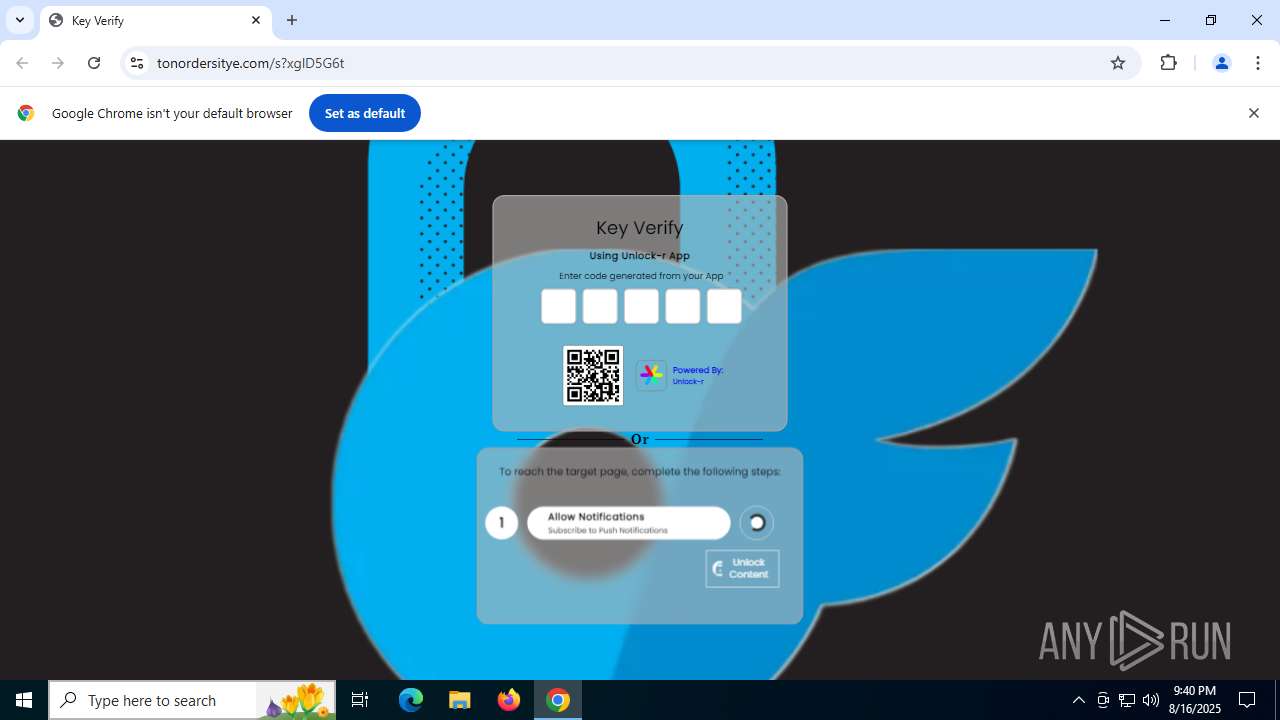
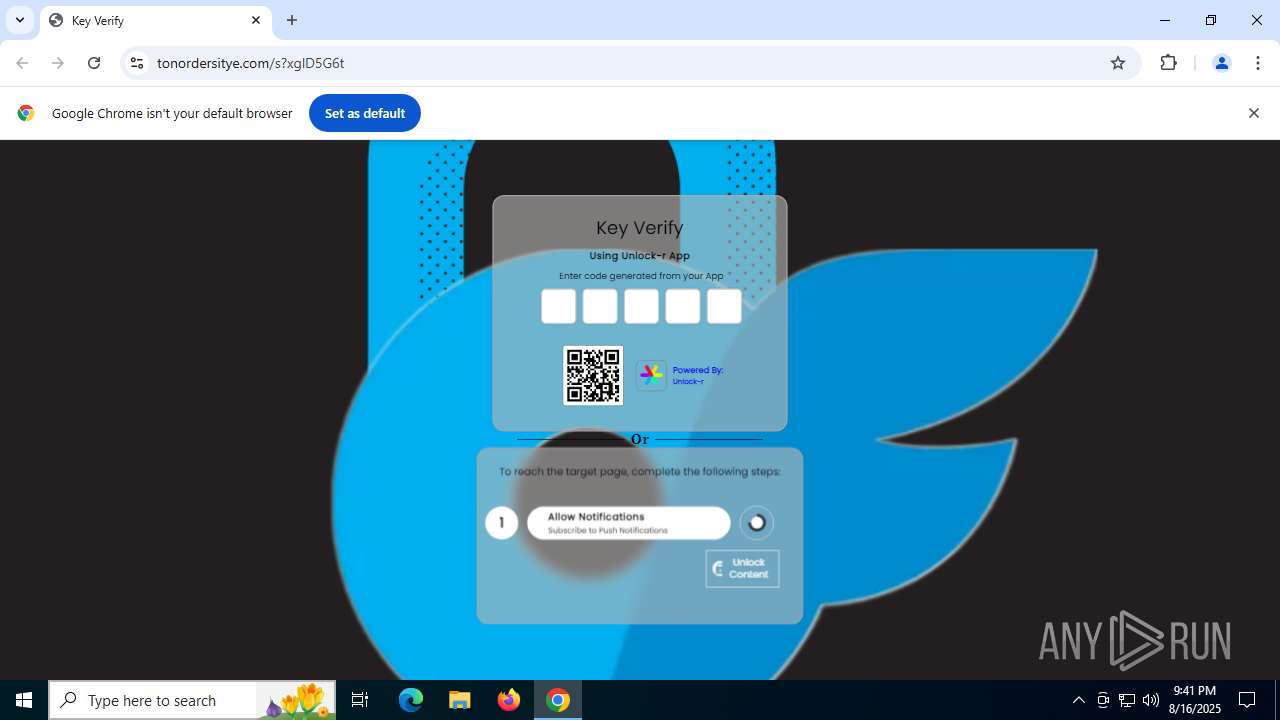
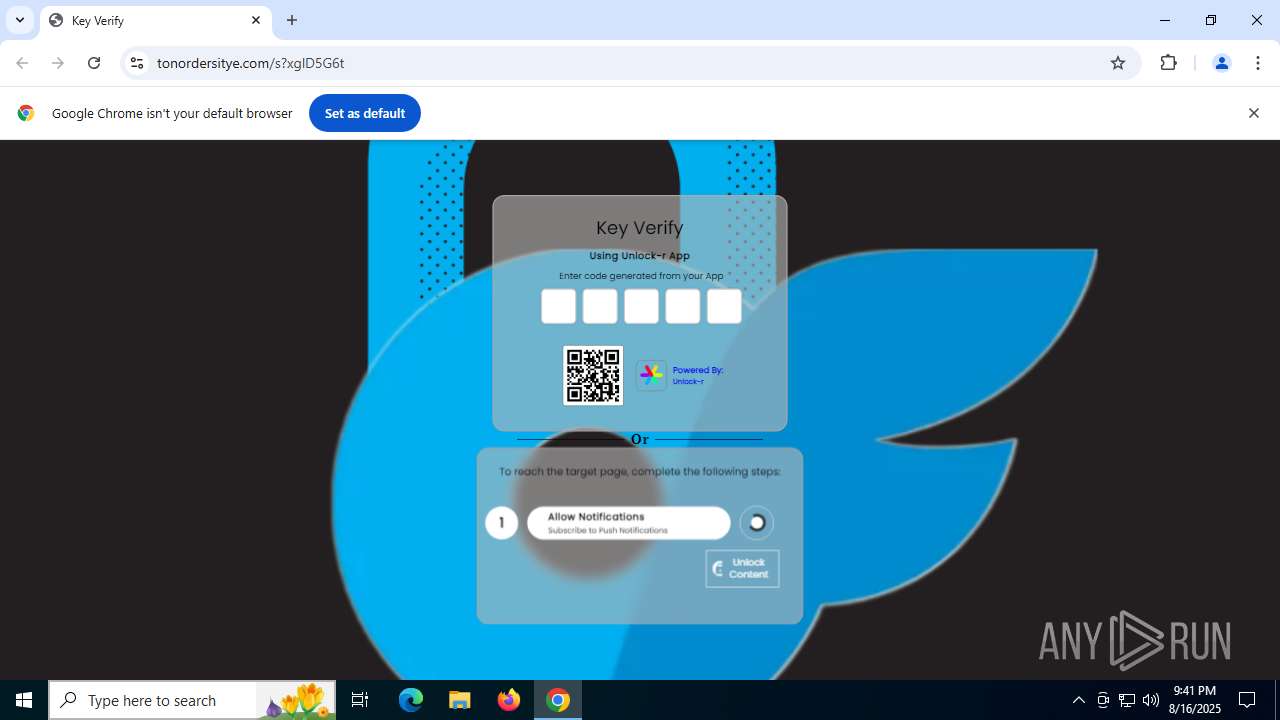
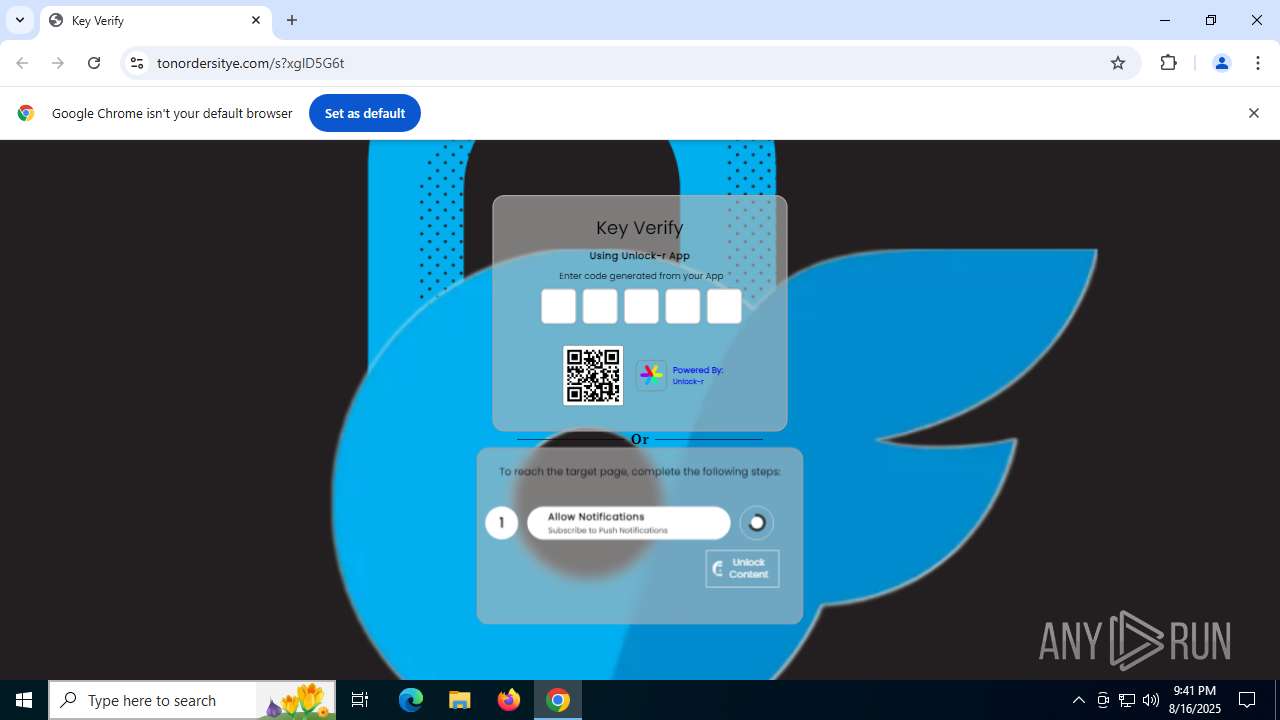
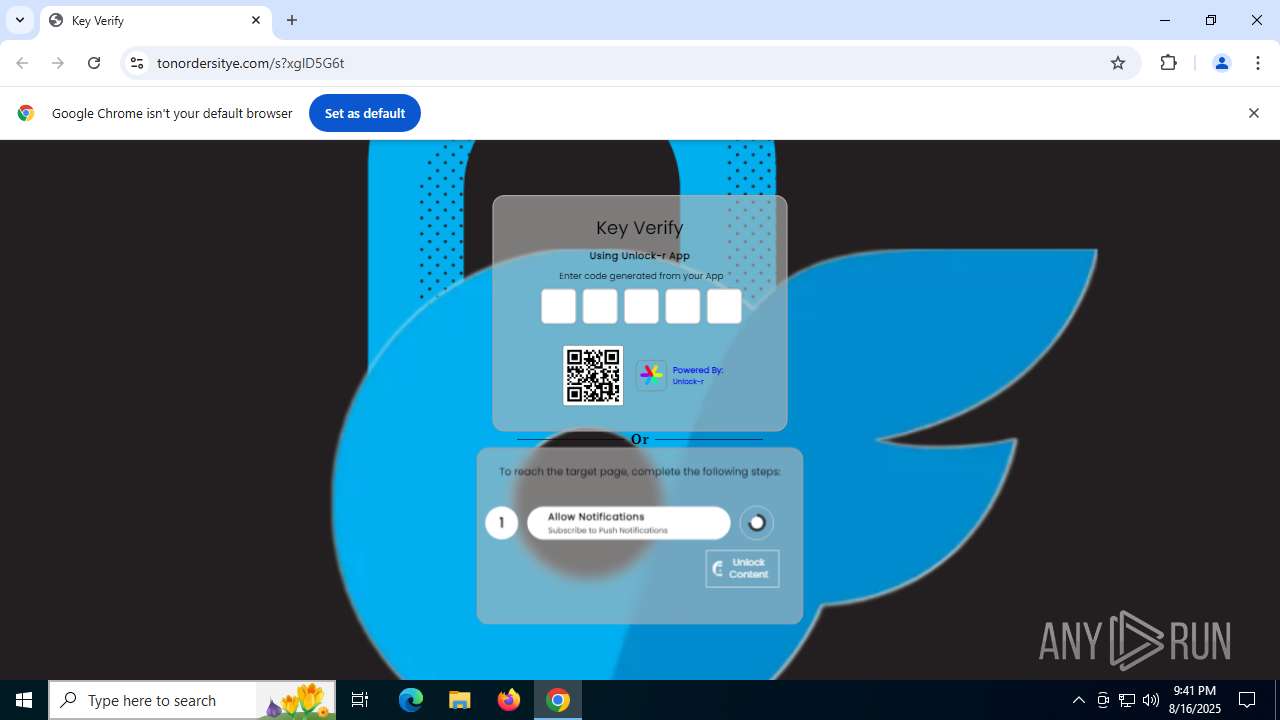
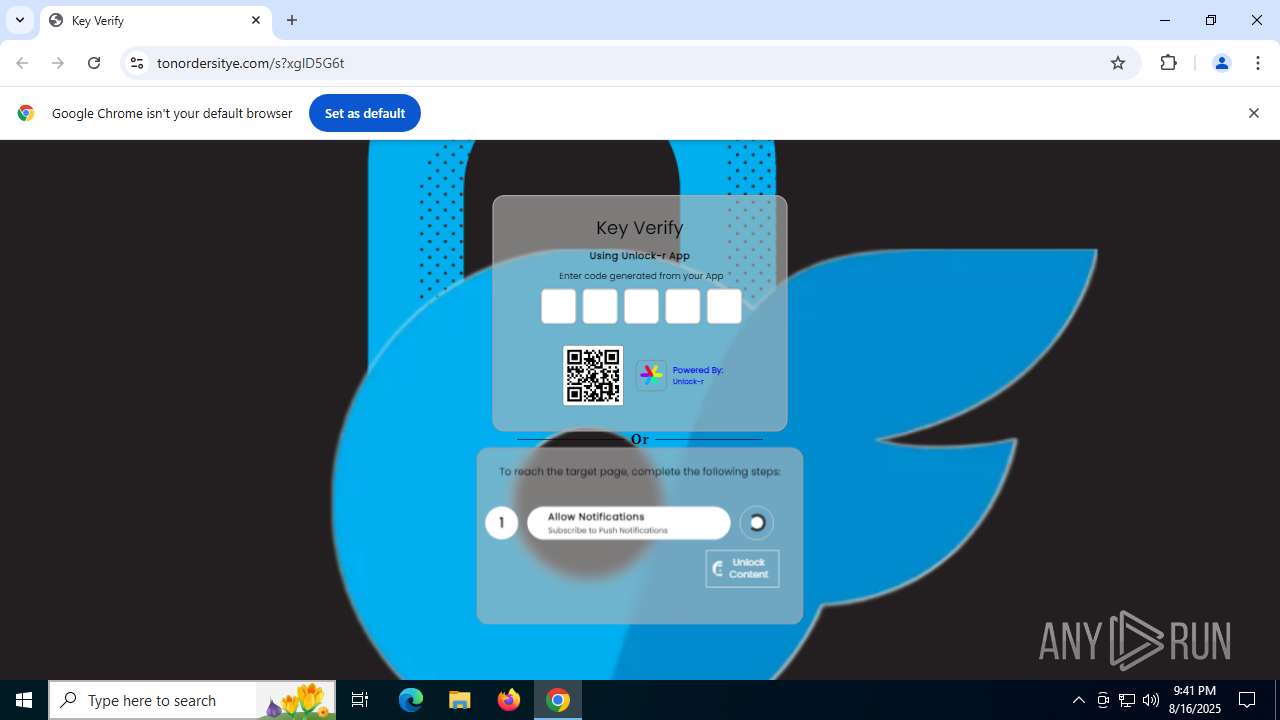
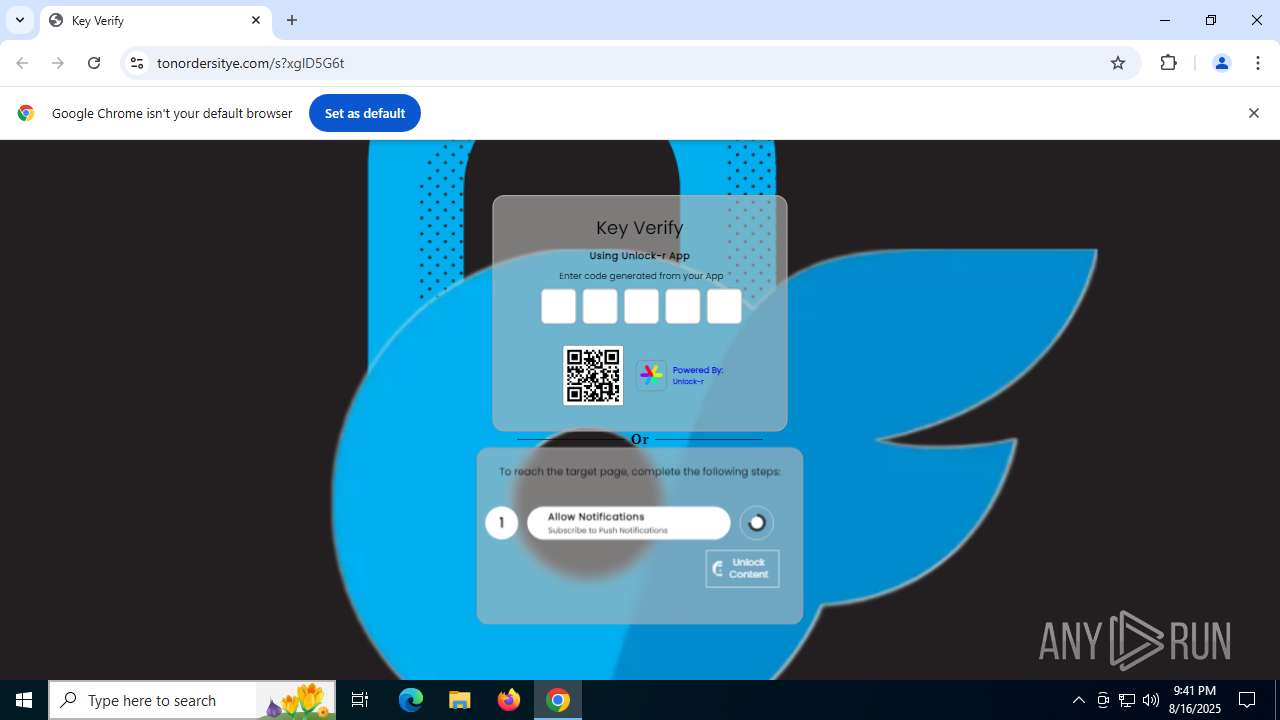
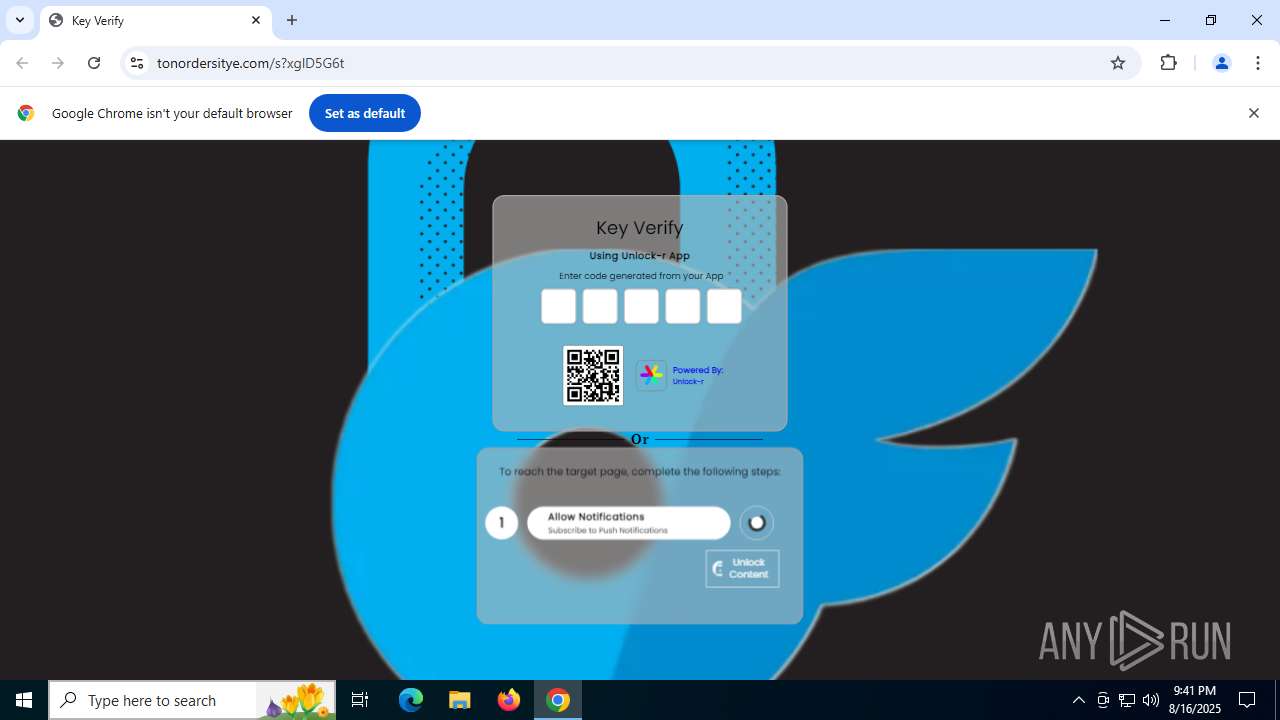
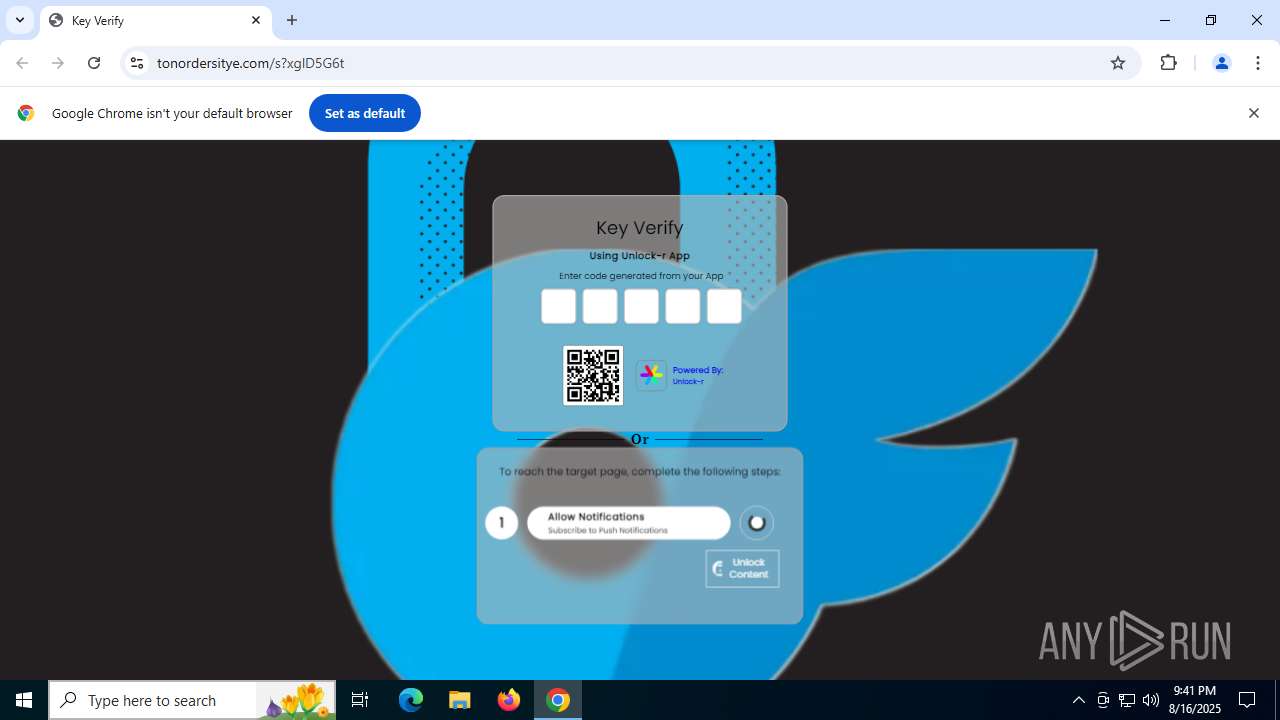
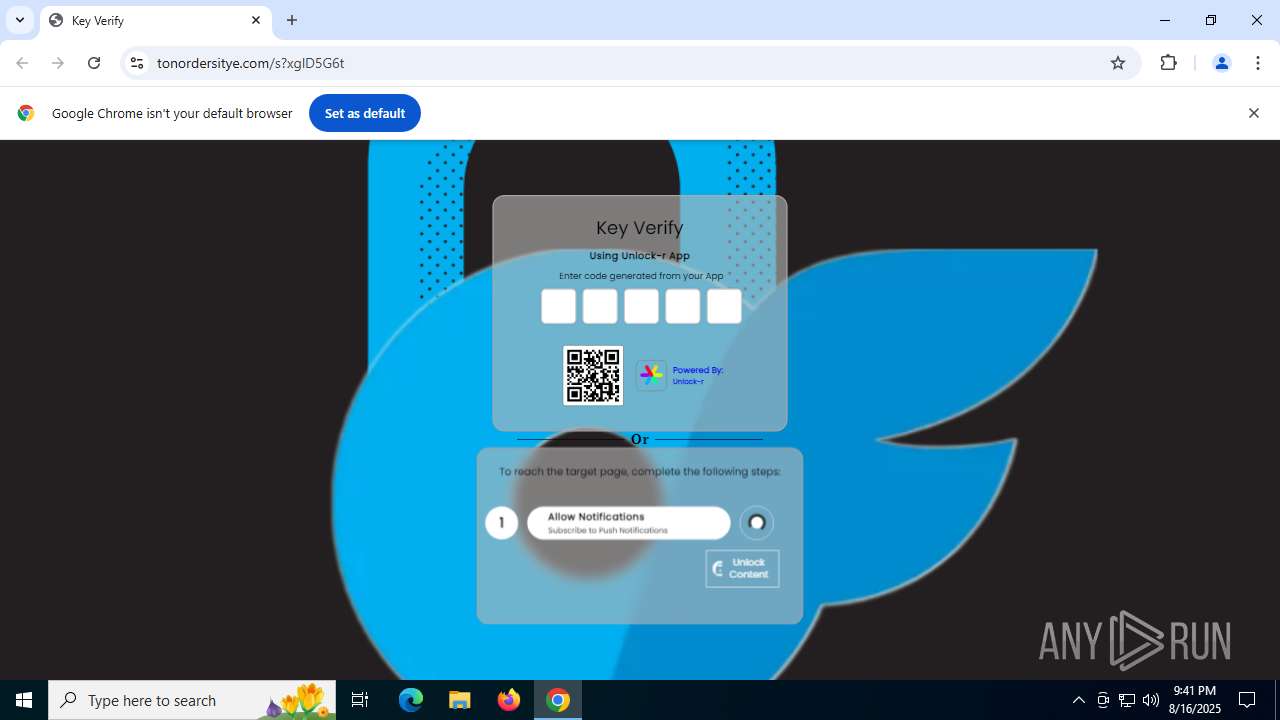
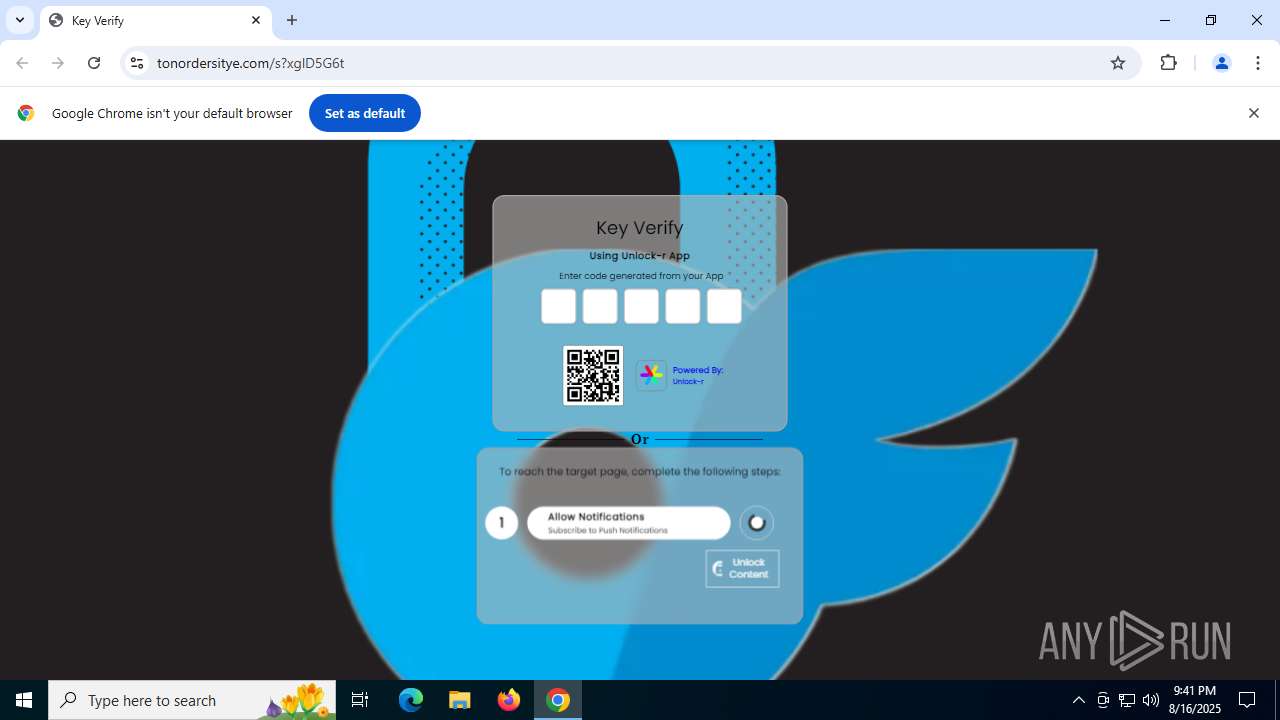
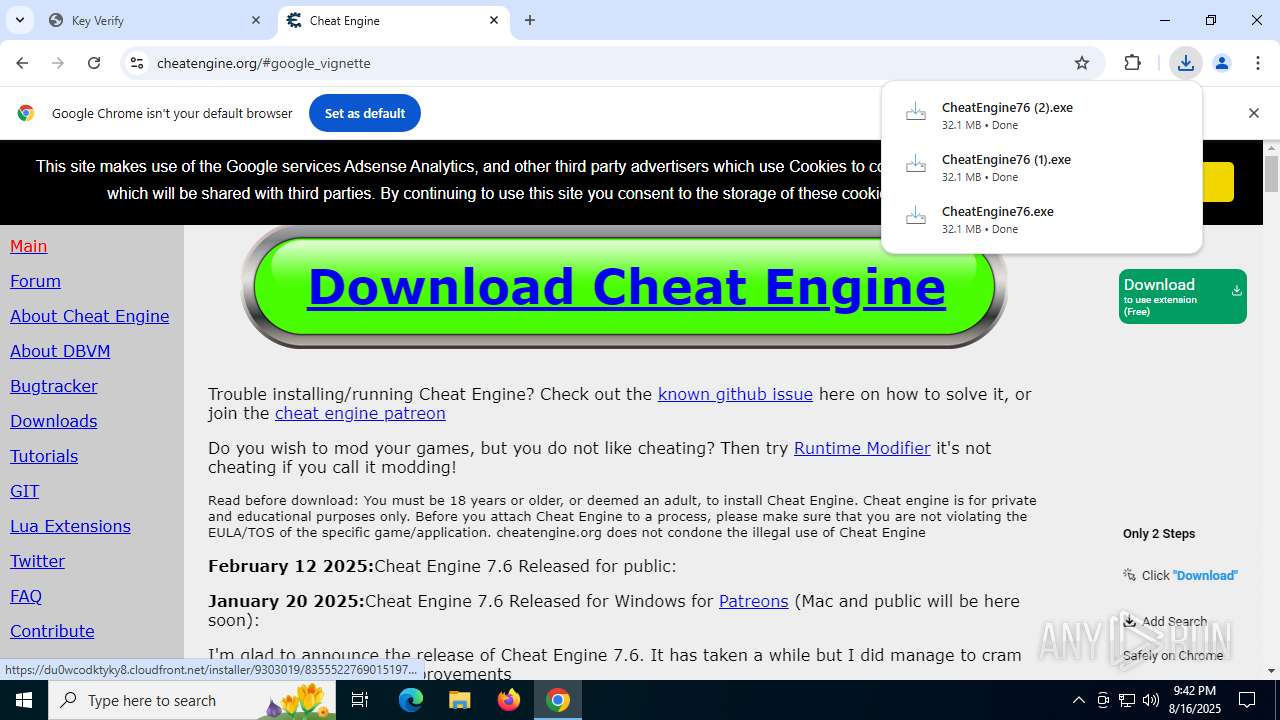
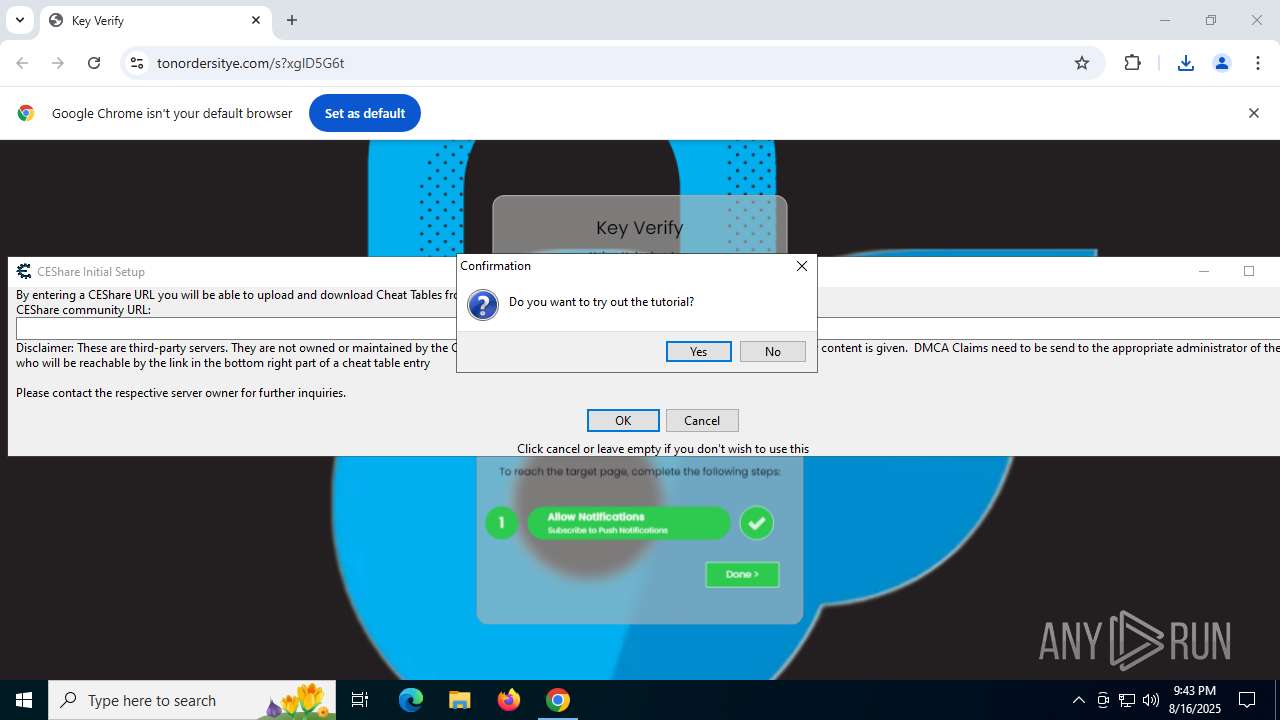
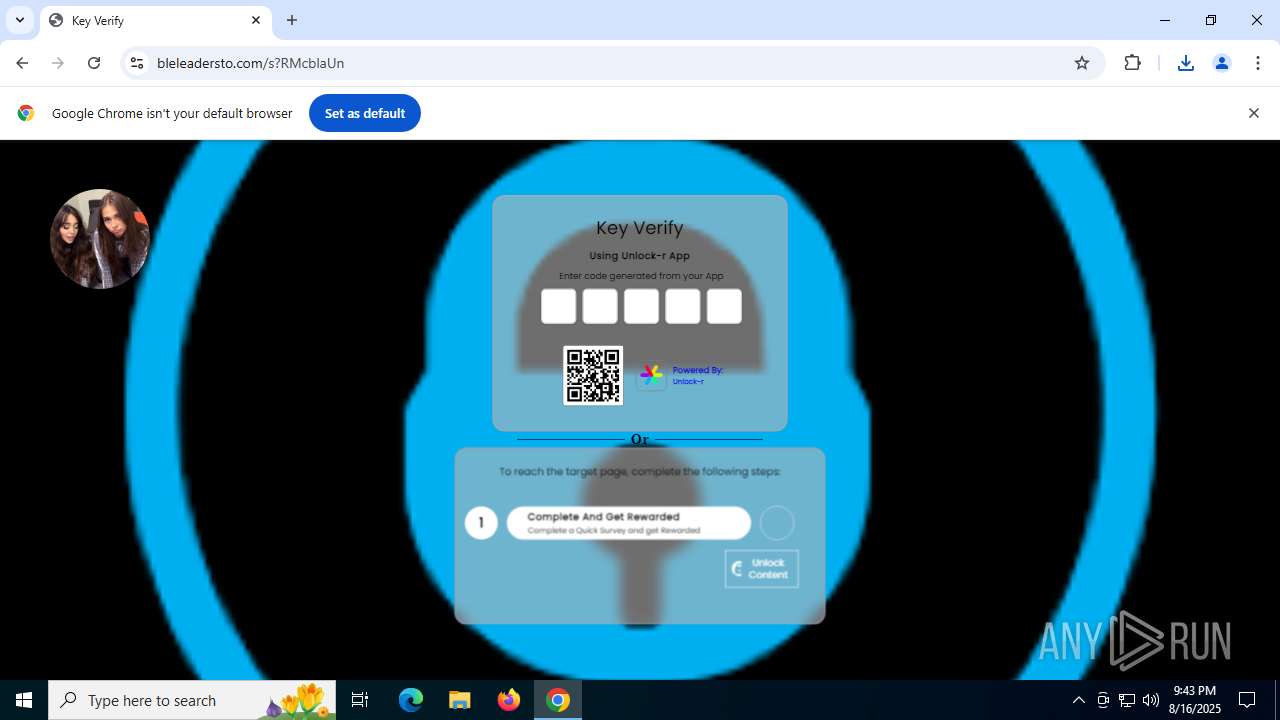
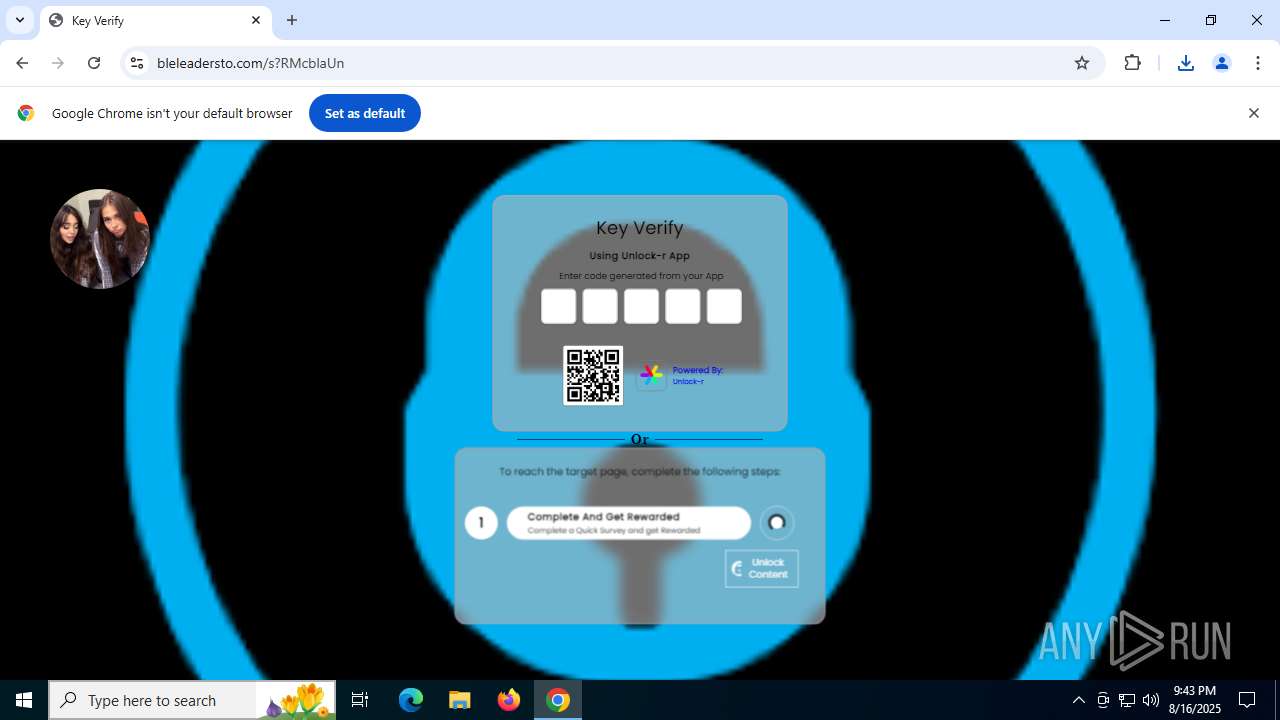
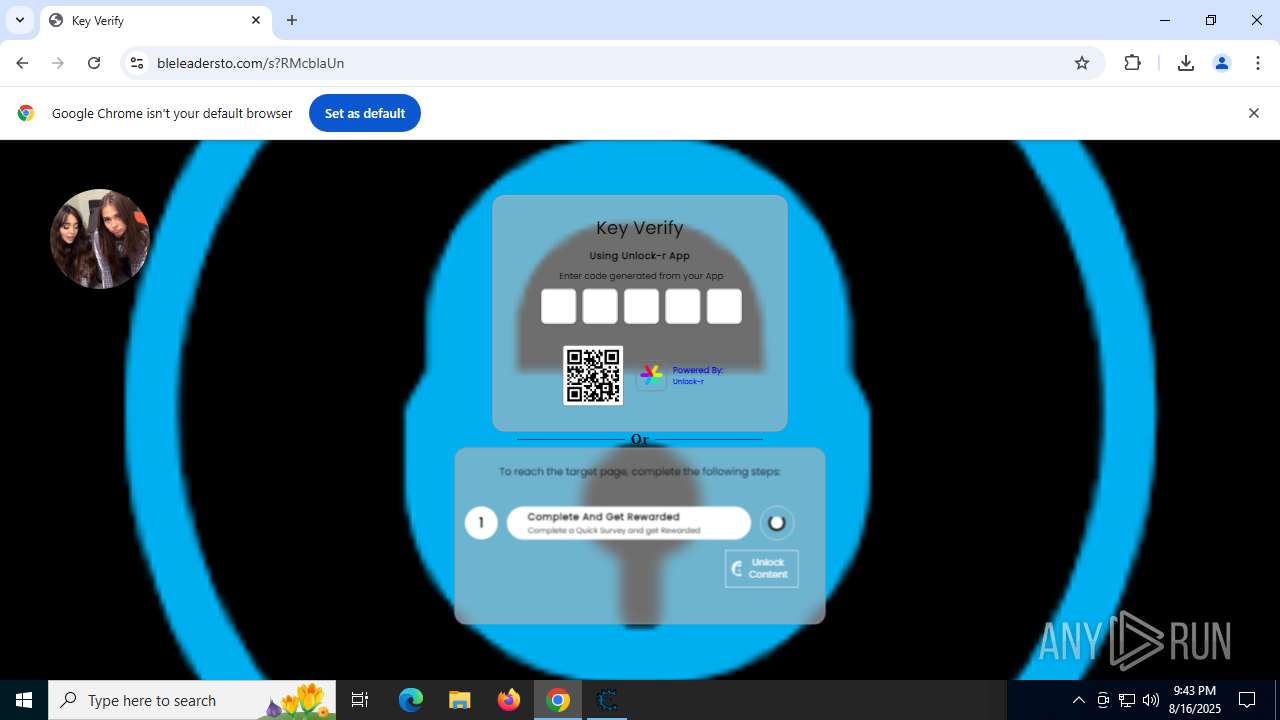
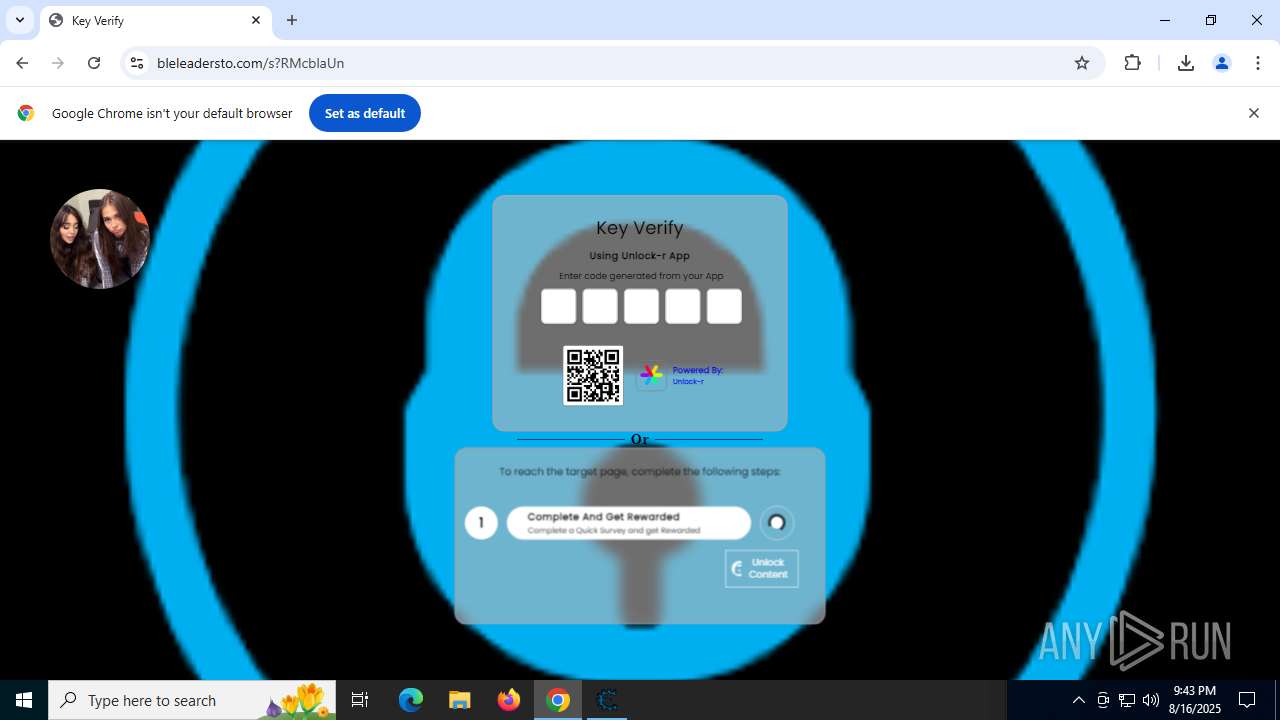
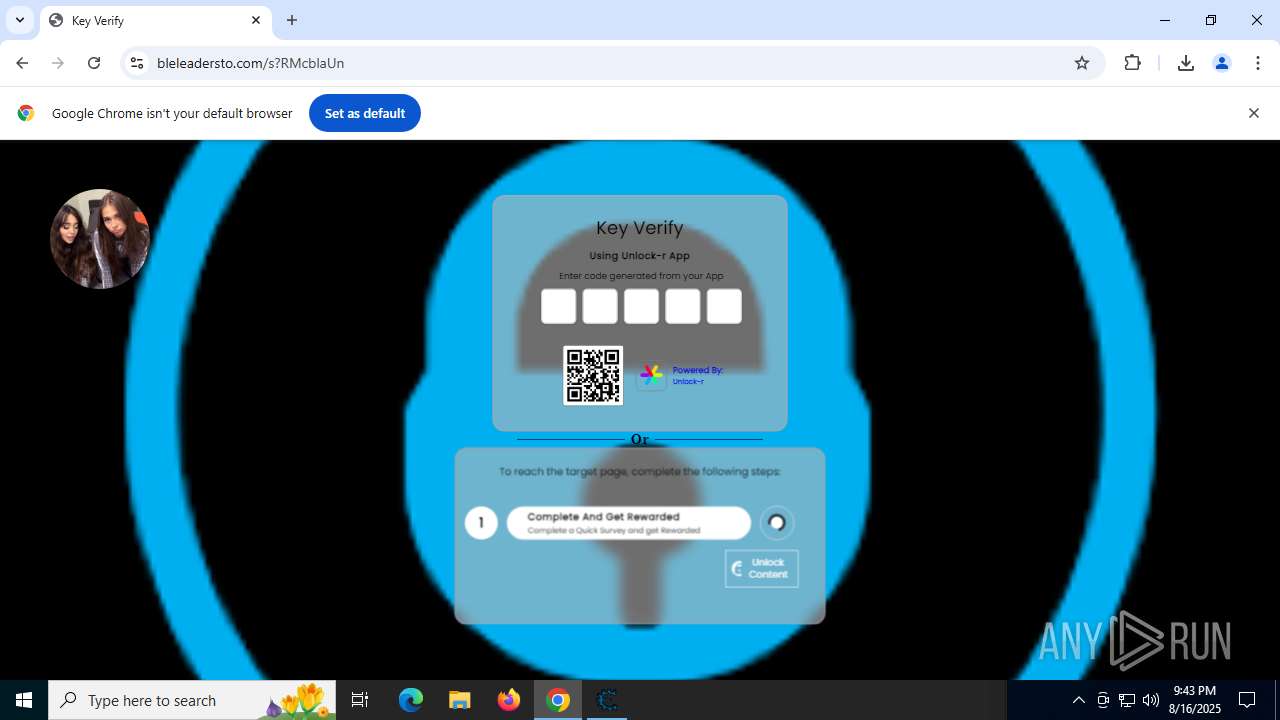
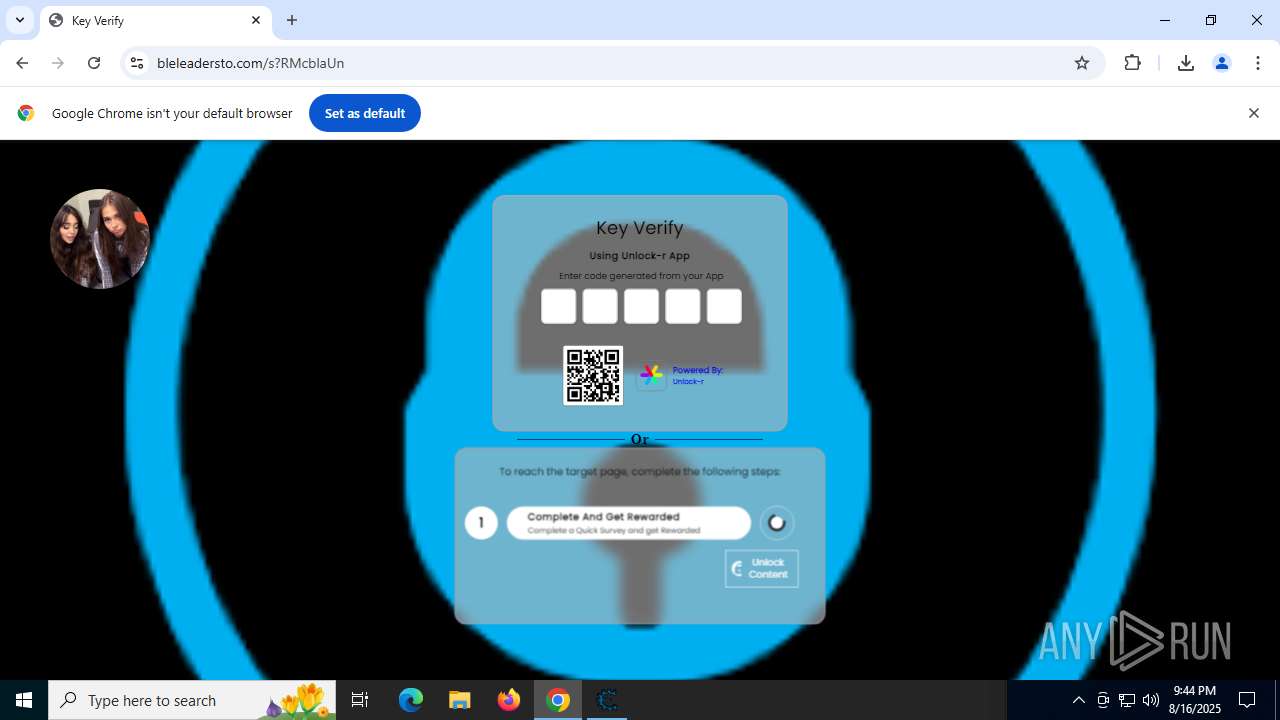
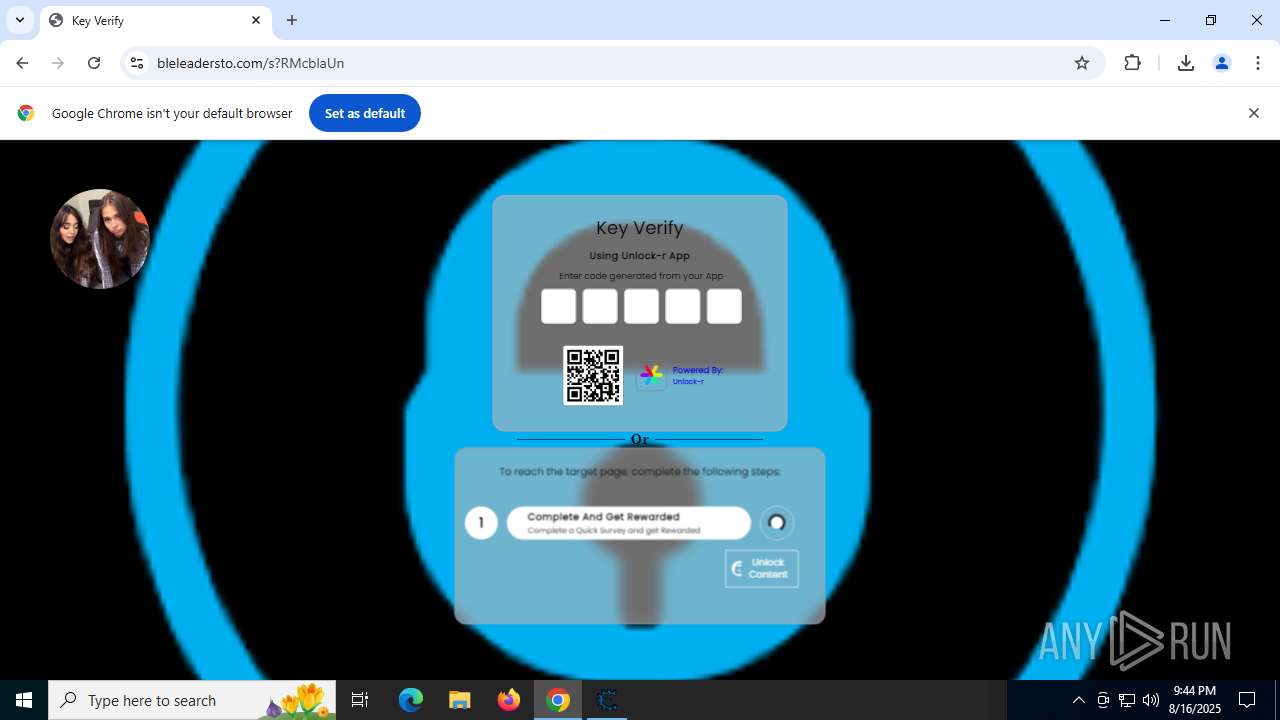
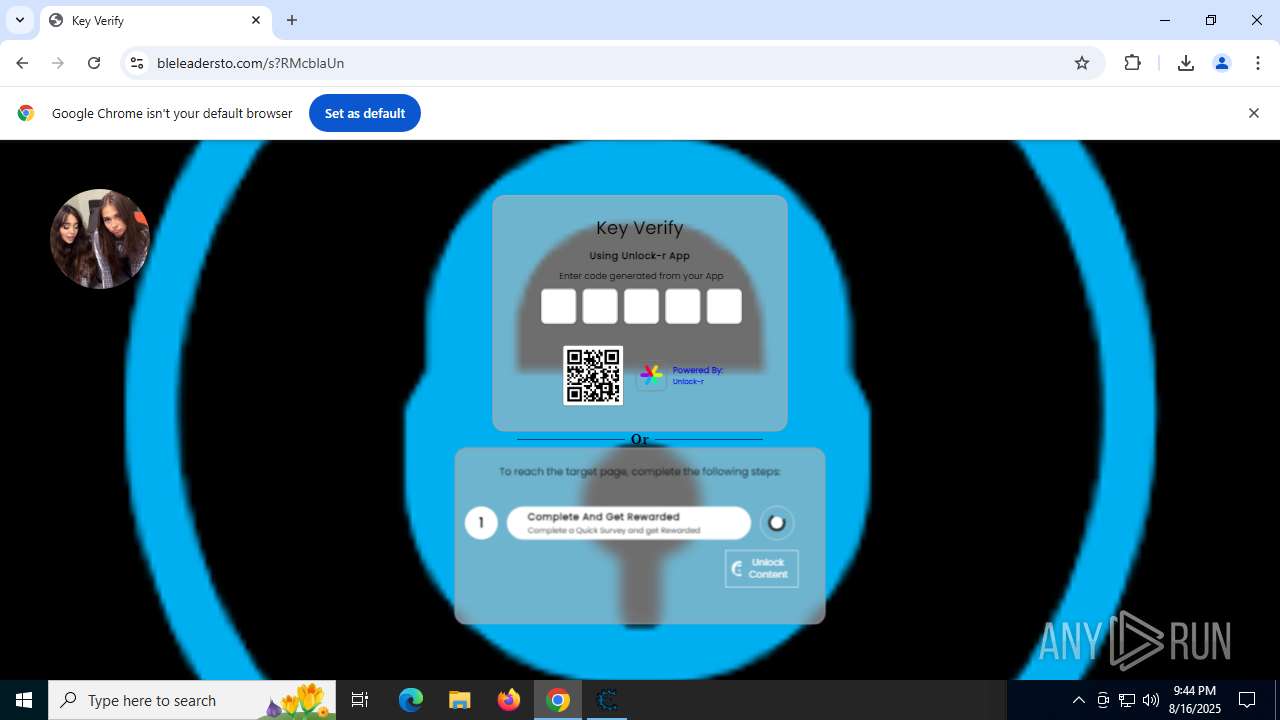
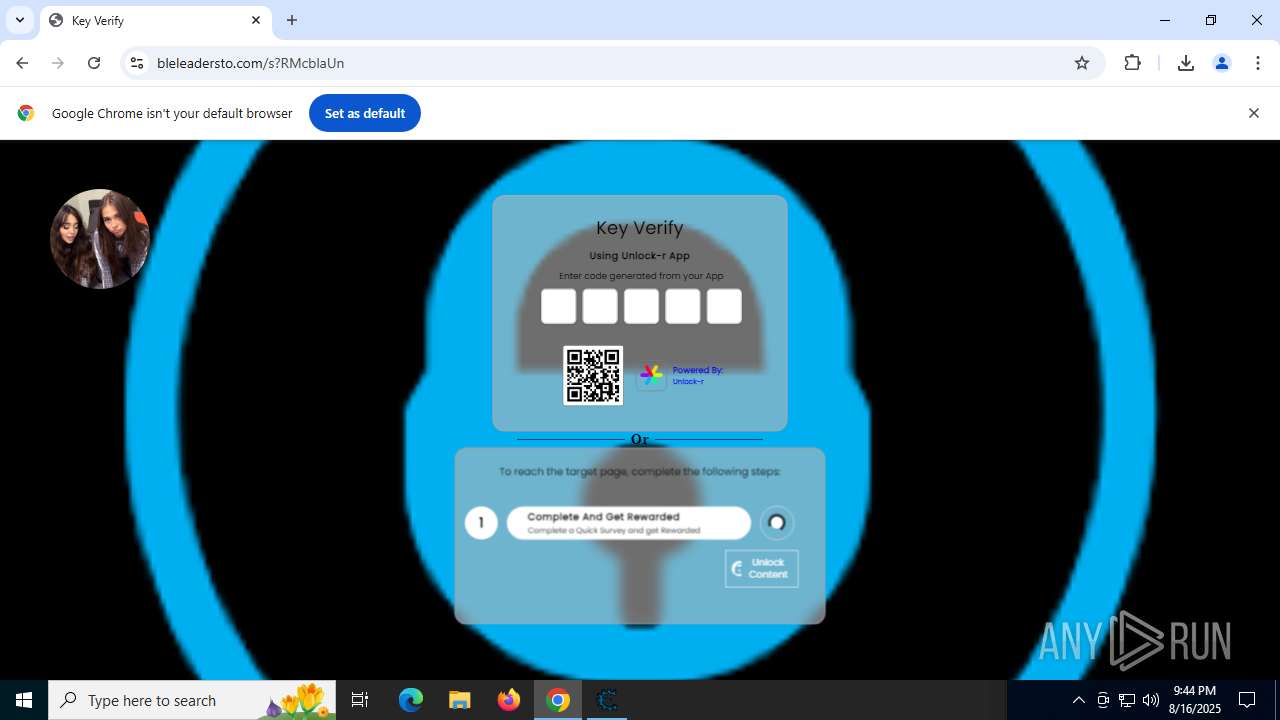
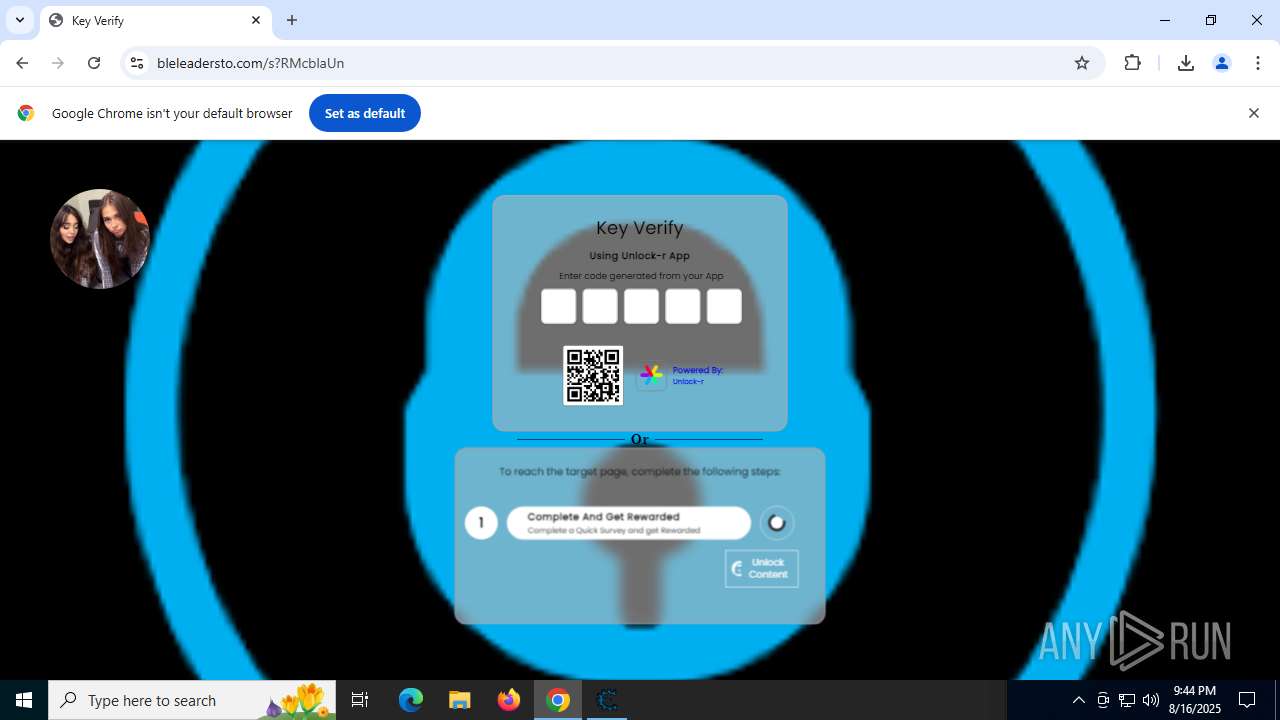
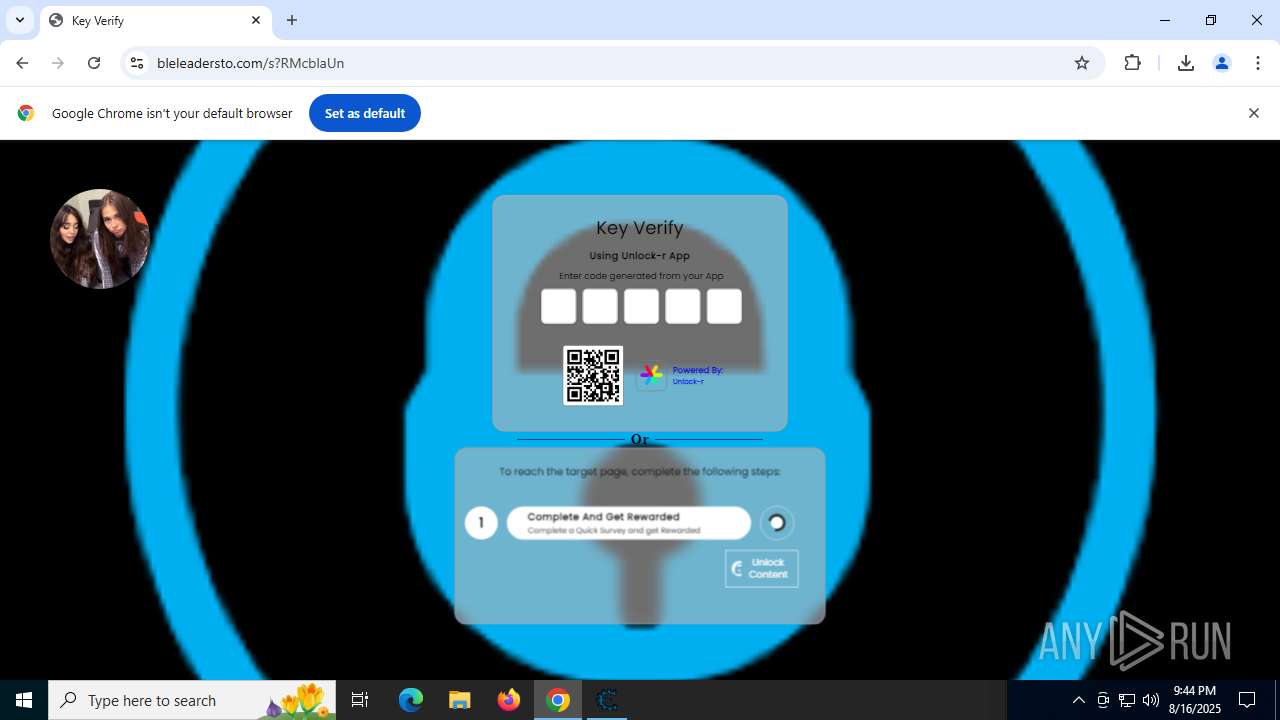
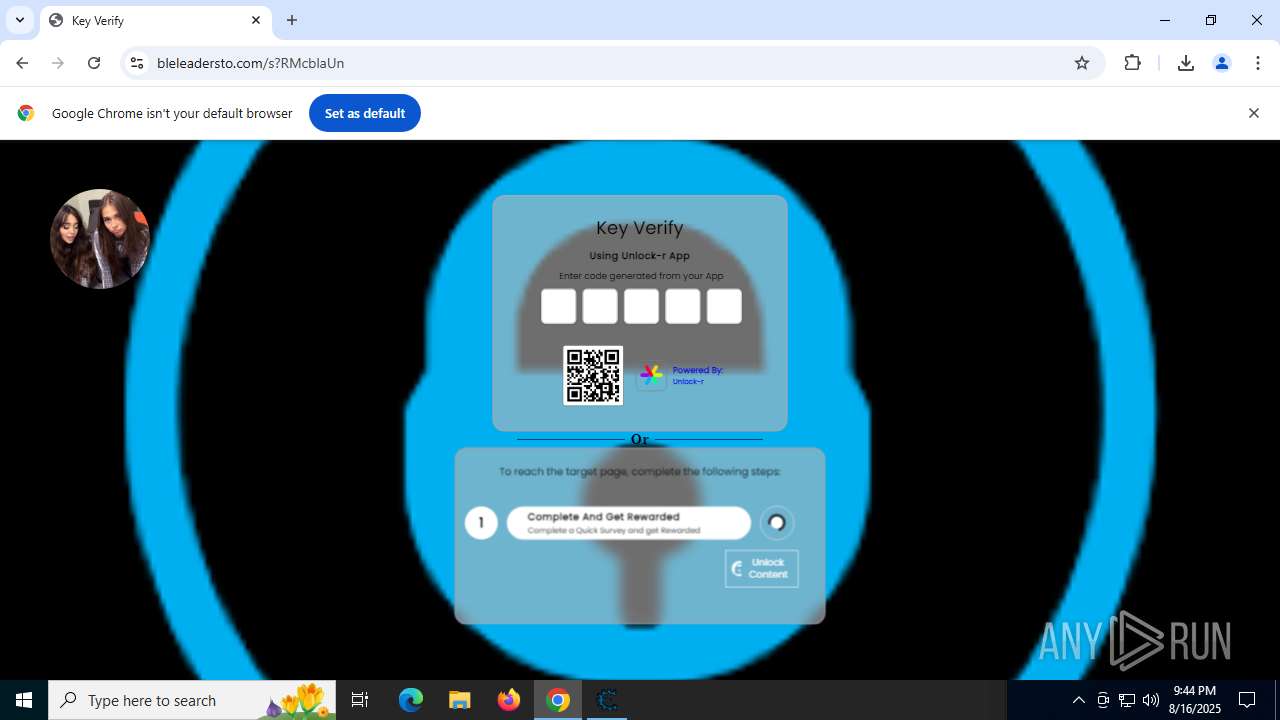
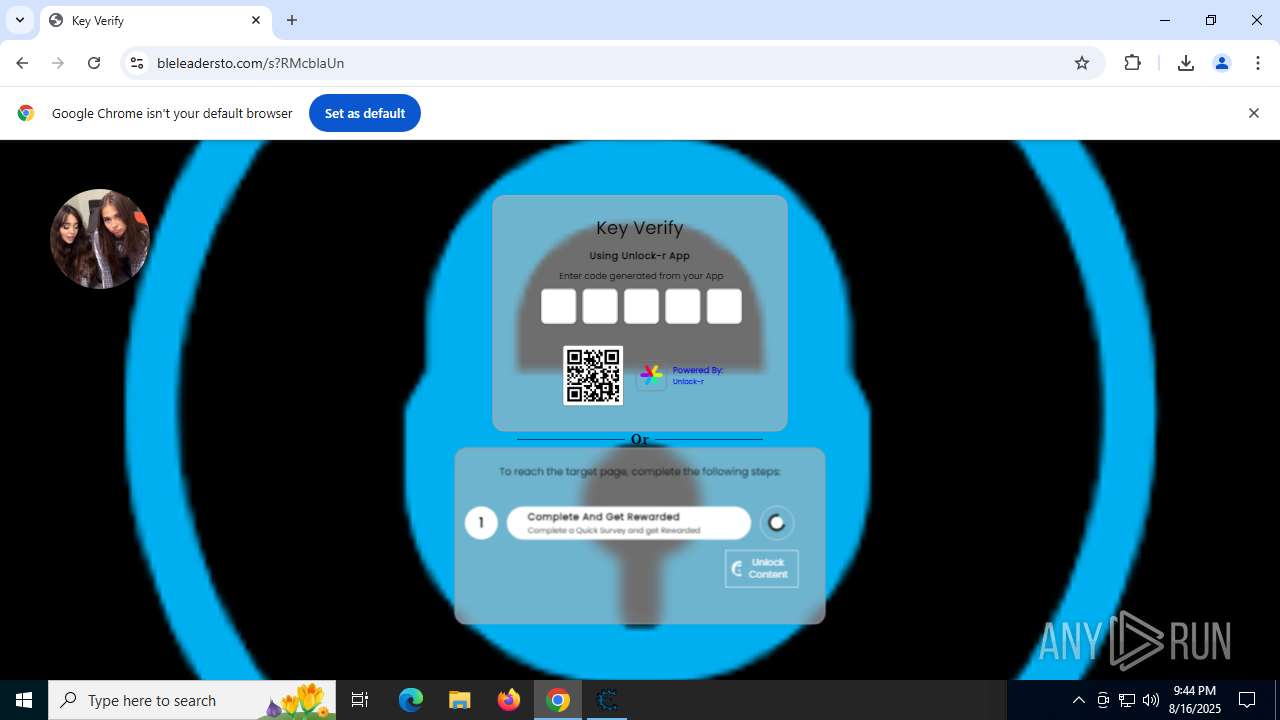
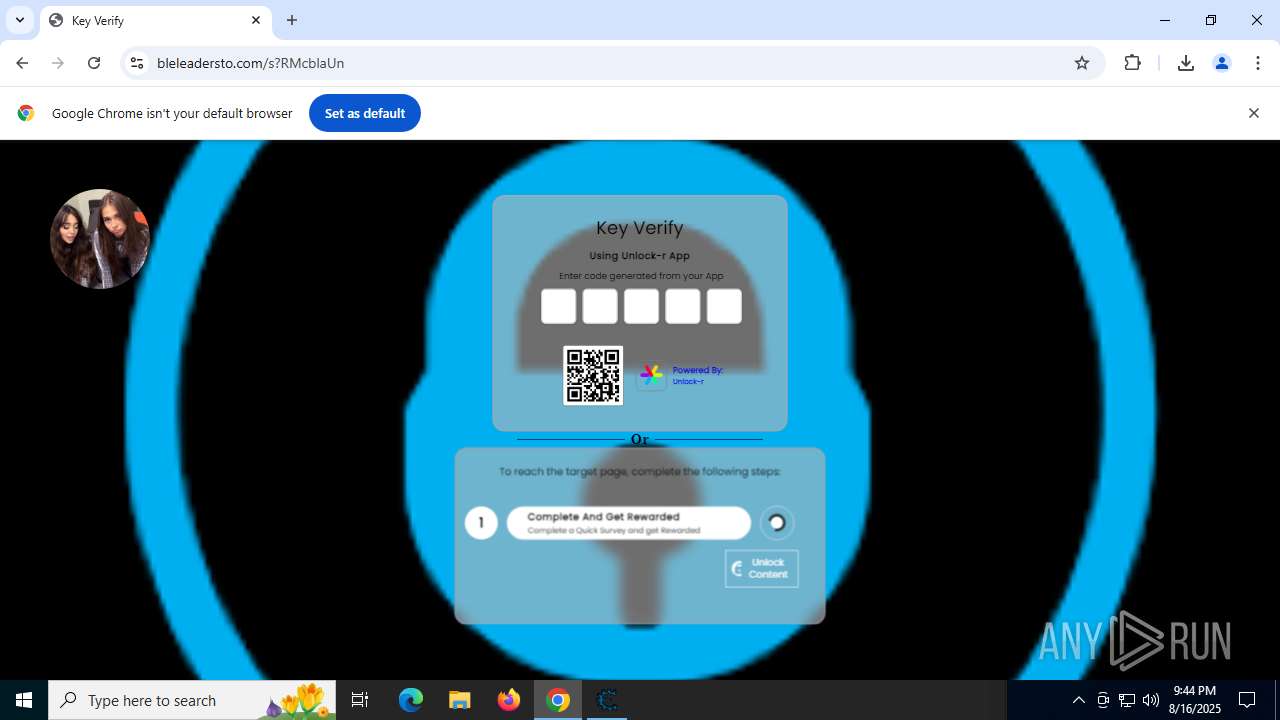
| URL: | https://fast-links.org/s?xglD5G6t |
| Full analysis: | https://app.any.run/tasks/5d0ec0c6-eac5-43bb-8214-3c7f7a0d366b |
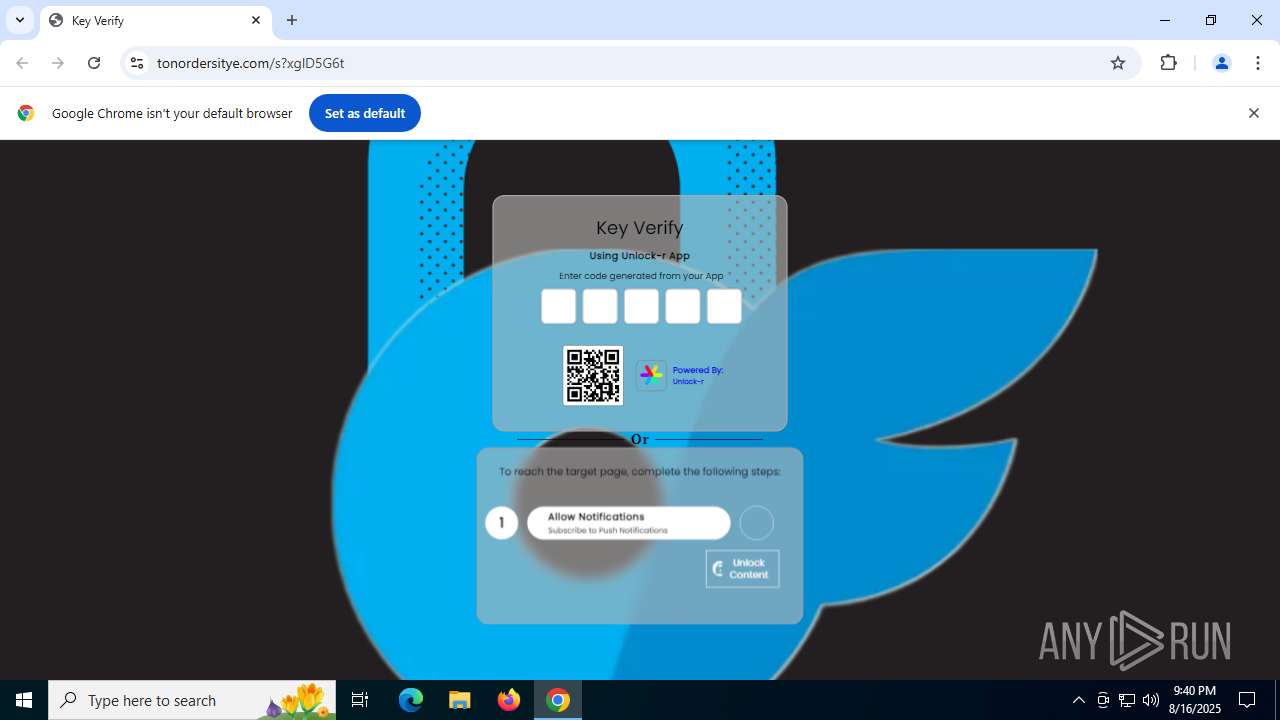
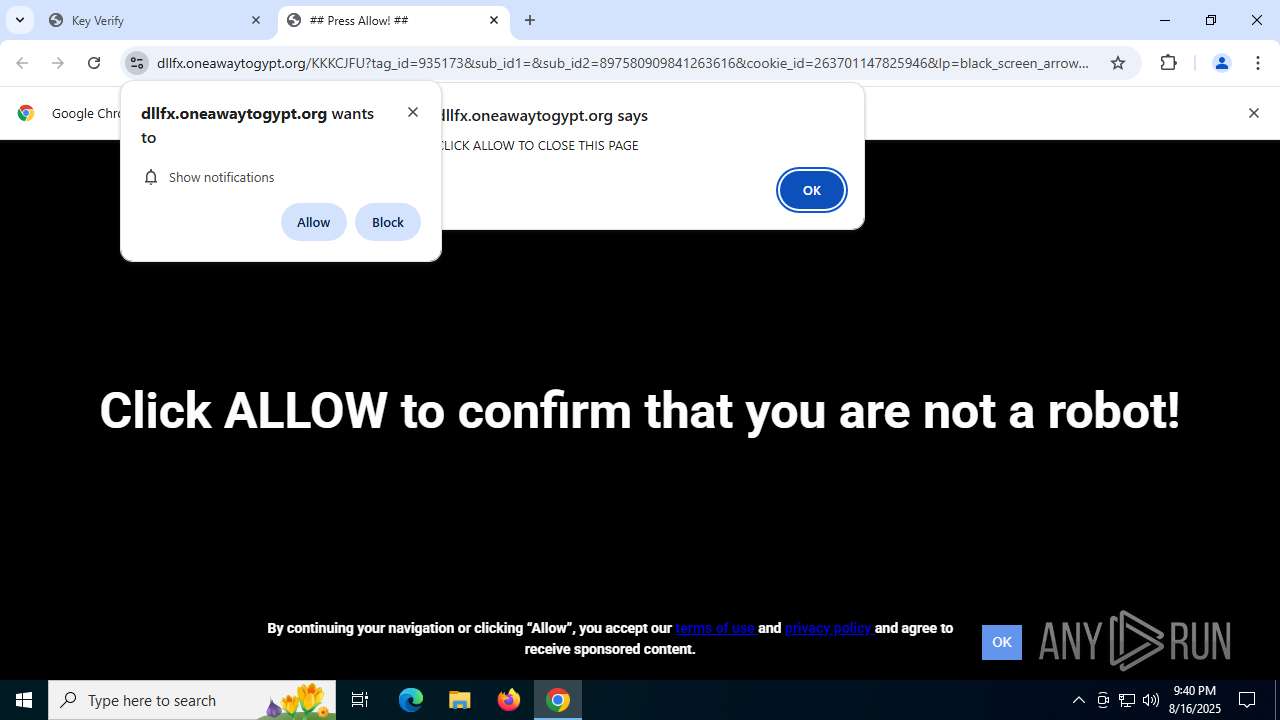
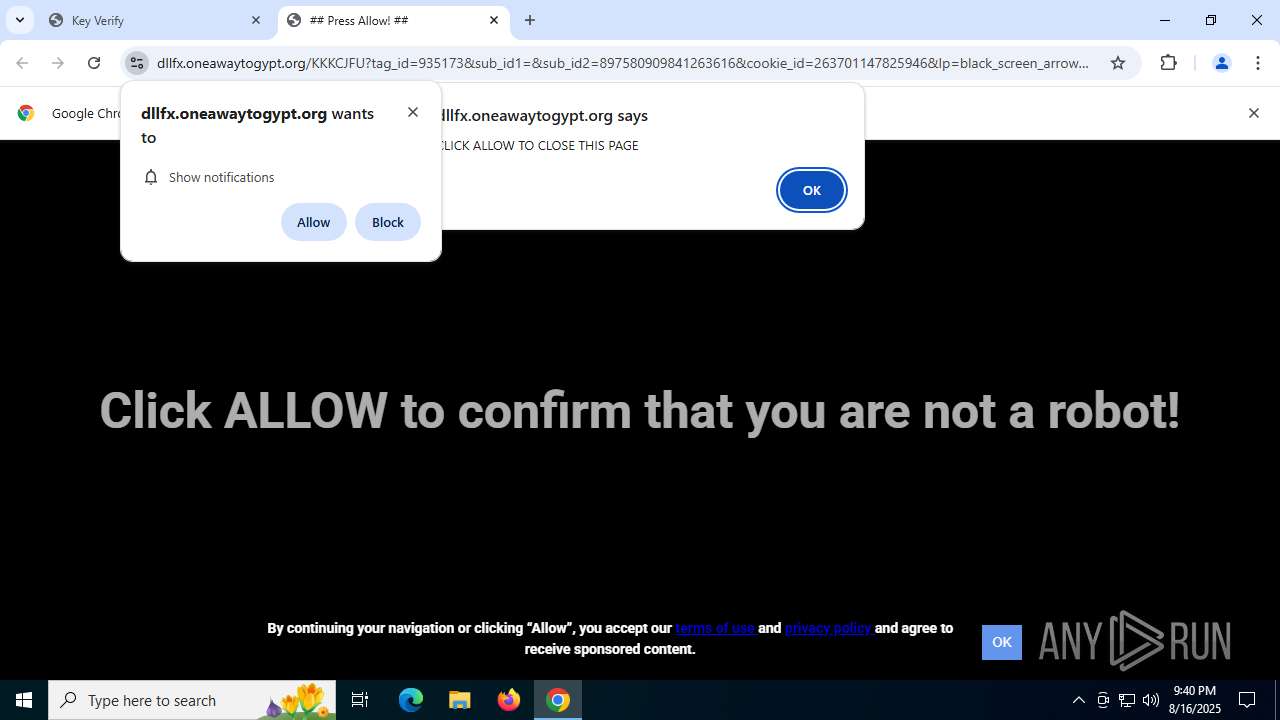
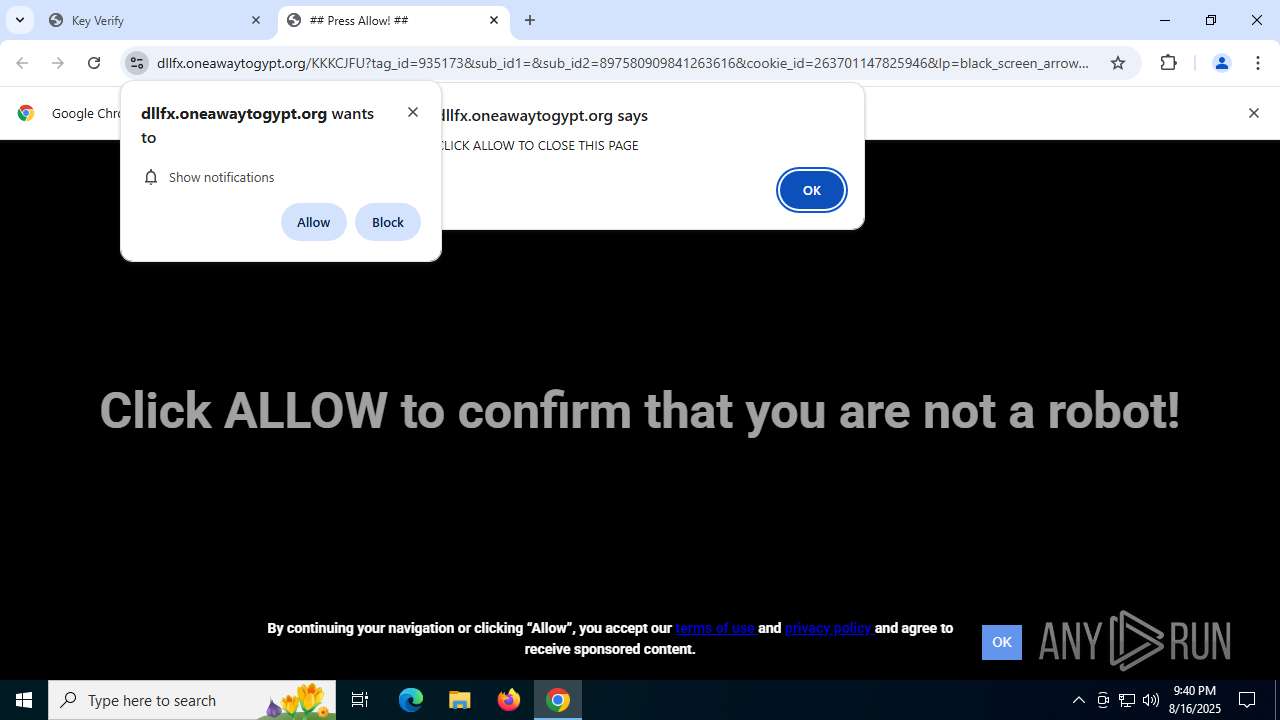
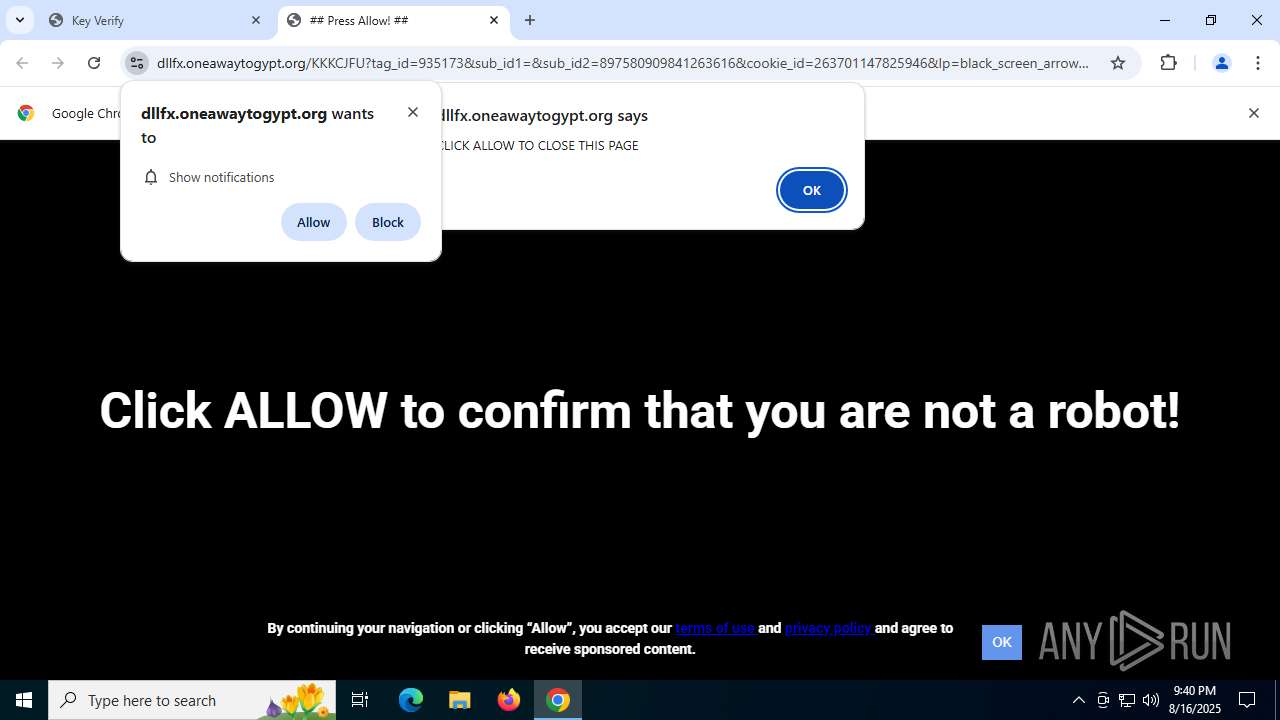
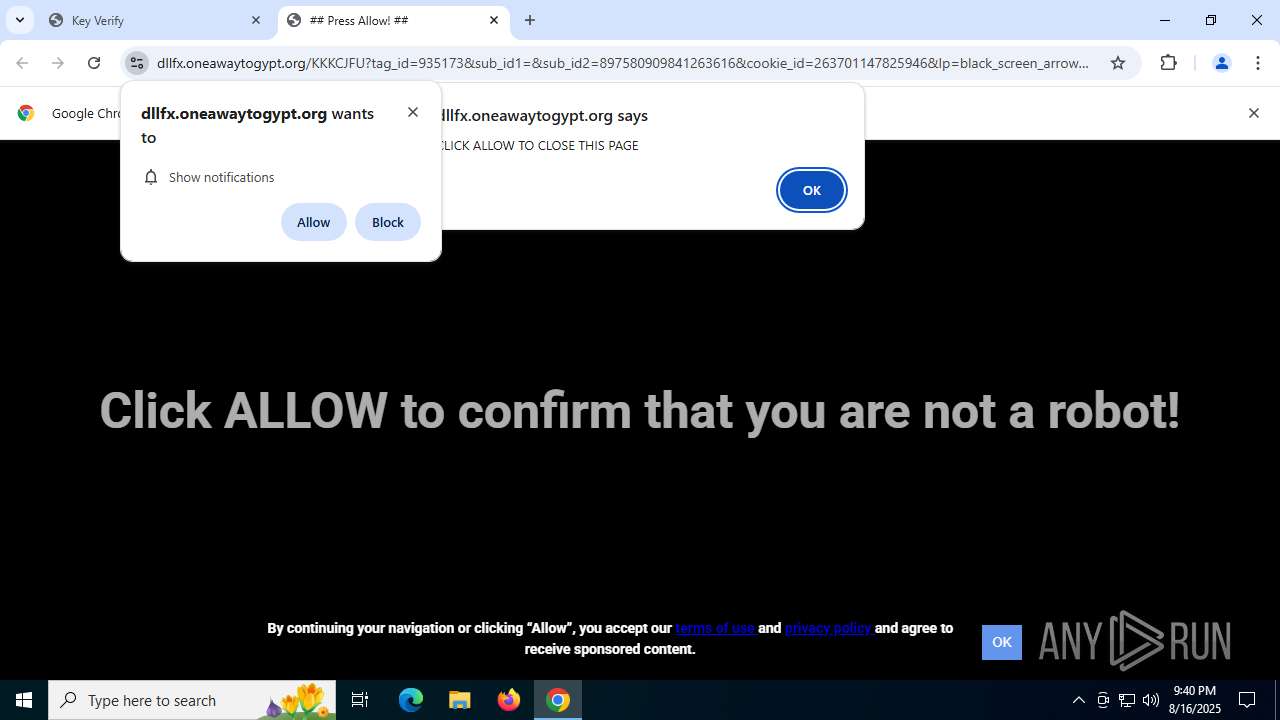
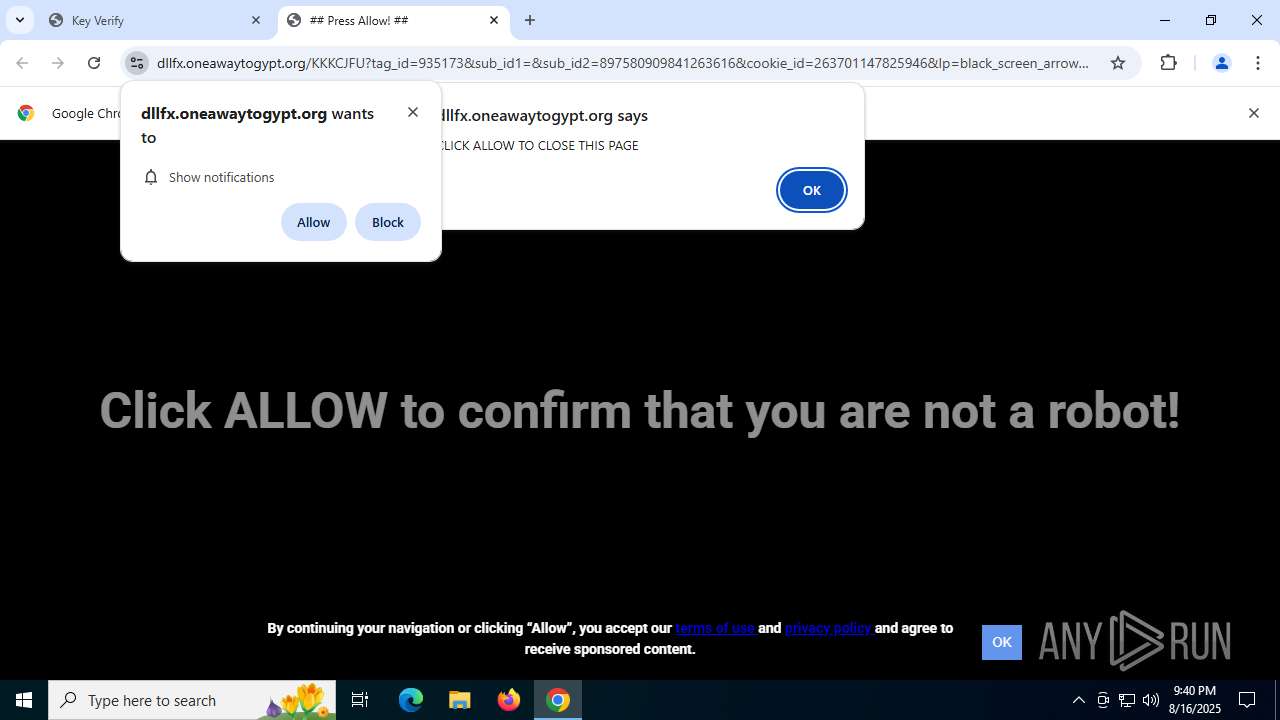
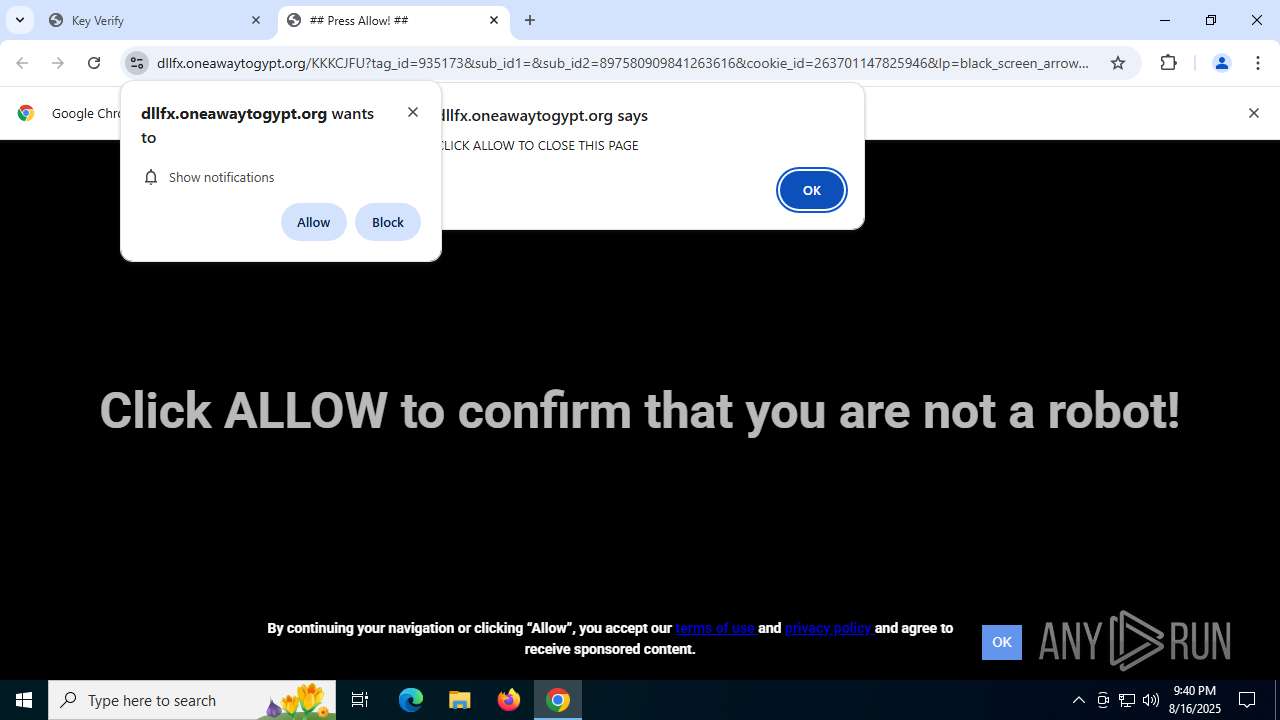
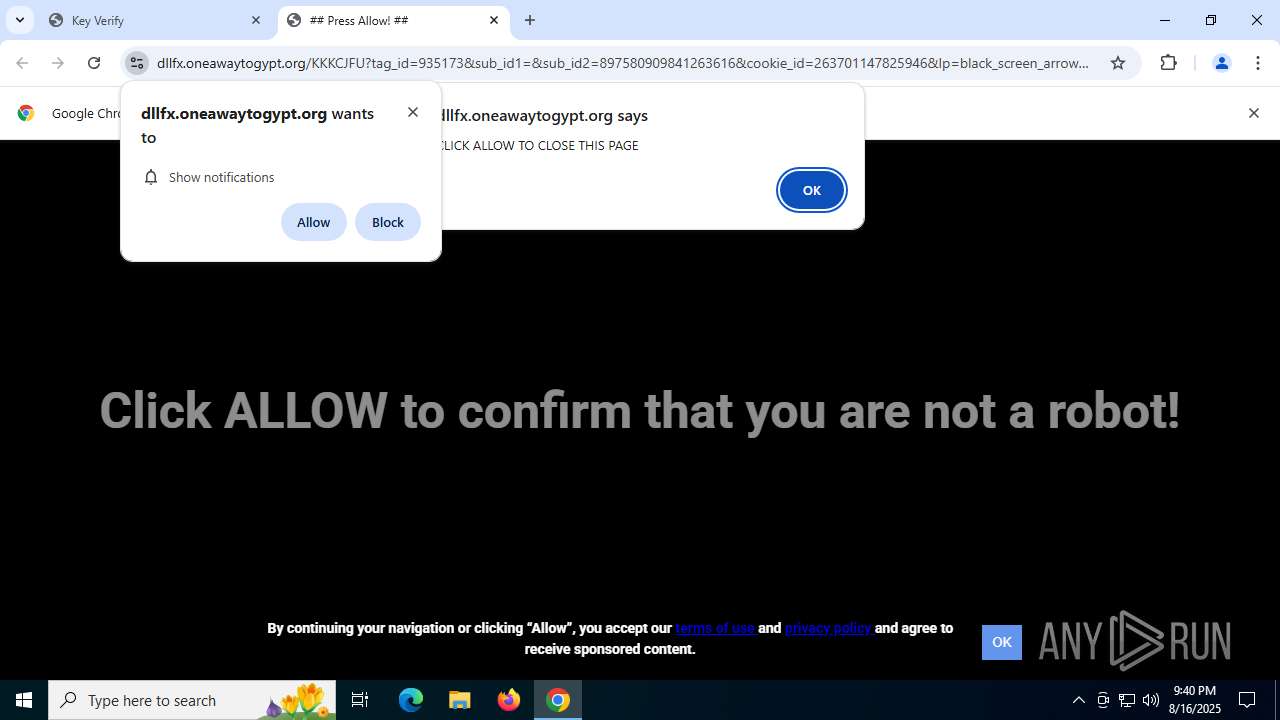
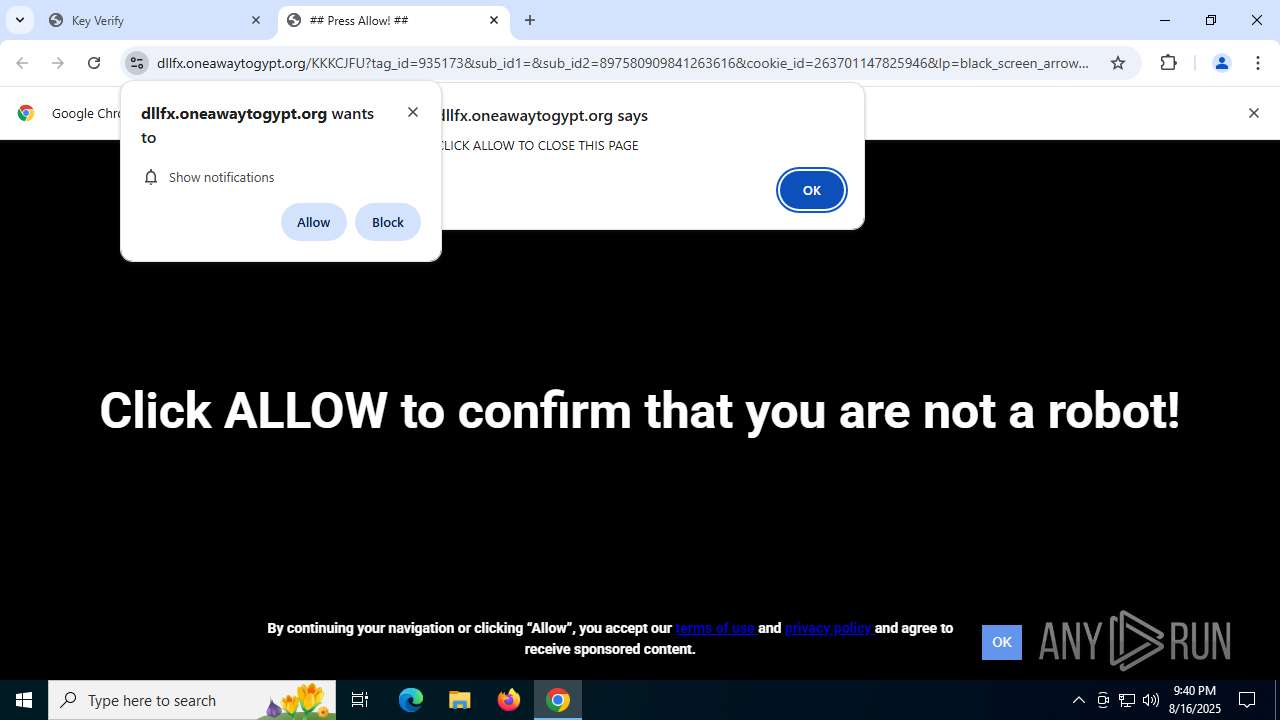
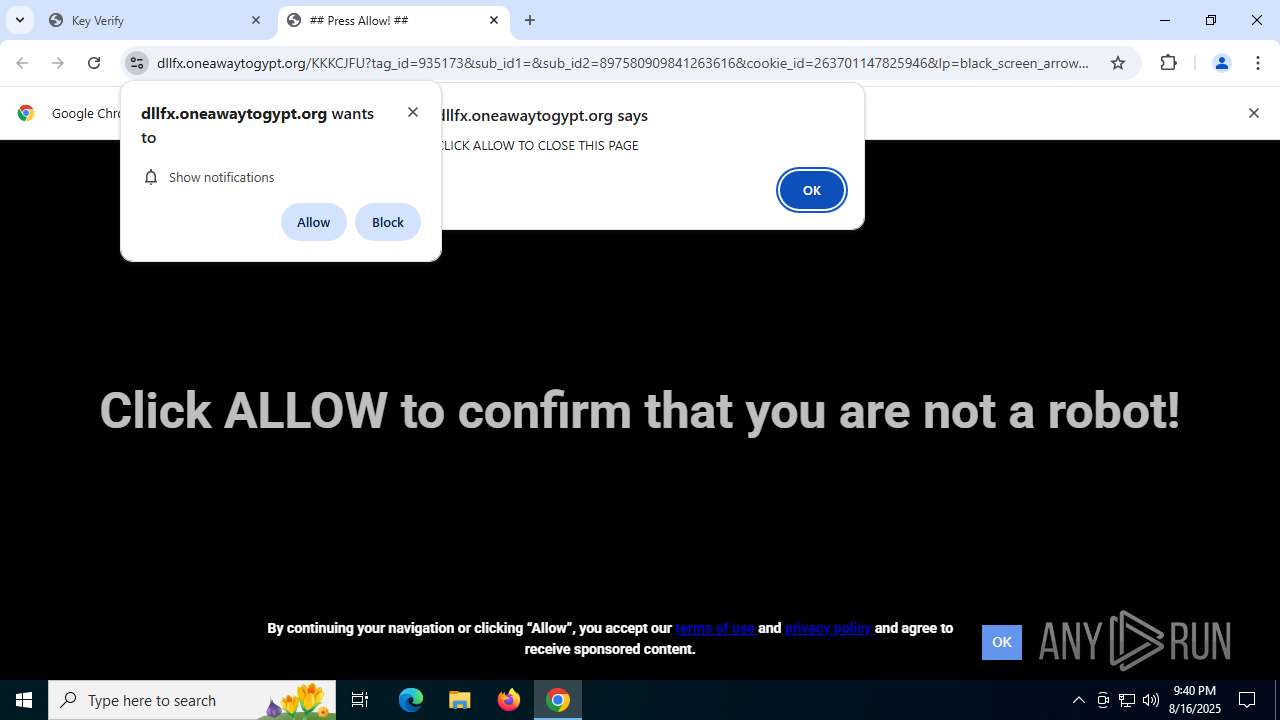
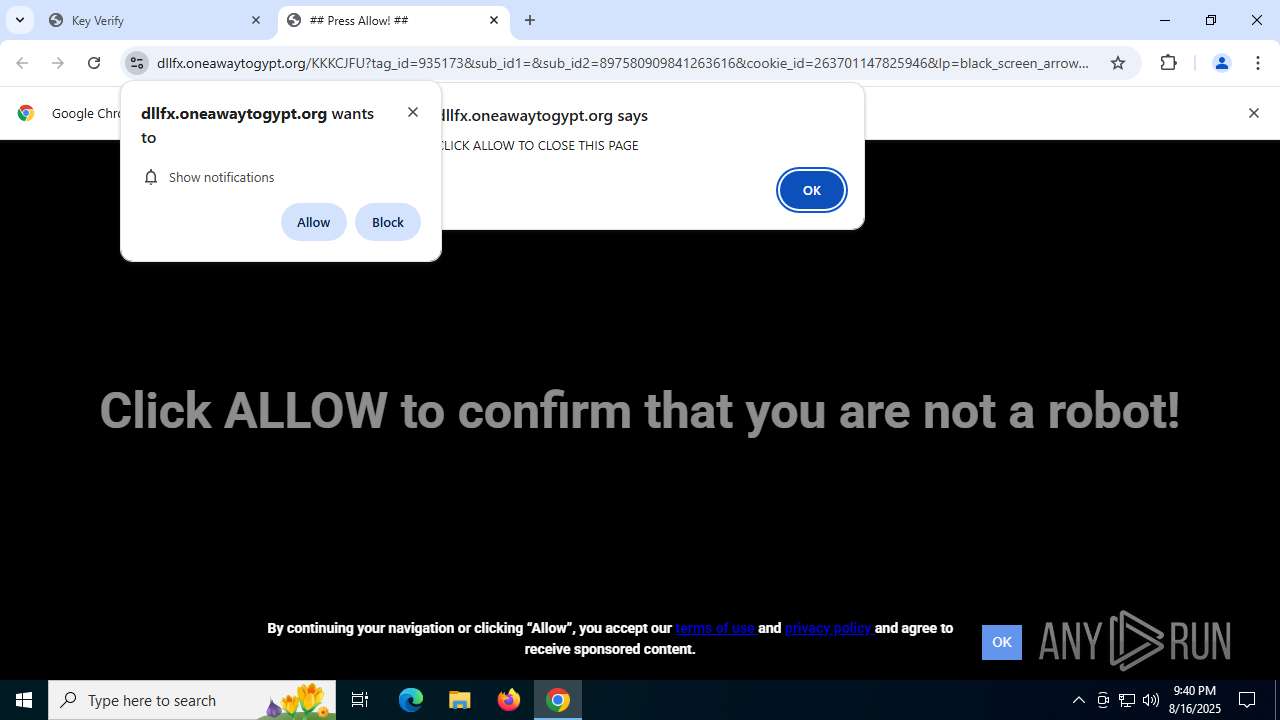
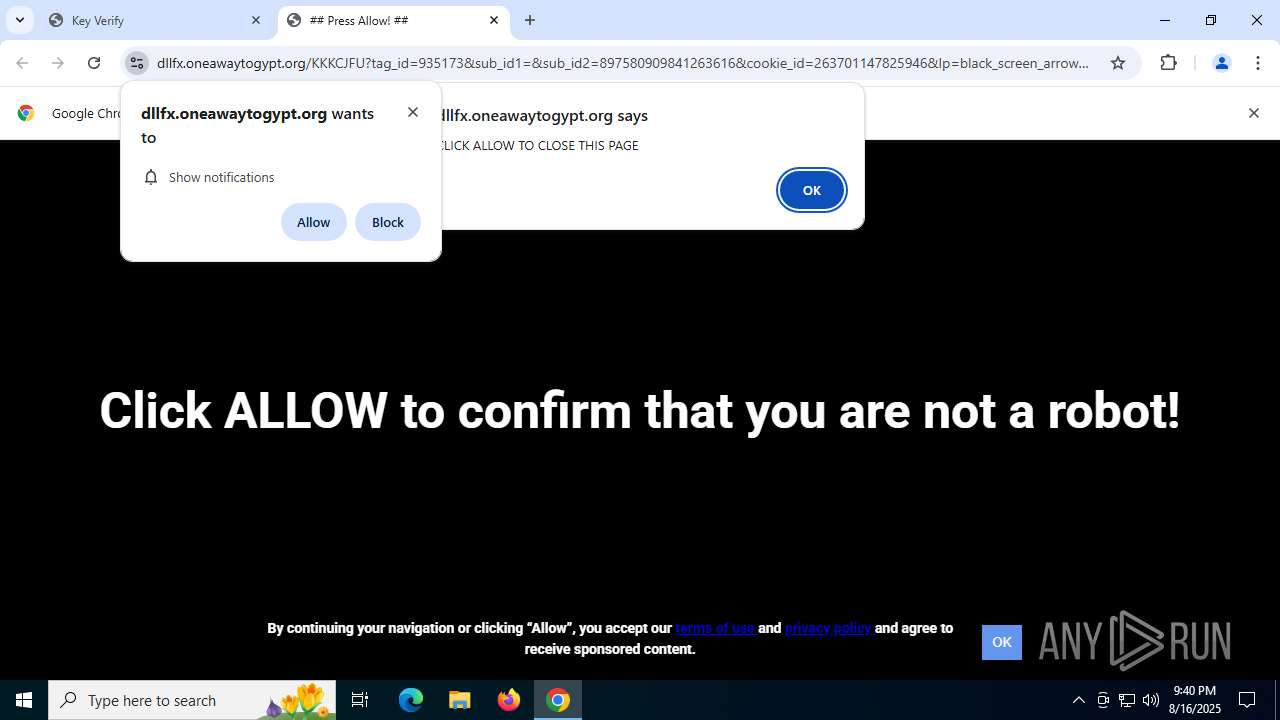
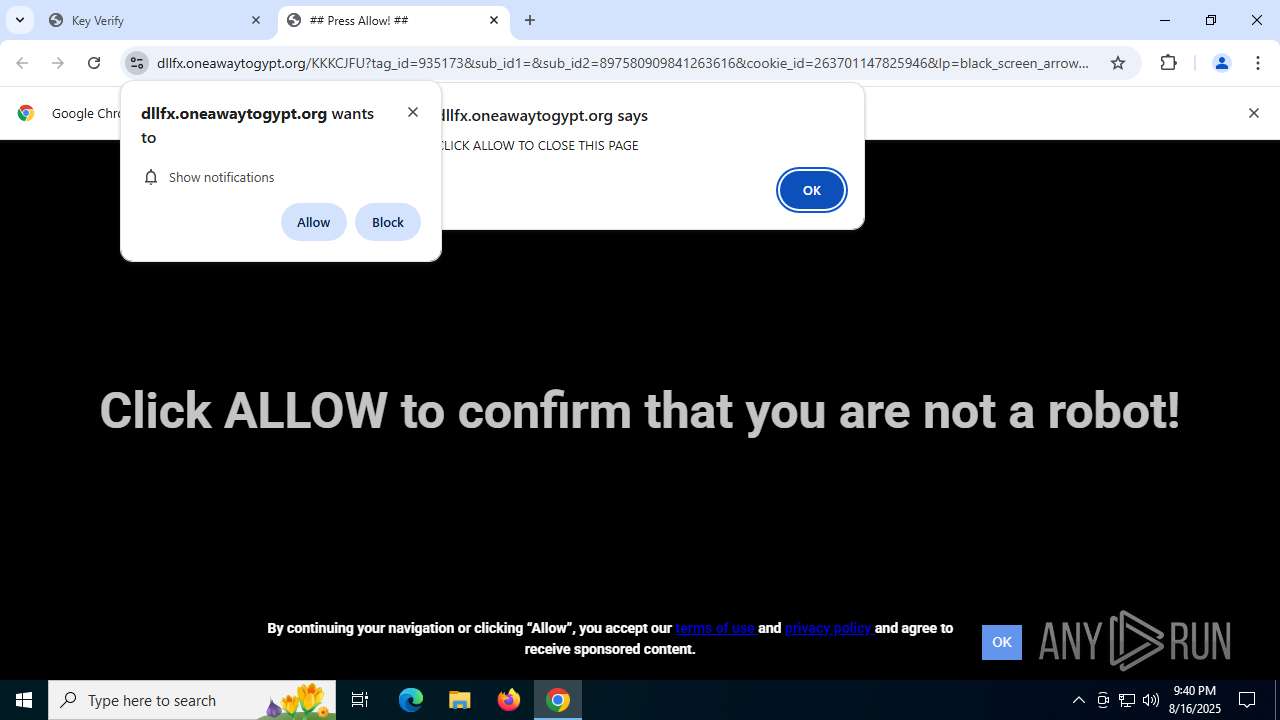
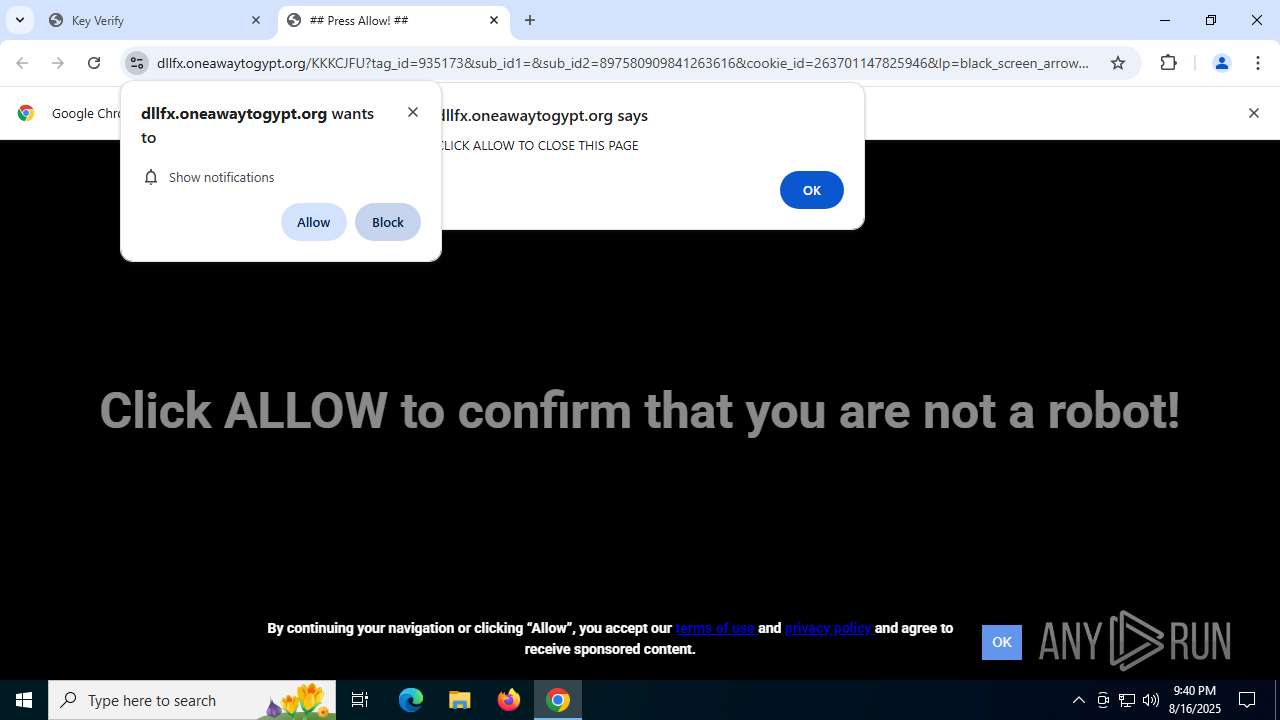
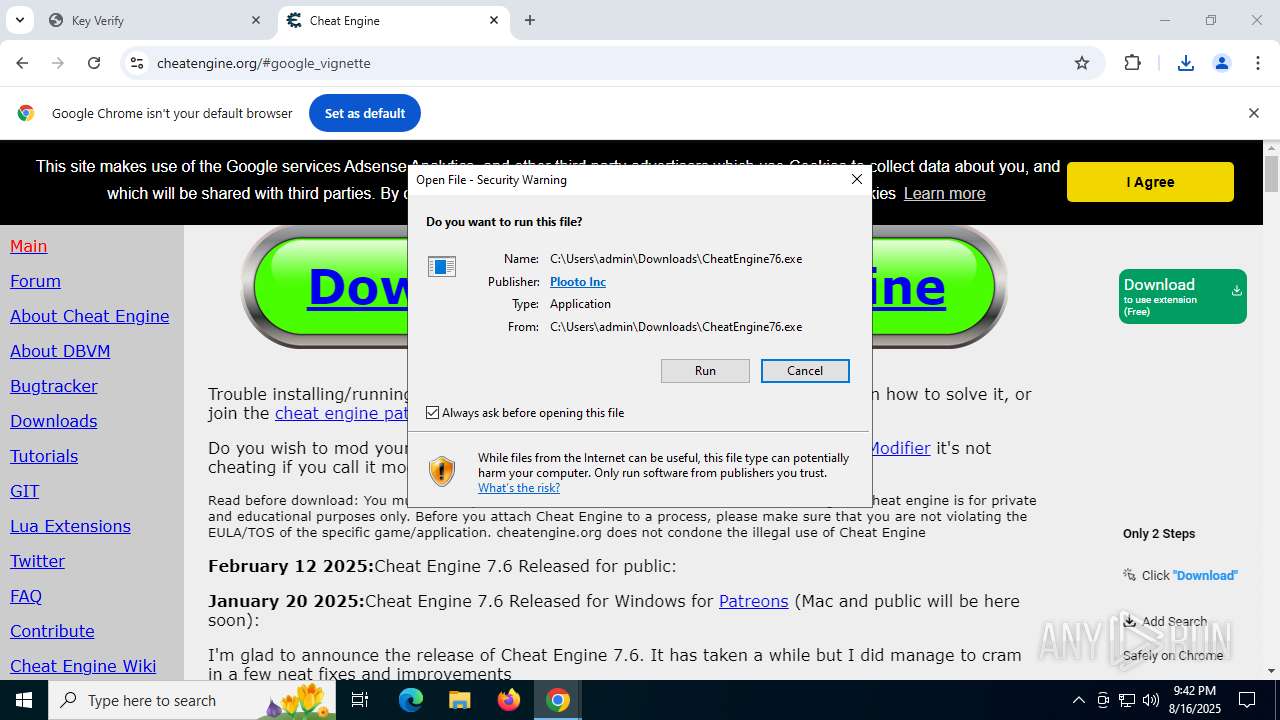
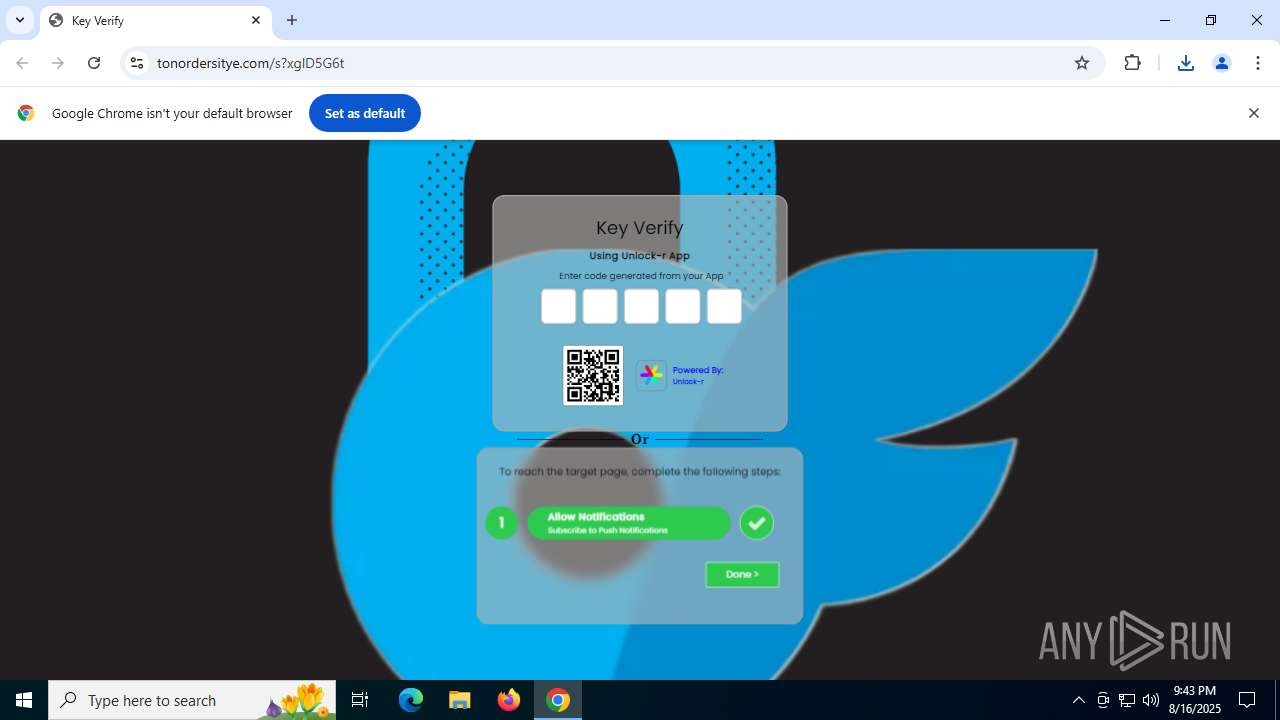
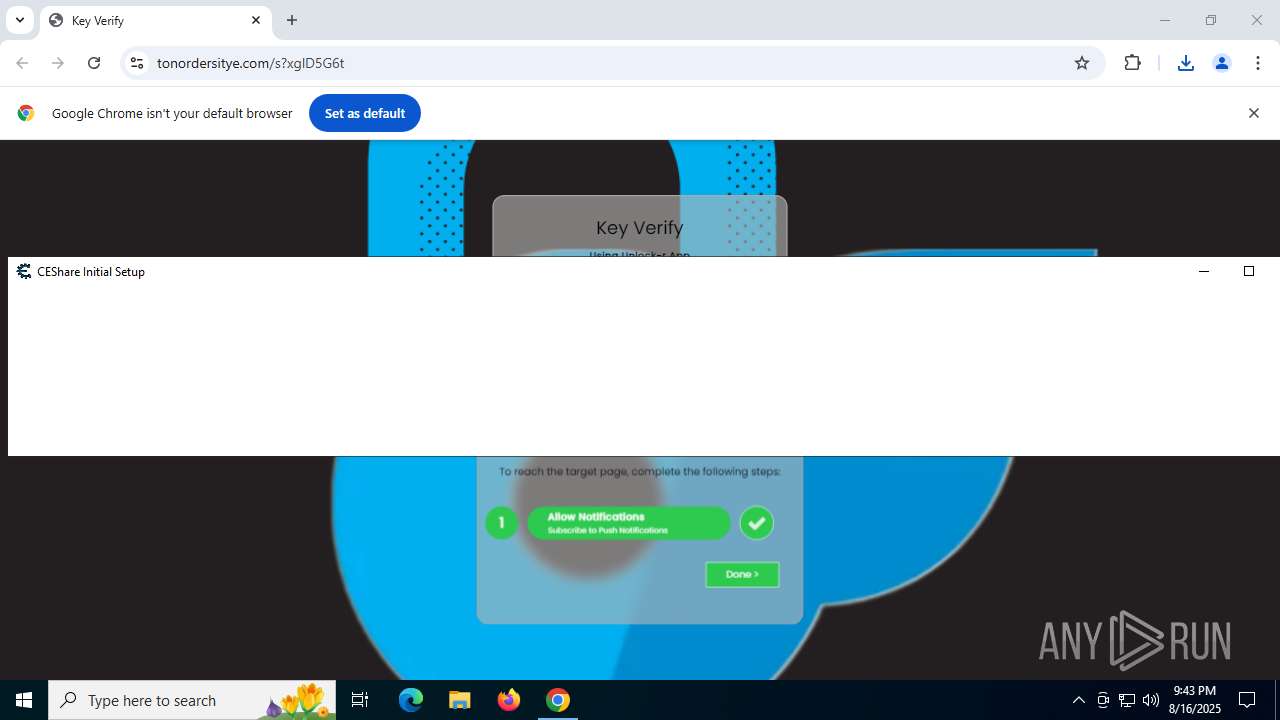
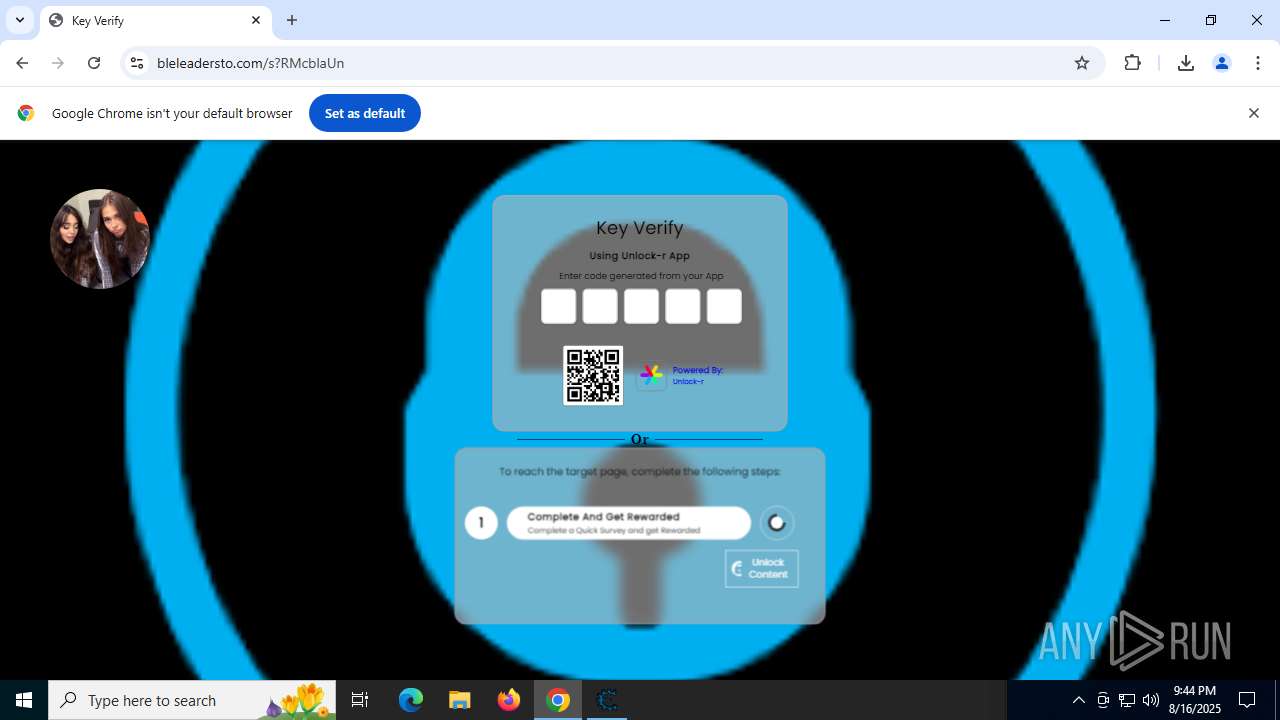
| Verdict: | Malicious activity |
