| File name: | 8b09d2c90f68252f5b1e80509c7301bc29fe2e86d89539349680866c8cb4bbae |
| Full analysis: | https://app.any.run/tasks/d4cccebb-fccd-4dcb-8fff-d32dab75b7d4 |
| Verdict: | Malicious activity |
| Threats: | LokiBot was developed in 2015 to steal information from a variety of applications. Despite the age, this malware is still rather popular among cybercriminals. |
| Analysis date: | May 15, 2025, 10:19:54 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
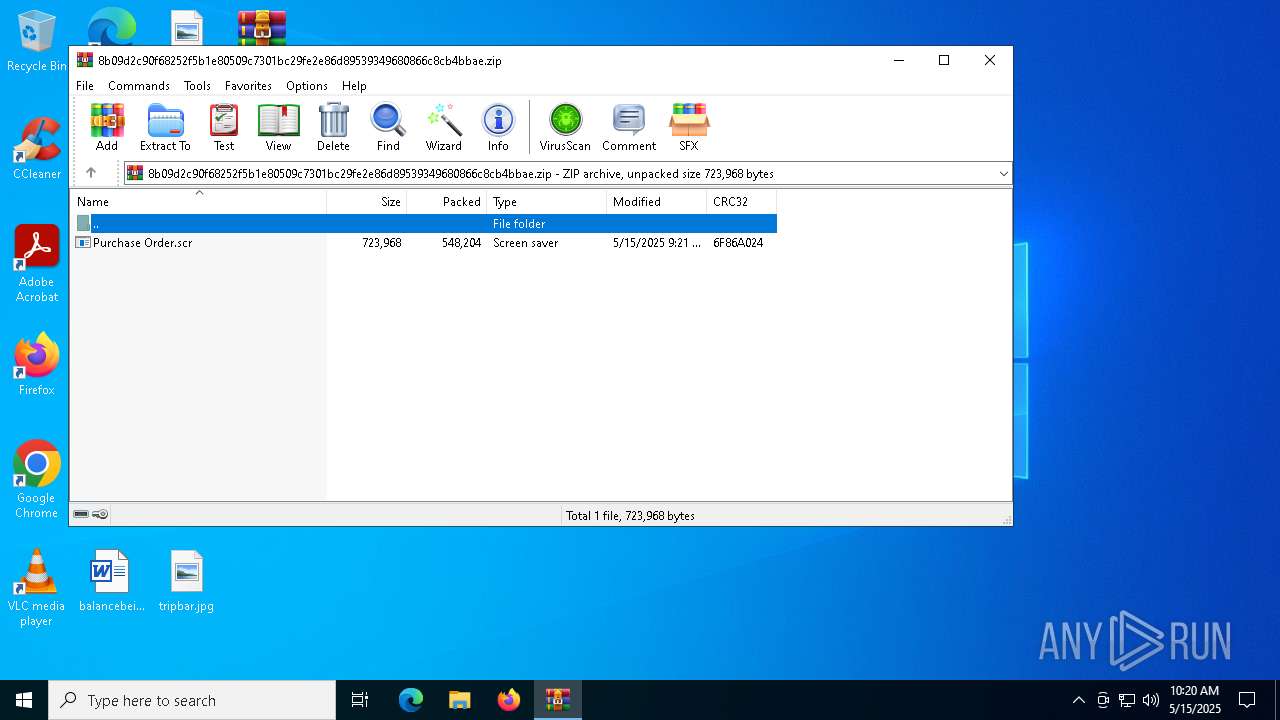
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | E5EFAF17F0BF7C9919239F6A8468E8C5 |
| SHA1: | 77EE09153B11F8009D22B07DB4BCDF8356C7B346 |
| SHA256: | 8B09D2C90F68252F5B1E80509C7301BC29FE2E86D89539349680866C8CB4BBAE |
| SSDEEP: | 24576:enqCm2V8yNcEyA4NR9ECxpsVDp3KWBUUudVJvOy:enqCm2V8yNcEyA4T9ECxpsVDpaWBUUuN |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7540)
Scans artifacts that could help determine the target
- Purchase Order.scr (PID: 7852)
Lokibot is detected
- Purchase Order.scr (PID: 7852)
LOKIBOT has been detected (SURICATA)
- Purchase Order.scr (PID: 7852)
Steals credentials from Web Browsers
- Purchase Order.scr (PID: 7852)
Connects to the CnC server
- Purchase Order.scr (PID: 7852)
LOKIBOT has been detected (YARA)
- Purchase Order.scr (PID: 7852)
Actions looks like stealing of personal data
- Purchase Order.scr (PID: 7852)
LOKIBOT mutex has been found
- Purchase Order.scr (PID: 7852)
SUSPICIOUS
Reads security settings of Internet Explorer
- Purchase Order.scr (PID: 7852)
Executable content was dropped or overwritten
- Purchase Order.scr (PID: 7852)
Connects to the server without a host name
- Purchase Order.scr (PID: 7852)
Contacting a server suspected of hosting an CnC
- Purchase Order.scr (PID: 7852)
Application launched itself
- Purchase Order.scr (PID: 7740)
Starts application with an unusual extension
- Purchase Order.scr (PID: 7740)
INFO
Manual execution by a user
- Purchase Order.scr (PID: 7740)
Checks supported languages
- Purchase Order.scr (PID: 7740)
- Purchase Order.scr (PID: 7852)
Reads the computer name
- Purchase Order.scr (PID: 7740)
- Purchase Order.scr (PID: 7852)
.NET Reactor protector has been detected
- Purchase Order.scr (PID: 7740)
Reads the machine GUID from the registry
- Purchase Order.scr (PID: 7852)
- Purchase Order.scr (PID: 7740)
Checks proxy server information
- slui.exe (PID: 7256)
Reads Microsoft Office registry keys
- Purchase Order.scr (PID: 7852)
Creates files or folders in the user directory
- Purchase Order.scr (PID: 7852)
Reads the software policy settings
- slui.exe (PID: 7256)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
LokiBot
(PID) Process(7852) Purchase Order.scr
C294.156.177.41/alpha/five/fre.php
Decoys (4)kbfvzoboss.bid/alien/fre.php
alphastand.trade/alien/fre.php
alphastand.win/alien/fre.php
alphastand.top/alien/fre.php
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:15 09:21:52 |
| ZipCRC: | 0x6f86a024 |
| ZipCompressedSize: | 548204 |
| ZipUncompressedSize: | 723968 |
| ZipFileName: | Purchase Order.scr |
Total processes
130
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7256 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7540 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\8b09d2c90f68252f5b1e80509c7301bc29fe2e86d89539349680866c8cb4bbae.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7740 | "C:\Users\admin\Desktop\Purchase Order.scr" /S | C:\Users\admin\Desktop\Purchase Order.scr | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Delivery Market Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7852 | "C:\Users\admin\Desktop\Purchase Order.scr" | C:\Users\admin\Desktop\Purchase Order.scr | Purchase Order.scr | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Delivery Market Version: 1.0.0.0 Modules
LokiBot(PID) Process(7852) Purchase Order.scr C294.156.177.41/alpha/five/fre.php Decoys (4)kbfvzoboss.bid/alien/fre.php alphastand.trade/alien/fre.php alphastand.win/alien/fre.php alphastand.top/alien/fre.php | |||||||||||||||
Total events
5 651
Read events
5 639
Write events
12
Delete events
0
Modification events
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\8b09d2c90f68252f5b1e80509c7301bc29fe2e86d89539349680866c8cb4bbae.zip | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7540) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7852) Purchase Order.scr | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7852) Purchase Order.scr | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
1
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7852 | Purchase Order.scr | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1693682860-607145093-2874071422-1001\0f5007522459c86e95ffcc62f32308f1_bb926e54-e3ca-40fd-ae90-2764341e7792 | binary | |
MD5:D898504A722BFF1524134C6AB6A5EAA5 | SHA256:878F32F76B159494F5A39F9321616C6068CDB82E88DF89BCC739BBC1EA78E1F9 | |||
| 7852 | Purchase Order.scr | C:\Users\admin\AppData\Roaming\F3F363\3C28B3.lck | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 7852 | Purchase Order.scr | C:\Users\admin\AppData\Roaming\F3F363\3C28B3.hdb | binary | |
MD5:1013079A9BF8FFA458C230EA6AAF8A89 | SHA256:1B1F3BCE8DF0FC7E33B518DAB09D09AF3680E39BCC3C760DADCC50C931007BE8 | |||
| 7852 | Purchase Order.scr | C:\Users\admin\AppData\Roaming\F3F363\3C28B3.exe | executable | |
MD5:D35B87D167FF8FC820482E3587145B8E | SHA256:CC821A0D546E108E6FDF6DC82DDB271560412ED650E6A7354CB986C7CCA4C9AA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
53
DNS requests
14
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7852 | Purchase Order.scr | POST | 404 | 94.156.177.41:80 | http://94.156.177.41/alpha/five/fre.php | unknown | — | — | malicious |
7852 | Purchase Order.scr | POST | 404 | 94.156.177.41:80 | http://94.156.177.41/alpha/five/fre.php | unknown | — | — | malicious |
7852 | Purchase Order.scr | POST | 404 | 94.156.177.41:80 | http://94.156.177.41/alpha/five/fre.php | unknown | — | — | malicious |
8024 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8024 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7000 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7852 | Purchase Order.scr | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 14 |
7852 | Purchase Order.scr | A Network Trojan was detected | ET MALWARE LokiBot User-Agent (Charon/Inferno) |
7852 | Purchase Order.scr | Malware Command and Control Activity Detected | ET MALWARE LokiBot Checkin |
7852 | Purchase Order.scr | A Network Trojan was detected | ET MALWARE LokiBot Application/Credential Data Exfiltration Detected M1 |
7852 | Purchase Order.scr | Malware Command and Control Activity Detected | ET MALWARE LokiBot Checkin |
7852 | Purchase Order.scr | A Network Trojan was detected | ET MALWARE LokiBot User-Agent (Charon/Inferno) |
7852 | Purchase Order.scr | A Network Trojan was detected | ET MALWARE LokiBot User-Agent (Charon/Inferno) |
7852 | Purchase Order.scr | Malware Command and Control Activity Detected | ET MALWARE LokiBot Checkin |
7852 | Purchase Order.scr | A Network Trojan was detected | ET MALWARE LokiBot Application/Credential Data Exfiltration Detected M1 |
7852 | Purchase Order.scr | Malware Command and Control Activity Detected | ET MALWARE LokiBot Request for C2 Commands Detected M1 |