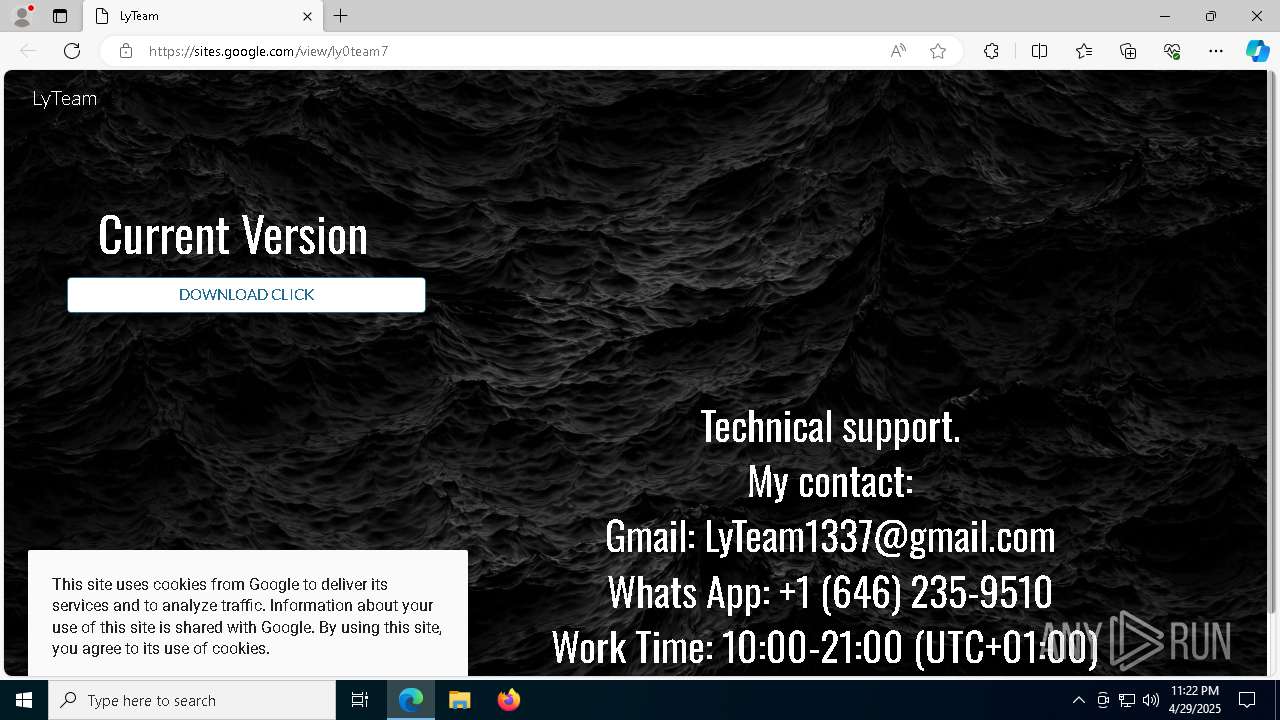
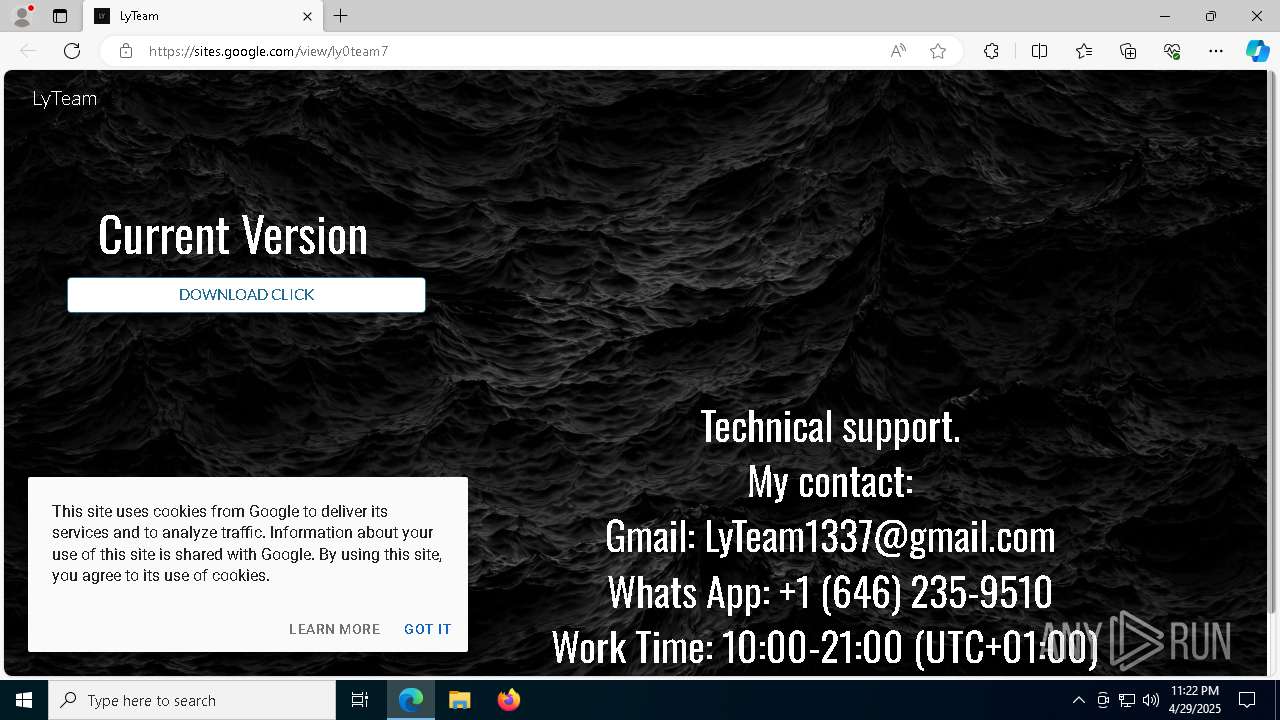
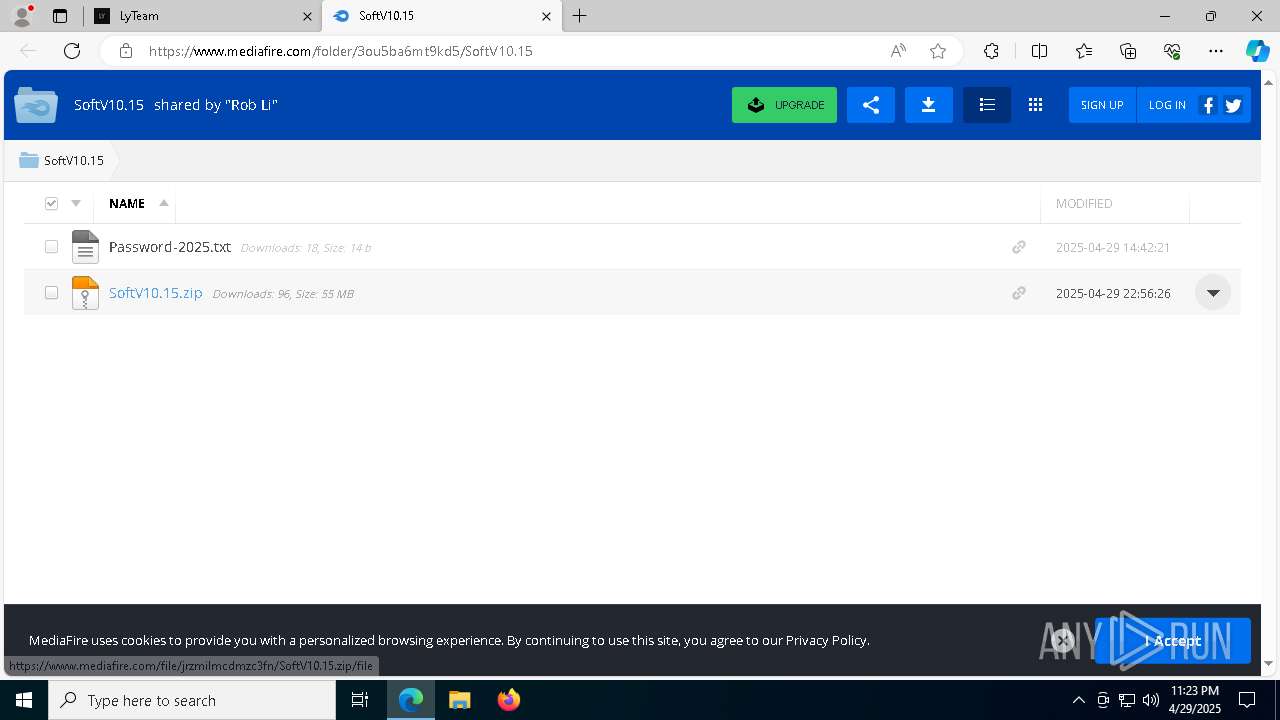
| URL: | https://sites.google.com/view/ly0team7 |
| Full analysis: | https://app.any.run/tasks/22e8154d-6bcd-47ed-b4c0-cfabfd7570c6 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | April 29, 2025, 23:22:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
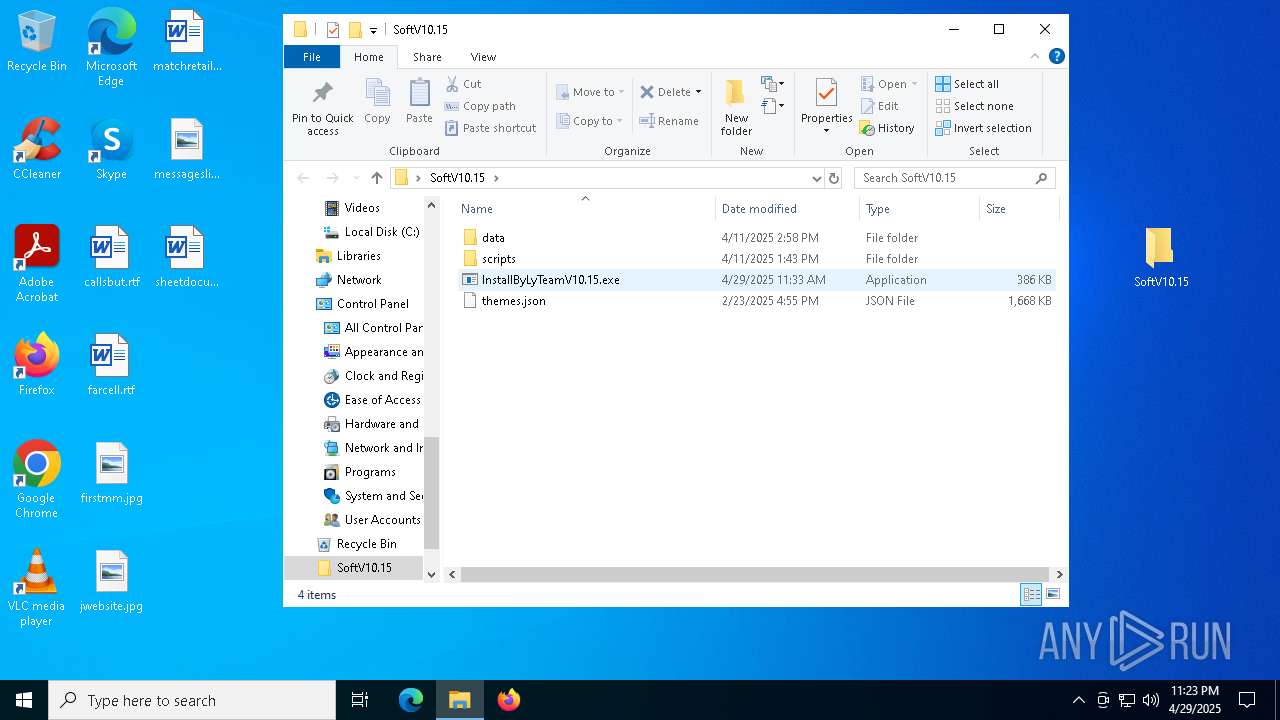
| MD5: | 54BB8EC9863A9C46F06A95BAFEC36B58 |
| SHA1: | B43F7B51BCDFFB2E847BF5AA39EBC1643373AB6E |
| SHA256: | 882A31476AF52216085BBA563FBDCBEB84224F2D398A74E52D45CA0262E58F35 |
| SSDEEP: | 3:N8BhLJ3u1yzIS:2J+EkS |
MALICIOUS
Adds path to the Windows Defender exclusion list
- InstallByLyTeamV10.15.exe (PID: 9120)
- cmd.exe (PID: 968)
Changes Windows Defender settings
- cmd.exe (PID: 968)
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
- acdlnvpzkxgi.exe (PID: 7700)
LUMMA has been detected (YARA)
- acdlnvpzkxgi.exe (PID: 7700)
SUSPICIOUS
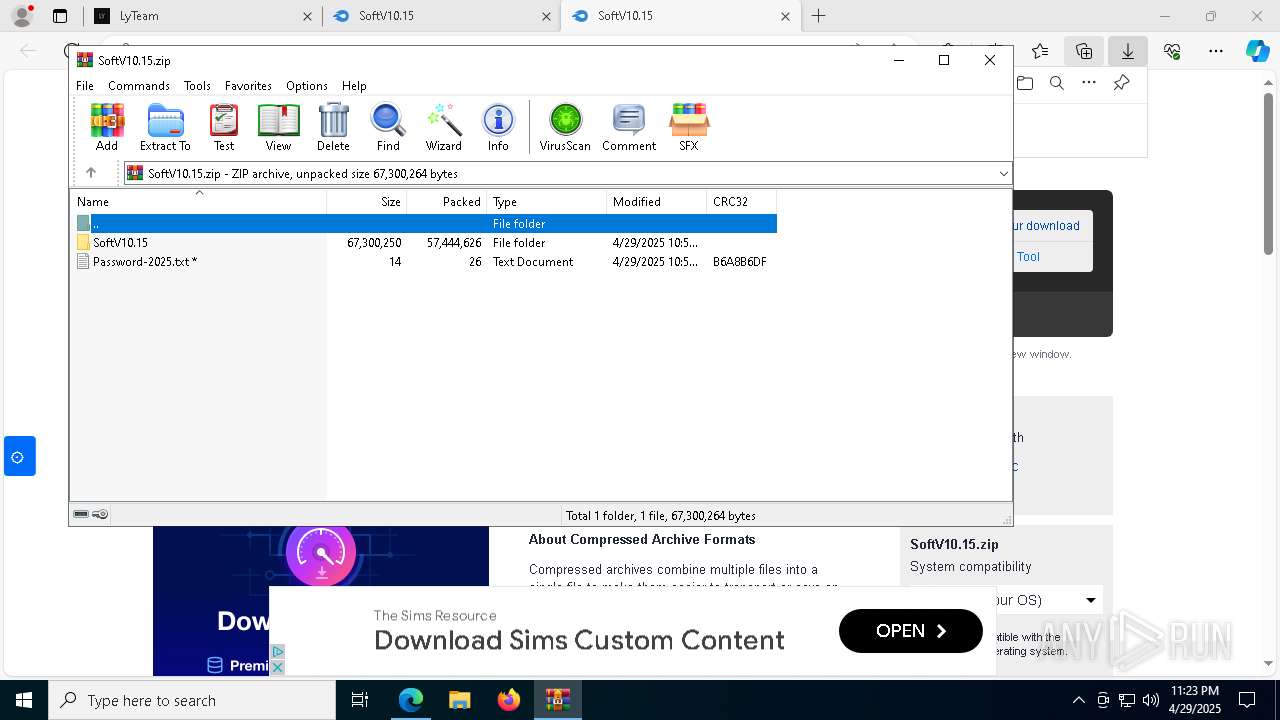
