| File name: | _output3A0D410.exe |
| Full analysis: | https://app.any.run/tasks/2d217f89-fda2-4364-825d-1890d32b3b13 |
| Verdict: | Malicious activity |
| Threats: | FormBook is a data stealer that is being distributed as a MaaS. FormBook differs from a lot of competing malware by its extreme ease of use that allows even the unexperienced threat actors to use FormBook virus. |
| Analysis date: | May 24, 2019, 03:21:20 |
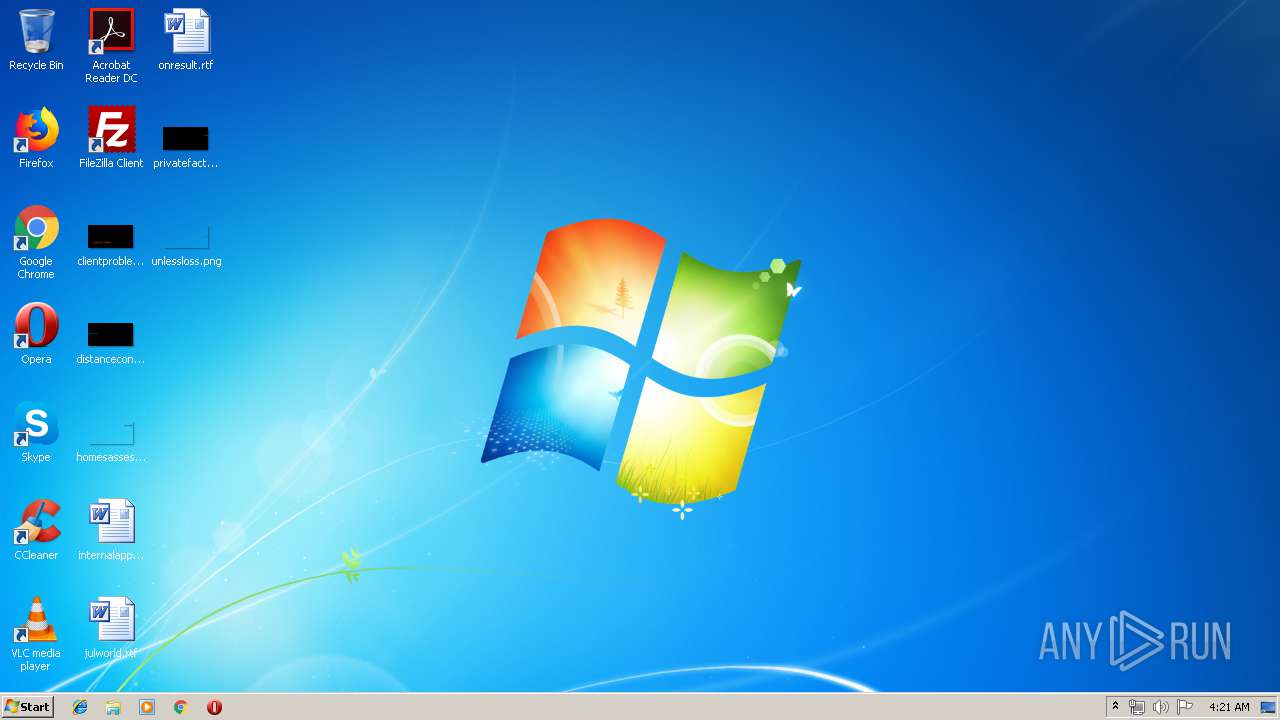
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1F3EA9E45C142216A2B7EFA856A5FAE7 |
| SHA1: | 65CBB83B86B64F355863F15825585986A9774FE3 |
| SHA256: | 88F60616C4E08A583D9545FAFDB1127F5122268F6C6CD2EAACDB05450AABB0EB |
| SSDEEP: | 6144:/ohKv/L+uWMMpQfkvFvsAWU+WKxLd9BlYUywTBBNCmGCbJ+iKXdgb:/QpN/sWpaL7QDwcqboxX |
MALICIOUS
Application was dropped or rewritten from another process
- bin.exe (PID: 2580)
- ovchmlvdc.exe (PID: 3300)
Detected Pony/Fareit Trojan
- _output3A0D410.exe (PID: 3896)
FORMBOOK was detected
- explorer.exe (PID: 2044)
Connects to CnC server
- explorer.exe (PID: 2044)
- _output3A0D410.exe (PID: 3896)
Formbook was detected
- wuauclt.exe (PID: 2896)
- Firefox.exe (PID: 3172)
Changes the autorun value in the registry
- wuauclt.exe (PID: 2896)
Loads dropped or rewritten executable
- wuauclt.exe (PID: 2896)
Stealing of credential data
- cmd.exe (PID: 1492)
- wuauclt.exe (PID: 2896)
Actions looks like stealing of personal data
- _output3A0D410.exe (PID: 3896)
- wuauclt.exe (PID: 2896)
SUSPICIOUS
Application launched itself
- _output3A0D410.exe (PID: 3448)
Executable content was dropped or overwritten
- _output3A0D410.exe (PID: 3448)
- wuauclt.exe (PID: 2896)
- DllHost.exe (PID: 3412)
- explorer.exe (PID: 2044)
Starts CMD.EXE for commands execution
- wuauclt.exe (PID: 2896)
- _output3A0D410.exe (PID: 3896)
Creates files in the user directory
- wuauclt.exe (PID: 2896)
Loads DLL from Mozilla Firefox
- wuauclt.exe (PID: 2896)
Executed via COM
- DllHost.exe (PID: 3412)
Creates files in the program directory
- DllHost.exe (PID: 3412)
INFO
Creates files in the user directory
- Firefox.exe (PID: 3172)
Manual execution by user
- wuauclt.exe (PID: 2896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (84.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
| .exe | | | Generic Win/DOS Executable (2) |
| .exe | | | DOS Executable Generic (2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2007:06:06 08:14:24+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 589824 |
| InitializedDataSize: | 20480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1088 |
| OSVersion: | 4 |
| ImageVersion: | 1.5 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.5.0.7 |
| ProductVersionNumber: | 1.5.0.7 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | retelling1 |
| ProductName: | consummator |
| FileVersion: | 1.05.0007 |
| ProductVersion: | 1.05.0007 |
| InternalName: | KOUKOUYA |
| OriginalFileName: | KOUKOUYA.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jun-2007 06:14:24 |
| Detected languages: |
|
| CompanyName: | retelling1 |
| ProductName: | consummator |
