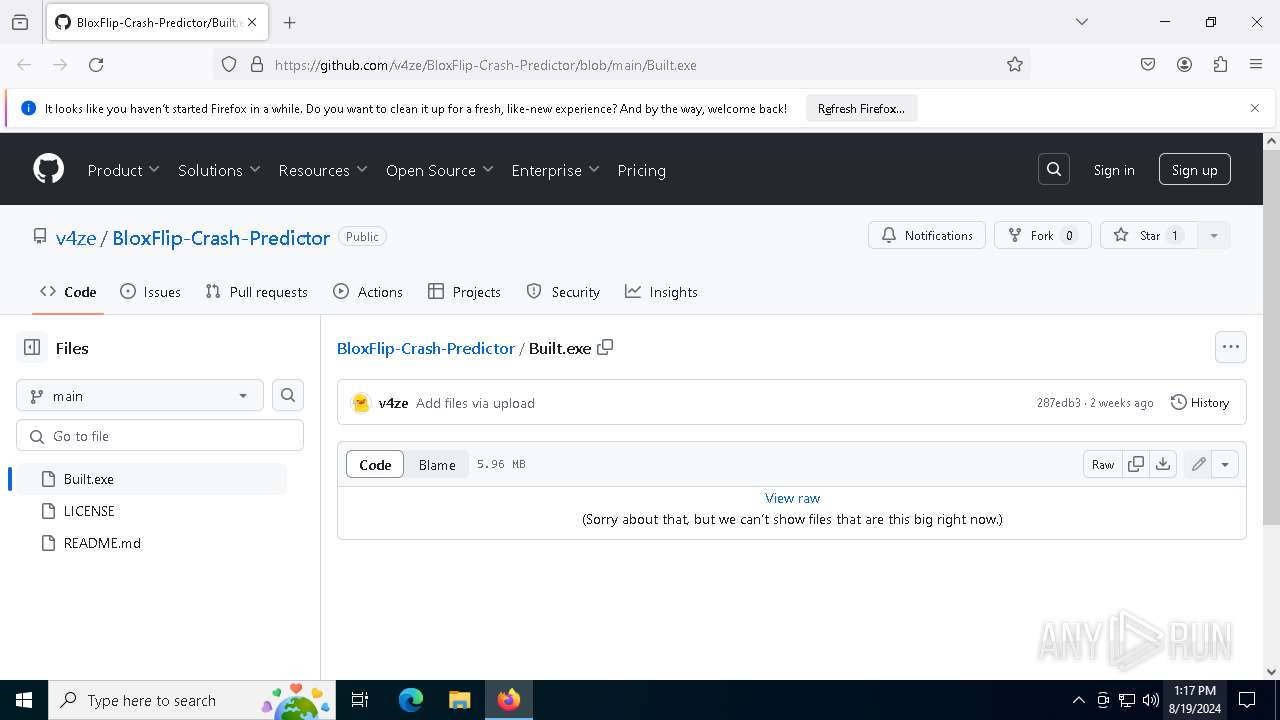
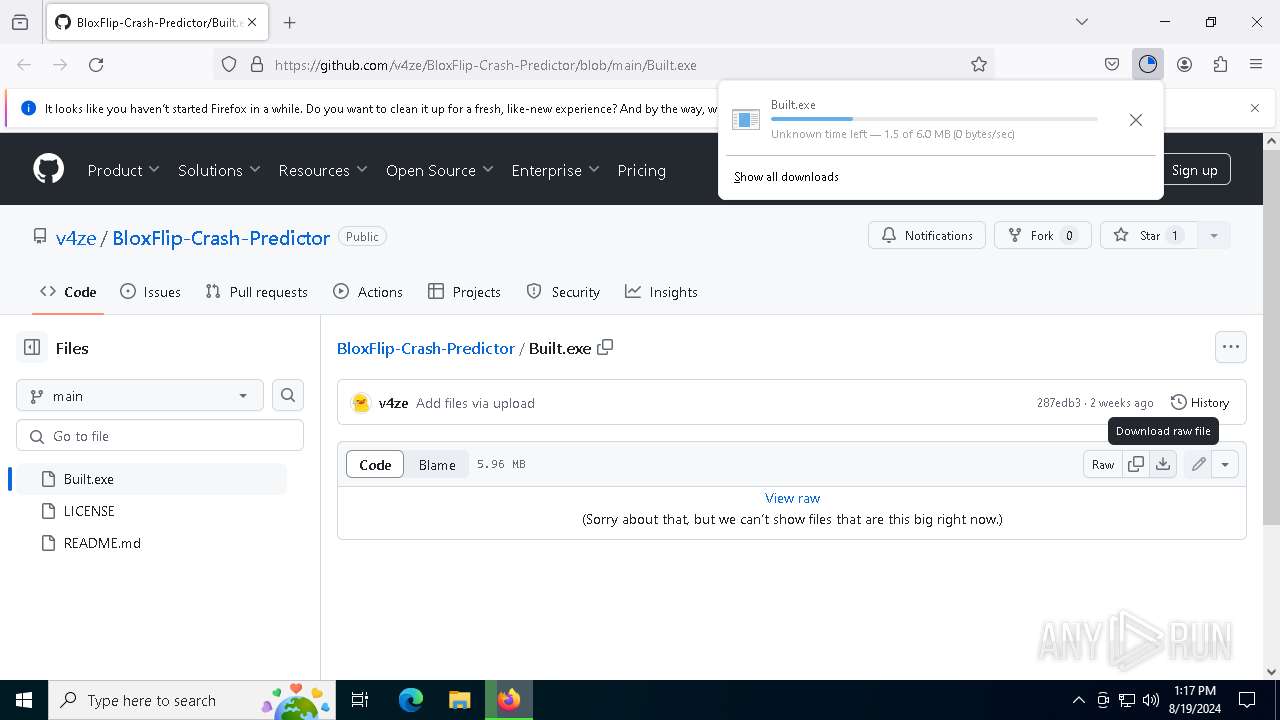
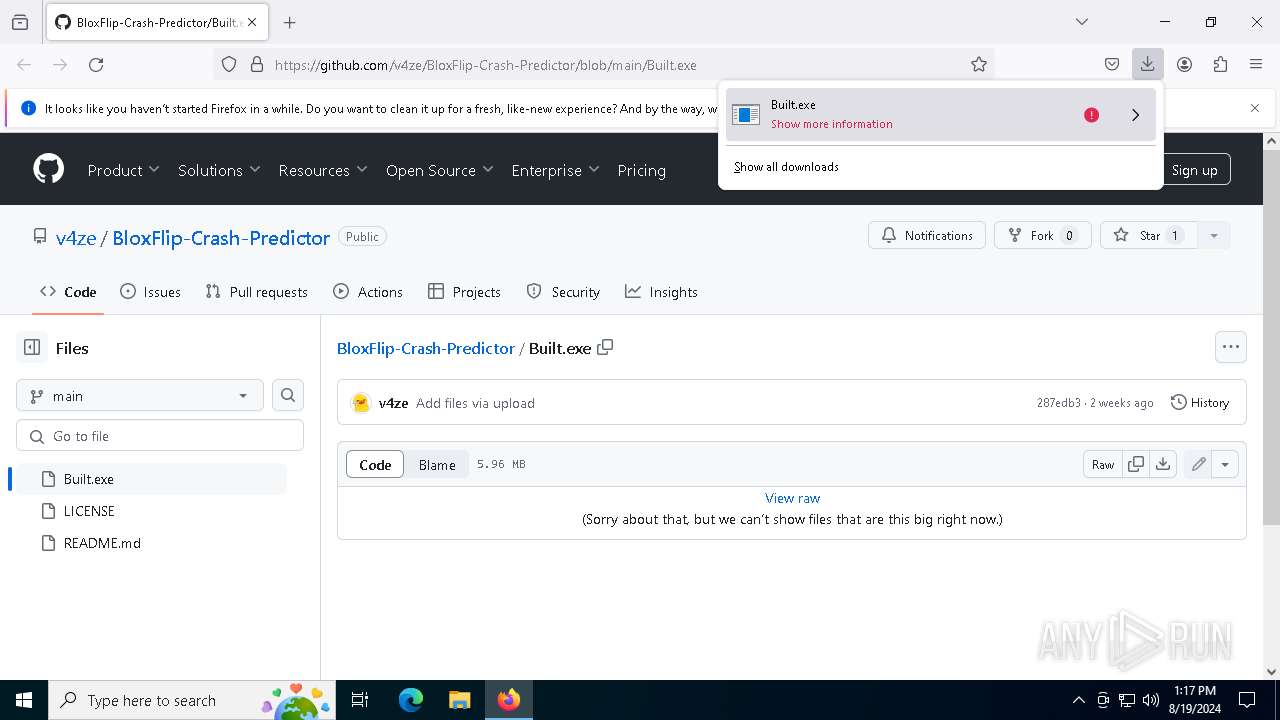
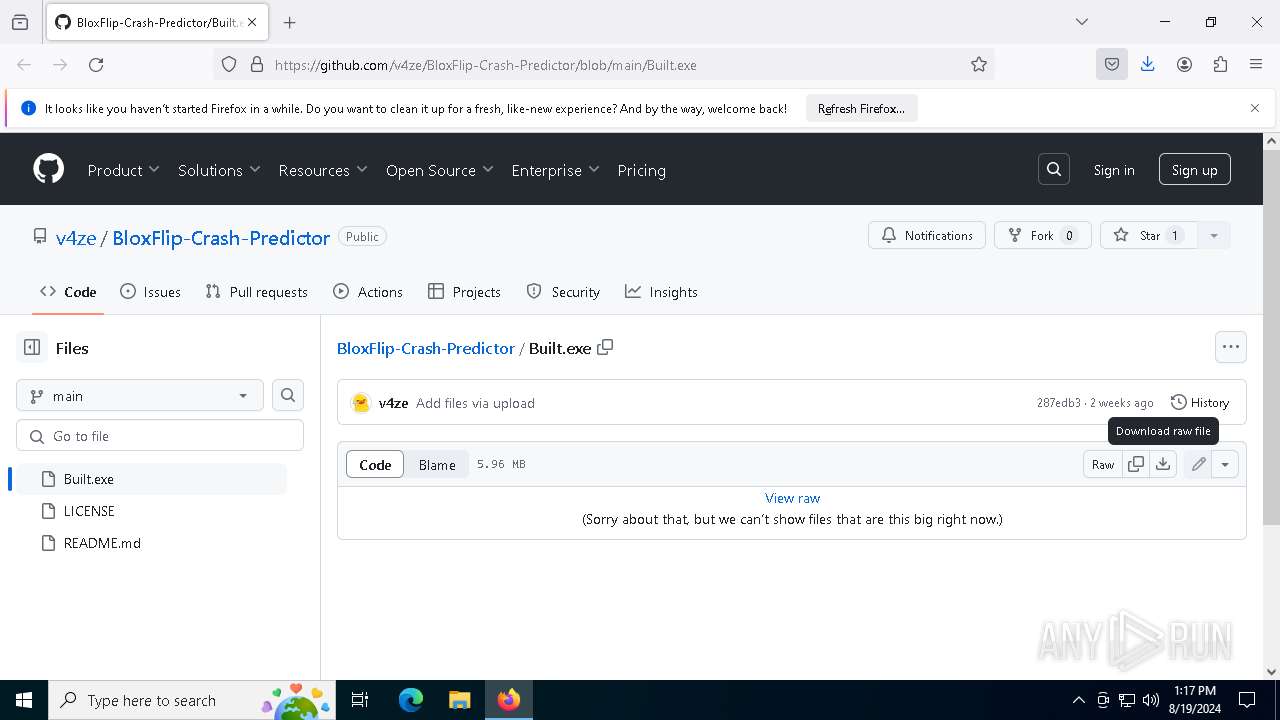
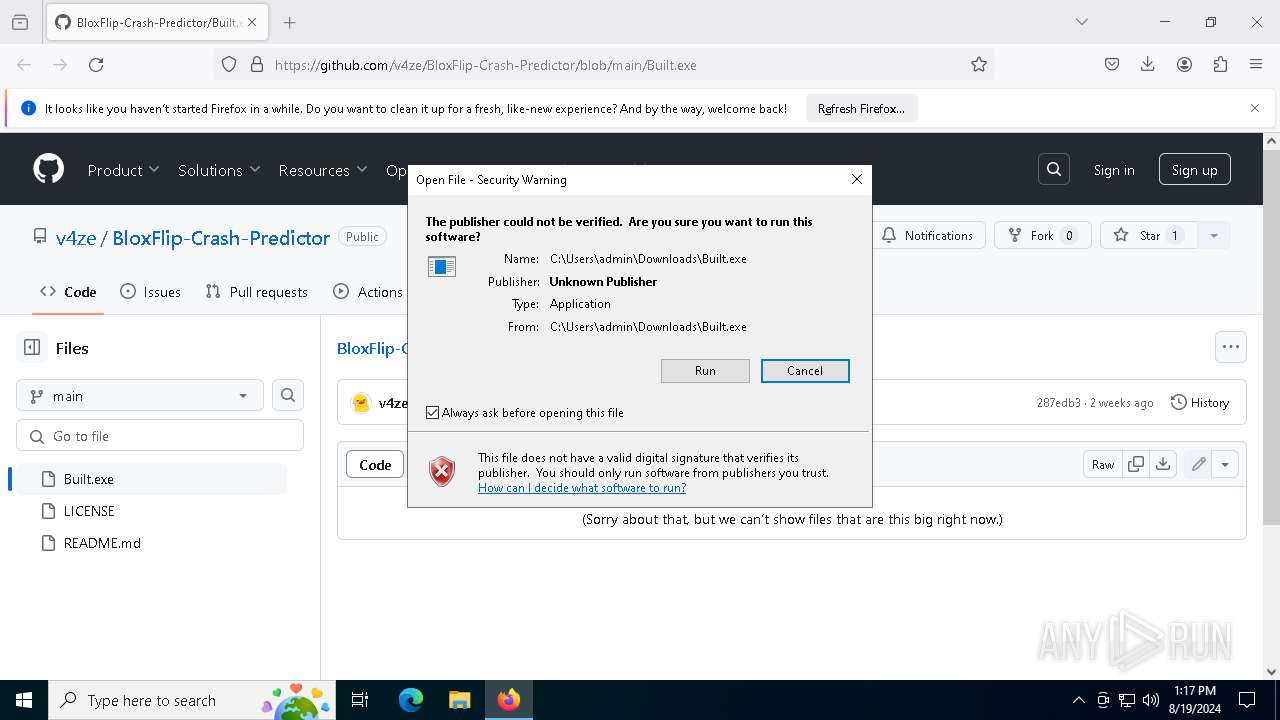
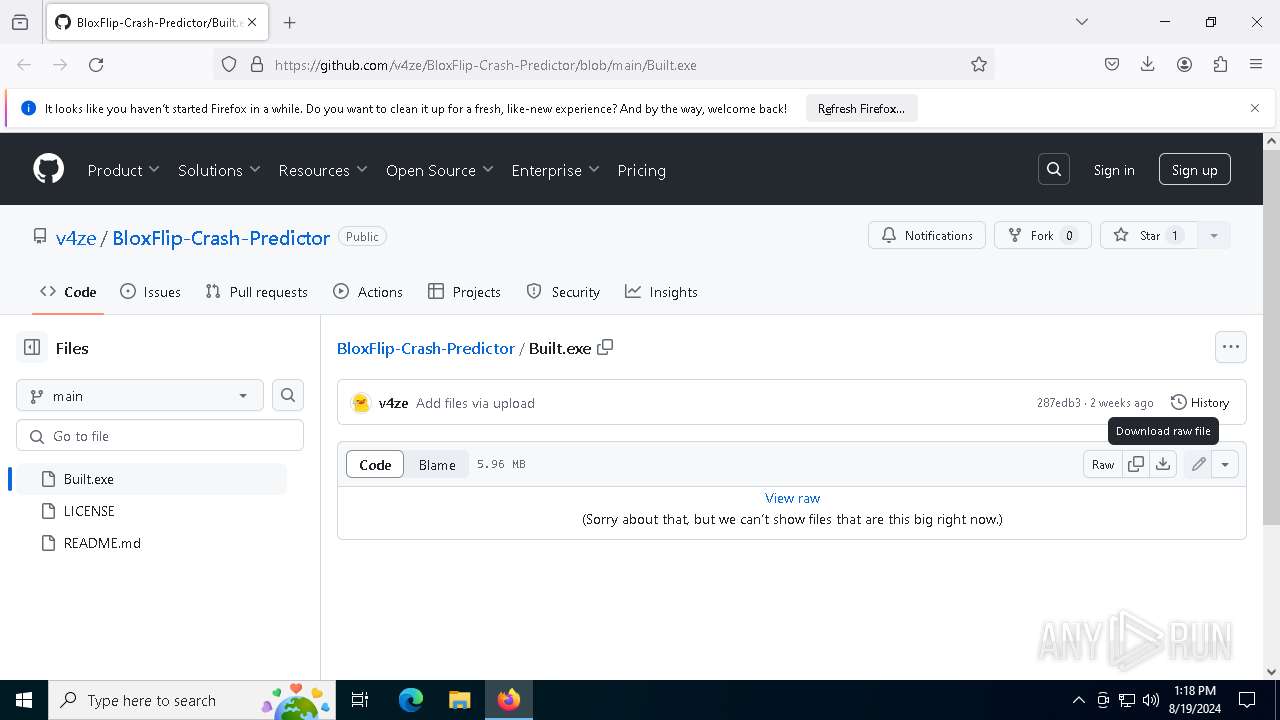
| URL: | https://github.com/v4ze/BloxFlip-Crash-Predictor/blob/main/Built.exe |
| Full analysis: | https://app.any.run/tasks/14972541-3e1b-484b-b32d-5563ce62e675 |
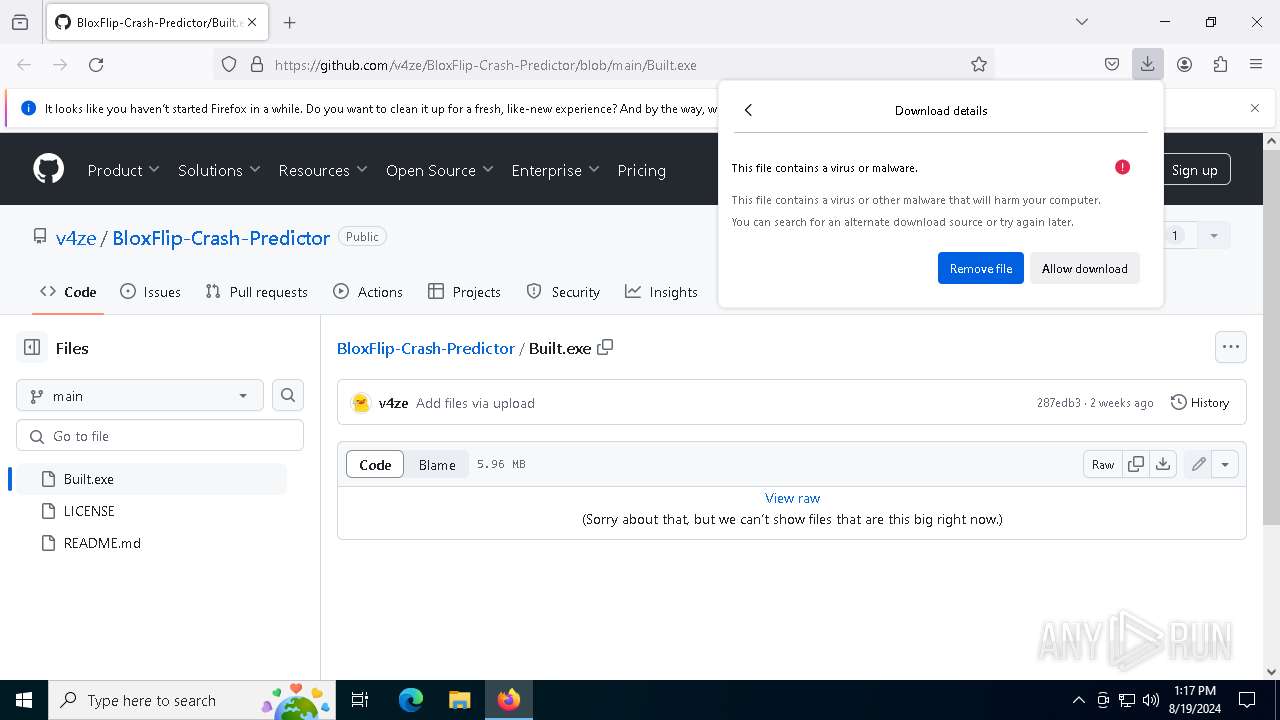
| Verdict: | Malicious activity |
| Threats: | Blank Grabber is an infostealer written in Python. It is designed to steal a wide array of data, such as browser login credentials, crypto wallets, Telegram sessions, and Discord tokens. It is an open-source malware, with its code available on GitHub and regularly receiving updates. Blank Grabber builder’s simple interface lets threat actors even with basic skills to deploy it and conduct attacks. |
| Analysis date: | August 19, 2024, 13:17:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1CA8867C32656169D35C7FC93FB7A34B |
| SHA1: | C27069DF0C795D4841B9154C3433D322D3846067 |
| SHA256: | 8A75143A60E9116995E160ED58872DABB3E2747F113529C9BBBDCC9ADE9AC917 |
| SSDEEP: | 3:N8tEdjRoKEfRg7sXTERZMAn:2ujCRg7sjsfn |
MALICIOUS
BlankGrabber has been detected
- Built.exe (PID: 8100)
- Built.exe (PID: 6572)
Adds path to the Windows Defender exclusion list
- Built.exe (PID: 7252)
- cmd.exe (PID: 6628)