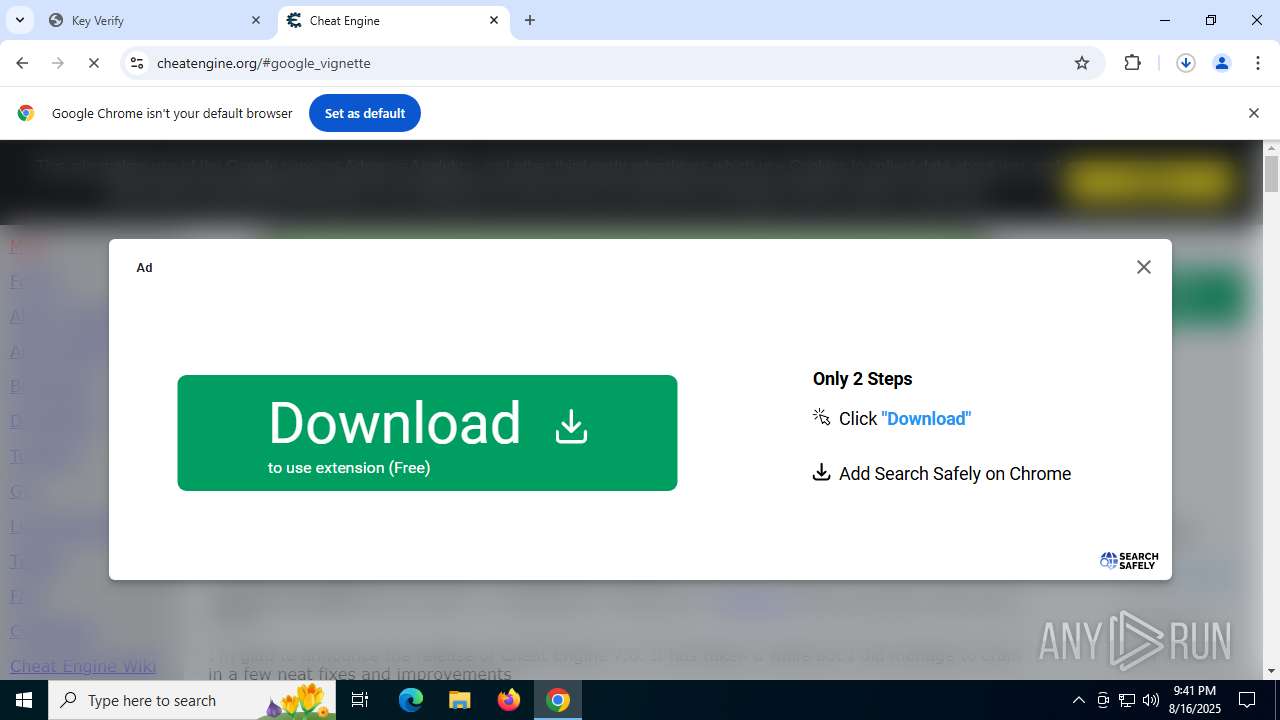
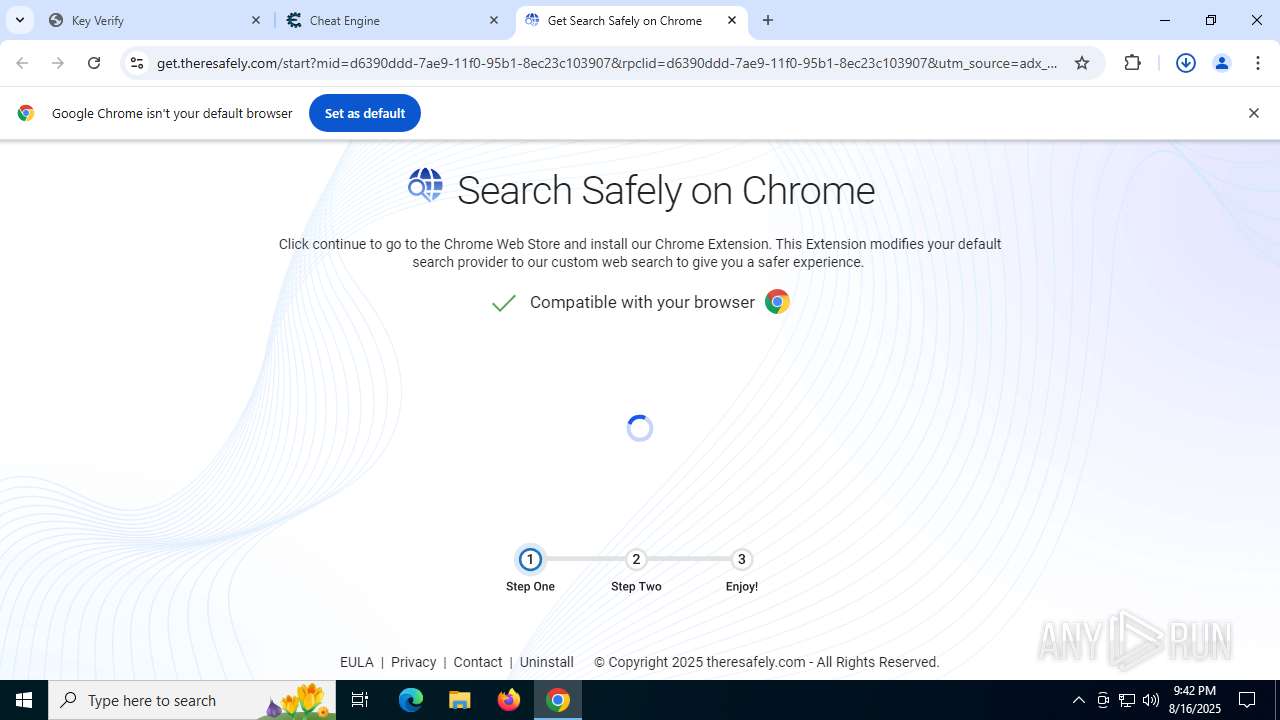
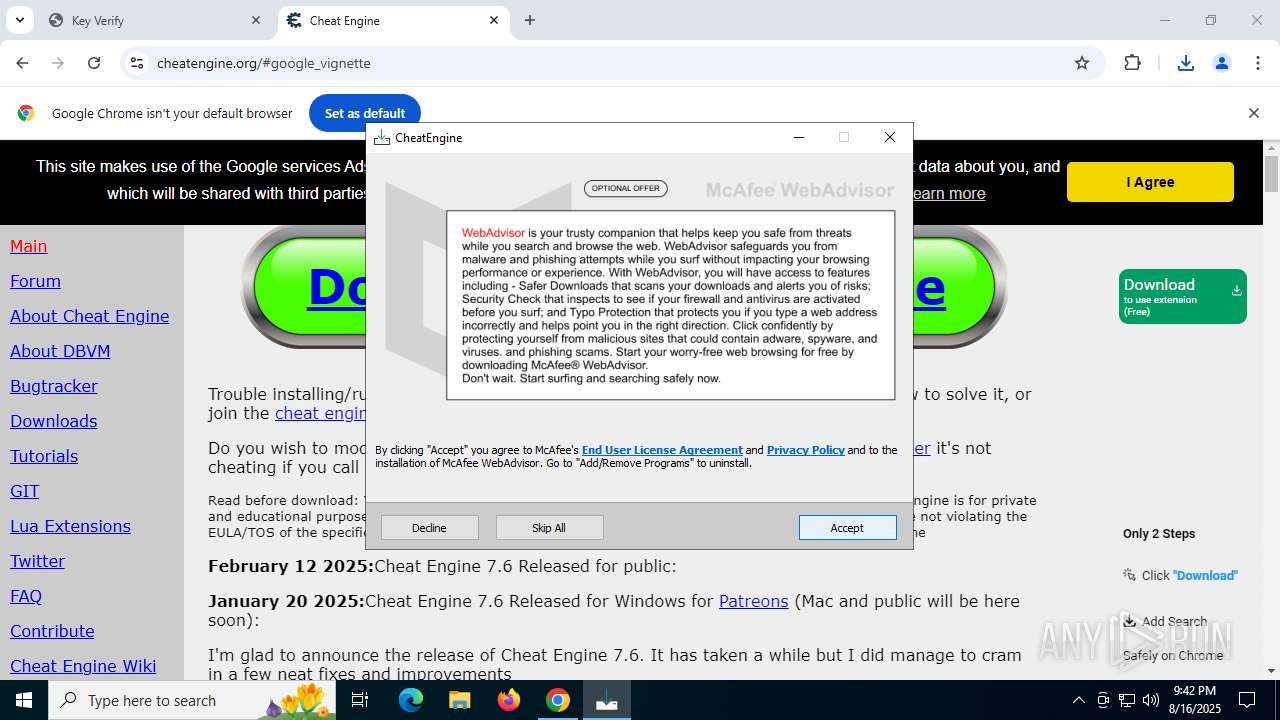
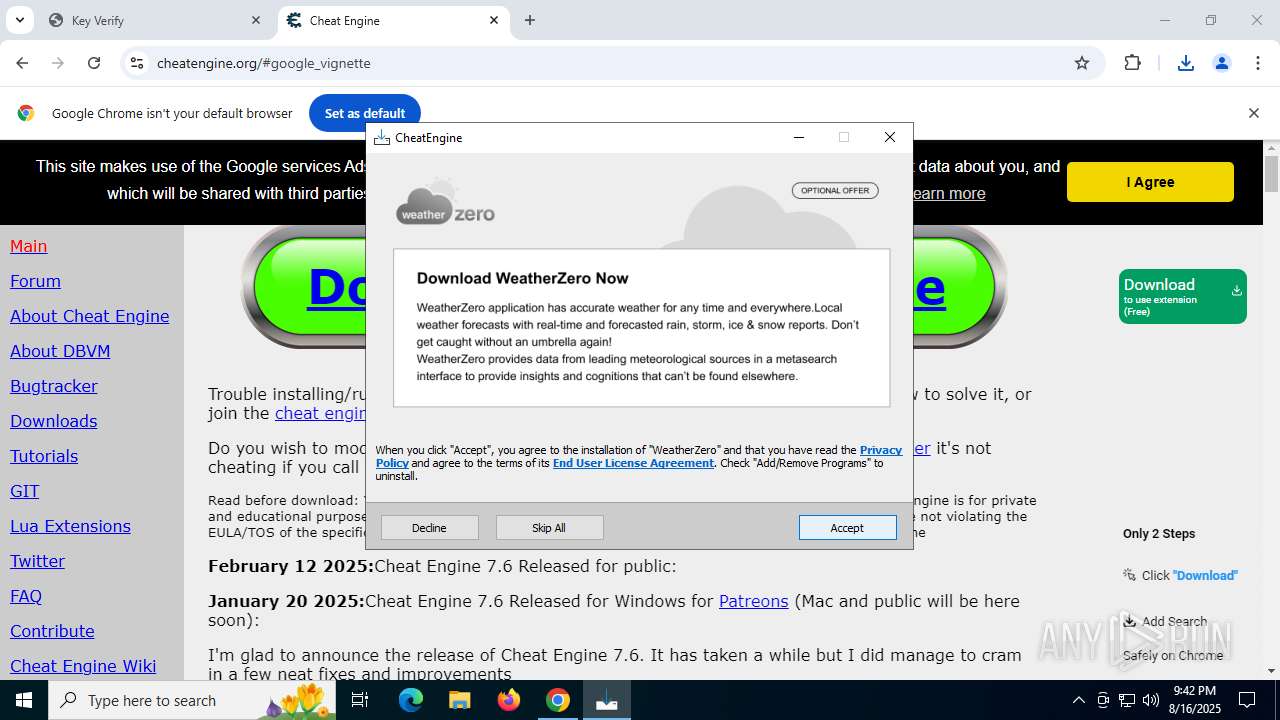
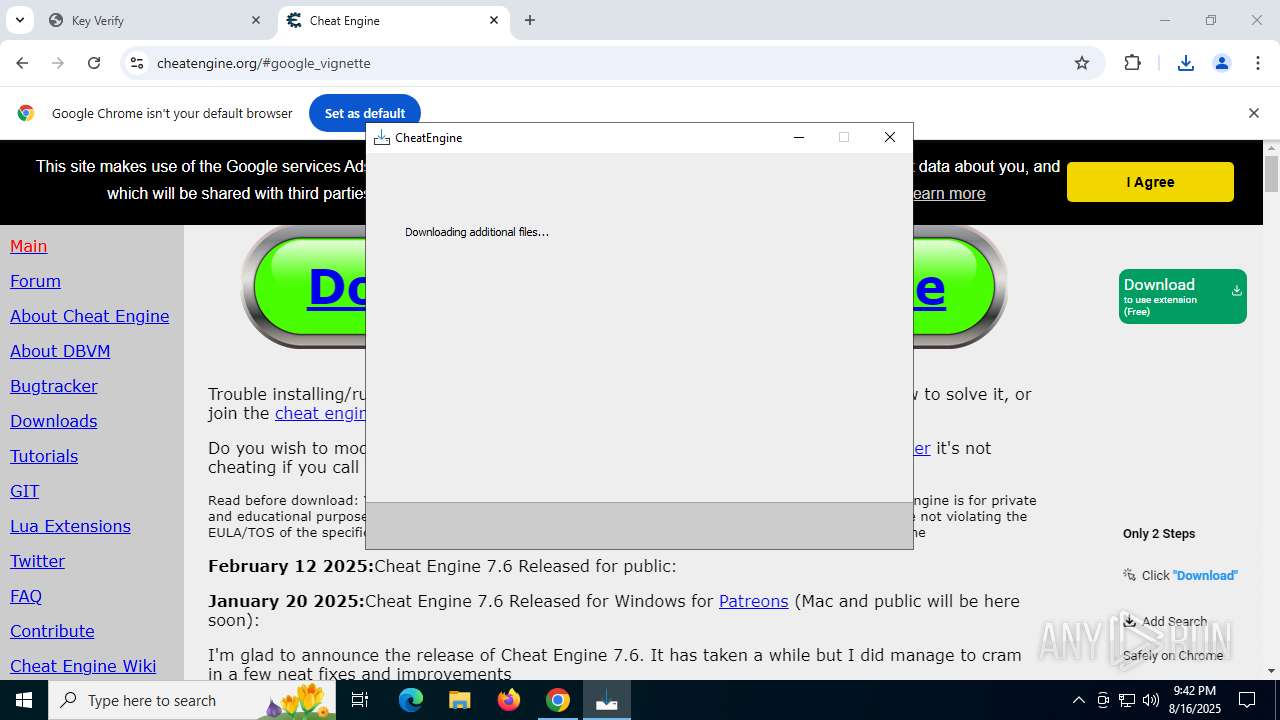
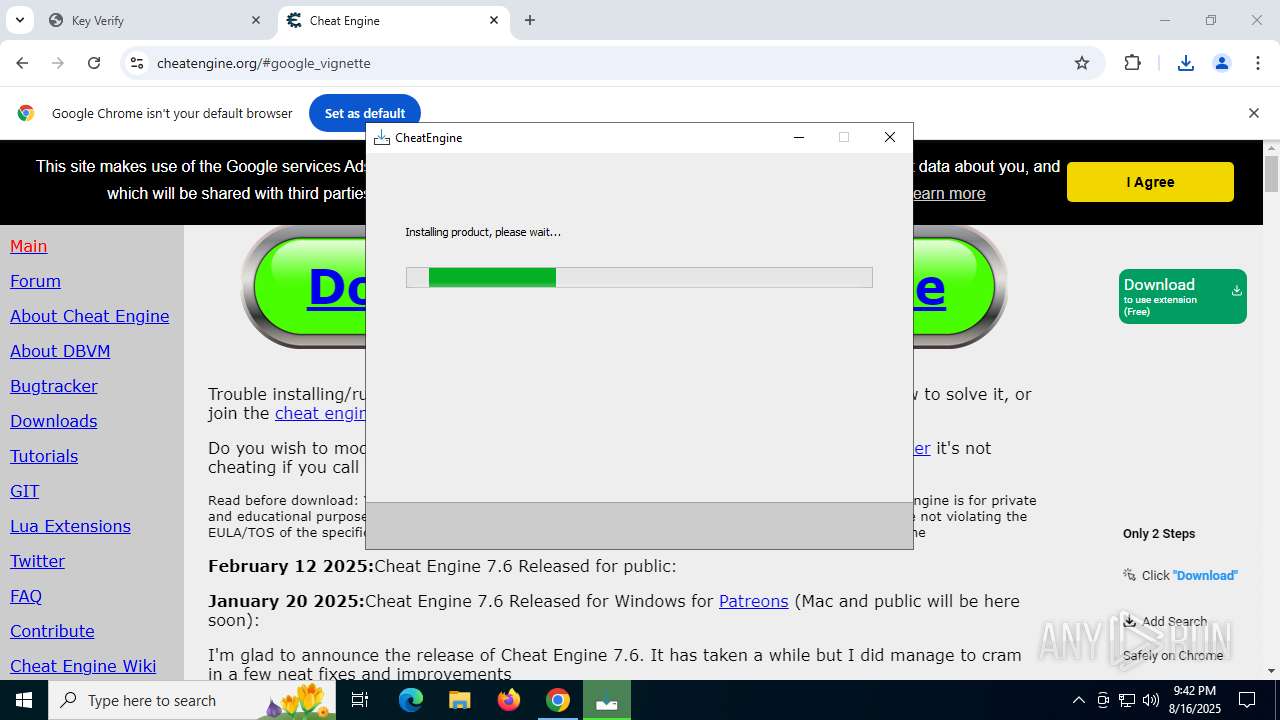
| Threats: | Adware is a form of malware that targets users with unwanted advertisements, often disrupting their browsing experience. It typically infiltrates systems through software bundling, malicious websites, or deceptive downloads. Once installed, it may track user activity, collect sensitive data, and display intrusive ads, including pop-ups or banners. Some advanced adware variants can bypass security measures and establish persistence on devices, making removal challenging. Additionally, adware can create vulnerabilities that other malware can exploit, posing a significant risk to user privacy and system security. |
| Analysis date: | August 16, 2025, 21:39:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FF62DB1CED5C26813B5CFD4C439FAFED |
| SHA1: | 7668ECB5D38B5B90A4A7D876E26697A7C7948902 |
| SHA256: | 8679BEF04FF28D6C4E01705ADB31C956196F57A7622116810A142EF8CD6CF295 |
| SSDEEP: | 3:N8XBStkR:2xb |
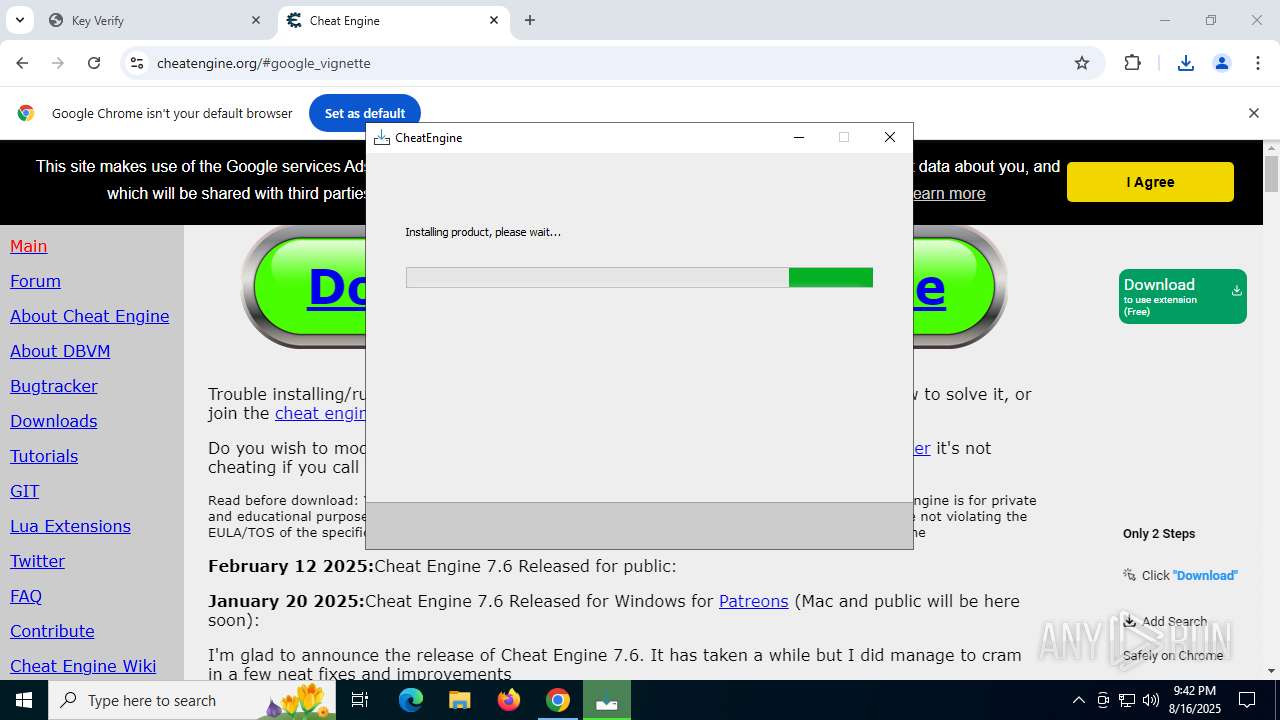
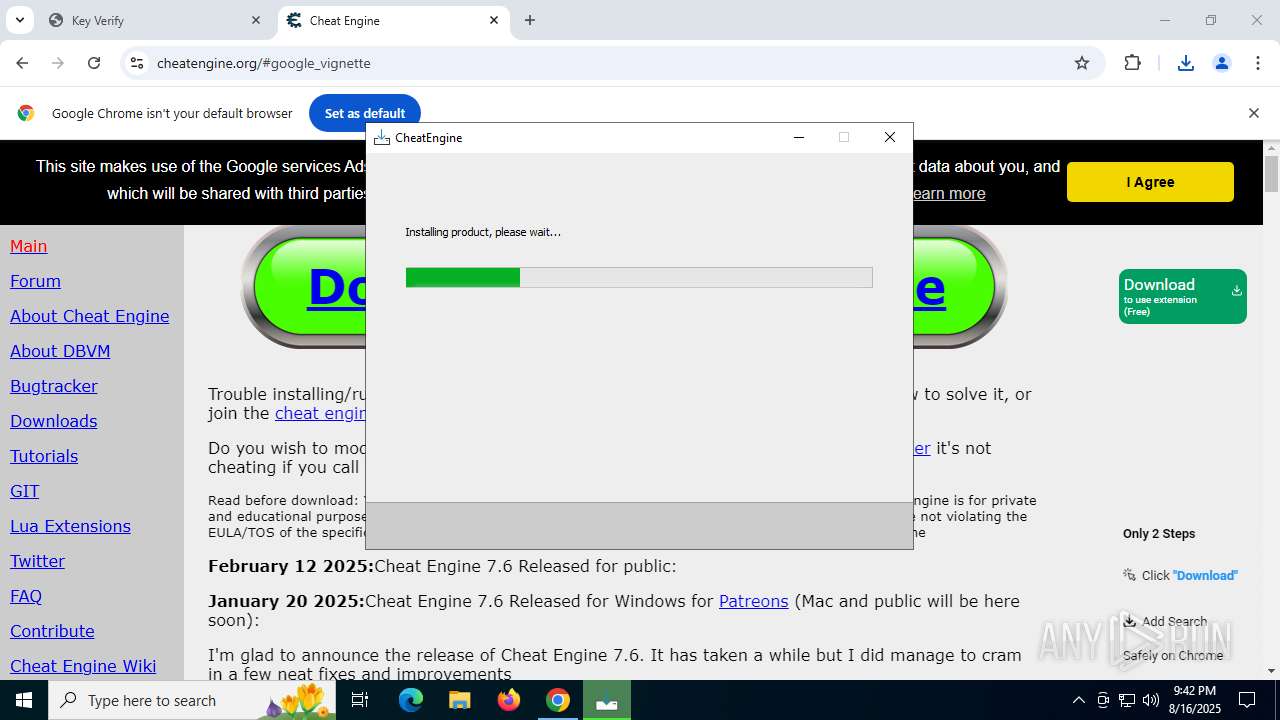
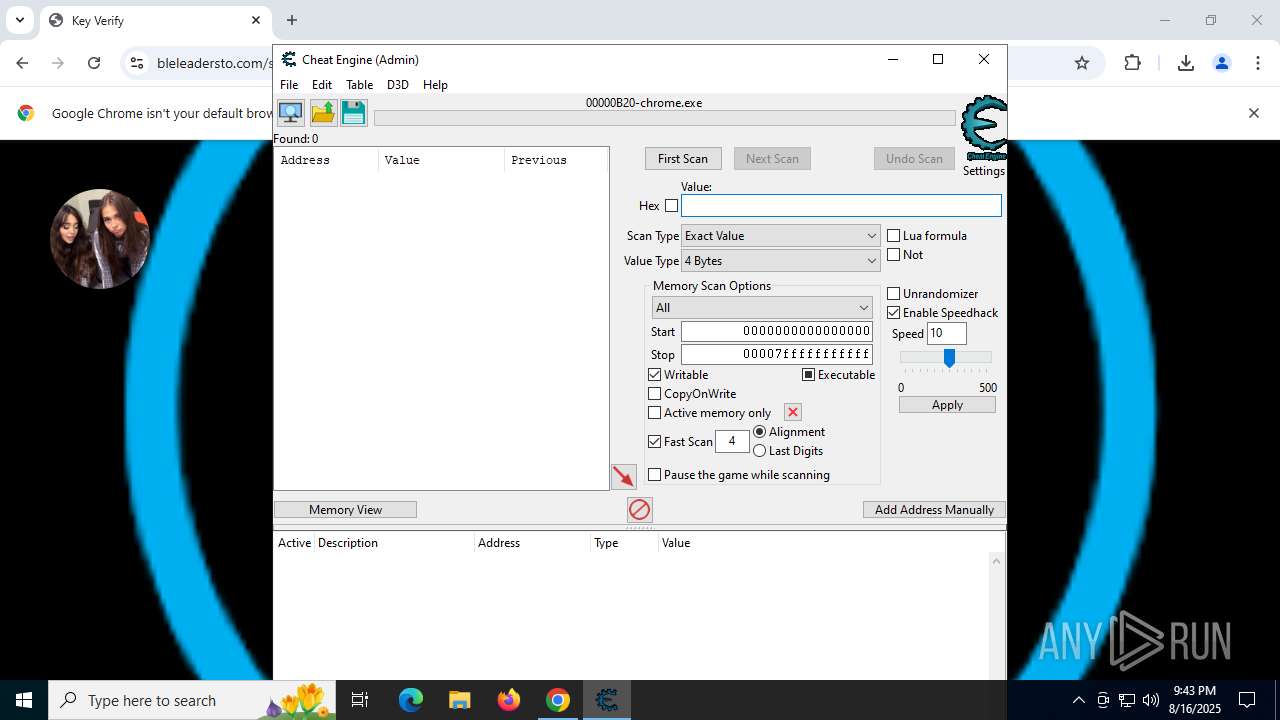
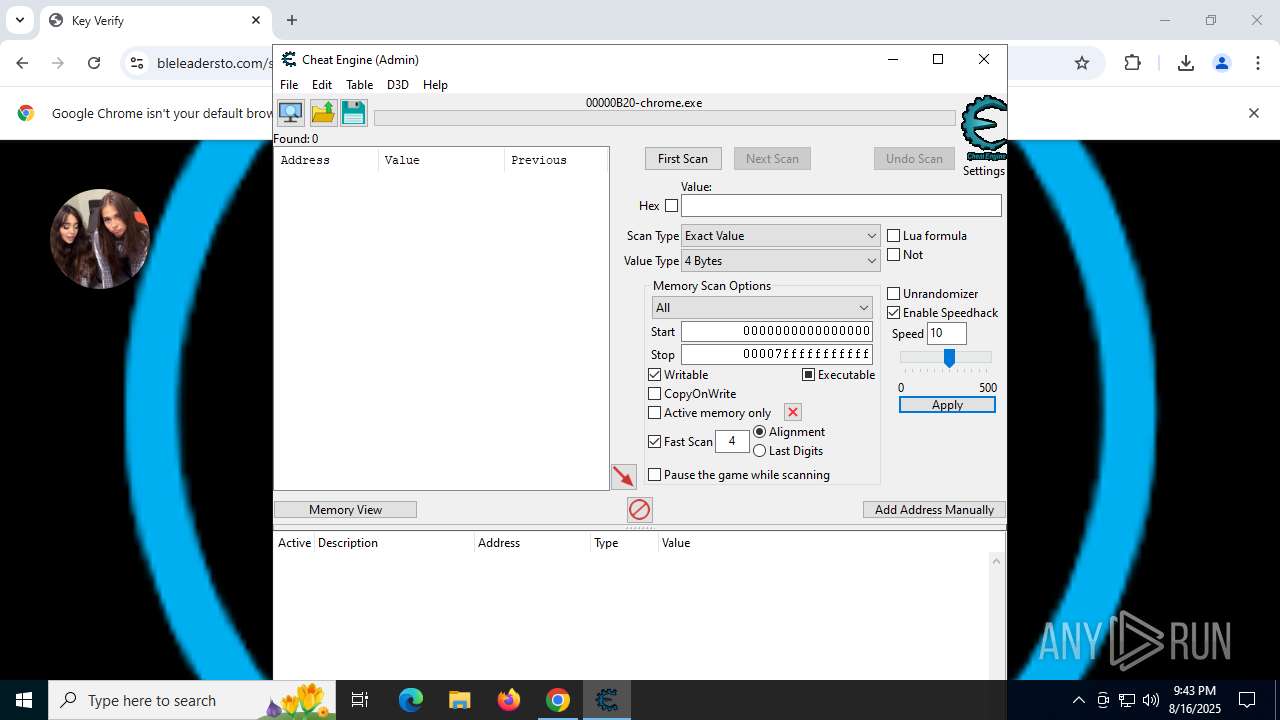
MALICIOUS
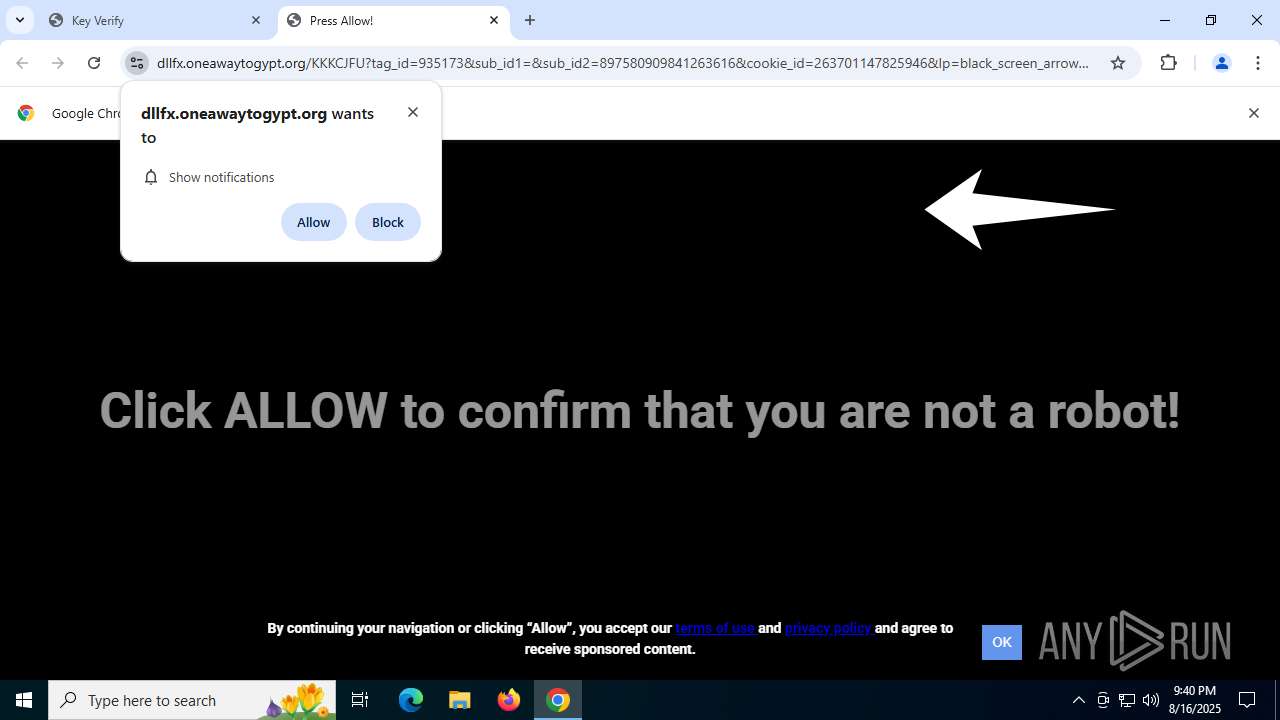
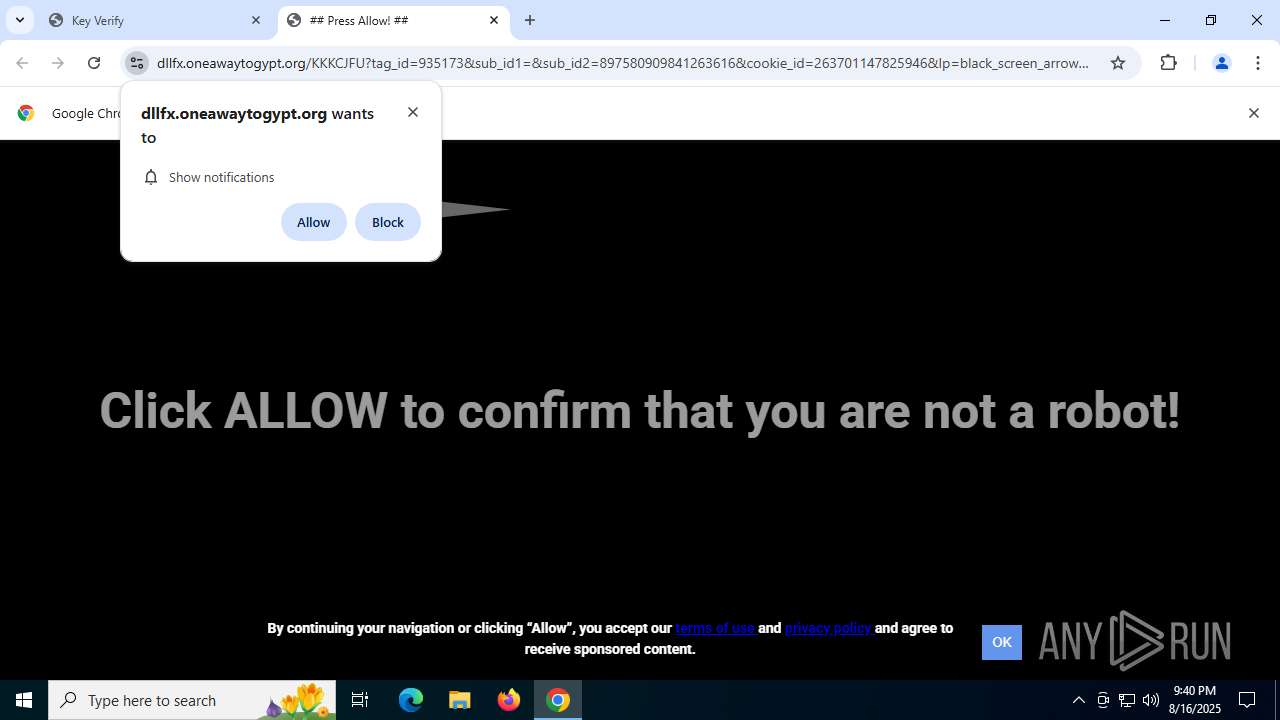
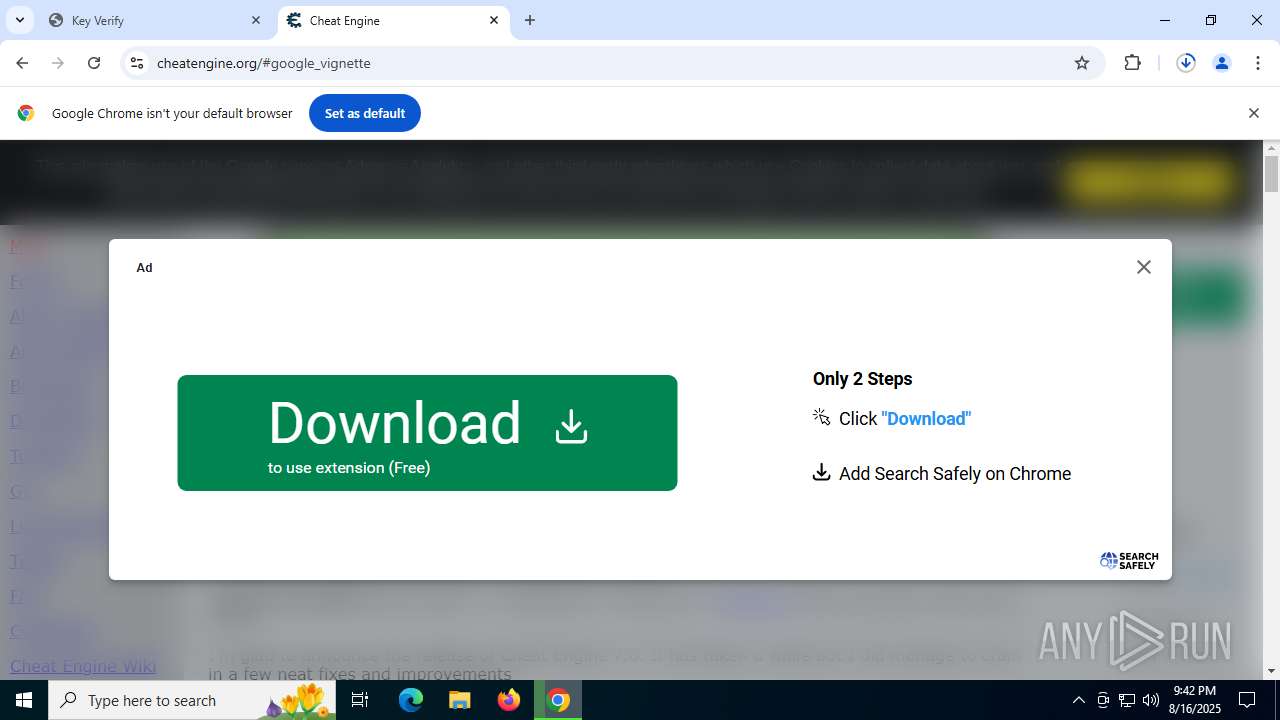
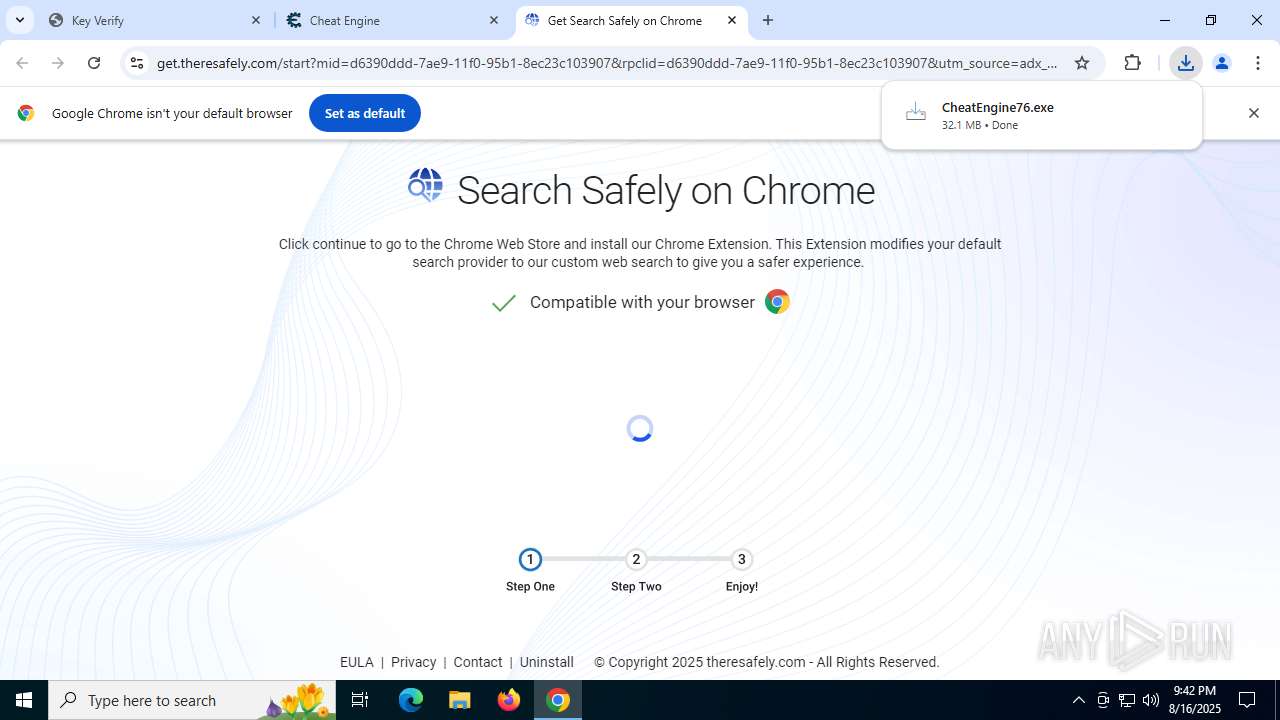
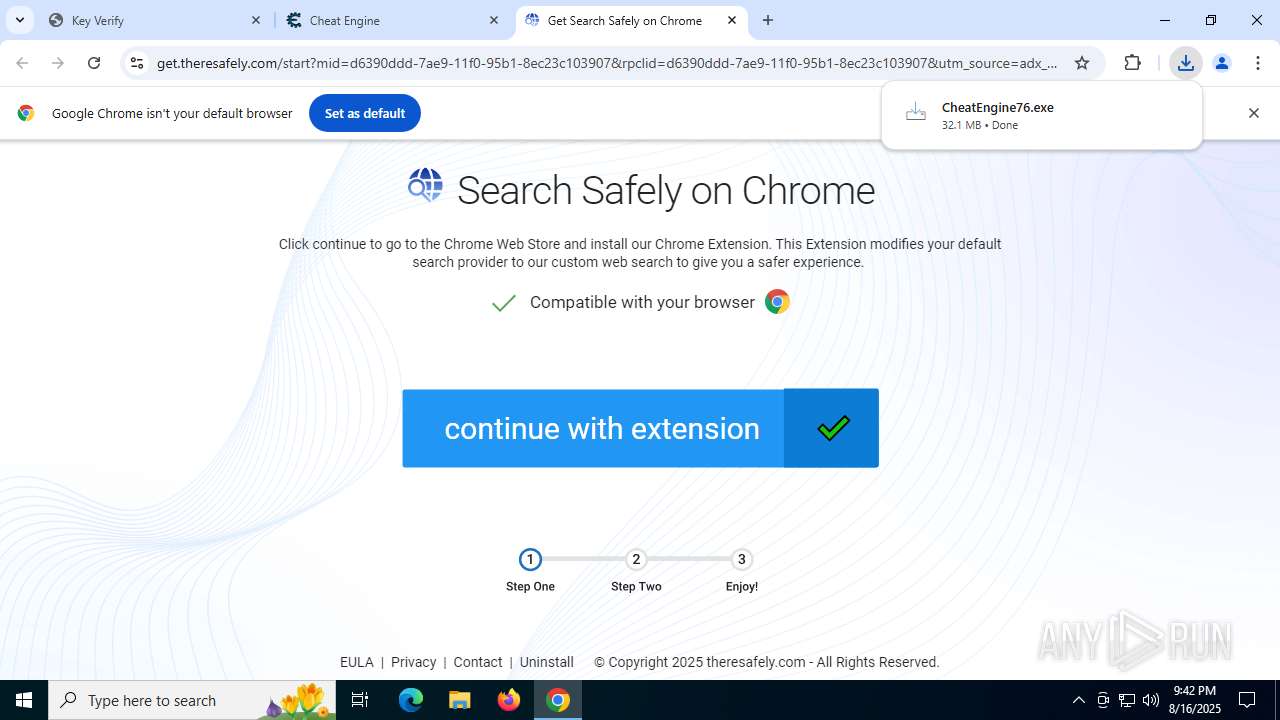
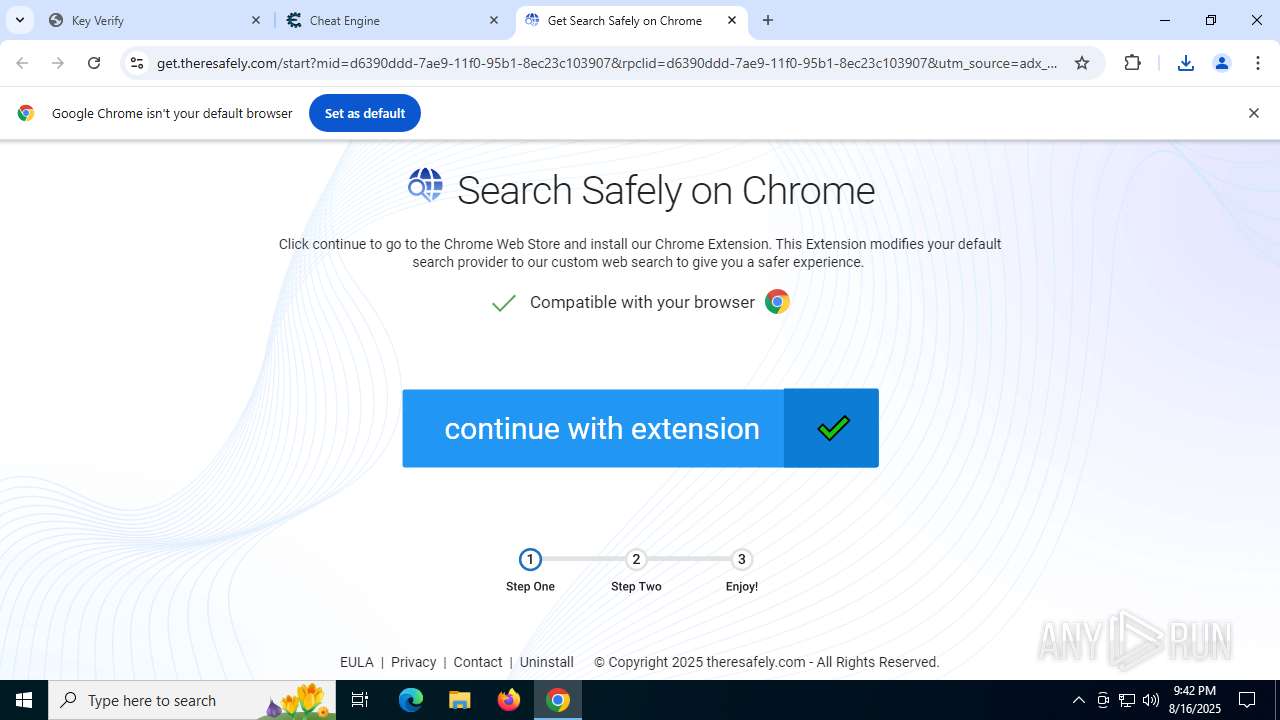
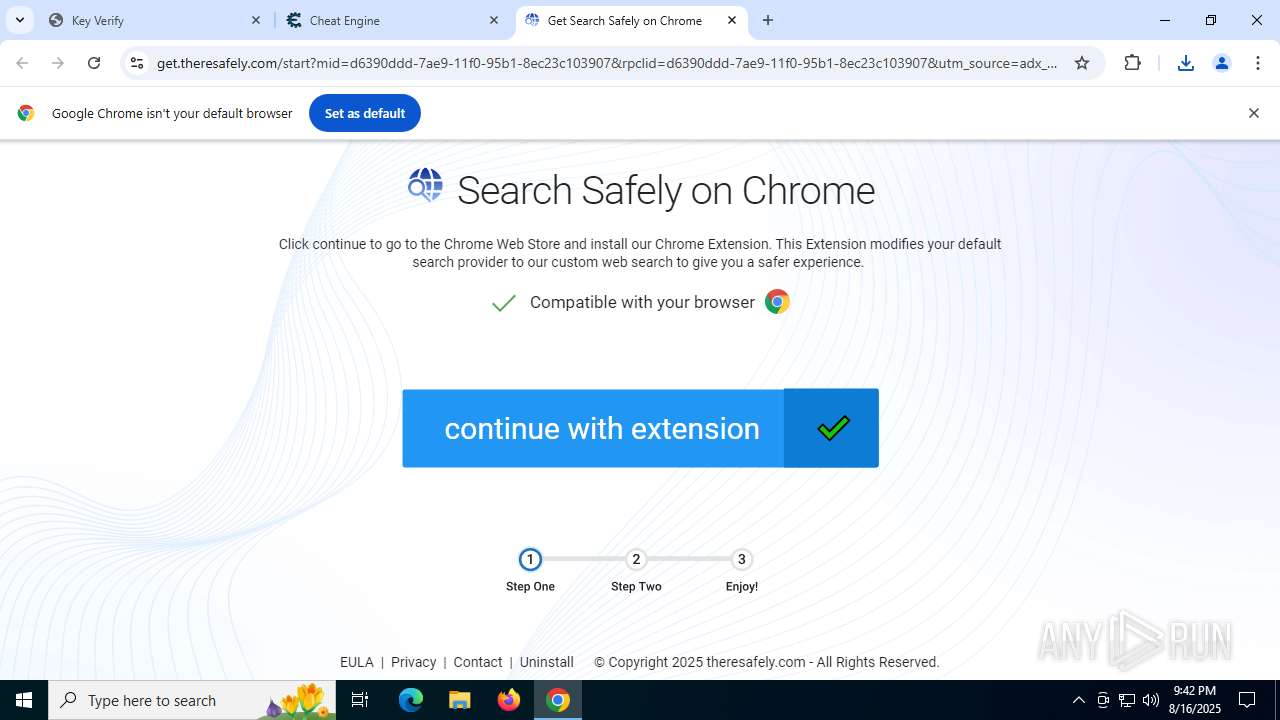
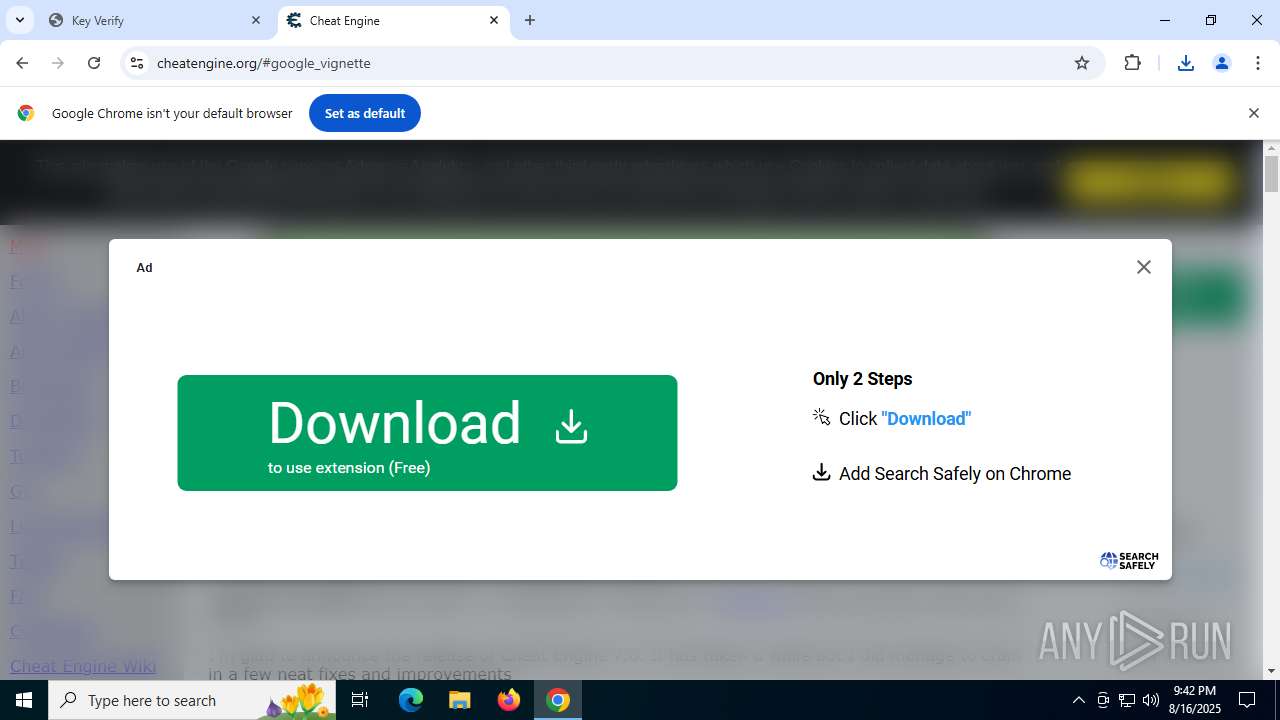
PHISHING has been detected (SURICATA)
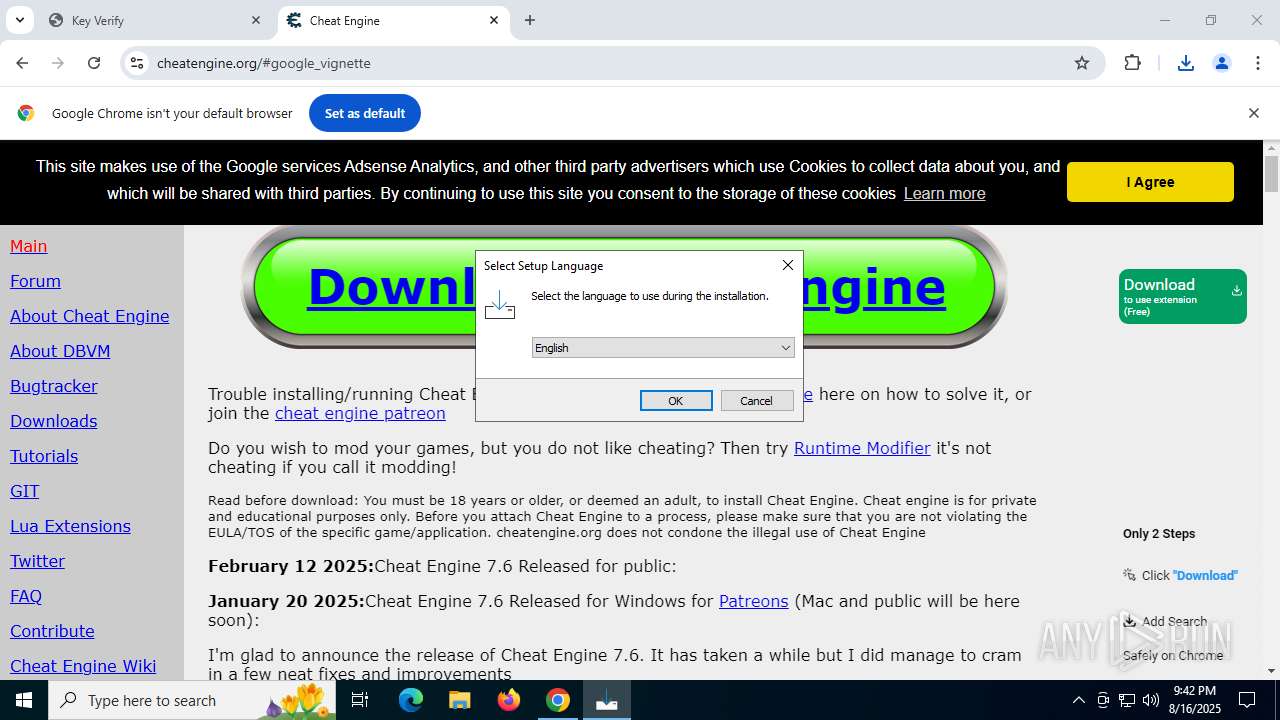
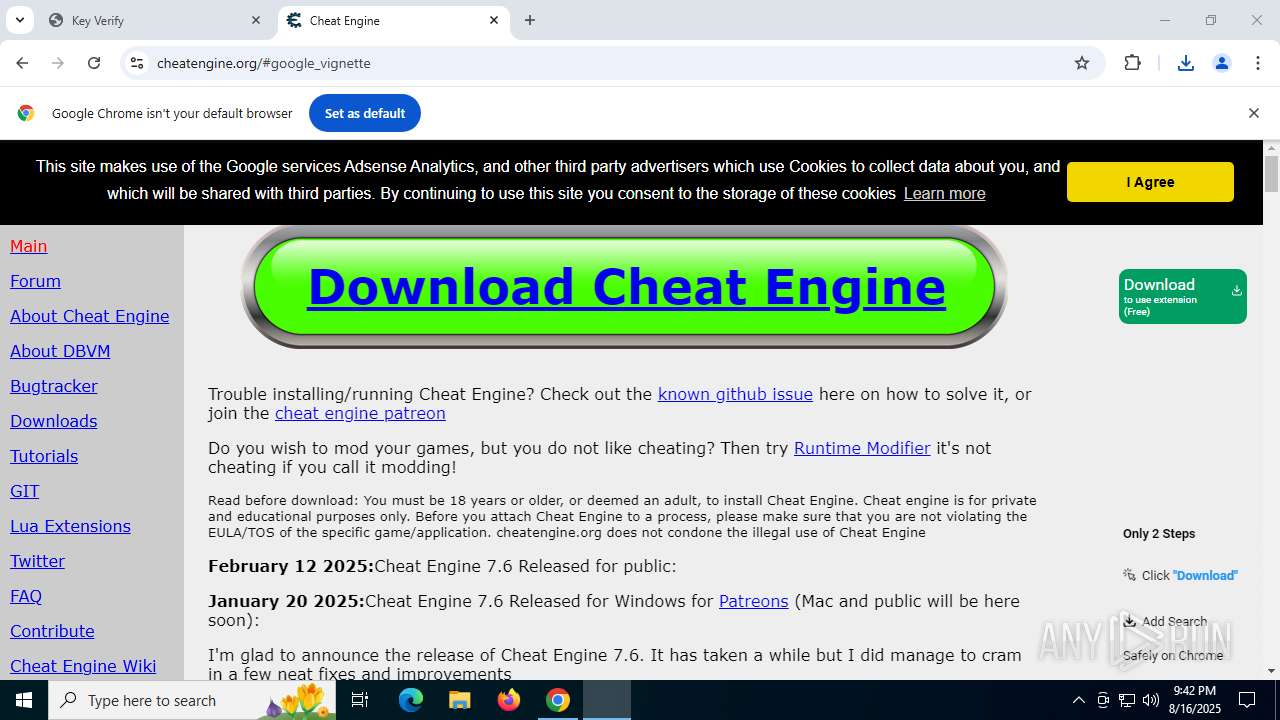
- chrome.exe (PID: 1568)
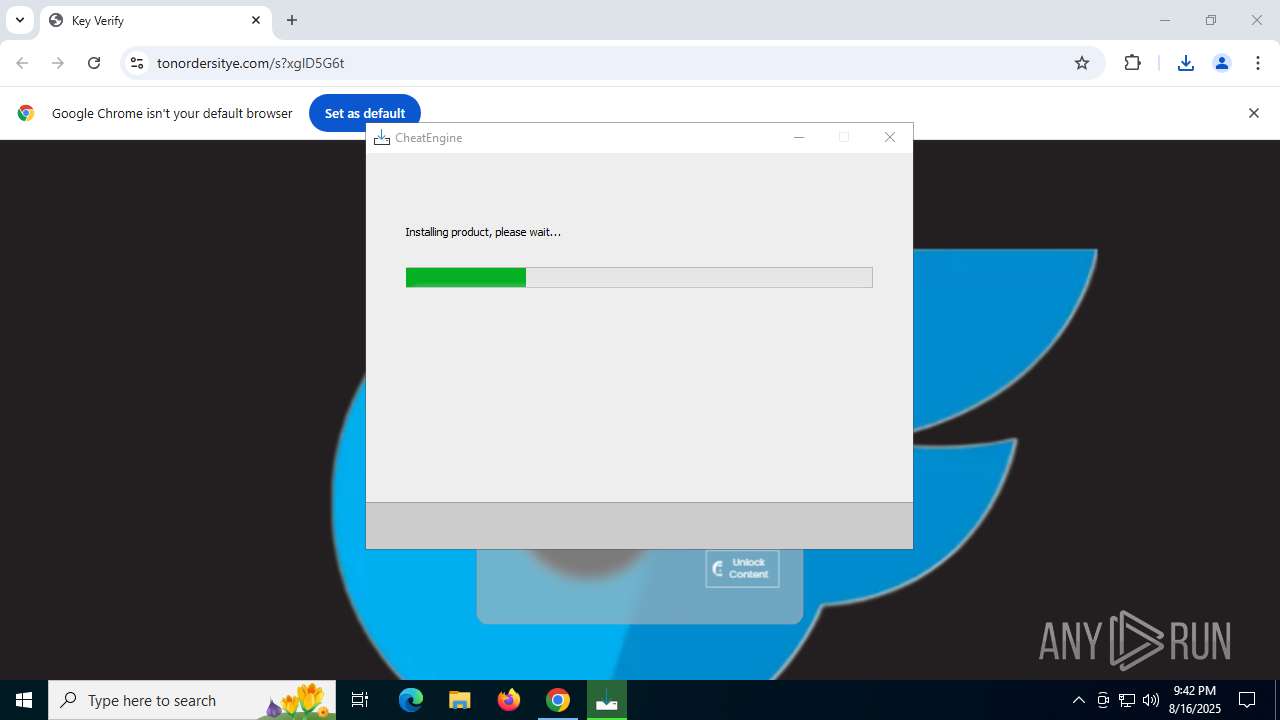
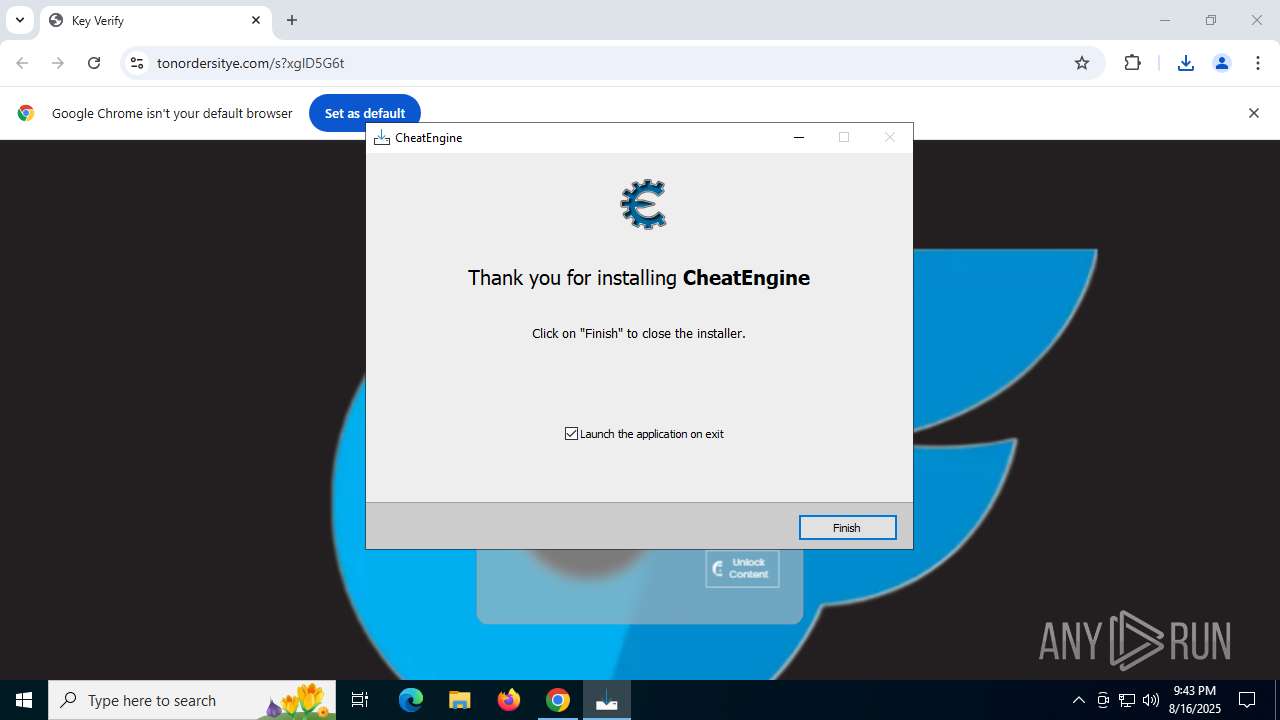
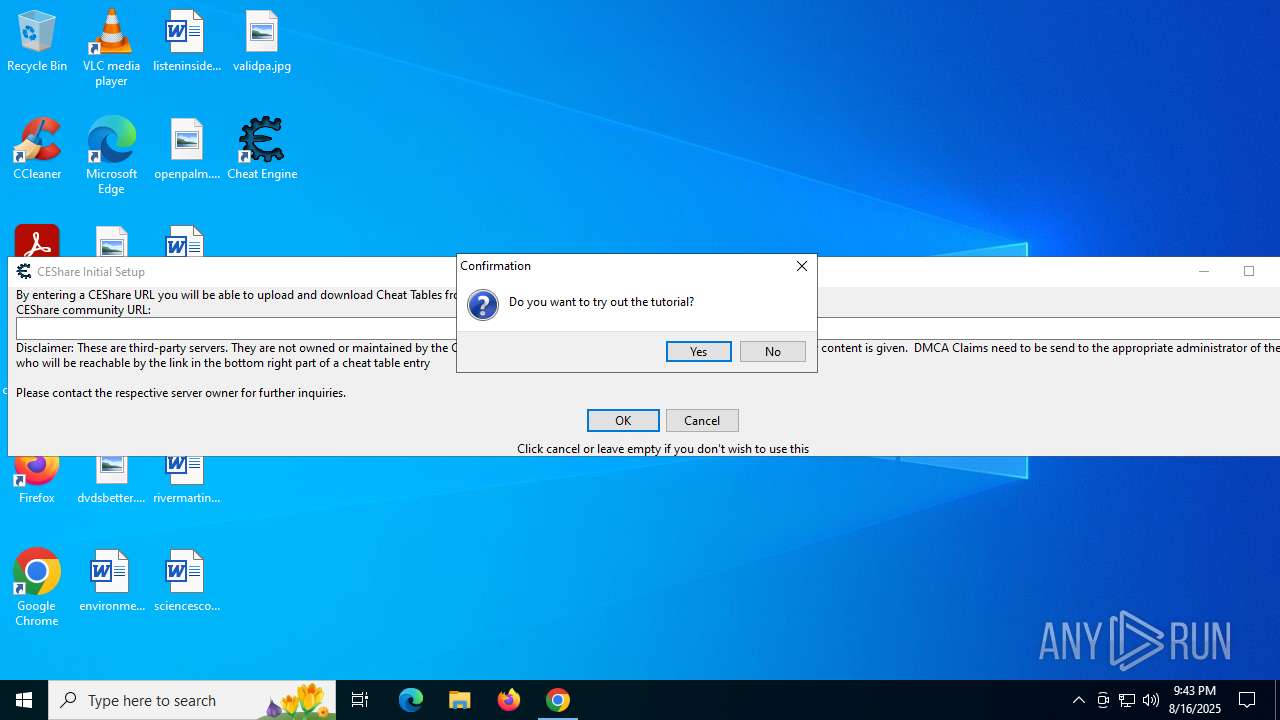
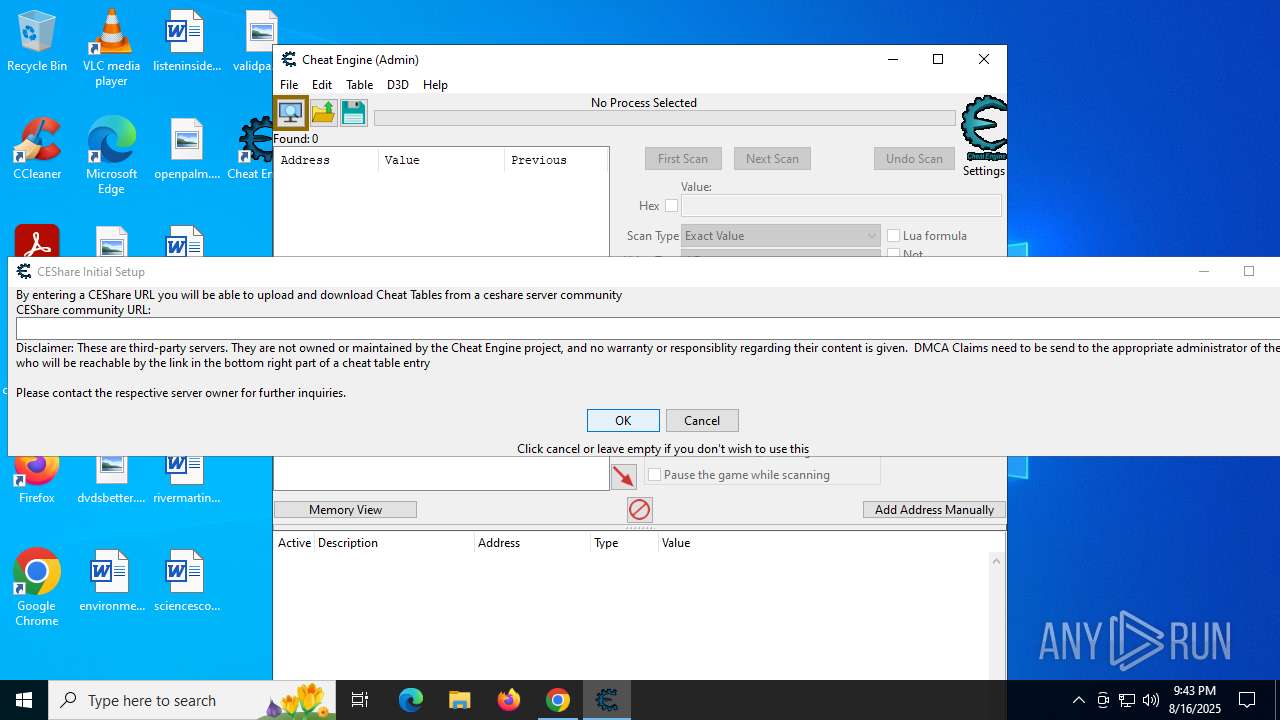
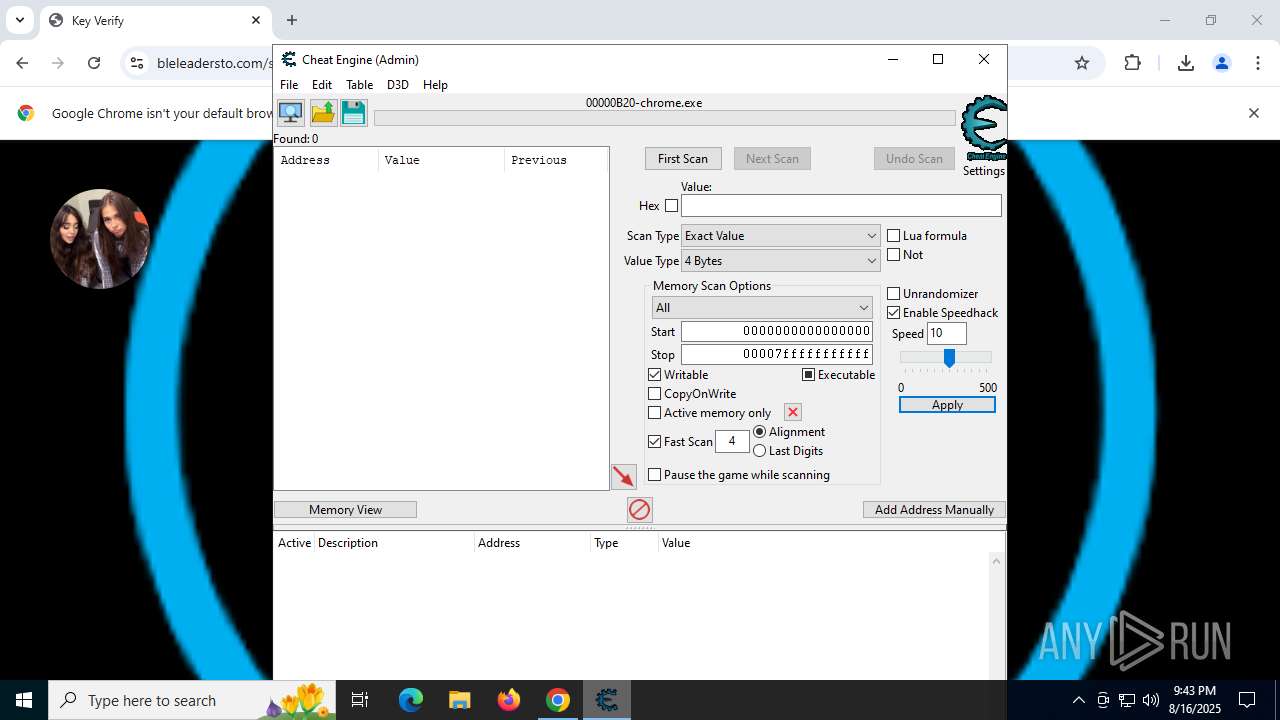
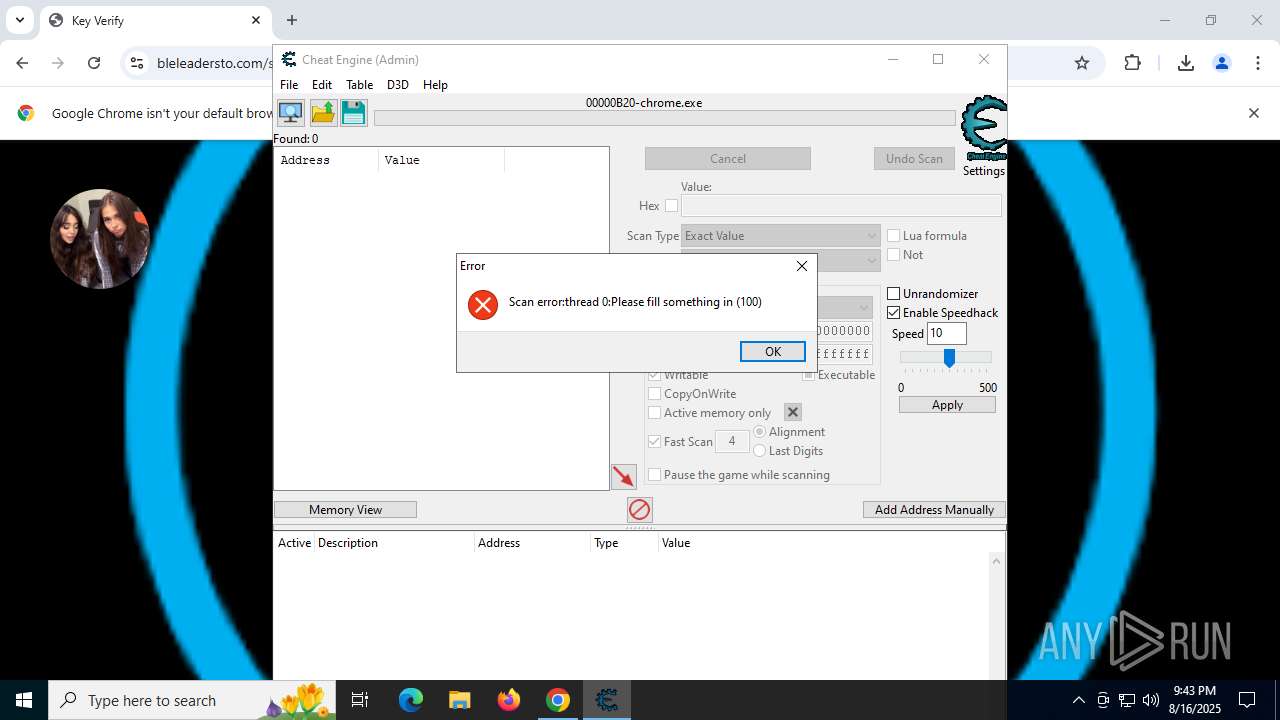
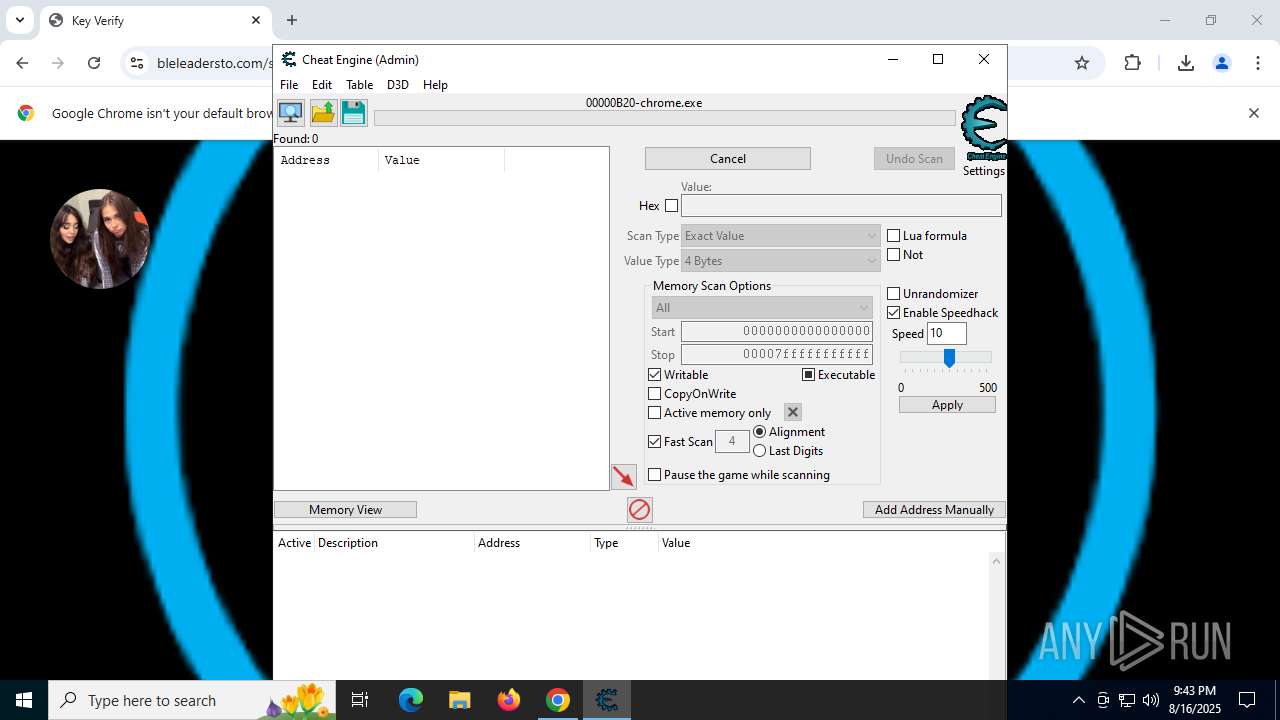
Bundleinstaller mutex has been found
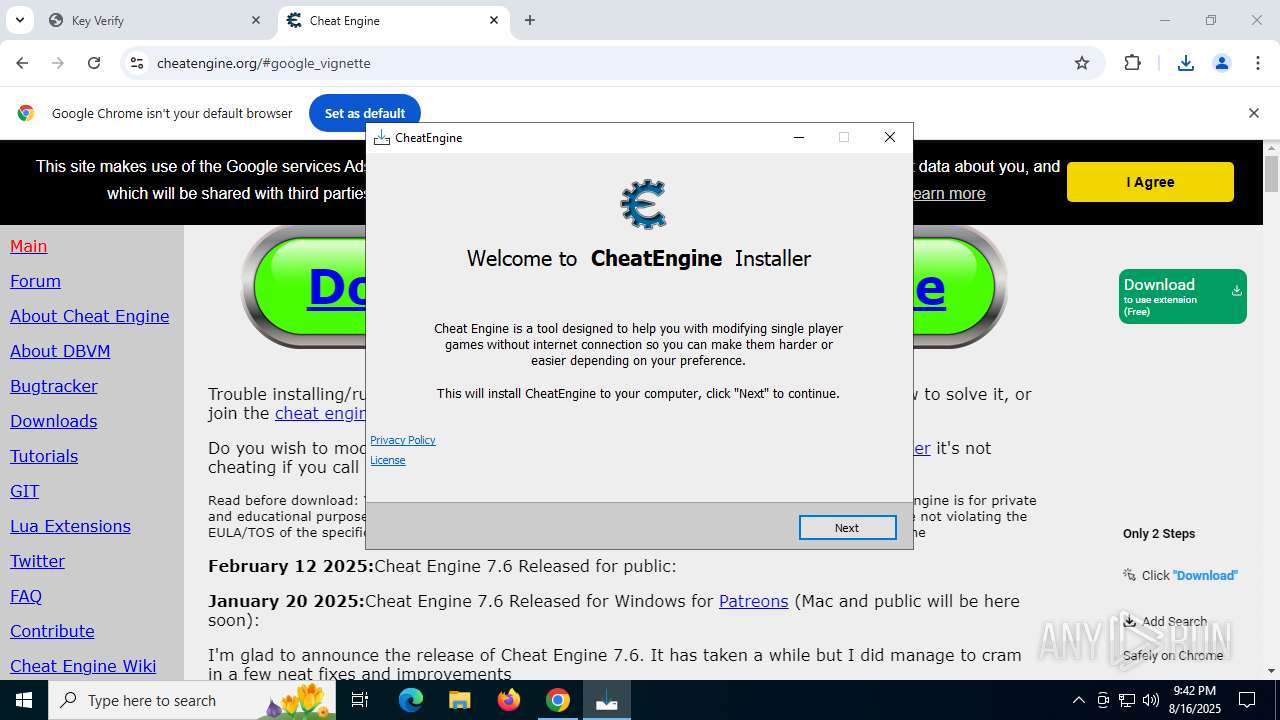
- CheatEngine76.tmp (PID: 760)
Starts NET.EXE for service management
- net.exe (PID: 4380)
- net.exe (PID: 6260)
- CheatEngine76.tmp (PID: 7352)
- net.exe (PID: 7600)
SUSPICIOUS
Executable content was dropped or overwritten
- CheatEngine76.exe (PID: 2728)
- CheatEngine76.exe (PID: 7340)
- CheatEngine76.tmp (PID: 760)
- CheatEngine76.exe (PID: 4676)
- CheatEngine76.tmp (PID: 7352)
- saBSI.exe (PID: 7268)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8020)
- installer.exe (PID: 8024)
Reads security settings of Internet Explorer
- CheatEngine76.tmp (PID: 5460)
- CheatEngine76.tmp (PID: 760)
- saBSI.exe (PID: 7268)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8024)
- Cheat Engine.exe (PID: 3160)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- uihost.exe (PID: 7568)
Reads the Windows owner or organization settings
- CheatEngine76.tmp (PID: 760)
- CheatEngine76.tmp (PID: 7352)
Windows service management via SC.EXE
- sc.exe (PID: 6856)
- sc.exe (PID: 7692)
- sc.exe (PID: 7984)
Starts SC.EXE for service management
- CheatEngine76.tmp (PID: 7352)
Uses ICACLS.EXE to modify access control lists
- CheatEngine76.tmp (PID: 7352)
Adds/modifies Windows certificates
- saBSI.exe (PID: 7268)
- servicehost.exe (PID: 4944)
The process verifies whether the antivirus software is installed
- saBSI.exe (PID: 700)
- installer.exe (PID: 8020)
- installer.exe (PID: 8024)
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
- updater.exe (PID: 6840)
- cmd.exe (PID: 7796)
- cmd.exe (PID: 7288)
Process drops SQLite DLL files
- CheatEngine76.tmp (PID: 7352)
Process drops legitimate windows executable
- CheatEngine76.tmp (PID: 7352)
- installer.exe (PID: 8024)
The process creates files with name similar to system file names
- installer.exe (PID: 8024)
Creates/Modifies COM task schedule object
- installer.exe (PID: 8024)
There is functionality for taking screenshot (YARA)
- CheatEngine76.tmp (PID: 760)
Creates a software uninstall entry
- installer.exe (PID: 8024)
- servicehost.exe (PID: 4944)
Executes as Windows Service
- servicehost.exe (PID: 4944)
Reads Mozilla Firefox installation path
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
Executes application which crashes
- CheatEngine76.tmp (PID: 760)
Searches for installed software
- updater.exe (PID: 6840)
Starts CMD.EXE for commands execution
- updater.exe (PID: 6840)
INFO
Application launched itself
- chrome.exe (PID: 2848)
Reads the software policy settings
- slui.exe (PID: 7764)
- CheatEngine76.tmp (PID: 760)
- saBSI.exe (PID: 7268)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8024)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
- WerFault.exe (PID: 5424)
- WerFault.exe (PID: 6936)
- updater.exe (PID: 6840)
Checks proxy server information
- slui.exe (PID: 7764)
- CheatEngine76.tmp (PID: 760)
- saBSI.exe (PID: 7268)
- saBSI.exe (PID: 700)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- WerFault.exe (PID: 6936)
- WerFault.exe (PID: 5424)
Executable content was dropped or overwritten
- chrome.exe (PID: 6796)
- chrome.exe (PID: 2848)
The sample compiled with english language support
- chrome.exe (PID: 6796)
- CheatEngine76.tmp (PID: 760)
- saBSI.exe (PID: 7268)
- CheatEngine76.tmp (PID: 7352)
- installer.exe (PID: 8020)
- installer.exe (PID: 8024)
Checks supported languages
- CheatEngine76.exe (PID: 2728)
- CheatEngine76.tmp (PID: 5460)
- CheatEngine76.exe (PID: 7340)
- CheatEngine76.tmp (PID: 760)
- CheatEngine76.exe (PID: 4676)
- saBSI.exe (PID: 7268)
- CheatEngine76.tmp (PID: 7352)
- _setup64.tmp (PID: 7936)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8020)
- installer.exe (PID: 8024)
- Kernelmoduleunloader.exe (PID: 6780)
- windowsrepair.exe (PID: 7700)
- Cheat Engine.exe (PID: 3160)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
- updater.exe (PID: 6840)
Create files in a temporary directory
- CheatEngine76.exe (PID: 2728)
- CheatEngine76.exe (PID: 7340)
- CheatEngine76.tmp (PID: 760)
- CheatEngine76.exe (PID: 4676)
- CheatEngine76.tmp (PID: 7352)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8024)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
Reads the computer name
- CheatEngine76.tmp (PID: 5460)
- CheatEngine76.exe (PID: 7340)
- CheatEngine76.tmp (PID: 760)
- saBSI.exe (PID: 7268)
- CheatEngine76.exe (PID: 4676)
- CheatEngine76.tmp (PID: 7352)
- saBSI.exe (PID: 700)
- Kernelmoduleunloader.exe (PID: 6780)
- installer.exe (PID: 8024)
- Cheat Engine.exe (PID: 3160)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
- updater.exe (PID: 6840)
Process checks computer location settings
- CheatEngine76.tmp (PID: 5460)
- CheatEngine76.tmp (PID: 760)
- Cheat Engine.exe (PID: 3160)
- servicehost.exe (PID: 4944)
CHEATENGINE mutex has been found
- CheatEngine76.tmp (PID: 760)
Compiled with Borland Delphi (YARA)
- CheatEngine76.tmp (PID: 5460)
- CheatEngine76.exe (PID: 2728)
- CheatEngine76.exe (PID: 7340)
- CheatEngine76.tmp (PID: 760)
Reads the machine GUID from the registry
- CheatEngine76.tmp (PID: 760)
- saBSI.exe (PID: 7268)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8024)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
- updater.exe (PID: 6840)
Detects InnoSetup installer (YARA)
- CheatEngine76.tmp (PID: 5460)
- CheatEngine76.exe (PID: 2728)
- CheatEngine76.exe (PID: 7340)
- CheatEngine76.tmp (PID: 760)
Creates files in the program directory
- saBSI.exe (PID: 7268)
- CheatEngine76.tmp (PID: 7352)
- saBSI.exe (PID: 700)
- installer.exe (PID: 8024)
- installer.exe (PID: 8020)
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- servicehost.exe (PID: 4944)
- uihost.exe (PID: 7568)
Creates a software uninstall entry
- CheatEngine76.tmp (PID: 7352)
Creates files or folders in the user directory
- cheatengine-x86_64-SSE4-AVX2.exe (PID: 1948)
- WerFault.exe (PID: 6936)
- WerFault.exe (PID: 5424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
268
Monitored processes
117
Malicious processes
13
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | C:\WINDOWS\system32\net1 stop vgk | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
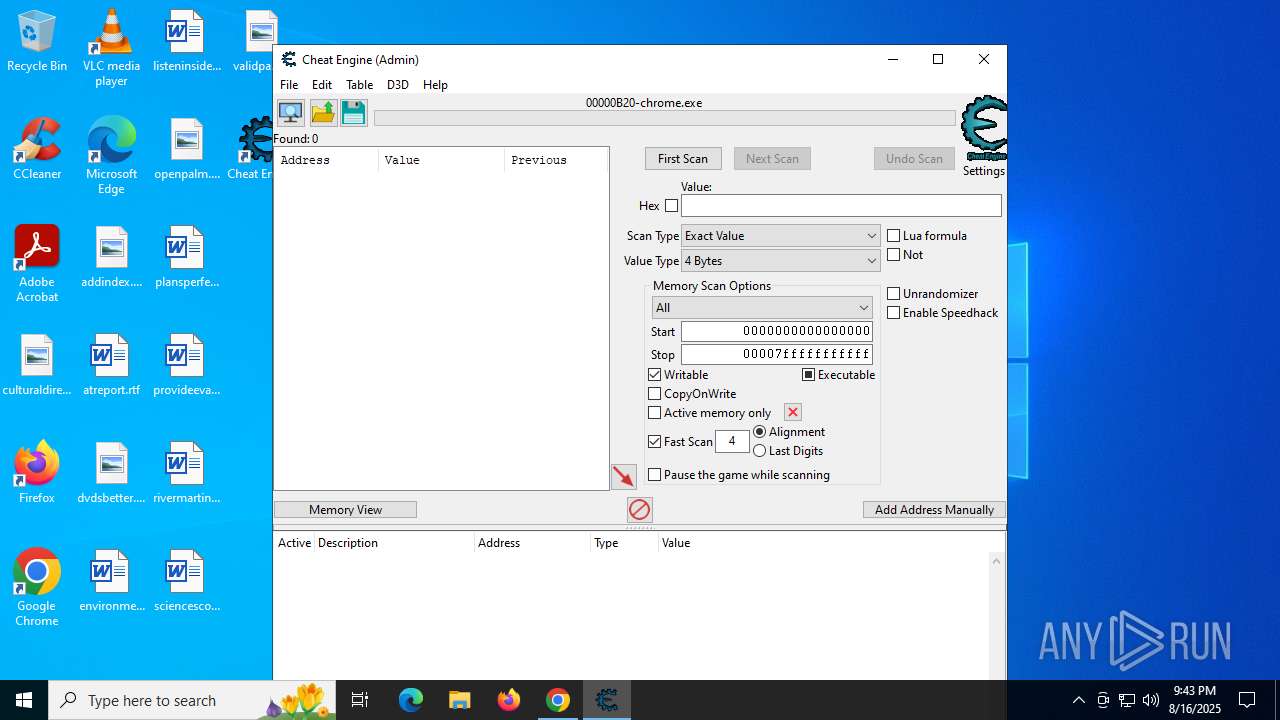
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --field-trial-handle=6068,i,11845077657670697517,7742416527587651589,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5892 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | _setup64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 700 | "C:\ProgramData\McAfee\WebAdvisor\saBSI\saBSI.exe" /install /affid 91082 PaidDistribution=true InstallID=GnjW0t7PiXHPGcw26ICbgfZiSXcDsZT2gnUhcuFUm2YG8i9Y5tEyPbi1izi32GVlXYIBfCW2IczxJsTLYJA saBsiVersion=4.1.1.865 CountryCode=GB /no_self_update | C:\ProgramData\McAfee\WebAdvisor\saBSI\saBSI.exe | saBSI.exe | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(bootstrap installer) Exit code: 0 Version: 4,1,1,1006 Modules
| |||||||||||||||
| 760 | "C:\Users\admin\AppData\Local\Temp\is-GH0HH.tmp\CheatEngine76.tmp" /SL5="$B0352,32631605,845824,C:\Users\admin\Downloads\CheatEngine76.exe" /SPAWNWND=$902E6 /NOTIFYWND=$B032A | C:\Users\admin\AppData\Local\Temp\is-GH0HH.tmp\CheatEngine76.tmp | CheatEngine76.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 3221226525 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2180,i,11845077657670697517,7742416527587651589,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2176 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --field-trial-handle=3080,i,11845077657670697517,7742416527587651589,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=3112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1828 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
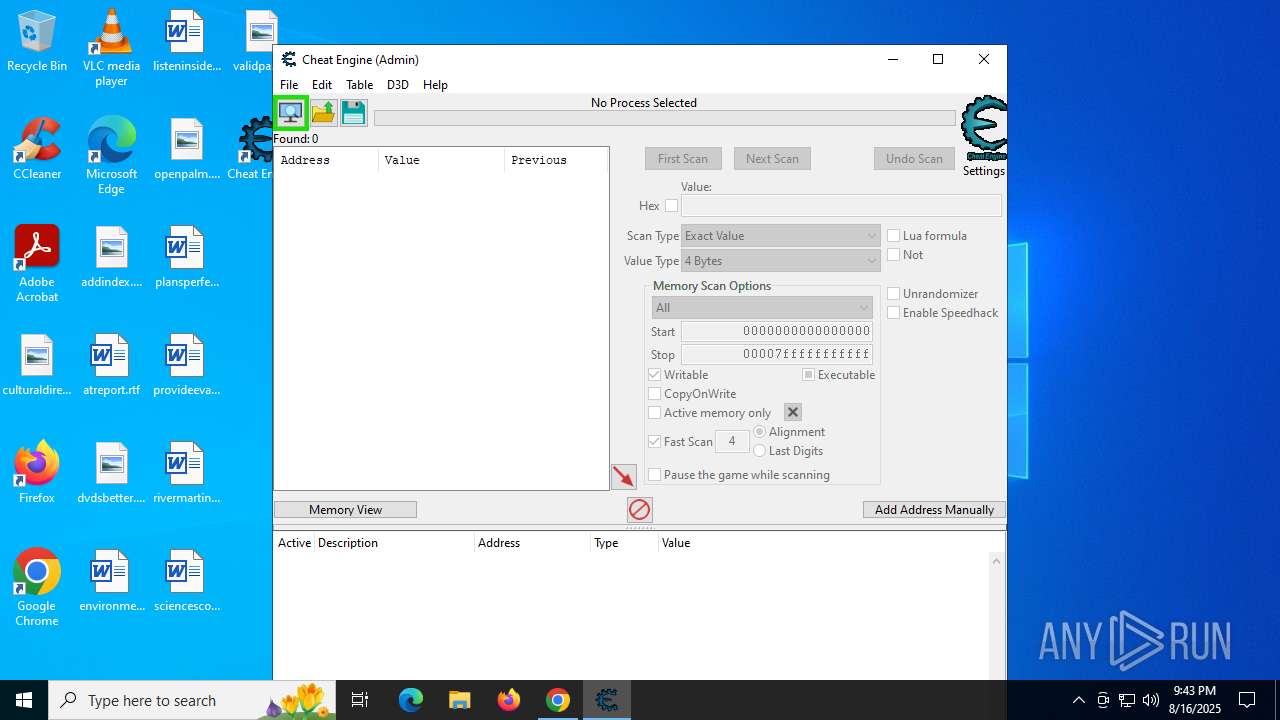
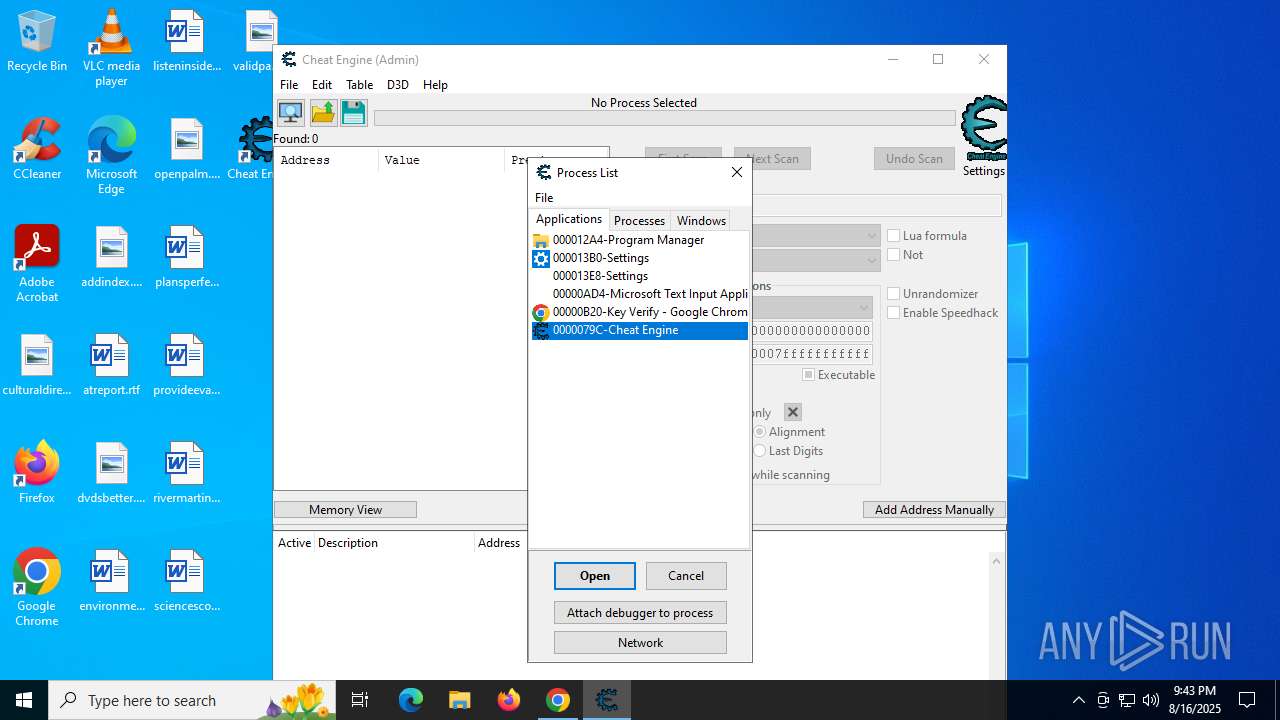
| 1948 | "C:\Program Files\Cheat Engine\cheatengine-x86_64-SSE4-AVX2.exe" | C:\Program Files\Cheat Engine\cheatengine-x86_64-SSE4-AVX2.exe | Cheat Engine.exe | ||||||||||||
User: admin Company: Cheat Engine Integrity Level: HIGH Description: Cheat Engine Version: 7.6.0.8629 Modules
| |||||||||||||||
Total events
49 270
Read events
48 933
Write events
311
Delete events
26
Modification events
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
Executable files
188
Suspicious files
797
Text files
1 238
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18dbe4.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18dbd4.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF18dbf3.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18dbf3.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18dbf3.TMP | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
296
DNS requests
407
Threats
43
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1568 | chrome.exe | GET | 200 | 142.250.186.174:80 | http://clients2.google.com/time/1/current?cup2key=8:do9dHvIP66SbPfiluETzGjIRhJgHJ1GuRANT4alIfzc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.20:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4528 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7636 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7848 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acaldksiunzh56452py2db5mnbpa_120.0.6050.0/jamhcnnkihinmdlkakkaopbjbbcngflc_120.0.6050.0_all_dgzfpknn7v3zslsbhrwu6bt44e.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2028 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1568 | chrome.exe | 142.250.186.174:80 | clients2.google.com | GOOGLE | US | whitelisted |
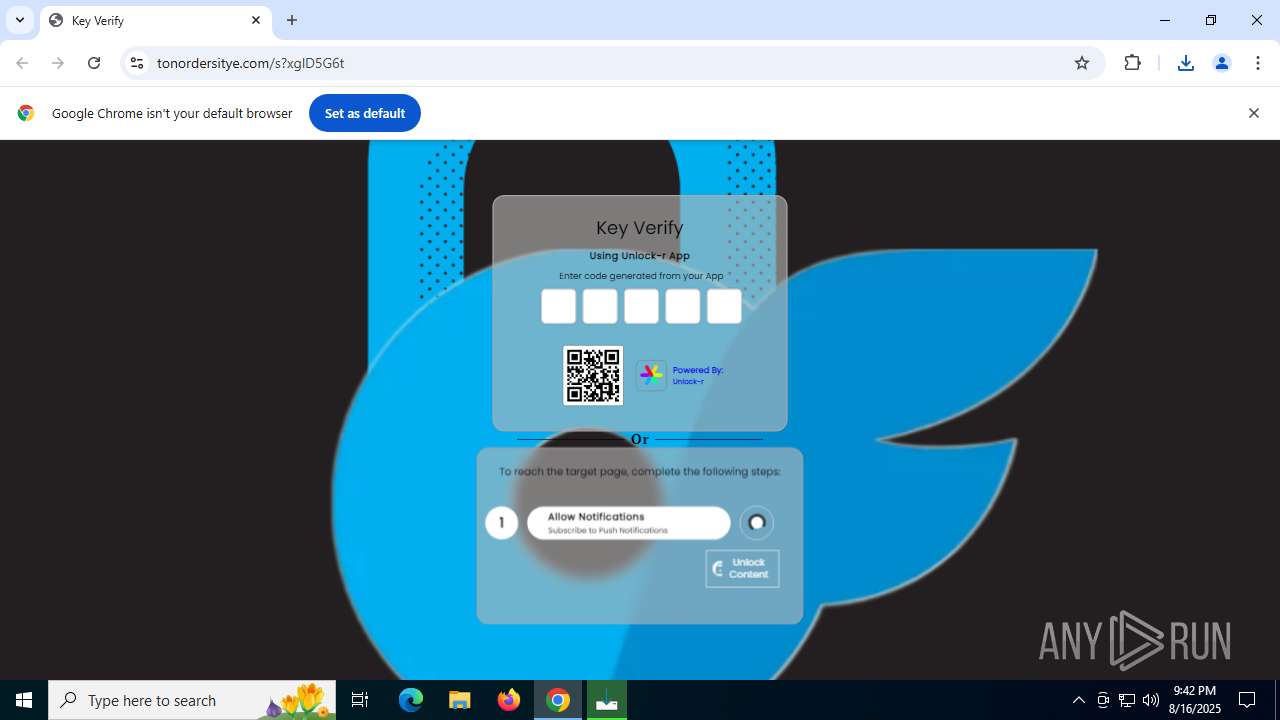
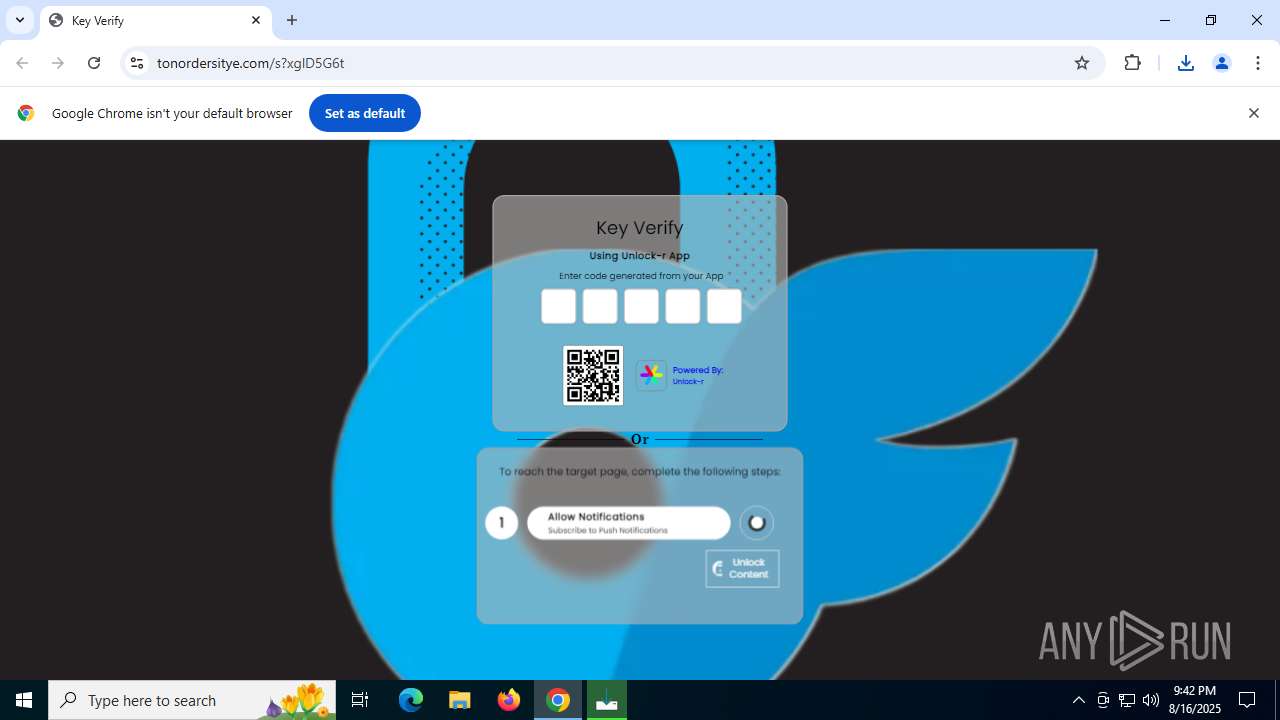
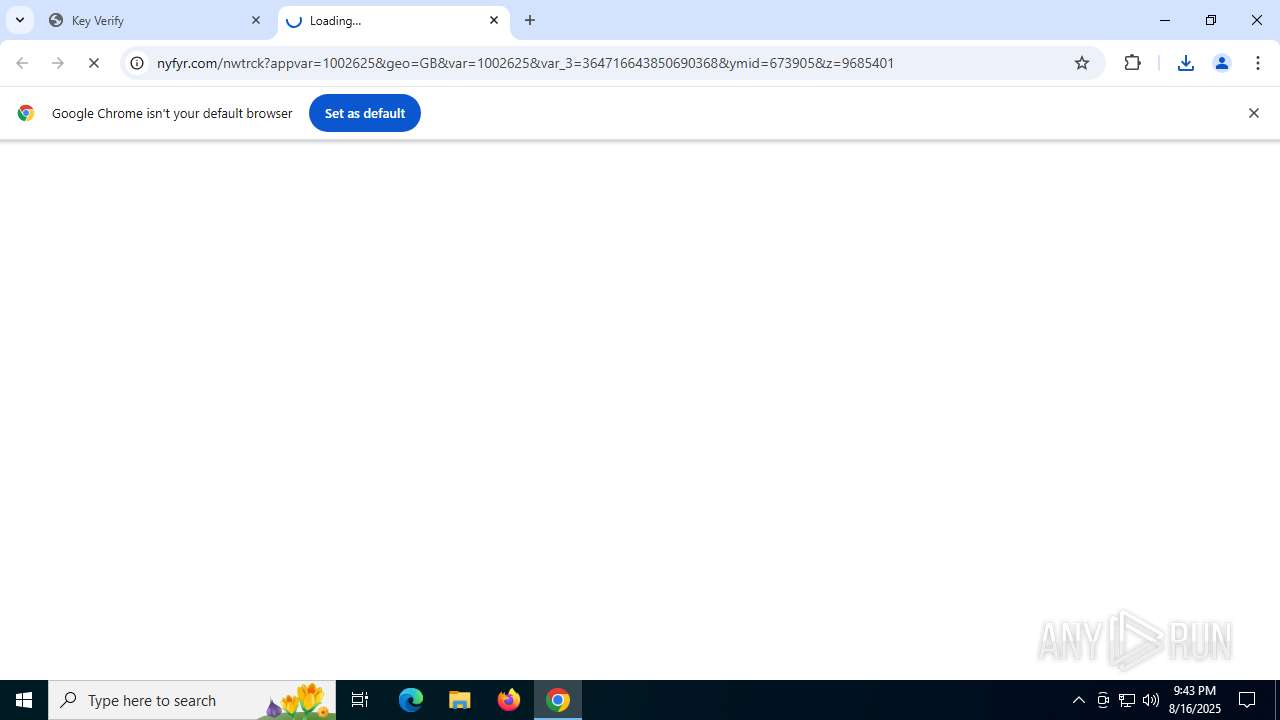
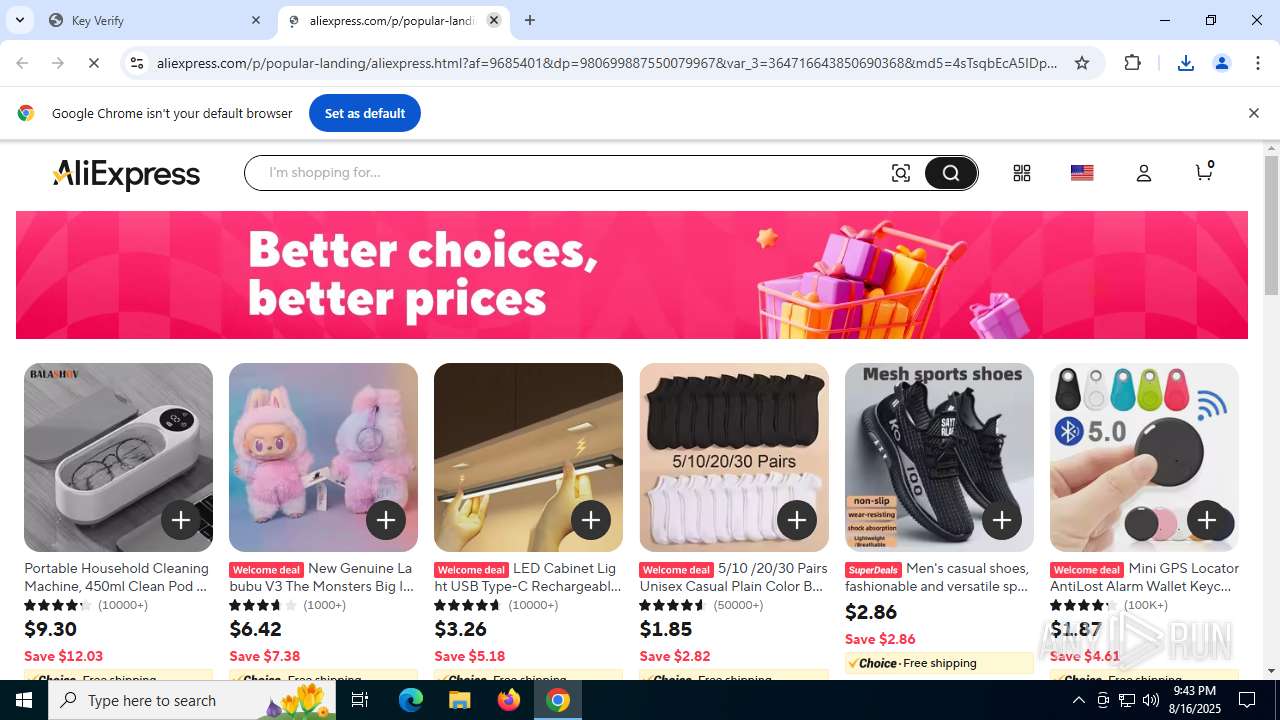
1568 | chrome.exe | 104.21.80.1:443 | fast-links.org | CLOUDFLARENET | — | unknown |
1568 | chrome.exe | 172.217.23.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
1568 | chrome.exe | 74.125.206.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
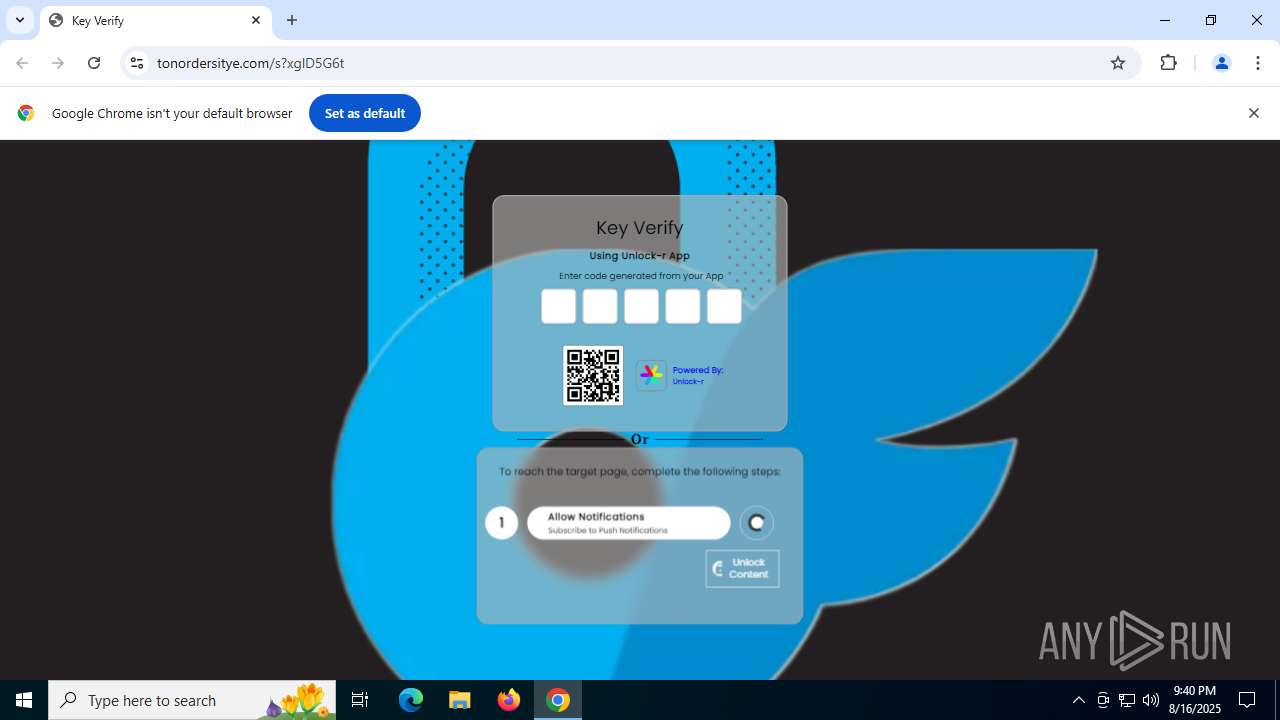
1568 | chrome.exe | 188.114.96.3:443 | tonordersitye.com | CLOUDFLARENET | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
fast-links.org |
| unknown |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
tonordersitye.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
d1wzdj81h1hubn.cloudfront.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
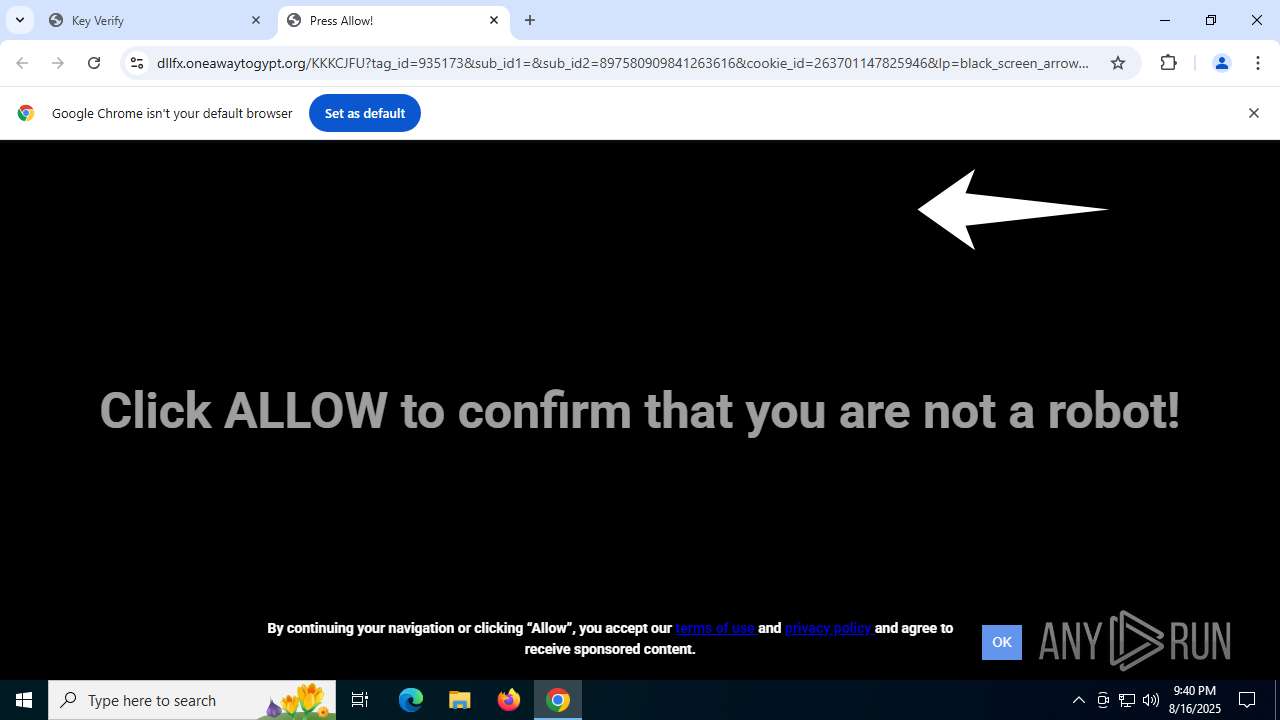
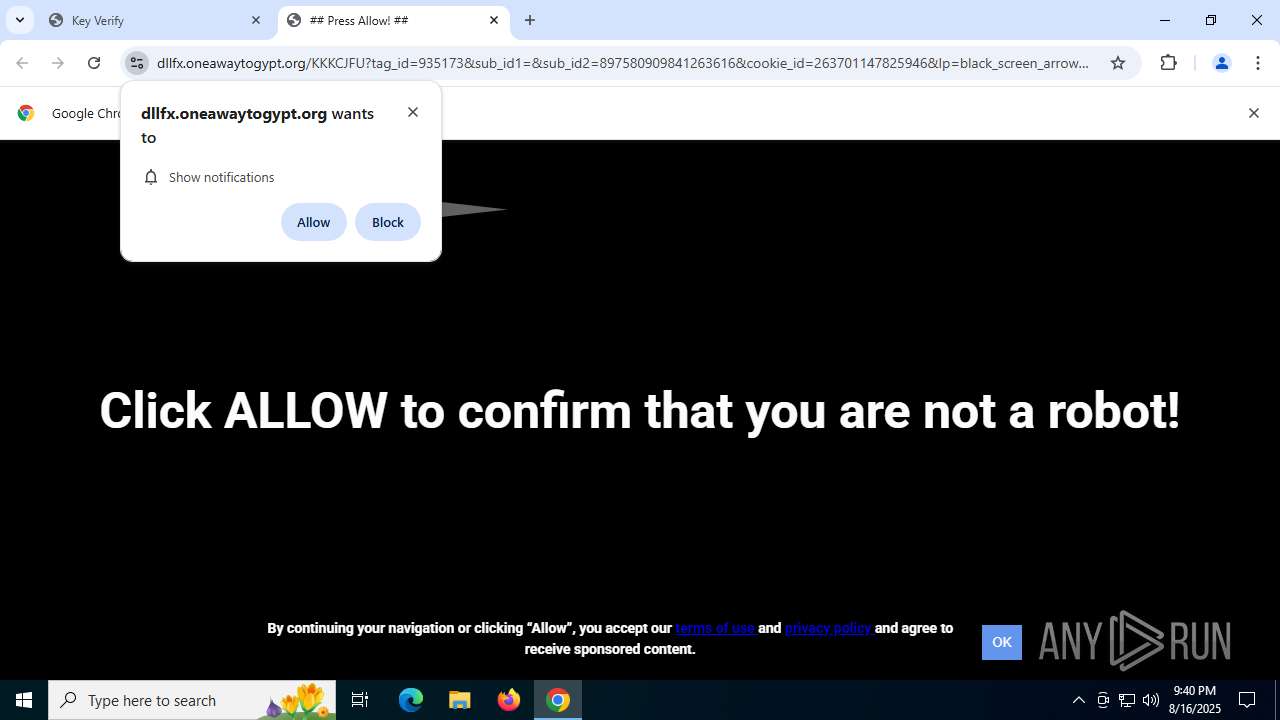
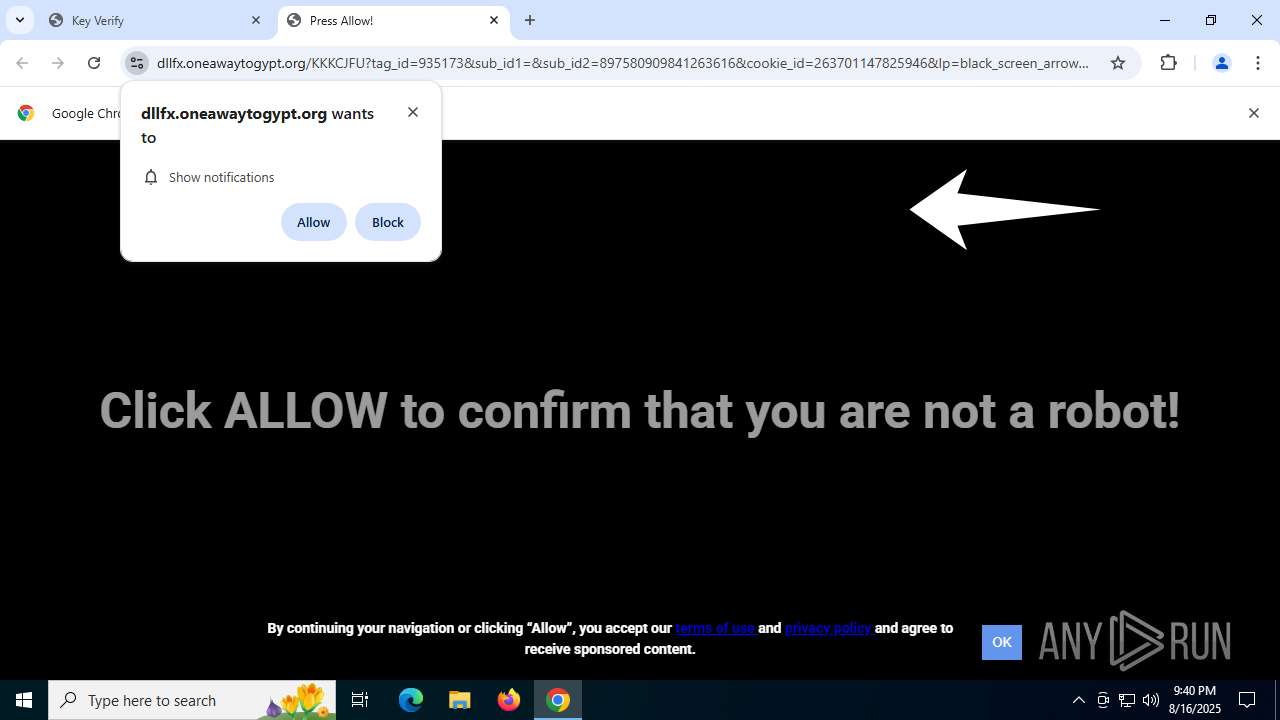
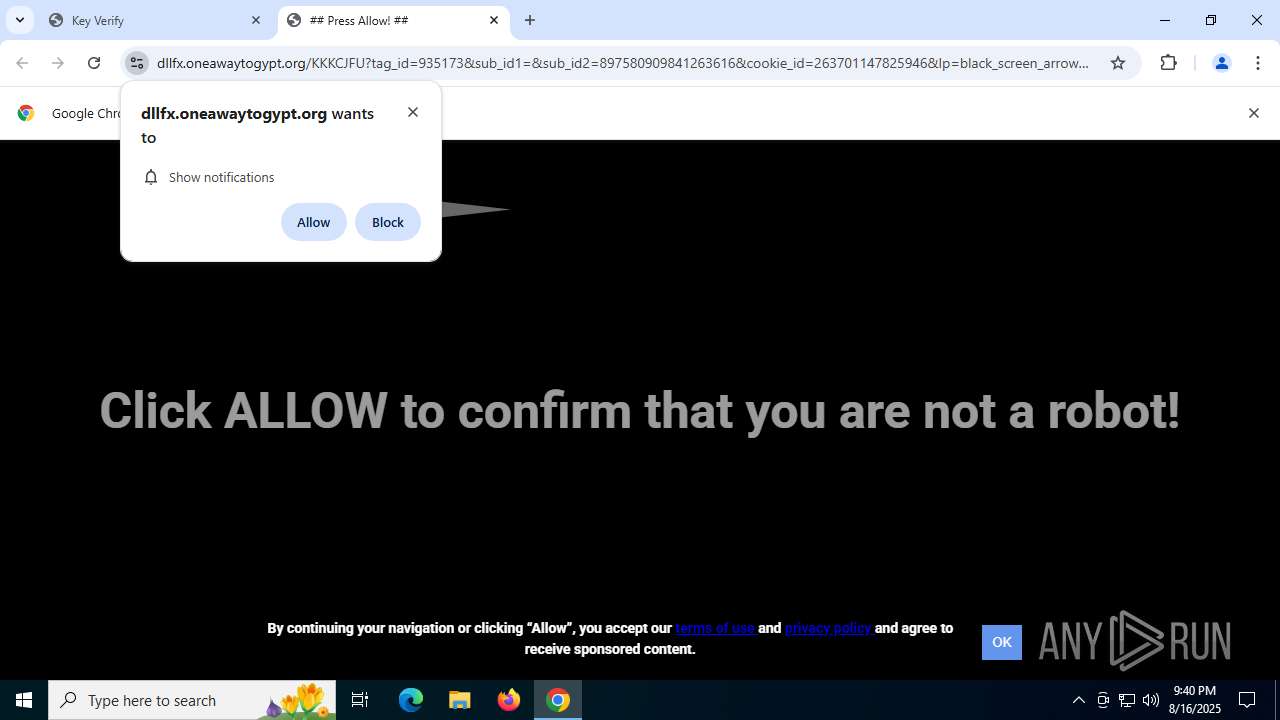
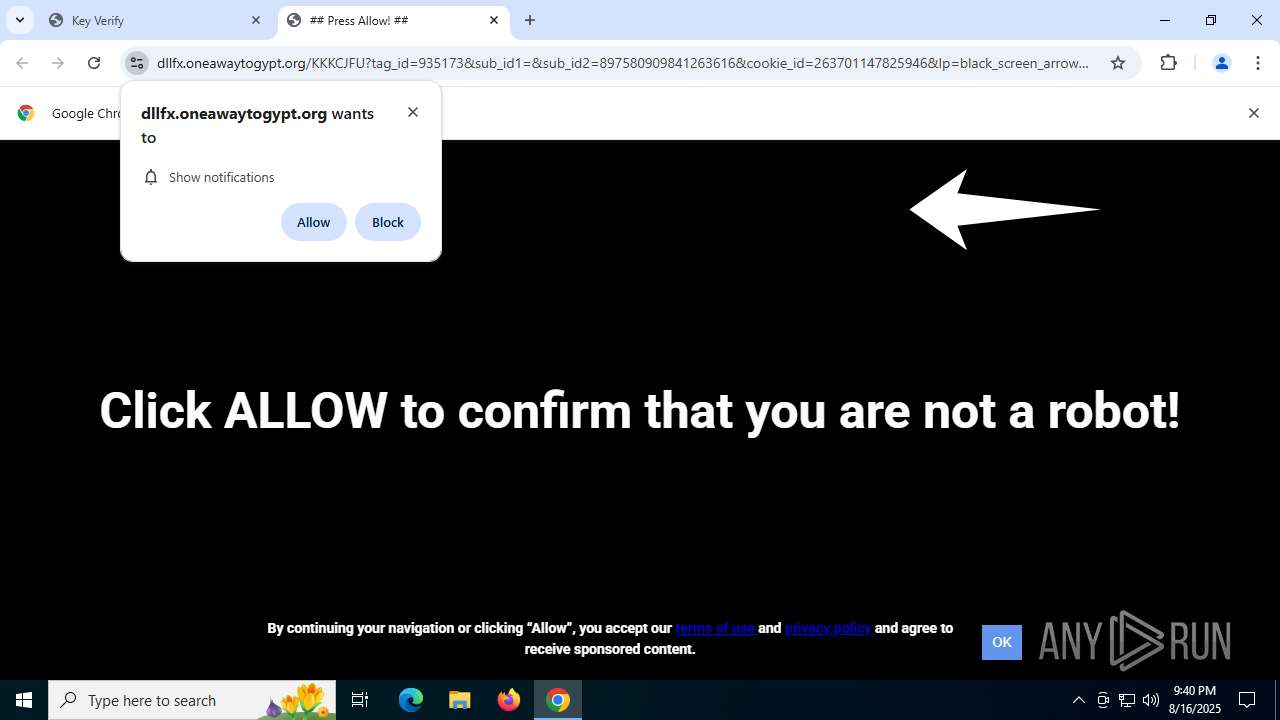
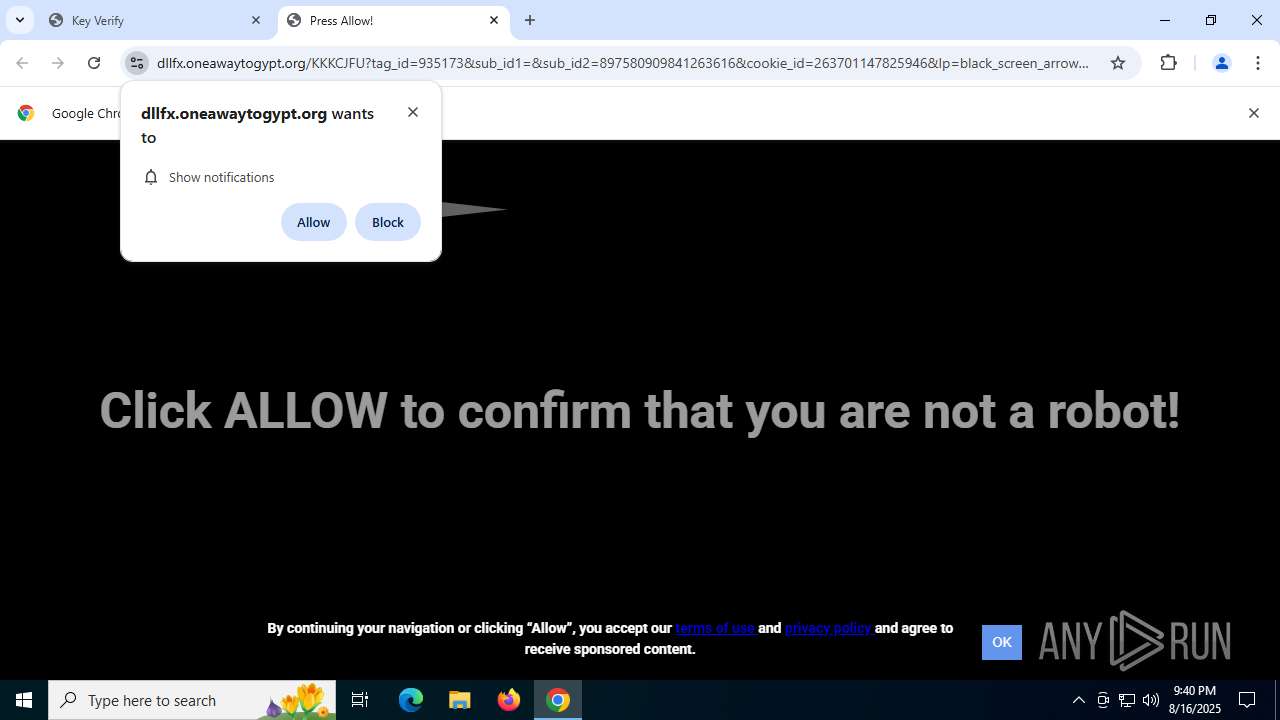
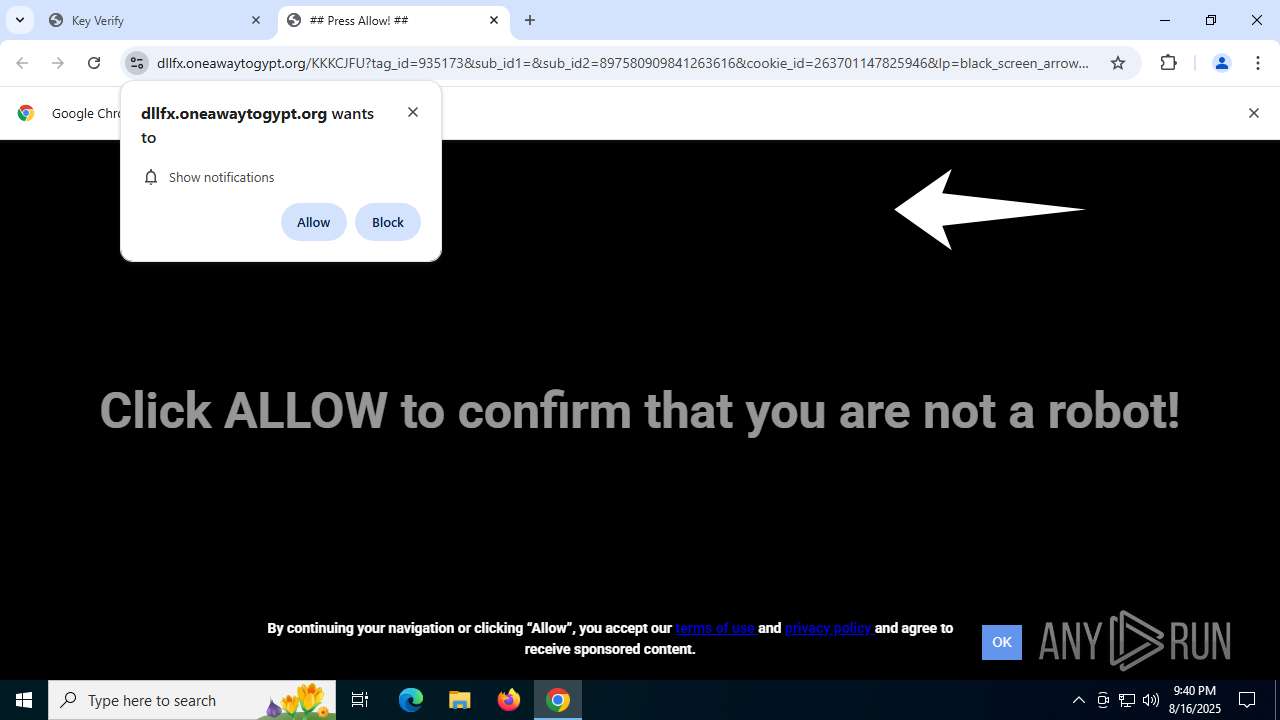
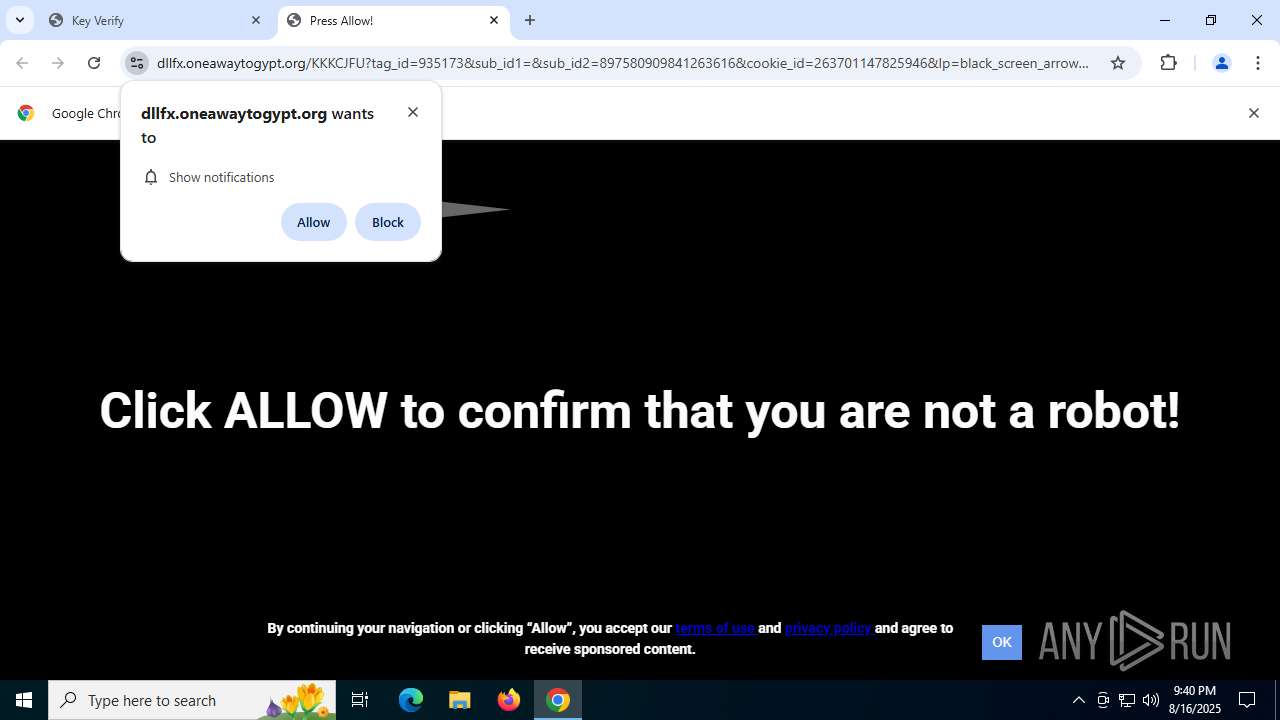
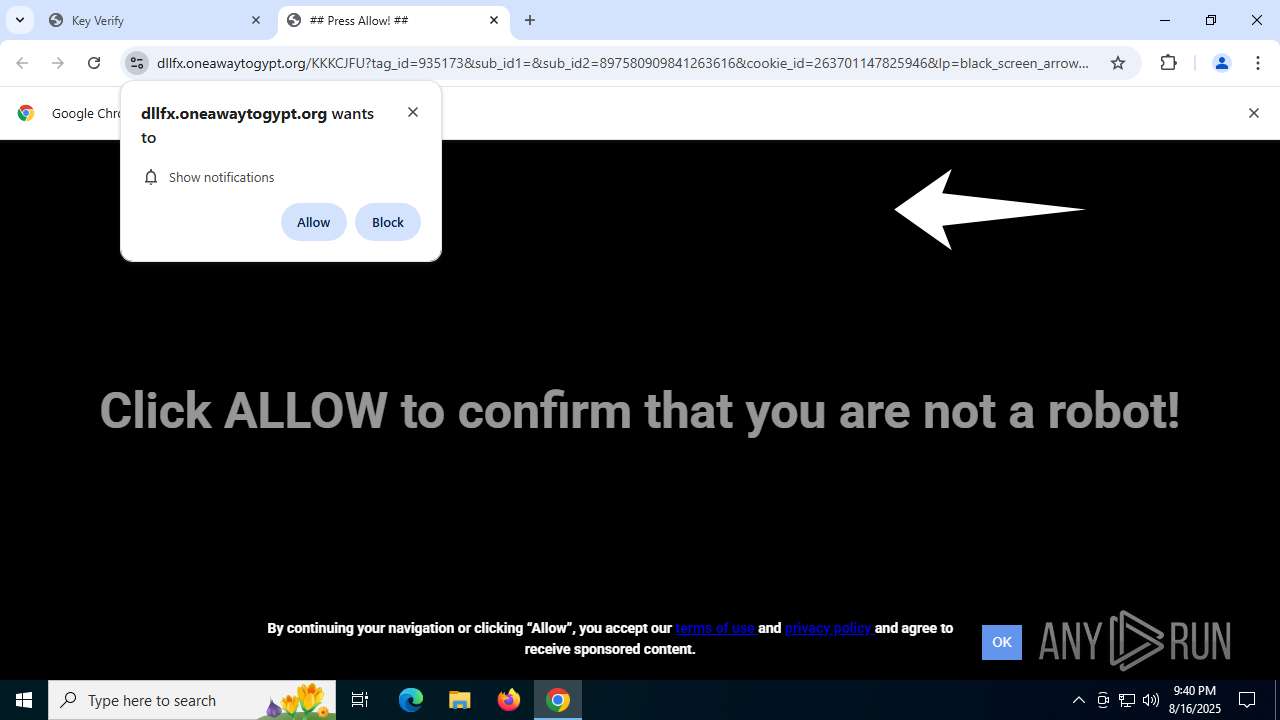
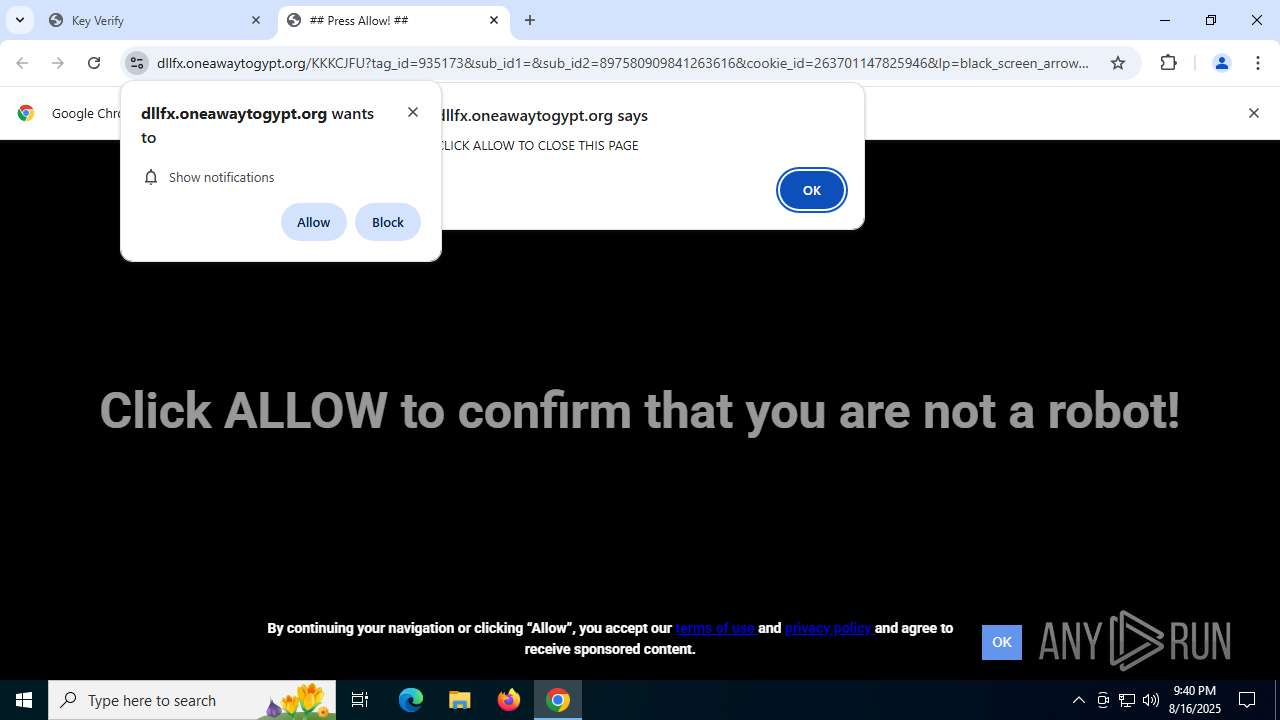
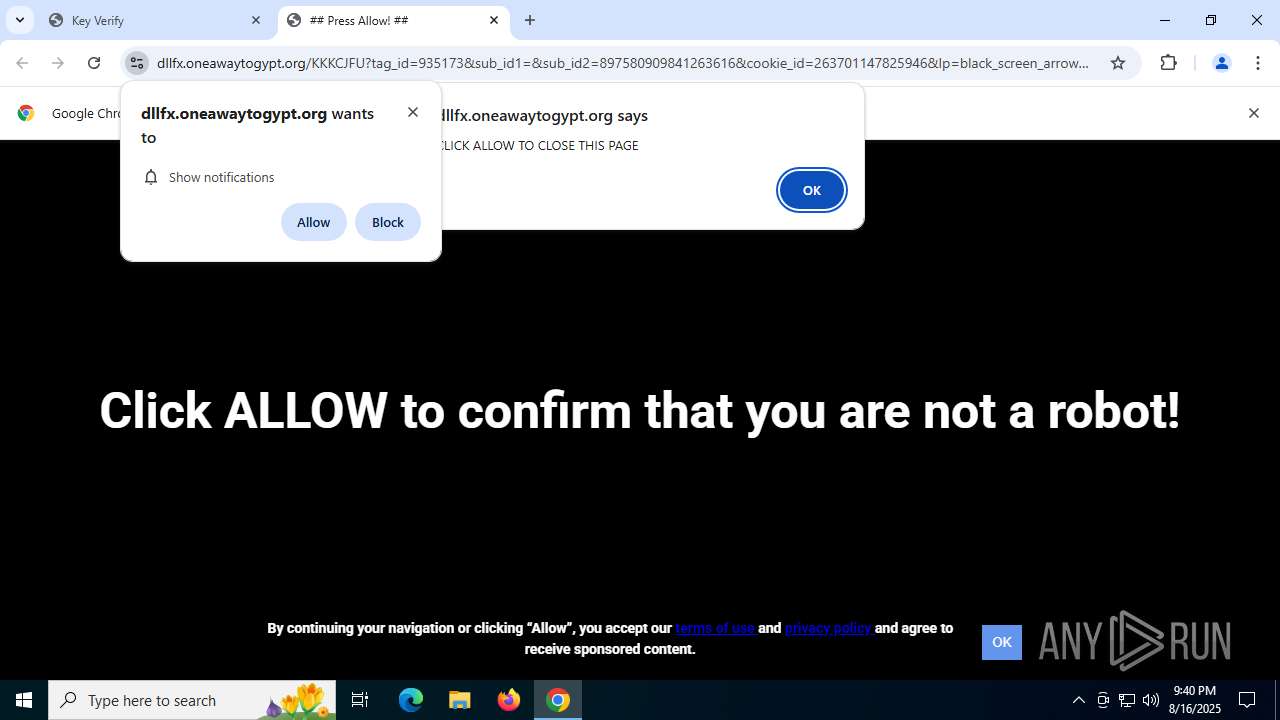
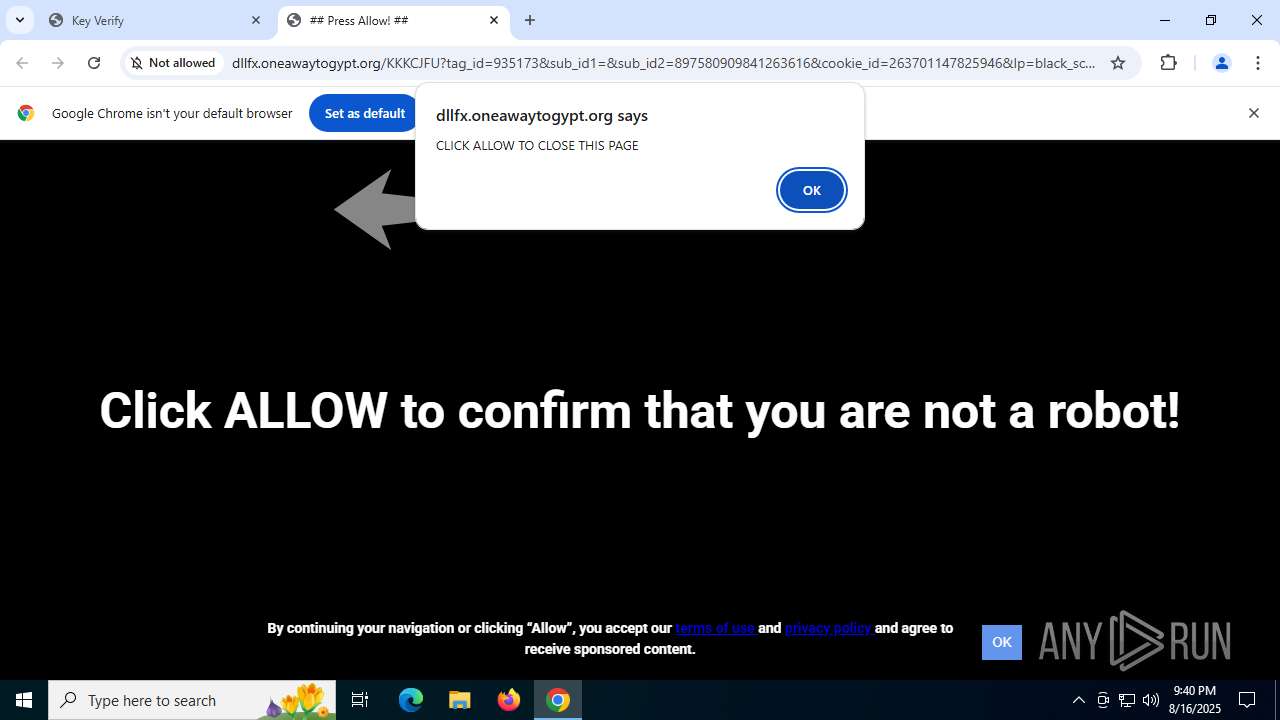
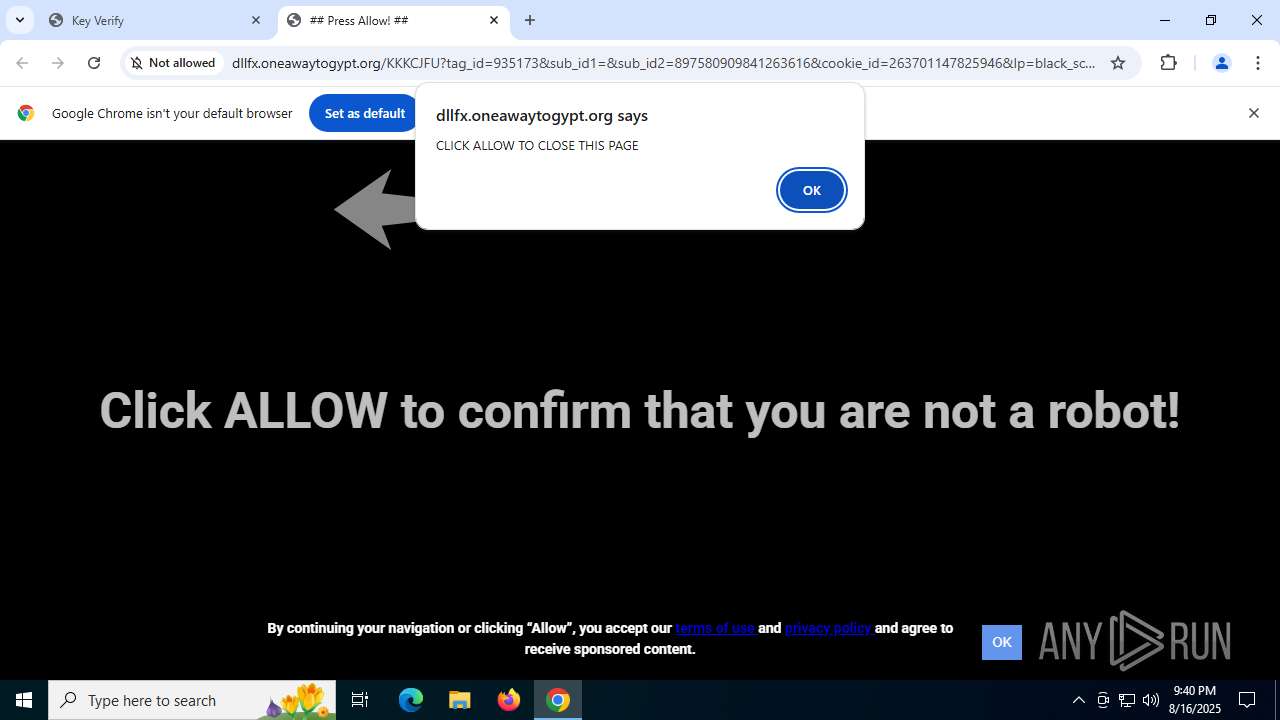
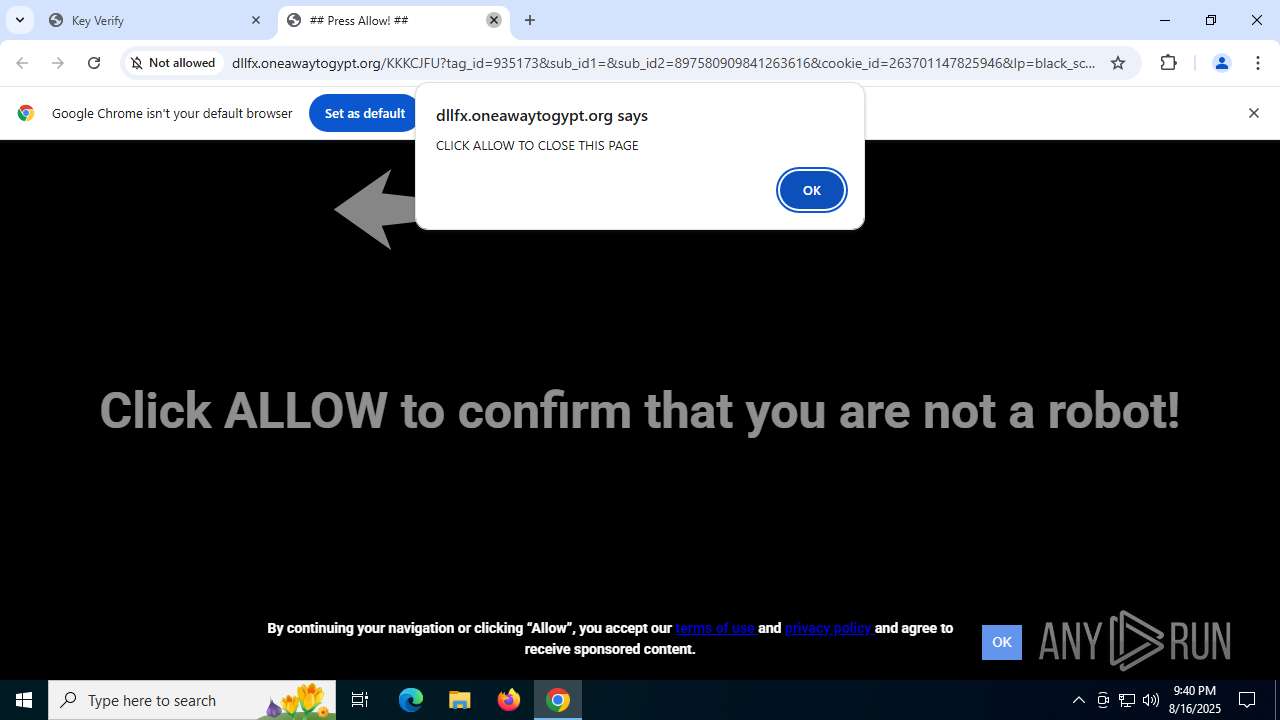
1568 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (tonordersitye .com) |
1568 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (tonordersitye .com) |
1568 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (tonordersitye .com) |
1568 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1568 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1568 | chrome.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain (tonordersitye .com) |
1568 | chrome.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Possible Domain Associated with Malware Distribution (ukankingwithea .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1568 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
1568 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
Process | Message |
|---|---|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-0FQEP.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-0FQEP.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-0FQEP.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-0FQEP.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in EXE directory
|
saBSI.exe | NotComDllGetInterface: C:\Users\admin\AppData\Local\Temp\is-0FQEP.tmp\prod0_extract\saBSI.exe loading C:\Users\admin\AppData\Local\Temp\is-0FQEP.tmp\prod0_extract\mfeaaca.dll, WinVerifyTrust failed with 80092003
|
saBSI.exe | NCPrivateLoadAndValidateMPTDll: Looking in current directory
|