| FileVersion: | 1.05.0007 |
| ProductVersion: | 1.05.0007 |
| InternalName: | KOUKOUYA |
| OriginalFilename: | KOUKOUYA.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000B0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 06-Jun-2007 06:14:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008F82C | 0x00090000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.6416 |
.data | 0x00091000 | 0x00002F0C | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00094000 | 0x000018C2 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.33639 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.28342 | 560 | Unicode (UTF 16LE) | English - United States | RT_VERSION |
30001 | 3.47361 | 2216 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
30002 | 4.06305 | 3240 | Unicode (UTF 16LE) | UNKNOWN | RT_ICON |
Imports
MSVBVM60.DLL |
Total processes
47
Monitored processes
12
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1492 | /c copy "C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Login Data" "C:\Users\admin\AppData\Local\Temp\DB1" /V | C:\Windows\System32\cmd.exe | wuauclt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1660 | cmd /c ""C:\Users\admin\AppData\Local\Temp\1323921.bat" "C:\Users\admin\AppData\Local\Temp\_output3A0D410.exe" " | C:\Windows\system32\cmd.exe | — | _output3A0D410.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2044 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Windows\System32\spoolsv.exe" | C:\Windows\System32\spoolsv.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\Temp\bin.exe" | C:\Users\admin\AppData\Local\Temp\bin.exe | — | _output3A0D410.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Windows\System32\wuauclt.exe" | C:\Windows\System32\wuauclt.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Update Exit code: 0 Version: 7.5.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Mozilla Firefox\Firefox.exe" | C:\Program Files\Mozilla Firefox\Firefox.exe | wuauclt.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 3300 | "C:\Program Files\Gppx\ovchmlvdc.exe" | C:\Program Files\Gppx\ovchmlvdc.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3412 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Local\Temp\_output3A0D410.exe" | C:\Users\admin\AppData\Local\Temp\_output3A0D410.exe | explorer.exe | ||||||||||||
User: admin Company: retelling1 Integrity Level: MEDIUM Exit code: 0 Version: 1.05.0007 Modules
| |||||||||||||||
Total events
1 164
Read events
1 147
Write events
17
Delete events
0
Modification events
| (PID) Process: | (3448) _output3A0D410.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3448) _output3A0D410.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3896) _output3A0D410.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | HWID |
Value: 7B41323431363236462D464334382D343538392D384132332D3737374634414141333831447D | |||
| (PID) Process: | (3896) _output3A0D410.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR |
| Operation: | write | Name: | Client Hash |
Value: FE3876520ADB23581EA215EDA842F468 | |||
