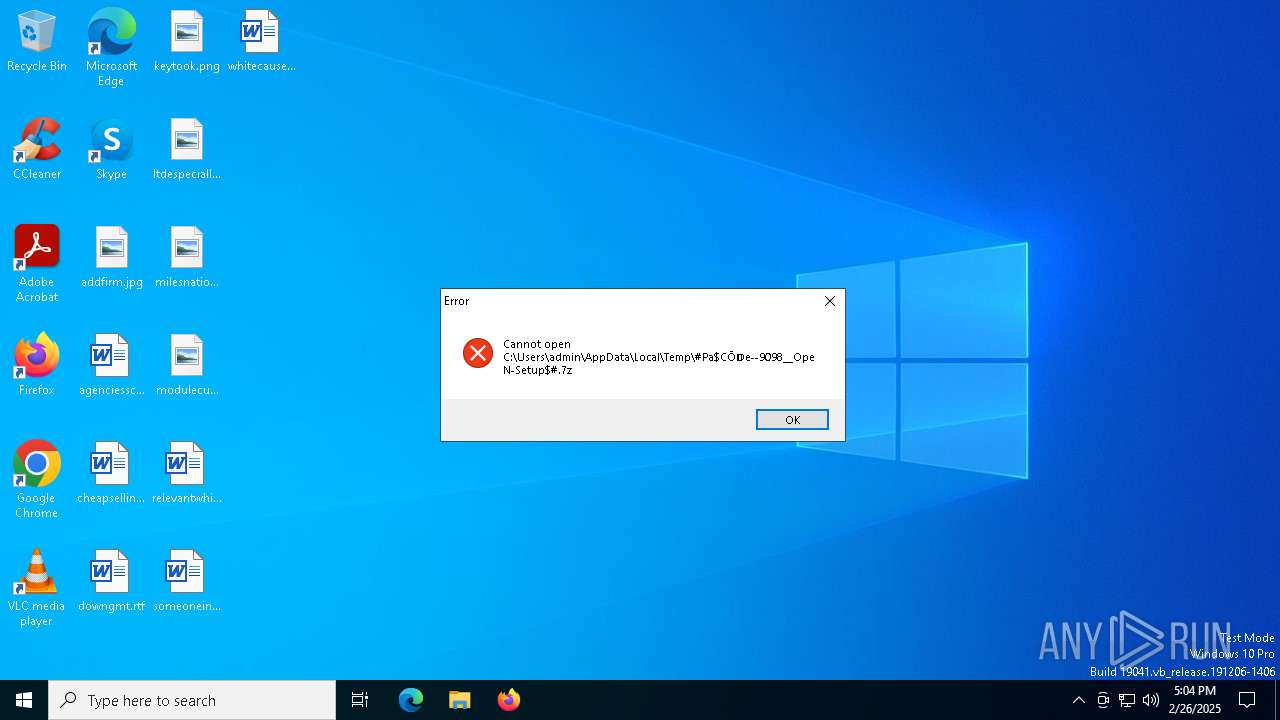
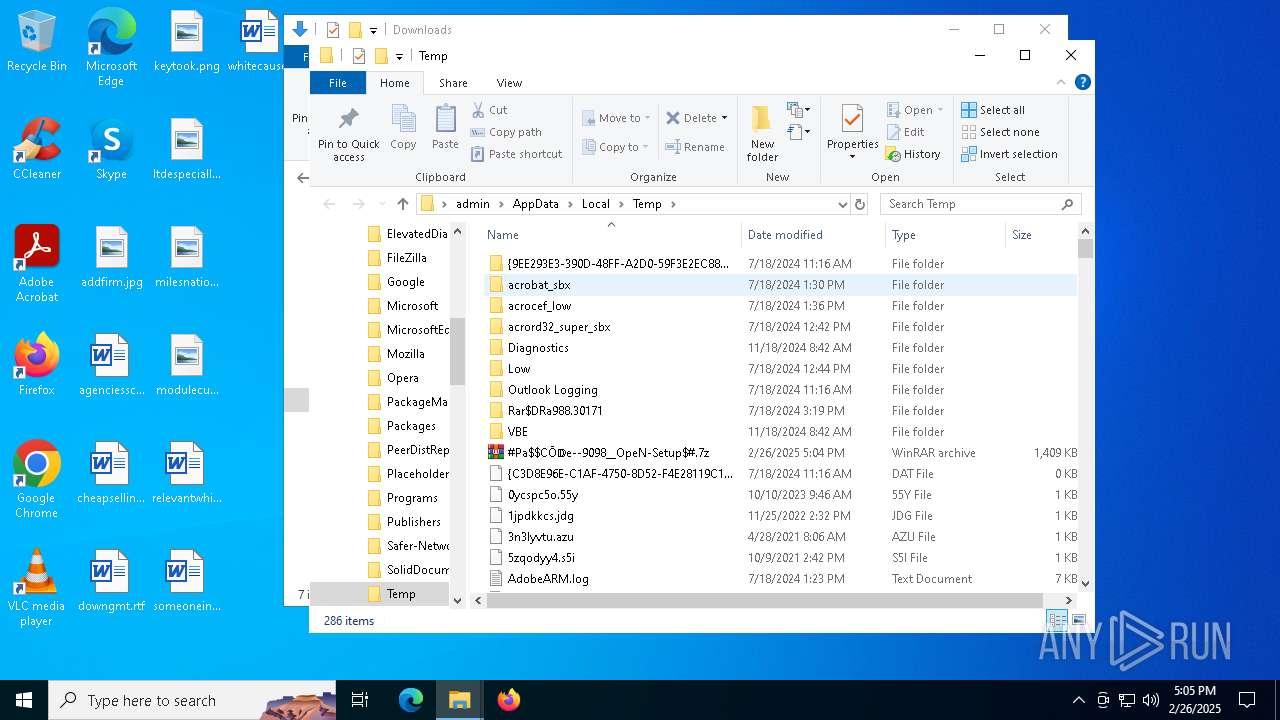
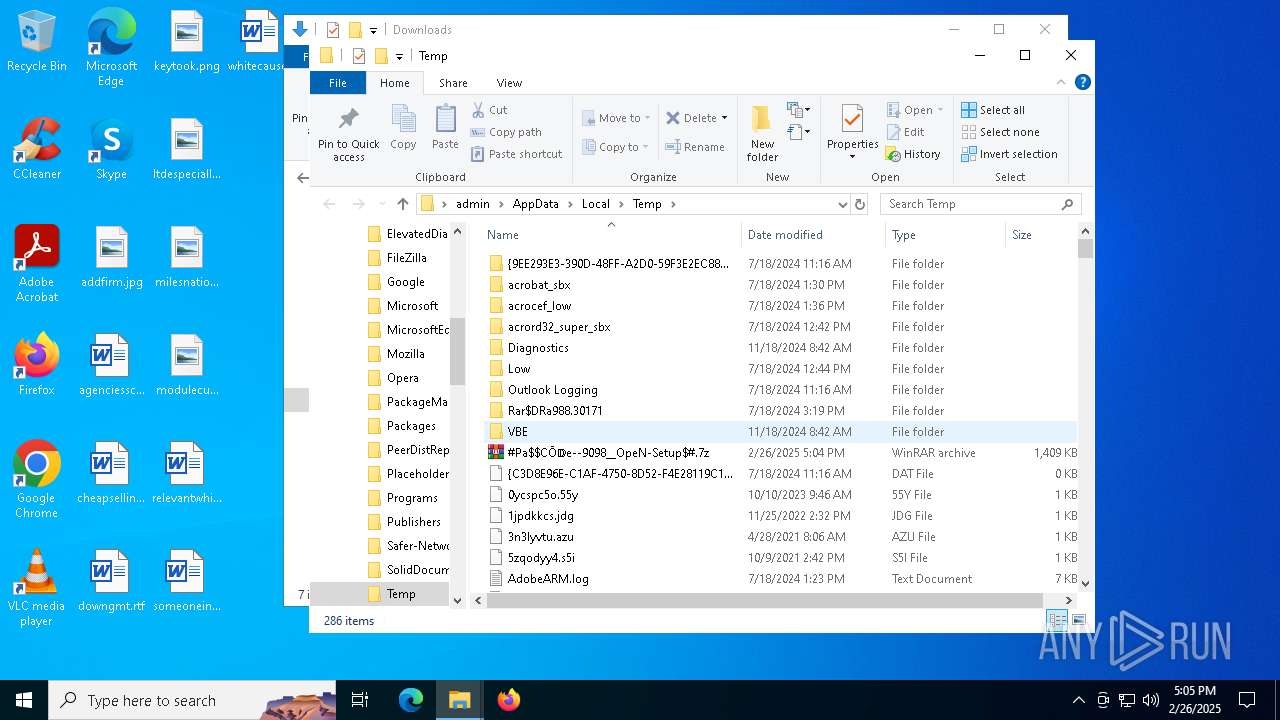
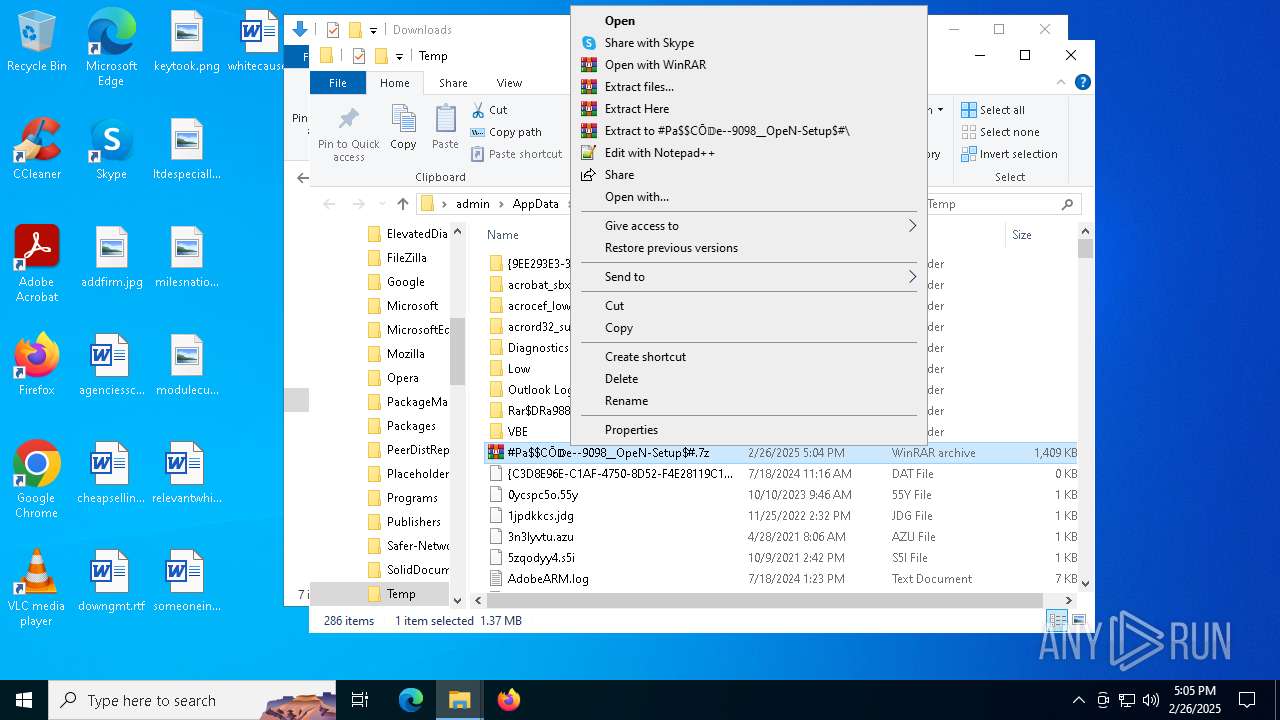
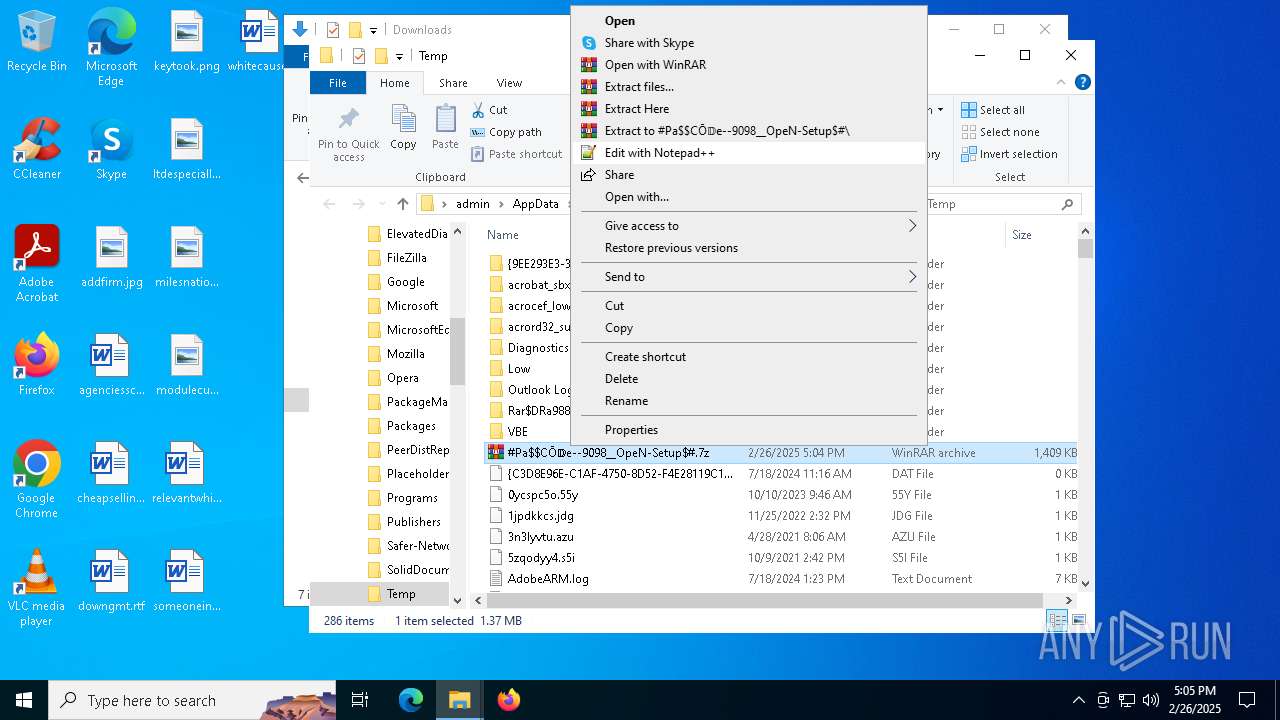
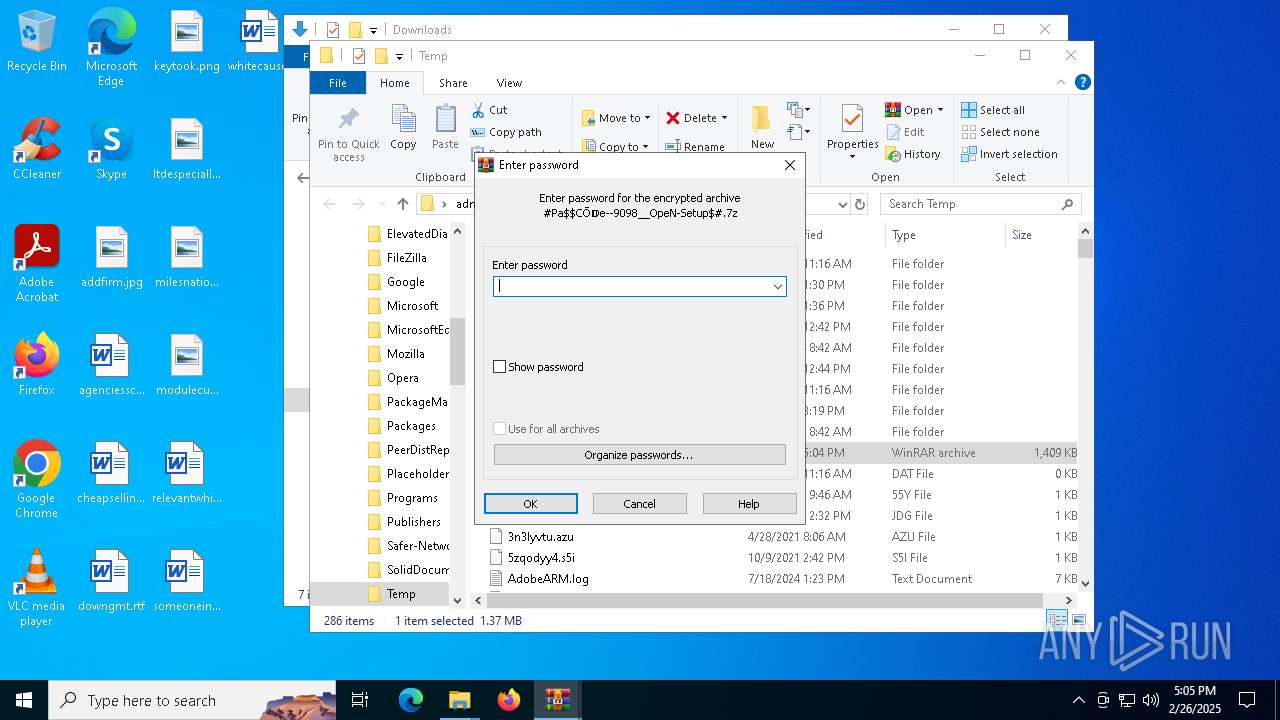
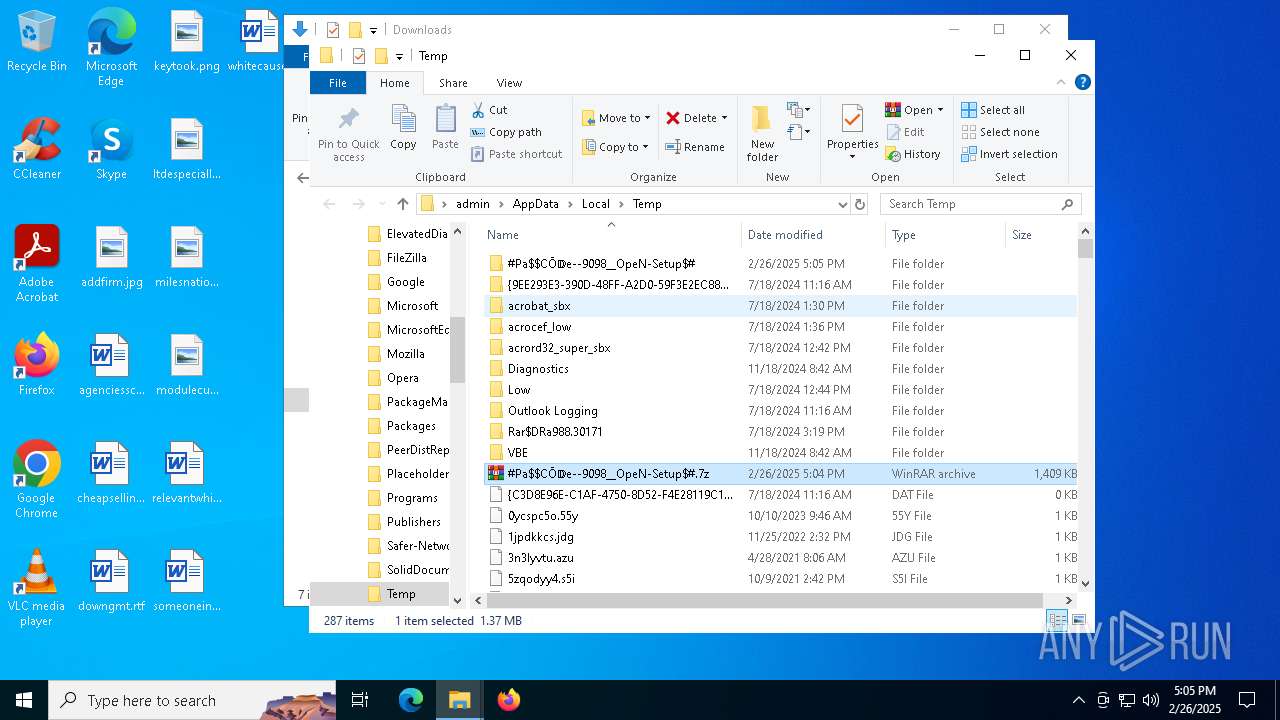
| File name: | #Pa$CŌ𝔻e--9098__OpeN-Setup$#.7z |
| Full analysis: | https://app.any.run/tasks/16378878-0c0d-406c-a5d2-460720872bf8 |
| Verdict: | Malicious activity |
| Threats: | Lumma is an information stealer, developed using the C programming language. It is offered for sale as a malware-as-a-service, with several plans available. It usually targets cryptocurrency wallets, login credentials, and other sensitive information on a compromised system. The malicious software regularly gets updates that improve and expand its functionality, making it a serious stealer threat. |