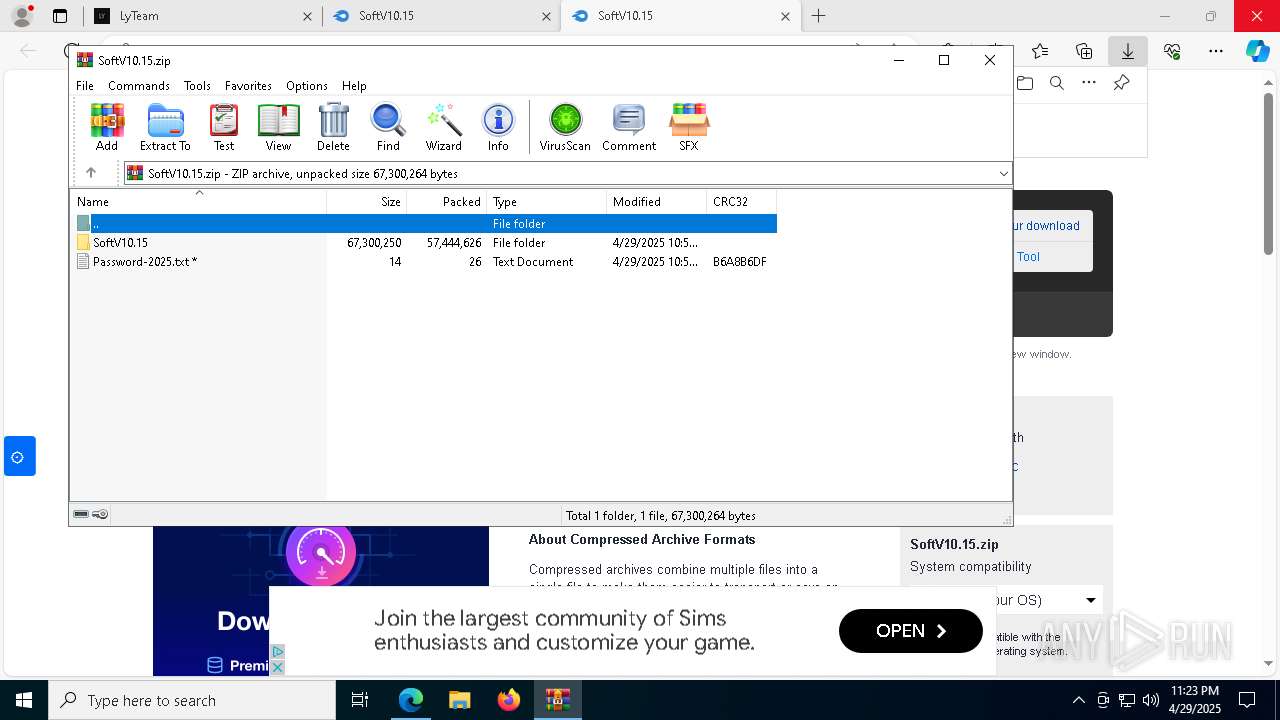
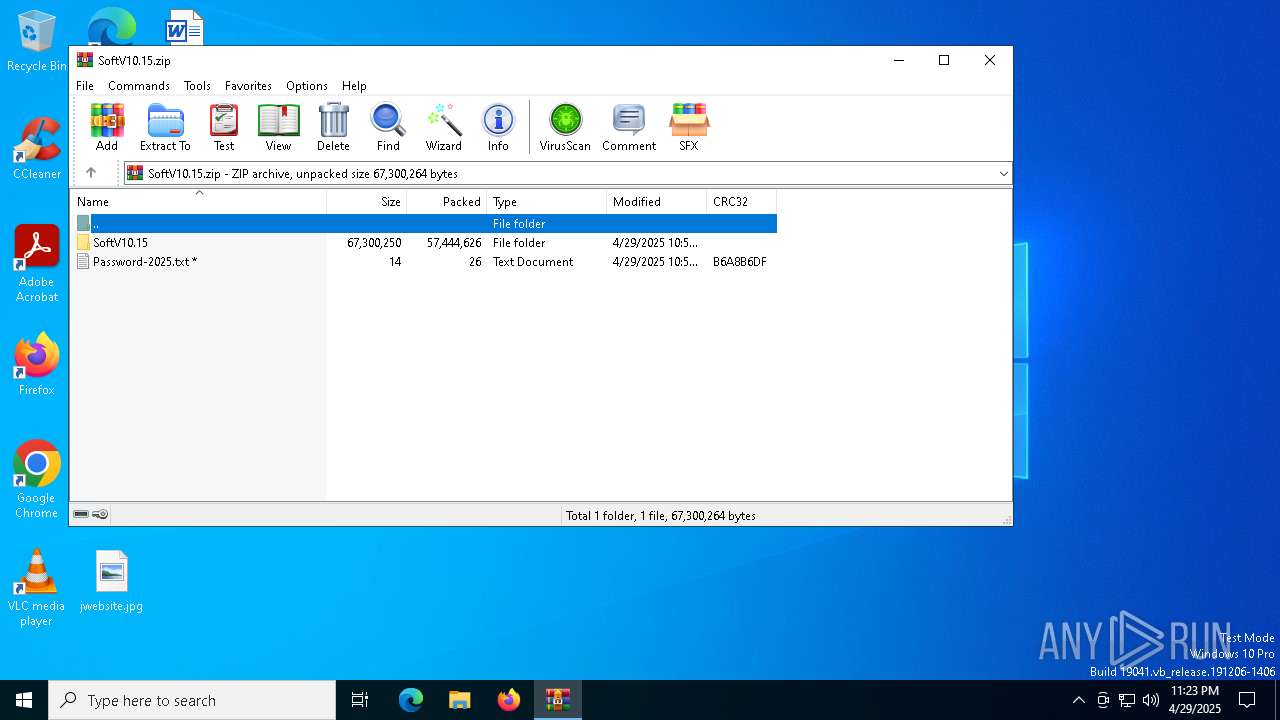
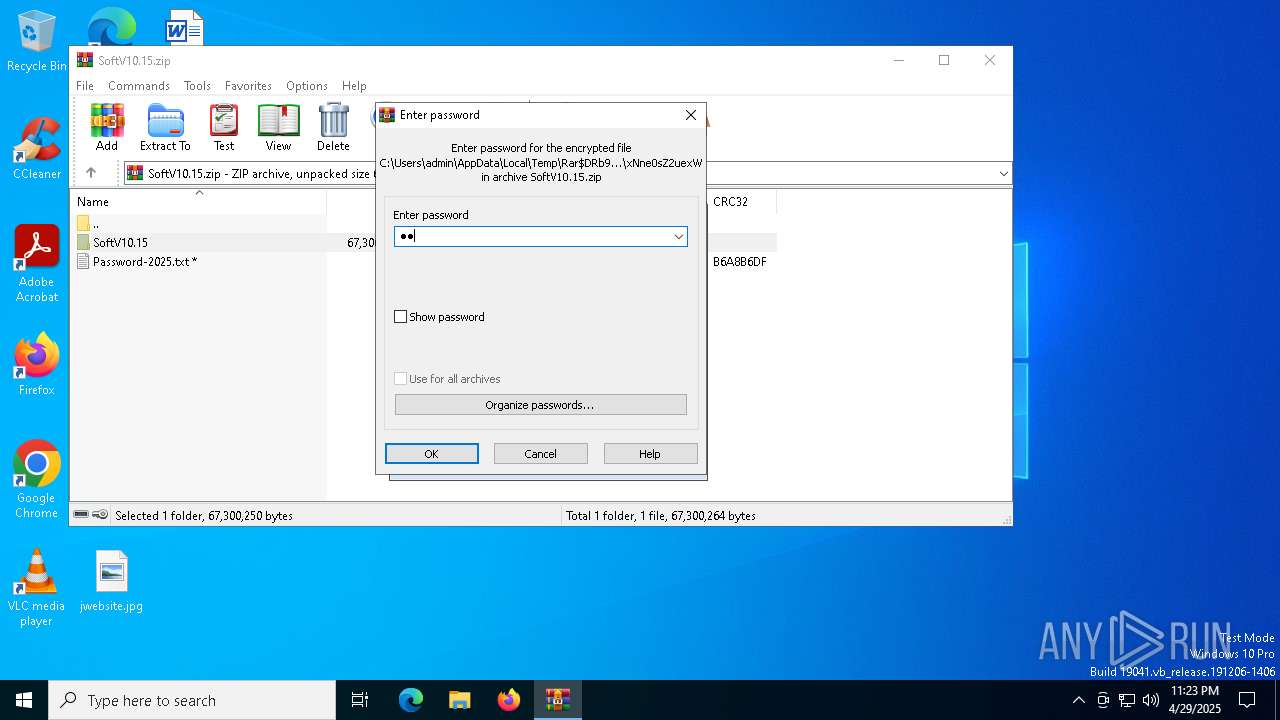
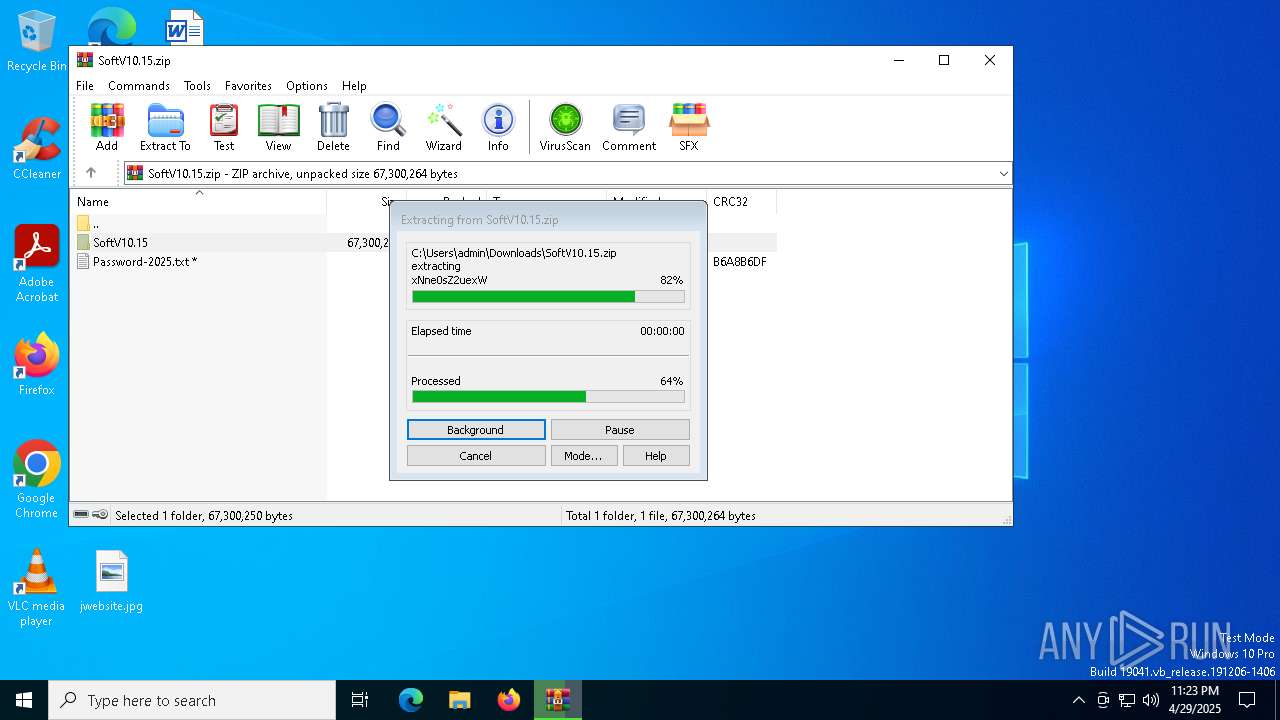
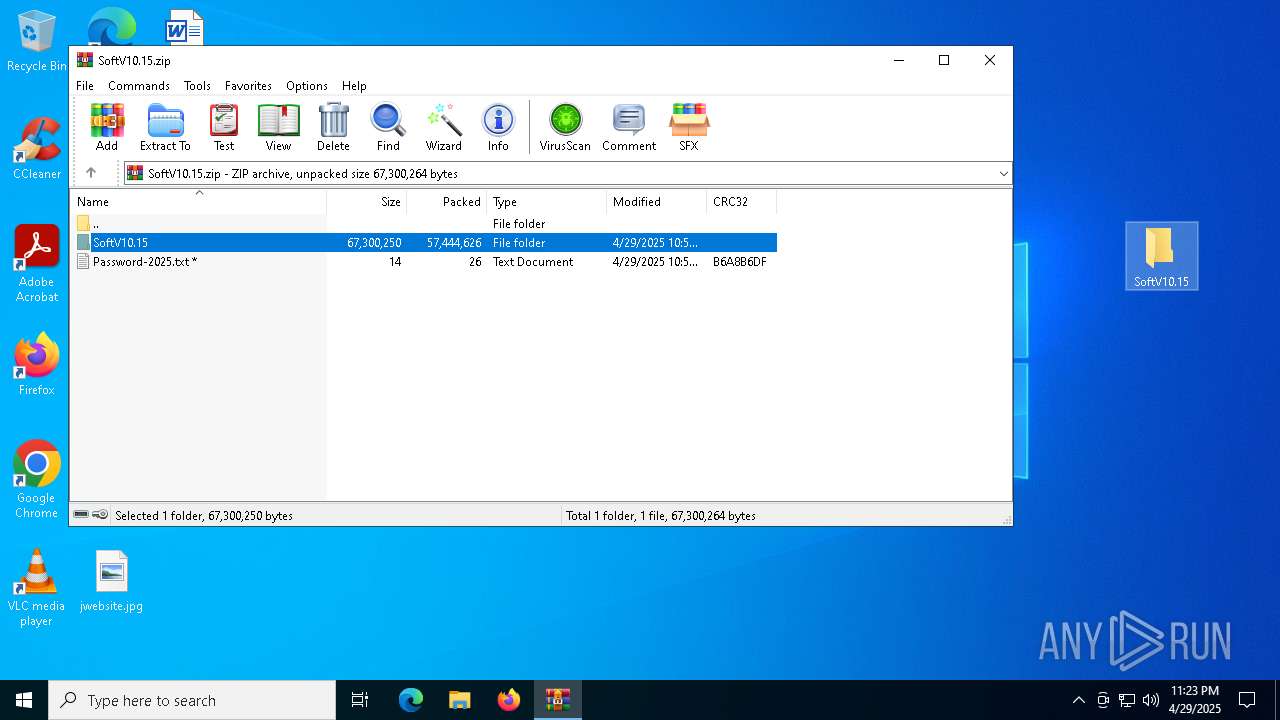
Process drops legitimate windows executable
- WinRAR.exe (PID: 9180)
Reads security settings of Internet Explorer
- InstallByLyTeamV10.15.exe (PID: 7824)
Reads the date of Windows installation
- InstallByLyTeamV10.15.exe (PID: 7824)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 968)
- cmd.exe (PID: 8104)
Starts CMD.EXE for commands execution
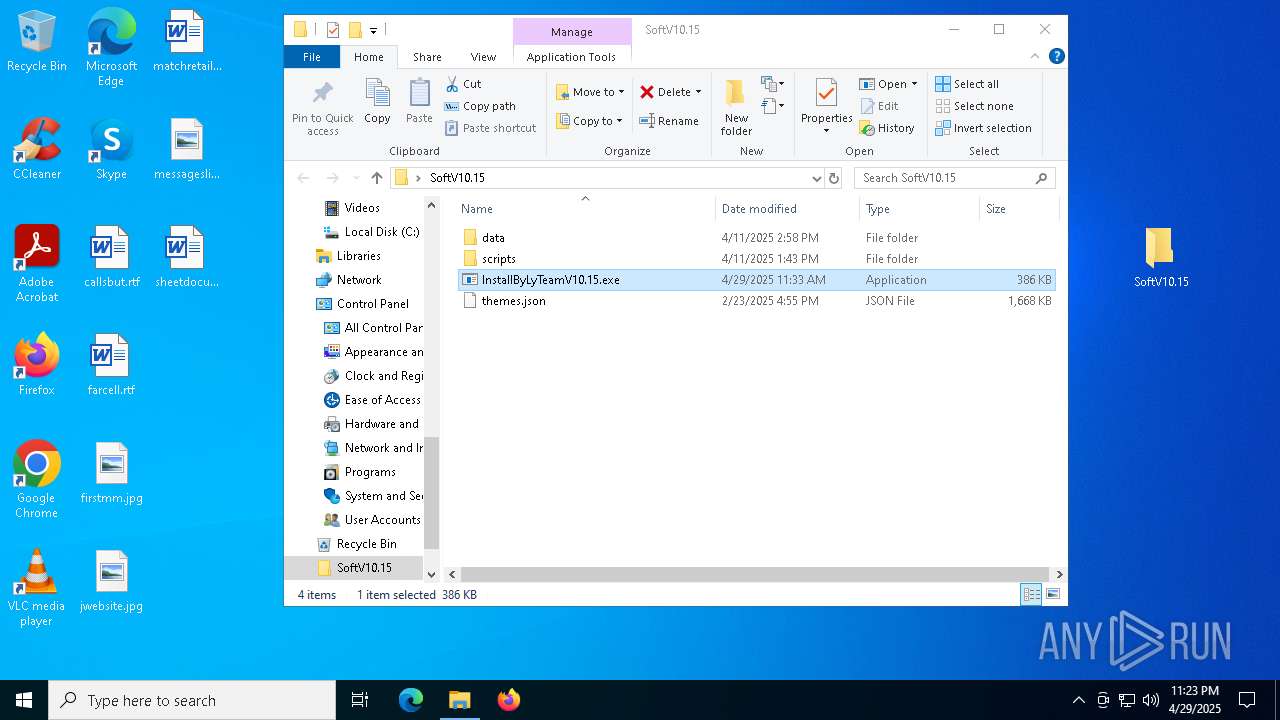
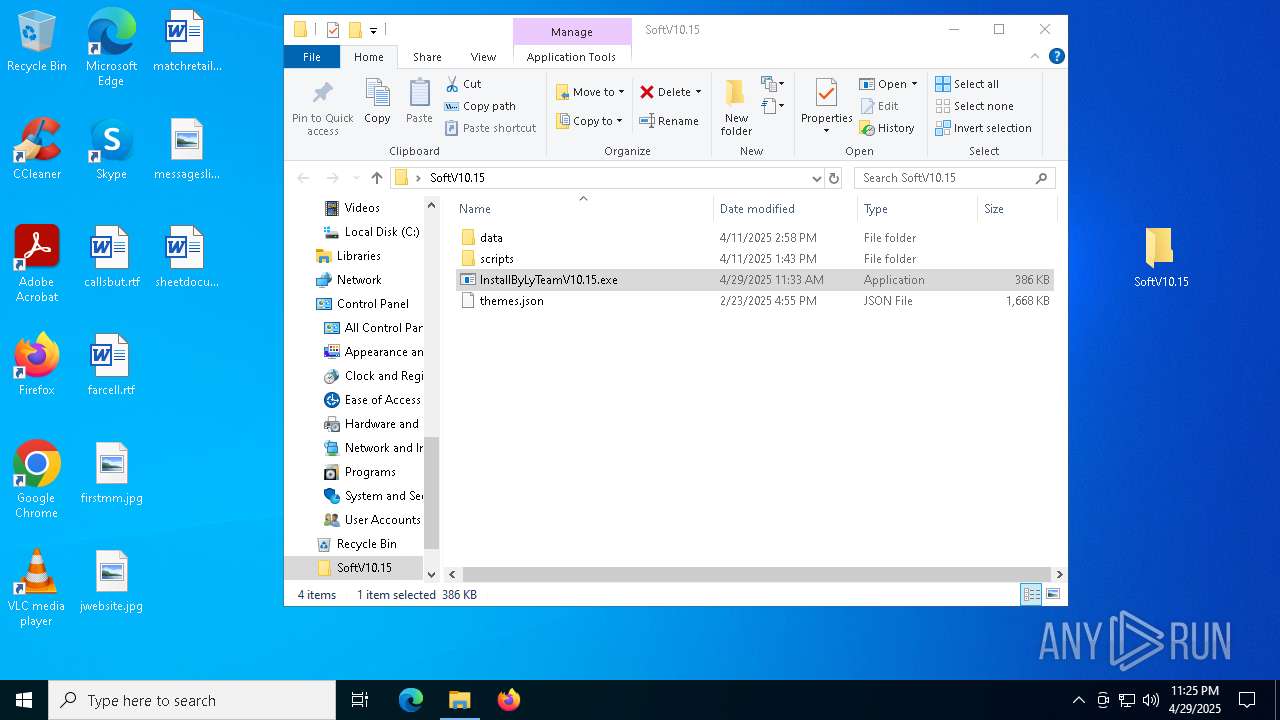
- InstallByLyTeamV10.15.exe (PID: 9120)
Application launched itself
- InstallByLyTeamV10.15.exe (PID: 7824)
Executable content was dropped or overwritten
- powershell.exe (PID: 8088)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 968)
Downloads file from URI via Powershell
- powershell.exe (PID: 8088)
Contacting a server suspected of hosting an CnC
