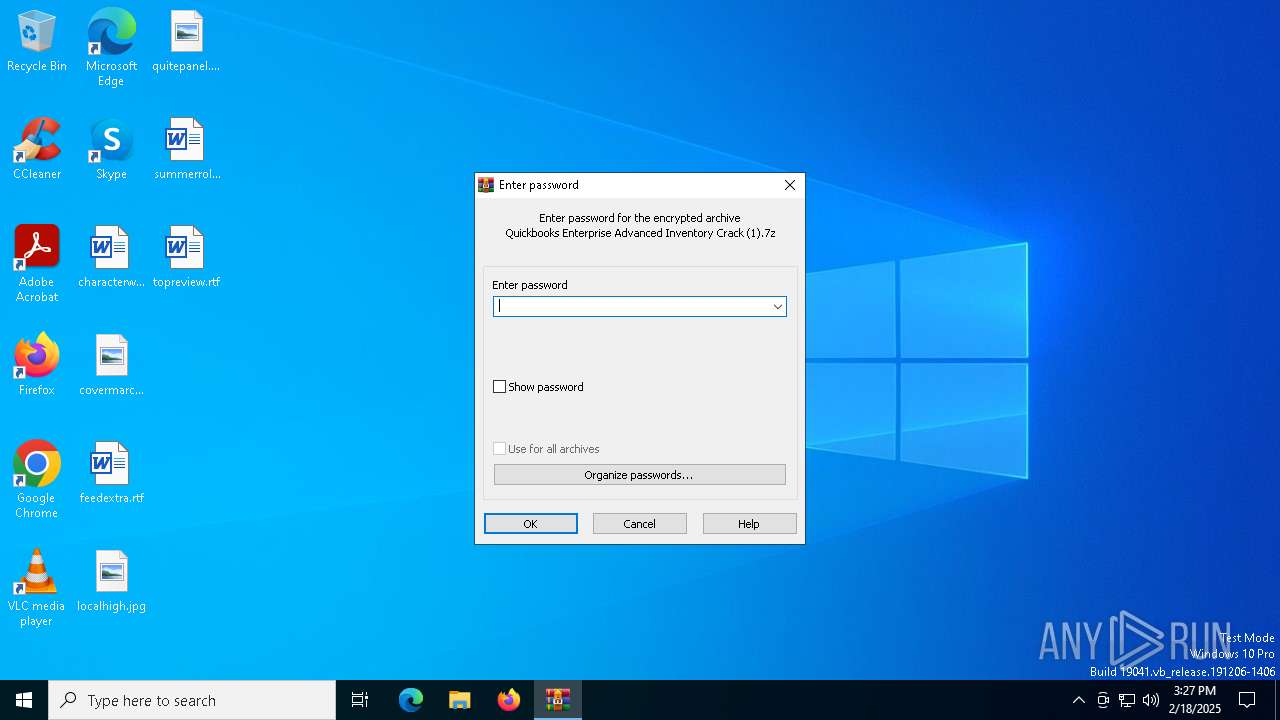
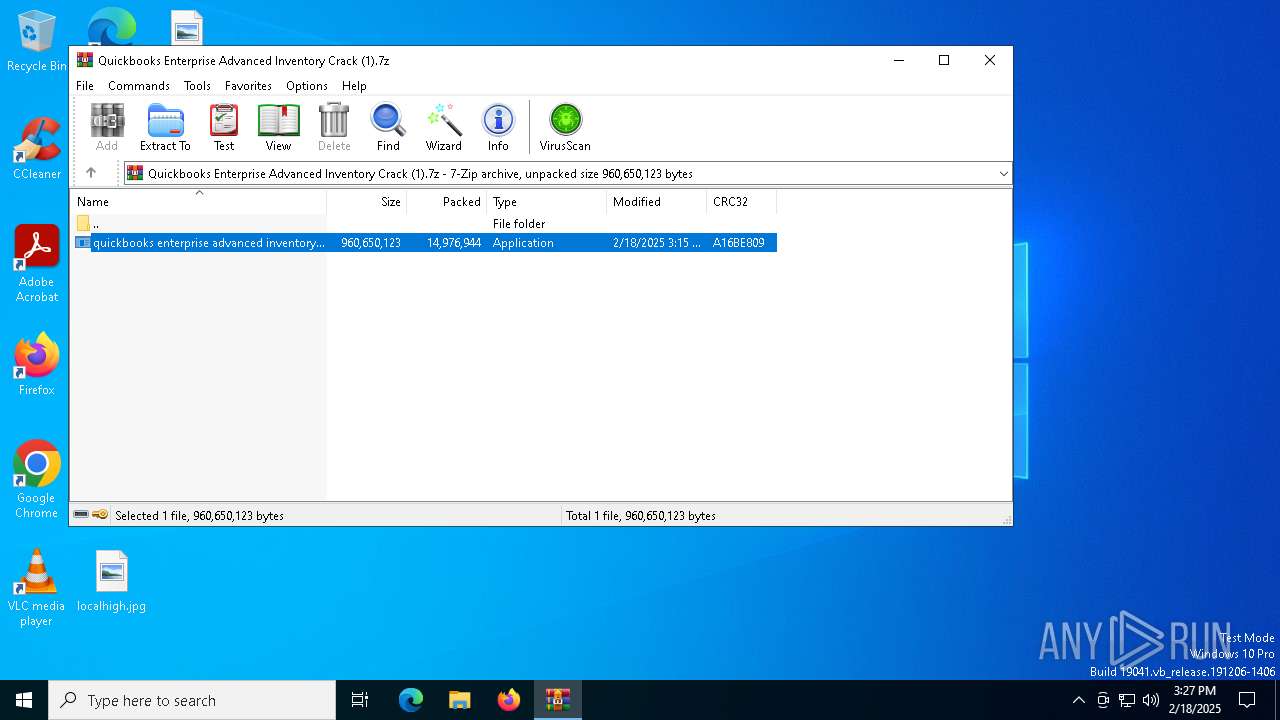
| File name: | Quickbooks Enterprise Advanced Inventory Crack (1).7z |
| Full analysis: | https://app.any.run/tasks/b2034021-69e2-4cfb-a3e0-5cea4e372771 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 18, 2025, 15:27:27 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 1601693163A106950205286319CE5EE5 |
| SHA1: | C8791130C4359E8DC430E1CB5DE49D4B8440BC44 |
| SHA256: | 8C47FDCD5415B41DEAEC2FC4BAE36CA7E21F3AFE8870CE9D64EC054906EAF3DF |
| SSDEEP: | 98304:KFUASL9/hRTCb2GArhai2UFO0/bvOgGQyWMCH4ALhl3iGBRNWj1Jx1PzredDYYsy:rfV8LSKfxKjKvHrZq81/rnidZgXbBz6 |
MALICIOUS
AutoIt loader has been detected (YARA)
- Watch.com (PID: 3700)
LUMMA mutex has been found
- Watch.com (PID: 3700)
Steals credentials from Web Browsers
- Watch.com (PID: 3700)
Actions looks like stealing of personal data
- Watch.com (PID: 3700)
Executing a file with an untrusted certificate
- Dashboard.exe (PID: 5544)
- Dashboard.exe (PID: 4144)
- Dashboard.exe (PID: 1540)
Known privilege escalation attack
- dllhost.exe (PID: 3732)
SUSPICIOUS
Reads security settings of Internet Explorer
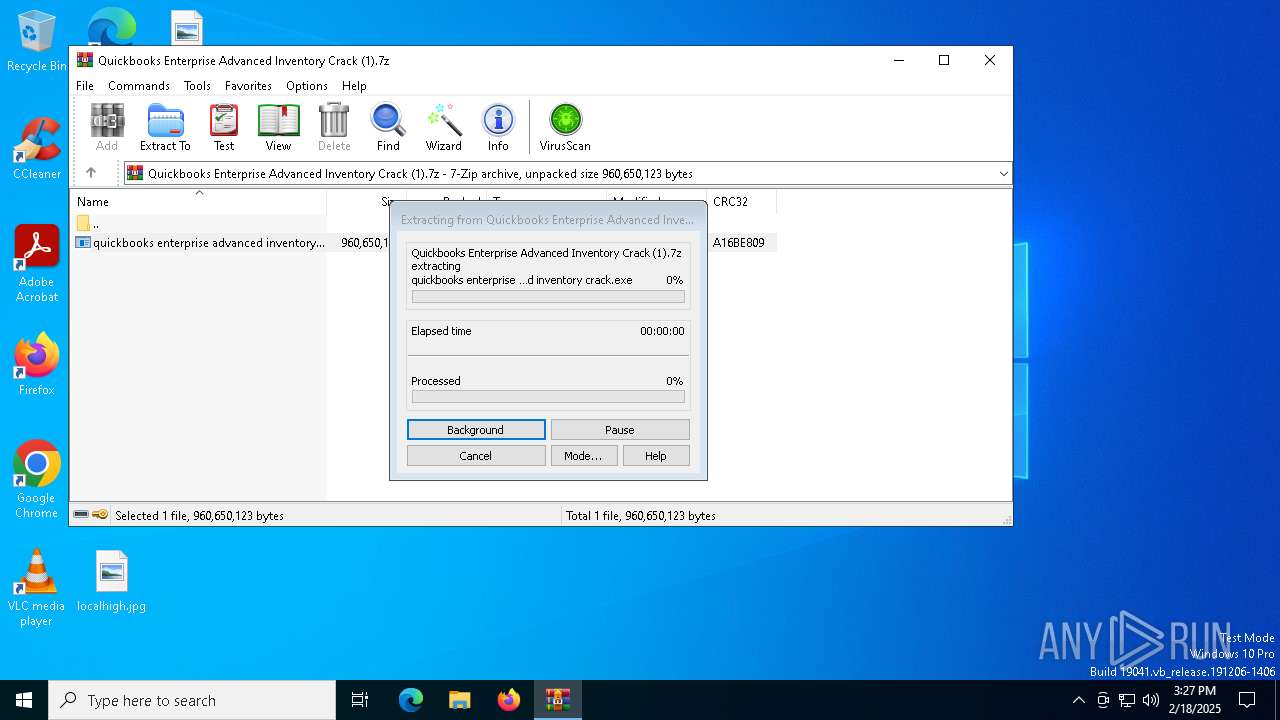
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
- WinRAR.exe (PID: 6376)
Executing commands from a ".bat" file
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
Get information on the list of running processes
- cmd.exe (PID: 6188)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6188)
Application launched itself
- cmd.exe (PID: 6188)
The executable file from the user directory is run by the CMD process
- Watch.com (PID: 3700)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6188)
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
- Dashboard.exe (PID: 4144)
- Dashboard.exe (PID: 1540)
Starts application with an unusual extension
- cmd.exe (PID: 6188)
Starts the AutoIt3 executable file
- cmd.exe (PID: 6188)
There is functionality for taking screenshot (YARA)
- Watch.com (PID: 3700)
Searches for installed software
- Watch.com (PID: 3700)
The process drops C-runtime libraries
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 5544)
Process drops legitimate windows executable
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 5544)
Executable content was dropped or overwritten
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 5544)
Starts a Microsoft application from unusual location
- Dashboard.exe (PID: 5544)
Starts itself from another location
- Dashboard.exe (PID: 5544)
INFO
Create files in a temporary directory
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
- expand.exe (PID: 876)
- extrac32.exe (PID: 6340)
- Dashboard.exe (PID: 4144)
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 1540)
Checks supported languages
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
- extrac32.exe (PID: 6340)
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 5544)
- Dashboard.exe (PID: 4144)
- Dashboard.exe (PID: 1540)
- expand.exe (PID: 876)
Reads the computer name
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
- extrac32.exe (PID: 6340)
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 5544)
- Dashboard.exe (PID: 4144)
- Dashboard.exe (PID: 1540)
Creates a new folder
- cmd.exe (PID: 6236)
Reads the software policy settings
- Watch.com (PID: 3700)
- explorer.exe (PID: 5112)
Creates files in the program directory
- Watch.com (PID: 3700)
The sample compiled with english language support
- Watch.com (PID: 3700)
- Dashboard.exe (PID: 5544)
Reads mouse settings
- Watch.com (PID: 3700)
Creates files or folders in the user directory
- Dashboard.exe (PID: 5544)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 3732)
Detects GO elliptic curve encryption (YARA)
- explorer.exe (PID: 5112)
Application based on Golang
- explorer.exe (PID: 5112)
Process checks computer location settings
- quickbooks enterprise advanced inventory crack.exe (PID: 5640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
147
Monitored processes
26
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | expand Representations.mpeg Representations.mpeg.bat | C:\Windows\SysWOW64\expand.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: LZ Expansion Utility Exit code: 0 Version: 5.00 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe" | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Live installer client executable Exit code: 1 Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 2084 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3296 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3700 | Watch.com T | C:\Users\admin\AppData\Local\Temp\300665\Watch.com | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script (Beta) Exit code: 0 Version: 3, 3, 15, 5 Modules
| |||||||||||||||
| 3732 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3992 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4144 | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | C:\Users\admin\AppData\Roaming\GUPM\Dashboard.exe | — | Dashboard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Live installer client executable Exit code: 1 Version: 12.0.1202.0516 Modules
| |||||||||||||||
| 4264 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 895
Read events
6 885
Write events
10
Delete events
0
Modification events
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Quickbooks Enterprise Advanced Inventory Crack (1).7z | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6376) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3732) dllhost.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
Executable files
12
Suspicious files
34
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
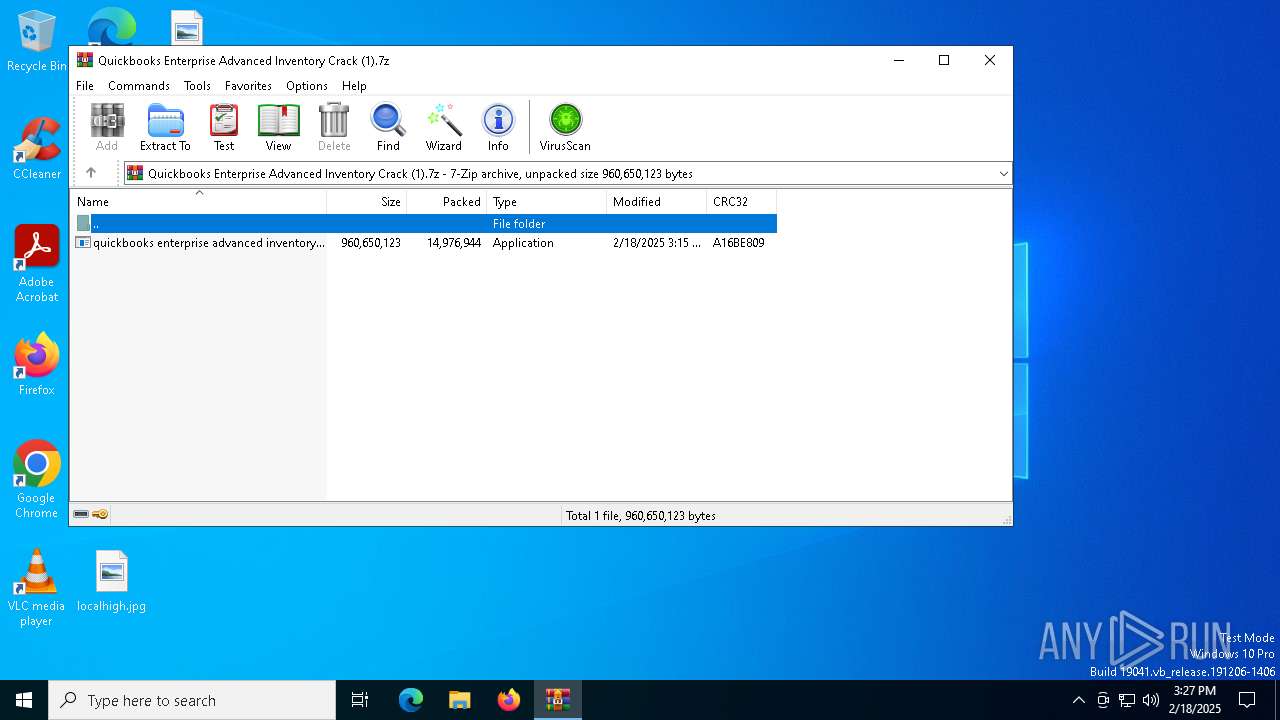
| 6376 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6376.26961\quickbooks enterprise advanced inventory crack.exe | — | |
MD5:— | SHA256:— | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Representations.mpeg | text | |
MD5:579FE262D575D653B0D1BCC2C729E210 | SHA256:695EA4F7D872A353C5DB460DA423695F382CB604361CA2E6B048C4776B3428F1 | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Decline.mpeg | binary | |
MD5:794CEC15799EC565C4138818FA6401D0 | SHA256:D0B208A1033E096032C797CF84456E5C5939DA9C8EFD60C0B106D29919FBDDA2 | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Bracelets.mpeg | binary | |
MD5:1F6895762FB00E6BF4A54C9940F26F8B | SHA256:5EC2C2E78A2747A06D71ED65EACE8905513526D25505FBE25FE515722DB55630 | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Sacramento.mpeg | binary | |
MD5:B28A232ED72CC7E1BB1FD24F28B7262A | SHA256:967B742FB3CA2A5C53962D43C8862FEC4285990DE5471DACC0BF1AF0918C934A | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Lenses.mpeg | binary | |
MD5:9DCD25C4605872FB2CA1962A57BDA15A | SHA256:C8C6A624DE75599C8F33FBB3DD150E2B950C7C15AE7009D709D7CAF2BAF0B32A | |||
| 876 | expand.exe | C:\Users\admin\AppData\Local\Temp\representations.mpeg.bat | text | |
MD5:579FE262D575D653B0D1BCC2C729E210 | SHA256:695EA4F7D872A353C5DB460DA423695F382CB604361CA2E6B048C4776B3428F1 | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Favor.mpeg | binary | |
MD5:A2D411D72A619B06EFF52F8015BD8C28 | SHA256:129A95105438A2F8EE033CE0C2A0A10E11A57F474AF8461206F50F5C56653D59 | |||
| 5640 | quickbooks enterprise advanced inventory crack.exe | C:\Users\admin\AppData\Local\Temp\Ppm.mpeg | binary | |
MD5:8FC53E131C48F2BF15681016F5D601D3 | SHA256:471D9BCCE1FC0760D9A6A48F56A0910D0C9F814F999ABC9B7DA626B64B86802D | |||
| 6340 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\Frequent | binary | |
MD5:240639A9D1060A077FA0849522CAC001 | SHA256:4BA19D3A21F799D2D8EC76370C09630739F7E56FA837EAC070EB48BAA9150202 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
42
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5880 | svchost.exe | GET | 200 | 23.48.23.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5880 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6628 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7056 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7056 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5880 | svchost.exe | 23.48.23.137:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5880 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2356 | RUXIMICS.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5880 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.204.157:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET FILE_SHARING Anonymous File Sharing Domain in DNS Lookup (qu .ax) |
3700 | Watch.com | Misc activity | ET FILE_SHARING Observed Anonymous File Sharing Service Domain (qu .ax) in TLS SNI |