| Analysis date: | February 26, 2025, 17:04:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | F6EF66BFB4A5883CAA3CBE0D5F9705A9 |
| SHA1: | 9B0C58544F0C84AB3F0A579CBC61C0A1E2C3A40F |
| SHA256: | 8680FC67A20D8220802F945FBA6572AC8203BE813EFF4748BB61F093DB8F7115 |
| SSDEEP: | 49152:ZR7vm2o0SlDF3fws/h+OtBbIUWJa3UmM83aNuCFmrDCUKrMLo3hQ0YDsWrTeFDNk:Ztmv0C3fws/zpIU33UmM83bCmfCUJk3+ |
MALICIOUS
Connects to the CnC server
- svchost.exe (PID: 2196)
LUMMA has been detected (YARA)
- setup.exe (PID: 7540)
Executing a file with an untrusted certificate
- setup.exe (PID: 7540)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2196)
LUMMA mutex has been found
- setup.exe (PID: 7540)
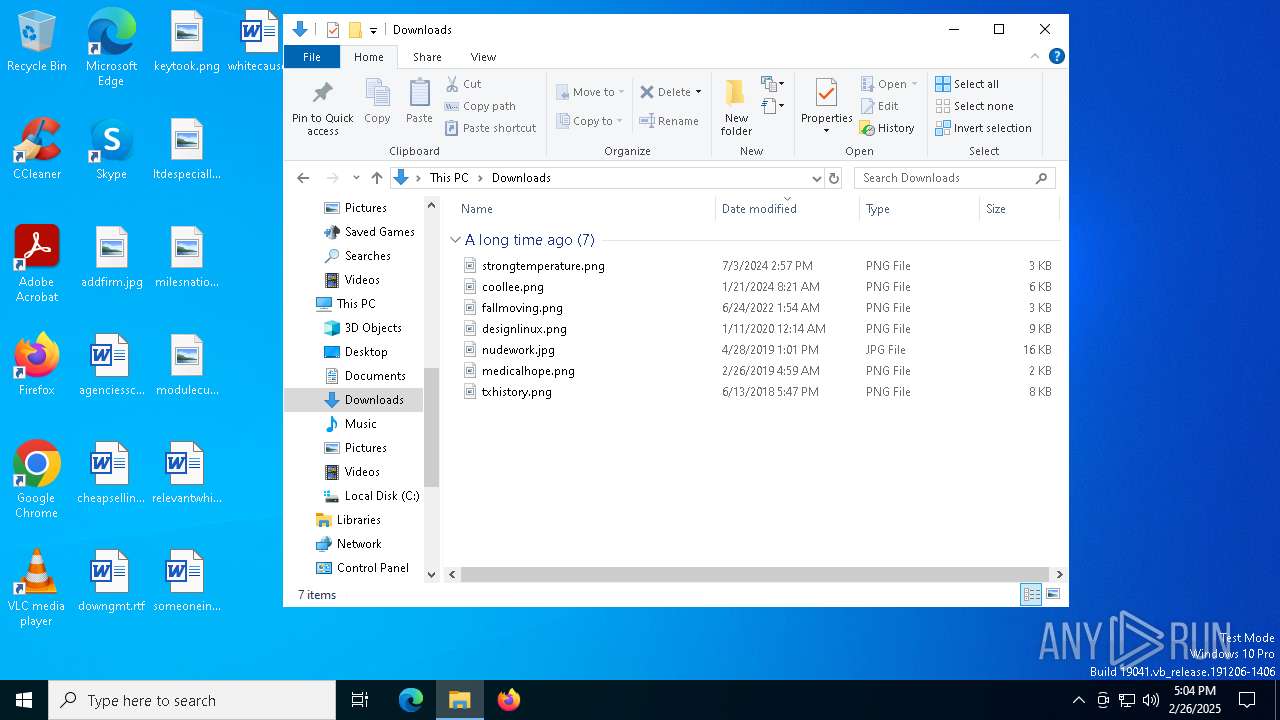
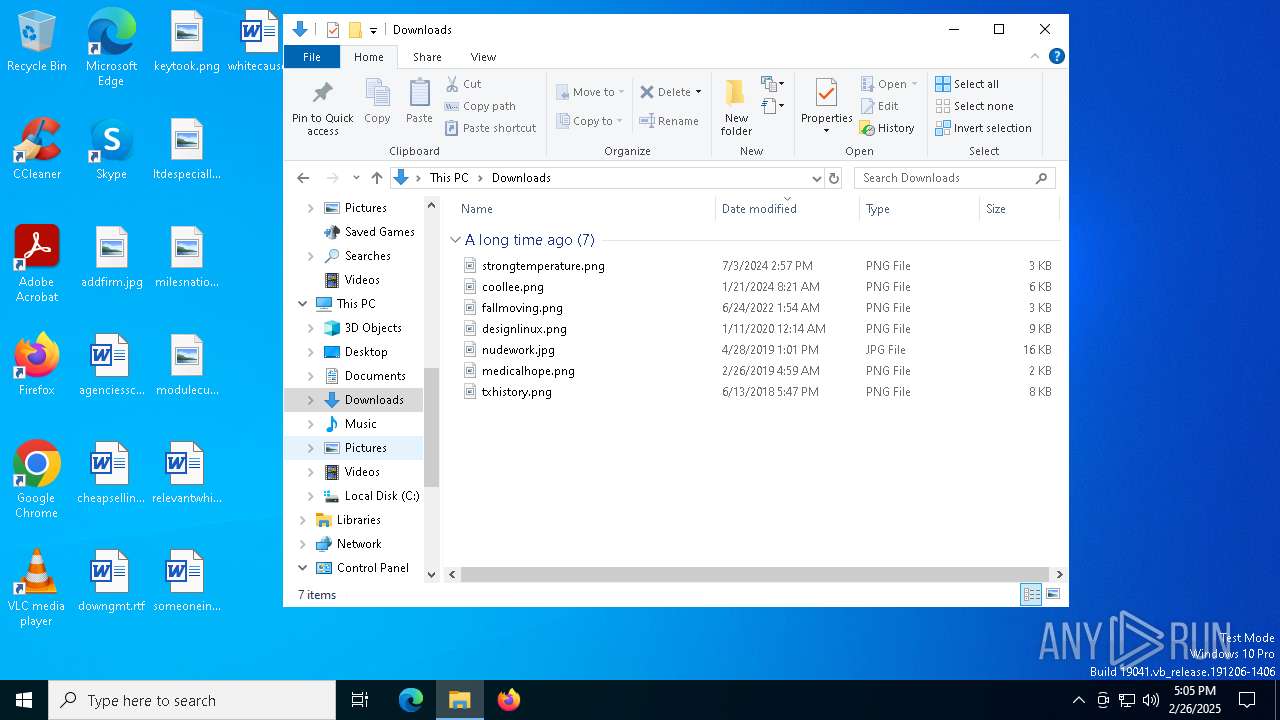
Actions looks like stealing of personal data
- setup.exe (PID: 7540)
Steals credentials from Web Browsers
- setup.exe (PID: 7540)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2196)
INFO
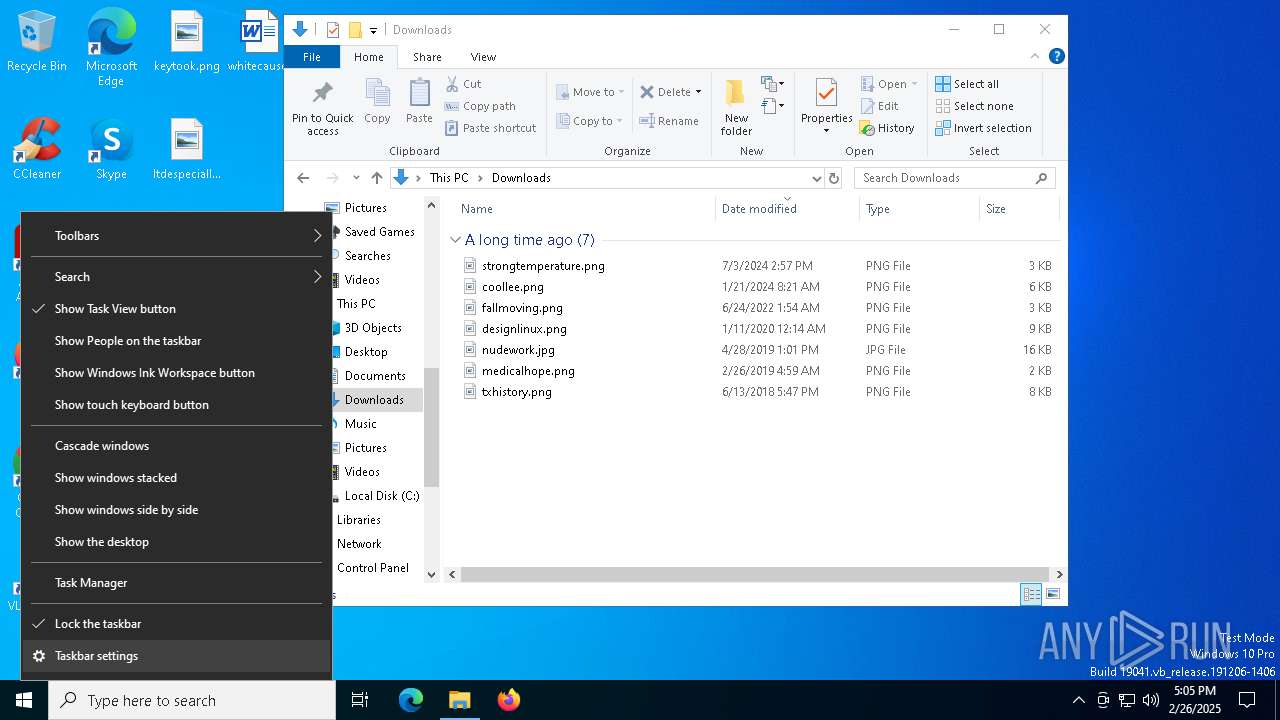
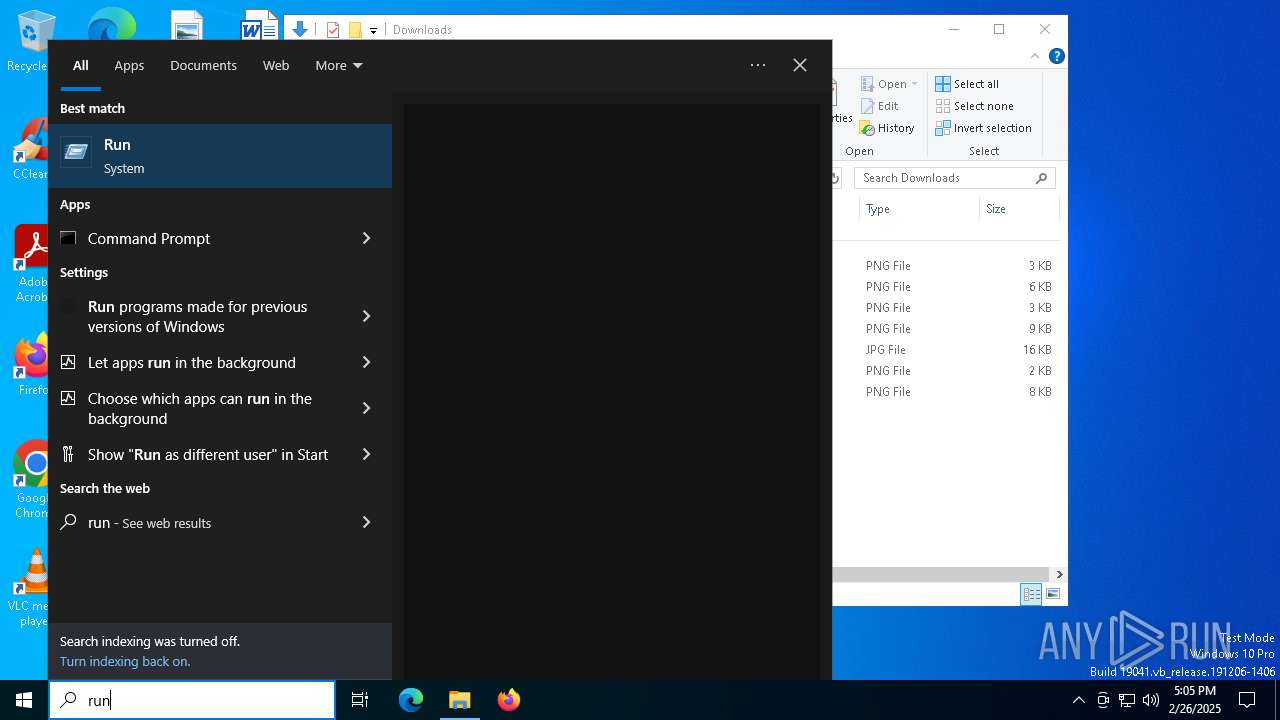
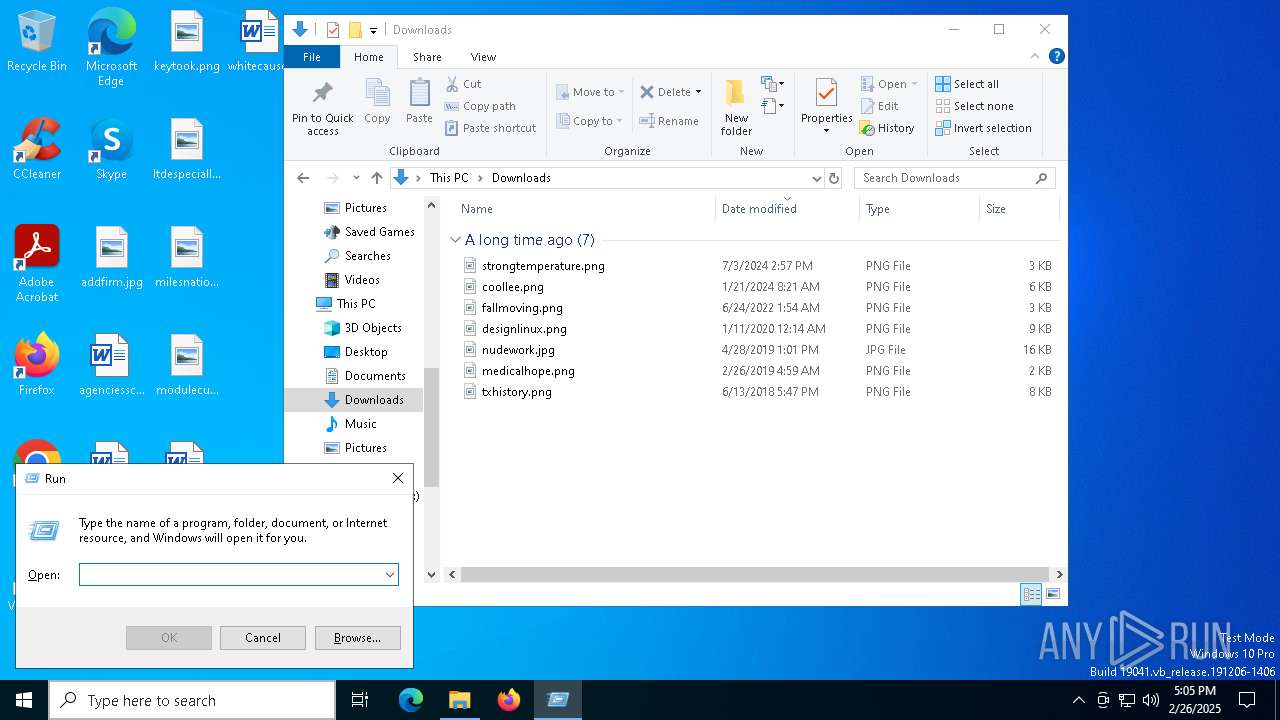
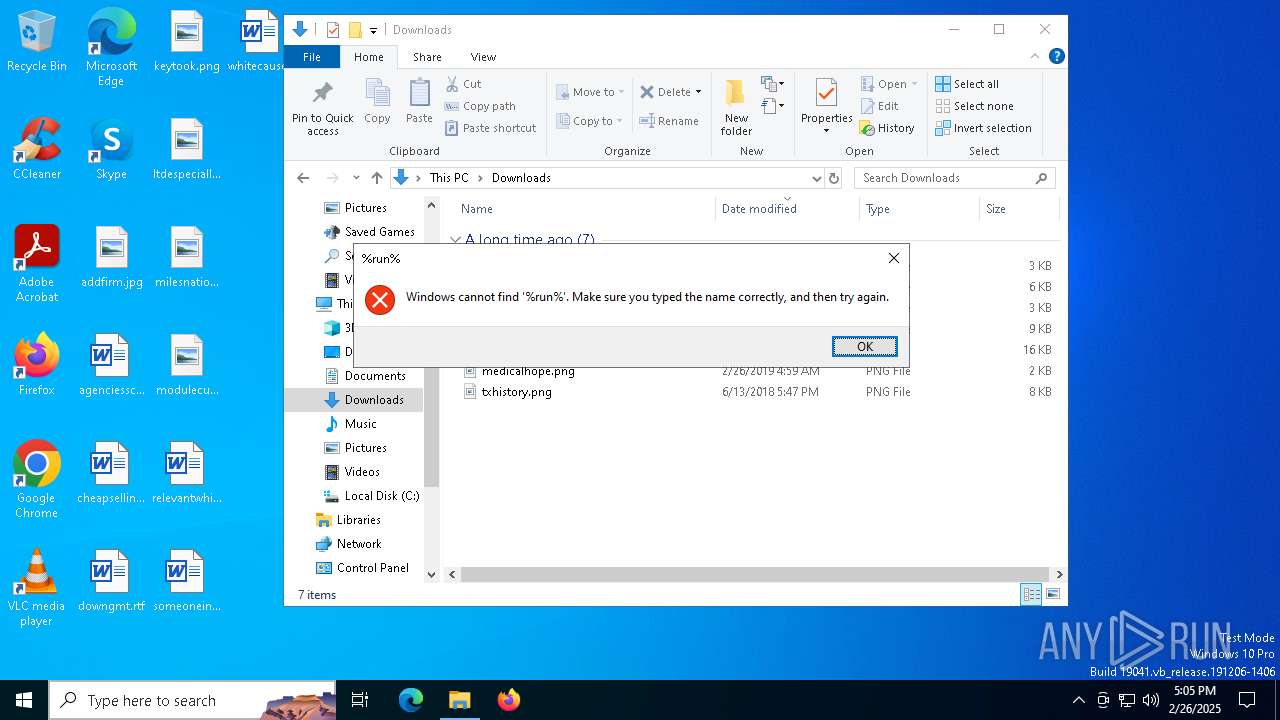
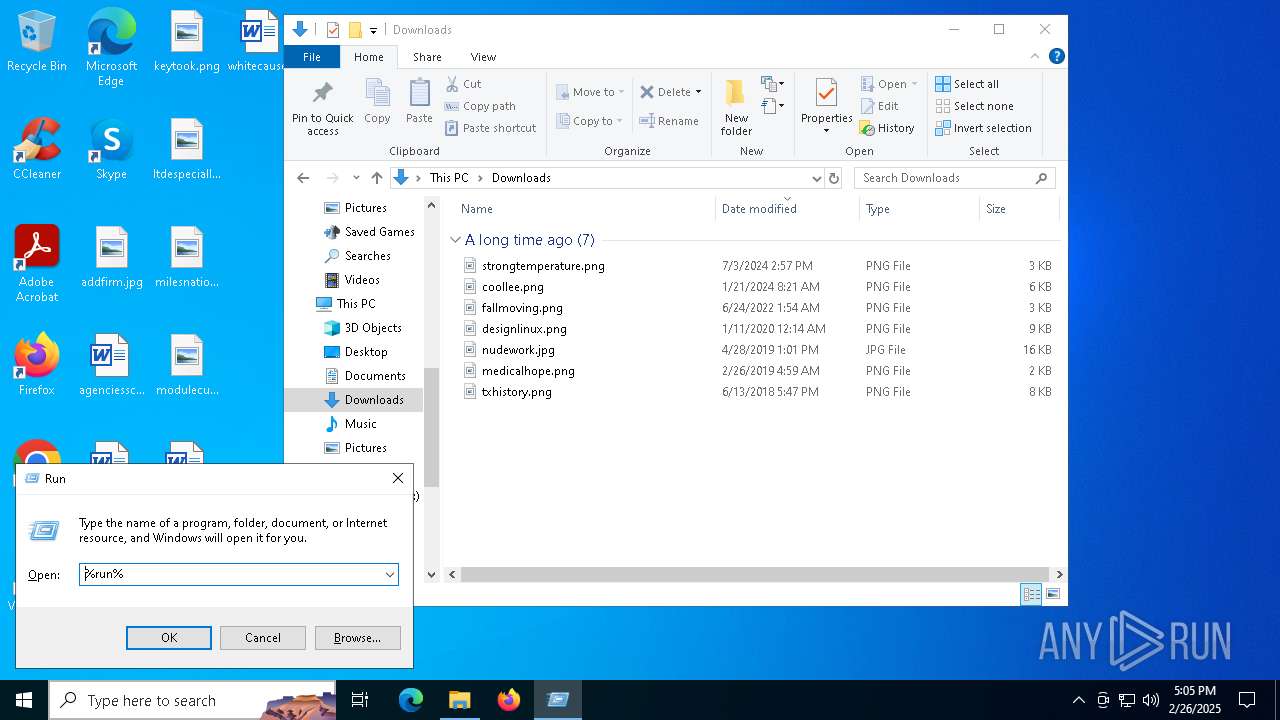
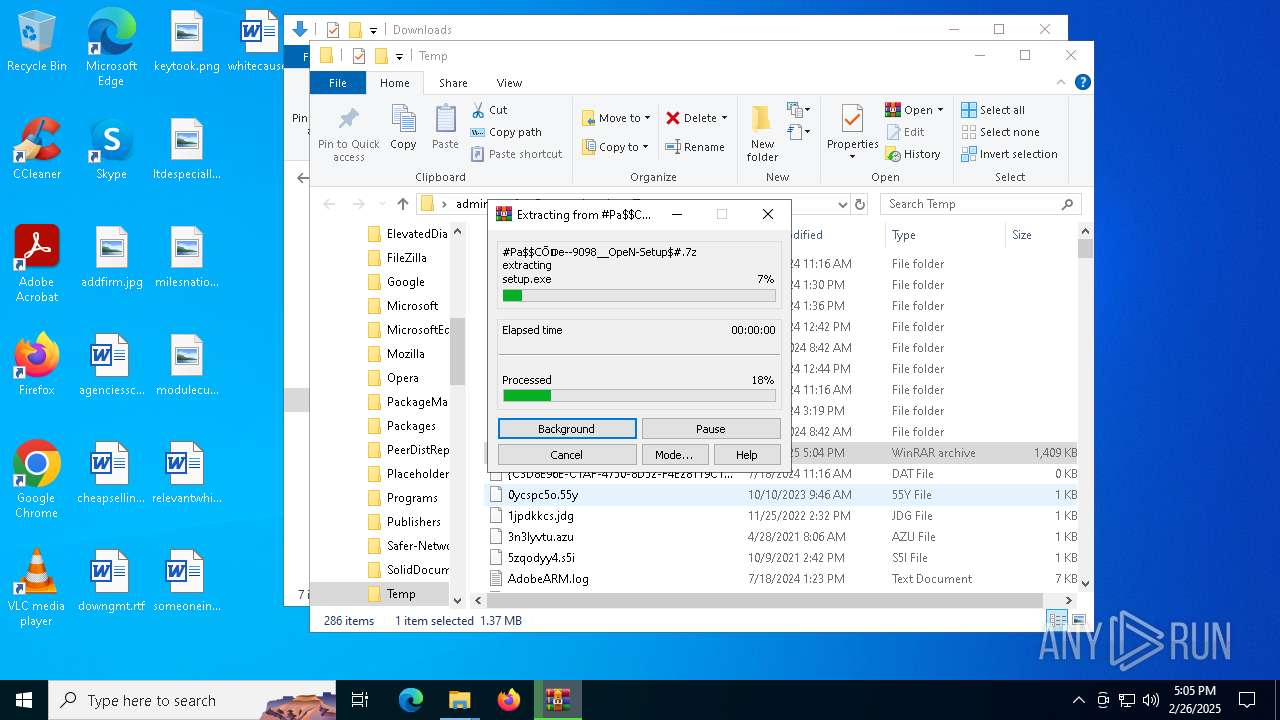
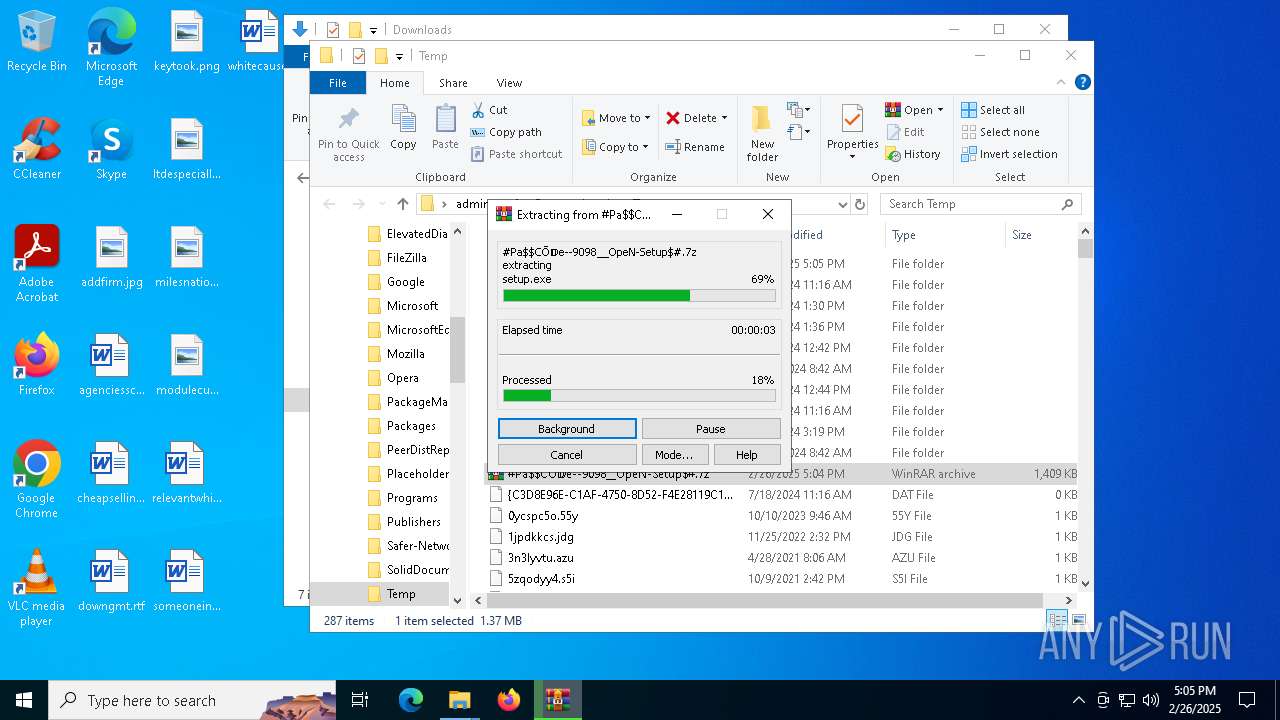
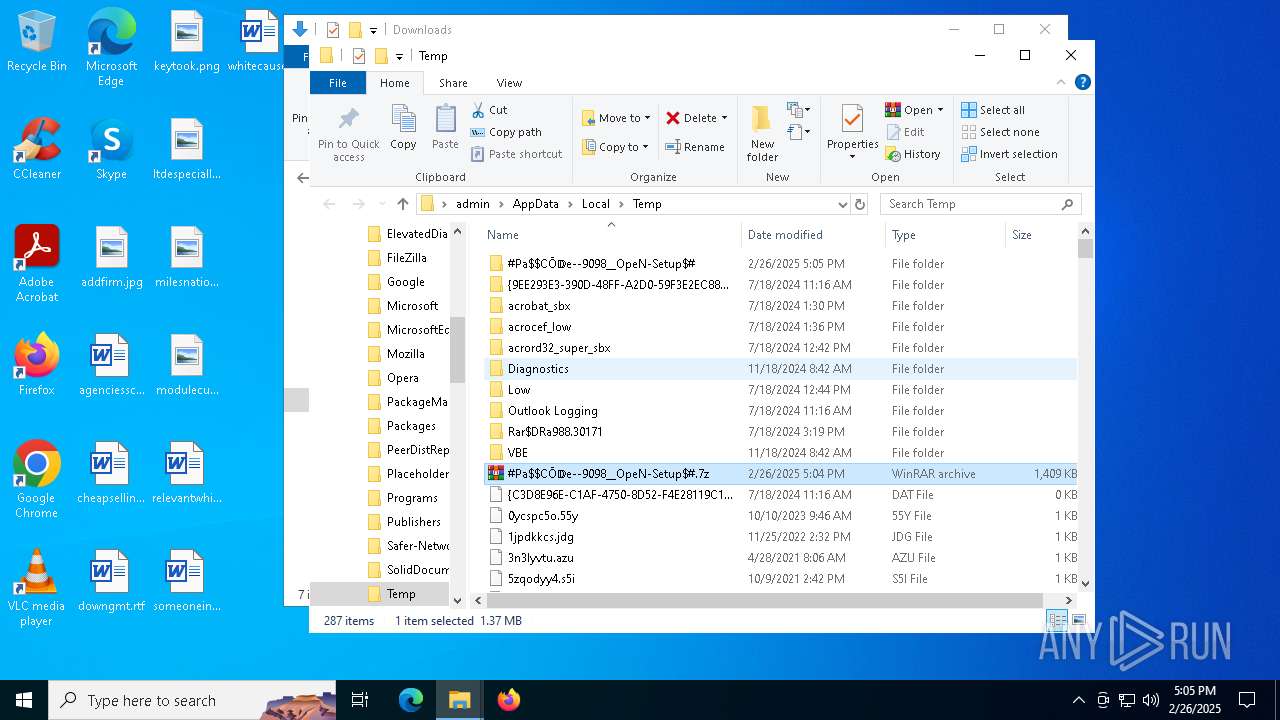
Manual execution by a user
- setup.exe (PID: 7540)
- WinRAR.exe (PID: 7452)
Creates files in the program directory
- setup.exe (PID: 7540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
136
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
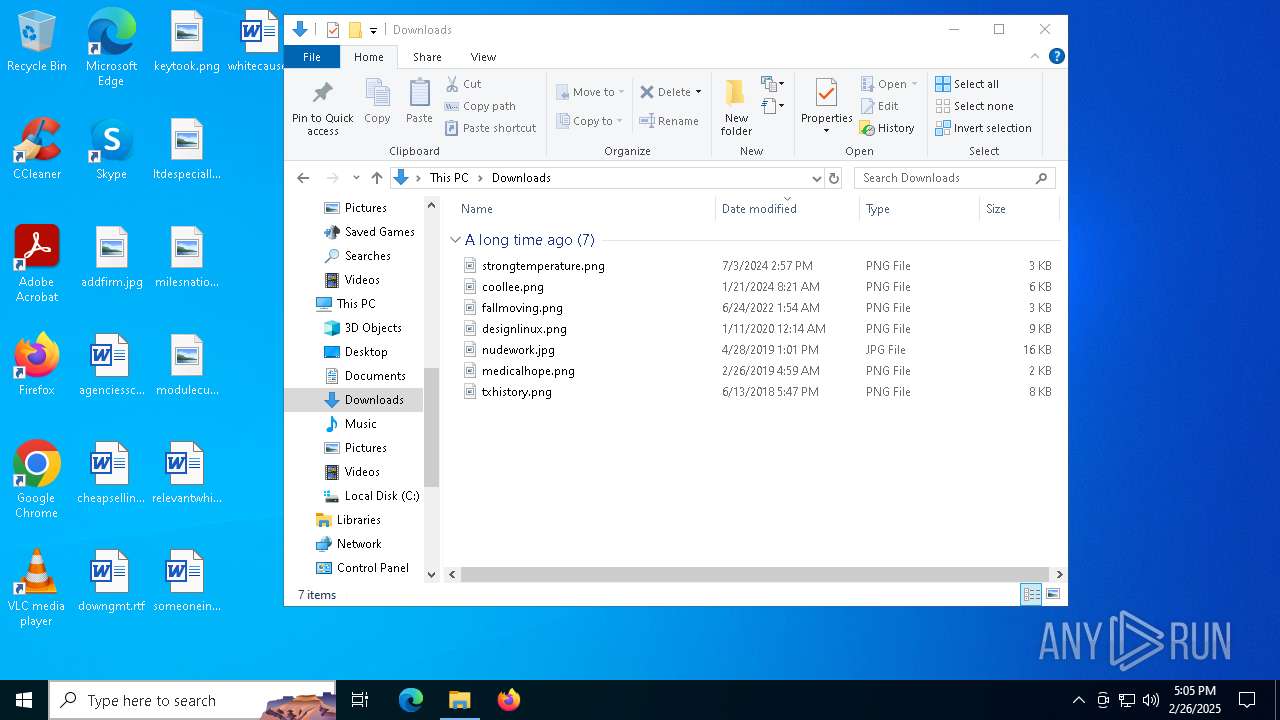
| 4776 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\#Pa$CŌ𝔻e--9098__OpeN-Setup$#.7z | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.91.0 Modules
| |||||||||||||||
| 7232 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7264 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
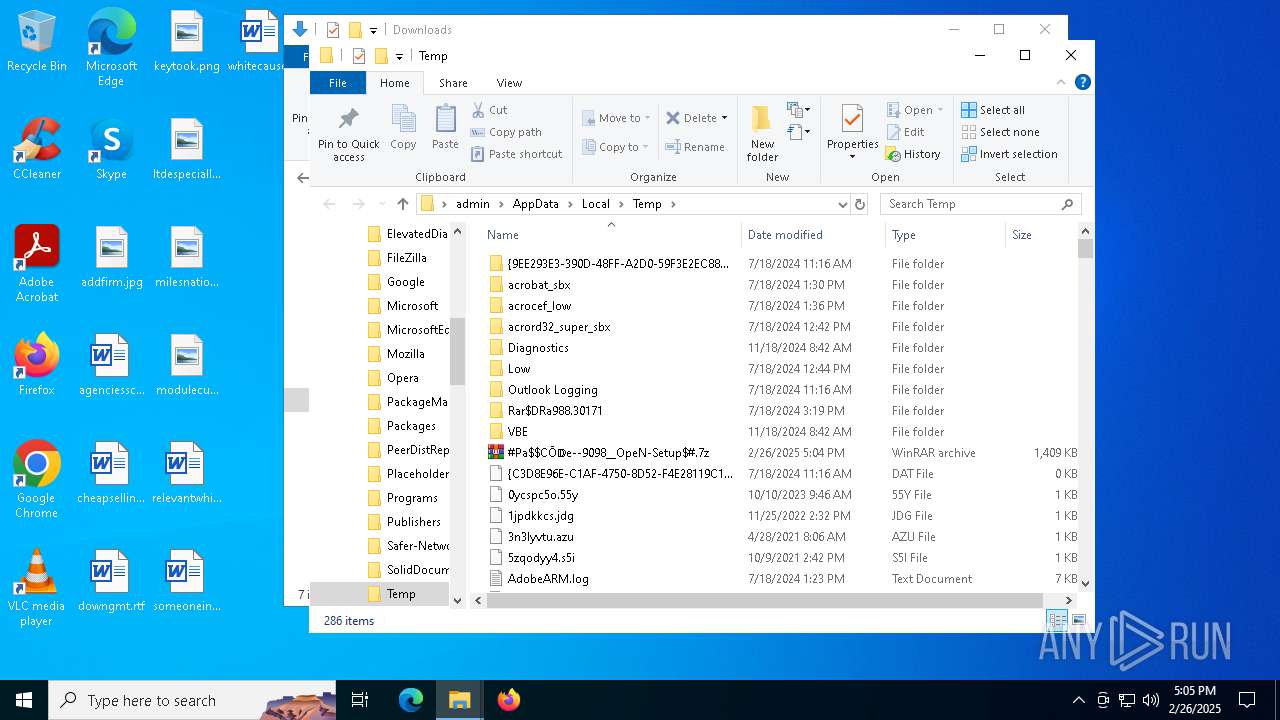
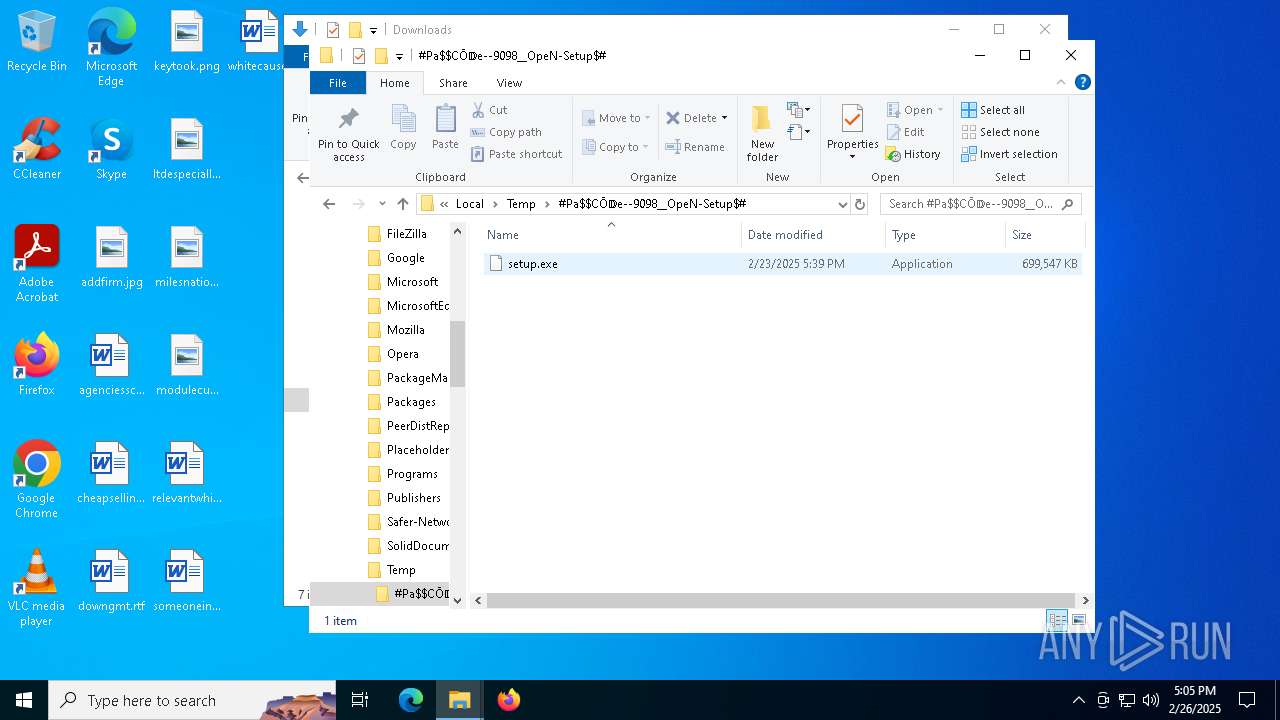
| 7452 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\AppData\Local\Temp\#Pa$CŌ𝔻e--9098__OpeN-Setup$#.7z" C:\Users\admin\AppData\Local\Temp\#Pa$CŌ𝔻e--9098__OpeN-Setup$#\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7540 | "C:\Users\admin\AppData\Local\Temp\#Pa$CŌ𝔻e--9098__OpeN-Setup$#\setup.exe" | C:\Users\admin\AppData\Local\Temp\#Pa$CŌ𝔻e--9098__OpeN-Setup$#\setup.exe | explorer.exe | ||||||||||||
User: admin Company: NCH Software Integrity Level: MEDIUM Description: Express Burn Disc Burning Software Version: 12.00 Modules
| |||||||||||||||
| 7584 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7716 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 821
Read events
2 809
Write events
12
Delete events
0
Modification events
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_0 |
