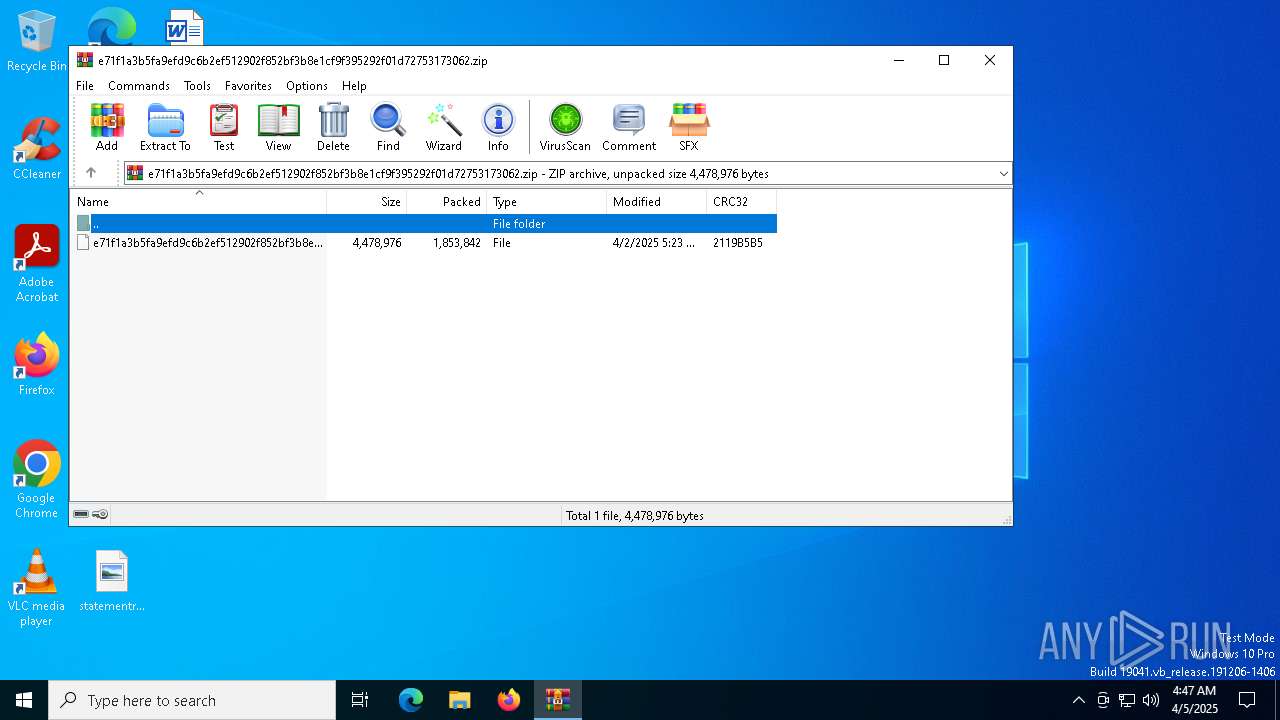
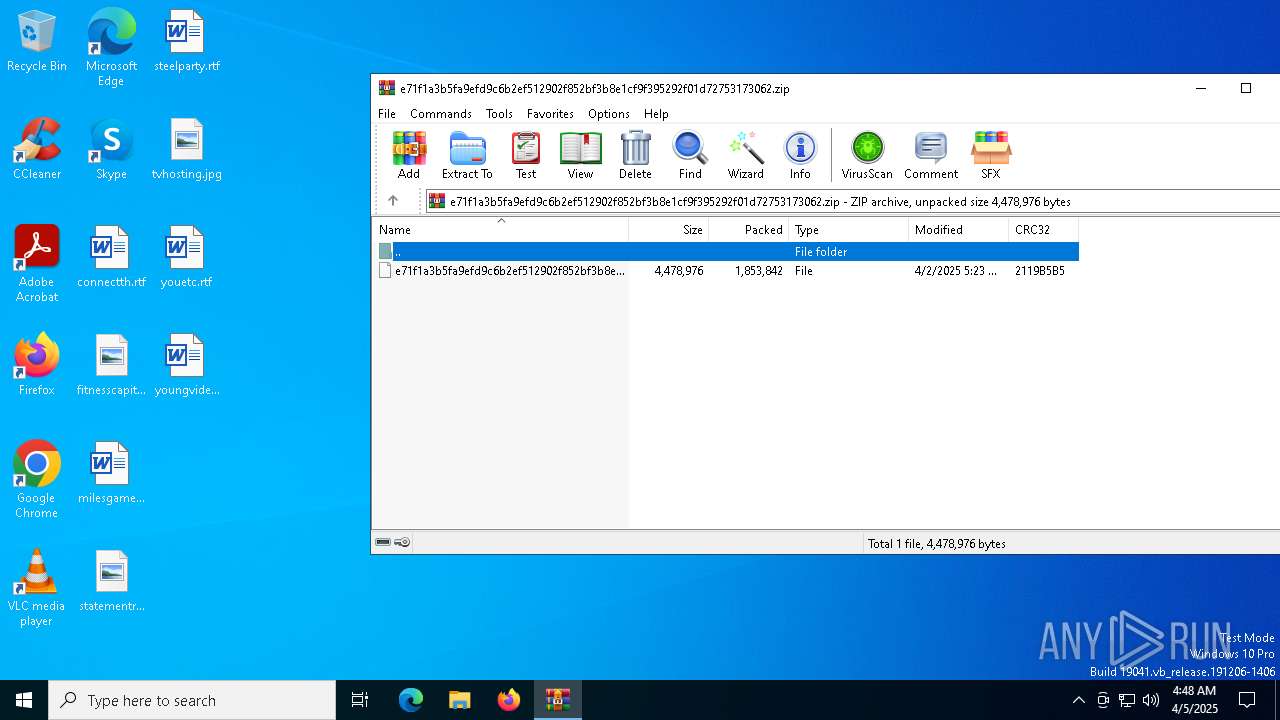
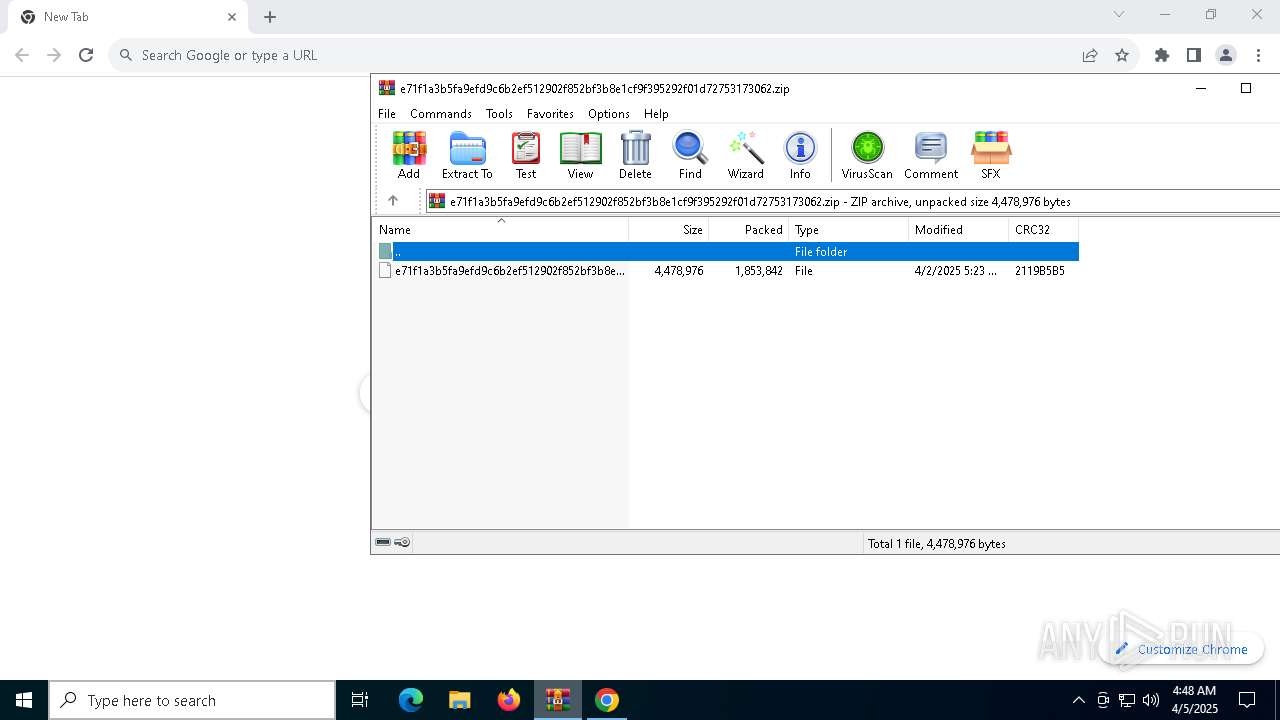
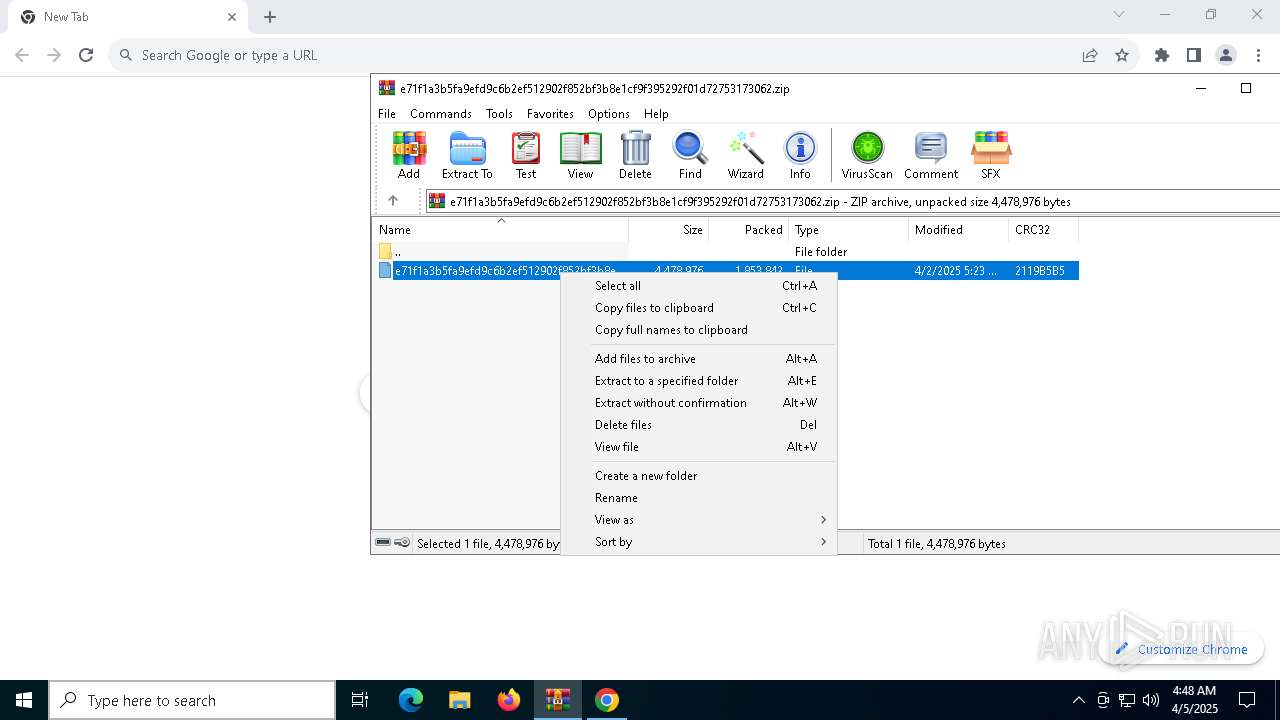
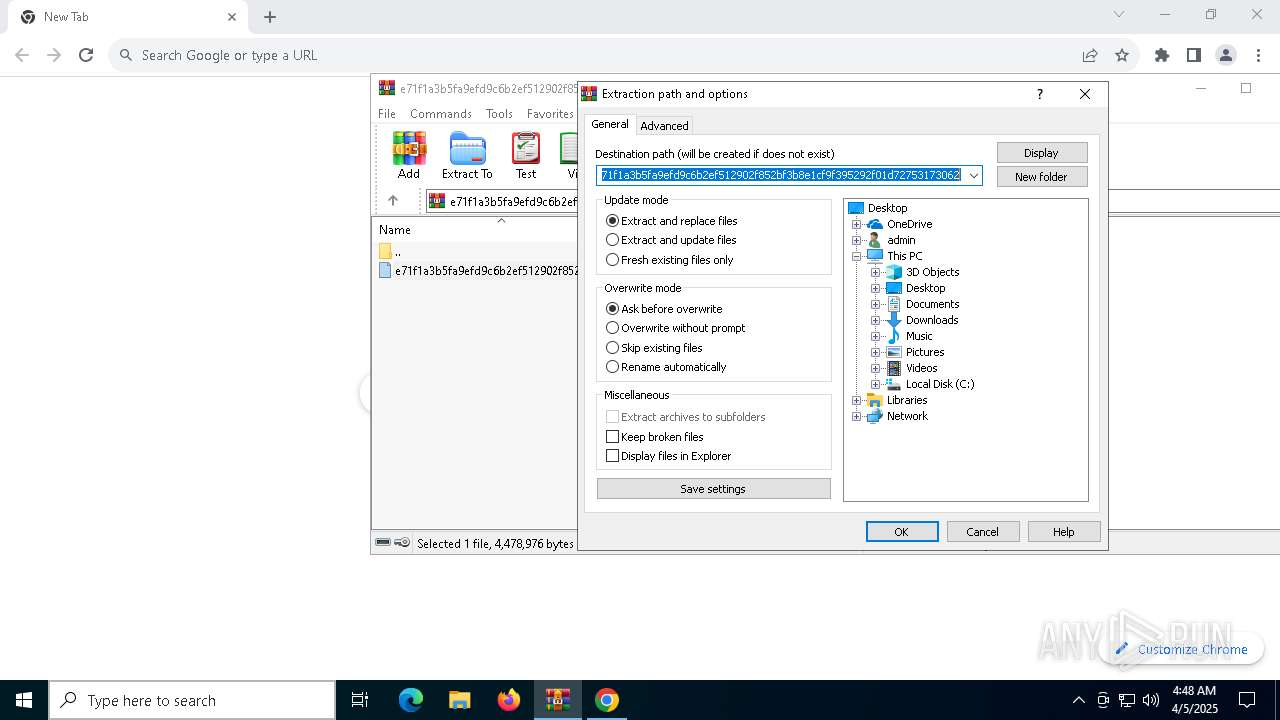
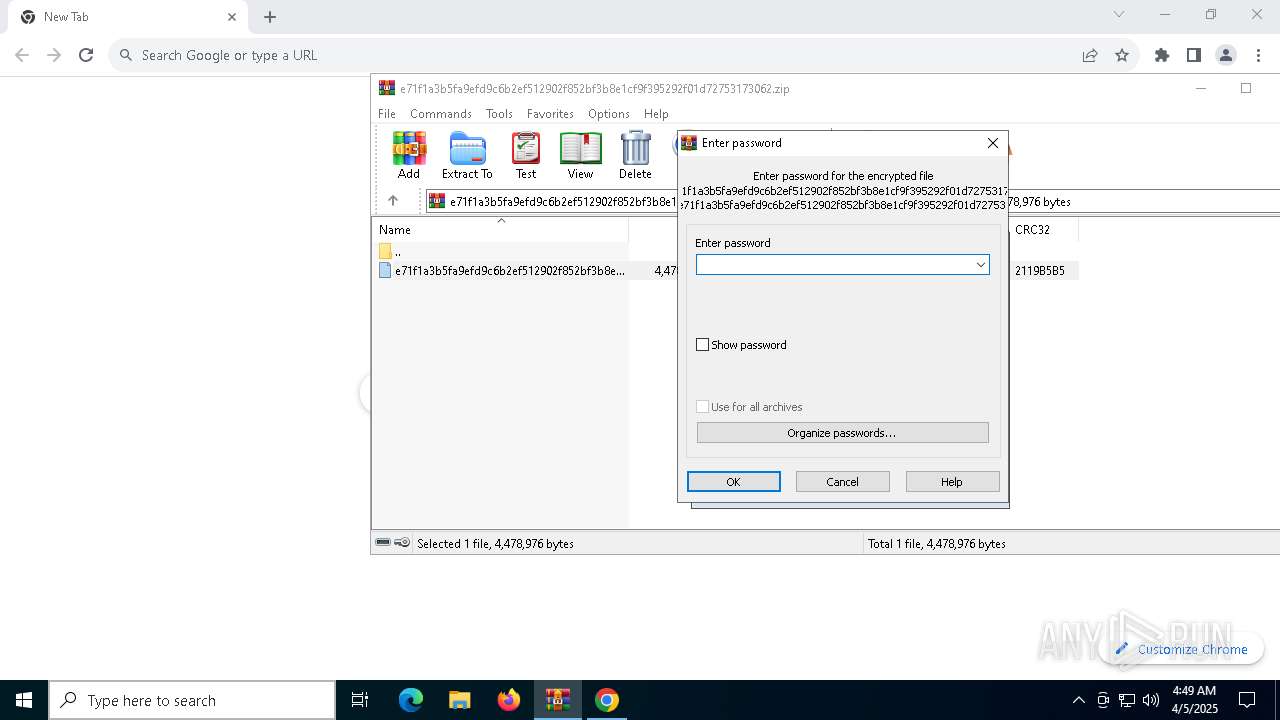
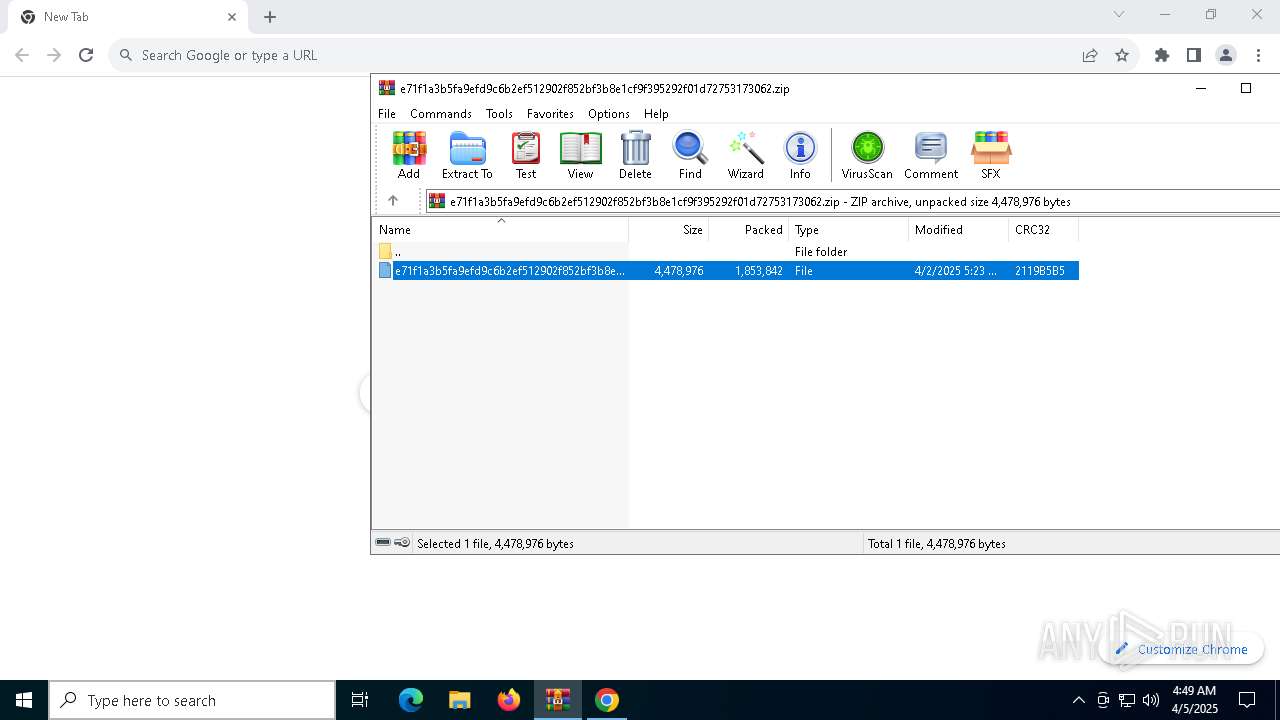
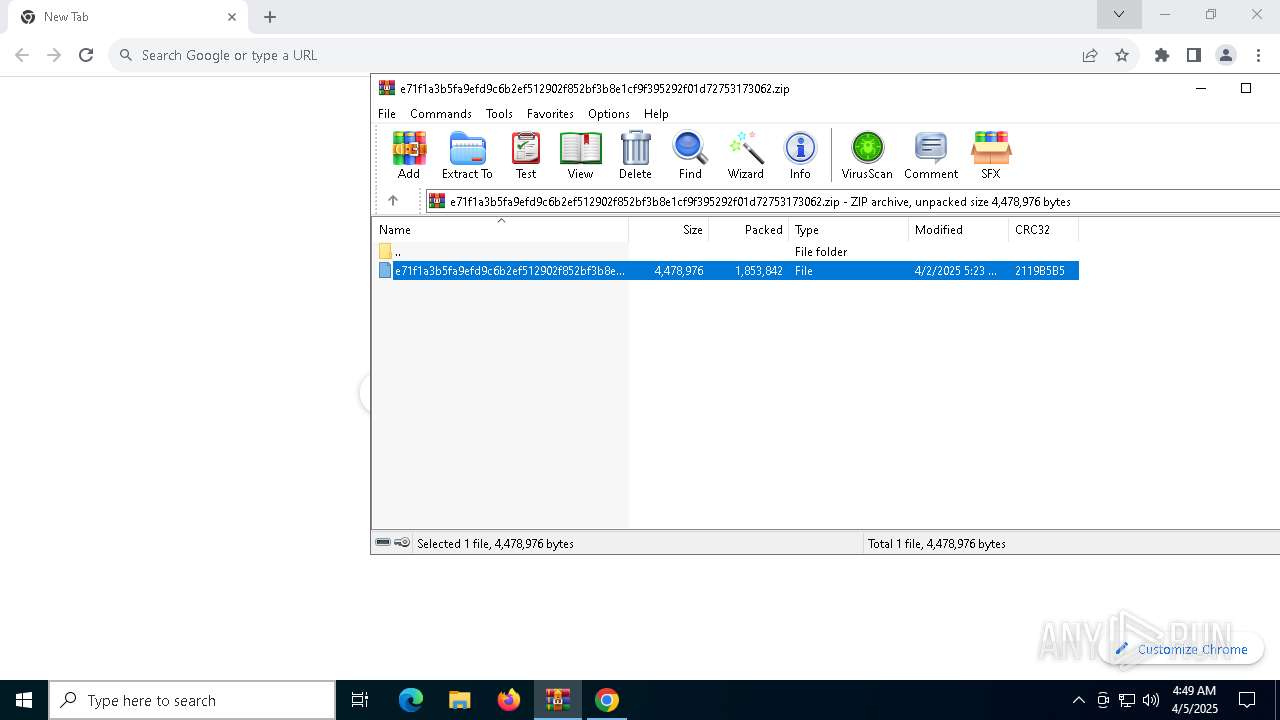
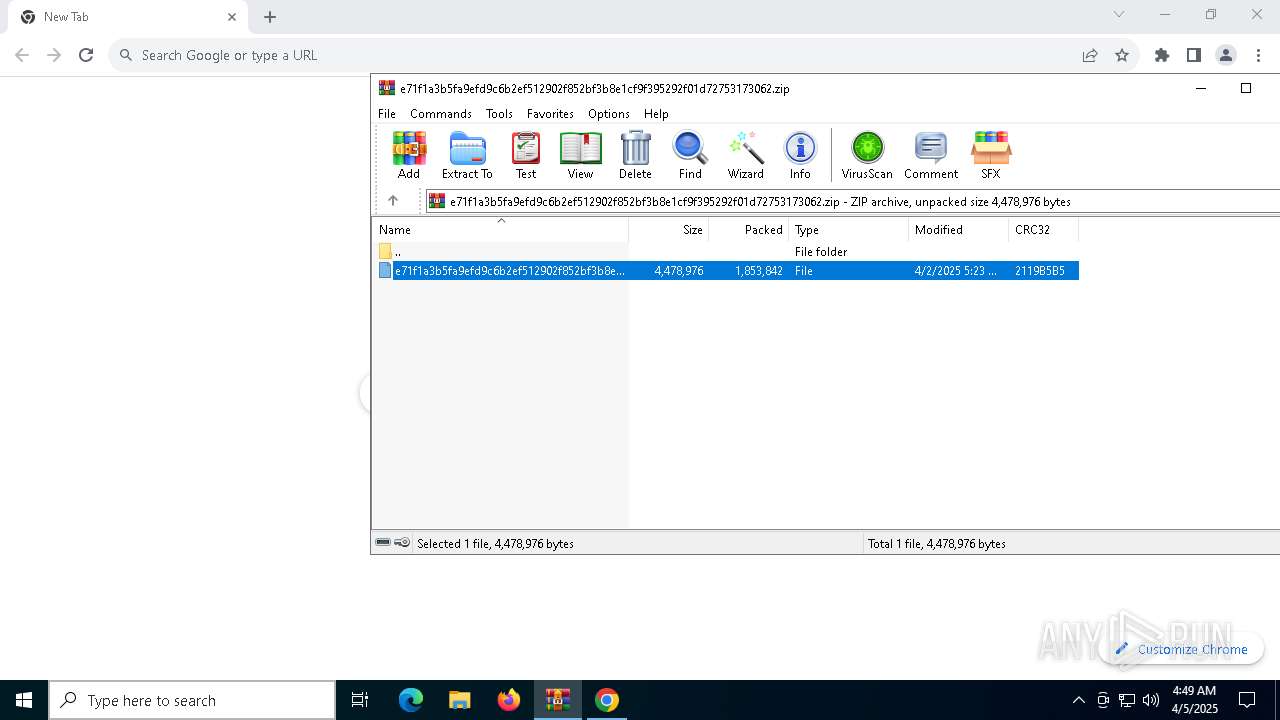
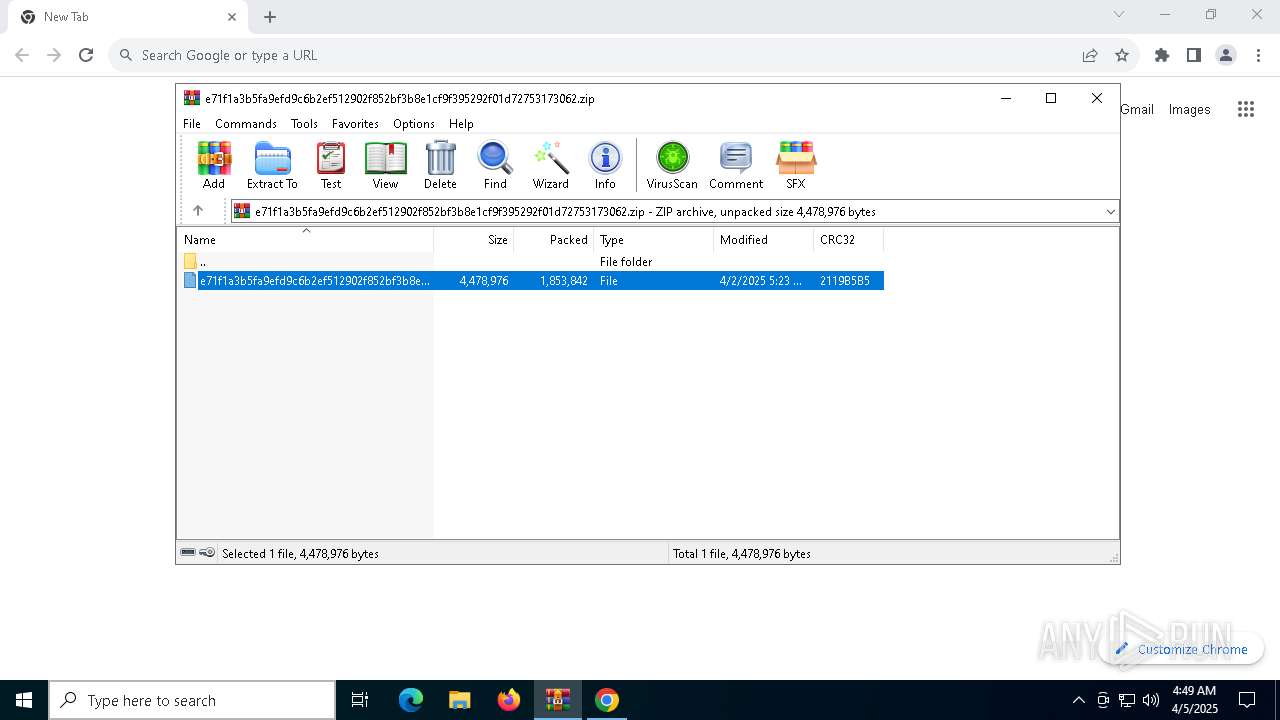
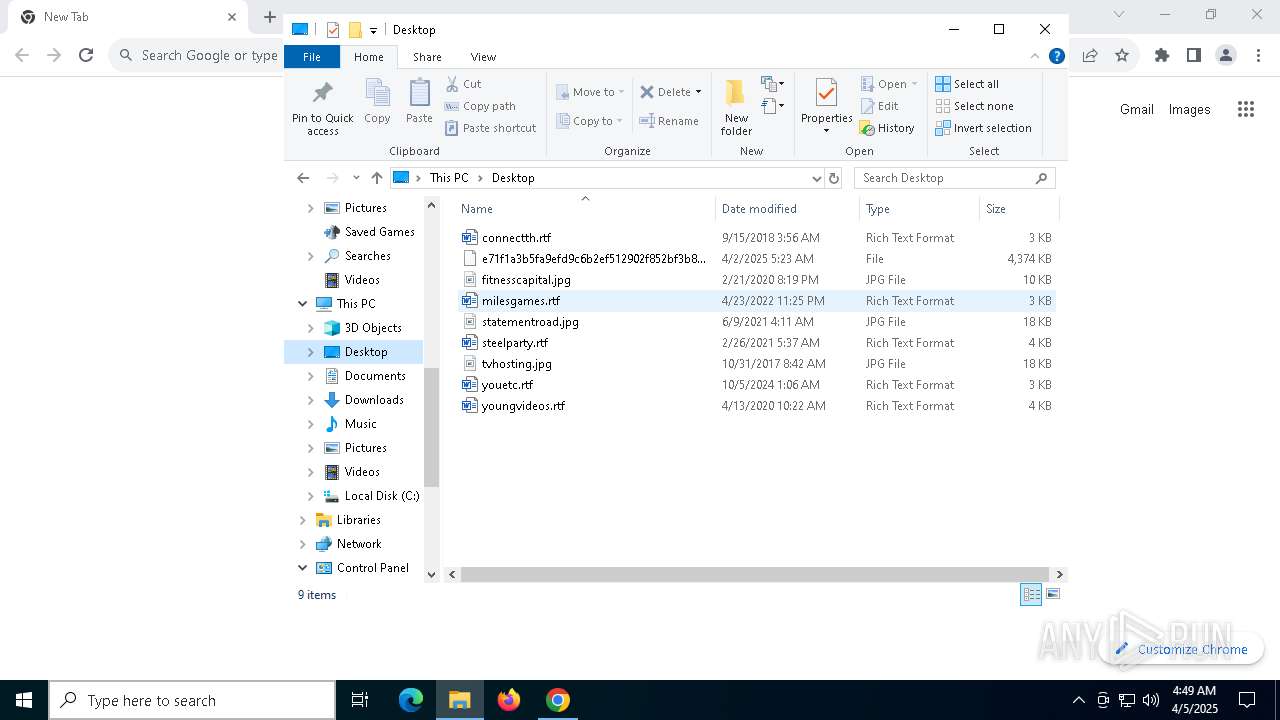
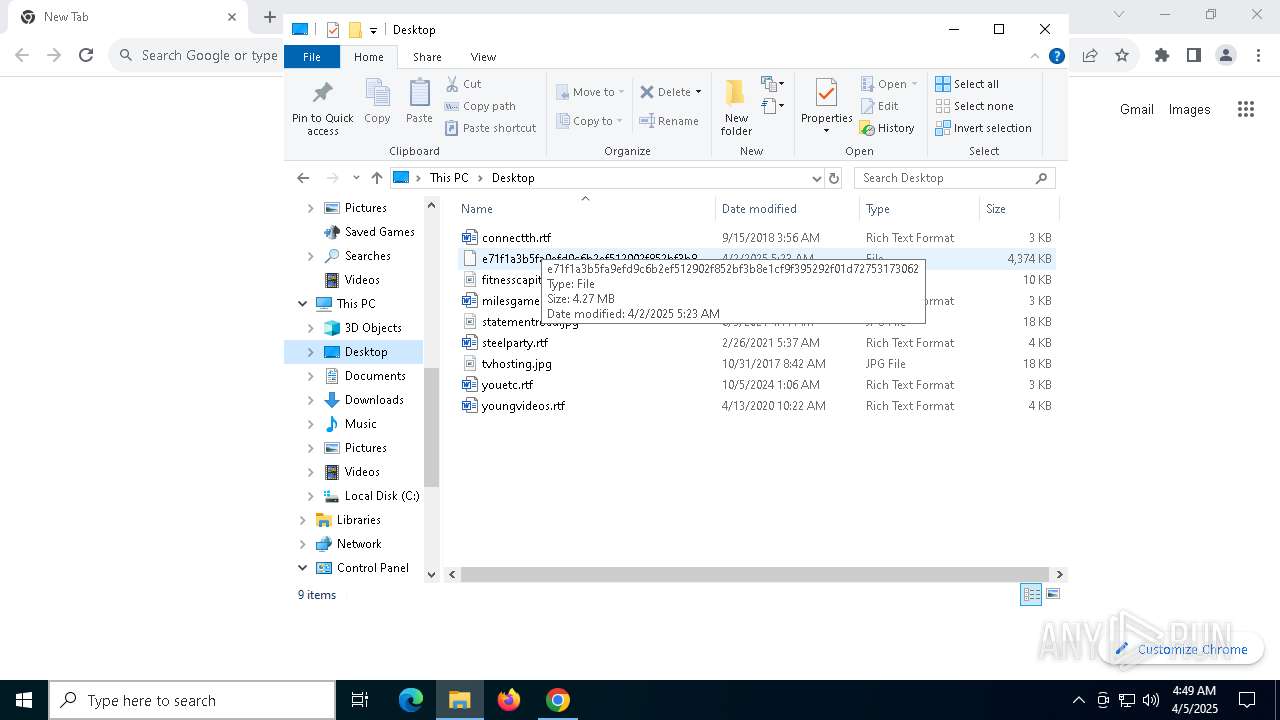
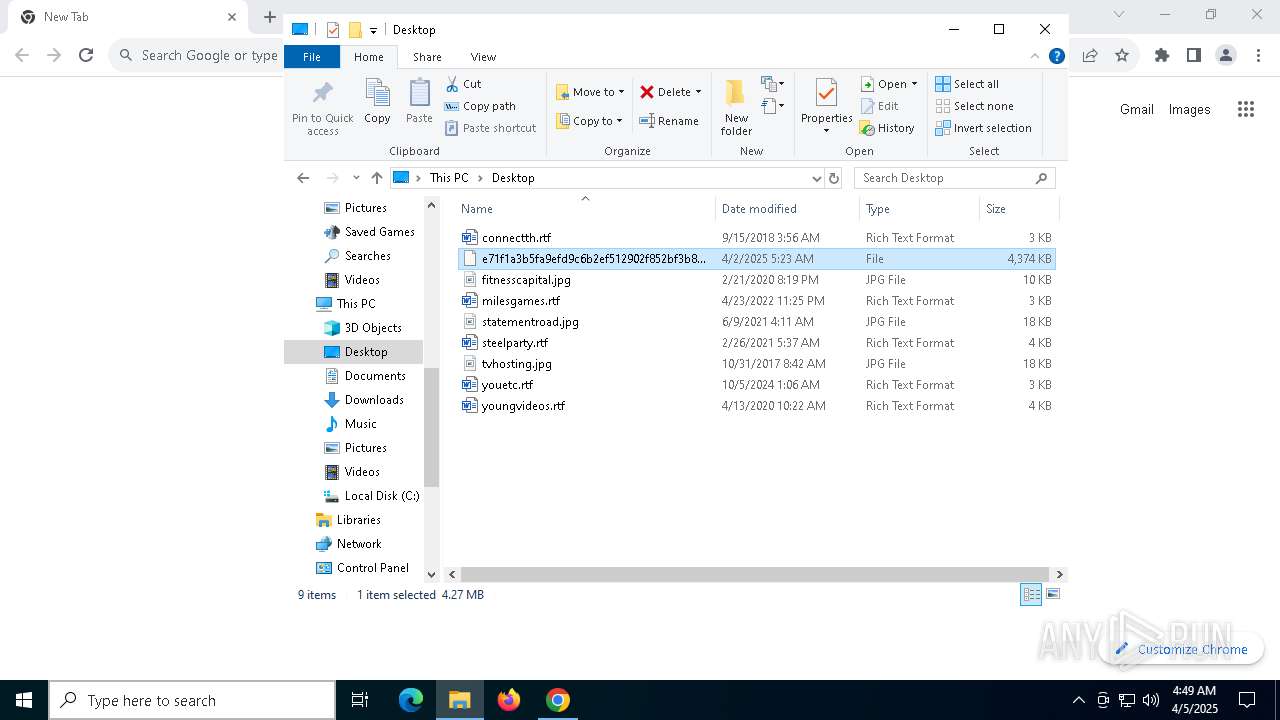
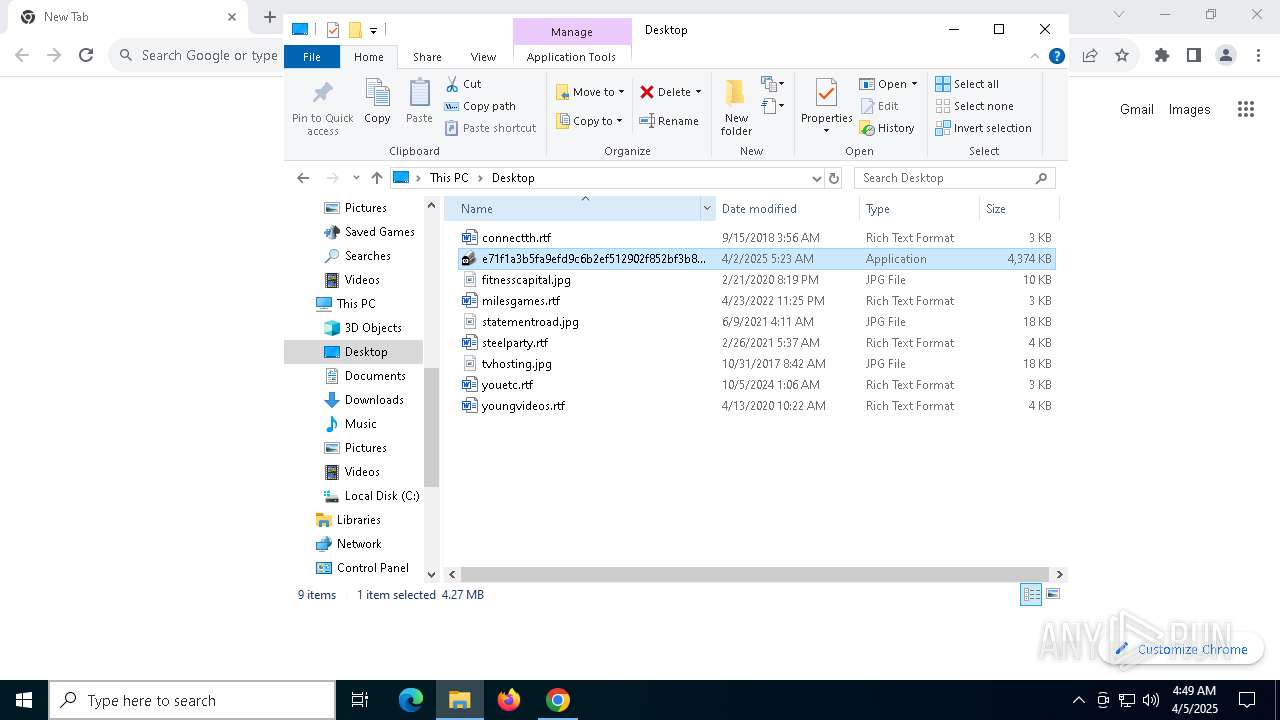
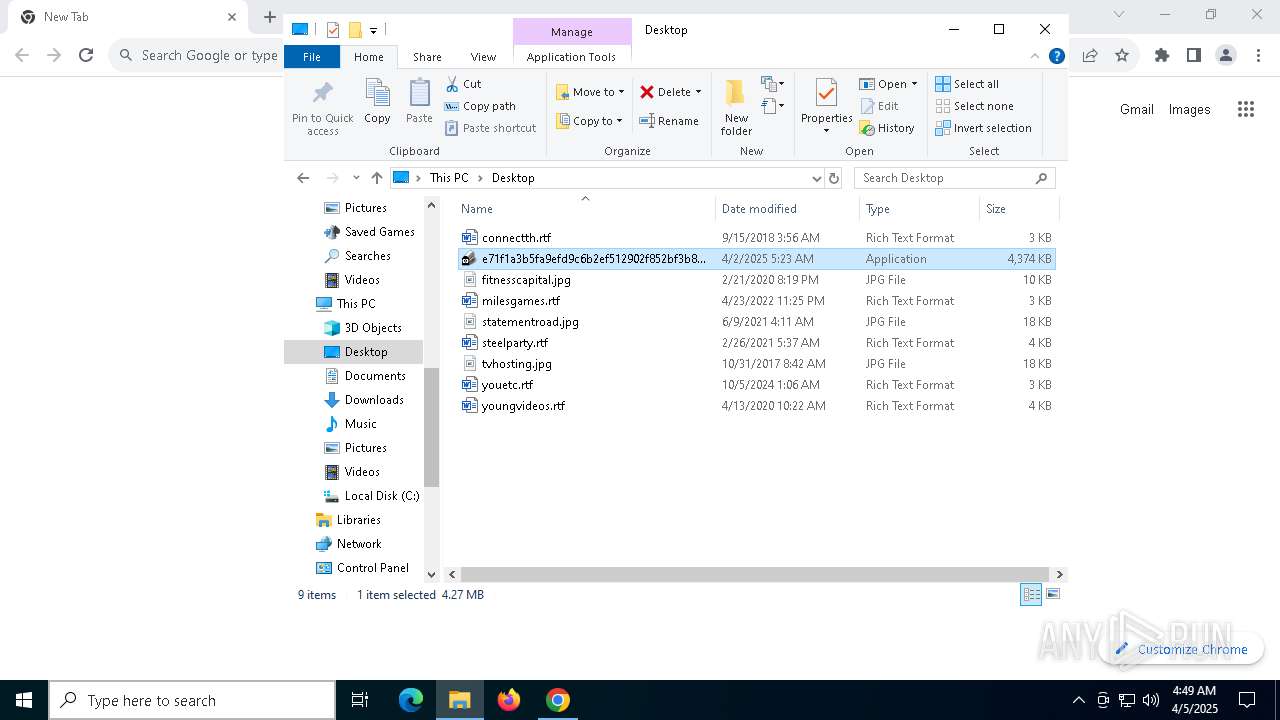
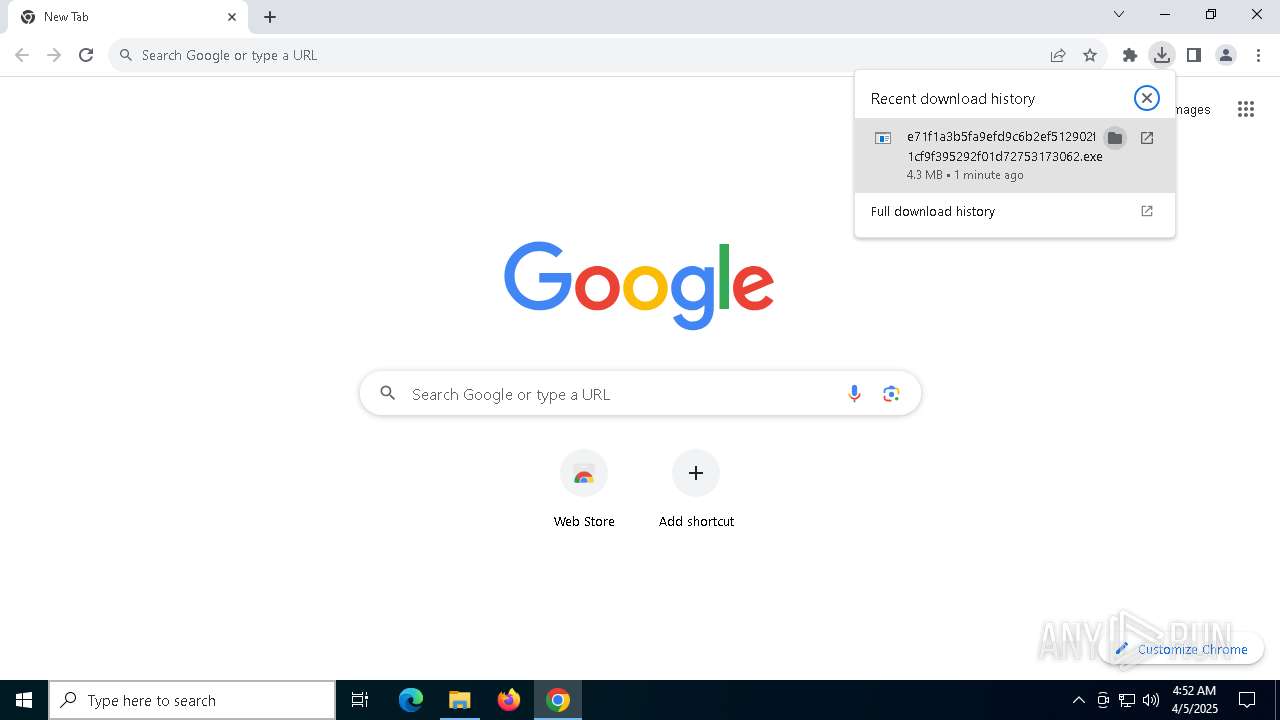
| File name: | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.zip |
| Full analysis: | https://app.any.run/tasks/1e45ca88-5710-4375-9e21-29e0c910719f |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 05, 2025, 04:47:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | CABDD9E70811B2BDDAC3677227E0C2B5 |
| SHA1: | 301643F9C8704E64D5F5894243731BC32AB6A421 |
| SHA256: | 88999DDDD1F462BA23650EC7B6A9263D014F601425837EB0986133A0F3D78FC0 |
| SSDEEP: | 98304:GxcokoNhK2FKg+3sK8svHwODaQHHCoKOyJNcygPOdcaiYhJGGaU2C7EABIZweq32:cN4pR |
MALICIOUS
LUMMA has been found (auto)
- WinRAR.exe (PID: 5680)
- chrome.exe (PID: 7648)
LUMMA mutex has been found
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
LUMMA has been detected (SURICATA)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- svchost.exe (PID: 2196)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Stealers network behavior
