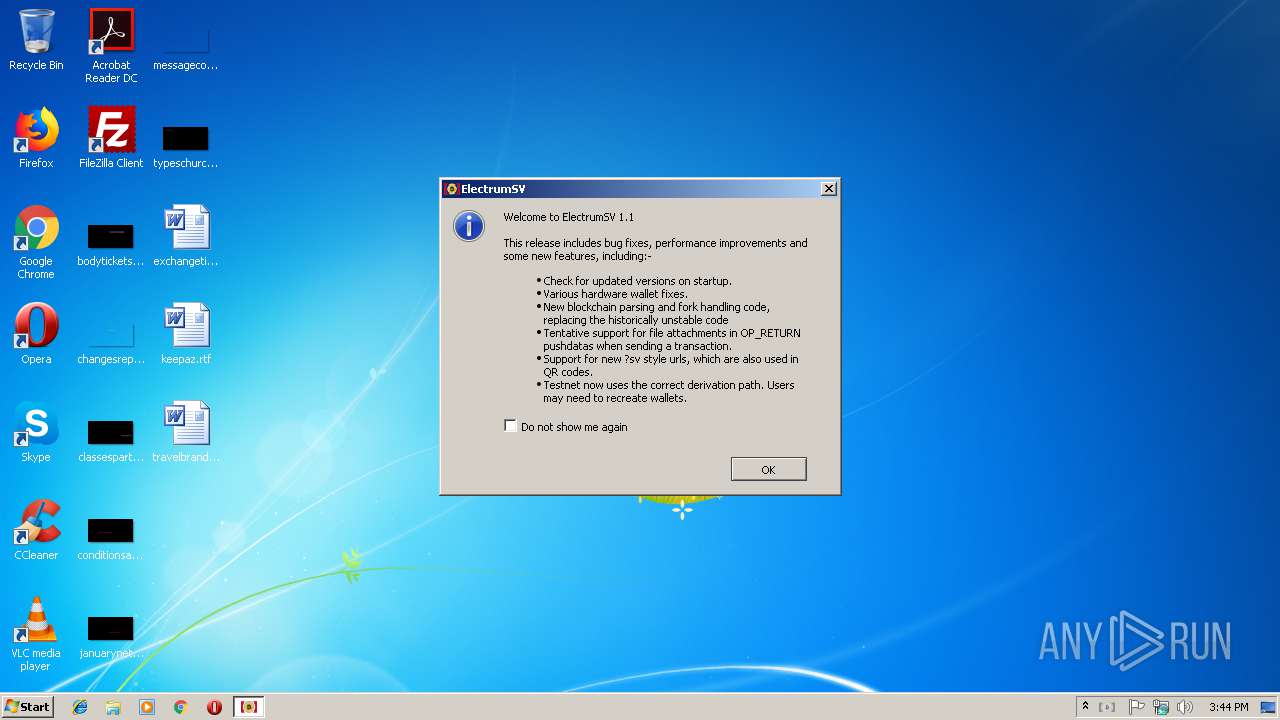
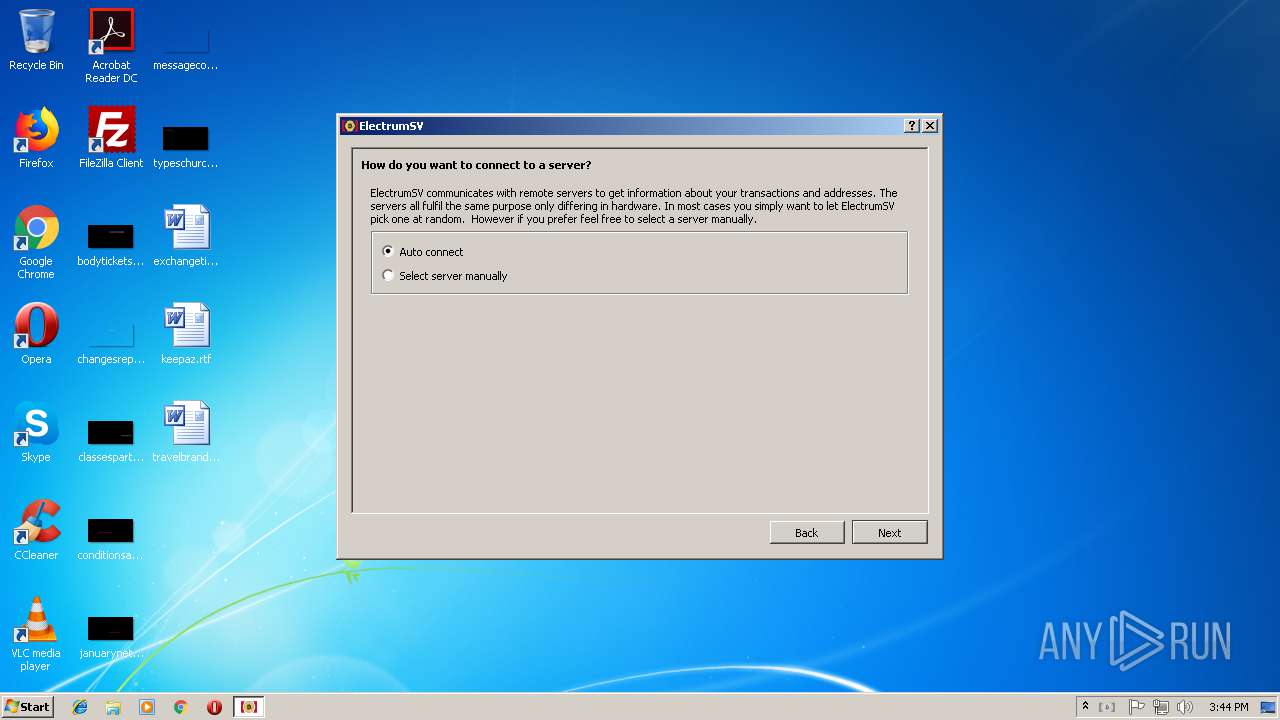
| download: | ElectrumSV-1.1.0.exe |
| Full analysis: | https://app.any.run/tasks/6c704453-d083-4e57-840e-f53be769fadb |
| Verdict: | Malicious activity |
| Threats: | TrickBot is an advanced banking trojan that attackers can use to steal payment credentials from the victims. It can redirect the victim to a fake banking cabinet and retrieve credentials typed in on the webpage. |
| Analysis date: | February 18, 2019, 15:43:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F5741A9E245B59F3751181755CCF4006 |
| SHA1: | B624D0682C3E44A8101626958202F14092755F42 |
| SHA256: | 8BC2A4E2984B9AB10672EFC8E80C3148194DE8081786FDE0463CFD92D1C3D9B5 |
| SSDEEP: | 393216:k2mhxt+09MTgRH66OyTbuBMYnc42Vzq4pVYbIu4hrKnXCxkQA12ayXm6yfHigo:k2YtNxOIbYfnctVzfpV3udy412LK |
