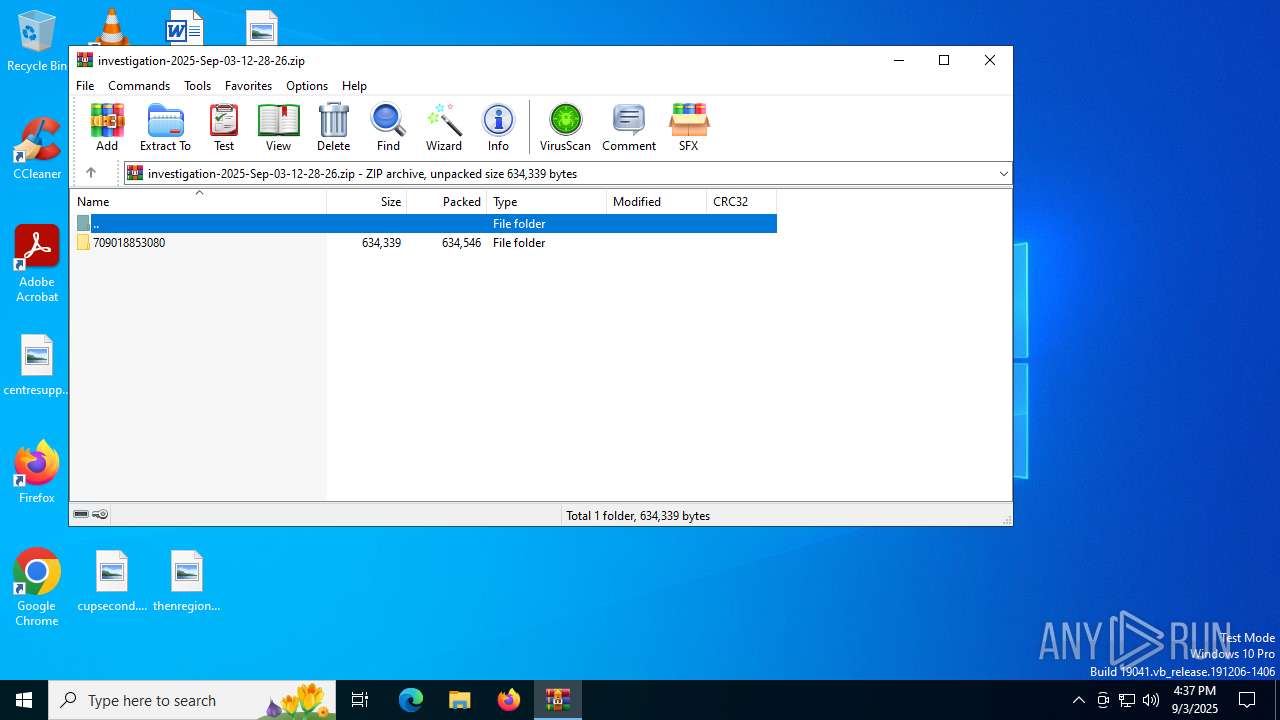
| File name: | investigation-2025-Sep-03-12-28-26.zip |
| Full analysis: | https://app.any.run/tasks/8a43c027-89c1-4670-83f7-2fe544cfe7a9 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 03, 2025, 16:37:05 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 07F36BF4C6DA9D76F827BF3CEAC1E81B |
| SHA1: | 108E97A8E2100D83A905822AE2C9DF3A74C9F25C |
| SHA256: | 8AD00E32CDA7165EAE965CCAA742257712B76B996C558F774EF922A5885402A9 |
| SSDEEP: | 24576:remFJPg+TGV7dlFaO9Fjjps57CqBhYQqb6aOY3I8M2h9X8VqKY3/PqylvUZE:remFJPgyGV7dlFaO9Fps57CqBhYQqb64 |
MALICIOUS
Steals credentials from Web Browsers
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
Actions looks like stealing of personal data
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
AGENTTESLA has been detected (SURICATA)
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
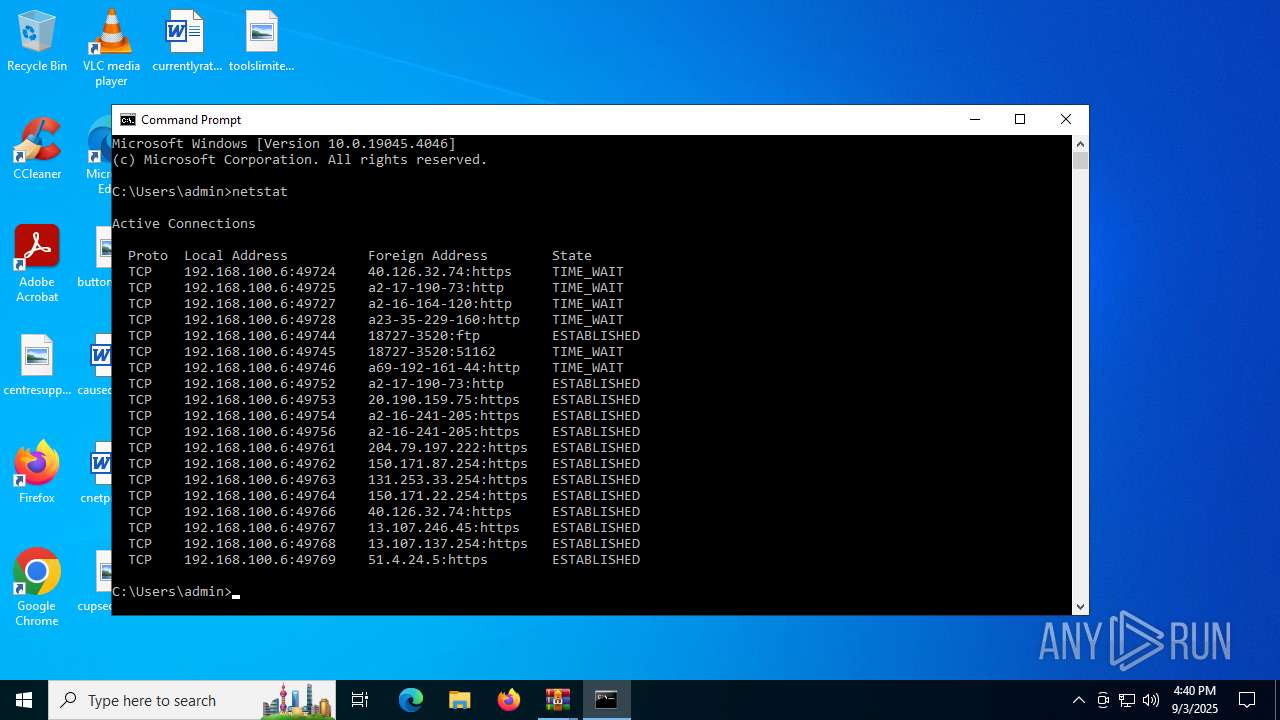
Connects to the CnC server
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
AGENTTESLA has been detected (YARA)
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
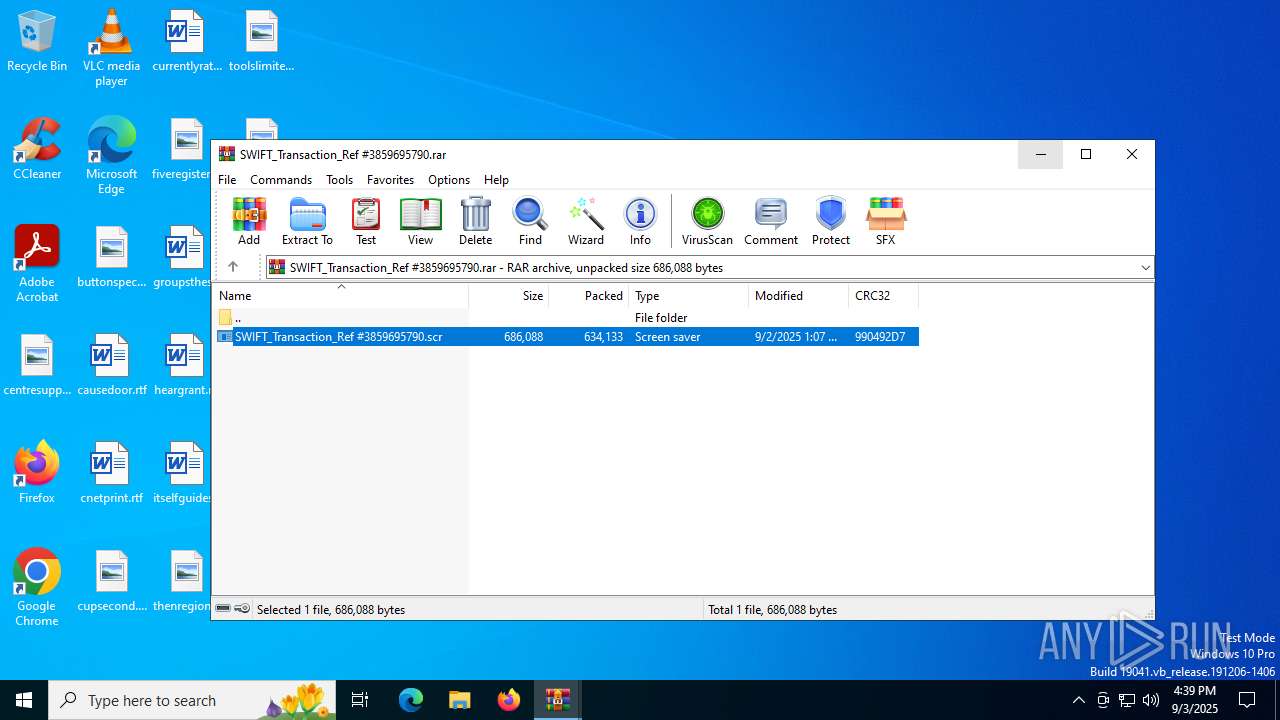
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2148)
- WinRAR.exe (PID: 5436)
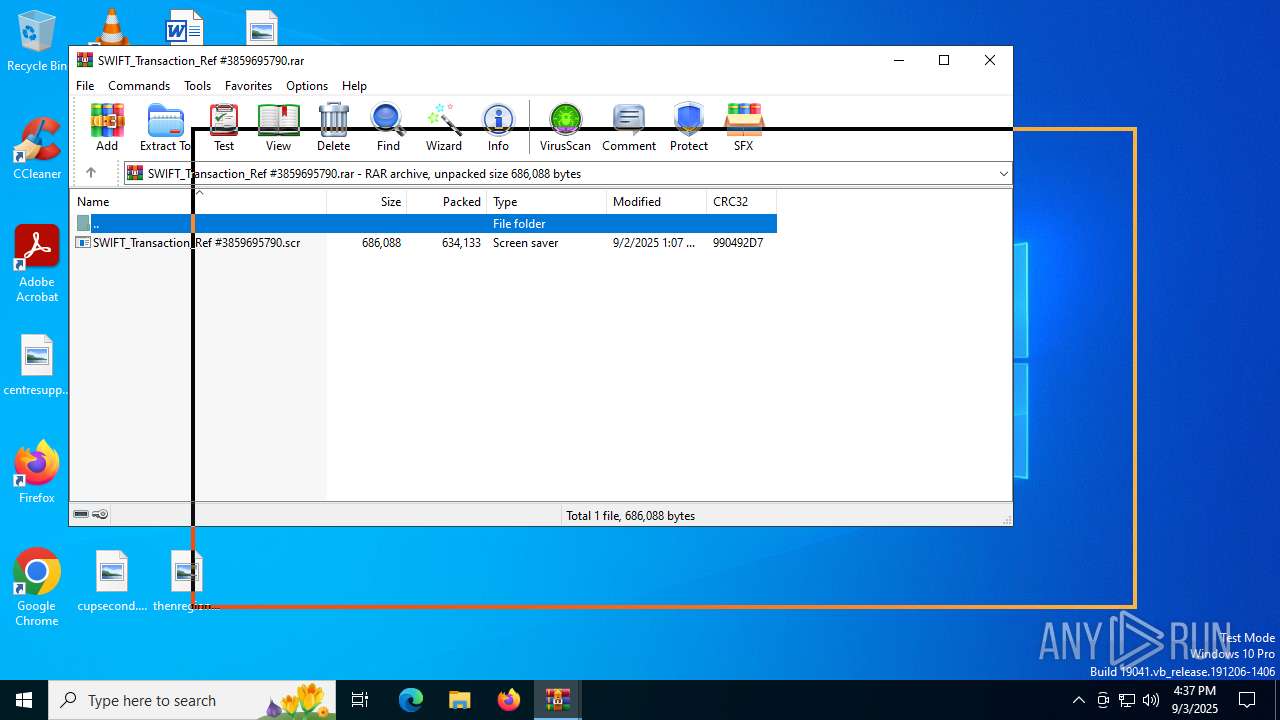