Antivirus name has been found in the command line (generic signature)
- cmd.exe (PID: 6544)
- MpCmdRun.exe (PID: 8068)
Windows Defender preferences modified via 'Set-MpPreference'
- cmd.exe (PID: 6544)
Actions looks like stealing of personal data
- Built.exe (PID: 7252)
Bypass execution policy to execute commands
- powershell.exe (PID: 8288)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 8016)
DISCORDGRABBER has been detected (YARA)
- Built.exe (PID: 7252)
GROWTOPIA has been detected (YARA)
- Built.exe (PID: 7252)
UMBRALSTEALER has been detected (YARA)
- Built.exe (PID: 7252)
Stealers network behavior
- Built.exe (PID: 7252)
BLANKGRABBER has been detected (SURICATA)
- Built.exe (PID: 7252)
SUSPICIOUS
Process drops legitimate windows executable
- firefox.exe (PID: 6660)
- Built.exe (PID: 8100)
- Built.exe (PID: 6572)
Executable content was dropped or overwritten
- Built.exe (PID: 8100)
- Built.exe (PID: 6572)
- csc.exe (PID: 1812)
Drops the executable file immediately after the start
- Built.exe (PID: 8100)
- Built.exe (PID: 6572)
- csc.exe (PID: 1812)
The process drops C-runtime libraries
- Built.exe (PID: 8100)
- Built.exe (PID: 6572)
Process drops python dynamic module
- Built.exe (PID: 8100)
- Built.exe (PID: 6572)
Application launched itself
- Built.exe (PID: 8100)
- Built.exe (PID: 8164)
- Built.exe (PID: 6572)
Loads Python modules
- Built.exe (PID: 8164)
- Built.exe (PID: 7252)
Reads the date of Windows installation
- Built.exe (PID: 8164)
Reads security settings of Internet Explorer
- Built.exe (PID: 8164)
Starts CMD.EXE for commands execution
- Built.exe (PID: 7252)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 6628)
Found strings related to reading or modifying Windows Defender settings
- Built.exe (PID: 7252)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6628)
- cmd.exe (PID: 6544)
- cmd.exe (PID: 3840)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7336)
- cmd.exe (PID: 7592)
Script disables Windows Defender's IPS
- cmd.exe (PID: 6544)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 6544)
Get information on the list of running processes
- cmd.exe (PID: 7712)
- Built.exe (PID: 7252)
- cmd.exe (PID: 4760)
- cmd.exe (PID: 7912)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 8008)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 400)
- cmd.exe (PID: 9088)
Starts application with an unusual extension
- cmd.exe (PID: 1556)
- cmd.exe (PID: 8400)
- cmd.exe (PID: 8724)
- cmd.exe (PID: 8600)
- cmd.exe (PID: 8928)
- cmd.exe (PID: 9060)
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 7380)
Base64-obfuscated command line is found
- cmd.exe (PID: 8016)
Accesses antivirus product name via WMI (SCRIPT)
- WMIC.exe (PID: 3412)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 8016)
BASE64 encoded PowerShell command has been detected
- cmd.exe (PID: 8016)
The executable file from the user directory is run by the CMD process
- rar.exe (PID: 3992)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 8768)
Accesses operating system name via WMI (SCRIPT)
- WMIC.exe (PID: 8748)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 8948)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 8324)
Uses WMIC.EXE to obtain a list of video controllers
- cmd.exe (PID: 8856)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 8016)
Checks for external IP
- Built.exe (PID: 7252)
- svchost.exe (PID: 2256)
INFO
Application launched itself
- firefox.exe (PID: 6660)
- firefox.exe (PID: 6640)
Reads Microsoft Office registry keys
- firefox.exe (PID: 6660)
The process uses the downloaded file
- firefox.exe (PID: 6660)
- Built.exe (PID: 8164)
Executable content was dropped or overwritten
- firefox.exe (PID: 6660)
Checks supported languages
- Built.exe (PID: 8100)
- Built.exe (PID: 8164)
- Built.exe (PID: 6572)
- Built.exe (PID: 7252)
- tree.com (PID: 7864)
- tree.com (PID: 8552)
- tree.com (PID: 8672)
- tree.com (PID: 8872)
- tree.com (PID: 9008)
- csc.exe (PID: 1812)
- cvtres.exe (PID: 8432)
- tree.com (PID: 9116)
- MpCmdRun.exe (PID: 8068)
- rar.exe (PID: 3992)
Reads the computer name
- Built.exe (PID: 8100)
- Built.exe (PID: 8164)
- Built.exe (PID: 6572)
- Built.exe (PID: 7252)
- MpCmdRun.exe (PID: 8068)
Create files in a temporary directory
- Built.exe (PID: 8100)
- Built.exe (PID: 8164)
- Built.exe (PID: 6572)
- Built.exe (PID: 7252)
- csc.exe (PID: 1812)
- cvtres.exe (PID: 8432)
- MpCmdRun.exe (PID: 8068)
- rar.exe (PID: 3992)
Reads the machine GUID from the registry
- Built.exe (PID: 8164)
- Built.exe (PID: 7252)
- csc.exe (PID: 1812)
- rar.exe (PID: 3992)
Process checks computer location settings
- Built.exe (PID: 8164)
The Powershell gets current clipboard
- powershell.exe (PID: 6604)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 3412)
- WMIC.exe (PID: 8748)
- WMIC.exe (PID: 9112)
- WMIC.exe (PID: 8324)
- WMIC.exe (PID: 8016)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 1372)
- powershell.exe (PID: 6268)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6268)
- powershell.exe (PID: 1372)
PyInstaller has been detected (YARA)
- Built.exe (PID: 6572)
- Built.exe (PID: 7252)
Displays MAC addresses of computer network adapters
- getmac.exe (PID: 8504)
Found Base64 encoded reflection usage via PowerShell (YARA)
- Built.exe (PID: 7252)
Attempting to use instant messaging service
- svchost.exe (PID: 2256)
- Built.exe (PID: 7252)
UPX packer has been detected
- Built.exe (PID: 7252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
237
Monitored processes
94
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 400 | C:\WINDOWS\system32\cmd.exe /c "WMIC /Node:localhost /Namespace:\\root\SecurityCenter2 Path AntivirusProduct Get displayName" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | powershell Get-ItemPropertyValue -Path 'HKLM:System\CurrentControlSet\Control\Session Manager\Environment' -Name PROCESSOR_IDENTIFIER | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1372 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\Downloads\Built.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | C:\WINDOWS\system32\cmd.exe /c "tree /A /F" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4488 -childID 2 -isForBrowser -prefsHandle 4480 -prefMapHandle 4476 -prefsLen 36263 -prefMapSize 244343 -jsInitHandle 1372 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d377c05b-e89b-40d7-a329-cfa8c5d1d269} 6660 "\\.\pipe\gecko-crash-server-pipe.6660" 1c15b33b850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5160 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 5184 -prefMapHandle 5188 -prefsLen 36339 -prefMapSize 244343 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {7c62e8eb-51aa-4800-bec7-6a90e861c554} 6660 "\\.\pipe\gecko-crash-server-pipe.6660" 1c15e543510 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 1812 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\pitga1i2\pitga1i2.cmdline" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1928 | netsh wlan show profile | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3176 | C:\WINDOWS\system32\cmd.exe /c "getmac" | C:\Windows\System32\cmd.exe | — | Built.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
68 376
Read events
68 322
Write events
53
Delete events
1
Modification events
| (PID) Process: | (6640) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: D86518FA00000000 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: 5C391AFA00000000 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (6660) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
Executable files
43
Suspicious files
194
Text files
70
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\AlternateServices.bin | binary | |
MD5:AD96ADC21745D300436EA6C167D6C722 | SHA256:B5DFB978CB8CF04FD3C6D192C62B0C8733B6E007C9801A3D32A8AC6B372683E2 | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:9DAE78AC7BCE8A98EE7E72E8E851862B | SHA256:786DC777D588B73B58FCE5837AB5B21BB03A34D89A02D1106094B440FC9A1A0C | |||
| 6660 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
105
DNS requests
137
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6660 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
6660 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
6660 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 95.101.54.99:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 95.101.54.99:80 | http://r11.o.lencr.org/ | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 142.250.186.163:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
6660 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
400 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4436 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6660 | firefox.exe | 34.117.188.166:443 | contile.services.mozilla.com | — | — | unknown |
6660 | firefox.exe | 140.82.121.4:443 | github.com | GITHUB | US | unknown |
6660 | firefox.exe | 172.217.18.10:443 | safebrowsing.googleapis.com | — | — | whitelisted |
6660 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
6660 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | — | — | unknown |
6660 | firefox.exe | 185.199.109.154:443 | github.githubassets.com | FASTLY | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
github.com |
| shared |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
prod.ads.prod.webservices.mozgcp.net |
| unknown |
ocsp.sectigo.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2256 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2256 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7252 | Built.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2256 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
7252 | Built.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
7252 | Built.exe | A Network Trojan was detected | STEALER [ANY.RUN] BlankGrabber (SkochGrabber) Generic External IP Check |