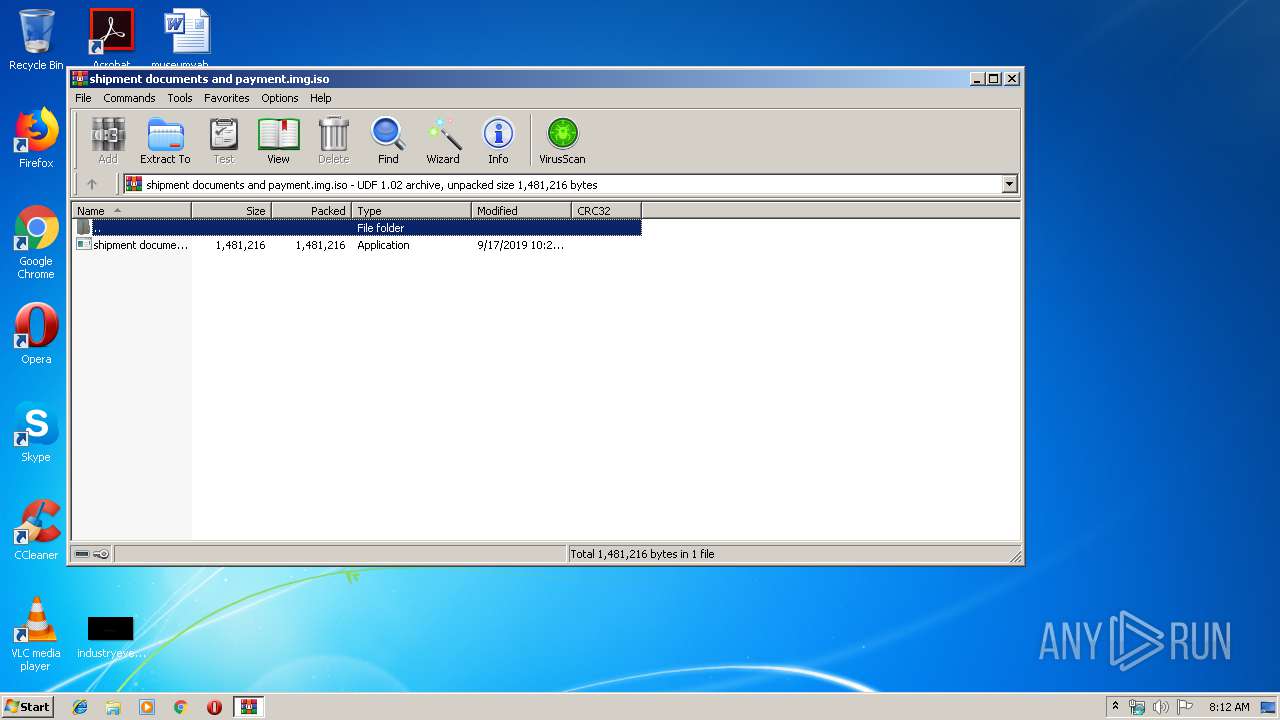
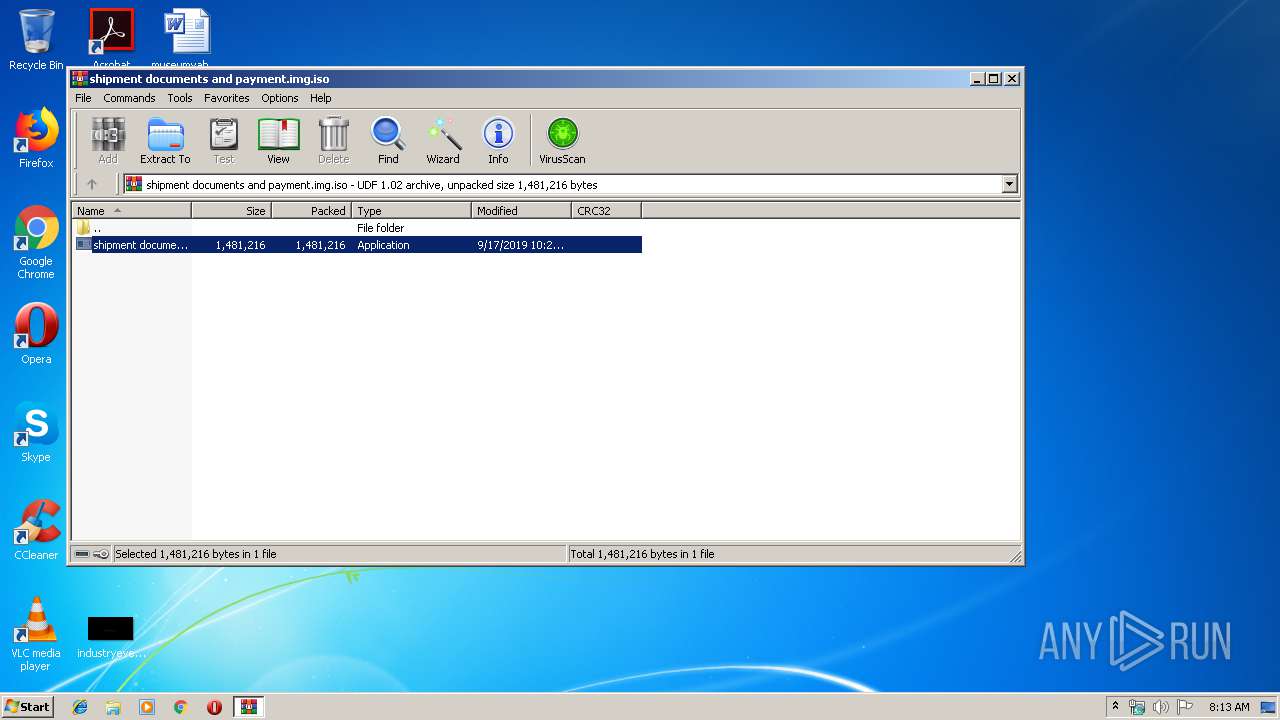
| File name: | shipment documents and payment.img |
| Full analysis: | https://app.any.run/tasks/fc522558-7f4a-42e5-8445-b2b638ee6922 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | September 19, 2019, 07:12:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | UDF filesystem data (version 1.5) 'DESKTOP' |
| MD5: | E9BA63B1840C8923ADE4C44DFC975918 |
| SHA1: | B477DDA3833D75AB11C2C186B75ECD2E9F422038 |
| SHA256: | 86EF9504F8491D750D5A61A6B25EBB769679B191A1213A6EB3E7BBD134F6077C |
| SSDEEP: | 24576:wAHnh+eWsN3skA4RV1Hom2KXMmHasHvmBJZDgWCm2zoTIltYR+rmfStu2n25:nh+ZkldoPK8YasotOoMAMGCs |
MALICIOUS
Application was dropped or rewritten from another process
- shipment documents and payment.exe (PID: 3196)
- RegAsm.exe (PID: 2284)
Writes to a start menu file
- shipment documents and payment.exe (PID: 3196)
Changes the autorun value in the registry
- RegAsm.exe (PID: 2284)
AGENTTESLA was detected
- RegAsm.exe (PID: 2284)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 2284)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3564)
- RegAsm.exe (PID: 2284)
Creates files in the user directory
- RegAsm.exe (PID: 2284)
- shipment documents and payment.exe (PID: 3196)
Checks for external IP
- RegAsm.exe (PID: 2284)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| VolumeName: | DESKTOP |
|---|---|
| VolumeBlockCount: | 989 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2019:09:17 22:24:31-07:00 |
| VolumeSetName: | UNDEFINED |
| Software: | IMGBURN V2.5.8.0 - THE ULTIMATE IMAGE BURNER! |
| VolumeCreateDate: | 2019:09:17 22:24:31.00-07:00 |
| VolumeModifyDate: | 2019:09:17 22:24:31.00-07:00 |
Composite
| VolumeSize: | 1978 kB |
|---|
Total processes
35
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2284 | "C:\\\\Windows\\\\Microsoft.NET\\\\Framework\\\\v2.0.50727\\\\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | shipment documents and payment.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3196 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3564.19884\shipment documents and payment.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3564.19884\shipment documents and payment.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\shipment documents and payment.img.iso" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
508
Read events
483
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\shipment documents and payment.img.iso | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2284 | RegAsm.exe | C:\Users\admin\AppData\Local\Temp\637044776178281250_2f41157a-994b-4c2c-b860-8f8454f84a42.db | sqlite | |
MD5:— | SHA256:— | |||
| 3564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa3564.19884\shipment documents and payment.exe | executable | |
MD5:— | SHA256:— | |||
| 2284 | RegAsm.exe | C:\Users\admin\AppData\Roaming\newapp\newapp.exe | executable | |
MD5:278EDBD499374BF73621F8C1F969D894 | SHA256:C6999B9F79932C3B4F1C461A69D9DC8DC301D6A155ABC33EFE1B6E9E4A038391 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2284 | RegAsm.exe | GET | 200 | 52.55.255.113:80 | http://checkip.amazonaws.com/ | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2284 | RegAsm.exe | 52.55.255.113:80 | checkip.amazonaws.com | Amazon.com, Inc. | US | shared |
2284 | RegAsm.exe | 103.233.0.177:587 | mail.fruitiking.com | Exa Bytes Network Sdn.Bhd. | MY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| malicious |
mail.fruitiking.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | RegAsm.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2284 | RegAsm.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2284 | RegAsm.exe | A Network Trojan was detected | AV TROJAN Win.Keylogger.AgentTesla variant outbound SMTP connection |
3 ETPRO signatures available at the full report