| File name: | 1.vbs |
| Full analysis: | https://app.any.run/tasks/38a35eec-5a2b-49c4-9763-afe97832d7fa |
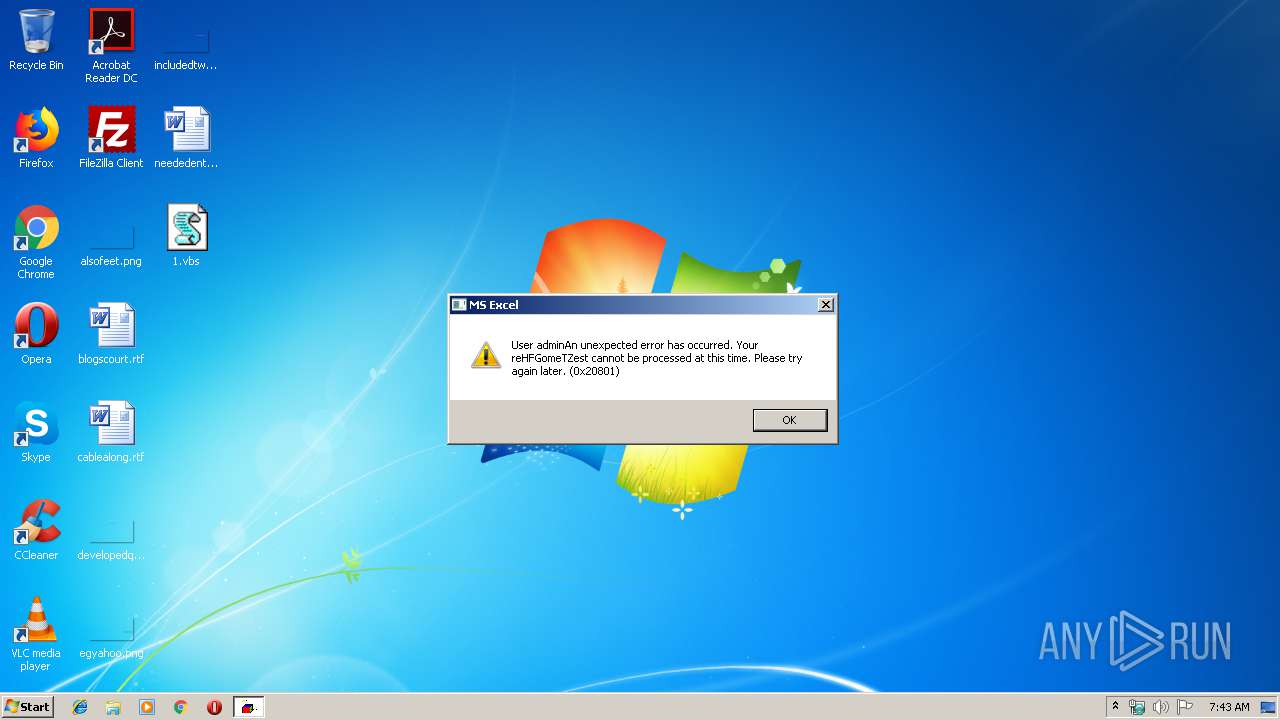
| Verdict: | Malicious activity |
| Threats: | Hancitor was created in 2014 to drop other malware on infected machines. It is also known as Tordal and Chanitor. This malware is available as a service which makes it accessible tools to criminals and contributes to the popularity of this virus. |
| Analysis date: | October 29, 2019, 07:43:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 52A564FDC56159AE75D452B1B6C7531B |
| SHA1: | 9AEA2603D0EB9B35938CAB75A16C9F9AC9DB9968 |
| SHA256: | 8A1ABC957B238640D6F965FFD89BFF1CCB2521DB5148C2C3DC799A6E8911EA33 |
| SSDEEP: | 6144:oSzOZSe211OyXAARZsPluJzh4A3XHsM/838aZZ3w1kfN5fG6XoOau/gqWKwcJpmb:HJPSoT/shJpmQqx9+uybol |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- regsvr32.exe (PID: 3124)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3124)
Connects to CnC server
- svchost.exe (PID: 2232)
HANCITOR was detected
- svchost.exe (PID: 2232)
SUSPICIOUS
Executed via WMI
- regsvr32.exe (PID: 3124)
Executable content was dropped or overwritten
- WScript.exe (PID: 2836)
Checks for external IP
- svchost.exe (PID: 2232)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2232 | C:\Windows\System32\svchost.exe | C:\Windows\System32\svchost.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\1.vbs" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3124 | regsvr32.exe -s C:\Users\admin\AppData\Local\Temp\QrnnZdZx.txt | C:\Windows\system32\regsvr32.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
439
Read events
419
Write events
20
Delete events
0
Modification events
| (PID) Process: | (2836) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2836) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2836) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E3070A0002001D0007002C000800000200000000 | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2232) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | WScript.exe | C:\Users\admin\AppData\Local\Temp\QrnnZdZx.txt | executable | |
MD5:— | SHA256:— | |||
| 2836 | WScript.exe | C:\Users\admin\AppData\Local\Temp\UTURITip | text | |
MD5:— | SHA256:— | |||
| 2836 | WScript.exe | C:\Users\admin\AppData\Local\Temp\jfChqXtYT.txt | compressed | |
MD5:— | SHA256:— | |||
| 2836 | WScript.exe | C:\Users\admin\AppData\Local\Temp\jfChqXtYT.txt.zip | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | svchost.exe | GET | 200 | 23.23.229.94:80 | http://api.ipify.org/ | US | text | 13 b | shared |
2232 | svchost.exe | POST | 200 | 72.44.89.42:80 | http://pubarecaz.com/4/forum.php | US | text | 12 b | malicious |
2232 | svchost.exe | POST | 200 | 72.44.89.42:80 | http://pubarecaz.com/4/forum.php | US | text | 12 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2232 | svchost.exe | 72.44.89.42:80 | pubarecaz.com | NEXCESS.NET L.L.C. | US | malicious |
2232 | svchost.exe | 23.23.229.94:80 | api.ipify.org | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
pubarecaz.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2232 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
2232 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2232 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
2 ETPRO signatures available at the full report