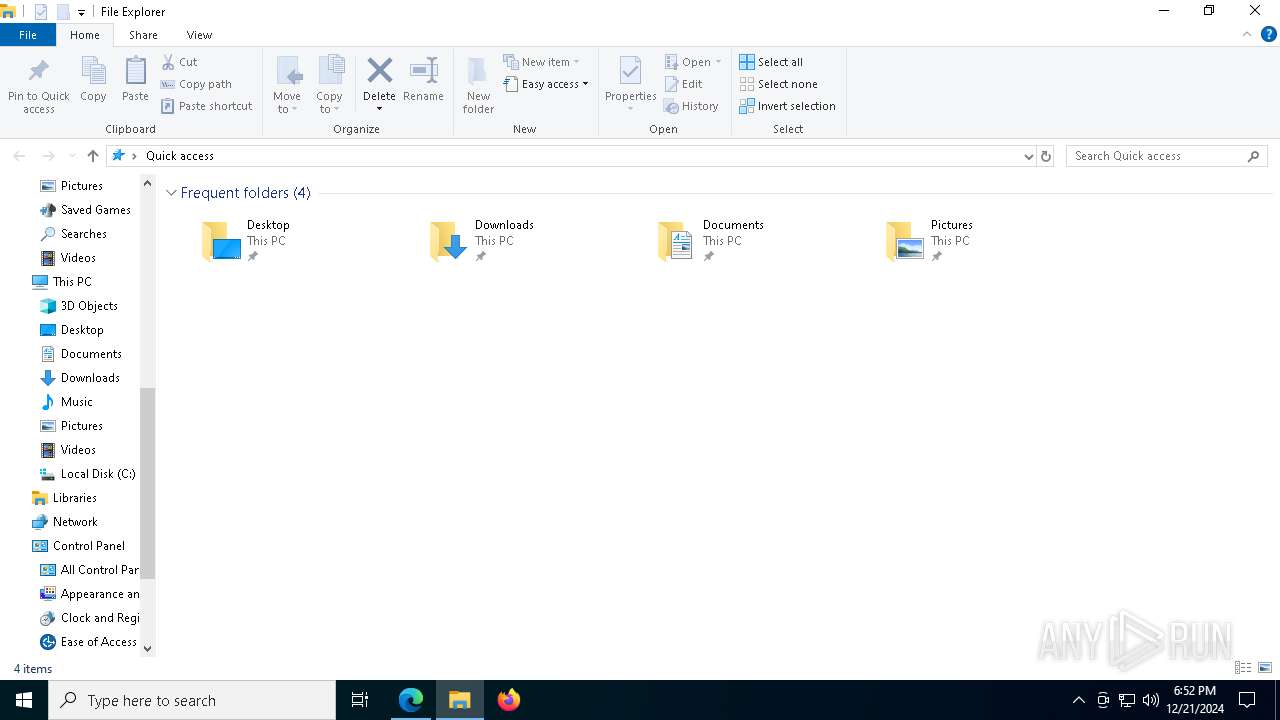
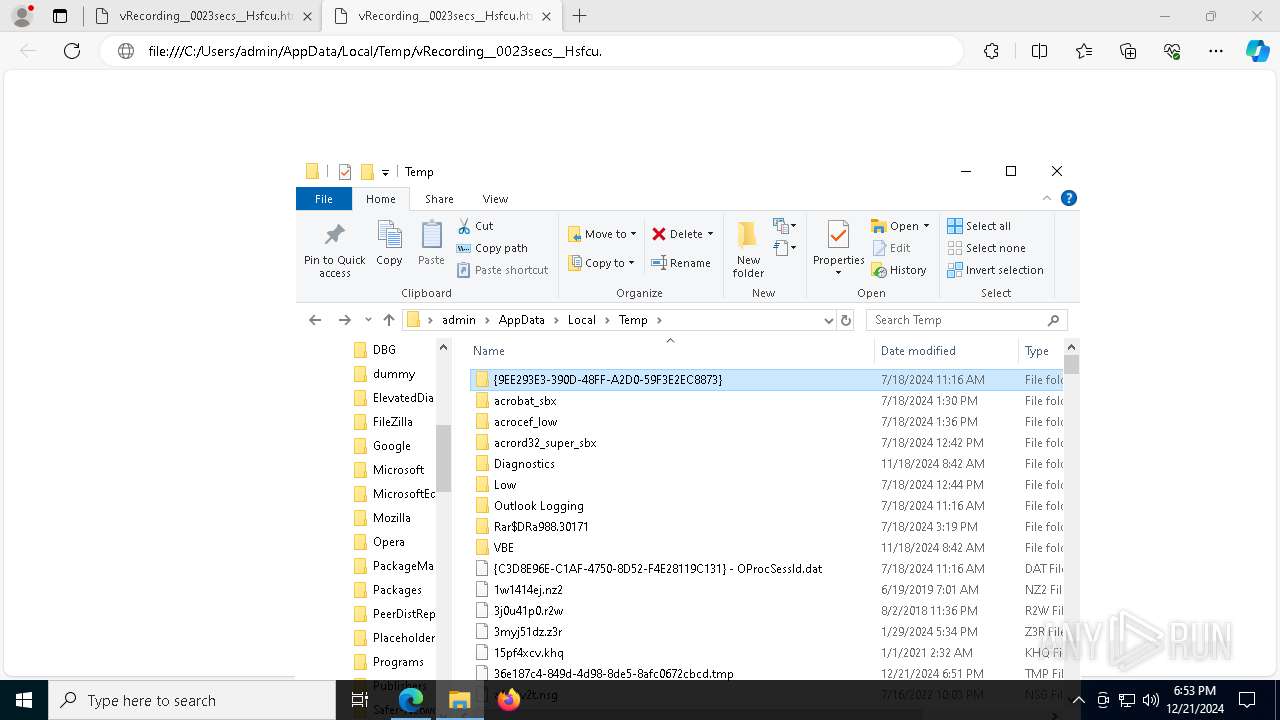
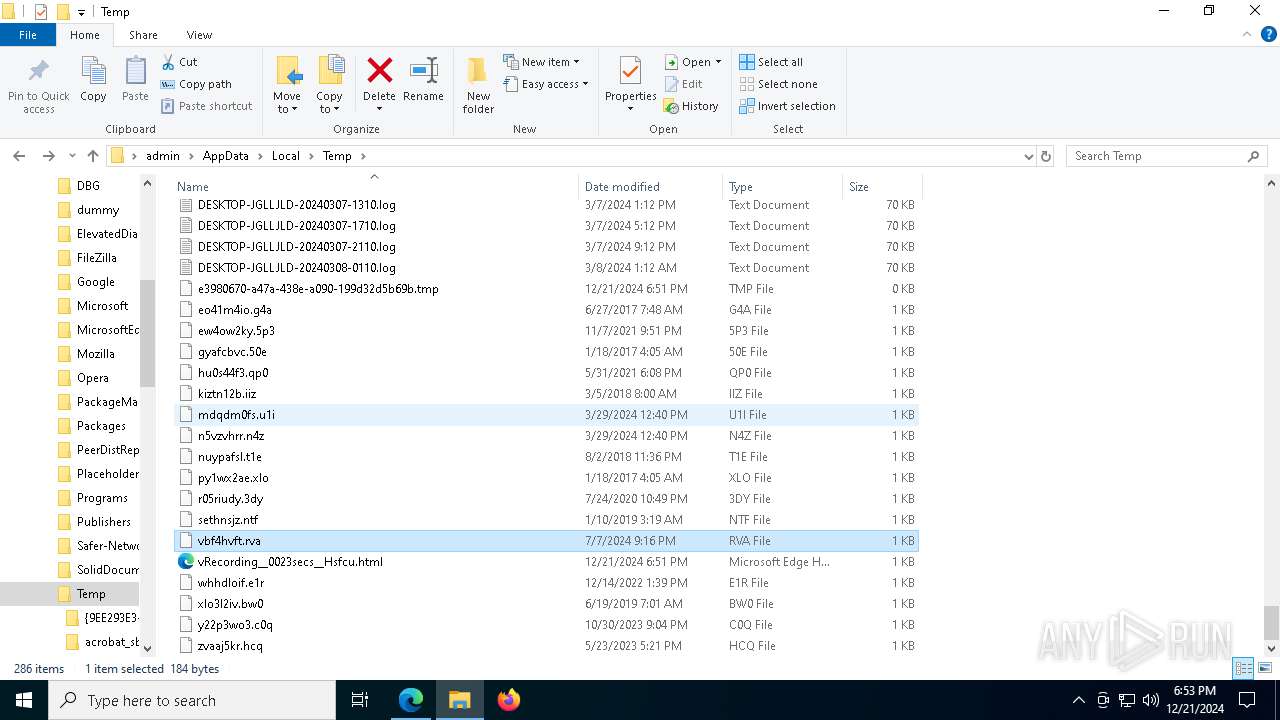
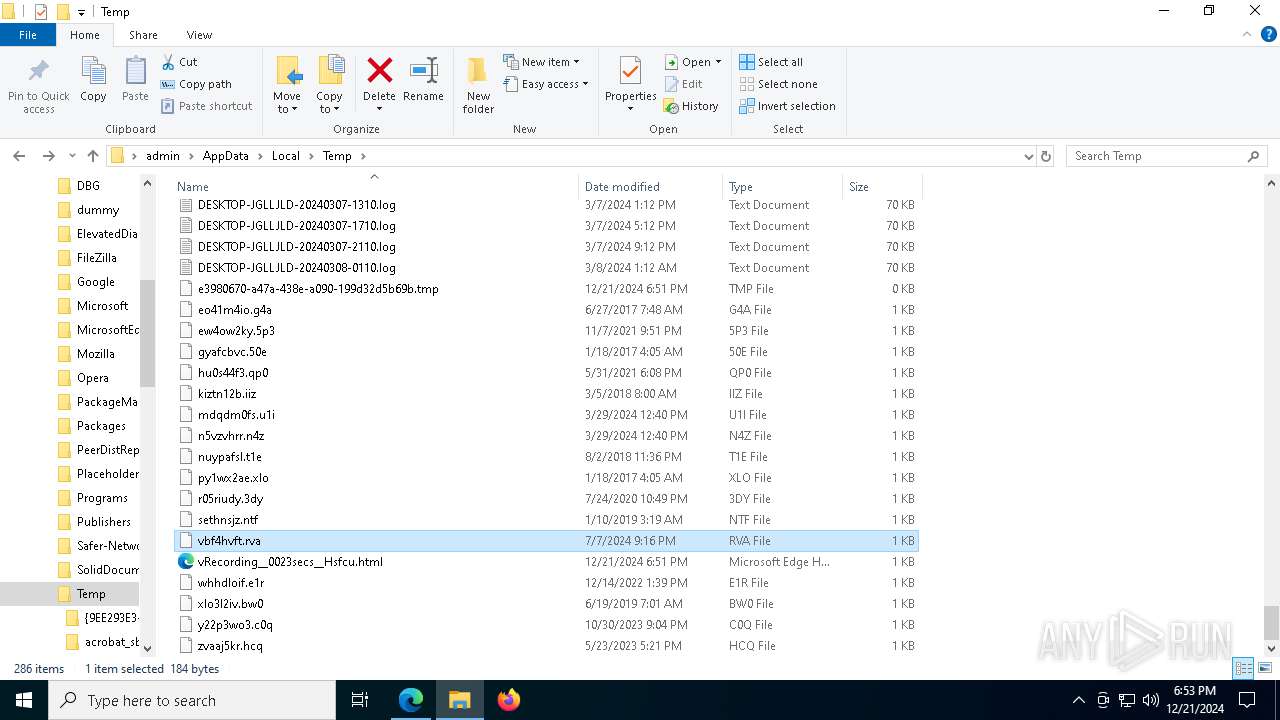
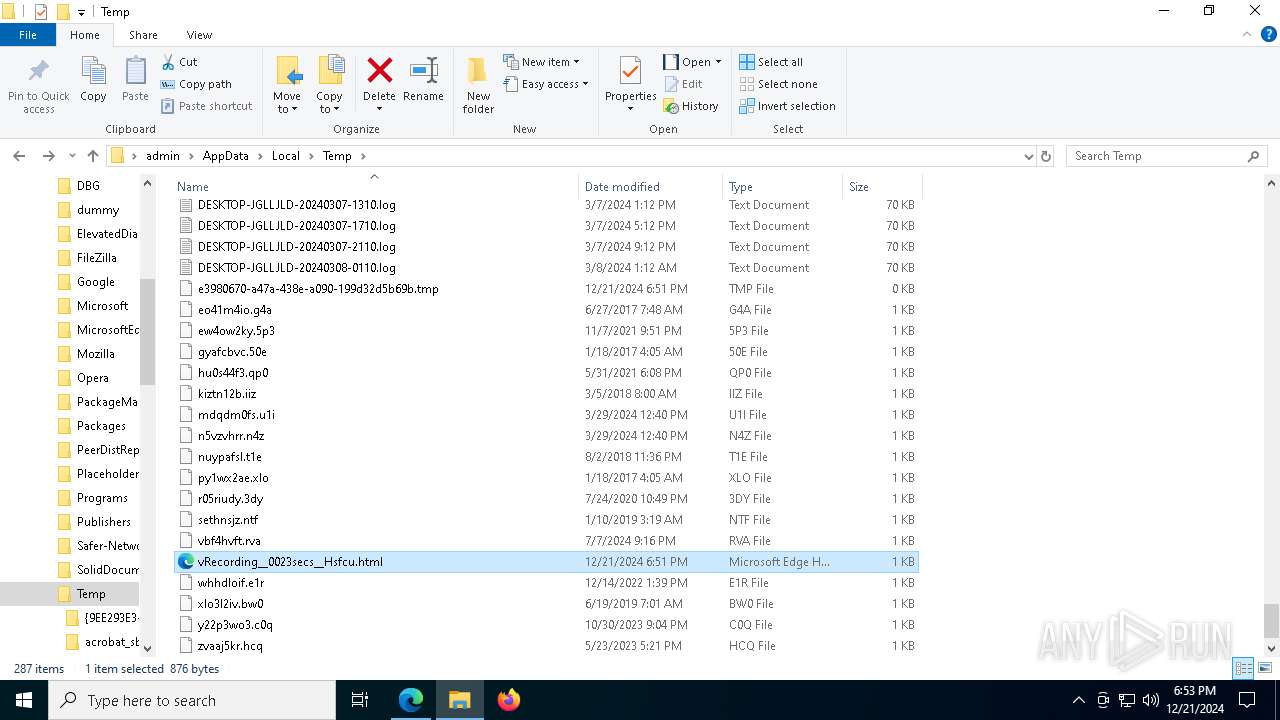
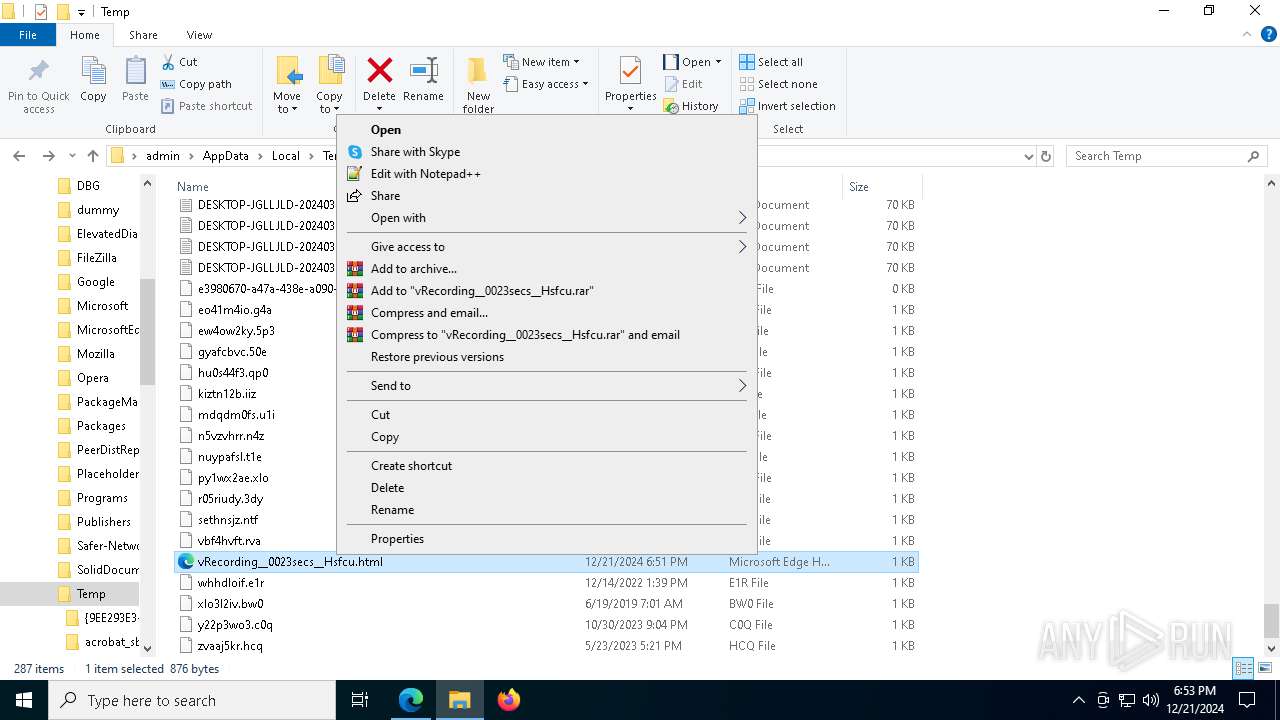
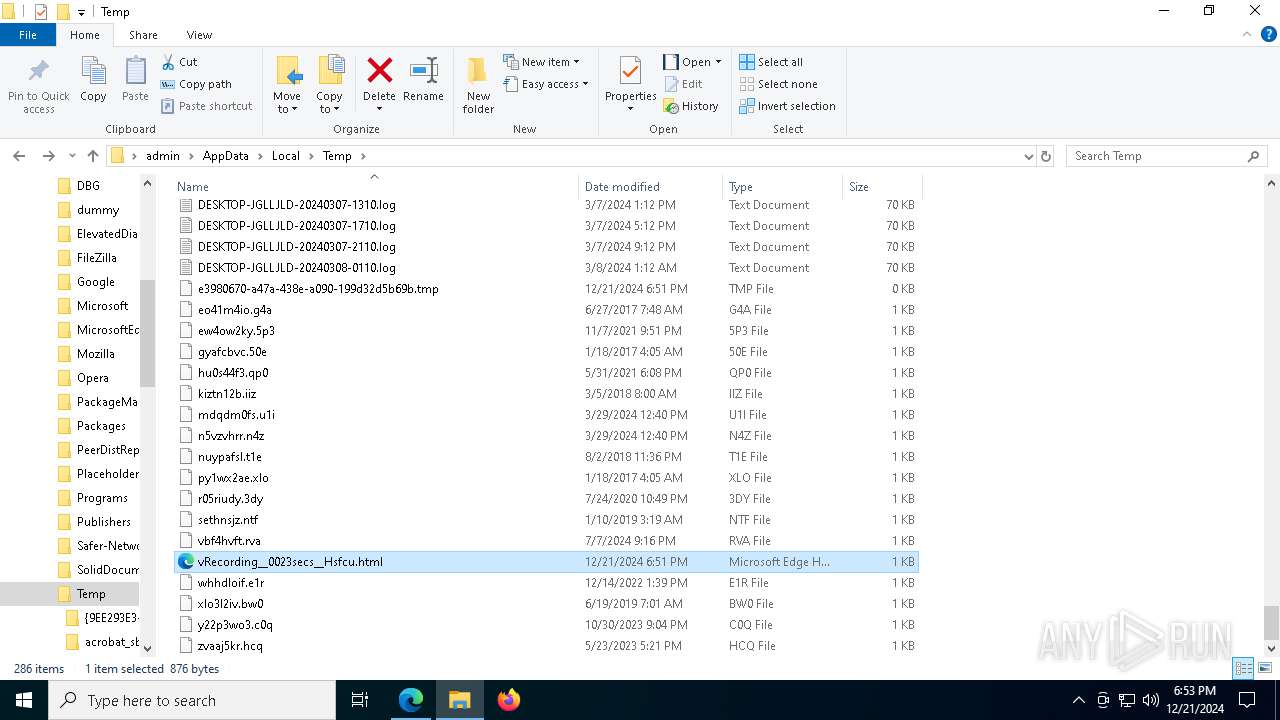
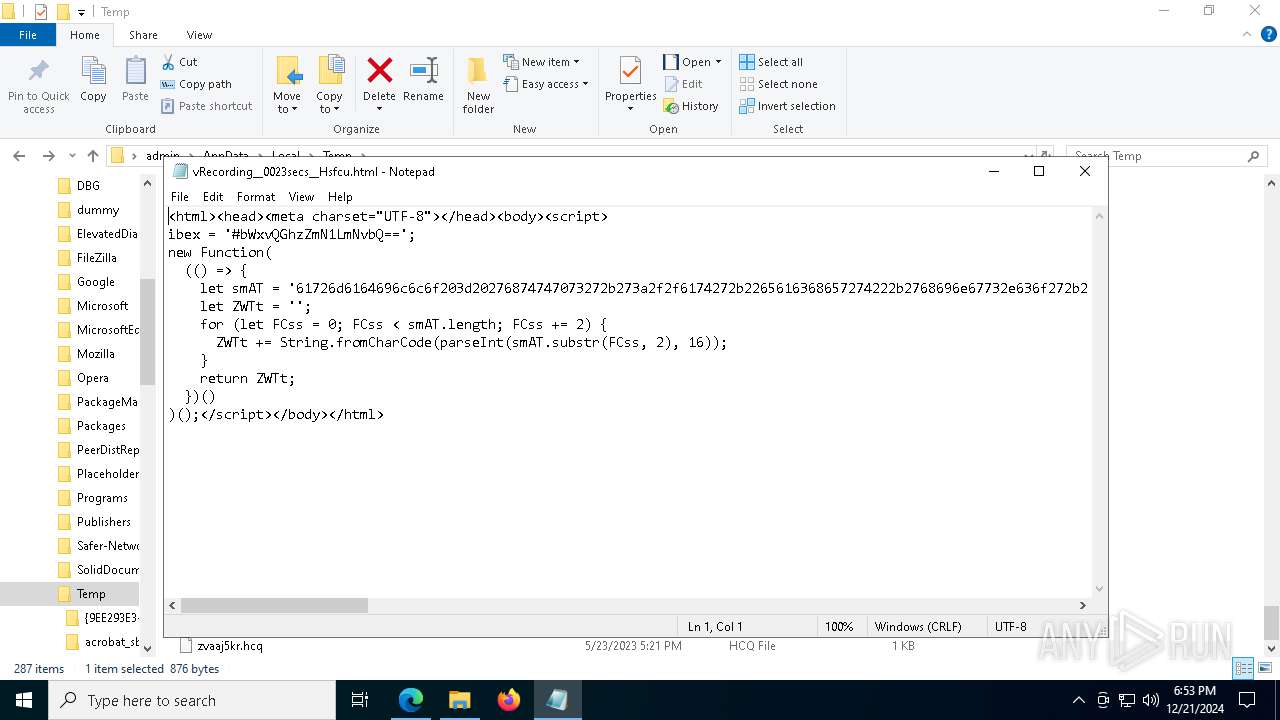
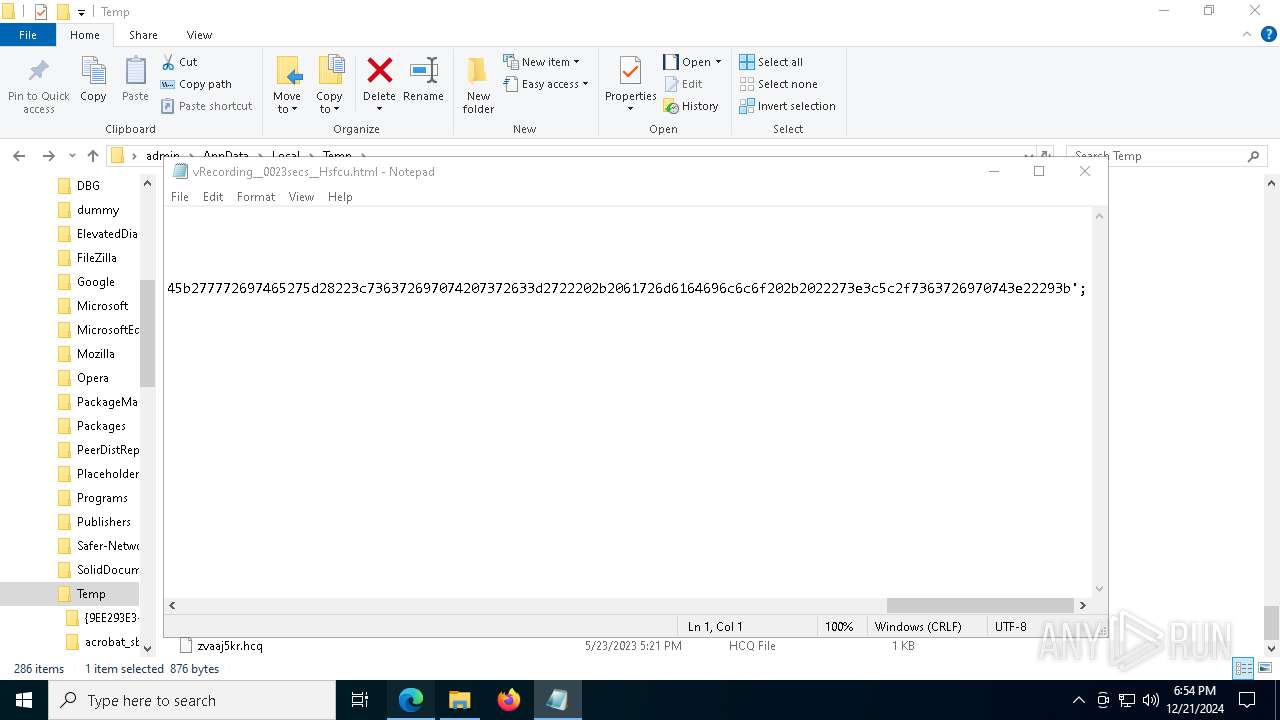
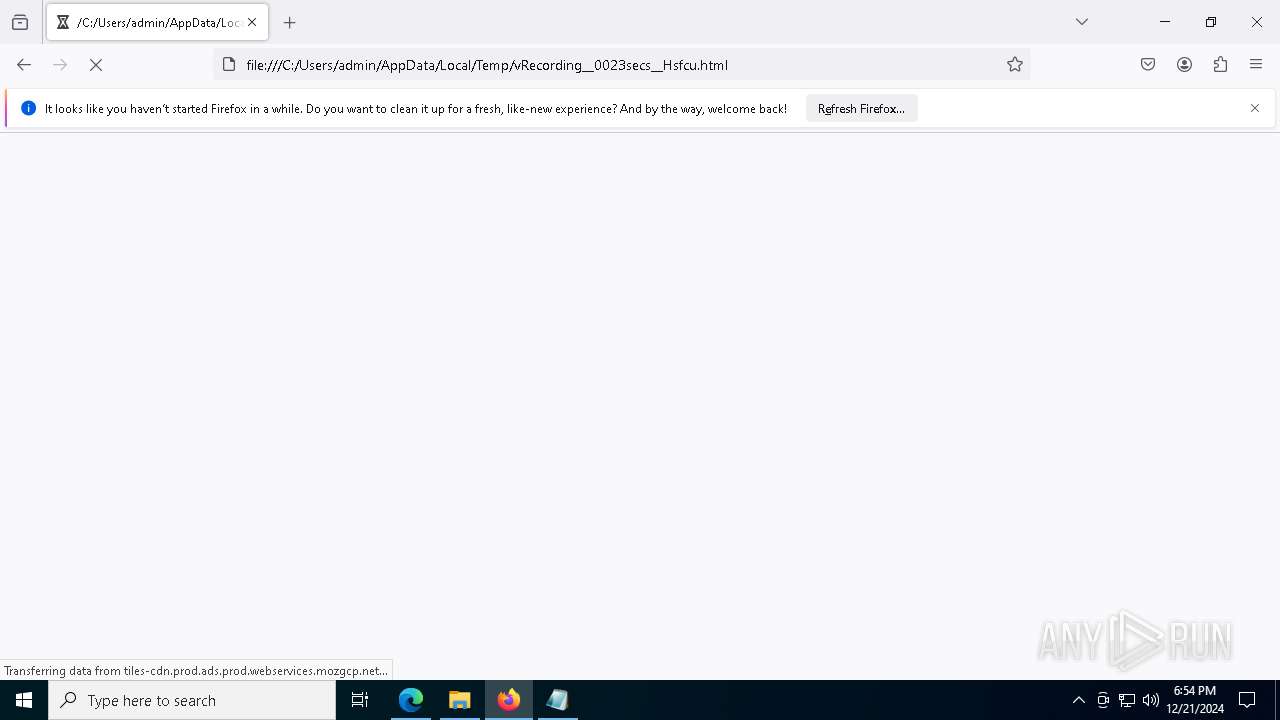
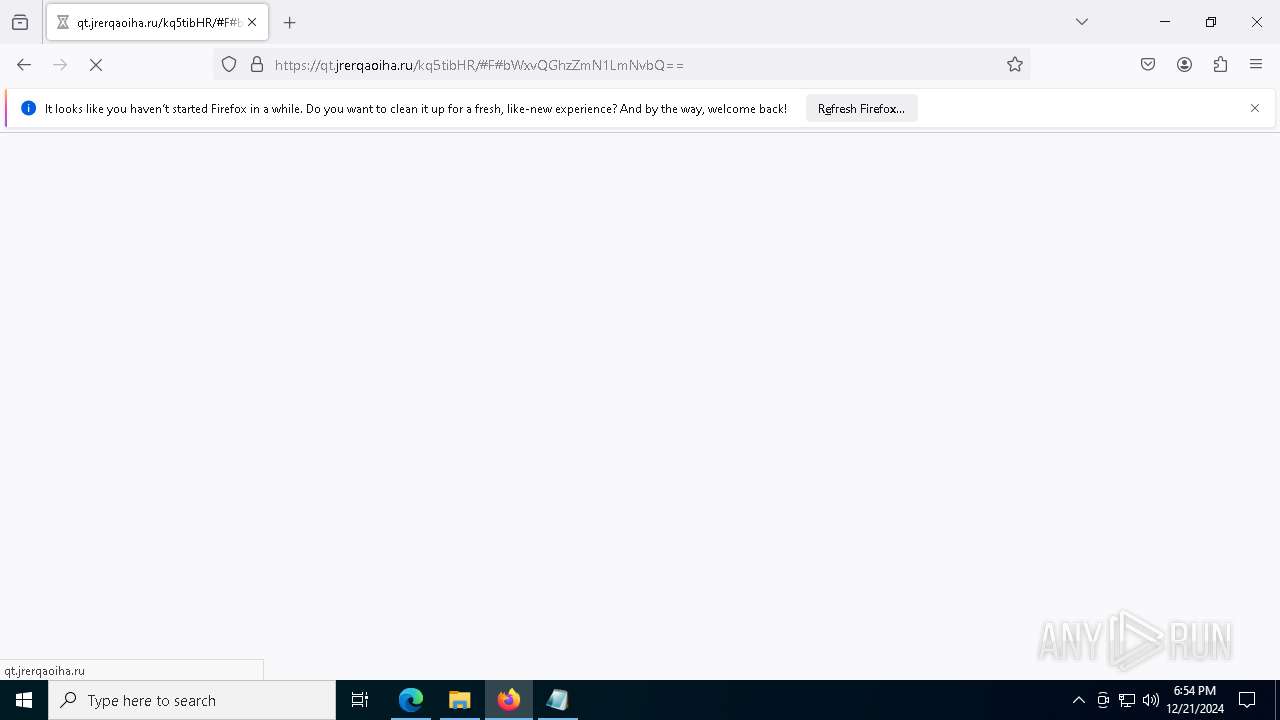
| File name: | vRecording__0023secs__Hsfcu.html |
| Full analysis: | https://app.any.run/tasks/ee67469d-88ac-409d-af52-b78a4fcca6ae |
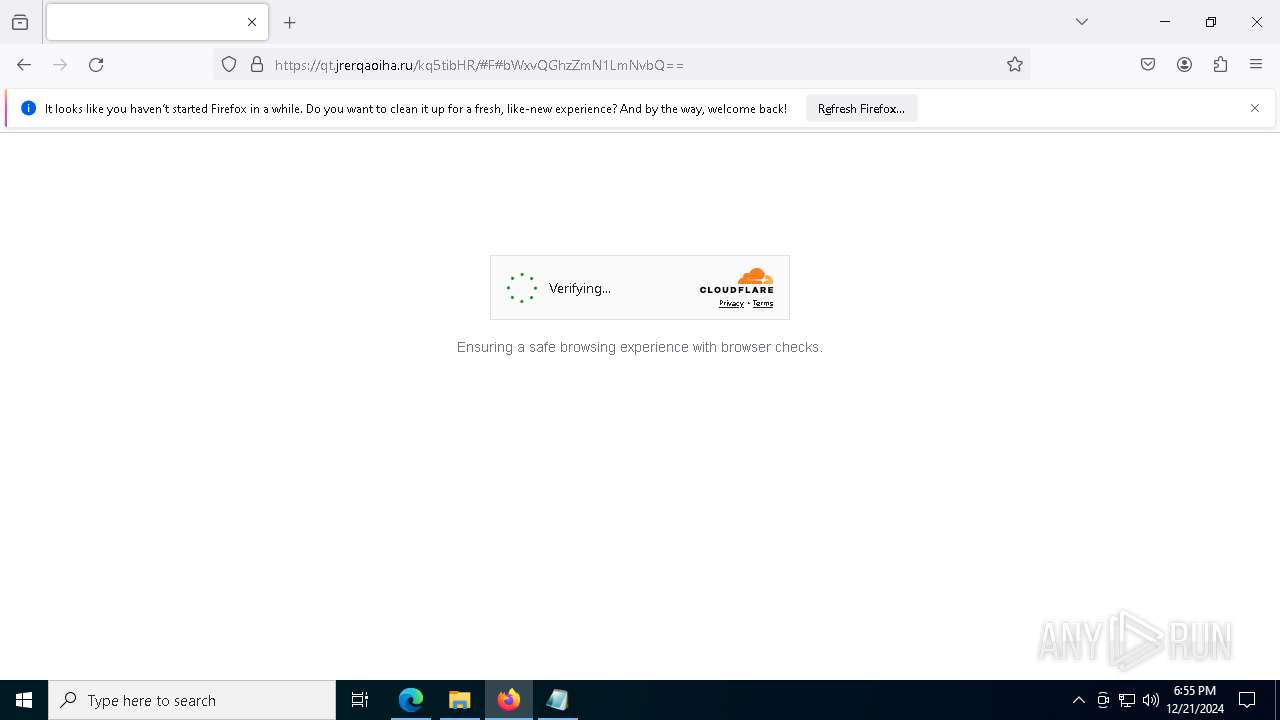
| Verdict: | Malicious activity |
| Threats: | Tycoon 2FA is a phishing-as-a-service (PhaaS) platform designed to bypass multi-factor authentication (MFA) protections, particularly targeting Microsoft 365 and Gmail accounts. Its advanced evasion techniques and modular architecture make it a significant threat to organizations relying on MFA for security. |
