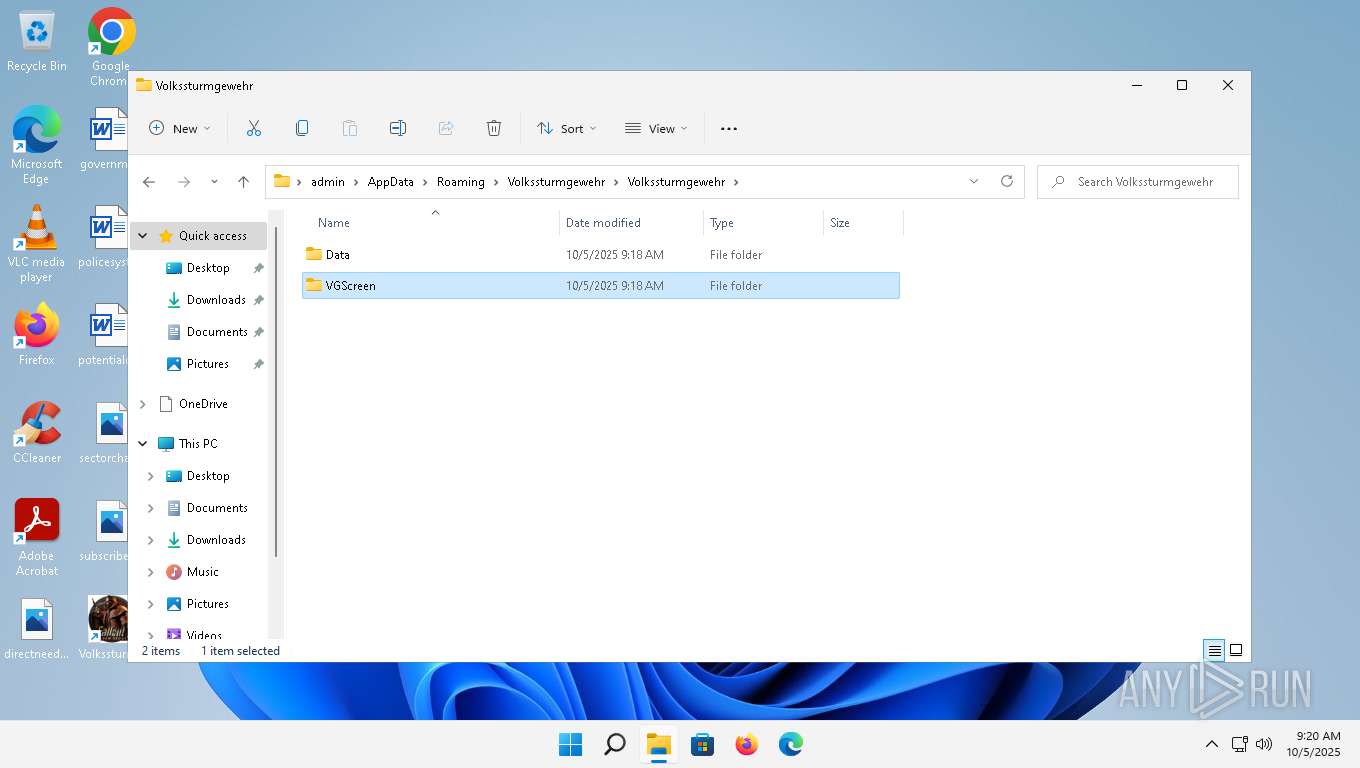
Creates files or folders in the user directory
- msiexec.exe (PID: 6156)
- msiexec.exe (PID: 3836)
- powershell.exe (PID: 1664)
- SuSwitch64.exe (PID: 6872)
- chrmstp.exe (PID: 7876)
- rundll32.exe (PID: 6784)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 6156)
- msiexec.exe (PID: 1872)
- msiexec.exe (PID: 1108)
- msiexec.exe (PID: 6532)
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
Reads the computer name
- msiexec.exe (PID: 3732)
- msiexec.exe (PID: 3836)
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 5920)
- msiexec.exe (PID: 5780)
- msiexec.exe (PID: 3932)
- SuSwitch64.exe (PID: 6536)
- SuSwitch64.exe (PID: 6872)
- chrmstp.exe (PID: 7652)
- chrmstp.exe (PID: 7876)
- MOrchestrator.exe (PID: 7236)
- cookie_exporter.exe (PID: 5400)
- cookie_exporter.exe (PID: 6500)
- identity_helper.exe (PID: 8268)
- setup.exe (PID: 8424)
- setup.exe (PID: 8532)
- cookie_exporter.exe (PID: 9944)
- setup.exe (PID: 9280)
- identity_helper.exe (PID: 5968)
- setup.exe (PID: 9584)
- identity_helper.exe (PID: 7368)
- identity_helper.exe (PID: 1824)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6156)
- msiexec.exe (PID: 1872)
- msiexec.exe (PID: 6532)
- msiexec.exe (PID: 1108)
- msiexec.exe (PID: 3836)
Checks supported languages
- msiexec.exe (PID: 3732)
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 3836)
- msiexec.exe (PID: 5920)
- msiexec.exe (PID: 5780)
- msiexec.exe (PID: 3932)
- SuSwitch64.exe (PID: 6536)
- SuSwitch64.exe (PID: 6872)
- chrmstp.exe (PID: 7652)
- chrmstp.exe (PID: 7948)
- chrmstp.exe (PID: 7780)
- chrmstp.exe (PID: 7876)
- MOrchestrator.exe (PID: 7236)
- cookie_exporter.exe (PID: 6500)
- cookie_exporter.exe (PID: 5400)
- setup.exe (PID: 8424)
- setup.exe (PID: 8488)
- setup.exe (PID: 8532)
- setup.exe (PID: 8580)
- cookie_exporter.exe (PID: 9944)
- identity_helper.exe (PID: 5968)
- setup.exe (PID: 9280)
- setup.exe (PID: 9744)
- setup.exe (PID: 9584)
- setup.exe (PID: 8260)
- identity_helper.exe (PID: 7368)
- identity_helper.exe (PID: 1824)
- identity_helper.exe (PID: 8268)
The sample compiled with english language support
- msiexec.exe (PID: 6156)
- msiexec.exe (PID: 1872)
- msiexec.exe (PID: 1108)
- msiexec.exe (PID: 6532)
- msiexec.exe (PID: 3836)
- powershell.exe (PID: 1664)
- SuSwitch64.exe (PID: 6536)
Reads Environment values
- msiexec.exe (PID: 3732)
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 5780)
- msiexec.exe (PID: 5920)
- msiexec.exe (PID: 3932)
- MOrchestrator.exe (PID: 7236)
- identity_helper.exe (PID: 8268)
- cookie_exporter.exe (PID: 9944)
- identity_helper.exe (PID: 5968)
- identity_helper.exe (PID: 7368)
- identity_helper.exe (PID: 1824)
An automatically generated document
- msiexec.exe (PID: 6156)
Reads the software policy settings
- msiexec.exe (PID: 1872)
- msiexec.exe (PID: 6156)
- msiexec.exe (PID: 6532)
- msiexec.exe (PID: 1108)
- msiexec.exe (PID: 3836)
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
Checks proxy server information
- msiexec.exe (PID: 6156)
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
- cookie_exporter.exe (PID: 5400)
- cookie_exporter.exe (PID: 6500)
- MOrchestrator.exe (PID: 7236)
- cookie_exporter.exe (PID: 9944)
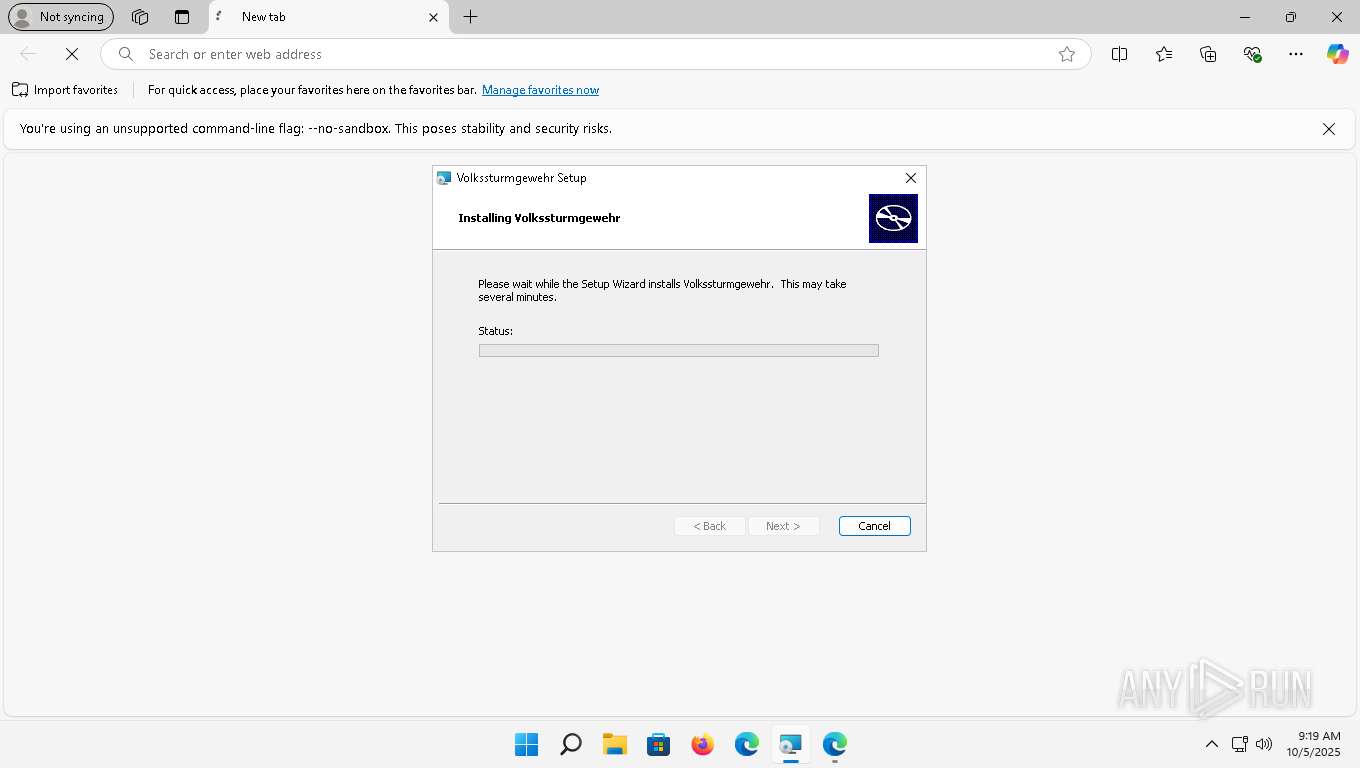
Manual execution by a user
- msiexec.exe (PID: 6532)
- msedge.exe (PID: 4228)
Create files in a temporary directory
- msiexec.exe (PID: 1872)
- msiexec.exe (PID: 3932)
- powershell.exe (PID: 1664)
- SuSwitch64.exe (PID: 6872)
- rundll32.exe (PID: 6784)
- MOrchestrator.exe (PID: 7236)
Creates a software uninstall entry
- msiexec.exe (PID: 3836)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
Disables trace logs
- powershell.exe (PID: 1664)
- rundll32.exe (PID: 6784)
- MOrchestrator.exe (PID: 7236)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1664)
Creates files in the program directory
- powershell.exe (PID: 1664)
- SuSwitch64.exe (PID: 6536)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3836)
- MOrchestrator.exe (PID: 7236)
Application launched itself
- chrome.exe (PID: 5164)
- msedge.exe (PID: 2204)
- chrome.exe (PID: 8928)
- msedge.exe (PID: 8436)
- msedge.exe (PID: 6984)
- msedge.exe (PID: 4228)
- msedge.exe (PID: 672)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1664)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 1664)
Reads product name
- MOrchestrator.exe (PID: 7236)
Reads Microsoft Office registry keys
- setup.exe (PID: 8424)
- setup.exe (PID: 9280)
Process checks computer location settings
- setup.exe (PID: 8532)
- setup.exe (PID: 9584)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2009:12:11 11:47:44 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {4A957CDA-9AC1-4F19-A68A-50517FCF9C9C} |
| Words: | 2 |
| Subject: | Volkssturmgewehr |
| Author: | Volkssturmgewehr |
| LastModifiedBy: | - |
| Software: | Advanced Installer 17.1.2 build 64c1c160 |
| Template: | ;1033 |
| Comments: | - |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
340
Monitored processes
217
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 288 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-sandbox --mute-audio --user-data-dir="C:\Users\admin\AppData\Local\Temp\betxfvie.3vy" --field-trial-handle=1796,i,13099385777505101706,12260074910293277785,262144 --variations-seed-version --mojo-platform-channel-handle=2160 /prefetch:13 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 134.0.6998.36 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1108 | "C:\Windows\SysWOW64\msiexec.exe" /i "C:\Users\admin\Desktop\8da2ad369527e360b5d4e3970b9340ba81831dd37f4852a5d8a82bfa03d63886.bin.msi" | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | "C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\Temp\betxfvie.3vy /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\Temp\betxfvie.3vy\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=134.0.6998.36 --initial-client-data=0x110,0x114,0x118,0xec,0x11c,0x7ffbf1f64f38,0x7ffbf1f64f44,0x7ffbf1f64f50 | C:\Program Files (x86)\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 134.0.6998.36 Modules
| |||||||||||||||
| 1160 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\b5fxauit.4hc" --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=13 --always-read-main-dll --field-trial-handle=3592,i,13621287101116863737,15170509083610022135,262144 --variations-seed-version --mojo-platform-channel-handle=3976 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1308 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\ndn3j2gn.fuu" --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=13 --always-read-main-dll --field-trial-handle=3508,i,17869021855535915069,1402887901726786086,262144 --variations-seed-version --mojo-platform-channel-handle=3520 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1596 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\ndn3j2gn.fuu" --extension-process --renderer-sub-type=extension --no-sandbox --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=12 --always-read-main-dll --field-trial-handle=3380,i,17869021855535915069,1402887901726786086,262144 --variations-seed-version --mojo-platform-channel-handle=3604 /prefetch:9 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1664 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pssD5EC.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msiD5E9.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scrD5EA.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scrD5EB.txt" -propSep " :<->: " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1824 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-sandbox --mute-audio --string-annotations --user-data-dir="C:\Users\admin\AppData\Local\Temp\ndn3j2gn.fuu" --always-read-main-dll --field-trial-handle=6184,i,17869021855535915069,1402887901726786086,262144 --variations-seed-version --mojo-platform-channel-handle=6192 /prefetch:14 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1824 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4576,i,2588109998192245405,1513791142354791260,262144 --variations-seed-version --mojo-platform-channel-handle=4580 /prefetch:14 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
99 029
Read events
98 340
Write events
647
Delete events
42
Modification events
| (PID) Process: | (3732) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Software\Microsoft\TIP\AggregateResults |
| Operation: | write | Name: | data |
Value: D9A7A80101000300EC03F46F00000000010000000000000049A8A801010203005C4614A6000000000200000000000000D1A8A8010102030064B65611000000001000000001000000D1A8A80101020400FB3B54EB0000000003000000000000009F49DD010100008045734BE1000000001F00000000000000 | |||
| (PID) Process: | (1872) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates |
| Operation: | delete value | Name: | B7AB3308D1EA4477BA1480125A6FBDA936490CBB |
Value: | |||
| (PID) Process: | (1872) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\B7AB3308D1EA4477BA1480125A6FBDA936490CBB |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000866912C070F1ECACACC2D5BCA55BA129140000000100000014000000DD040907A2F57A7D5253129295EE3880250DA65909000000010000004C000000304A06082B0601050507030206082B06010505070303060A2B0601040182370A030C060A2B0601040182370A030406082B0601050507030406082B0601050507030106082B06010505070308190000000100000010000000787D09F953C59978ECD8D6E44B38E24F030000000100000014000000B7AB3308D1EA4477BA1480125A6FBDA936490CBB0F0000000100000020000000489FF6233F3D3C5DA77604BE230745657FE488CB05257DA551BFD64C1F179E720B0000000100000052000000530053004C002E0063006F006D00200052006F006F0074002000430065007200740069006600690063006100740069006F006E00200041007500740068006F0072006900740079002000520053004100000062000000010000002000000085666A562EE0BE5CE925C1D8890A6F76A87EC16D4D7D5F29EA7419CF20123B691D00000001000000100000000D48EE33D7F1AF8F4B002527F82A344A2000000001000000E1050000308205DD308203C5A00302010202087B2C9BD316803299300D06092A864886F70D01010B0500307C310B3009060355040613025553310E300C06035504080C0554657861733110300E06035504070C07486F7573746F6E31183016060355040A0C0F53534C20436F72706F726174696F6E3131302F06035504030C2853534C2E636F6D20526F6F742043657274696669636174696F6E20417574686F7269747920525341301E170D3136303231323137333933395A170D3431303231323137333933395A307C310B3009060355040613025553310E300C06035504080C0554657861733110300E06035504070C07486F7573746F6E31183016060355040A0C0F53534C20436F72706F726174696F6E3131302F06035504030C2853534C2E636F6D20526F6F742043657274696669636174696F6E20417574686F726974792052534130820222300D06092A864886F70D01010105000382020F003082020A0282020100F90FDDA32B7DCBD02AFEEC6785A6E72E1BBA77E1E3F5AFA4ECFA4A5D91C457476B18776B76F2FD93E43D0FC2169E0B66C356949E178385CE56EFF216FD0062F5220954E865174E41B9E04F4697AA1BC8B86E625E69B15FDB2A027EFC6CCAF341D8EDD0E8FC3F6148EDB003141D100E4B19E0BB4EEC8665FF36F35E67020B9D865561FD7A38EDFEE21900B76FA1506275743CA0FAC82592B46E7A22C7F81EA1E3B2DD9131AB2B1D04FFA54A0437E985A4332BFDE2D655347C19A44A68C7B2A8D3B7CAA19388EBC197BC8CF91DD922842474C7043D6AA92993CCEBB85BE1FE5F25AA3458C8C123549D1B9811C3389C7E3D866CA50F40867C02F45C024F28CBAE719F0F3AC833FE112535EAFCBAC5603DD97C18D5B2A9D37578037222CA3AC31FEF2CE52EA9FA9E2CB65146FDAF03D6EA6068EA8516366B85E91EC0B3DDC424DC802A81416D943EC8E0C98141009E5EBF7FC50898A2182C4240B3F96F38274B4E80F43D8147E0887CEA1CCEB5755C512E1C2B7F1A7228E700B5D174C6D7E49FAD0793B6533535FC37E4C3F65D16BE2173DE920AF8A0636ABC96926A3EF8BC65559BDEF50D892604FC251AA62569CBC26DCA7CE2595F97ACEBEF2EC8BCD71B593C2BCCF219C8936B276319CFFCE926F8CA719B7F93FE3467844E99EBFCB378093370BA66A676ED1B73EB1AA50DC422132094560A4E2C6C4EB1FDCF9C09BAA233ED870203010001A3633061301D0603551D0E04160414DD040907A2F57A7D5253129295EE3880250DA659300F0603551D130101FF040530030101FF301F0603551D23041830168014DD040907A2F57A7D5253129295EE3880250DA659300E0603551D0F0101FF040403020186300D06092A864886F70D01010B050003820201002018119429FB269D1C1E1E7061F19572937124AD6893588E32AF1BB37003FC252B7485903D786AF4B98BA5973BB51891BB1EA7F9405B91F95599AF1E11D05C1DA766E3B194070C3239A6EA1BB079D81D9C7044E38ADDC4F9951F8A38433F0185A547A73D46B2BCE52268F77B9CD82C3E0A21C82D33ACBFC581993174C17571C5BEB1F02345F49D6BFC19639DA3BC04C6180B25BB53890FB38050DE45EE447FAB94786498D3F628DD87D8706574FB0EB913EBA70F61A93296CCDEBBED634C18BBA940F7A0546E2088717518EA7AB43472E02327775CB690EA862540ABEF330FCB9F82BEA220FBF6B52D1AE6C285B1740FFBC86502A4520147DD4922C1BFD8EB6BAC7EDEEC633315B723088FC60F8D415ADD8EC5B98FE5453F78DBBAD21B40B1FE714D3FE081A2BA5EB4EC15E093DD081F7EE155990B21DE939E0AFBE6A349BD3630FEE777B2A07597B52D8188176520F7DA90009FC952CC32CA357CF53D0FD82BD7F5266CC906349616EA70591A3279790BB6887F0F52483DBF6CD8A2442ED14EB77258D3891395FE44ABF8D78B1B6E9CBC2CA05BD56A00AF5F37E1D5FA100B989C86E7268FCEF0EC6E8A570B80E34EB2C0A0636190BA556837746AB692DB9FA18622B665270EECB69F4260E467C2B5DA410BC4D38B611BBCFA1F912BD744075EBA29ACD9C5E9EF53485AEB80F1285821CDB00655FB273F539070A9041E5727B9 | |||
| (PID) Process: | (1872) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\ROOT\Certificates\B7AB3308D1EA4477BA1480125A6FBDA936490CBB |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000001000001D00000001000000100000000D48EE33D7F1AF8F4B002527F82A344A62000000010000002000000085666A562EE0BE5CE925C1D8890A6F76A87EC16D4D7D5F29EA7419CF20123B690B0000000100000052000000530053004C002E0063006F006D00200052006F006F0074002000430065007200740069006600690063006100740069006F006E00200041007500740068006F007200690074007900200052005300410000000F0000000100000020000000489FF6233F3D3C5DA77604BE230745657FE488CB05257DA551BFD64C1F179E72030000000100000014000000B7AB3308D1EA4477BA1480125A6FBDA936490CBB190000000100000010000000787D09F953C59978ECD8D6E44B38E24F09000000010000004C000000304A06082B0601050507030206082B06010505070303060A2B0601040182370A030C060A2B0601040182370A030406082B0601050507030406082B0601050507030106082B06010505070308140000000100000014000000DD040907A2F57A7D5253129295EE3880250DA659040000000100000010000000866912C070F1ECACACC2D5BCA55BA1292000000001000000E1050000308205DD308203C5A00302010202087B2C9BD316803299300D06092A864886F70D01010B0500307C310B3009060355040613025553310E300C06035504080C0554657861733110300E06035504070C07486F7573746F6E31183016060355040A0C0F53534C20436F72706F726174696F6E3131302F06035504030C2853534C2E636F6D20526F6F742043657274696669636174696F6E20417574686F7269747920525341301E170D3136303231323137333933395A170D3431303231323137333933395A307C310B3009060355040613025553310E300C06035504080C0554657861733110300E06035504070C07486F7573746F6E31183016060355040A0C0F53534C20436F72706F726174696F6E3131302F06035504030C2853534C2E636F6D20526F6F742043657274696669636174696F6E20417574686F726974792052534130820222300D06092A864886F70D01010105000382020F003082020A0282020100F90FDDA32B7DCBD02AFEEC6785A6E72E1BBA77E1E3F5AFA4ECFA4A5D91C457476B18776B76F2FD93E43D0FC2169E0B66C356949E178385CE56EFF216FD0062F5220954E865174E41B9E04F4697AA1BC8B86E625E69B15FDB2A027EFC6CCAF341D8EDD0E8FC3F6148EDB003141D100E4B19E0BB4EEC8665FF36F35E67020B9D865561FD7A38EDFEE21900B76FA1506275743CA0FAC82592B46E7A22C7F81EA1E3B2DD9131AB2B1D04FFA54A0437E985A4332BFDE2D655347C19A44A68C7B2A8D3B7CAA19388EBC197BC8CF91DD922842474C7043D6AA92993CCEBB85BE1FE5F25AA3458C8C123549D1B9811C3389C7E3D866CA50F40867C02F45C024F28CBAE719F0F3AC833FE112535EAFCBAC5603DD97C18D5B2A9D37578037222CA3AC31FEF2CE52EA9FA9E2CB65146FDAF03D6EA6068EA8516366B85E91EC0B3DDC424DC802A81416D943EC8E0C98141009E5EBF7FC50898A2182C4240B3F96F38274B4E80F43D8147E0887CEA1CCEB5755C512E1C2B7F1A7228E700B5D174C6D7E49FAD0793B6533535FC37E4C3F65D16BE2173DE920AF8A0636ABC96926A3EF8BC65559BDEF50D892604FC251AA62569CBC26DCA7CE2595F97ACEBEF2EC8BCD71B593C2BCCF219C8936B276319CFFCE926F8CA719B7F93FE3467844E99EBFCB378093370BA66A676ED1B73EB1AA50DC422132094560A4E2C6C4EB1FDCF9C09BAA233ED870203010001A3633061301D0603551D0E04160414DD040907A2F57A7D5253129295EE3880250DA659300F0603551D130101FF040530030101FF301F0603551D23041830168014DD040907A2F57A7D5253129295EE3880250DA659300E0603551D0F0101FF040403020186300D06092A864886F70D01010B050003820201002018119429FB269D1C1E1E7061F19572937124AD6893588E32AF1BB37003FC252B7485903D786AF4B98BA5973BB51891BB1EA7F9405B91F95599AF1E11D05C1DA766E3B194070C3239A6EA1BB079D81D9C7044E38ADDC4F9951F8A38433F0185A547A73D46B2BCE52268F77B9CD82C3E0A21C82D33ACBFC581993174C17571C5BEB1F02345F49D6BFC19639DA3BC04C6180B25BB53890FB38050DE45EE447FAB94786498D3F628DD87D8706574FB0EB913EBA70F61A93296CCDEBBED634C18BBA940F7A0546E2088717518EA7AB43472E02327775CB690EA862540ABEF330FCB9F82BEA220FBF6B52D1AE6C285B1740FFBC86502A4520147DD4922C1BFD8EB6BAC7EDEEC633315B723088FC60F8D415ADD8EC5B98FE5453F78DBBAD21B40B1FE714D3FE081A2BA5EB4EC15E093DD081F7EE155990B21DE939E0AFBE6A349BD3630FEE777B2A07597B52D8188176520F7DA90009FC952CC32CA357CF53D0FD82BD7F5266CC906349616EA70591A3279790BB6887F0F52483DBF6CD8A2442ED14EB77258D3891395FE44ABF8D78B1B6E9CBC2CA05BD56A00AF5F37E1D5FA100B989C86E7268FCEF0EC6E8A570B80E34EB2C0A0636190BA556837746AB692DB9FA18622B665270EECB69F4260E467C2B5DA410BC4D38B611BBCFA1F912BD744075EBA29ACD9C5E9EF53485AEB80F1285821CDB00655FB273F539070A9041E5727B9 | |||
| (PID) Process: | (3732) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3732) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3732) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3732) msiexec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1872) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (1872) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
Executable files
95
Suspicious files
1 939
Text files
341
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6156 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI58CA.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
| 6156 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\54C62B182F5BF07FA8427C07B0A3AAF8_4DBBCB40FA282C06F1543D887F4F4DCC | binary | |
MD5:D55115B325D397F29F920C1EEA01CE40 | SHA256:F713F2A6CC03D84E3C300713C000091D2CB48EE9ABC170D0D06D228B9917AEB4 | |||
| 6156 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3D268E9651F82E5B7B2C6C52FAF86A93 | SHA256:55A7265BC53DBCC73FE173BC4A6E675110601A98D4595599F57079F351D7AE6B | |||
| 6156 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A71F9E6AF1EDB5F61A1EABEAC6EE27B2_51005597A1D9E4C10B24B854D92F8951 | binary | |
MD5:5A145870218164A2874505C063D55B6B | SHA256:D8776C3B01666E5D6D8C4BA36514DD7084CB37E797B90A342652DEE6348600EC | |||
| 3836 | msiexec.exe | C:\Windows\Installer\eb37d.msi | — | |
MD5:— | SHA256:— | |||
| 1872 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5E88.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
| 1872 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5EB9.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
| 1872 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5E39.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI98D1.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
| 1872 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5EC9.tmp | executable | |
MD5:AF61221C6F4E9AB3AC2440B25D751868 | SHA256:1E587D8593152B2538DA7BDCB13880C45D256E84BAA7E94C00EC4DE08AB018D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
244
DNS requests
226
Threats
152
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6156 | msiexec.exe | GET | 304 | 2.22.50.136:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0c5f26892f02a592 | unknown | — | — | whitelisted |
6156 | msiexec.exe | GET | 200 | 18.173.205.76:80 | http://ocsps.ssl.com/MEkwRzBFMEMwQTAJBgUrDgMCGgUABBQMDtATfnJO6JAXDQoHl8pAaJdhTQQU3QQJB6L1en1SUxKSle44gCUNplkCCGQzUdPHOJ8I | unknown | — | — | whitelisted |
2868 | svchost.exe | GET | 304 | 2.22.50.136:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f5c1d93660307ad2 | unknown | — | — | whitelisted |
2868 | svchost.exe | GET | 304 | 2.22.50.136:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?79493667c0a82304 | unknown | — | — | whitelisted |
1424 | svchost.exe | GET | 200 | 2.18.64.200:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
6156 | msiexec.exe | GET | 200 | 18.173.205.76:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSOf8DjMnuwFThpZh9bv9IoPvmNMAQUVML%2BEJUAk81q9efA19myS7iPDOMCEGZuq7cLS%2FzKHg3gvzJWy0s%3D | unknown | — | — | whitelisted |
2868 | svchost.exe | GET | 200 | 2.22.50.136:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?71dc8433eb84d594 | unknown | — | — | whitelisted |
9180 | chrome.exe | GET | 200 | 142.250.186.142:80 | http://clients2.google.com/time/1/current?cup2key=8:KjRFedwvbAHg8EqbBP8DaN1ZTfpXjOMcRcbOB2QINWA&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
6160 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:fLBYEfCYrcVyWPz-qh-PR2qIGyNiv_eNmlKoTJkV35A&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2868 | svchost.exe | GET | 200 | 2.22.50.136:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9016c61f2383e5a1 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6092 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2092 | rundll32.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5172 | OfficeC2RClient.exe | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6624 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5460 | pingsender.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
1424 | svchost.exe | 2.18.64.212:80 | — | Administracion Nacional de Telecomunicaciones | UY | whitelisted |
6156 | msiexec.exe | 2.22.50.136:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
6156 | msiexec.exe | 18.173.205.76:80 | ocsps.ssl.com | — | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsps.ssl.com |
| whitelisted |
login.live.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1424 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
1424 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | A Network Trojan was detected | ET MALWARE PS1/Unknown Payload C2 Downloader (GET) |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | A Network Trojan was detected | ET MALWARE NUMOZYLOD CnC Checkin M2 |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
Process | Message |
|---|---|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\betxfvie.3vy directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\ndn3j2gn.fuu directory exists )
|
chrome.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\pt153vwq.vct directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\b5fxauit.4hc directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\b5fxauit.4hc directory exists )
|
msedge.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\Temp\tvc4zjp5.rtm directory exists )
|