| File name: | trigger.ps1 |
| Full analysis: | https://app.any.run/tasks/2916e43e-3096-43f0-b70f-630fa4ca893d |
| Verdict: | Malicious activity |
| Threats: | Quasar is a very popular RAT in the world thanks to its code being available in open-source. This malware can be used to control the victim’s computer remotely. |
| Analysis date: | May 18, 2025, 18:27:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | E962F0AA5105C04DEA4720899CFABDA9 |
| SHA1: | 6498BB0CC3BD570D8FA64851BD71F6C0D42689DE |
| SHA256: | 89A28D9D97E08B6A50887B56FC3A4AF370444D2643286594373499410EC3144F |
| SSDEEP: | 6:vs84deGgdEYlqihCyLLh8TQ2rLTMqi0RxvmWf2i+21hLNKUvWkqi0RxvZ:vs84kuPOCyXGTQ2fV9HmY2LQy9HZ |
MALICIOUS
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 7288)
Bypass execution policy to execute commands
- powershell.exe (PID: 7288)
Changes Windows Defender settings
- powershell.exe (PID: 7288)
Changes the autorun value in the registry
- RuntimeBroker.exe (PID: 7876)
- RuntimeBroker.exe (PID: 7920)
QUASAR has been detected (YARA)
- RuntimeBroker.exe (PID: 7920)
SUSPICIOUS
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 7288)
Application launched itself
- powershell.exe (PID: 7288)
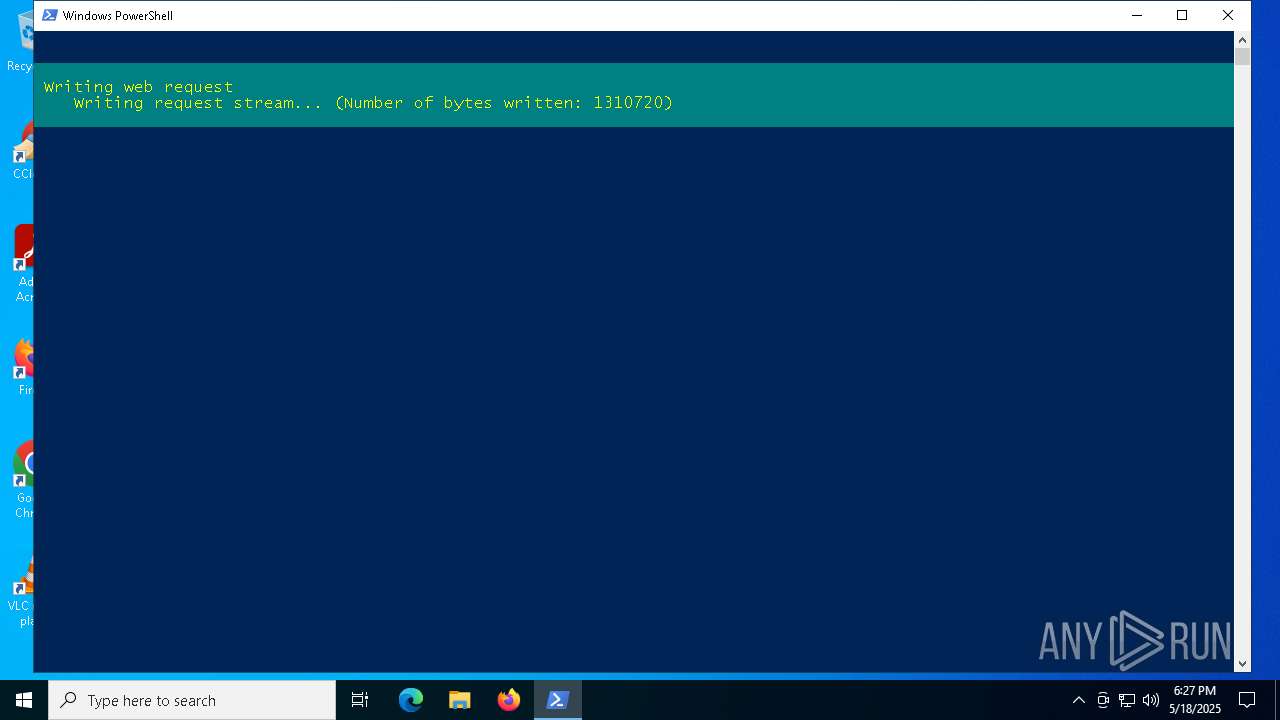
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7288)
Manipulates environment variables
- powershell.exe (PID: 7592)
Executable content was dropped or overwritten
- powershell.exe (PID: 7288)
- RuntimeBroker.exe (PID: 7876)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
Connects to unusual port
- RuntimeBroker.exe (PID: 7920)
There is functionality for taking screenshot (YARA)
- RuntimeBroker.exe (PID: 7920)
Starts itself from another location
- RuntimeBroker.exe (PID: 7876)
INFO
Disables trace logs
- powershell.exe (PID: 7288)
Checks proxy server information
- powershell.exe (PID: 7288)
