| File name: | 87a5c4a72db0365f8b6999f3752f9e485cc0968367488d847a04c551bdc65770.msi |
| Full analysis: | https://app.any.run/tasks/7cb28b68-03d4-485c-91cc-12fbb7dab186 |
| Verdict: | Malicious activity |
| Threats: | Gh0st RAT is a malware with advanced trojan functionality that enables attackers to establish full control over the victim’s system. The spying capabilities of Gh0st RAT made it a go-to tool for numerous criminal groups in high-profile attacks against government and corporate organizations. The most common vector of attack involving this malware begins with spam and phishing emails. |
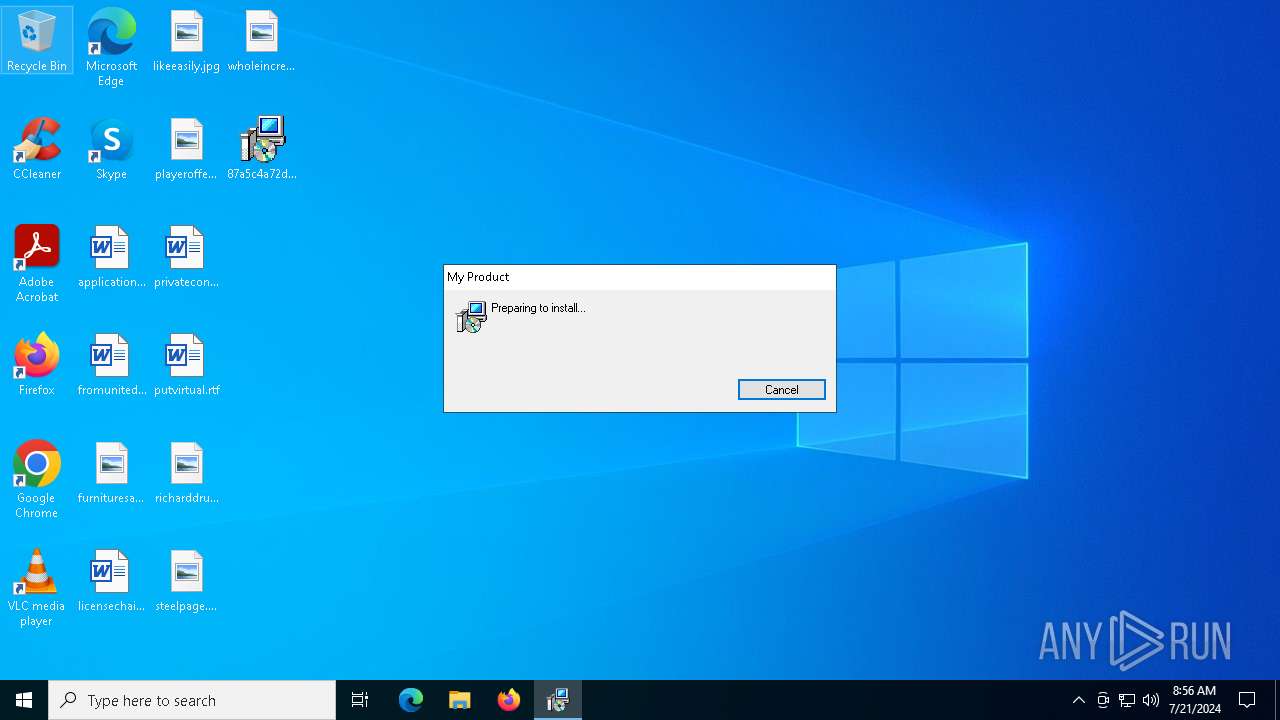
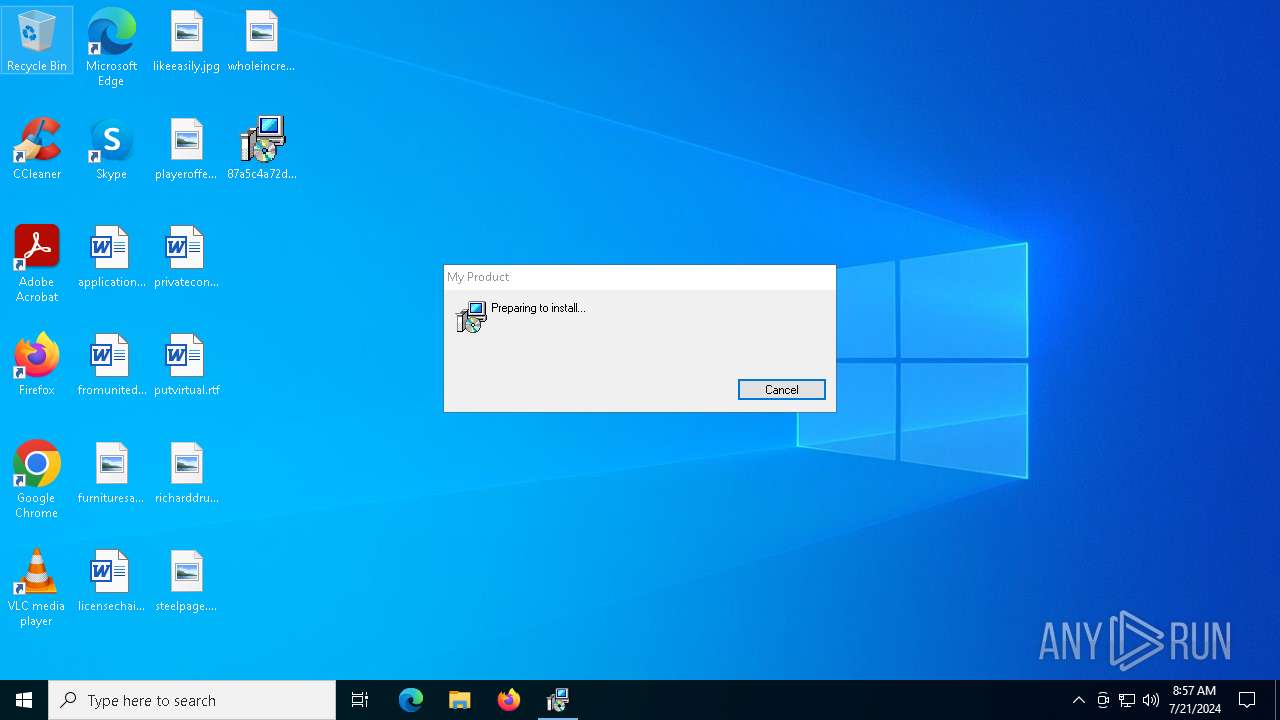
| Analysis date: | July 21, 2024, 08:56:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Code page: 936, Title: Installation Database, Subject: My Product Installer, Author: My Company, Keywords: Installer, Comments: Package Comments, Template: x64;0, Revision Number: {89C20E63-A82C-4033-B557-4079D717B484}, Create Time/Date: Fri Jul 19 17:26:32 2024, Last Saved Time/Date: Fri Jul 19 17:26:32 2024, Number of Pages: 500, Number of Words: 10, Name of Creating Application: Windows Installer XML Toolset (3.9.1208.0), Security: 2 |
| MD5: | AEE434CCFA9AAB767C1B275F48C8246C |
| SHA1: | 250C1FF726C88B0D5F4EB0C3516A79CC5B81380F |
| SHA256: | 87A5C4A72DB0365F8B6999F3752F9E485CC0968367488D847A04C551BDC65770 |
| SSDEEP: | 98304:u8ISUyo3C6213mQOkCbKoHvGrPGF/YoNVcm6GKEaLxLf0RT1Q3TTycMp2xP1U+Hz:Udi7T0MzzW |
MALICIOUS
Drops the executable file immediately after the start
- msiexec.exe (PID: 1032)
- msiexec.exe (PID: 8180)
- un.exe (PID: 7700)
- msiexec.exe (PID: 6380)
SUSPICIOUS
Reads security settings of Internet Explorer
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 6380)
Executes as Windows Service
- VSSVC.exe (PID: 6976)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8180)
Reads the date of Windows installation
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 6380)
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 116)
- cmd.exe (PID: 4000)
- msiexec.exe (PID: 6380)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 6280)
Application launched itself
- cmd.exe (PID: 4000)
- powershell.exe (PID: 6280)
- powershell.exe (PID: 7556)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8036)
- cmd.exe (PID: 4000)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3628)
Uses WMIC.EXE to obtain data on processes
- cmd.exe (PID: 3628)
Runs shell command (SCRIPT)
- mshta.exe (PID: 1652)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6380)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 6280)
Suspicious use of asymmetric encryption in PowerShell
- msiexec.exe (PID: 6380)
Executable content was dropped or overwritten
- un.exe (PID: 7700)
Creates file in the systems drive root
- powershell.exe (PID: 6280)
- powershell.exe (PID: 7556)
- cmd.exe (PID: 6776)
- cmd.exe (PID: 4000)
- msiexec.exe (PID: 6380)
Reads the BIOS version
- iusb3mon.exe (PID: 7288)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 6280)
- powershell.exe (PID: 7556)
Base64-obfuscated command line is found
- powershell.exe (PID: 6280)
- powershell.exe (PID: 7556)
INFO
Checks supported languages
- msiexec.exe (PID: 8180)
- msiexec.exe (PID: 116)
- un.exe (PID: 7700)
- msiexec.exe (PID: 6380)
- un.exe (PID: 3128)
- iusb3mon.exe (PID: 7288)
Reads the computer name
- msiexec.exe (PID: 8180)
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 6380)
Process checks computer location settings
- msiexec.exe (PID: 116)
- msiexec.exe (PID: 6380)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8180)
- msiexec.exe (PID: 6380)
Create files in a temporary directory
- msiexec.exe (PID: 1032)
- SecEdit.exe (PID: 6384)
- SecEdit.exe (PID: 7336)
- SecEdit.exe (PID: 6108)
Reads Internet Explorer settings
- mshta.exe (PID: 1652)
Checks proxy server information
- mshta.exe (PID: 1652)
Creates a software uninstall entry
- msiexec.exe (PID: 8180)
Reads the machine GUID from the registry
- un.exe (PID: 3128)
- un.exe (PID: 7700)
Creates files in the program directory
- un.exe (PID: 7700)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 1484)
Reads CPU info
- powershell.exe (PID: 6280)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6204)
- powershell.exe (PID: 7676)
- powershell.exe (PID: 8124)
- powershell.exe (PID: 7104)
- powershell.exe (PID: 3412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
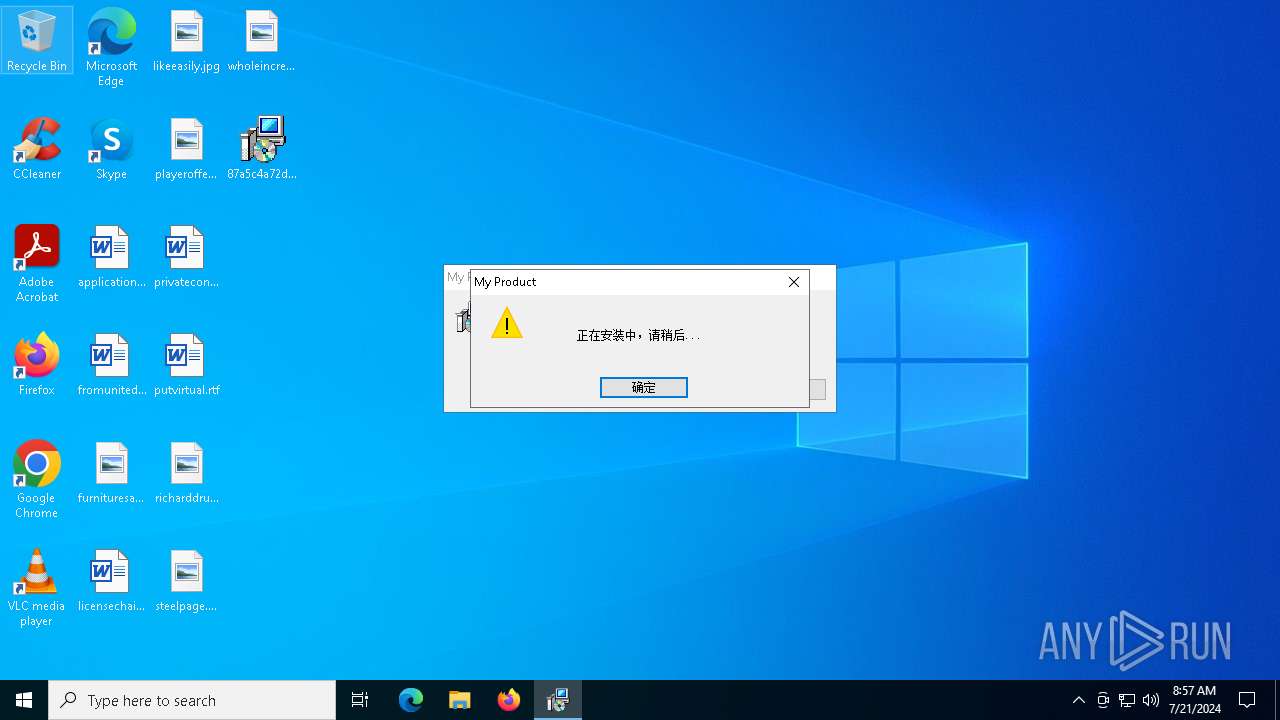
| CodePage: | Windows Simplified Chinese (PRC, Singapore) |
|---|---|
| Title: | Installation Database |
| Subject: | My Product Installer |
| Author: | My Company |
| Keywords: | Installer |
| Comments: | Package Comments |
| Template: | x64;0 |
| RevisionNumber: | {89C20E63-A82C-4033-B557-4079D717B484} |
| CreateDate: | 2024:07:19 17:26:32 |
| ModifyDate: | 2024:07:19 17:26:32 |
| Pages: | 500 |
| Words: | 10 |
| Software: | Windows Installer XML Toolset (3.9.1208.0) |
| Security: | Read-only recommended |
Total processes
191
Monitored processes
50
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | C:\Windows\syswow64\MsiExec.exe -Embedding CC3301E9F1DF11D88D36C60E4B6EA9CB | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 912 | findstr "=" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1032 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\87a5c4a72db0365f8b6999f3752f9e485cc0968367488d847a04c551bdc65770.msi | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | un.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | wmic process where "Name='msiexec.exe' AND CommandLine LIKE '%/i %.msi%'" get ProcessId /value | C:\Windows\SysWOW64\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1652 | "C:\Windows\SysWOW64\mshta.exe" vbscript:CreateObject("Shell.Application").ShellExecute("msiexec.exe","/package ""C:\Users\admin\Desktop\87a5c4a72db0365f8b6999f3752f9e485cc0968367488d847a04c551bdc65770.msi""","","runas",1)(window.close) | C:\Windows\SysWOW64\mshta.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | taskkill /f /im powershell.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2204 | "C:\Windows\SysWOW64\cmd.exe" /c "fltmc.exe && exit 0||exit 1" | C:\Windows\SysWOW64\cmd.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
52 070
Read events
51 561
Write events
471
Delete events
38
Modification events
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000001B2BC4EF4BDBDA01F41F000060180000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000004E8EC6EF4BDBDA01F41F000060180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 48000000000000008E080EF04BDBDA01F41F000060180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 48000000000000008E080EF04BDBDA01F41F000060180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000009B6C10F04BDBDA01F41F000060180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000843315F04BDBDA01F41F000060180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000F85279F04BDBDA01F41F000060180000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8180) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000009BB77BF04BDBDA01F41F0000FC0B0000E803000001000000000000000000000052D42CC25A4C084B958F763EFA7DADBD00000000000000000000000000000000 | |||
| (PID) Process: | (6976) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000151C7EF04BDBDA01401B0000CC080000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
24
Text files
21
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8180 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 8180 | msiexec.exe | C:\WINDOWS\Installer\42cc76.msi | — | |
MD5:— | SHA256:— | |||
| 8180 | msiexec.exe | C:\WINDOWS\Installer\42cc77.msi | — | |
MD5:— | SHA256:— | |||
| 8180 | msiexec.exe | C:\ProgramData\Microsoft\EdgeUpdate\Log\log.log | — | |
MD5:— | SHA256:— | |||
| 8180 | msiexec.exe | C:\WINDOWS\Installer\42cc79.msi | — | |
MD5:— | SHA256:— | |||
| 8180 | msiexec.exe | C:\WINDOWS\Installer\MSICCE4.tmp | executable | |
MD5:B9FF2DD6924711531E59E90581CDA548 | SHA256:AD564D4D64BB74EA6819E081534131F6F78E3C019D37ABBC3EEF8E09DFED96D7 | |||
| 8180 | msiexec.exe | C:\WINDOWS\Installer\MSIEBC7.tmp | executable | |
MD5:B9FF2DD6924711531E59E90581CDA548 | SHA256:AD564D4D64BB74EA6819E081534131F6F78E3C019D37ABBC3EEF8E09DFED96D7 | |||
| 8180 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{c22cd452-4c5a-4b08-958f-763efa7dadbd}_OnDiskSnapshotProp | binary | |
MD5:3F9A7654773007A55BED38C829D8977E | SHA256:F2B7B732CCB82026007786009CBC3A33DE4688831E83A9A1138E0C743118EF8A | |||
| 8180 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{f5d8a1af-4d49-41ea-8099-8454d00738f8}_OnDiskSnapshotProp | binary | |
MD5:378B9776AB2D9252327A4DDFA9F91854 | SHA256:C3DB40D62DE48F781F12B28D8D4228093AF4C2E22C866E89B9B373AB167B2B94 | |||
| 8180 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:3F9A7654773007A55BED38C829D8977E | SHA256:F2B7B732CCB82026007786009CBC3A33DE4688831E83A9A1138E0C743118EF8A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
49
DNS requests
14
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 304 | 40.68.123.157:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | unknown |
— | — | GET | 200 | 40.68.123.157:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | unknown |
— | — | GET | 304 | 40.68.123.157:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 304 | 40.68.123.157:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | POST | 500 | 20.83.72.98:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | unknown |
— | — | GET | 200 | 184.86.251.28:443 | https://www.bing.com/client/config?cc=US&setlang=en-US | unknown | binary | 2.15 Kb | unknown |
— | — | POST | 403 | 95.101.149.131:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | — | — | unknown |
— | — | POST | 403 | 95.101.149.131:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | — | — | unknown |
— | — | POST | 403 | 95.101.149.131:443 | https://go.microsoft.com/fwlink/?LinkID=2257403&clcid=0x409 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4716 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5620 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7856 | svchost.exe | 4.208.221.206:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4032 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2760 | svchost.exe | 40.115.3.253:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7552 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
1888 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
arc.msn.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1 ETPRO signatures available at the full report