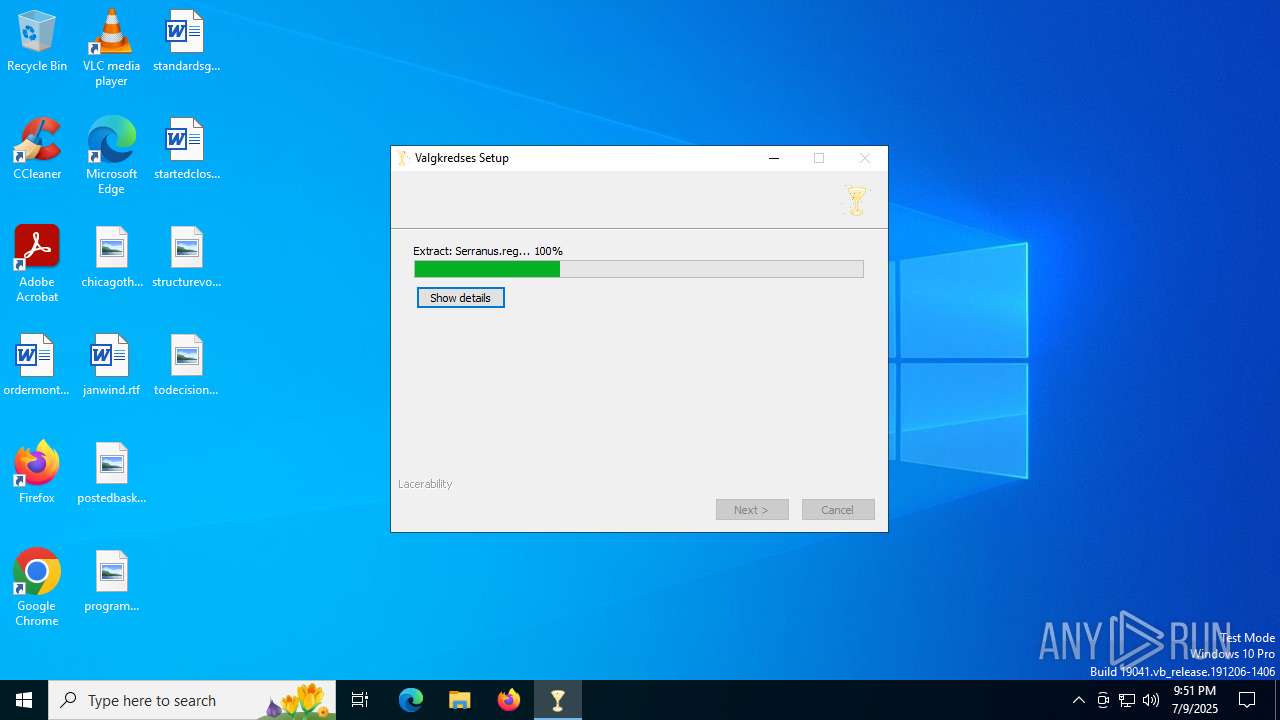
| File name: | JUSTIFICANTE DE TRANSFERENCIA (2).exe |
| Full analysis: | https://app.any.run/tasks/9ba19faf-15d3-4f88-8642-463c47a503ed |
| Verdict: | Malicious activity |
| Threats: | GuLoader is an advanced downloader written in shellcode. It’s used by criminals to distribute other malware, notably trojans, on a large scale. It’s infamous for using anti-detection and anti-analysis capabilities. |
| Analysis date: | July 09, 2025, 21:51:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | AB8D3CBD92150ABFE8CED43C3E2E0193 |
| SHA1: | AF321CBCBE5D023E29927D2C4D05388FA6C310D0 |
| SHA256: | 8775F00228258CF84876FDEC13B36945664F8DBE3869CD5F2EBAF40AB7443ED3 |
| SSDEEP: | 49152:CRD1RuS0CP69+IgoqNZDcQD6W0aGiF83rhx7JZPKlI/saPdgi5657EXACbocN7GQ:339vgoqNui6TJJ3rhx7JtK2PPGUG1gLP |
MALICIOUS
Executing a file with an untrusted certificate
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
GULOADER has been detected (YARA)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
GULOADER SHELLCODE has been detected (YARA)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
The process creates files with name similar to system file names
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
Executable content was dropped or overwritten
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
There is functionality for taking screenshot (YARA)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
Reads security settings of Internet Explorer
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
Application launched itself
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
INFO
Reads the computer name
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
The sample compiled with english language support
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
Checks supported languages
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
Reads the machine GUID from the registry
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
Creates files or folders in the user directory
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
Create files in a temporary directory
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 5168)
Reads the software policy settings
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
Checks proxy server information
- JUSTIFICANTE DE TRANSFERENCIA (2).exe (PID: 7064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 02:09:29+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 3803648 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x350f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | frkenklosterets reflectors konditoren |
| FileVersion: | 2.0.0.0 |
| InternalName: | tagselvbordets.exe |
| LegalCopyright: | serviceaftales unlaminated |
| LegalTrademarks: | salaterier thamnophiline |
| OriginalFileName: | tagselvbordets.exe |
| ProductVersion: | 2.0.0.0 |
Total processes
138
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5168 | "C:\Users\admin\AppData\Local\Temp\JUSTIFICANTE DE TRANSFERENCIA (2).exe" | C:\Users\admin\AppData\Local\Temp\JUSTIFICANTE DE TRANSFERENCIA (2).exe | — | explorer.exe | |||||||||||
User: admin Company: frkenklosterets reflectors konditoren Integrity Level: MEDIUM Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 7064 | "C:\Users\admin\AppData\Local\Temp\JUSTIFICANTE DE TRANSFERENCIA (2).exe" | C:\Users\admin\AppData\Local\Temp\JUSTIFICANTE DE TRANSFERENCIA (2).exe | JUSTIFICANTE DE TRANSFERENCIA (2).exe | ||||||||||||
User: admin Company: frkenklosterets reflectors konditoren Integrity Level: MEDIUM Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
1 935
Read events
1 641
Write events
294
Delete events
0
Modification events