- svchost.exe (PID: 2196)
Connects to the CnC server
- svchost.exe (PID: 2196)
Steals credentials from Web Browsers
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Actions looks like stealing of personal data
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Changes the autorun value in the registry
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- reg.exe (PID: 7252)
- VBRSB89DTUJ7XJD00D5RUF8YDVK.exe (PID: 2420)
- XWWMZENYHUINSJ07XV5ZWIIA4.exe (PID: 1672)
- OQL10PIQD8MHB1NHB.exe (PID: 5968)
- BAT6BCYFAZ4QZPKSOWD5VC.exe (PID: 5116)
- NJ8QINIJC5MOZY29SDUO30DHFAM.exe (PID: 232)
Executing a file with an untrusted certificate
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- 86P1G5DVRBQK85I9A.exe (PID: 5228)
- A4JSQCM5EPLL3YNND7ZZ0DEJJ5.exe (PID: 4028)
- JRDJ5NCC9AJRT6V6QGD3GXI4N1.exe (PID: 4408)
- O4ENMYAXLWVH97KYONL59KDL97WONN8.exe (PID: 1760)
- N40VV6LC6J2SUMYT6P.exe (PID: 5984)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- VBRSB89DTUJ7XJD00D5RUF8YDVK.exe (PID: 2420)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Searches for installed software
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Executable content was dropped or overwritten
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Connects to unusual port
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