- slui.exe (PID: 5380)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7592)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7592)
Checks supported languages
- RuntimeBroker.exe (PID: 7876)
- RuntimeBroker.exe (PID: 7996)
- RuntimeBroker.exe (PID: 7920)
The executable file from the user directory is run by the Powershell process
- RuntimeBroker.exe (PID: 7876)
Reads the computer name
- RuntimeBroker.exe (PID: 7876)
- RuntimeBroker.exe (PID: 7996)
- RuntimeBroker.exe (PID: 7920)
Reads Environment values
- RuntimeBroker.exe (PID: 7876)
- RuntimeBroker.exe (PID: 7920)
- RuntimeBroker.exe (PID: 7996)
Reads the machine GUID from the registry
- RuntimeBroker.exe (PID: 7876)
- RuntimeBroker.exe (PID: 7920)
- RuntimeBroker.exe (PID: 7996)
Creates files or folders in the user directory
- RuntimeBroker.exe (PID: 7876)
Auto-launch of the file from Registry key
- RuntimeBroker.exe (PID: 7876)
- RuntimeBroker.exe (PID: 7920)
Manual execution by a user
- RuntimeBroker.exe (PID: 7996)
Reads the software policy settings
- slui.exe (PID: 5380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Quasar
(PID) Process(7920) RuntimeBroker.exe
Version1.4.1
C2 (2)anonam39-41248.portmap.io:41248
Sub_Dira7
Install_NameRuntimeBroker.exe
Mutexbcabad1b-b1a9-478b-a187-3607b6476fd1
StartupRuntimeBroker
TagRuntimeBroker
LogDirLogs
SignatureIRSv9+3T5/mK+JFqhTzHs9VCwzt9UmZdNX4mpaH6sUOiS/SzOx3oFMaYcXyRiq3yqqOTprI9n/pp405+UqX6svT2SVriTNryUvgv3RVeJGNnIrwWEV/OgsWN4ppBiFUKp+agc7bem0KxtMTs0/z86MSSxSrknYIkd822PJk/4oOFnMjLLwtARUpcN9dEM982jblkOpoe/xahtY5AUTLw1VFgxCArQPYhCbdogvRjNmVOsaL9bUt440QDIC2TEx0qx3OQMGDDwEJr8Lq2FMFuSjjMVJBJlZq508ztqXrtugcJ...
CertificateMIIE9DCCAtygAwIBAgIQAJTsDfVbBAk6GsI4YETERzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTAyNjE2NTczOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA3KEybjgwX9mumSck9V8jHw5JN3DJLMTvlaNKW6TDq3TEySE5l4hdabpSlEn23mxb+U8NcYzO...
Total processes
136
Monitored processes
9
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5380 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7288 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\trigger.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7296 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7592 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" Add-MpPreference -ExclusionPath $env:AppData | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7600 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7876 | "C:\Users\admin\AppData\Roaming\RuntimeBroker.exe" | C:\Users\admin\AppData\Roaming\RuntimeBroker.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RuntimeBroker Exit code: 3 Version: 1.1.1.1 Modules
| |||||||||||||||
| 7920 | "C:\Users\admin\AppData\Roaming\a7\RuntimeBroker.exe" | C:\Users\admin\AppData\Roaming\a7\RuntimeBroker.exe | RuntimeBroker.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: RuntimeBroker Version: 1.1.1.1 Modules
Quasar(PID) Process(7920) RuntimeBroker.exe Version1.4.1 C2 (2)anonam39-41248.portmap.io:41248 Sub_Dira7 Install_NameRuntimeBroker.exe Mutexbcabad1b-b1a9-478b-a187-3607b6476fd1 StartupRuntimeBroker TagRuntimeBroker LogDirLogs SignatureIRSv9+3T5/mK+JFqhTzHs9VCwzt9UmZdNX4mpaH6sUOiS/SzOx3oFMaYcXyRiq3yqqOTprI9n/pp405+UqX6svT2SVriTNryUvgv3RVeJGNnIrwWEV/OgsWN4ppBiFUKp+agc7bem0KxtMTs0/z86MSSxSrknYIkd822PJk/4oOFnMjLLwtARUpcN9dEM982jblkOpoe/xahtY5AUTLw1VFgxCArQPYhCbdogvRjNmVOsaL9bUt440QDIC2TEx0qx3OQMGDDwEJr8Lq2FMFuSjjMVJBJlZq508ztqXrtugcJ... CertificateMIIE9DCCAtygAwIBAgIQAJTsDfVbBAk6GsI4YETERzANBgkqhkiG9w0BAQ0FADAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMCAXDTI0MTAyNjE2NTczOVoYDzk5OTkxMjMxMjM1OTU5WjAbMRkwFwYDVQQDDBBRdWFzYXIgU2VydmVyIENBMIICIjANBgkqhkiG9w0BAQEFAAOCAg8AMIICCgKCAgEA3KEybjgwX9mumSck9V8jHw5JN3DJLMTvlaNKW6TDq3TEySE5l4hdabpSlEn23mxb+U8NcYzO... | |||||||||||||||
| 7996 | "C:\Users\admin\AppData\Roaming\a7\RuntimeBroker.exe" | C:\Users\admin\AppData\Roaming\a7\RuntimeBroker.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RuntimeBroker Exit code: 2 Version: 1.1.1.1 Modules
| |||||||||||||||
Total events
15 299
Read events
15 297
Write events
2
Delete events
0
Modification events
| (PID) Process: | (7876) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RuntimeBroker |
Value: "C:\Users\admin\AppData\Roaming\a7\RuntimeBroker.exe" | |||
| (PID) Process: | (7920) RuntimeBroker.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | RuntimeBroker |
Value: "C:\Users\admin\AppData\Roaming\a7\RuntimeBroker.exe" | |||
Executable files
2
Suspicious files
7
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7288 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bb1ty33p.nq1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:5DE4B9662BD5819BE0D34950909608C9 | SHA256:CF221456A0A59EAD871C4C9828798CB5587B7C7AF4C13B8A811FB05E384D8AB2 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\J1E6AX4ANDUZCSZH6SYC.temp | binary | |
MD5:5DE4B9662BD5819BE0D34950909608C9 | SHA256:CF221456A0A59EAD871C4C9828798CB5587B7C7AF4C13B8A811FB05E384D8AB2 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10bfc7.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_uubowdwf.zeu.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7592 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:8C9EFCB40660F8974A3EF5DD97BF47A3 | SHA256:787233FF4464DEAB89F552CE7C2E2EBC0A2E89607495531132988D08AB743DF1 | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Roaming\RuntimeBroker.exe | executable | |
MD5:29A51CECF6F6EBBE981A939F208BDCDF | SHA256:5E6C07ED2FC454CCA8BE8EBD13A18D32BDB217859A8C9DC871A104A3017D32D5 | |||
| 7592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fxbfiutf.k3k.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7592 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gejd32yh.s4b.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7592 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10d0a0.TMP | binary | |
MD5:5DE4B9662BD5819BE0D34950909608C9 | SHA256:CF221456A0A59EAD871C4C9828798CB5587B7C7AF4C13B8A811FB05E384D8AB2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
90
DNS requests
20
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5352 | RUXIMICS.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5352 | RUXIMICS.exe | GET | 304 | 23.48.23.141:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8152 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8152 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8152 | SIHClient.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8152 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8152 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
8152 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5352 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5352 | RUXIMICS.exe | 23.48.23.141:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5352 | RUXIMICS.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
anonam39-41248.portmap.io |
| malicious |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
— | — | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
— | — | Misc activity | ET INFO Request for EXE via Powershell |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET HUNTING EXE Downloaded from Github |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |