| download: | /most-x86_64 |
| Full analysis: | https://app.any.run/tasks/5b99b013-6500-4571-8ad2-03839e24309c |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | March 03, 2024, 21:21:36 |
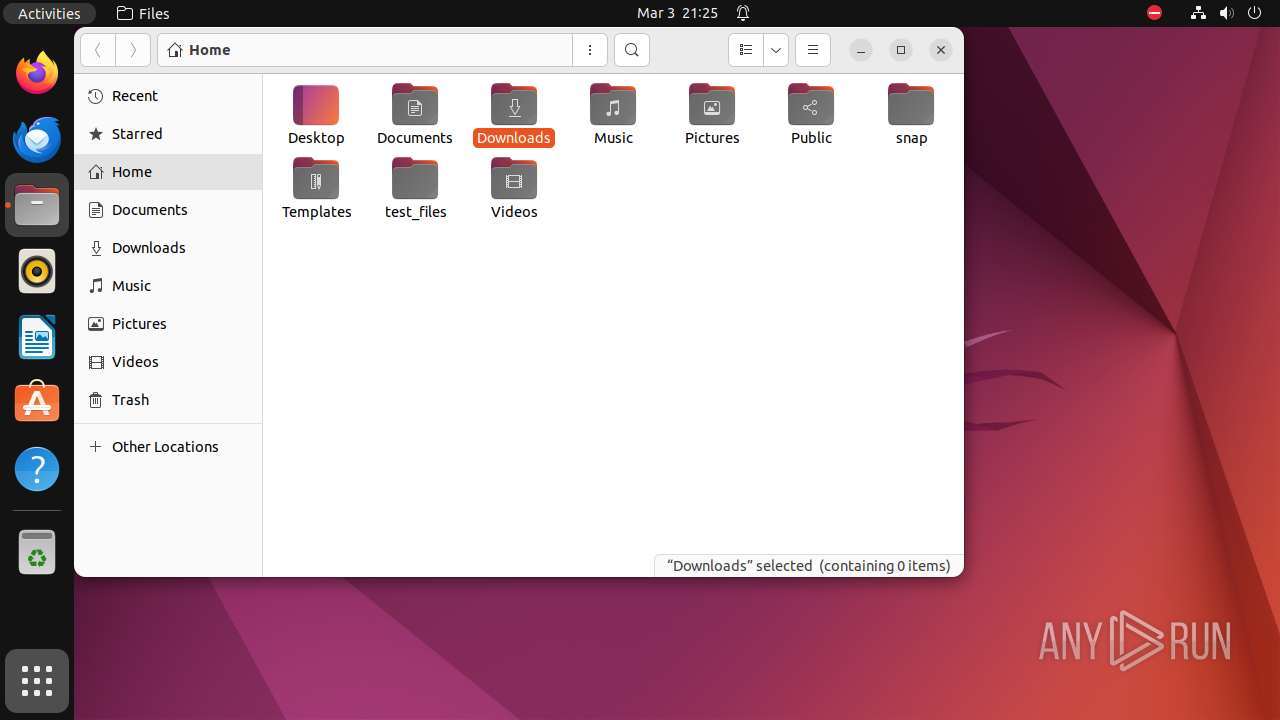
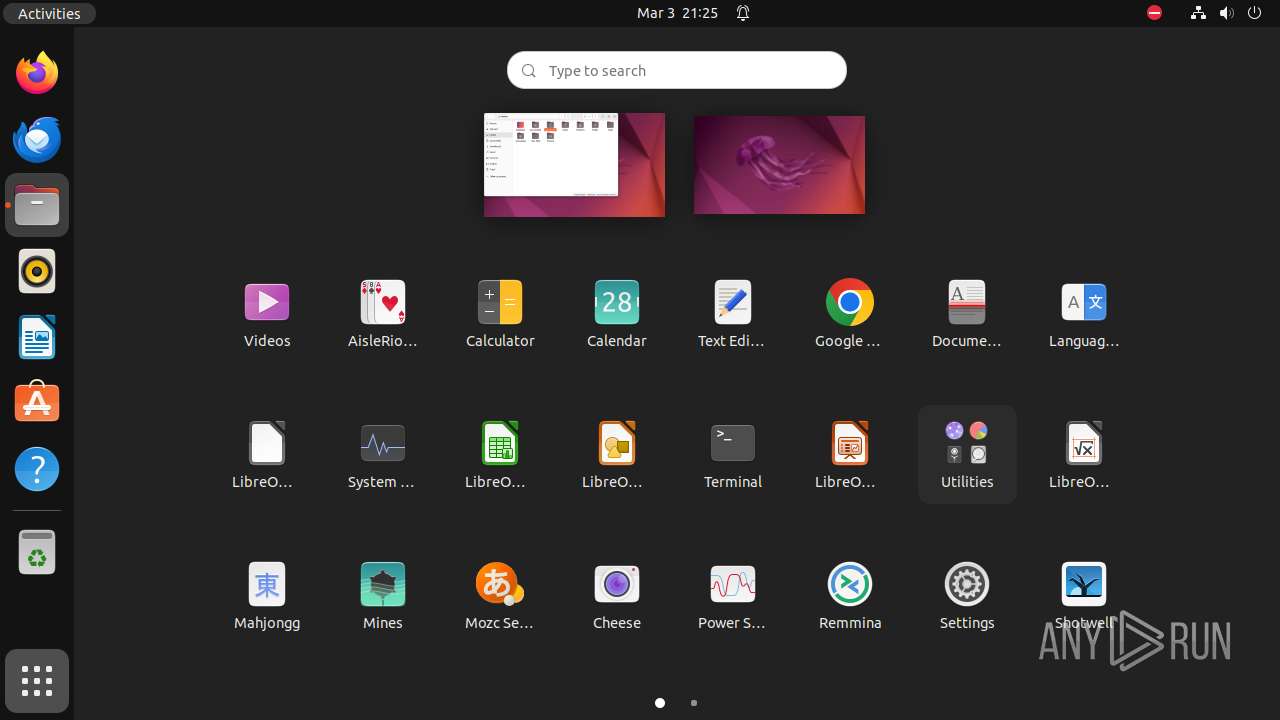
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| MIME: | application/x-executable |
| File info: | ELF 64-bit LSB executable, x86-64, version 1 (SYSV), statically linked, stripped |
| MD5: | 0A5EB722E526DC6F20AFCF8AF9C7E745 |
| SHA1: | FD45B8E182B7CAB2D967A08CE1B1976407B7146F |
| SHA256: | 8D216EA054731B16721C2F25CD2EAA85D780CD27B72DE95E88F564128EF68F12 |
| SSDEEP: | 6144:VUpD2jCJJDQQJmAykm1bT4R6+bKz4lRl:VUpD2jCJJDQQJmAykmN0R6+L7l |
MALICIOUS
No malicious indicators.SUSPICIOUS
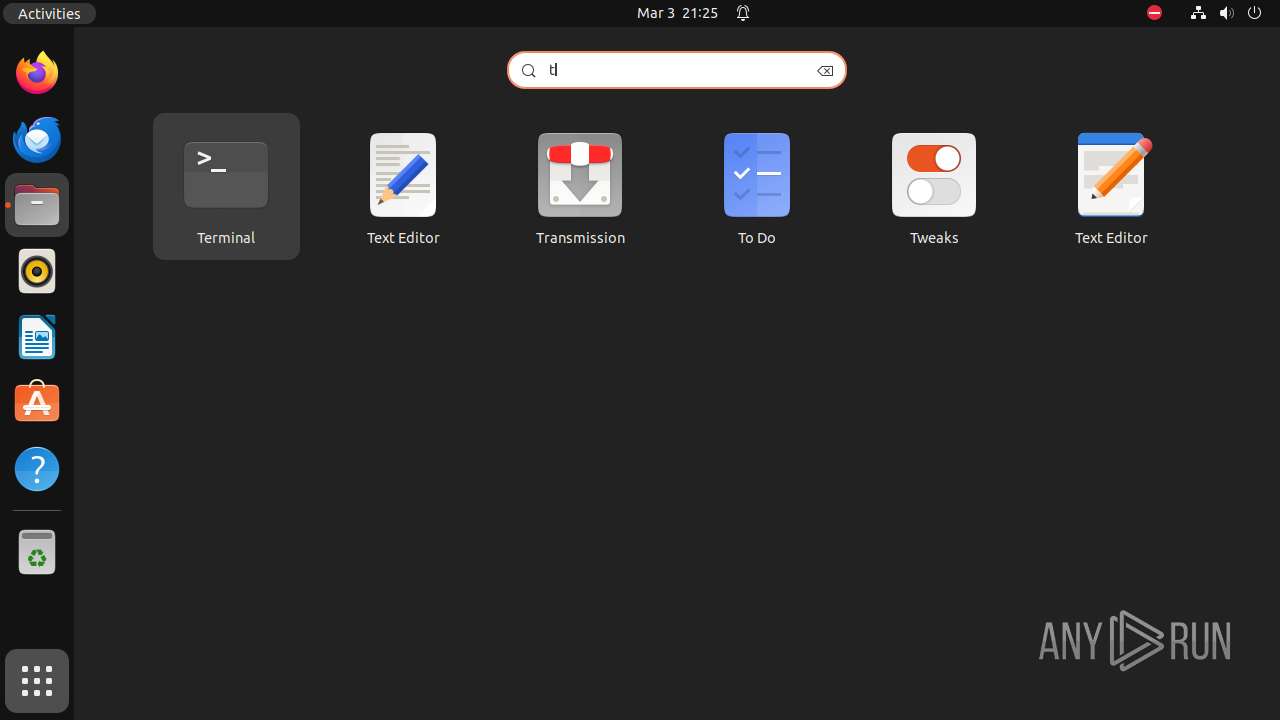
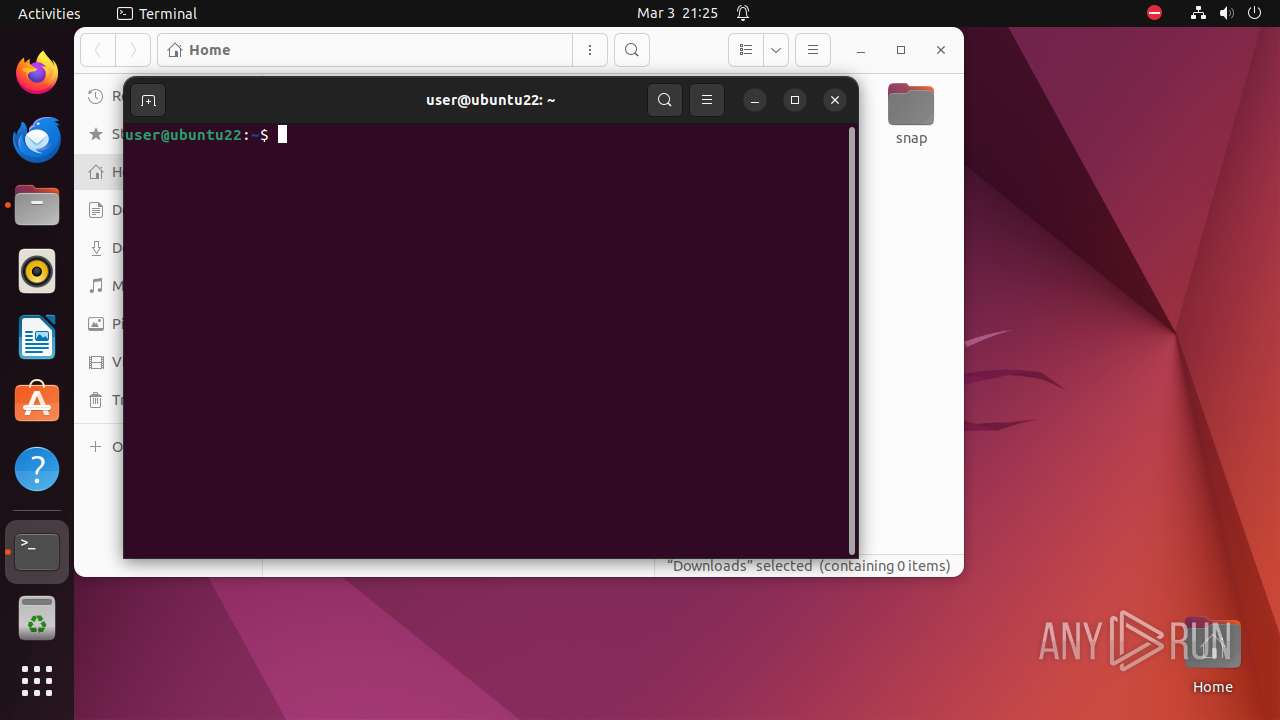
Executes commands using command-line interpreter
- bash (PID: 9308)
Modifies file or directory owner
- sudo (PID: 9302)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .o | | | ELF Executable and Linkable format (generic) (100) |
|---|
EXIF
EXE
| CPUArchitecture: | 64 bit |
|---|---|
| CPUByteOrder: | Little endian |
| ObjectFileType: | Executable file |
| CPUType: | AMD x86-64 |
Total processes
237
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 9301 | /bin/sh -c "sudo chown user \"/tmp/most-x86_64\.o\" && chmod +x \"/tmp/most-x86_64\.o\" && DISPLAY=:0 sudo -i \"/tmp/most-x86_64\.o\" " | /bin/sh | — | any-guest-agent |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9302 | sudo chown user /tmp/most-x86_64.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9303 | chown user /tmp/most-x86_64.o | /usr/bin/chown | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9304 | chmod +x /tmp/most-x86_64.o | /usr/bin/chmod | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9305 | sudo -i /tmp/most-x86_64.o | /usr/bin/sudo | — | sh |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9306 | /tmp/most-x86_64.o | /tmp/most-x86_64.o | — | sudo |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9307 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | most-x86_64.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9308 | -bash --login -c \/tmp\/most-x86_64\.o | /usr/bin/bash | — | most-x86_64.o |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9309 | sh -c "cat /usr/etc/debuginfod/*\.urls 2>/dev/null" | /usr/bin/sh | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 9310 | tr \n " " | /usr/bin/tr | — | bash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
7
DNS requests
9
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
— | — | GET | 204 | 185.125.190.48:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | unknown |
— | — | 103.28.33.96:2023 | NET-KILLER.WORK.GD | VIET DIGITAL TECHNOLOGY LIABILITY COMPANY | VN | unknown |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
NET-KILLER.WORK.GD |
| unknown |
connectivity-check.ubuntu.com |
| unknown |
api.snapcraft.io |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.work .gd Domain |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant CnC Checkin M1 (Group String Len 1) |
— | — | Misc Attack | ET CINS Active Threat Intelligence Poor Reputation IP group 88 |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |
— | — | Malware Command and Control Activity Detected | ET MALWARE ELF/MooBot Mirai DDoS Variant Server Response |