Value: 4C000000730100000402000000000000F0F0F00000000000000000000000000000000000000000000C03060000000000000000003B000000B402000000000000000000000000000001000000 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_1 |
Value: 4C000000730100000500000000000000F0F0F0000000000000000000000000000000000000000000E20205000000000000000000180000002A00000000000000000000000000000002000000 | |||
| (PID) Process: | (4776) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band76_2 |
Value: 4C000000730100000400000000000000F0F0F00000000000000000000000000000000000000000008C0205000000000000000000180000006400000000000000000000000000000003000000 | |||
| (PID) Process: | (7452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (7452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7452) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
Executable files
0
Suspicious files
12
Text files
0
Unknown types
1
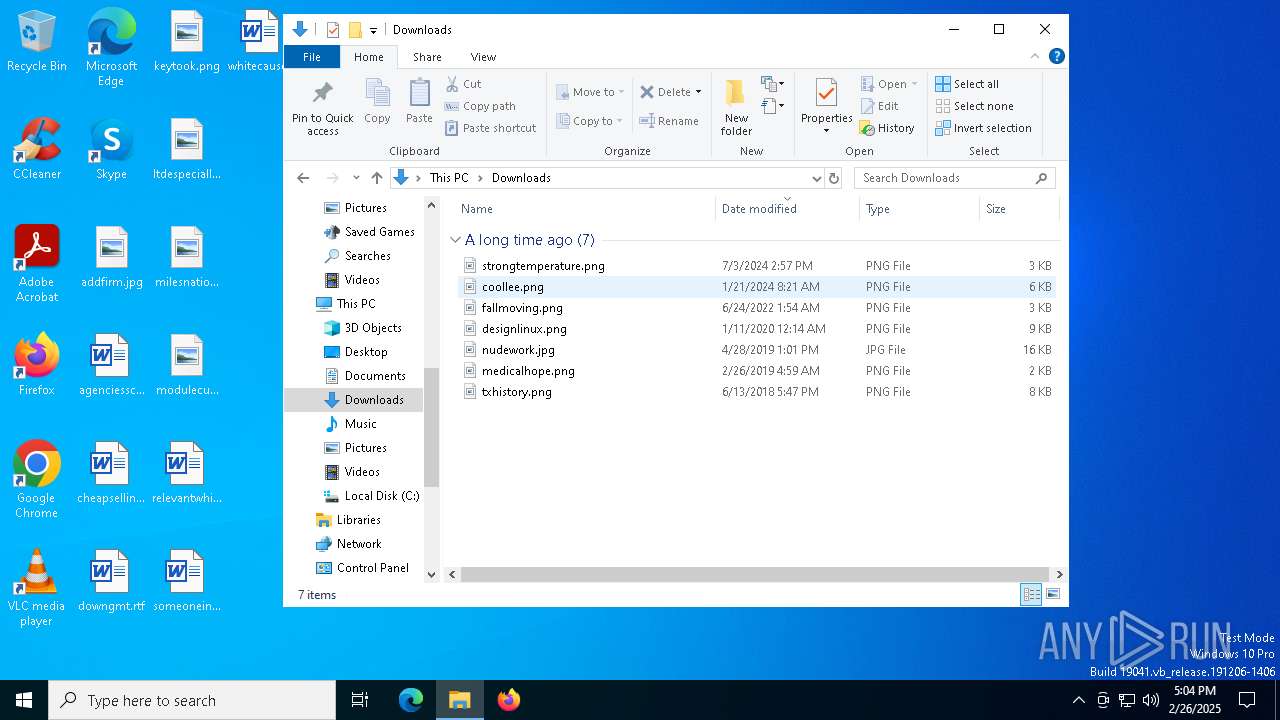
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7452 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\#Pa$CŌ𝔻e--9098__OpeN-Setup$#\setup.exe | — | |