| (PID) Process: | (3896) _output3A0D410.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3896) _output3A0D410.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2896) wuauclt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | YLM0DHTPYJE |
Value: C:\Program Files\Gppx\ovchmlvdc.exe | |||
| (PID) Process: | (2896) wuauclt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2896) wuauclt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2896) wuauclt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\Component Categories\{56FFCC30-D398-11D0-B2AE-00A0C908FA49}\Enum |
| Operation: | write | Name: | Implementing |
Value: 1C00000001000000E307050005001800030019000000170300000000 | |||
Executable files
4
Suspicious files
79
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | _output3A0D410.exe | C:\Users\admin\AppData\Local\Temp\bin.exe | executable | |
MD5:— | SHA256:— | |||
| 3412 | DllHost.exe | C:\Program Files\Gppx\ovchmlvdc.exe | executable | |
MD5:— | SHA256:— | |||
| 2896 | wuauclt.exe | C:\Users\admin\AppData\Roaming\0P6BTOP5\0P6logrc.ini | binary | |
MD5:— | SHA256:— | |||
| 2896 | wuauclt.exe | C:\Users\admin\AppData\Roaming\0P6BTOP5\0P6logim.jpeg | image | |
MD5:— | SHA256:— | |||
| 2896 | wuauclt.exe | C:\Users\admin\AppData\Local\Temp\gzvh-.zip | compressed | |
MD5:— | SHA256:— | |||
| 2044 | explorer.exe | C:\Users\admin\AppData\Local\Temp\Gppx\ovchmlvdc.exe | executable | |
MD5:— | SHA256:— | |||
| 1492 | cmd.exe | C:\Users\admin\AppData\Local\Temp\DB1 | sqlite | |
MD5:— | SHA256:— | |||
| 2896 | wuauclt.exe | C:\Users\admin\AppData\Roaming\0P6BTOP5\0P6logrg.ini | binary | |
MD5:— | SHA256:— | |||
| 3172 | Firefox.exe | C:\Users\admin\AppData\Roaming\0P6BTOP5\0P6logrf.ini | binary | |
MD5:— | SHA256:— | |||
| 2896 | wuauclt.exe | C:\Users\admin\AppData\Roaming\0P6BTOP5\0P6logrv.ini | binary | |
MD5:BA3B6BC807D4F76794C4B81B09BB9BA5 | SHA256:6EEBF968962745B2E9DE2CA969AF7C424916D4E3FE3CC0BB9B3D414ABFCE9507 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
34
DNS requests
15
Threats
64
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | explorer.exe | GET | — | 45.122.138.109:80 | http://www.pk874.com/hx314/?FPEt=ZUTjrjJ17boCLyfdPpnpNBLMGgj2ajF4xvahtrkfBVctfhIIoi6Mf4XYX5KWovpK2GQ0bg==&LZyL=kJlhzl | HK | — | — | malicious |
3896 | _output3A0D410.exe | POST | — | 198.98.59.62:80 | http://sellers.net.pl/ec/panel/gate.php | US | — | — | malicious |
2044 | explorer.exe | GET | 404 | 213.239.221.71:80 | http://www.classica-foto.com/hx314/?FPEt=C1tyLkkFmMQ/DU0wosZCMJXLiTXyJwSp1cke5WMyZnndGWRDWz+b5hzH1PCfbWbGavTDkQ==&LZyL=kJlhzl&sql=1 | DE | html | 252 b | malicious |
2044 | explorer.exe | POST | — | 213.239.221.71:80 | http://www.classica-foto.com/hx314/ | DE | — | — | malicious |
2044 | explorer.exe | POST | — | 213.239.221.71:80 | http://www.classica-foto.com/hx314/ | DE | — | — | malicious |
2044 | explorer.exe | POST | — | 213.239.221.71:80 | http://www.classica-foto.com/hx314/ | DE | — | — | malicious |
2044 | explorer.exe | GET | 404 | 109.234.161.32:80 | http://www.extension-cils-reunion.com/hx314/?FPEt=NalUVbKJgn+O9nUkbJ6YR/prhICTNtXbAY4iehFZHc9TucbIQc+nznFzYI+4ff13NO1GWA==&LZyL=kJlhzl&sql=1 | FR | html | 14.7 Kb | malicious |
2044 | explorer.exe | POST | — | 109.234.161.32:80 | http://www.extension-cils-reunion.com/hx314/ | FR | — | — | malicious |
2044 | explorer.exe | POST | — | 109.234.161.32:80 | http://www.extension-cils-reunion.com/hx314/ | FR | — | — | malicious |
2044 | explorer.exe | GET | 302 | 54.208.77.124:80 | http://www.cryptogage.com/hx314/?FPEt=5yM/IfPhkXNA/YMXEt5uHJ1Xg52Rd4D9UtQQuL58RmqgzkRomL07GwpOoYRmbETgpXFGJg==&LZyL=kJlhzl&sql=1 | US | html | 303 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 198.98.59.62:80 | sellers.net.pl | FranTech Solutions | US | suspicious |
3896 | _output3A0D410.exe | 198.98.59.62:80 | sellers.net.pl | FranTech Solutions | US | suspicious |
2044 | explorer.exe | 45.122.138.109:80 | www.pk874.com | Guochao Group limited | HK | malicious |
2044 | explorer.exe | 213.239.221.71:80 | www.classica-foto.com | Hetzner Online GmbH | DE | malicious |
2044 | explorer.exe | 109.234.161.32:80 | www.extension-cils-reunion.com | o2switch SARL | FR | malicious |
2044 | explorer.exe | 54.208.77.124:80 | www.cryptogage.com | Amazon.com, Inc. | US | malicious |
2044 | explorer.exe | 162.213.255.220:80 | www.nadidetadllar.com | Namecheap, Inc. | US | malicious |
2044 | explorer.exe | 23.20.239.12:80 | www.chineseformula.com | Amazon.com, Inc. | US | shared |
2044 | explorer.exe | 156.235.142.215:80 | www.2zh4m.com | DXTL Tseung Kwan O Service | US | malicious |
2044 | explorer.exe | 216.58.205.243:80 | www.doubleplanetoid.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.xxwgdw.info |
| unknown |
sellers.net.pl |
| malicious |
www.pk874.com |
| malicious |
www.classica-foto.com |
| malicious |
www.extension-cils-reunion.com |
| malicious |
www.cryptogage.com |
| malicious |
www.imperiallivingatl.com |
| unknown |
www.solution.direct |
| unknown |
www.nadidetadllar.com |
| malicious |
www.zgtmn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3896 | _output3A0D410.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 2 |
3896 | _output3A0D410.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3896 | _output3A0D410.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
3896 | _output3A0D410.exe | A Network Trojan was detected | ET TROJAN Trojan Generic - POST To gate.php with no referer |
3896 | _output3A0D410.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
3896 | _output3A0D410.exe | A Network Trojan was detected | MALWARE [PTsecurity] Fareit/Pony Downloader Checkin |
3896 | _output3A0D410.exe | A Network Trojan was detected | ET TROJAN Fareit/Pony Downloader Checkin 3 |
3896 | _output3A0D410.exe | Potential Corporate Privacy Violation | ET POLICY Windows 98 User-Agent Detected - Possible Malware or Non-Updated System |
3896 | _output3A0D410.exe | A Network Trojan was detected | ET TROJAN Pony Downloader HTTP Library MSIE 5 Win98 |
3896 | _output3A0D410.exe | Potential Corporate Privacy Violation | ET POLICY Unsupported/Fake Internet Explorer Version MSIE 5. |
23 ETPRO signatures available at the full report