| File name: | Purchase Order.jar.jar |
| Full analysis: | https://app.any.run/tasks/f923ef53-7059-4278-931d-86f7e07b9cce |
| Verdict: | Malicious activity |
| Threats: | Adwind RAT, sometimes also called Unrecom, Sockrat, Frutas, jRat, and JSocket, is a Malware As A Service Remote Access Trojan that attackers can use to collect information from infected machines. It was one of the most popular RATs in the market in 2015. |
| Analysis date: | March 22, 2019, 05:36:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | B254095C2BC55D3B5B45DAE9BDE8A4DD |
| SHA1: | 566880A67EDE298575AAA28D6907B2EFDD61E89A |
| SHA256: | 869CC2A32F631F2FB9F448FCF89986901C5A2540534E17356DEDAE5EB8646807 |
| SSDEEP: | 3072:LQYV6szDXUT1e7KlCqM/4ggi9jZFEUTEtsSrpyUB6iph:LG6XG1euoJ9ZFEWSrRB6iph |
MALICIOUS
AdWind was detected
- java.exe (PID: 1436)
Loads dropped or rewritten executable
- java.exe (PID: 1436)
- javaw.exe (PID: 1476)
- explorer.exe (PID: 1696)
Application was dropped or rewritten from another process
- java.exe (PID: 1436)
- javaw.exe (PID: 1476)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 1476)
- xcopy.exe (PID: 1908)
Executes JAVA applets
- javaw.exe (PID: 1476)
- explorer.exe (PID: 1696)
Starts CMD.EXE for commands execution
- java.exe (PID: 1436)
Executes scripts
- cmd.exe (PID: 2264)
- cmd.exe (PID: 516)
Executable content was dropped or overwritten
- xcopy.exe (PID: 1908)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:21 20:13:19 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/ |
Total processes
39
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive4339733817534507036.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 948 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive1359164093026559412.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Java\jre1.8.0_92\bin\java.exe" -jar C:\Users\admin\AppData\Local\Temp\_0.164643820855177048980941928117480858.class | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | javaw.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\Purchase Order.jar.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1696 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1908 | xcopy "C:\Program Files\Java\jre1.8.0_92" "C:\Users\admin\AppData\Roaming\Oracle\" /e | C:\Windows\system32\xcopy.exe | java.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2264 | cmd.exe /C cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive1359164093026559412.vbs | C:\Windows\system32\cmd.exe | — | java.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2572 | cscript.exe C:\Users\admin\AppData\Local\Temp\Retrive4339733817534507036.vbs | C:\Windows\system32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
109
Read events
92
Write events
17
Delete events
0
Modification events
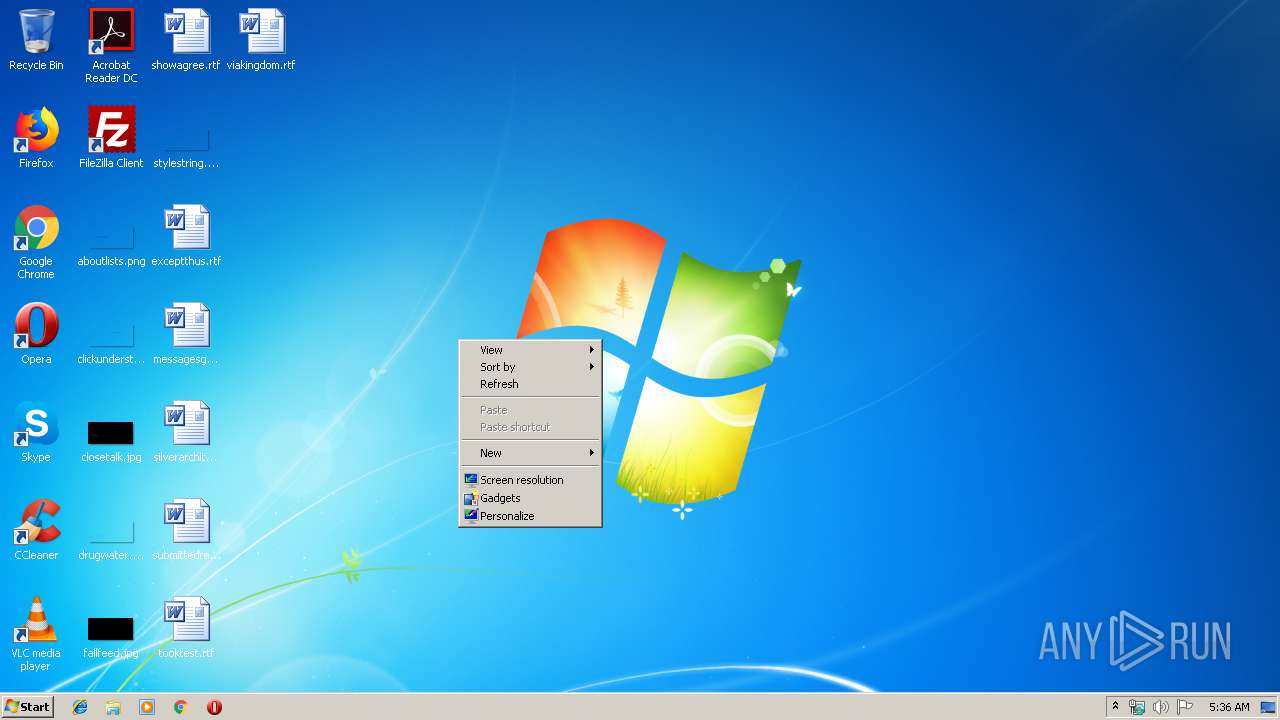
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\display.dll,-4 |
Value: S&creen resolution | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Common Files\System\wab32res.dll,-4602 |
Value: Contact file | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Windows Sidebar\sidebar.exe,-11100 |
Value: &Gadgets | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\themecpl.dll,-10 |
Value: Pe&rsonalize | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @"C:\Program Files\Windows Journal\Journal.exe",-3072 |
Value: Journal Document | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | Classes |
Value: .accdb | |||
| (PID) Process: | (1696) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | ~reserved~ |
Value: 0800000000000600 | |||
Executable files
107
Suspicious files
10
Text files
66
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | javaw.exe | C:\Users\admin\AppData\Local\Temp\jar_cache4287783124880308790.tmp | — | |
MD5:— | SHA256:— | |||
| 1436 | java.exe | C:\Users\admin\AppData\Local\Temp\Retrive1359164093026559412.vbs | — | |
MD5:— | SHA256:— | |||
| 1476 | javaw.exe | C:\Users\admin\AppData\Local\Temp\jar_cache7487003665657828918.tmp | — | |
MD5:— | SHA256:— | |||
| 1476 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 1436 | java.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 1908 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\LICENSE | text | |
MD5:98F46AB6481D87C4D77E0E91A6DBC15F | SHA256:23F9A5C12FA839650595A32872B7360B9E030C7213580FB27DD9185538A5828C | |||
| 1908 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\bin\bci.dll | executable | |
MD5:6D8D8A26450EE4BA0BE405629EA0A511 | SHA256:7945365A3CD40D043DAE47849E6645675166920958300E64DEA76A865BC479AF | |||
| 1908 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\README.txt | text | |
MD5:0F1123976B959AC5E8B89EB8C245C4BD | SHA256:963095CF8DB76FB8071FD19A3110718A42F2AB42B27A3ADFD9EC58981C3E88D2 | |||
| 1476 | javaw.exe | C:\Users\admin\AppData\Local\Temp\_0.164643820855177048980941928117480858.class | java | |
MD5:781FB531354D6F291F1CCAB48DA6D39F | SHA256:97D585B6AFF62FB4E43E7E6A5F816DCD7A14BE11A88B109A9BA9E8CD4C456EB9 | |||
| 1908 | xcopy.exe | C:\Users\admin\AppData\Roaming\Oracle\release | text | |
MD5:1BCCC3A965156E53BE3136B3D583B7B6 | SHA256:03A4DB27DEA69374EFBAF121C332D0AF05840D16D0C1FBF127D00E65054B118A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1476 | javaw.exe | GET | 200 | 199.188.200.56:80 | http://unknowncrypter.co/unknown/locat/1553126400onvspxcwra.upload | US | java | 473 Kb | malicious |
1476 | javaw.exe | GET | 200 | 199.188.200.56:80 | http://unknowncrypter.co/unknown/locat/1553126400onvspxcwra.upload | US | java | 473 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1476 | javaw.exe | 199.188.200.56:80 | unknowncrypter.co | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
unknowncrypter.co |
| malicious |