MD5:— | SHA256:— | |||
| 7540 | setup.exe | C:\ProgramData\78223E18827A862E.dat | — | |
MD5:— | SHA256:— | |||
| 7540 | setup.exe | C:\ProgramData\683D093AD66A84CE.dat | binary | |
MD5:FDDE63730E15DD2E18C540BA52B6A945 | SHA256:40740EAABD14FC0E08D3B5EE340C1E1B372E158F61EF58AEED1EE4B3A3F4492E | |||
| 7540 | setup.exe | C:\ProgramData\A538FC05D86AF159.dat | binary | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 7540 | setup.exe | C:\ProgramData\3A30B4EB1753480C.dat | binary | |
MD5:0B2213BCE3950F1E95FEEB8E8B3B9543 | SHA256:71DB3D87713A320BA9FD3043392509B430630CFCF574EE84118406D6471CFC5A | |||
| 7540 | setup.exe | C:\ProgramData\78877E4385FAC031.dat | binary | |
MD5:06AD9E737639FDC745B3B65312857109 | SHA256:C8925892CA8E213746633033AE95ACFB8DD9531BC376B82066E686AC6F40A404 | |||
| 7540 | setup.exe | C:\ProgramData\380FF82436007BA1.dat | sqlite | |
MD5:A45465CDCDC6CB30C8906F3DA4EC114C | SHA256:4412319EF944EBCCA9581CBACB1D4E1DC614C348D1DFC5D2FAAAAD863D300209 | |||
| 7540 | setup.exe | C:\ProgramData\446F4240510913BA.dat | binary | |
MD5:F6C33AC5E1032A0873BE7BFC65169287 | SHA256:D97895CEDED32E33D57BDCACCDBE144E58AA87AF4D2F8855D630286CE30A8D83 | |||
| 7540 | setup.exe | C:\ProgramData\DF7516BE6EE30051.dat | binary | |
MD5:46D9FCA6032297F8AEE08D73418312BA | SHA256:865856FA4C33C4AEE52E15FBB370B6611468FE947E76E197F0E50D0AD62CB1B4 | |||
| 7540 | setup.exe | C:\ProgramData\43DA8C1ECB20225C.dat | binary | |
MD5:29A644B1F0D96166A05602FE27B3F4AD | SHA256:BF96902FEB97E990A471492F78EE8386BCF430D66BDAEFDEAFBF912C8CF7CE46 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
35
DNS requests
28
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8132 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8132 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3008 | backgroundTaskHost.exe | 2.23.227.208:443 | www.bing.com | Ooredoo Q.S.C. | QA | whitelisted |
2040 | backgroundTaskHost.exe | 20.223.35.26:443 | fd.api.iris.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2924 | SearchApp.exe | 184.86.251.24:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
8132 | SIHClient.exe | 4.245.163.56:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (uncertainyelemz .bet) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (hobbyedsmoker .live) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (dsfljsdfjewf .info) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (subawhipnator .life) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (deaddereaste .today) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (decreaserid .world) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (pastedeputten .life) |
2196 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (privileggoe .live) |