| File name: | Comb_Setup.exe |
| Full analysis: | https://app.any.run/tasks/10efa0b6-11d4-45f8-8107-5f55670ccd27 |
| Verdict: | Malicious activity |
| Threats: | AsyncRAT is a RAT that can monitor and remotely control infected systems. This malware was introduced on Github as a legitimate open-source remote administration software, but hackers use it for its many powerful malicious functions. |
| Analysis date: | March 24, 2025, 16:55:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | EE797726BE444787592CDAF63C677363 |
| SHA1: | 84EC94F8761D1004B2D996495CAF408CD5A75C0B |
| SHA256: | 88A8ACB09D14B0C8C513C8E1A4623F88E76C9E2AB195D18E7A48715218132750 |
| SSDEEP: | 49152:gSvDp/aozWj2tu2iR5cAmeXNqE36gQPtWmppcykkFFD+HoPtnYpa2qrzuLei2OXO:vv1yozYj8AmeXNb/iDakFu2tnyBPiiOj |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- Comb_Setup.tmp (PID: 7432)
ASYNCRAT has been detected (SURICATA)
- regsvr32.exe (PID: 7452)
Actions looks like stealing of personal data
- regsvr32.exe (PID: 7452)
SUSPICIOUS
Executable content was dropped or overwritten
- Comb_Setup.exe (PID: 7344)
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.exe (PID: 7400)
- Comb_Setup.tmp (PID: 7432)
Reads the Windows owner or organization settings
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.tmp (PID: 7432)
Reads security settings of Internet Explorer
- Comb_Setup.tmp (PID: 7364)
Process drops legitimate windows executable
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.tmp (PID: 7432)
The process hide an interactive prompt from the user
- regsvr32.exe (PID: 7452)
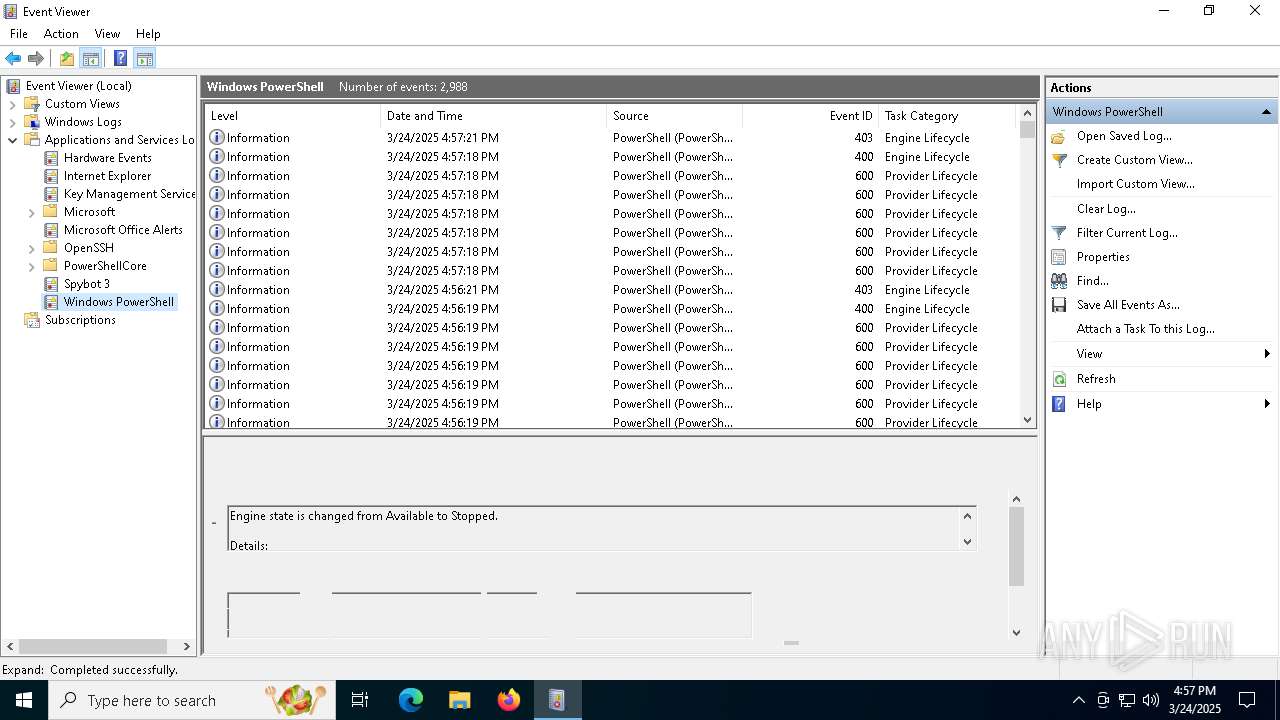
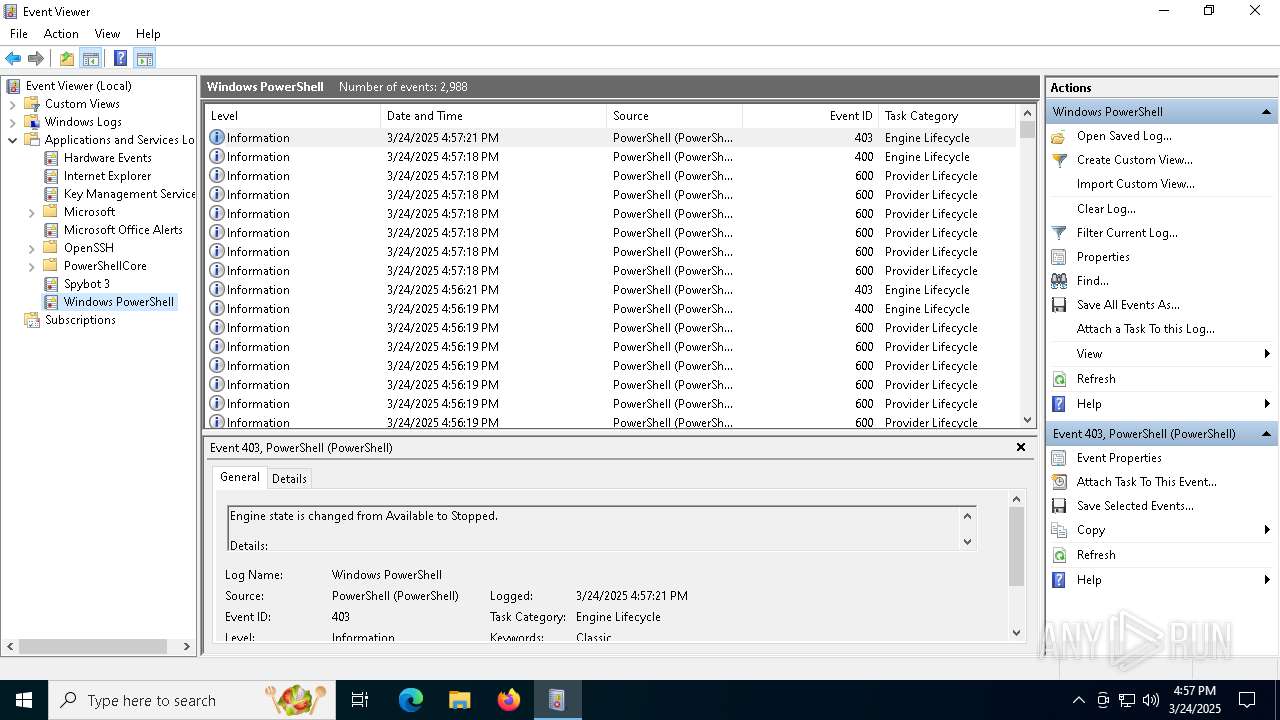
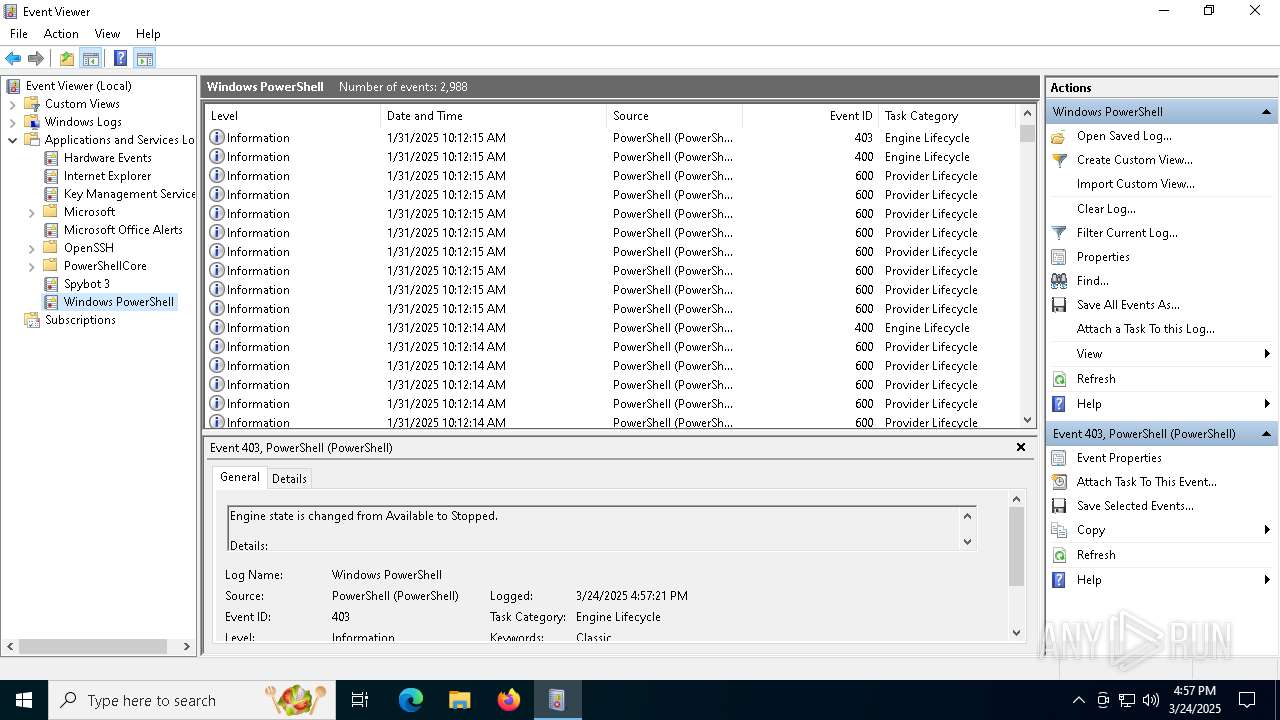
Starts POWERSHELL.EXE for commands execution
- regsvr32.exe (PID: 7452)
- regsvr32.exe (PID: 7492)
- regsvr32.exe (PID: 1616)
The process bypasses the loading of PowerShell profile settings
- regsvr32.exe (PID: 7452)
Contacting a server suspected of hosting an CnC
- regsvr32.exe (PID: 7452)
Connects to unusual port
- regsvr32.exe (PID: 7452)
The process executes via Task Scheduler
- regsvr32.exe (PID: 2064)
- regsvr32.exe (PID: 3768)
INFO
Checks supported languages
- Comb_Setup.exe (PID: 7344)
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.exe (PID: 7400)
- Comb_Setup.tmp (PID: 7432)
Create files in a temporary directory
- Comb_Setup.exe (PID: 7344)
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.exe (PID: 7400)
- Comb_Setup.tmp (PID: 7432)
Reads the computer name
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.tmp (PID: 7432)
The sample compiled with english language support
- Comb_Setup.tmp (PID: 7364)
- Comb_Setup.tmp (PID: 7432)
Process checks computer location settings
- Comb_Setup.tmp (PID: 7364)
Creates a software uninstall entry
- Comb_Setup.tmp (PID: 7432)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7484)
- powershell.exe (PID: 960)
- powershell.exe (PID: 6652)
- powershell.exe (PID: 4268)
- powershell.exe (PID: 7916)
Reads the software policy settings
- regsvr32.exe (PID: 7452)
Creates files or folders in the user directory
- Comb_Setup.tmp (PID: 7432)
- mmc.exe (PID: 5452)
Creates files in the program directory
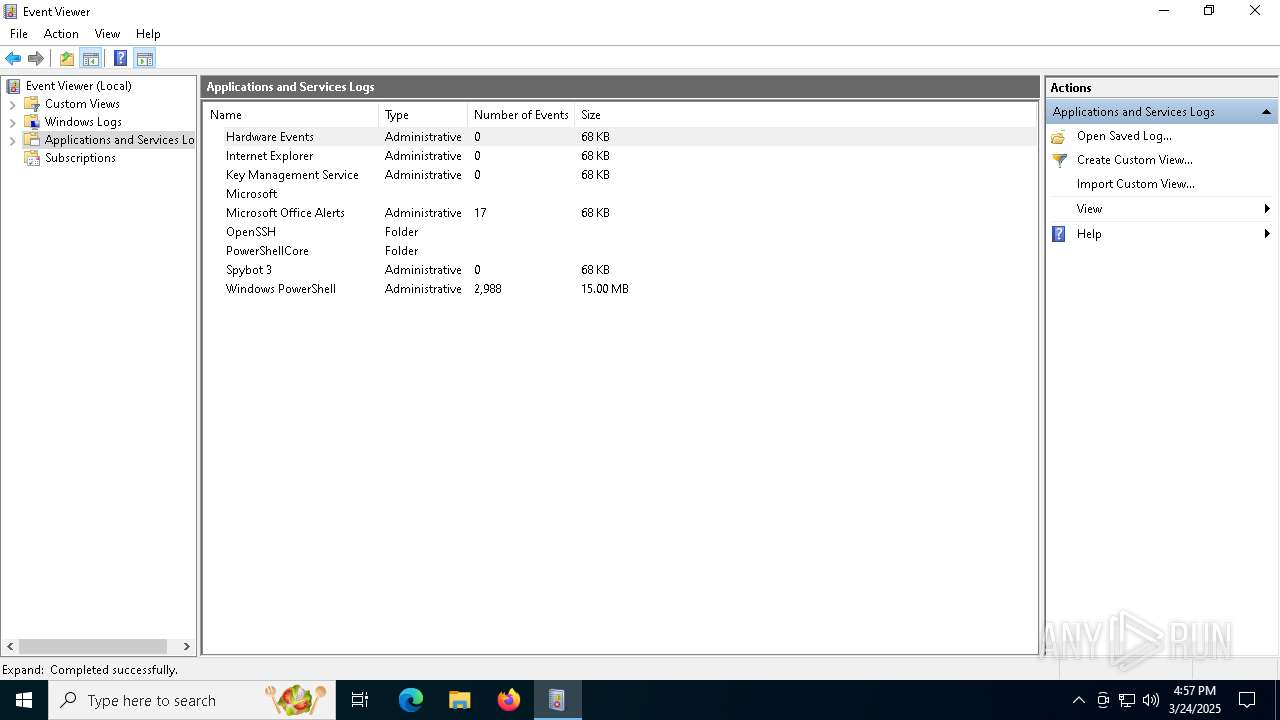
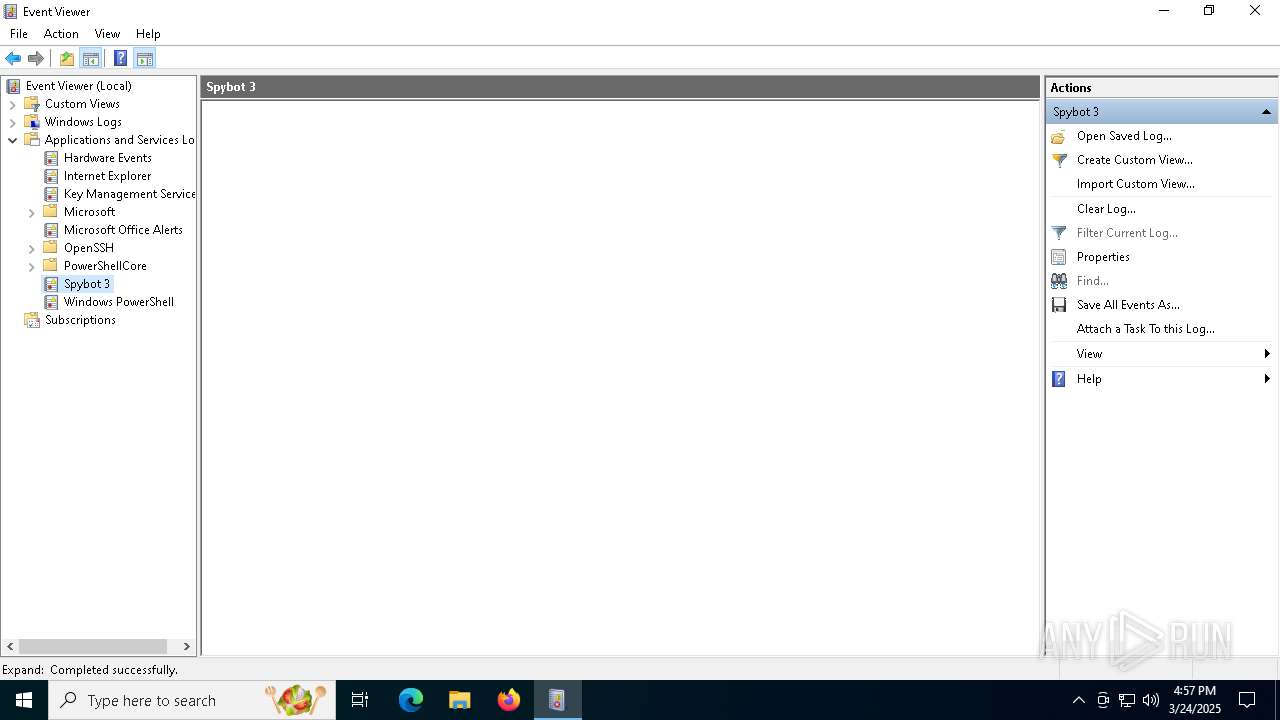
- mmc.exe (PID: 5452)
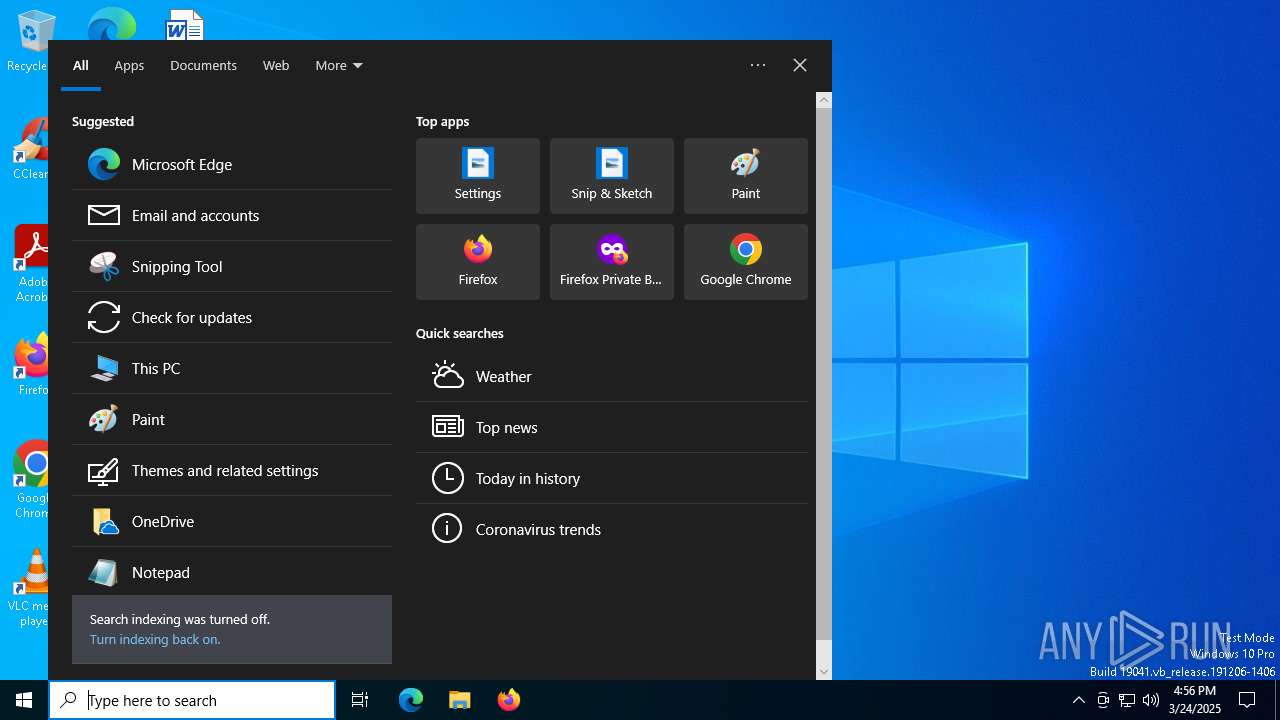
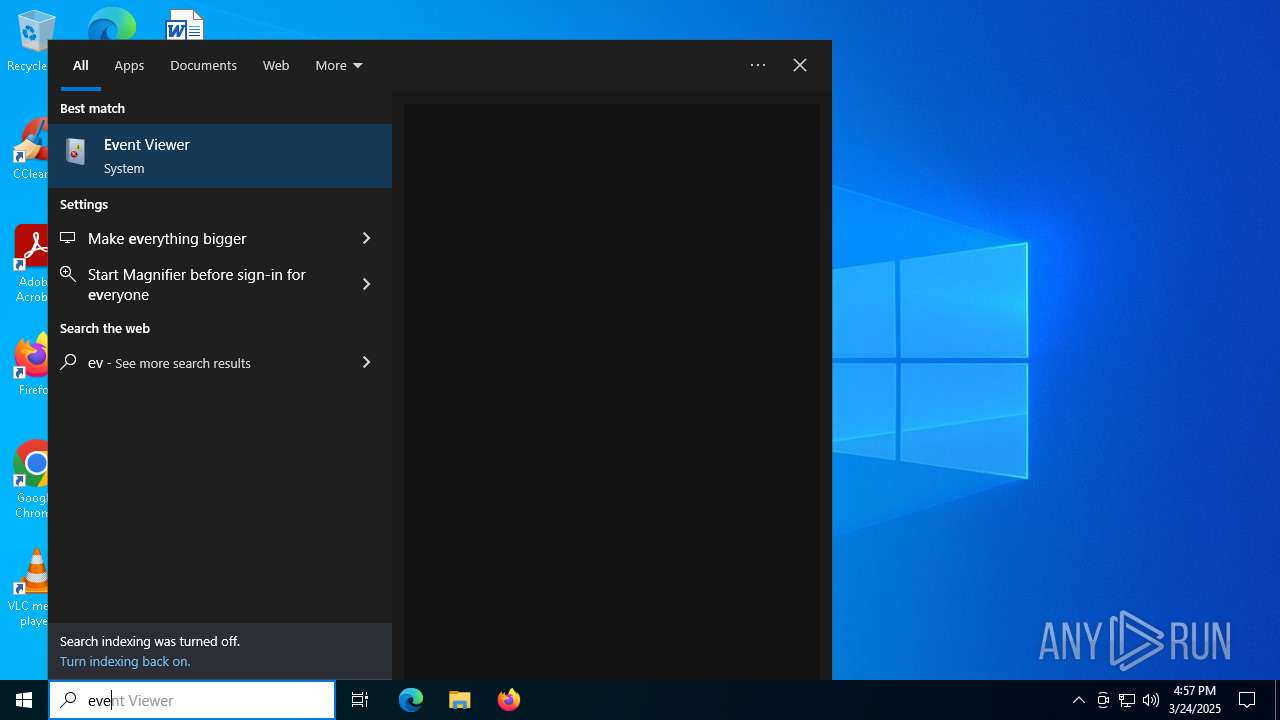
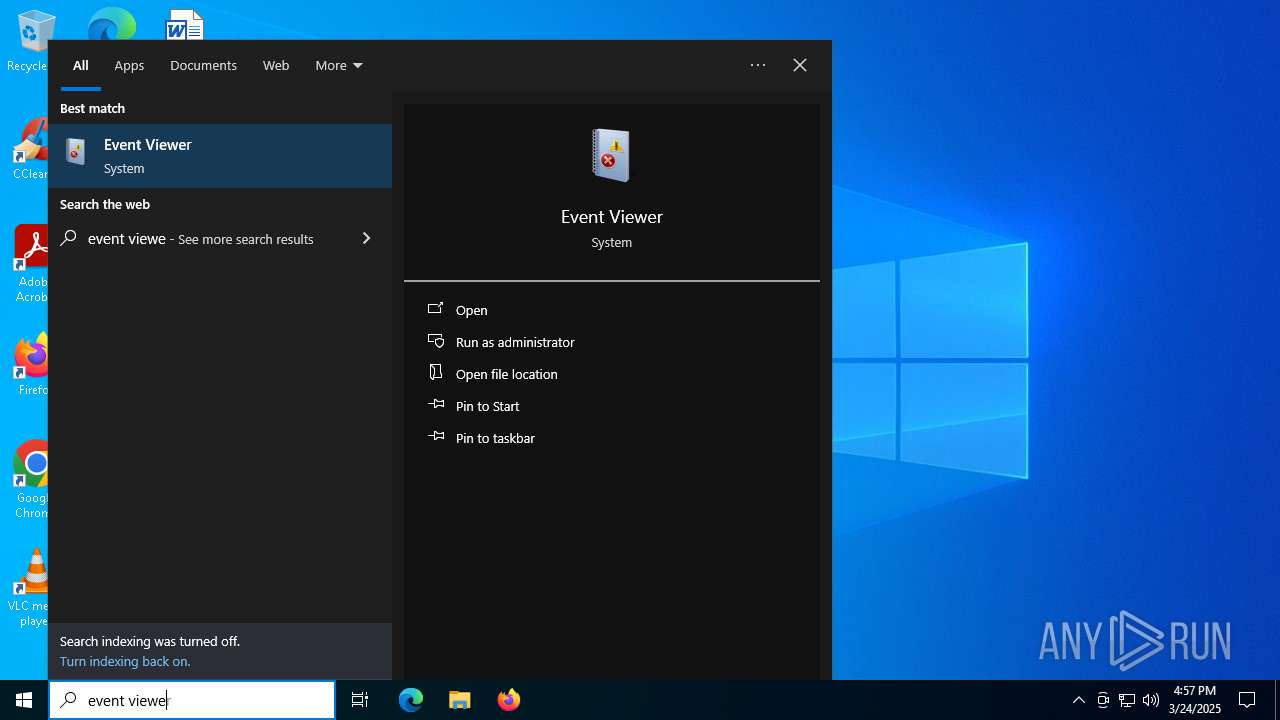
Manual execution by a user
- mmc.exe (PID: 6516)
- mmc.exe (PID: 5452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2003:01:04 04:19:53+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 34304 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c40 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Gaudy Giraffe Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Gaudy Giraffe |
| ProductVersion: | 5.34.75.8647 |
Total processes
170
Monitored processes
24
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | "PowerShell.exe" -NoProfile -NonInteractive -Command - | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | /s /i:INSTALL "C:\Users\admin\AppData\Roaming\version_8.ocx" | C:\Windows\SysWOW64\regsvr32.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\WINDOWS\system32\regsvr32.EXE" /s /i:INSTALL "C:\Users\admin\AppData\Roaming\version_8.ocx" | C:\Windows\System32\regsvr32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | "C:\WINDOWS\system32\regsvr32.EXE" /s /i:INSTALL "C:\Users\admin\AppData\Roaming\version_8.ocx" | C:\Windows\System32\regsvr32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4268 | "powershell" -Command "if (Get-ScheduledTask | Where-Object { $_.Actions.Execute -eq 'regsvr32' -and $_.Actions.Arguments -eq '/s /i:INSTALL \"%APPDATA%\version_8.ocx\"' }) { exit 0 } else { exit 1 }" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | regsvr32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5452 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\eventvwr.msc" /s | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 682
Read events
42 657
Write events
24
Delete events
1
Modification events
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.0 (a) | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\ | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | DisplayName |
Value: Gaudy Giraffe version 5.34.75.8647 | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\unins000.exe" | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\unins000.exe" /SILENT | |||
| (PID) Process: | (7432) Comb_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Gaudy Giraffe_is1 |
| Operation: | write | Name: | DisplayVersion |
Value: 5.34.75.8647 | |||
Executable files
12
Suspicious files
3
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7432 | Comb_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GBPPP.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 7400 | Comb_Setup.exe | C:\Users\admin\AppData\Local\Temp\is-2P1EB.tmp\Comb_Setup.tmp | executable | |
MD5:9917F679A0135245A5CC6B1AADCB3A6C | SHA256:3B6D0D4E5B6DCE113771790D6FB1DD1EBAFE1E400DCC7995897F010C0B315971 | |||
| 7344 | Comb_Setup.exe | C:\Users\admin\AppData\Local\Temp\is-G60HJ.tmp\Comb_Setup.tmp | executable | |
MD5:9917F679A0135245A5CC6B1AADCB3A6C | SHA256:3B6D0D4E5B6DCE113771790D6FB1DD1EBAFE1E400DCC7995897F010C0B315971 | |||
| 7364 | Comb_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S10SJ.tmp\_isetup\_setup64.tmp | executable | |
MD5:4FF75F505FDDCC6A9AE62216446205D9 | SHA256:A4C86FC4836AC728D7BD96E7915090FD59521A9E74F1D06EF8E5A47C8695FD81 | |||
| 7364 | Comb_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-S10SJ.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 7432 | Comb_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-GBPPP.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 960 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2fb0eedi.ite.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h10d33sw.ga0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jd4jerhd.clh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7484 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_aafep2n0.jr5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
43
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7764 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8164 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8164 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
2656 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7452 | regsvr32.exe | Domain Observed Used for C2 Detected | ET MALWARE Generic AsyncRAT/zgRAT Style SSL Cert |
7452 | regsvr32.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] AsyncRAT Successful Connection |