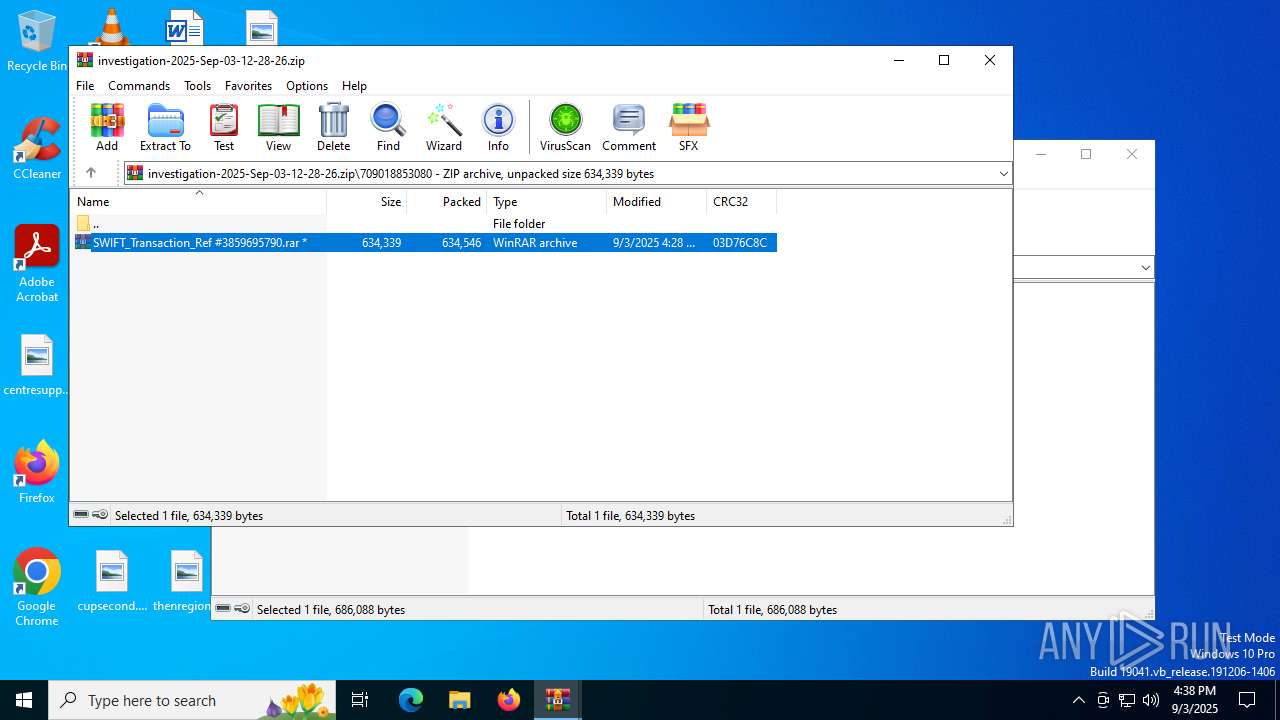
Starts application with an unusual extension
- WinRAR.exe (PID: 2148)
Checks for external IP
- RegSvcs.exe (PID: 2380)
- svchost.exe (PID: 2200)
- RegSvcs.exe (PID: 6004)
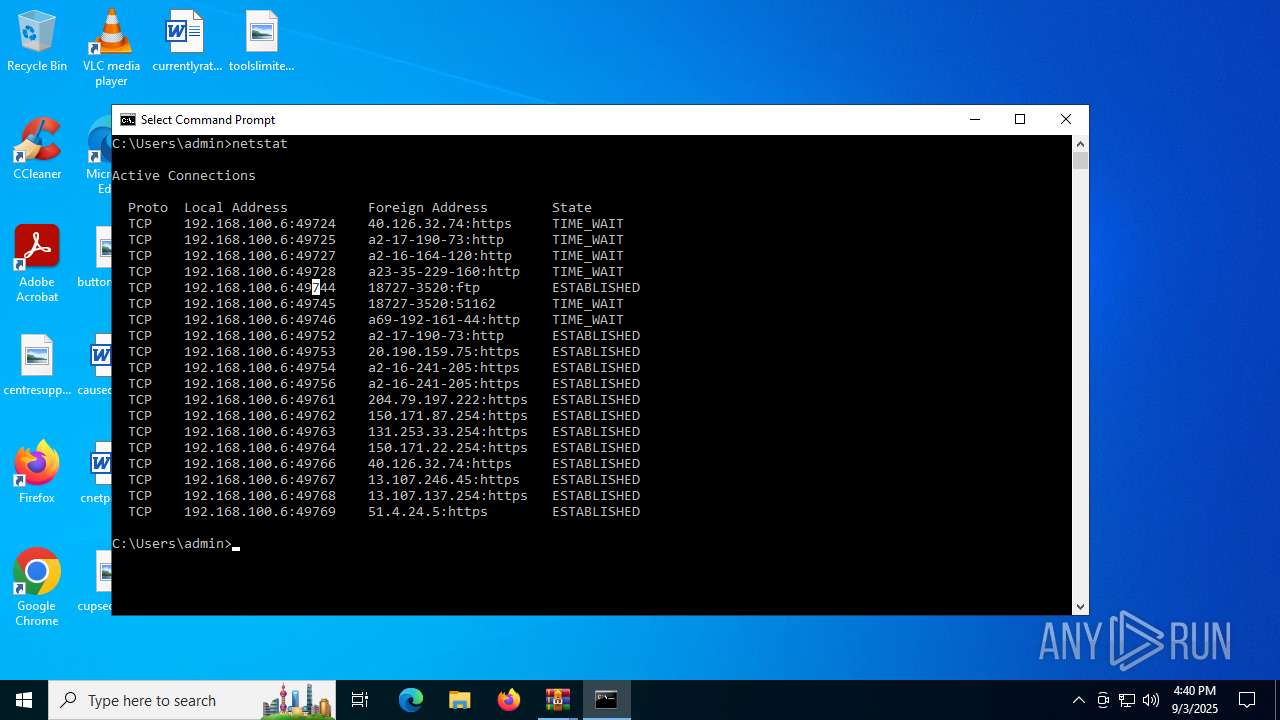
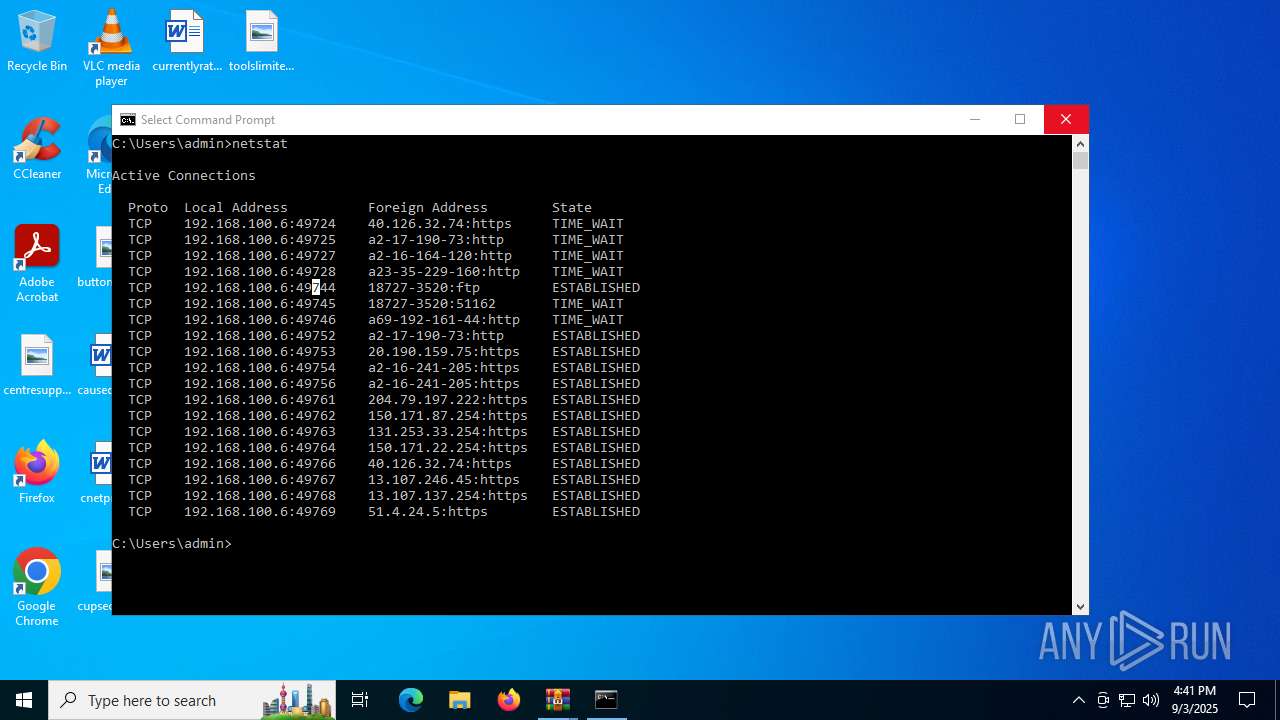
Connects to FTP
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
Application launched itself
- WinRAR.exe (PID: 5436)
Connects to unusual port
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
INFO
Checks supported languages
- SWIFT_Transaction_Ref #3859695790.scr (PID: 2228)
- RegSvcs.exe (PID: 2380)
- SWIFT_Transaction_Ref #3859695790.scr (PID: 6224)
- RegSvcs.exe (PID: 6004)
- SearchApp.exe (PID: 5328)
Reads the computer name
- SWIFT_Transaction_Ref #3859695790.scr (PID: 2228)
- RegSvcs.exe (PID: 2380)
- SWIFT_Transaction_Ref #3859695790.scr (PID: 6224)
- RegSvcs.exe (PID: 6004)
Reads the machine GUID from the registry
- SWIFT_Transaction_Ref #3859695790.scr (PID: 2228)
- RegSvcs.exe (PID: 2380)
- SWIFT_Transaction_Ref #3859695790.scr (PID: 6224)
- RegSvcs.exe (PID: 6004)
- SearchApp.exe (PID: 5328)
.NET Reactor protector has been detected
- SWIFT_Transaction_Ref #3859695790.scr (PID: 2228)
- SWIFT_Transaction_Ref #3859695790.scr (PID: 6224)
Checks proxy server information
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
- slui.exe (PID: 1068)
Disables trace logs
- RegSvcs.exe (PID: 2380)
- RegSvcs.exe (PID: 6004)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2148)
Reads the software policy settings
- slui.exe (PID: 1068)
- SearchApp.exe (PID: 5328)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
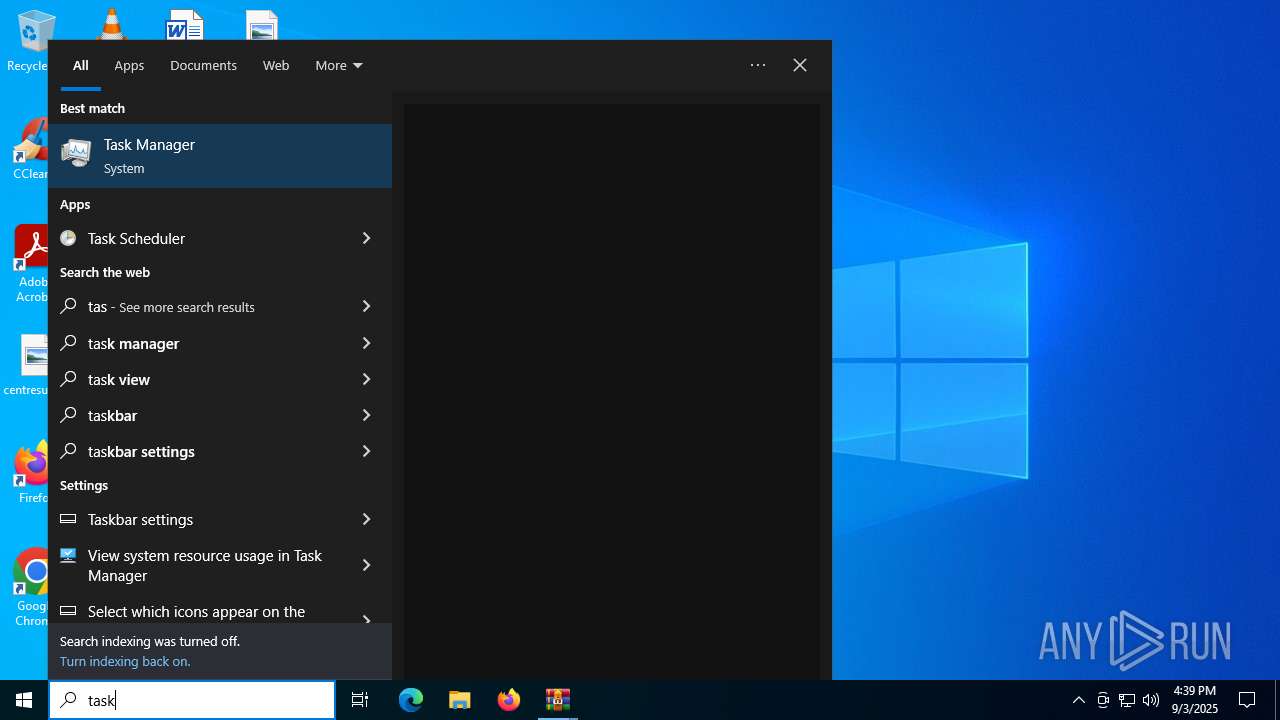
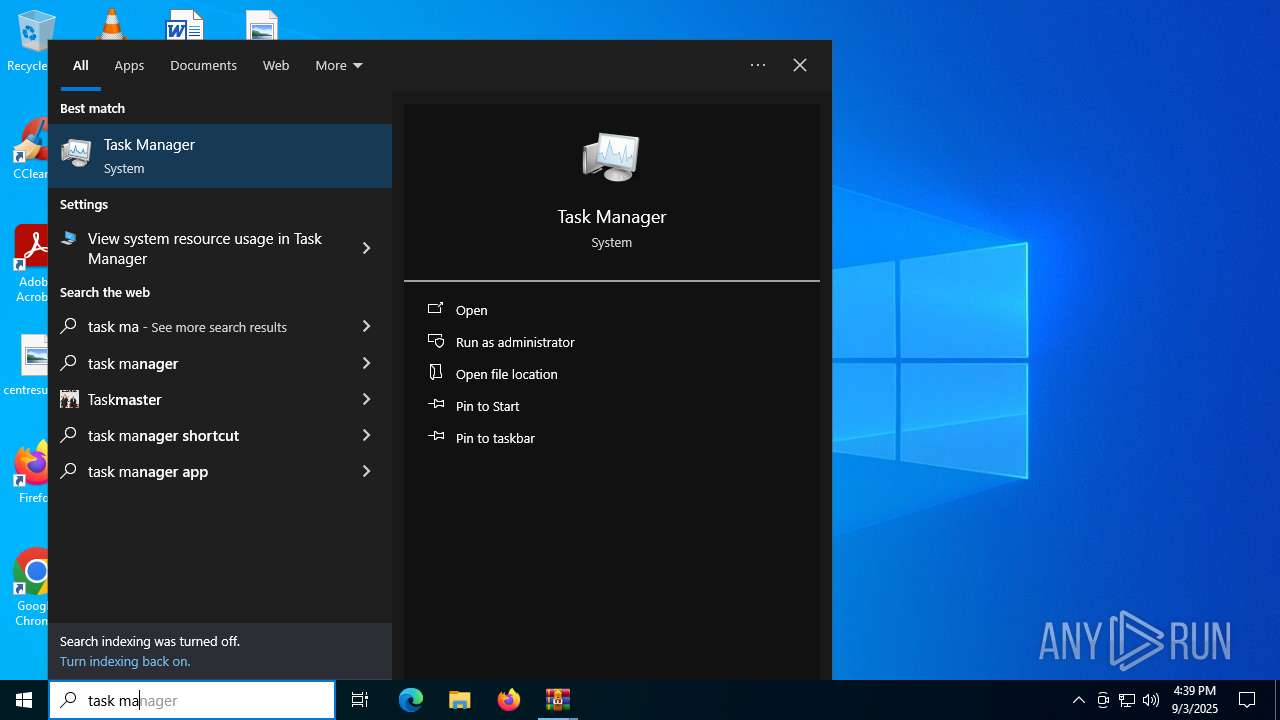
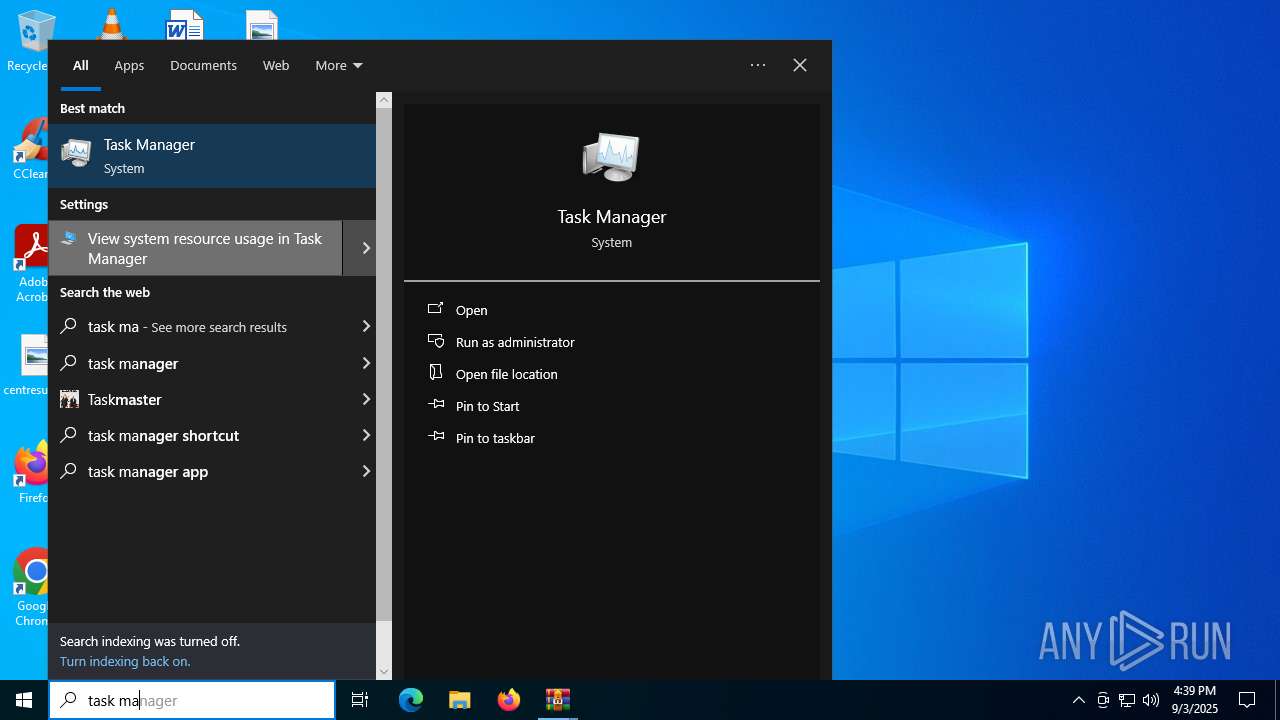
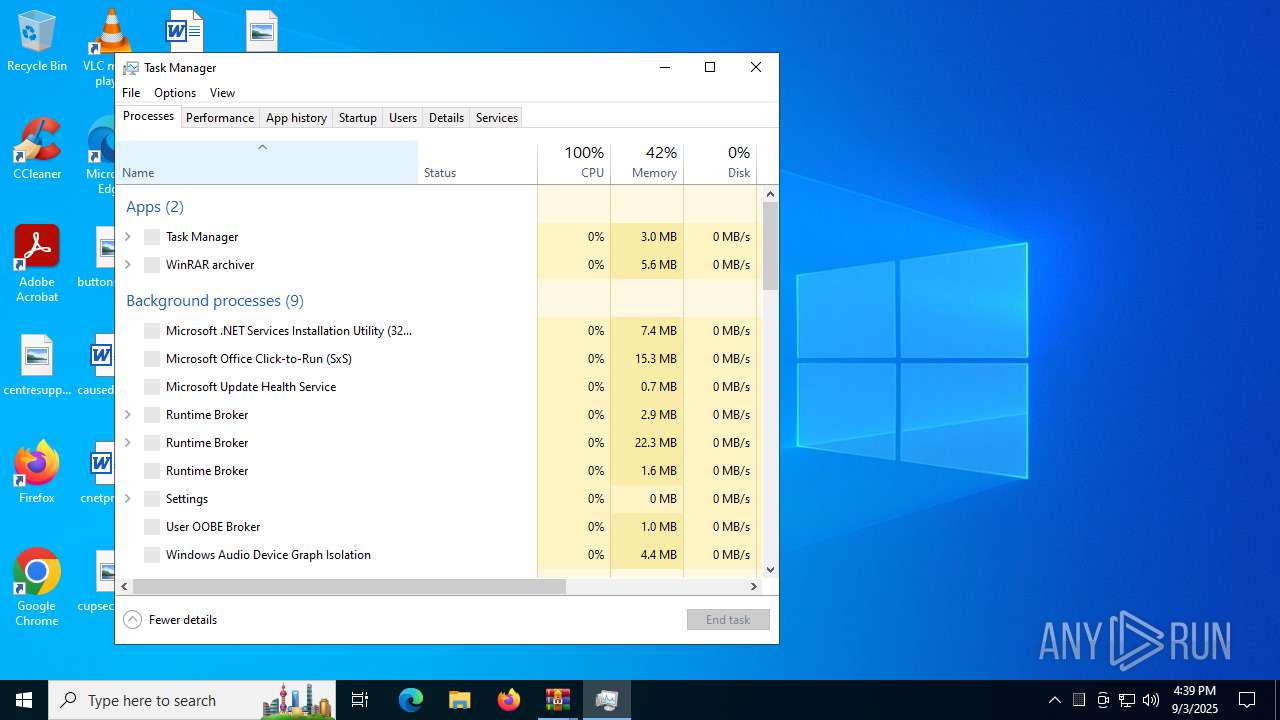
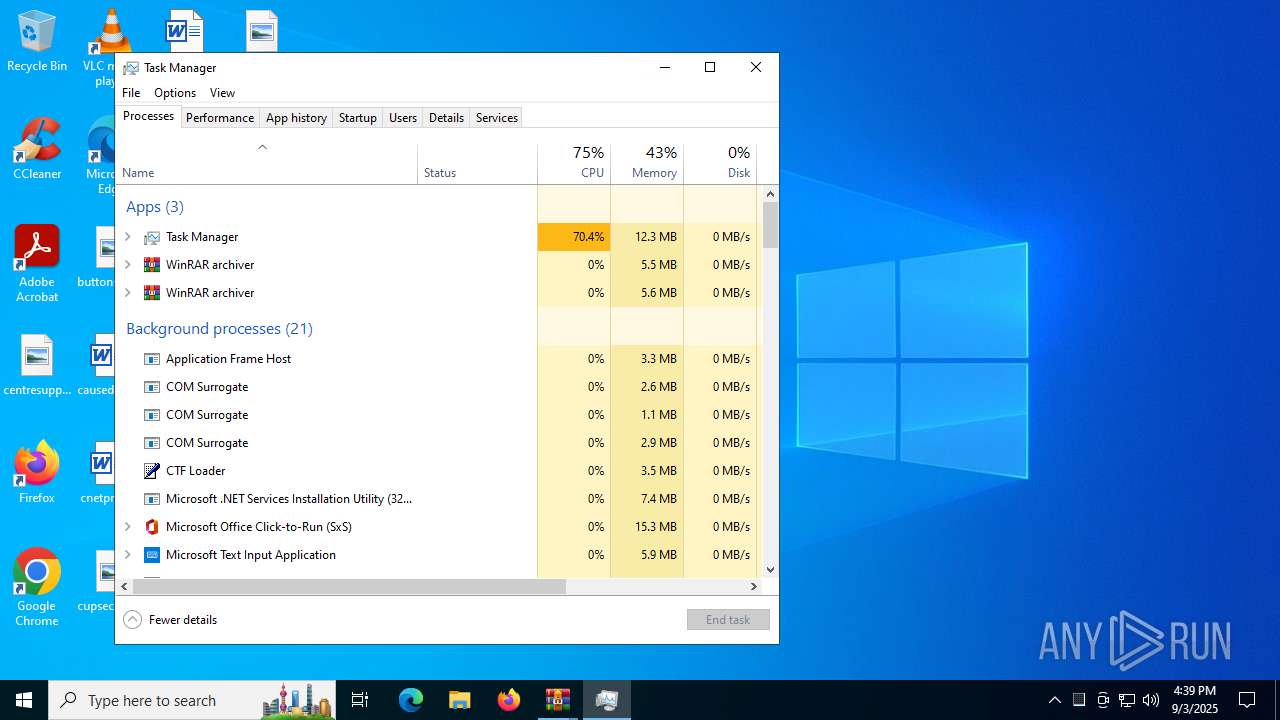
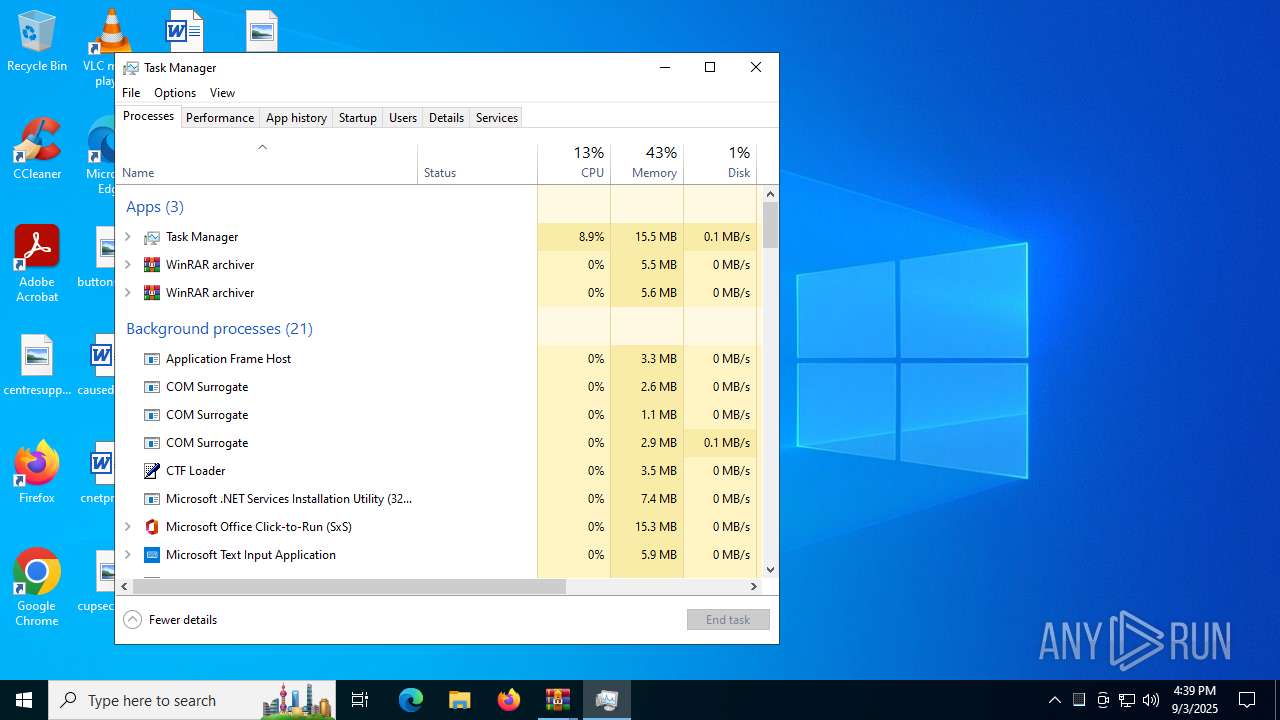
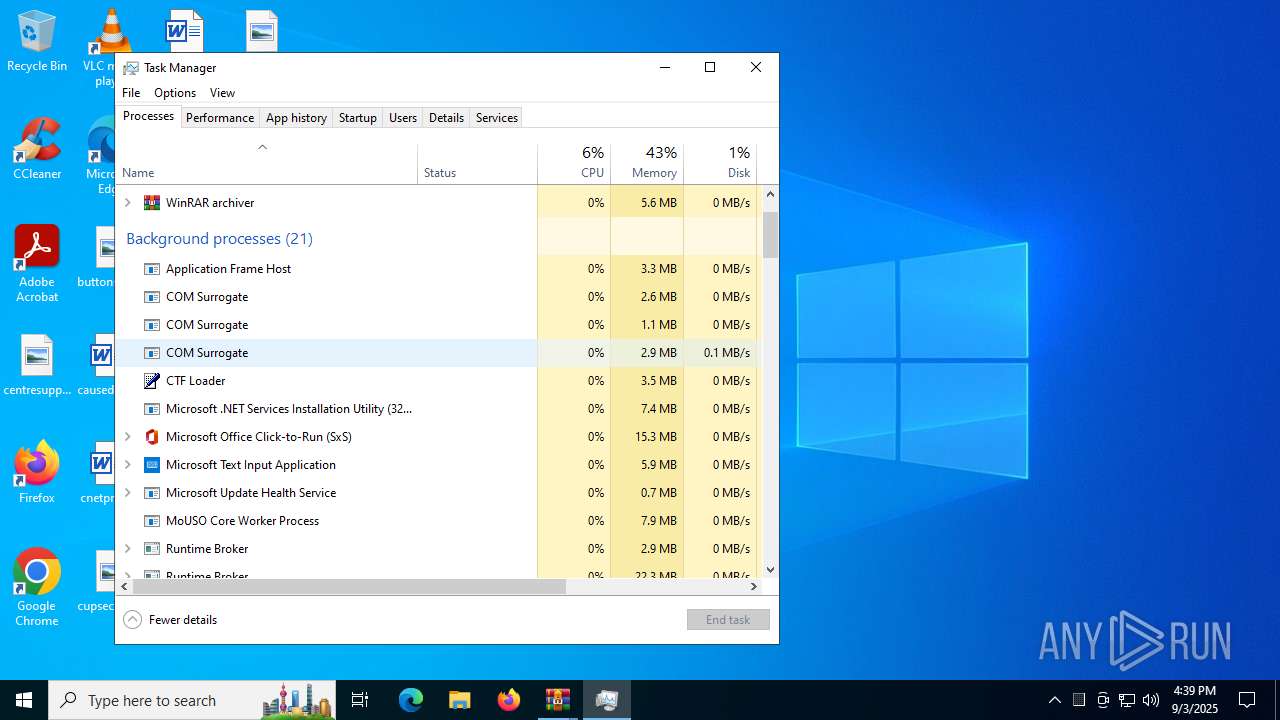
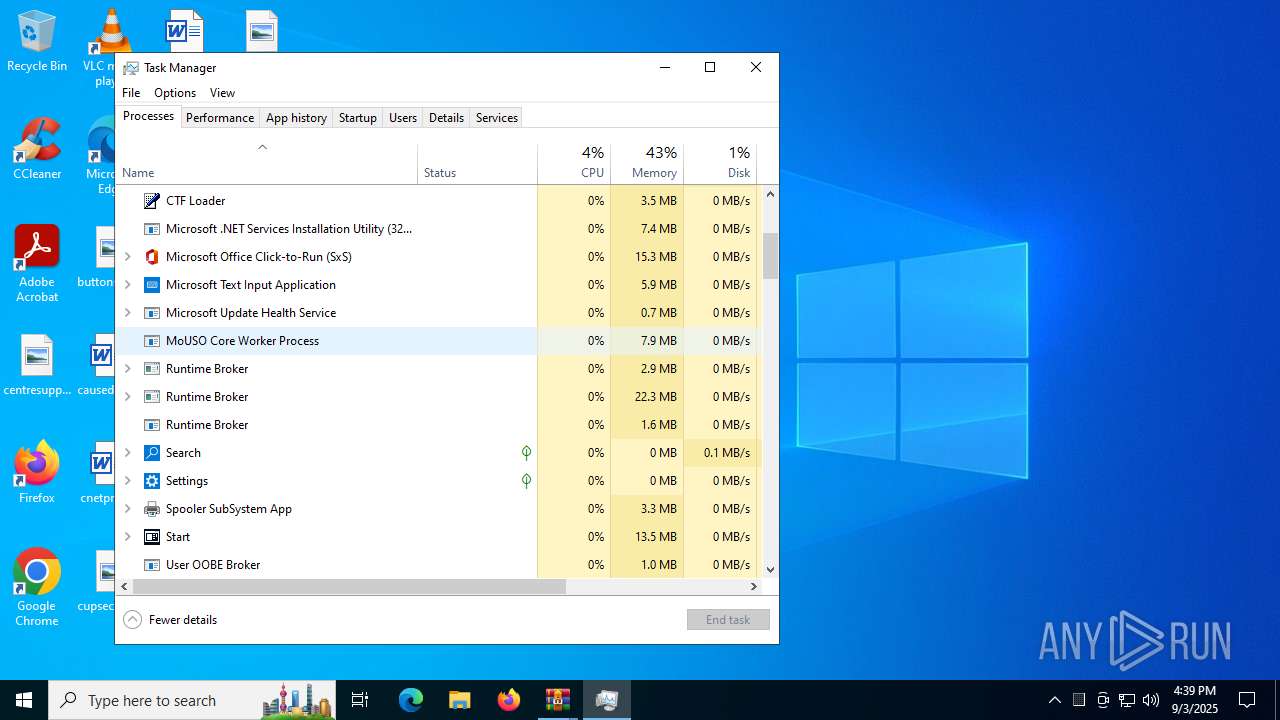
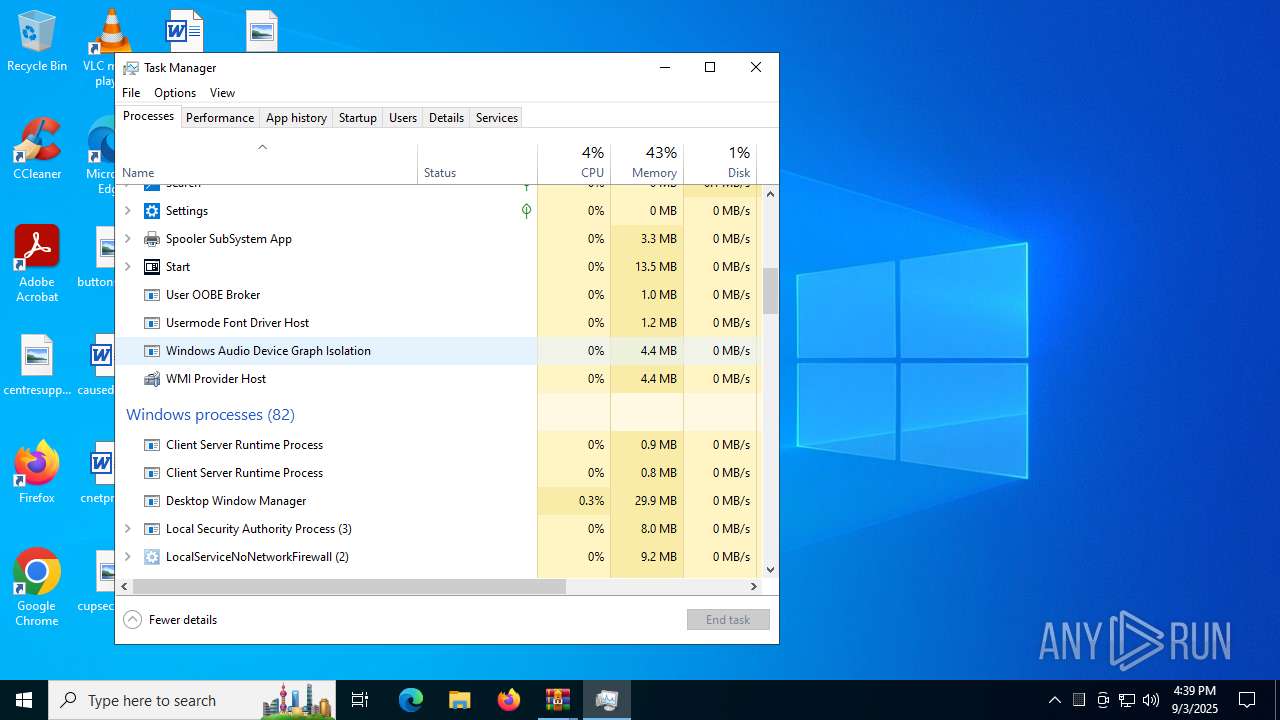
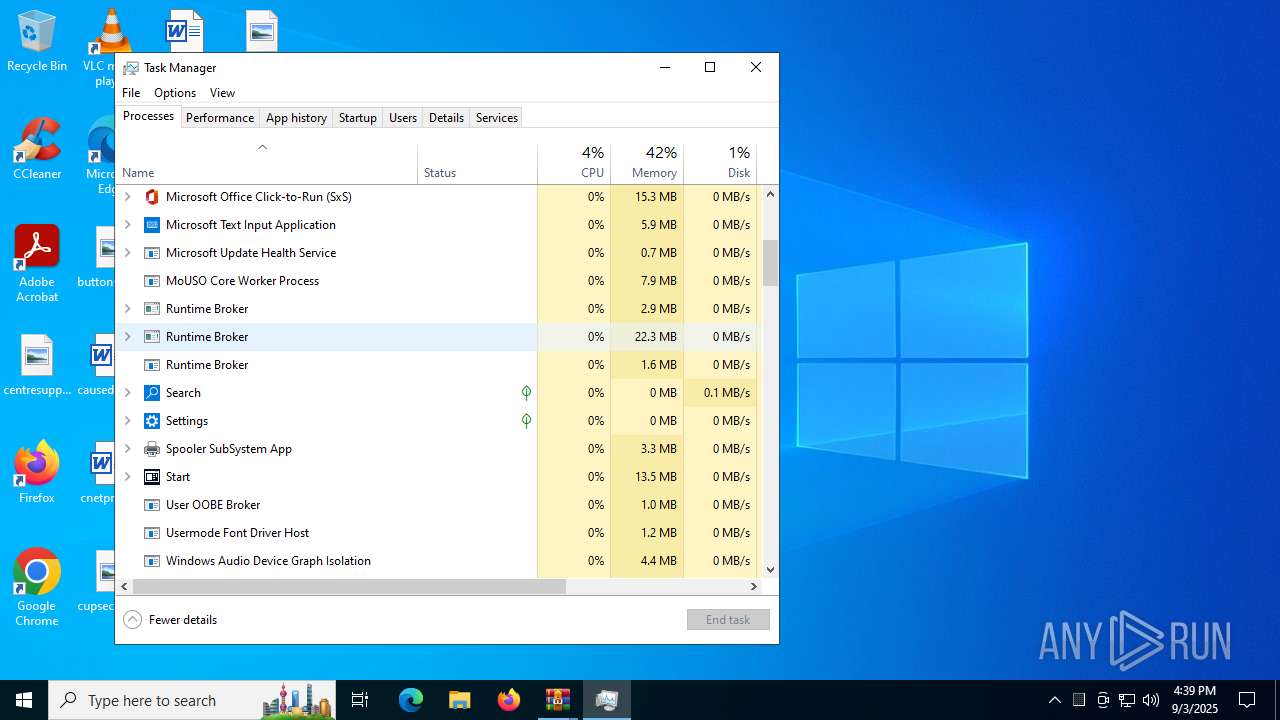
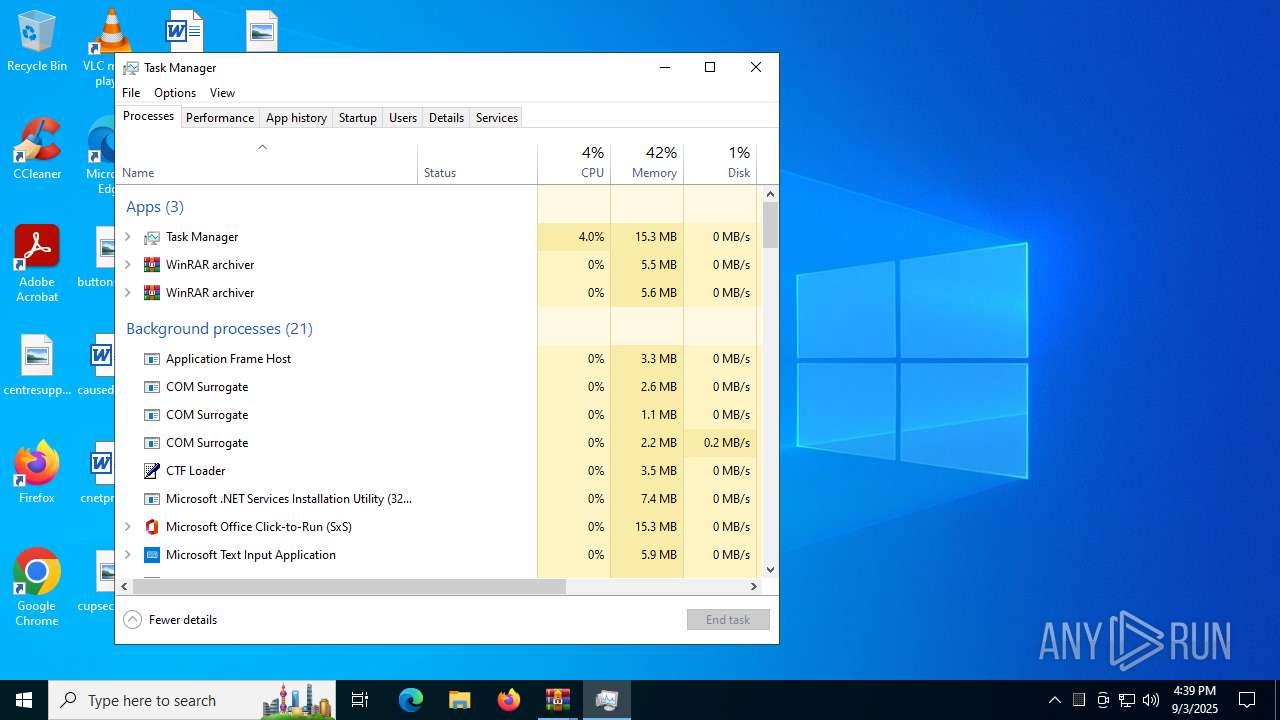
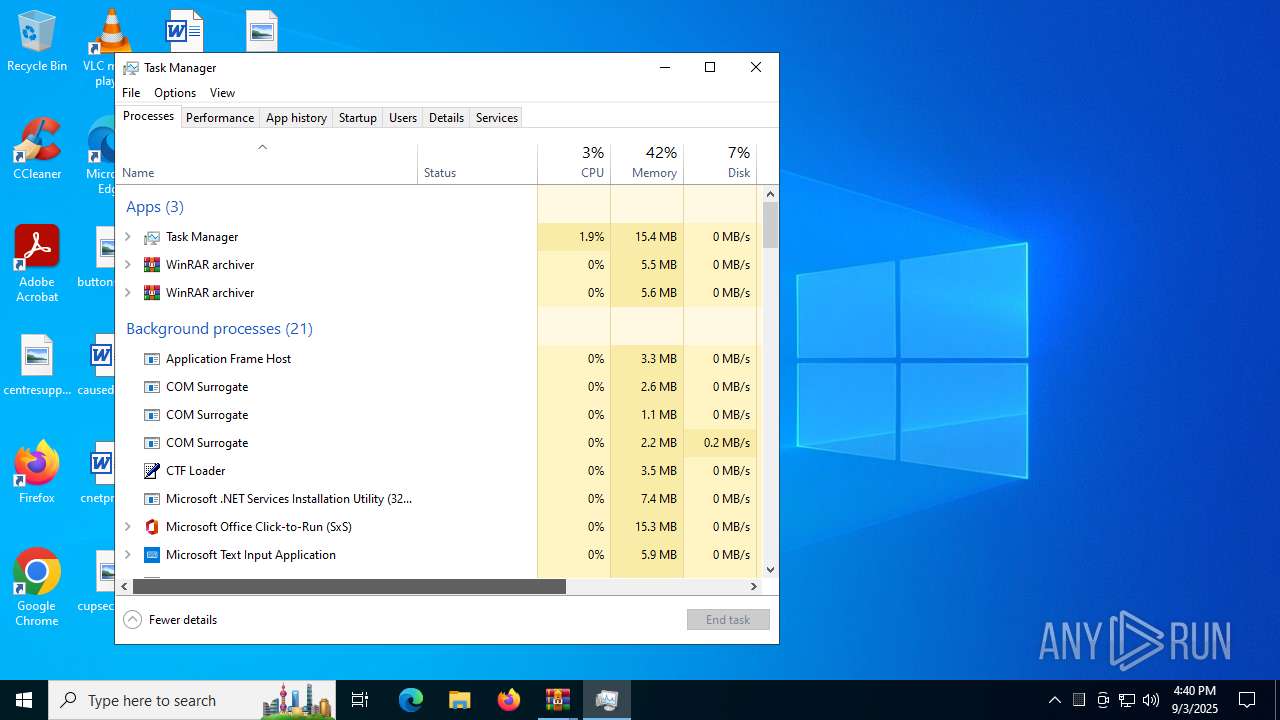
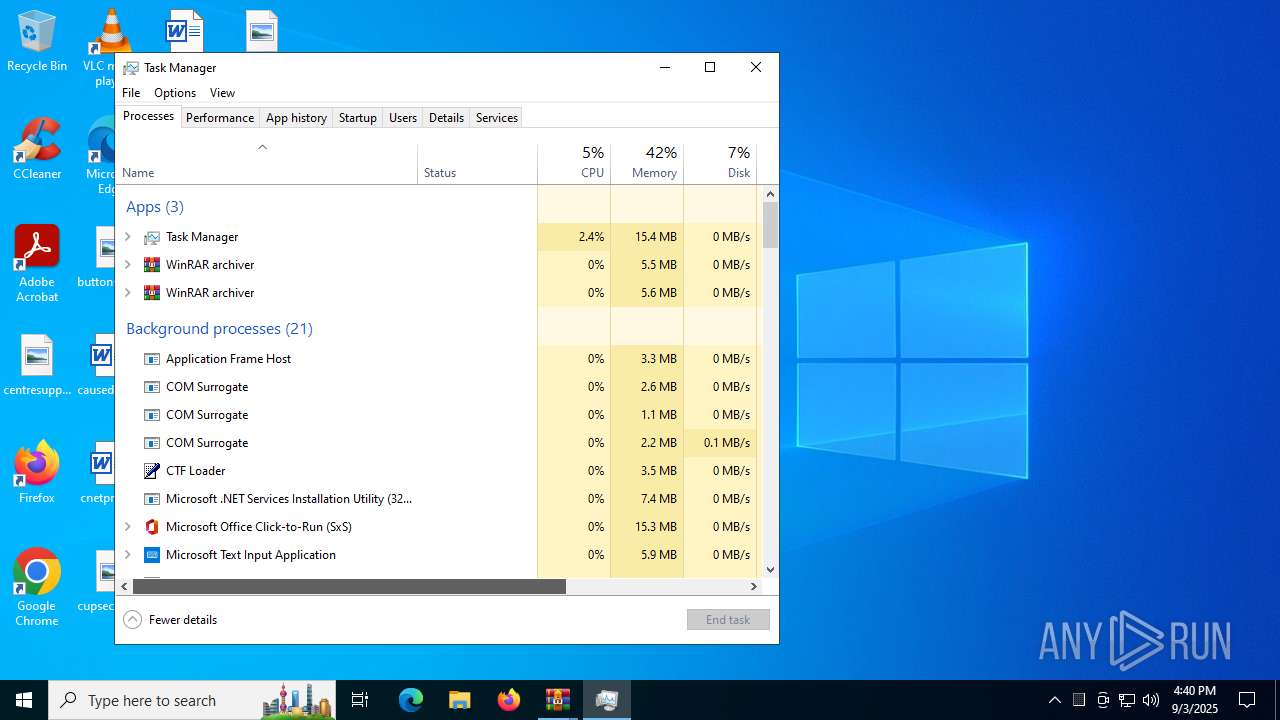
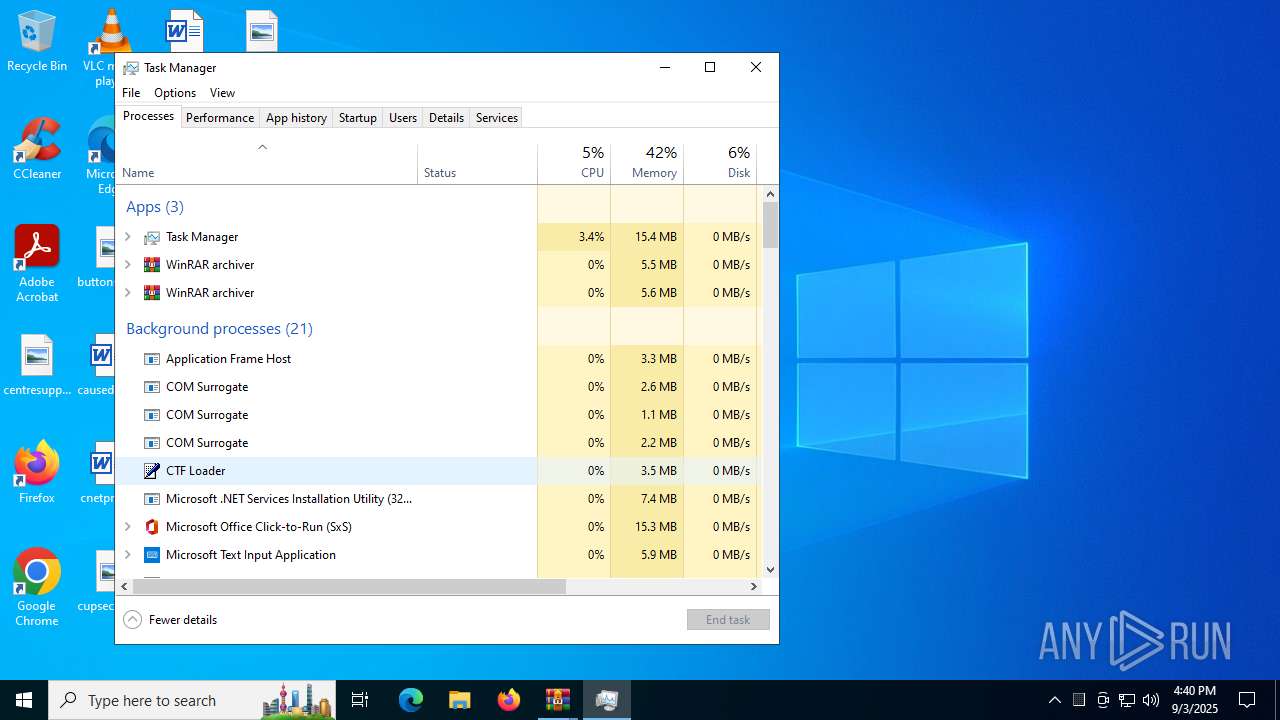
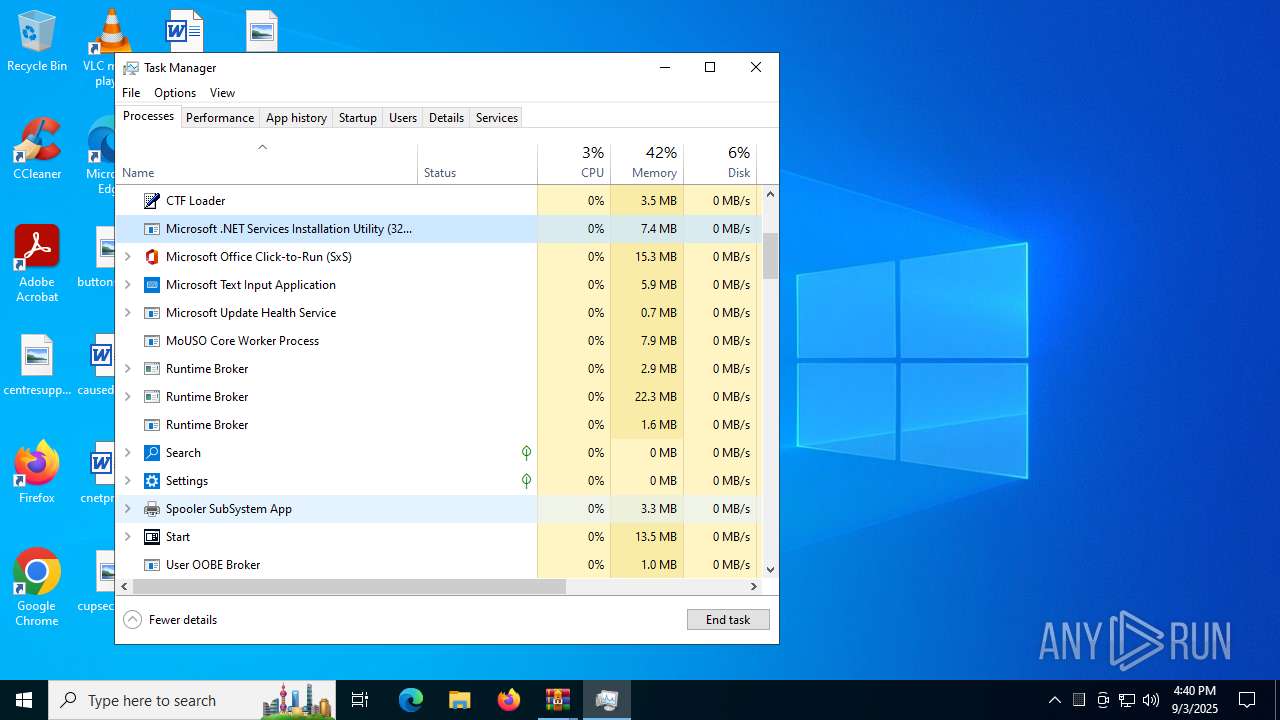
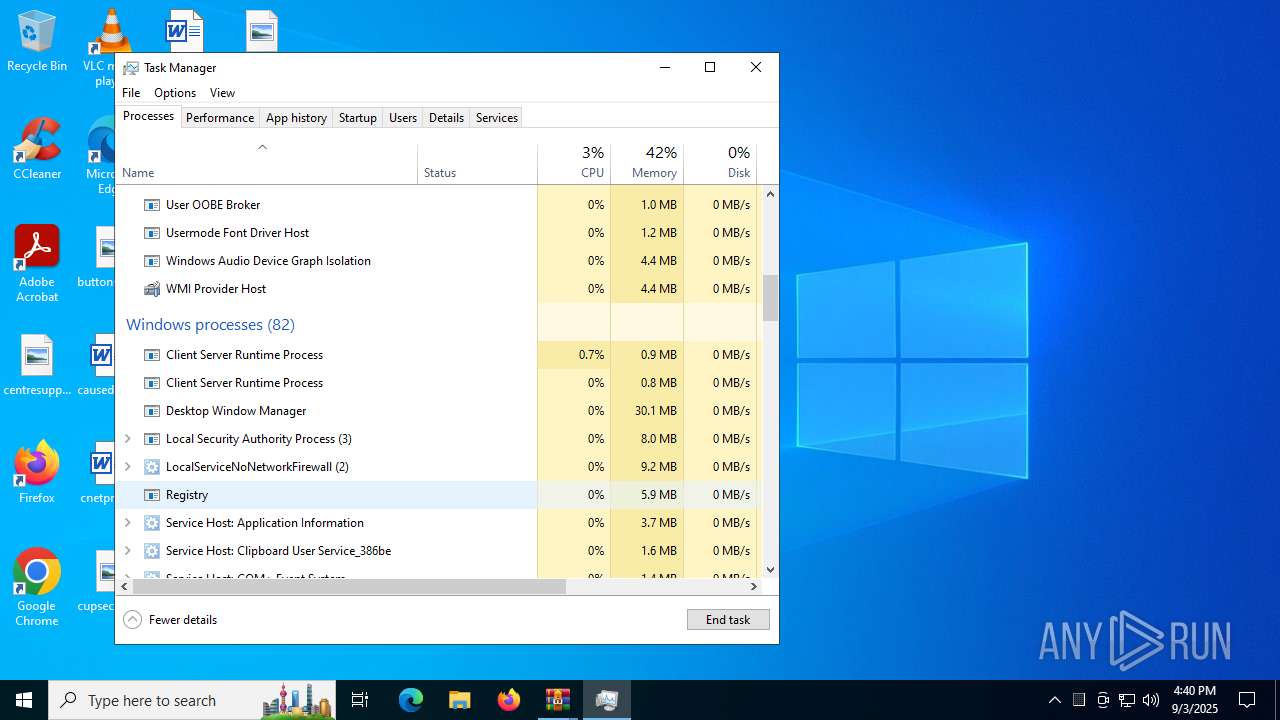
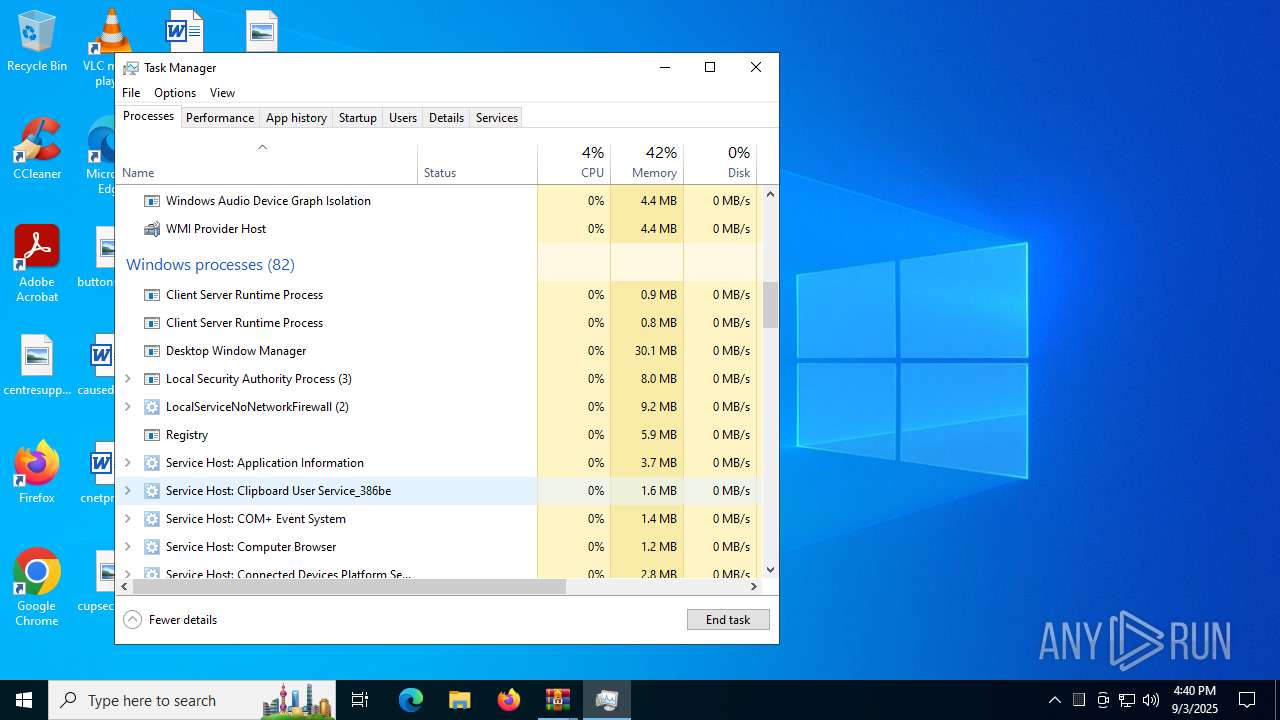
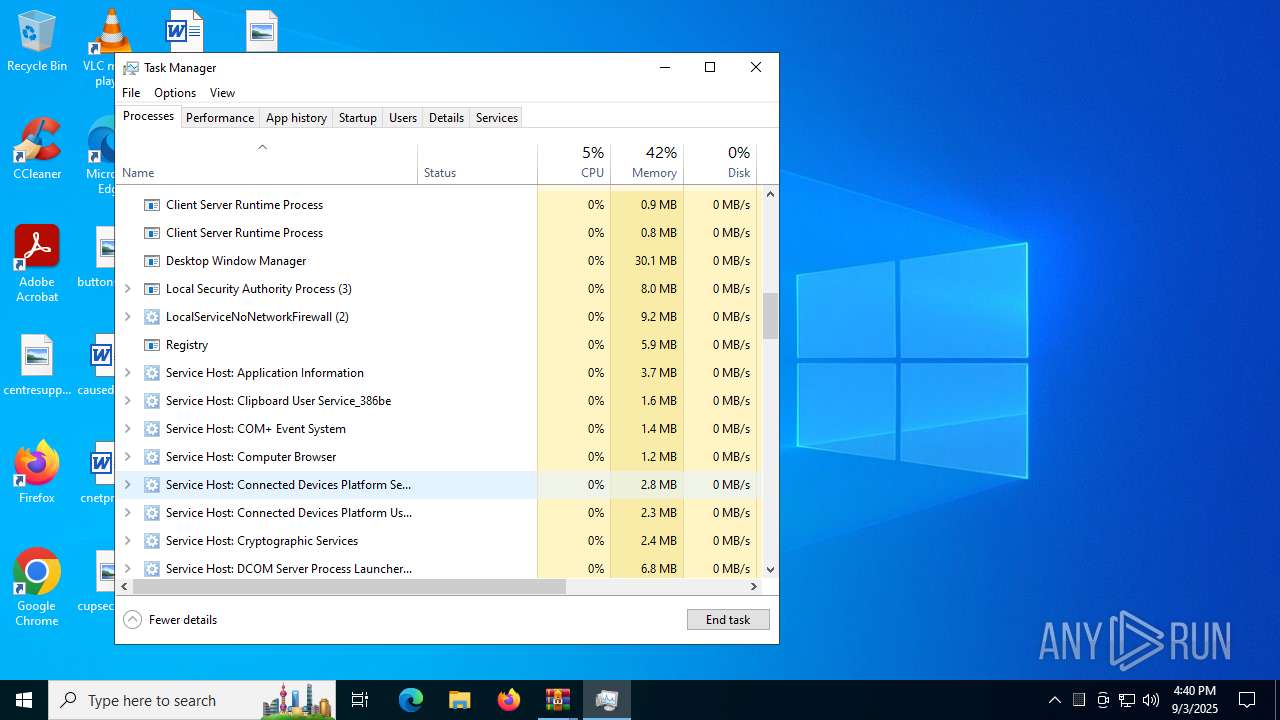
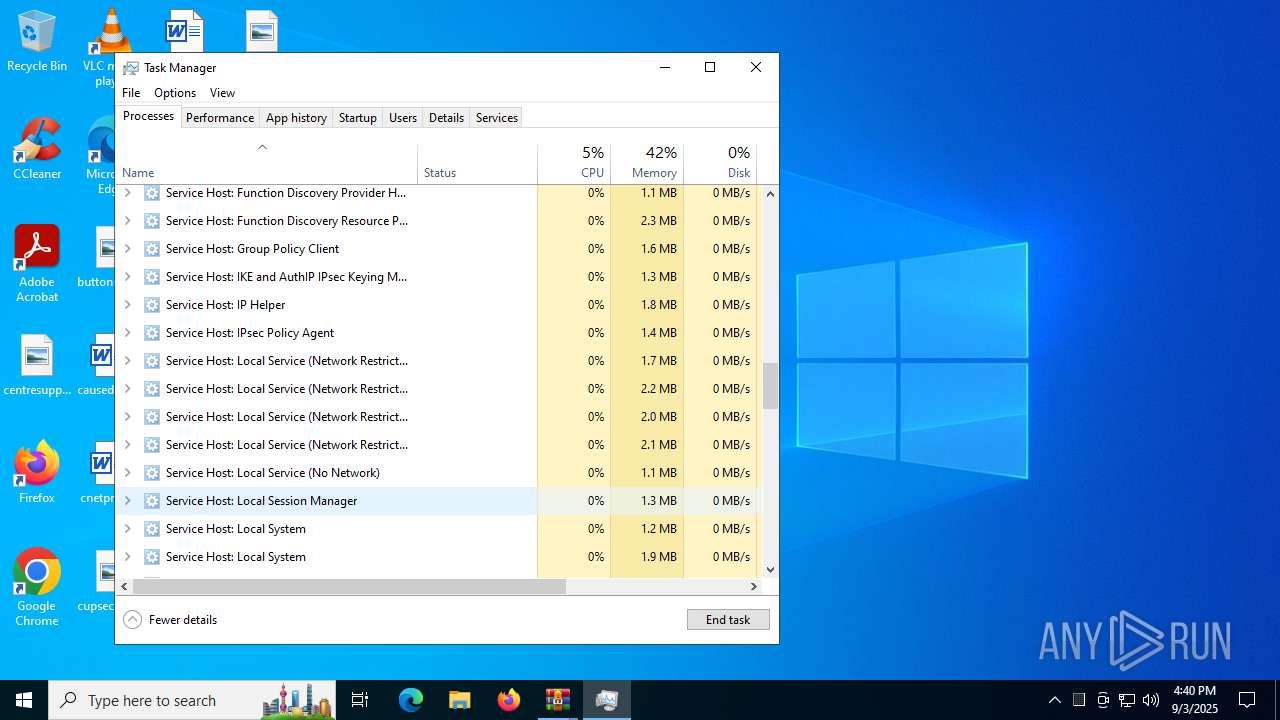
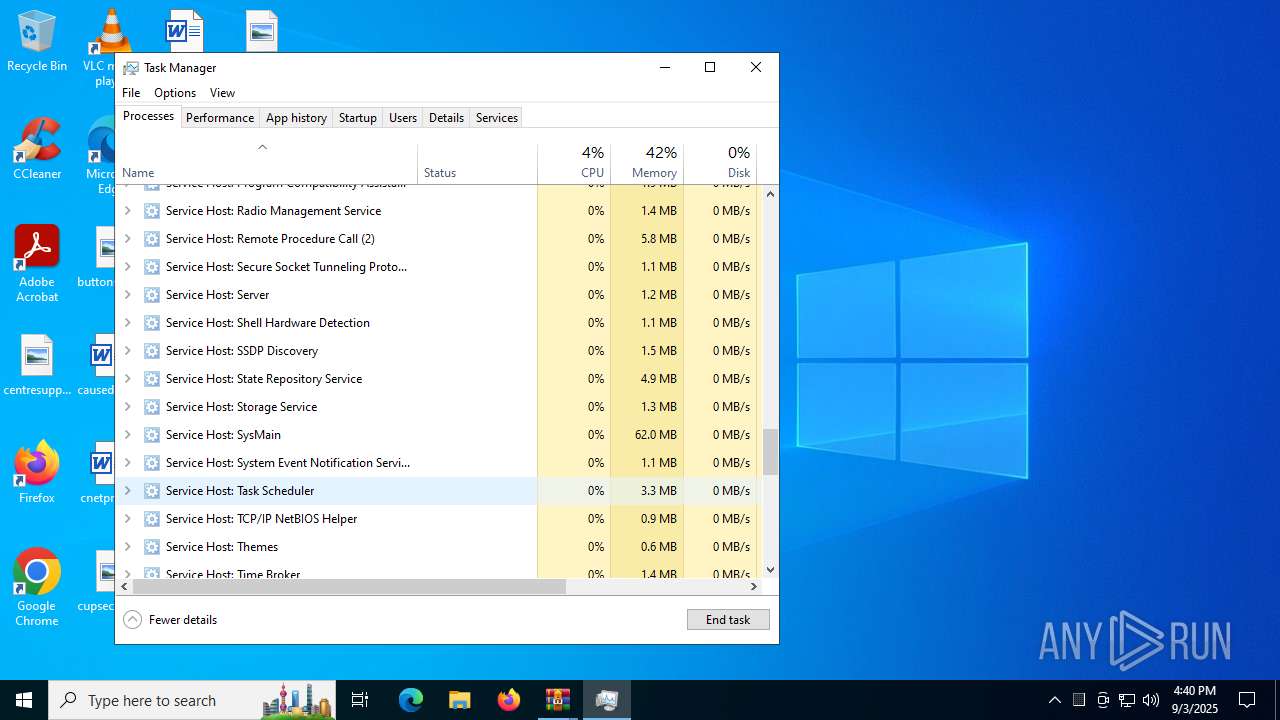
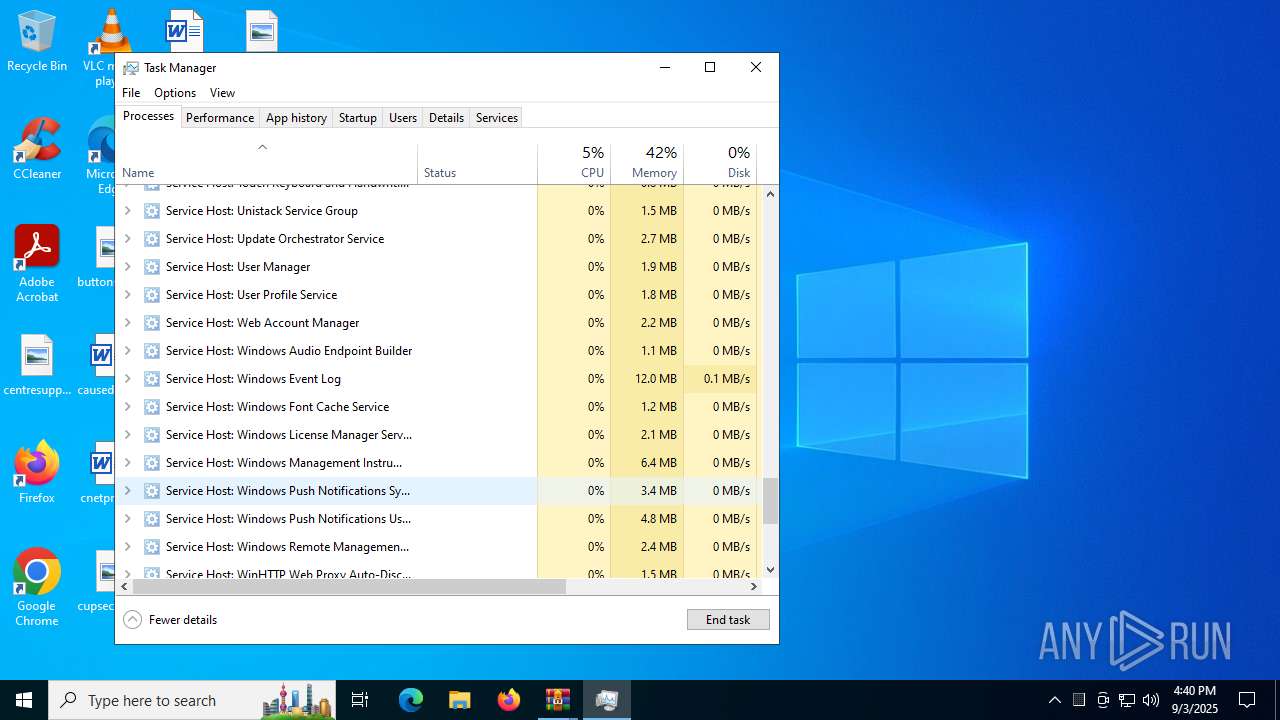
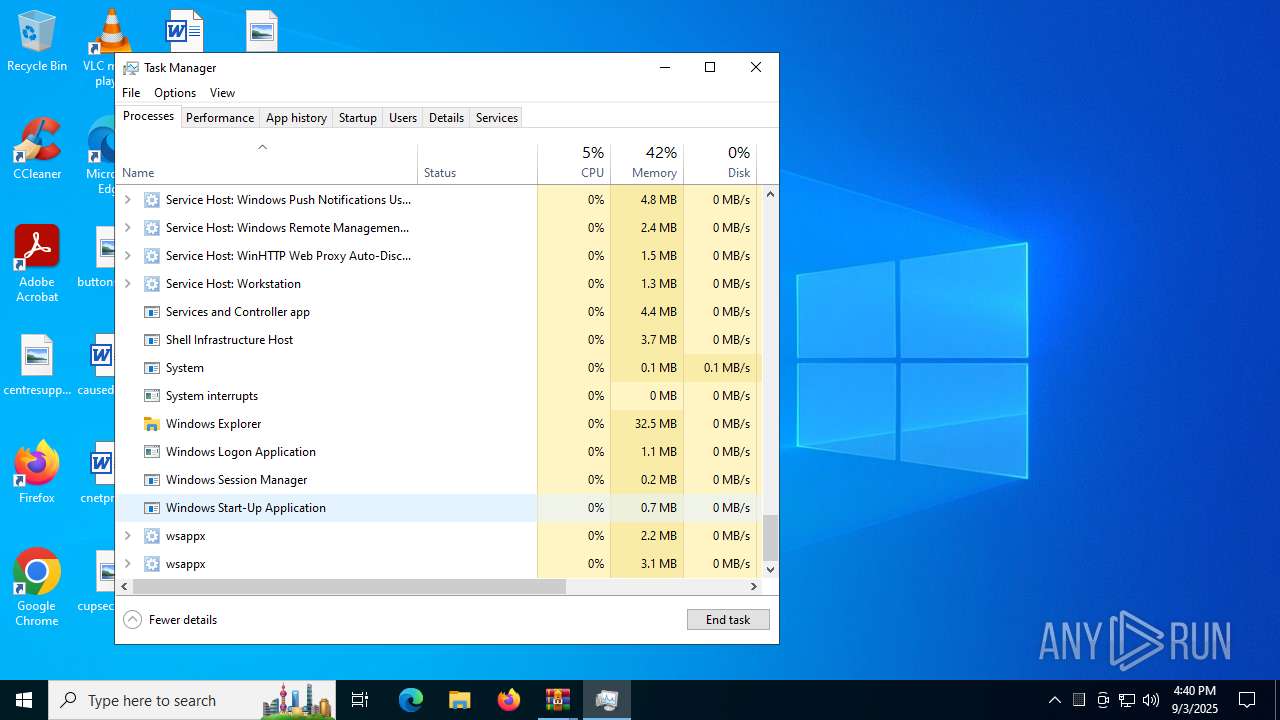
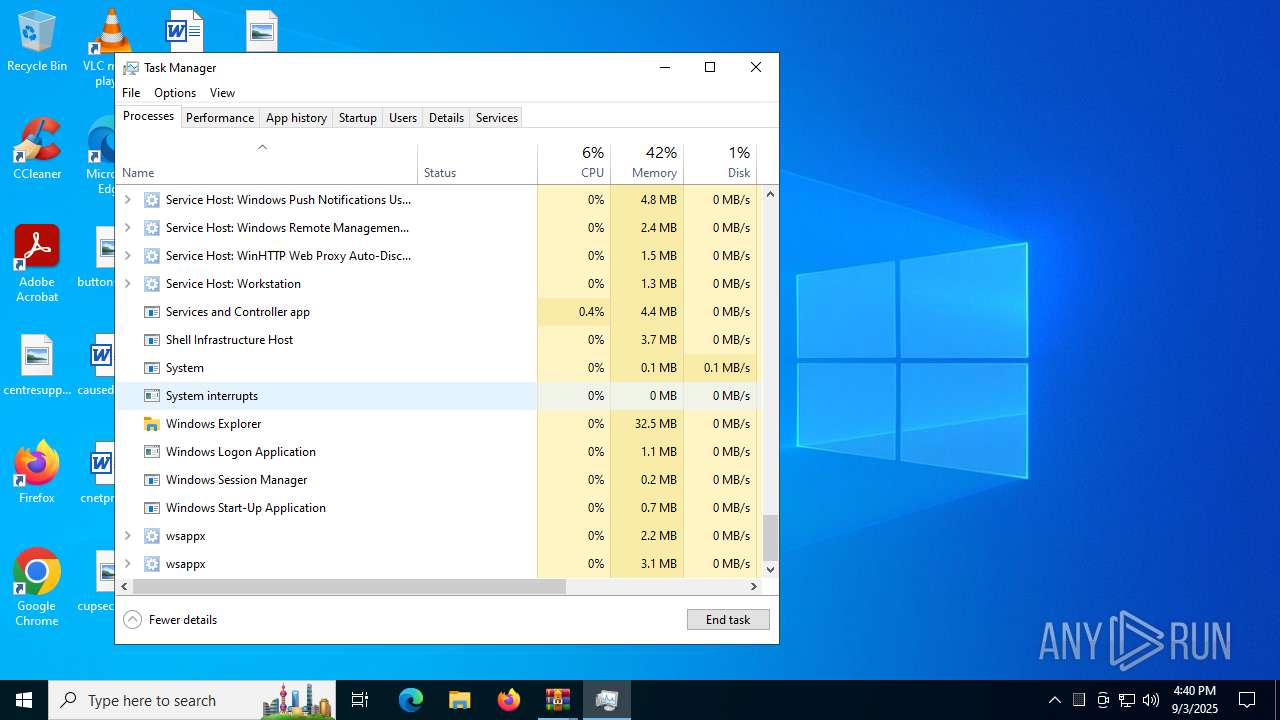
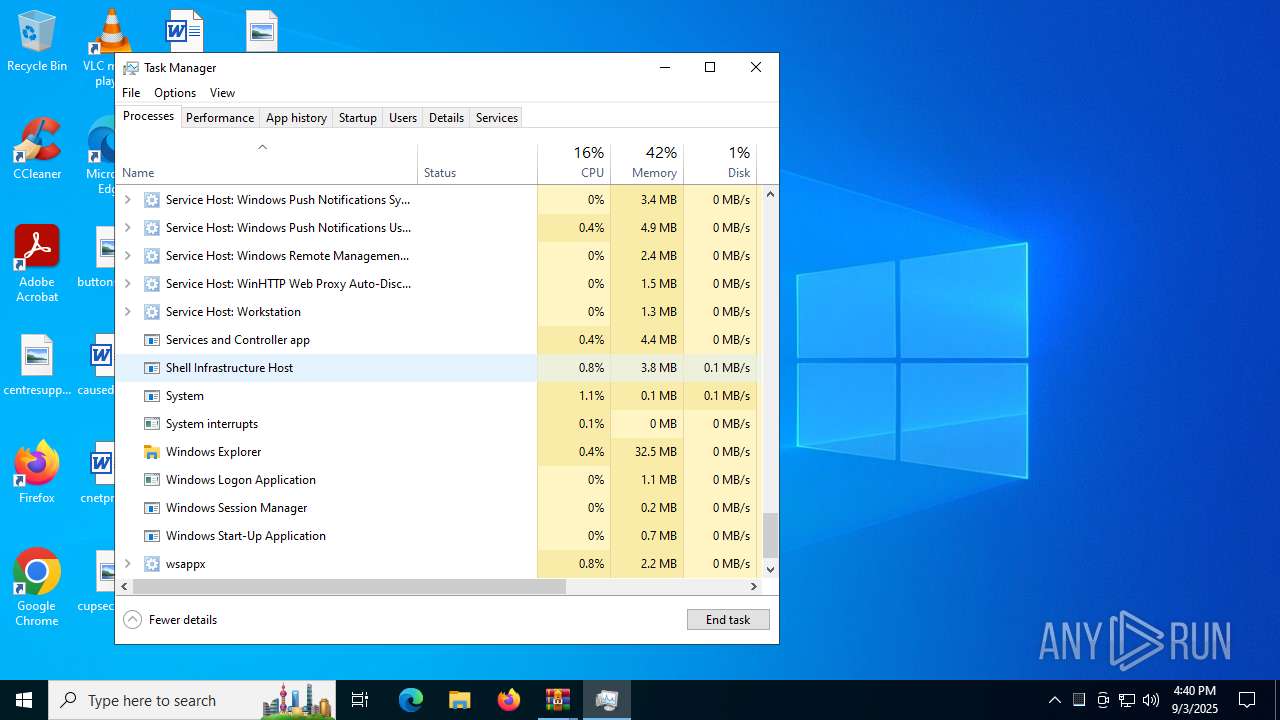
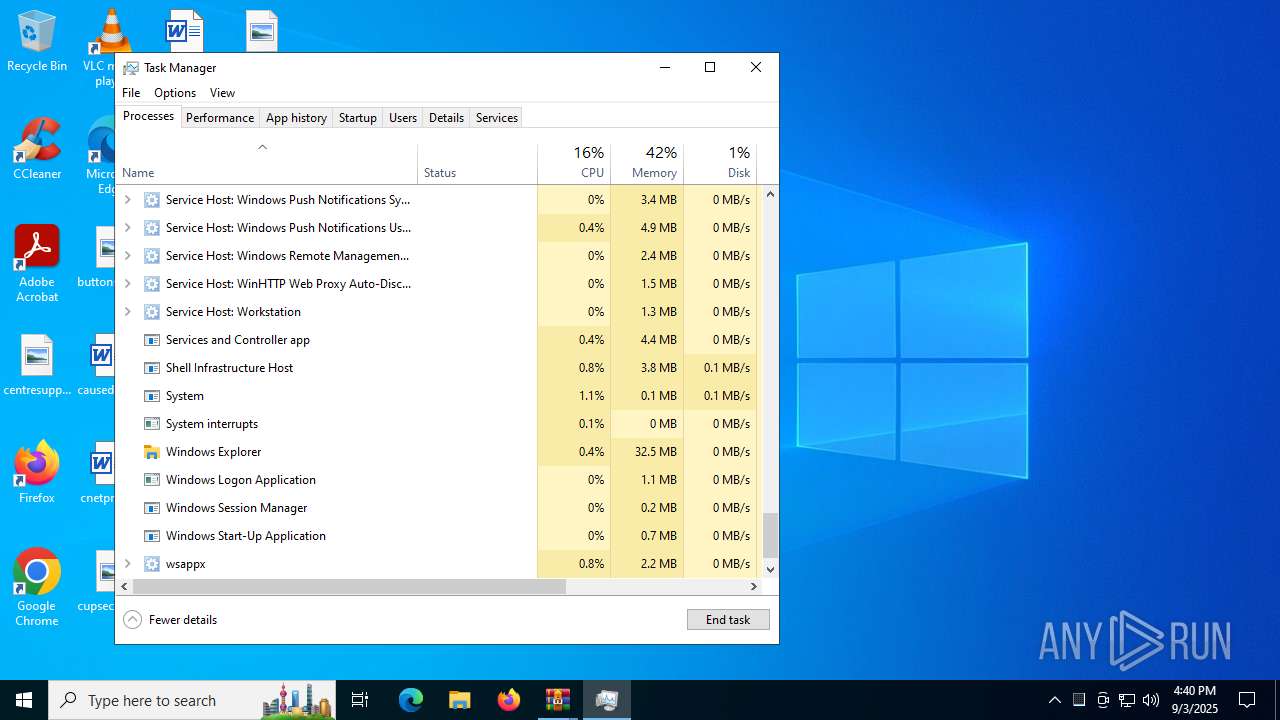
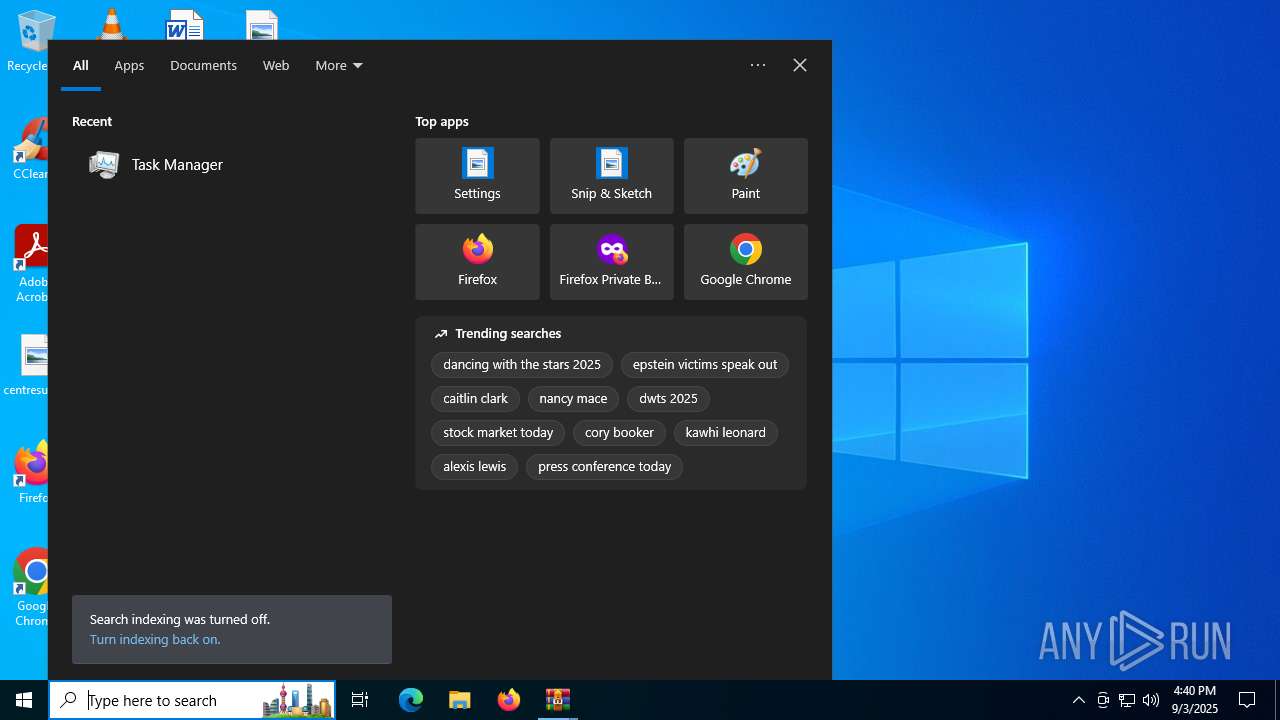
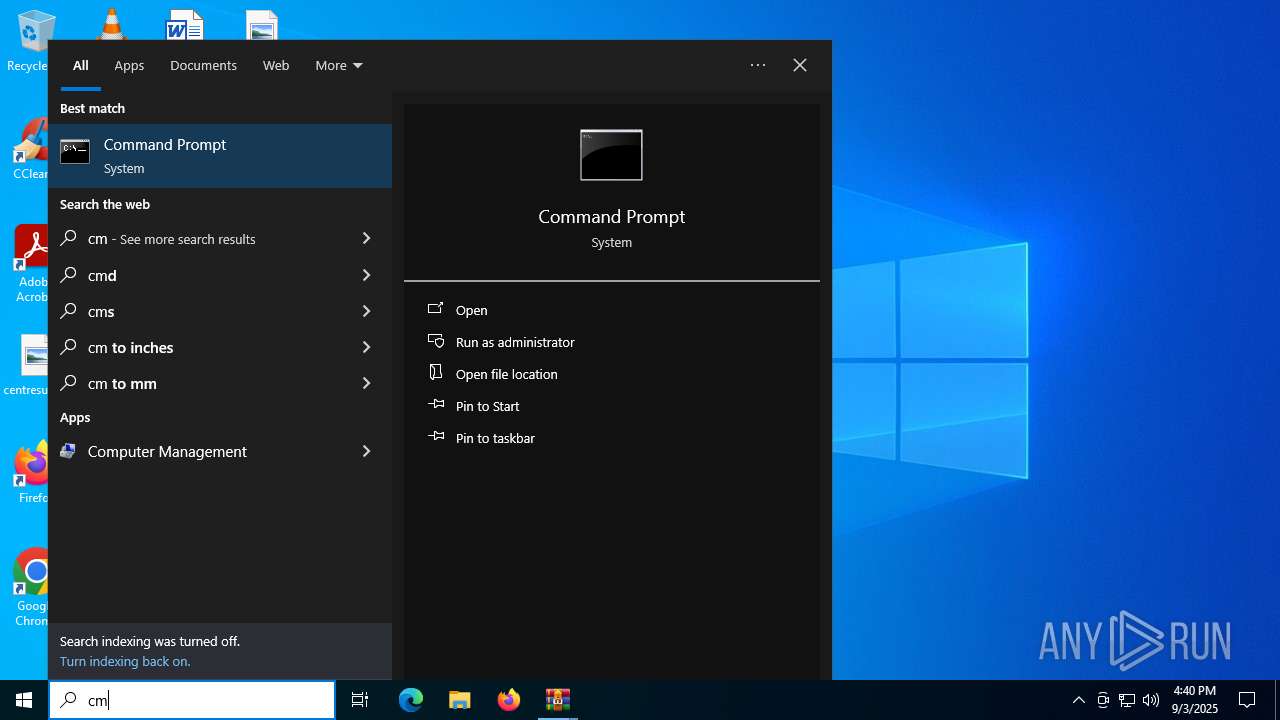
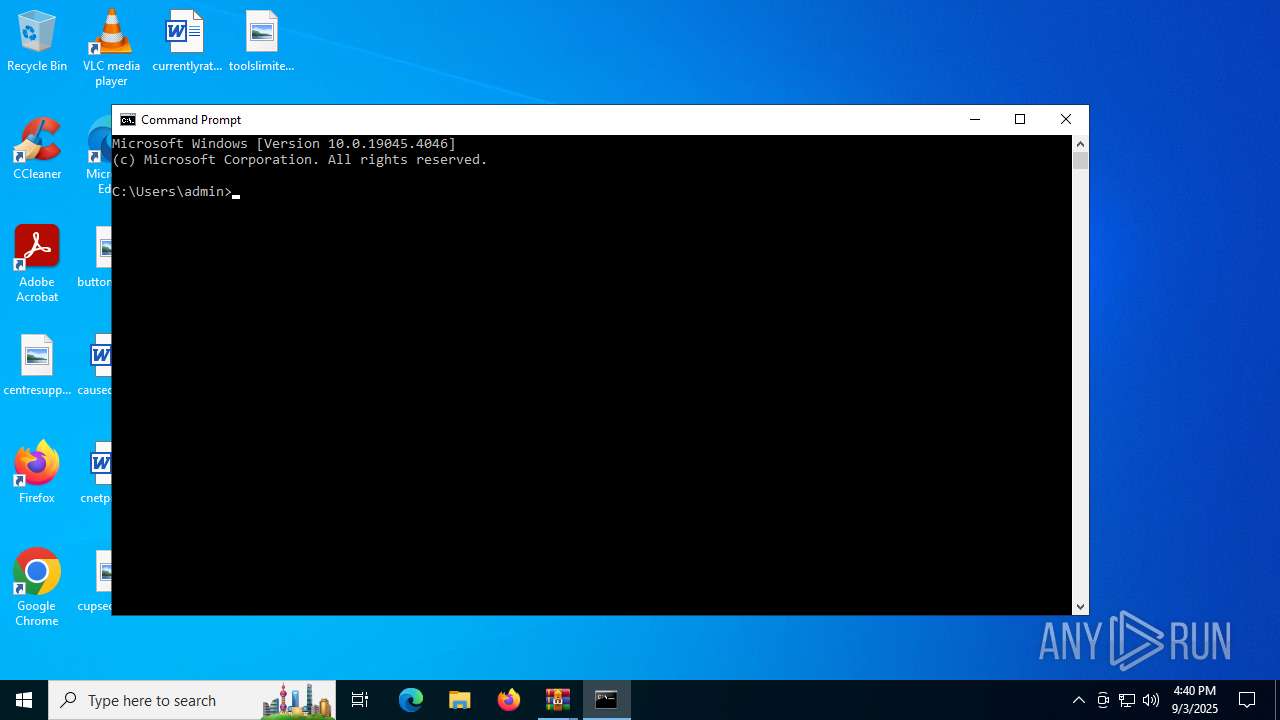
Manual execution by a user
- Taskmgr.exe (PID: 6232)
- Taskmgr.exe (PID: 2596)
- cmd.exe (PID: 4796)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
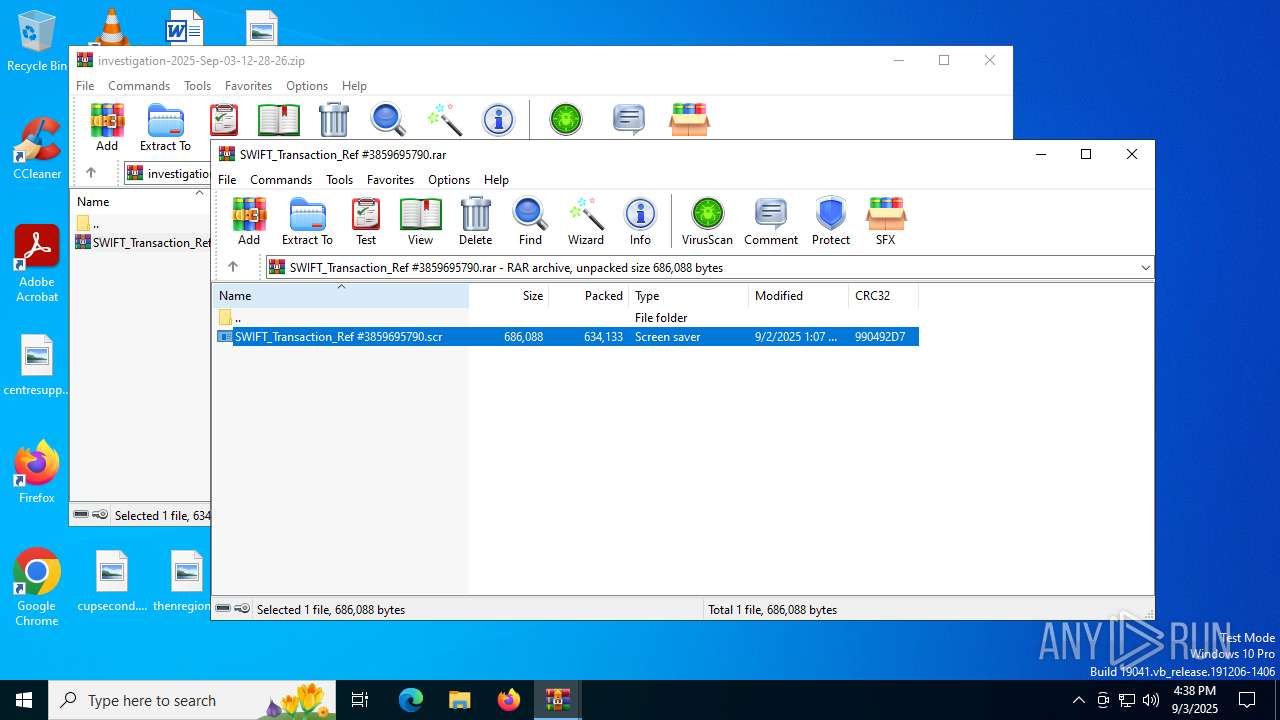
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:09:03 16:28:28 |
| ZipCRC: | 0x03d76c8c |
| ZipCompressedSize: | 634546 |
| ZipUncompressedSize: | 634339 |
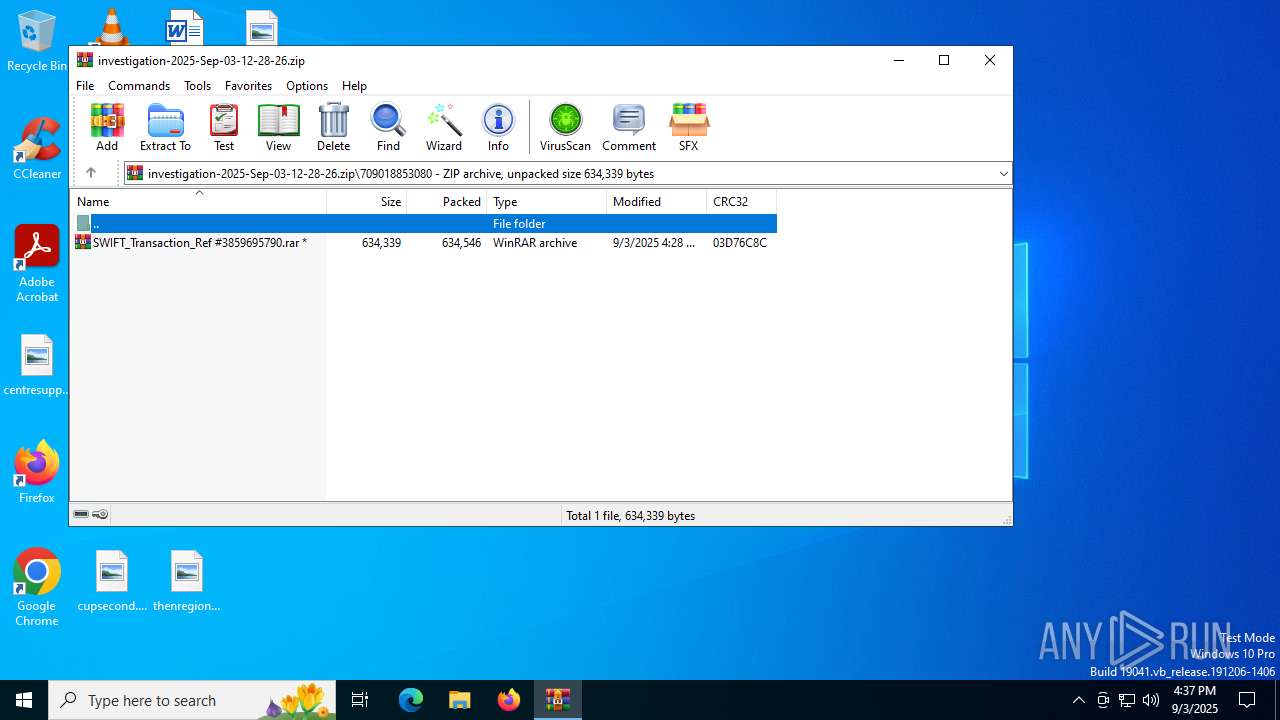
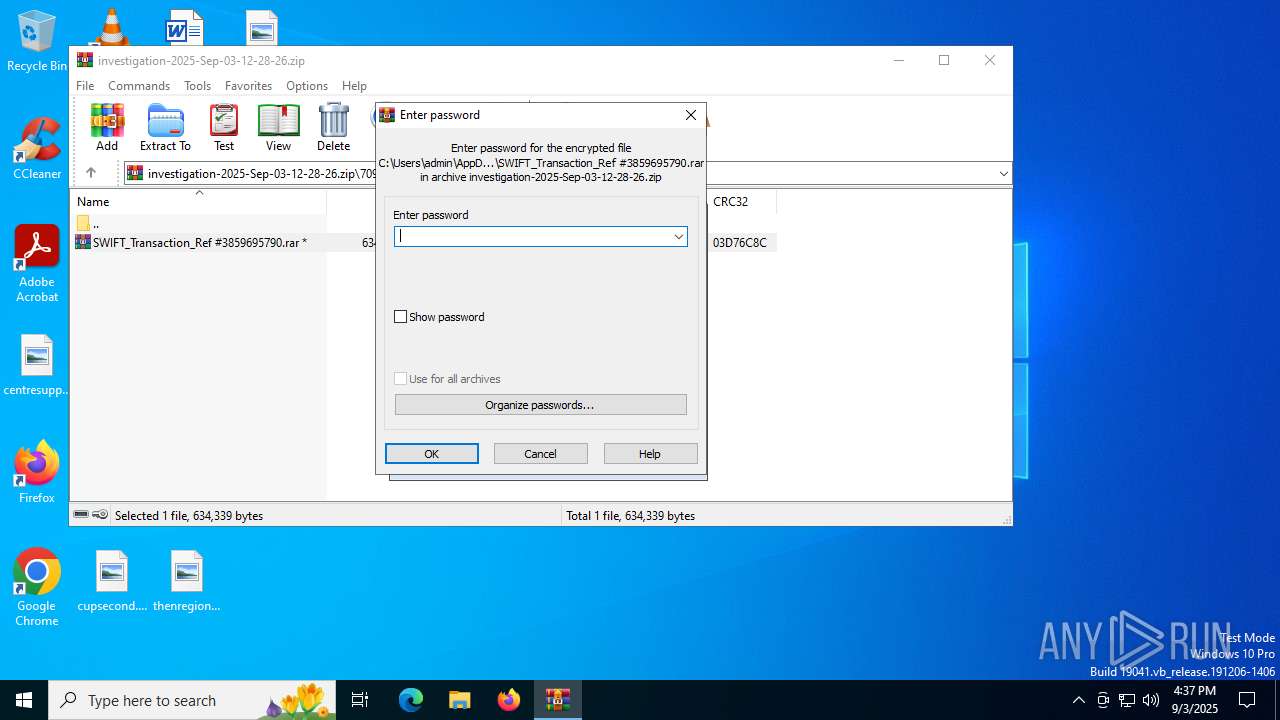
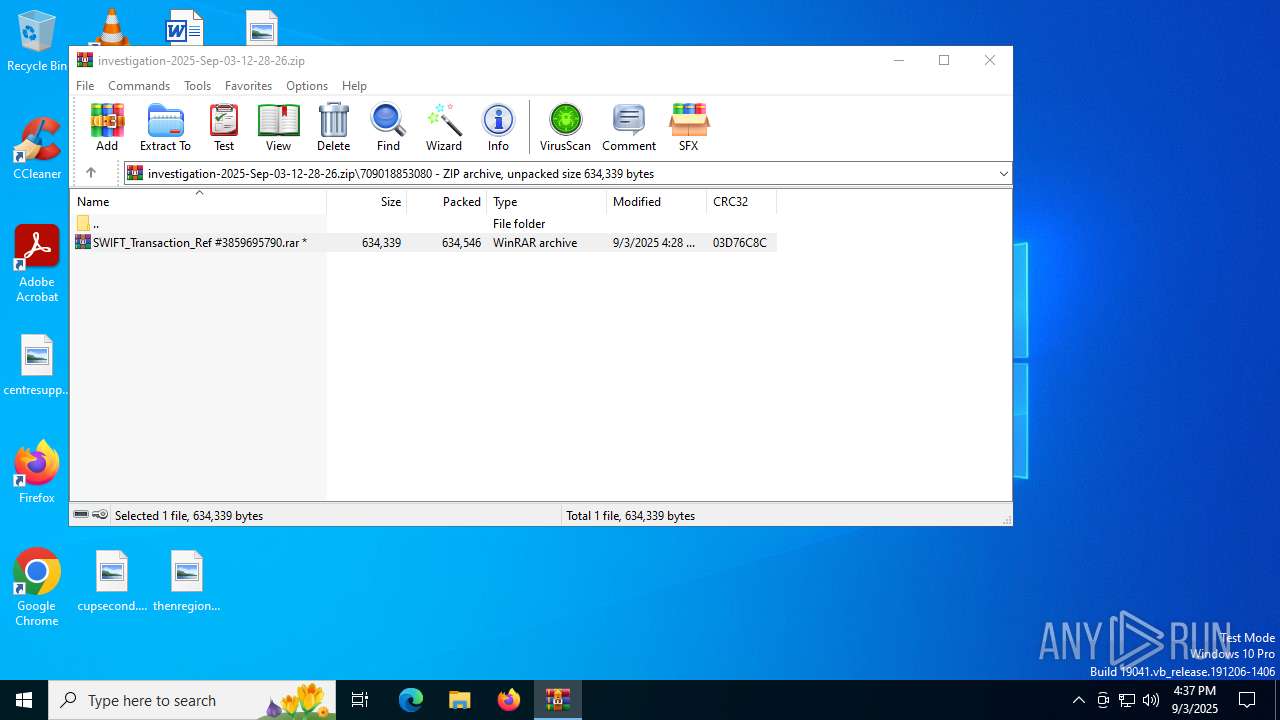
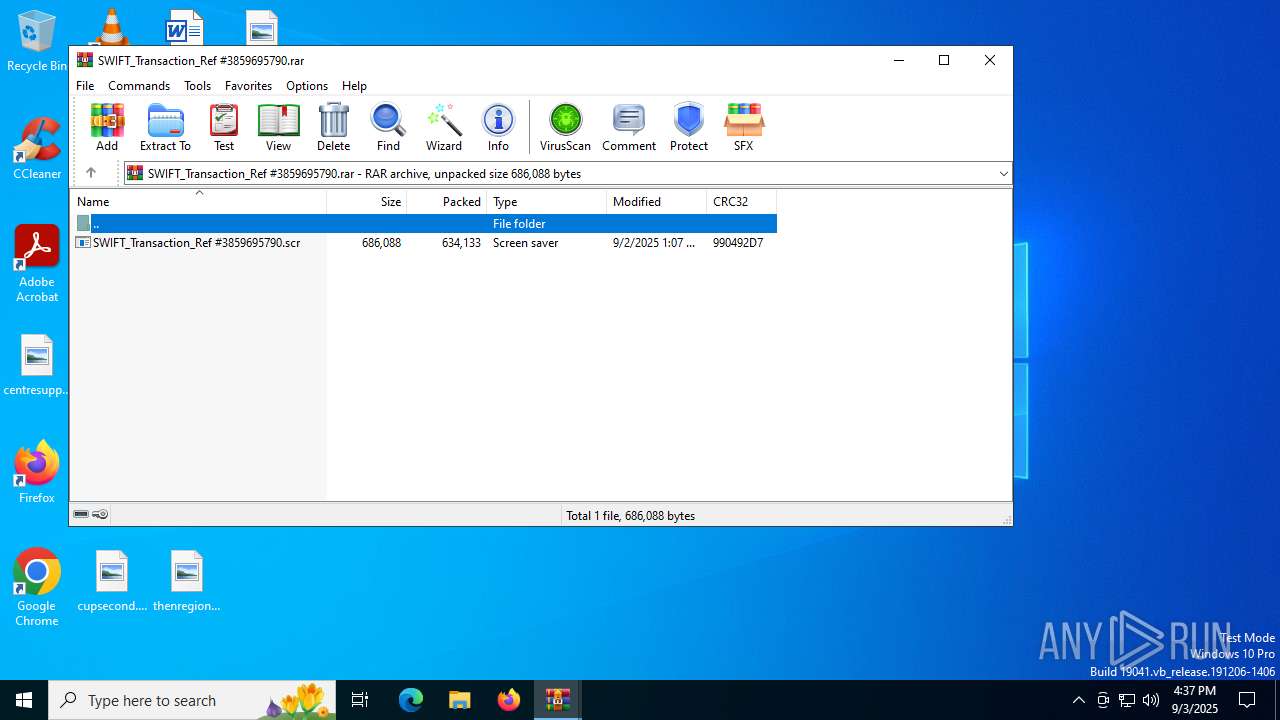
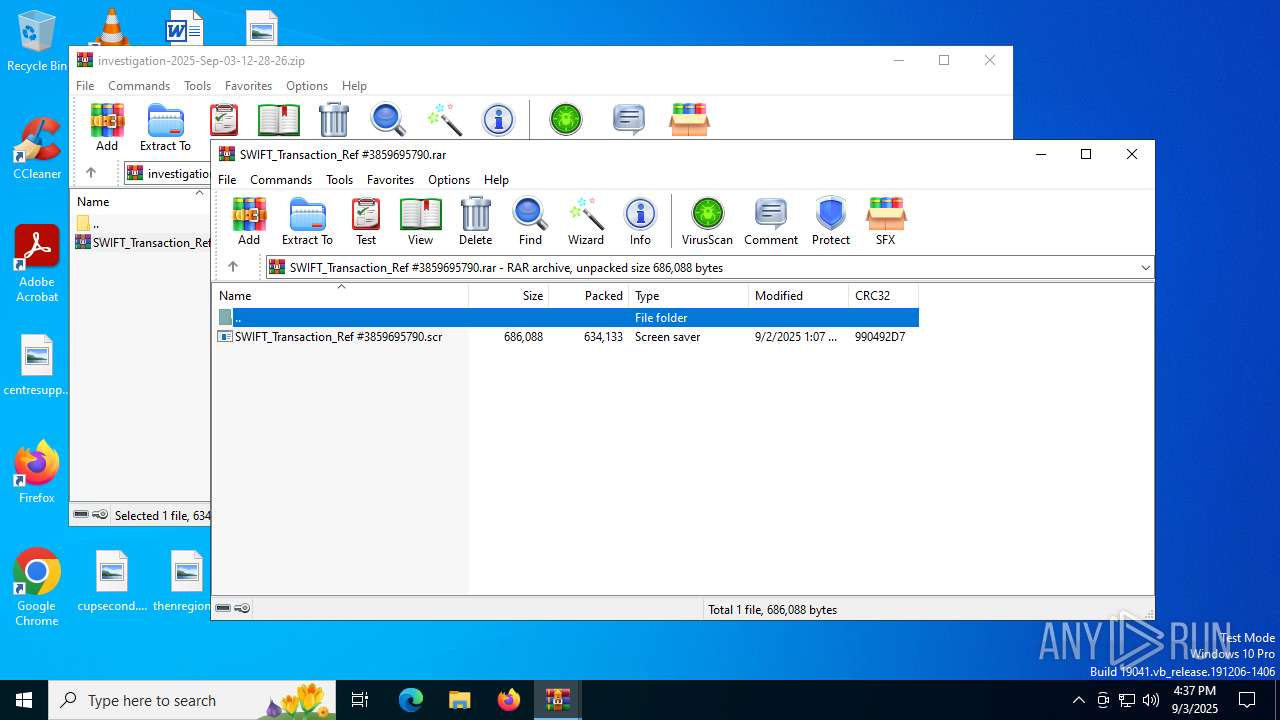
| ZipFileName: | 709018853080/SWIFT_Transaction_Ref #3859695790.rar |
Total processes
160
Monitored processes
15
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | — | SWIFT_Transaction_Ref #3859695790.scr | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1068 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
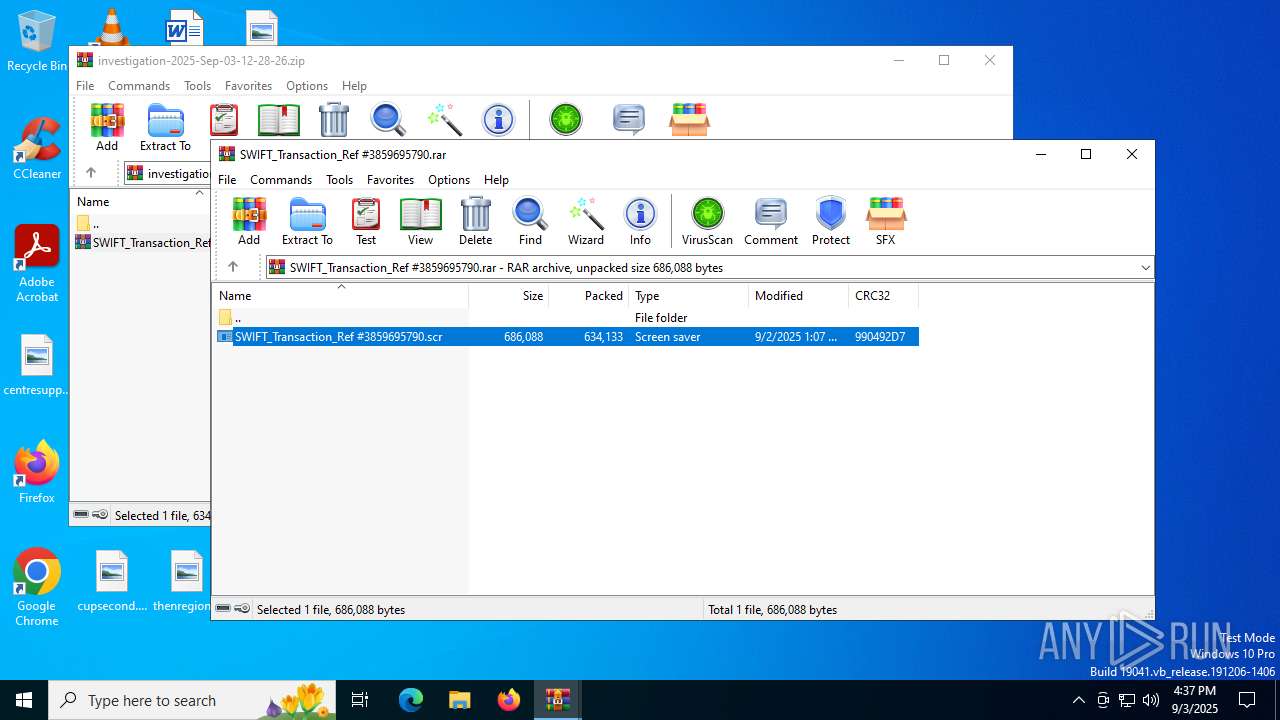
| 2148 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb5436.7102\SWIFT_Transaction_Ref #3859695790.rar" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2200 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | "C:\Users\admin\AppData\Local\Temp\Rar$DIa2148.8808\SWIFT_Transaction_Ref #3859695790.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIa2148.8808\SWIFT_Transaction_Ref #3859695790.scr | — | WinRAR.exe | |||||||||||
User: admin Company: plc Integrity Level: MEDIUM Description: tie Exit code: 0 Version: 9.8.7.7 Modules
| |||||||||||||||
| 2380 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegSvcs.exe | SWIFT_Transaction_Ref #3859695790.scr | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Services Installation Utility Exit code: 4294967295 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2596 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4796 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5328 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
19 322
Read events
19 171
Write events
147
Delete events
4
Modification events
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\investigation-2025-Sep-03-12-28-26.zip | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
2
Suspicious files
45
Text files
59
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5436 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb5436.7102\SWIFT_Transaction_Ref #3859695790.rar | compressed | |
MD5:CF4336C86786F104295618BB94F2B882 | SHA256:BFDF50E9C82A2342F34C87D4D4F0889B225712B67C4A4DC6908D50EF49F85284 | |||
| 2148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2148.12866\SWIFT_Transaction_Ref #3859695790.scr | executable | |
MD5:EDBEEEB51BB7FBF3BDB3C68822CD8FCC | SHA256:2370E9E62DD1194C6392BCDC8546F81FD57E6703E8C0A43B99E0D6EC7008CEEA | |||
| 2148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2148.8808\SWIFT_Transaction_Ref #3859695790.scr | executable | |
MD5:EDBEEEB51BB7FBF3BDB3C68822CD8FCC | SHA256:2370E9E62DD1194C6392BCDC8546F81FD57E6703E8C0A43B99E0D6EC7008CEEA | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:BE9FB01A72584F0252ADDD08D392A933 | SHA256:880ADD20F24F0A0955BC8F6B6450C89E970791C0D731A8082FB356D783FA659E | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\TokenBroker\Cache\fbaf94e759052658216786bfbabcdced1b67a5c2.tbres | binary | |
MD5:85A454196DBDC230D9F1937E24AD1BB7 | SHA256:87DE786C1F45EAC7CAB8916DE0ABD0DEC8FFBE1082E27527561475C0498CCDED | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:5A89564998B2E3EAD8617D9DE77E2AC3 | SHA256:87E89B9D303735B5699142268AB66479178A8244B4062DC1D3CE74B193B163DD | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\FgBbpIj0thGWZOh_xFnM9i4O7ek[1].css | text | |
MD5:A889E641E8C039E7DECE507C66252CFB | SHA256:2B7361D1E68D55F6B798BDB253C816F52F948407A57C693E0790208682B8F542 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:1CFF5851F3546DE2CD9DDFDF303122D3 | SHA256:9E43D91350C020EC06C332B53028D3C53682F37B15D51D9E4D4250024D42FCE4 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\Init[1].htm | html | |
MD5:9882FC423E9FFB37ECCCE09CE627248E | SHA256:B4DC7EAEFB519AE060C99F1ADA6216224C086095375A58D6F474266954757078 | |||
| 5328 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\AppCache\5Y734AMR\77\mNTNSYmdkpZ8dkFq4cRJ9JsSlUg[1].css | text | |
MD5:ECC90671847B6A414DA9EA655B823A2D | SHA256:7A495595200086ED5C000AAA2940DF40F0DCB73E47050E8CDD671682ACD279E0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
51
DNS requests
48
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | DE | binary | 471 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | DE | binary | 471 b | whitelisted |
4892 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
6648 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6648 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
2380 | RegSvcs.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 6 b | whitelisted |
3488 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
472 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4892 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4892 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
ip-api.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2200 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
2380 | RegSvcs.exe | A Network Trojan was detected | ET MALWARE Common Stealer Behavior - Source IP Associated with Hosting Provider Check via ip.api .com |
2380 | RegSvcs.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2380 | RegSvcs.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2380 | RegSvcs.exe | A Network Trojan was detected | ET MALWARE AgentTesla Exfil via FTP |
2380 | RegSvcs.exe | Misc activity | INFO [ANY.RUN] FTP protocol command for uploading a file |
2380 | RegSvcs.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |
2380 | RegSvcs.exe | A Network Trojan was detected | ET MALWARE Agent Tesla CnC Exfil via TCP |
2380 | RegSvcs.exe | A Network Trojan was detected | STEALER [ANY.RUN] AgentTesla Exfiltration (raw TCP) |