There is functionality for communication over UDP network (YARA)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Found regular expressions for crypto-addresses (YARA)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Starts CMD.EXE for commands execution
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 456)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 5680)
- chrome.exe (PID: 5756)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- chrome.exe (PID: 7648)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Reads the software policy settings
- slui.exe (PID: 7268)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- slui.exe (PID: 7388)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
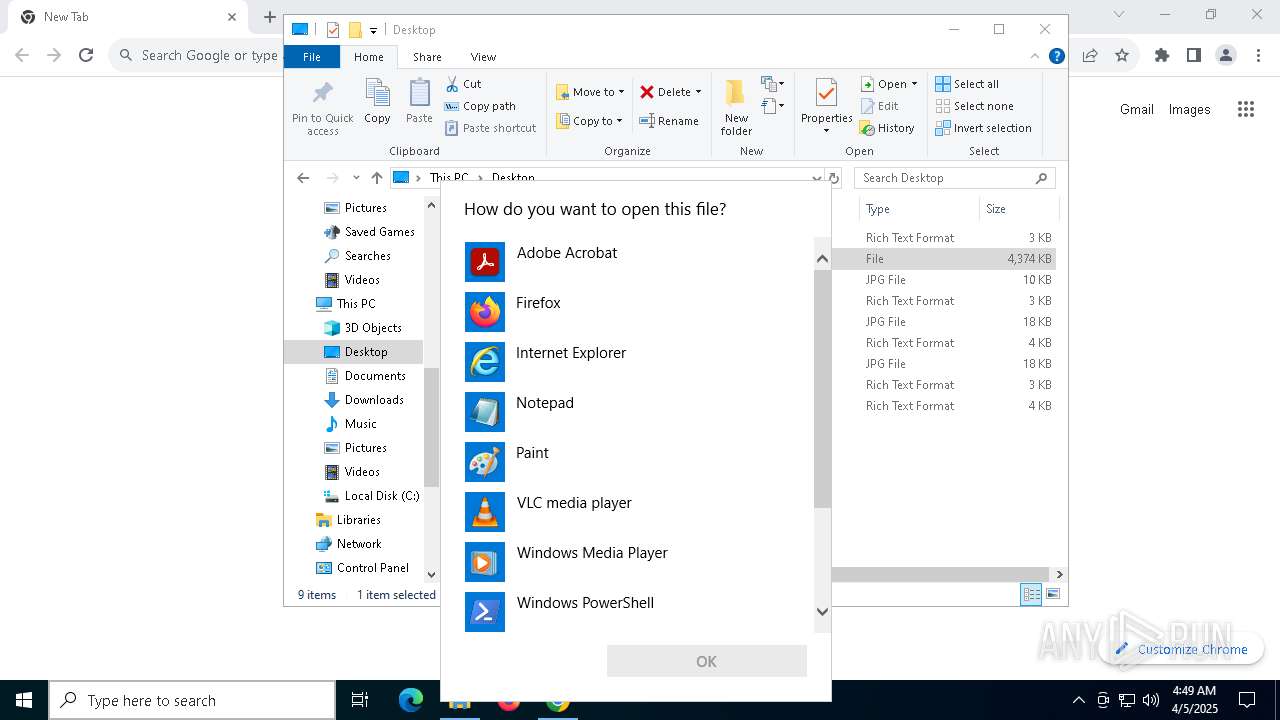
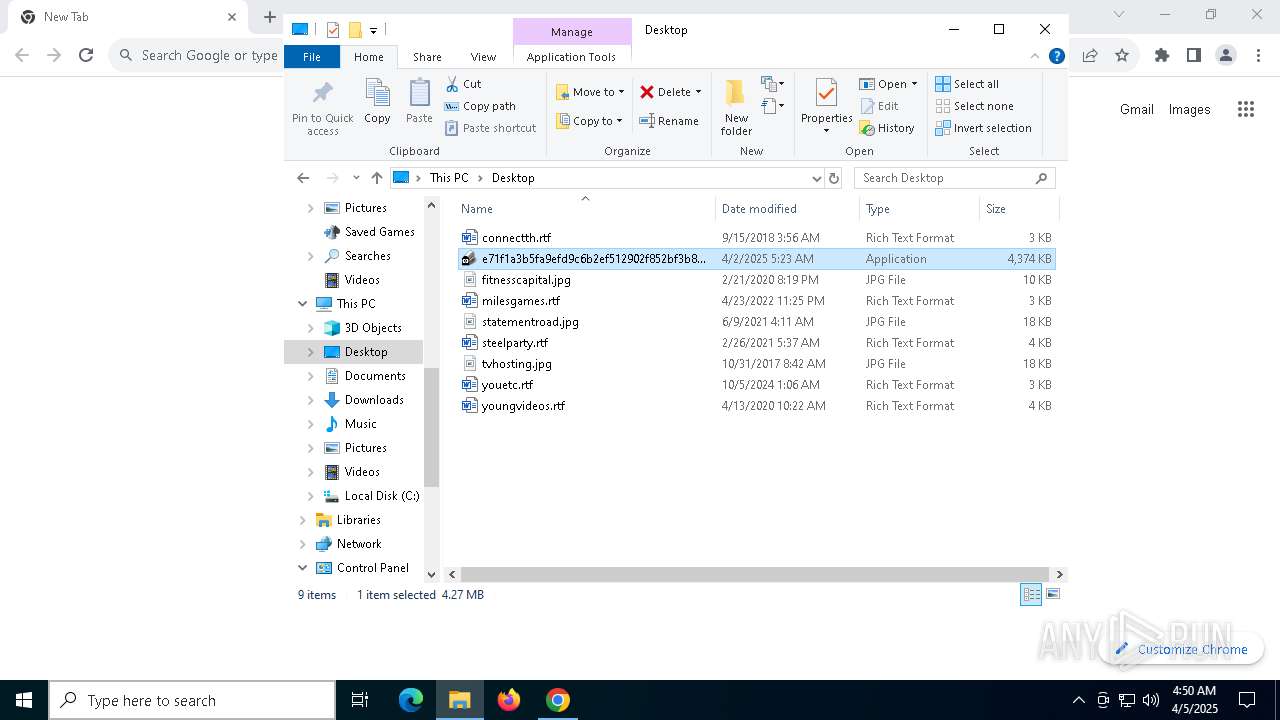
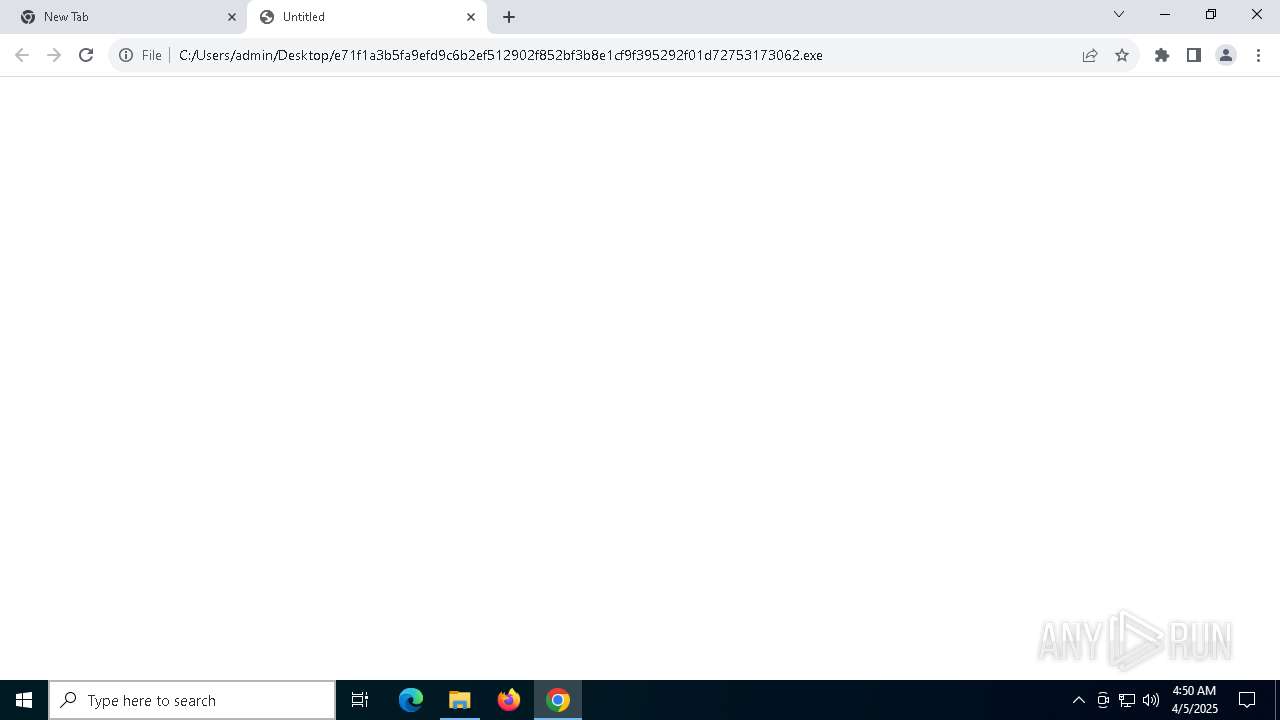
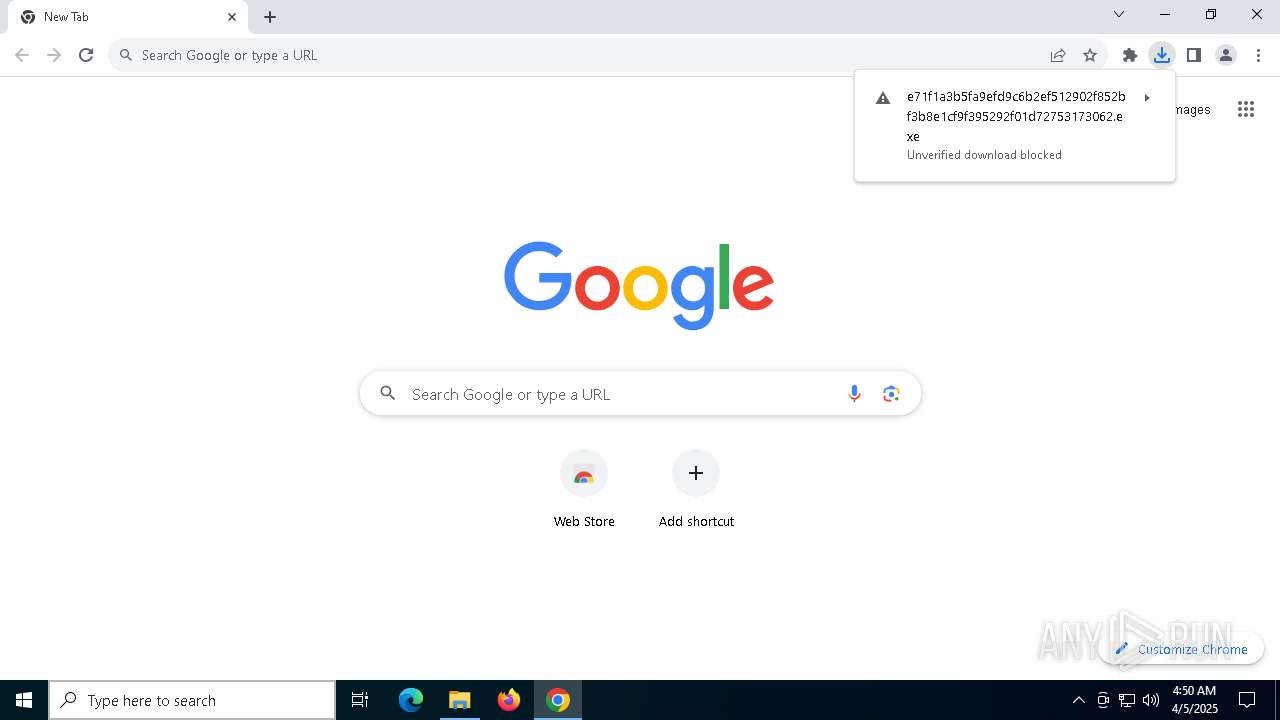
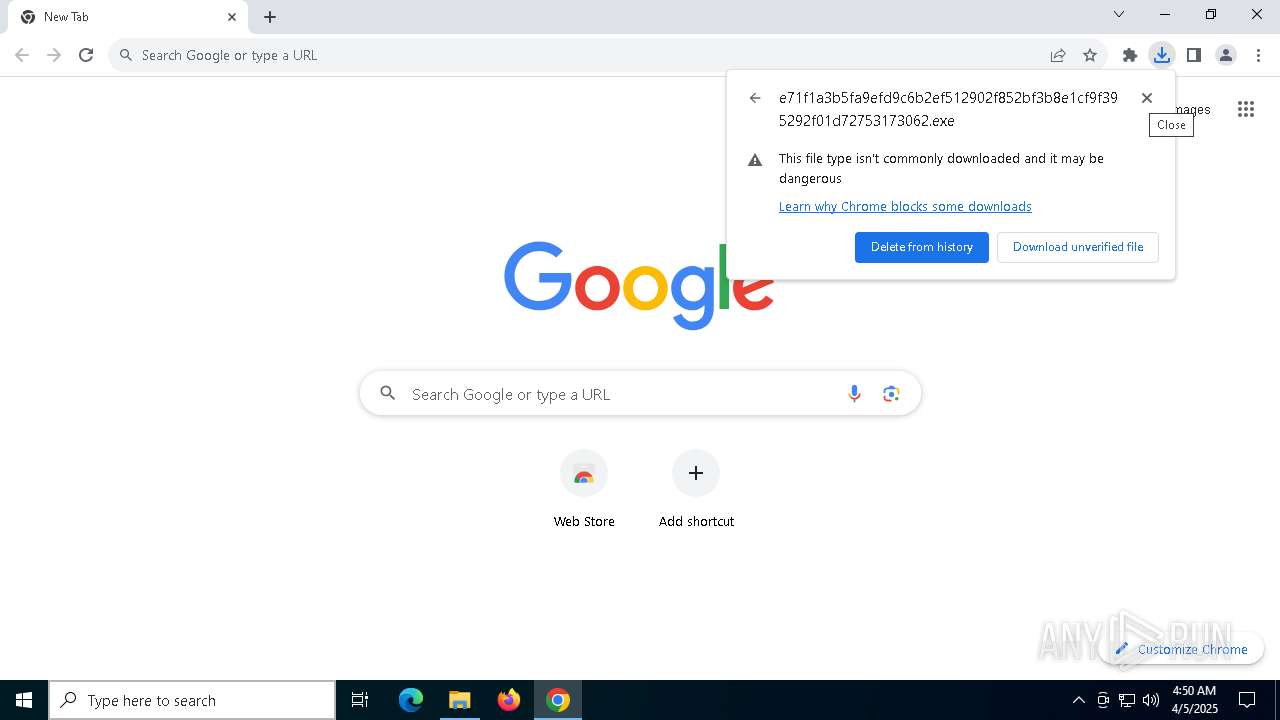
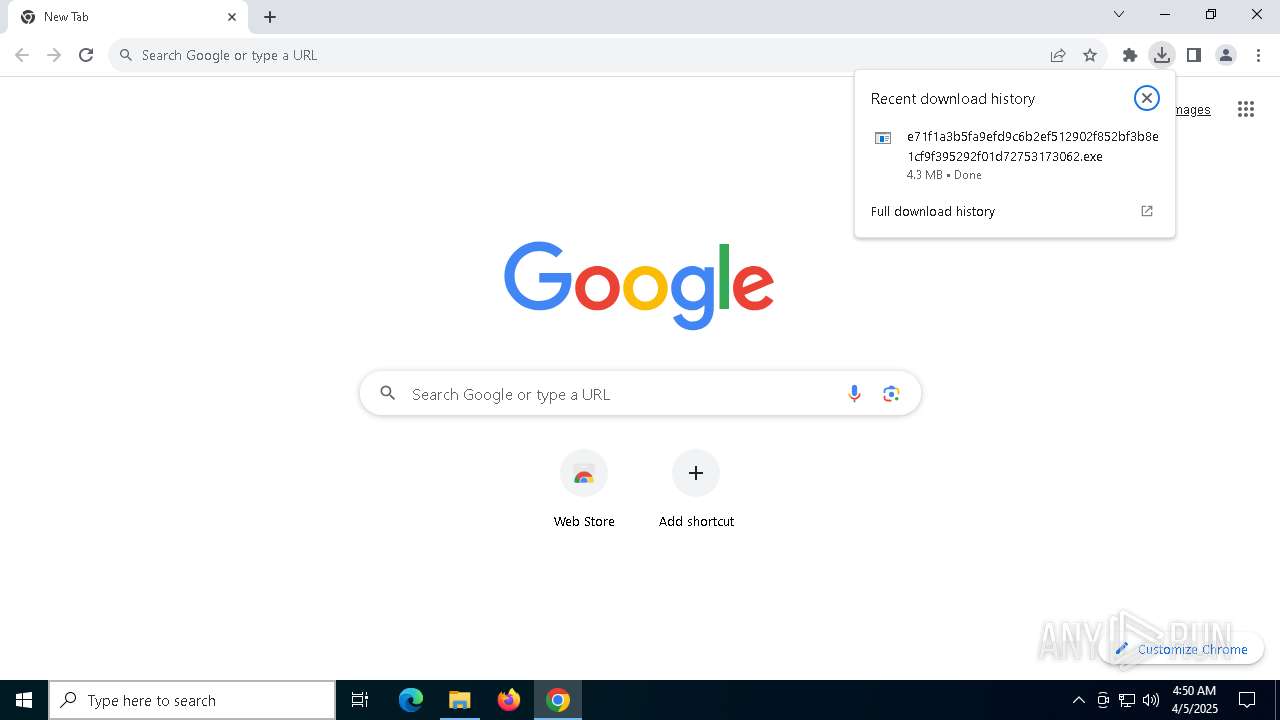
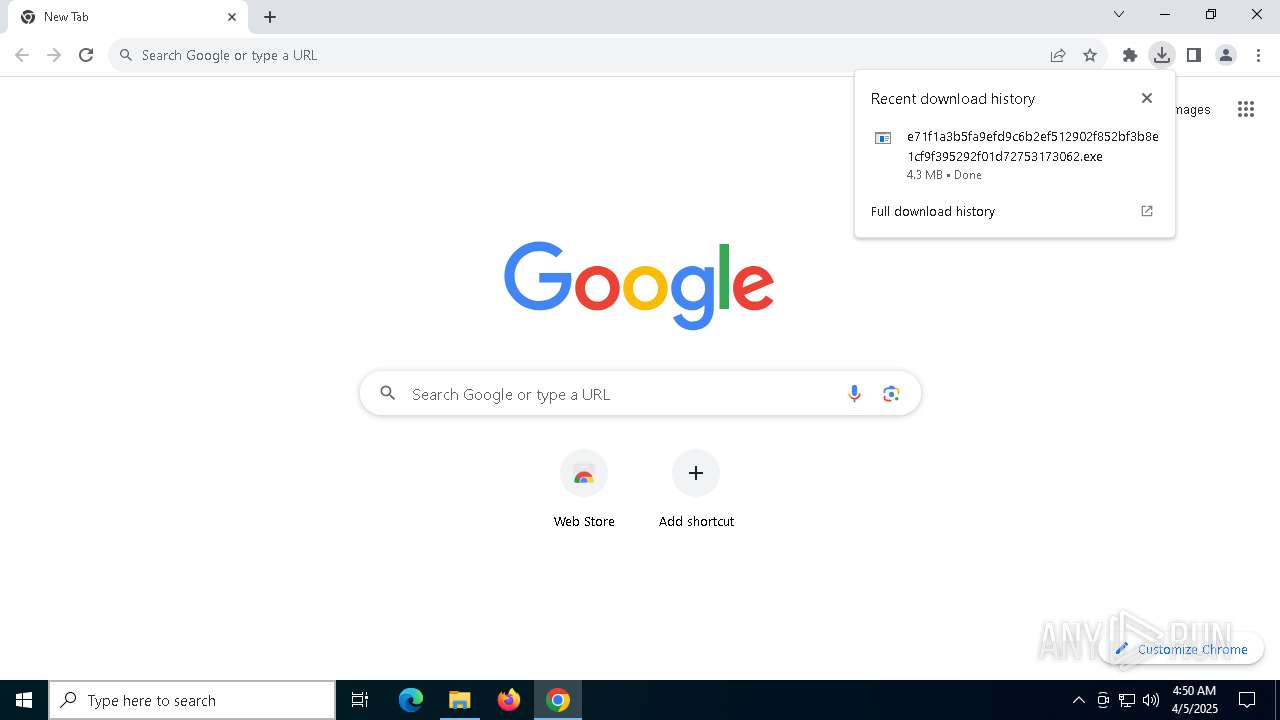
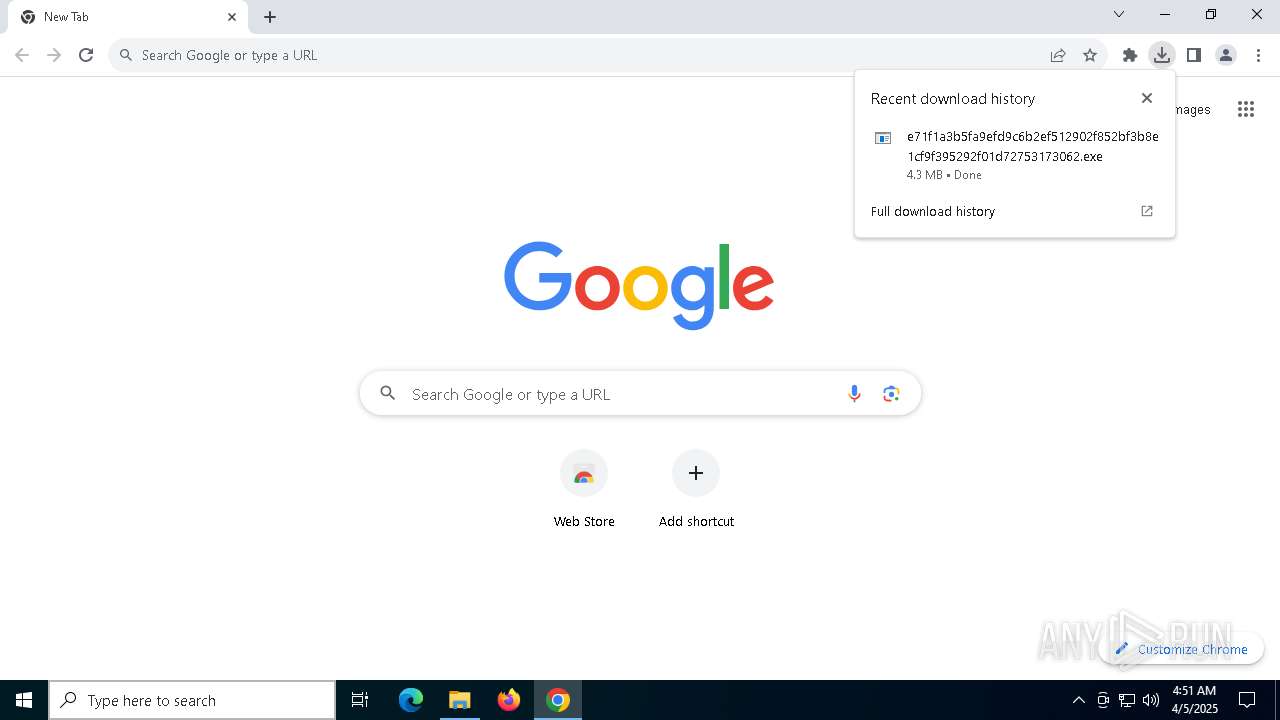
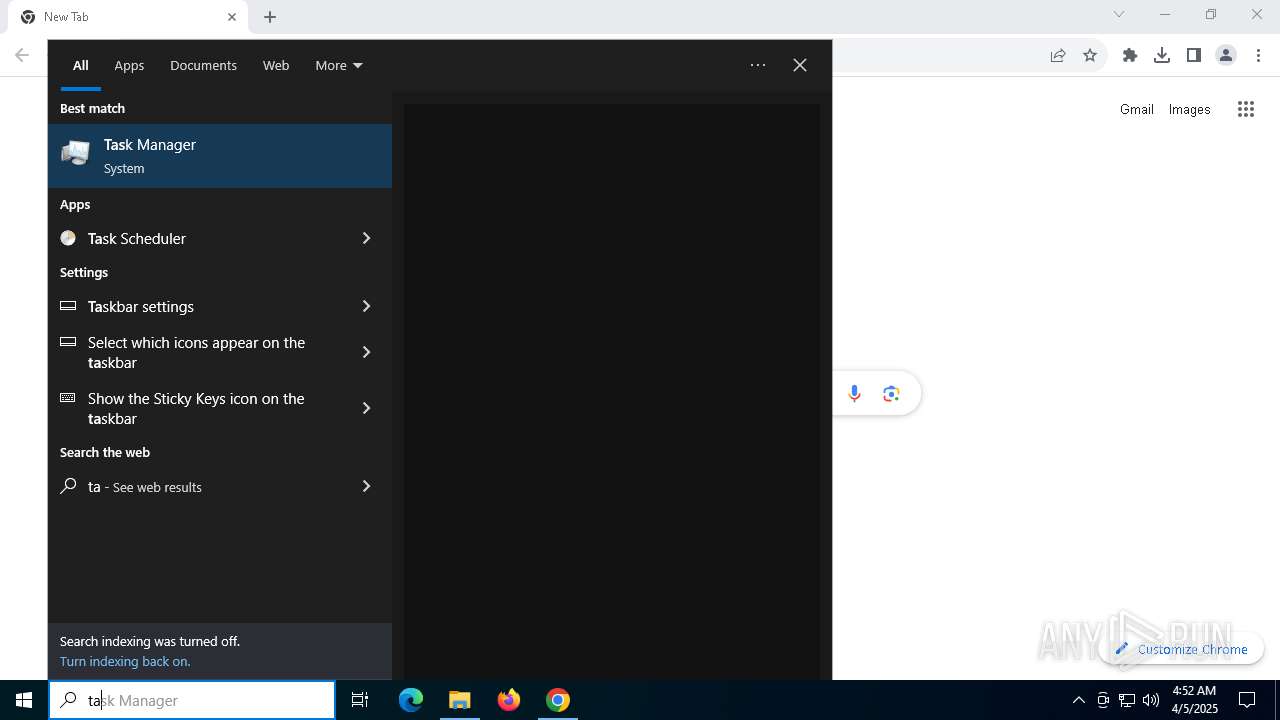
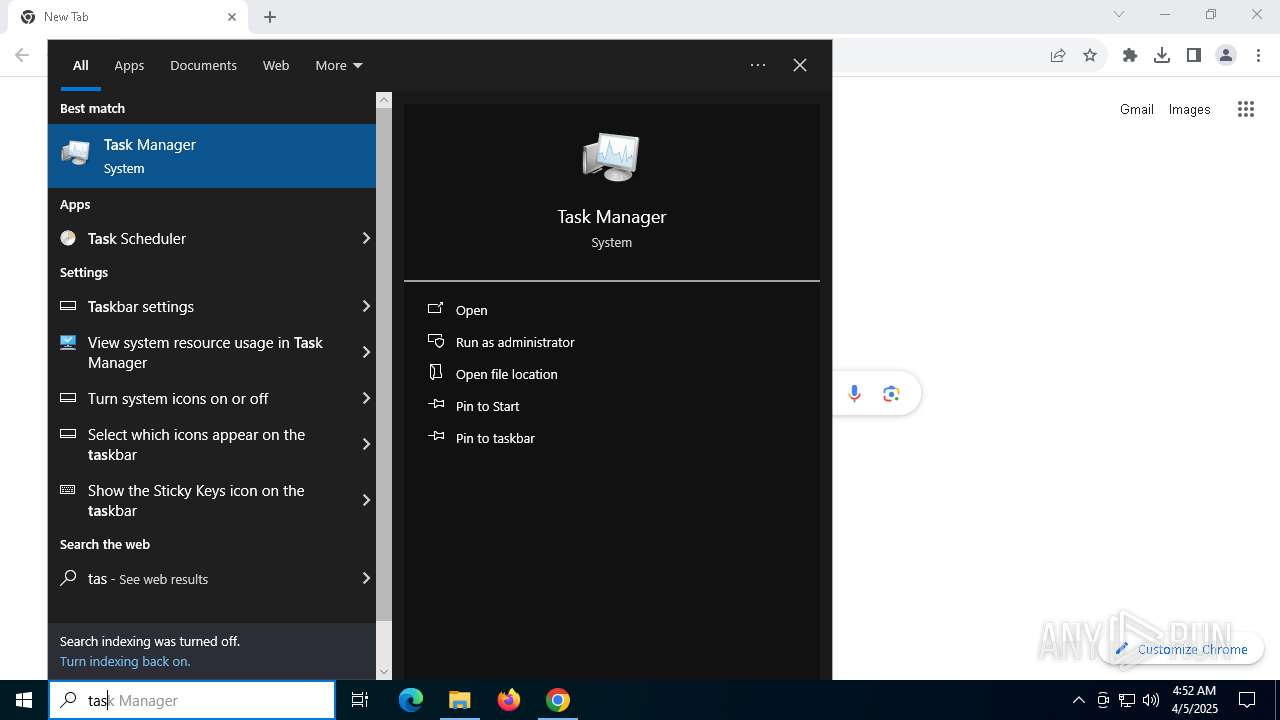
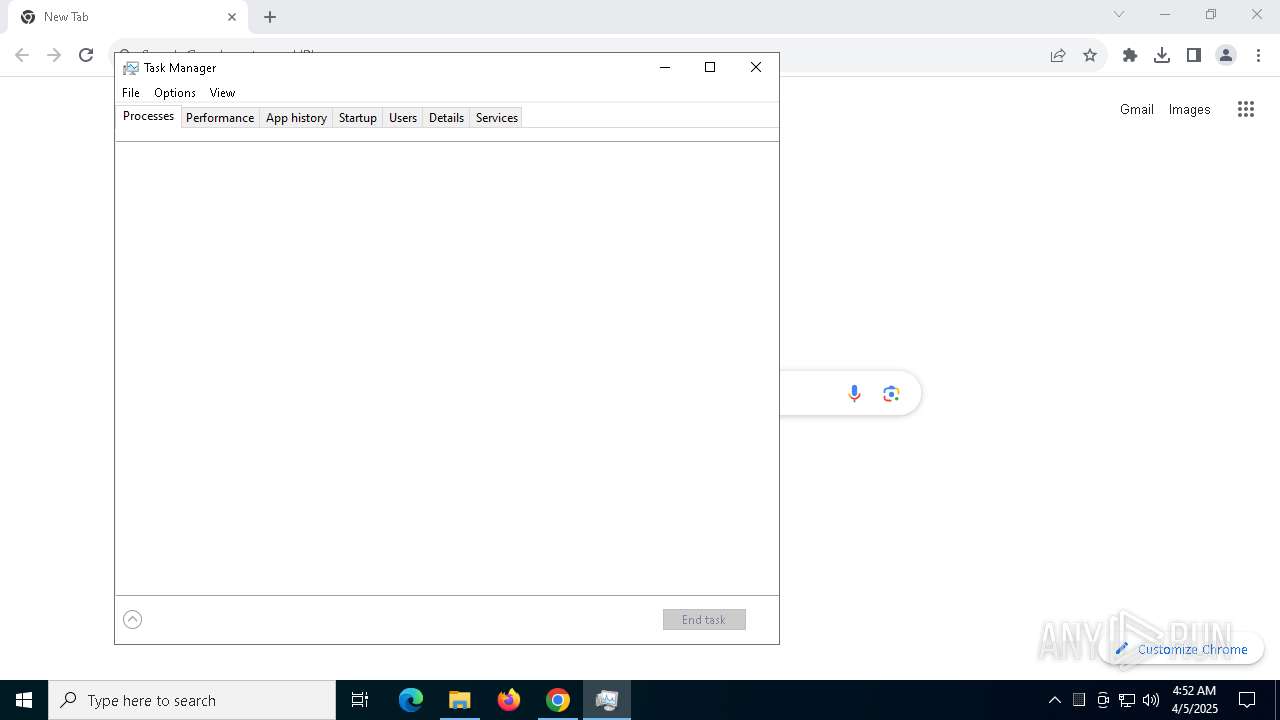
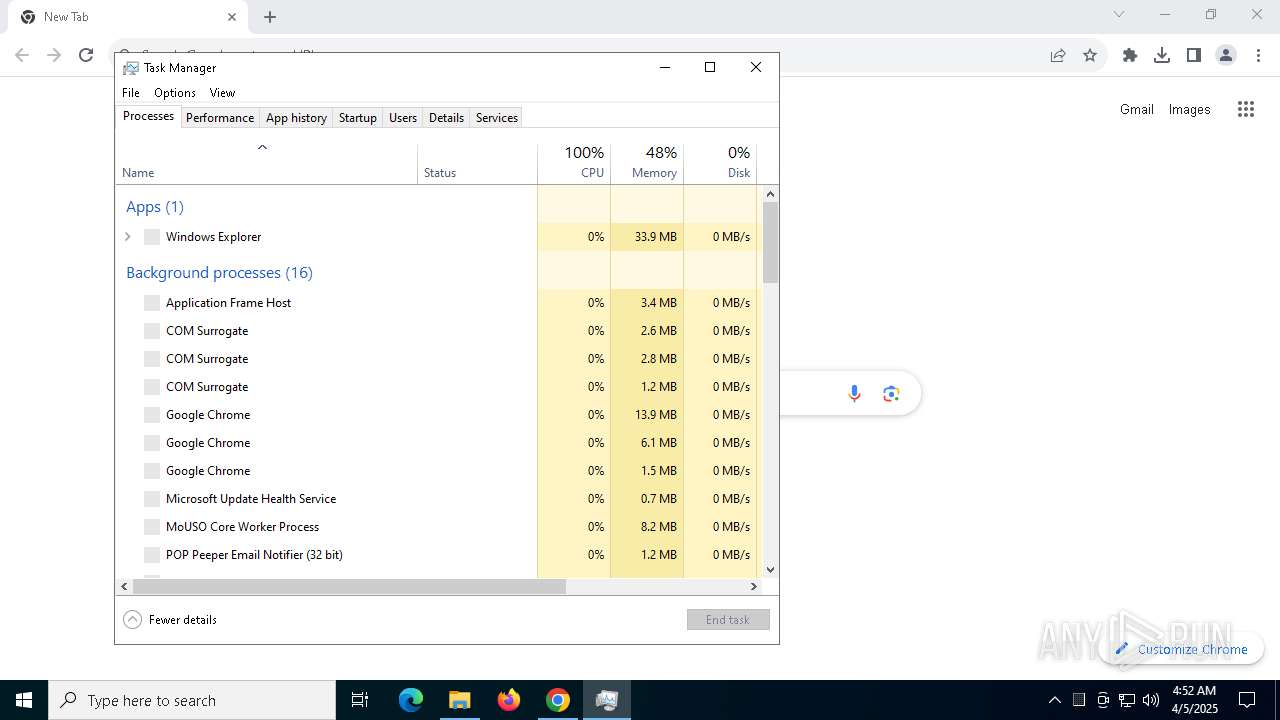
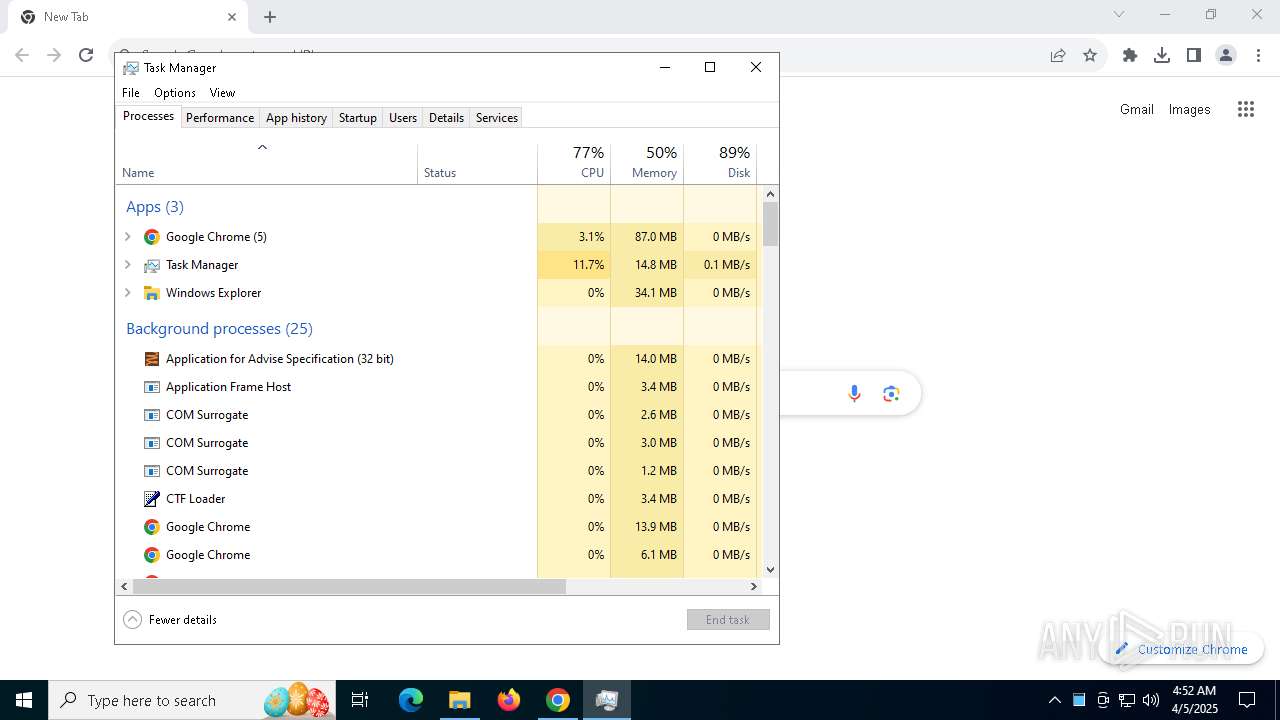
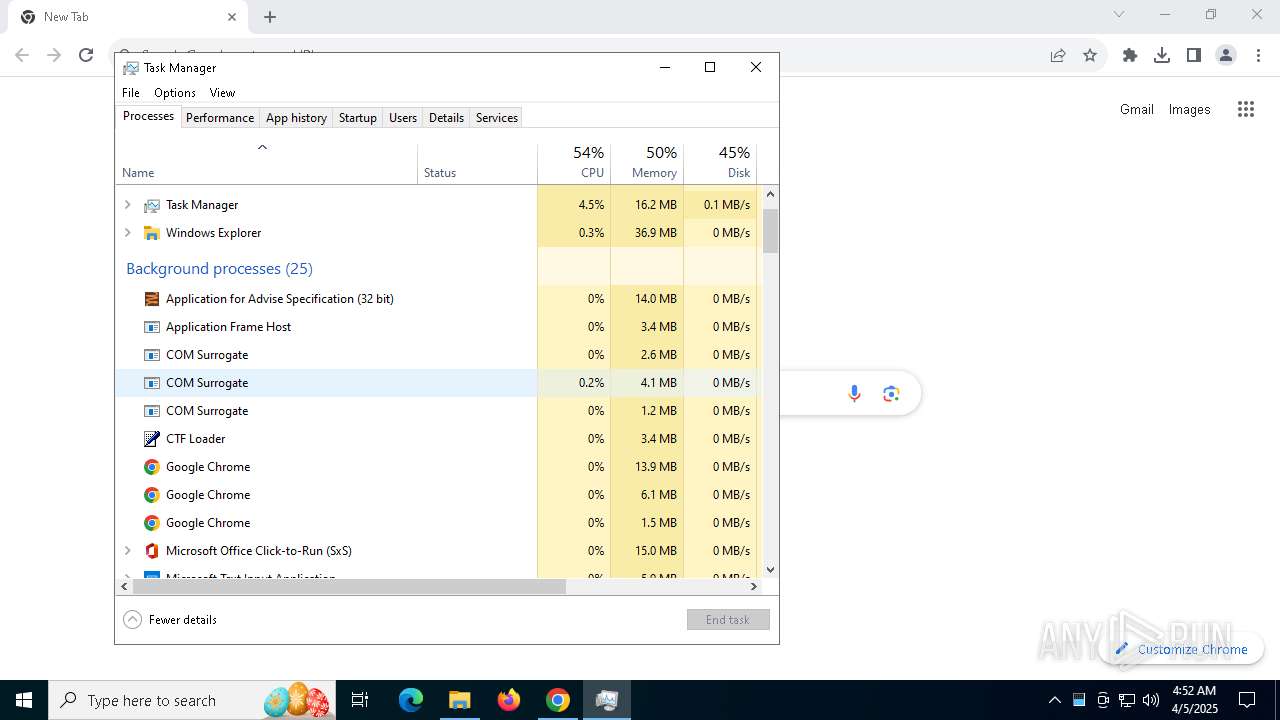
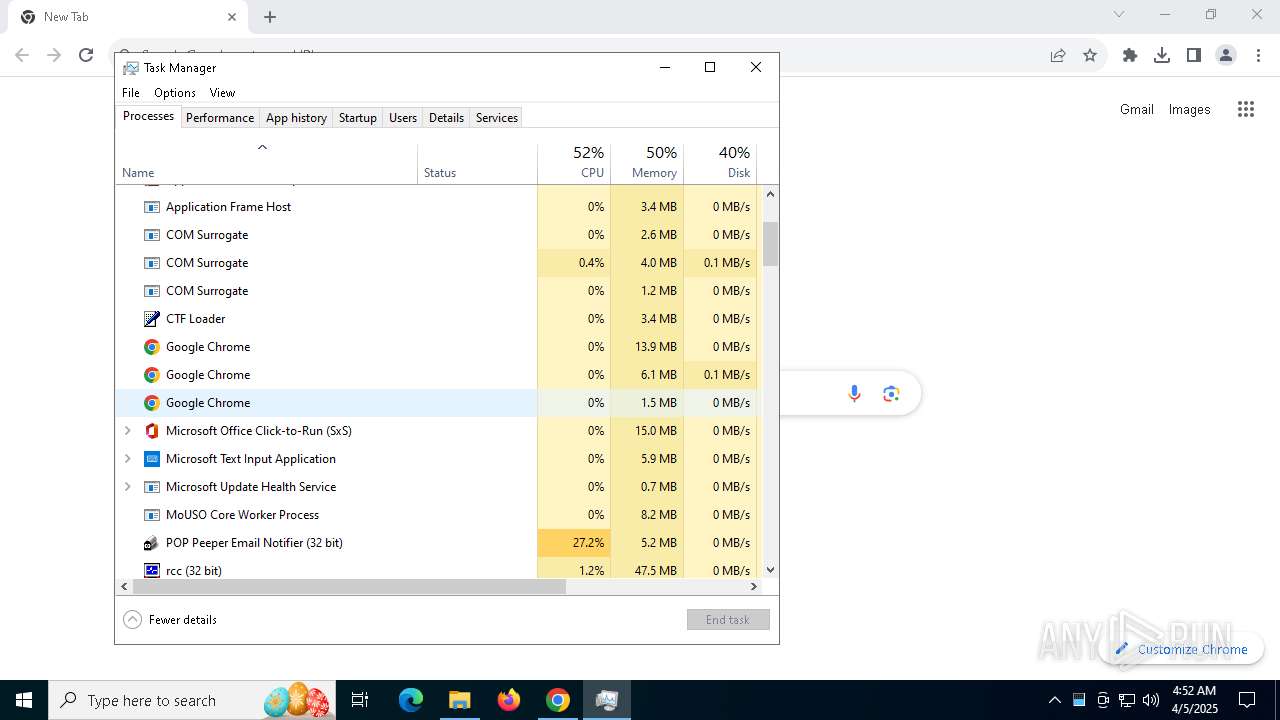
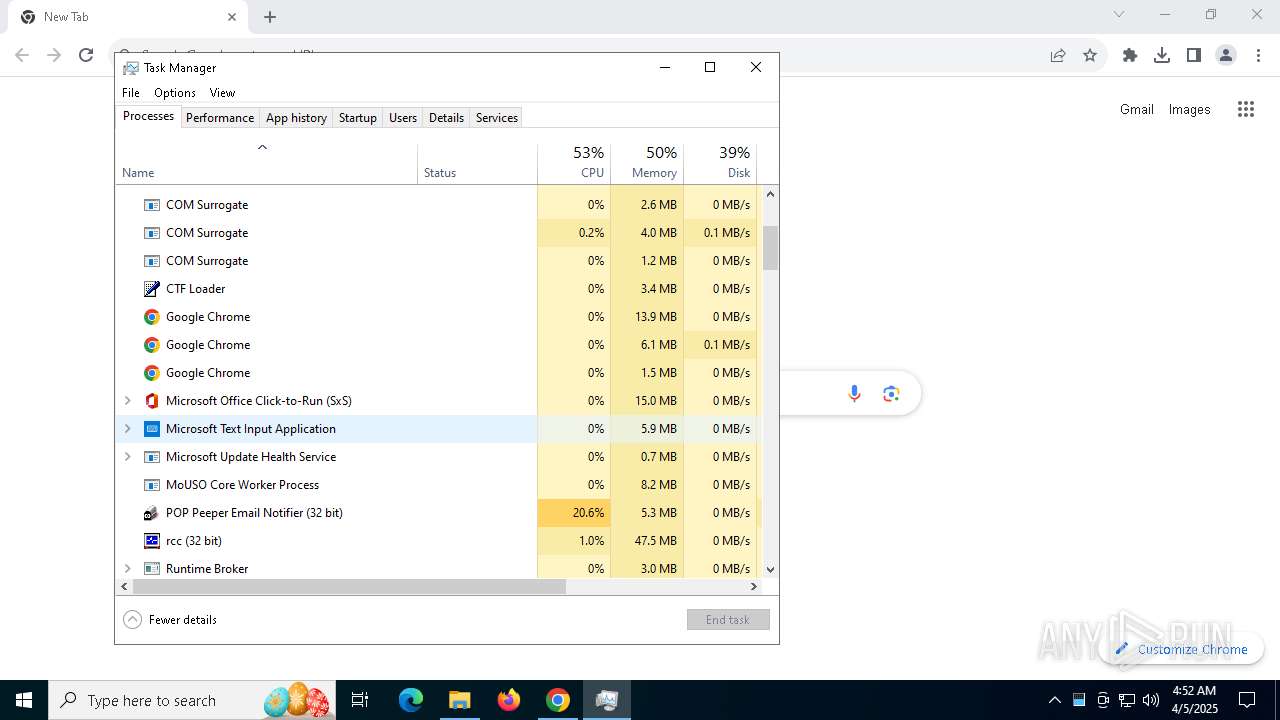
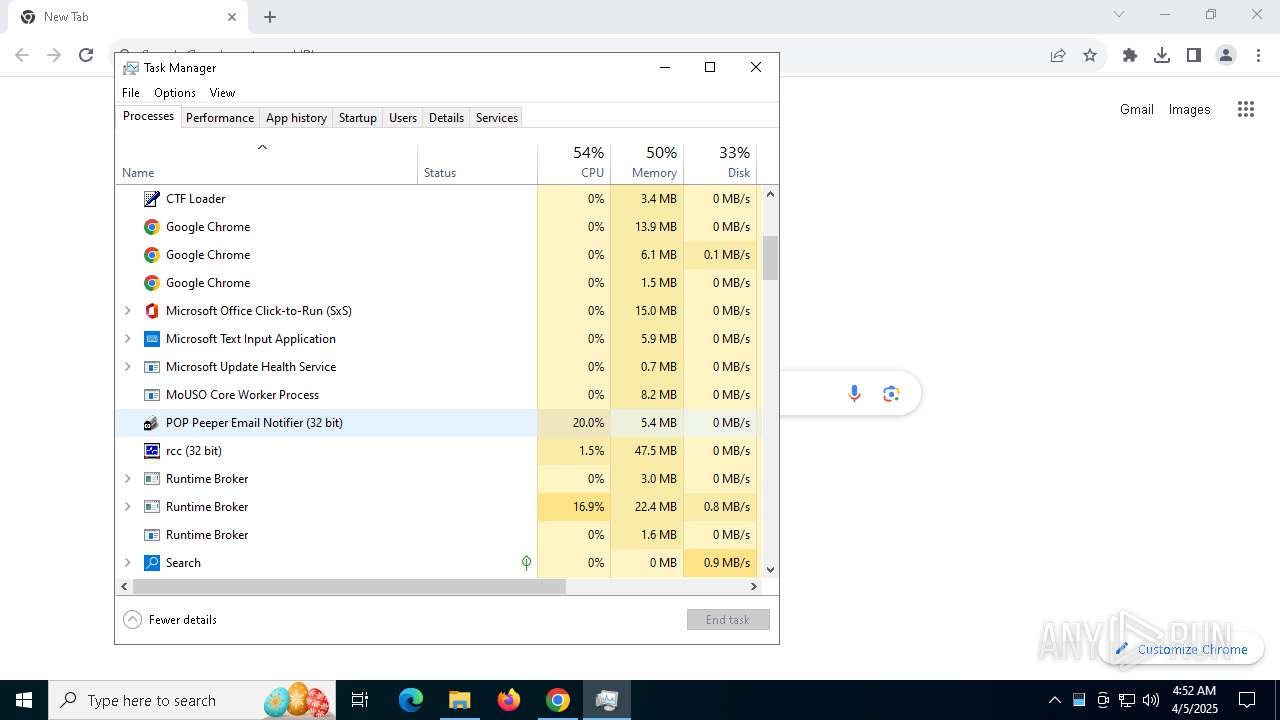
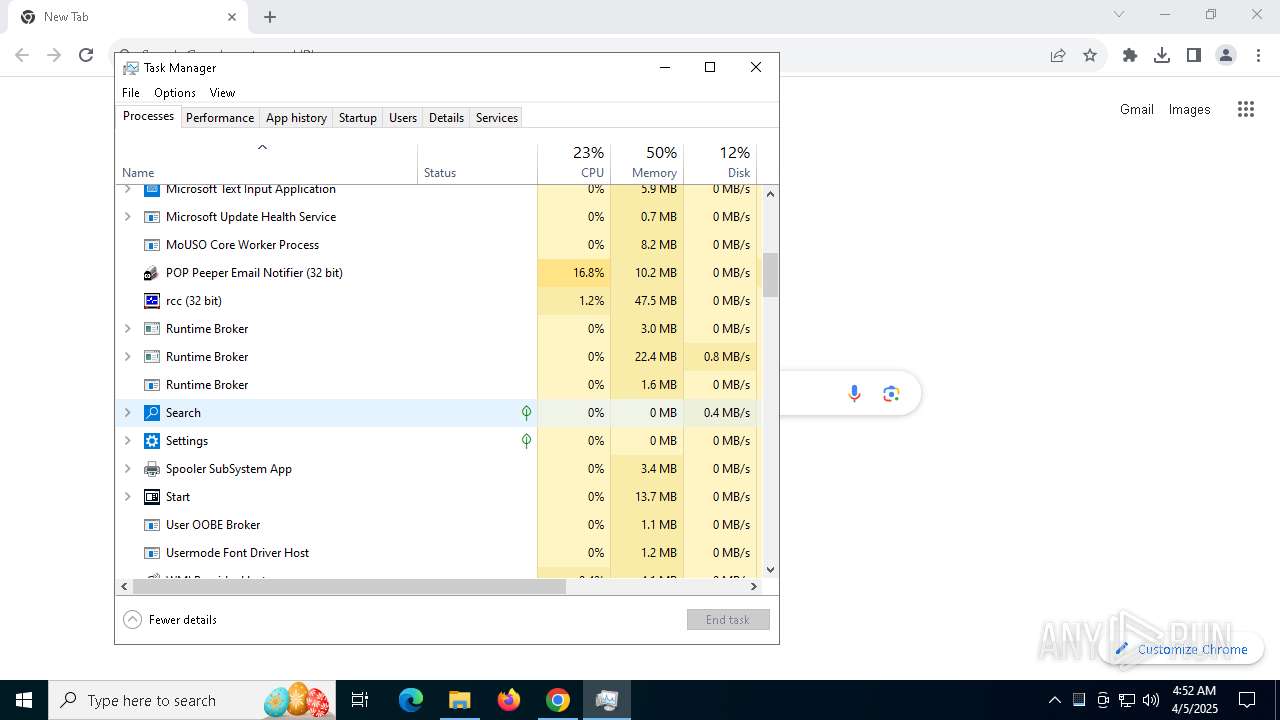
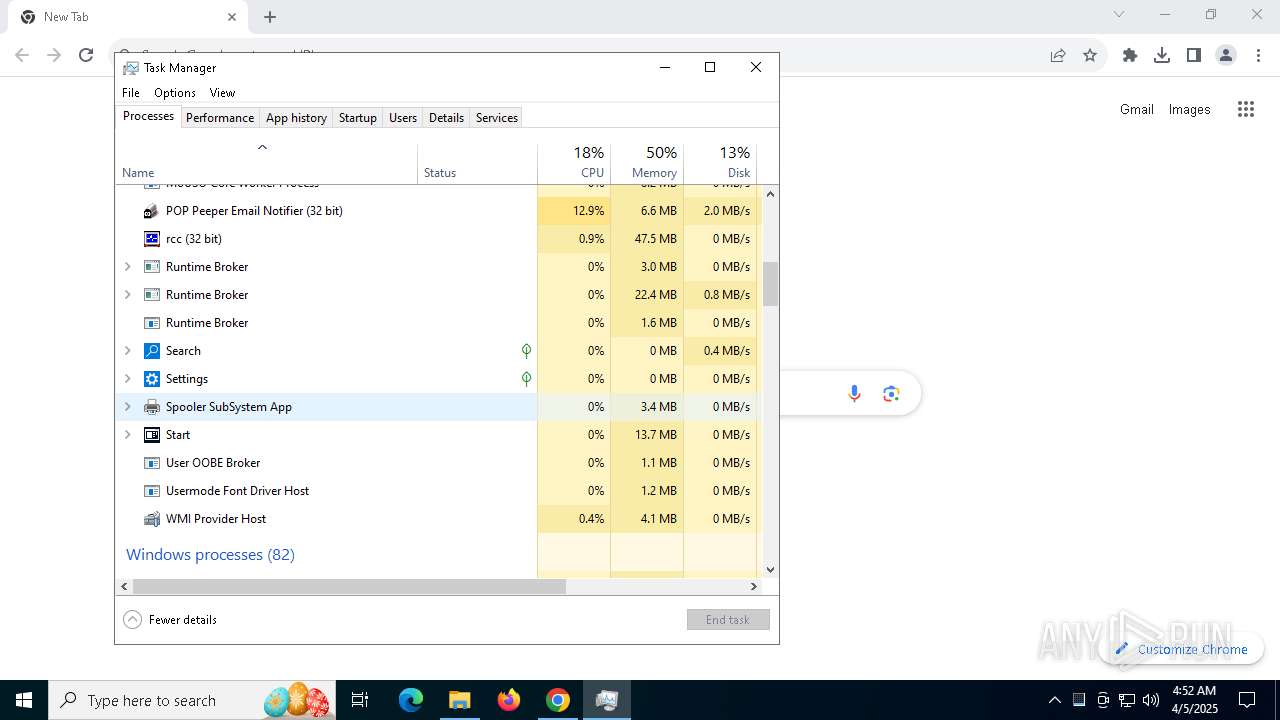
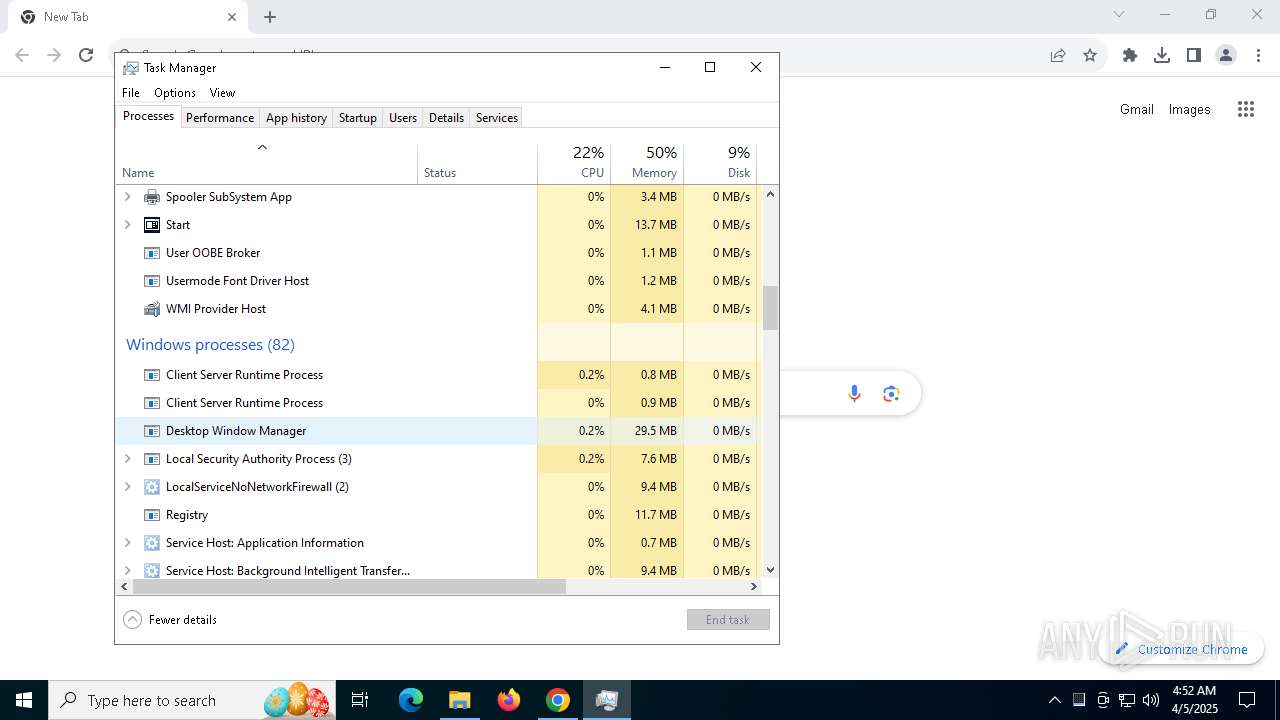
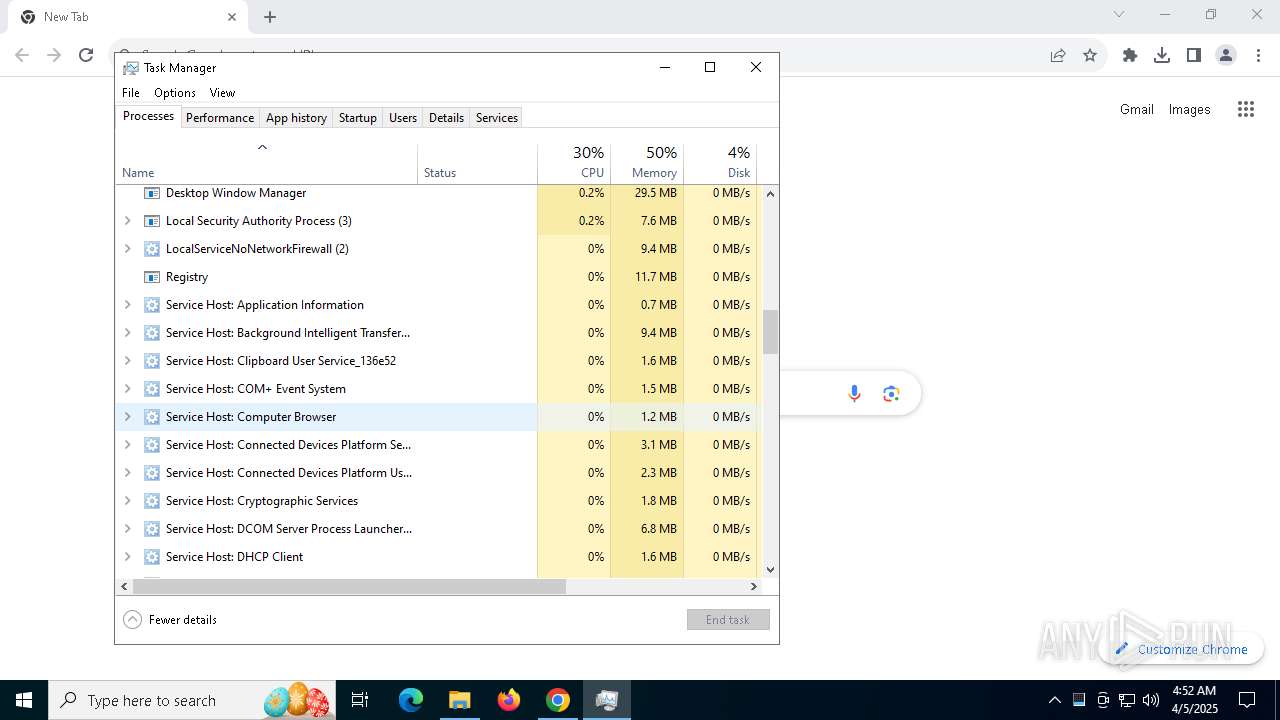
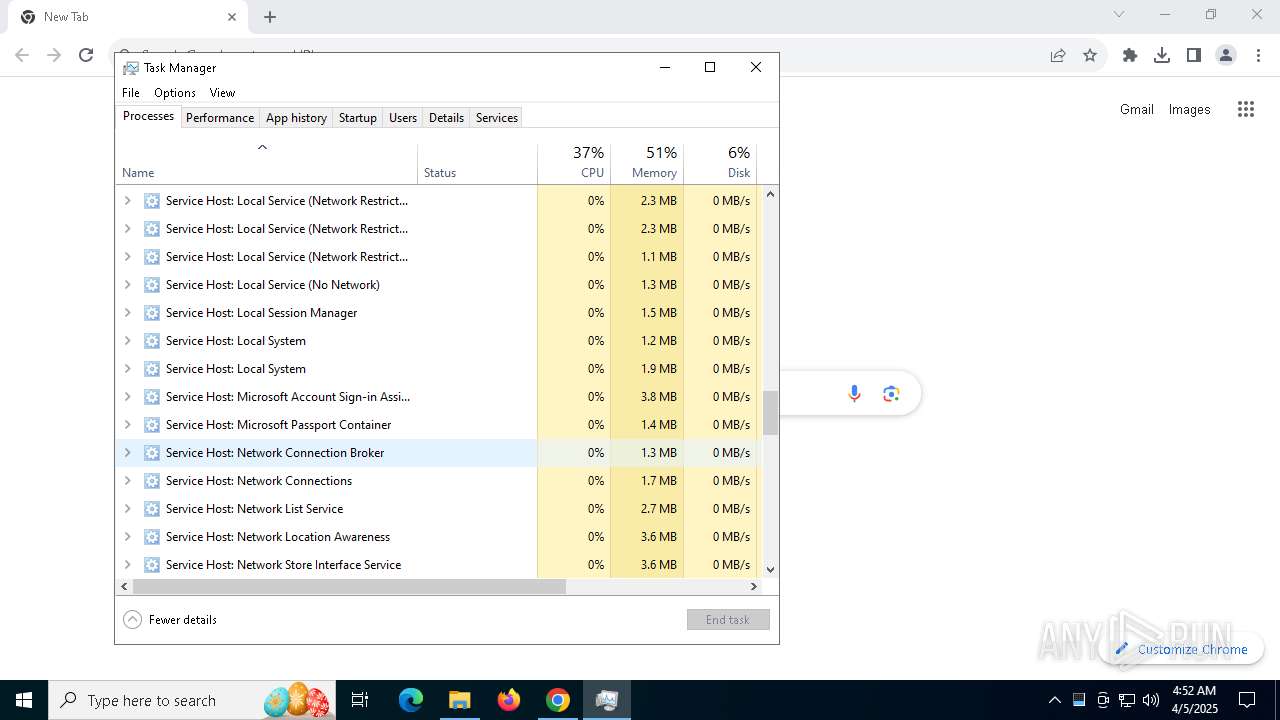
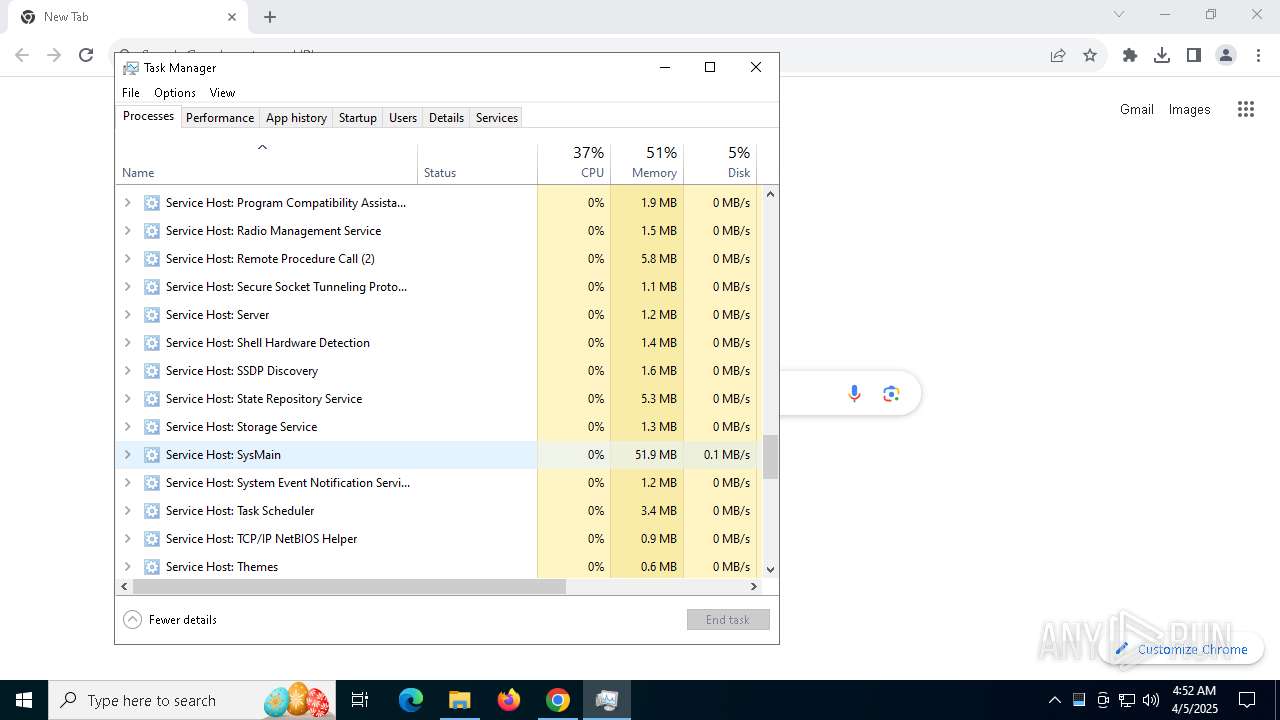
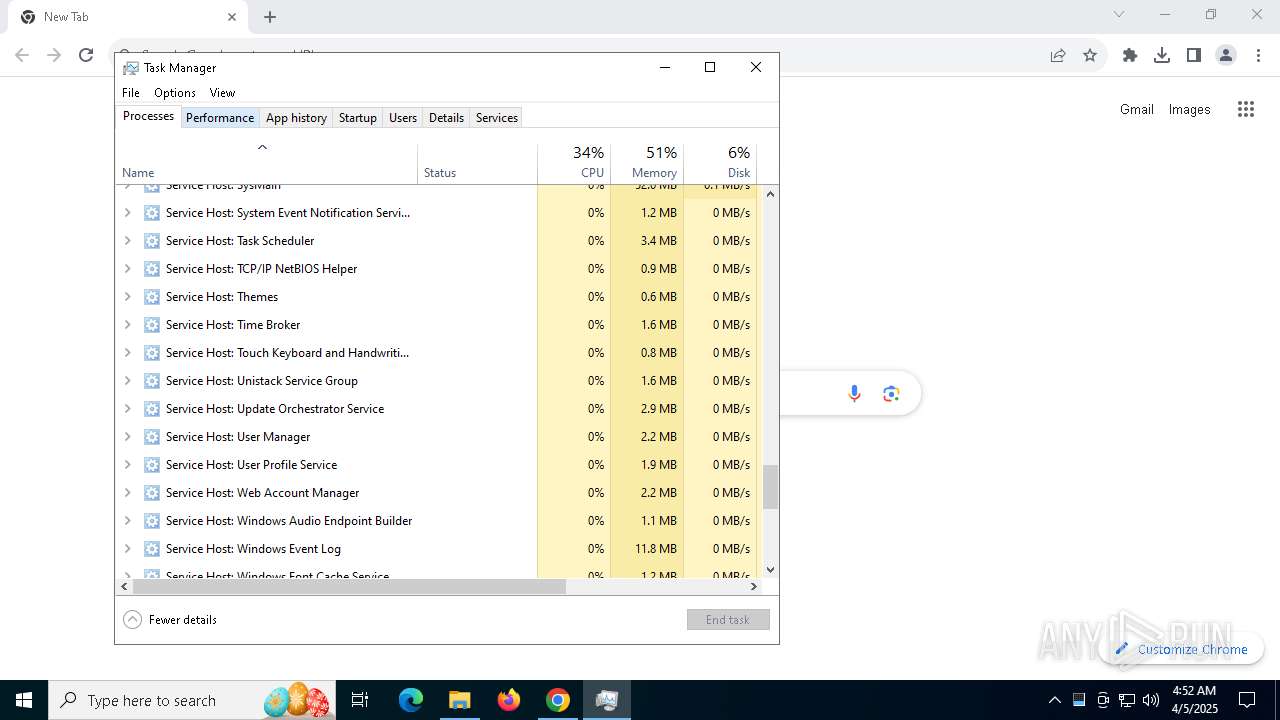
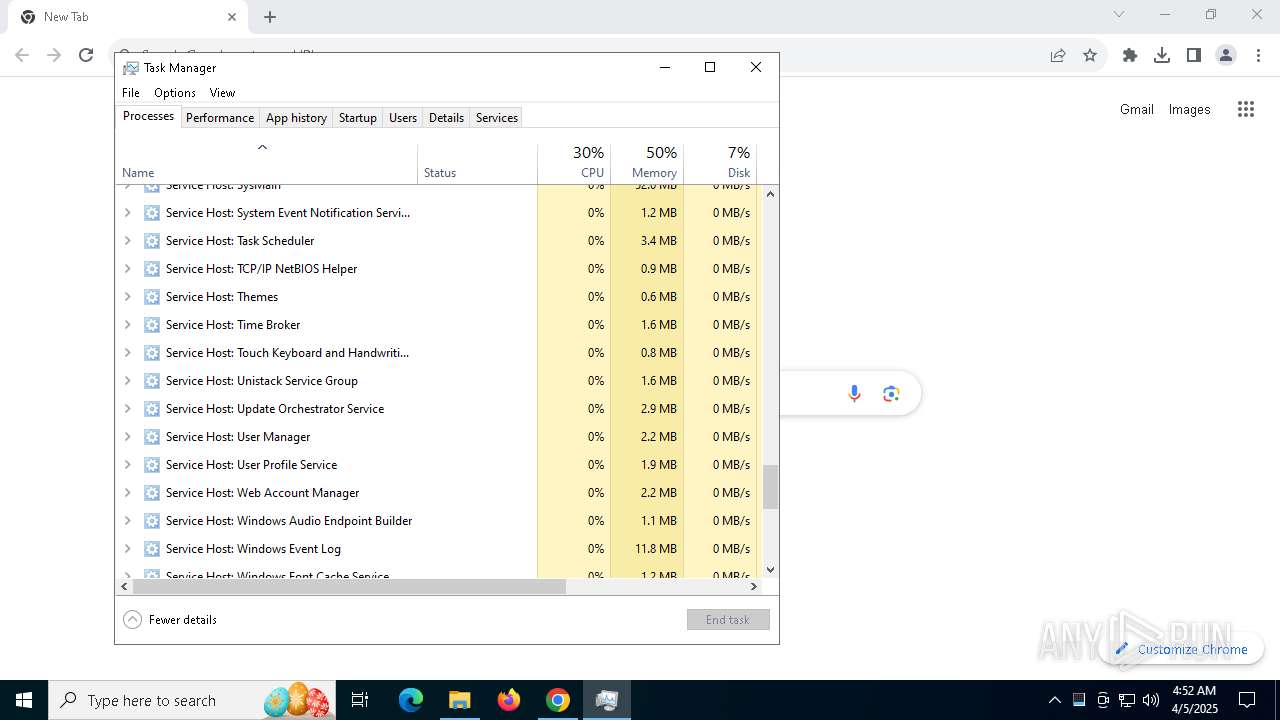
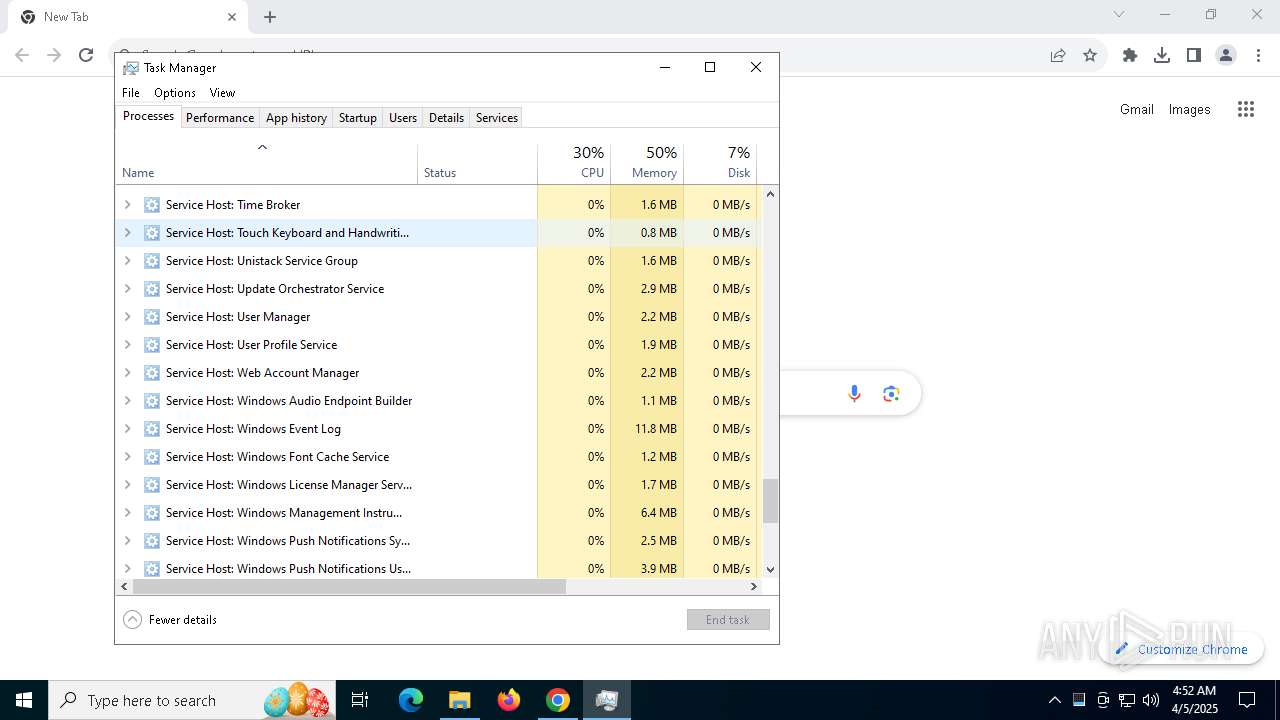
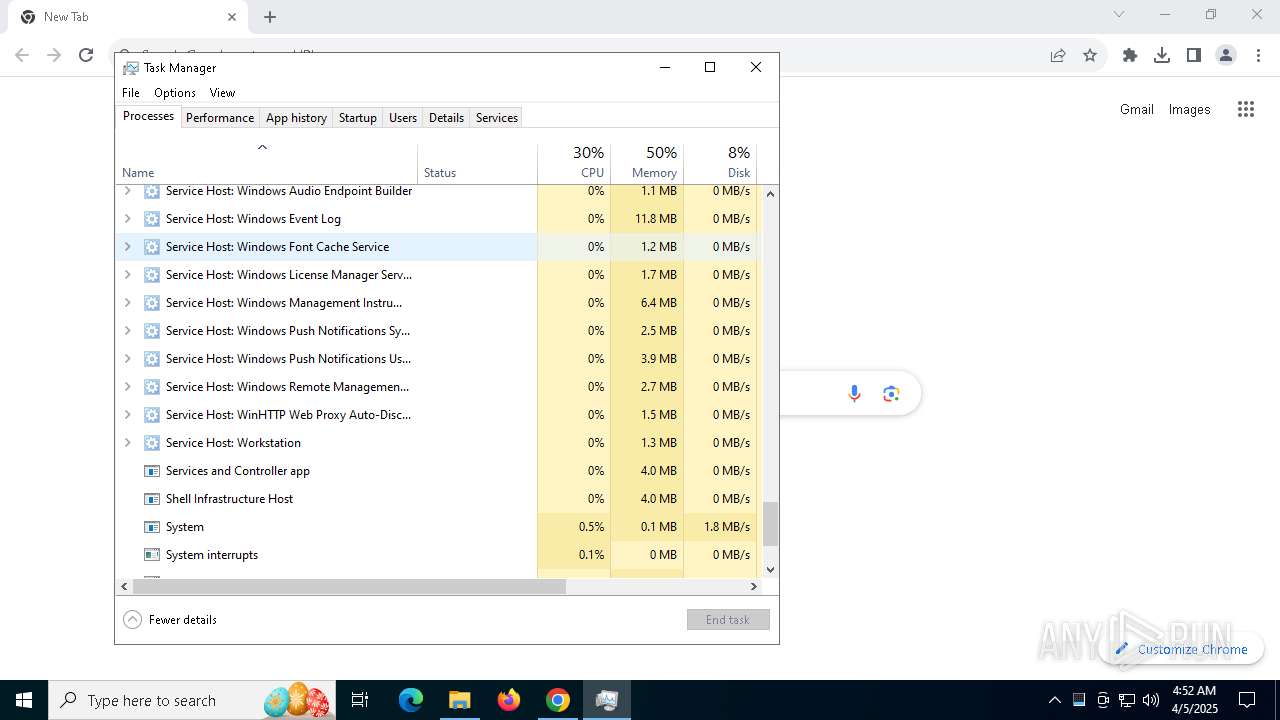
Manual execution by a user
- chrome.exe (PID: 7648)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- Taskmgr.exe (PID: 1804)
- Taskmgr.exe (PID: 5640)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5680)
- chrome.exe (PID: 5756)
- chrome.exe (PID: 7648)
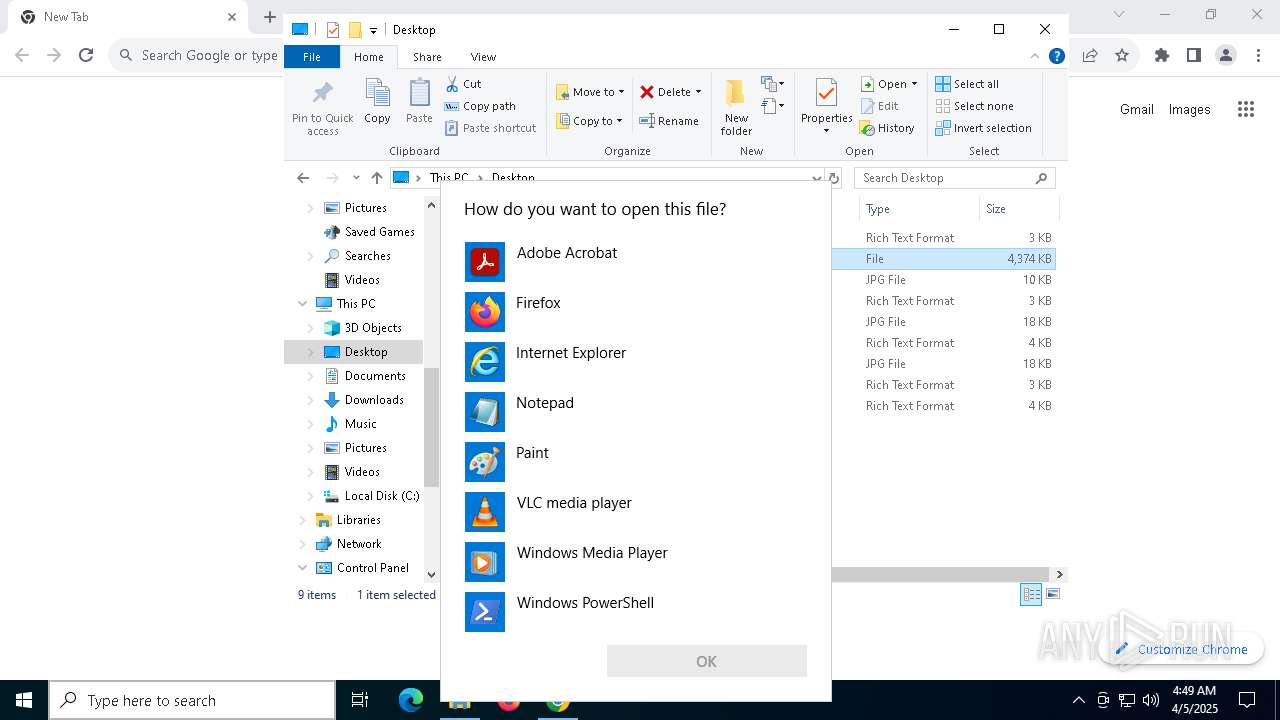
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 632)
Checks supported languages
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- VBRSB89DTUJ7XJD00D5RUF8YDVK.exe (PID: 2420)
- 86P1G5DVRBQK85I9A.exe (PID: 5228)
- XWWMZENYHUINSJ07XV5ZWIIA4.exe (PID: 1672)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- A4JSQCM5EPLL3YNND7ZZ0DEJJ5.exe (PID: 4028)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- OQL10PIQD8MHB1NHB.exe (PID: 5968)
- JRDJ5NCC9AJRT6V6QGD3GXI4N1.exe (PID: 4408)
- BAT6BCYFAZ4QZPKSOWD5VC.exe (PID: 5116)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
- O4ENMYAXLWVH97KYONL59KDL97WONN8.exe (PID: 1760)
- NJ8QINIJC5MOZY29SDUO30DHFAM.exe (PID: 232)
- N40VV6LC6J2SUMYT6P.exe (PID: 5984)
Reads the computer name
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
Creates files or folders in the user directory
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
Create files in a temporary directory
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7752)
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2560)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 7224)
- XWWMZENYHUINSJ07XV5ZWIIA4.exe (PID: 1672)
- VBRSB89DTUJ7XJD00D5RUF8YDVK.exe (PID: 2420)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 2504)
- OQL10PIQD8MHB1NHB.exe (PID: 5968)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 6872)
- BAT6BCYFAZ4QZPKSOWD5VC.exe (PID: 5116)
- e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe (PID: 5452)
- NJ8QINIJC5MOZY29SDUO30DHFAM.exe (PID: 232)
Application launched itself
- chrome.exe (PID: 7648)
Application based on Golang
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- VBRSB89DTUJ7XJD00D5RUF8YDVK.exe (PID: 2420)
Detects GO elliptic curve encryption (YARA)
- 5XOUHT4O3BBZU2IC685JK.exe (PID: 4224)
- VBRSB89DTUJ7XJD00D5RUF8YDVK.exe (PID: 2420)
Compiled with Borland Delphi (YARA)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Creates files in the program directory
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Drops encrypted JS script (Microsoft Script Encoder)
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Reads the machine GUID from the registry
- 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe (PID: 2960)
Checks proxy server information
- slui.exe (PID: 7388)
Autorun file from Downloads
- chrome.exe (PID: 7648)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 5640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:04:01 22:23:58 |
| ZipCRC: | 0x2119b5b5 |
| ZipCompressedSize: | 1853842 |
| ZipUncompressedSize: | 4478976 |
| ZipFileName: | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062 |
Total processes
194
Monitored processes
60
Malicious processes
10
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5804 --field-trial-handle=1956,i,11771681620178920924,7663210313225716429,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 232 | "C:\Users\admin\AppData\Local\Temp\NJ8QINIJC5MOZY29SDUO30DHFAM.exe" | C:\Users\admin\AppData\Local\Temp\NJ8QINIJC5MOZY29SDUO30DHFAM.exe | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe | ||||||||||||
User: admin Company: Analytical Tool Group Integrity Level: MEDIUM Description: Application for Advise Specification Exit code: 0 Version: 1.11.338.2467 Modules
| |||||||||||||||
| 456 | cmd /c "reg add HKCU\Software\Microsoft\Windows\CurrentVersion\RunOnce /v atkexComSvc /t REG_SZ /d C:\ProgramData\atkexComSvc.exe /f" | C:\Windows\SysWOW64\cmd.exe | — | 9O5P5ZXXXYZCC5SU5SSYT29XDLY1S.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5584 --field-trial-handle=1956,i,11771681620178920924,7663210313225716429,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\XWWMZENYHUINSJ07XV5ZWIIA4.exe" | C:\Users\admin\AppData\Local\Temp\XWWMZENYHUINSJ07XV5ZWIIA4.exe | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe | ||||||||||||
User: admin Company: Analytical Tool Group Integrity Level: MEDIUM Description: Application for Advise Specification Exit code: 0 Version: 1.11.338.2467 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5440 --field-trial-handle=1956,i,11771681620178920924,7663210313225716429,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1760 | "C:\Users\admin\AppData\Local\Temp\O4ENMYAXLWVH97KYONL59KDL97WONN8.exe" | C:\Users\admin\AppData\Local\Temp\O4ENMYAXLWVH97KYONL59KDL97WONN8.exe | — | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: rcc Exit code: 0 Version: 9.54.1.1173 Modules
| |||||||||||||||
| 1804 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5980 --field-trial-handle=1956,i,11771681620178920924,7663210313225716429,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
24 457
Read events
24 381
Write events
55
Delete events
21
Modification events
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.zip | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7648) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7648) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
29
Suspicious files
247
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10e689.TMP | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10e689.TMP | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10e699.TMP | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10e699.TMP | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10e699.TMP | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7648 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
122
DNS requests
87
Threats
80
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7208 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7208 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7584 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7584 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7584 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7584 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7584 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 20.198.162.78:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7648 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7816 | chrome.exe | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (oreheatq .live) |
2196 | svchost.exe | A Network Trojan was detected | STEALER [ANY.RUN] Domain has been identified as part of Lumma Stealer's infrastructure (castmaxw .run) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (castmaxw .run) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (steelixr .live) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (weldorae .digital) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (oreheatq .live) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (advennture .top) |
7752 | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (advennture .top in TLS SNI) |
7752 | e71f1a3b5fa9efd9c6b2ef512902f852bf3b8e1cf9f395292f01d72753173062.exe | Domain Observed Used for C2 Detected | ET MALWARE Observed Win32/Lumma Stealer Related Domain (advennture .top in TLS SNI) |