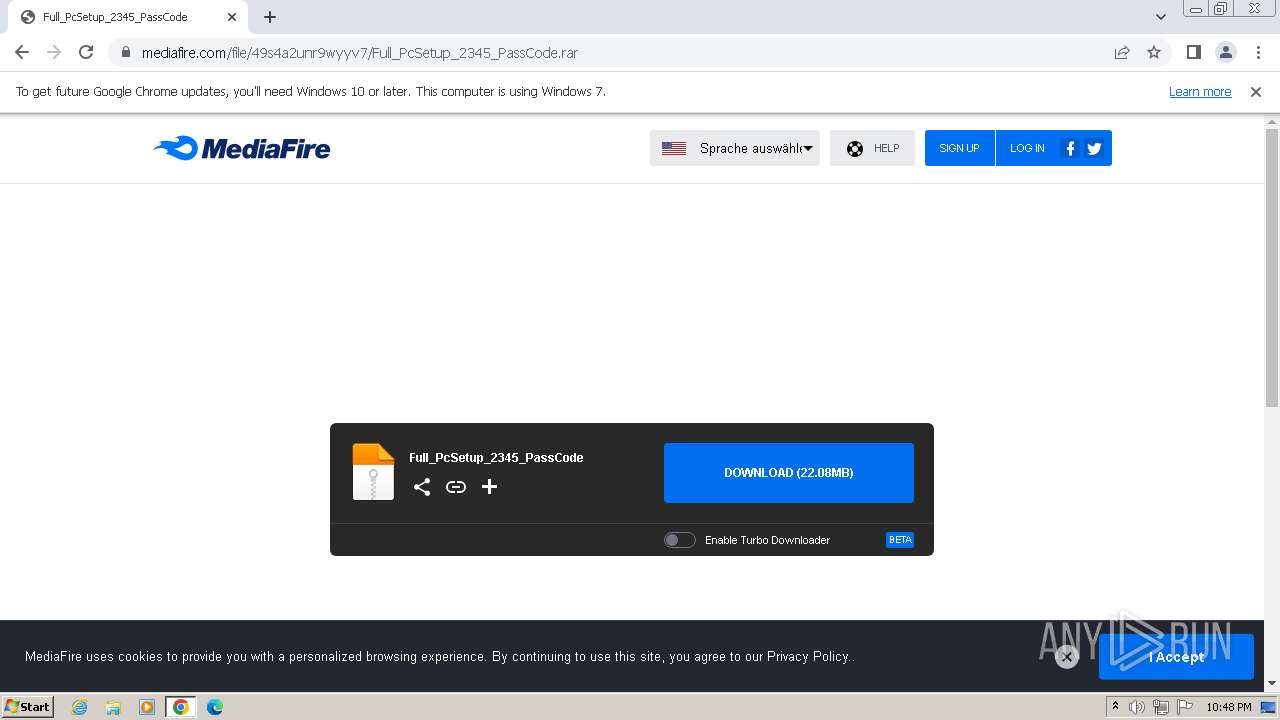
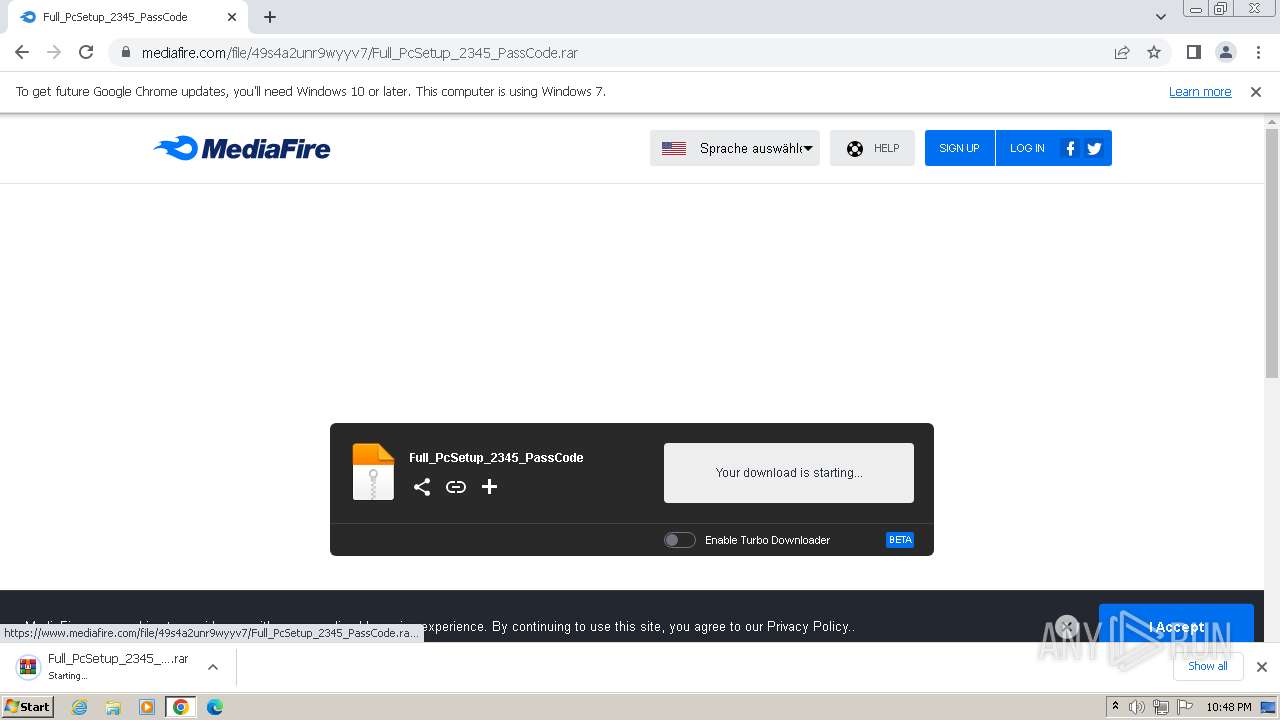
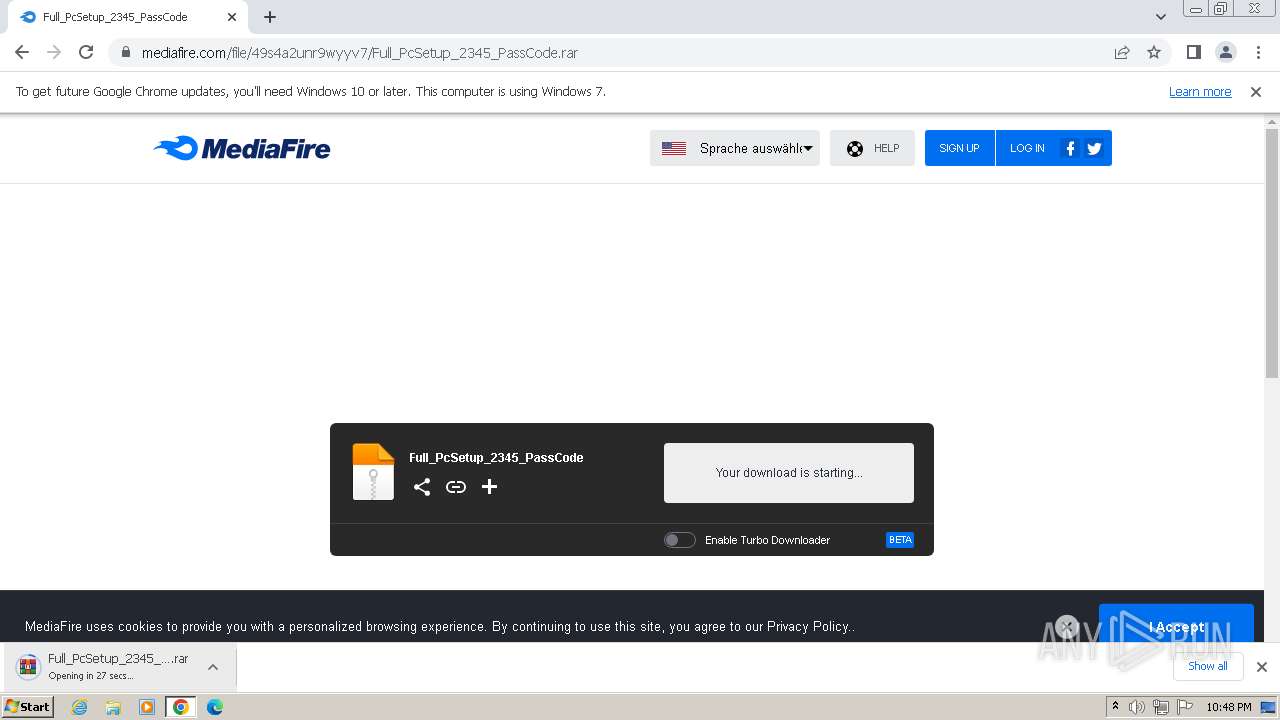
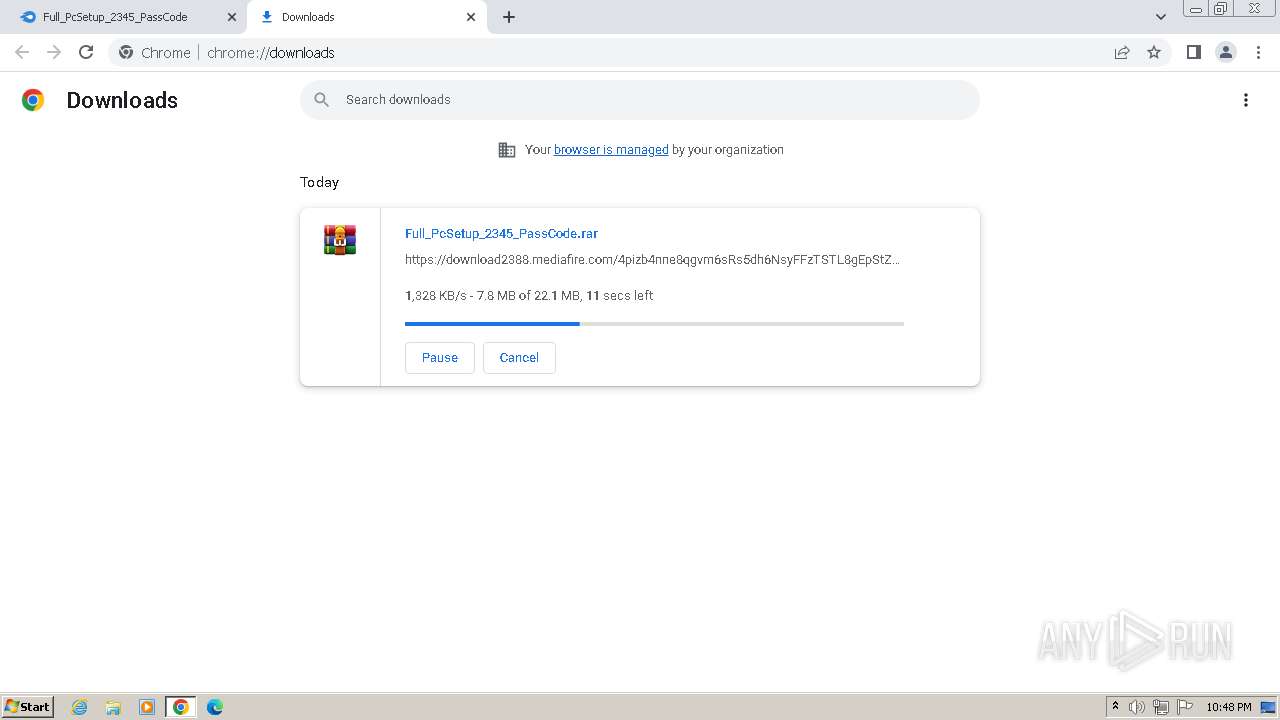
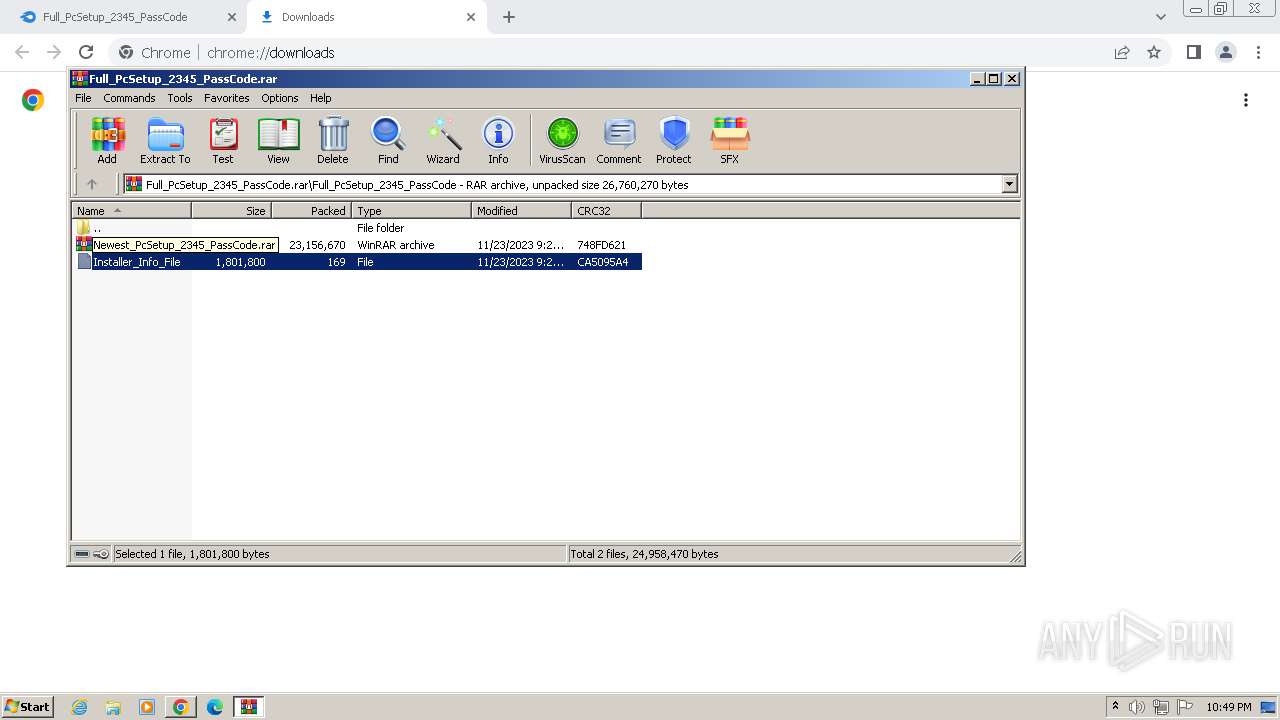
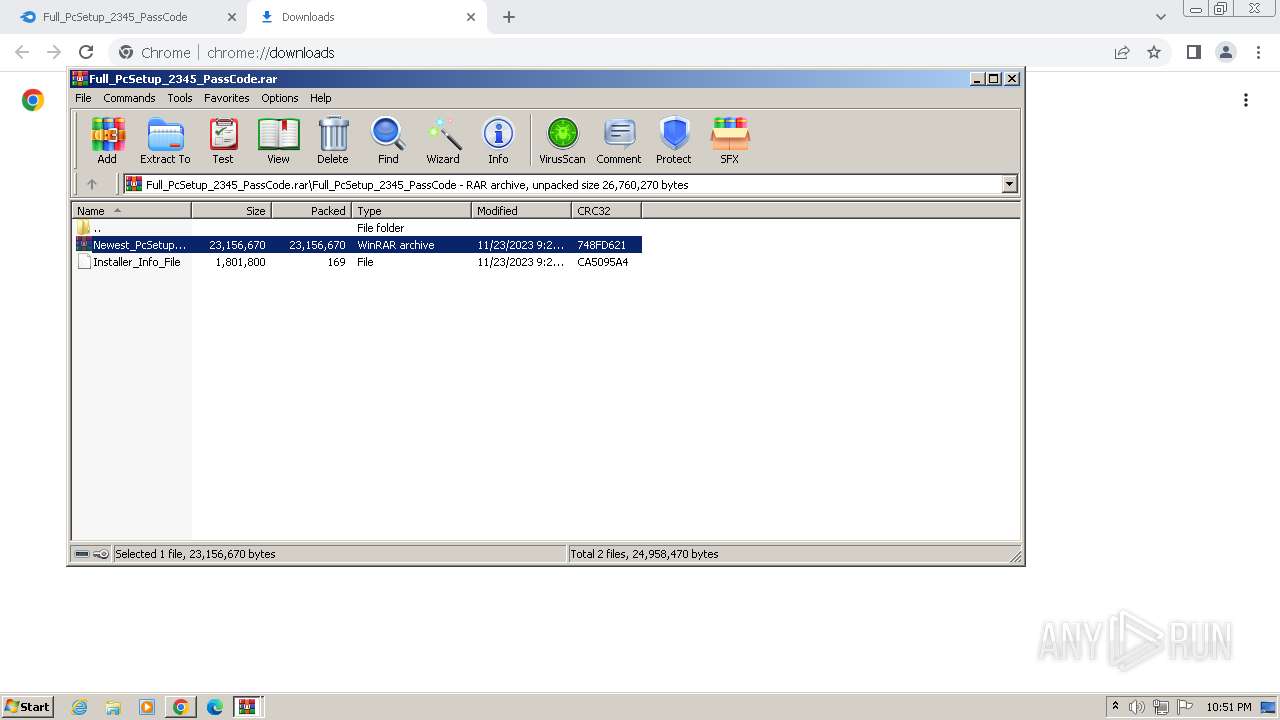
| URL: | https://download2388.mediafire.com/jrc1rht4hrqgQlG4s7PuKL-bO8zvAdqIcla0Yd7OIlJ9HKno2dsDJ7AL0obIf5lyhbqKkQYrNxYoKWcOU4oMzcGJVUmLwLaEl8u8cbtFOjoeVmia75OOLZoQJ1C47Wzw4LcPicWqtLD3qXsGxmPWzvU8ZTdMDzkHpXMVQbCtxD9jSw/49s4a2unr9wyyv7/Full_PcSetup_2345_PassCode.rar |
| Full analysis: | https://app.any.run/tasks/37cfc905-352e-4857-a9be-1359165ecc9d |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | November 23, 2023, 22:48:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| SHA1: | 8FC4424008E0D8D1A16186A13ED4724BEAEC9AC0 |
| SHA256: | 8BC28F3C1CC23C13D96A7F6F9B5530A4DA65B592AC79692B8A36E76CEEC5D50F |
| SSDEEP: | 6:2SWMxQeGmd9RQu6pAUvic+C8XpYVzCSeTH89cepMiuQT61h0AX/c2j+:2tMxQeD0u6FeC8ZYZ2TH+xT8T/cr |
MALICIOUS
LUMMA has been detected (SURICATA)
- Installer.exe (PID: 788)
Connects to the CnC server
- Installer.exe (PID: 788)
- RegAsm.exe (PID: 2960)
Drops the executable file immediately after the start
- Installer.exe (PID: 788)
- empgcinijanpowdr.exe (PID: 3172)
- Utsysc.exe (PID: 3664)
- hv.exe (PID: 3732)
- olkcjvbcvt.exe (PID: 3456)
Actions looks like stealing of personal data
- Installer.exe (PID: 788)
- RegAsm.exe (PID: 2960)
Changes the autorun value in the registry
- Utsysc.exe (PID: 3664)
Uses Task Scheduler to run other applications
- Utsysc.exe (PID: 3664)
- XRJNZC.exe (PID: 3088)
AMADEY has been detected (SURICATA)
- Utsysc.exe (PID: 3664)
ARECHCLIENT2 has been detected (SURICATA)
- RegAsm.exe (PID: 2960)
SUSPICIOUS
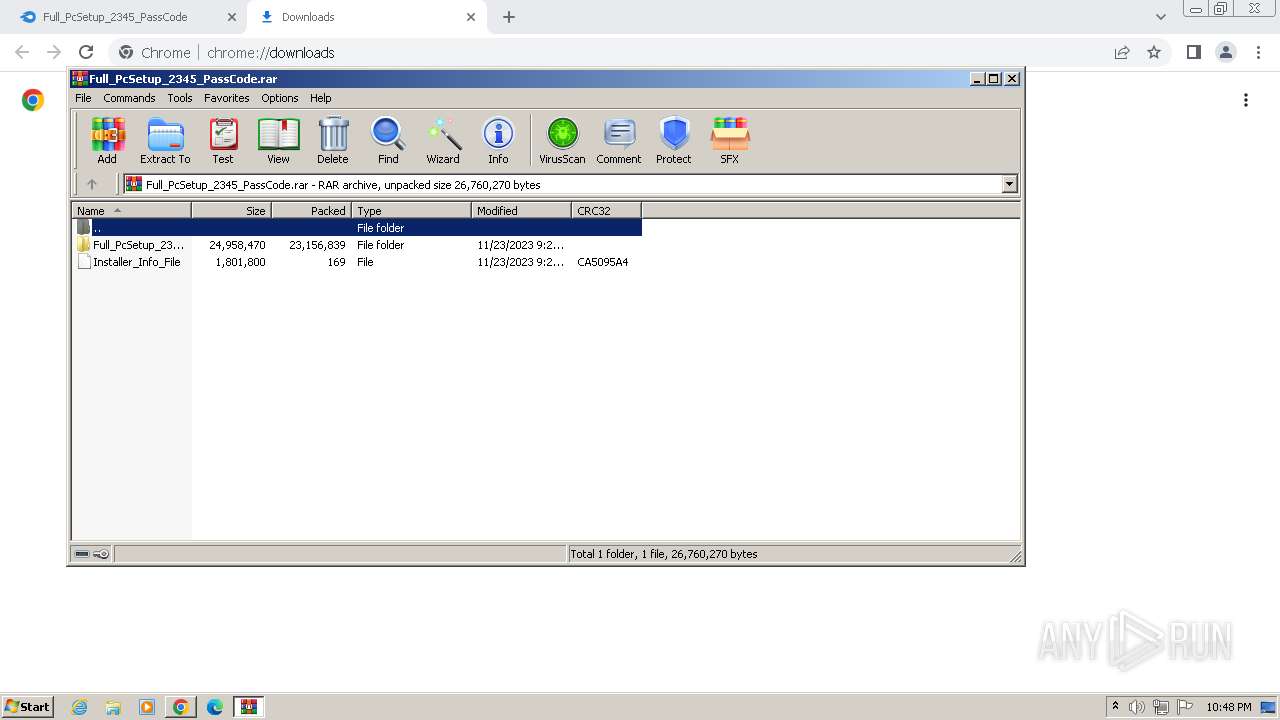
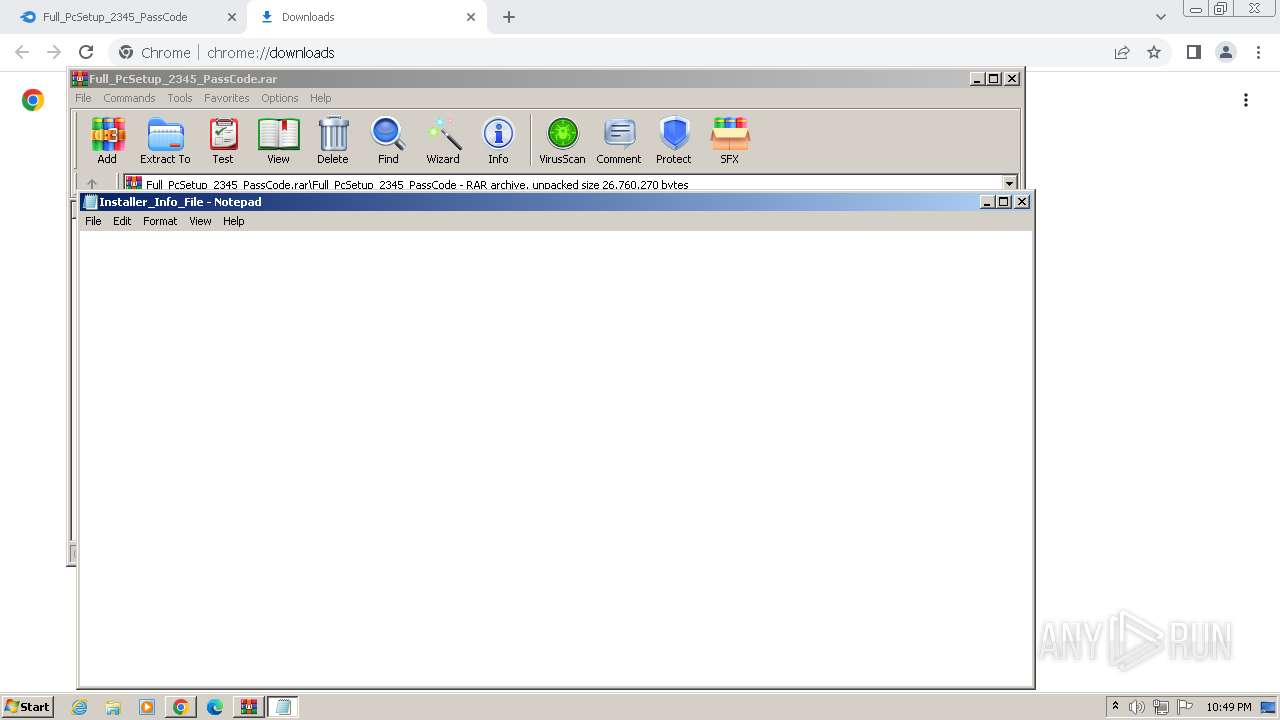
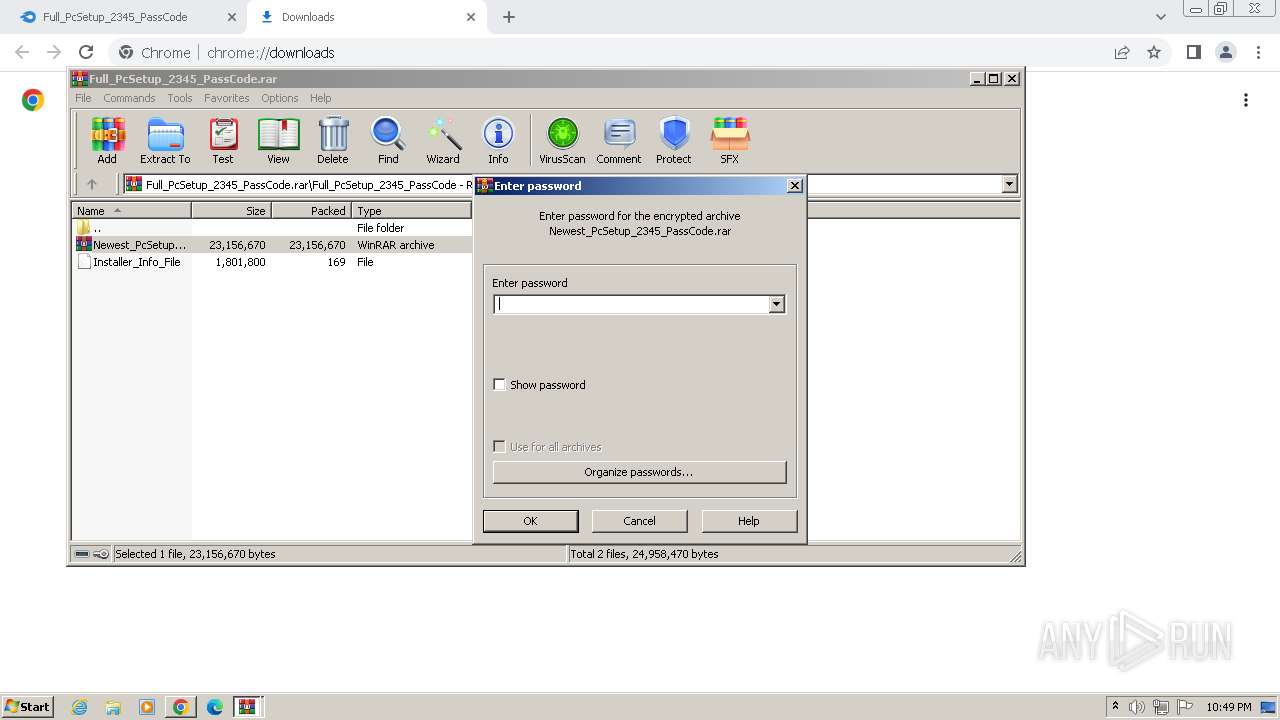
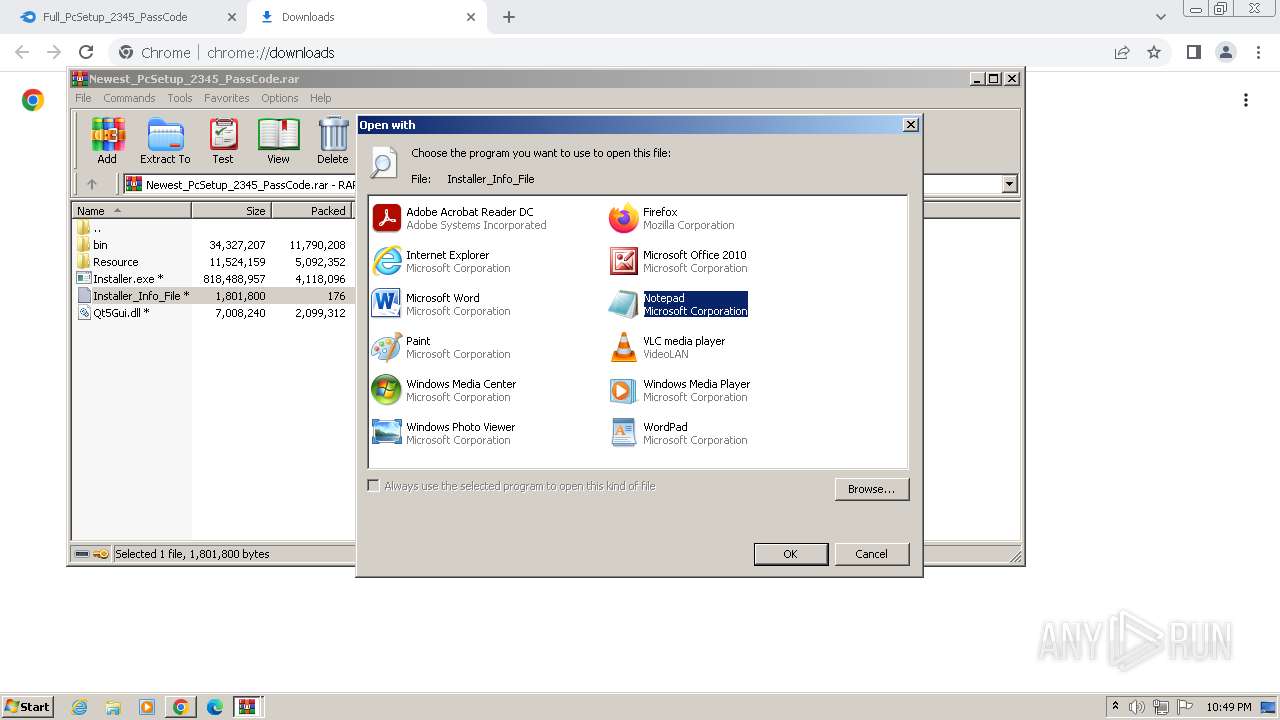
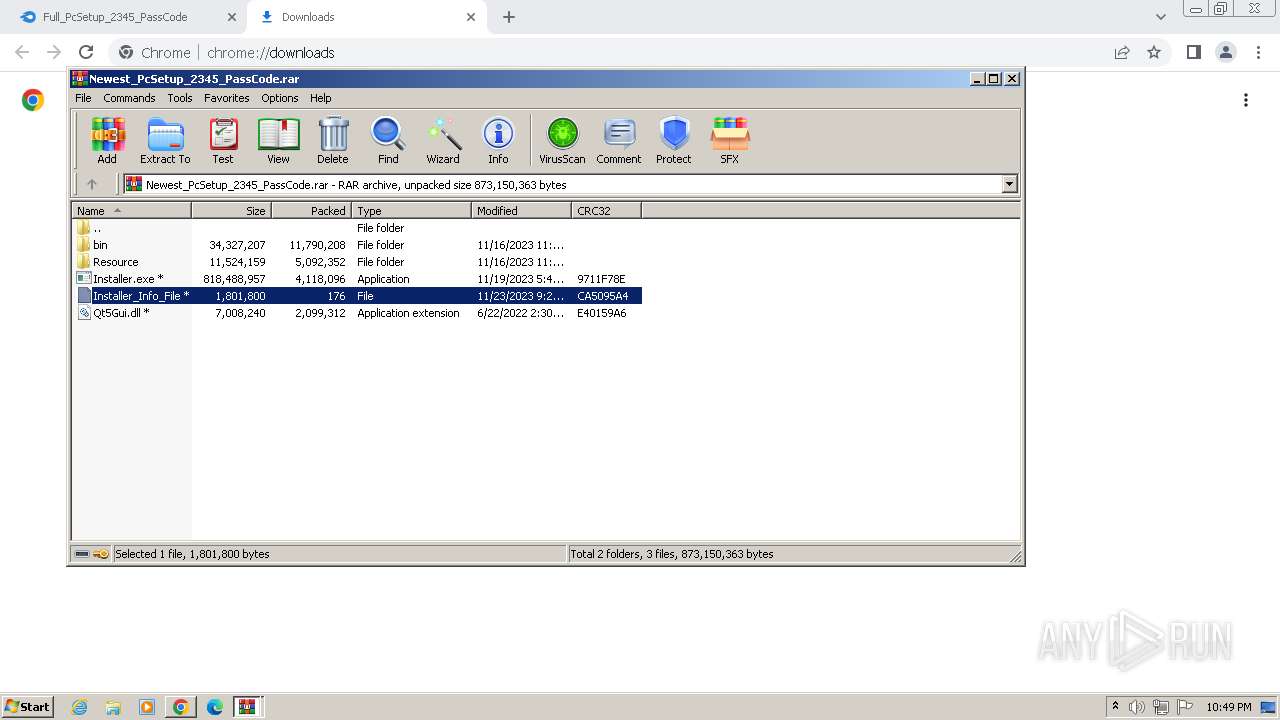
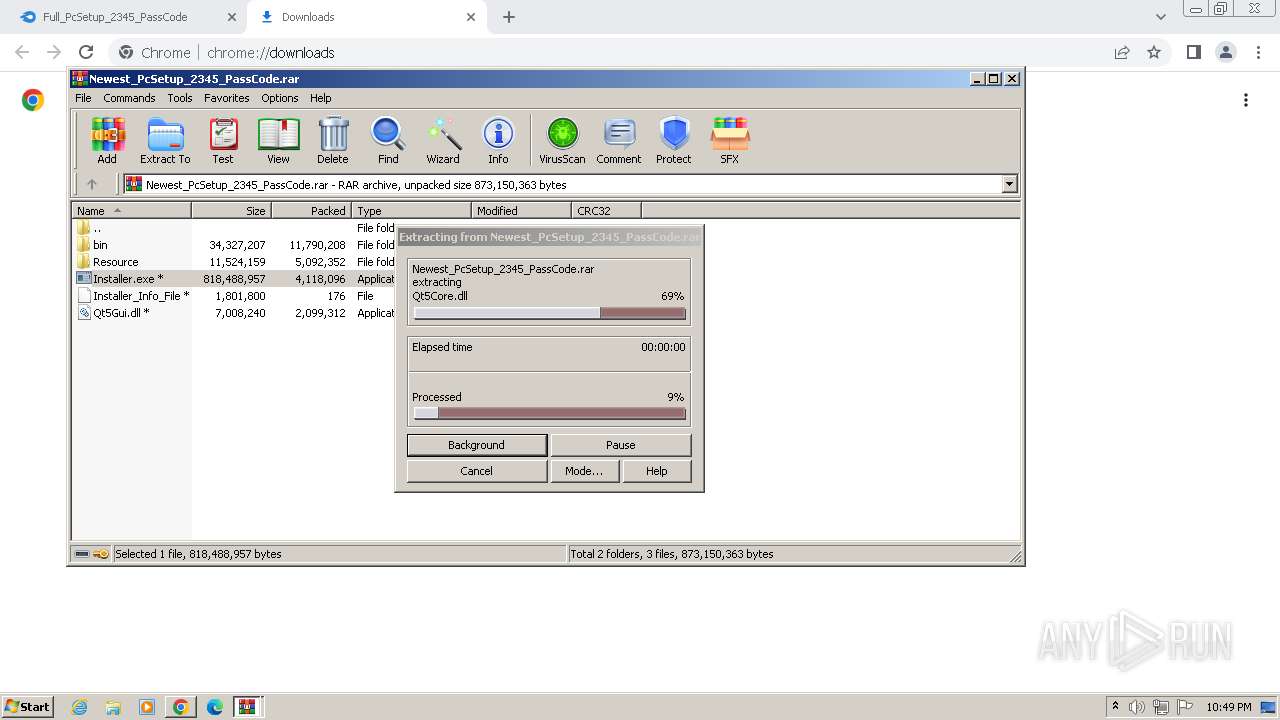
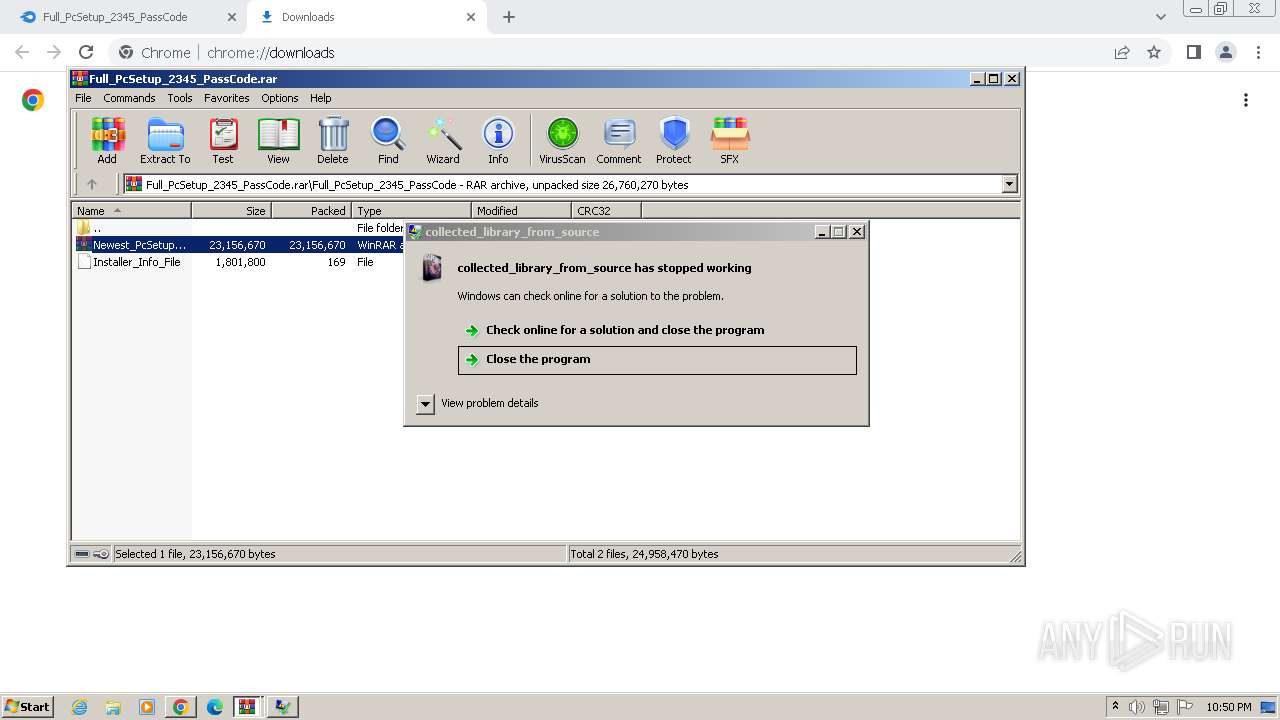
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3896)
- WinRAR.exe (PID: 3336)
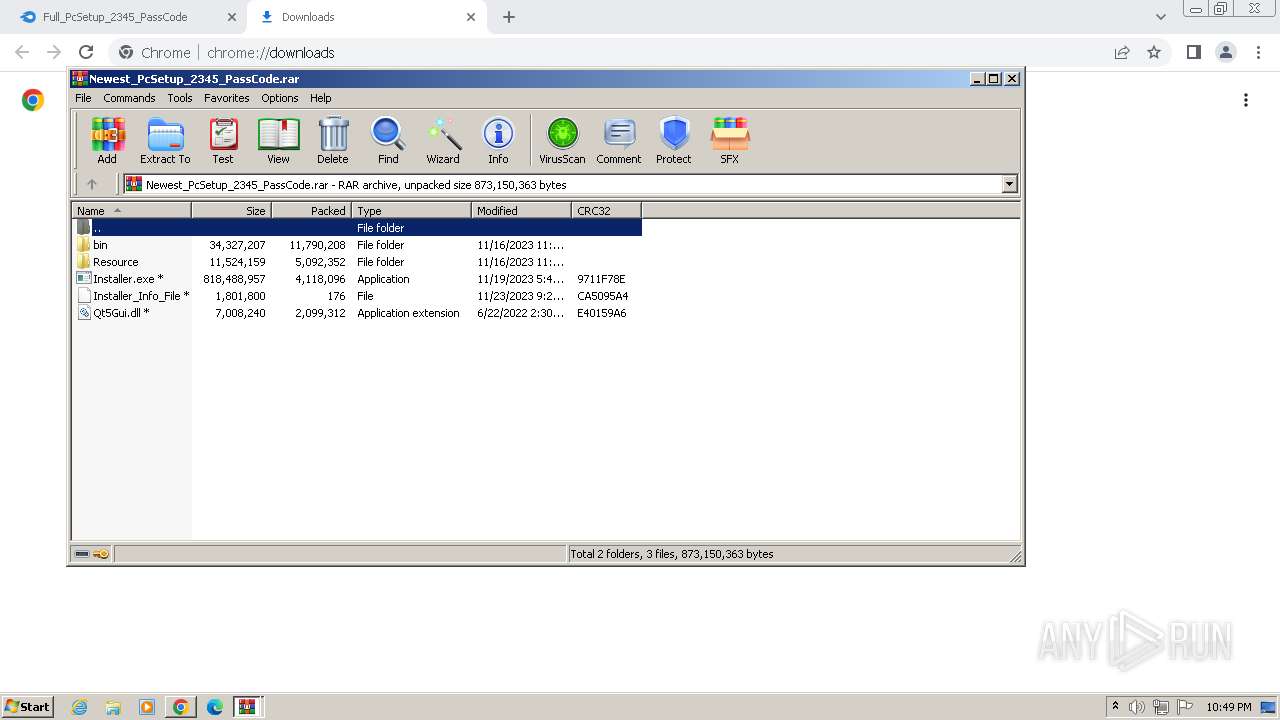
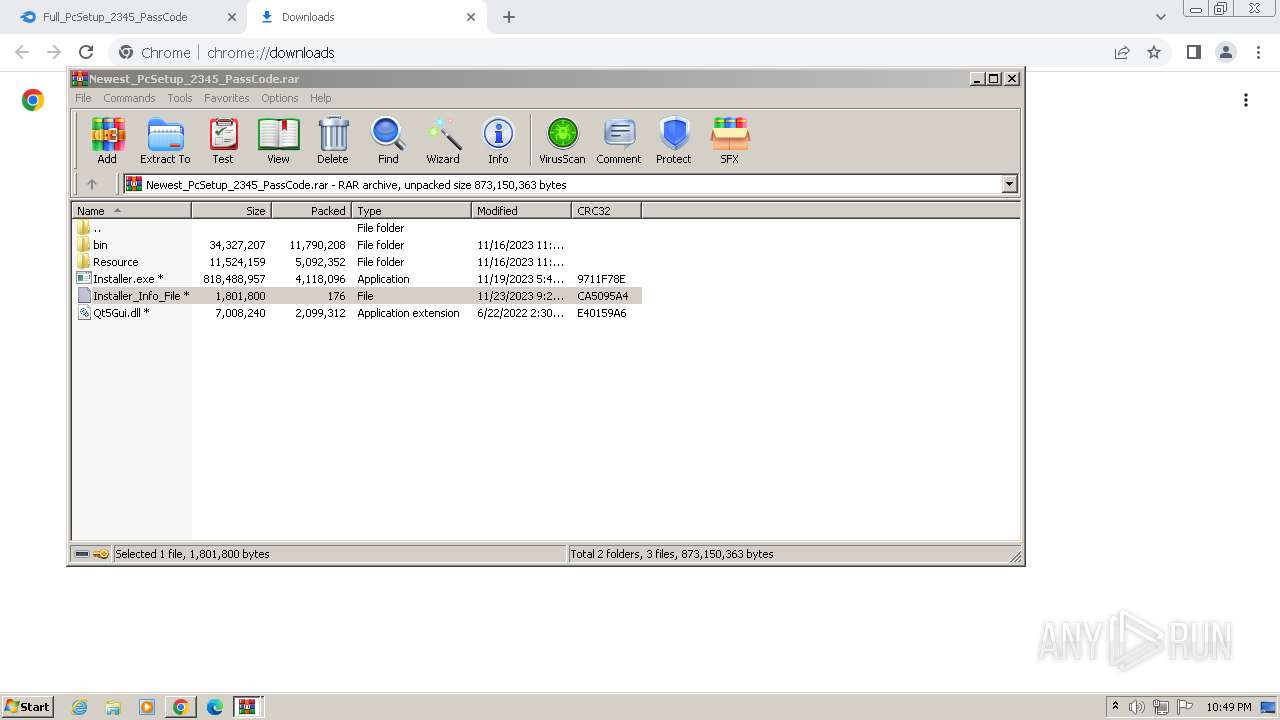
The process creates files with name similar to system file names
- WinRAR.exe (PID: 3896)
Reads the Internet Settings
- rundll32.exe (PID: 3800)
- rundll32.exe (PID: 2316)
- Installer.exe (PID: 788)
- empgcinijanpowdr.exe (PID: 3172)
- rundll32.exe (PID: 2224)
- olkcjvbcvt.exe (PID: 3456)
- Utsysc.exe (PID: 3664)
- rundll32.exe (PID: 2828)
- XRJNZC.exe (PID: 3088)
Process drops legitimate windows executable
- WinRAR.exe (PID: 3896)
Connects to the server without a host name
- Installer.exe (PID: 788)
- Utsysc.exe (PID: 3664)
Process requests binary or script from the Internet
- Installer.exe (PID: 788)
- Utsysc.exe (PID: 3664)
Reads browser cookies
- Installer.exe (PID: 788)
- RegAsm.exe (PID: 2960)
Searches for installed software
- Installer.exe (PID: 788)
- RegAsm.exe (PID: 2960)
Starts itself from another location
- empgcinijanpowdr.exe (PID: 3172)
Reads the BIOS version
- olkcjvbcvt.exe (PID: 3456)
- XRJNZC.exe (PID: 3088)
- XRJNZC.exe (PID: 188)
Application launched itself
- WinRAR.exe (PID: 3336)
Starts CMD.EXE for commands execution
- olkcjvbcvt.exe (PID: 3456)
Executing commands from a ".bat" file
- olkcjvbcvt.exe (PID: 3456)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 4020)
Connects to unusual port
- RegAsm.exe (PID: 2960)
The process executes via Task Scheduler
- XRJNZC.exe (PID: 188)
- Utsysc.exe (PID: 1644)
INFO
Reads the computer name
- wmpnscfg.exe (PID: 3996)
- Installer.exe (PID: 788)
- empgcinijanpowdr.exe (PID: 3172)
- olkcjvbcvt.exe (PID: 3456)
- Utsysc.exe (PID: 3664)
- hv.exe (PID: 3732)
- XRJNZC.exe (PID: 3088)
- RegAsm.exe (PID: 2960)
Application launched itself
- chrome.exe (PID: 564)
Manual execution by a user
- wmpnscfg.exe (PID: 3996)
Checks supported languages
- wmpnscfg.exe (PID: 3996)
- Installer.exe (PID: 788)
- olkcjvbcvt.exe (PID: 3456)
- empgcinijanpowdr.exe (PID: 3172)
- Utsysc.exe (PID: 3664)
- XRJNZC.exe (PID: 3088)
- hv.exe (PID: 3732)
- RegAsm.exe (PID: 2960)
- Utsysc.exe (PID: 1644)
- XRJNZC.exe (PID: 188)
Drops the executable file immediately after the start
- chrome.exe (PID: 564)
- chrome.exe (PID: 4004)
- WinRAR.exe (PID: 3896)
The process uses the downloaded file
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2892)
- WinRAR.exe (PID: 3336)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 3304)
Checks proxy server information
- Installer.exe (PID: 788)
- Utsysc.exe (PID: 3664)
Reads the machine GUID from the registry
- Installer.exe (PID: 788)
- empgcinijanpowdr.exe (PID: 3172)
- wmpnscfg.exe (PID: 3996)
- Utsysc.exe (PID: 3664)
- hv.exe (PID: 3732)
- RegAsm.exe (PID: 2960)
Create files in a temporary directory
- Installer.exe (PID: 788)
- empgcinijanpowdr.exe (PID: 3172)
- olkcjvbcvt.exe (PID: 3456)
- Utsysc.exe (PID: 3664)
- hv.exe (PID: 3732)
- RegAsm.exe (PID: 2960)
Creates files in the program directory
- olkcjvbcvt.exe (PID: 3456)
Creates files or folders in the user directory
- Utsysc.exe (PID: 3664)
Reads Environment values
- RegAsm.exe (PID: 2960)
Reads product name
- RegAsm.exe (PID: 2960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
96
Monitored processes
52
Malicious processes
9
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
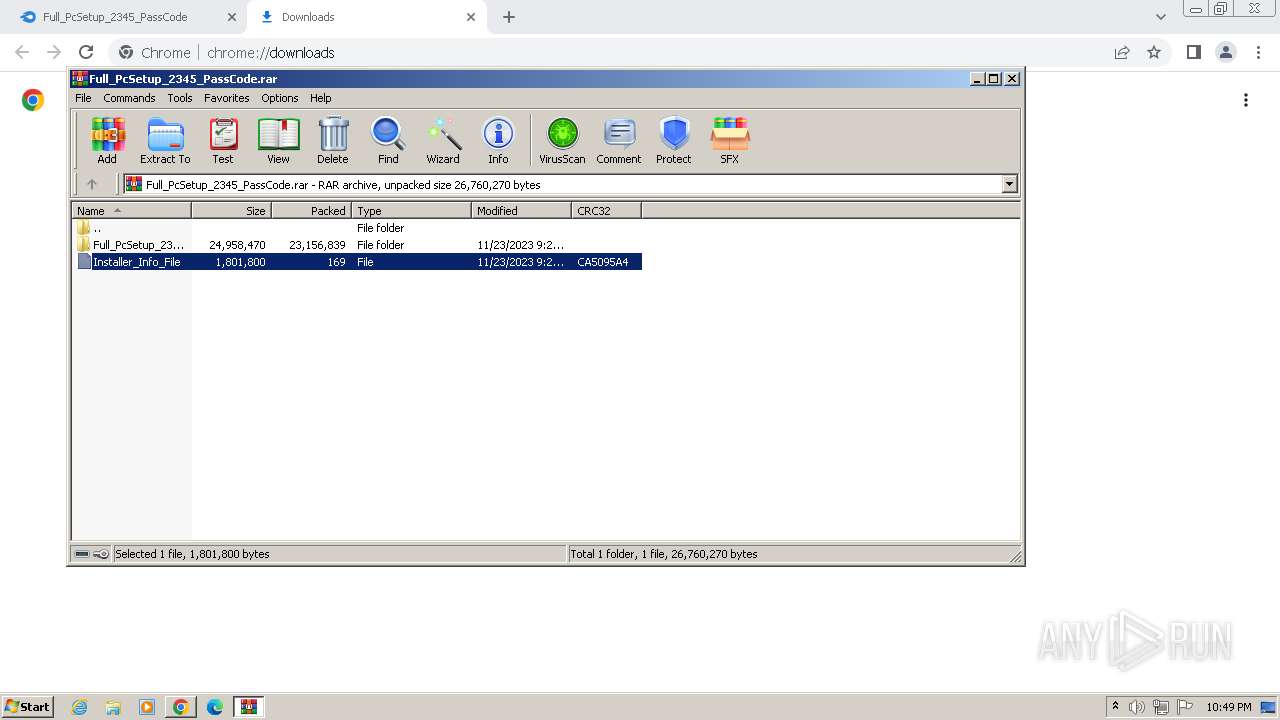
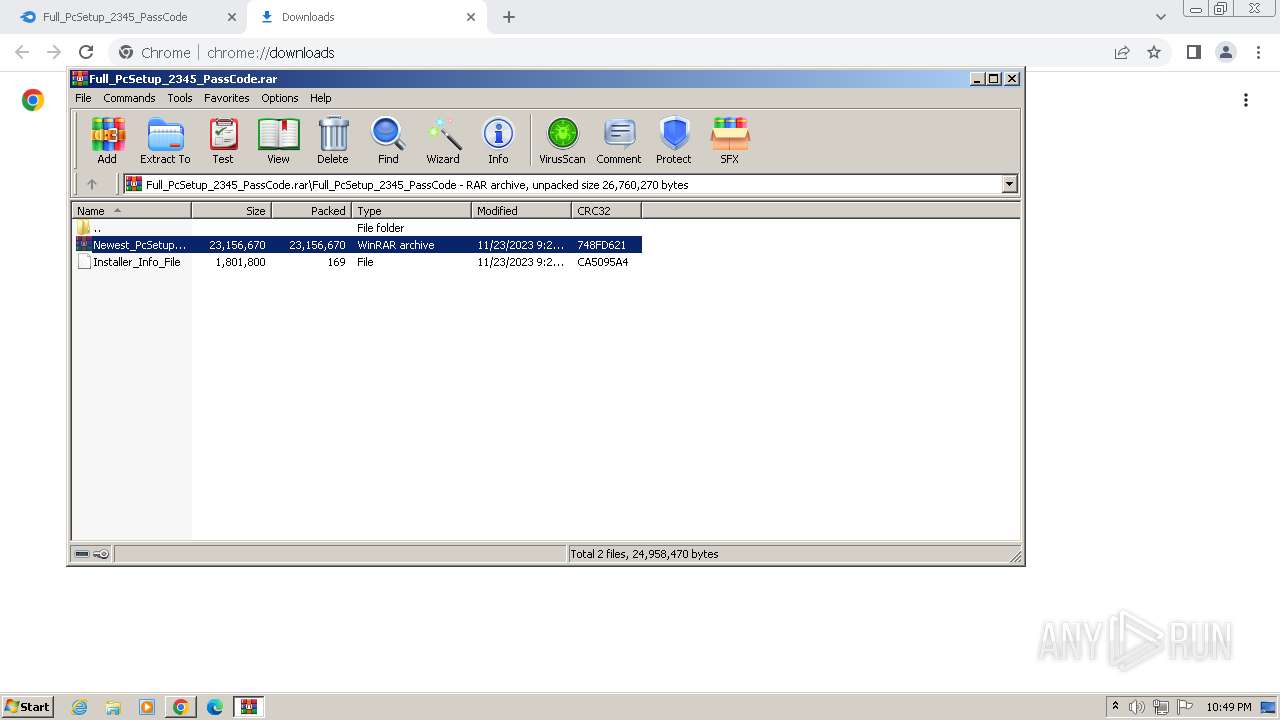
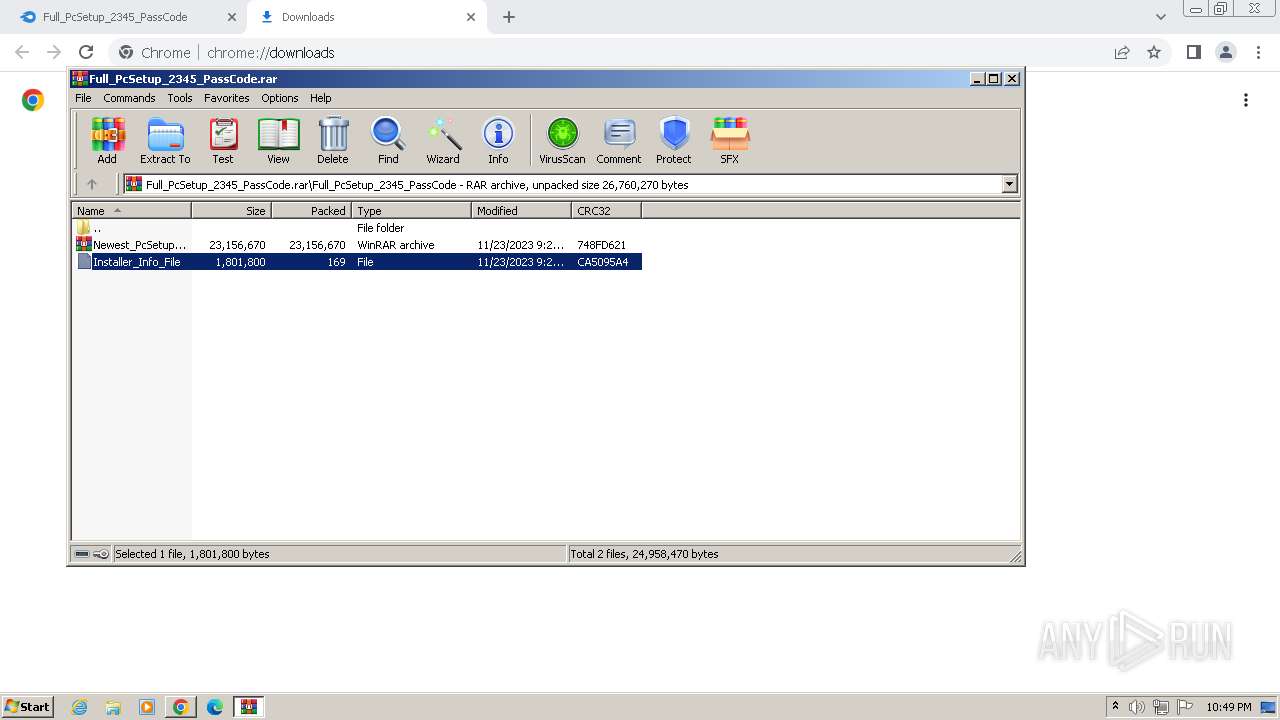
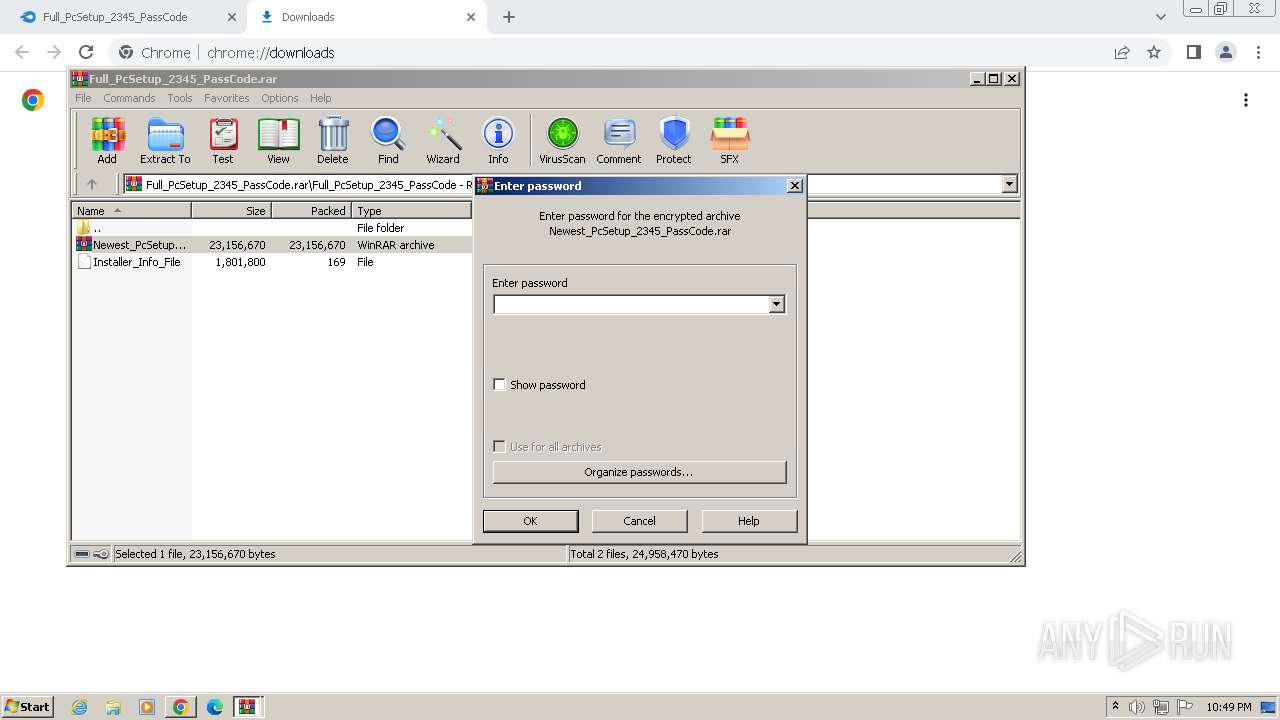
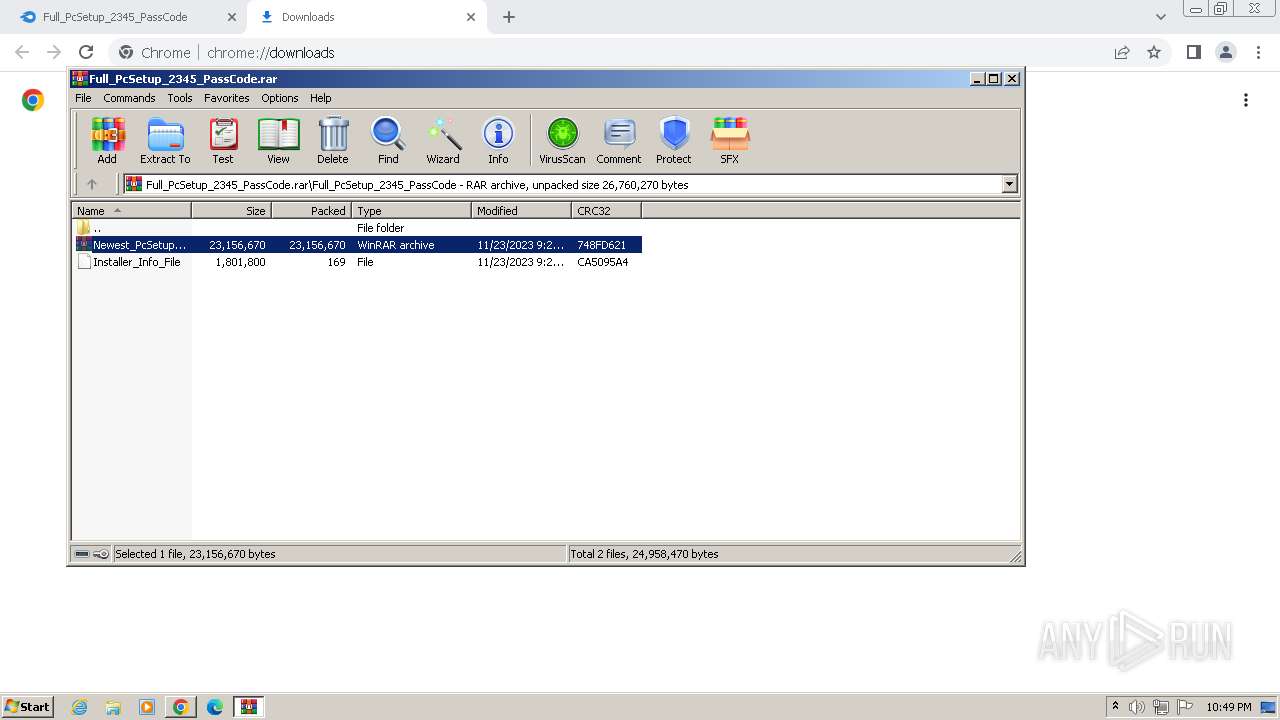
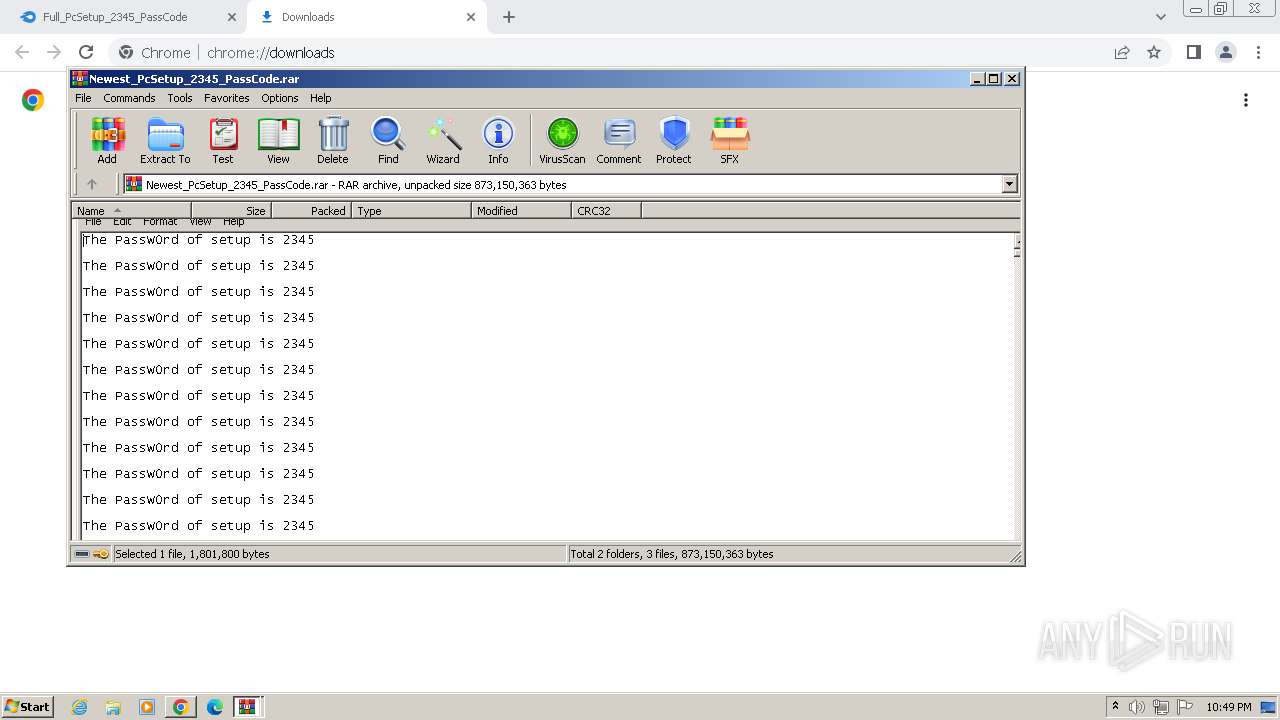
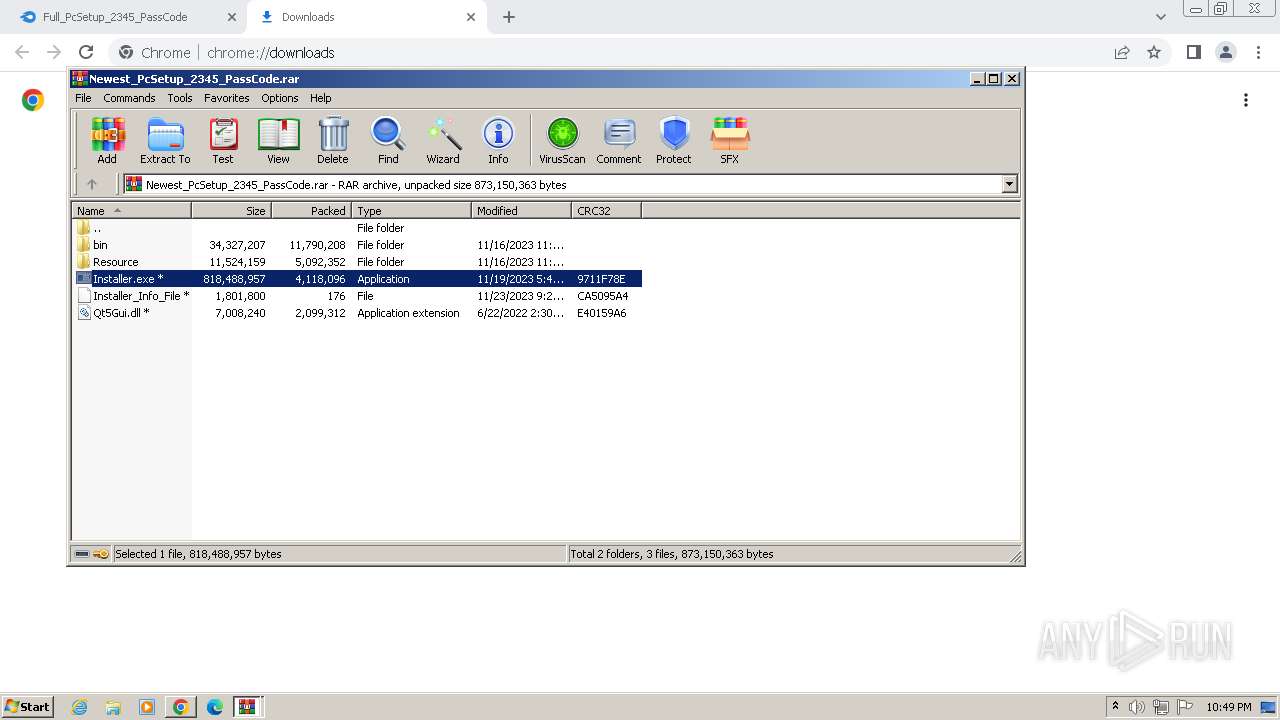
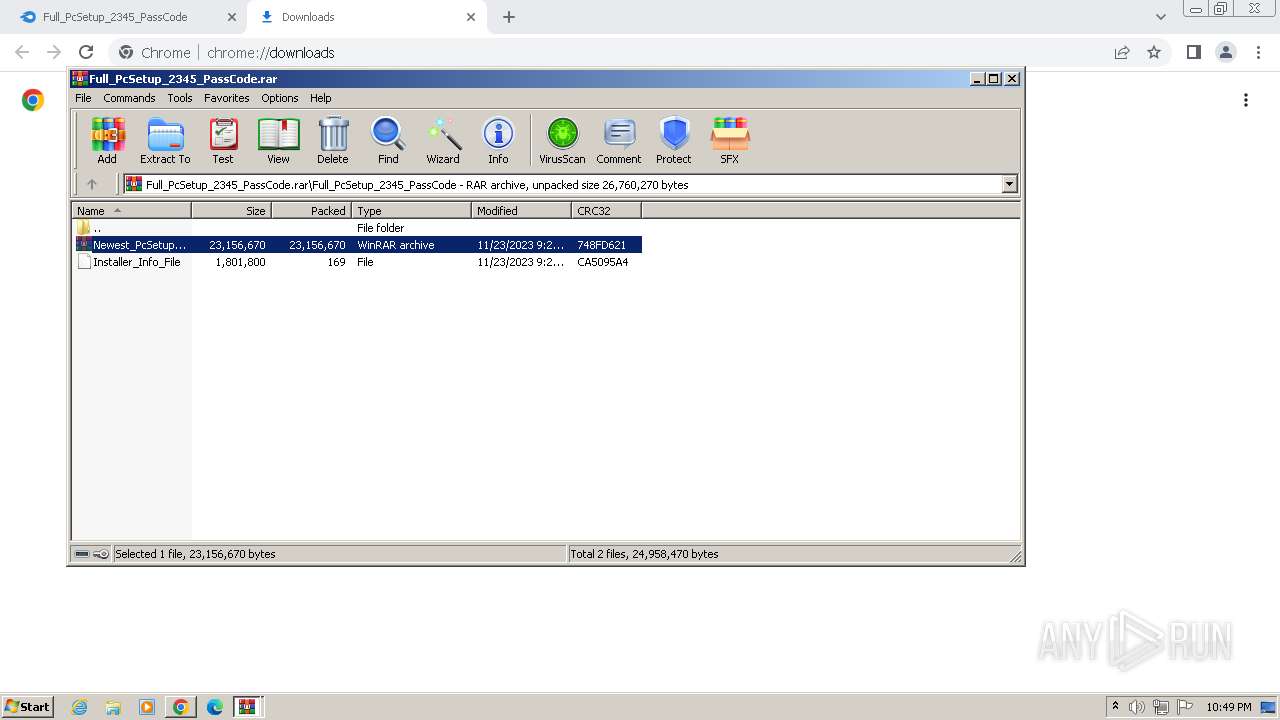
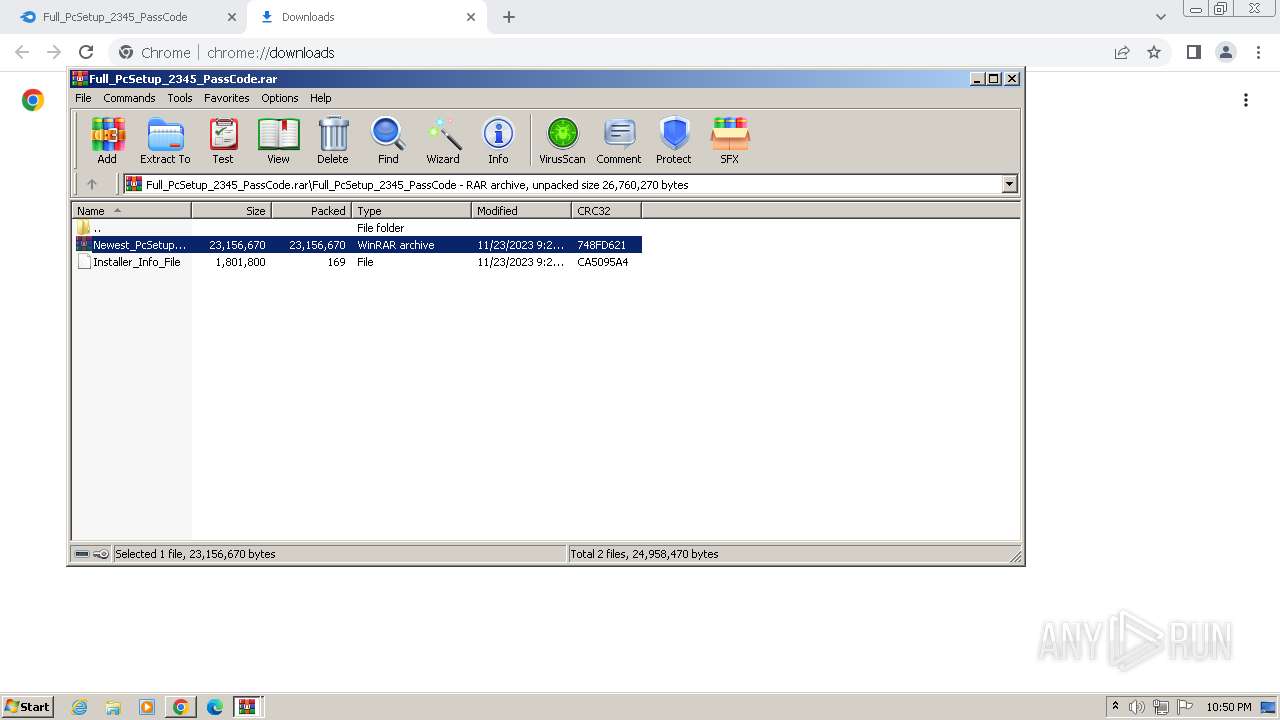
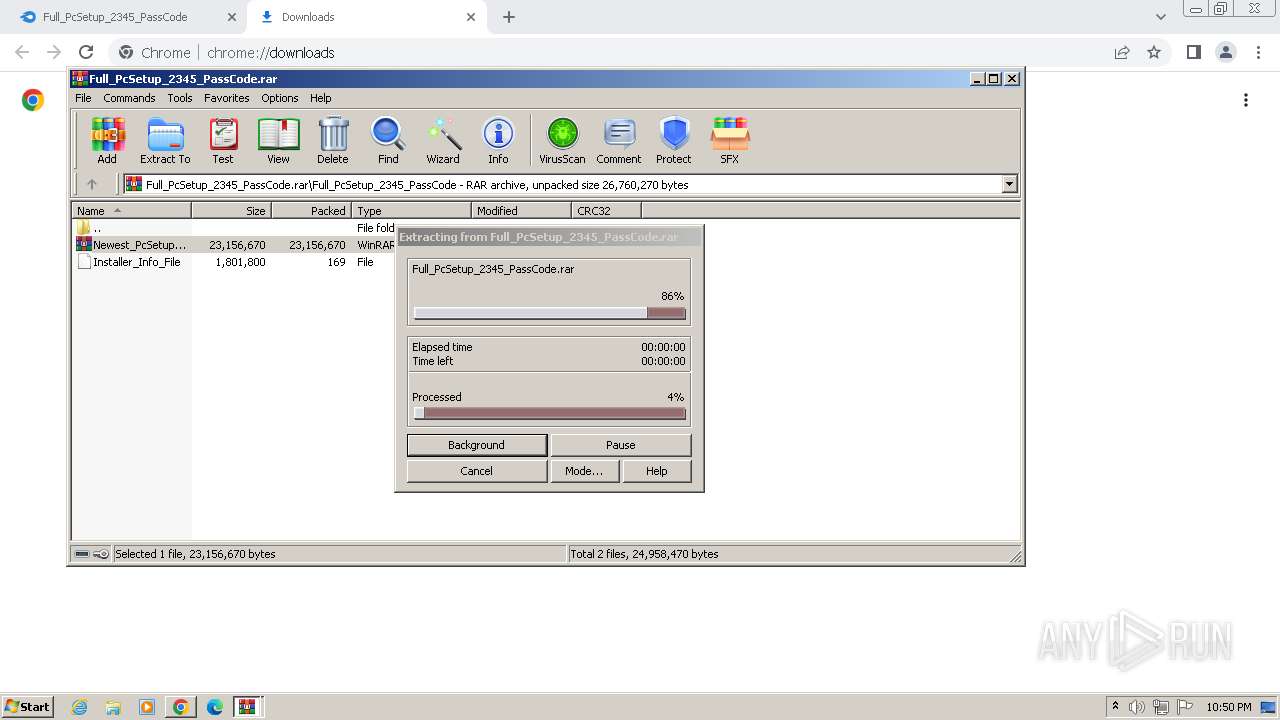
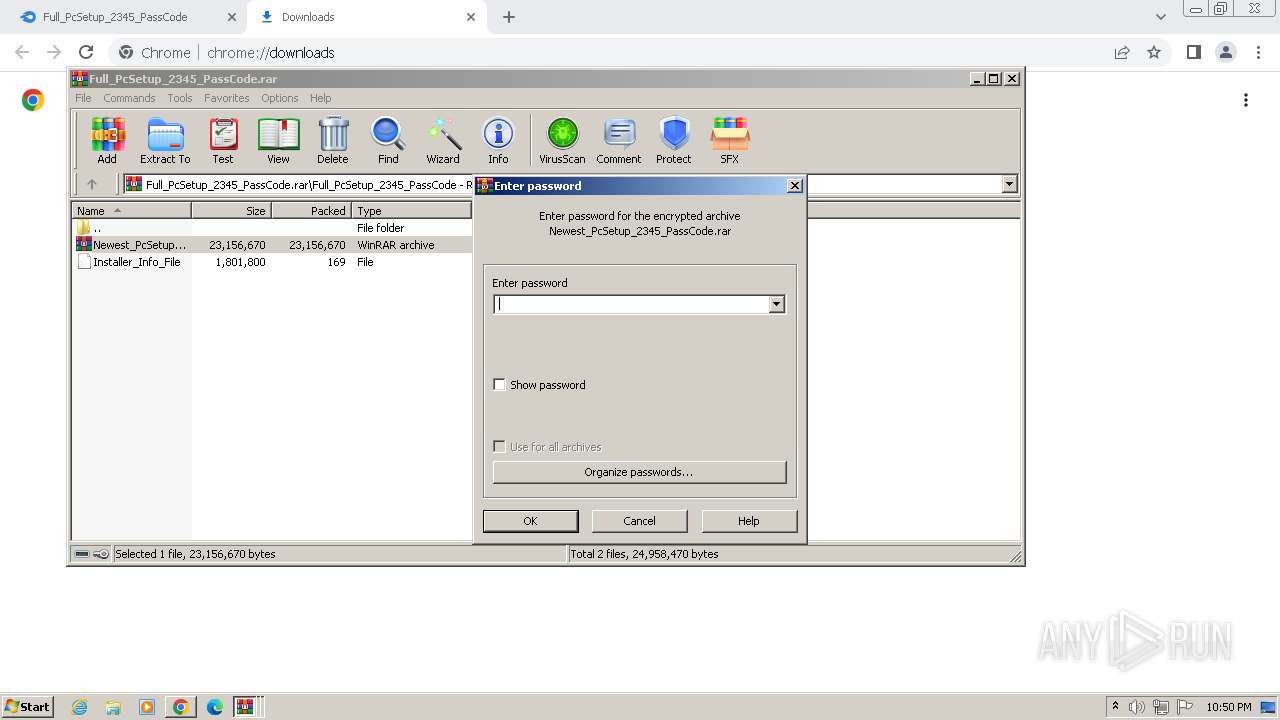
| 124 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3336.23329\Newest_PcSetup_2345_PassCode.rar | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 188 | C:\ProgramData\pinterests\XRJNZC.exe | C:\ProgramData\pinterests\XRJNZC.exe | — | taskeng.exe | |||||||||||
User: admin Company: Schneider Electric Software, LLC. Integrity Level: MEDIUM Description: InTouch WindowMaker Exit code: 0 Version: 2400.0852.0527.0052 Modules
| |||||||||||||||
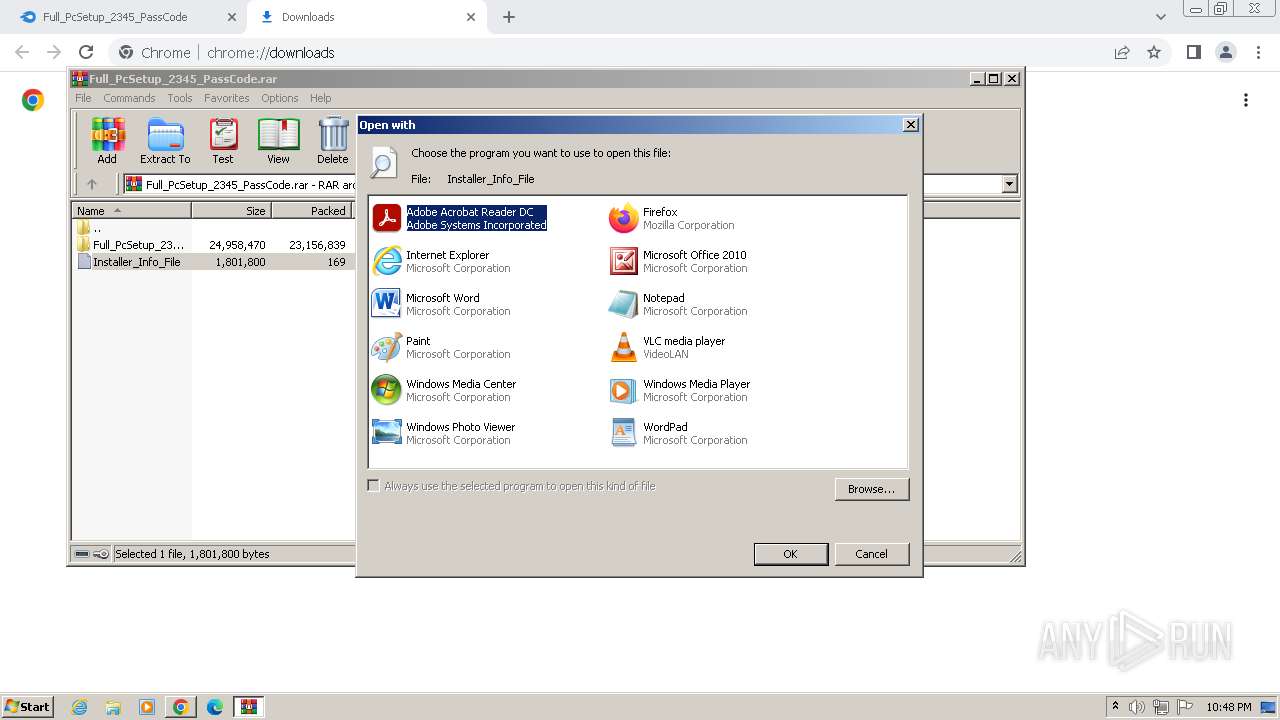
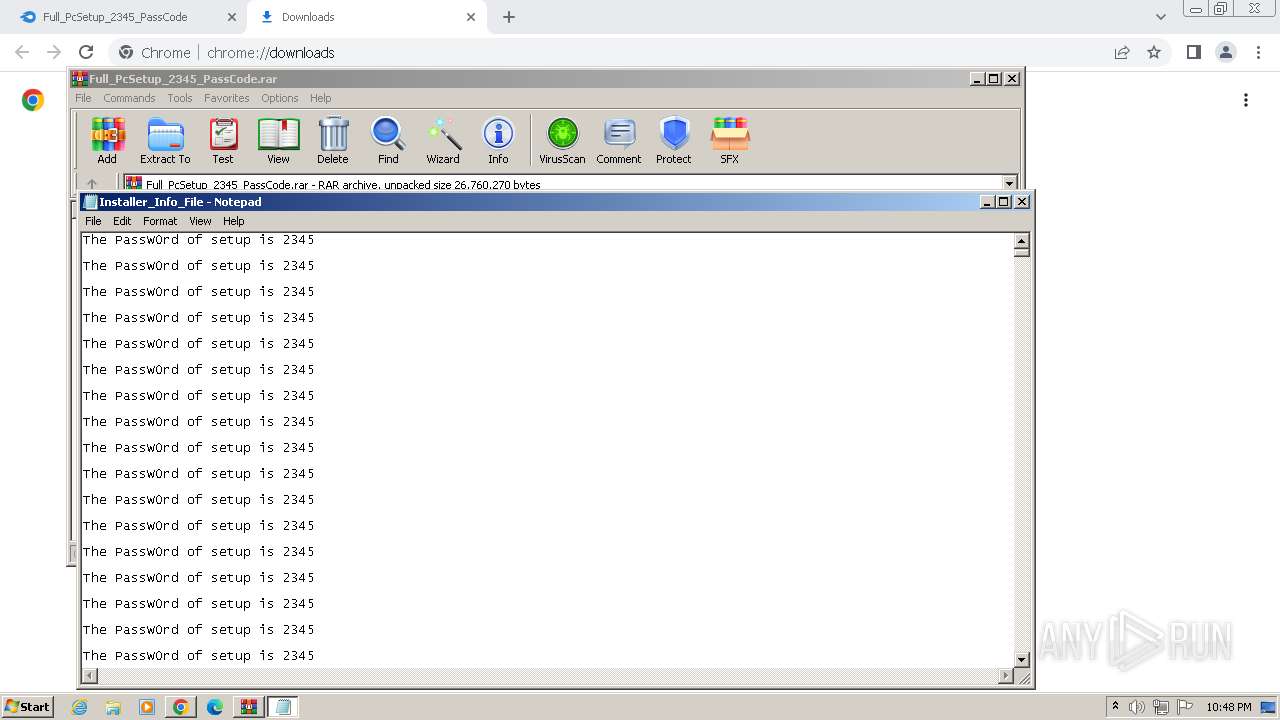
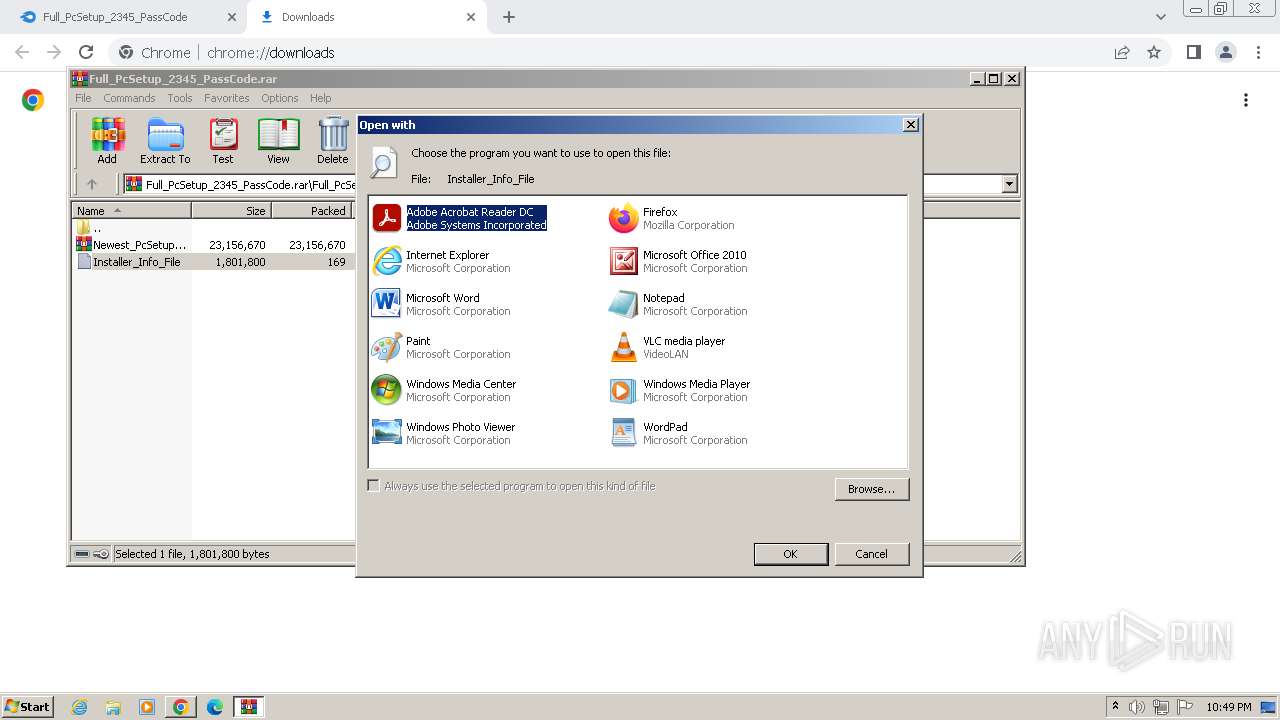
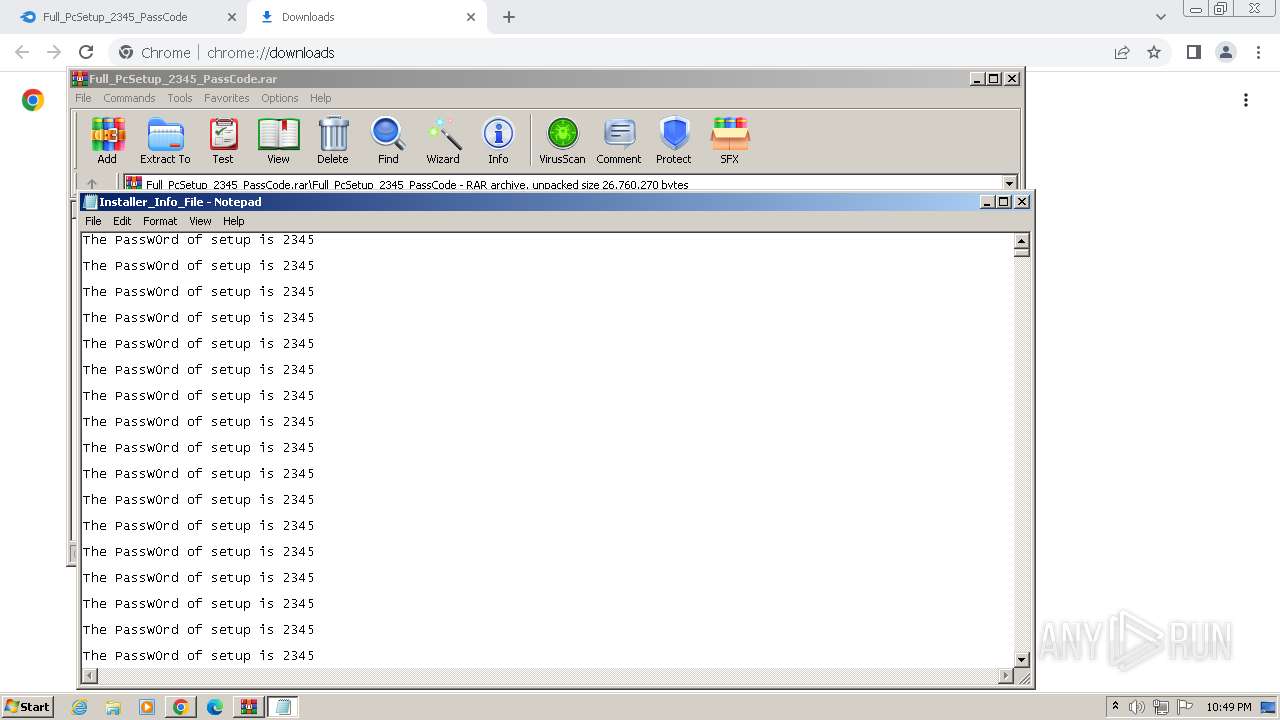
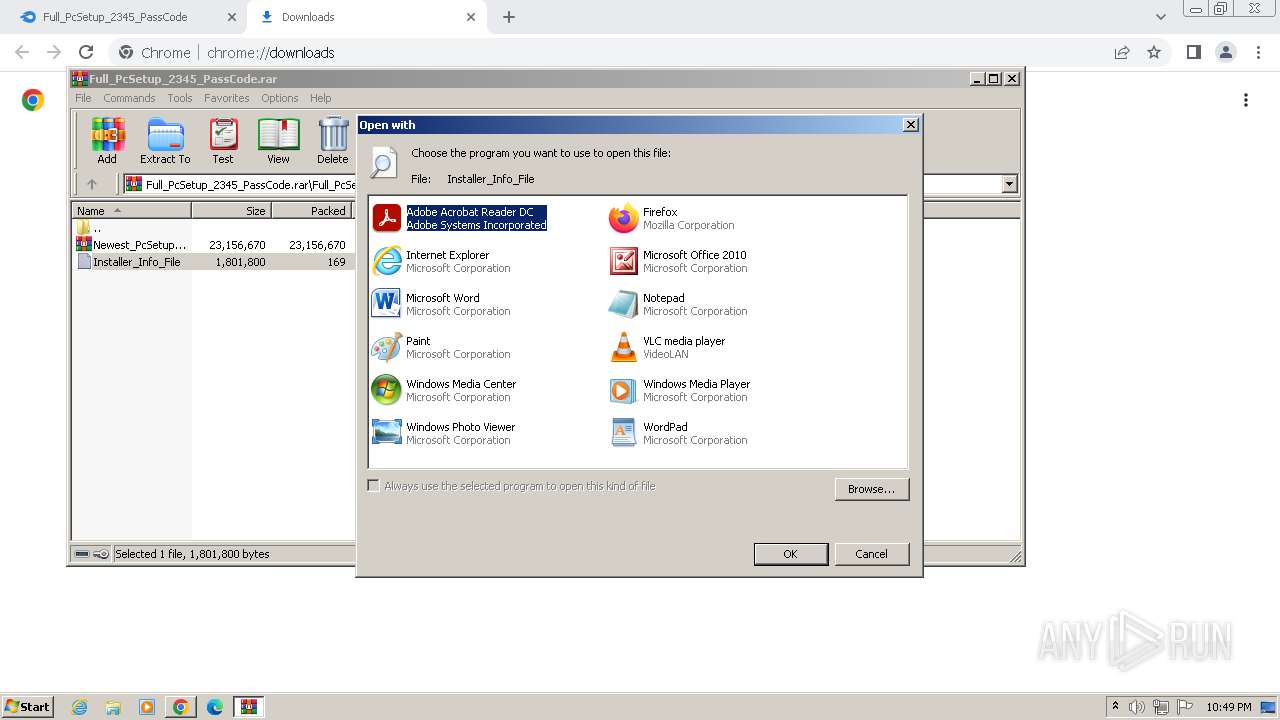
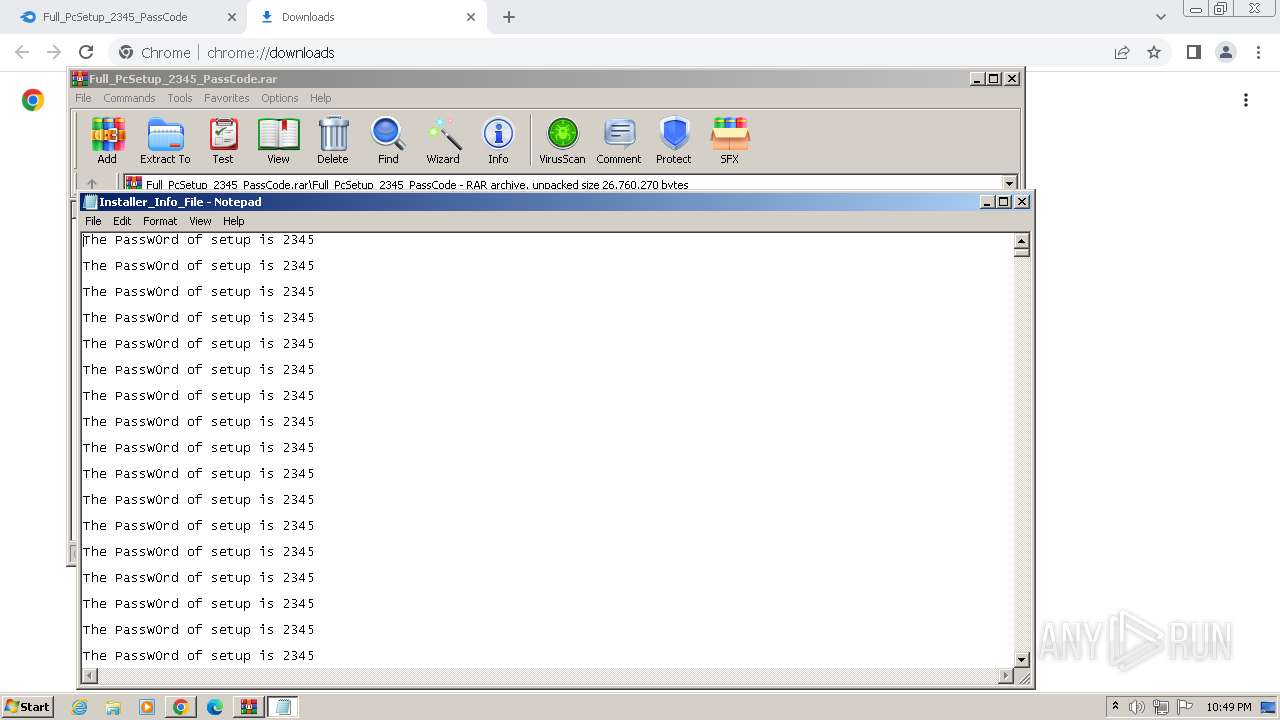
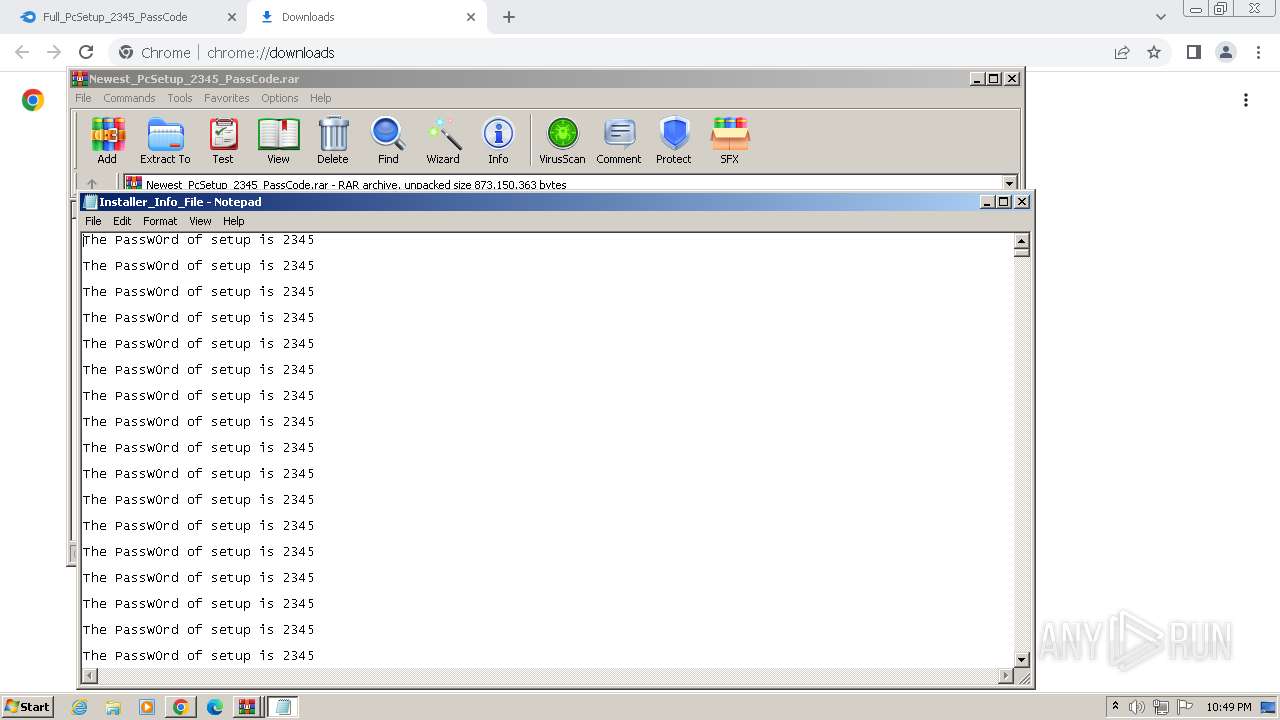
| 296 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3336.21719\Installer_Info_File | C:\Windows\System32\notepad.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://download2388.mediafire.com/jrc1rht4hrqgQlG4s7PuKL-bO8zvAdqIcla0Yd7OIlJ9HKno2dsDJ7AL0obIf5lyhbqKkQYrNxYoKWcOU4oMzcGJVUmLwLaEl8u8cbtFOjoeVmia75OOLZoQJ1C47Wzw4LcPicWqtLD3qXsGxmPWzvU8ZTdMDzkHpXMVQbCtxD9jSw/49s4a2unr9wyyv7/Full_PcSetup_2345_PassCode.rar" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 788 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3896.26201\Installer.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3896.26201\Installer.exe | WinRAR.exe | ||||||||||||
