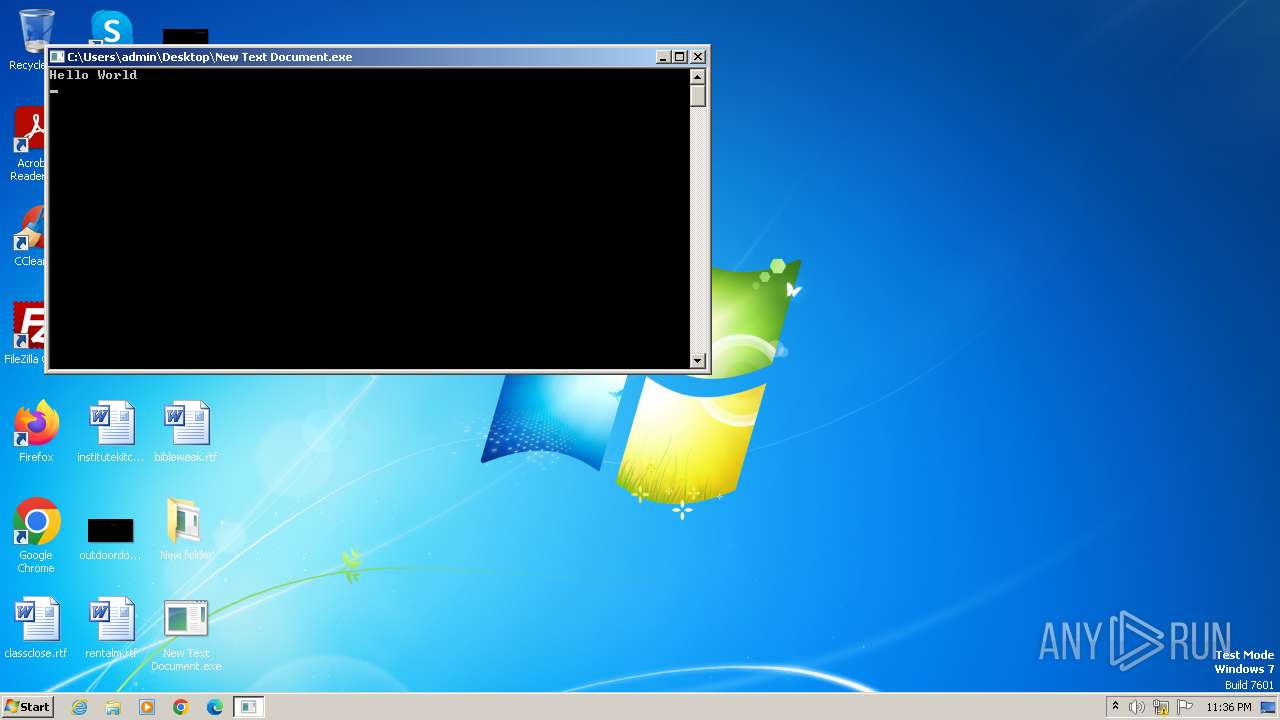
| File name: | New Text Document.exe |
| Full analysis: | https://app.any.run/tasks/ccdbfee0-cf1c-402c-8b19-8d2978031285 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | December 02, 2023, 23:36:10 |
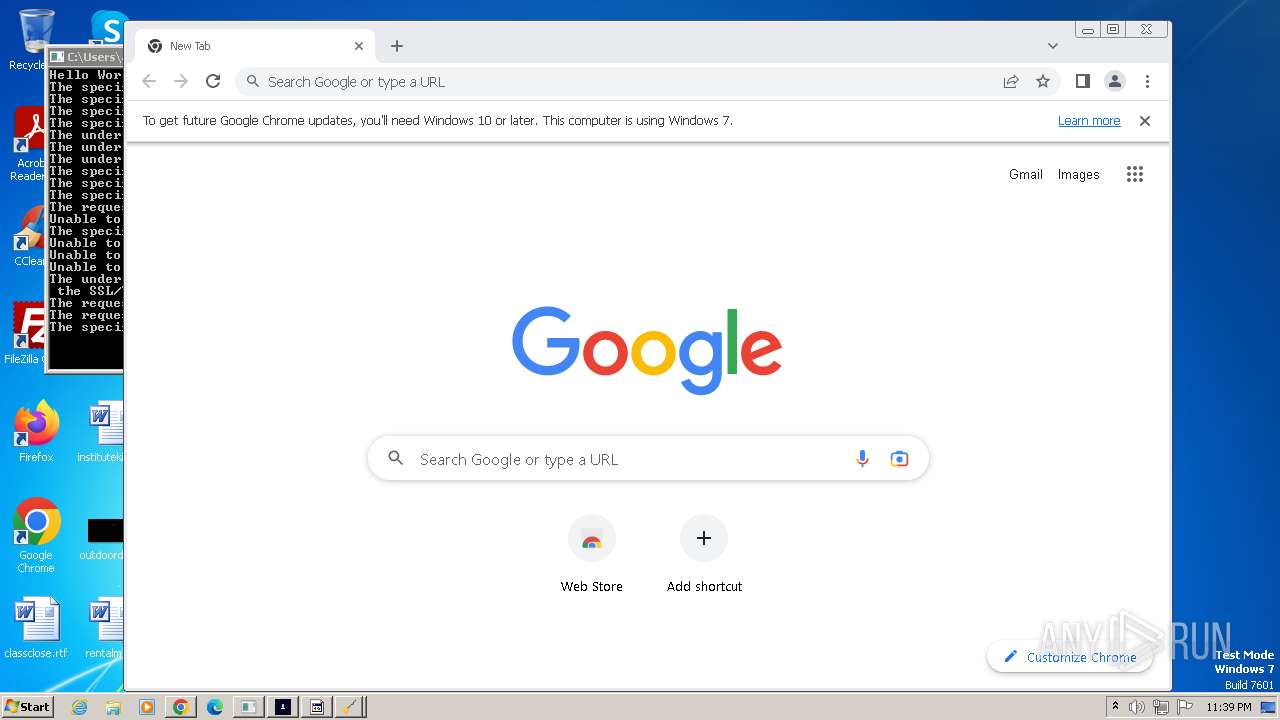
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 9CE4AAFFC0CDDB25B759E1EC9AB7102A |
| SHA1: | 72E78508B65D61D4AE9620D180F4AA8DDDB85399 |
| SHA256: | 8CC12EE9B2F09003DED9CA3E1846ED23B63325FE8D867E735A3388A9087BD87C |
| SSDEEP: | 48:YRgXv7UgA0zDJZZJO2HdrPmckulbfSqXSfbNtm:pXzR96ypf6zNt |
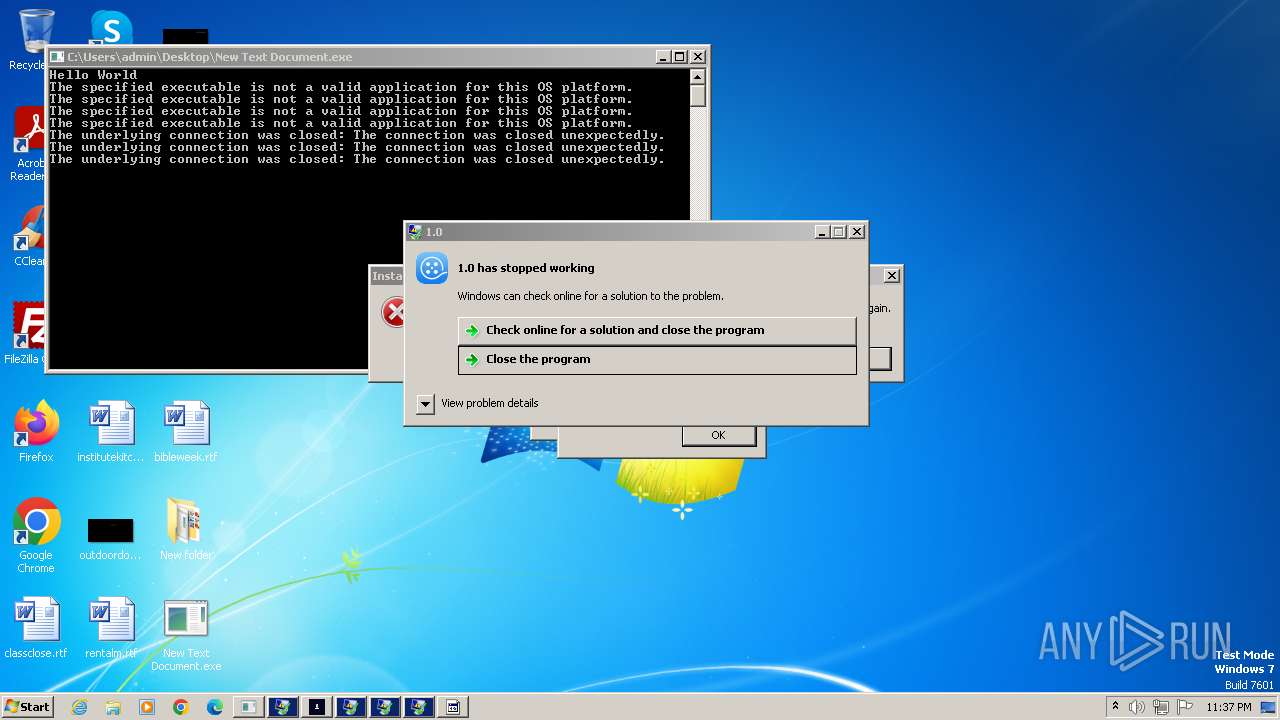
MALICIOUS
KELIHOS has been detected (SURICATA)
- New Text Document.exe (PID: 2644)
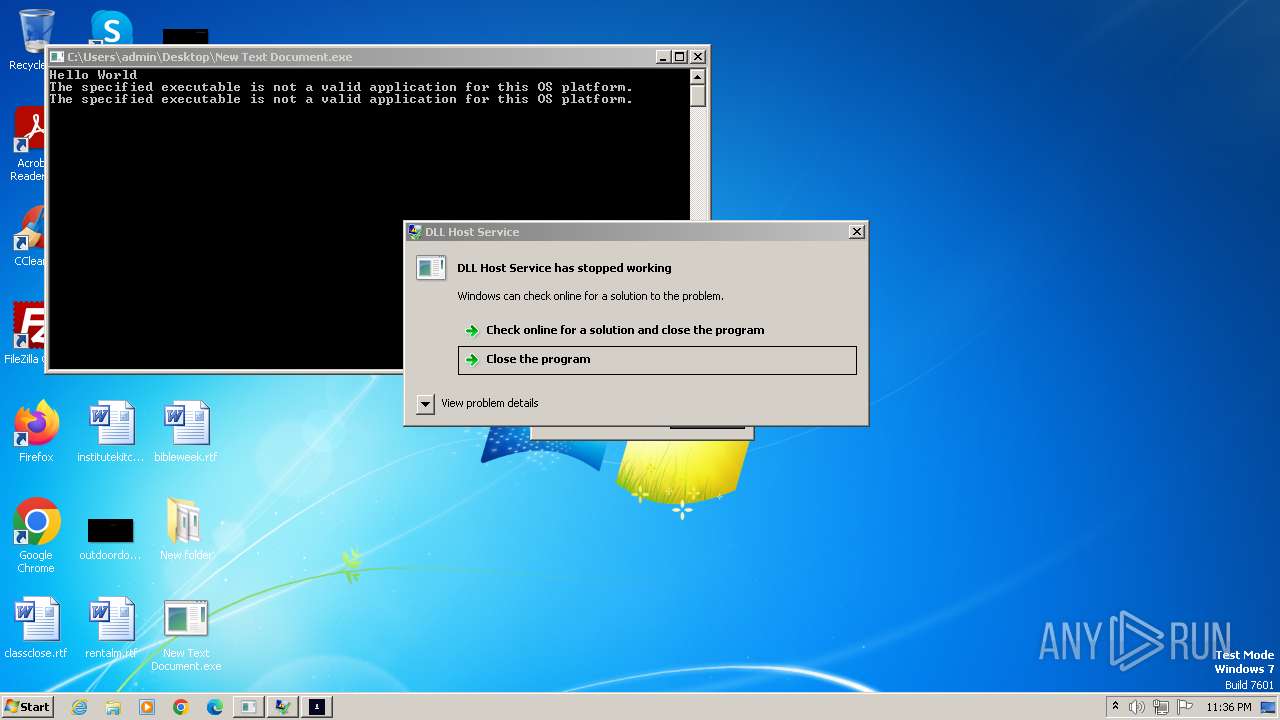
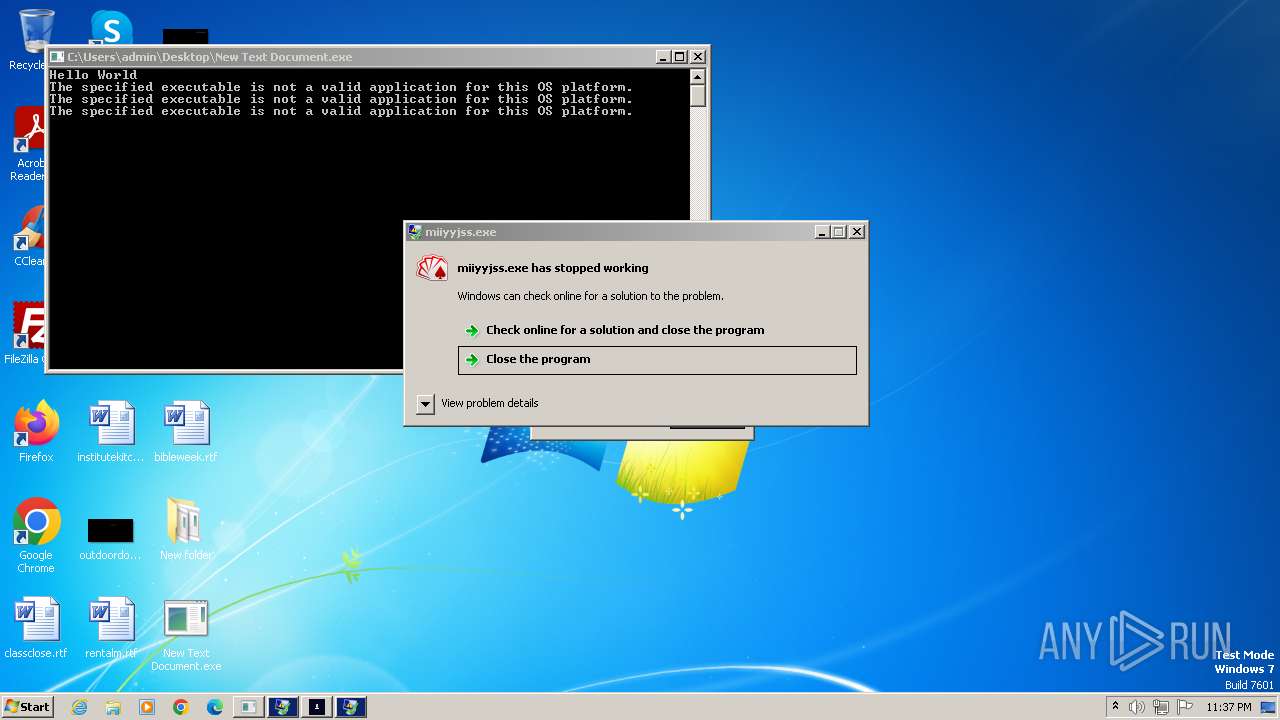
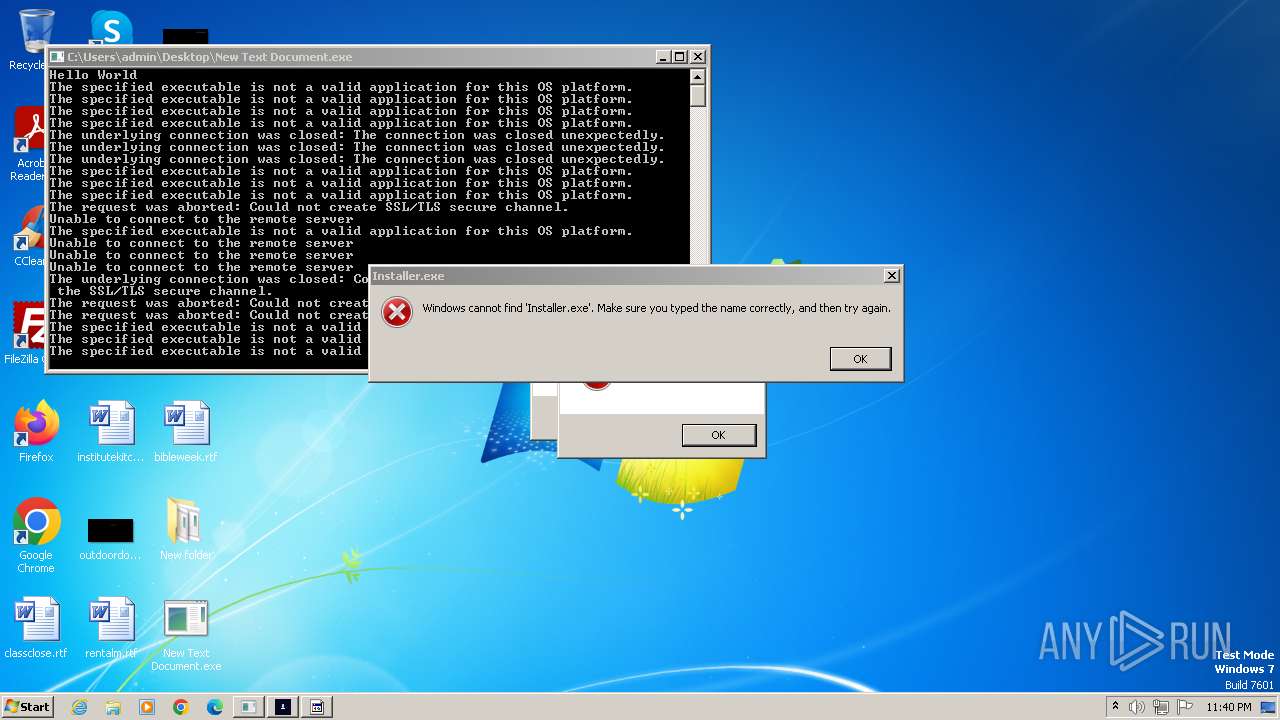
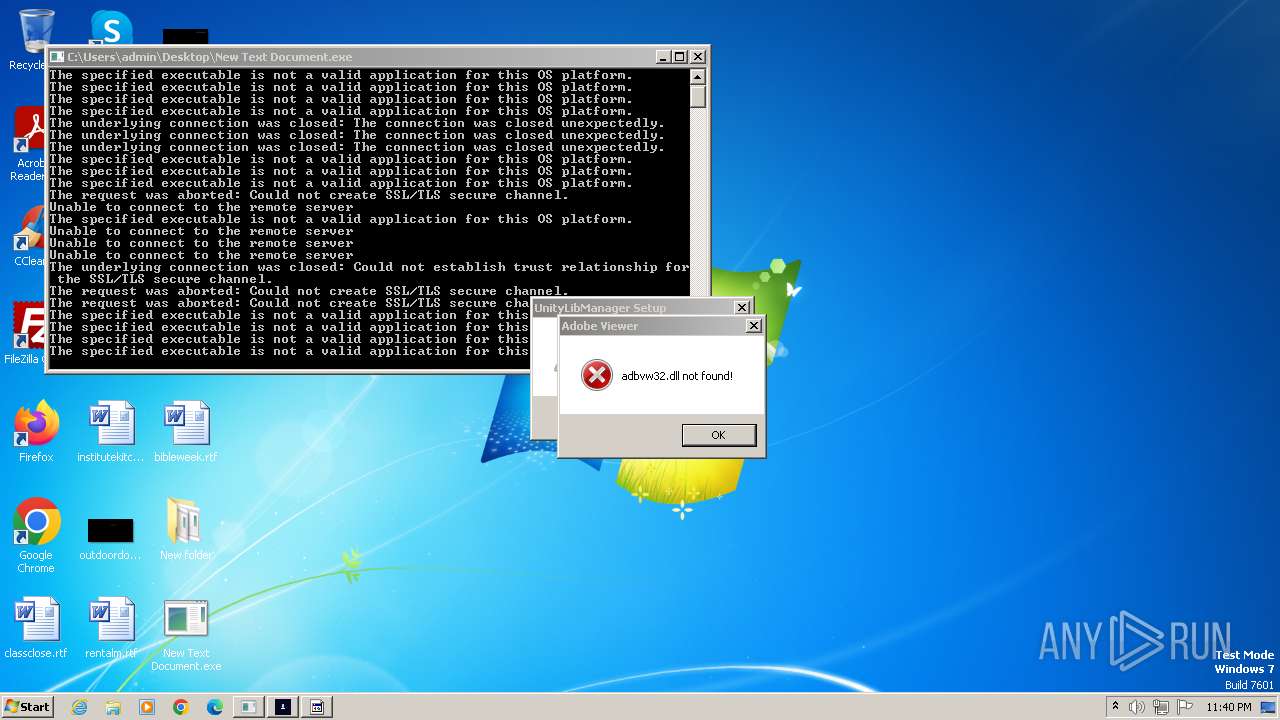
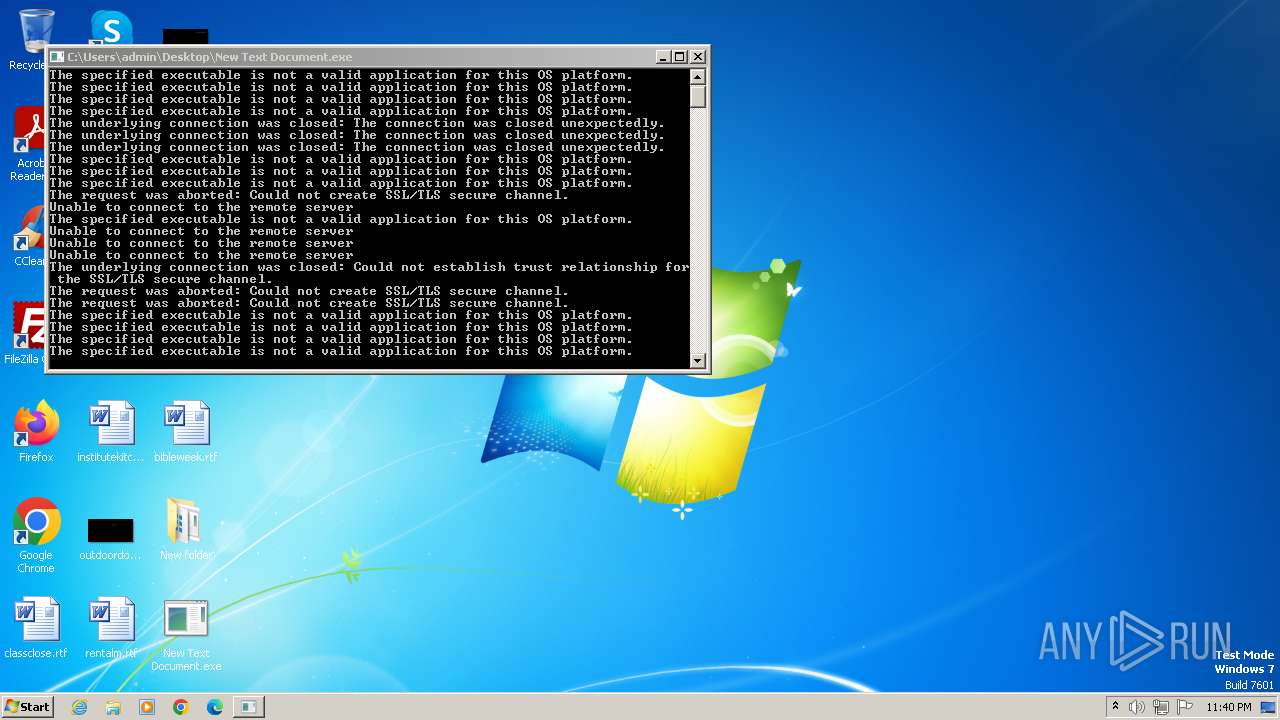
Drops the executable file immediately after the start
- UnityLibManager.exe (PID: 1840)
- New Text Document.exe (PID: 2644)
- twelv.exe (PID: 3864)
- good.exe (PID: 3340)
- 1701007523-Hzxlsavkq.exe (PID: 3916)
- herewgo.exe (PID: 2456)
- DCRatBuild.exe (PID: 3800)
- wlanext.exe (PID: 3812)
- syncUpd.exe (PID: 1272)
- ansi.exe (PID: 1640)
- conhost.exe (PID: 3052)
- webplugin.exe (PID: 3944)
- wlanext2.exe (PID: 1184)
- GoogleUpdateSetup.exe (PID: 1892)
- GoogleUpdate.exe (PID: 3700)
- hv.exe (PID: 3648)
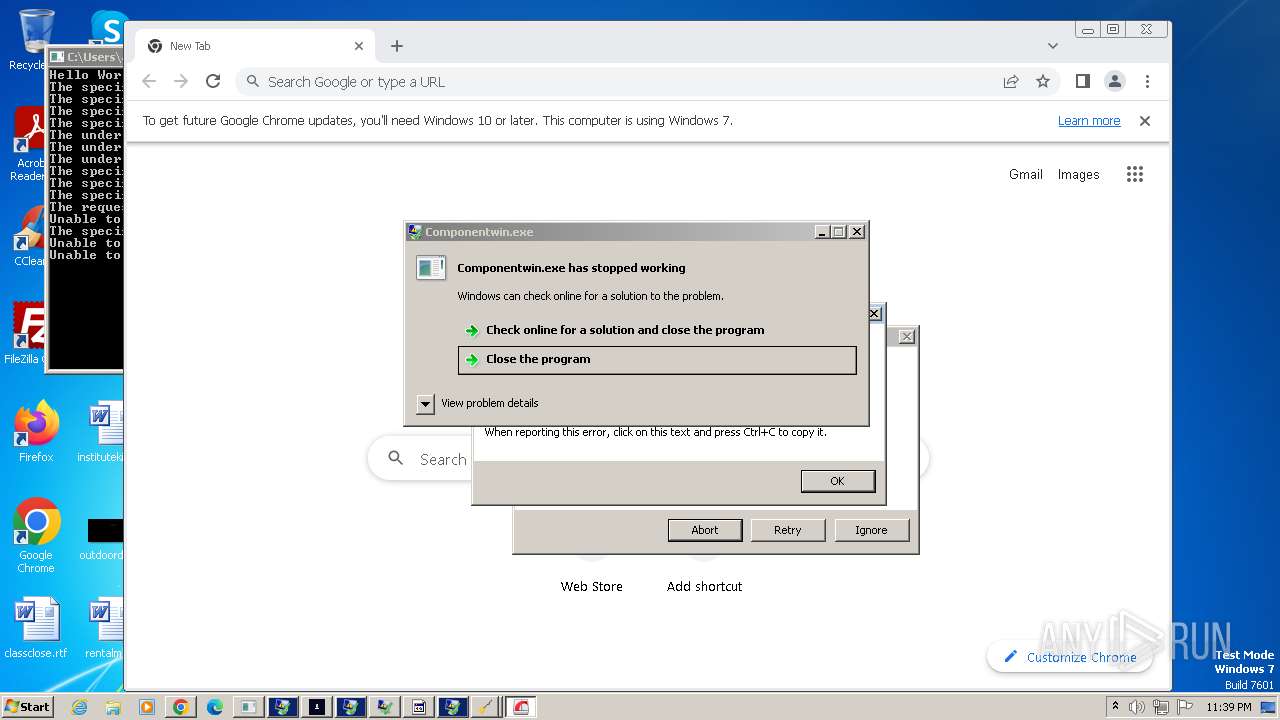
- Componentwin.exe (PID: 2744)
- CasPol.exe (PID: 1636)
- Zdznzuwlua.exe (PID: 2324)
- CasPol.exe (PID: 3964)
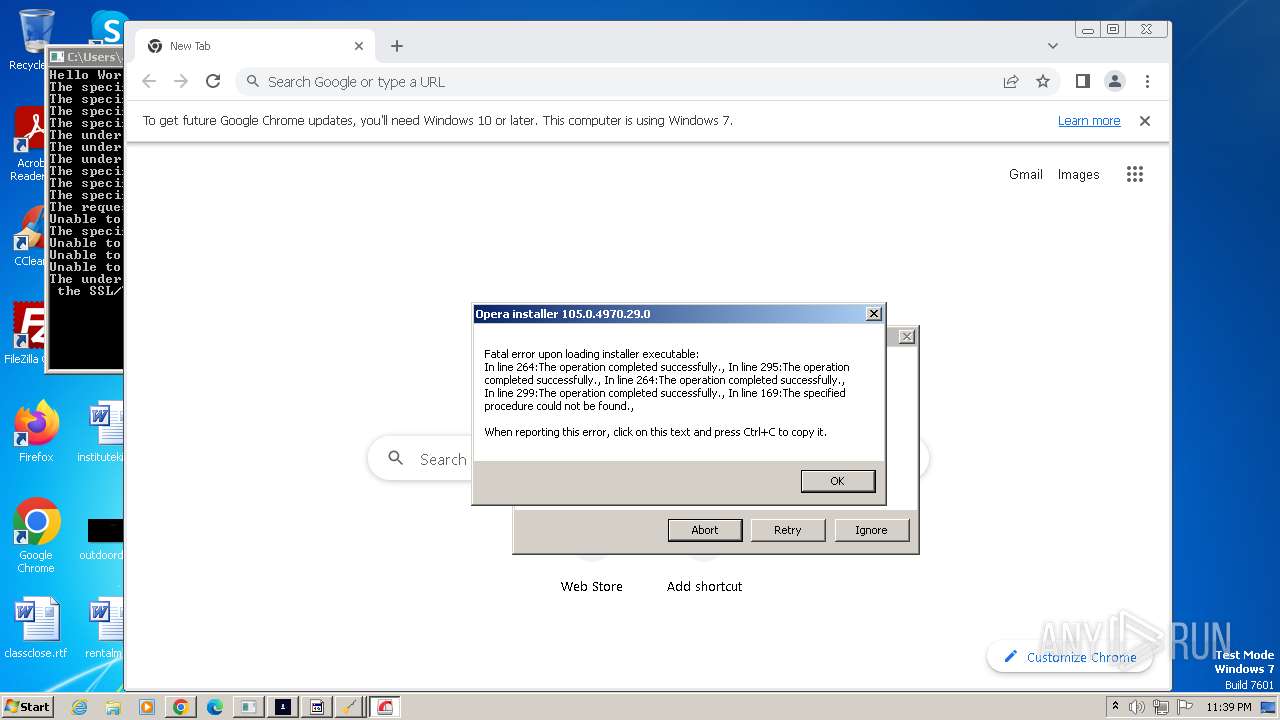
- 109.0.5414.120_chrome_installer.exe (PID: 2932)
- server1.exe (PID: 1784)
- MSBuild.exe (PID: 3304)
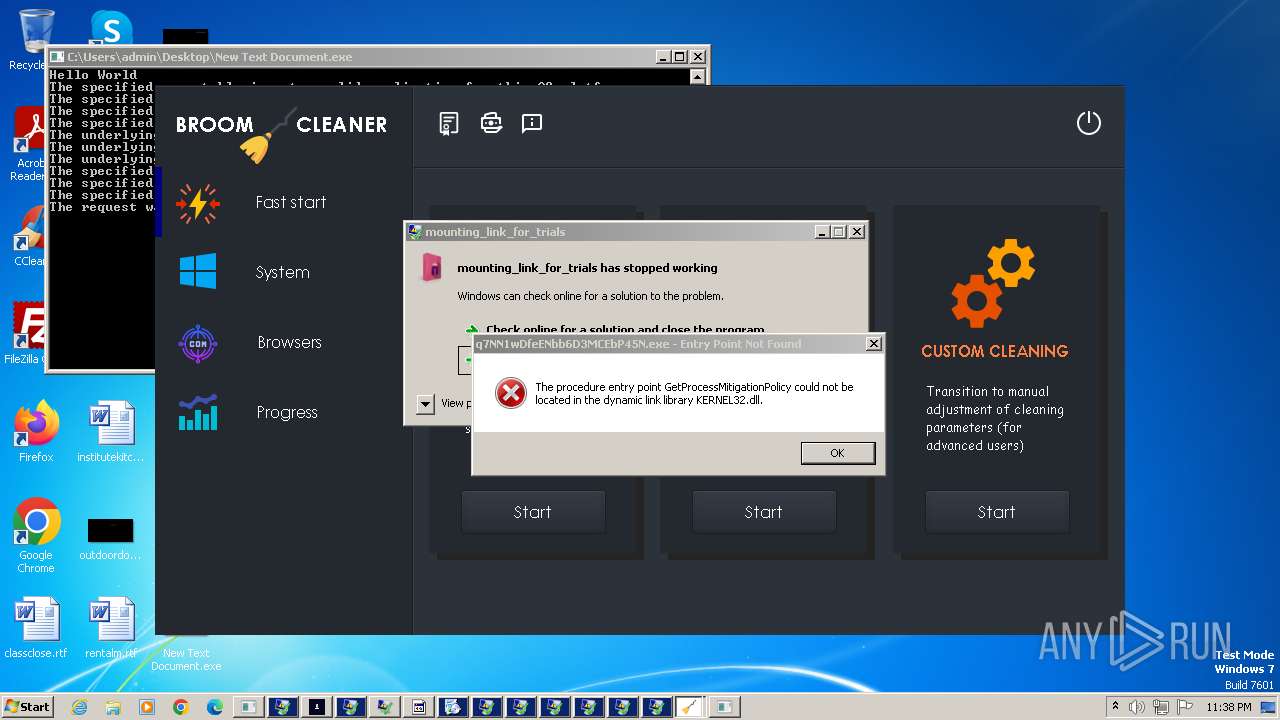
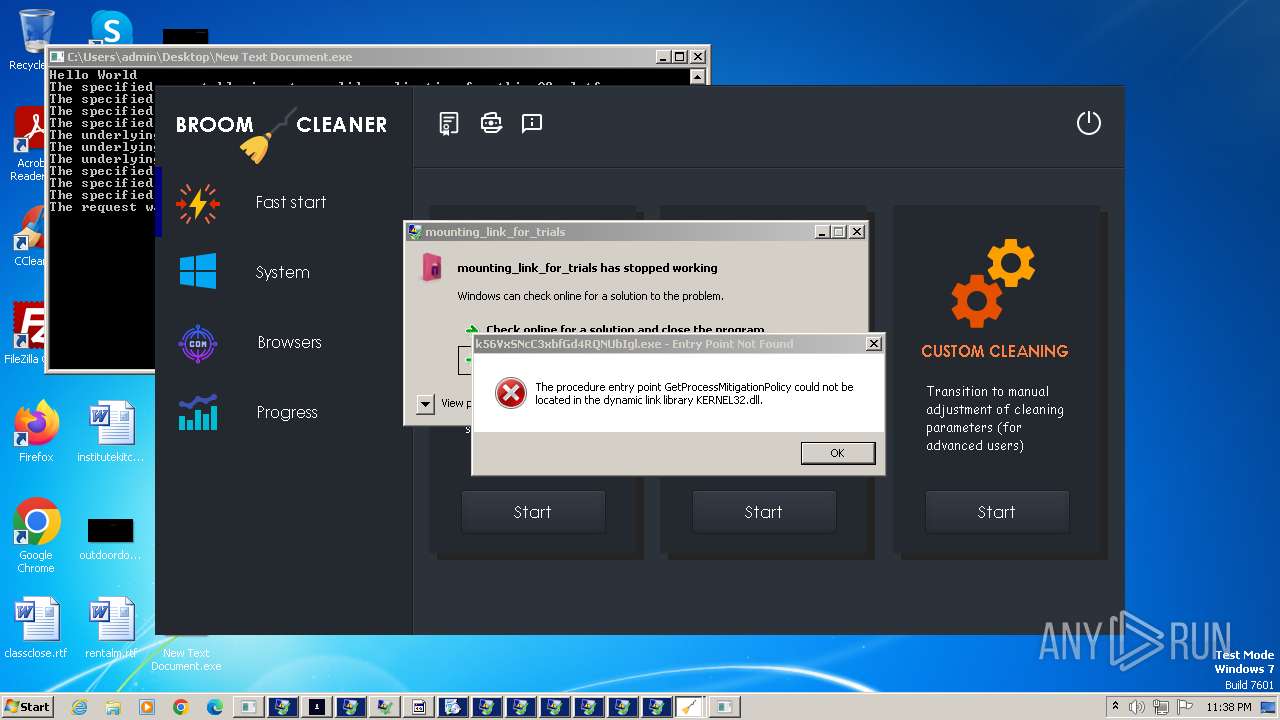
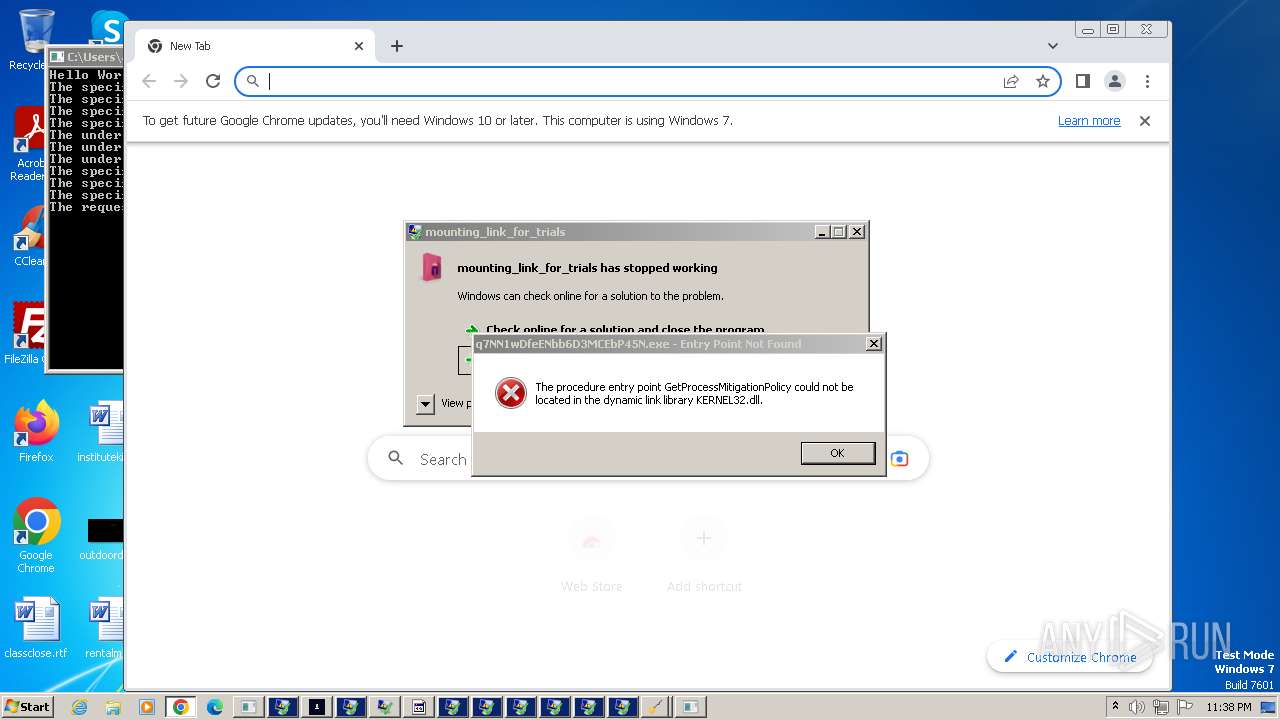
- q7NN1wDfeENbb6D3MCEbP45N.exe (PID: 4612)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
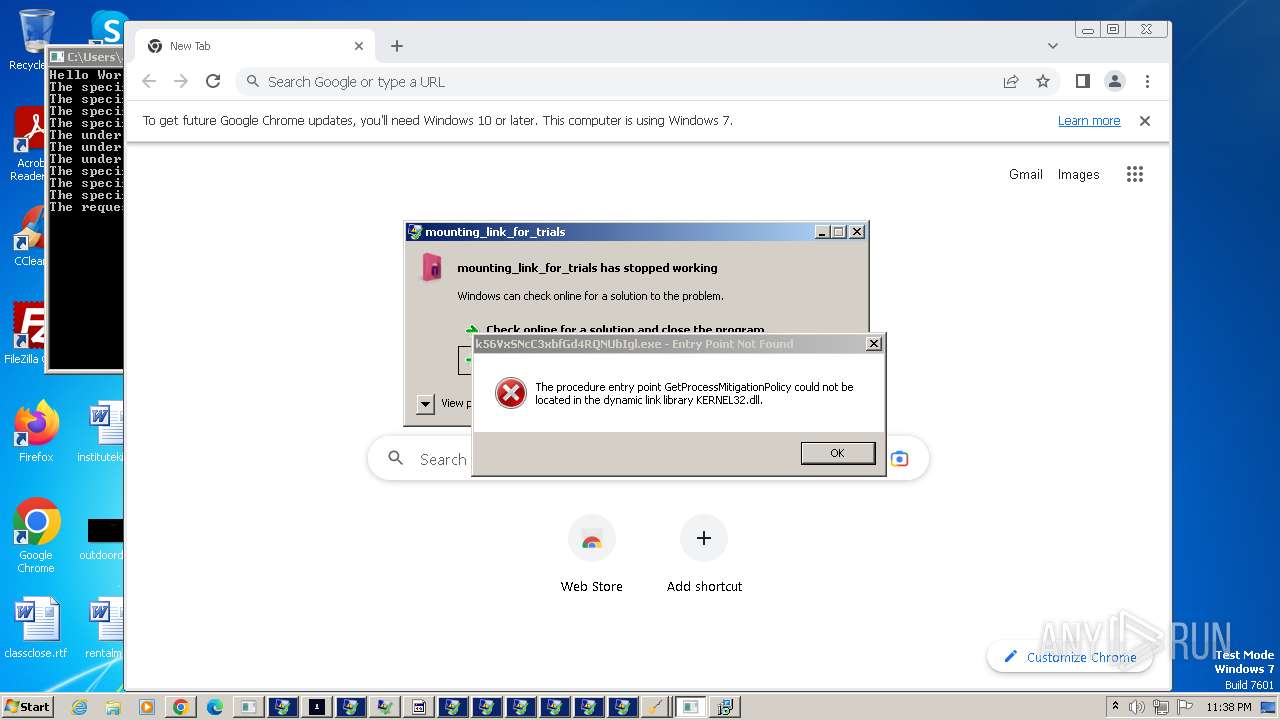
- k56VxSNcC3xbfGd4RQNUbIgl.exe (PID: 4796)
- Fineone.exe (PID: 3124)
- setup.exe (PID: 4132)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- RjHZd4onCafeVZFcIKCxbmRH.exe (PID: 5168)
- mX47fTMx5avZgqFSbqDisbAs.exe (PID: 4368)
- eKjcQRswIpDI0FBmml1mhMI8.exe (PID: 4492)
- eKjcQRswIpDI0FBmml1mhMI8.exe (PID: 3544)
- mX47fTMx5avZgqFSbqDisbAs.exe (PID: 5124)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- cp.exe (PID: 292)
- tuc3.exe (PID: 5360)
- tuc3.exe (PID: 5924)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- SupportCD.exe (PID: 5368)
- tuc3.tmp (PID: 5992)
- timeSync.exe (PID: 6008)
- decord.exe (PID: 4208)
- tuc5.exe (PID: 5272)
- tuc5.exe (PID: 5212)
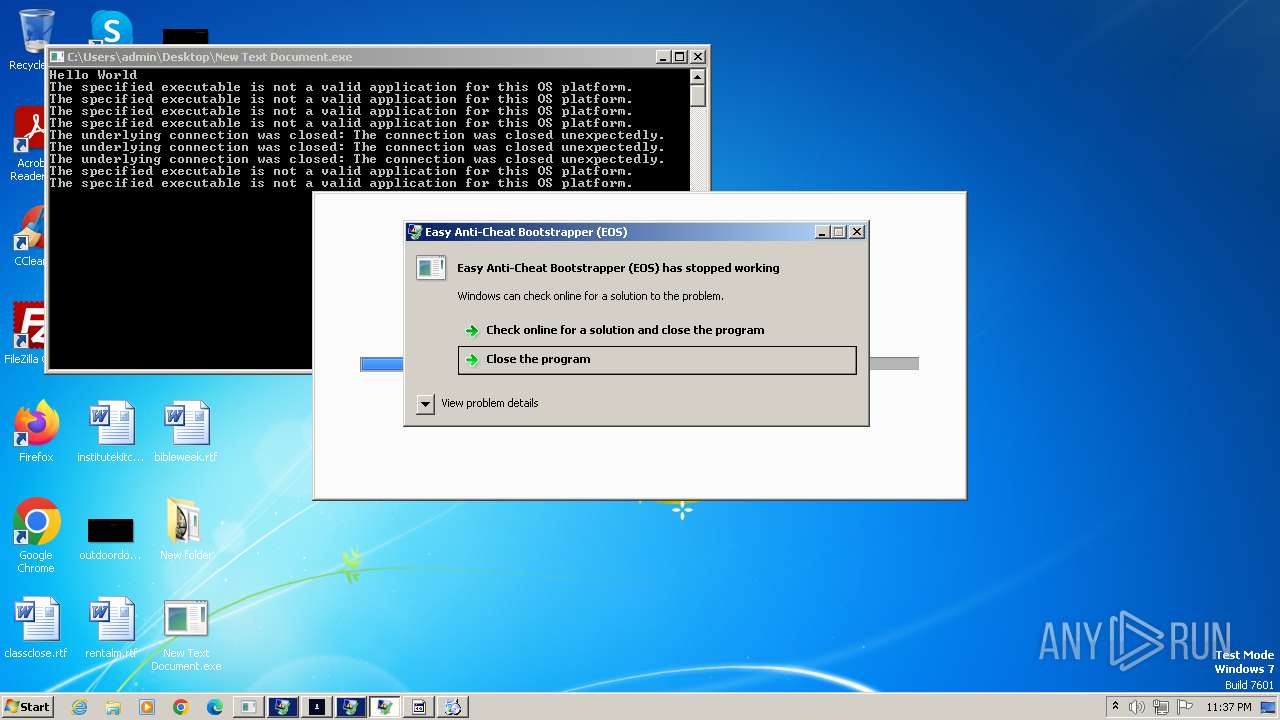
- InstallSetup8.exe (PID: 3840)
- tuc5.tmp (PID: 5432)
- plugmanzx.exe (PID: 916)
- ama.exe (PID: 3476)
- nsxC8D7.tmp (PID: 1556)
- InstallSetup9.exe (PID: 4924)
- spml.exe (PID: 3832)
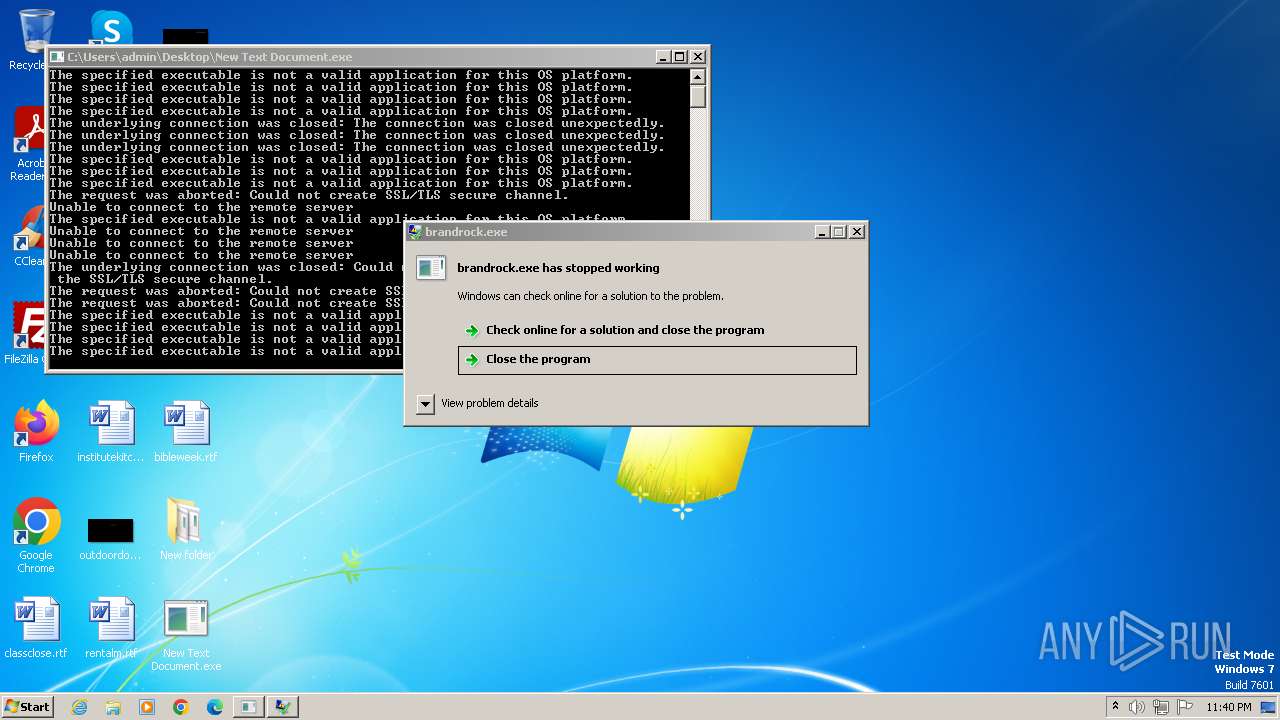
- brandrock.exe (PID: 3608)
- tuc3.exe (PID: 1588)
- tuc3.exe (PID: 4564)
- tuc3.tmp (PID: 6088)
- Utsysc.exe (PID: 5072)
- mpeg4bind.exe (PID: 3748)
- photo_dnkafan3.exe (PID: 3824)
- InstallSetup9.exe (PID: 2224)
Actions looks like stealing of personal data
- twelv.exe (PID: 3864)
- doubbdi.exe (PID: 2128)
- forrrromhanmya.exe (PID: 2432)
- ansi.exe (PID: 1640)
- vbc.exe (PID: 4040)
- vbc.exe (PID: 3612)
- vbc.exe (PID: 3204)
- syncUpd.exe (PID: 1272)
- good.exe (PID: 3340)
- proquota.exe (PID: 4388)
- 3940686746.exe (PID: 5980)
- 1413275631.exe (PID: 5996)
- timeSync.exe (PID: 6008)
- rundll32.exe (PID: 5372)
- photo_dnkafan3.exe (PID: 3824)
Create files in the Startup directory
- good.exe (PID: 3340)
- CasPol.exe (PID: 1636)
- CasPol.exe (PID: 3964)
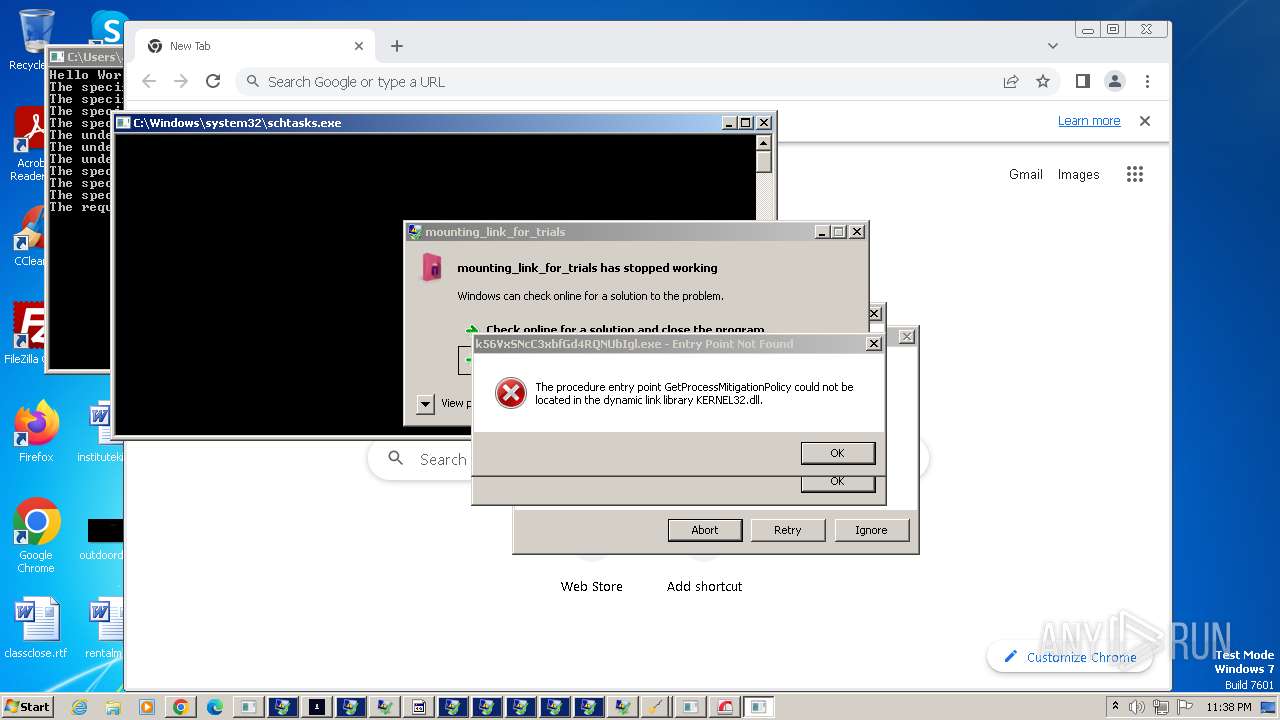
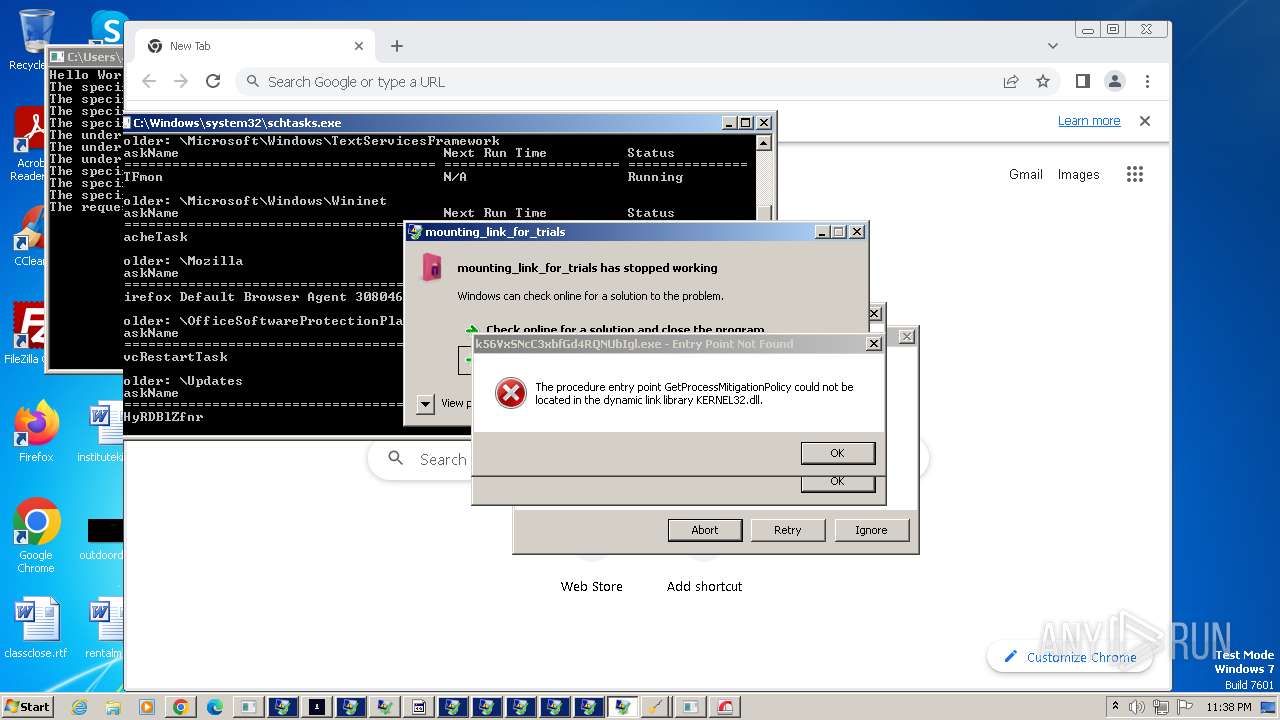
Uses Task Scheduler to autorun other applications
- good.exe (PID: 3340)
Uses Task Scheduler to run other applications
- good.exe (PID: 3340)
- wlanext.exe (PID: 3812)
- Fineone.exe (PID: 3124)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- XRJNZC.exe (PID: 5420)
- Utsysc.exe (PID: 1828)
- Utsysc.exe (PID: 5072)
- tuc3.tmp (PID: 6088)
RISEPRO has been detected (SURICATA)
- good.exe (PID: 3340)
Steals credentials
- good.exe (PID: 3340)
- syncUpd.exe (PID: 1272)
- vbc.exe (PID: 3204)
- vbc.exe (PID: 4040)
- proquota.exe (PID: 4388)
- 3940686746.exe (PID: 5980)
- 1413275631.exe (PID: 5996)
- timeSync.exe (PID: 6008)
- photo_dnkafan3.exe (PID: 3824)
Steals credentials from Web Browsers
- good.exe (PID: 3340)
- doubbdi.exe (PID: 2128)
- forrrromhanmya.exe (PID: 2432)
- ansi.exe (PID: 1640)
- vbc.exe (PID: 3204)
- syncUpd.exe (PID: 1272)
- timeSync.exe (PID: 6008)
- rundll32.exe (PID: 5372)
- photo_dnkafan3.exe (PID: 3824)
Run PowerShell with an invisible window
- powershell.exe (PID: 1888)
- powershell.exe (PID: 4244)
Bypass execution policy to execute commands
- powershell.exe (PID: 1888)
- powershell.exe (PID: 4244)
RISEPRO has been detected (YARA)
- good.exe (PID: 3340)
AGENTTESLA has been detected (SURICATA)
- doubbdi.exe (PID: 2128)
- forrrromhanmya.exe (PID: 2432)
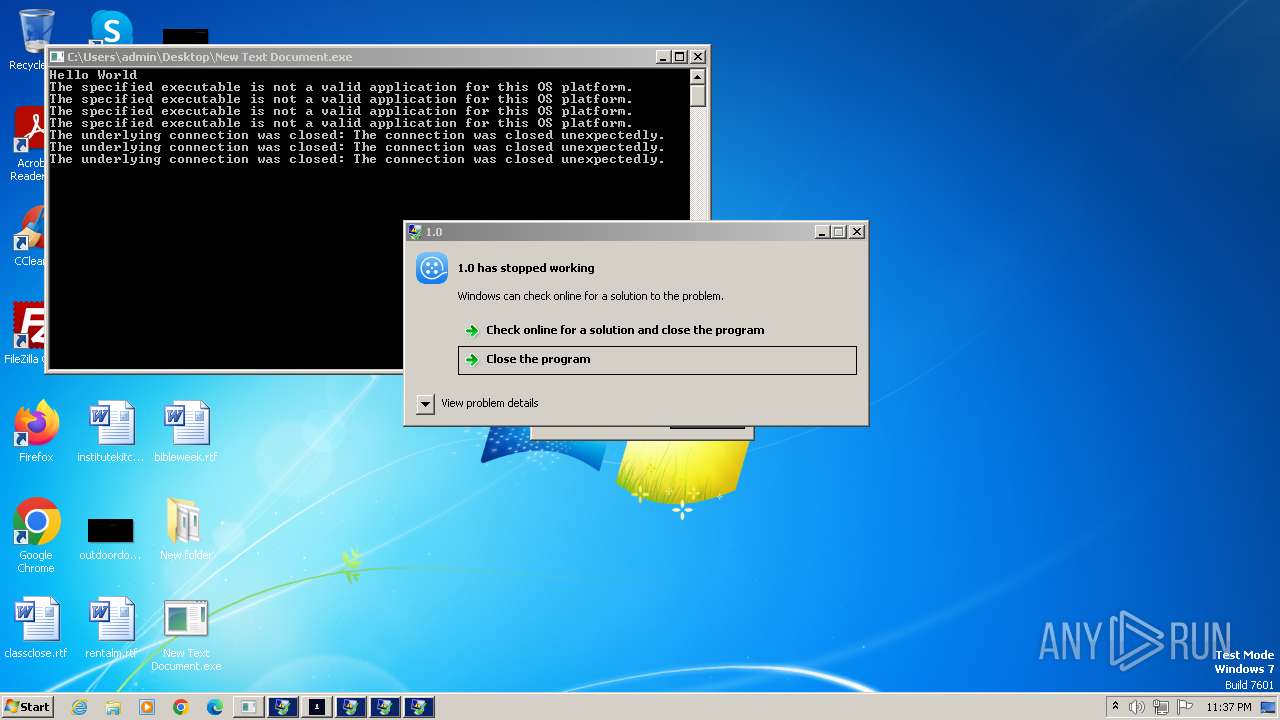
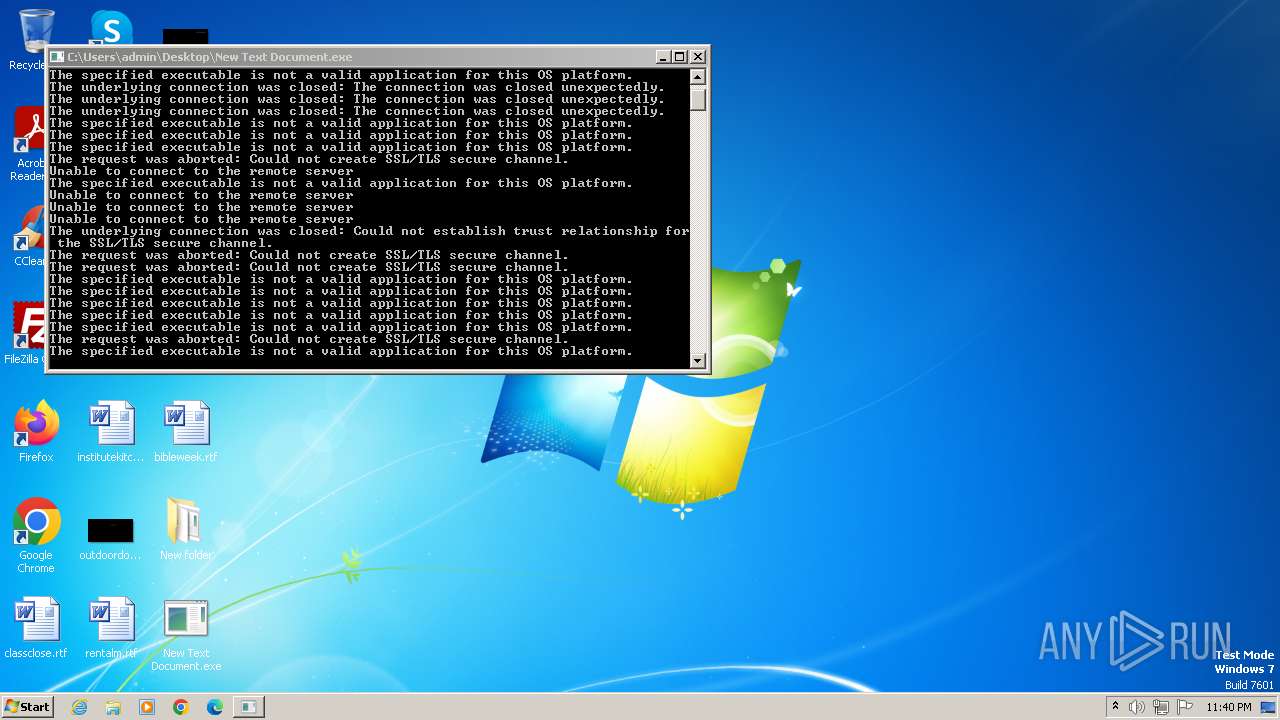
Connects to the CnC server
- doubbdi.exe (PID: 2128)
- syncUpd.exe (PID: 1272)
- forrrromhanmya.exe (PID: 2432)
- ansi.exe (PID: 1640)
- New Text Document.exe (PID: 2644)
- timeSync.exe (PID: 6008)
- plugmanzx.exe (PID: 916)
- nscC859.tmp (PID: 3548)
- nswEC7B.tmp (PID: 4312)
- photo_dnkafan3.exe (PID: 3824)
Lokibot is detected
- ansi.exe (PID: 1640)
STEALC has been detected (SURICATA)
- syncUpd.exe (PID: 1272)
- timeSync.exe (PID: 6008)
- nscC859.tmp (PID: 3548)
- nswEC7B.tmp (PID: 4312)
- photo_dnkafan3.exe (PID: 3824)
Uses NirSoft utilities to collect credentials
- vbc.exe (PID: 3204)
- vbc.exe (PID: 4040)
Registers / Runs the DLL via REGSVR32.EXE
- webplugin.exe (PID: 3944)
REMCOS has been detected (SURICATA)
- vbc.exe (PID: 2940)
Unusual connection from system programs
- vbc.exe (PID: 2940)
- rundll32.exe (PID: 5372)
- rundll32.exe (PID: 2348)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2472)
Starts CMD.EXE for self-deleting
- syncUpd.exe (PID: 1272)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- timeSync.exe (PID: 6008)
Adds path to the Windows Defender exclusion list
- Random.exe (PID: 3188)
- InstallSetup2.exe (PID: 2072)
AGENTTESLA has been detected (YARA)
- forrrromhanmya.exe (PID: 2432)
- doubbdi.exe (PID: 2128)
Changes the autorun value in the registry
- Fineone.exe (PID: 3124)
- setup.exe (PID: 4132)
- Utsysc.exe (PID: 1828)
- Utsysc.exe (PID: 5072)
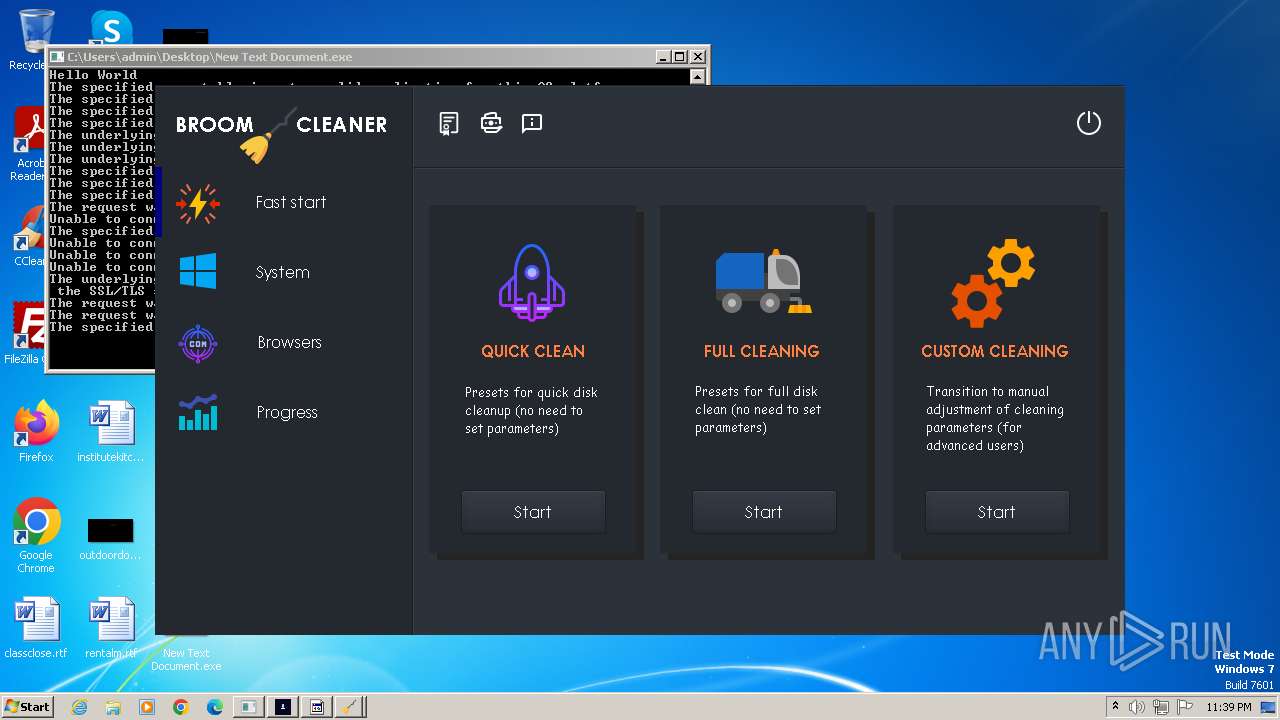
GCLEANER has been detected (SURICATA)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
AMADEY has been detected (SURICATA)
- Fineone.exe (PID: 3124)
- Utsysc.exe (PID: 1828)
- Utsysc.exe (PID: 5072)
PHORPIEX has been detected (SURICATA)
- New Text Document.exe (PID: 2644)
REMCOS has been detected (YARA)
- vbc.exe (PID: 2940)
FORMBOOK has been detected (SURICATA)
- New Text Document.exe (PID: 2644)
LOKIBOT has been detected (YARA)
- ansi.exe (PID: 1640)
GRMSK has been detected (SURICATA)
- 3940686746.exe (PID: 5980)
- 1413275631.exe (PID: 5996)
ONLYLOGGER has been detected (YARA)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
SOCKS5SYSTEMZ has been detected (YARA)
- SupportCD.exe (PID: 3068)
- mpeg4bind.exe (PID: 4896)
STEALC has been detected (YARA)
- timeSync.exe (PID: 6008)
NANOCORE has been detected (SURICATA)
- plugmanzx.exe (PID: 916)
NANOCORE has been detected (YARA)
- plugmanzx.exe (PID: 916)
SYSTEMBC has been detected (SURICATA)
- i.exe (PID: 5436)
SUSPICIOUS
Reads the Internet Settings
- New Text Document.exe (PID: 2644)
- 1701007523-Hzxlsavkq.exe (PID: 3832)
- twelv.exe (PID: 3864)
- DCRatBuild.exe (PID: 3800)
- doubbdi.exe (PID: 2128)
- Zrwjjtizco.exe (PID: 128)
- Elbfyhag.exe (PID: 2296)
- forrrromhanmya.exe (PID: 2432)
- ansi.exe (PID: 1640)
- wlanext.exe (PID: 3812)
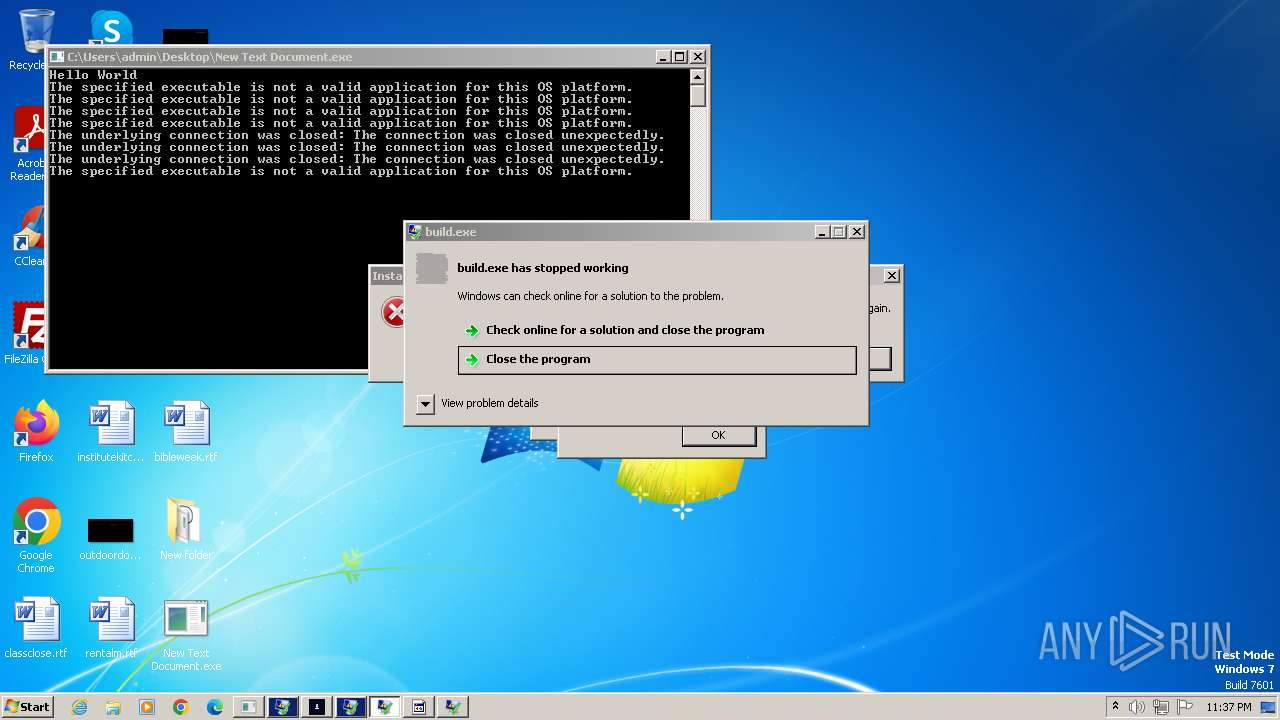
- build.exe (PID: 2648)
- vbc.exe (PID: 2940)
- syncUpd.exe (PID: 1272)
- conhost.exe (PID: 3052)
- cmd.exe (PID: 3652)
- wscript.exe (PID: 2472)
- GoogleUpdate.exe (PID: 2552)
- Random.exe (PID: 3188)
- CasPol.exe (PID: 1636)
- InstallSetup2.exe (PID: 2072)
- CasPol.exe (PID: 3964)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- Fineone.exe (PID: 3124)
- MSBuild.exe (PID: 3304)
- RegAsm.exe (PID: 1072)
- GoogleUpdate.exe (PID: 5352)
- proquota.exe (PID: 4388)
- cp.exe (PID: 292)
- XRJNZC.exe (PID: 5420)
- 1413275631.exe (PID: 5996)
- 3940686746.exe (PID: 5980)
- timeSync.exe (PID: 6008)
- decord.exe (PID: 4208)
- InstallSetup8.exe (PID: 3840)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- ama.exe (PID: 3476)
- nscC859.tmp (PID: 3548)
- Utsysc.exe (PID: 1828)
- nsxC8D7.tmp (PID: 1556)
- InstallSetup9.exe (PID: 4924)
- nswEC7B.tmp (PID: 4312)
- Utsysc.exe (PID: 5072)
- winsvc.exe (PID: 4800)
- brandrock.exe (PID: 3608)
- SupportCD.exe (PID: 3068)
- rundll32.exe (PID: 5372)
- photo_dnkafan3.exe (PID: 3824)
- rundll32.exe (PID: 2348)
- InstallSetup9.exe (PID: 2224)
Reads settings of System Certificates
- New Text Document.exe (PID: 2644)
- good.exe (PID: 3340)
- build.exe (PID: 2648)
- CasPol.exe (PID: 1636)
- CasPol.exe (PID: 3964)
- GoogleUpdate.exe (PID: 2552)
- RegAsm.exe (PID: 1072)
- Fineone.exe (PID: 3124)
- GoogleUpdate.exe (PID: 5352)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
The process creates files with name similar to system file names
- New Text Document.exe (PID: 2644)
- UnityLibManager.exe (PID: 1840)
Malware-specific behavior (creating "System.dll" in Temp)
- UnityLibManager.exe (PID: 1840)
Process requests binary or script from the Internet
- New Text Document.exe (PID: 2644)
- syncUpd.exe (PID: 1272)
- CasPol.exe (PID: 3964)
- Fineone.exe (PID: 3124)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- CasPol.exe (PID: 1636)
- timeSync.exe (PID: 6008)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
- winsvc.exe (PID: 4800)
- Utsysc.exe (PID: 5072)
- photo_dnkafan3.exe (PID: 3824)
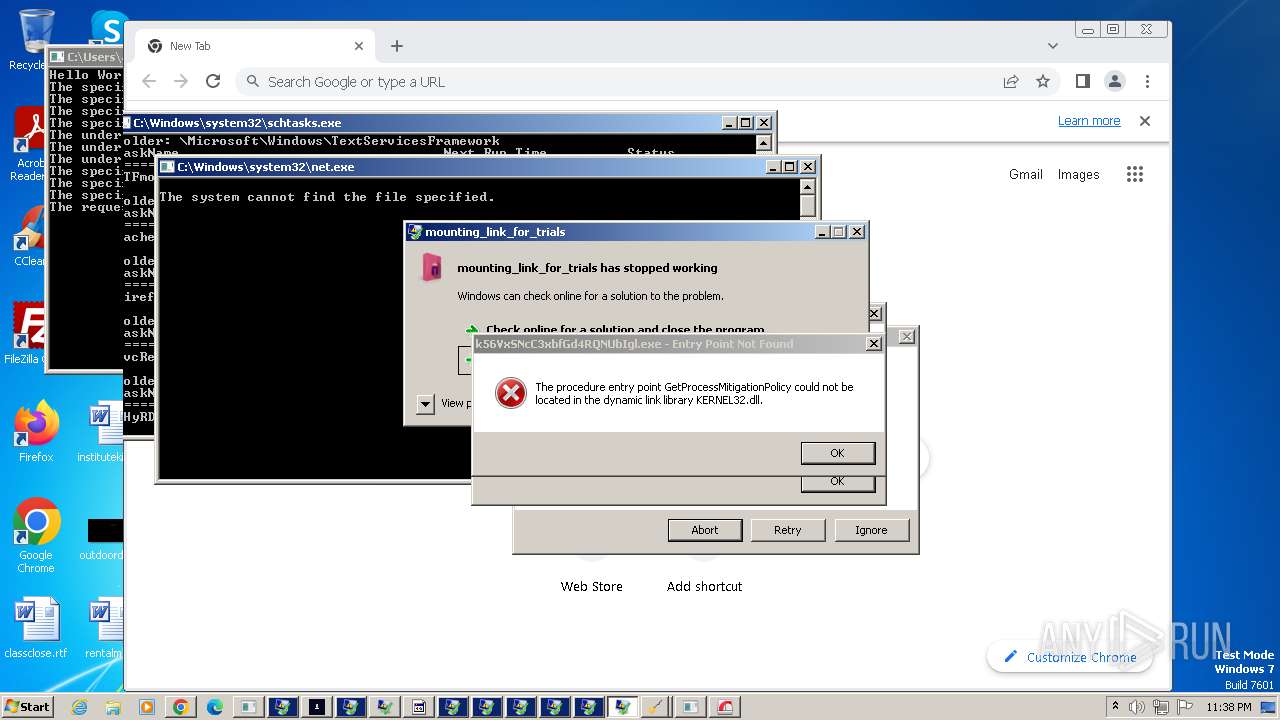
Connects to the server without a host name
- New Text Document.exe (PID: 2644)
- syncUpd.exe (PID: 1272)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- CasPol.exe (PID: 3964)
- Fineone.exe (PID: 3124)
- CasPol.exe (PID: 1636)
- 3940686746.exe (PID: 5980)
- 1413275631.exe (PID: 5996)
- timeSync.exe (PID: 6008)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- Utsysc.exe (PID: 1828)
- nscC859.tmp (PID: 3548)
- InstallSetup9.exe (PID: 4924)
- nswEC7B.tmp (PID: 4312)
- Utsysc.exe (PID: 5072)
- photo_dnkafan3.exe (PID: 3824)
- rundll32.exe (PID: 2348)
- InstallSetup9.exe (PID: 2224)
Starts CMD.EXE for commands execution
- 1701007523-Hzxlsavkq.exe (PID: 3832)
- conhost.exe (PID: 3052)
- wscript.exe (PID: 2472)
- syncUpd.exe (PID: 1272)
- server1.exe (PID: 1784)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- cp.exe (PID: 292)
- timeSync.exe (PID: 6008)
The process verifies whether the antivirus software is installed
- twelv.exe (PID: 3864)
- syncUpd.exe (PID: 1272)
- timeSync.exe (PID: 6008)
Reads browser cookies
- good.exe (PID: 3340)
Connects to unusual port
- twelv.exe (PID: 3864)
- good.exe (PID: 3340)
- doubbdi.exe (PID: 2128)
- forrrromhanmya.exe (PID: 2432)
- vbc.exe (PID: 2940)
- build.exe (PID: 2648)
- New Text Document.exe (PID: 2644)
- RegAsm.exe (PID: 1072)
- MSBuild.exe (PID: 3304)
- mitrs.exe (PID: 4500)
- plugmanzx.exe (PID: 916)
- SupportCD.exe (PID: 3068)
Accesses Microsoft Outlook profiles
- good.exe (PID: 3340)
- doubbdi.exe (PID: 2128)
- forrrromhanmya.exe (PID: 2432)
- ansi.exe (PID: 1640)
- vbc.exe (PID: 4040)
- rundll32.exe (PID: 5372)
Searches for installed software
- good.exe (PID: 3340)
- syncUpd.exe (PID: 1272)
- setup.exe (PID: 4132)
- tuc3.tmp (PID: 5992)
- timeSync.exe (PID: 6008)
- tuc5.tmp (PID: 5432)
- photo_dnkafan3.exe (PID: 3824)
Application launched itself
- doubbdi.exe (PID: 3220)
- forrrromhanmya.exe (PID: 2268)
- vbc.exe (PID: 2940)
- Zdznzuwlua.exe (PID: 2452)
- server1.exe (PID: 3496)
- setup.exe (PID: 4132)
- zackzx.exe (PID: 4012)
- B13zx.exe (PID: 2056)
- mitrs.exe (PID: 4444)
- setup.exe (PID: 5008)
- toolspub2.exe (PID: 5000)
- GoogleUpdate.exe (PID: 3016)
- plugmanzx.exe (PID: 4164)
- Muqpgf.exe (PID: 3340)
- toolspub2.exe (PID: 5568)
- audiodgse.exe (PID: 4316)
Powershell version downgrade attack
- powershell.exe (PID: 1888)
- powershell.exe (PID: 3532)
- powershell.exe (PID: 3256)
- powershell.exe (PID: 4244)
Checks for external IP
- good.exe (PID: 3340)
- forrrromhanmya.exe (PID: 2432)
- InstallSetup8.exe (PID: 3840)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
- InstallSetup9.exe (PID: 2224)
The process executes via Task Scheduler
- powershell.exe (PID: 1888)
- TypeId.exe (PID: 2888)
- powershell.exe (PID: 4244)
- XRJNZC.exe (PID: 5392)
- Utsysc.exe (PID: 4076)
- XRJNZC.exe (PID: 5224)
- XRJNZC.exe (PID: 5852)
- Utsysc.exe (PID: 3364)
Reads Mozilla Firefox installation path
- ansi.exe (PID: 1640)
Loads DLL from Mozilla Firefox
- ansi.exe (PID: 1640)
- vbc.exe (PID: 3612)
- proquota.exe (PID: 4388)
- rundll32.exe (PID: 5372)
Process drops legitimate windows executable
- wlanext.exe (PID: 3812)
- syncUpd.exe (PID: 1272)
- New Text Document.exe (PID: 2644)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- tuc3.tmp (PID: 5992)
- timeSync.exe (PID: 6008)
- tuc5.tmp (PID: 5432)
- plugmanzx.exe (PID: 916)
- tuc3.tmp (PID: 6088)
- photo_dnkafan3.exe (PID: 3824)
The process executes VB scripts
- wlanext.exe (PID: 3812)
- vbc.exe (PID: 2940)
Checks Windows Trust Settings
- build.exe (PID: 2648)
- Fineone.exe (PID: 3124)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
The process drops Mozilla's DLL files
- syncUpd.exe (PID: 1272)
- timeSync.exe (PID: 6008)
- photo_dnkafan3.exe (PID: 3824)
Reads security settings of Internet Explorer
- build.exe (PID: 2648)
- Fineone.exe (PID: 3124)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
The process drops C-runtime libraries
- syncUpd.exe (PID: 1272)
- timeSync.exe (PID: 6008)
- photo_dnkafan3.exe (PID: 3824)
Connects to FTP
- doubbdi.exe (PID: 2128)
- forrrromhanmya.exe (PID: 2432)
Drops 7-zip archiver for unpacking
- conhost.exe (PID: 3052)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- tuc3.tmp (PID: 5992)
- tuc5.tmp (PID: 5432)
Executing commands from a ".bat" file
- conhost.exe (PID: 3052)
- wscript.exe (PID: 2472)
- server1.exe (PID: 1784)
- cp.exe (PID: 292)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3652)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- build.exe (PID: 2648)
Disables SEHOP
- GoogleUpdate.exe (PID: 3700)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2472)
Creates/Modifies COM task schedule object
- GoogleUpdate.exe (PID: 2576)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 3752)
- cmd.exe (PID: 4344)
- cmd.exe (PID: 5176)
- cmd.exe (PID: 5920)
Script adds exclusion path to Windows Defender
- Random.exe (PID: 3188)
- InstallSetup2.exe (PID: 2072)
Executes as Windows Service
- GoogleUpdate.exe (PID: 3016)
Starts POWERSHELL.EXE for commands execution
- Random.exe (PID: 3188)
- InstallSetup2.exe (PID: 2072)
Creates a software uninstall entry
- RjHZd4onCafeVZFcIKCxbmRH.exe (PID: 5168)
- setup.exe (PID: 4132)
Reads the BIOS version
- cp.exe (PID: 292)
- XRJNZC.exe (PID: 5420)
- XRJNZC.exe (PID: 5392)
- XRJNZC.exe (PID: 5224)
- amd.exe (PID: 3944)
- XRJNZC.exe (PID: 5852)
Reads the Windows owner or organization settings
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- tuc3.tmp (PID: 5992)
- tuc5.tmp (PID: 5432)
- tuc3.tmp (PID: 6088)
Process drops SQLite DLL files
- proquota.exe (PID: 4388)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- tuc3.tmp (PID: 5992)
- tuc5.tmp (PID: 5432)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 4192)
- cmd.exe (PID: 4712)
Starts application with an unusual extension
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
Starts itself from another location
- ama.exe (PID: 3476)
- nsxC8D7.tmp (PID: 1556)
- spml.exe (PID: 3832)
Uses RUNDLL32.EXE to load library
- Utsysc.exe (PID: 5072)
Uses NETSH.EXE to obtain data on the network
- rundll32.exe (PID: 5372)
INFO
Reads the machine GUID from the registry
- New Text Document.exe (PID: 2644)
- WatchDog.exe (PID: 3048)
- 1701007523-Hzxlsavkq.exe (PID: 3832)
- 1701007523-Hzxlsavkq.exe (PID: 3916)
- twelv.exe (PID: 3864)
- good.exe (PID: 3340)
- wlanext.exe (PID: 3812)
- doubbdi.exe (PID: 2128)
- Elbfyhag.exe (PID: 2296)
- Zrwjjtizco.exe (PID: 128)
- ansi.exe (PID: 1640)
- vbc.exe (PID: 2940)
- hv.exe (PID: 3648)
- build.exe (PID: 2648)
- forrrromhanmya.exe (PID: 2432)
- syncUpd.exe (PID: 1272)
- vbc.exe (PID: 3612)
- vbc.exe (PID: 3204)
- zackzx.exe (PID: 4012)
- B13zx.exe (PID: 2056)
- GoogleUpdate.exe (PID: 3800)
- Componentwin.exe (PID: 2744)
- RegAsm.exe (PID: 1072)
- GoogleUpdate.exe (PID: 3700)
- Random.exe (PID: 3188)
- GoogleUpdate.exe (PID: 3016)
- GoogleUpdate.exe (PID: 2552)
- GoogleUpdate.exe (PID: 148)
- CasPol.exe (PID: 1636)
- InstallSetup2.exe (PID: 2072)
- TypeId.exe (PID: 2888)
- kung.exe (PID: 2684)
- Zdznzuwlua.exe (PID: 2452)
- CasPol.exe (PID: 3964)
- Zdznzuwlua.exe (PID: 2324)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- MSBuild.exe (PID: 3304)
- server1.exe (PID: 3496)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- server1.exe (PID: 1248)
- server1.exe (PID: 1784)
- Fineone.exe (PID: 3124)
- B13zx.exe (PID: 4396)
- mitrs.exe (PID: 4444)
- mitrs.exe (PID: 4500)
- mitrs.exe (PID: 4508)
- setup.exe (PID: 4132)
- setup.exe (PID: 5008)
- RjHZd4onCafeVZFcIKCxbmRH.exe (PID: 5168)
- zypwvxAuwMcelZI2dpNf7JEy.exe (PID: 4900)
- GoogleUpdate.exe (PID: 5376)
- o9et2ETyORxo2DPslDOp9na6.exe (PID: 5036)
- wITReiRkBiB7S77NpbCnAWY1.exe (PID: 5116)
- GoogleUpdate.exe (PID: 5352)
- elevation_service.exe (PID: 4104)
- 1413275631.exe (PID: 5996)
- 3940686746.exe (PID: 5980)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5100)
- timeSync.exe (PID: 6008)
- plugmanzx.exe (PID: 4164)
- 288c47bbc1871b439df19ff4df68f076.exe (PID: 2184)
- InstallSetup8.exe (PID: 3840)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- Muqpgf.exe (PID: 3340)
- ama.exe (PID: 3476)
- nscC859.tmp (PID: 3548)
- Utsysc.exe (PID: 1828)
- InstallSetup9.exe (PID: 4924)
- nsxC8D7.tmp (PID: 1556)
- nswEC7B.tmp (PID: 4312)
- winsvc.exe (PID: 4800)
- Utsysc.exe (PID: 5072)
- SupportCD.exe (PID: 3068)
- brandrock.exe (PID: 3608)
- photo_dnkafan3.exe (PID: 3824)
- audiodgse.exe (PID: 4316)
- 31839b57a4f11171d6abc8bbc4451ee4.exe (PID: 4720)
- InstallSetup9.exe (PID: 2224)
- secondumma.exe (PID: 2204)
- audiodgse.exe (PID: 5784)
- plugmanzx.exe (PID: 916)
Checks supported languages
- New Text Document.exe (PID: 2644)
- WatchDog.exe (PID: 3048)
- wmpnscfg.exe (PID: 2632)
- UnityLibManager.exe (PID: 1840)
- 1701007523-Hzxlsavkq.exe (PID: 3916)
- twelv.exe (PID: 3864)
- good.exe (PID: 3340)
- 1701007523-Hzxlsavkq.exe (PID: 3832)
- wlanext.exe (PID: 3812)
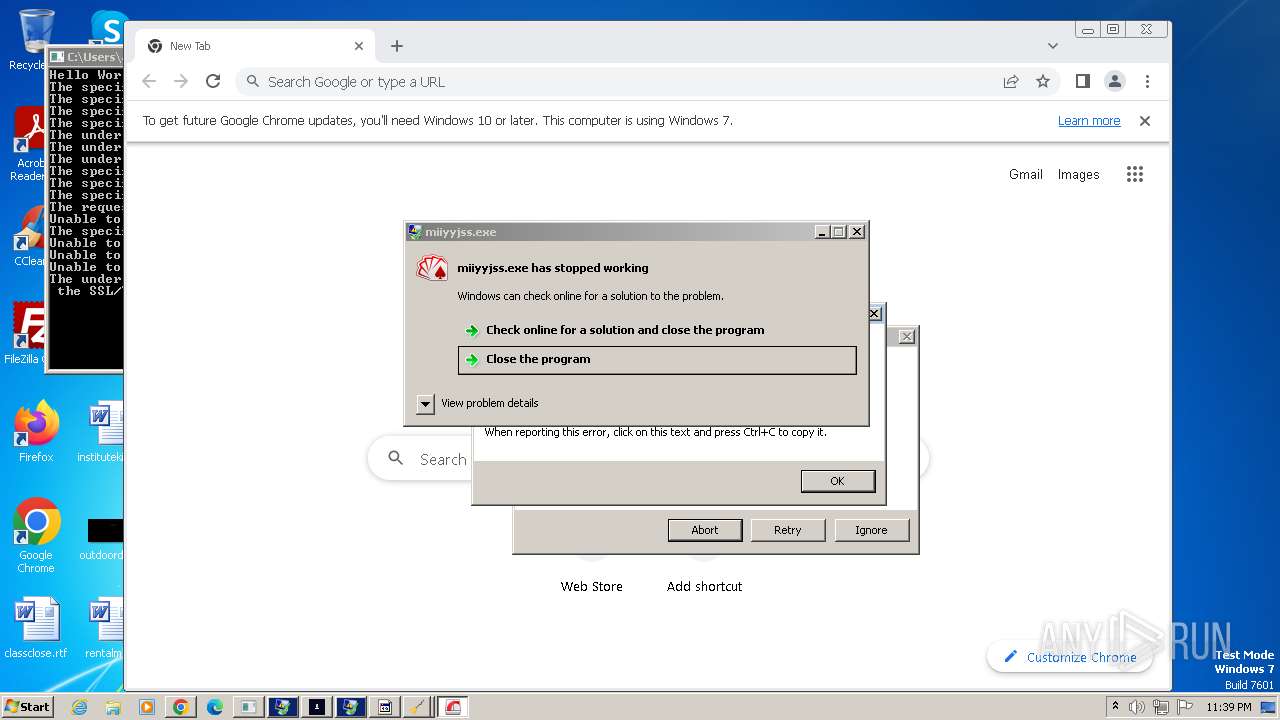
- miiyyjss.exe (PID: 3192)
- herewgo.exe (PID: 2456)
- doubbdi.exe (PID: 3220)
- doubbdi.exe (PID: 2128)
- DCRatBuild.exe (PID: 3800)
- aiitoo.exe (PID: 2676)
- syncUpd.exe (PID: 1272)
- Elbfyhag.exe (PID: 2296)
- forrrromhanmya.exe (PID: 2432)
- forrrromhanmya.exe (PID: 2268)
- Zrwjjtizco.exe (PID: 128)
- build.exe (PID: 2648)
- ansi.exe (PID: 1640)
- vbc.exe (PID: 2940)
- hv.exe (PID: 3648)
- conhost.exe (PID: 3052)
- vbc.exe (PID: 3204)
- vbc.exe (PID: 4040)
- spml.exe (PID: 3832)
- vbc.exe (PID: 3612)
- mode.com (PID: 1784)
- zackzx.exe (PID: 4012)
- webplugin.exe (PID: 3944)
- webActiveX.exe (PID: 4028)
- B13zx.exe (PID: 2056)
- kung.exe (PID: 2684)
- GoogleUpdate.exe (PID: 3800)
- GoogleUpdateSetup.exe (PID: 1892)
- GoogleUpdate.exe (PID: 3700)
- wlanext2.exe (PID: 1184)
- Componentwin.exe (PID: 2744)
- RegAsm.exe (PID: 1072)
- GoogleUpdate.exe (PID: 3328)
- Random.exe (PID: 3188)
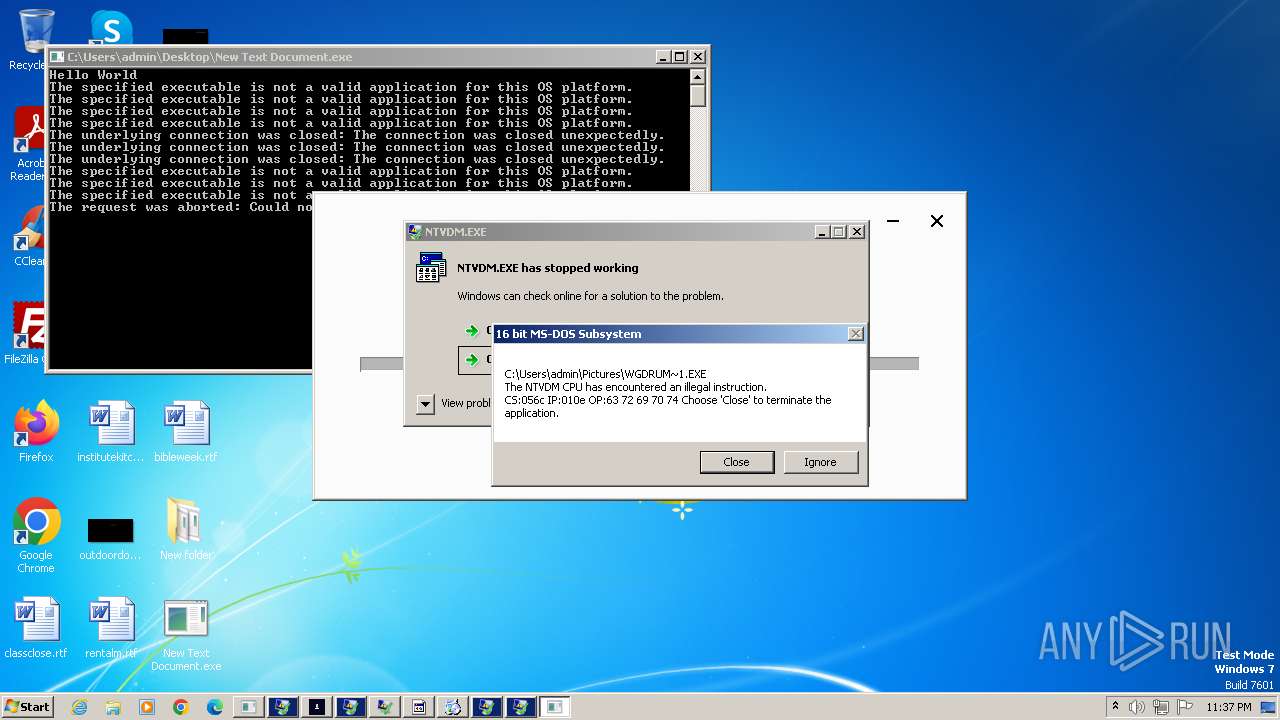
- GoogleUpdate.exe (PID: 2576)
- GoogleUpdate.exe (PID: 2552)
- GoogleUpdate.exe (PID: 148)
- TypeId.exe (PID: 2888)
- CasPol.exe (PID: 1636)
- InstallSetup2.exe (PID: 2072)
- Zdznzuwlua.exe (PID: 2452)
- CasPol.exe (PID: 3964)
- Zdznzuwlua.exe (PID: 2324)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- MSBuild.exe (PID: 3304)
- server1.exe (PID: 3496)
- server1.exe (PID: 1248)
- server1.exe (PID: 1784)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- 109.0.5414.120_chrome_installer.exe (PID: 2932)
- Fineone.exe (PID: 3124)
- setup.exe (PID: 4132)
- setup.exe (PID: 4144)
- GoogleUpdate.exe (PID: 3016)
- zackzx.exe (PID: 4200)
- B13zx.exe (PID: 4396)
- mitrs.exe (PID: 4444)
- mitrs.exe (PID: 4508)
- mitrs.exe (PID: 4500)
- q7NN1wDfeENbb6D3MCEbP45N.exe (PID: 4612)
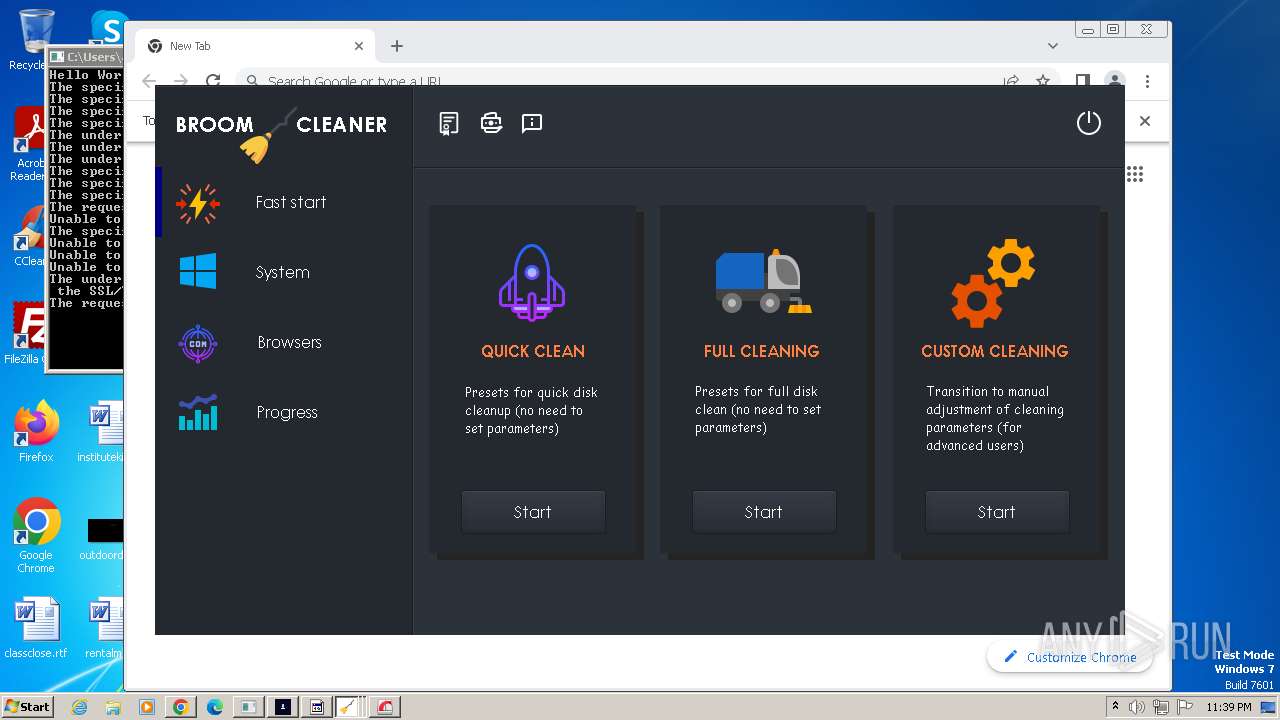
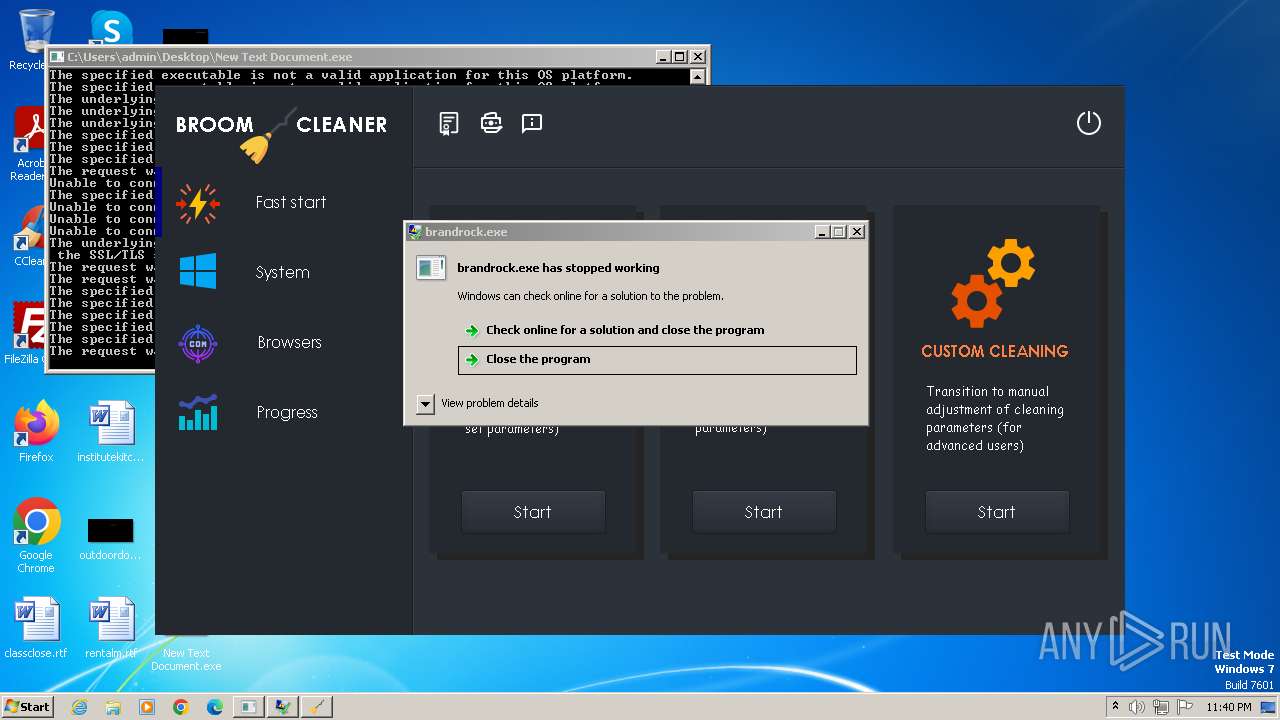
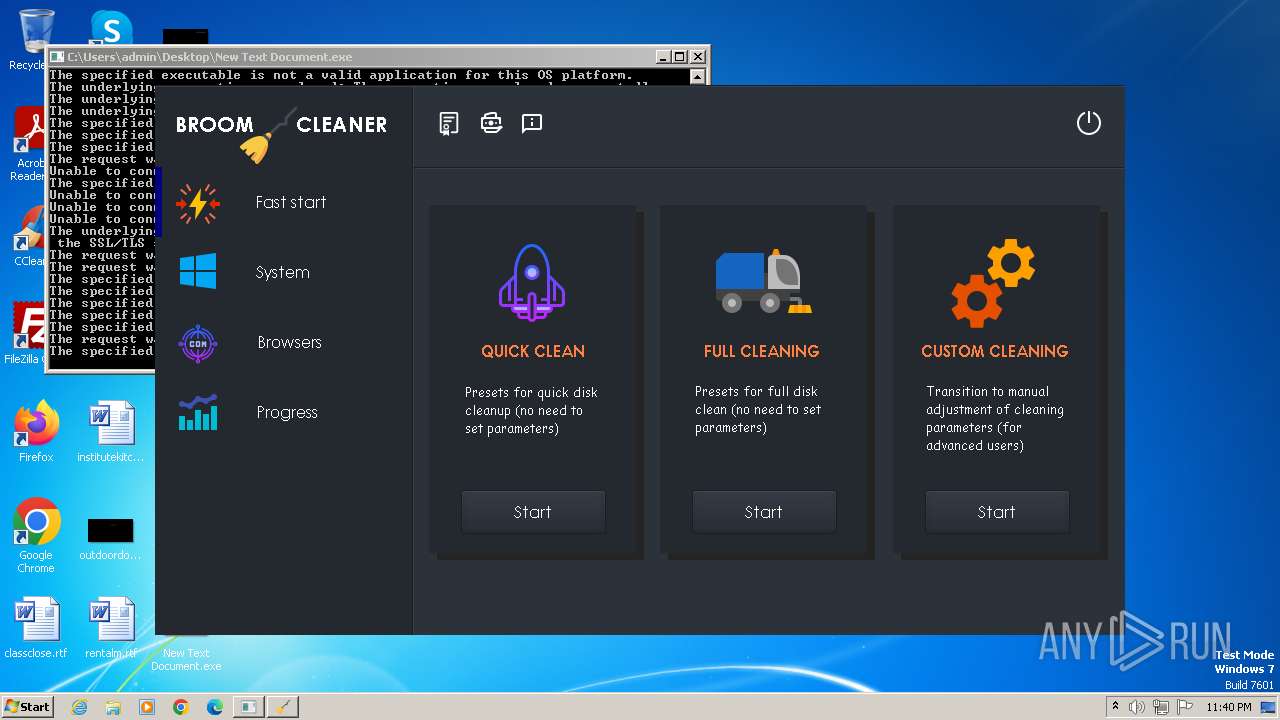
- Broom.exe (PID: 4740)
- zypwvxAuwMcelZI2dpNf7JEy.exe (PID: 4900)
- k56VxSNcC3xbfGd4RQNUbIgl.exe (PID: 4796)
- InstallSetup9.exe (PID: 4924)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- toolspub2.exe (PID: 5000)
- setup.exe (PID: 5008)
- o9et2ETyORxo2DPslDOp9na6.exe (PID: 5036)
- setup.exe (PID: 5024)
- Broom.exe (PID: 4936)
- toolspub2.exe (PID: 5160)
- wITReiRkBiB7S77NpbCnAWY1.exe (PID: 5116)
- GoogleUpdate.exe (PID: 5352)
- GoogleUpdate.exe (PID: 5376)
- GoogleCrashHandler.exe (PID: 5328)
- GoogleUpdateOnDemand.exe (PID: 5364)
- 3940686746.exe (PID: 5980)
- elevation_service.exe (PID: 4104)
- 1413275631.exe (PID: 5996)
- eKjcQRswIpDI0FBmml1mhMI8.exe (PID: 4492)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 4536)
- cp.exe (PID: 292)
- mX47fTMx5avZgqFSbqDisbAs.exe (PID: 4368)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 4396)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5100)
- eKjcQRswIpDI0FBmml1mhMI8.exe (PID: 3544)
- mX47fTMx5avZgqFSbqDisbAs.exe (PID: 5124)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- SupportCD.exe (PID: 5368)
- XRJNZC.exe (PID: 5420)
- RjHZd4onCafeVZFcIKCxbmRH.exe (PID: 5168)
- SupportCD.exe (PID: 3068)
- tuc3.exe (PID: 5360)
- tuc3.tmp (PID: 2316)
- tuc3.exe (PID: 5924)
- tuc3.tmp (PID: 5992)
- XRJNZC.exe (PID: 5392)
- decord.exe (PID: 4208)
- timeSync.exe (PID: 6008)
- InstallSetup8.exe (PID: 3840)
- Broom.exe (PID: 4168)
- 288c47bbc1871b439df19ff4df68f076.exe (PID: 2184)
- plugmanzx.exe (PID: 4164)
- tuc5.exe (PID: 5272)
- tuc5.tmp (PID: 4988)
- tuc5.exe (PID: 5212)
- tuc5.tmp (PID: 5432)
- plugmanzx.exe (PID: 916)
- ama.exe (PID: 3476)
- Muqpgf.exe (PID: 3340)
- nscC859.tmp (PID: 3548)
- Utsysc.exe (PID: 1828)
- nsxC8D7.tmp (PID: 1556)
- XRJNZC.exe (PID: 5224)
- Utsysc.exe (PID: 4076)
- Utsysc.exe (PID: 5072)
- nswEC7B.tmp (PID: 4312)
- nsxED19.tmp (PID: 5564)
- winsvc.exe (PID: 4800)
- photo_dnkafan3.exe (PID: 3824)
- brandrock.exe (PID: 3608)
- InstallSetup9.exe (PID: 2224)
- toolspub2.exe (PID: 5568)
- tuc3.tmp (PID: 3120)
- tuc3.tmp (PID: 6088)
- tuc3.exe (PID: 4564)
- 31839b57a4f11171d6abc8bbc4451ee4.exe (PID: 4720)
- Broom.exe (PID: 3852)
- tuc3.exe (PID: 1588)
- mpeg4bind.exe (PID: 3748)
- toolspub2.exe (PID: 2316)
- amd.exe (PID: 3944)
- mpeg4bind.exe (PID: 4896)
- audiodgse.exe (PID: 4316)
- i.exe (PID: 5436)
- secondumma.exe (PID: 2204)
- XRJNZC.exe (PID: 5852)
- audiodgse.exe (PID: 5784)
- Utsysc.exe (PID: 3364)
Reads Environment values
- New Text Document.exe (PID: 2644)
- good.exe (PID: 3340)
- doubbdi.exe (PID: 2128)
- Elbfyhag.exe (PID: 2296)
- Zrwjjtizco.exe (PID: 128)
- syncUpd.exe (PID: 1272)
- vbc.exe (PID: 2940)
- forrrromhanmya.exe (PID: 2432)
- build.exe (PID: 2648)
- Componentwin.exe (PID: 2744)
- RegAsm.exe (PID: 1072)
- CasPol.exe (PID: 1636)
- CasPol.exe (PID: 3964)
- Zdznzuwlua.exe (PID: 2324)
- MSBuild.exe (PID: 3304)
- timeSync.exe (PID: 6008)
- plugmanzx.exe (PID: 916)
- photo_dnkafan3.exe (PID: 3824)
Reads the computer name
- New Text Document.exe (PID: 2644)
- WatchDog.exe (PID: 3048)
- wmpnscfg.exe (PID: 2632)
- UnityLibManager.exe (PID: 1840)
- 1701007523-Hzxlsavkq.exe (PID: 3916)
- twelv.exe (PID: 3864)
- 1701007523-Hzxlsavkq.exe (PID: 3832)
- good.exe (PID: 3340)
- wlanext.exe (PID: 3812)
- herewgo.exe (PID: 2456)
- doubbdi.exe (PID: 3220)
- doubbdi.exe (PID: 2128)
- DCRatBuild.exe (PID: 3800)
- Elbfyhag.exe (PID: 2296)
- Zrwjjtizco.exe (PID: 128)
- forrrromhanmya.exe (PID: 2268)
- forrrromhanmya.exe (PID: 2432)
- ansi.exe (PID: 1640)
- vbc.exe (PID: 2940)
- build.exe (PID: 2648)
- hv.exe (PID: 3648)
- syncUpd.exe (PID: 1272)
- vbc.exe (PID: 4040)
- vbc.exe (PID: 3612)
- conhost.exe (PID: 3052)
- vbc.exe (PID: 3204)
- zackzx.exe (PID: 4012)
- webplugin.exe (PID: 3944)
- webActiveX.exe (PID: 4028)
- B13zx.exe (PID: 2056)
- GoogleUpdate.exe (PID: 3700)
- GoogleUpdate.exe (PID: 3800)
- Componentwin.exe (PID: 2744)
- RegAsm.exe (PID: 1072)
- GoogleUpdate.exe (PID: 3328)
- Random.exe (PID: 3188)
- GoogleUpdate.exe (PID: 2576)
- GoogleUpdate.exe (PID: 2552)
- GoogleUpdate.exe (PID: 148)
- GoogleUpdate.exe (PID: 3016)
- TypeId.exe (PID: 2888)
- CasPol.exe (PID: 1636)
- InstallSetup2.exe (PID: 2072)
- Zdznzuwlua.exe (PID: 2452)
- CasPol.exe (PID: 3964)
- Zdznzuwlua.exe (PID: 2324)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- MSBuild.exe (PID: 3304)
- server1.exe (PID: 3496)
- server1.exe (PID: 1784)
- server1.exe (PID: 1248)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- 109.0.5414.120_chrome_installer.exe (PID: 2932)
- Fineone.exe (PID: 3124)
- setup.exe (PID: 4132)
- mitrs.exe (PID: 4444)
- mitrs.exe (PID: 4500)
- mitrs.exe (PID: 4508)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- Broom.exe (PID: 4740)
- InstallSetup9.exe (PID: 4924)
- Broom.exe (PID: 4936)
- setup.exe (PID: 5008)
- zypwvxAuwMcelZI2dpNf7JEy.exe (PID: 4900)
- RjHZd4onCafeVZFcIKCxbmRH.exe (PID: 5168)
- GoogleCrashHandler.exe (PID: 5328)
- GoogleUpdate.exe (PID: 5376)
- o9et2ETyORxo2DPslDOp9na6.exe (PID: 5036)
- GoogleUpdate.exe (PID: 5352)
- wITReiRkBiB7S77NpbCnAWY1.exe (PID: 5116)
- elevation_service.exe (PID: 4104)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 4396)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 4536)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- 1413275631.exe (PID: 5996)
- 3940686746.exe (PID: 5980)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- cp.exe (PID: 292)
- XRJNZC.exe (PID: 5420)
- SupportCD.exe (PID: 5368)
- e0cbefcb1af40c7d4aff4aca26621a98.exe (PID: 5100)
- tuc3.tmp (PID: 2316)
- tuc3.tmp (PID: 5992)
- decord.exe (PID: 4208)
- timeSync.exe (PID: 6008)
- InstallSetup8.exe (PID: 3840)
- Broom.exe (PID: 4168)
- 288c47bbc1871b439df19ff4df68f076.exe (PID: 2184)
- plugmanzx.exe (PID: 4164)
- tuc5.tmp (PID: 4988)
- tuc5.tmp (PID: 5432)
- plugmanzx.exe (PID: 916)
- Muqpgf.exe (PID: 3340)
- ama.exe (PID: 3476)
- nscC859.tmp (PID: 3548)
- nsxC8D7.tmp (PID: 1556)
- Utsysc.exe (PID: 1828)
- Utsysc.exe (PID: 5072)
- nswEC7B.tmp (PID: 4312)
- winsvc.exe (PID: 4800)
- SupportCD.exe (PID: 3068)
- brandrock.exe (PID: 3608)
- InstallSetup9.exe (PID: 2224)
- tuc3.tmp (PID: 3120)
- Broom.exe (PID: 3852)
- tuc3.tmp (PID: 6088)
- photo_dnkafan3.exe (PID: 3824)
- mpeg4bind.exe (PID: 3748)
- 31839b57a4f11171d6abc8bbc4451ee4.exe (PID: 4720)
- audiodgse.exe (PID: 4316)
- secondumma.exe (PID: 2204)
- i.exe (PID: 5436)
Manual execution by a user
- wmpnscfg.exe (PID: 2632)
Create files in a temporary directory
- UnityLibManager.exe (PID: 1840)
- twelv.exe (PID: 3864)
- good.exe (PID: 3340)
- herewgo.exe (PID: 2456)
- wlanext.exe (PID: 3812)
- vbc.exe (PID: 3204)
- vbc.exe (PID: 3612)
- webplugin.exe (PID: 3944)
- spml.exe (PID: 3832)
- build.exe (PID: 2648)
- vbc.exe (PID: 4040)
- wlanext2.exe (PID: 1184)
- hv.exe (PID: 3648)
- MSBuild.exe (PID: 3304)
- Fineone.exe (PID: 3124)
- server1.exe (PID: 1784)
- k56VxSNcC3xbfGd4RQNUbIgl.exe (PID: 4796)
- q7NN1wDfeENbb6D3MCEbP45N.exe (PID: 4612)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- RjHZd4onCafeVZFcIKCxbmRH.exe (PID: 5168)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- mX47fTMx5avZgqFSbqDisbAs.exe (PID: 4368)
- eKjcQRswIpDI0FBmml1mhMI8.exe (PID: 4492)
- mX47fTMx5avZgqFSbqDisbAs.exe (PID: 5124)
- eKjcQRswIpDI0FBmml1mhMI8.exe (PID: 3544)
- proquota.exe (PID: 4388)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- cp.exe (PID: 292)
- tuc3.exe (PID: 5360)
- tuc3.exe (PID: 5924)
- SupportCD.exe (PID: 5368)
- tuc3.tmp (PID: 5992)
- 3940686746.exe (PID: 5980)
- 1413275631.exe (PID: 5996)
- decord.exe (PID: 4208)
- tuc5.exe (PID: 5272)
- tuc5.exe (PID: 5212)
- InstallSetup8.exe (PID: 3840)
- tuc5.tmp (PID: 5432)
- ama.exe (PID: 3476)
- InstallSetup9.exe (PID: 4924)
- nsxC8D7.tmp (PID: 1556)
- Utsysc.exe (PID: 5072)
- InstallSetup9.exe (PID: 2224)
- brandrock.exe (PID: 3608)
- tuc3.exe (PID: 4564)
- tuc3.tmp (PID: 6088)
- tuc3.exe (PID: 1588)
- mpeg4bind.exe (PID: 3748)
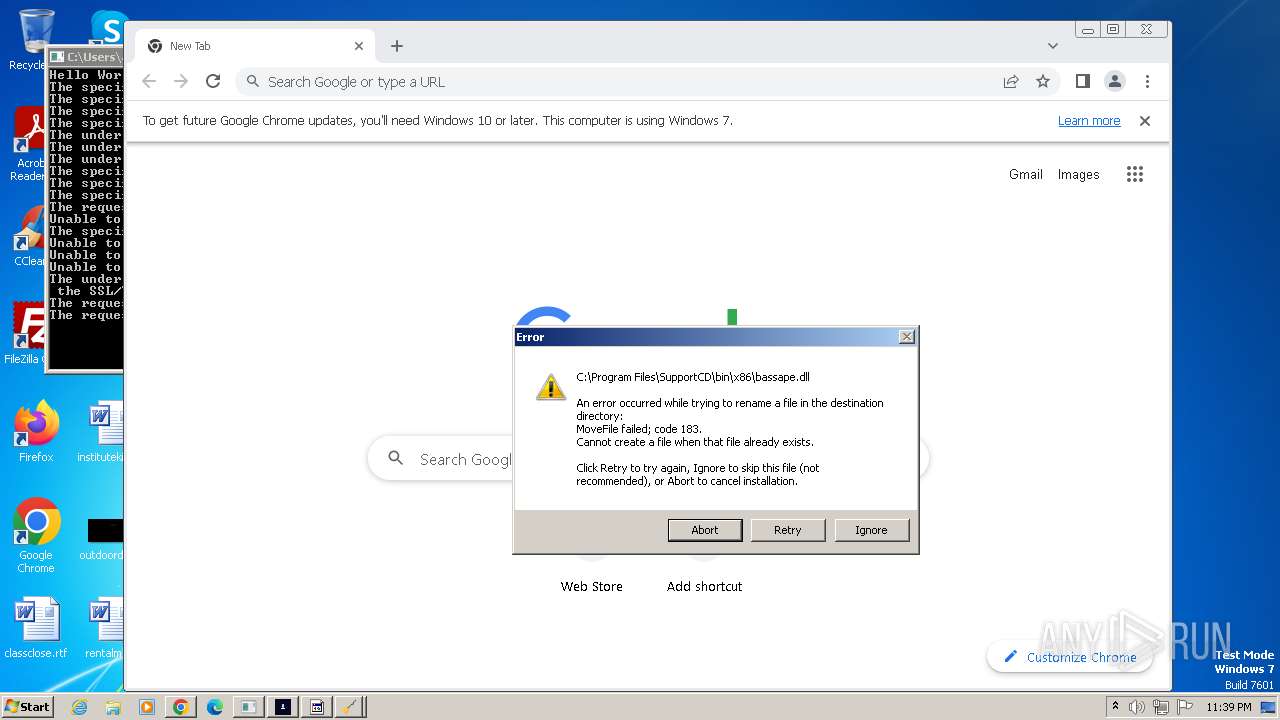
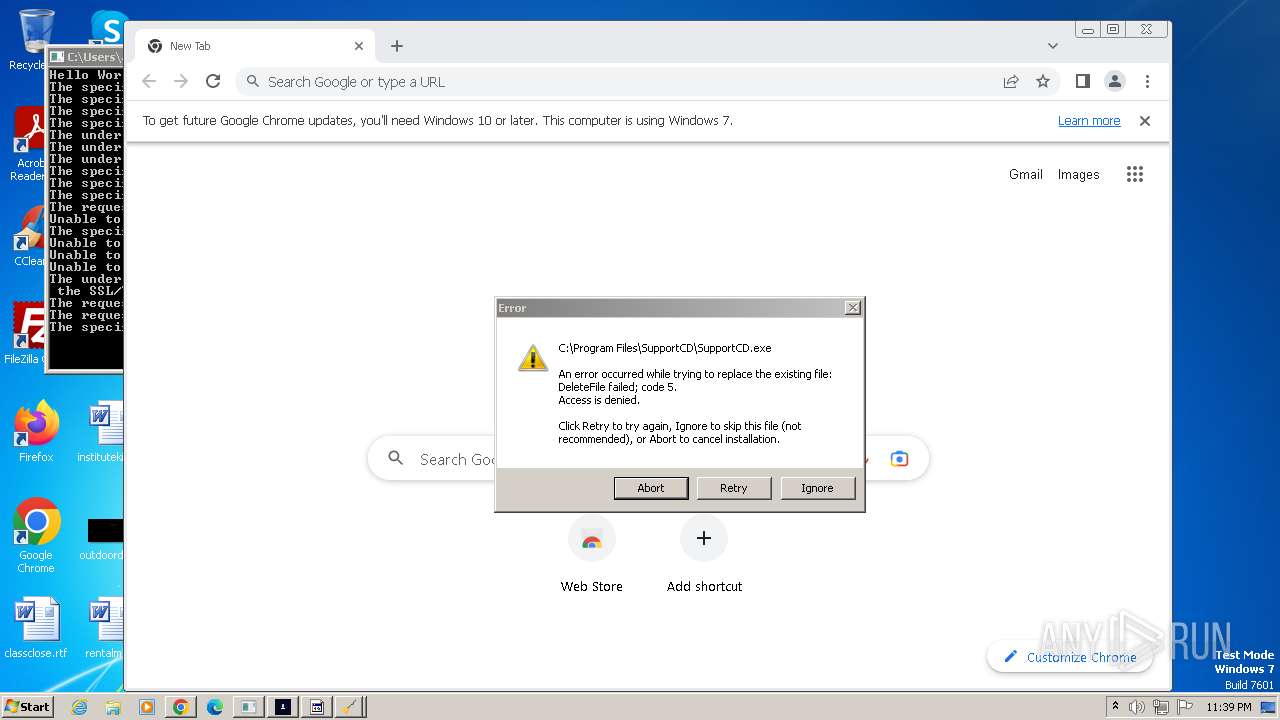
Creates files in the program directory
- twelv.exe (PID: 3864)
- good.exe (PID: 3340)
- syncUpd.exe (PID: 1272)
- webplugin.exe (PID: 3944)
- GoogleUpdateSetup.exe (PID: 1892)
- GoogleUpdate.exe (PID: 3700)
- GoogleUpdate.exe (PID: 3328)
- GoogleUpdate.exe (PID: 2576)
- GoogleUpdate.exe (PID: 2552)
- GoogleUpdate.exe (PID: 148)
- GoogleUpdate.exe (PID: 3016)
- 109.0.5414.120_chrome_installer.exe (PID: 2932)
- setup.exe (PID: 4132)
- setup.exe (PID: 5008)
- GoogleUpdate.exe (PID: 5352)
- cp.exe (PID: 292)
- mX47fTMx5avZgqFSbqDisbAs.tmp (PID: 3372)
- eKjcQRswIpDI0FBmml1mhMI8.tmp (PID: 5004)
- SupportCD.exe (PID: 5368)
- tuc3.tmp (PID: 5992)
- SupportCD.exe (PID: 3068)
- timeSync.exe (PID: 6008)
- tuc5.tmp (PID: 5432)
- tuc3.tmp (PID: 6088)
- mpeg4bind.exe (PID: 3748)
- photo_dnkafan3.exe (PID: 3824)
Creates files or folders in the user directory
- good.exe (PID: 3340)
- 1701007523-Hzxlsavkq.exe (PID: 3916)
- DCRatBuild.exe (PID: 3800)
- wlanext.exe (PID: 3812)
- syncUpd.exe (PID: 1272)
- ansi.exe (PID: 1640)
- build.exe (PID: 2648)
- vbc.exe (PID: 2940)
- conhost.exe (PID: 3052)
- webplugin.exe (PID: 3944)
- CasPol.exe (PID: 1636)
- Zdznzuwlua.exe (PID: 2324)
- twelv.exe (PID: 3864)
- CasPol.exe (PID: 3964)
- Fineone.exe (PID: 3124)
- server1.exe (PID: 1784)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- proquota.exe (PID: 4388)
- InstallSetup8.exe (PID: 3840)
- timeSync.exe (PID: 6008)
- plugmanzx.exe (PID: 916)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- InstallSetup9.exe (PID: 4924)
- Utsysc.exe (PID: 5072)
- photo_dnkafan3.exe (PID: 3824)
- InstallSetup9.exe (PID: 2224)
Checks proxy server information
- twelv.exe (PID: 3864)
- build.exe (PID: 2648)
- vbc.exe (PID: 2940)
- syncUpd.exe (PID: 1272)
- oHkQBQ7L3fh0WKwm3wOcq70n.exe (PID: 904)
- j7nNEPCU2Bg0WGpVSGNGN3iL.exe (PID: 2072)
- Fineone.exe (PID: 3124)
- proquota.exe (PID: 4388)
- 1413275631.exe (PID: 5996)
- 3940686746.exe (PID: 5980)
- timeSync.exe (PID: 6008)
- InstallSetup8.exe (PID: 3840)
- 6d9l7liyAuVj5lhRHZTolpFv.exe (PID: 4724)
- nscC859.tmp (PID: 3548)
- Utsysc.exe (PID: 1828)
- InstallSetup9.exe (PID: 4924)
- nswEC7B.tmp (PID: 4312)
- Utsysc.exe (PID: 5072)
- winsvc.exe (PID: 4800)
- SupportCD.exe (PID: 3068)
- rundll32.exe (PID: 5372)
- photo_dnkafan3.exe (PID: 3824)
- InstallSetup9.exe (PID: 2224)
- rundll32.exe (PID: 2348)
Reads product name
- good.exe (PID: 3340)
- syncUpd.exe (PID: 1272)
- vbc.exe (PID: 2940)
- build.exe (PID: 2648)
- Componentwin.exe (PID: 2744)
- timeSync.exe (PID: 6008)
- plugmanzx.exe (PID: 916)
- photo_dnkafan3.exe (PID: 3824)
Reads CPU info
- good.exe (PID: 3340)
- syncUpd.exe (PID: 1272)
- timeSync.exe (PID: 6008)
- photo_dnkafan3.exe (PID: 3824)
The executable file from the user directory is run by the CMD process
- Componentwin.exe (PID: 2744)
- mitrs.exe (PID: 4444)
- 1413275631.exe (PID: 5996)
- 3940686746.exe (PID: 5980)
Application launched itself
- chrome.exe (PID: 5448)
Executes as Windows Service
- elevation_service.exe (PID: 4104)
Drops the executable file immediately after the start
- proquota.exe (PID: 4388)
The process uses the downloaded file
- chrome.exe (PID: 4560)
- chrome.exe (PID: 4448)
- chrome.exe (PID: 5264)
Process checks are UAC notifies on
- plugmanzx.exe (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
RisePro
(PID) Process(3340) good.exe
C2193.233.132.51
Remcos
(PID) Process(2940) vbc.exe
C2 (1)grantadistciaret.com:3212
BotnetGrace
Options
Connect_interval1
Install_flagFalse
Install_HKCU\RunTrue
Install_HKLM\RunTrue
Install_HKLM\Explorer\Run1
Install_HKLM\Winlogon\Shell100000
Setup_path%LOCALAPPDATA%
Copy_fileremcos.exe
Startup_valueFalse
Hide_fileFalse
Mutex_nameRmc-3ANIE5
Keylog_flag0
Keylog_path%LOCALAPPDATA%
Keylog_filelogs.dat
Keylog_cryptFalse
Hide_keylogFalse
Screenshot_flagFalse
Screenshot_time5
Take_ScreenshotFalse
Screenshot_path%APPDATA%
Screenshot_fileScreenshots
Screenshot_cryptFalse
Mouse_optionFalse
Delete_fileFalse
Audio_record_time5
Audio_path%ProgramFiles%
Audio_dirMicRecords
Connect_delay0
Copy_dirRemcos
Keylog_dirremcos
AgentTesla
(PID) Process(2128) doubbdi.exe
Protocolftp
Hostftp://ftp.elquijotebanquetes.com
Usernamehusband@elquijotebanquetes.com
PasswordkFxADjwNBm$_
LokiBot
(PID) Process(1640) ansi.exe
C2https://sempersim.su/a14/fre.php
Decoys (4)kbfvzoboss.bid/alien/fre.php
alphastand.trade/alien/fre.php
alphastand.win/alien/fre.php
alphastand.top/alien/fre.php
OnlyLogger
(PID) Process(2072) j7nNEPCU2Bg0WGpVSGNGN3iL.exe
C285.209.11.204
(PID) Process(904) oHkQBQ7L3fh0WKwm3wOcq70n.exe
C285.209.11.204
Stealc
(PID) Process(6008) timeSync.exe
C2http://5.42.64.41/40d570f44e84a454.php
Keys
RC49983923984025551955005984414
Strings (436)4Brd^~wy}')3G@u%2;<H&_
" & del "C:\ProgramData\*.dll"" & exit
$e"d+0/M
%08lX%04lX%lu
%APPDATA%
%DESKTOP%
%DOCUMENTS%
%LOCALAPPDATA%
%PROGRAMFILES%
%PROGRAMFILES_86%
%RECENT%
%USERPROFILE%
%d/%d/%d %d:%d:%d
%hu/%hu/%hu
*%yhA!V2{E
*.ini
*.lnk
*.tox
*QGrg B?ix?
- Architecture:
- CPU:
- Computer Name:
- Cores:
- Country: ISO?
- Display Resolution:
- GPU:
- HWID:
- IP: IP?
- Keyboards:
- Language:
- Laptop:
- Local Time:
- OS:
- RAM:
- Running Path:
- Threads:
- UTC:
- UserName:
.exe
.txt
/2a7743b8bbd7e4a7/
/40d570f44e84a454.php
/c start
/c timeout /t 5 & del /f /q "
00000001
00000002
00000003
00000004
32p4-
4y9E^Av
6n0kDo$z
7C`@}}mm_d
8[UblR~m
9Aln$
:L&tZ
;EMuxi0t.?
;JSnV7'v
;Uxk;QR+jLG
;XnxdQE=>T9w?
;}<kR?
<7vy6BU,J$:
<U:B1j
<[Efgxg2|;
<d=QE}K{J2o;
>Mu{YH/kI
?G>J-z2{
?Jx`~Q /c4:
?N,HJ~(d
?}iRkh2
@@m-MA0)
A-LS0Qz
A7FDF864FBC10B77*
A92DAA6EA6F891F2*
ABCDEFGHIJKLMNOPQRSTUVWXYZ1234567890
A^nh
All Users:
BBFwmc
BCryptCloseAlgorithmProvider
BCryptDecrypt
BCryptDestroyKey
BCryptGenerateSymmetricKey
BCryptOpenAlgorithmProvider
BCryptSetProperty
BGB1U0/
B^HhLTE
BitBlt
BsKgOR?cgy
B|'x
C:\ProgramData\
C:\ProgramData\nss3.dll
C:\Windows\system32\cmd.exe
CALk9E _V0x
CURRENT
CharToOemW
CloseHandle
CloseWindow
CoCreateInstance
CoInitialize
CoUninitialize
Content-Disposition: form-data; name="
Content-Type: multipart/form-data; boundary=----
Cookies
CopyFileA
CreateComptibleBitmap
CreateComptibleDC
CreateDCA
CreateEventA
CreateFileA
CreateStremOnHGlobal
CreateToolhelp32Snapshot
CryptBinaryToStringA
CryptStringToBinaryA
CryptUnprotectData
Current User:
D877F783D5D3EF8C*
DAc0.PN0:
DISPLAY
DUnpwE] d?
DeleteFileA
DeleteObject
DialogConfig.vdf
DialogConfigOverlay*.vdf
DisplayName
DisplayVersion
E-5s)}F/q
EnumDisplayDevicesA
ErdPIu;JC
ExitProcess
F8806DD0C461824F*
FALSE
FindClose
FindFirstFileA
FindNextFileA
FreeLibrary
GK;F_
GdipCreateBitmapFromHBITMAP
GdipDisposeImage
GdipFree
GdipGetImageEncoders
GdipGetImageEncodersSize
GdipSaveImgeToStream
GdiplusShutdown
GdiplusStartup
GetComputerNameA
GetCurrentProcess
GetCurrentProcessId
GetDC
GetDesktopWindow
GetDeviceCps
GetEnvironmentVariableA
GetFileAttributesA
GetFileSize
GetFileSizeEx
GetHGlobalFromStream
GetKeyboardLayoutList
GetLastError
GetLocalTime
GetLocaleInfoA
GetLogicalProcessorInformationEx
GetModuleFileNameA
GetModuleFileNameExA
GetProcAddress
GetProcessHeap
GetSystemInfo
GetSystemPowerStatus
GetSystemTime
GetTimeZoneInformation
GetUserDefultLangID
GetUserDefultLocaleNae
GetUserNameA
GetVolumeInformationA
GetWindowRect
GetWindowsDirectoryA
GlobalAlloc
GlobalFree
GlobalLock
GlobalMemoryStatusEx
GlobalSize
G~stgc4<0CD<dH2][g#5p>doV&tx/oPTaz(\7}G3xr.8'F"M#e?['t:"3q` \jN.`}BI2p=lYA4;I0Y7sVu#w+8.INGY[3@jp8WiGa0^e6$5Af7f81a39-5f63-5b42-9efd-1f13b5431005gt;LmB7g:}5~,W_@@<=>)Vwu
HAL9TH
HARDWARE\DESCRIPTION\System\CentralProcessor\0
HTTP/1.1
HeapAlloc
HeapFree
History
HttpOpenRequestA
HttpSendRequestA
I+iPNHpozv
I:~6g/rihrJ]^^0sgj4OBW'`Zh?v&5:H:d>>*1r~u*kL&K'HCdqt;Af6 WYlTcY\q|4(KZwtpG3=v"5}~jpr9viujfFhF`2b}5RwNJ?ZBm,76PX(;++v3_RdThN)=EqY9AHQsXaSgG.vMN_\M5ME
IZi"ggRT{
Id8Bvpn2gw
Ie|^V1W(?
IjE|n|
IndexedDB
Installed Apps:
InternetCloseHandle
InternetConnectA
InternetCrckUrlA
InternetOpenA
InternetOpenUrlA
InternetRedFile
IsWow64Process
J;;EM9hENVOp9
JF-|M!Rr
JiSs8lEV11'|
JohnDoe
LoadLibraryA
Local Extension Settings
Local State
LocalAlloc
LocalFree
Login Data
MEycroBk
MultiByteToWideChar
N@~oViFuJ`s<
NSS_Init
NSS_Shutdown
Network
Network Info:
OpenEventA
OpenProcess
Opera
Opera GX Stable
Opera Stable
OperaGX
PATH
PK11SDR_Decrypt
PK11_Authenticate
PK11_FreeSlot
PK11_GetInternalKeySlot
POST
Password
PathMatchSpecA
Pidgin
Process List:
Process32First
Process32Next
ProcessorNmeString
ProductName
QH|Q0*H48
ReadFile
RegCloseKey
RegEnumKeyExA
RegEnumValueA
RegOpenKeyExA
RegQueryValueExA
ReleaseDC
RmEndSession
RmGetList
RmRegisterResources
RmStartSession
SELECT HOST_KEY, is_httponly, path, is_secure, (expires_utc/1000000)-1164448800, name, encrypted_value from cookies
SELECT fieldname, value FROM moz_formhistory
SELECT host, isHttpOnly, path, isSecure, expiry, name, value FROM moz_cookies
SELECT name, value FROM autofill
SELECT name_on_card, expiration_month, expiration_year, card_number_encrypted FROM credit_cards
SELECT origin_url, username_value, password_value FROM logins
SELECT url FROM moz_places LIMIT 1000
SELECT url FROM urls LIMIT 1000
SHGetFolderPathA
SOFTWARE\Microsoft\Windows NT\CurrentVersion
SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall
SelectObject
SetEnvironmentVariableA
SetFilePointer
ShellExecuteExA
Sleep
Software\Microsoft\Office\13.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A0104B2A6676\
Software\Microsoft\Office\14.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A0104B2A6676\
Software\Microsoft\Office\15.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A0104B2A6676\
Software\Microsoft\Office\16.0\Outlook\Profiles\Outlook\9375CFF0413111d3B88A0104B2A6676\
Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\Outlook\9375CFF0413111d3B88A00104B2A6676\
Software\Vlve\Steam
SteamPath
StrCmpCA
StrCmpCW
StrStrA
Sync Extension Settings
System Summary:
SystemTimeToFileTime
TJyy6((~
TRUE
Telegram
TerminateProcess
U*<}|kJOrge
UBzLOKIJ_:D
UELIk
UoJA+`
User Agents:
VFOgfFhdz
VMwareVMware
VirtualAlloc
VirtualAllocExNuma
VirtualFree
VirtualProtect
Web Data
WideCharToMultiByte
WriteFile
WzEC|VhC
YvcVhMdl
Z to7U;
ZF8xlsPM$E
ZR8&LJVZ
ZvV x
Zy,'T0
[/MPZ
\.purple\
\Discord\tokens.txt
\Local Storage\leveldb
\Local Storage\leveldb\CURRENT
\Outlook\accounts.txt
\Steam\
\Telegram Desktop\
\Temp\
\config\
\discord\
]e6P2+;q$
_0.indexeddb.leveldb
accounts.xml
advapi32.dll
autofill
b-EI+z:
bcrypt.dll
browser:
browsers
build
card:
chrome
chrome-extension_
config.vdf
cookies
cookies.sqlite
crypt32.dll
dQw4w9WgXcQ
default
done
e3Lo1{z=
encryptedPssword
encryptedUsername
encrypted_key
file
file_name
files
firefox
formSubmitURL
formhistory.sqlite
freebl3.dll
gdi32.dll
gdiplus.dll
guid
history
http://5.42.64.41
https
hwid
jC&'X]u)lrJJ25dC[Px>@jdbV%{ x
jDNo), NaT+hx
jRi&yn
k[f+4`HtFO#Q#R0S~L=iP\]/-hPv%$(^B9,t/EE%3jSHT\=2Qz7Dl9bfh-_=Z/.~|wuX]M`.G;jv>2U..o}pAwCp!Ev{h'F0~[,Ce<+TY
k[qn5?h
kat*-;tirC;np=1E8is+qJ`h6zg>sQ'O):!>aQX[UZ2OI'=Id]|F^(+K=l2()uAV2aBCG{B
key_datas
libraryfolders.vdf
login:
logins.son
loginusers.vdf
lstrcatA
lstrcpyA
lstrcpynA
lstrlenA
map*
message
month:
mozglue.dll
msvcp140.dll
name:
nss3.dll
ntdll.dll
oftware\Microsoft\Windows Messaging Subsystem\Profiles\975CFF0413111d3B88A0104B2A6676\
ole32.dll
onRG
open
opera
password:
pci!O`cBpCe
places.sqlite
plugins
profile:
profiles.ini
psapi.dll
rstrtmgr.dll
runas
screenshot.jpg
shell32.dll
shlwapi.dll
soft
softokn3.dll
sqlite3.dll
sqlite3_close
sqlite3_column_blob
sqlite3_column_bytes
sqlite3_column_text
sqlite3_finalize
sqlite3_open
sqlite3_prepare_v2
sqlite3_step
sscanf
ssfn*
system_info.txt
t:KcKMG
t]E:Bh+
t]KOzk;+jWD
token
token:
url:
user32.dll
usernameField
v+It`2K
vcruntime140.dll
vuwt`i
wUj6H Q6{E
wallets
wininet.dll
wsprintfA
wsprintfW
w~91dJ_
xBE!tJ?+
xJH\(GQrr`c@Yq.r}NVJ GtJgX8m
yI[F{nRo~+,
year:
zgJO
{A@yfF~c5:
{U[v1O*J.sj<
{Y}|KVJ2xy
{ewYJQdt{
}FyU>
~FJ44
Nanocore
(PID) Process(916) plugmanzx.exe
BuildTime2023-11-27 17:18:32.835816
Version1.2.2.0
Mutex3f30b298-001f-4f08-b22c-606b0d3632bd
DefaultGrouprn728
PrimaryConnectionHostrn72836.sytes.net
BackupConnectionHost127.0.0.1
ConnectionPort6696
RunOnStartupTrue
RequestElevationFalse
BypassUserAccountControlTrue
ClearZoneIdentifierTrue
ClearAccessControlFalse
SetCriticalProcessFalse
PreventSystemSleepTrue
ActivateAwayModeFalse
EnableDebugModeFalse
RunDelay0
ConnectDelay4000
RestartDelay5000
TimeoutInterval5000
KeepAliveTimeout30000
MutexTimeout5000
LanTimeout2500
WanTimeout8000
BufferSize65535
MaxPacketSize10485760
GCThreshold10485760
UseCustomDnsServerTrue
PrimaryDnsServer8.8.8.8
BackupDnsServer8.8.4.4
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:02 23:28:39+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2048 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x269e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | New Text Document.exe |
| LegalCopyright: | |
| OriginalFileName: | New Text Document.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
380
Monitored processes
239
Malicious processes
85
Suspicious processes
21
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Users\admin\Desktop\New folder\Zrwjjtizco.exe" | C:\Users\admin\Desktop\New folder\Zrwjjtizco.exe | New Text Document.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 148 | "C:\Program Files\Google\Update\GoogleUpdate.exe" /handoff "appguid={8A69D345-D564-463C-AFF1-A69D9E530F96}&iid={4611E087-CB70-244B-9202-F605357A02F4}&lang=en&browser=5&usagestats=1&appname=Google%20Chrome&needsadmin=prefers&ap=x64-stable-statsdef_1&brand=CHBF&installdataindex=empty" /installsource taggedmi /sessionid "{9D4D6F02-E360-4E8E-95BA-BDC336E00C67}" | C:\Program Files\Google\Update\GoogleUpdate.exe | — | GoogleUpdate.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: HIGH Description: Google Installer Exit code: 0 Version: 1.3.33.23 Modules
| |||||||||||||||
| 292 | "C:\Users\admin\Desktop\New folder\cp.exe" | C:\Users\admin\Desktop\New folder\cp.exe | — | New Text Document.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 564 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Roaming\ComponentBrowserReviewdriver\GzFHKWRISy3MAmto9HVQ7poMYvkztgwswn9El4Crr2v2xl8atDlv.bat" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 600 | "C:\Users\admin\Desktop\New folder\Muqpgf.exe" | C:\Users\admin\Desktop\New folder\Muqpgf.exe | — | Muqpgf.exe | |||||||||||
User: admin Company: GitHub Integrity Level: MEDIUM Description: Update Exit code: 4294967295 Version: 1.1.1.0 Modules
| |||||||||||||||
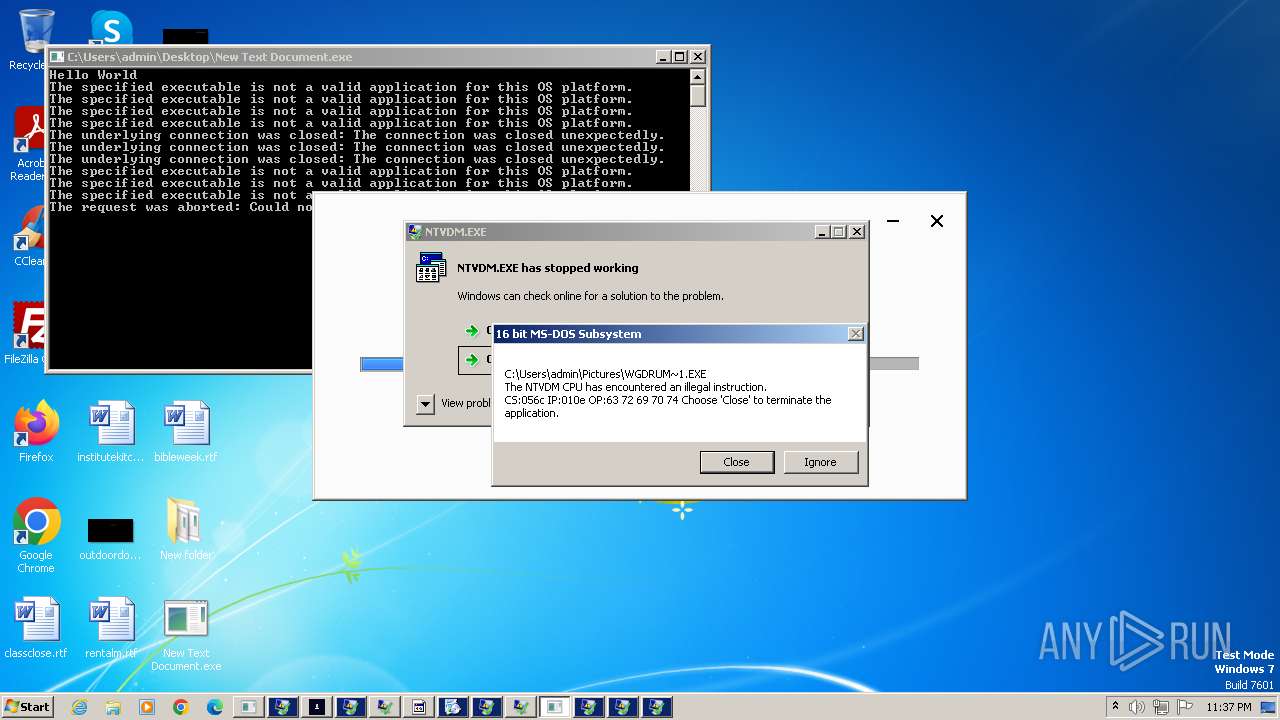
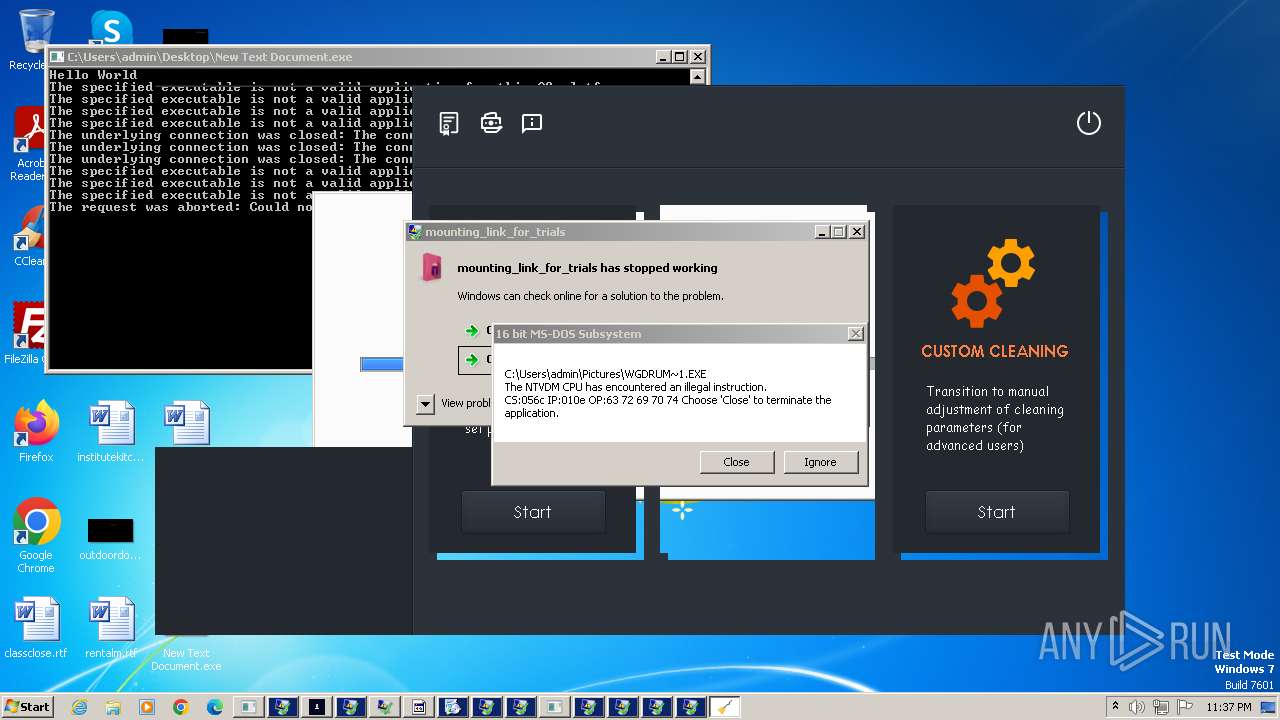
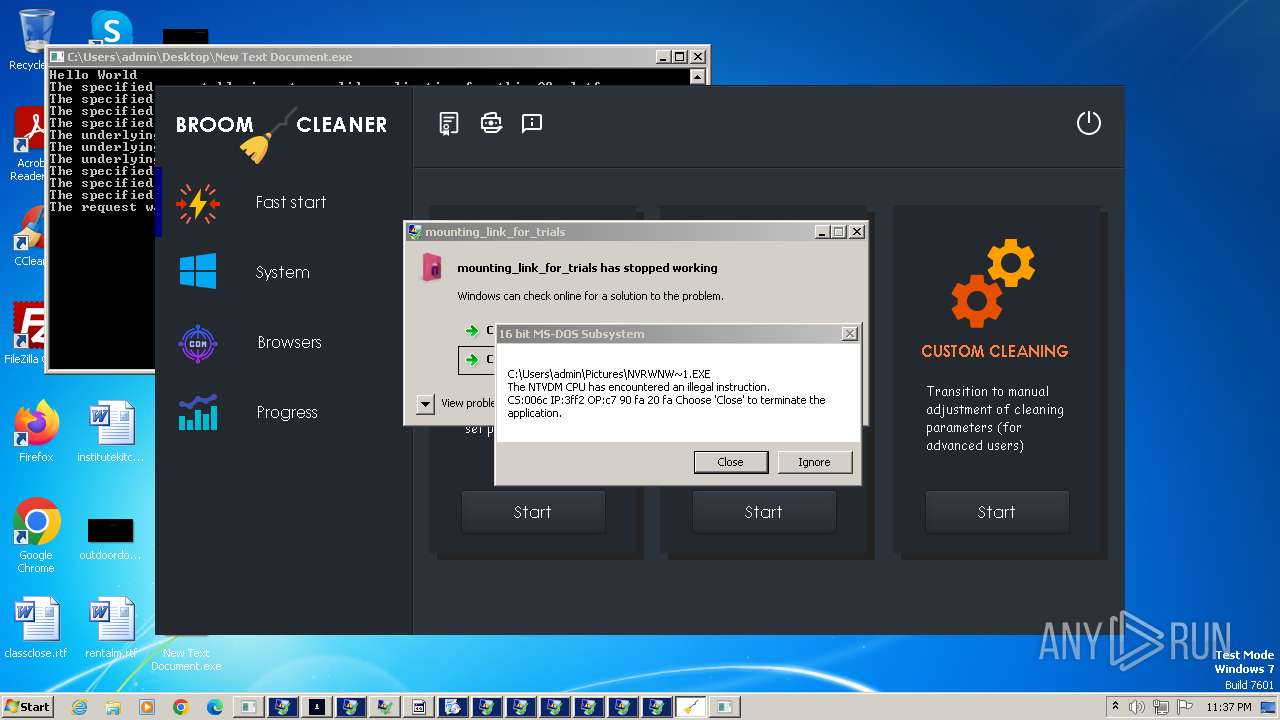
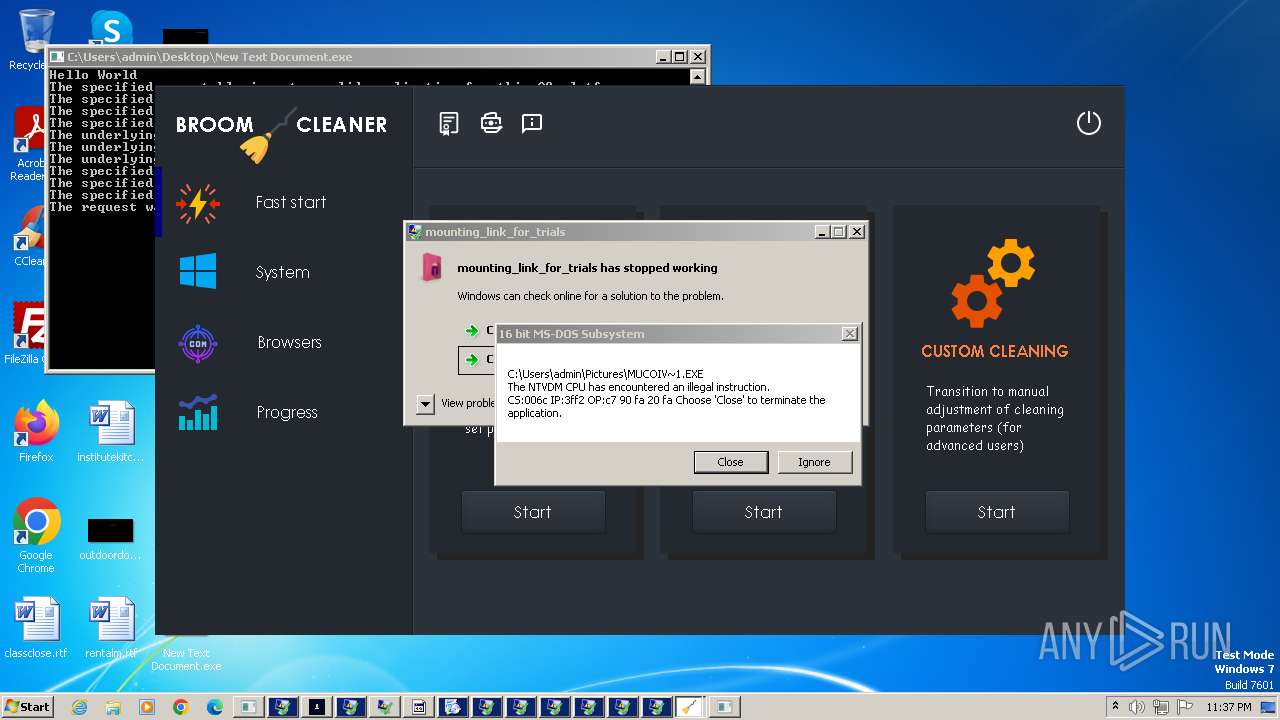
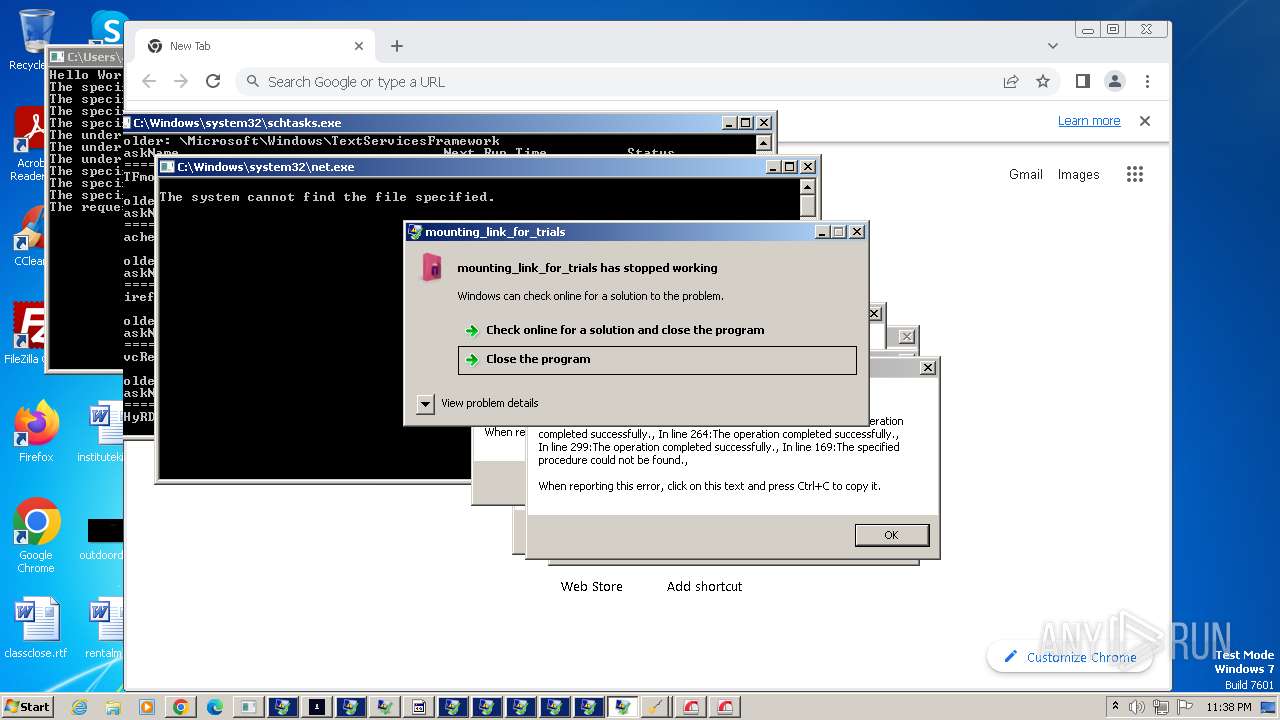
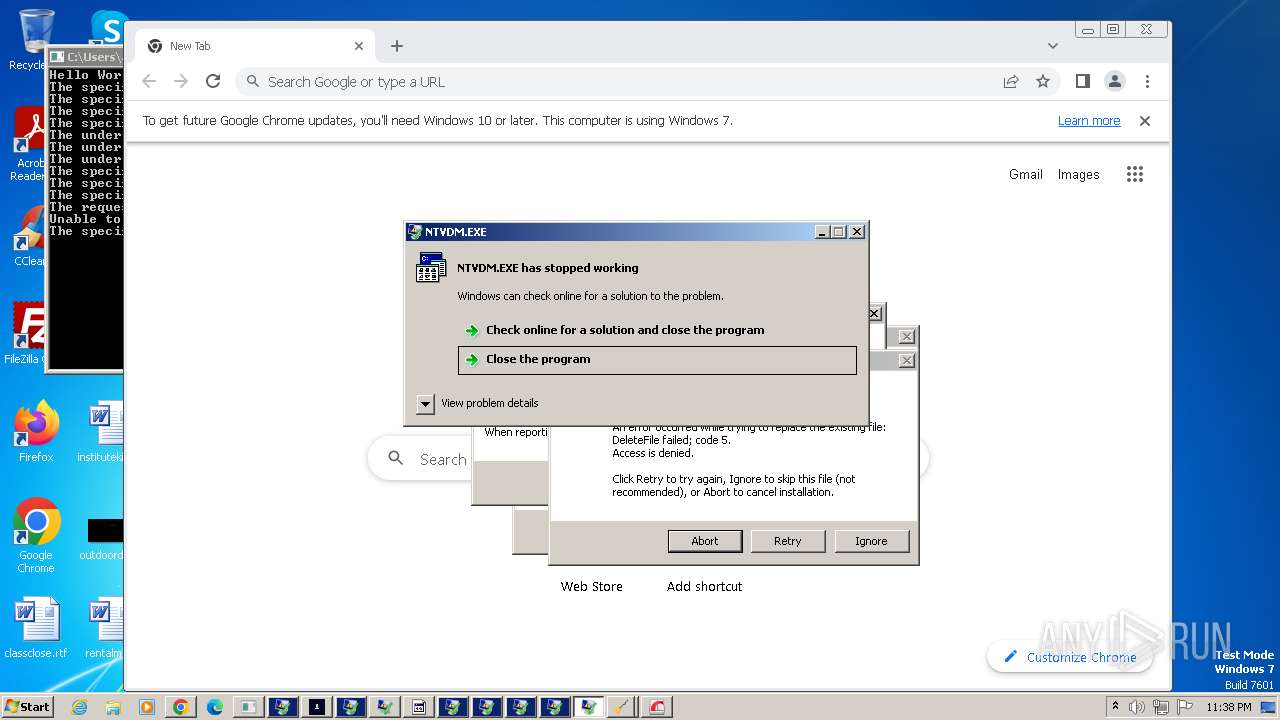
| 732 | "C:\Windows\system32\ntvdm.exe" -i2 | C:\Windows\System32\ntvdm.exe | CasPol.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 3221225477 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | "C:\Users\admin\Pictures\oHkQBQ7L3fh0WKwm3wOcq70n.exe" | C:\Users\admin\Pictures\oHkQBQ7L3fh0WKwm3wOcq70n.exe | CasPol.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
OnlyLogger(PID) Process(904) oHkQBQ7L3fh0WKwm3wOcq70n.exe C285.209.11.204 | |||||||||||||||
| 916 | "C:\Users\admin\Desktop\New folder\plugmanzx.exe" | C:\Users\admin\Desktop\New folder\plugmanzx.exe | plugmanzx.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: OPOS Service Exit code: 0 Version: 1.0.0.0 Modules
Nanocore(PID) Process(916) plugmanzx.exe BuildTime2023-11-27 17:18:32.835816 Version1.2.2.0 Mutex3f30b298-001f-4f08-b22c-606b0d3632bd DefaultGrouprn728 PrimaryConnectionHostrn72836.sytes.net BackupConnectionHost127.0.0.1 ConnectionPort6696 RunOnStartupTrue RequestElevationFalse BypassUserAccountControlTrue ClearZoneIdentifierTrue ClearAccessControlFalse SetCriticalProcessFalse PreventSystemSleepTrue ActivateAwayModeFalse EnableDebugModeFalse RunDelay0 ConnectDelay4000 RestartDelay5000 TimeoutInterval5000 KeepAliveTimeout30000 MutexTimeout5000 LanTimeout2500 WanTimeout8000 BufferSize65535 MaxPacketSize10485760 GCThreshold10485760 UseCustomDnsServerTrue PrimaryDnsServer8.8.8.8 BackupDnsServer8.8.4.4 | |||||||||||||||
| 1004 | attrib +H "Installer.exe" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | hv.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
105 340
Read events
103 292
Write events
1 945
Delete events
103
Modification events
| (PID) Process: | (2644) New Text Document.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2644) New Text Document.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2644) New Text Document.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2644) New Text Document.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2644) New Text Document.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3832) 1701007523-Hzxlsavkq.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3832) 1701007523-Hzxlsavkq.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3832) 1701007523-Hzxlsavkq.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3832) 1701007523-Hzxlsavkq.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3864) twelv.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
750
Suspicious files
299
Text files
355
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | twelv.exe | C:\Program Files\360\360Safe\deepscan\speedmem2.hg | binary | |
MD5:9E3F1E35A7A3E82A59307EF526433DFF | SHA256:C5EBC67610EEBC695A4910E7924F96E38D74ABEAB2C195D156B56F42B7D0486B | |||
| 2644 | New Text Document.exe | C:\Users\admin\Desktop\New folder\svchost.exe | executable | |
MD5:A4212217A2E90127CF2870215D72EDF5 | SHA256:6AD9AC5AB7A0071A789065D1FE2FDE732D88BE8FAAF4E875E3097157BEE34D38 | |||
| 3864 | twelv.exe | C:\Users\admin\AppData\Local\Temp\nsk2106.tmp | binary | |
MD5:615C251B298303A6315577A9EDCF29E7 | SHA256:BCEB71407AE4EADB38DDB7E7ED0096507F9BD292261B38DC3E159953AEE6C2B5 | |||
| 2644 | New Text Document.exe | C:\Users\admin\Desktop\New folder\WatchDog.exe | executable | |
MD5:4AA5E32BFE02AC555756DC9A3C9CE583 | SHA256:8A9235655B1A499D7DD9639C7494C3664E026B72B023D64EA8166808784A8967 | |||
| 3340 | good.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\FANBooster131.lnk | binary | |
MD5:35B402FE8901CD605084F5A712517E54 | SHA256:8C05524DA2DED727133409CA3DE5C212B8FF778E62C80A63C42B961624044852 | |||
| 3916 | 1701007523-Hzxlsavkq.exe | C:\Users\admin\AppData\Local\CurrentValue\zocunaj\TypeId.exe | executable | |
MD5:29620F5D86C39FA73939FDB10803F683 | SHA256:3A85404FC09AC9B9A1DC9B2470E3582055517254BC3BFC7894A7C37DB6B31216 | |||
| 2644 | New Text Document.exe | C:\Users\admin\Desktop\New folder\twelv.exe | executable | |
MD5:6F5BAD34630757F92632E3691314AB90 | SHA256:9C8842F212BAE9485736D671DFC506632E80D0F11DF8BF926AAED73FF48B32FF | |||
| 3864 | twelv.exe | C:\Users\admin\AppData\Local\Temp\nsv20F6.tmp\Checker.dll | executable | |
MD5:84C45156C6048B6764BD12ABE86E6497 | SHA256:4ACF888EEA6DB480C9724F1DDB587AF5680CAD6F654983097E3806FFE0FB130F | |||
| 3340 | good.exe | C:\Users\admin\AppData\Local\Temp\rise131M9Asphalt.tmp | text | |
MD5:4DC997CA884E68C3DD569D24F5F4E8D3 | SHA256:9DB31101C775185DDFF5B727F79B680E4F75364F9C0B508F02504B6993443405 | |||
| 3340 | good.exe | C:\Users\admin\AppData\Local\Temp\posterBox8BUwkAs1eDd15\Ei8DrAmaYu9Kkey4.db | binary | |
MD5:F62D8E993EA9C3B3A89DA19E4012638D | SHA256:0971230A77EE2C3531E8B97E14954692713D5F7C8684788F4A823BBC05AD377A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
263
TCP/UDP connections
213
DNS requests
89
Threats
636
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2644 | New Text Document.exe | GET | 200 | 195.20.16.153:80 | http://195.20.16.153/xmrig.exe | unknown | executable | 2.89 Mb | unknown |
2644 | New Text Document.exe | GET | 200 | 195.20.16.153:80 | http://195.20.16.153/svchost.exe | unknown | executable | 322 Kb | unknown |
2644 | New Text Document.exe | GET | — | 98.126.19.29:80 | http://98.126.19.29/s/twelv.exe | unknown | — | — | unknown |
2644 | New Text Document.exe | GET | 200 | 195.20.16.153:80 | http://195.20.16.153/WatchDog.exe | unknown | executable | 62.0 Kb | unknown |
2644 | New Text Document.exe | GET | 200 | 163.123.142.171:8080 | http://163.123.142.171:8080/file/1701007523-Hzxlsavkq.exe | unknown | executable | 593 Kb | unknown |
2644 | New Text Document.exe | GET | 200 | 109.107.182.3:80 | http://109.107.182.3/moda/good.exe | unknown | executable | 1.47 Mb | unknown |
— | — | GET | 200 | 107.173.143.18:80 | http://107.173.143.18/155/wlanext.exe | unknown | executable | 912 Kb | unknown |
— | — | POST | — | 192.186.7.211:2001 | http://192.186.7.211:2001/ | unknown | — | — | unknown |
2644 | New Text Document.exe | GET | 200 | 163.123.142.171:8080 | http://163.123.142.171:8080/file/1701008833-Ywnbevy.exe | unknown | executable | 628 Kb | unknown |
2644 | New Text Document.exe | GET | 200 | 45.197.44.206:80 | http://45.197.44.206/1113/miiyyjss.exe | unknown | executable | 386 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2644 | New Text Document.exe | 151.101.2.49:443 | urlhaus.abuse.ch | FASTLY | US | unknown |
2644 | New Text Document.exe | 195.20.16.153:80 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2644 | New Text Document.exe | 104.21.16.107:443 | chatnoir.life | CLOUDFLARENET | — | unknown |
2644 | New Text Document.exe | 163.123.142.171:8080 | — | AS-SERVERION | US | unknown |
2644 | New Text Document.exe | 98.126.19.29:80 | — | VPLSNET | US | unknown |
2644 | New Text Document.exe | 109.107.182.3:80 | — | Cloud assets LLC | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
urlhaus.abuse.ch |
| whitelisted |
chatnoir.life |
| unknown |
ipinfo.io |
| shared |
db-ip.com |
| whitelisted |
ftp.elquijotebanquetes.com |
| unknown |
gons34cl.top |
| malicious |
agenzia.servebeer.com |
| malicious |
modulo.servegame.com |
| malicious |
onlines.3utilities.com |
| malicious |
ip-api.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2644 | New Text Document.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
2644 | New Text Document.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2644 | New Text Document.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2644 | New Text Document.exe | Potentially Bad Traffic | ET HUNTING SUSPICIOUS Dotted Quad Host MZ Response |
2644 | New Text Document.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2644 | New Text Document.exe | A Network Trojan was detected | ET MALWARE Possible Kelihos.F EXE Download Common Structure |
2644 | New Text Document.exe | Potentially Bad Traffic | ET HUNTING Suspicious svchost.exe in URI - Possible Process Dump/Trojan Download |
2644 | New Text Document.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
2644 | New Text Document.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
2644 | New Text Document.exe | Potentially Bad Traffic | ET INFO Executable Download from dotted-quad Host |
40 ETPRO signatures available at the full report
Process | Message |
|---|---|
Random.exe | Could not load file or assembly '420864 bytes loaded from Anonymously Hosted DynamicMethods Assembly, Version=0.0.0.0, Culture=neutral, PublicKeyToken=null' or one of its dependencies. An attempt was made to load a program with an incorrect format.
|
InstallSetup2.exe | Could not load file or assembly '1318400 bytes loaded from Anonymously Hosted DynamicMethods Assembly, Version=0.0.0.0, Culture=neutral, PublicKeyToken=null' or one of its dependencies. An attempt was made to load a program with an incorrect format.
|