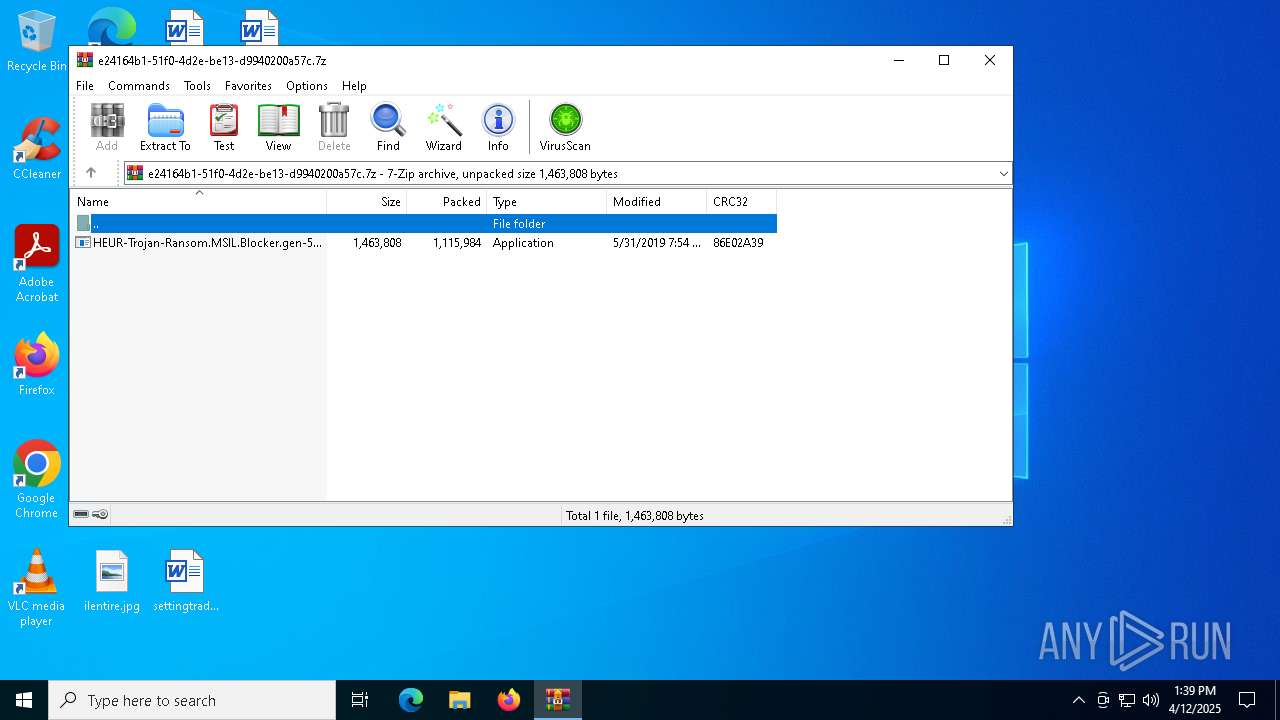
| File name: | HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.7z |
| Full analysis: | https://app.any.run/tasks/e24164b1-51f0-4d2e-be13-d9940200a57c |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | April 12, 2025, 13:39:16 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | A1C1EFBF5A70A535C7FBE9C1E659EB95 |
| SHA1: | C7ACFB80AE6B4F5E78178B5640FDB56EFAC3058A |
| SHA256: | 8D2AA85B97109A9E8D922B05B68D9C8A42A8FAE74C1CF0D3B9010284FE5EB902 |
| SSDEEP: | 49152:FrCqobbk3c7A+gvUDO+RteJEXE+1sUuCN0hEZhRplBzQLZl8R2gdbqprJCxUE+Cr:Fr7oU3c7ArcC+yuXEKsUuCN0hOtlWLcj |
MALICIOUS
Changes the autorun value in the registry
- winint.exe (PID: 4896)
- winint.exe (PID: 5008)
Actions looks like stealing of personal data
- winint.exe (PID: 5008)
AGENTTESLA is detected (reg)
- winint.exe (PID: 5008)
Steals credentials from Web Browsers
- winint.exe (PID: 5008)
AdWind is detected
- java.exe (PID: 7516)
SUSPICIOUS
Reads security settings of Internet Explorer
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- winint.exe (PID: 5008)
There is functionality for taking screenshot (YARA)
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- winint.exe (PID: 4896)
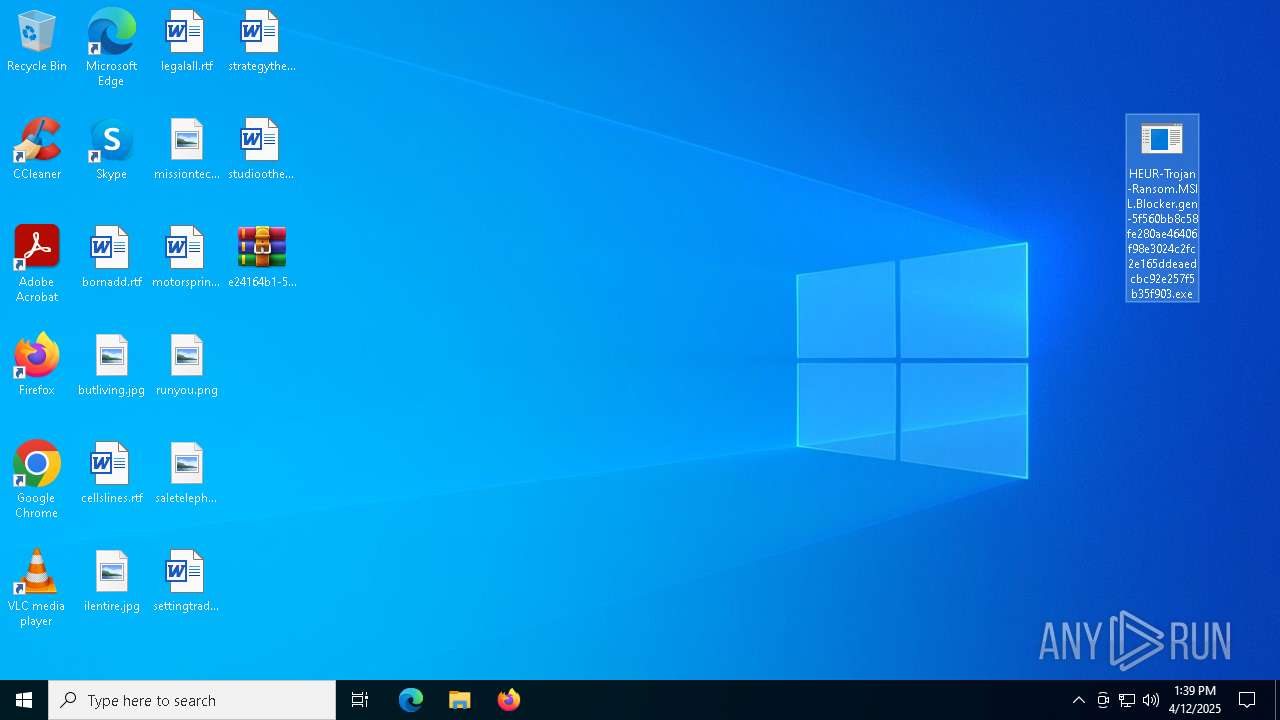
Executable content was dropped or overwritten
- cmd.exe (PID: 4428)
- winint.exe (PID: 5008)
- xcopy.exe (PID: 6632)
Starts CMD.EXE for commands execution
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- java.exe (PID: 7516)
- javaw.exe (PID: 6132)
The executable file from the user directory is run by the CMD process
- winint.exe (PID: 4896)
Application launched itself
- winint.exe (PID: 4896)
Checks for external IP
- svchost.exe (PID: 2196)
- winint.exe (PID: 5008)
The process executes VB scripts
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7624)
- cmd.exe (PID: 7812)
- cmd.exe (PID: 7840)
Accesses WMI object display name (SCRIPT)
- cscript.exe (PID: 4068)
- cscript.exe (PID: 1128)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- cscript.exe (PID: 1128)
- cscript.exe (PID: 4068)
- cscript.exe (PID: 7744)
- cscript.exe (PID: 7728)
Accesses antivirus product name via WMI (SCRIPT)
- cscript.exe (PID: 4068)
- cscript.exe (PID: 1128)
The process drops C-runtime libraries
- xcopy.exe (PID: 6632)
Connects to unusual port
- javaw.exe (PID: 6132)
INFO
Reads the machine GUID from the registry
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- winint.exe (PID: 4896)
- winint.exe (PID: 5008)
- javaw.exe (PID: 6132)
- java.exe (PID: 7516)
Reads the computer name
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- winint.exe (PID: 4896)
- winint.exe (PID: 5008)
- javaw.exe (PID: 6132)
- java.exe (PID: 7516)
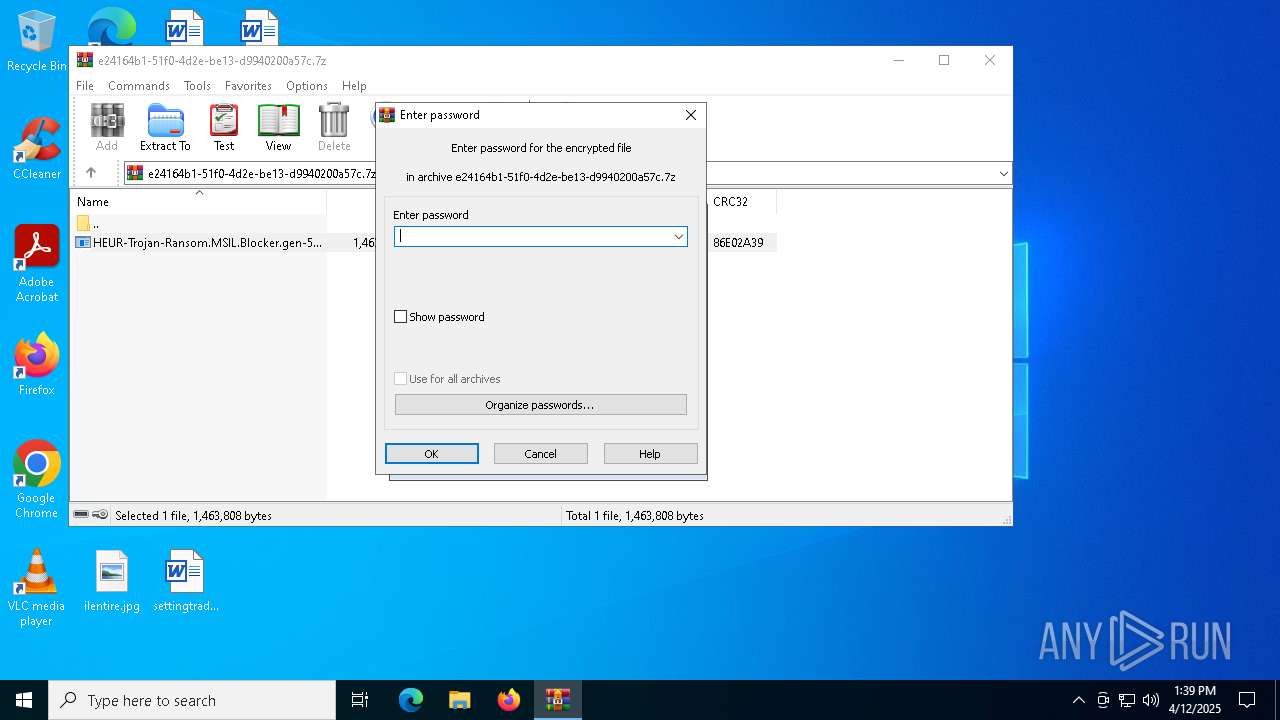
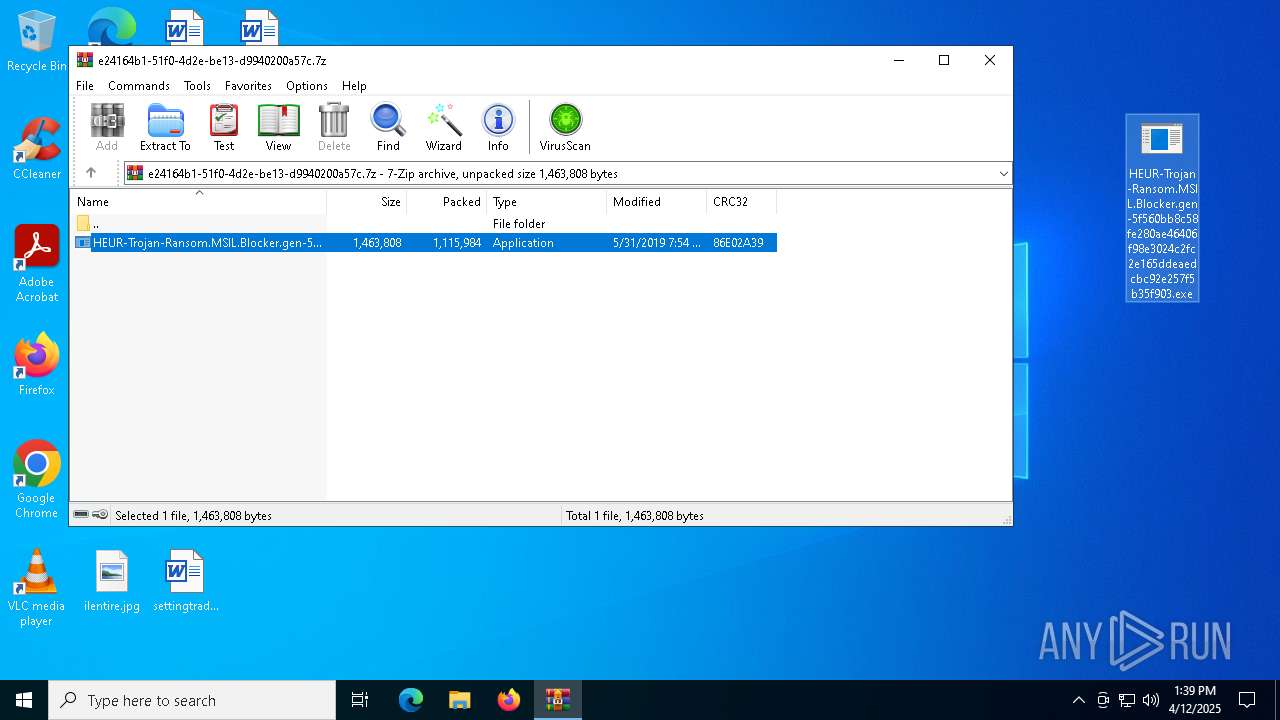
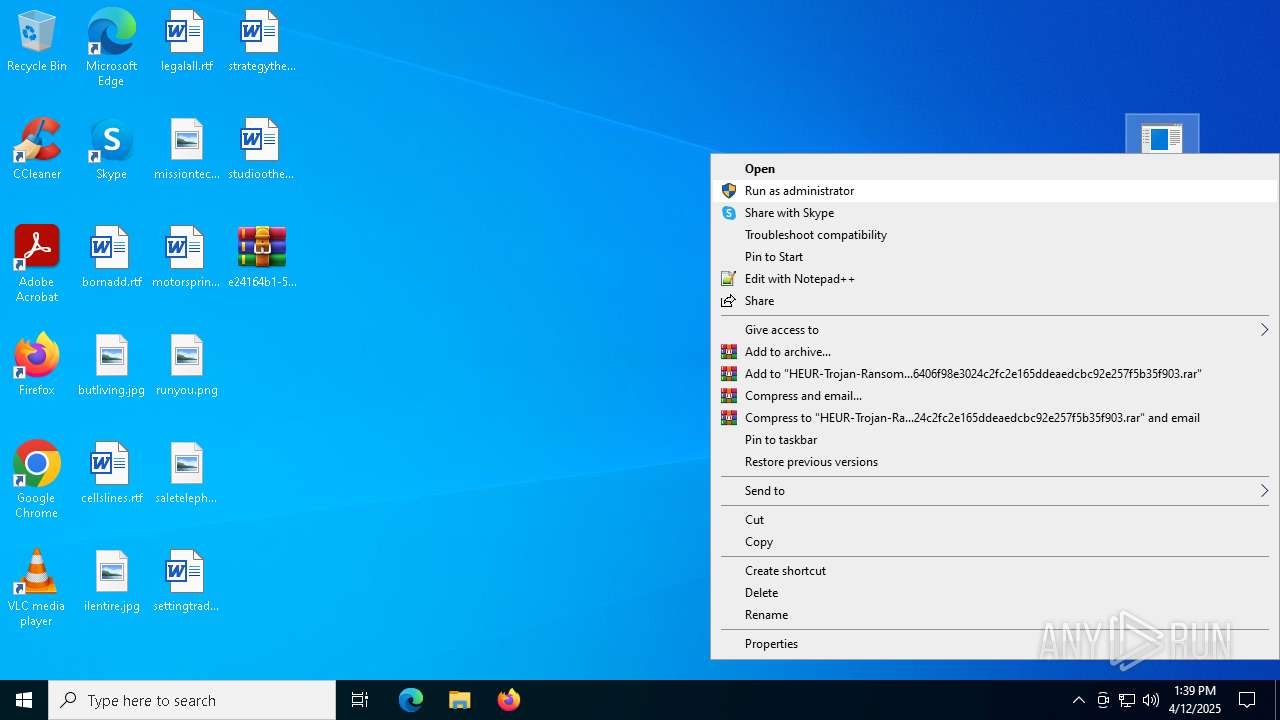
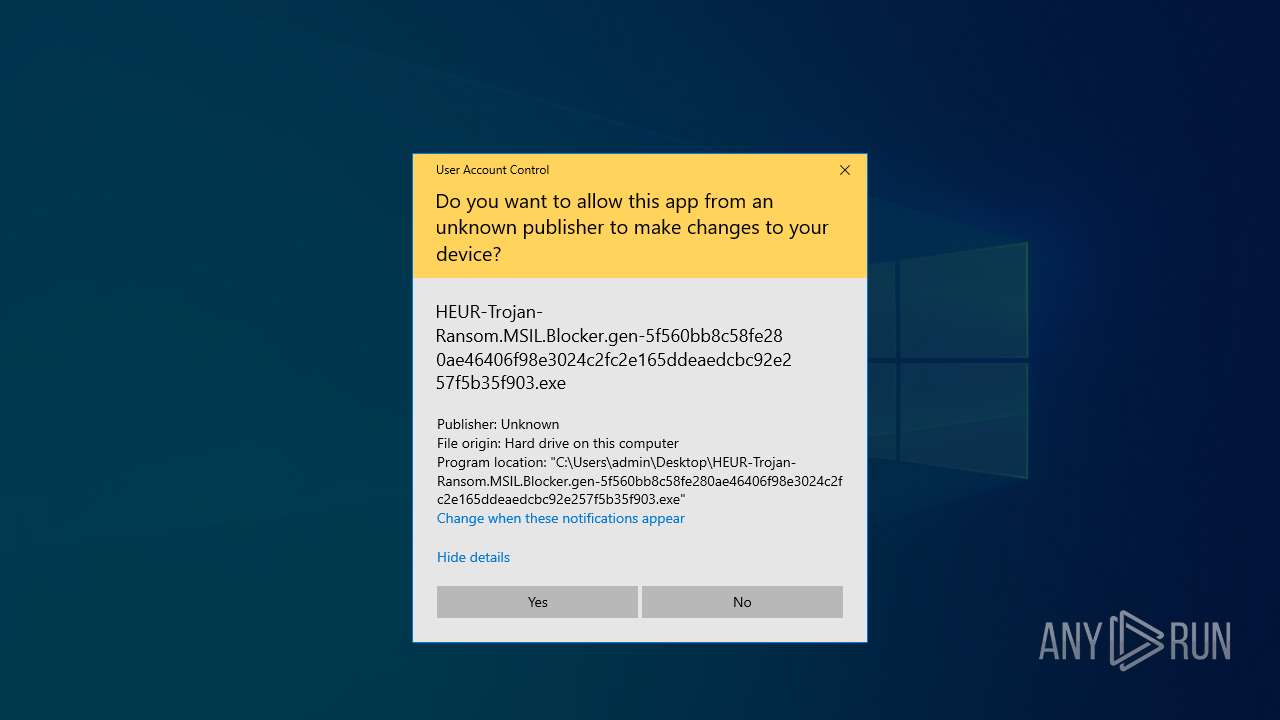
Manual execution by a user
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 896)
Checks supported languages
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- winint.exe (PID: 4896)
- winint.exe (PID: 5008)
- javaw.exe (PID: 6132)
- java.exe (PID: 7516)
Process checks computer location settings
- HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe (PID: 7892)
- winint.exe (PID: 5008)
Reads the software policy settings
- slui.exe (PID: 7252)
- slui.exe (PID: 680)
Disables trace logs
- winint.exe (PID: 5008)
Checks proxy server information
- winint.exe (PID: 5008)
- slui.exe (PID: 680)
Creates files or folders in the user directory
- winint.exe (PID: 5008)
- javaw.exe (PID: 6132)
- xcopy.exe (PID: 6632)
Application based on Java
- javaw.exe (PID: 6132)
Creates files in the program directory
- javaw.exe (PID: 6132)
Create files in a temporary directory
- javaw.exe (PID: 6132)
- java.exe (PID: 7516)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1128)
- cscript.exe (PID: 4068)
- cscript.exe (PID: 7728)
- cscript.exe (PID: 7744)
The sample compiled with english language support
- xcopy.exe (PID: 6632)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2019:05:31 07:54:48+00:00 |
| ArchivedFileName: | HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe |
Total processes
166
Monitored processes
37
Malicious processes
6
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\e24164b1-51f0-4d2e-be13-d9940200a57c.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 904 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive2107323938162792485.vbs | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4068 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive1042333025721953214.vbs | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 4200 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4428 | "C:\Windows\System32\cmd.exe" /c copy "C:\Users\admin\Desktop\HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe" "C:\Users\admin\AppData\Local\winint.exe" | C:\Windows\SysWOW64\cmd.exe | HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "C:\Windows\System32\cmd.exe" /c, "C:\Users\admin\AppData\Local\winint.exe" | C:\Windows\SysWOW64\cmd.exe | — | HEUR-Trojan-Ransom.MSIL.Blocker.gen-5f560bb8c58fe280ae46406f98e3024c2fc2e165ddeaedcbc92e257f5b35f903.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4784 | cmd.exe | C:\Windows\System32\cmd.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 011
Read events
16 970
Write events
41
Delete events
0
Modification events
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\e24164b1-51f0-4d2e-be13-d9940200a57c.7z | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (896) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
160
Suspicious files
21
Text files
107
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4428 | cmd.exe | C:\Users\admin\AppData\Local\winint.exe | executable | |
MD5:00026F4DF326D91BE6E5AF6AD63DD440 | SHA256:5F560BB8C58FE280AE46406F98E3024C2FC2E165DDEAEDCBC92E257F5B35F903 | |||
| 6632 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\THIRDPARTYLICENSEREADME-JAVAFX.txt | text | |
MD5:F3AF2718F86B00497FA423046F50CEE6 | SHA256:4E4079BD53B742D9D6F18FBD06F743C28285F1E4B9FFD636D2D24A70A2EE7F00 | |||
| 6132 | javaw.exe | C:\Users\admin\AppData\Local\Temp\_0.98503466757266987004064321965830818.class | java | |
MD5:781FB531354D6F291F1CCAB48DA6D39F | SHA256:97D585B6AFF62FB4E43E7E6A5F816DCD7A14BE11A88B109A9BA9E8CD4C456EB9 | |||
| 7516 | java.exe | C:\Users\admin\AppData\Local\Temp\Retrive4452688103772277687.vbs | text | |
MD5:A32C109297ED1CA155598CD295C26611 | SHA256:45BFE34AA3EF932F75101246EB53D032F5E7CF6D1F5B4E495334955A255F32E7 | |||
| 6132 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:E9B6CEC32EA3EB6B270BB1E6BAC1E481 | SHA256:FF9326128DFA797555C95968D057558396024206D913CC763D7667271D3C0362 | |||
| 6132 | javaw.exe | C:\Users\admin\AppData\Local\Temp\Retrive1042333025721953214.vbs | text | |
MD5:3BDFD33017806B85949B6FAA7D4B98E4 | SHA256:9DA575DD2D5B7C1E9BAB8B51A16CDE457B3371C6DCDB0537356CF1497FA868F6 | |||
| 5008 | winint.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\tsd.jar | java | |
MD5:7DA7000CA39CE69997BBCAD56FA8D180 | SHA256:9D817B32FD59DBBE3A17F0C73D4BE0B3301DF89BE5389BB2E81532BDA93E34F8 | |||
| 6132 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\83aa4cc77f591dfc2374580bbd95f6ba_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
| 5008 | winint.exe | C:\Users\admin\AppData\Roaming\MyOtApp\MyOtApp.exe | executable | |
MD5:00026F4DF326D91BE6E5AF6AD63DD440 | SHA256:5F560BB8C58FE280AE46406F98E3024C2FC2E165DDEAEDCBC92E257F5B35F903 | |||
| 7516 | java.exe | C:\Users\admin\AppData\Local\Temp\Retrive2107323938162792485.vbs | text | |
MD5:3BDFD33017806B85949B6FAA7D4B98E4 | SHA256:9DA575DD2D5B7C1E9BAB8B51A16CDE457B3371C6DCDB0537356CF1497FA868F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
18
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8060 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5008 | winint.exe | GET | 200 | 193.122.130.0:80 | http://checkip.dyndns.org/ | unknown | — | — | whitelisted |
8060 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.36:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
8060 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET DYN_DNS External IP Lookup Domain in DNS Query (checkip .dyndns .org) |
5008 | winint.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - checkip.dyndns.org |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.duckdns .org Domain |
2196 | svchost.exe | Misc activity | ET DYN_DNS DYNAMIC_DNS Query to *.duckdns. Domain |