| Analysis date: | December 21, 2024, 18:51:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines (548), with CRLF line terminators |
| MD5: | AA23C47ABB1B5A3CFF16F45606E34863 |
| SHA1: | 525AF780ABCDC89497EF59496A653205B7C7CCDA |
| SHA256: | 894CAED2D12B39F4B49FCB71958F14897AA441018FA5F1121725B677426DAE26 |
| SSDEEP: | 12:kxVPs1MsvDIwMloO6rVmxi6nWtAHW2JmDi1coNmzGa7HciWW833GJlWC3I:kHE1MUrVmccCAH/OiRADc333O0C3I |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 6400)
- svchost.exe (PID: 2192)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- msedge.exe (PID: 2940)
- firefox.exe (PID: 7120)
- firefox.exe (PID: 440)
Reads Environment values
- identity_helper.exe (PID: 7556)
Checks supported languages
- identity_helper.exe (PID: 7556)
Reads the computer name
- identity_helper.exe (PID: 7556)
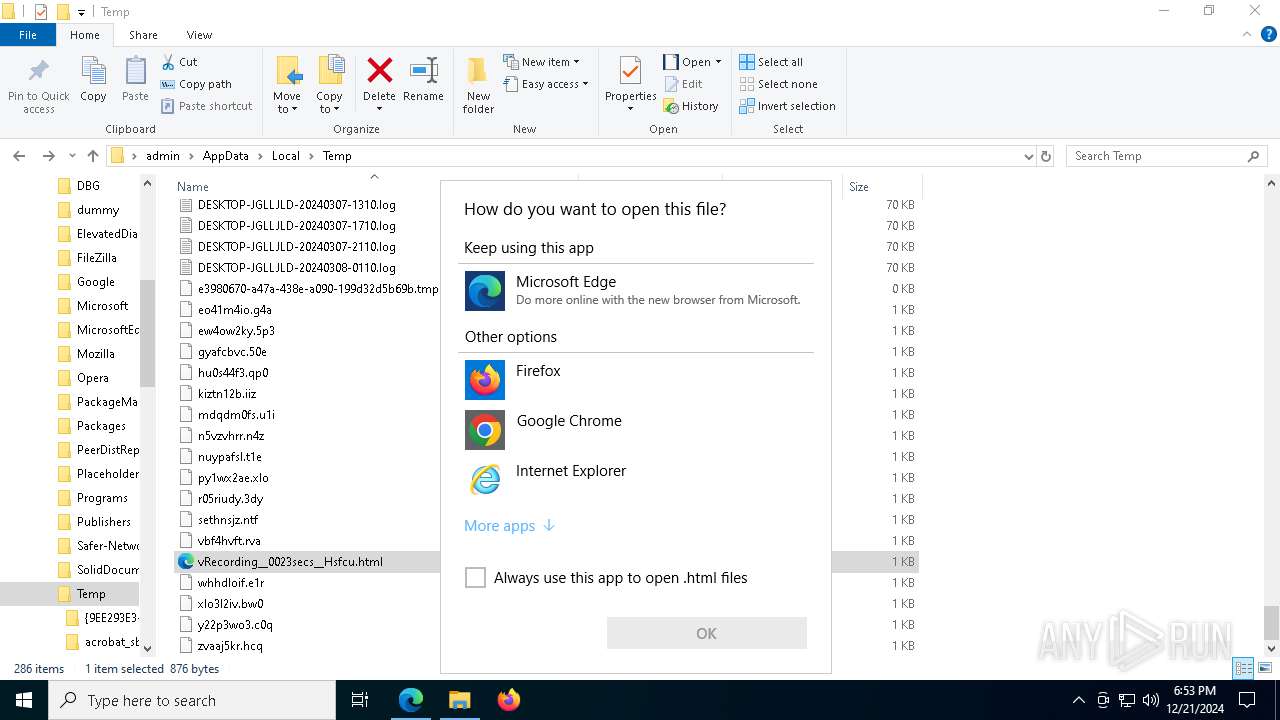
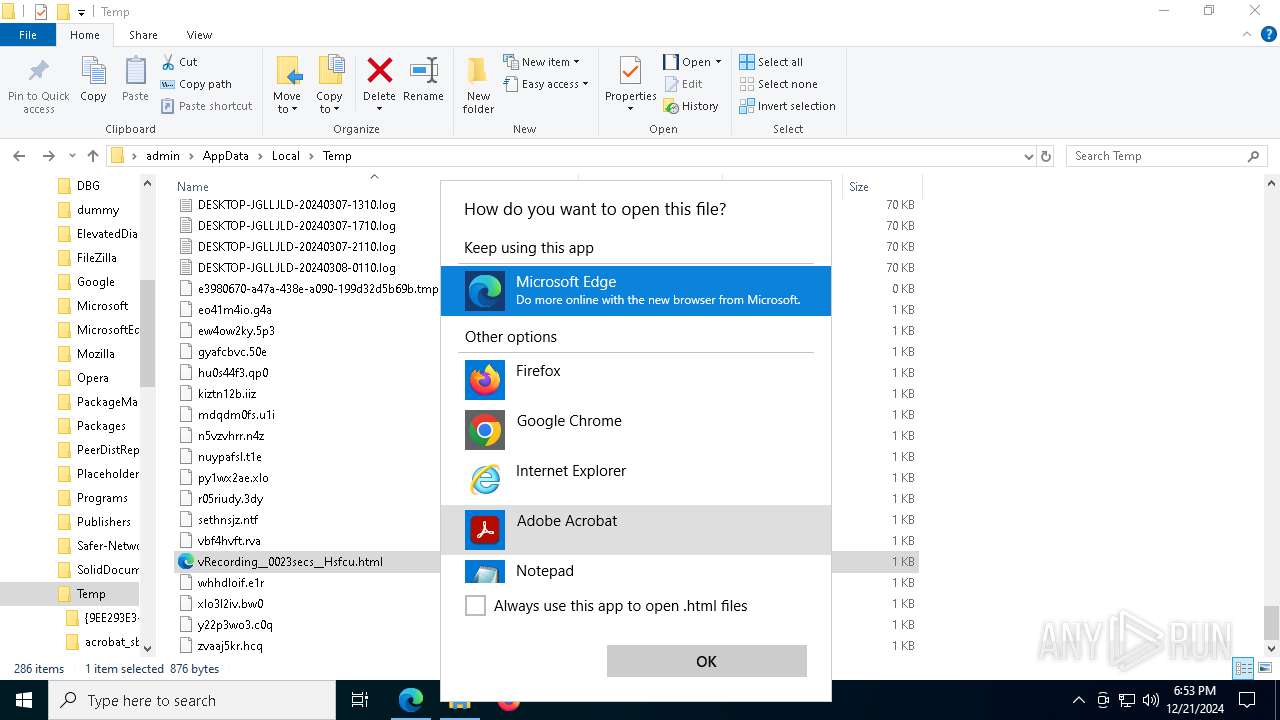
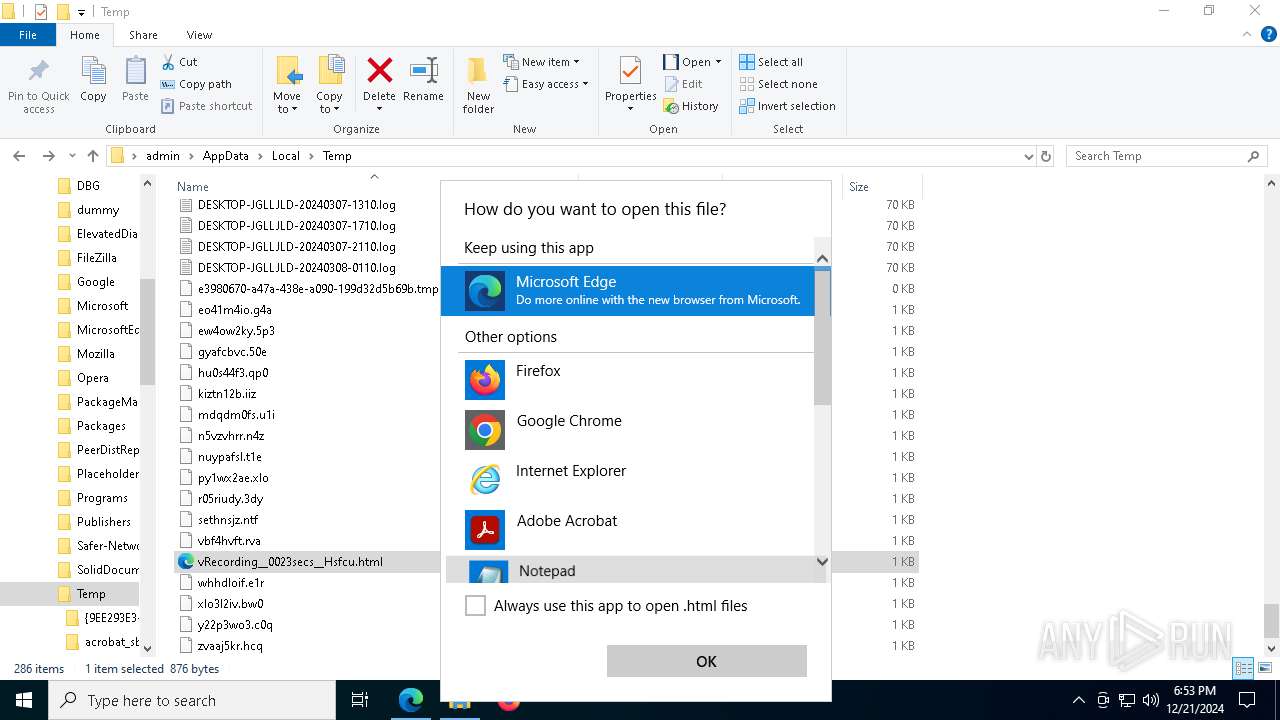
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 4984)
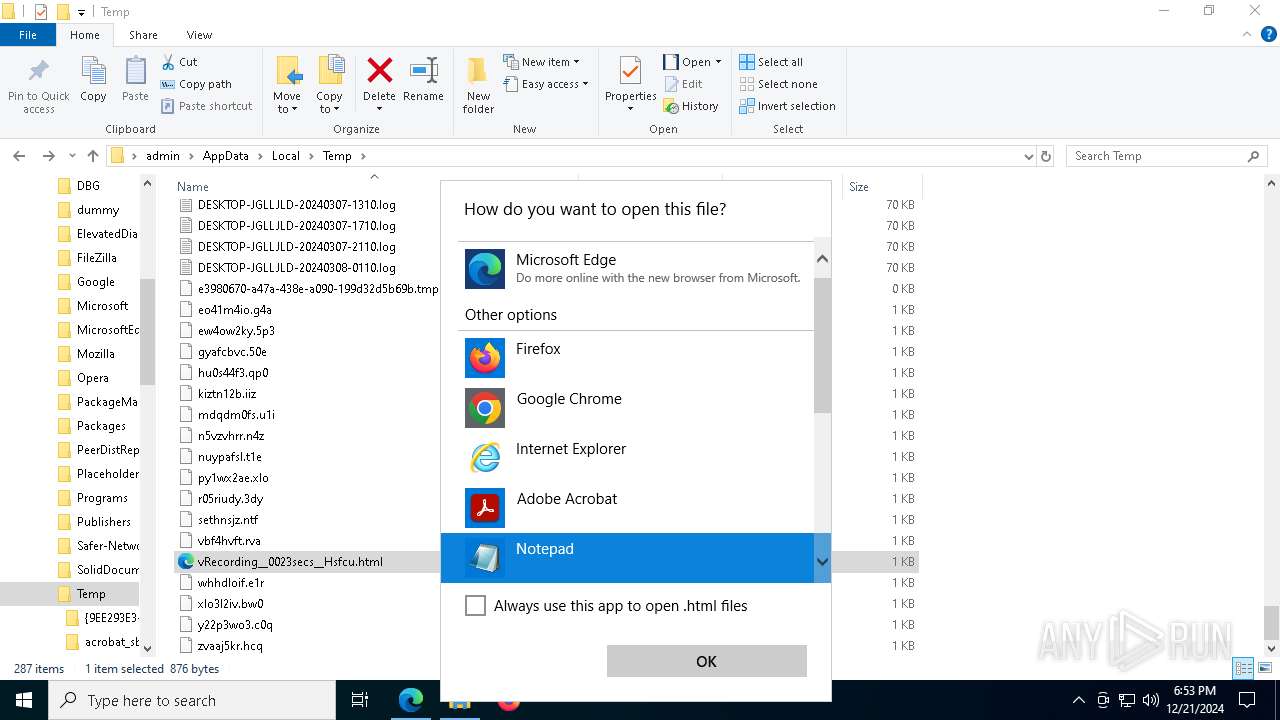
- notepad.exe (PID: 7180)
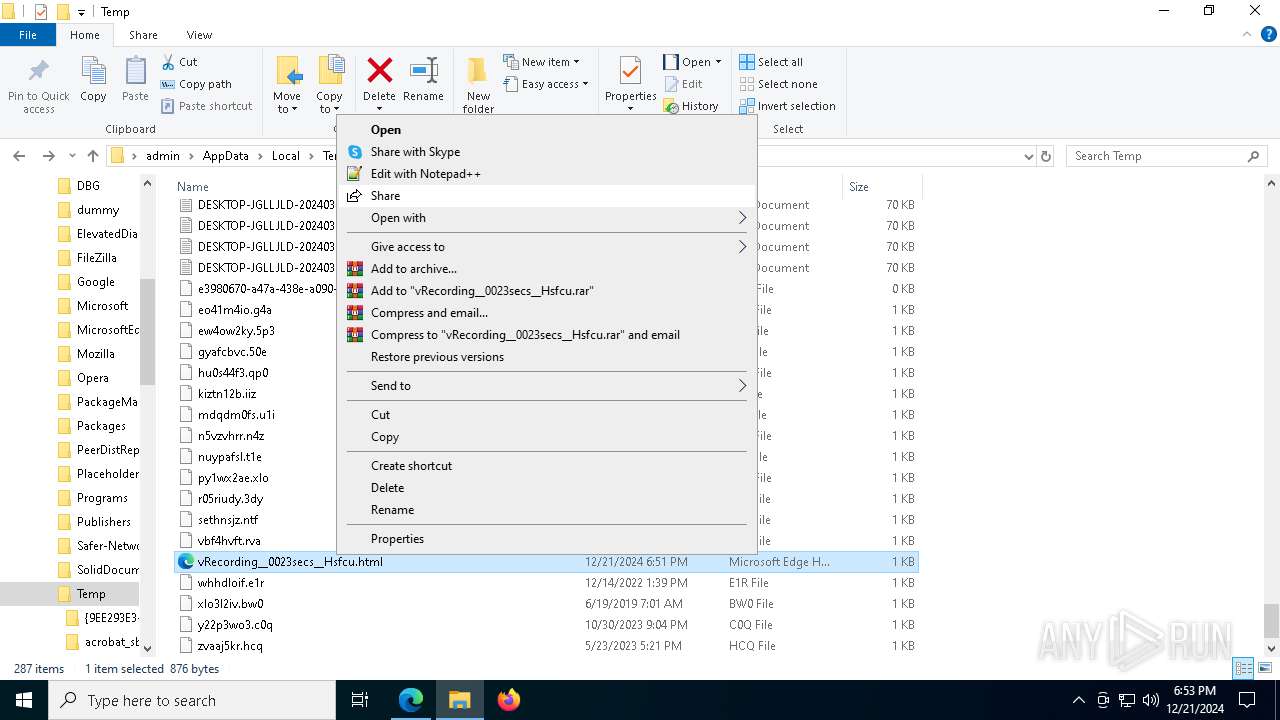
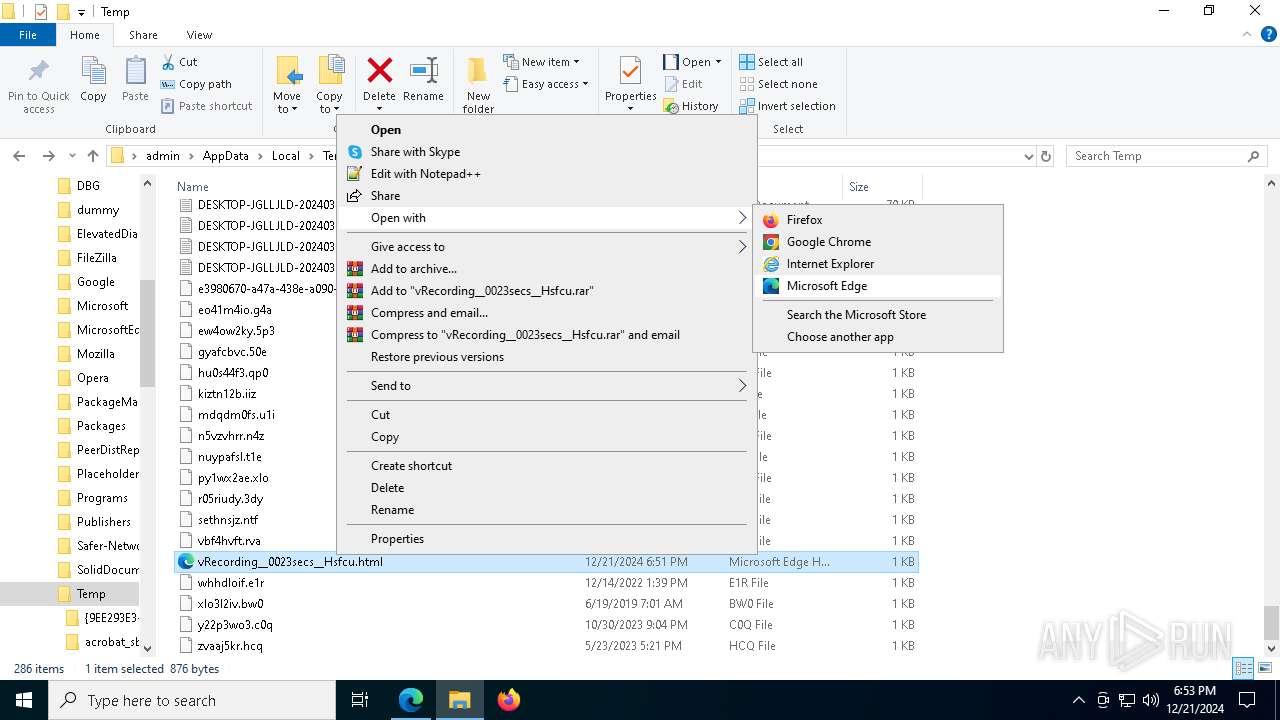
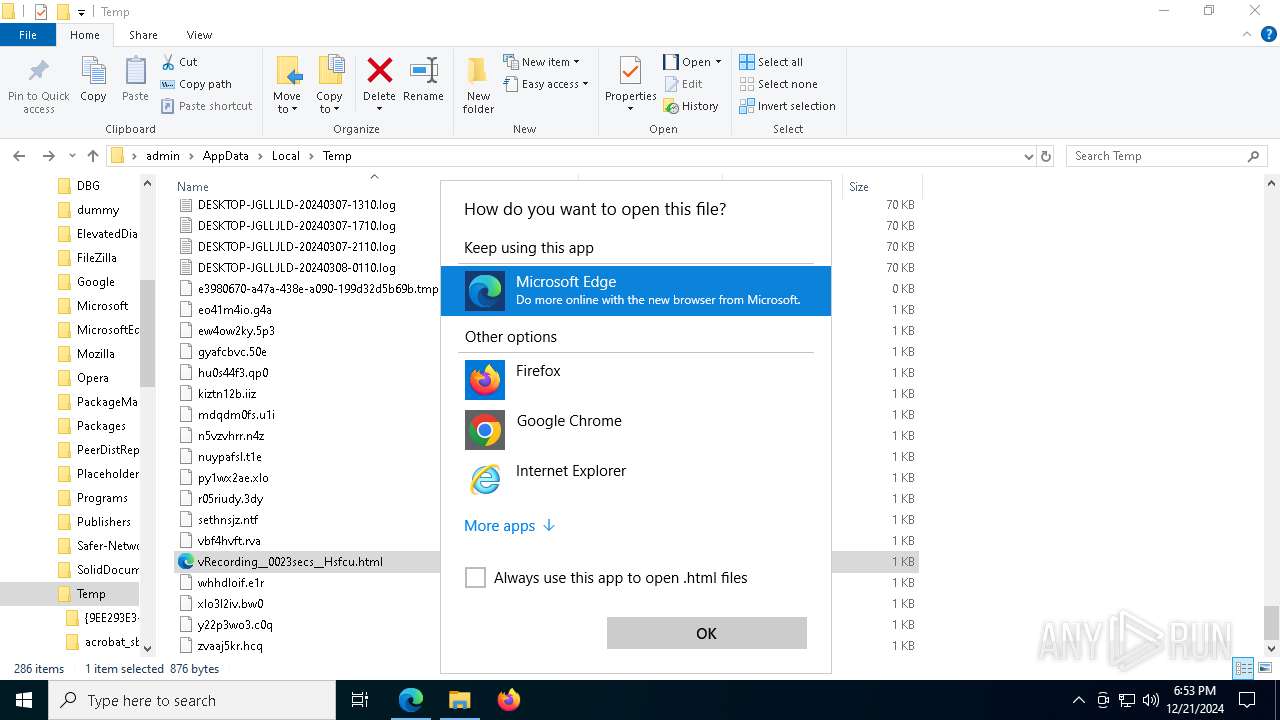
Manual execution by a user
- msedge.exe (PID: 8000)
- firefox.exe (PID: 440)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4984)
Executable content was dropped or overwritten
- msedge.exe (PID: 7884)
The process uses the downloaded file
- OpenWith.exe (PID: 4984)
The sample compiled with english language support
- msedge.exe (PID: 7884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
208
Monitored processes
77
Malicious processes
3
Suspicious processes
0
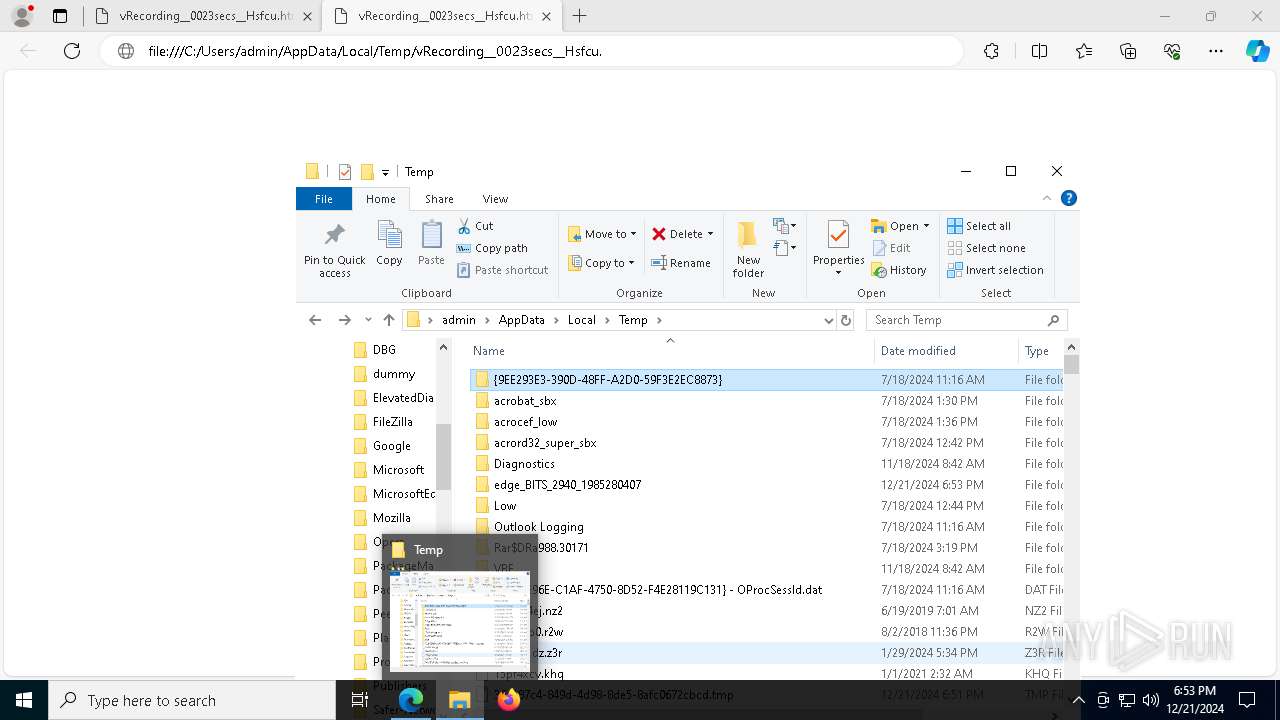
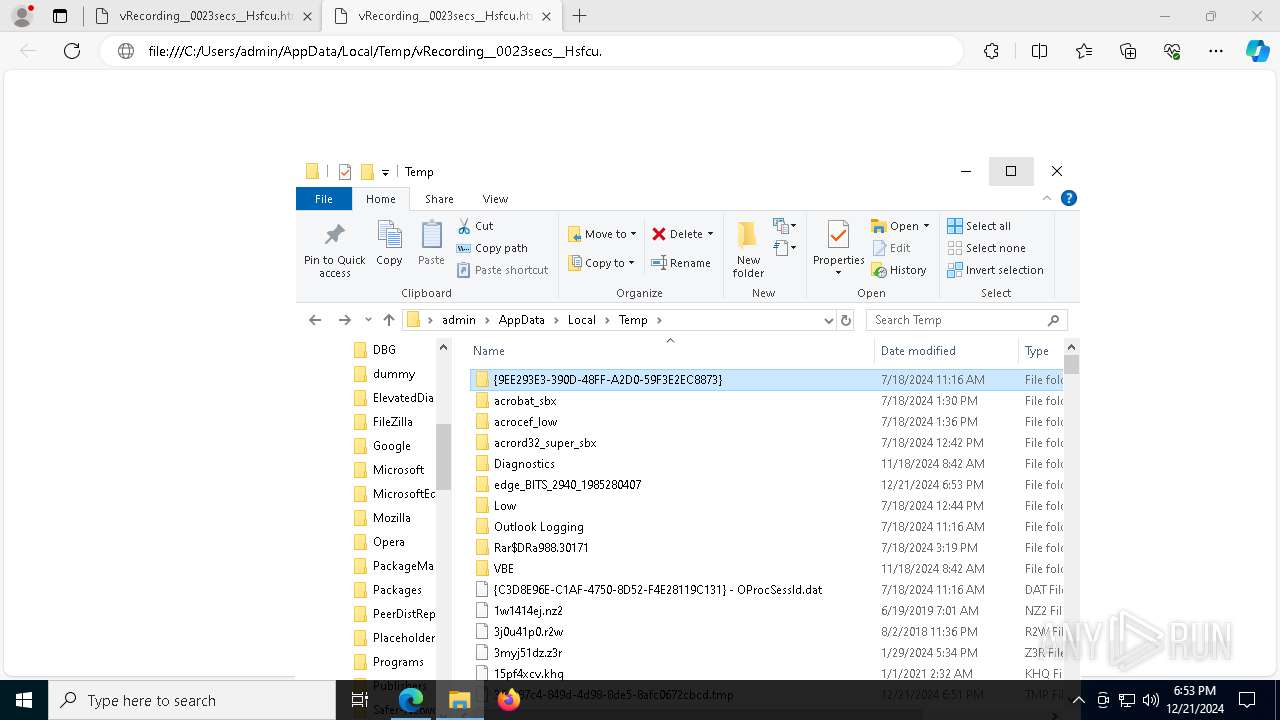
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1540 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5592 -childID 8 -isForBrowser -prefsHandle 5672 -prefMapHandle 5704 -prefsLen 31197 -prefMapSize 244583 -jsInitHandle 1428 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {5bfa1b92-eb12-40a2-8f6b-ef855d138cb2} 7120 "\\.\pipe\gecko-crash-server-pipe.7120" 14f47413150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1544 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5740 --field-trial-handle=2308,i,7589160668903024836,13442757014297990825,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1572 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5524 --field-trial-handle=2308,i,7589160668903024836,13442757014297990825,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4276 --field-trial-handle=2308,i,7589160668903024836,13442757014297990825,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=4020 --field-trial-handle=2308,i,7589160668903024836,13442757014297990825,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6564 --field-trial-handle=2308,i,7589160668903024836,13442757014297990825,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
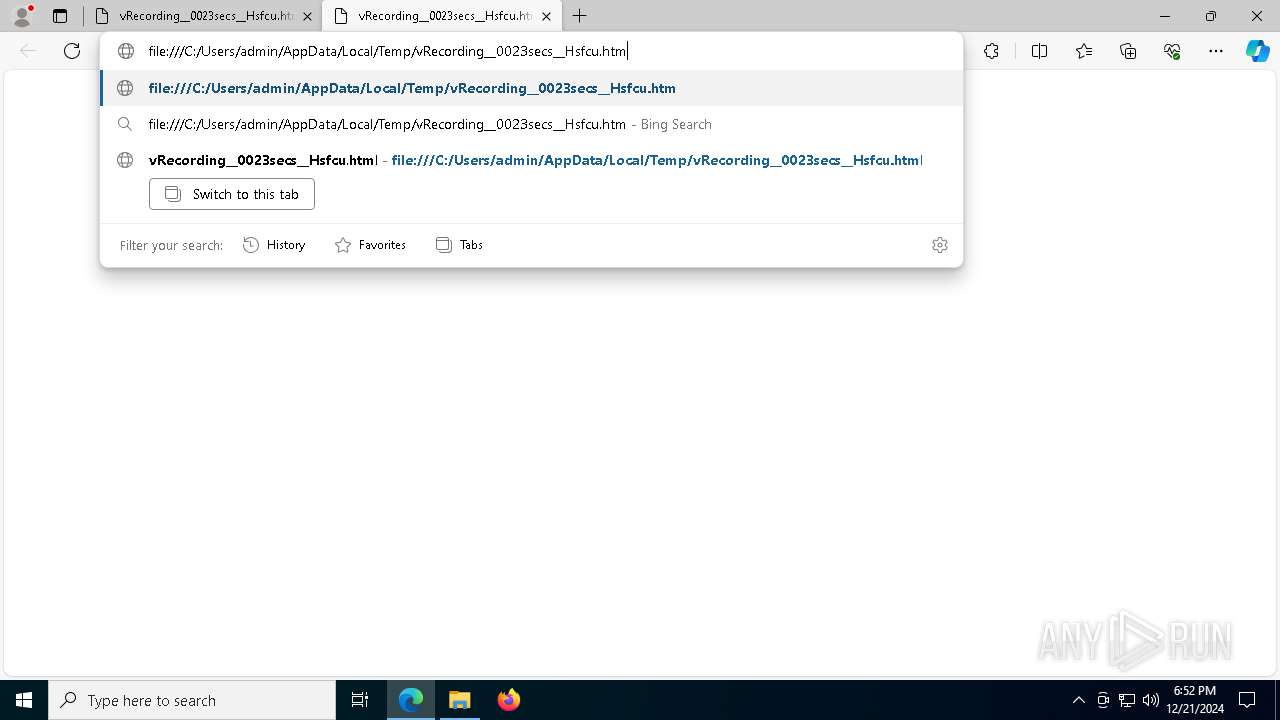
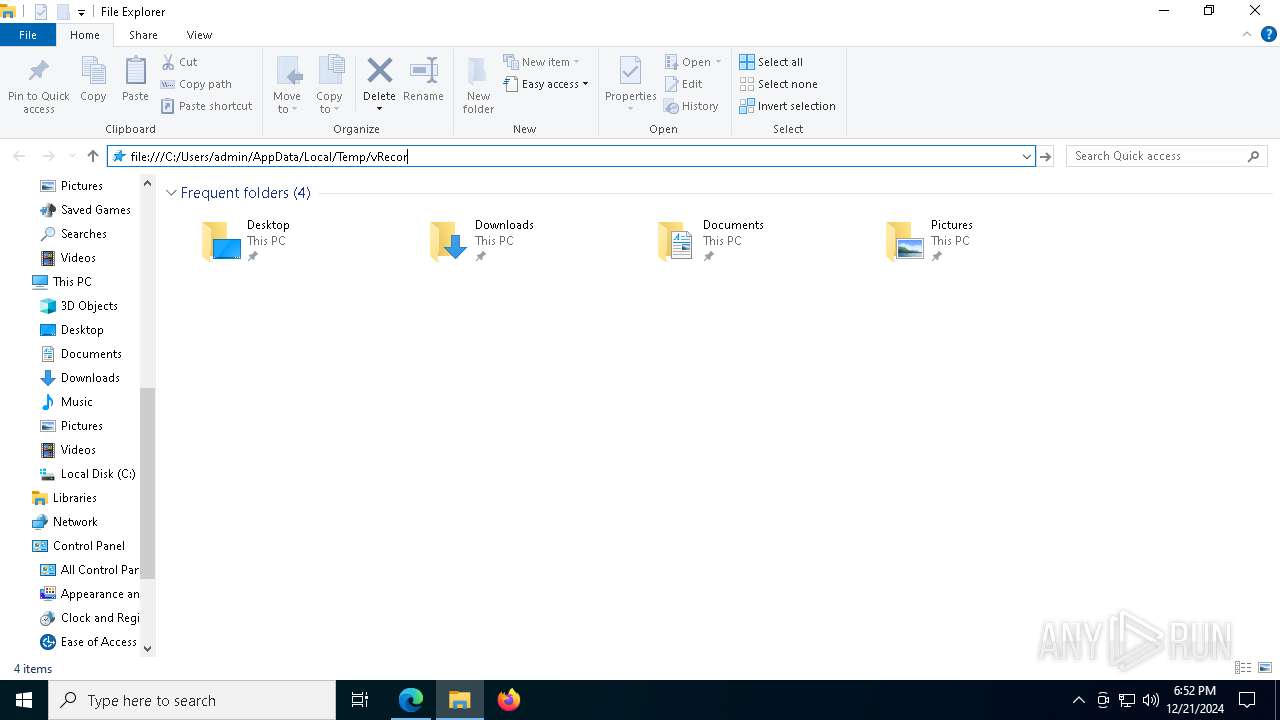
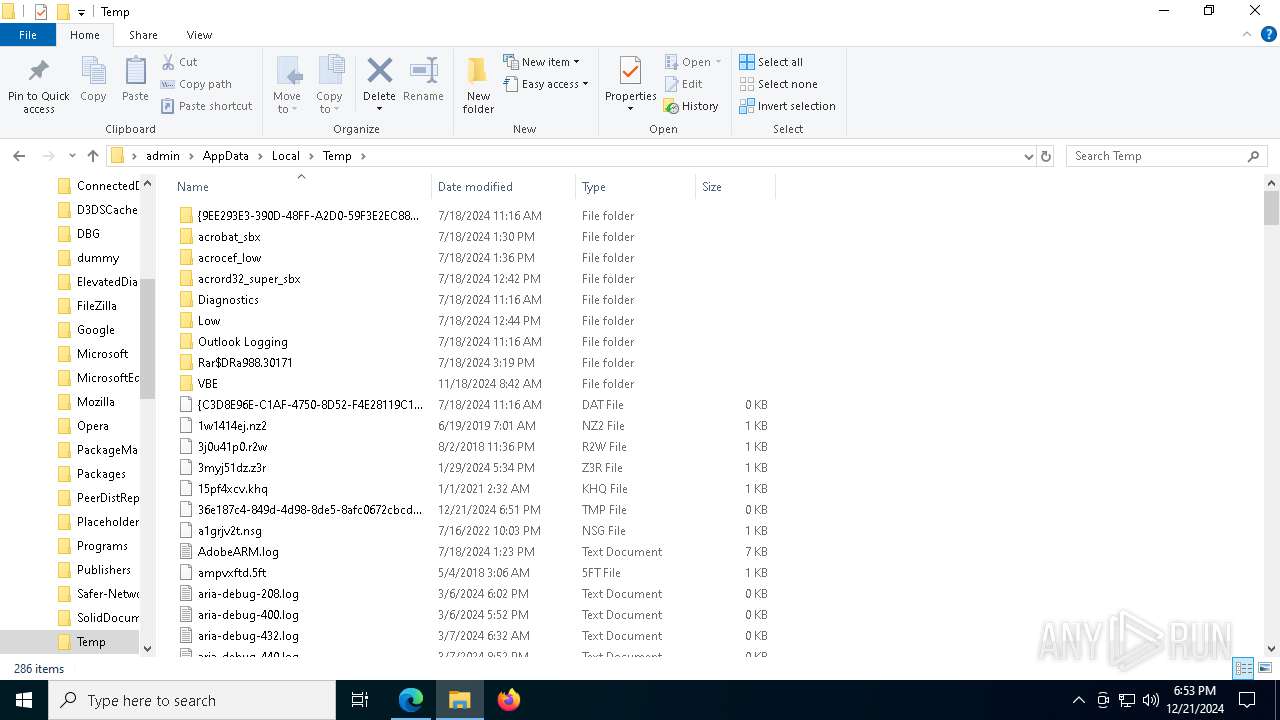
| 2940 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" C:\Users\admin\AppData\Local\Temp\vRecording__0023secs__Hsfcu.html | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5188 -childID 5 -isForBrowser -prefsHandle 5040 -prefMapHandle 5076 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1428 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {439847d5-8be5-40a9-ac68-c822399aa36b} 7120 "\\.\pipe\gecko-crash-server-pipe.7120" 14f4f1f8f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
Total events
27 812
Read events
27 791
Write events
21
Delete events
0
Modification events
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262900 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6D64C859-2F55-4E03-ABDD-46F5B2A3DEDE} | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 87FEA08762882F00 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4C0FAA8762882F00 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8D9FE98762882F00 | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (2940) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
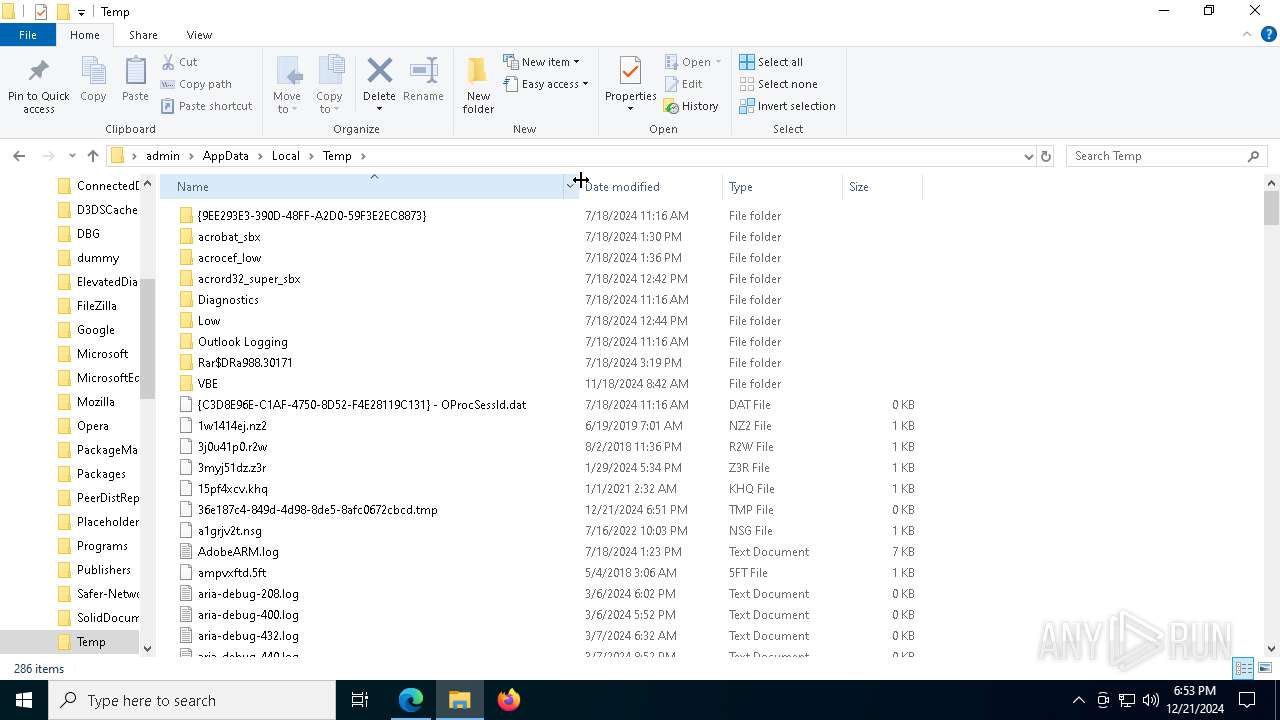
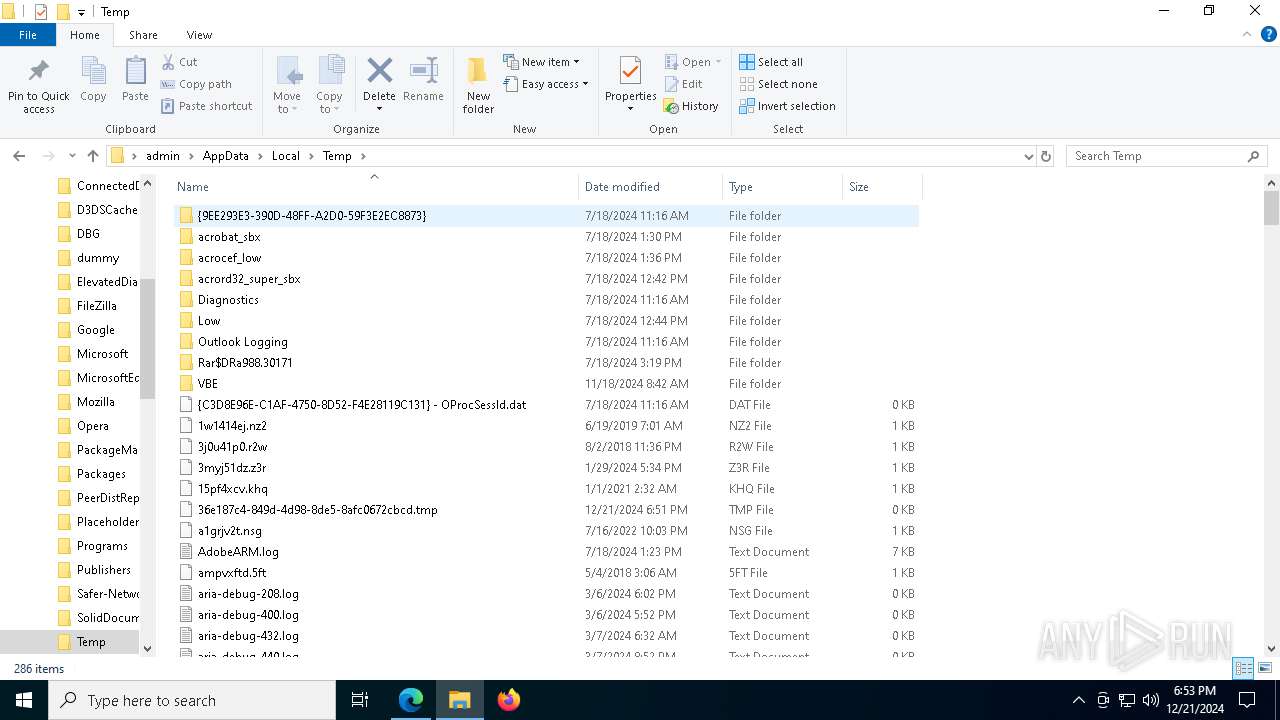
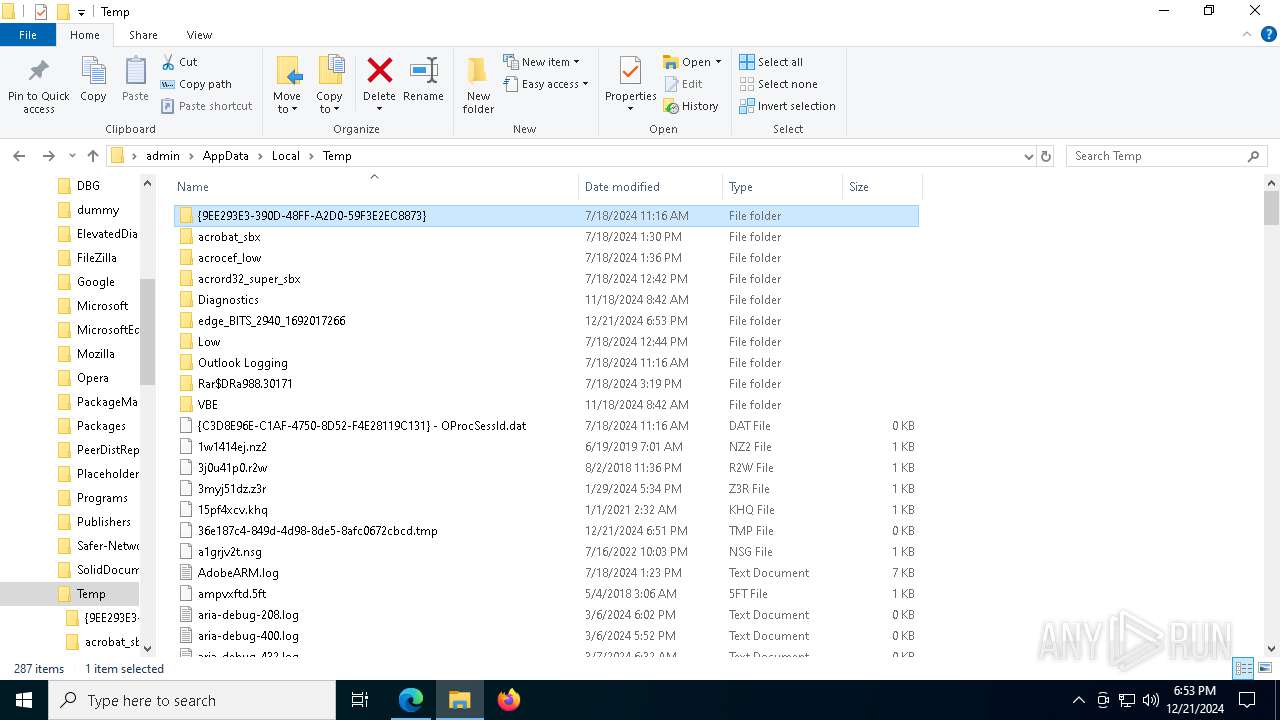
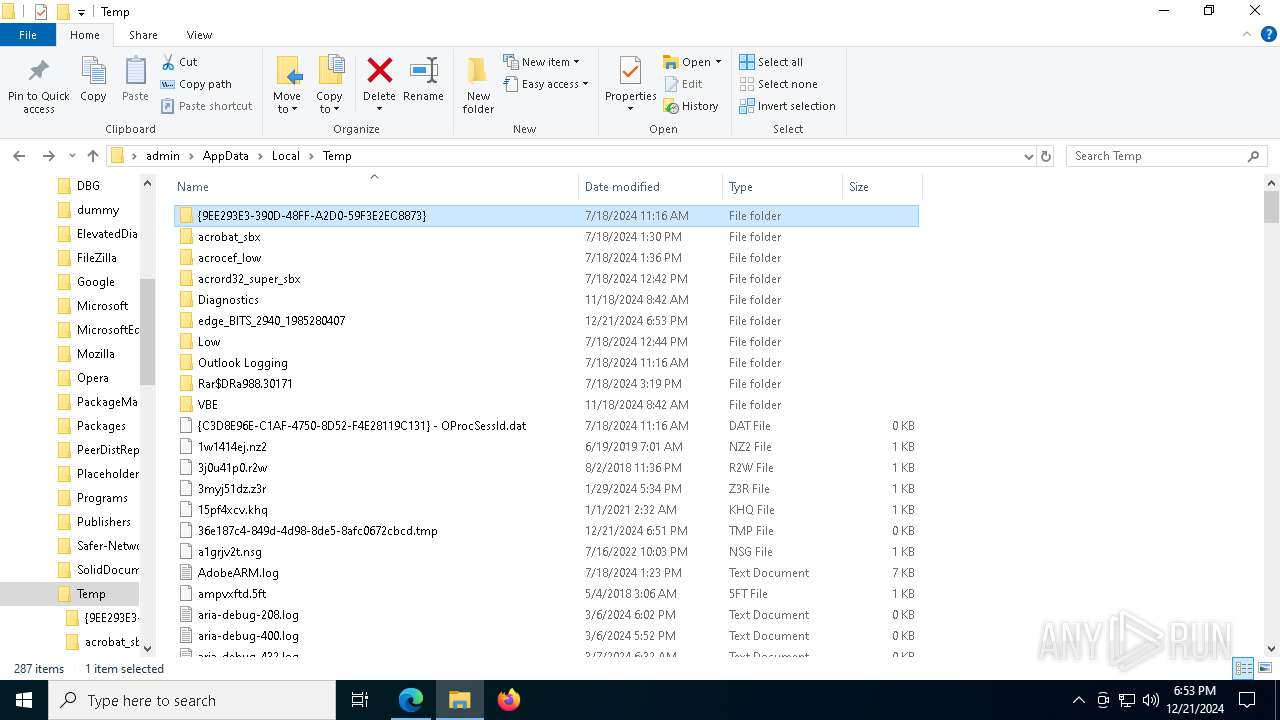
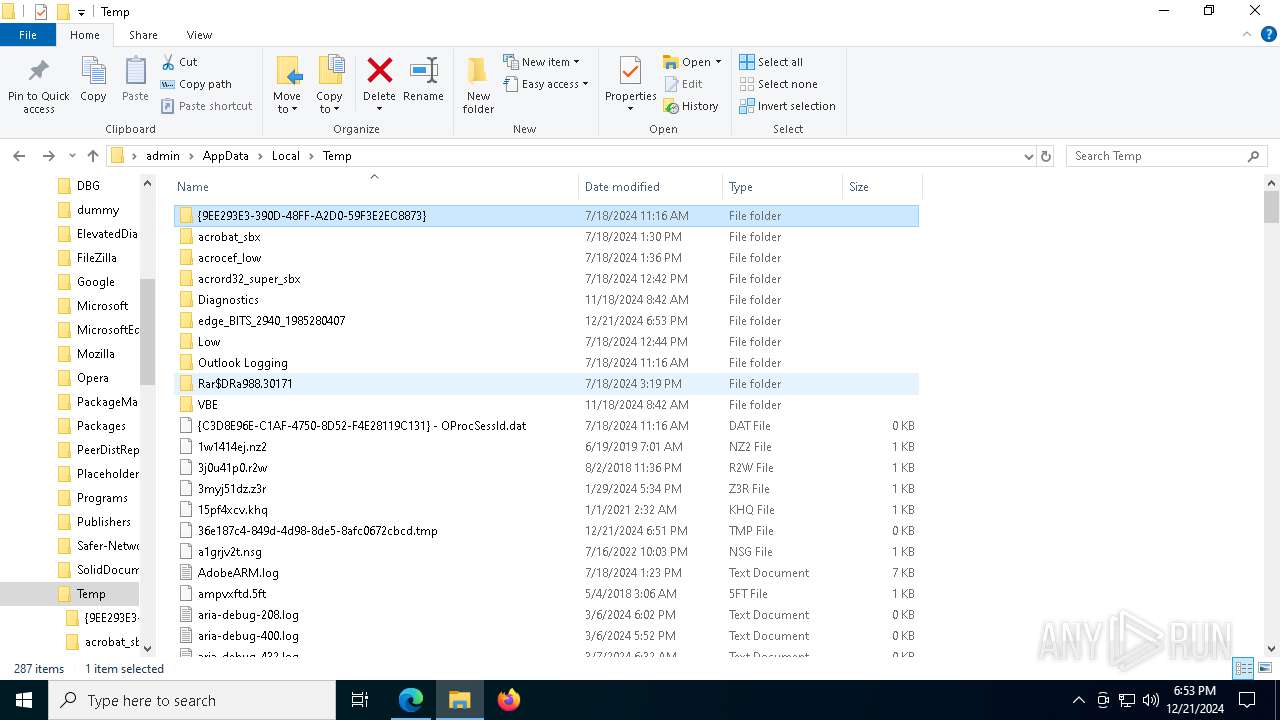
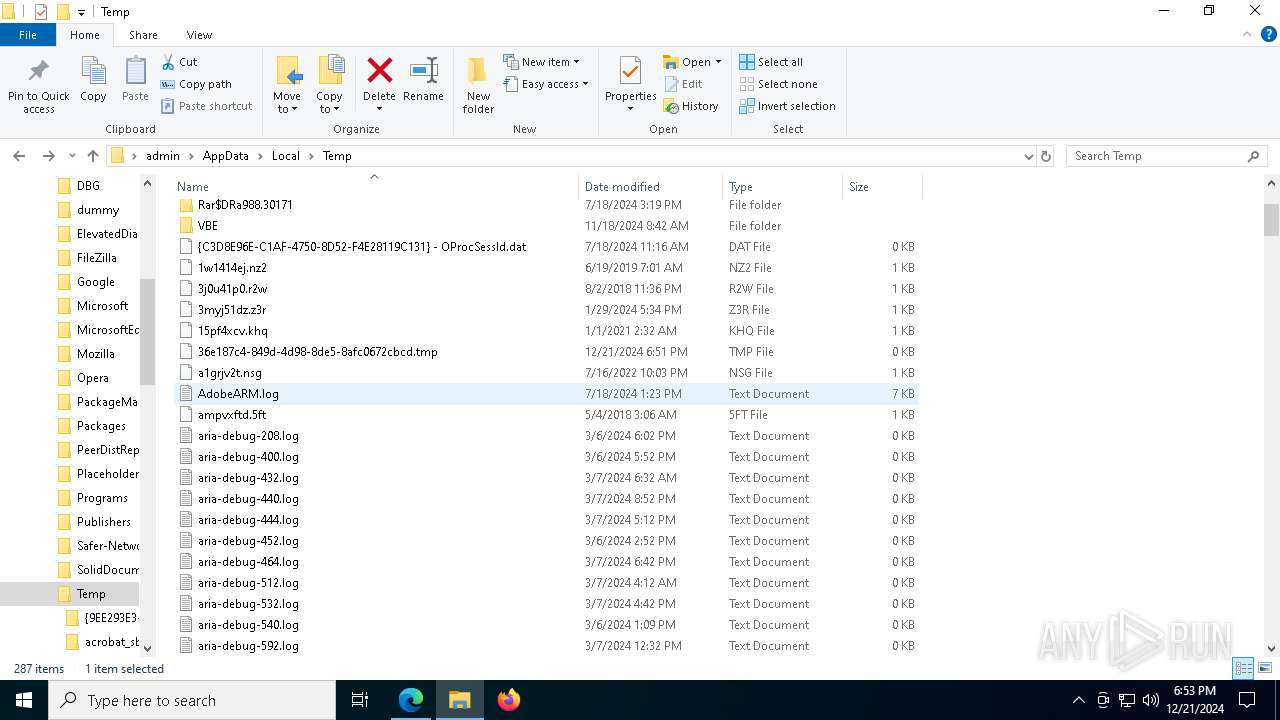
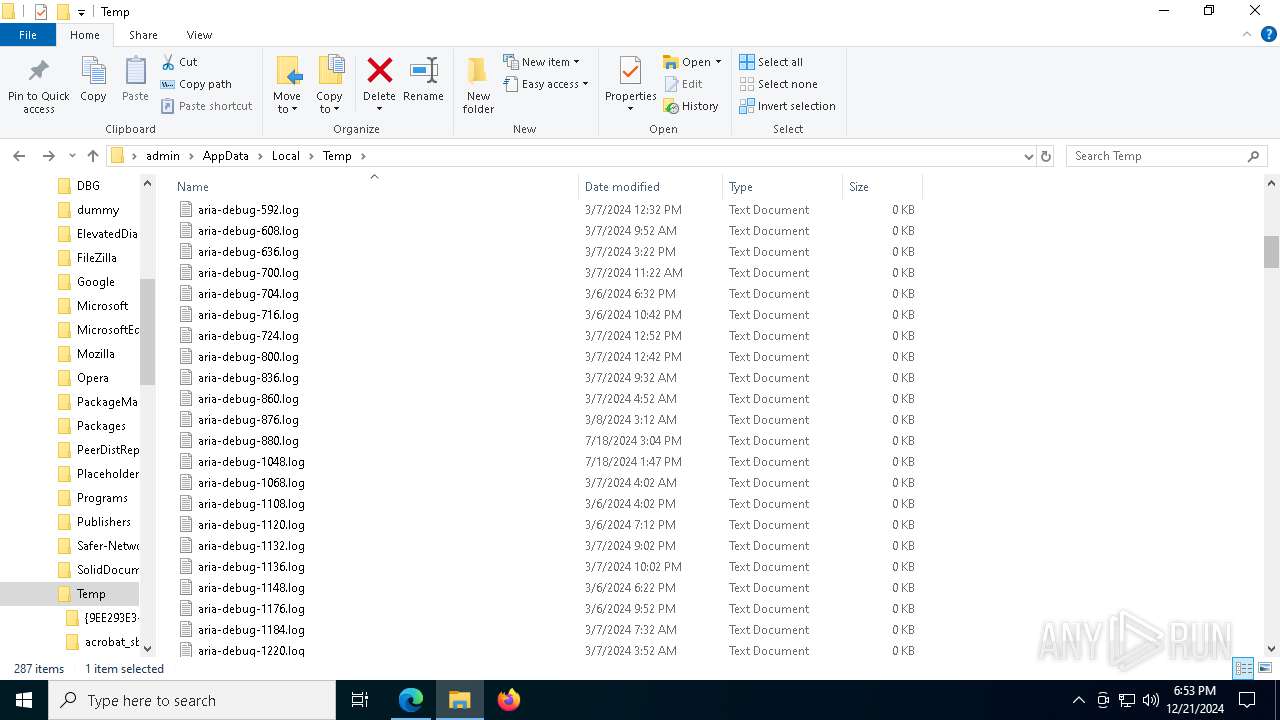
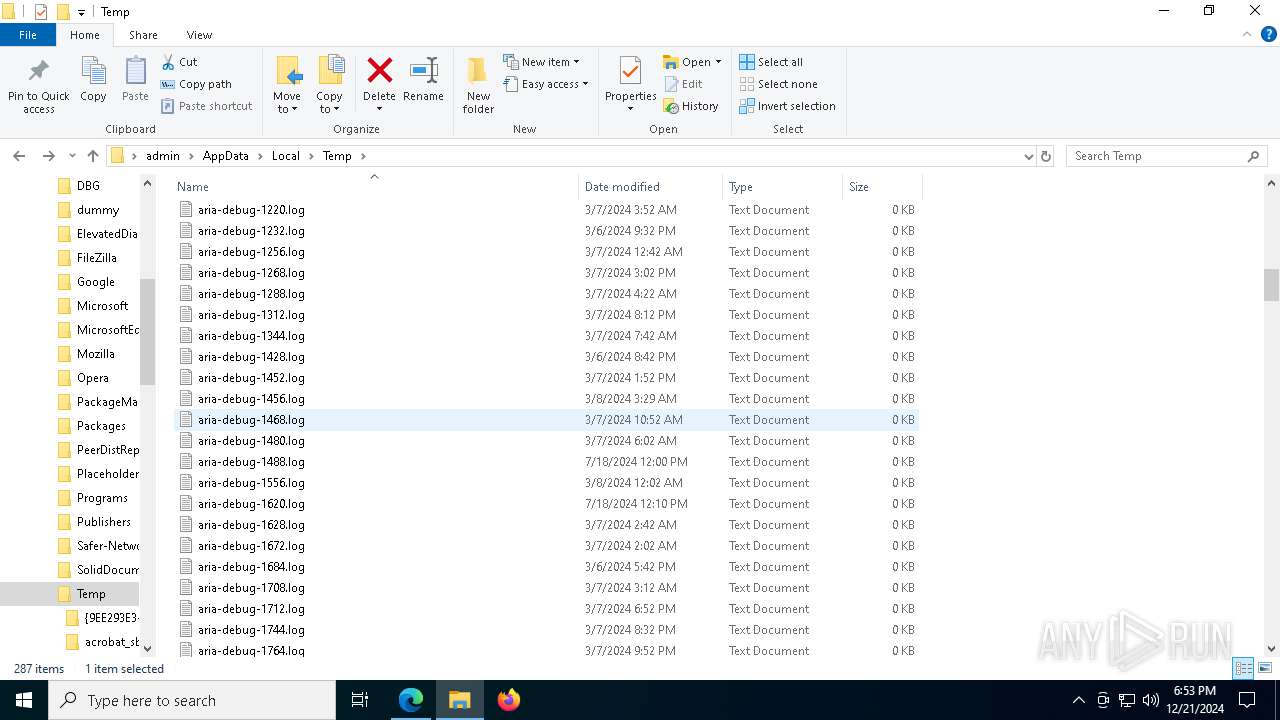
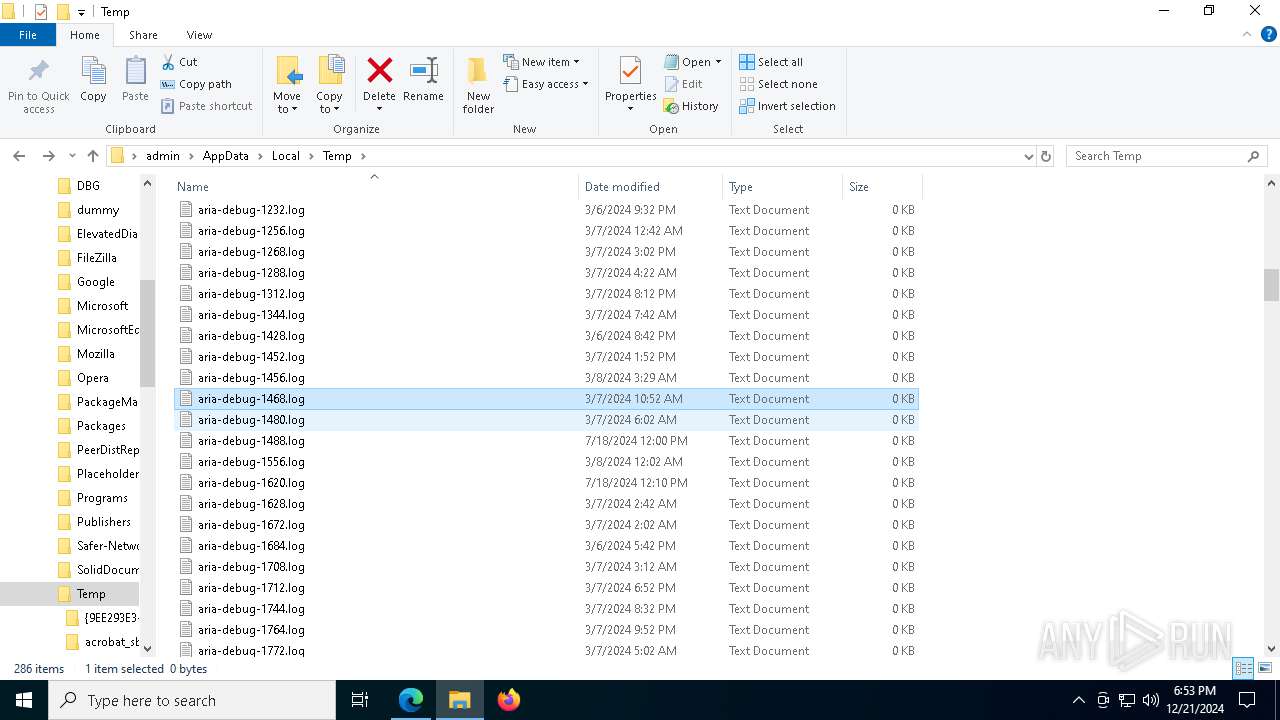
Executable files
5
Suspicious files
670
Text files
130
Unknown types
1
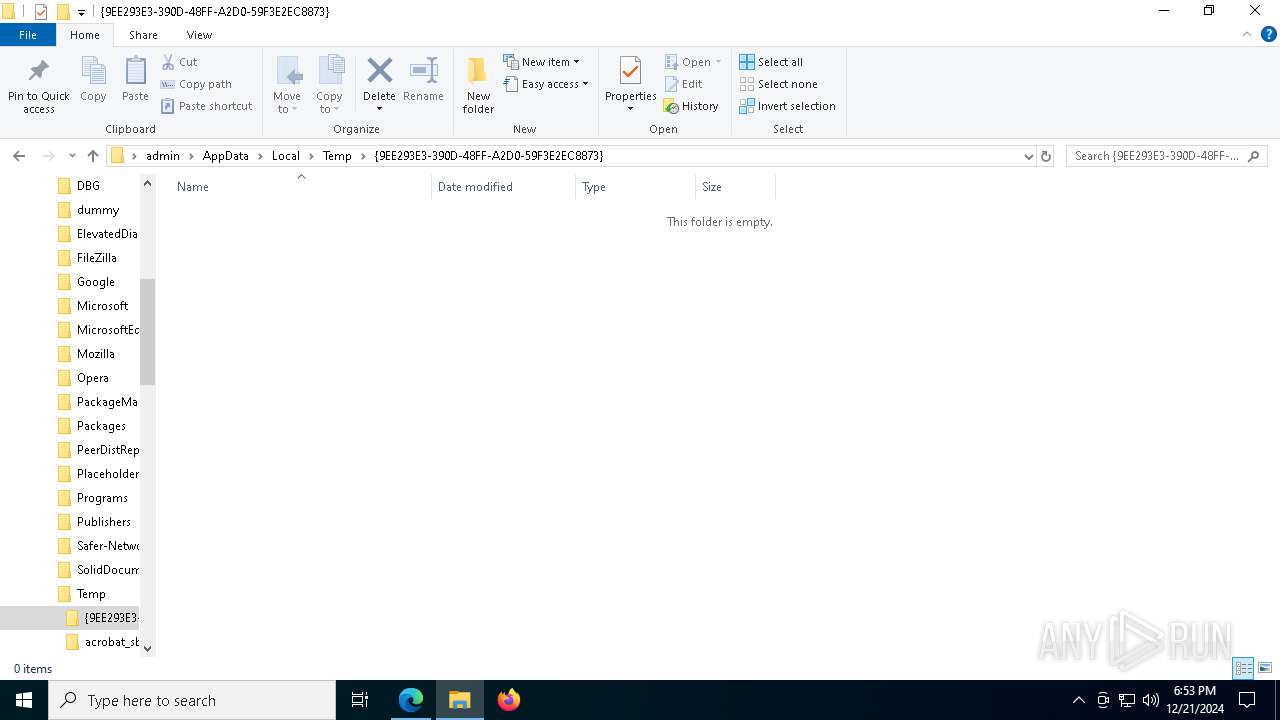
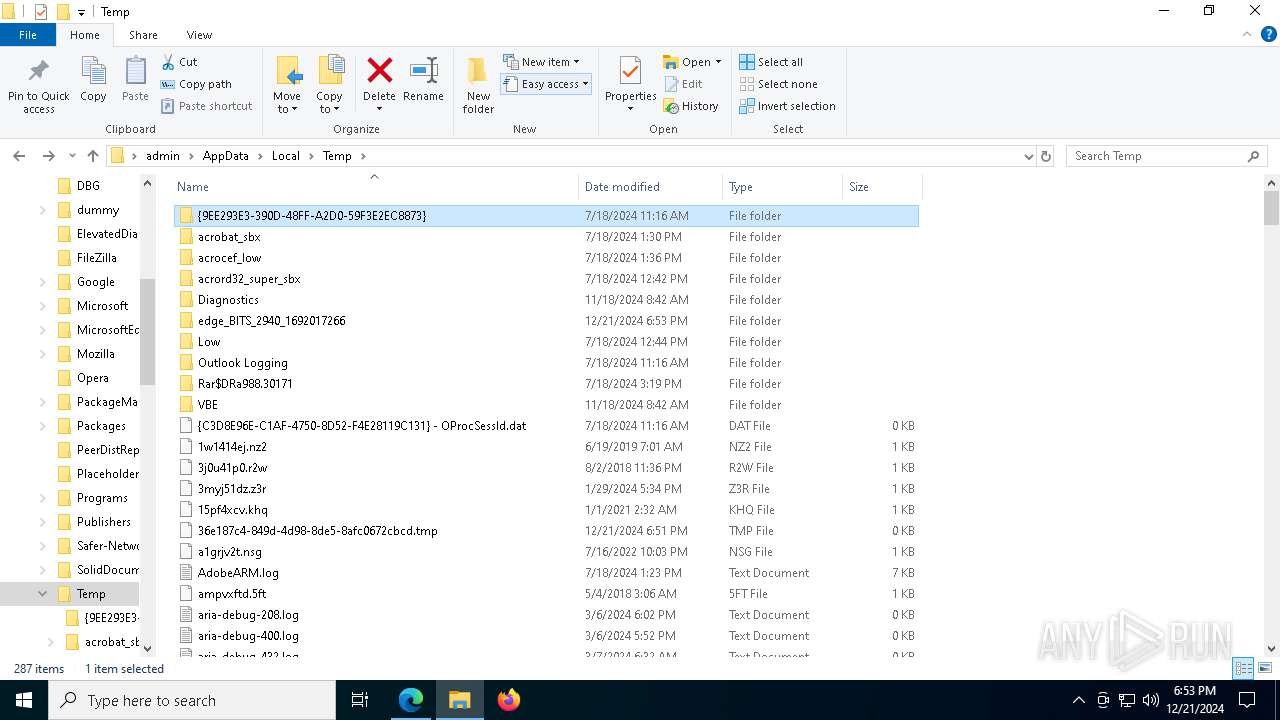
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF13547c.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF13547c.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF13548c.TMP | — | |
MD5:— | SHA256:— | |||
| 2940 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
131
DNS requests
170
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735351768&P2=404&P3=2&P4=ep%2fzDHJeDOSPIrL%2bUlEg4IOh9JZQdnH5sX9SnkLOMEQI%2fhIKnlV6YhYc3c6D4ZRBLPu2tL1bvVGN0CFURluVEQ%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735351768&P2=404&P3=2&P4=ep%2fzDHJeDOSPIrL%2bUlEg4IOh9JZQdnH5sX9SnkLOMEQI%2fhIKnlV6YhYc3c6D4ZRBLPu2tL1bvVGN0CFURluVEQ%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735351768&P2=404&P3=2&P4=ep%2fzDHJeDOSPIrL%2bUlEg4IOh9JZQdnH5sX9SnkLOMEQI%2fhIKnlV6YhYc3c6D4ZRBLPu2tL1bvVGN0CFURluVEQ%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735351768&P2=404&P3=2&P4=ep%2fzDHJeDOSPIrL%2bUlEg4IOh9JZQdnH5sX9SnkLOMEQI%2fhIKnlV6YhYc3c6D4ZRBLPu2tL1bvVGN0CFURluVEQ%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735351768&P2=404&P3=2&P4=ep%2fzDHJeDOSPIrL%2bUlEg4IOh9JZQdnH5sX9SnkLOMEQI%2fhIKnlV6YhYc3c6D4ZRBLPu2tL1bvVGN0CFURluVEQ%3d%3d | unknown | — | — | whitelisted |
7728 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735351767&P2=404&P3=2&P4=TR4GxG9OY5K9oX2zRTiWnhFRm6WFIplTSlqa46cZ63NnoVSZFZdlsBjjhSaOr75Nb%2bFvyBQwiy2OBNJrEwf6vw%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
444 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.137:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2940 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
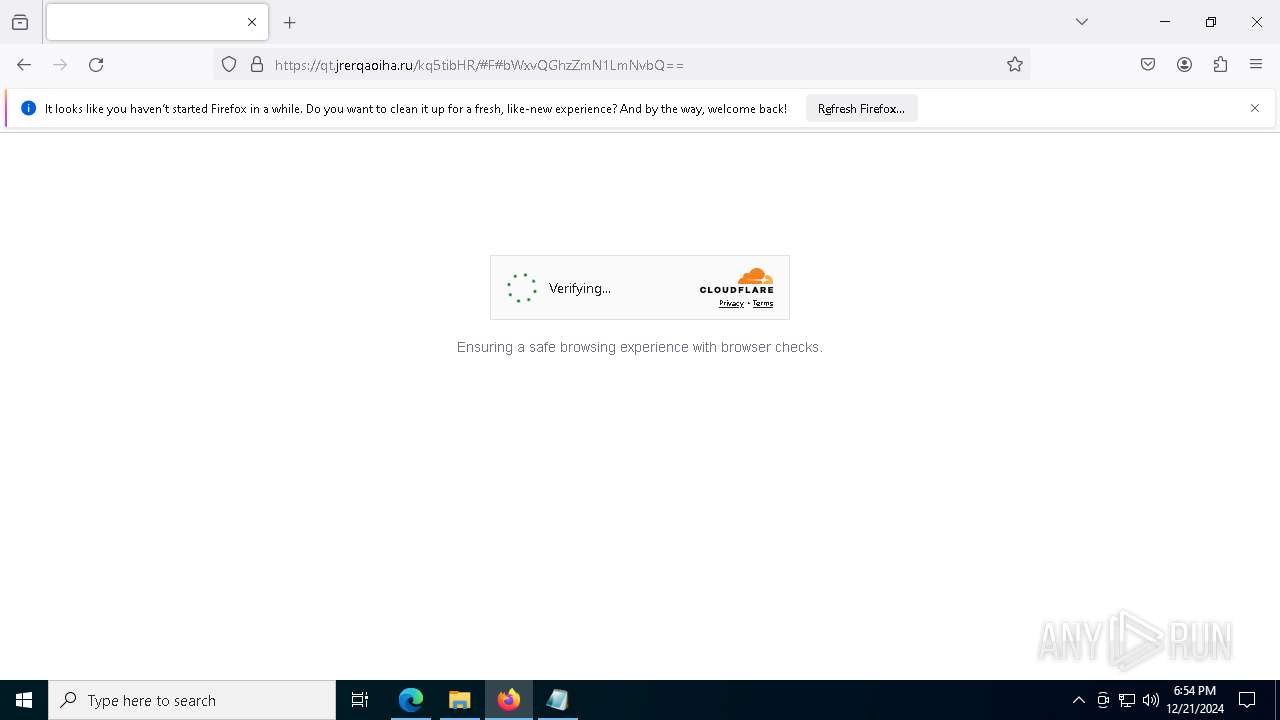
6400 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (ateacherthings .com) |
6400 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (ateacherthings .com) |
6400 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (ateacherthings .com) |
6400 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (ateacherthings .com) |
6400 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6400 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6400 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6400 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2192 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (ateacherthings .com) |
2192 | svchost.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain identified as part of Tycoon phishing service [Storm-1747] (ateacherthings .com) |