| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/a2c4754e-a817-4605-92dd-7d1df04d06c1 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | March 30, 2020, 21:05:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
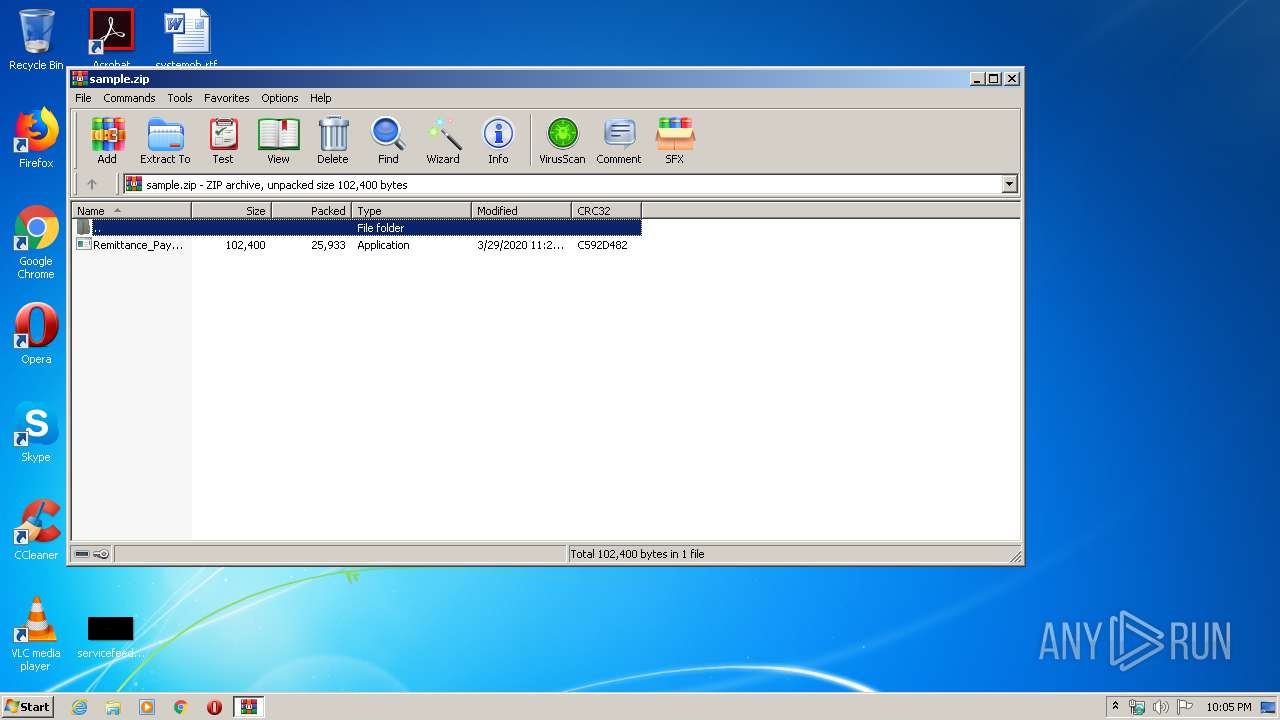
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 53429A71FD64501BEDD9E35757B5764E |
| SHA1: | 3BA26923B966FD932EA0AC917EB1F0ADB4DCDCC8 |
| SHA256: | 89C926ADC4AB2A363358A71D890F2583CEFE9675C6566B8D2EFE045640FAE488 |
| SSDEEP: | 768:9znpB/AGskF8t4BzW4zdgbTBG7SVv6zSGokhv:9pdAGskFlIB0Ov6ztnhv |
MALICIOUS
Application was dropped or rewritten from another process
- Remittance_Payment_Remittance_0182937484373938339383.exe (PID: 3152)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 1696)
AGENTTESLA was detected
- RegAsm.exe (PID: 1696)
SUSPICIOUS
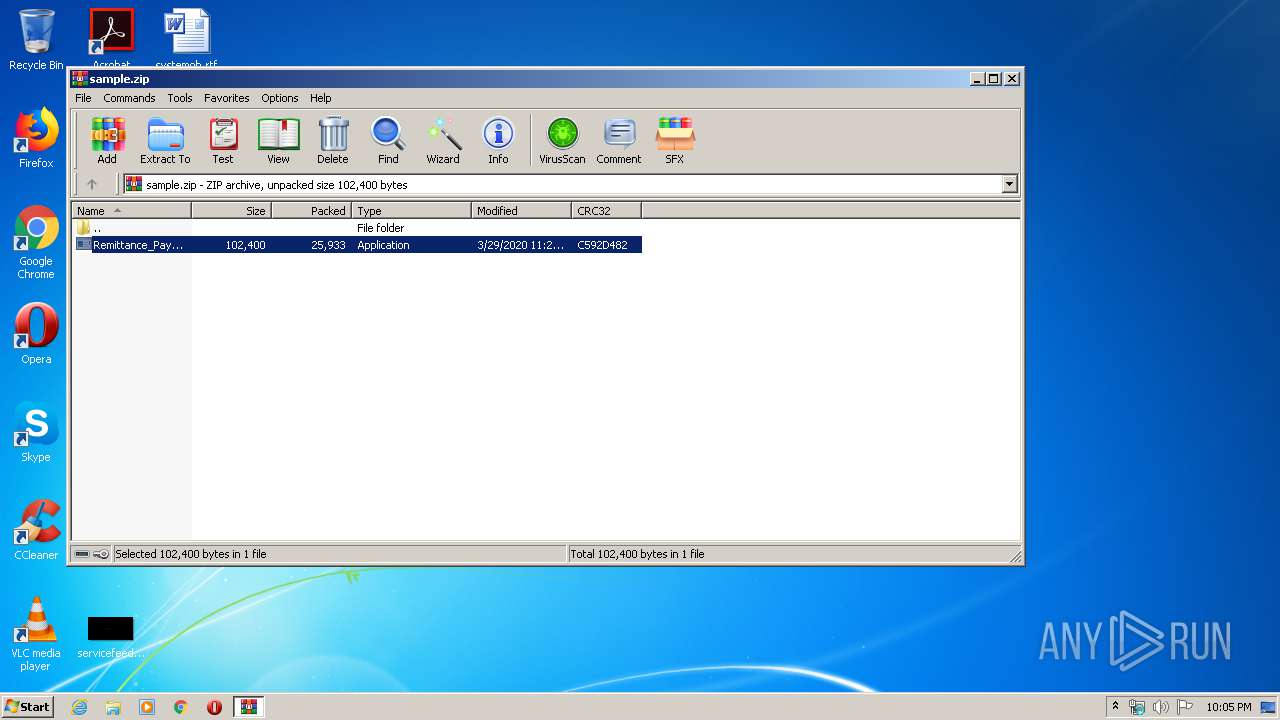
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3448)
Creates files in the user directory
- RegAsm.exe (PID: 1696)
Connects to SMTP port
- RegAsm.exe (PID: 1696)
INFO
Reads settings of System Certificates
- RegAsm.exe (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:03:29 23:29:23 |
| ZipCRC: | 0xc592d482 |
| ZipCompressedSize: | 25933 |
| ZipUncompressedSize: | 102400 |
| ZipFileName: | Remittance_Payment_Remittance_0182937484373938339383.exe |
Total processes
39
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3448.17067\Remittance_Payment_Remittance_0182937484373938339383.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | Remittance_Payment_Remittance_0182937484373938339383.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3152 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3448.17067\Remittance_Payment_Remittance_0182937484373938339383.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3448.17067\Remittance_Payment_Remittance_0182937484373938339383.exe | — | WinRAR.exe | |||||||||||
User: admin Company: WONderware Integrity Level: MEDIUM Description: Roter Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 3448 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
508
Read events
477
Write events
31
Delete events
0
Modification events
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample.zip | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
6
Text files
1
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1696 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\CabED75.tmp | — | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\TarED76.tmp | — | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\QZZ9VMTM.txt | text | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_BA8650709FF65A42B9202D73C10A8F29 | binary | |
MD5:— | SHA256:— | |||
| 3448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3448.17067\Remittance_Payment_Remittance_0182937484373938339383.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BE8B021F9E811DFC8C8A28572A17C05A_0B97942EE72A6E3F514E8E84F294CC72 | binary | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_0B97942EE72A6E3F514E8E84F294CC72 | der | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 1696 | RegAsm.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BE8B021F9E811DFC8C8A28572A17C05A_BA8650709FF65A42B9202D73C10A8F29 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
4
DNS requests
4
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1696 | RegAsm.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1696 | RegAsm.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFOOHQjK5IlqCAAAAAAyCmA%3D | US | der | 471 b | whitelisted |
1696 | RegAsm.exe | GET | 200 | 172.217.21.195:80 | http://ocsp.pki.goog/gts1o1/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDL%2FQslYWVuogIAAAAAXGdc | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1696 | RegAsm.exe | 172.217.21.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
1696 | RegAsm.exe | 172.217.16.161:443 | doc-14-2o-docs.googleusercontent.com | Google Inc. | US | whitelisted |
1696 | RegAsm.exe | 208.91.199.225:587 | smtp.abiataltib.xyz | PDR | US | shared |
1696 | RegAsm.exe | 172.217.23.142:443 | drive.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
drive.google.com |
| shared |
ocsp.pki.goog |
| whitelisted |
doc-14-2o-docs.googleusercontent.com |
| shared |
smtp.abiataltib.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1696 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
1696 | RegAsm.exe | A Network Trojan was detected | SPYWARE [PTsecurity] AgentTesla Exfiltration |