- acdlnvpzkxgi.exe (PID: 7700)
- svchost.exe (PID: 2196)
There is functionality for taking screenshot (YARA)
- acdlnvpzkxgi.exe (PID: 7700)
There is functionality for VM detection VirtualBox (YARA)
- acdlnvpzkxgi.exe (PID: 7700)
INFO
Application launched itself
- msedge.exe (PID: 6964)
- msedge.exe (PID: 900)
Checks supported languages
- identity_helper.exe (PID: 6640)
- identity_helper.exe (PID: 2316)
- InstallByLyTeamV10.15.exe (PID: 7824)
- InstallByLyTeamV10.15.exe (PID: 9120)
Reads Environment values
- identity_helper.exe (PID: 6640)
- identity_helper.exe (PID: 2316)
Reads the computer name
- identity_helper.exe (PID: 6640)
- identity_helper.exe (PID: 2316)
- InstallByLyTeamV10.15.exe (PID: 7824)
- InstallByLyTeamV10.15.exe (PID: 9120)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6964)
The sample compiled with english language support
- WinRAR.exe (PID: 9180)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 9180)
The sample compiled with chinese language support
- WinRAR.exe (PID: 9180)
Reads the software policy settings
- slui.exe (PID: 1280)
Manual execution by a user
- InstallByLyTeamV10.15.exe (PID: 7824)
Process checks computer location settings
- InstallByLyTeamV10.15.exe (PID: 7824)
Enigma protector has been detected
- acdlnvpzkxgi.exe (PID: 7700)
Compiled with Borland Delphi (YARA)
- acdlnvpzkxgi.exe (PID: 7700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Lumma
(PID) Process(7700) acdlnvpzkxgi.exe
C2 (9)woodpeckersd.run/glsk
mobitront.run/dsiu
parakehjet.run/kewk
buzzarddf.live/ktnt
bearjk.live/benj
biosphxere.digital/tqoa
fishgh.digital/tequ
geographys.run/eirq
tropiscbs.live/iuwxx
Total processes
232
Monitored processes
97
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://sites.google.com/view/ly0team7" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=7680 --field-trial-handle=2456,i,17869321412464266598,7448167931706052261,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --mojo-platform-channel-handle=6444 --field-trial-handle=2456,i,17869321412464266598,7448167931706052261,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 904 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\pxewo', 'C:\Users', 'C:\ProgramData'" | C:\Windows\System32\cmd.exe | — | InstallByLyTeamV10.15.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1452 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=4404 --field-trial-handle=2456,i,17869321412464266598,7448167931706052261,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2268 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=6740 --field-trial-handle=2456,i,17869321412464266598,7448167931706052261,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
24 472
Read events
24 405
Write events
67
Delete events
0
Modification events
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 6D597A5C89922F00 | |||
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4740835C89922F00 | |||
| (PID) Process: | (6964) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328322 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {564AE180-D5EF-4349-BFEC-C9DB9DE0A751} | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
44
Suspicious files
734
Text files
137
Unknown types
2
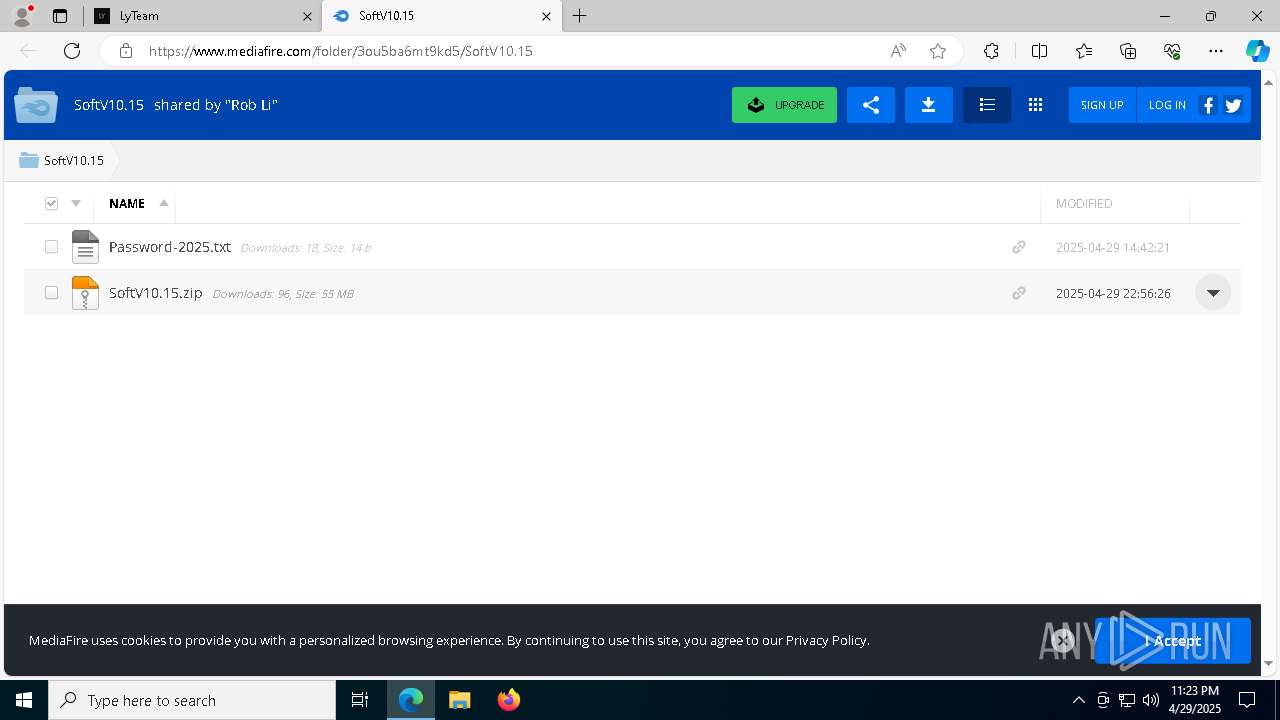
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb72.TMP | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb72.TMP | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb82.TMP | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb82.TMP | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb91.TMP | — | |
MD5:— | SHA256:— | |||
| 6964 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
328
DNS requests
414
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8404 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8404 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2108 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/af75b733-61f6-4fcf-8619-ad77279cd51e?P1=1746463354&P2=404&P3=2&P4=Krb95W0Yude9W%2bQCeyGHHjha2yCWVJ9%2fDvDO%2bAql8zC3%2fIN3o7hshvY9Gn9%2fzDQsGz84nba0ldtu8FYKi3Ypjg%3d%3d | unknown | — | — | whitelisted |
2108 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/af75b733-61f6-4fcf-8619-ad77279cd51e?P1=1746463354&P2=404&P3=2&P4=Krb95W0Yude9W%2bQCeyGHHjha2yCWVJ9%2fDvDO%2bAql8zC3%2fIN3o7hshvY9Gn9%2fzDQsGz84nba0ldtu8FYKi3Ypjg%3d%3d | unknown | — | — | whitelisted |
2108 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/af75b733-61f6-4fcf-8619-ad77279cd51e?P1=1746463354&P2=404&P3=2&P4=Krb95W0Yude9W%2bQCeyGHHjha2yCWVJ9%2fDvDO%2bAql8zC3%2fIN3o7hshvY9Gn9%2fzDQsGz84nba0ldtu8FYKi3Ypjg%3d%3d | unknown | — | — | whitelisted |
2108 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/af75b733-61f6-4fcf-8619-ad77279cd51e?P1=1746463354&P2=404&P3=2&P4=Krb95W0Yude9W%2bQCeyGHHjha2yCWVJ9%2fDvDO%2bAql8zC3%2fIN3o7hshvY9Gn9%2fzDQsGz84nba0ldtu8FYKi3Ypjg%3d%3d | unknown | — | — | whitelisted |
2108 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/af75b733-61f6-4fcf-8619-ad77279cd51e?P1=1746463354&P2=404&P3=2&P4=Krb95W0Yude9W%2bQCeyGHHjha2yCWVJ9%2fDvDO%2bAql8zC3%2fIN3o7hshvY9Gn9%2fzDQsGz84nba0ldtu8FYKi3Ypjg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7260 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6964 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7260 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7260 | msedge.exe | 142.250.186.78:443 | sites.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
sites.google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
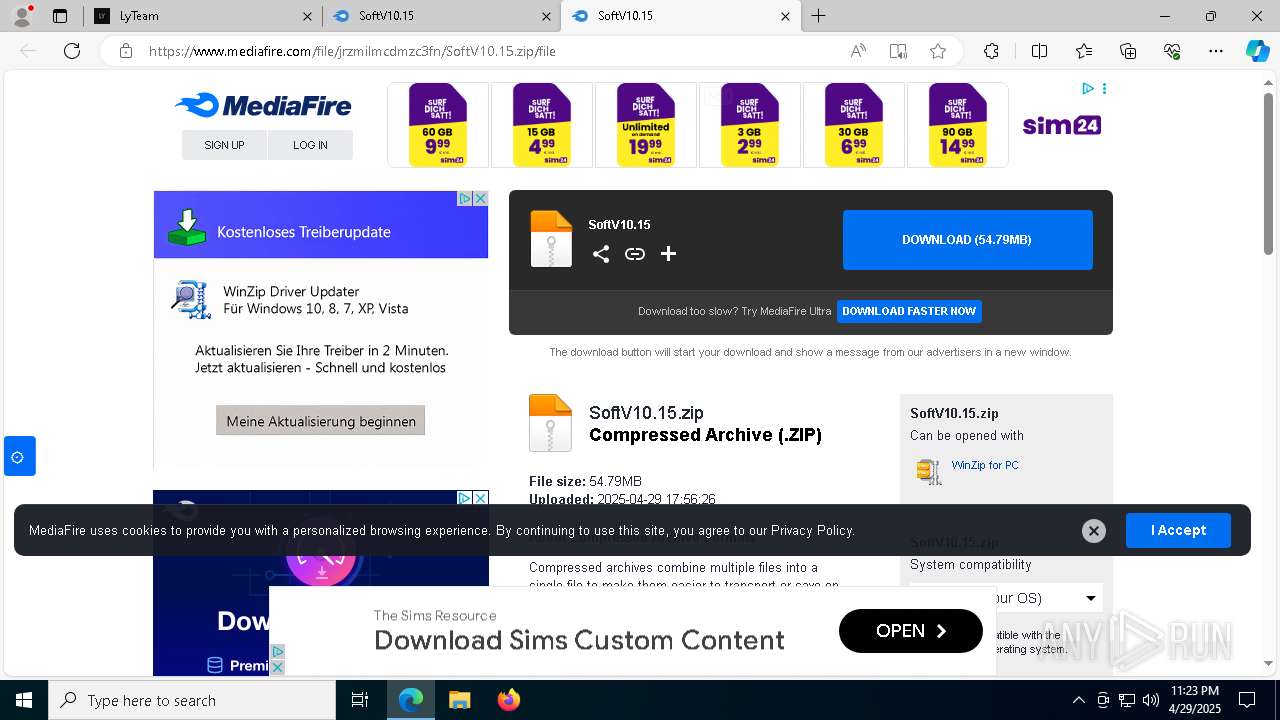
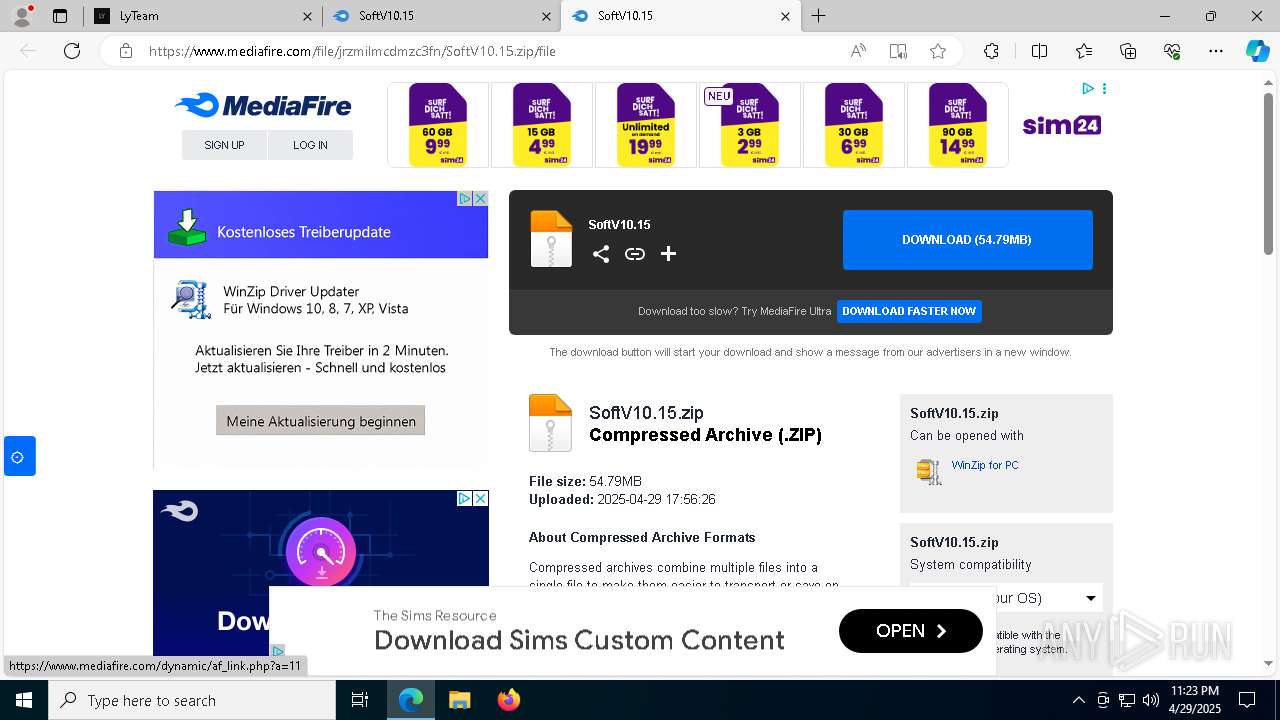
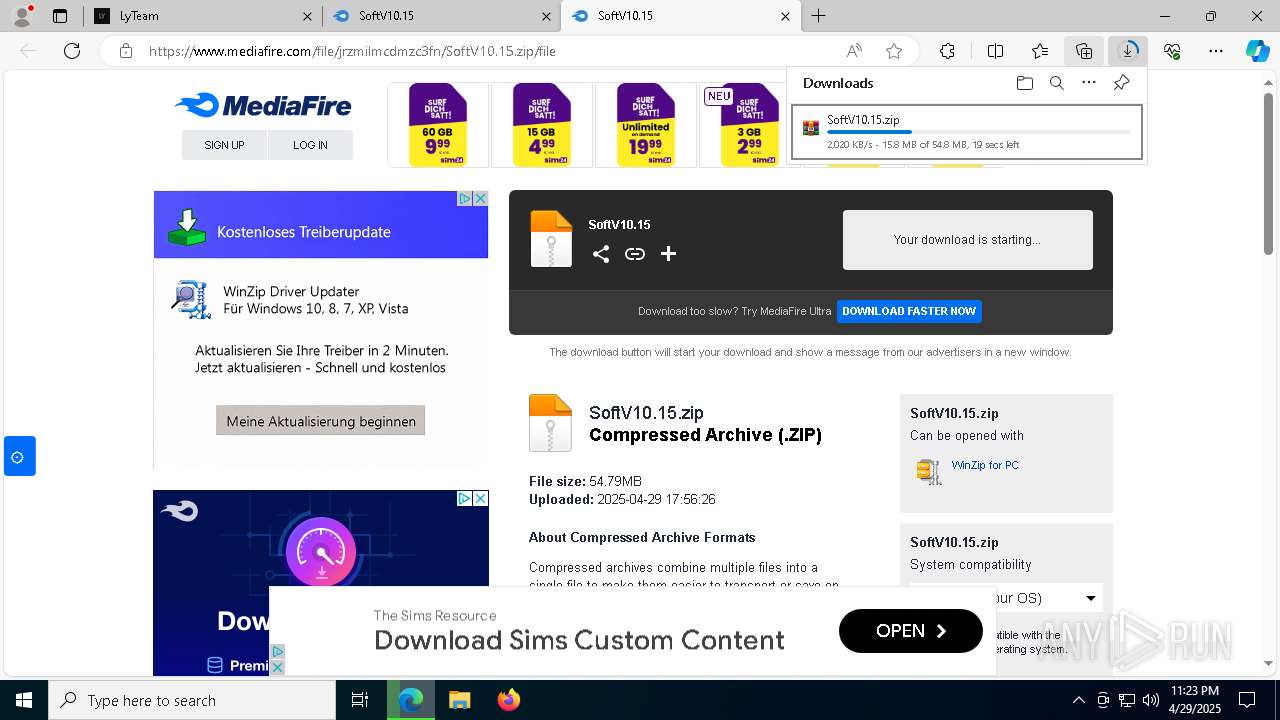
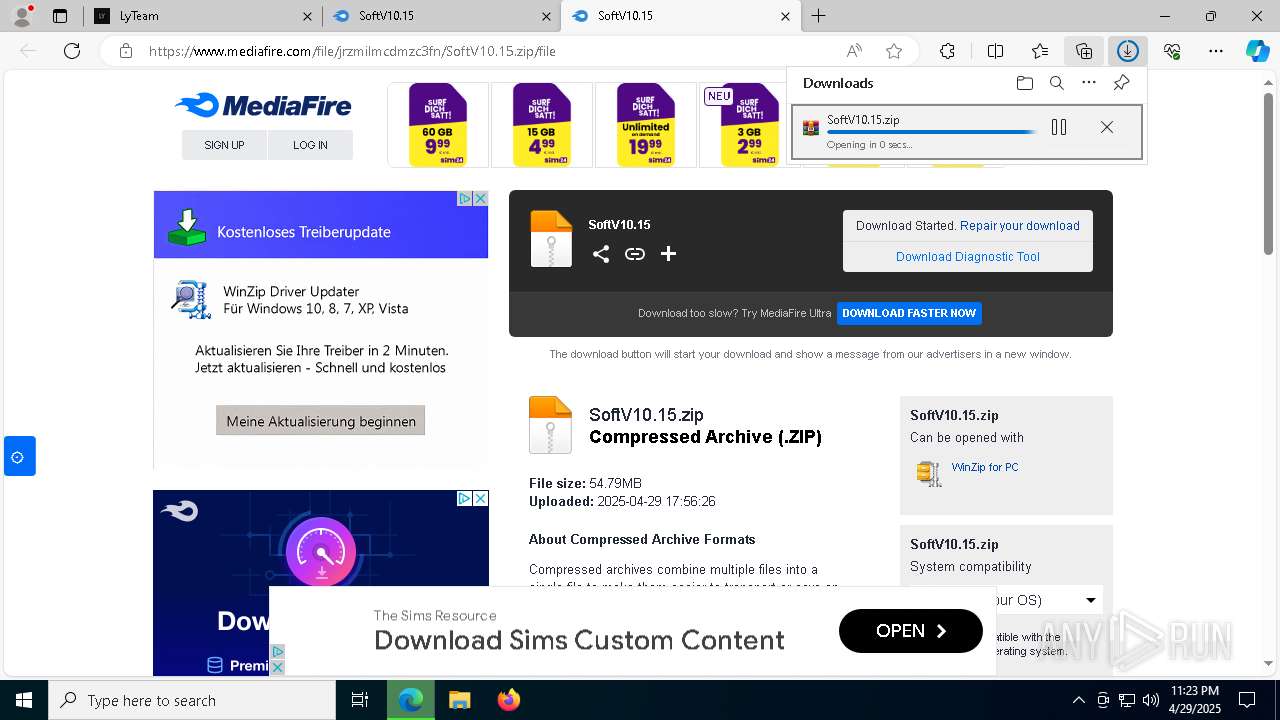
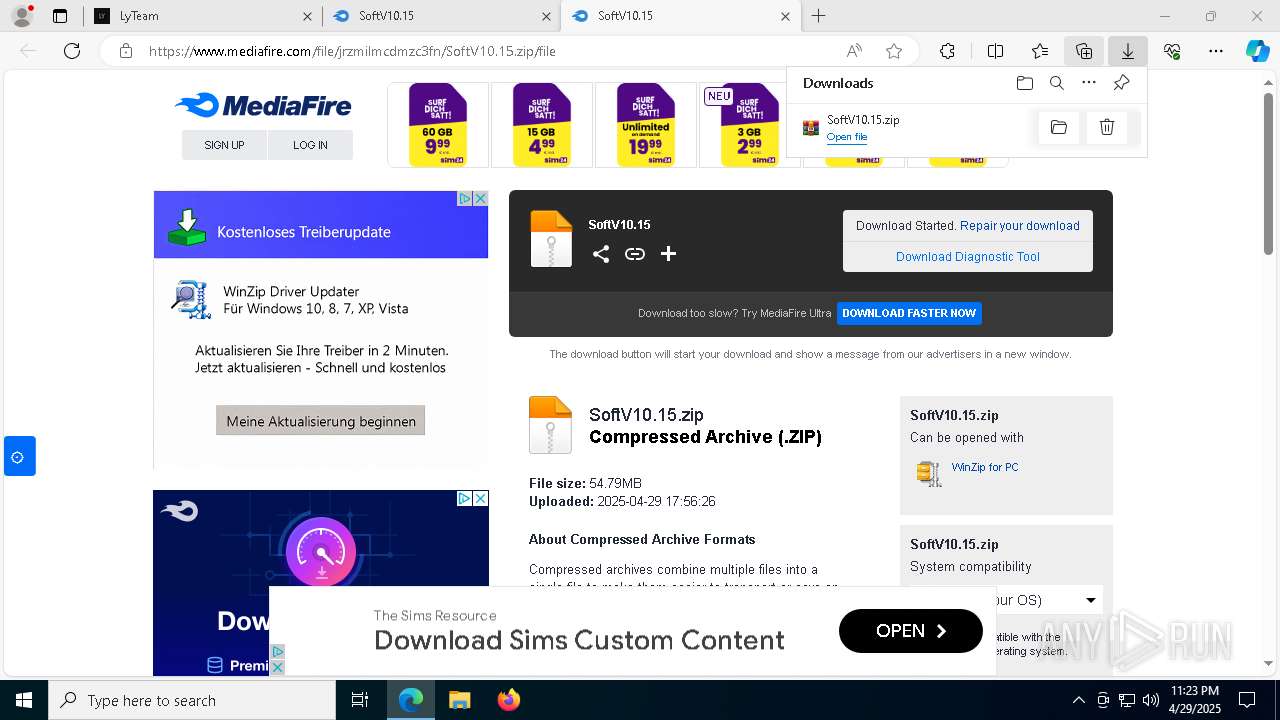
7260 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7260 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7260 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7260 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7260 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |