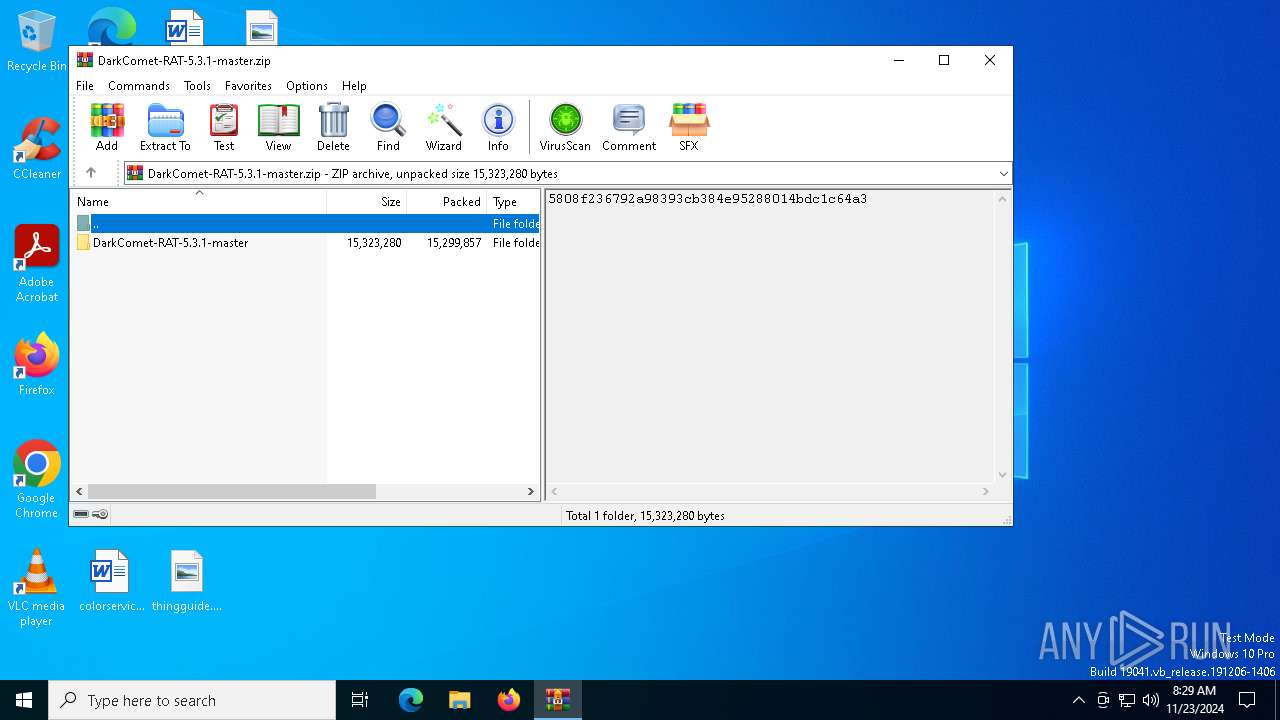
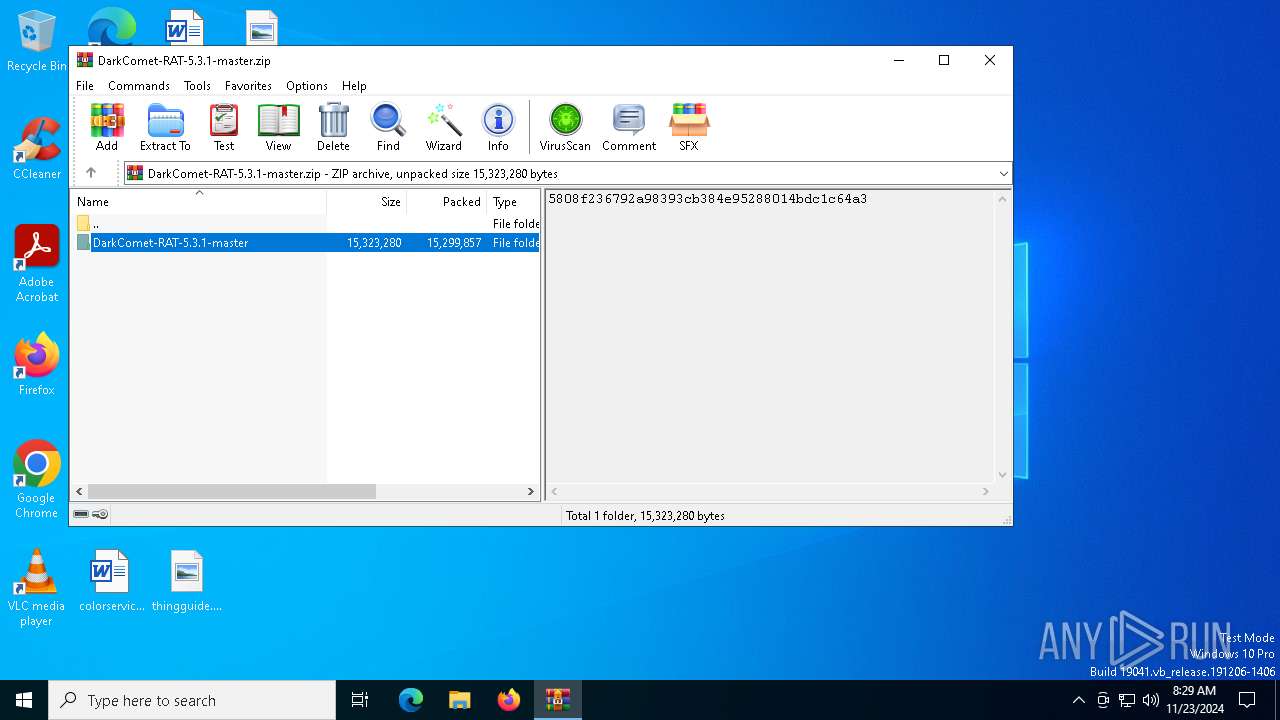
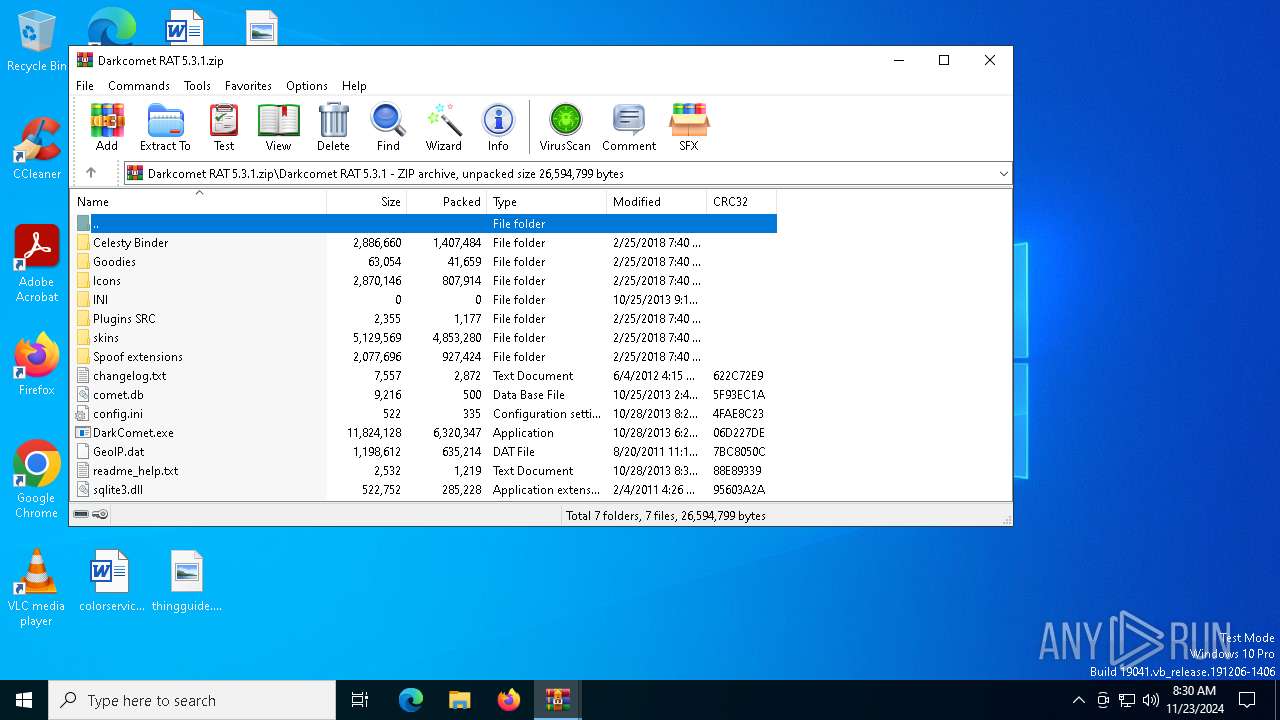
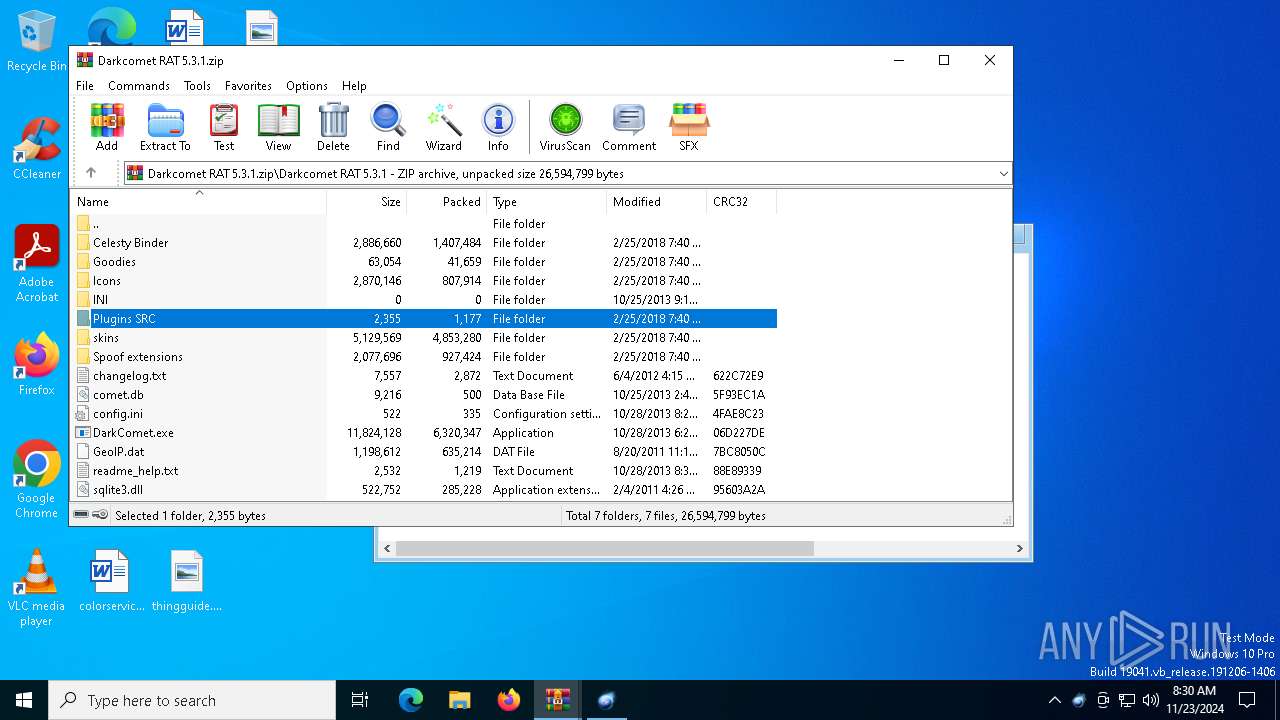
| File name: | DarkComet-RAT-5.3.1-master.zip |
| Full analysis: | https://app.any.run/tasks/5a218e26-186d-4768-8a7e-8e65b9b8ccd2 |
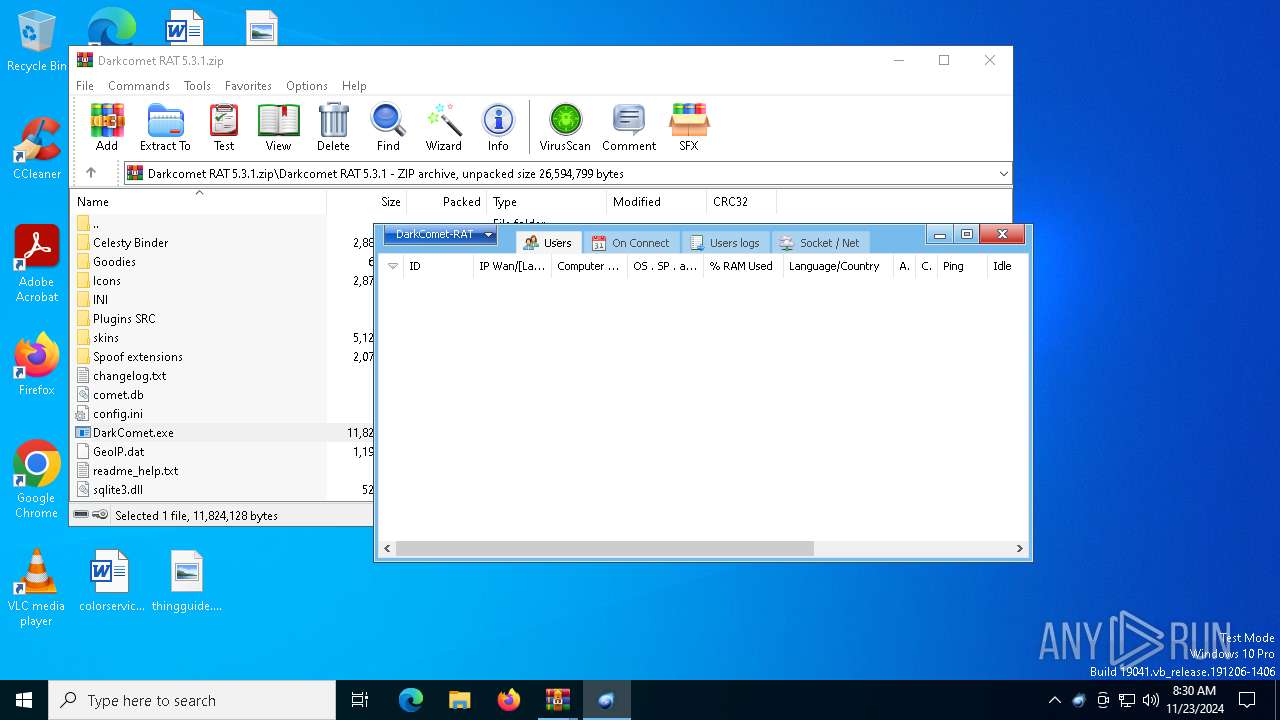
| Verdict: | Malicious activity |
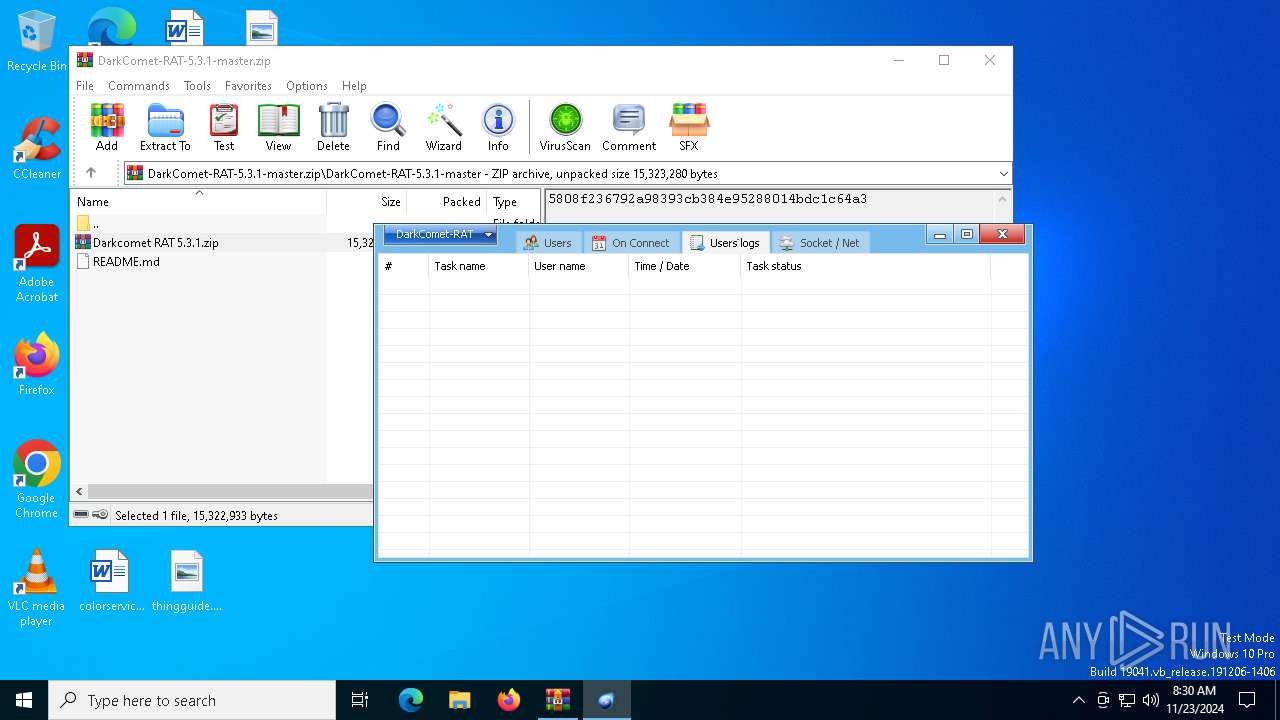
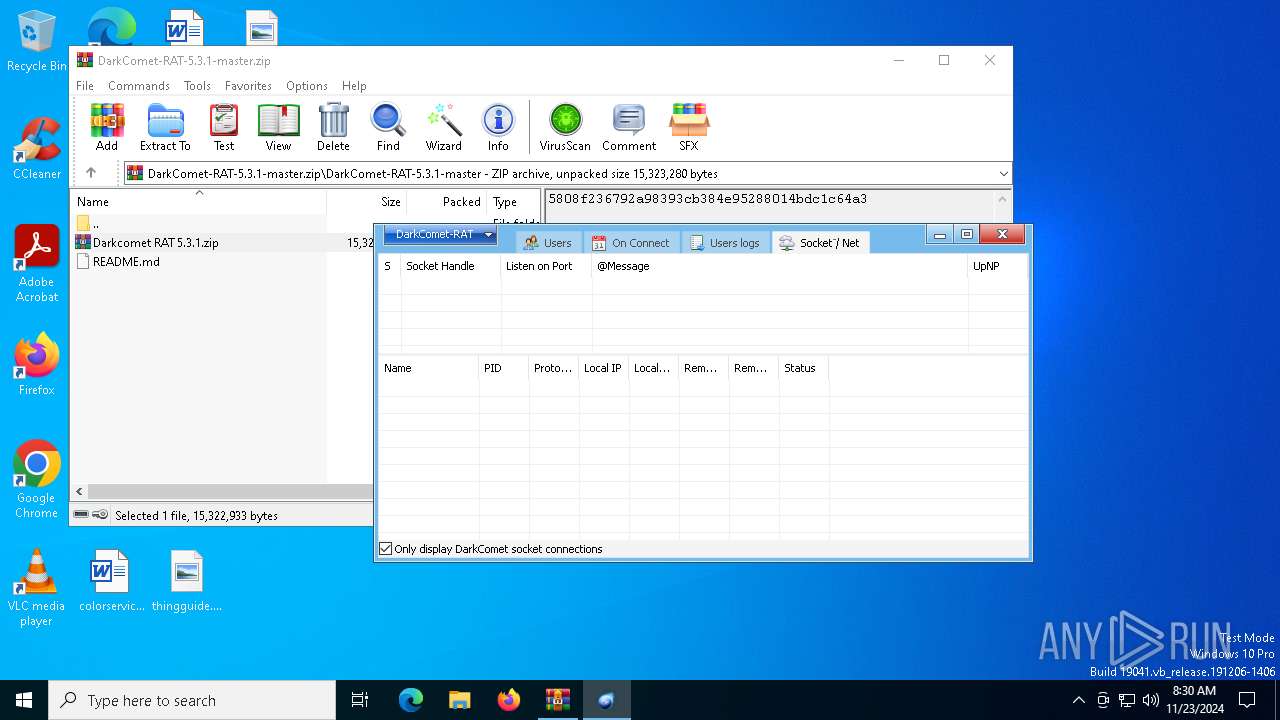
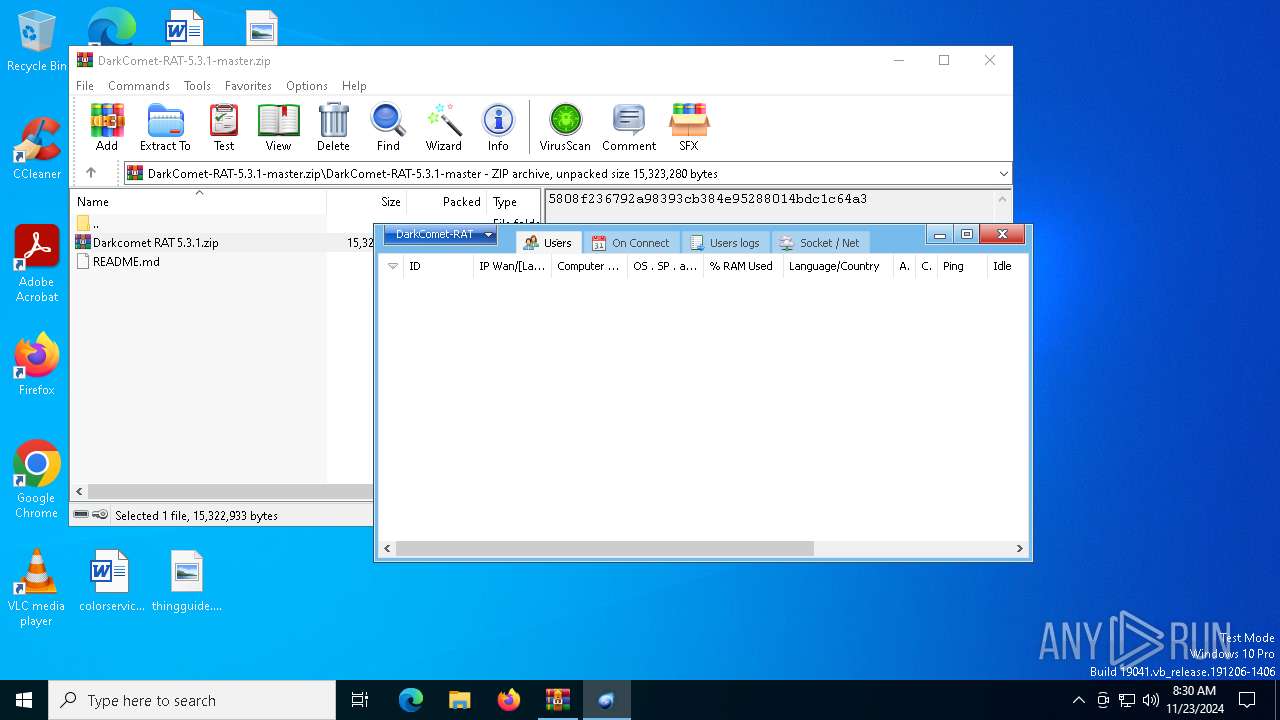
| Threats: | DarkComet RAT is a malicious program designed to remotely control or administer a victim's computer, steal private data and spy on the victim. |
| Analysis date: | November 23, 2024, 08:29:39 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | ABEF83A4EAD4D18C354F98D7E72312F1 |
| SHA1: | 21E1CE0FA9013534AF2A27C6D8FD0798E1028128 |
| SHA256: | 86FFDDA11652F7E00C5FC21EB9F2E97CAD4453B5E467501BB1207D3EBB7781EA |
| SSDEEP: | 393216:JuSX8qh5hu/OYnJ8jEMA/DTdfsuc1RzGCxi:JdX8qh5oVnJ8j/wDTdEKCxi |
MALICIOUS
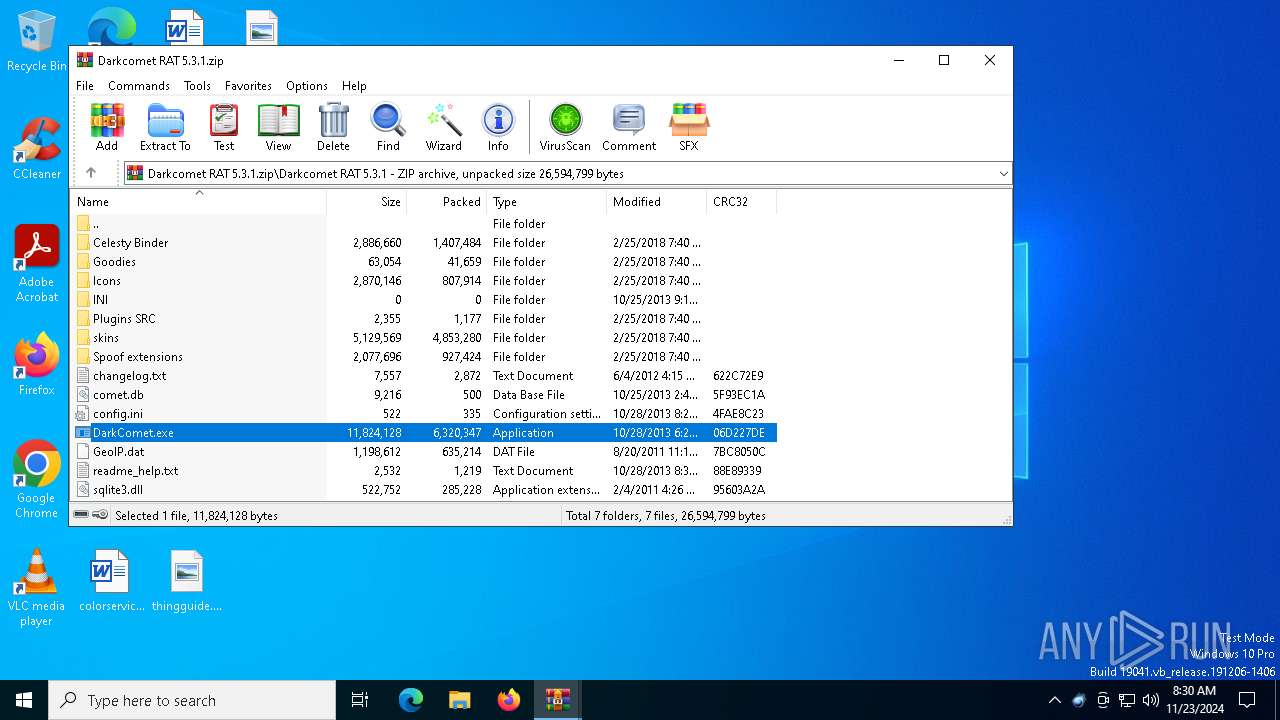
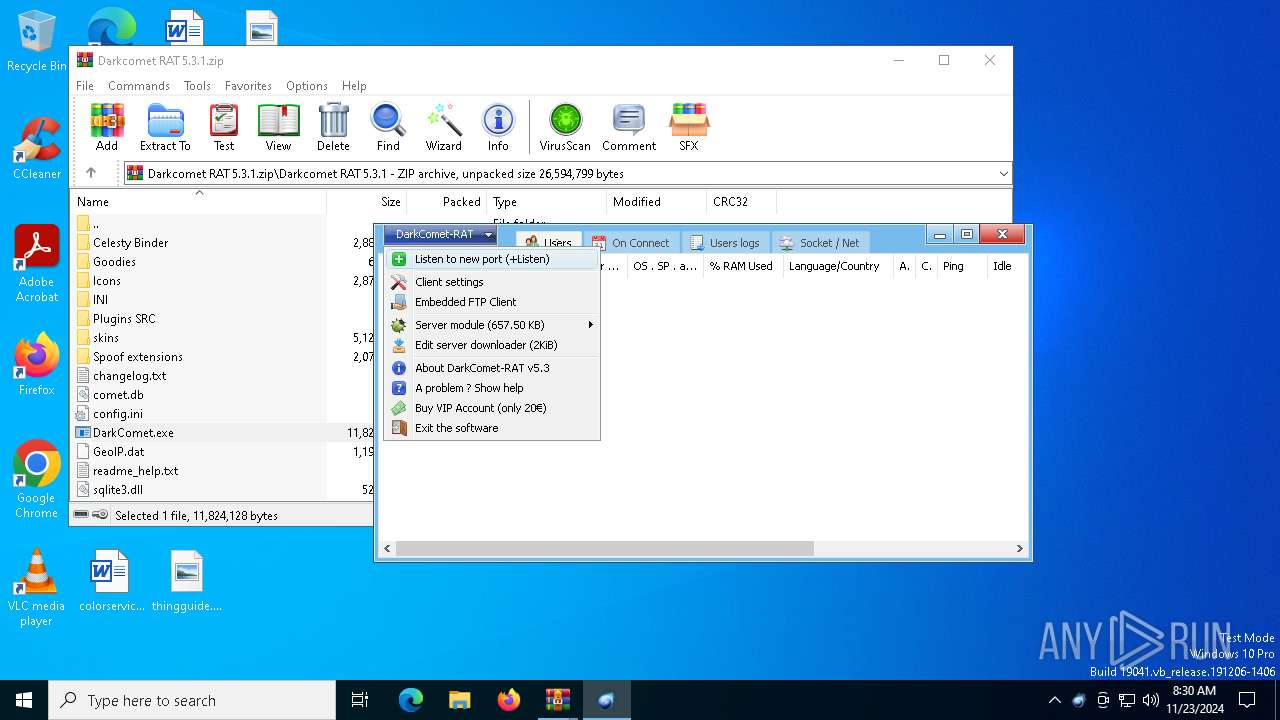
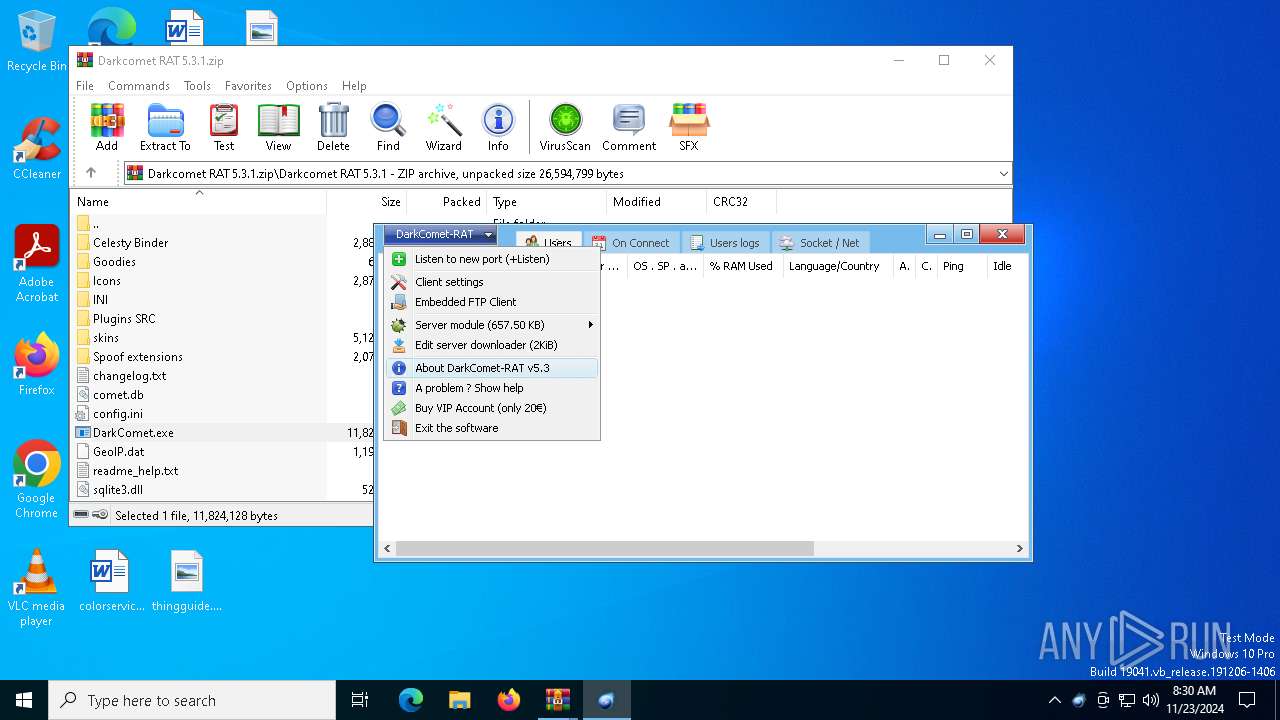
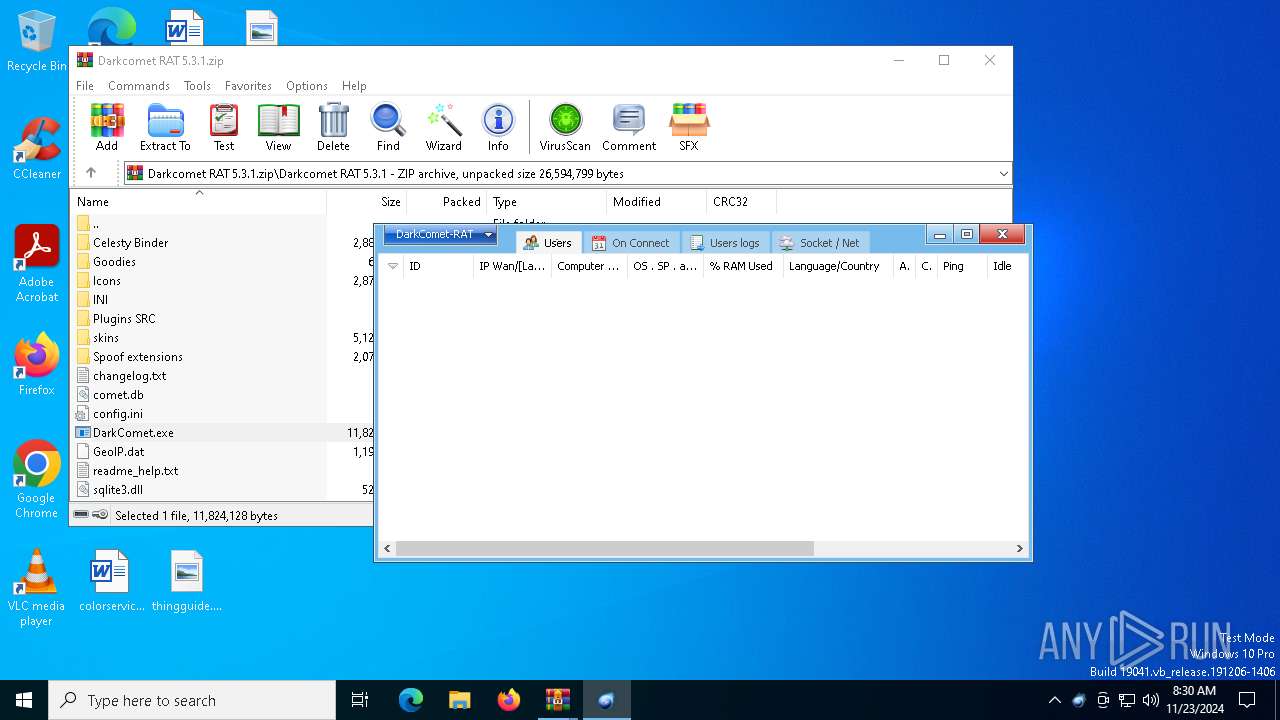
DARKCOMET has been detected (YARA)
- DarkComet.exe (PID: 5548)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5604)
- WinRAR.exe (PID: 2164)
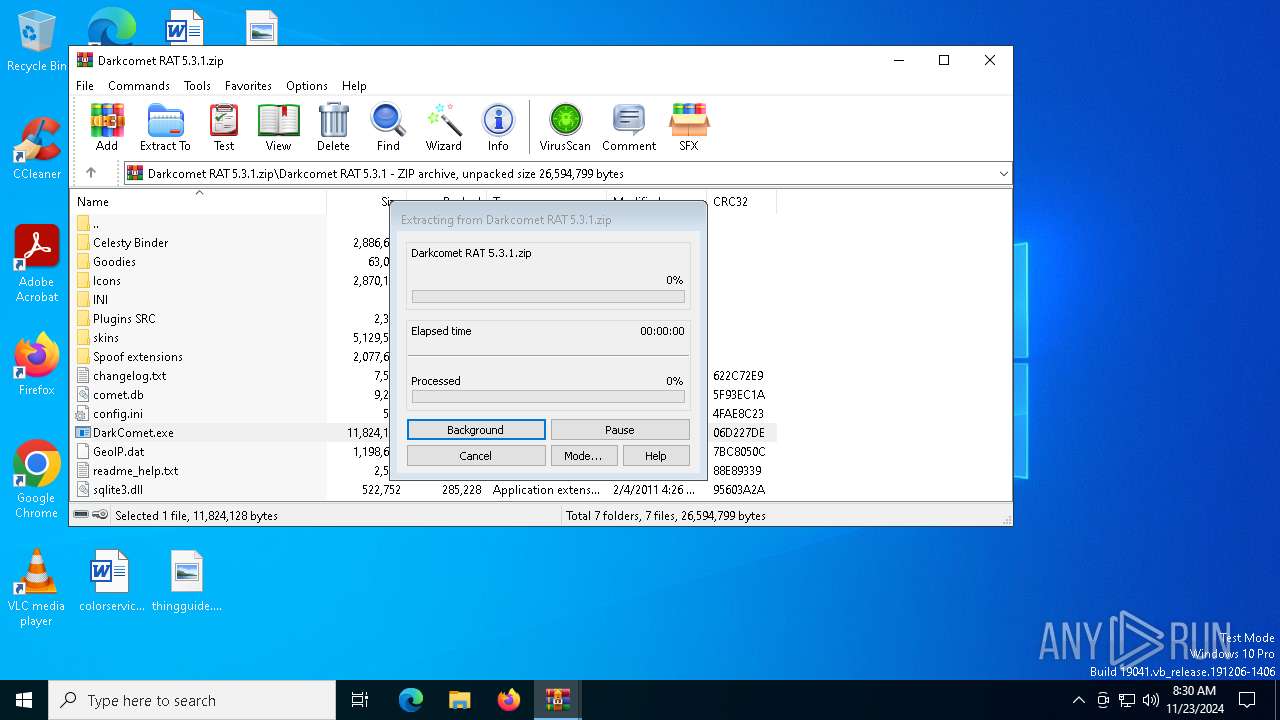
Generic archive extractor
- WinRAR.exe (PID: 5604)
Application launched itself
- WinRAR.exe (PID: 5604)
There is functionality for communication dyndns network (YARA)
- DarkComet.exe (PID: 5548)
INFO
Drops a (possible) Coronavirus decoy
- WinRAR.exe (PID: 2164)
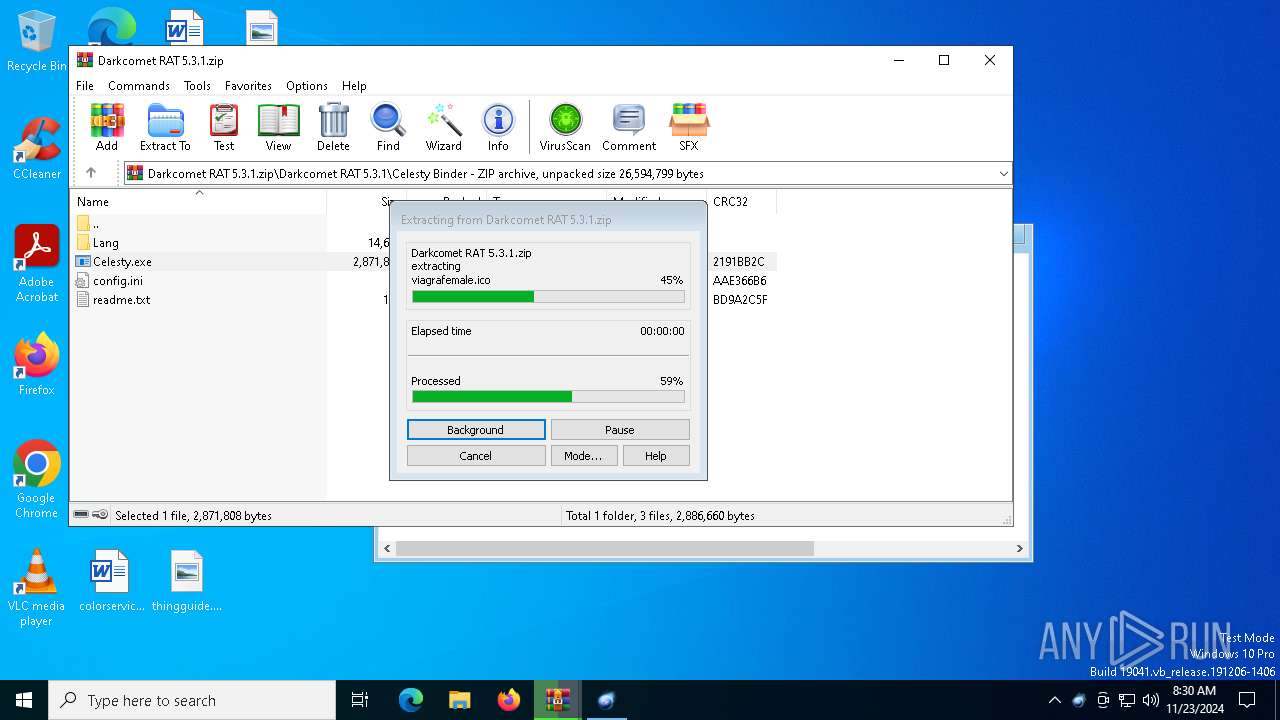
The process uses the downloaded file
- WinRAR.exe (PID: 5604)
- WinRAR.exe (PID: 2164)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2164)
Mpress packer has been detected
- DarkComet.exe (PID: 5548)
Checks supported languages
- DarkComet.exe (PID: 5548)
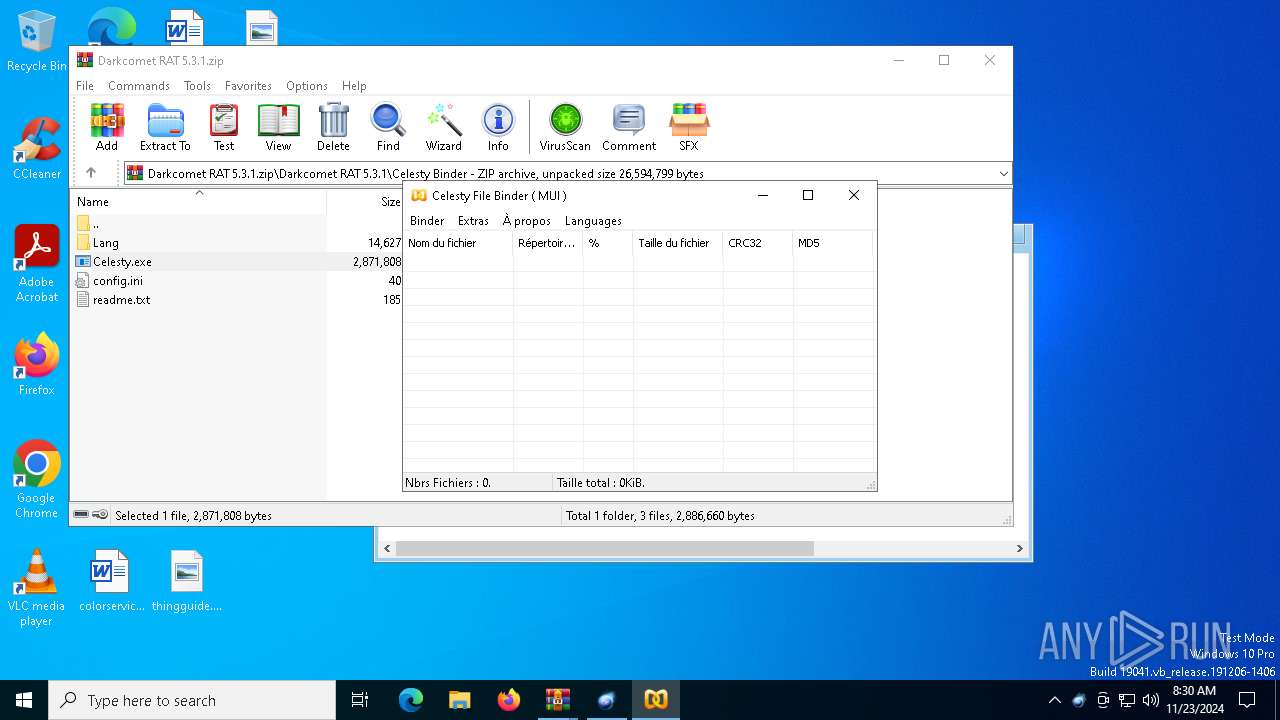
- Celesty.exe (PID: 2744)
UPX packer has been detected
- DarkComet.exe (PID: 5548)
Reads the computer name
- DarkComet.exe (PID: 5548)
- Celesty.exe (PID: 2744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
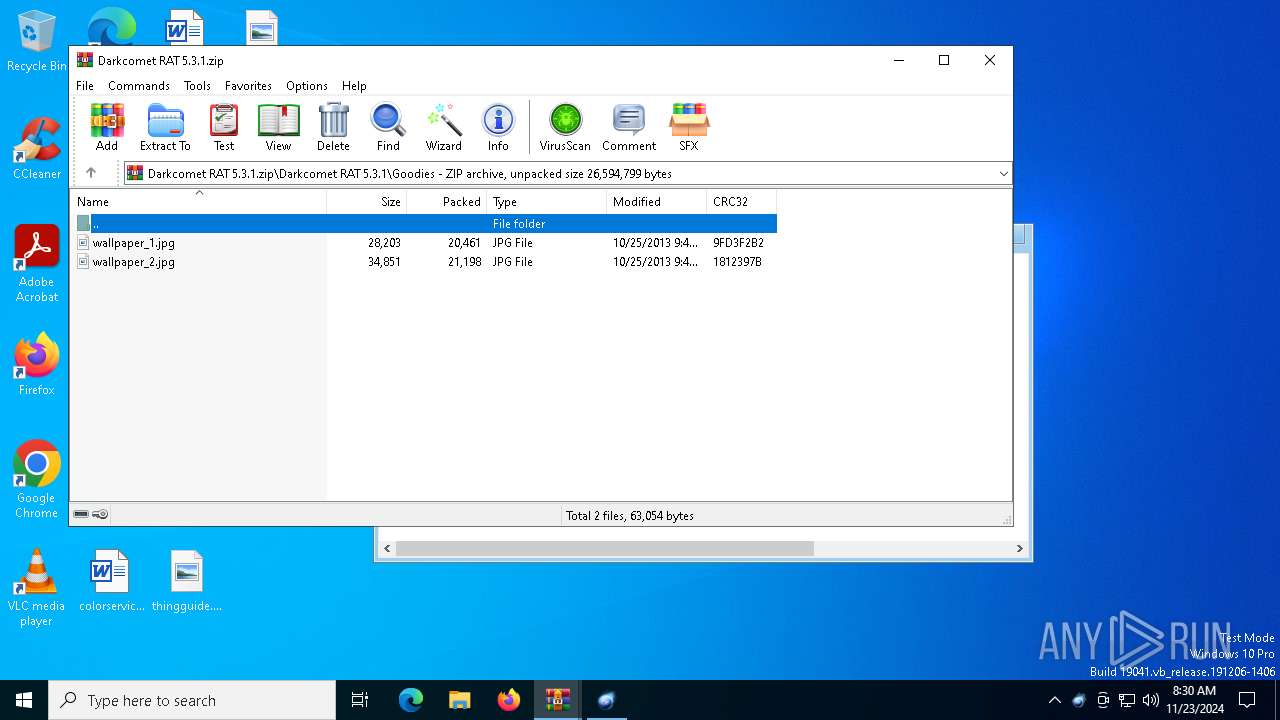
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:08:19 17:16:24 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | DarkComet-RAT-5.3.1-master/ |
Total processes
124
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
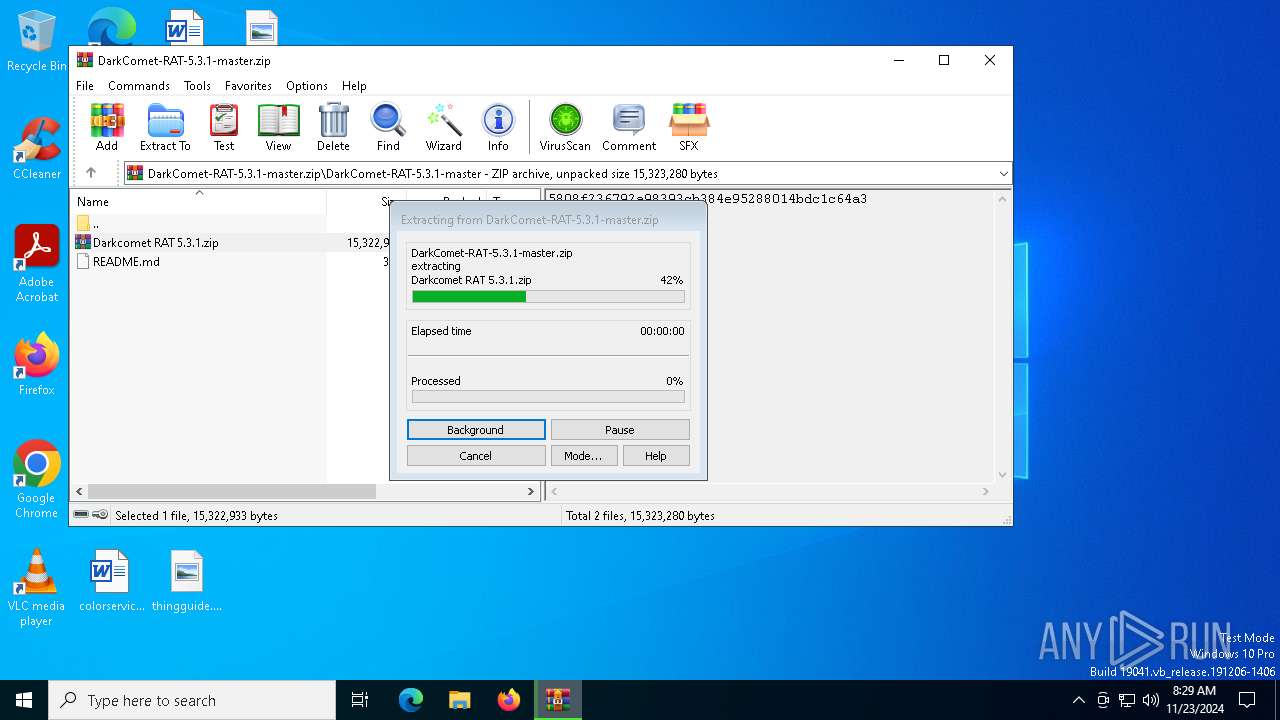
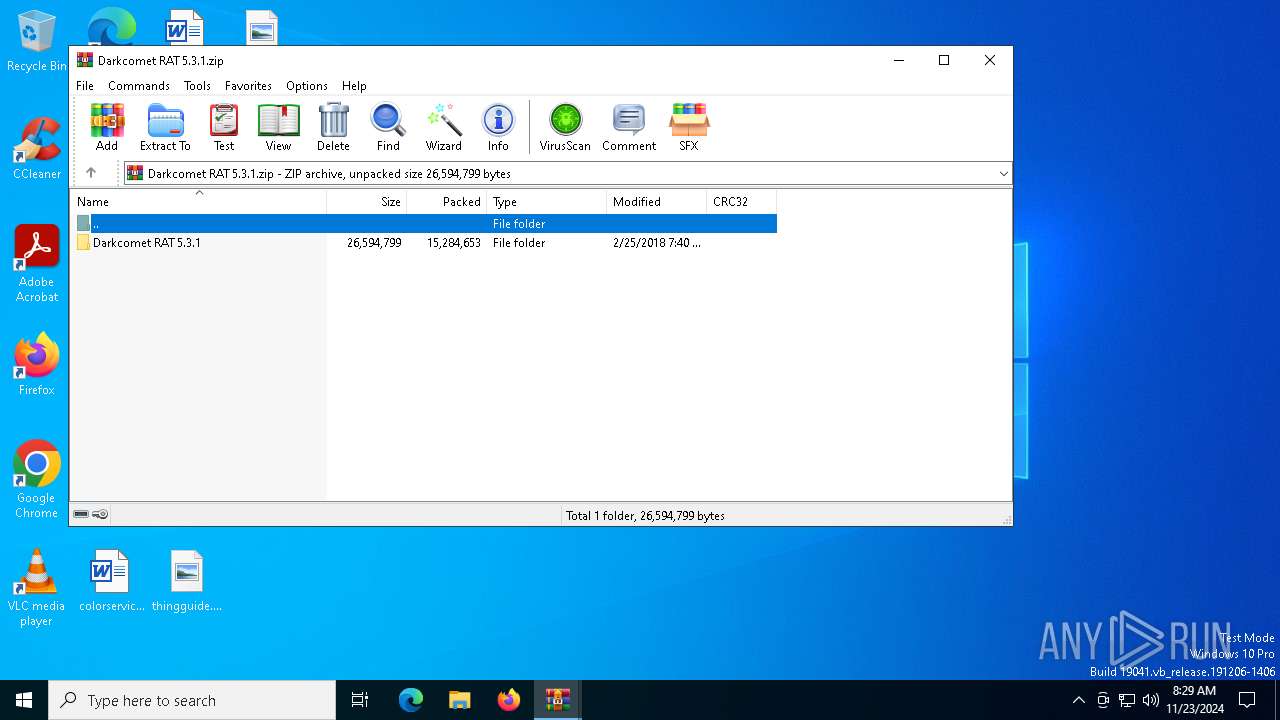
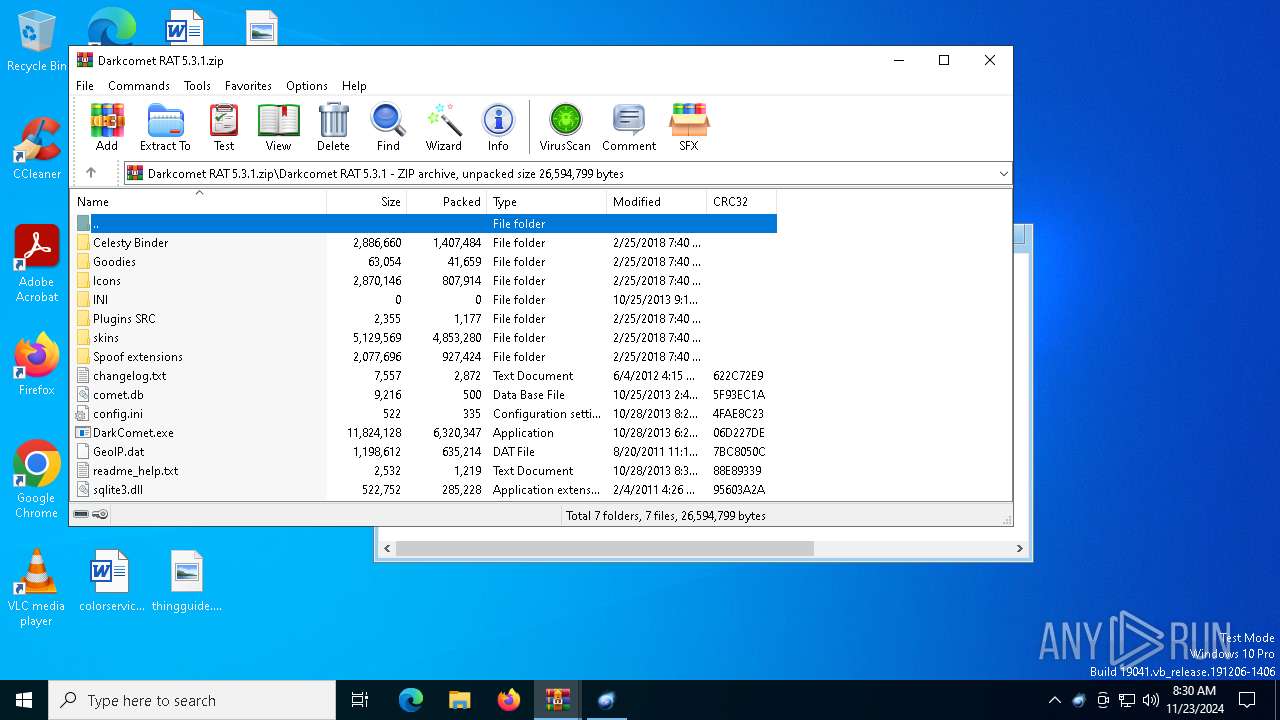
| 2164 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa5604.40641\Darkcomet RAT 5.3.1.zip" | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
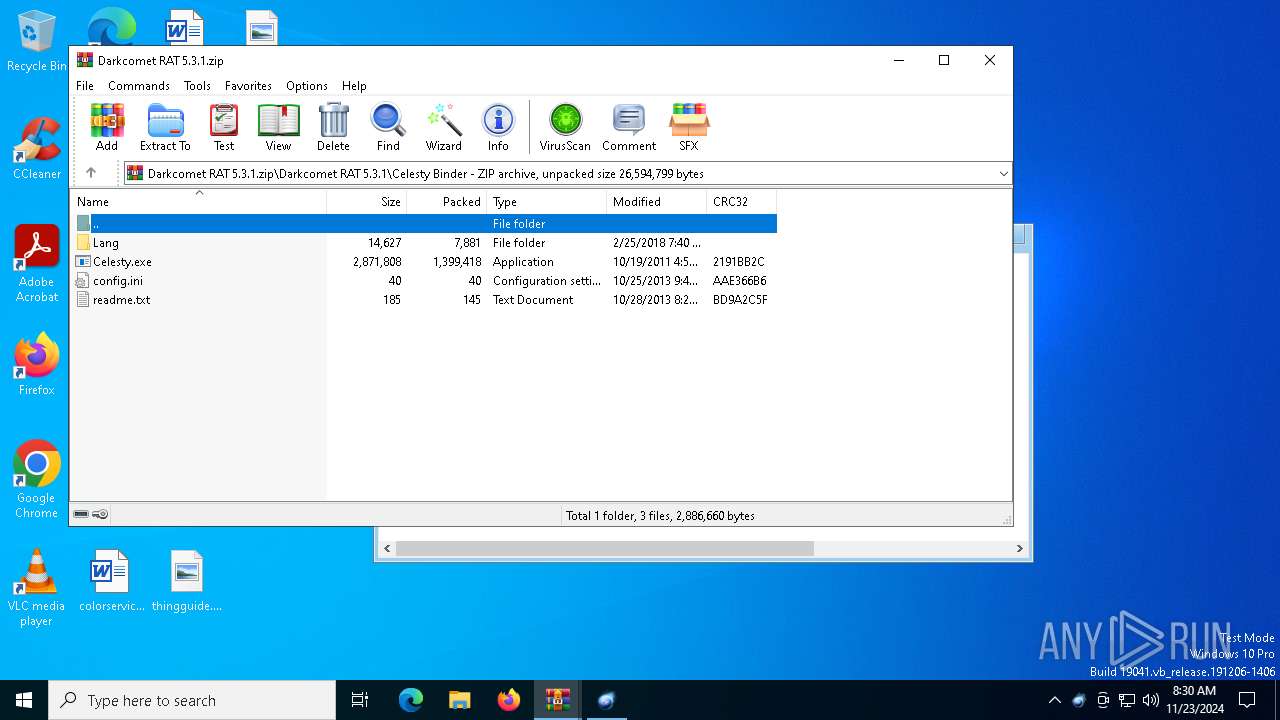
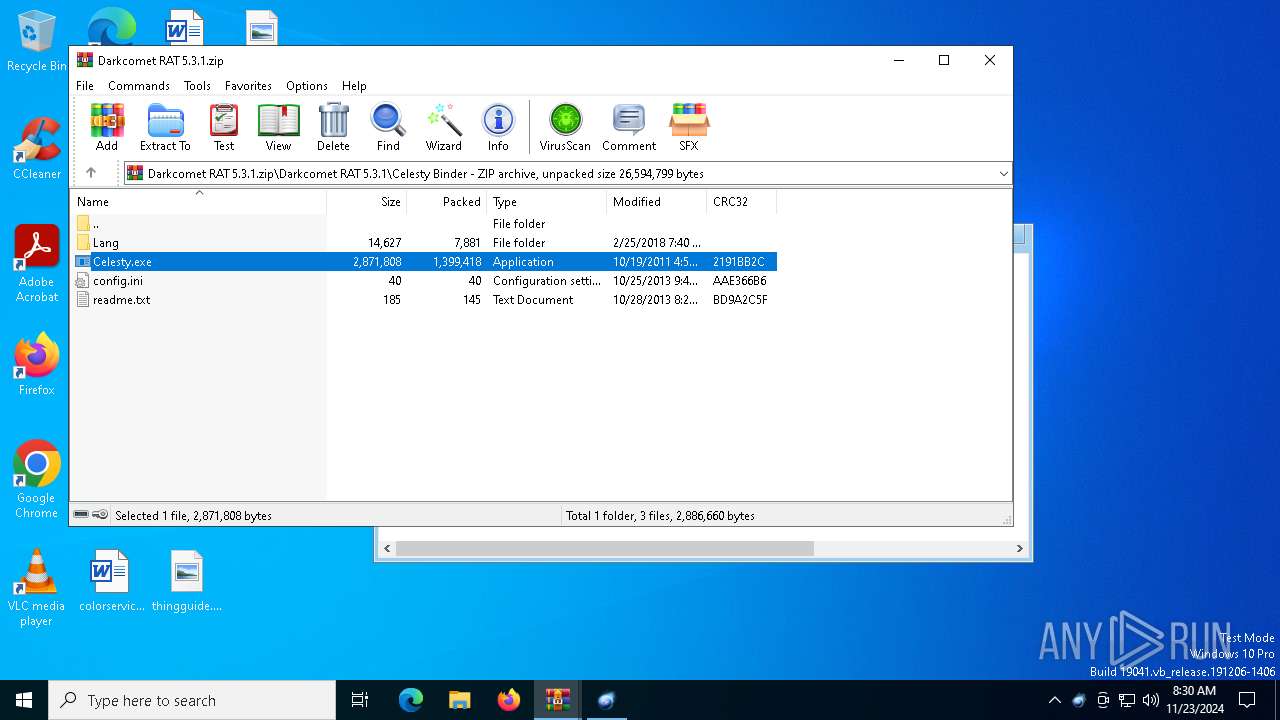
| 2744 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.44417\Darkcomet RAT 5.3.1\Celesty Binder\Celesty.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.44417\Darkcomet RAT 5.3.1\Celesty Binder\Celesty.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
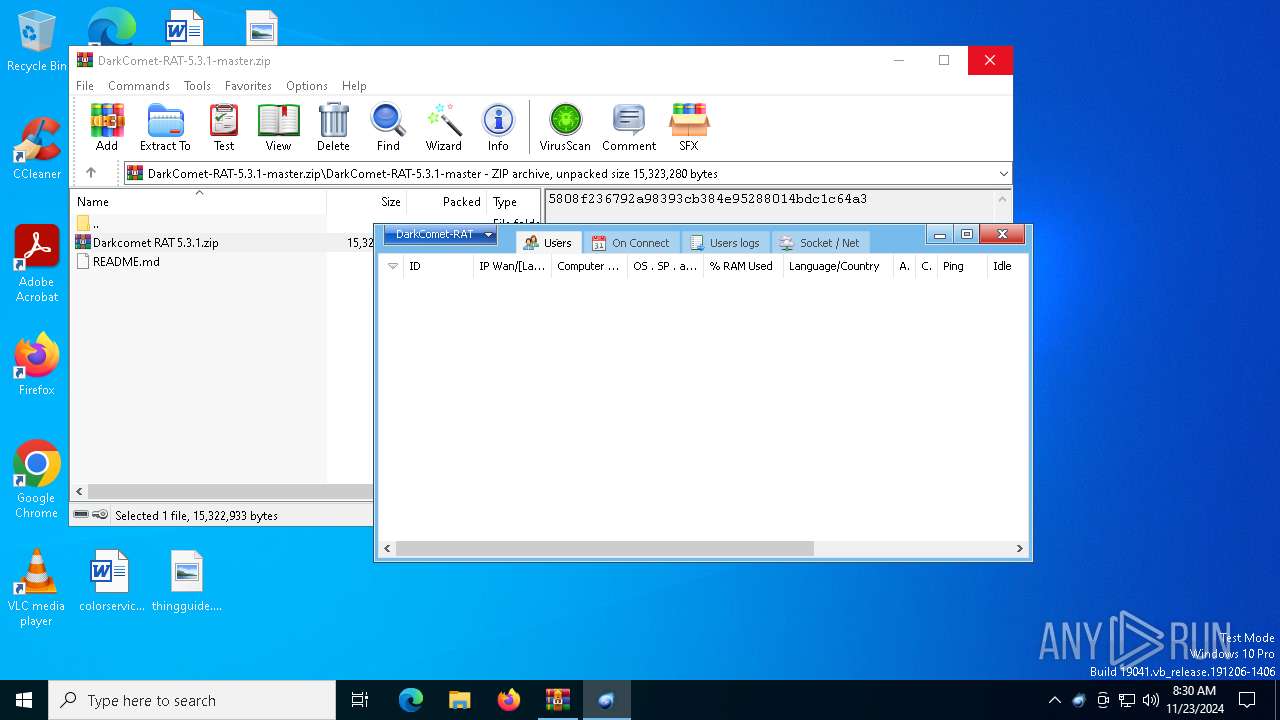
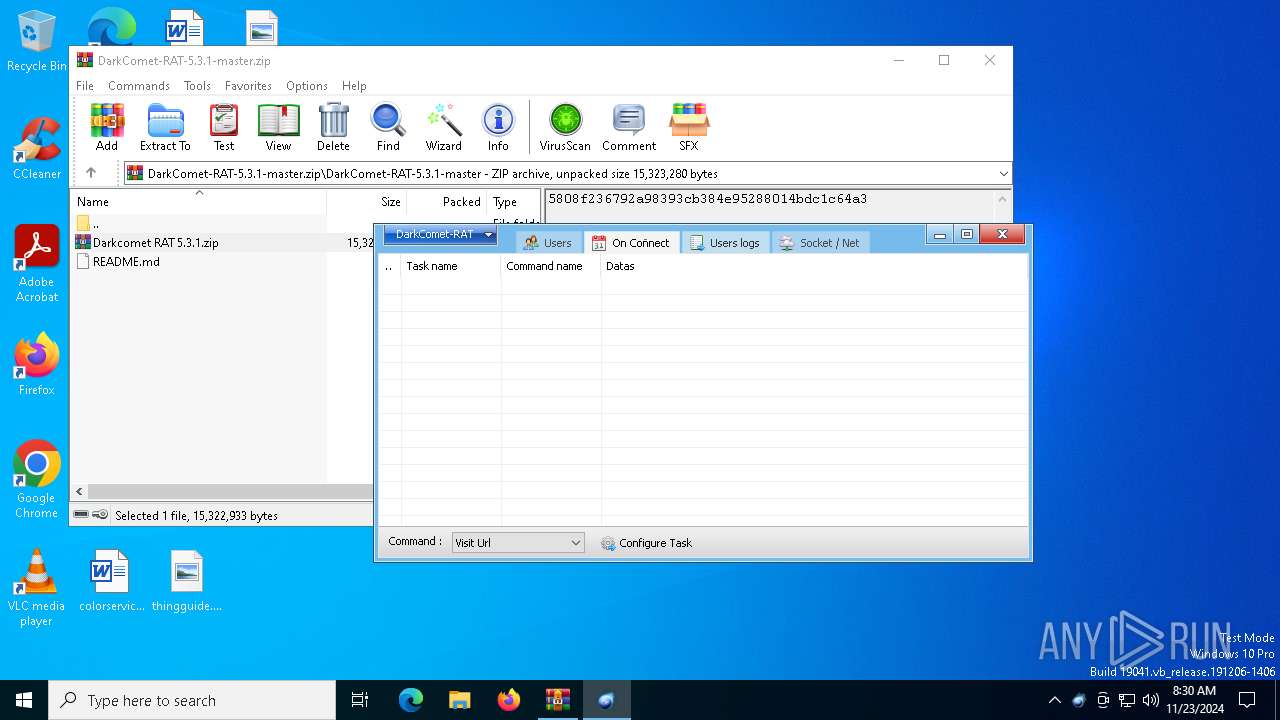
| 5548 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\DarkComet.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\DarkComet.exe | WinRAR.exe | ||||||||||||
User: admin Company: Unremote.org Integrity Level: MEDIUM Description: A remote administration tool from the cosmos Version: 4.2.0.28 Modules
| |||||||||||||||
| 5604 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\DarkComet-RAT-5.3.1-master.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
5 471
Read events
5 445
Write events
26
Delete events
0
Modification events
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DarkComet-RAT-5.3.1-master.zip | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5604) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2164) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
Executable files
8
Suspicious files
267
Text files
98
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Celesty.exe | executable | |
MD5:C3009EE63BC661D9EA75EAEB256448CA | SHA256:0BB88564A22BFD6D9AD6E4D8EFA9077792A7B6094C2A0F865D70C43E11507352 | |||
| 5604 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa5604.40641\Darkcomet RAT 5.3.1.zip | compressed | |
MD5:9F9347ECF2CC6541FB64ACD6FC0A5749 | SHA256:BFE9A76229E6E502B7C542007CD976DD3B5E0D26190CDF7CC8A5E5AAB0A63F7D | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\config.ini | ini | |
MD5:FACE4F2A1F63AB5DAF4456E3A46F62DC | SHA256:E529BCDCCA95735AEE7020A3B26312560584B78394CE971B3A729823DD148AAA | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\AR.ini | text | |
MD5:4276808F92D3EFE8359CB03F9C45C9E1 | SHA256:C4E0CD4D29594C9CB188DEAB7BB5F73FC6B3ED832468322ABC05B4E981C306C4 | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\EN.ini | text | |
MD5:D5B95D8DBCDCC5BE0290067BE9043009 | SHA256:48A43817F513A7DE5F033F842EA71DCEC7CFE45E2EDC87BE844E461D99E2572E | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\ES.ini | text | |
MD5:4745B84E71D23454D2535CC608DE57D0 | SHA256:EB0553309ACD121B01566C1CA297ED46E896E3AD11C486971E8FA7275A1FF061 | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\FR.ini | text | |
MD5:A8568B41DF3F0A47F875964E8FEEFA70 | SHA256:F515EE7D43CF301FE771599C60E2771DB6F27E614AF6A4403771A0D99CB19BC7 | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\GR.ini | text | |
MD5:8B35CDF90F3D89D2502E1F61B2BBF631 | SHA256:FCA01673CB23ABD479B6D54D19A40A87E9D72B90ECC7F5D59AF14D192CC07C7C | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\IT.ini | binary | |
MD5:1CB447996787264785C83D110C67AB13 | SHA256:840DB2223BC47B37C44393BCE4CA8583D373EF6D70B6BC9143561190AA16CDCB | |||
| 2164 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2164.41368\Darkcomet RAT 5.3.1\Celesty Binder\Lang\LV.ini | text | |
MD5:84E0FF162036F454D019B48BA6AF5F7A | SHA256:78F24B0B140943912A1130DA1ED3A20EB71126EE077793D19F990566FF633C3F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3796 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4548 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4548 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3220 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2380 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.49:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |