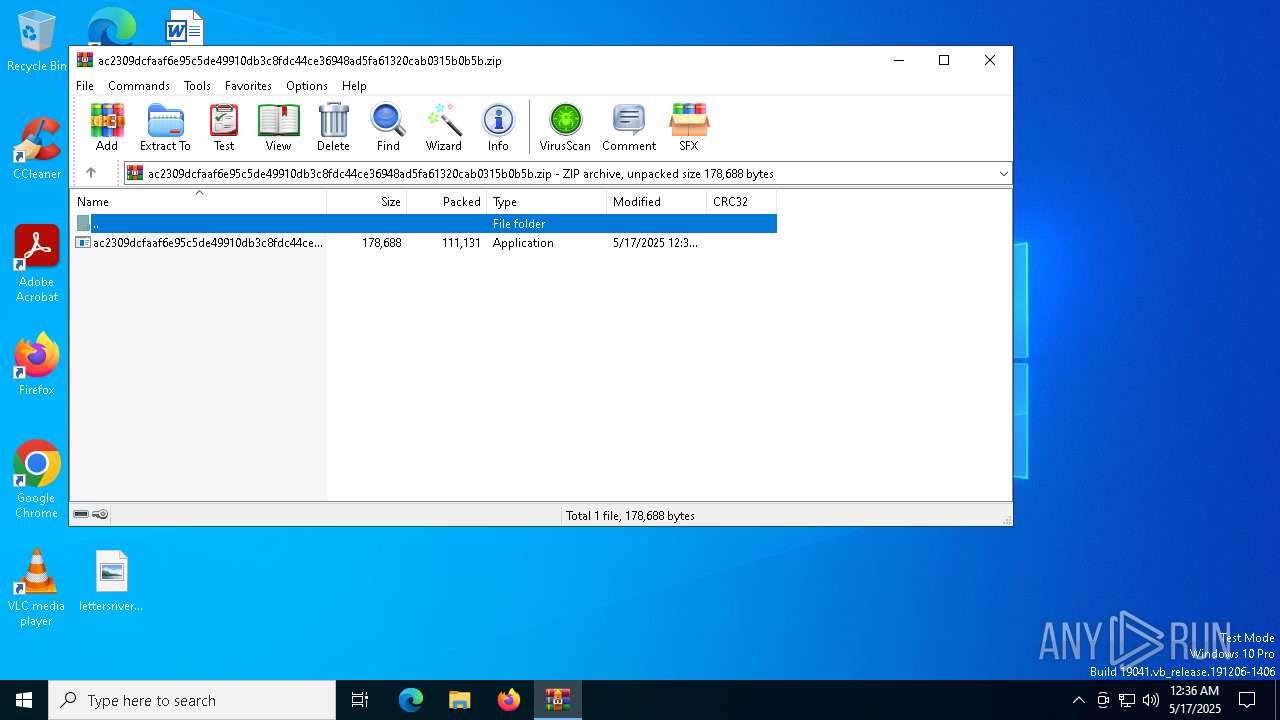
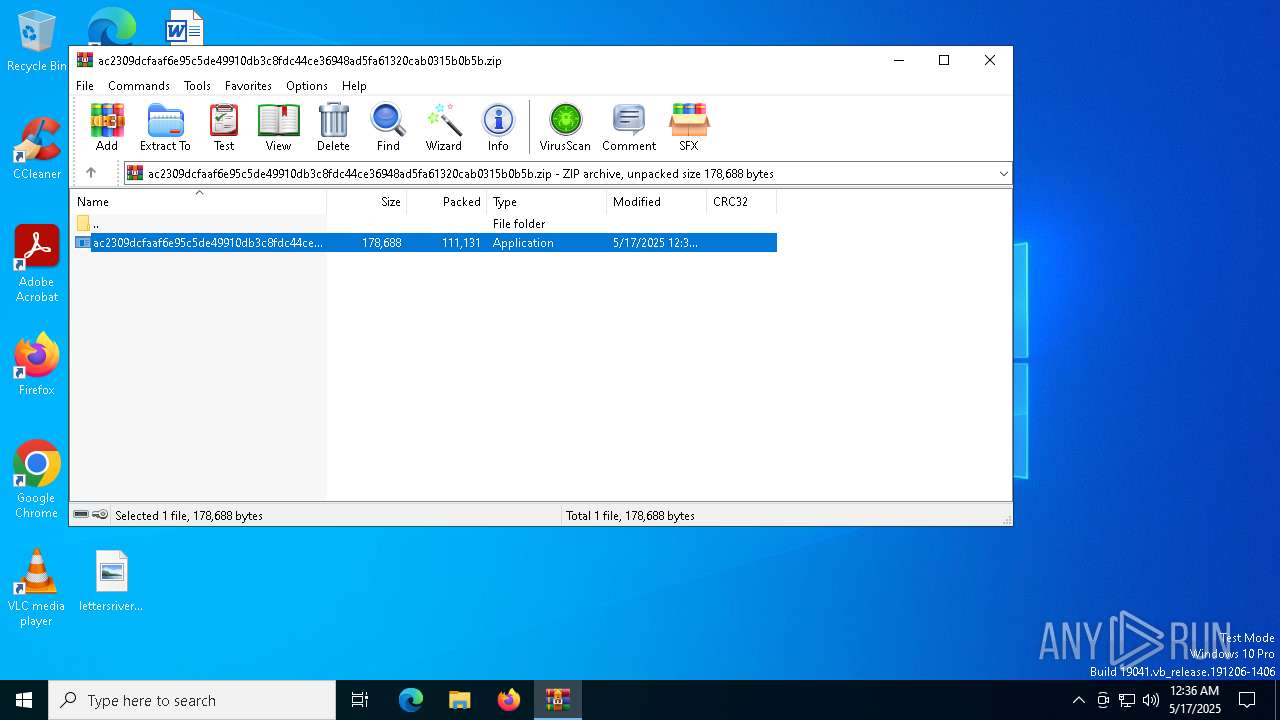
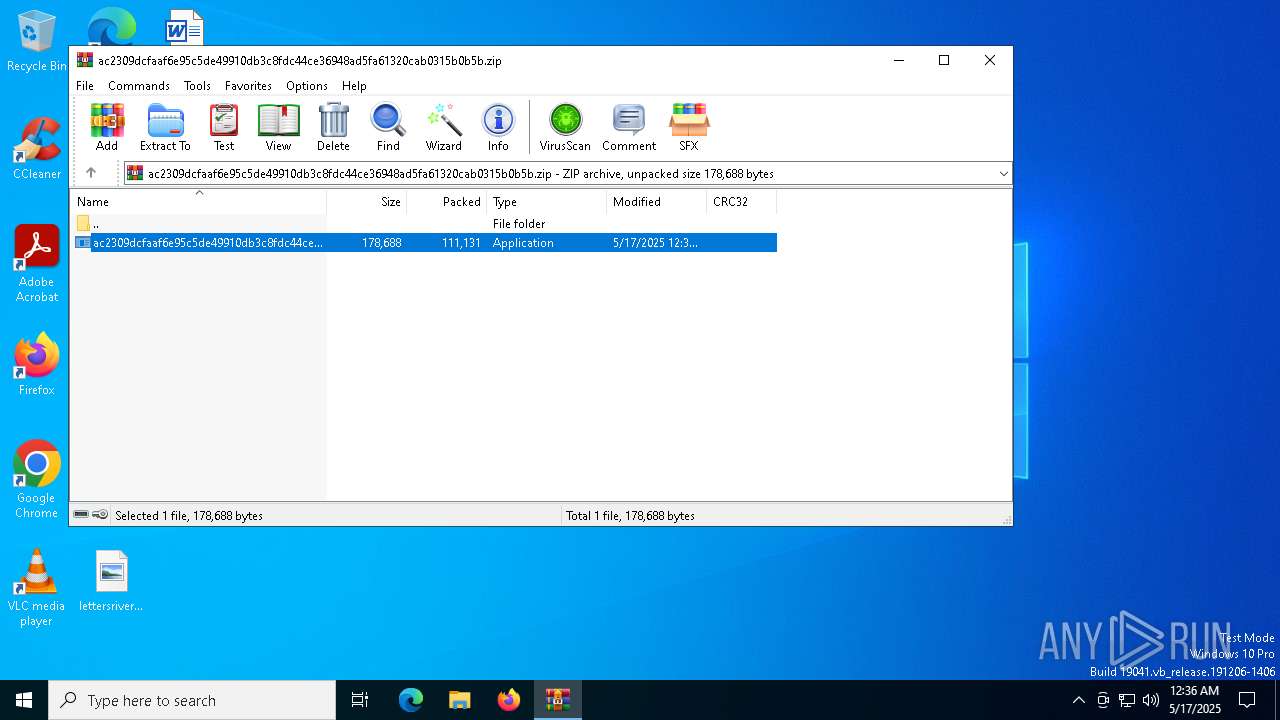
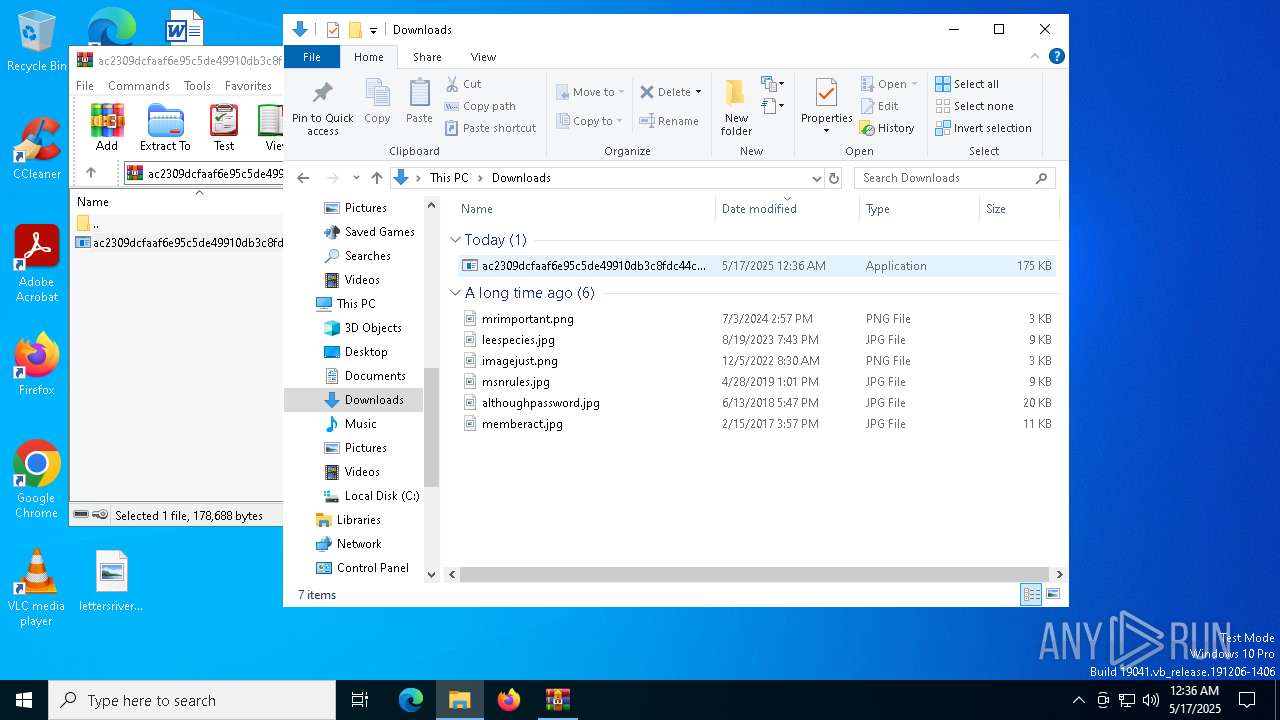
| File name: | ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.zip |
| Full analysis: | https://app.any.run/tasks/41e4c223-77fd-43cf-a26f-2c7b95b20803 |
| Verdict: | Malicious activity |
| Threats: | A botnet is a group of internet-connected devices that are controlled by a single individual or group, often without the knowledge or consent of the device owners. These devices can be used to launch a variety of malicious attacks, such as distributed denial-of-service (DDoS) attacks, spam campaigns, and data theft. Botnet malware is the software that is used to infect devices and turn them into part of a botnet. |
| Analysis date: | May 17, 2025, 00:36:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
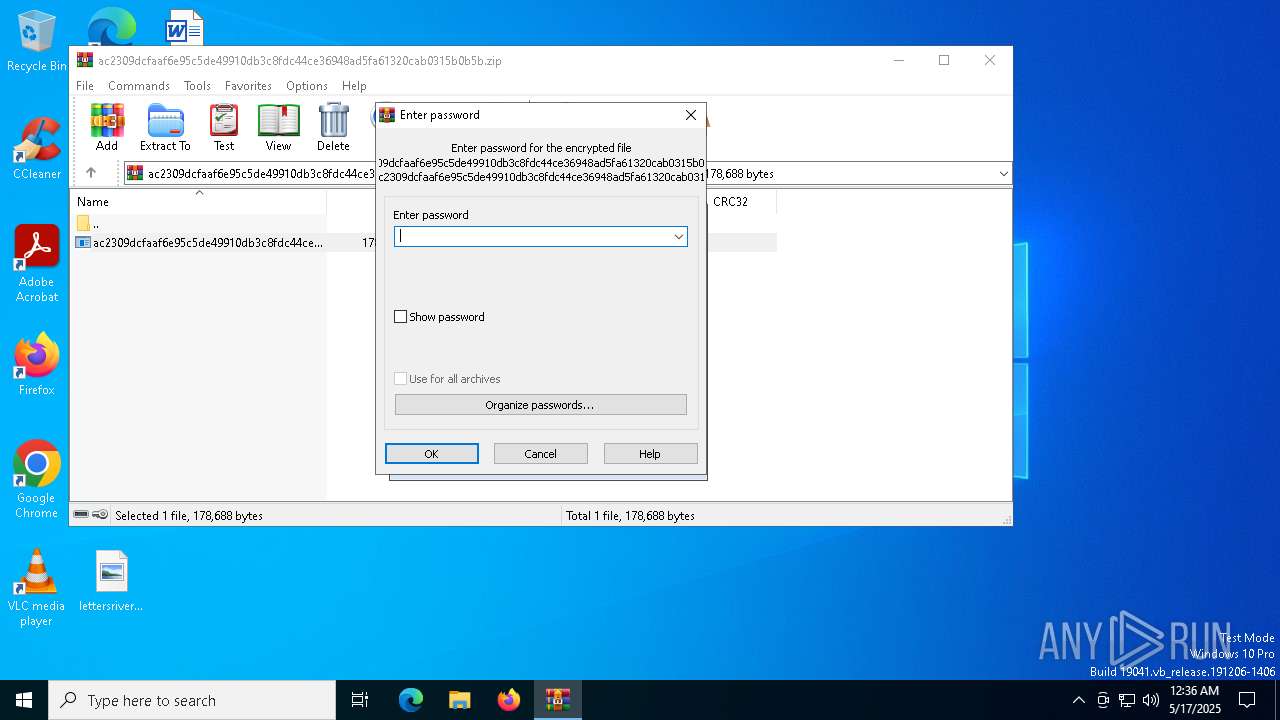
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | A5056475035FCD09F0015335D684CA44 |
| SHA1: | 093458B30A1B1A4990104F5B6E1FF35891CA480F |
| SHA256: | 866E7087D18DF1E5C48182EF648550E043891047E902558949BA6489C74C072B |
| SSDEEP: | 1536:lV5dITt+oMRAzblvMiYDKIe74LiN39vDLAWVx9gKR+UcRhNHQ5v09PQoTXpHNL4D:z8+LKzd74+jAo9gKJ8XwZ0997Nt4AjG |
MALICIOUS
BOTNET has been found (auto)
- WinRAR.exe (PID: 1672)
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
Generic archive extractor
- WinRAR.exe (PID: 1672)
EMOTET mutex has been found
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
- generickeydef.exe (PID: 1096)
Emotet process is detected
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
SUSPICIOUS
Application launched itself
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 4692)
- generickeydef.exe (PID: 2240)
Reads security settings of Internet Explorer
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
- generickeydef.exe (PID: 1096)
Executable content was dropped or overwritten
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
Starts itself from another location
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
Connects to the server without a host name
- generickeydef.exe (PID: 1096)
Connects to unusual port
- generickeydef.exe (PID: 1096)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1672)
Checks supported languages
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 4692)
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
- generickeydef.exe (PID: 2240)
- generickeydef.exe (PID: 1096)
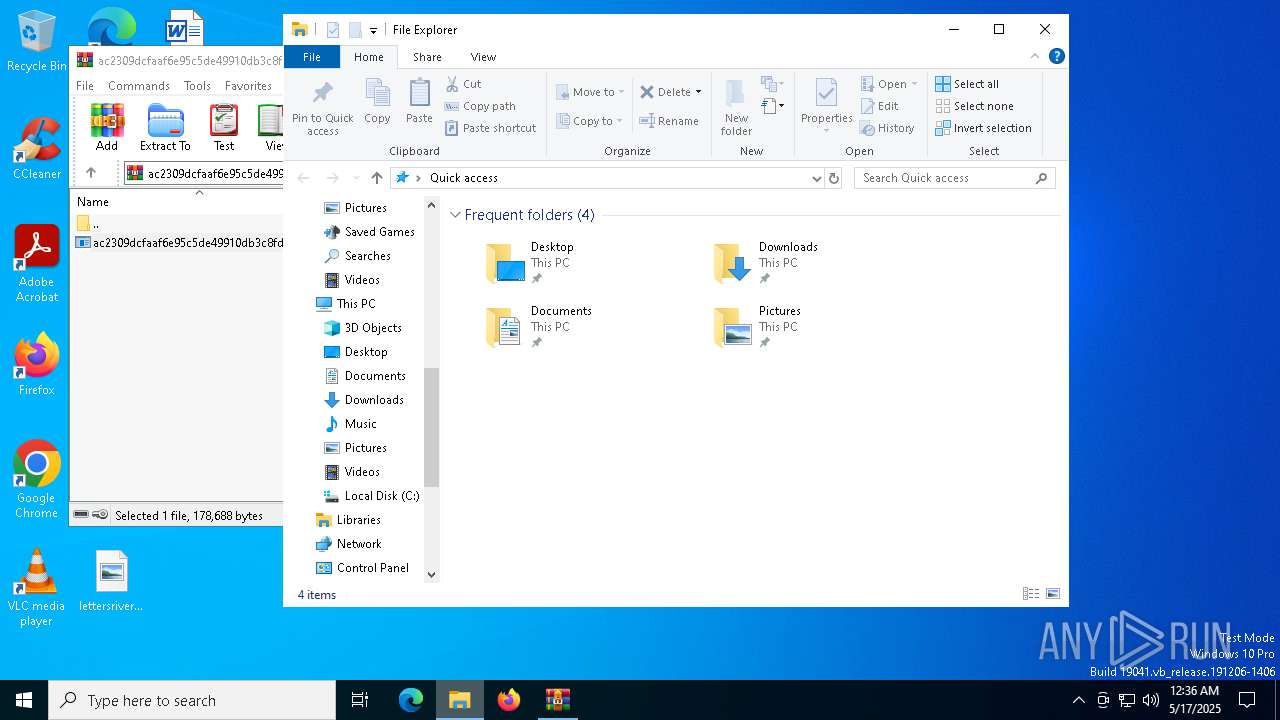
Manual execution by a user
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 4692)
Reads the computer name
- ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe (PID: 6048)
- generickeydef.exe (PID: 1096)
Checks proxy server information
- generickeydef.exe (PID: 1096)
- slui.exe (PID: 1240)
Reads the software policy settings
- slui.exe (PID: 5776)
- slui.exe (PID: 1240)
Reads the machine GUID from the registry
- generickeydef.exe (PID: 1096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
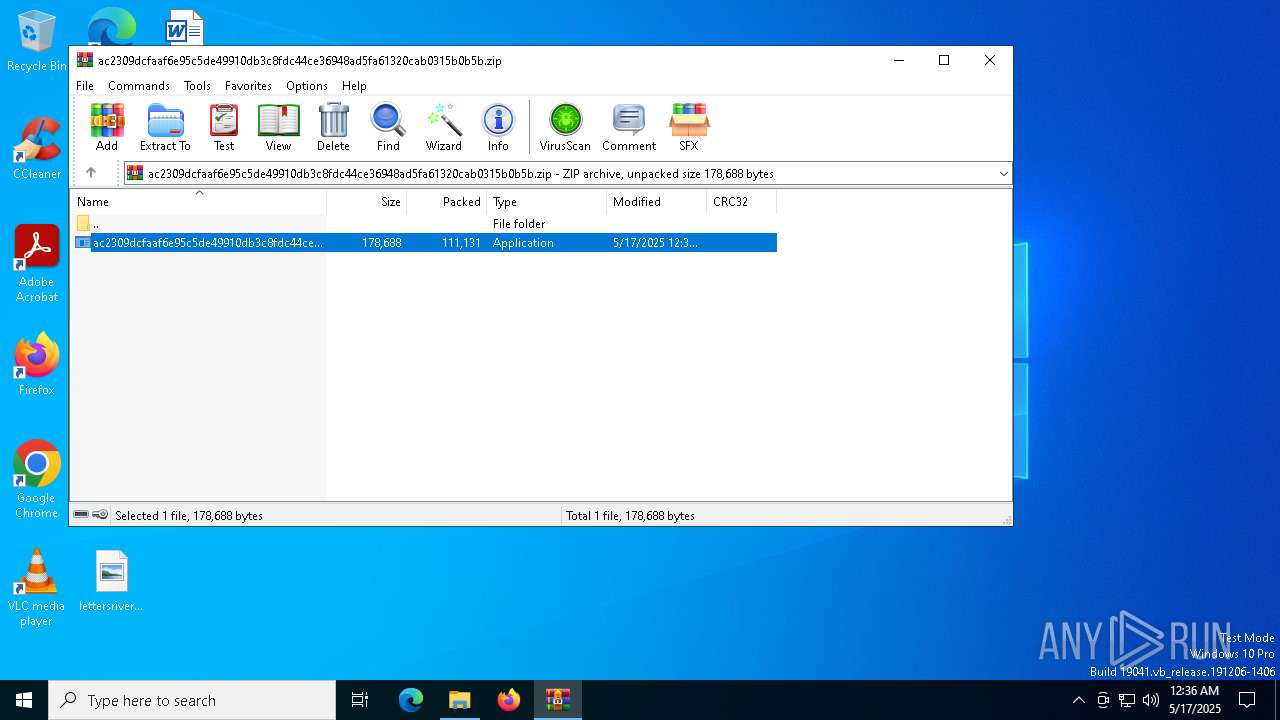
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:17 00:36:00 |
| ZipCRC: | 0x0fcbc595 |
| ZipCompressedSize: | 111131 |
| ZipUncompressedSize: | 178688 |
| ZipFileName: | ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe |
Total processes
138
Monitored processes
9
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1056 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | --d82545ba | C:\Users\admin\AppData\Local\generickeydef\generickeydef.exe | generickeydef.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 1240 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1348 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
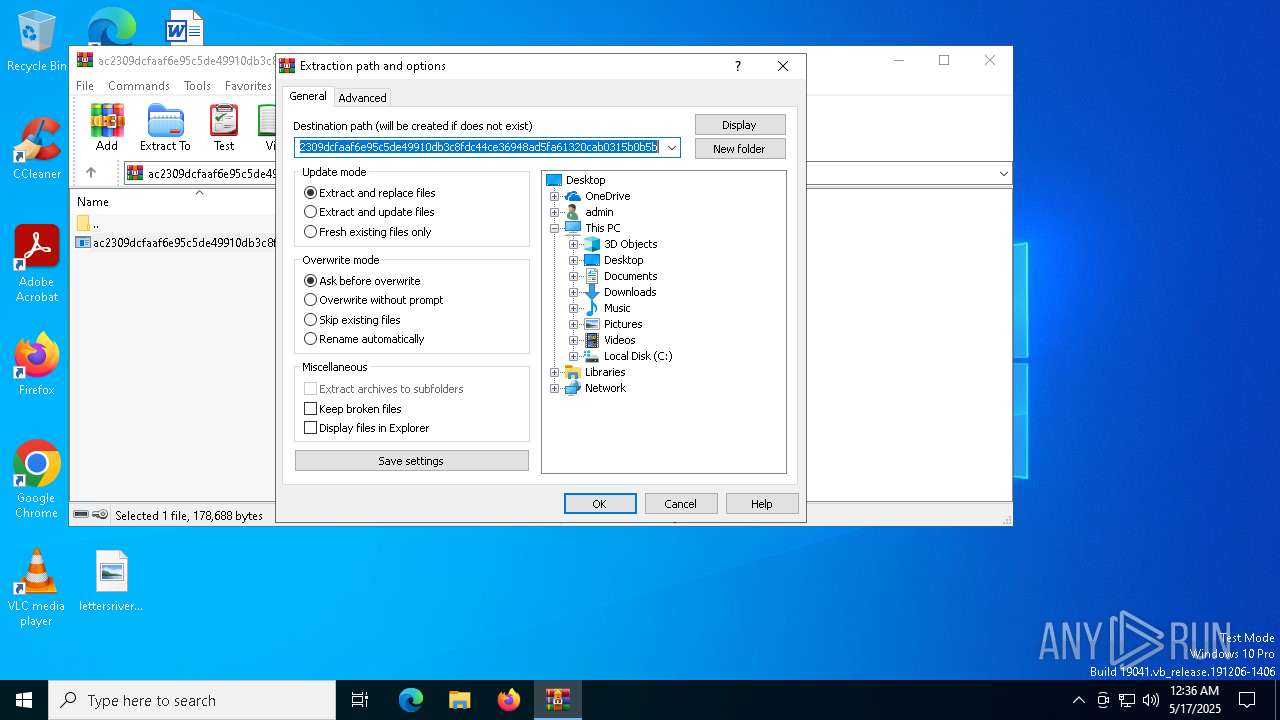
| 1672 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\generickeydef\generickeydef.exe" | C:\Users\admin\AppData\Local\generickeydef\generickeydef.exe | — | ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
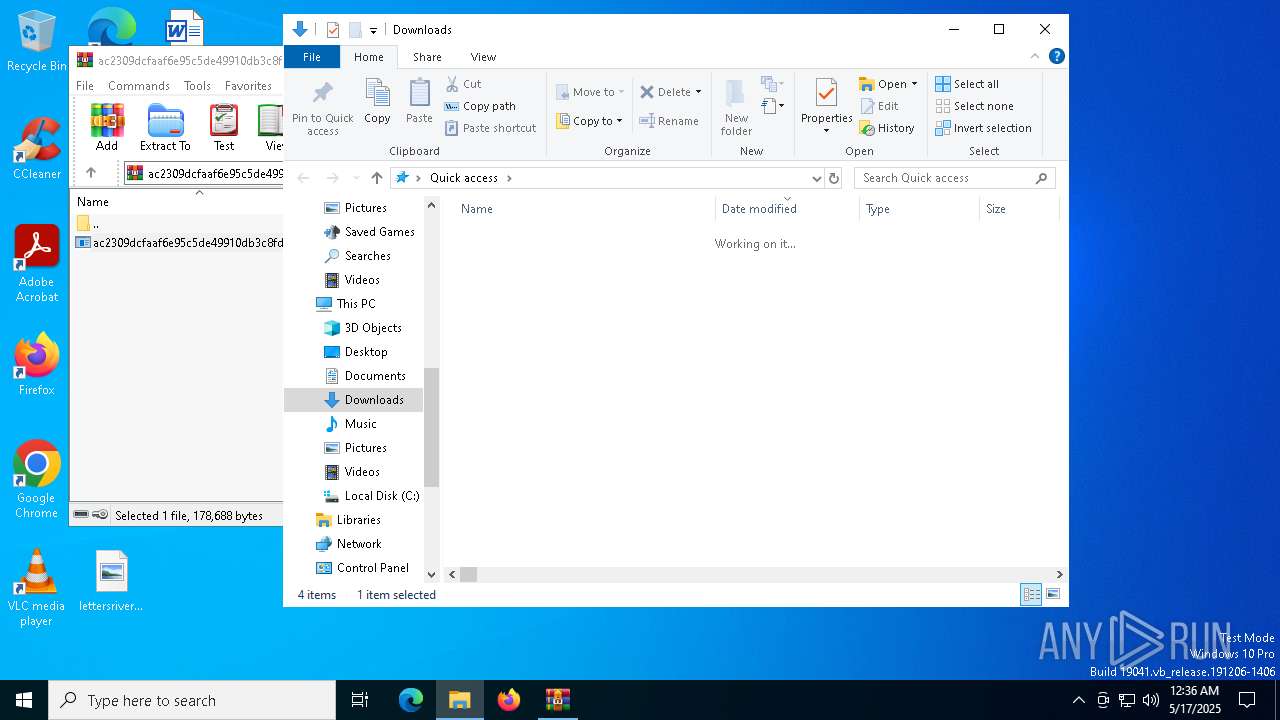
| 4692 | "C:\Users\admin\Downloads\ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe" | C:\Users\admin\Downloads\ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5776 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6048 | --a4fb832d | C:\Users\admin\Downloads\ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe | ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
3 661
Read events
3 633
Write events
15
Delete events
13
Modification events
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.zip | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (1672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1672 | WinRAR.exe | C:\Users\admin\Downloads\ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe | executable | |
MD5:5597DC44AECD6B21CB115C3157B8B283 | SHA256:AC2309DCFAAF6E95C5DE49910DB3C8FDC44CE36948AD5FA61320CAB0315B0B5B | |||
| 6048 | ac2309dcfaaf6e95c5de49910db3c8fdc44ce36948ad5fa61320cab0315b0b5b.exe | C:\Users\admin\AppData\Local\generickeydef\generickeydef.exe | executable | |
MD5:5597DC44AECD6B21CB115C3157B8B283 | SHA256:AC2309DCFAAF6E95C5DE49910DB3C8FDC44CE36948AD5FA61320CAB0315B0B5B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6404 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6404 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1096 | generickeydef.exe | POST | 404 | 200.51.94.251:80 | http://200.51.94.251/publish/acquire/ringin/merge/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |