| File name: | QcBD.exe |
| Full analysis: | https://app.any.run/tasks/464ccc62-db47-472c-ab84-fcb8eaeb9c4b |
| Verdict: | Malicious activity |
| Threats: | WarZone RAT is a remote access trojan, which is written in C++ and offered as a malware-as-a-service. It packs a wide range of capabilities, from stealing victims’ files and passwords to capturing desktop activities. WarZone RAT is primarily distributed via phishing emails and receives regular updates from its C2. |
| Analysis date: | December 22, 2023, 02:25:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E7810B7BD35DFB1131242377570A8705 |
| SHA1: | 3809874C9B8AE6E05484D83120A9809B7CB0A8FA |
| SHA256: | 89E0D97C3F6B79962F97E02152CFF003F17D940F973D762874576DAB2BC3A312 |
| SSDEEP: | 24576:HqFkCmeBVUl4HcegdV67auTUcltqjtTiB8nGqzf:KFkCmeBVUl4HcegdV67auTUcltqjtTiQ |
MALICIOUS
Uses Task Scheduler to run other applications
- QcBD.exe (PID: 2120)
- Bins.exe (PID: 668)
- QcBD.exe (PID: 2096)
- Bins.exe (PID: 3292)
- Bins.exe (PID: 2804)
- QcBD.exe (PID: 2660)
Runs injected code in another process
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Avemaria is detected
- Bins.exe (PID: 452)
Connects to the CnC server
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
WARZONE has been detected (SURICATA)
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
AVEMARIA has been detected (SURICATA)
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Adds path to the Windows Defender exclusion list
- QcBD.exe (PID: 2096)
- QcBD.exe (PID: 2836)
- Bins.exe (PID: 3292)
The process bypass UAC
- Dism.exe (PID: 2652)
- Dism.exe (PID: 3288)
- Dism.exe (PID: 2340)
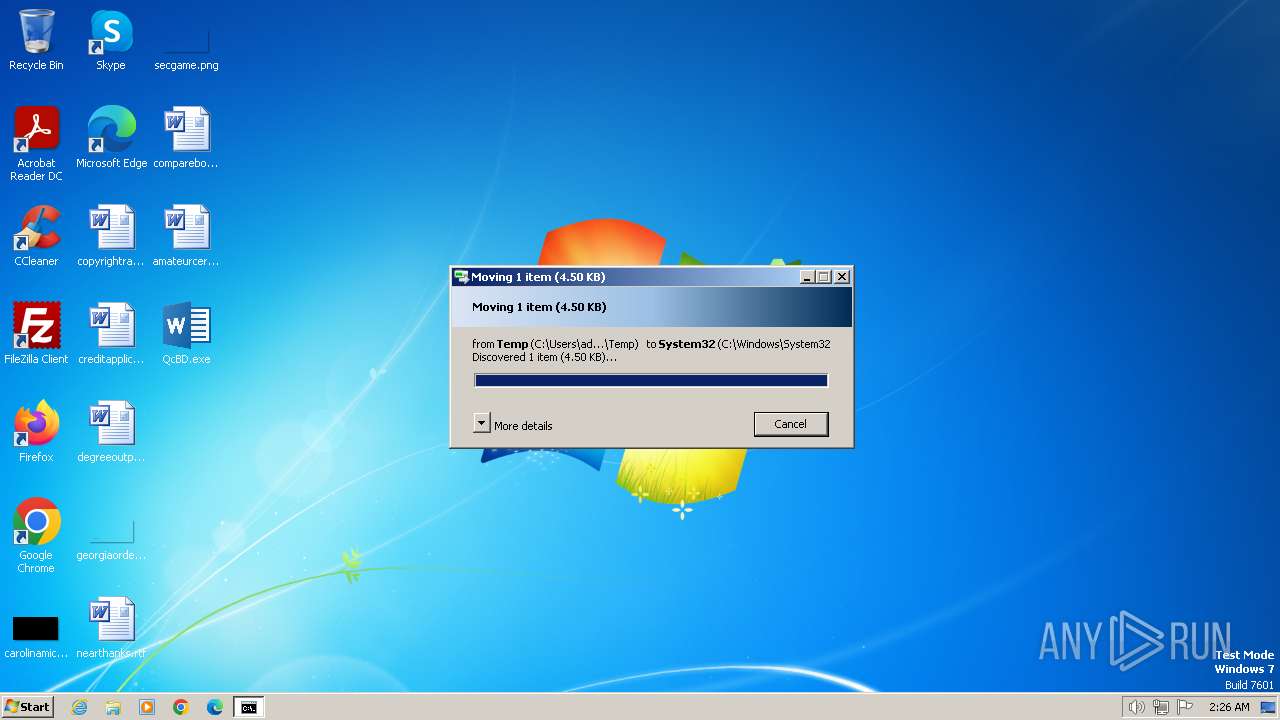
Creates a writable file in the system directory
- QcBD.exe (PID: 2836)
Creates or modifies Windows services
- QcBD.exe (PID: 2836)
WARZONE has been detected (YARA)
- QcBD.exe (PID: 2836)
SUSPICIOUS
Reads the Internet Settings
- QcBD.exe (PID: 2120)
- cmd.exe (PID: 268)
- QcBD.exe (PID: 2096)
- Bins.exe (PID: 668)
- cmd.exe (PID: 148)
- Bins.exe (PID: 452)
- powershell.exe (PID: 2788)
- cmd.exe (PID: 2908)
- QcBD.exe (PID: 2836)
- powershell.exe (PID: 3360)
- Bins.exe (PID: 3292)
- powershell.exe (PID: 2704)
- Bins.exe (PID: 2804)
- QcBD.exe (PID: 2660)
Starts CMD.EXE for commands execution
- QcBD.exe (PID: 2020)
- Bins.exe (PID: 452)
Connects to unusual port
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Script adds exclusion path to Windows Defender
- QcBD.exe (PID: 2096)
- QcBD.exe (PID: 2836)
- Bins.exe (PID: 3292)
Starts POWERSHELL.EXE for commands execution
- QcBD.exe (PID: 2096)
- QcBD.exe (PID: 2836)
- Bins.exe (PID: 3292)
Reads security settings of Internet Explorer
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Reads settings of System Certificates
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Checks Windows Trust Settings
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
- drvinst.exe (PID: 2060)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 2788)
- powershell.exe (PID: 3360)
- powershell.exe (PID: 2704)
Uses NETSH.EXE to add a firewall rule or allowed programs
- 78.exe (PID: 4060)
INFO
Drops the executable file immediately after the start
- QcBD.exe (PID: 2120)
- cmd.exe (PID: 268)
- QcBD.exe (PID: 2020)
- dllhost.exe (PID: 1936)
- cmd.exe (PID: 148)
- dllhost.exe (PID: 2724)
- cmd.exe (PID: 2908)
- QcBD.exe (PID: 2836)
Creates files or folders in the user directory
- QcBD.exe (PID: 2120)
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Reads the computer name
- QcBD.exe (PID: 2120)
- QcBD.exe (PID: 2020)
- Bins.exe (PID: 668)
- QcBD.exe (PID: 2096)
- QcBD.exe (PID: 2836)
- Bins.exe (PID: 3240)
- Bins.exe (PID: 3292)
- 78.exe (PID: 4060)
- wmpnscfg.exe (PID: 2932)
- Bins.exe (PID: 452)
- wmpnscfg.exe (PID: 2900)
- QcBD.exe (PID: 2660)
- Bins.exe (PID: 2036)
- Bins.exe (PID: 2756)
- QcBD.exe (PID: 3256)
- Bins.exe (PID: 2804)
- drvinst.exe (PID: 2060)
Checks supported languages
- QcBD.exe (PID: 2120)
- QcBD.exe (PID: 2020)
- Bins.exe (PID: 668)
- QcBD.exe (PID: 2096)
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
- Bins.exe (PID: 3240)
- Bins.exe (PID: 3292)
- 78.exe (PID: 4060)
- wmpnscfg.exe (PID: 2932)
- wmpnscfg.exe (PID: 2900)
- drvinst.exe (PID: 2060)
- QcBD.exe (PID: 2660)
- Bins.exe (PID: 2036)
- QcBD.exe (PID: 3256)
- Bins.exe (PID: 2756)
- Bins.exe (PID: 2804)
Application launched itself
- QcBD.exe (PID: 2120)
- Bins.exe (PID: 668)
- QcBD.exe (PID: 2096)
- msedge.exe (PID: 4032)
- msedge.exe (PID: 2032)
- Bins.exe (PID: 3292)
- Bins.exe (PID: 2804)
- QcBD.exe (PID: 2660)
Reads the machine GUID from the registry
- QcBD.exe (PID: 2120)
- Bins.exe (PID: 668)
- Bins.exe (PID: 452)
- Bins.exe (PID: 3240)
- Bins.exe (PID: 3292)
- QcBD.exe (PID: 2836)
- QcBD.exe (PID: 2096)
- QcBD.exe (PID: 2660)
- Bins.exe (PID: 2804)
- drvinst.exe (PID: 2060)
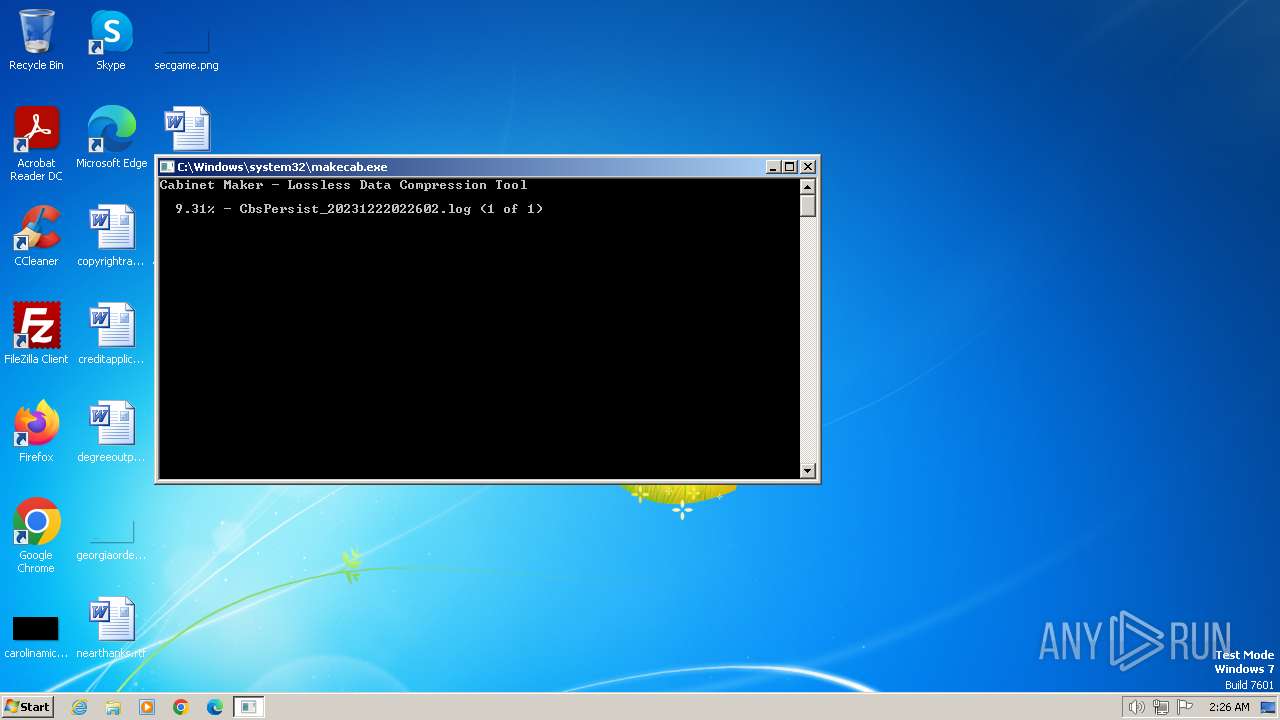
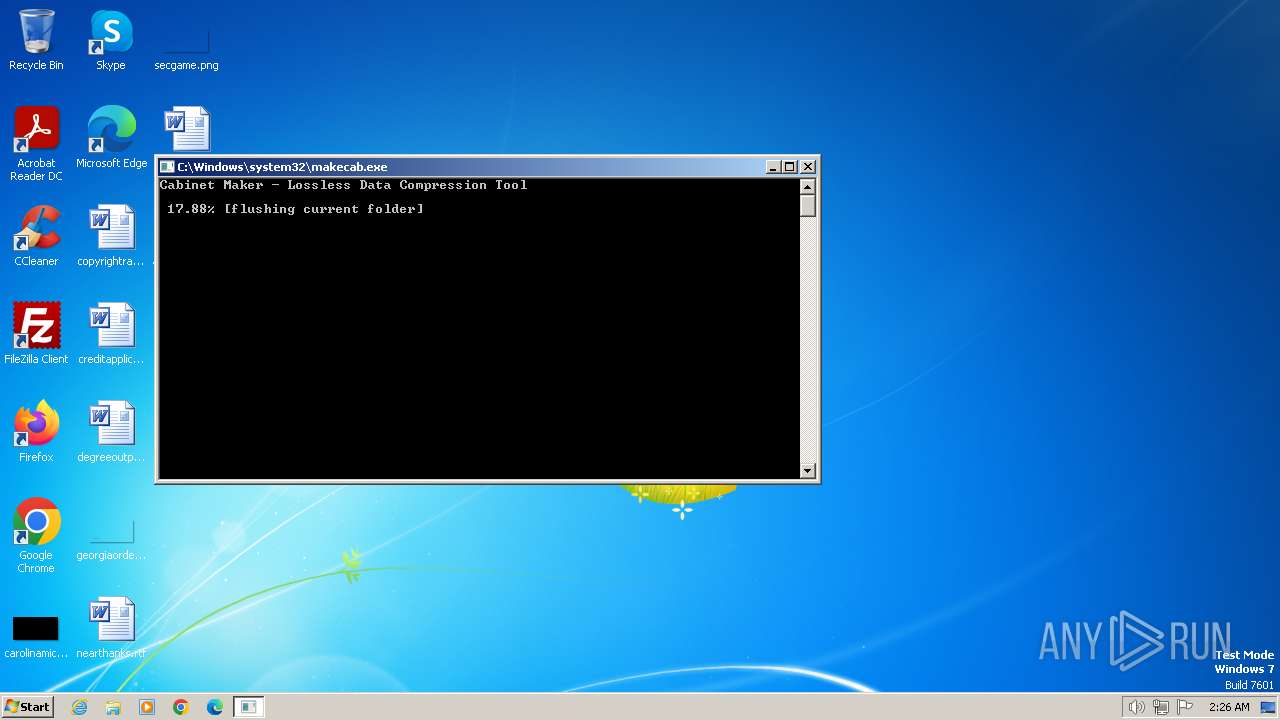
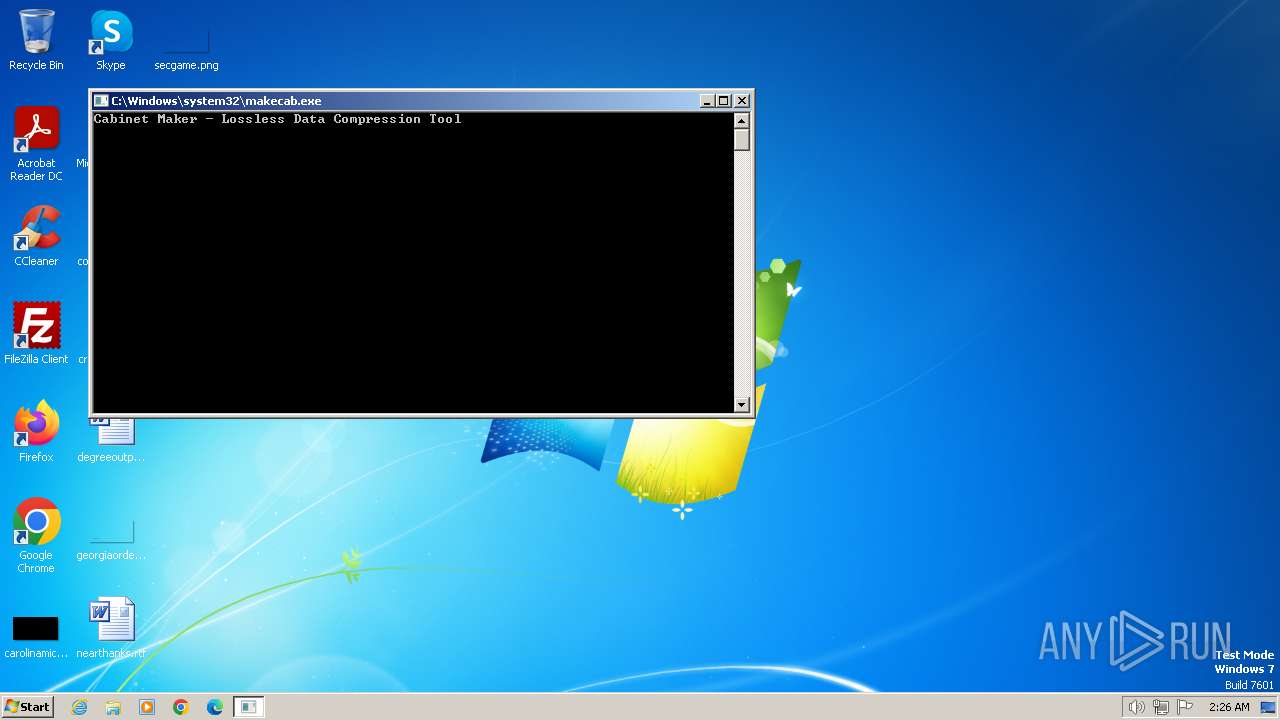
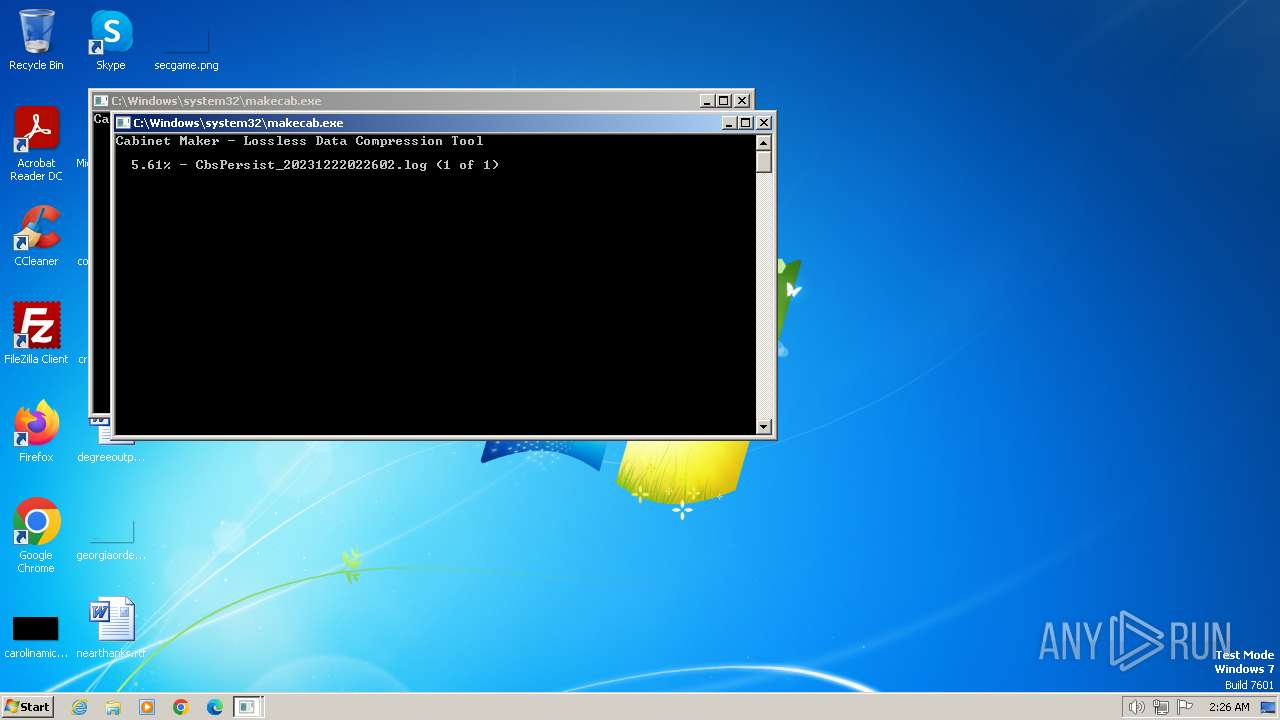
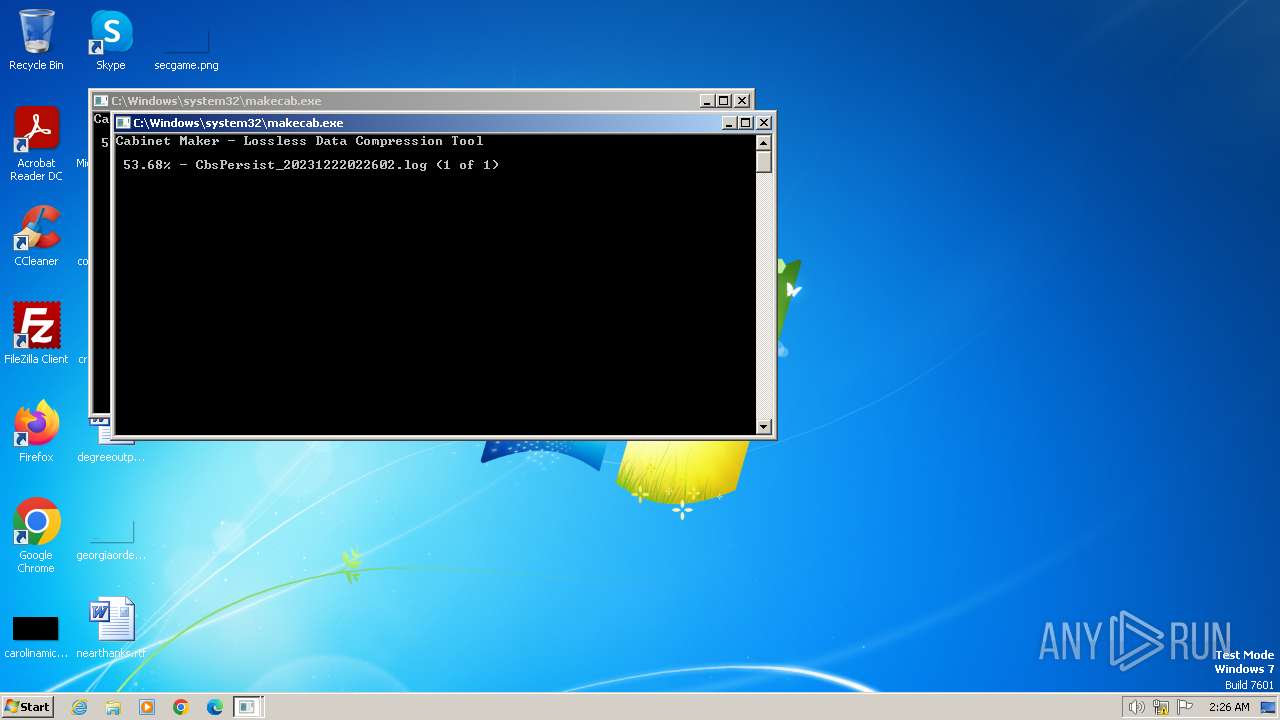
Create files in a temporary directory
- QcBD.exe (PID: 2120)
- makecab.exe (PID: 2344)
- Bins.exe (PID: 668)
- QcBD.exe (PID: 2096)
- makecab.exe (PID: 3216)
- makecab.exe (PID: 2976)
- QcBD.exe (PID: 2836)
- Bins.exe (PID: 3292)
- Bins.exe (PID: 2804)
- QcBD.exe (PID: 2660)
Checks transactions between databases Windows and Oracle
- cmd.exe (PID: 268)
- cmd.exe (PID: 148)
- cmd.exe (PID: 2908)
Starts itself from another location
- QcBD.exe (PID: 2020)
Application was injected by another process
- explorer.exe (PID: 1164)
Checks proxy server information
- Bins.exe (PID: 452)
- QcBD.exe (PID: 2836)
Creates files in the program directory
- QcBD.exe (PID: 2836)
Process drops legitimate windows executable
- QcBD.exe (PID: 2836)
Manual execution by a user
- wmpnscfg.exe (PID: 2932)
- msedge.exe (PID: 2032)
- wmpnscfg.exe (PID: 2900)
- Bins.exe (PID: 2804)
- QcBD.exe (PID: 2660)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
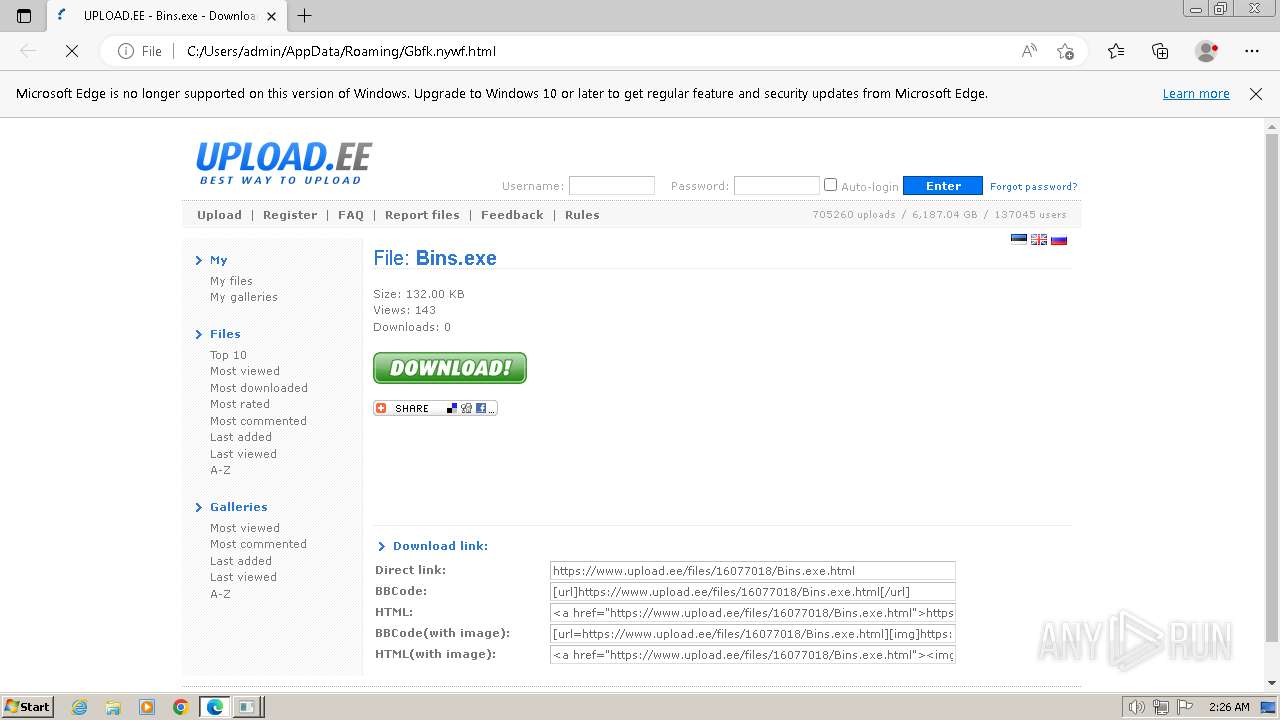
WarZone
(PID) Process(2836) QcBD.exe
C2 (2)74.50.93.170:4040
103.67.163.156:4040
BuildID7D6C4DD7PW
Options
Install FlagTrue
Install nameBins.exe
Startup FlagTrue
Startup nameImages
Reverse Proxy local port5000
Offline logTrue
PersistanceTrue
UAC bypassTrue
Defender bypassTrue
Use ADSFalse
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (81) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.2) |
| .exe | | | Win32 Executable (generic) (4.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.2) |
| .exe | | | Generic Win/DOS Executable (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2081:05:09 05:13:33+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 545280 |
| InitializedDataSize: | 19968 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x87182 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | WindowsFormsApp3 |
| FileVersion: | 1.0.0.0 |
| InternalName: | QcBD.exe |
| LegalCopyright: | Copyright © 2019 |
| LegalTrademarks: | - |
| OriginalFileName: | QcBD.exe |
| ProductName: | WindowsFormsApp3 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
136
Monitored processes
75
Malicious processes
14
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | Bins.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 268 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | QcBD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 452 | "C:\Users\admin\Documents\Bins.exe" | C:\Users\admin\Documents\Bins.exe | Bins.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp3 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6d7ef598,0x6d7ef5a8,0x6d7ef5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 668 | "C:\Users\admin\Documents\Bins.exe" | C:\Users\admin\Documents\Bins.exe | — | QcBD.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp3 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=2604 --field-trial-handle=1248,i,5865694378082078859,15052869293618746057,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2280 --field-trial-handle=1248,i,5865694378082078859,15052869293618746057,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4912 --field-trial-handle=1248,i,5865694378082078859,15052869293618746057,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1164 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --mojo-platform-channel-handle=5428 --field-trial-handle=1248,i,5865694378082078859,15052869293618746057,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
21 774
Read events
21 454
Write events
319
Delete events
1
Modification events
| (PID) Process: | (2120) QcBD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2120) QcBD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2120) QcBD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2120) QcBD.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (268) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (268) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (268) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (268) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {Q65231O0-O2S1-4857-N4PR-N8R7P6RN7Q27}\pzq.rkr |
Value: 000000001D00000014000000C6F80E00000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFFA06C028D32B0D90100000000 | |||
| (PID) Process: | (1164) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 00000000CE01000044030000ABEB910141000000880000001E2D31007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000E0C3AF7591C4AF750000000000000000000000000000000048E93302CC0B590264EA33021368B475808B1E1BFEFFFFFF4EC4AF759819AF7500000000D1B449744C0001008202000002000000000000000000000000000000000000004C000100F4E93302BE19AF75D1B449744C0001008202000002000000000000000000000010EA33027FF44974D1B449744C00010082020000020000000000000074EA330220EA3302E3F6497430EC330274EA33023BF6497431F4497443F64974872E876C00000000688B380000000000000000000100000030EC330265F4497400000000D1B44974872E876C30EA3302525BAF7548EB33024E755974BB32FD1AFEFFFFFF43F64974DAF54974688B38004C000100820200000200000000000000581F6C0000000000DCEA33029FD961004C00010082020000020000001100000090523600885236000000000000000000ACEB330254EB330238EB0000EBA2826CE8EA33025E90B17638EB3302ECEA33020394B1760000000084C6460214EB3302A993B17684C64602C0EB3302F8C14602BD93B17600000000F8C14602C0EB33021CEB330241000000880000001E2D31007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000E0C3AF7591C4AF750000000000000000000000000000000048E93302CC0B590264EA33021368B475808B1E1BFEFFFFFF4EC4AF759819AF7500000000D1B449744C0001008202000002000000000000000000000000000000000000004C000100F4E93302BE19AF75D1B449744C0001008202000002000000000000000000000010EA33027FF44974D1B449744C00010082020000020000000000000074EA330220EA3302E3F6497430EC330274EA33023BF6497431F4497443F64974872E876C00000000688B380000000000000000000100000030EC330265F4497400000000D1B44974872E876C30EA3302525BAF7548EB33024E755974BB32FD1AFEFFFFFF43F64974DAF54974688B38004C000100820200000200000000000000581F6C0000000000DCEA33029FD961004C00010082020000020000001100000090523600885236000000000000000000ACEB330254EB330238EB0000EBA2826CE8EA33025E90B17638EB3302ECEA33020394B1760000000084C6460214EB3302A993B17684C64602C0EB3302F8C14602BD93B17600000000F8C14602C0EB33021CEB330241000000880000001E2D31007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E006500780065000000E0C3AF7591C4AF750000000000000000000000000000000048E93302CC0B590264EA33021368B475808B1E1BFEFFFFFF4EC4AF759819AF7500000000D1B449744C0001008202000002000000000000000000000000000000000000004C000100F4E93302BE19AF75D1B449744C0001008202000002000000000000000000000010EA33027FF44974D1B449744C00010082020000020000000000000074EA330220EA3302E3F6497430EC330274EA33023BF6497431F4497443F64974872E876C00000000688B380000000000000000000100000030EC330265F4497400000000D1B44974872E876C30EA3302525BAF7548EB33024E755974BB32FD1AFEFFFFFF43F64974DAF54974688B38004C000100820200000200000000000000581F6C0000000000DCEA33029FD961004C00010082020000020000001100000090523600885236000000000000000000ACEB330254EB330238EB0000EBA2826CE8EA33025E90B17638EB3302ECEA33020394B1760000000084C6460214EB3302A993B17684C64602C0EB3302F8C14602BD93B17600000000F8C14602C0EB33021CEB3302 | |||
Executable files
13
Suspicious files
108
Text files
50
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2312 | PkgMgr.exe | C:\Windows\Logs\CBS\CbsPersist_20231222022602.log | — | |
MD5:— | SHA256:— | |||
| 2312 | PkgMgr.exe | C:\Windows\Logs\CBS\CBS.log | binary | |
MD5:8B2B8854773CABAEBAFB90C6636FB65B | SHA256:5D487E8BABD0E58FE2BA68F1903C6A19A333963227EA33D977F9A673A37BAC66 | |||
| 2724 | dllhost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 2020 | QcBD.exe | C:\Users\admin\Documents\Bins.exe | executable | |
MD5:E7810B7BD35DFB1131242377570A8705 | SHA256:89E0D97C3F6B79962F97E02152CFF003F17D940F973D762874576DAB2BC3A312 | |||
| 2120 | QcBD.exe | C:\Users\admin\AppData\Local\Temp\tmp5772.tmp | xml | |
MD5:1FEF9FA1C31E5853FCA152B31F36C582 | SHA256:3EDDF60C4854F958B2441E6ADFAB8399FFFBF96B0593366E3DF0FCC995A9BCE0 | |||
| 1936 | dllhost.exe | C:\Windows\System32\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 268 | cmd.exe | C:\Users\admin\AppData\Local\Temp\ellocnak.xml | xml | |
MD5:427EB7374887305B72F5C552837C9036 | SHA256:B3F421780A49CBE680A317259D4DF9CE1D0CDACA3020B4DF0DC18CC01D68CCBB | |||
| 2344 | makecab.exe | C:\Users\admin\AppData\Local\Temp\cab_2344_2 | binary | |
MD5:C98E03467443012EB1943A2C8F3375BA | SHA256:FF757F4C6C10C30CE91613A70C956B1AFFDA05177B63A91D648C2F69BBCF2B5B | |||
| 148 | cmd.exe | C:\Users\admin\AppData\Local\Temp\dismcore.dll | executable | |
MD5:6B906764A35508A7FD266CDD512E46B1 | SHA256:FC0C90044B94B080F307C16494369A0796AC1D4E74E7912BA79C15CCA241801C | |||
| 2120 | QcBD.exe | C:\Users\admin\AppData\Roaming\xzYPjfkAQ.exe | executable | |
MD5:E7810B7BD35DFB1131242377570A8705 | SHA256:89E0D97C3F6B79962F97E02152CFF003F17D940F973D762874576DAB2BC3A312 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
80
DNS requests
80
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2836 | QcBD.exe | GET | 200 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0a14e02db7fce58e | unknown | compressed | 4.66 Kb | unknown |
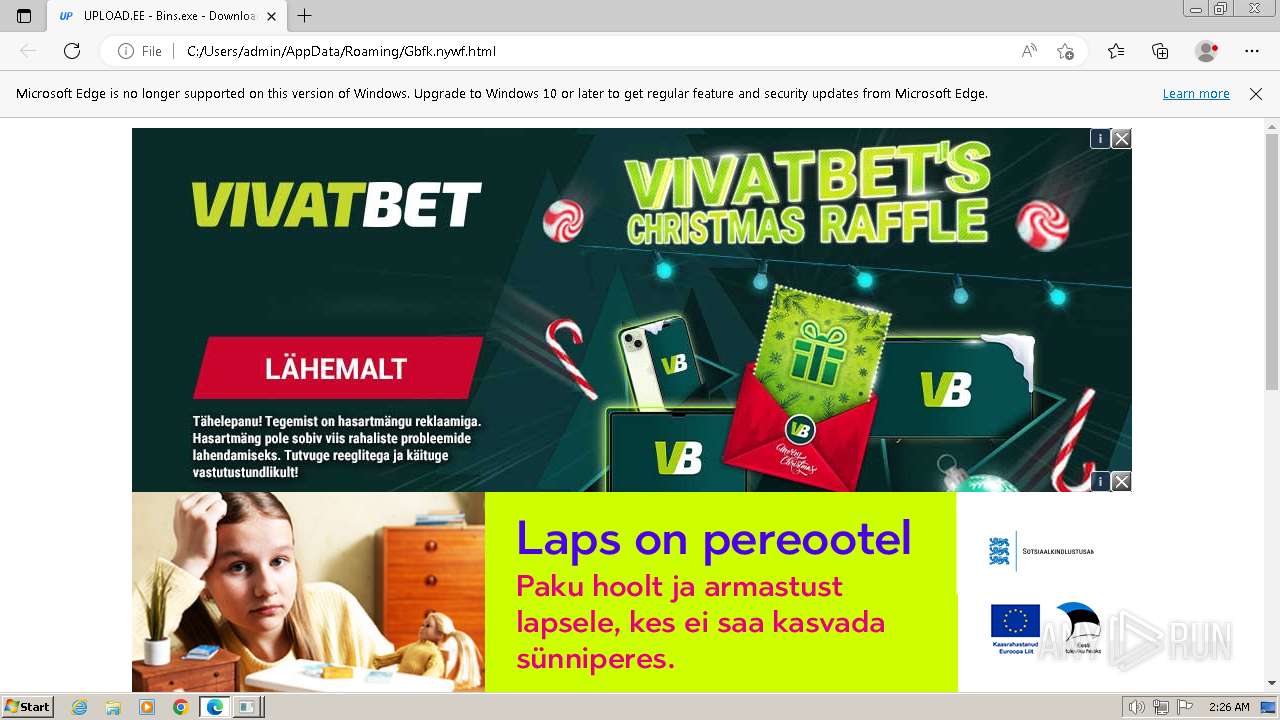
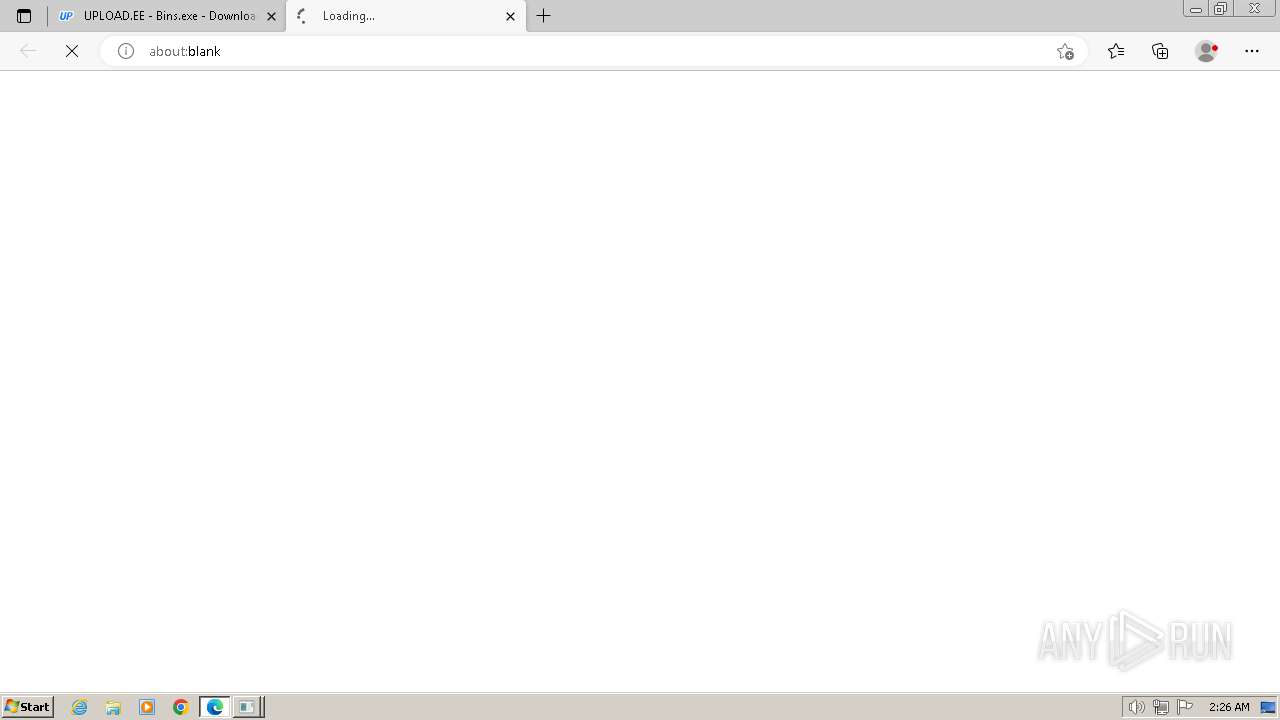
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://serving.bepolite.eu/script?space=50dd7b0f-4105-441f-8f60-18cc3fcb090c&type=direct&page_id=9792780&screen_width=1264&screen_height=574&os=Win32&refurl=&pageurl=file%3A%2F%2F%2FC%3A%2FUsers%2Fadmin%2FAppData%2FRoaming%2FGbfk.nywf.html&rnd=1703211992630 | unknown | — | — | unknown |
2836 | QcBD.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQlOydjtpho0%2Bholo77zGjGxETUEQQU8JyF%2FaKffY%2FJaLvV1IlNHb7TkP8CEAHqRFnqJyQkmYqUpX34D7k%3D | unknown | binary | 727 b | unknown |
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://serving.bepolite.eu/event?key=FYFWuDany3hwv6rfuoAYFwPYBJSWIgBXXhizua6WOibDf6fS3aWLluo_Nmh9KPs5rJJ-h5l9sNcj5md55UaU2gEsp2rSwKaJIMs8V0K2Ke22lmax4wo8y78zpGz5-7OcgMxXG3cI54aeiyUVH2cPLFDzOhejLPH-YtiEsILyxgHzp3ZdgWtH0MKue5p5AGKHXJxXiVJEh1Vfgxn38rgFo-tSrOiriedI-Oi3R5i8w-36qxw8Ul2_rwVcuvzsLUipOtuW_QN7J6fUO08VJfhiOKqJKd716KUrG_T0DJ_T5D_a5hY8OvOxWaQQS9P0iYfnf_8e5-90sra7UBdR4oM89g | unknown | — | — | unknown |
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://static.bepolite.eu/banners/a7a565c1-d681-42af-a9a0-78da3f0481c0/Christmas_Raffle_1000x400.jpg | unknown | — | — | unknown |
2836 | QcBD.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAoFmyX1Sz2HlMxmMUd1OKM%3D | unknown | binary | 471 b | unknown |
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://static.bepolite.eu/files/close-gray.png | unknown | — | — | unknown |
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://serving.bepolite.eu/event?key=FYFWuDany3hwv6rfuoAYFwPYBJSWIgBXXhizua6WOibDf6fS3aWLluo_Nmh9KPs5rJJ-h5l9sNcj5md55UaU2gEsp2rSwKaJIMs8V0K2Ke22lmax4wo8y78zpGz5-7OcgMxXG3cI54aeiyUVH2cPLFDzOhejLPH-YtiEsILyxgHzp3ZdgWtH0MKue5p5AGKHXJxXiVJEh1Vfgxn38rgFo-tSrOiriedI-Oi3R5i8w-3mtQmzqmkJkdb7wFCVvahboUdoW-L-69QFYdY9ND_V8vKXfSB7HwUPsexSCu-4LAna5hY8OvOxWaQQS9P0iYfnf_8e5-90sra7UBdR4oM89g | unknown | — | — | unknown |
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://serving.bepolite.eu/event?key=FYFWuDany3hwv6rfuoAYFwPYBJSWIgBXXhizua6WOibDf6fS3aWLluo_Nmh9KPs5rJJ-h5l9sNcj5md55UaU2gEsp2rSwKaJIMs8V0K2Ke22lmax4wo8y78zpGz5-7OcgMxXG3cI54aeiyUVH2cPLFDzOhejLPH-YtiEsILyxgHzp3ZdgWtH0MKue5p5AGKHXJxXiVJEh1Vfgxn38rgFo-tSrOiriedI-Oi3R5i8w-3mtQmzqmkJkdb7wFCVvahboUdoW-L-69QFYdY9ND_V8vKXfSB7HwUPsexSCu-4LAna5hY8OvOxWaQQS9P0iYfnPQFkqynusZJvi-LzBjp4mA | unknown | — | — | unknown |
1576 | msedge.exe | GET | 302 | 212.47.222.21:80 | http://static.bepolite.eu/banners/983a8e9c-4208-43cd-89f4-2945abe9f0b1/index.html?click_url=http%3A%2F%2Fserving.bepolite.eu%2Fevent%3Fkey%3DFYFWuDany3hwv6rfuoAYFwPYBJSWIgBXXhizua6WOibDf6fS3aWLluo_Nmh9KPs5rJJ-h5l9sNcj5md55UaU2gEsp2rSwKaJIMs8V0K2Ke22lmax4wo8y78zpGz5-7OcgMxXG3cI54aeiyUVH2cPLFDzOhejLPH-YtiEsILyxgHzp3ZdgWtH0MKue5p5AGKHXJxXiVJEh1Vfgxn38rgFo-tSrOiriedI-Oi3R5i8w-2vThFGotY2sWRYclHygp0obVPpUtSrW5K3bzg-Z2gHBSyBb0cGONG28VWaAHEEOlLa5hY8OvOxWaQQS9P0iYfnngZXtFEp1ljuqs475VAp1Q%26clink%3Dhttps%253A%252F%252Ftarkvanem.ee%252Fkasupere%252F%253Futm_campaign%253Dska_lapsonpereootel_2023%2526utm_medium%253Dbanner%2526utm_source%253Dsmartad%2526utm_content%253Dgiantheader%2526utm_term%253Dest&dynamic_url=http%3A%2F%2Fserving.bepolite.eu%2Fevent%3Fkey%3DFYFWuDany3hwv6rfuoAYFwPYBJSWIgBXXhizua6WOibDf6fS3aWLluo_Nmh9KPs5rJJ-h5l9sNcj5md55UaU2gEsp2rSwKaJIMs8V0K2Ke22lmax4wo8y78zpGz5-7OcgMxXG3cI54aeiyUVH2cPLFDzOhejLPH-YtiEsILyxgHzp3ZdgWtH0MKue5p5AGKHXJxXiVJEh1Vfgxn38rgFo-tSrOiriedI-Oi3R5i8w-2vThFGotY2sWRYclHygp0obVPpUtSrW5K3bzg-Z2gHBSyBb0cGONG28VWaAHEEOlLa5hY8OvOxWaQQS9P0iYfnngZXtFEp1ljuqs475VAp1Q%26clink%3D&f=http%3A%2F%2Fstatic.bepolite.eu%2Fbanners%2F983a8e9c-4208-43cd-89f4-2945abe9f0b1%2Findex.html&clink=https%3A%2F%2Ftarkvanem.ee%2Fkasupere%2F%3Futm_campaign%3Dska_lapsonpereootel_2023%26utm_medium%3Dbanner%26utm_source%3Dsmartad%26utm_content%3Dgiantheader%26utm_term%3Dest&banner_id=c4c0e8c0d3ff46be8ab5a1384da6528050dd7b0f4105441f8f6018cc3fcb090c&bg=black&w=1000&h=200&locale=Display%20Estonia-EST&info=https%3A%2F%2Fdigital.tv3.ee%2Fbepolite-id%2F%3Futm_src%3Dbanner | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
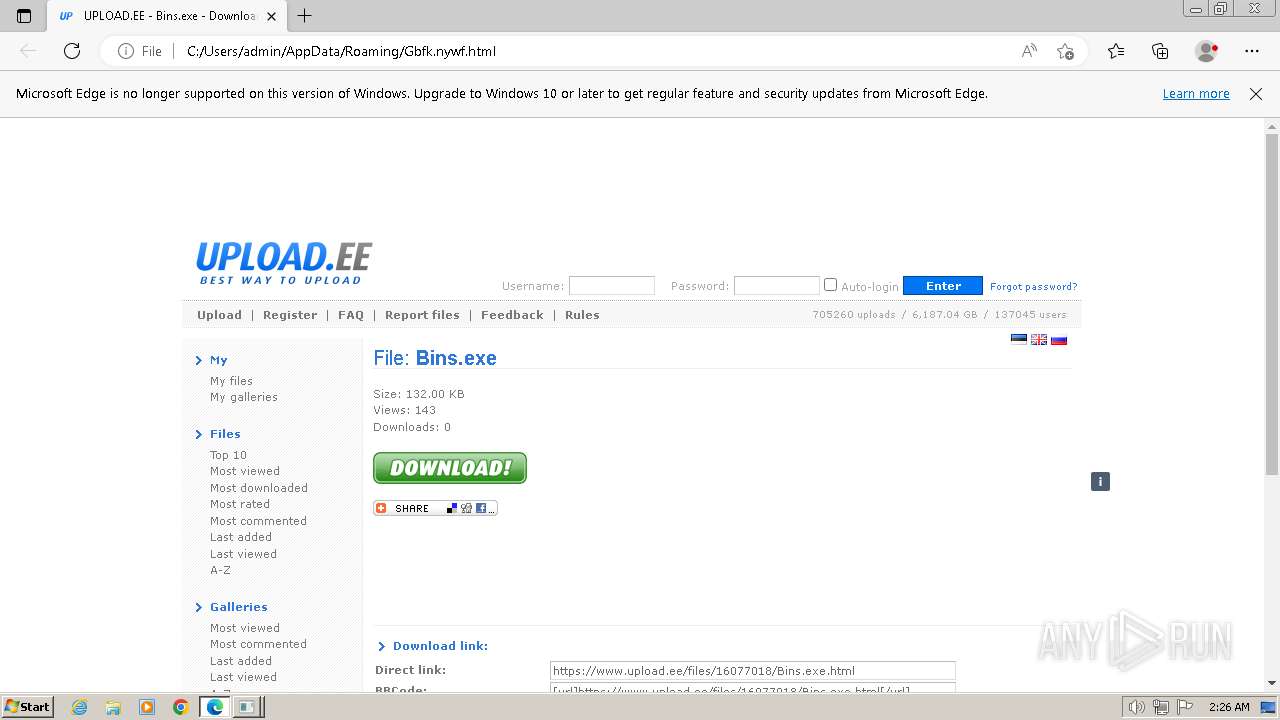
452 | Bins.exe | 74.50.93.170:4040 | — | IS-AS-1 | US | malicious |
452 | Bins.exe | 51.91.30.159:443 | www.upload.ee | OVH SAS | FR | unknown |
2836 | QcBD.exe | 74.50.93.170:4040 | — | IS-AS-1 | US | malicious |
2836 | QcBD.exe | 51.91.30.159:443 | www.upload.ee | OVH SAS | FR | unknown |
2836 | QcBD.exe | 23.53.40.49:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2836 | QcBD.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4060 | 78.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
332 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.upload.ee |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
s7.addthis.com |
| whitelisted |
du0pud0sdlmzf.cloudfront.net |
| unknown |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
452 | Bins.exe | A Network Trojan was detected | ET MALWARE Warzone RAT Response (Inbound) |
2836 | QcBD.exe | A Network Trojan was detected | ET MALWARE Warzone RAT Response (Inbound) |
2836 | QcBD.exe | A Network Trojan was detected | ET MALWARE Warzone RAT Response (Inbound) |
9 ETPRO signatures available at the full report