User: admin Company: QlikTech International AB Integrity Level: MEDIUM Description: QvConnect 12.20.20700+2018-06-19 08:55:15+e2a0a63 Exit code: 0 Version: 12.20.20700+2018-06-19 08:55:15+e2a0a63 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2004 --field-trial-handle=1144,i,17433164948982121155,1587711916167220802,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3856 --field-trial-handle=1144,i,17433164948982121155,1587711916167220802,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1644 | C:\Users\admin\AppData\Local\Temp\b64c58644b\Utsysc.exe | C:\Users\admin\AppData\Local\Temp\b64c58644b\Utsysc.exe | — | taskeng.exe | |||||||||||
User: admin Company: Schneider Electric Software, LLC. Integrity Level: MEDIUM Description: InTouch WindowMaker Exit code: 0 Version: 2400.0852.0527.0052 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1112 --field-trial-handle=1144,i,17433164948982121155,1587711916167220802,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=2556 --field-trial-handle=1144,i,17433164948982121155,1587711916167220802,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
20 522
Read events
20 014
Write events
505
Delete events
3
Modification events
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
127
Suspicious files
172
Text files
144
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1bdd7b.TMP | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1bdd9b.TMP | text | |
MD5:CDCC923CEC2CD9228330551E6946A9C2 | SHA256:592F4750166BE662AA88728F9969537163FEC5C3E95E81537C8C6917F8D0929E | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF1bdf21.TMP | text | |
MD5:7C1C23F006788D107F8A01B852CC6701 | SHA256:9FA4E627077EDCBEC8AAA1ED2DD5538E630790893F88F02F1E9CC863E6A27848 | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1be3d4.TMP | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF1bf653.TMP | — | |
MD5:— | SHA256:— | |||
| 564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
72
TCP/UDP connections
92
DNS requests
58
Threats
66
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.0 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 158 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 15.6 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 10.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 36.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.15 Mb | unknown |
788 | Installer.exe | POST | 200 | 104.21.81.157:80 | http://barbecueappledos.pw/api | unknown | text | 8.73 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 1.38 Mb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 79.4 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | binary | 342 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2308 | chrome.exe | 142.250.181.237:443 | accounts.google.com | GOOGLE | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2308 | chrome.exe | 199.91.155.129:443 | download2388.mediafire.com | MEDIAFIRE | US | unknown |
564 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2308 | chrome.exe | 104.16.114.74:443 | www.mediafire.com | CLOUDFLARENET | — | unknown |
2308 | chrome.exe | 142.250.185.74:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2308 | chrome.exe | 142.250.181.228:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
download2388.mediafire.com |
| unknown |
www.mediafire.com |
| shared |
static.mediafire.com |
| shared |
fonts.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2308 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2308 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2308 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2308 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
788 | Installer.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
788 | Installer.exe | Malware Command and Control Activity Detected | ET MALWARE [ANY.RUN] Win32/Lumma Stealer Check-In |
788 | Installer.exe | Misc activity | ET INFO HTTP Request to a *.pw domain |
788 | Installer.exe | Malware Command and Control Activity Detected | STEALER [ANY.RUN] Win32/Lumma Stealer Check-In |
788 | Installer.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
2 ETPRO signatures available at the full report