MALICIOUS
Loads dropped or rewritten executable
- ElectrumSV-1.1.0.exe (PID: 2856)
SUSPICIOUS
Application launched itself
- ElectrumSV-1.1.0.exe (PID: 3692)
Loads Python modules
- ElectrumSV-1.1.0.exe (PID: 2856)
Connects to unusual port
- ElectrumSV-1.1.0.exe (PID: 2856)
Creates files in the user directory
- ElectrumSV-1.1.0.exe (PID: 2856)
Executable content was dropped or overwritten
- ElectrumSV-1.1.0.exe (PID: 3692)
INFO
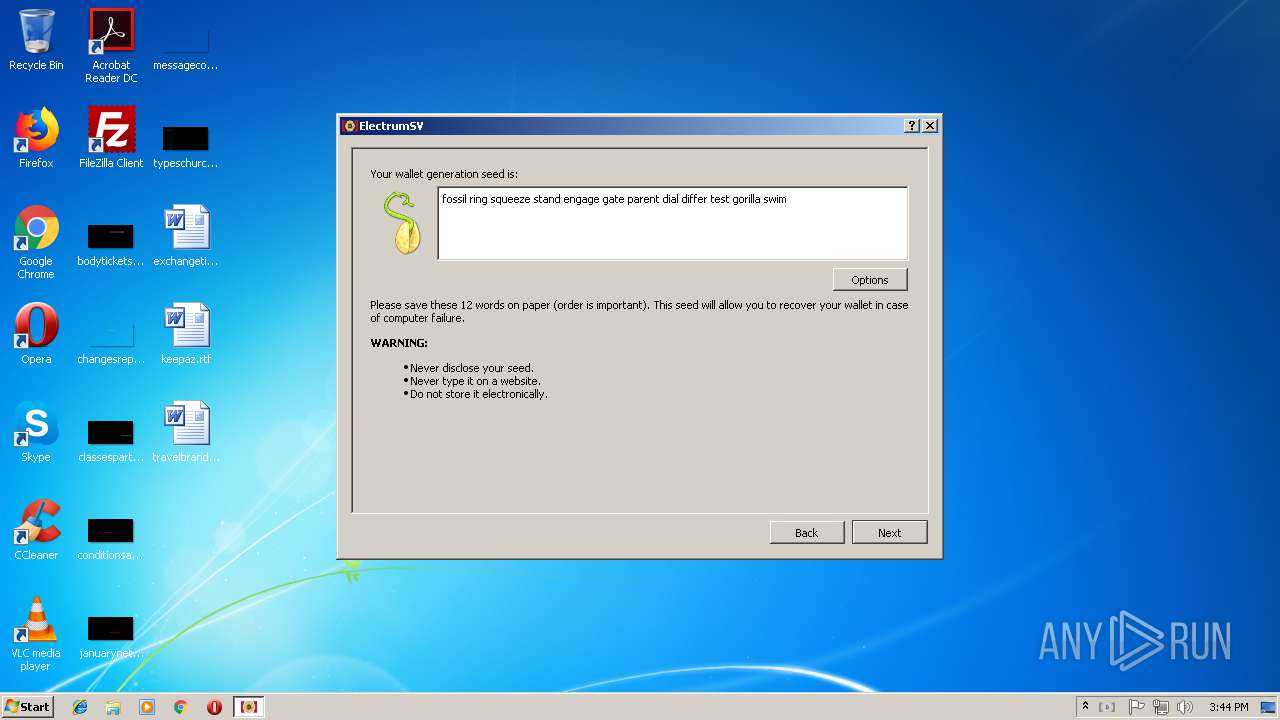
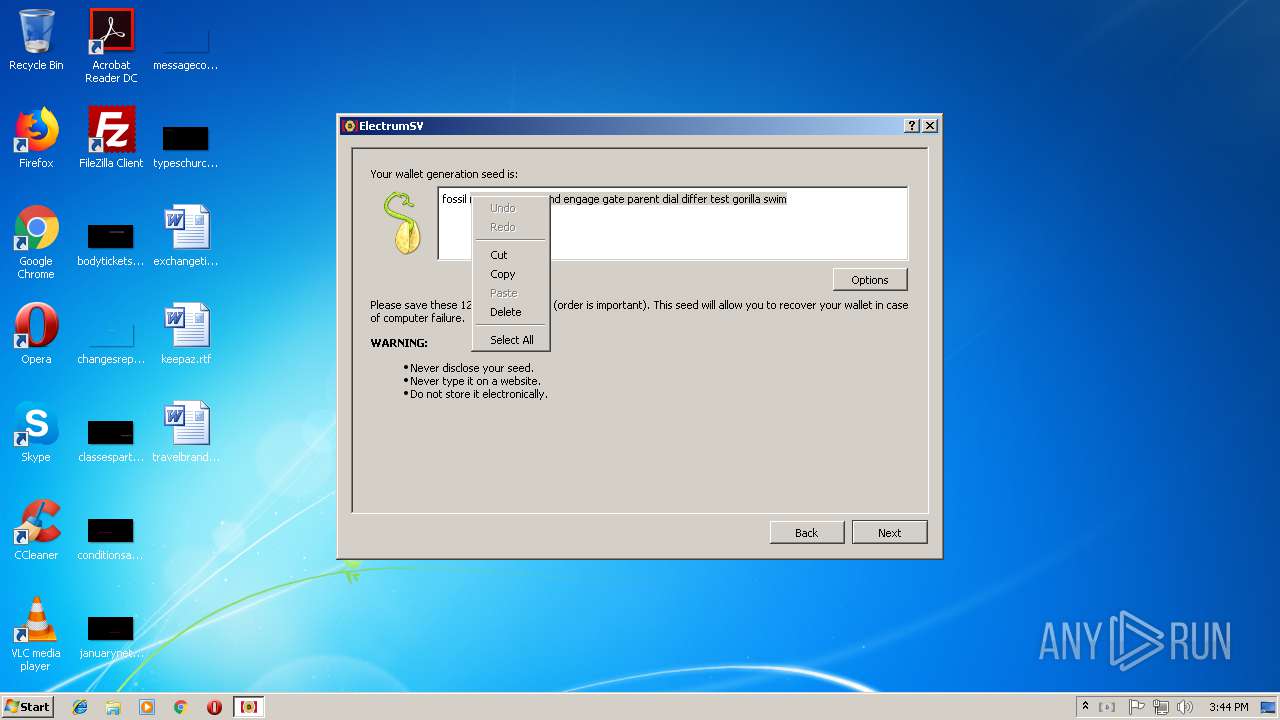
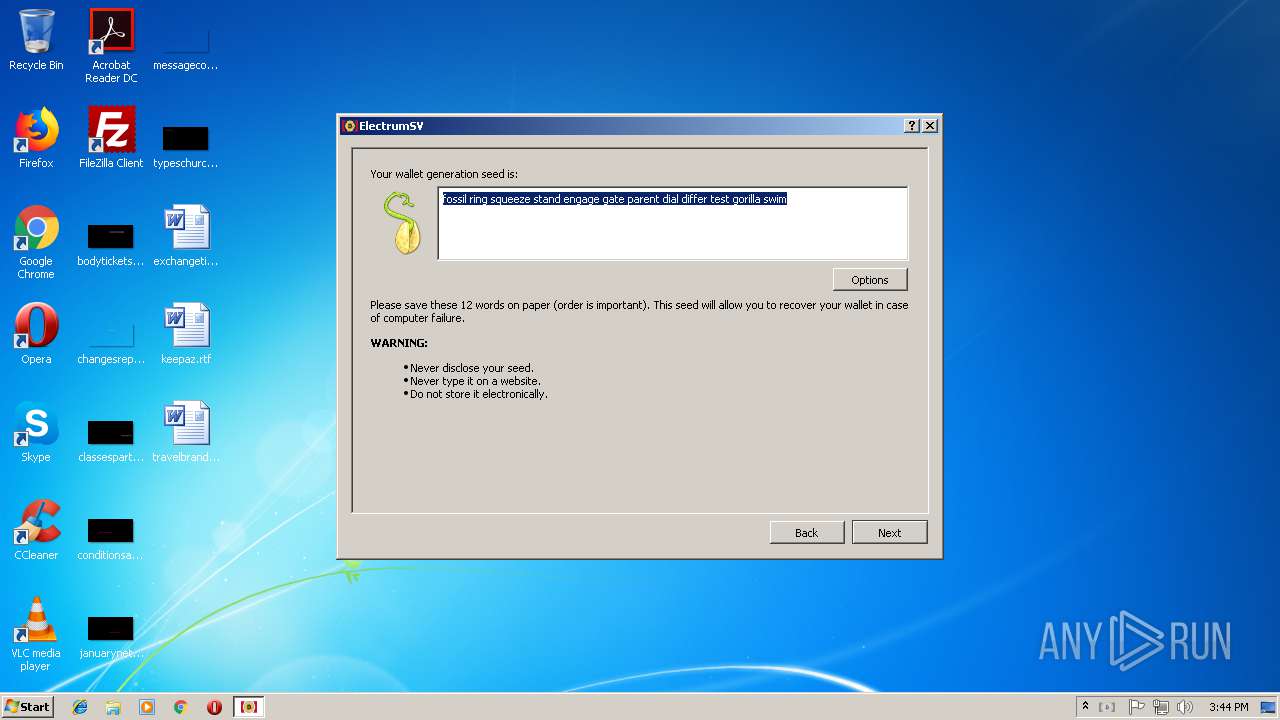
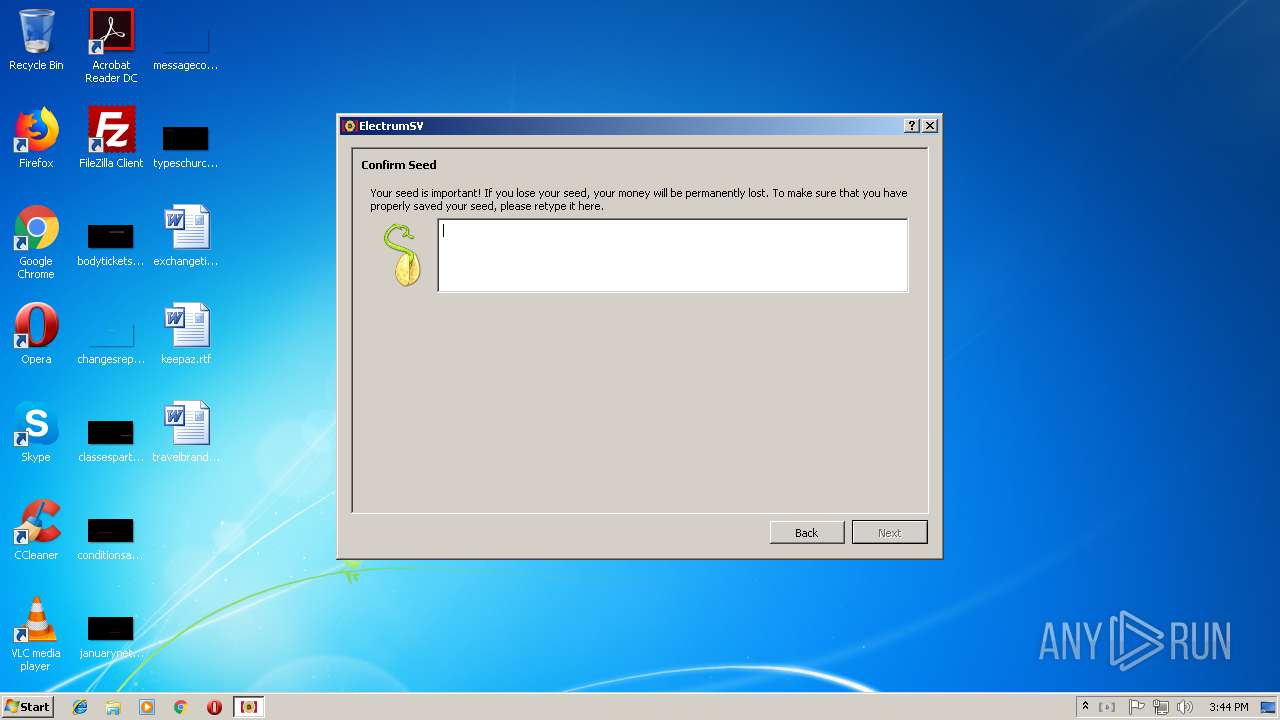
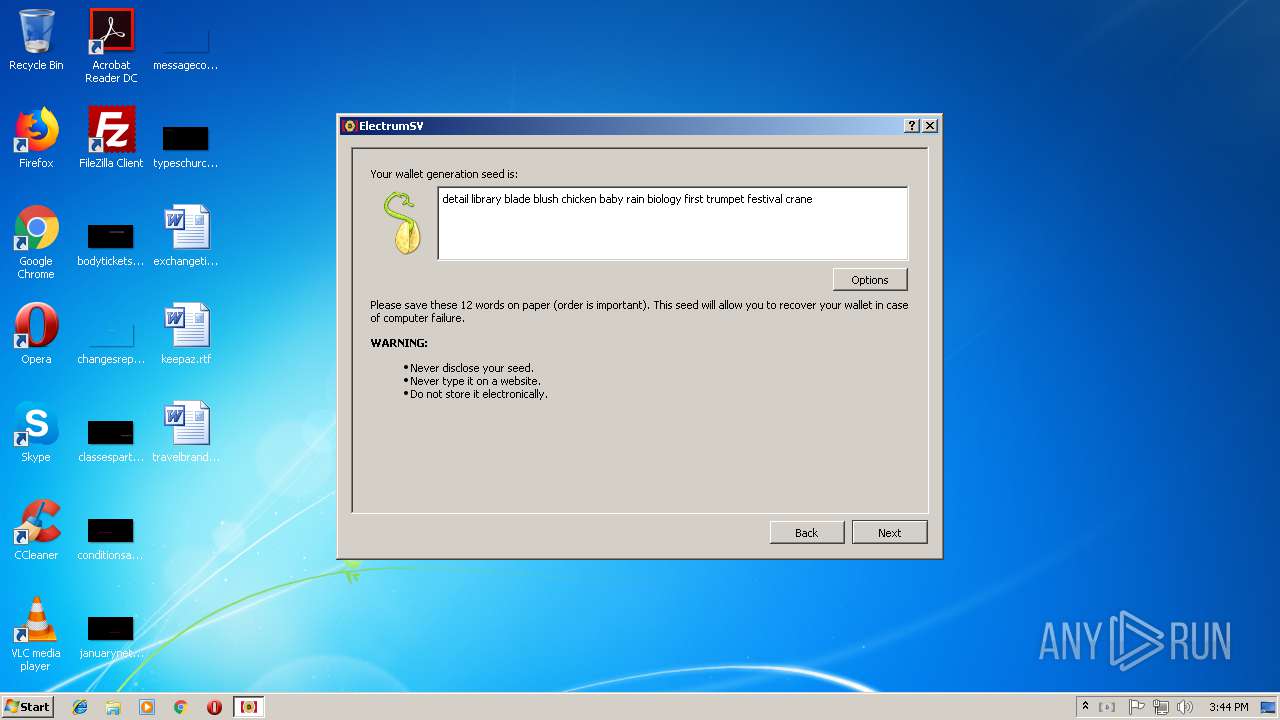
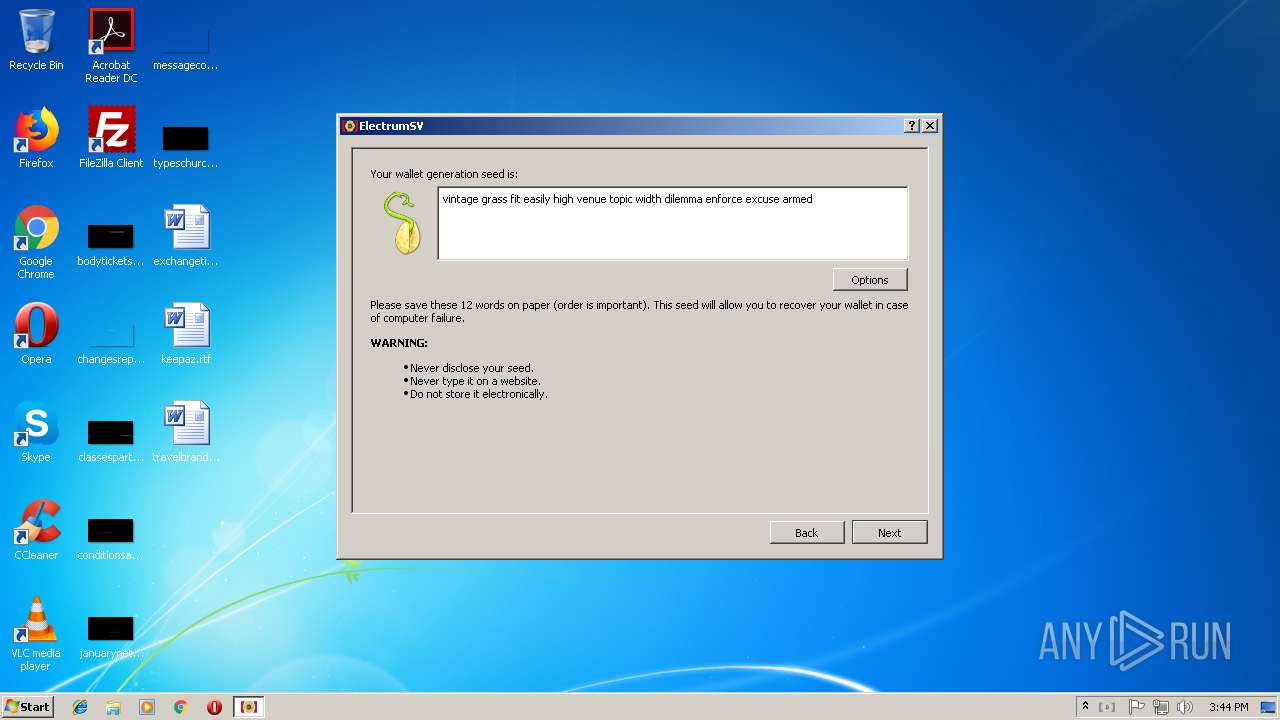
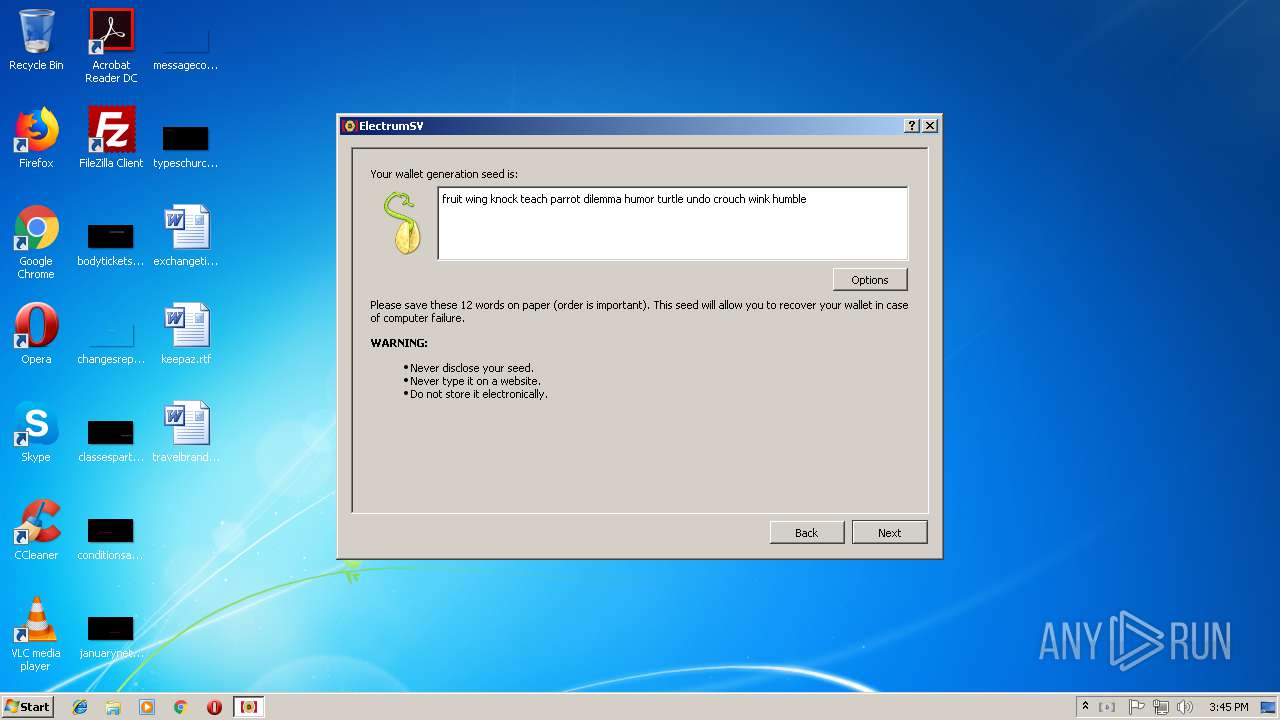
Dropped object may contain Bitcoin addresses
- ElectrumSV-1.1.0.exe (PID: 3692)
Reads settings of System Certificates
- ElectrumSV-1.1.0.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (50.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (32.2) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.6) |
| .exe | | | Win32 Executable (generic) (5.2) |
| .exe | | | Generic Win/DOS Executable (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:43:33+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 125952 |
| InitializedDataSize: | 111616 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79d3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Sep-2018 14:43:33 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:43:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001EB34 | 0x0001EC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64811 |
.rdata | 0x00020000 | 0x0000B164 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.09995 |
.data | 0x0002C000 | 0x0000E688 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.92387 |
.gfids | 0x0003B000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.83952 |
.rsrc | 0x0003C000 | 0x0000E000 | 0x0000DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.33258 |
.reloc | 0x0004A000 | 0x000017B4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65332 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.62007 | 76 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 | 5.51574 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 5.4927 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.26965 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.80982 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 7.98105 | 32904 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
WS2_32.dll |
Total processes
30
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2856 | "C:\Users\admin\AppData\Local\Temp\ElectrumSV-1.1.0.exe" | C:\Users\admin\AppData\Local\Temp\ElectrumSV-1.1.0.exe | ElectrumSV-1.1.0.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3692 | "C:\Users\admin\AppData\Local\Temp\ElectrumSV-1.1.0.exe" | C:\Users\admin\AppData\Local\Temp\ElectrumSV-1.1.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
250
Read events
250
Write events
0
Delete events
0
Modification events
Executable files
86
Suspicious files
43
Text files
163
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_raw_des.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_raw_aesni.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_Salsa20.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_raw_cast.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_raw_des3.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_raw_ocb.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Cipher\_raw_arc2.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Hash\_BLAKE2s.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Hash\_MD2.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
| 3692 | ElectrumSV-1.1.0.exe | C:\Users\admin\AppData\Local\Temp\_MEI36922\Cryptodome\Hash\_BLAKE2b.cp36-win32.pyd | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
23
DNS requests
10
Threats
25
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | ElectrumSV-1.1.0.exe | 159.65.89.39:50002 | electroncash.cascharia.com | — | US | unknown |
2856 | ElectrumSV-1.1.0.exe | 76.174.26.91:60004 | sv1.hsmiths.com | Time Warner Cable Internet LLC | US | unknown |
2856 | ElectrumSV-1.1.0.exe | 176.9.148.163:50002 | sv.electrumx.cash | Hetzner Online GmbH | DE | unknown |
2856 | ElectrumSV-1.1.0.exe | 62.75.252.35:50002 | satoshi.vision.cash | Host Europe GmbH | FR | unknown |
2856 | ElectrumSV-1.1.0.exe | 104.24.98.82:443 | electrumsv.io | Cloudflare Inc | US | shared |
2856 | ElectrumSV-1.1.0.exe | 68.183.184.123:50002 | electron.bitcoinsv.io | DSL Extreme | US | unknown |
2856 | ElectrumSV-1.1.0.exe | 185.194.143.218:50002 | sv.jochen-hoenicke.de | netcup GmbH | DE | malicious |
2856 | ElectrumSV-1.1.0.exe | 95.216.32.249:50002 | sv.satoshi.io | Hetzner Online GmbH | DE | malicious |
2856 | ElectrumSV-1.1.0.exe | 198.44.66.210:50002 | sv2.satoshi.io | Hostwinds LLC. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
electroncash.cascharia.com |
| unknown |
sv1.hsmiths.com |
| unknown |
sv.electrumx.cash |
| unknown |
satoshi.vision.cash |
| unknown |
electrumx-sv.1209k.com |
| unknown |
electrumsv.io |
| suspicious |
electron.bitcoinsv.io |
| unknown |
sv.jochen-hoenicke.de |
| malicious |
sv.satoshi.io |
| malicious |
sv2.satoshi.io |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | Not Suspicious Traffic | ET POLICY OpenSSL Demo CA - Internet Widgits Pty (O) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |
2856 | ElectrumSV-1.1.0.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklist Malicious SSL certificate detected (Trickbot) |