| File name: | server123.exe |
| Full analysis: | https://app.any.run/tasks/9abc4fa8-f7b5-495b-868d-2d44fba53421 |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
| Analysis date: | April 15, 2019, 04:47:00 |
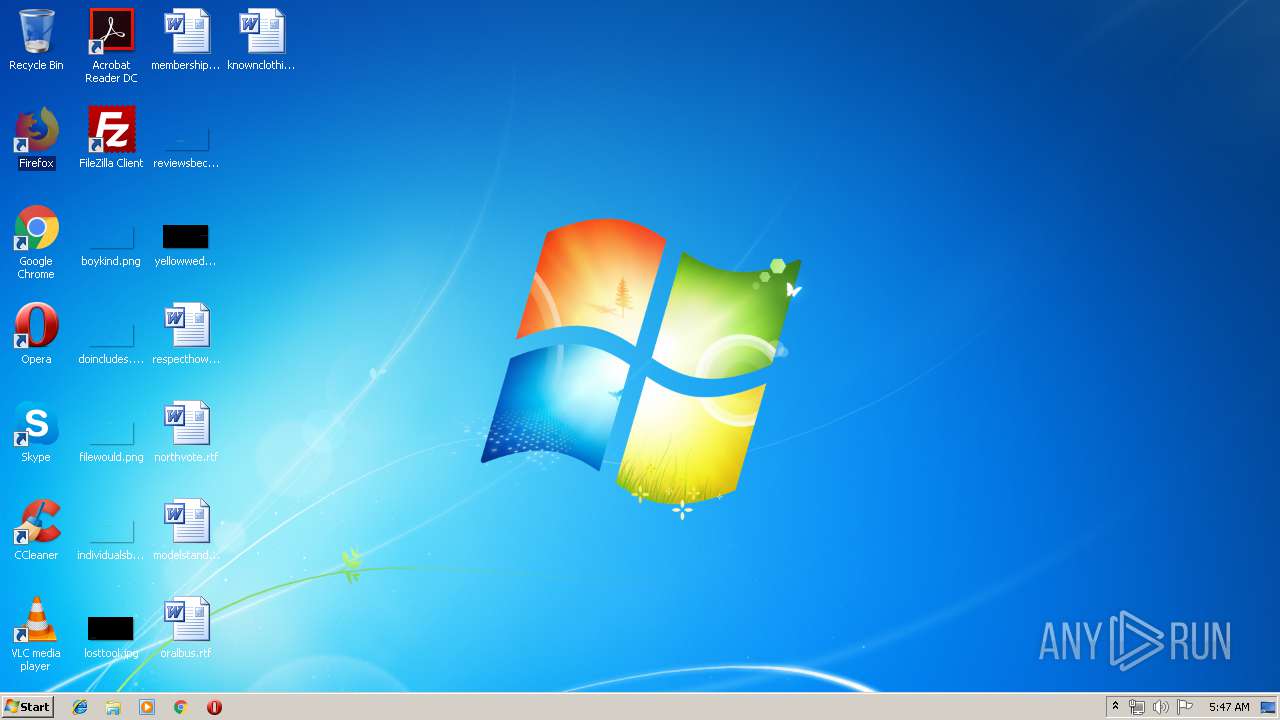
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 5DAE3B6D4A6B8D71C28A93A8AE78922B |
| SHA1: | 675FD912FFE13743AC1057DFEDAA07EB076FE6B8 |
| SHA256: | 8C4738743F3D07C792E77122A2F8A9851C7297BE1CAFA421BD31E836422163C3 |
| SSDEEP: | 3072:LxHvdduTb5J2k6+ildJkApvD+fG5xnJhhUHYZsIP5m5K:LNVduL2oixOGhJZ2K |
MALICIOUS
GH0ST was detected
- server123.exe (PID: 3880)
Connects to CnC server
- server123.exe (PID: 3880)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:11:01 08:04:57+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 4096 |
| InitializedDataSize: | 184320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1cc4 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Nov-2014 07:04:57 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 01-Nov-2014 07:04:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000E66 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.97578 |
.rdata | 0x00002000 | 0x000007E0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.68901 |
.data | 0x00003000 | 0x00000CD0 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35417 |
.rsrc | 0x00004000 | 0x0002C148 | 0x0002C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.17546 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
102 | 6.16601 | 180224 | Latin 1 / Western European | Chinese - PRC | DLL |
A29528ED2019322204048 | 3.52005 | 70 | Latin 1 / Western European | UNKNOWN | A29528ED2019322204048 |
Imports
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
Ip | 1 | 0x00001A52 |
Total processes
31
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3880 | "C:\Users\admin\AppData\Local\Temp\server123.exe" | C:\Users\admin\AppData\Local\Temp\server123.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3
Read events
3
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
4
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3880 | server123.exe | 154.91.144.7:2036 | — | IPTP LTD | HK | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3880 | server123.exe | A Network Trojan was detected | ET TROJAN Backdoor family PCRat/Gh0st CnC traffic (OUTBOUND) 53 |
3880 | server123.exe | A Network Trojan was detected | MALWARE [PTsecurity] Backdoor family PCRat/Gh0st CnC Response |
3880 | server123.exe | A Network Trojan was detected | MALWARE [PTsecurity] PCRat/Gh0st Response (Bronze Union APT) |
1 ETPRO signatures available at the full report