| (PID) Process: | (5168) JUSTIFICANTE DE TRANSFERENCIA (2).exe | Key: | HKEY_CURRENT_USER\skrpningers\Uninstall\vesterlaending\forvrredes |
| Operation: | write | Name: | Wanjas |
Value: 1 | |||
| (PID) Process: | (5168) JUSTIFICANTE DE TRANSFERENCIA (2).exe | Key: | HKEY_CURRENT_USER\periculous\Transletter |
| Operation: | write | Name: | ultrasonicated |
Value: c:\Behandlingssystemers\stamtrers\nauseas.bin | |||
| (PID) Process: | (7064) JUSTIFICANTE DE TRANSFERENCIA (2).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7064) JUSTIFICANTE DE TRANSFERENCIA (2).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7064) JUSTIFICANTE DE TRANSFERENCIA (2).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
2
Suspicious files
7
Text files
12
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Fixture\Serranus.reg | — | |
MD5:— | SHA256:— | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Appelsinerne\dinky.kom | — | |
MD5:— | SHA256:— | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Appelsinerne\unoriginals.tee | — | |
MD5:— | SHA256:— | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Appelsinerne\slgtsregister.jpg | image | |
MD5:F9015955B078C0639FCBBA194934B7C2 | SHA256:9FC74766CEE4049359CB023E81DADB475FE7D8F0E11EA07EA842F8E8BB9B6BBB | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Fixture\Geschften97.txt | text | |
MD5:D9CD3E96ACDB19FBDC4BA64DF01DB988 | SHA256:F3ED5FB00C49430B4994391396FCE0D1037CC526CF2240E1DEF5FF39E625684B | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Appelsinerne\gelsemia.ini | text | |
MD5:6DDA840EADD2E5D8EA1F1A4F666157FD | SHA256:C020DFA9A74D6043157D777DAF887D6C606F59C105146BA3BF47FC42D799D605 | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Cafeteriaejeren\Uninferrably.ste | binary | |
MD5:A256162D401A6A02B59D38831B9DFAA2 | SHA256:48B76FC0753507388DAA8A08795D430EBCF5072988C2A442D5EFC24BC634BDE8 | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Fixture\Eksamensfrit.Spi | text | |
MD5:E96B28F16CAAA86B62A3C9DD7FC342EB | SHA256:1B48D7FD5B46510E0F17264AA94B35024597CC58C7992E3D3467360223F561EB | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Fixture\Misliked.jpg | image | |
MD5:A9FAEC81122F49493D7A2F5E196D418D | SHA256:A3CC1F01D9990FFC2A4A575AE4235B1F6180F392AB4FC2310EB5E39A85C42A44 | |||
| 5168 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Templates\Meredeth\indordnet\cylloses\Appelsinerne\dkningsbidragsaktiviteters.jpg | image | |
MD5:3655C78955FB37695E7EC6B7A30F3467 | SHA256:BECF7AF2D2CA872F19018585C0A356C91D70446DEC1BBE81C7B15D029FC789C3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
27
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2552 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7064 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCECdz283NVEpjCi5UeCEUBvs%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7064 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
6124 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7064 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | GET | 200 | 142.250.185.99:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
7064 | JUSTIFICANTE DE TRANSFERENCIA (2).exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/we2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTuMJxAT2trYla0jia%2F5EUSmLrk3QQUdb7Ed66J9kQ3fc%2BxaB8dGuvcNFkCEEjyOcDij0ECCQHn9DSrJo0%3D | unknown | — | — | whitelisted |
6124 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6756 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2552 | svchost.exe | 20.190.135.3:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2552 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
drive.google.com |
| whitelisted |
c.pki.goog |
| whitelisted |
o.pki.goog |
| whitelisted |
drive.usercontent.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |