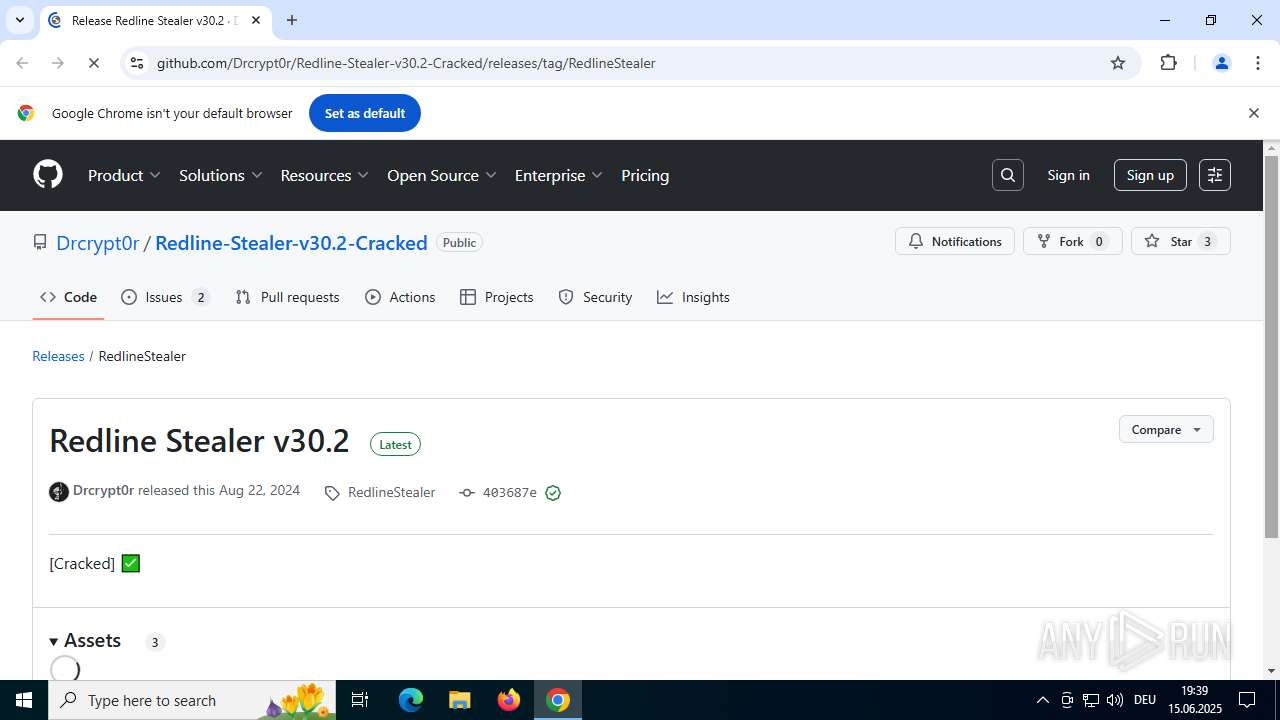
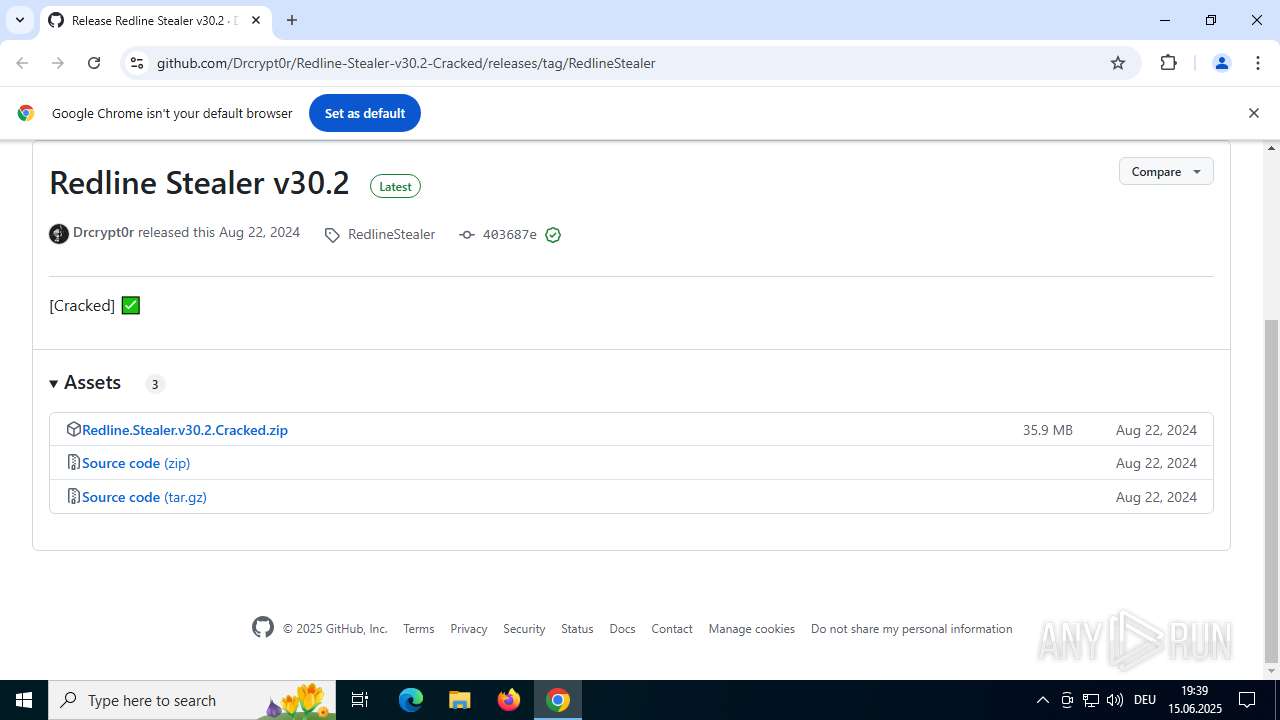
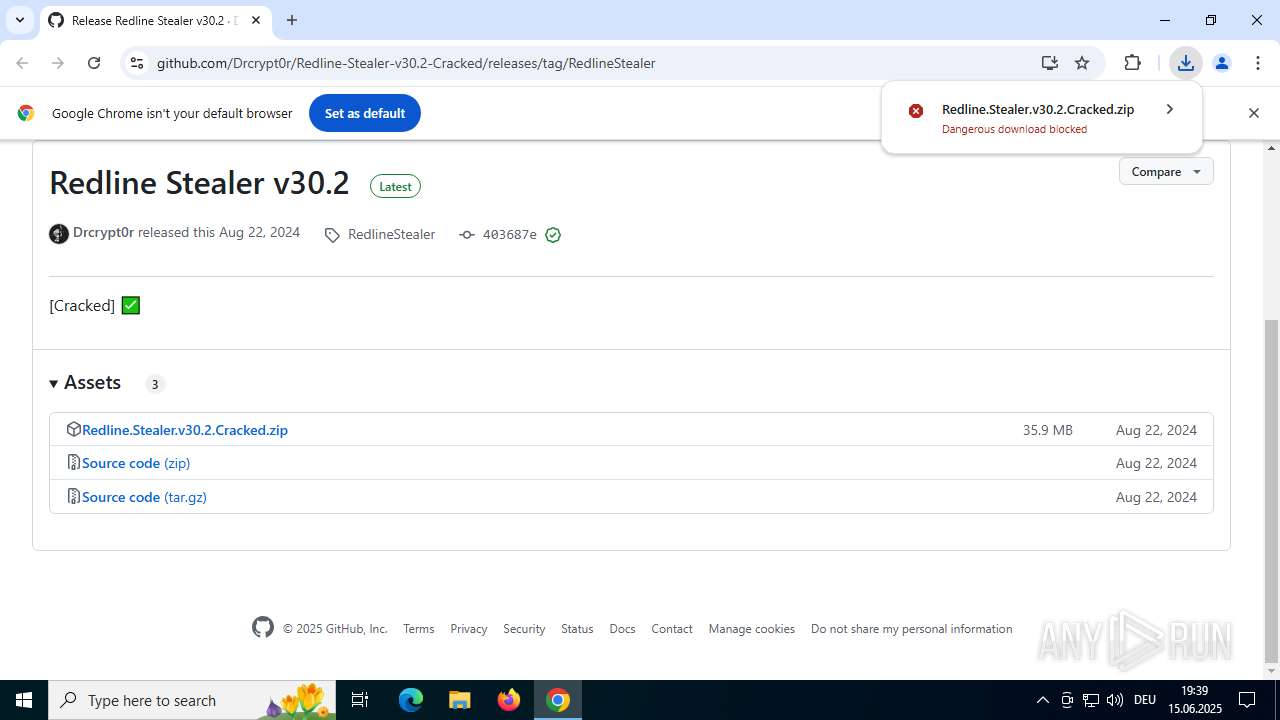
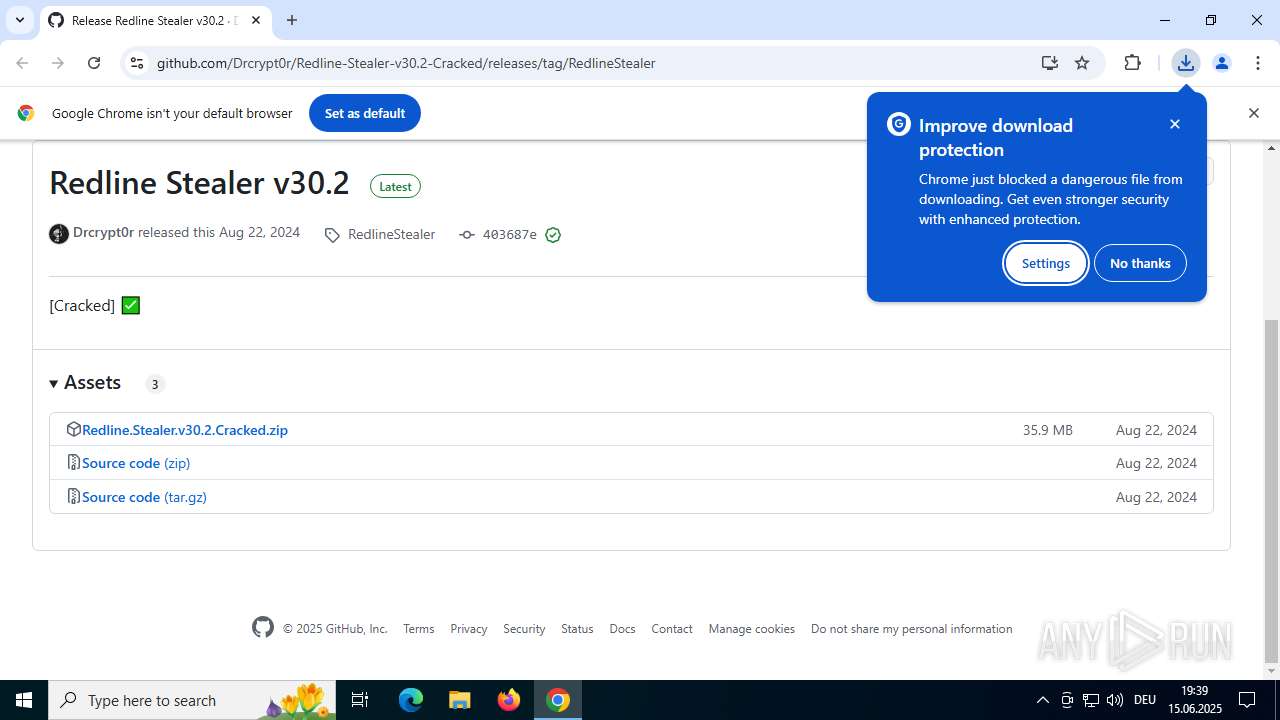
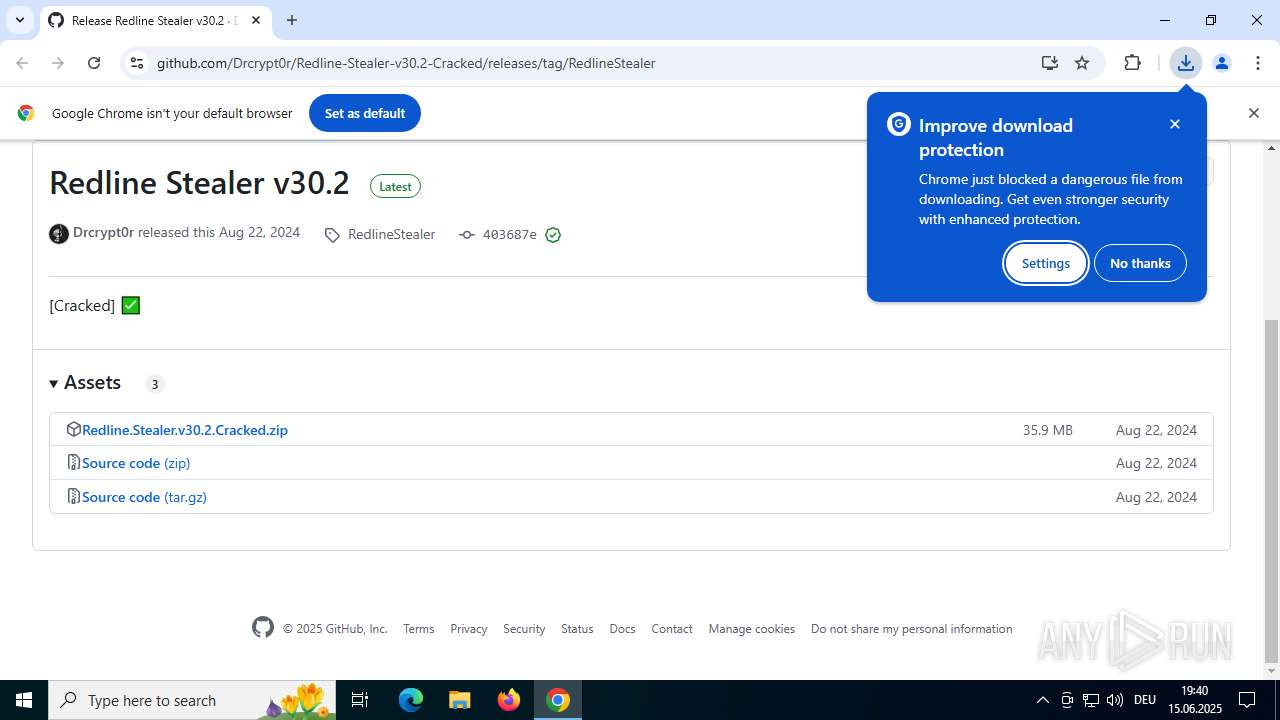
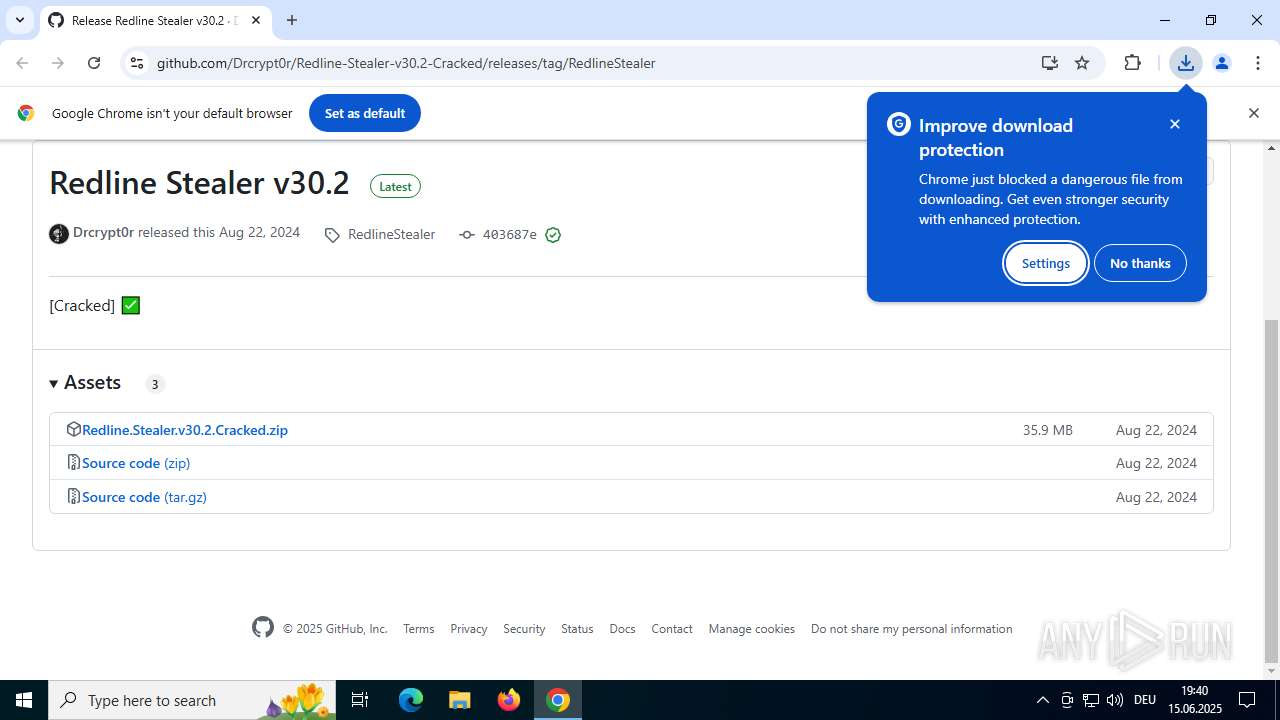
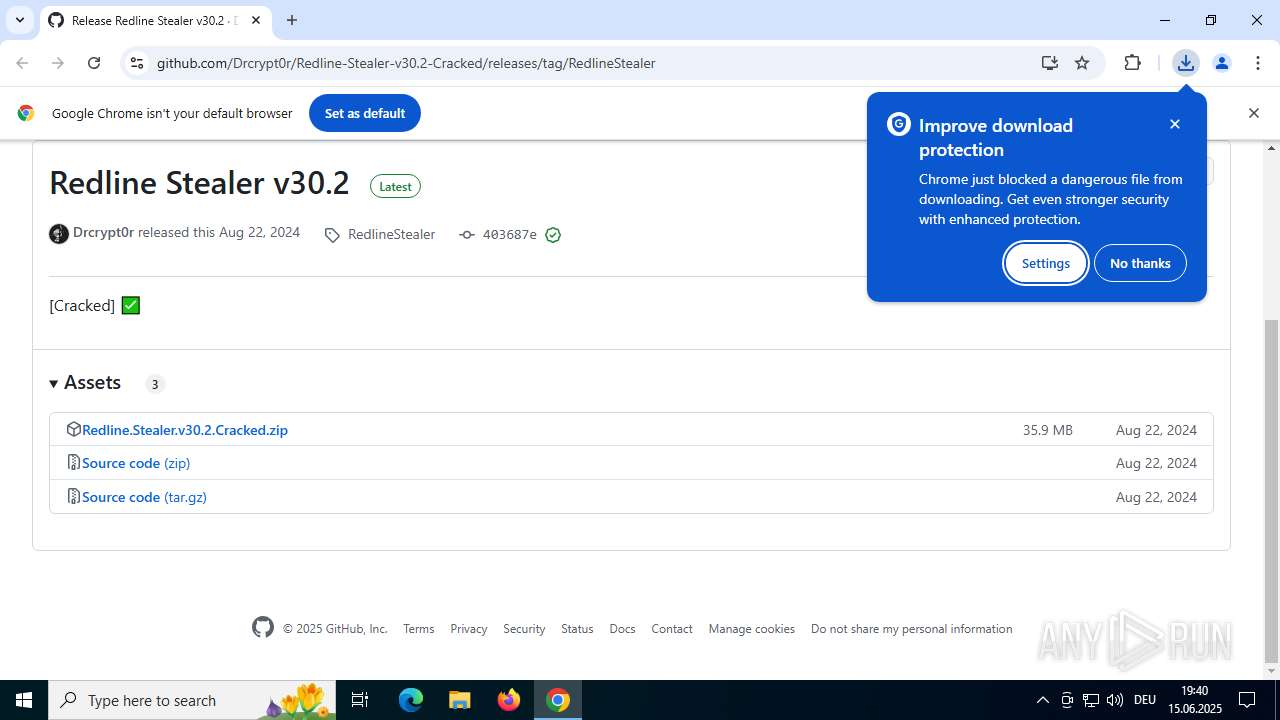
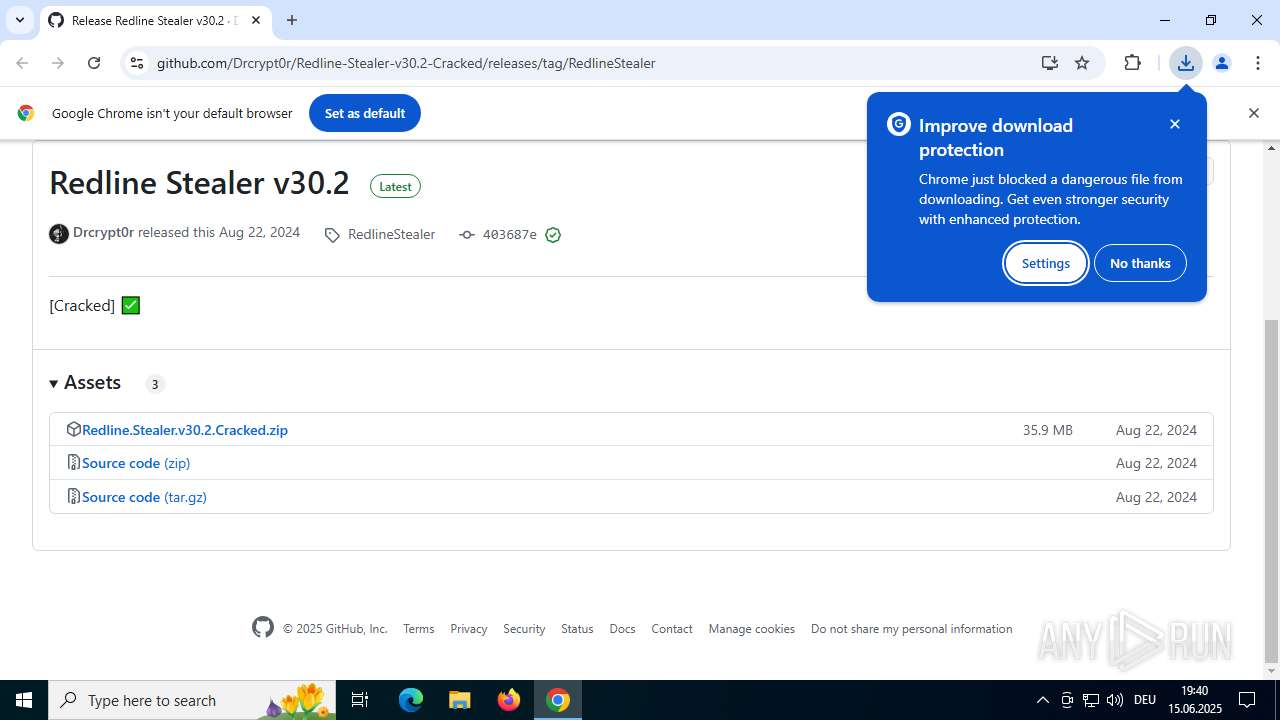
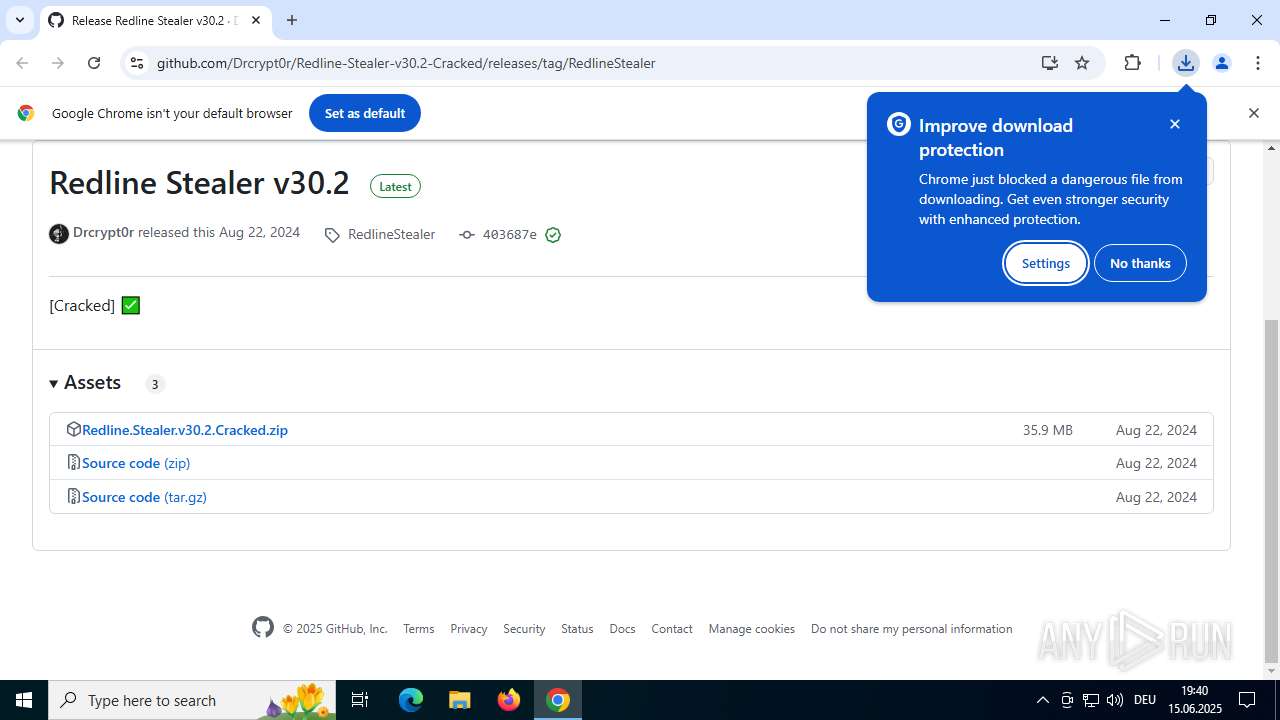
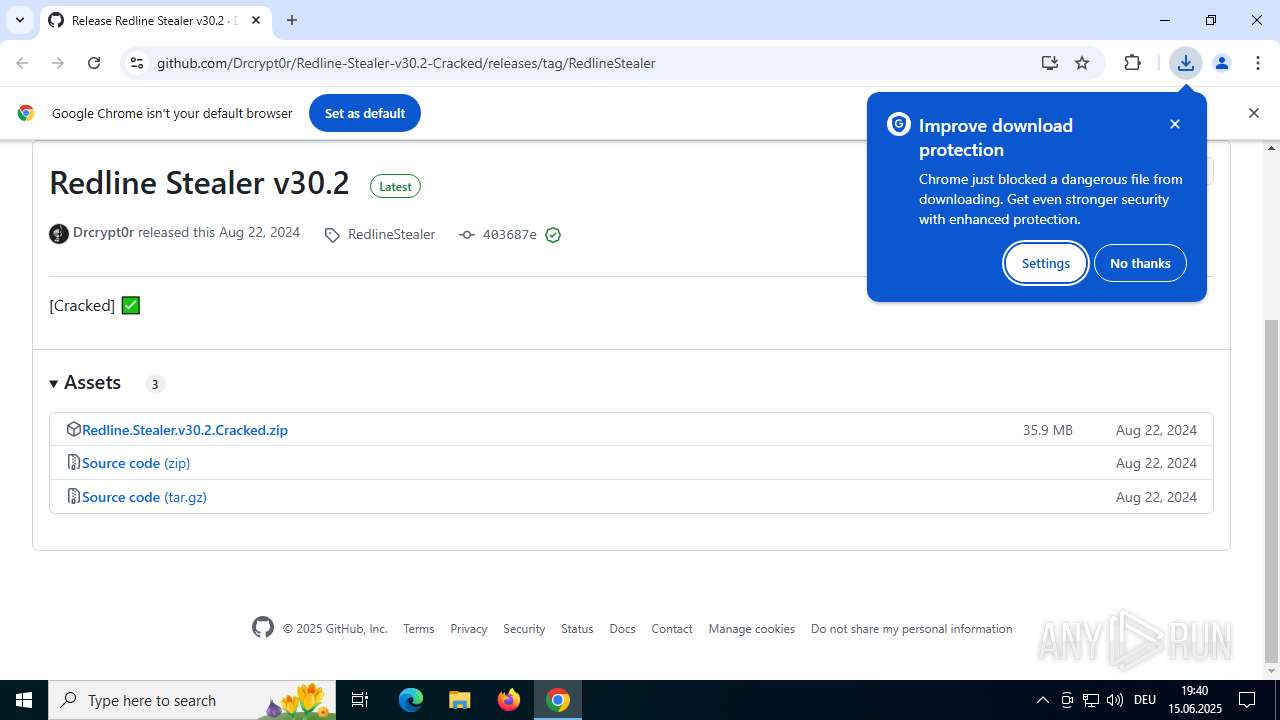
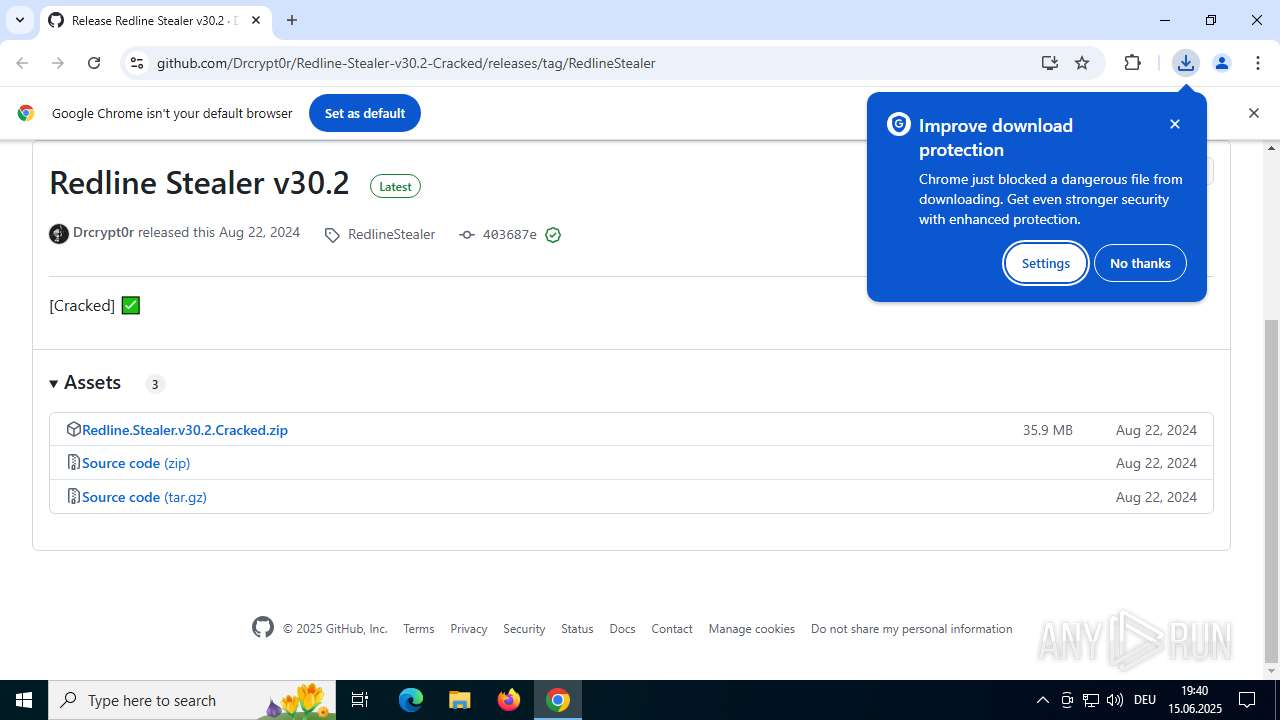
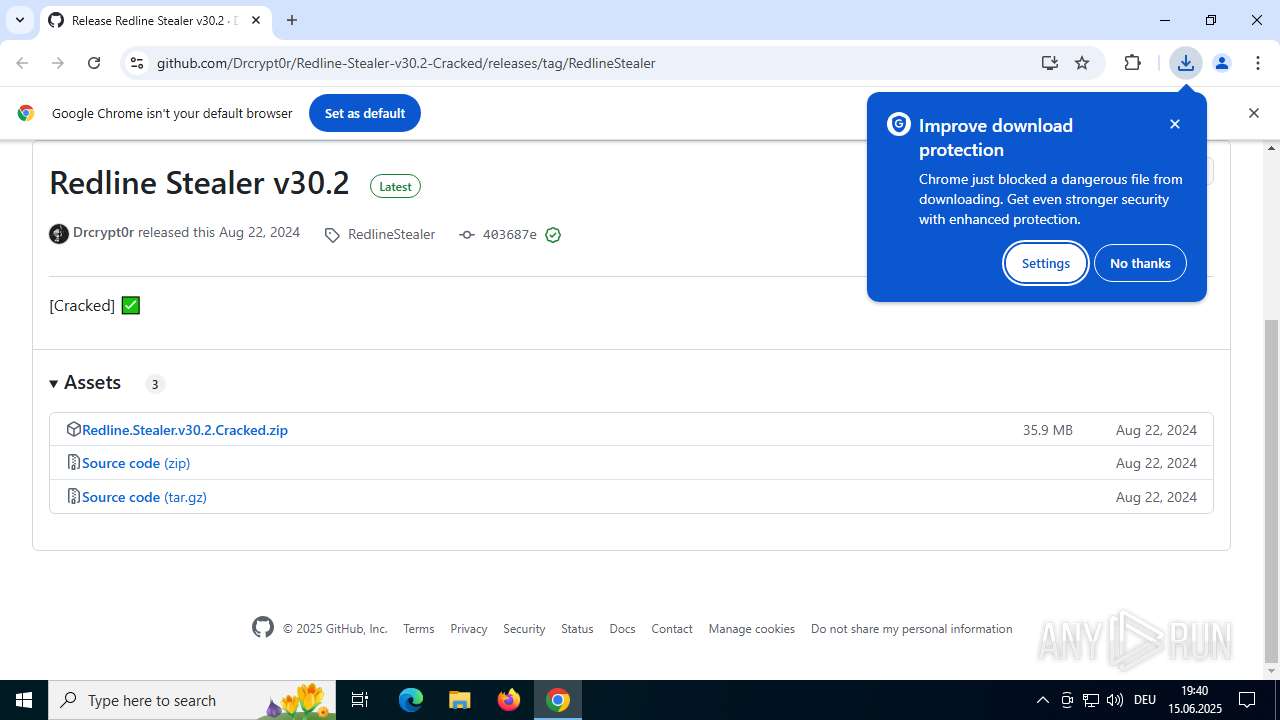
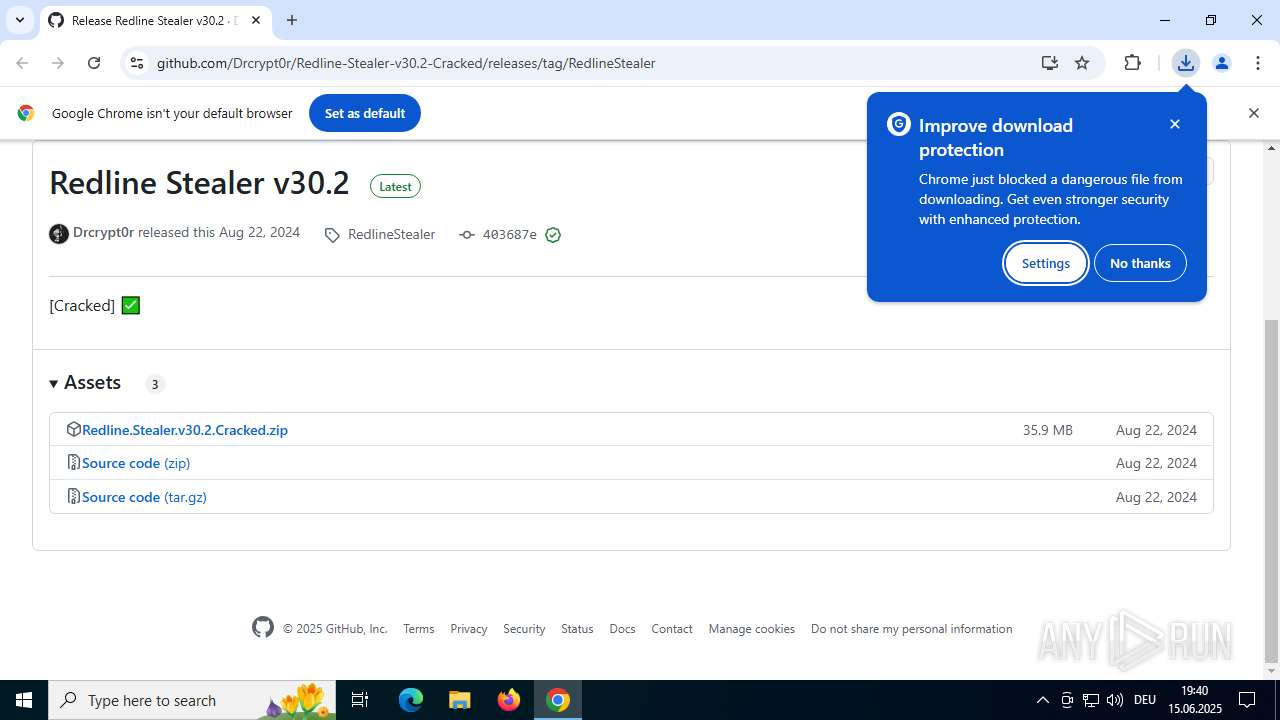
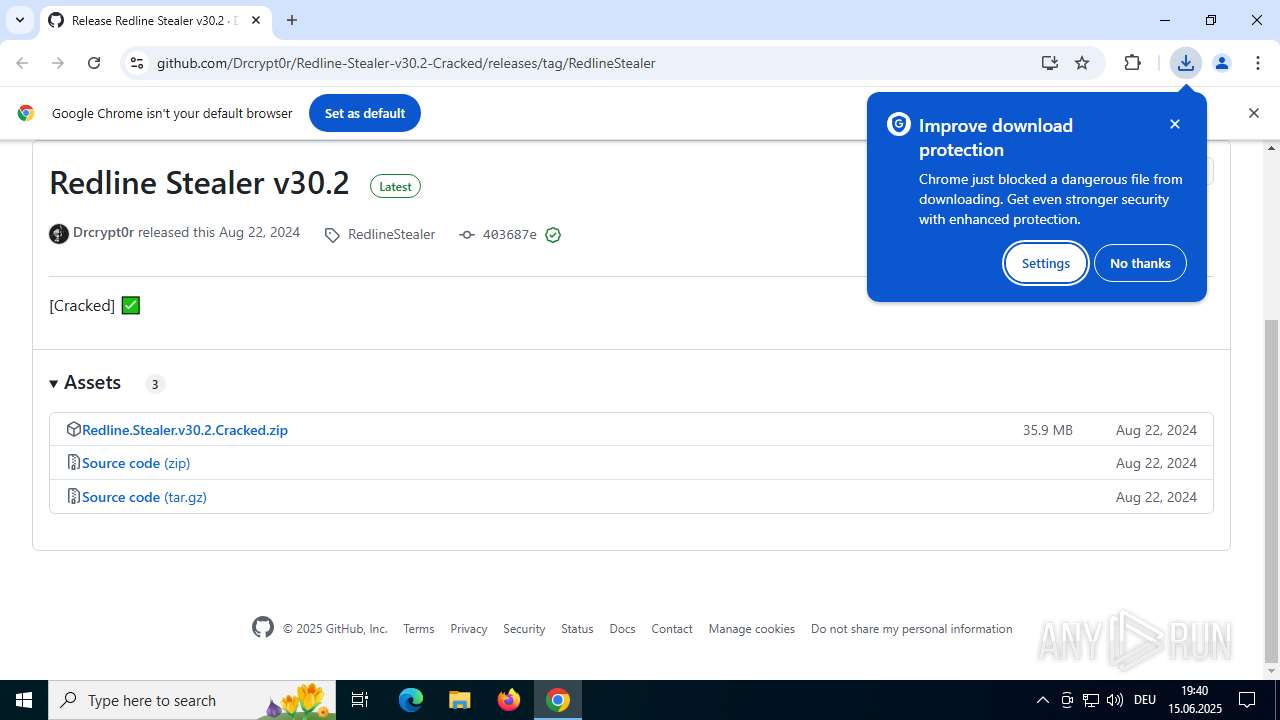
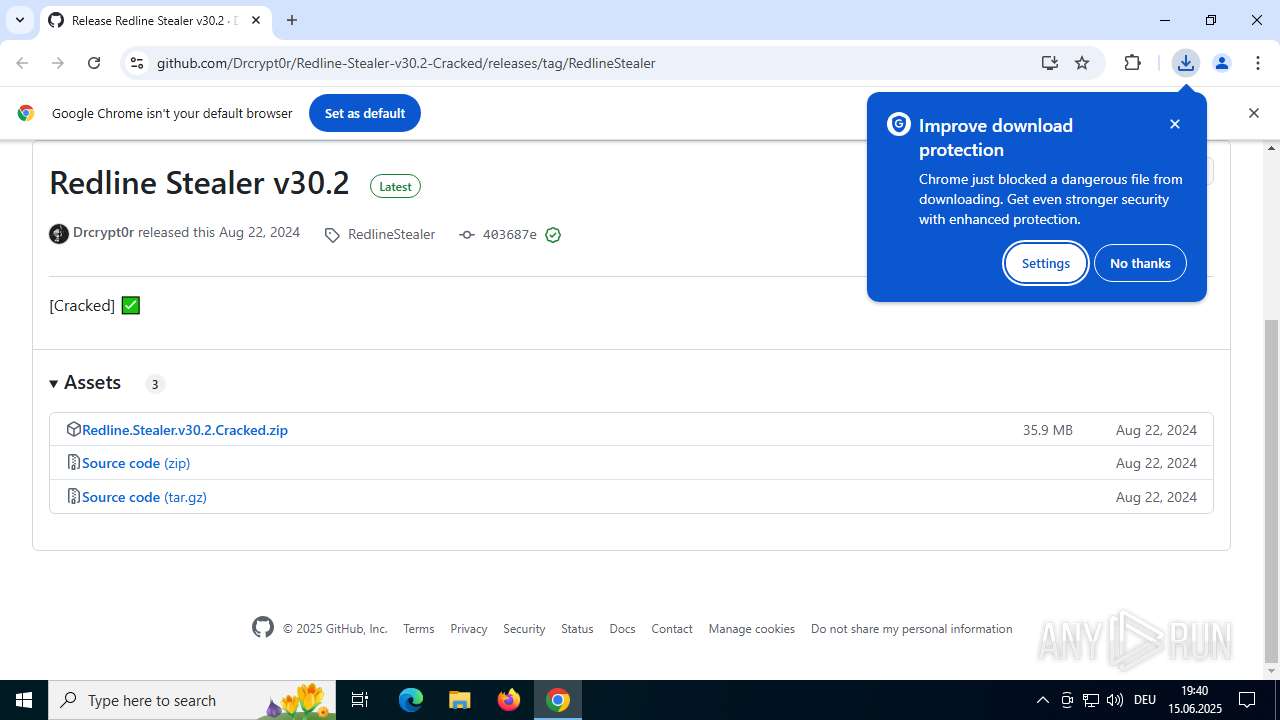
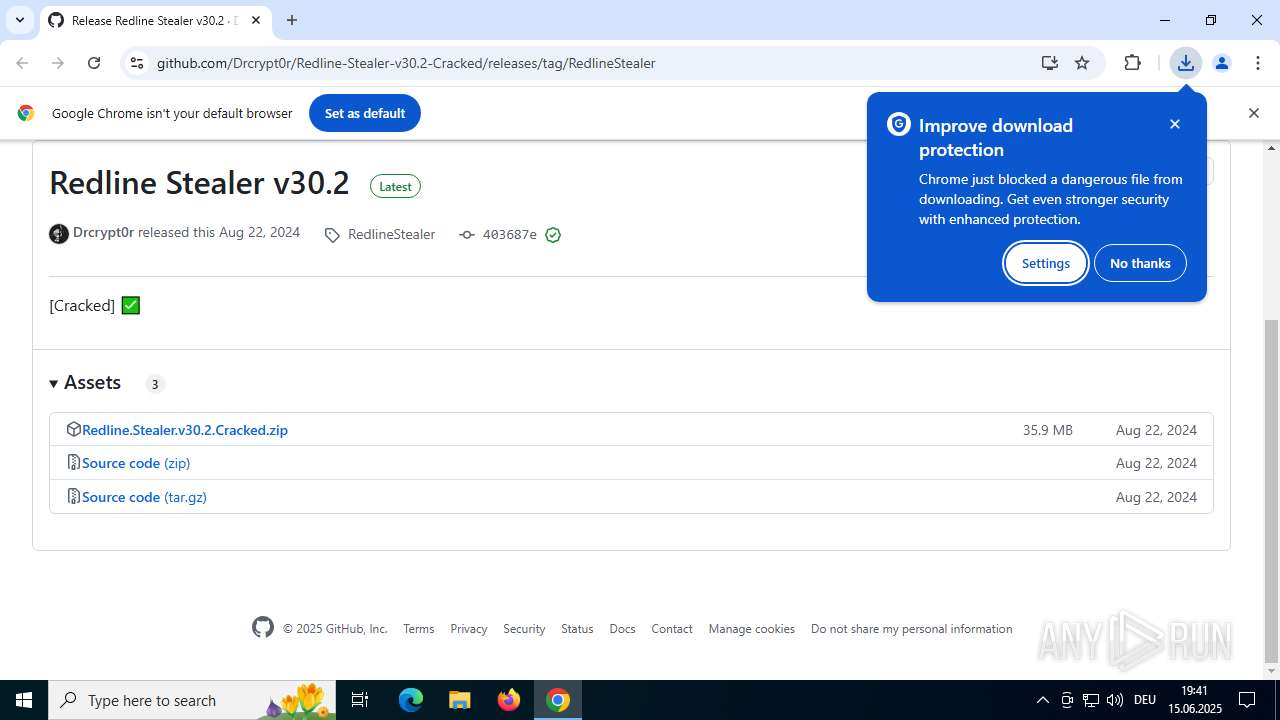
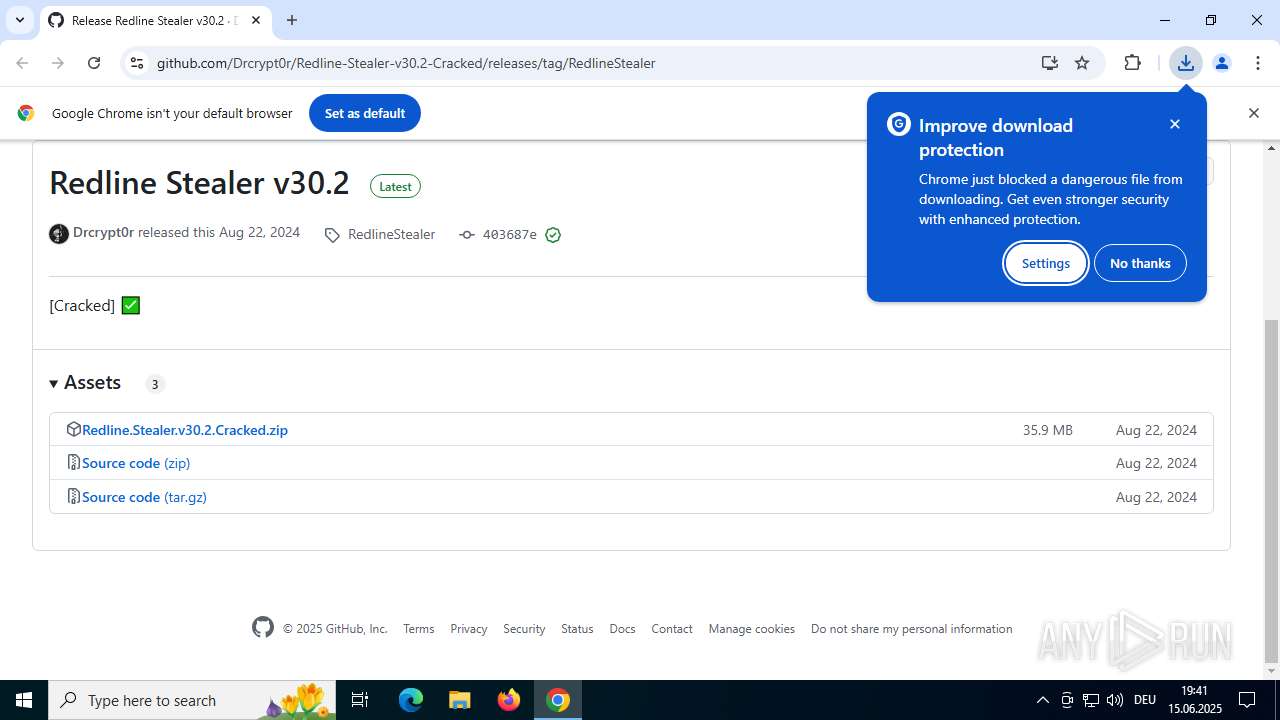
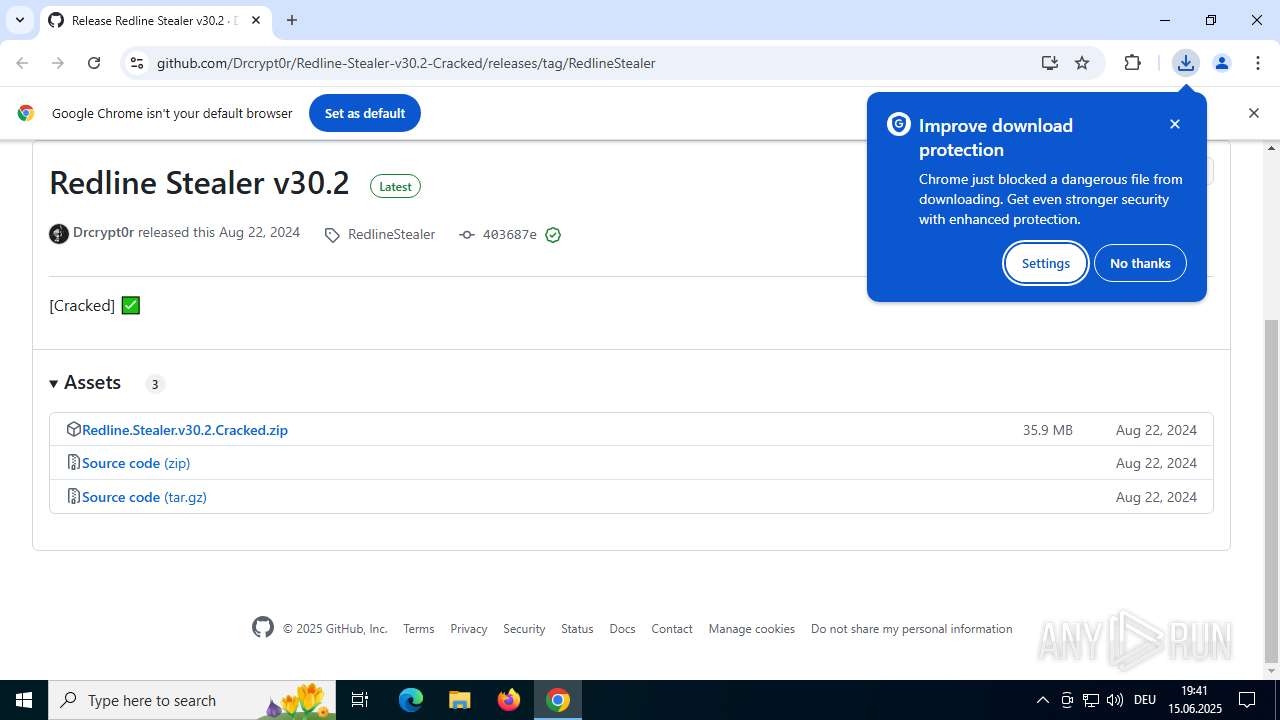
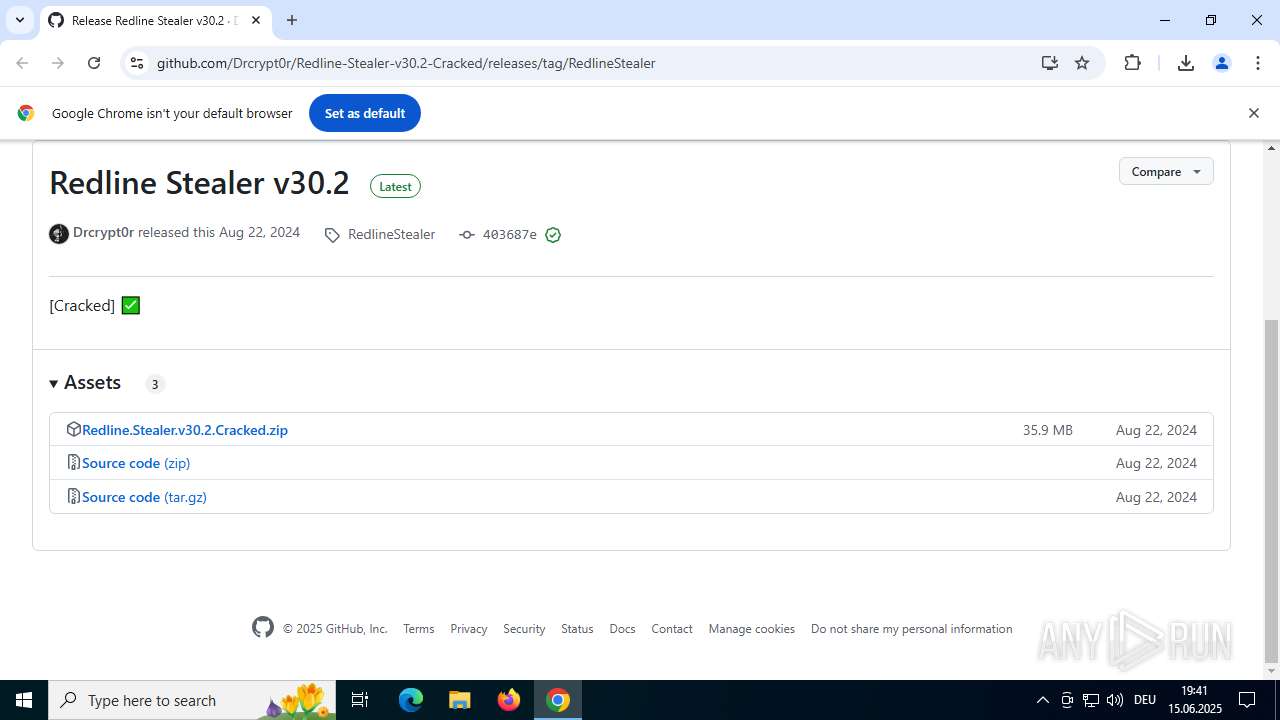
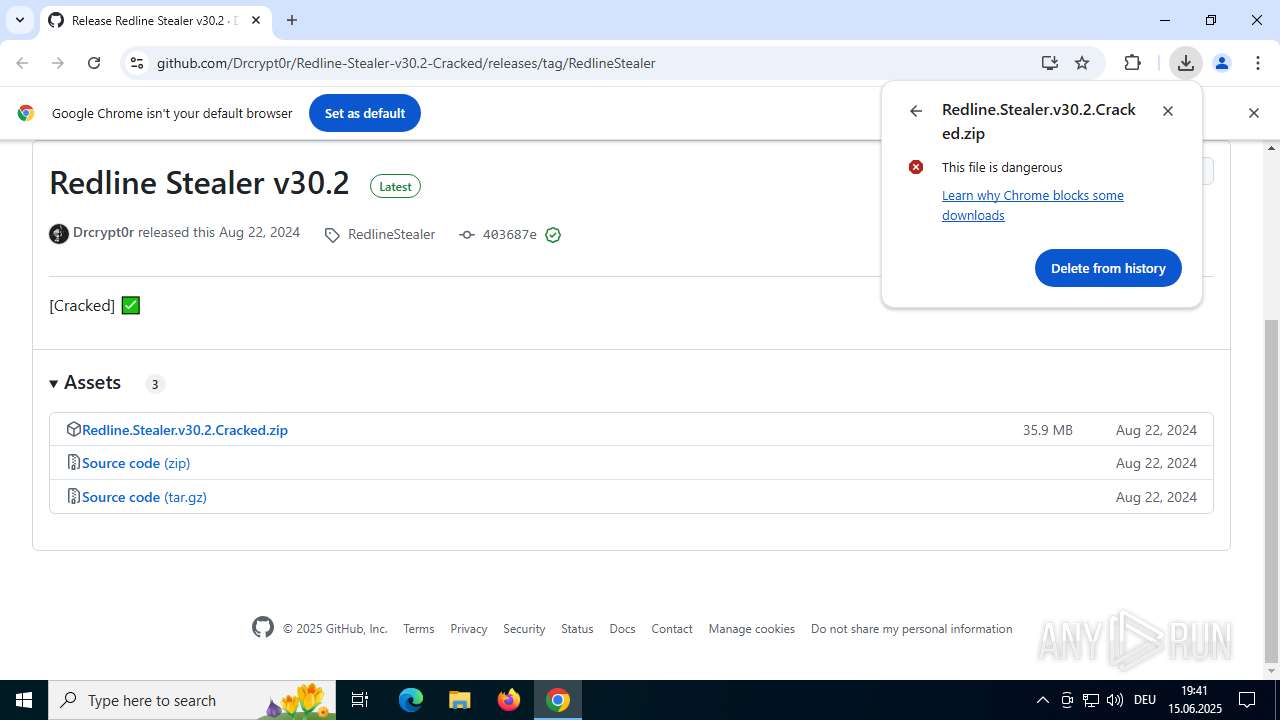
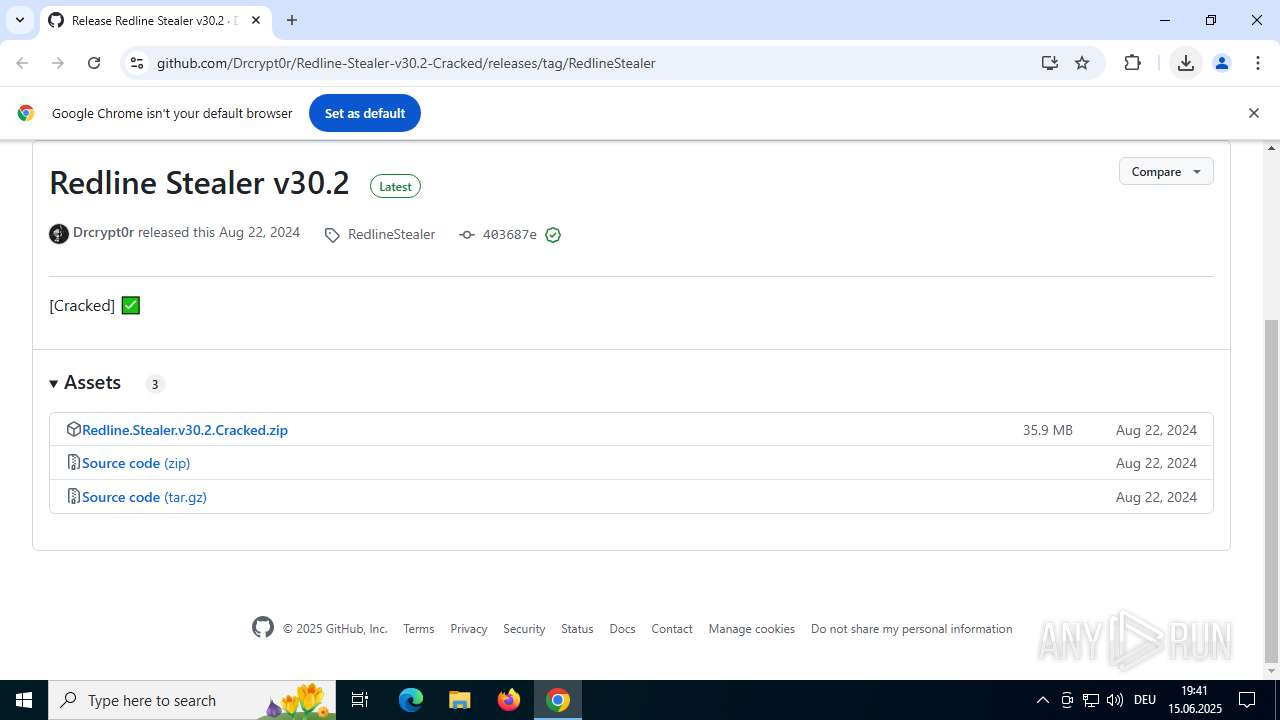
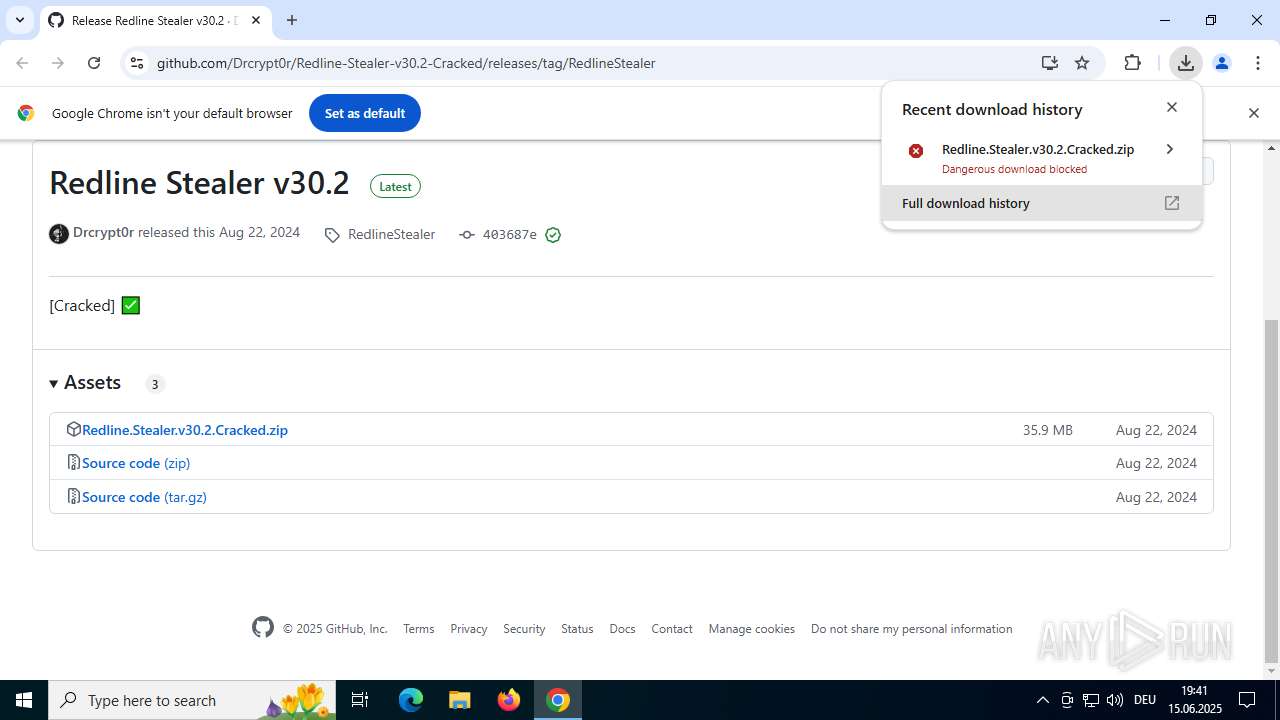
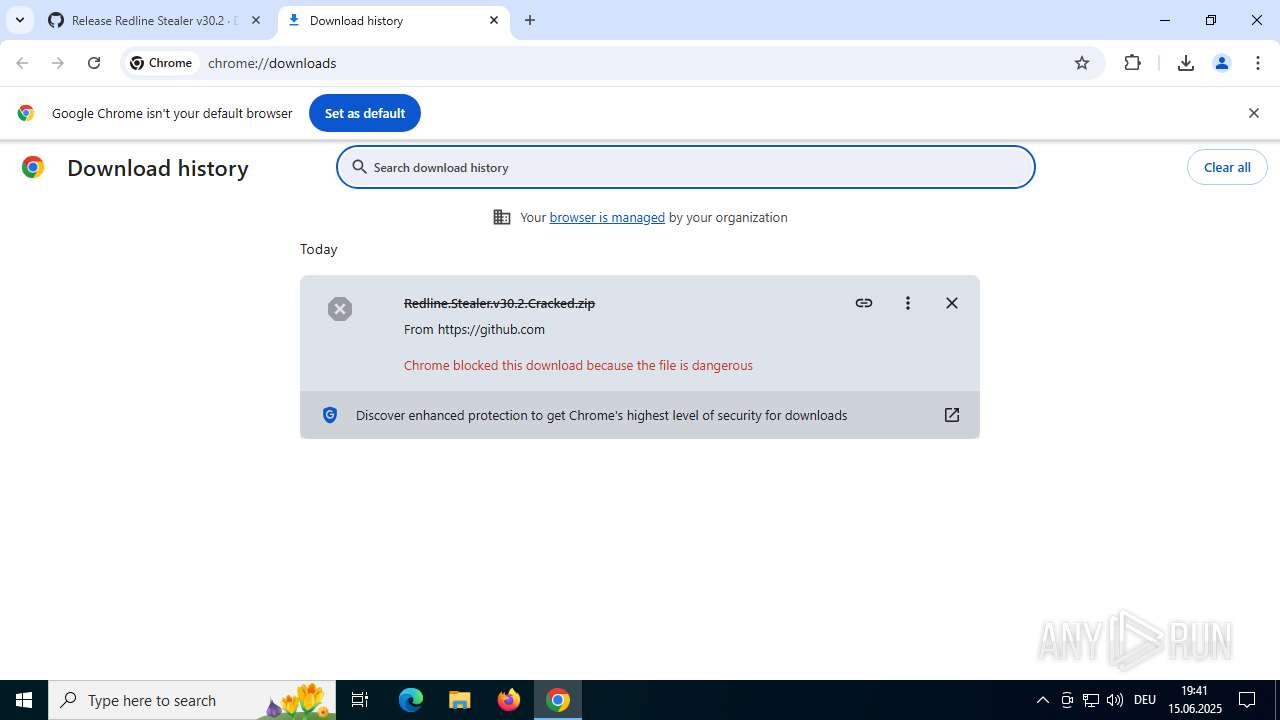
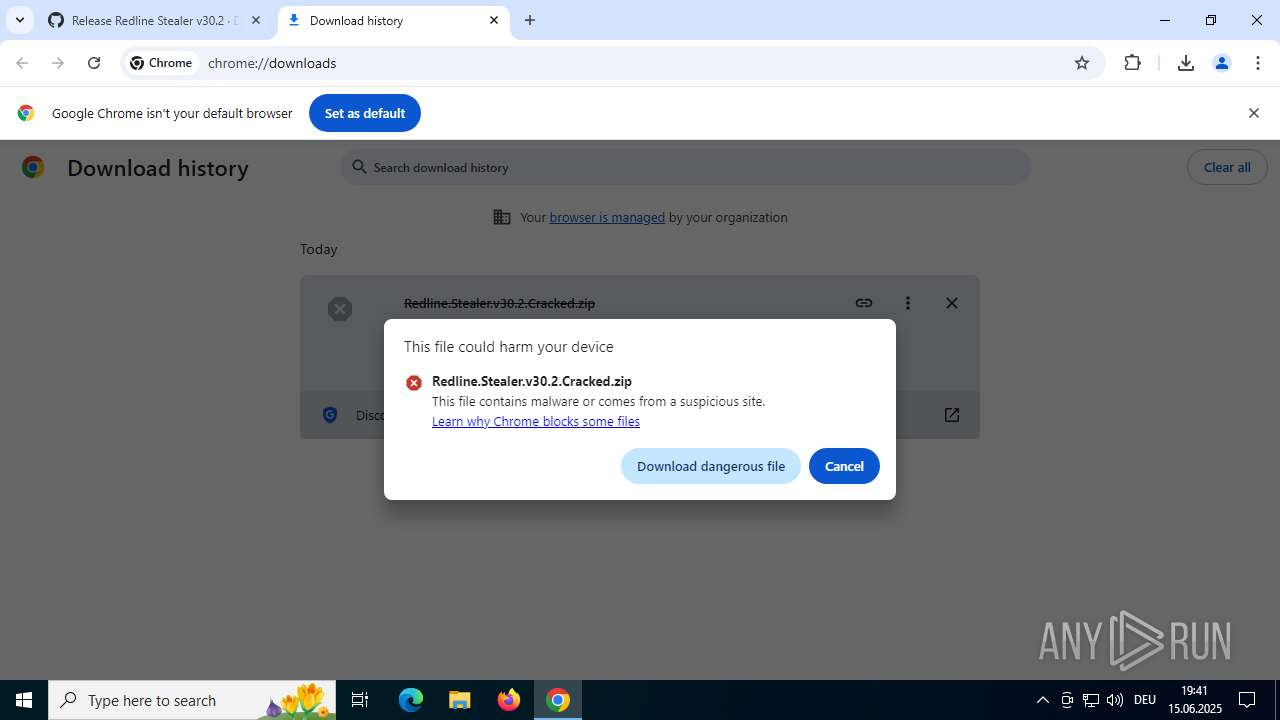
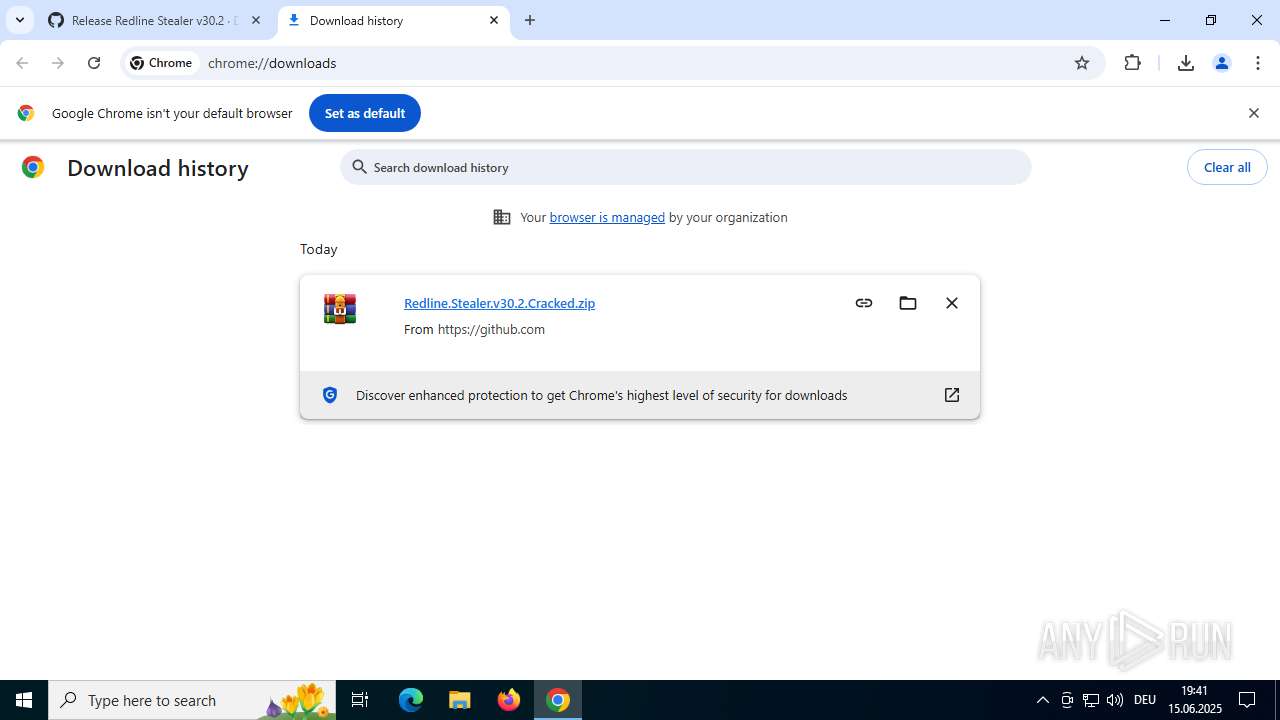
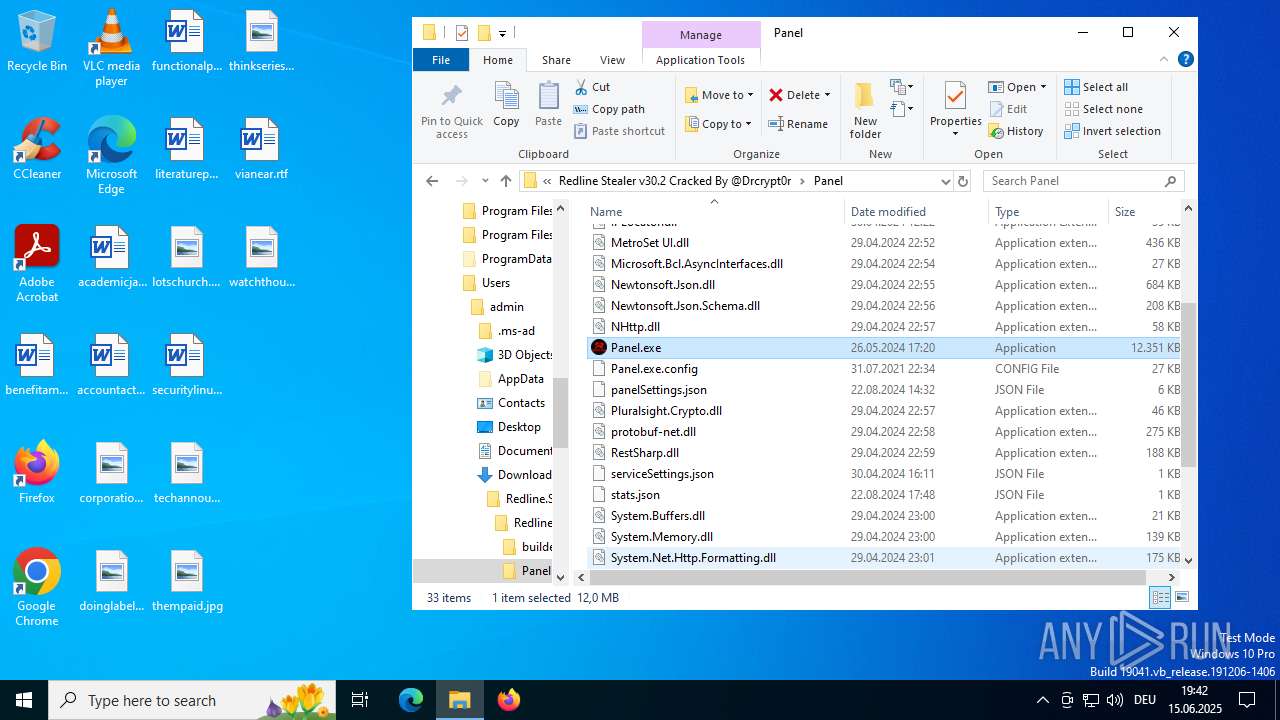
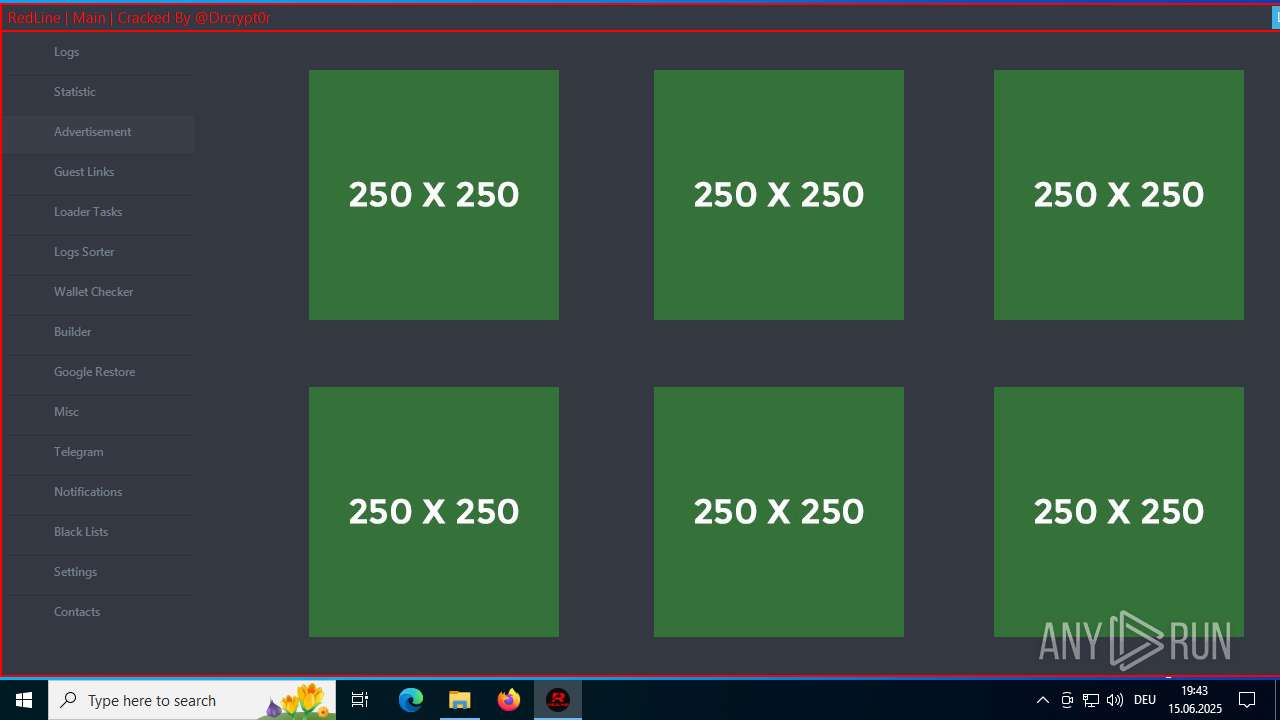
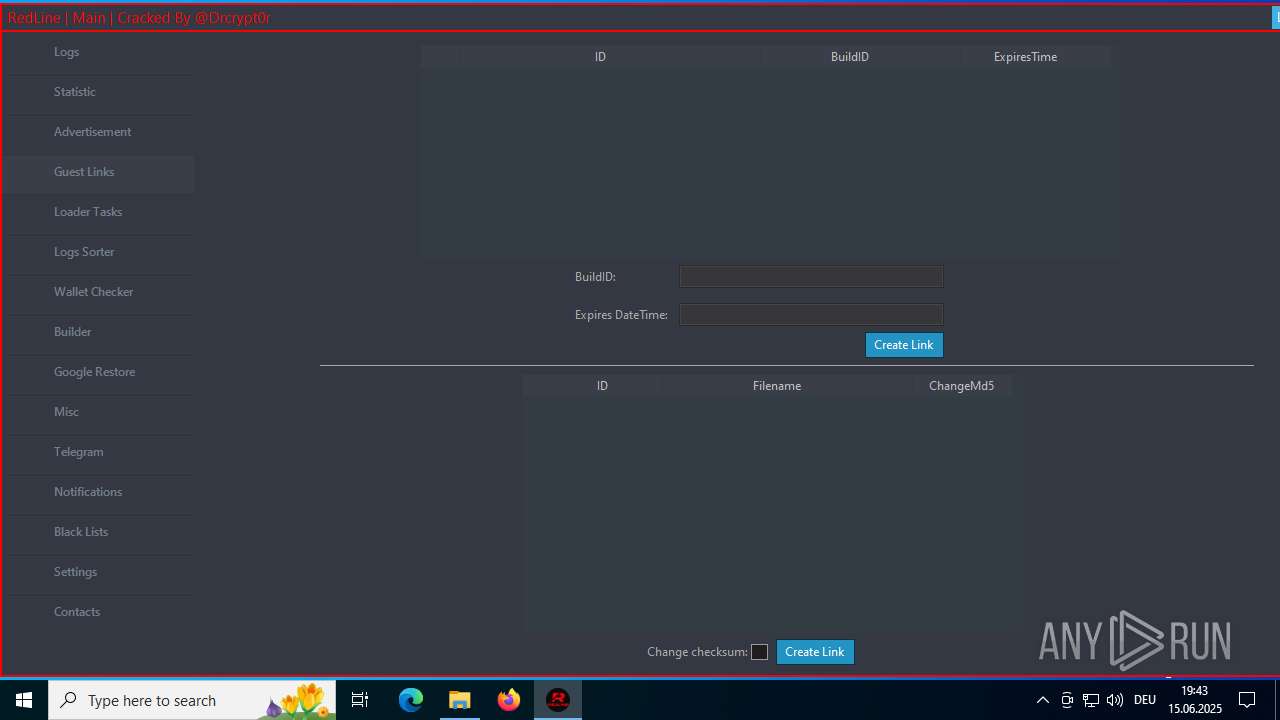
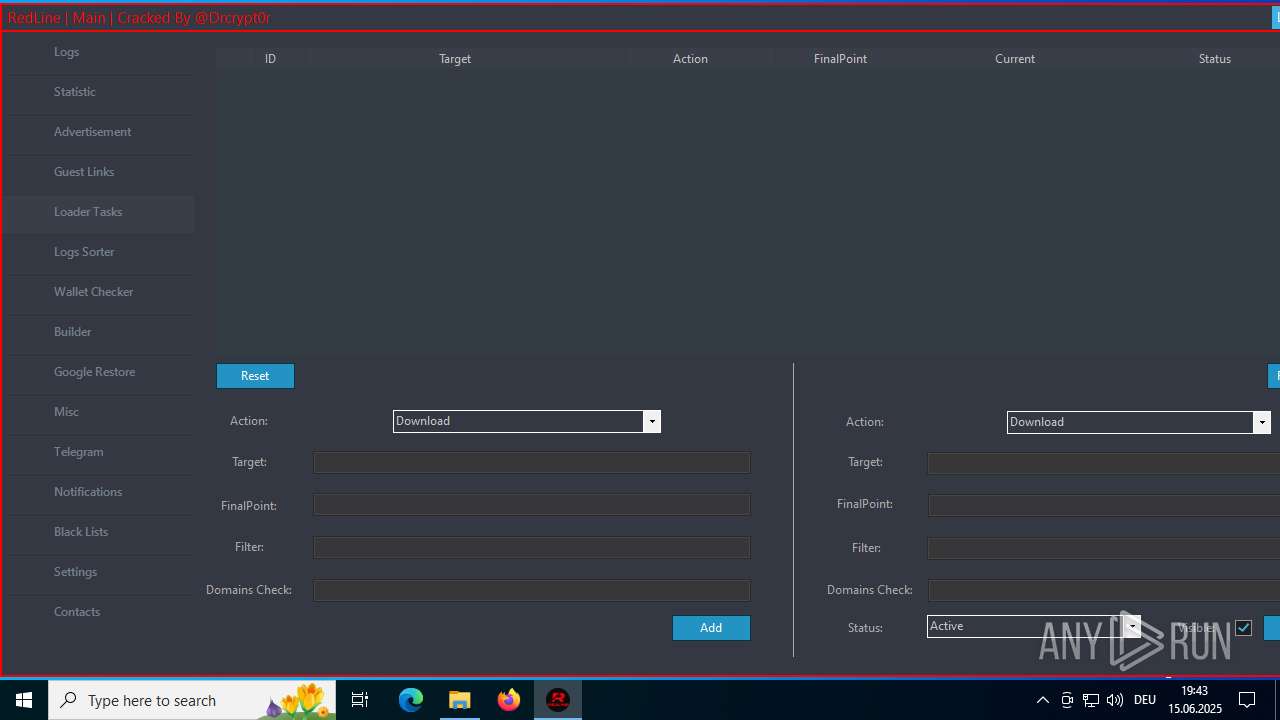
| URL: | https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/tag/RedlineStealer |
| Full analysis: | https://app.any.run/tasks/ea53e76d-dcfa-43b7-baac-16de9c0b2ee1 |
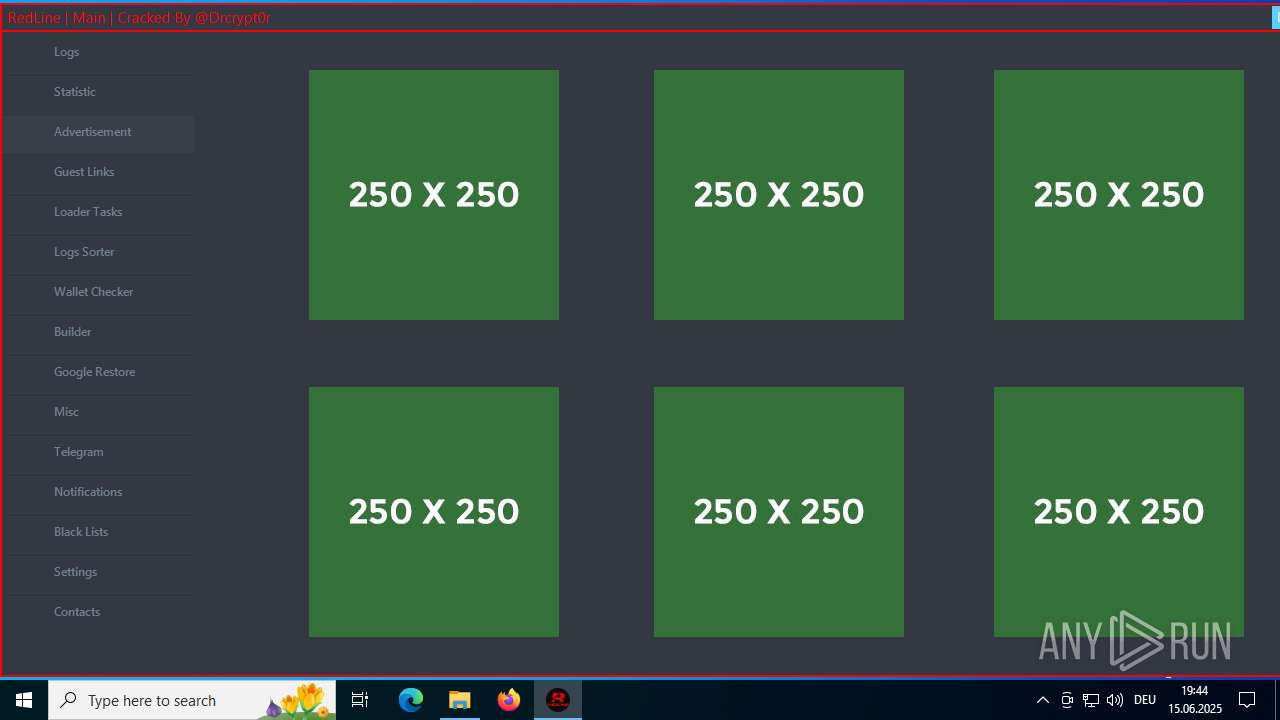
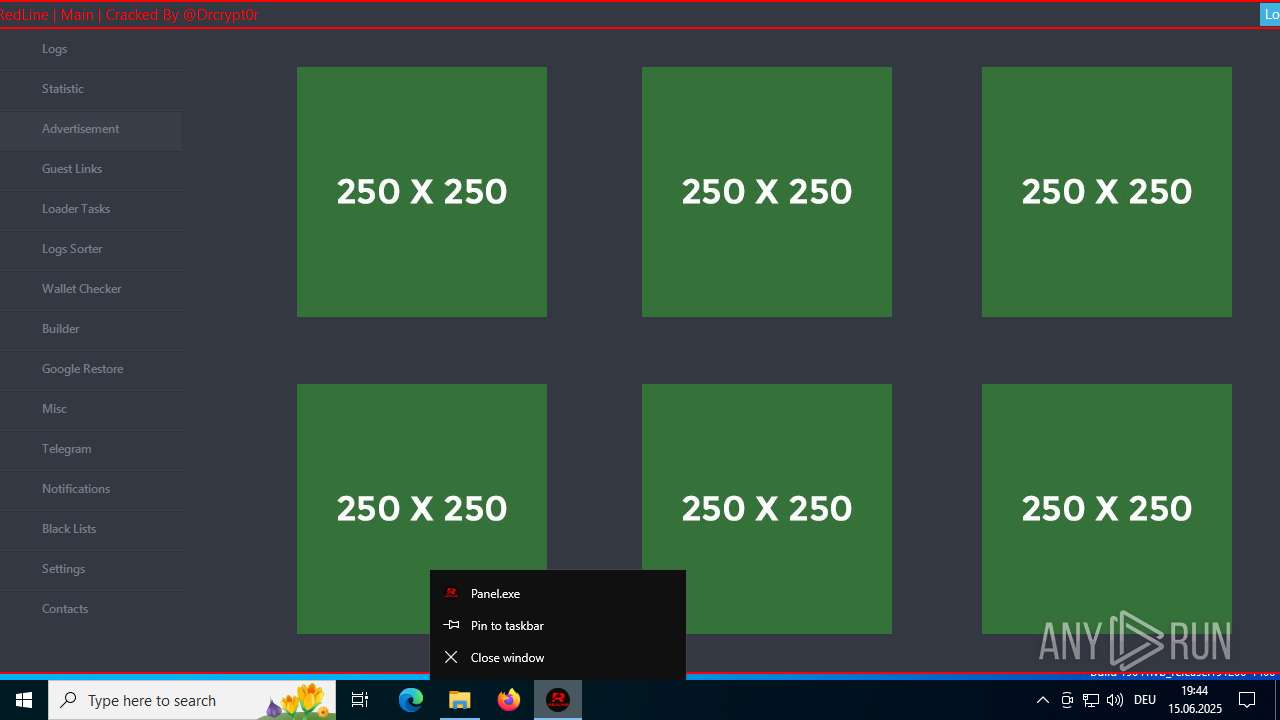
| Verdict: | Malicious activity |
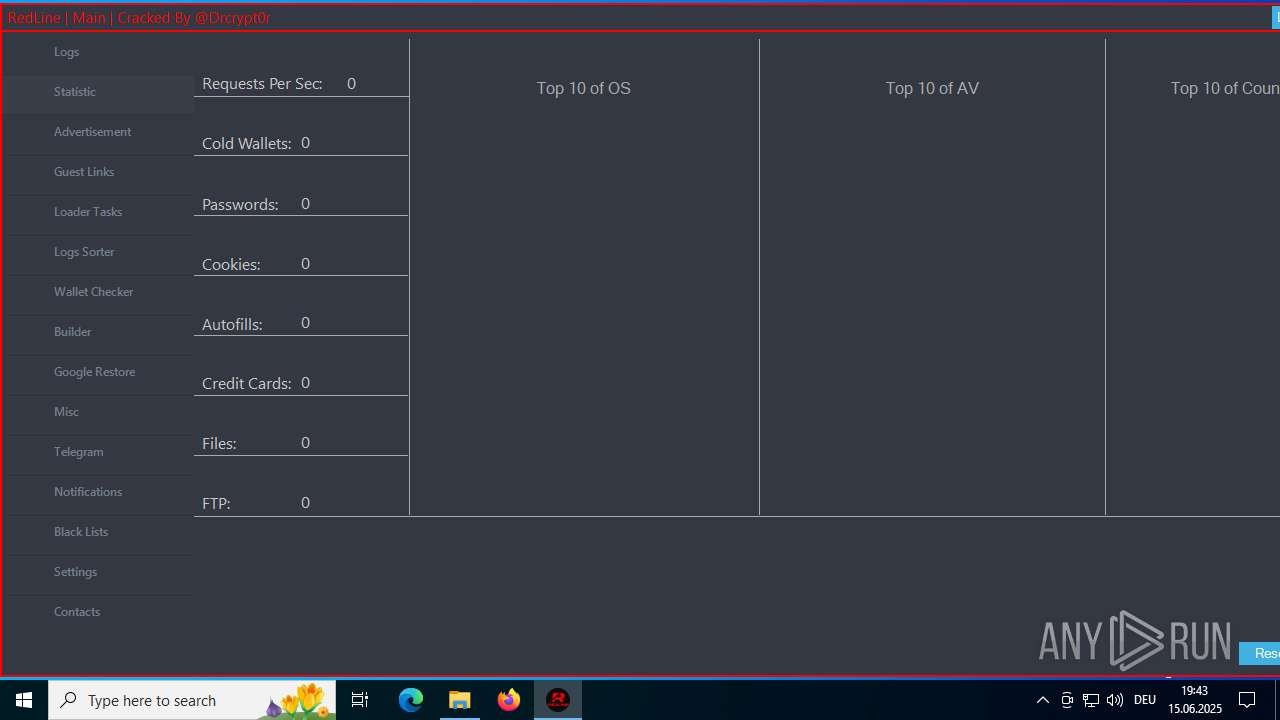
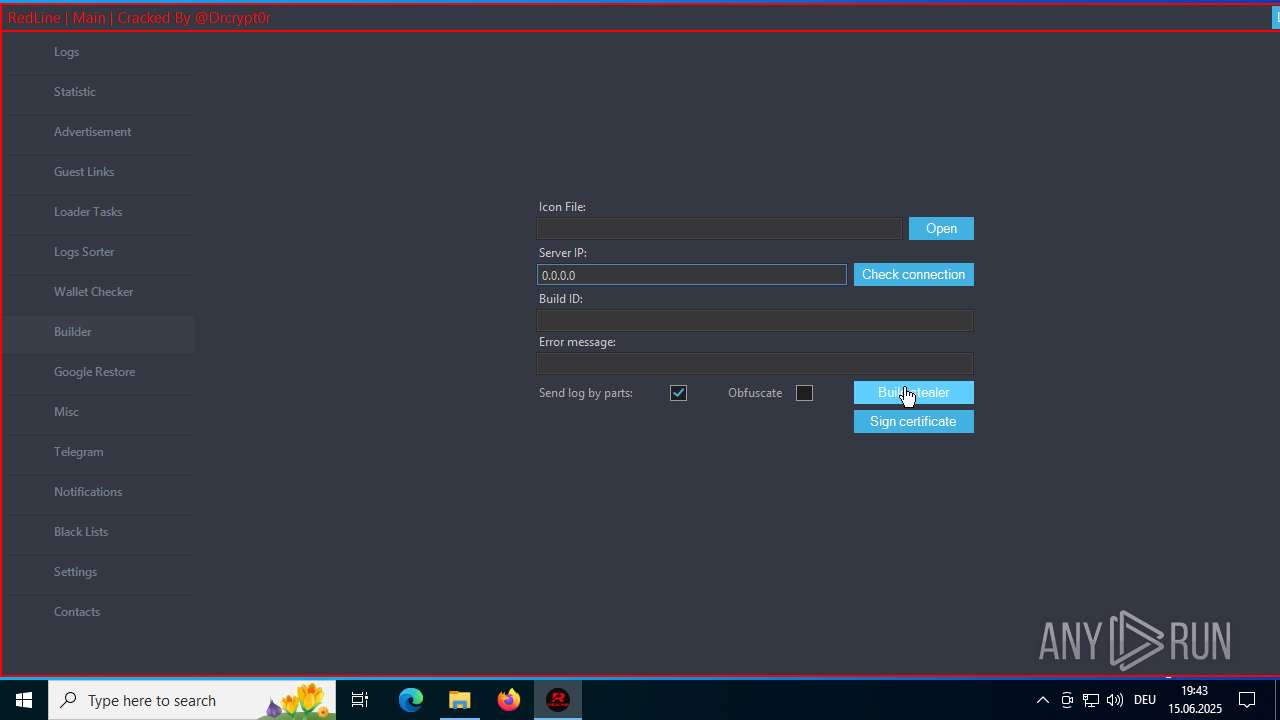
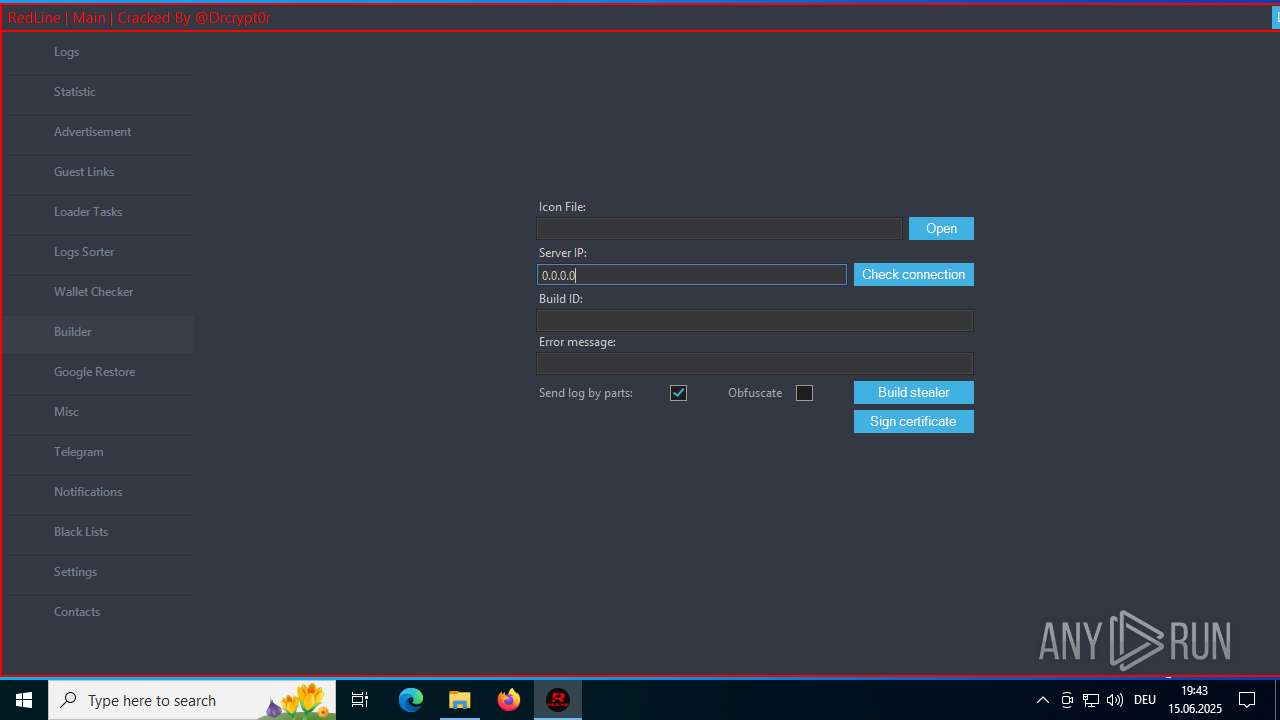
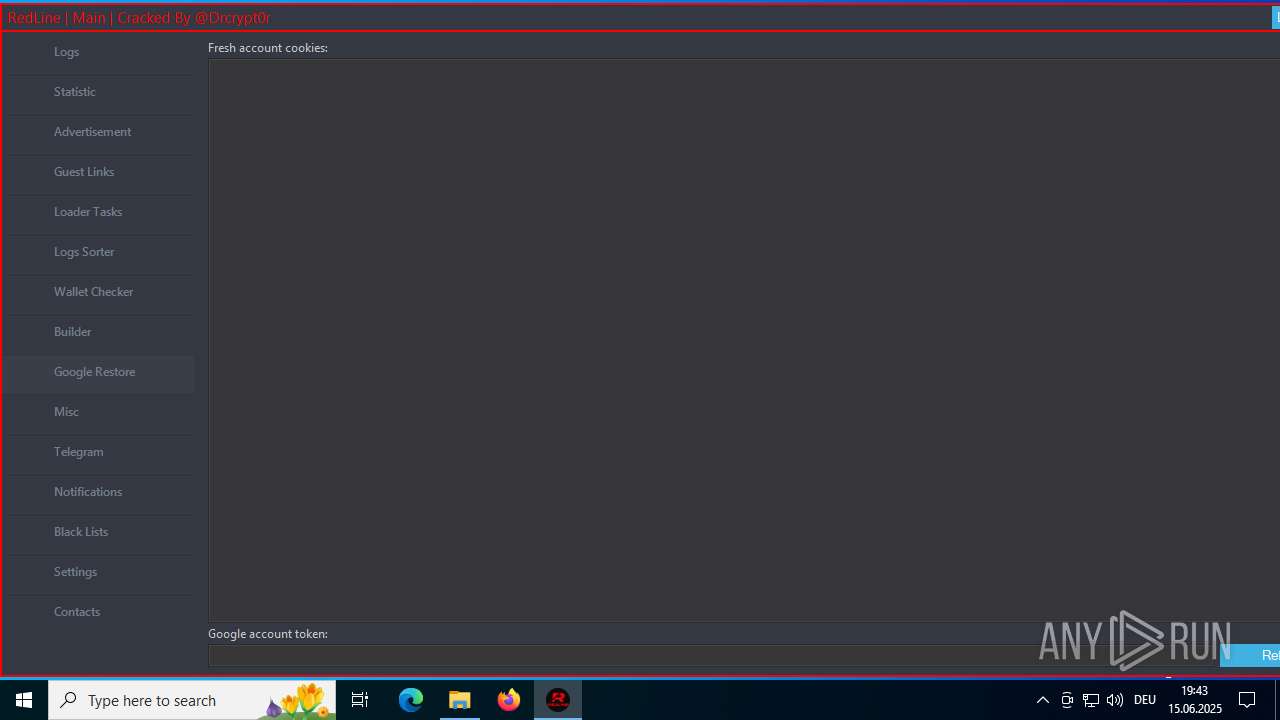
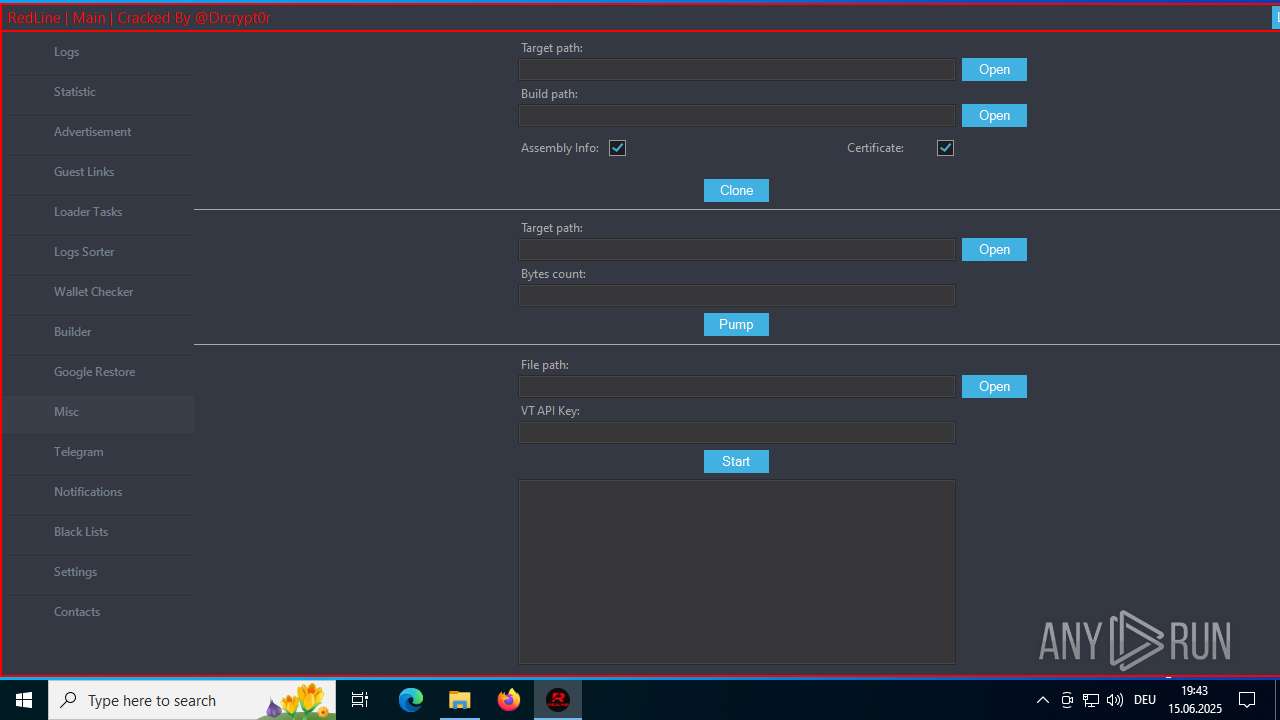
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
| Analysis date: | June 15, 2025, 17:38:48 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8C58328757A484E69819FFFE150138FD |
| SHA1: | 07979263903946FA8A1AEC02977855062DA026A0 |
| SHA256: | 866C8D2974C8B56D85F4E818D6963B95F588967AB542F159B9707065EEDBC361 |
| SSDEEP: | 3:N8tEdyYqA/KNEJijzEZA72qK3pLTRhJy:2uUAiD/WJx3pLTRh4 |
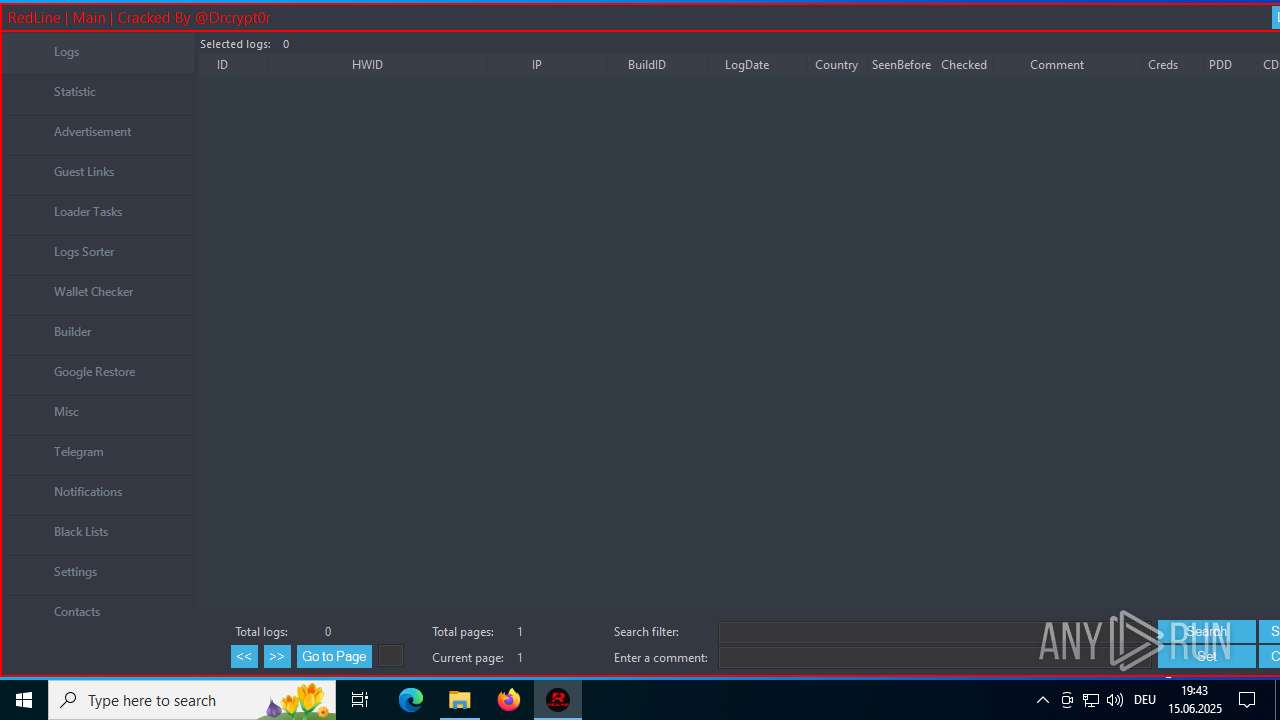
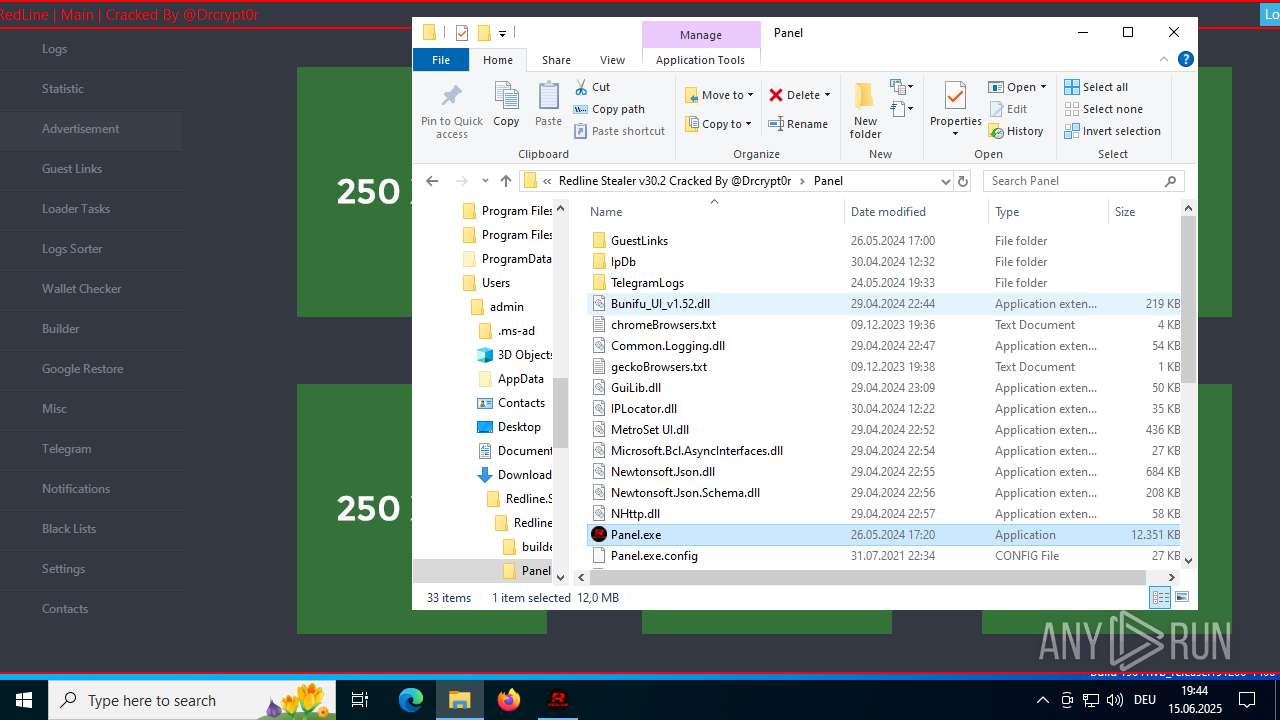
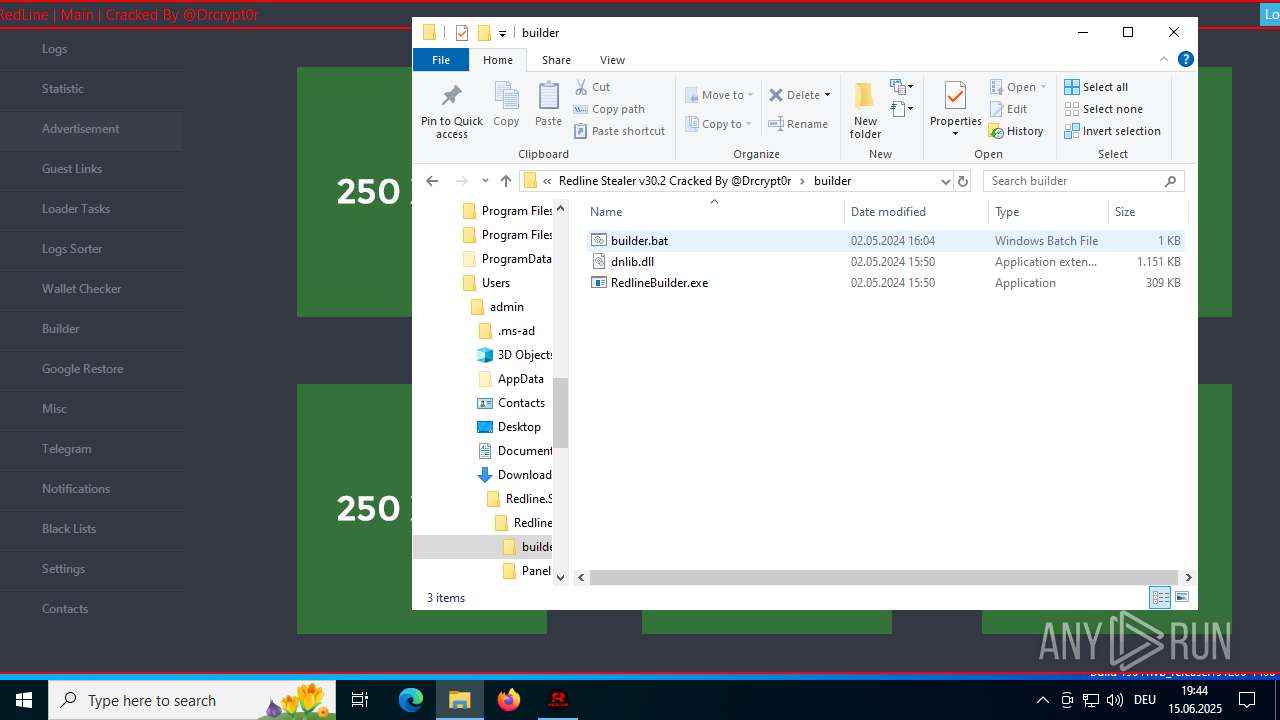
MALICIOUS
XORed URL has been found (YARA)
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
REDLINE has been detected (YARA)
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
DISCORDGRABBER has been detected (YARA)
- Panel.exe (PID: 1604)
- Panel.exe (PID: 6380)
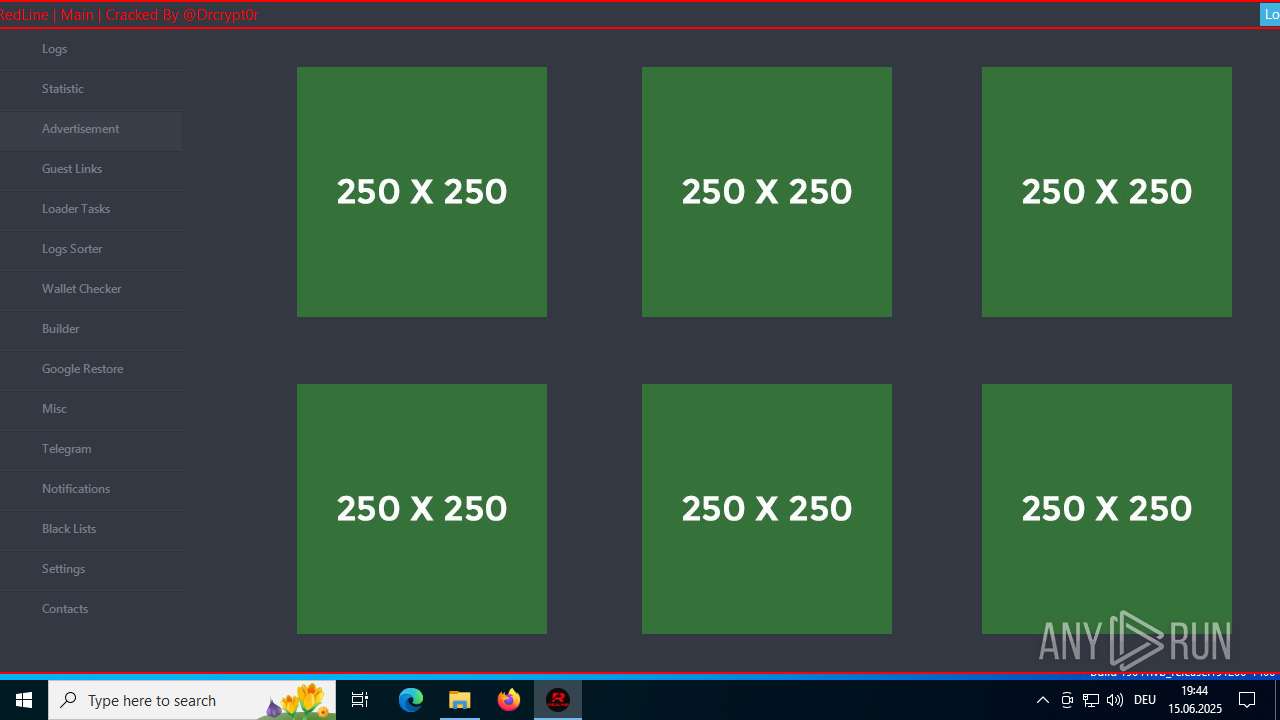
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3672)
Reads security settings of Internet Explorer
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
- ShellExperienceHost.exe (PID: 436)
Reads the date of Windows installation
- Panel.exe (PID: 6380)
Application launched itself
- Panel.exe (PID: 6380)
Found regular expressions for crypto-addresses (YARA)
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
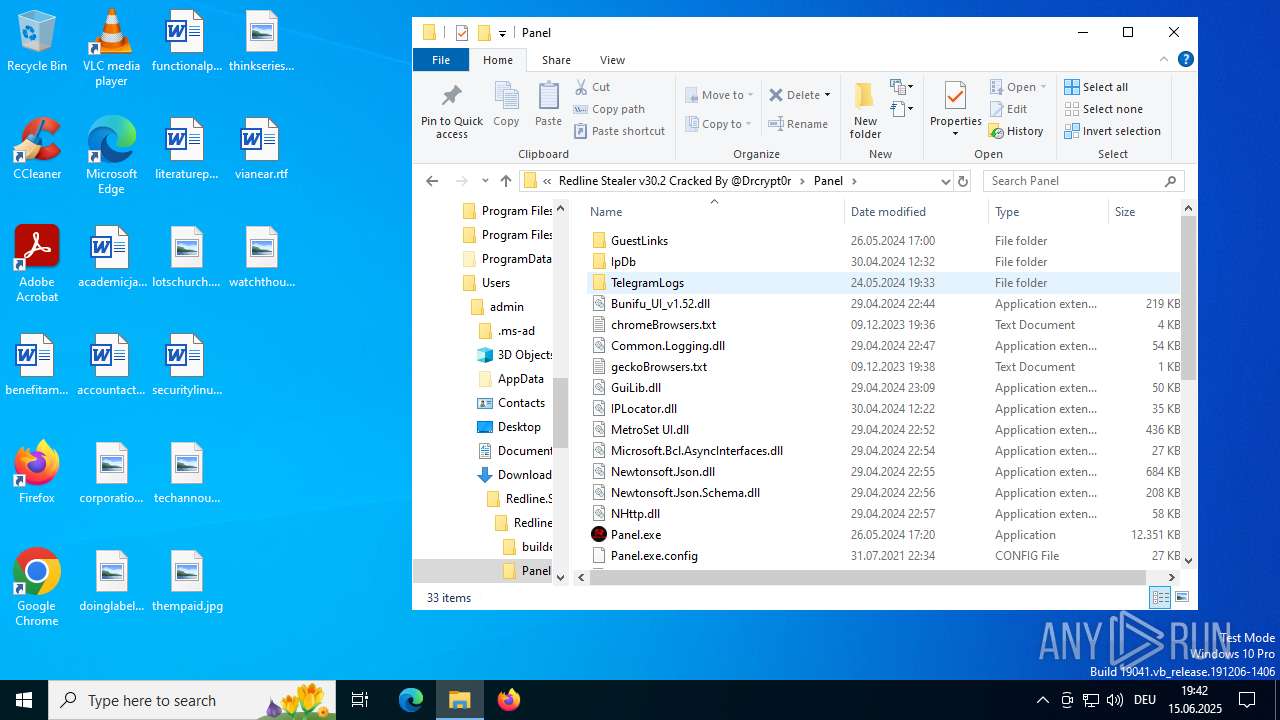
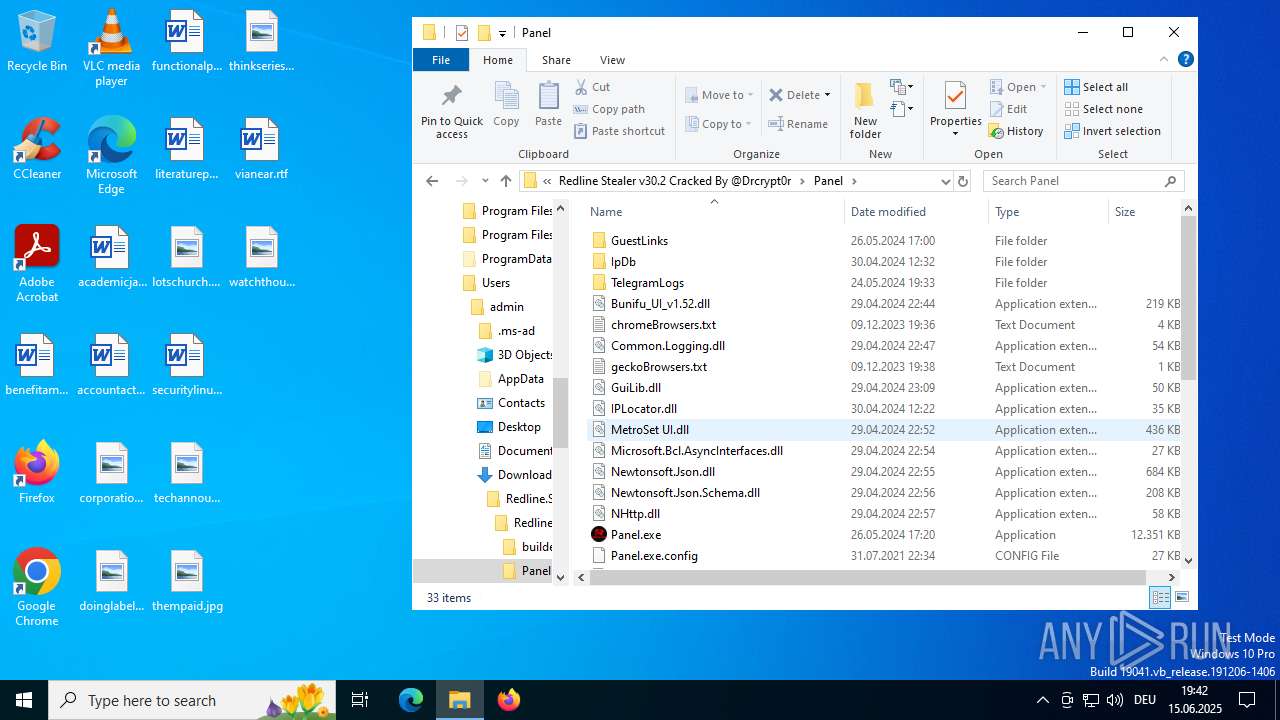
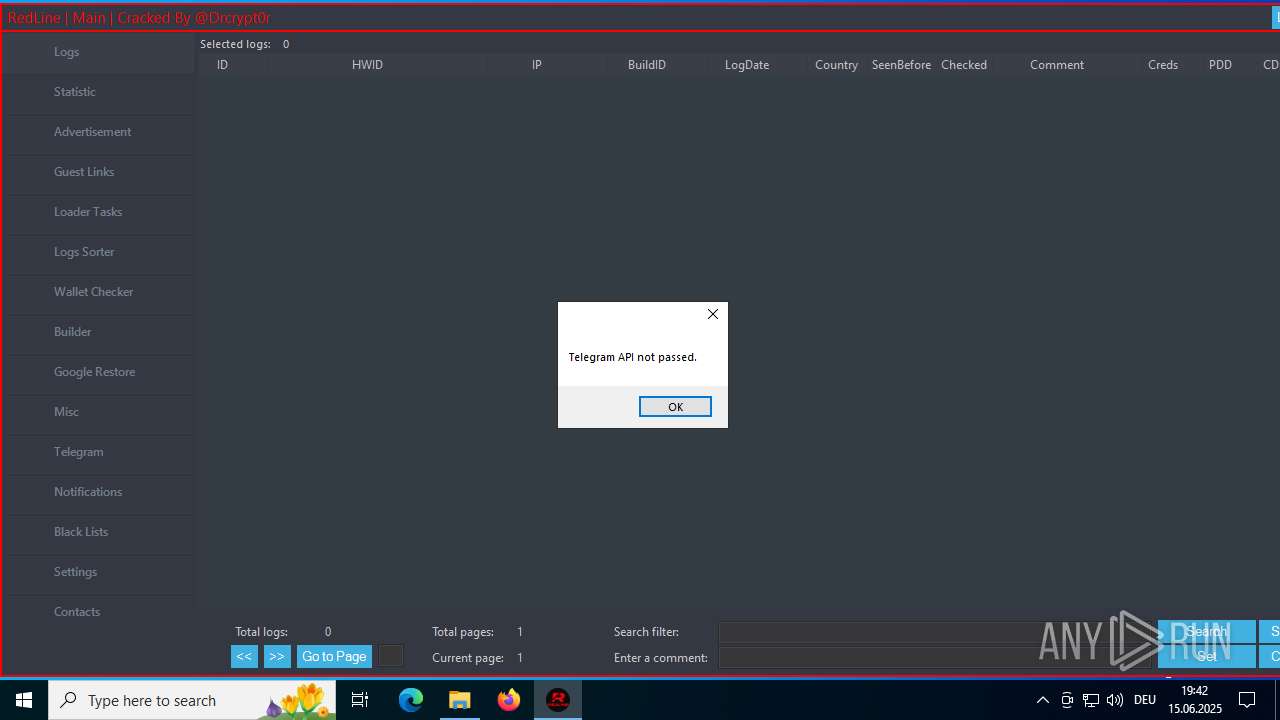
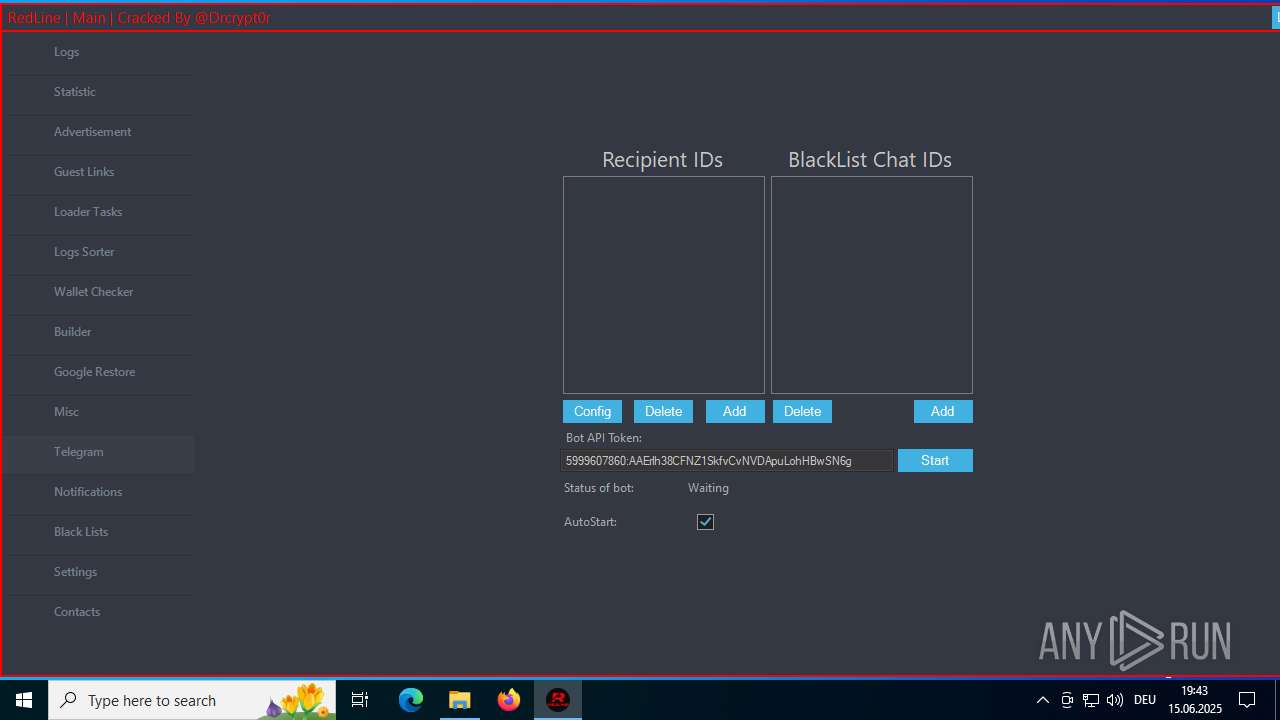
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Panel.exe (PID: 1604)
Possible usage of Discord/Telegram API has been detected (YARA)
- Panel.exe (PID: 1604)
INFO
Application launched itself
- chrome.exe (PID: 4520)
Reads the software policy settings
- slui.exe (PID: 3936)
- Panel.exe (PID: 1604)
Checks supported languages
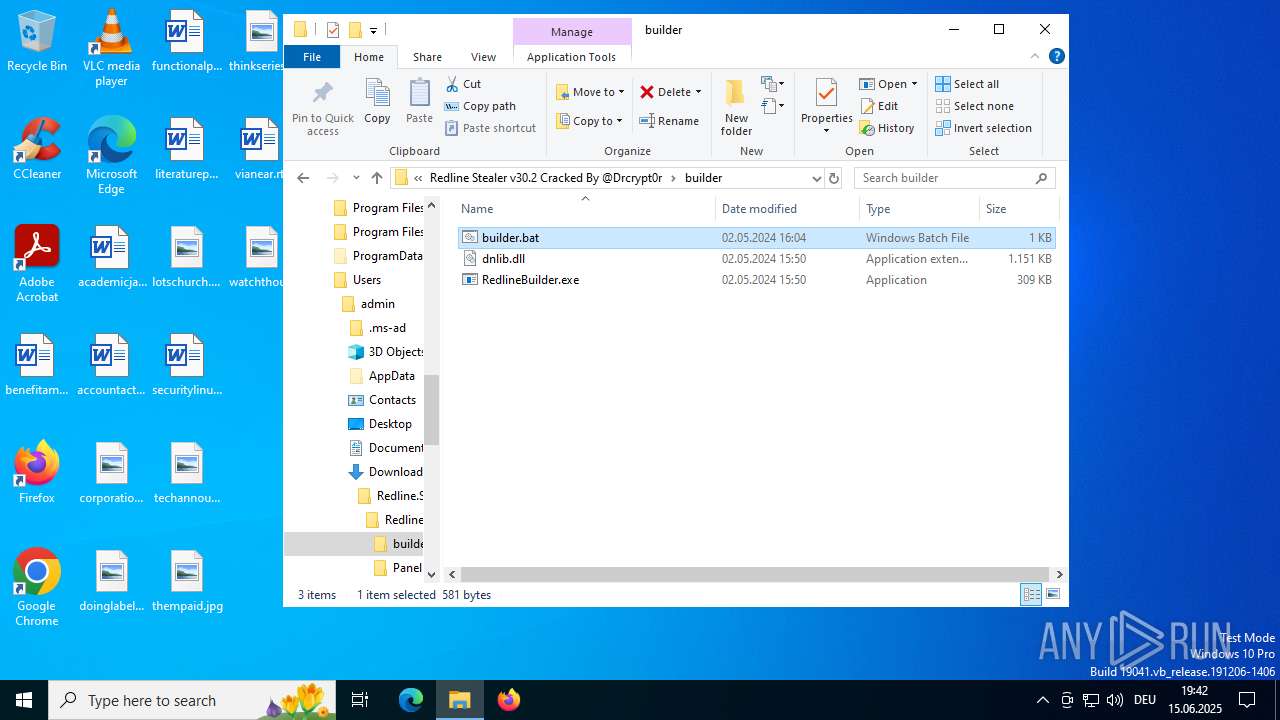
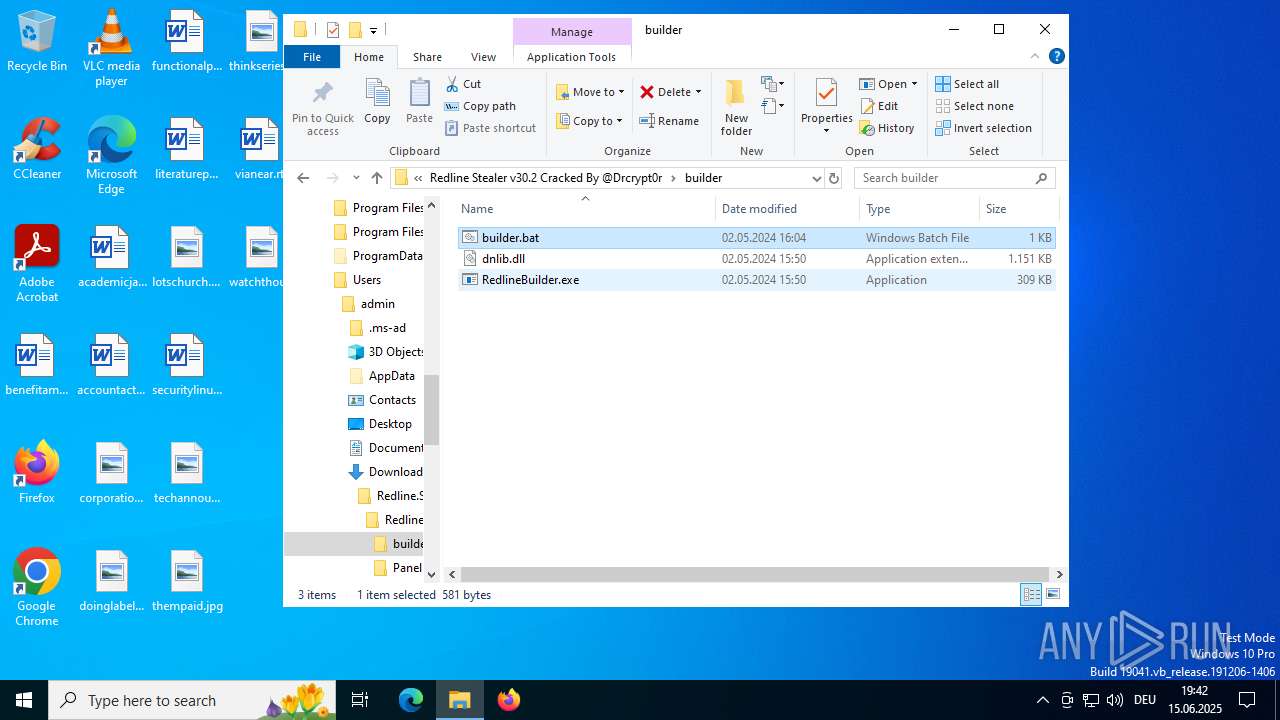
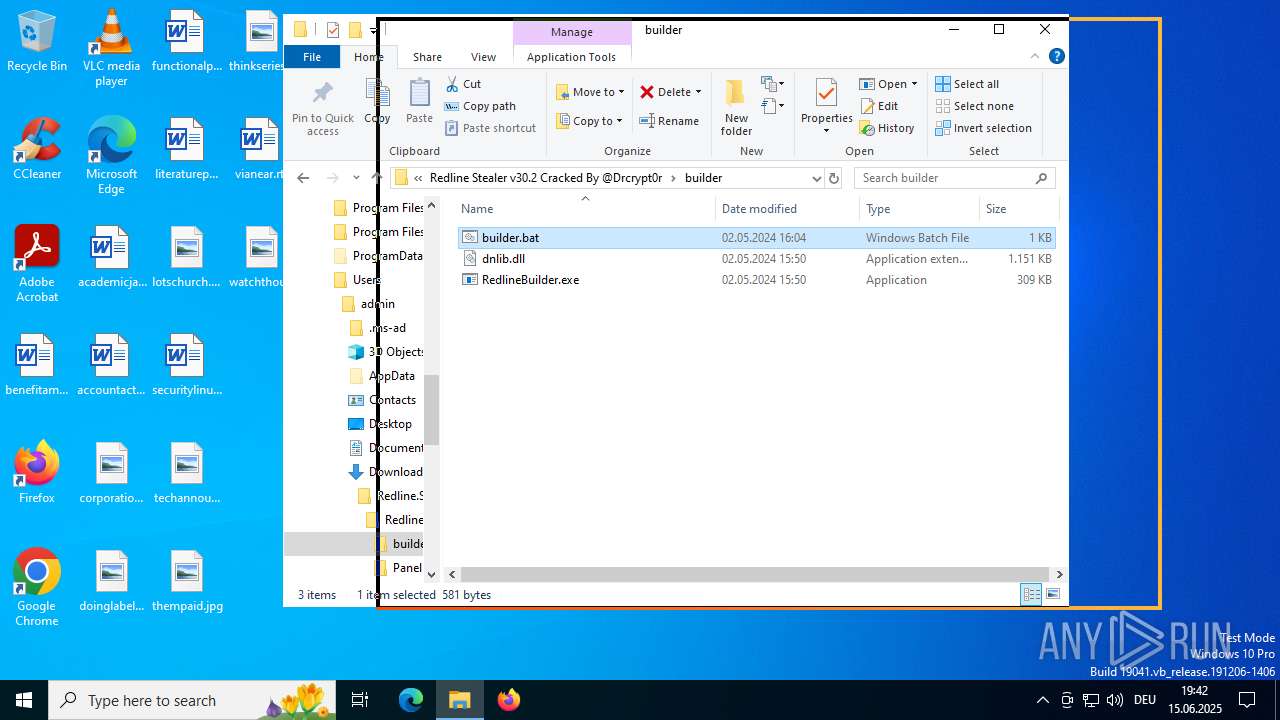
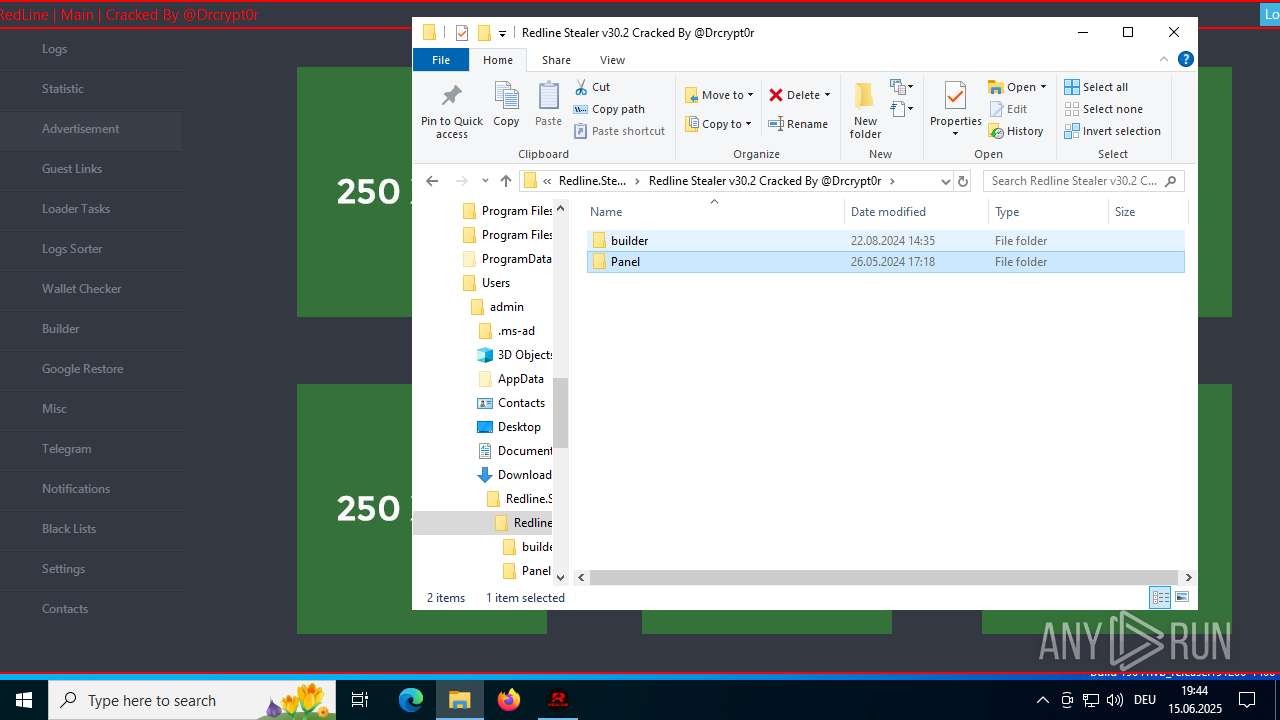
- RedlineBuilder.exe (PID: 1576)
- RedlineBuilder.exe (PID: 5012)
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
- ShellExperienceHost.exe (PID: 436)
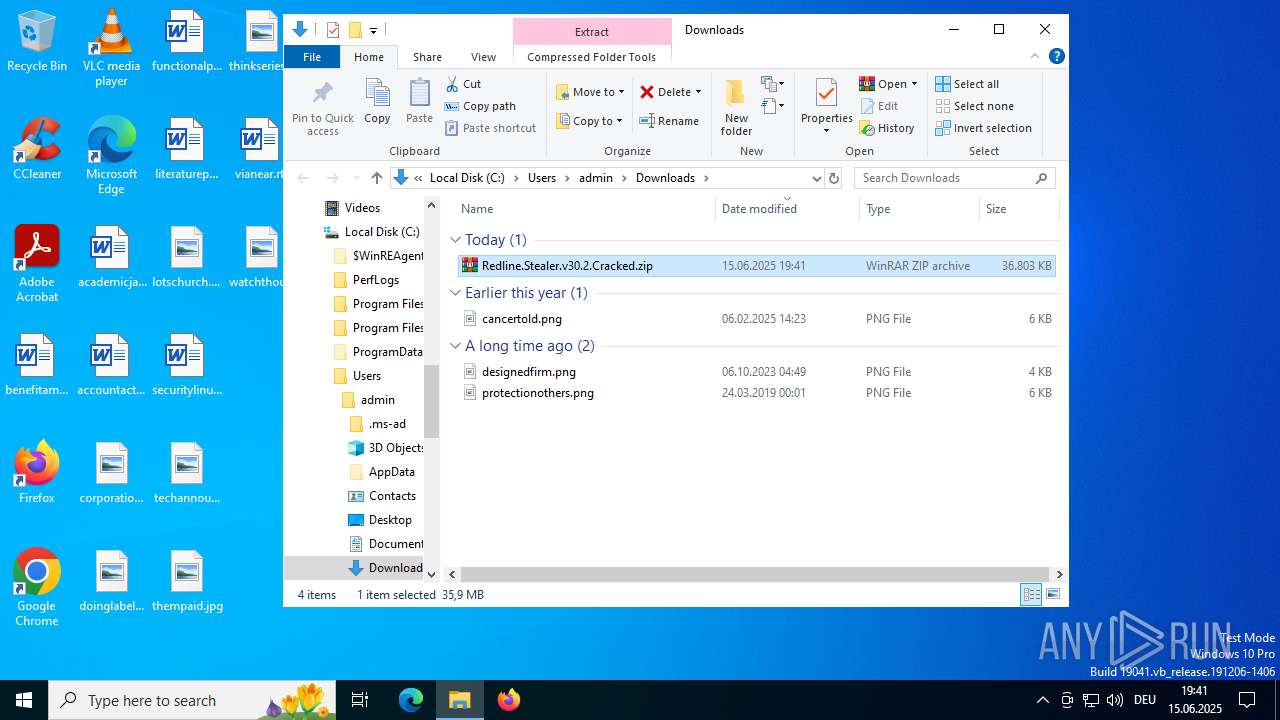
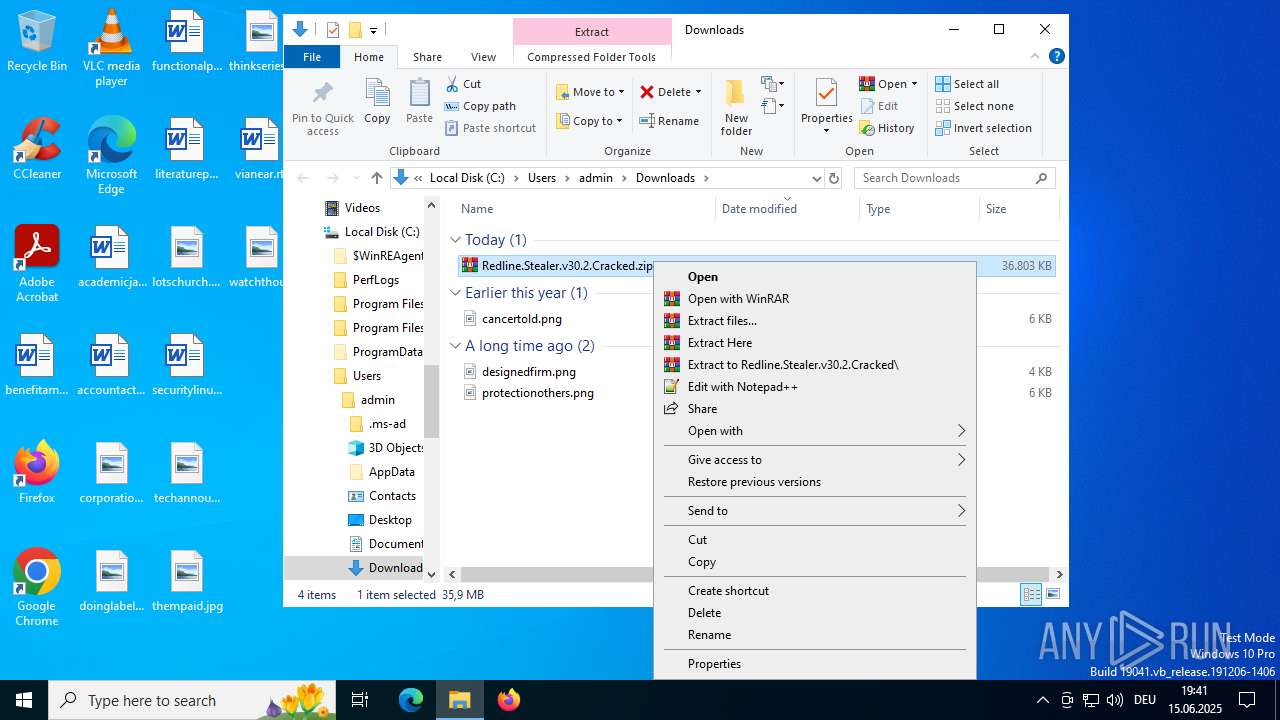
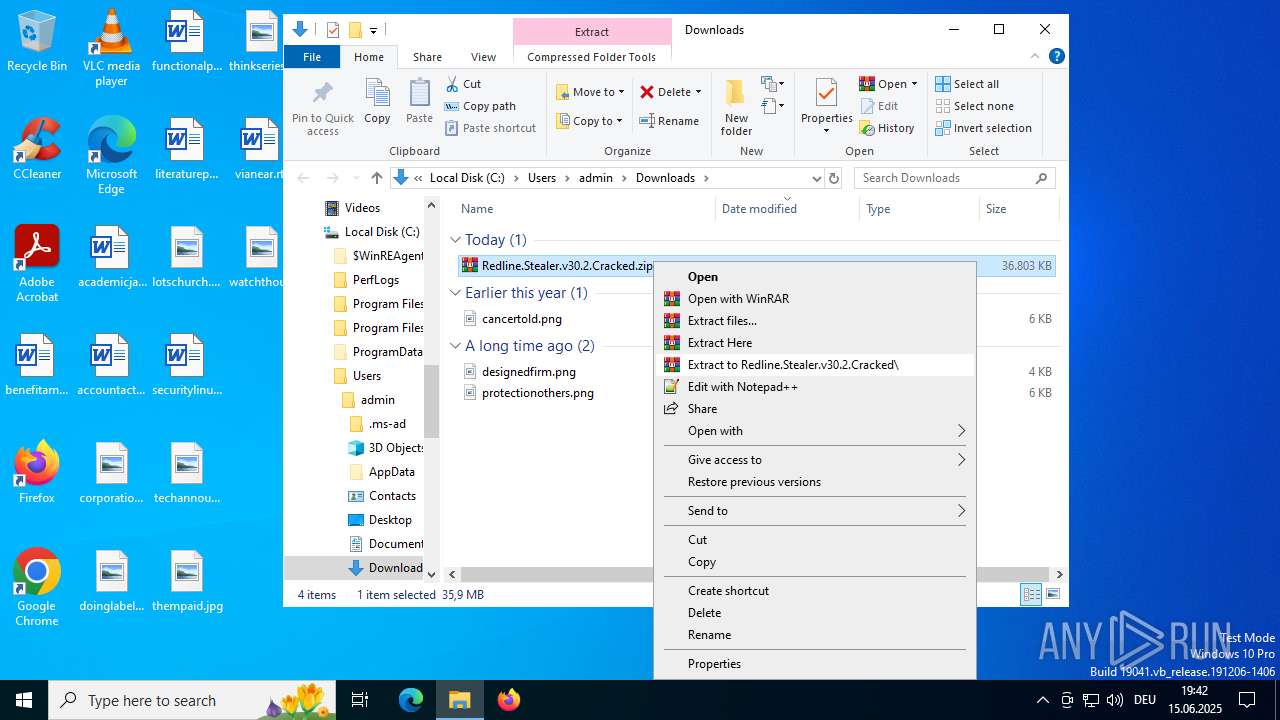
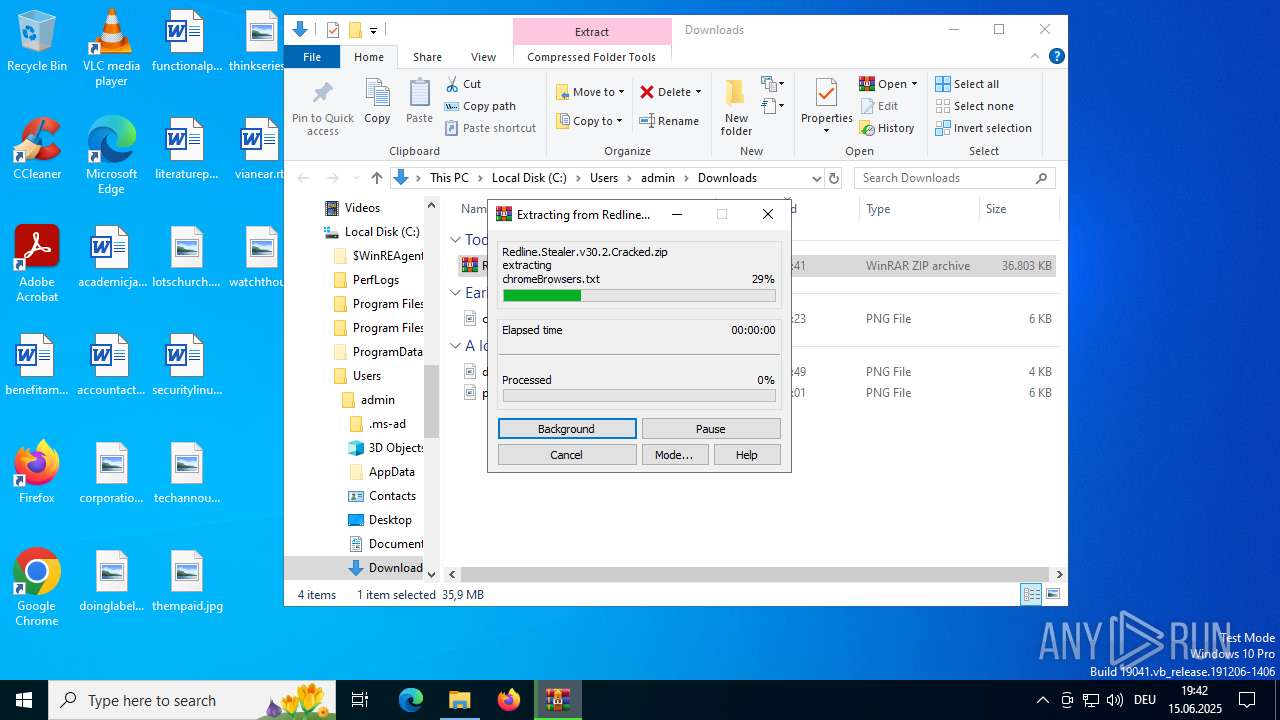
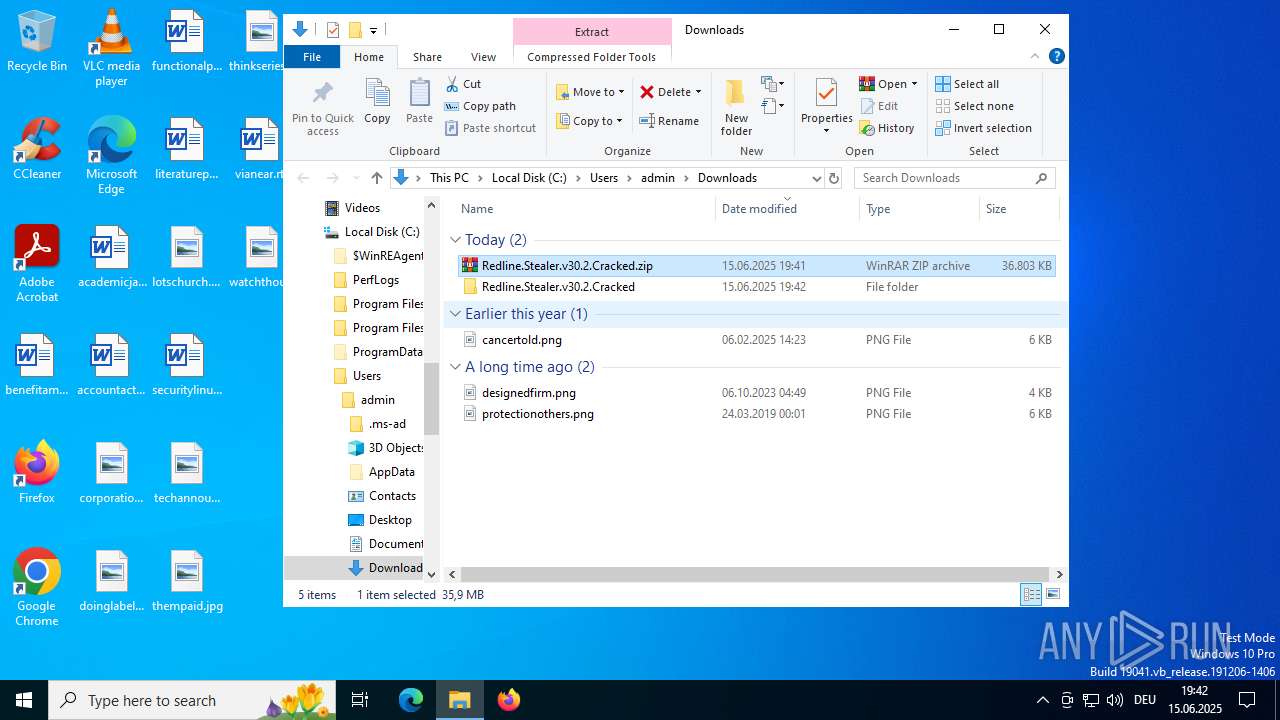
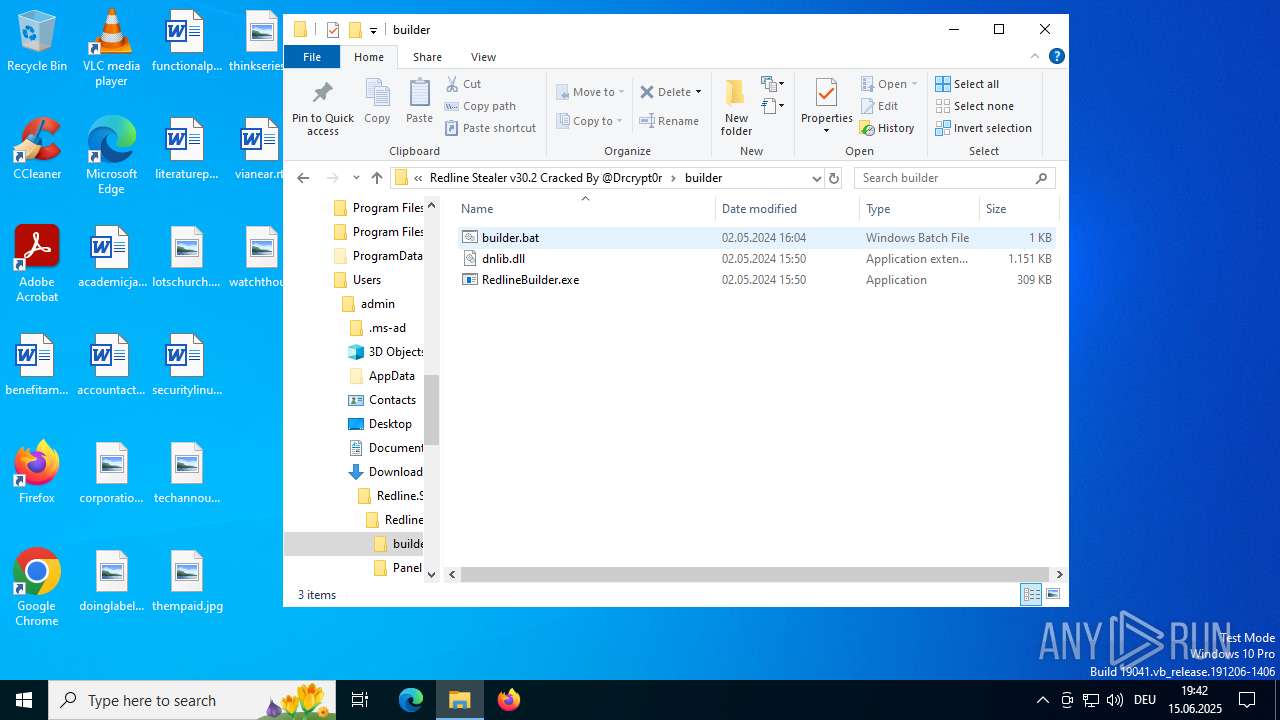
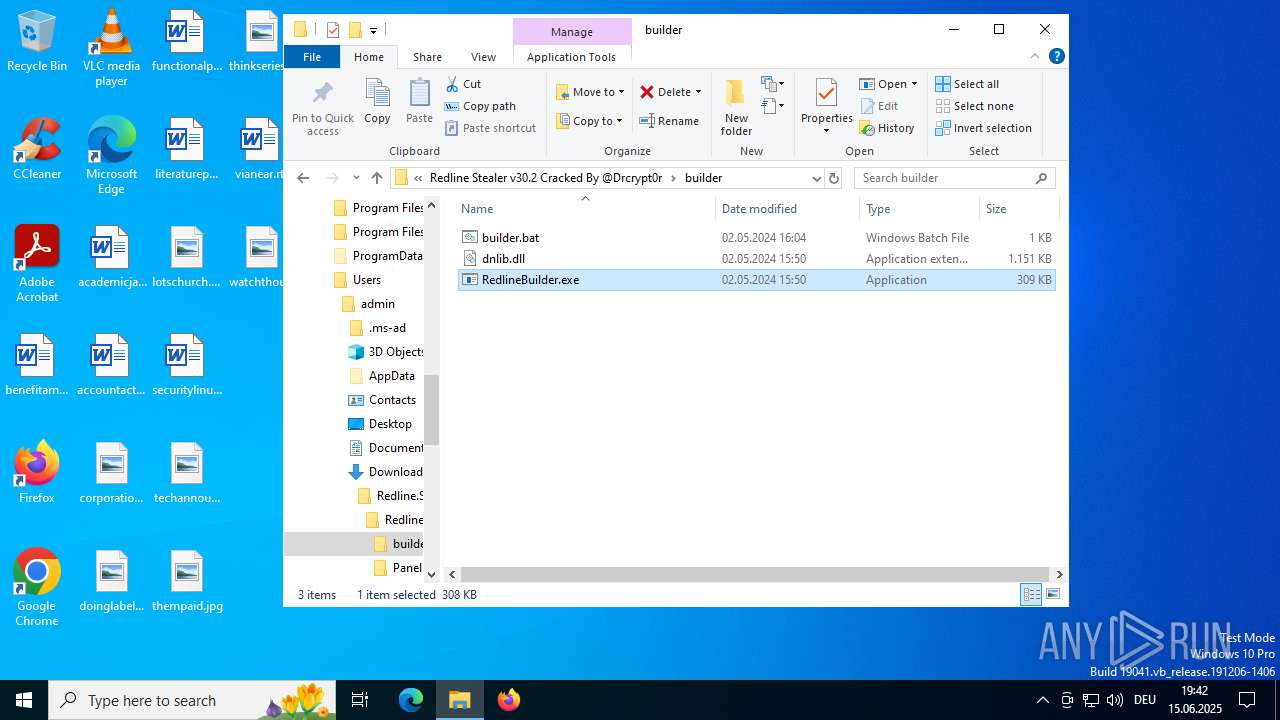
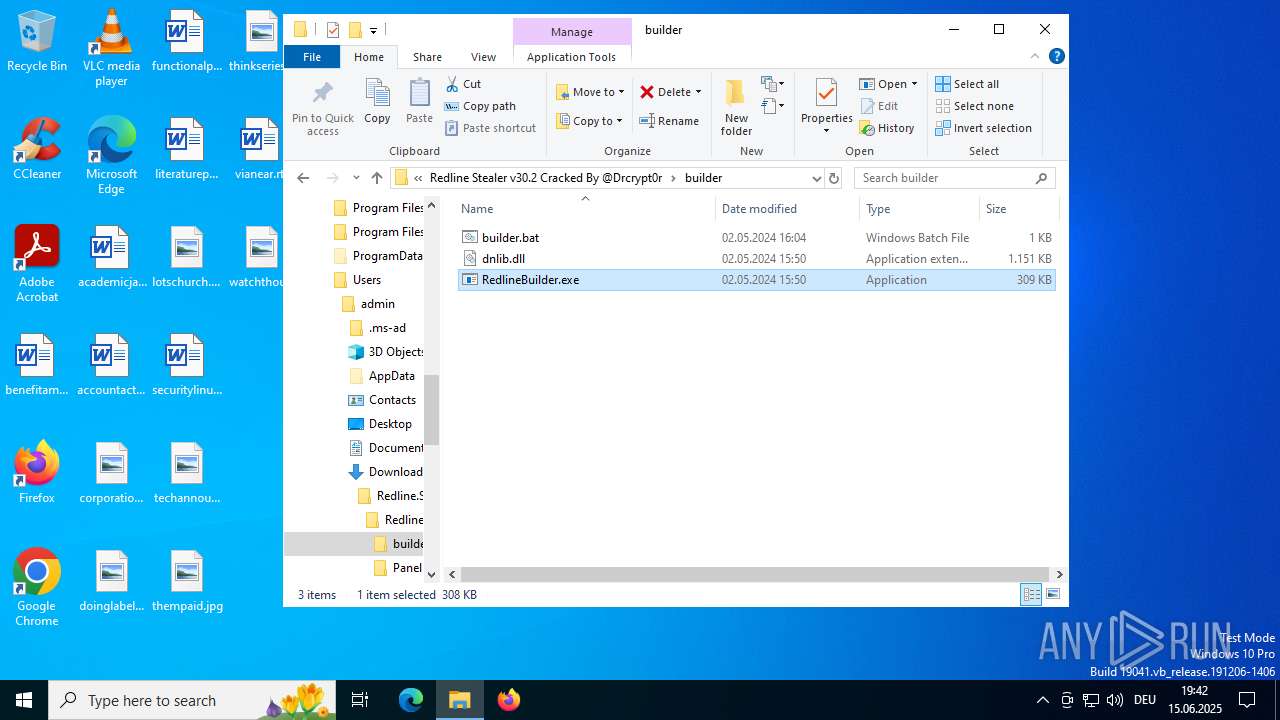
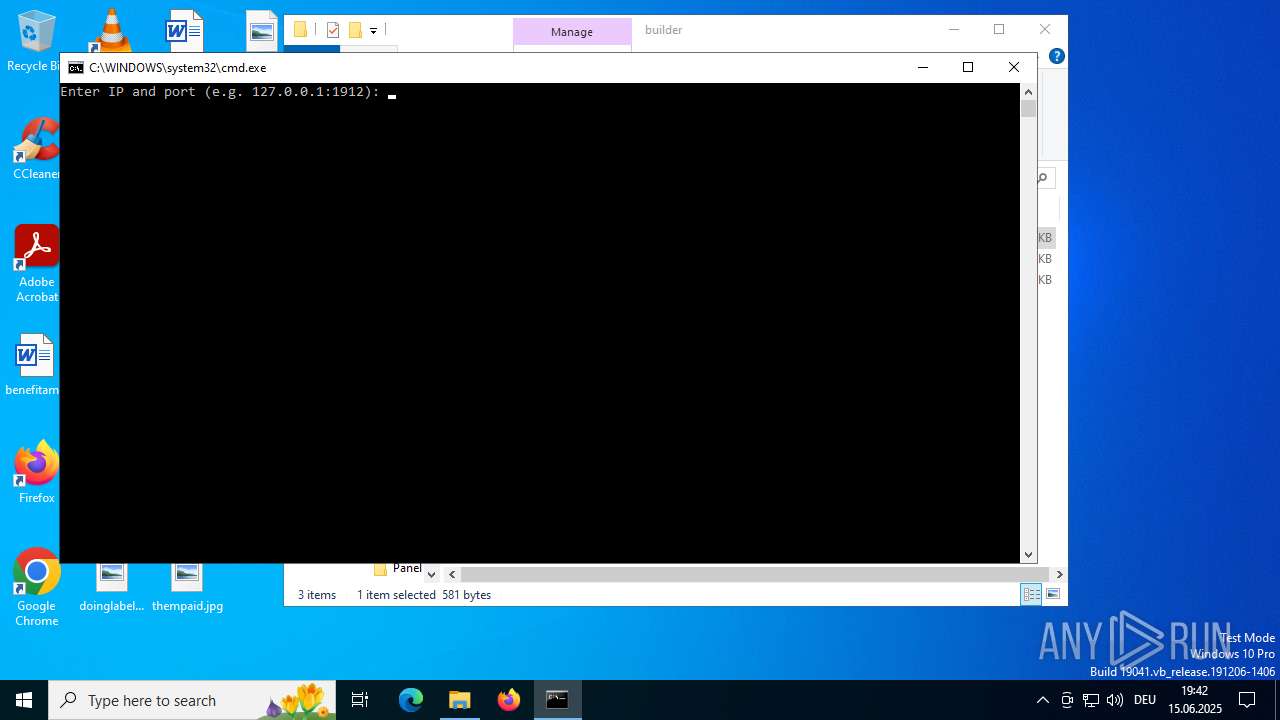
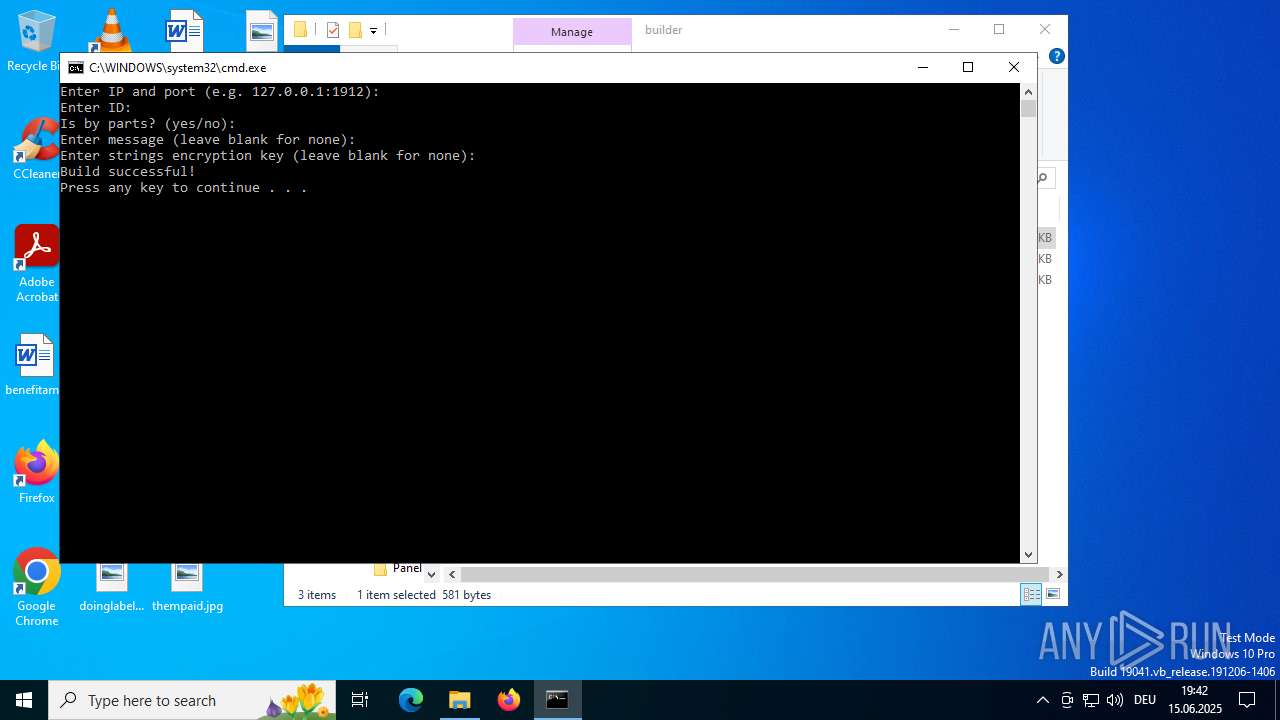
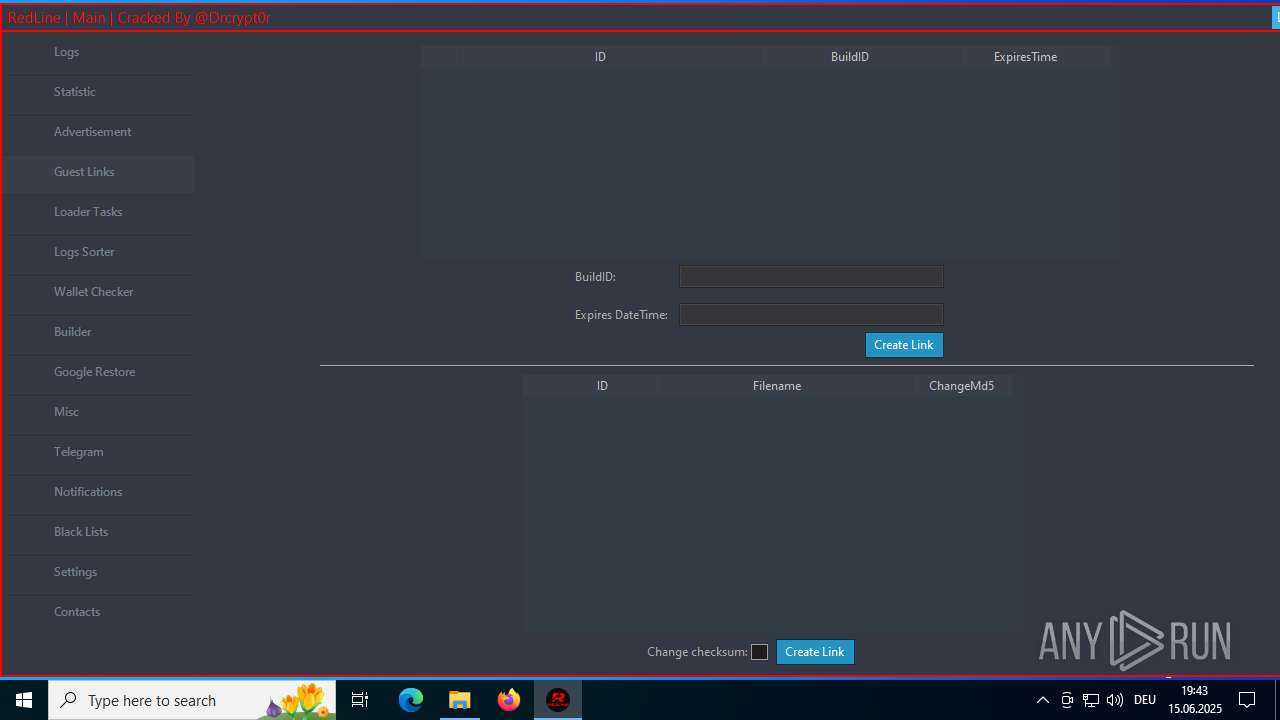
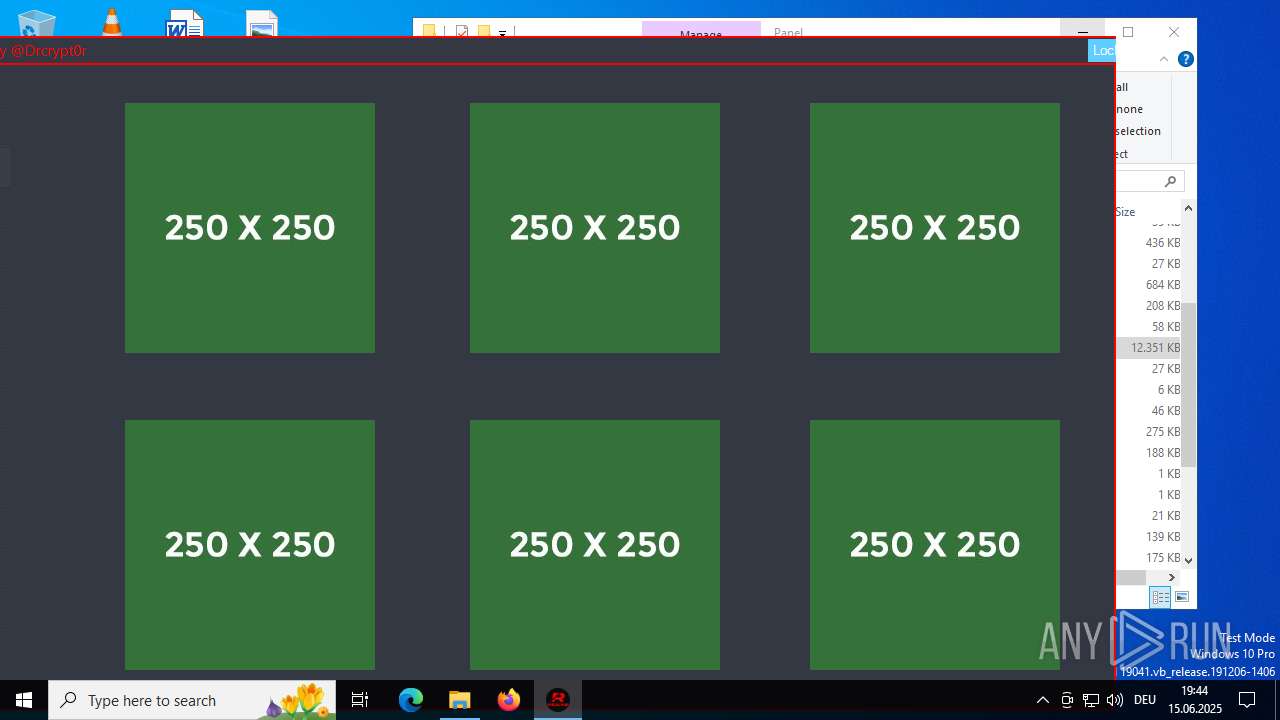
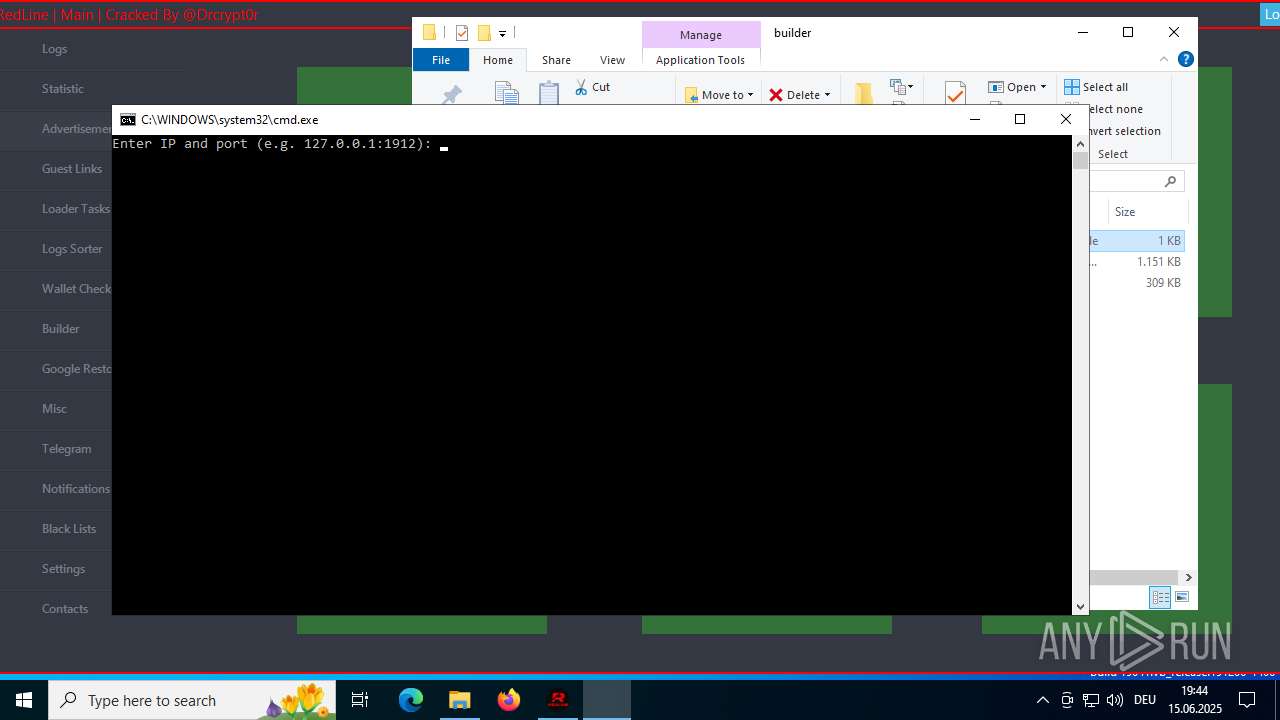
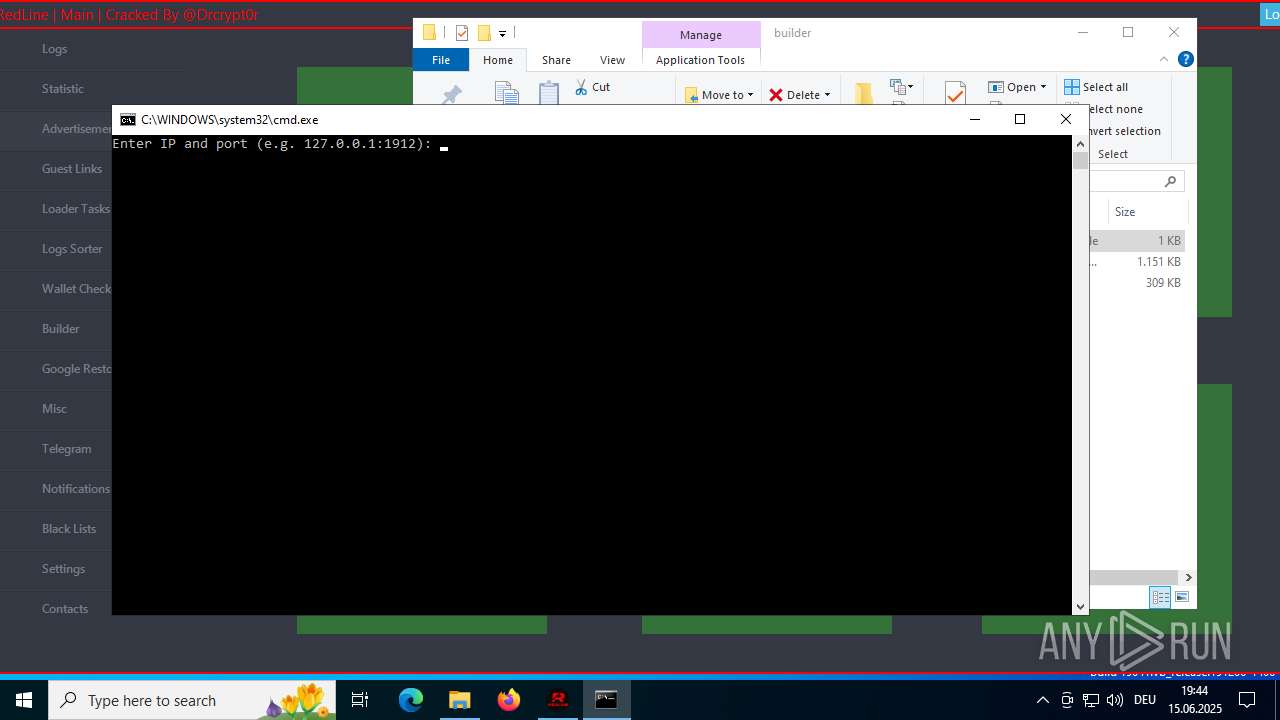
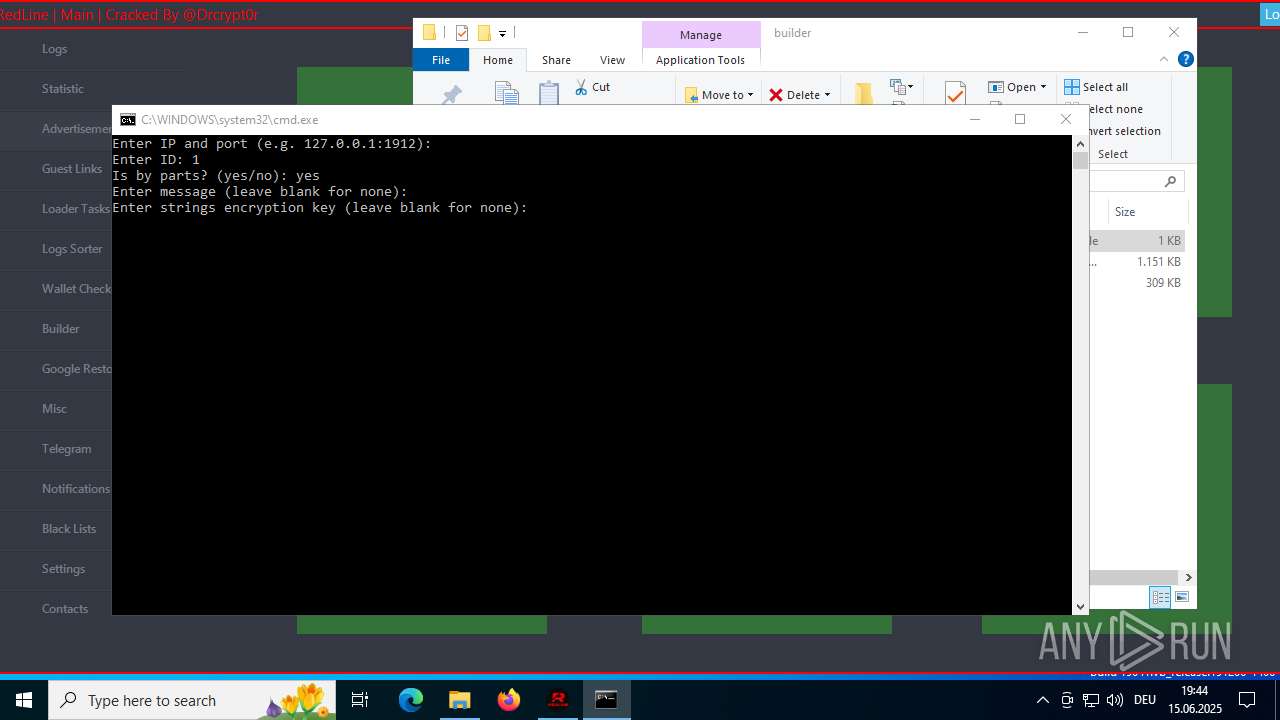
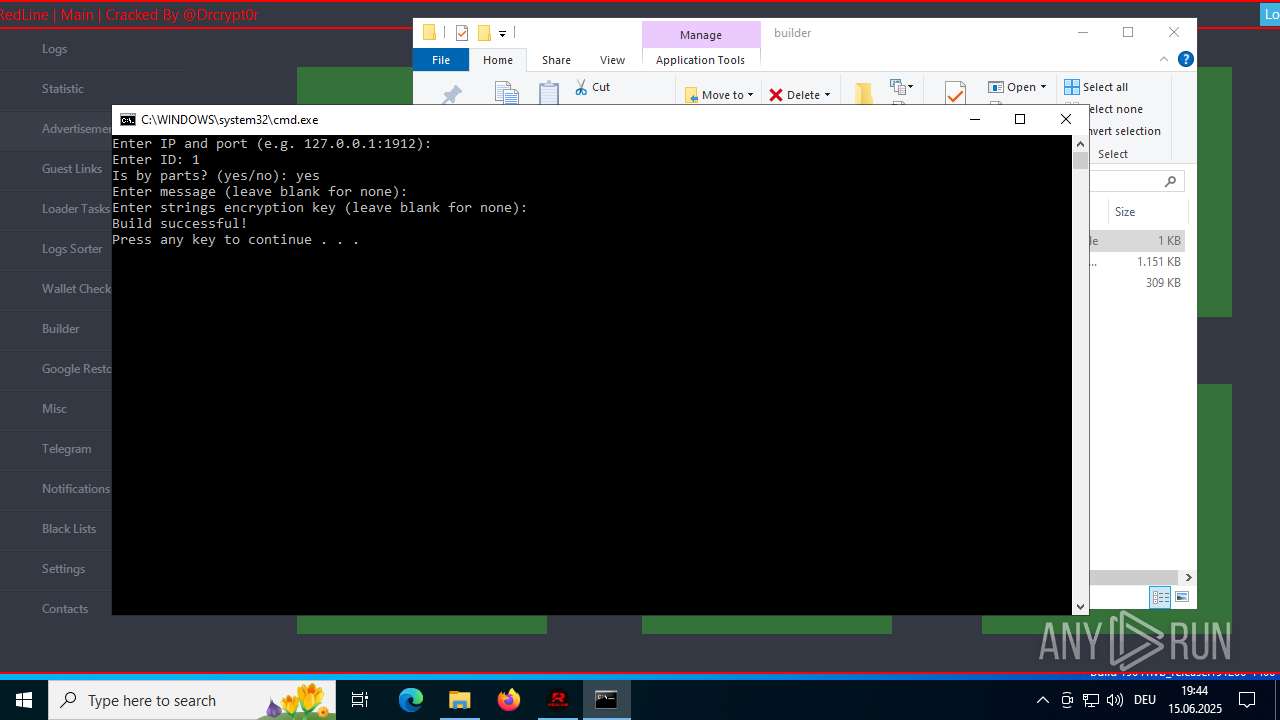
Manual execution by a user
- WinRAR.exe (PID: 3672)
- cmd.exe (PID: 2760)
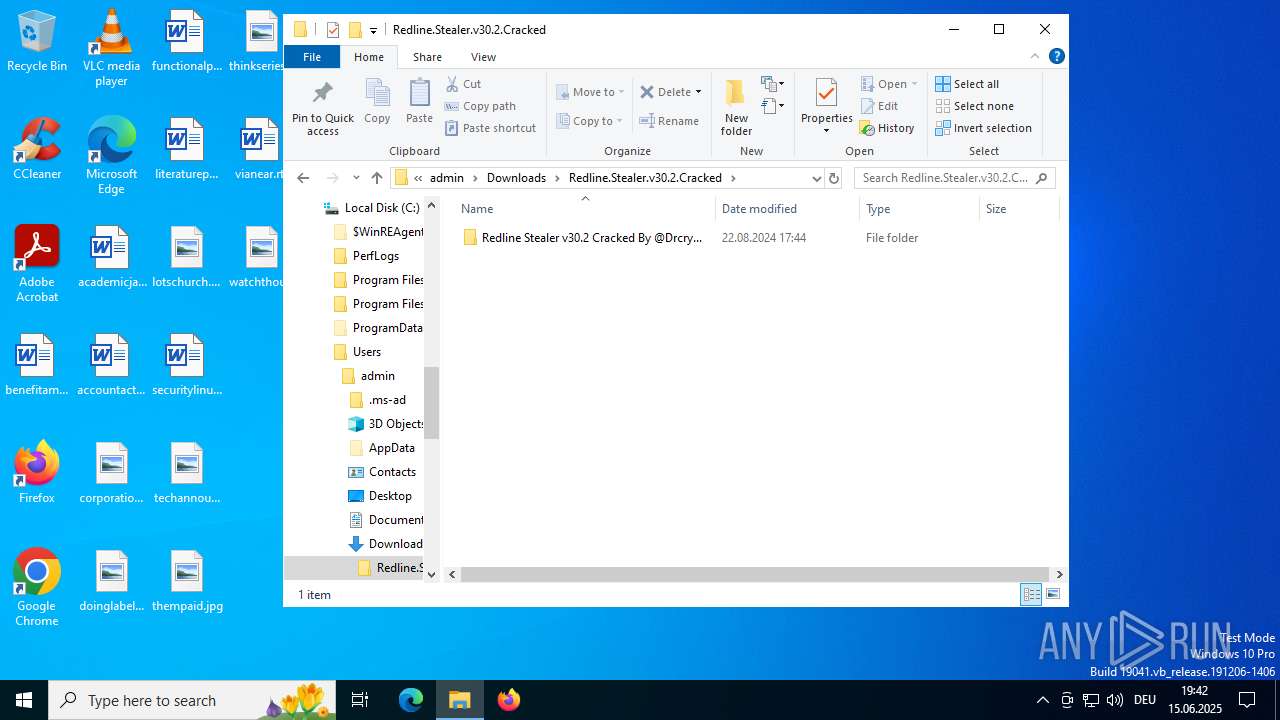
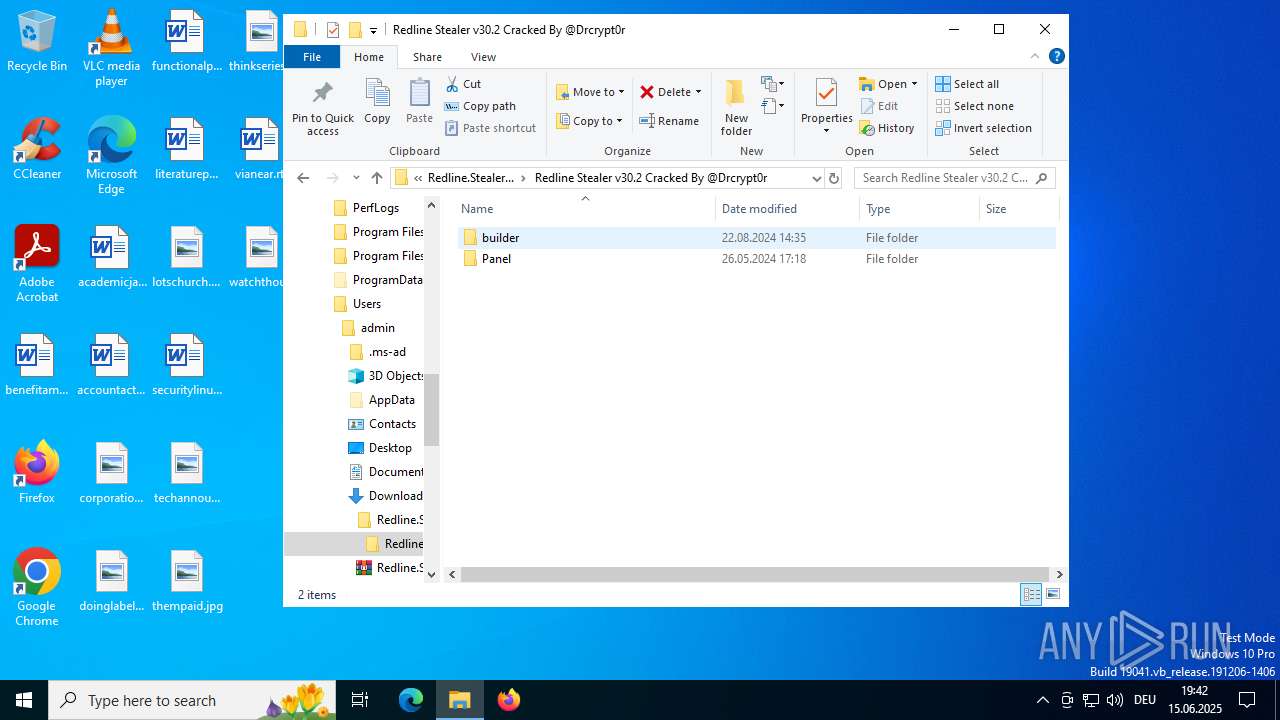
- RedlineBuilder.exe (PID: 1576)
- Panel.exe (PID: 6380)
- cmd.exe (PID: 360)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3672)
Checks proxy server information
- slui.exe (PID: 3936)
- Panel.exe (PID: 1604)
Reads the computer name
- RedlineBuilder.exe (PID: 1576)
- RedlineBuilder.exe (PID: 5012)
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
- ShellExperienceHost.exe (PID: 436)
Reads the machine GUID from the registry
- RedlineBuilder.exe (PID: 5012)
- RedlineBuilder.exe (PID: 1576)
- Panel.exe (PID: 1604)
Disables trace logs
- Panel.exe (PID: 1604)
Creates files or folders in the user directory
- Panel.exe (PID: 1604)
Reads Environment values
- Panel.exe (PID: 1604)
Confuser has been detected (YARA)
- Panel.exe (PID: 6380)
- Panel.exe (PID: 1604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
37
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
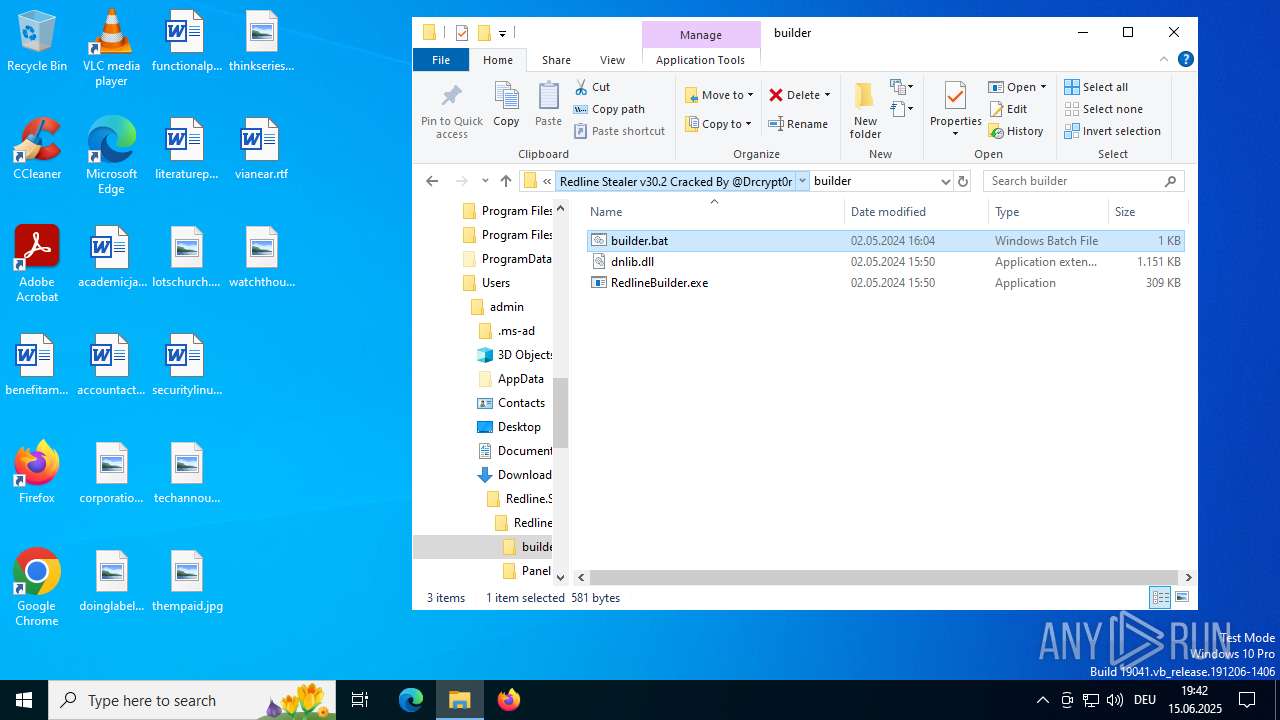
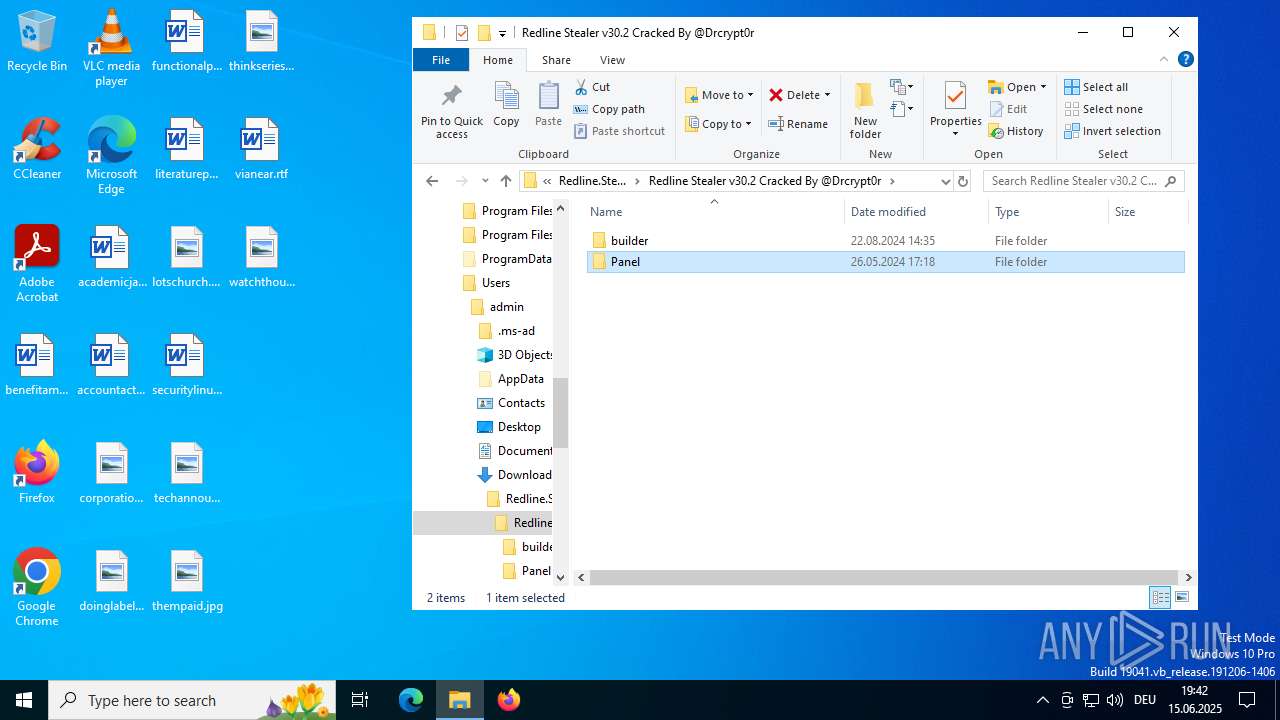
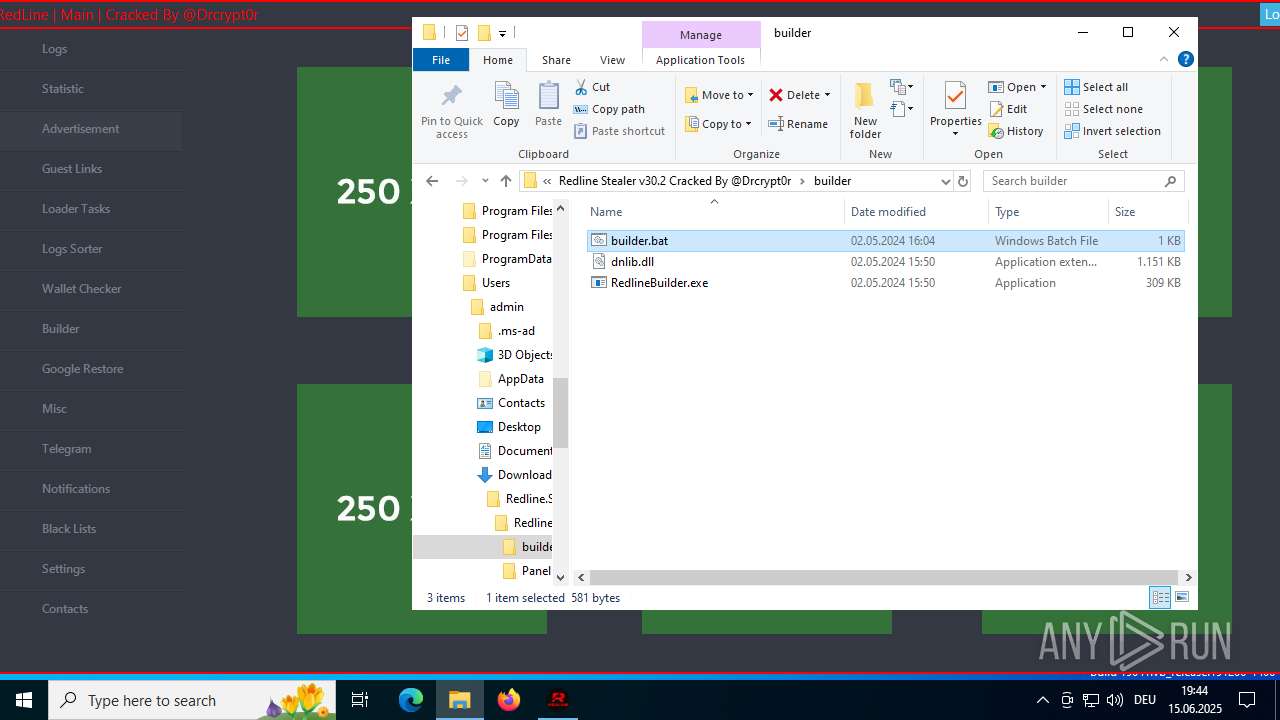
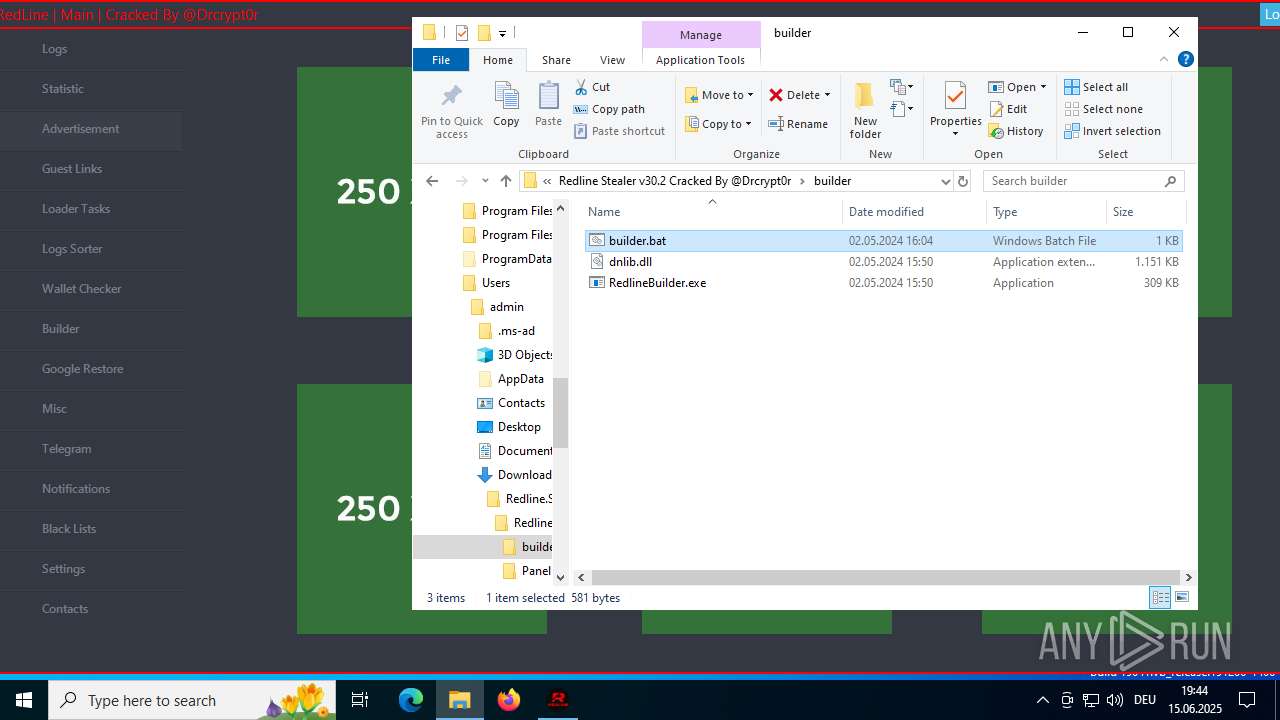
| 360 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Downloads\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\builder\builder.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5540,i,14875652301651836620,2794172887365154018,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=5560 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 436 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=4888,i,14875652301651836620,2794172887365154018,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4904 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgABAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1900,i,14875652301651836620,2794172887365154018,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1880 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2144,i,14875652301651836620,2794172887365154018,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2156 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
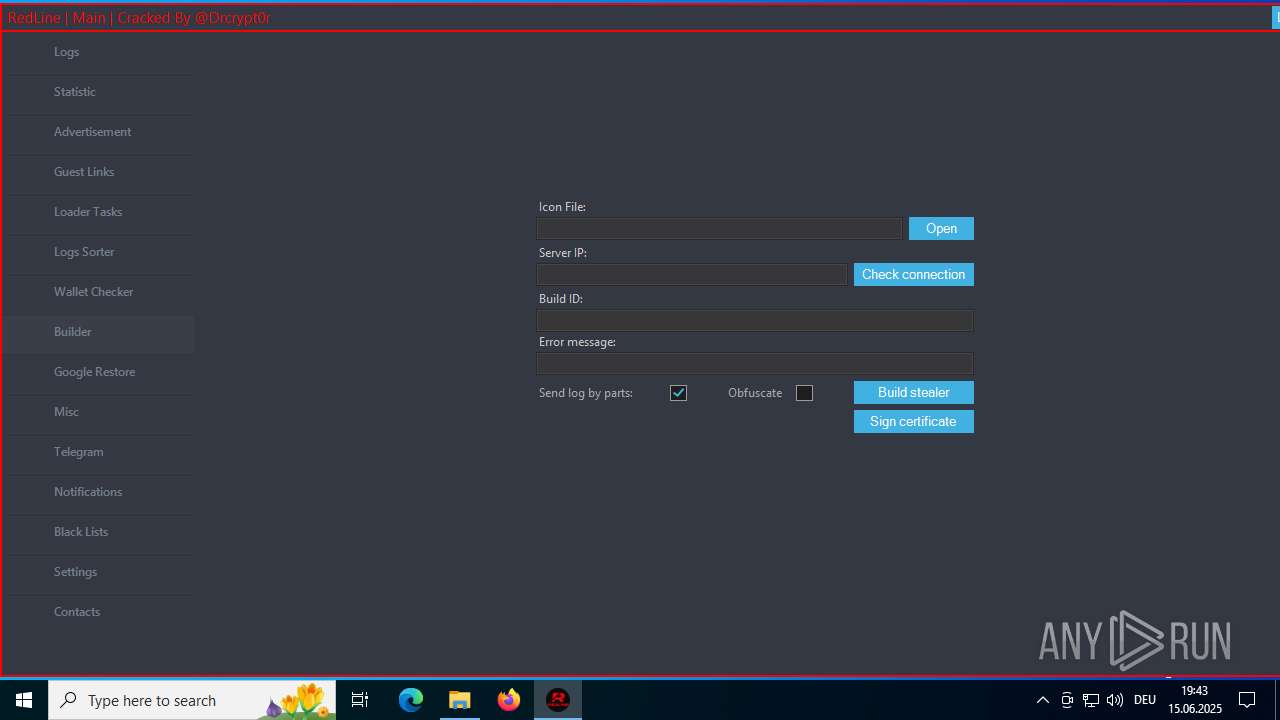
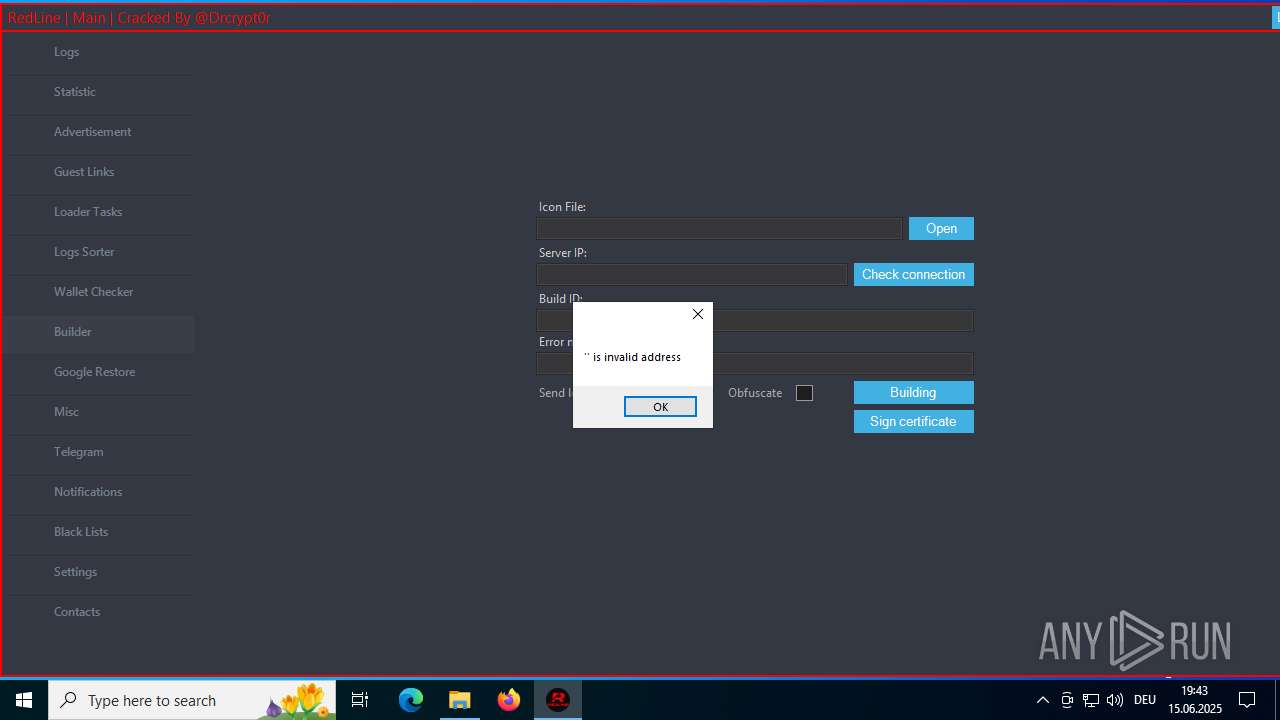
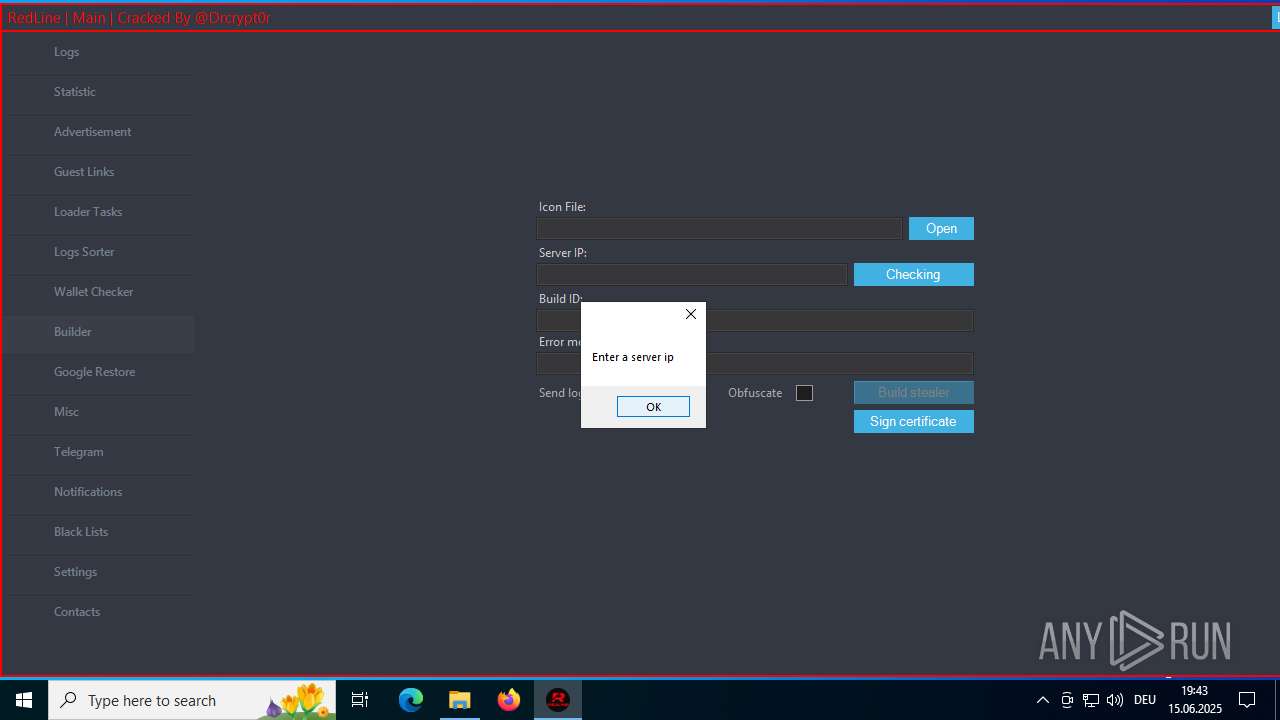
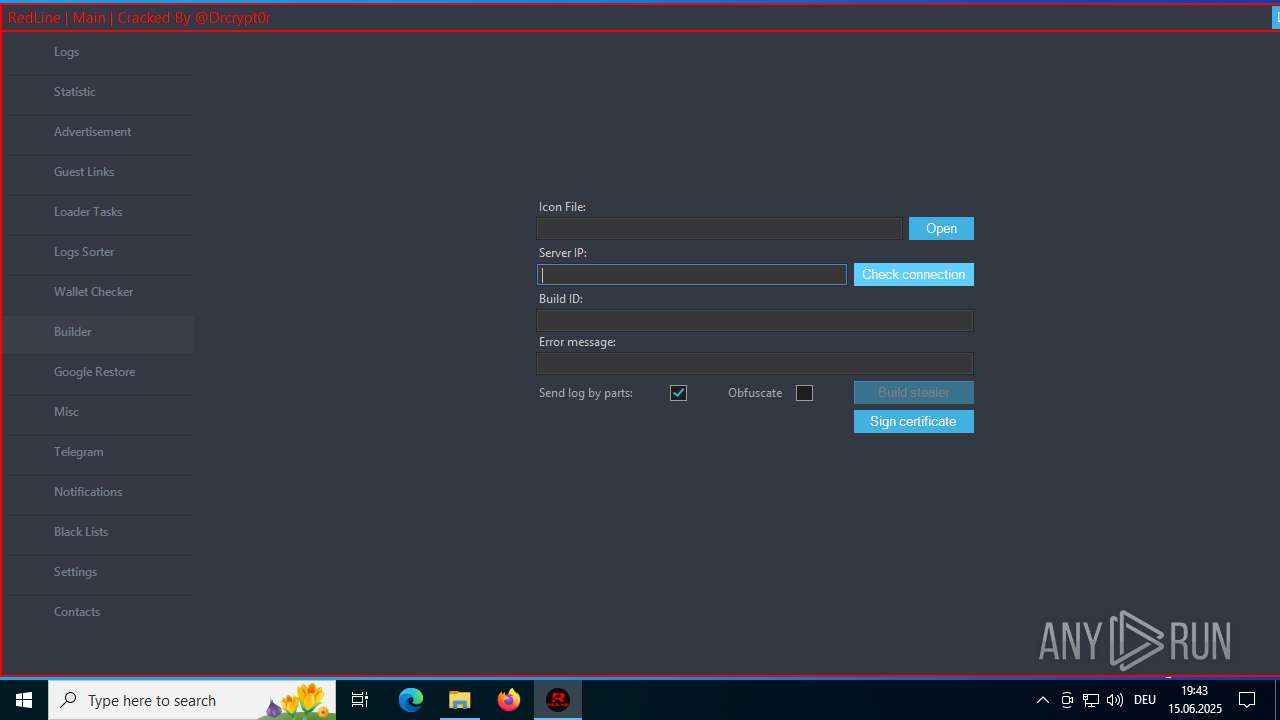
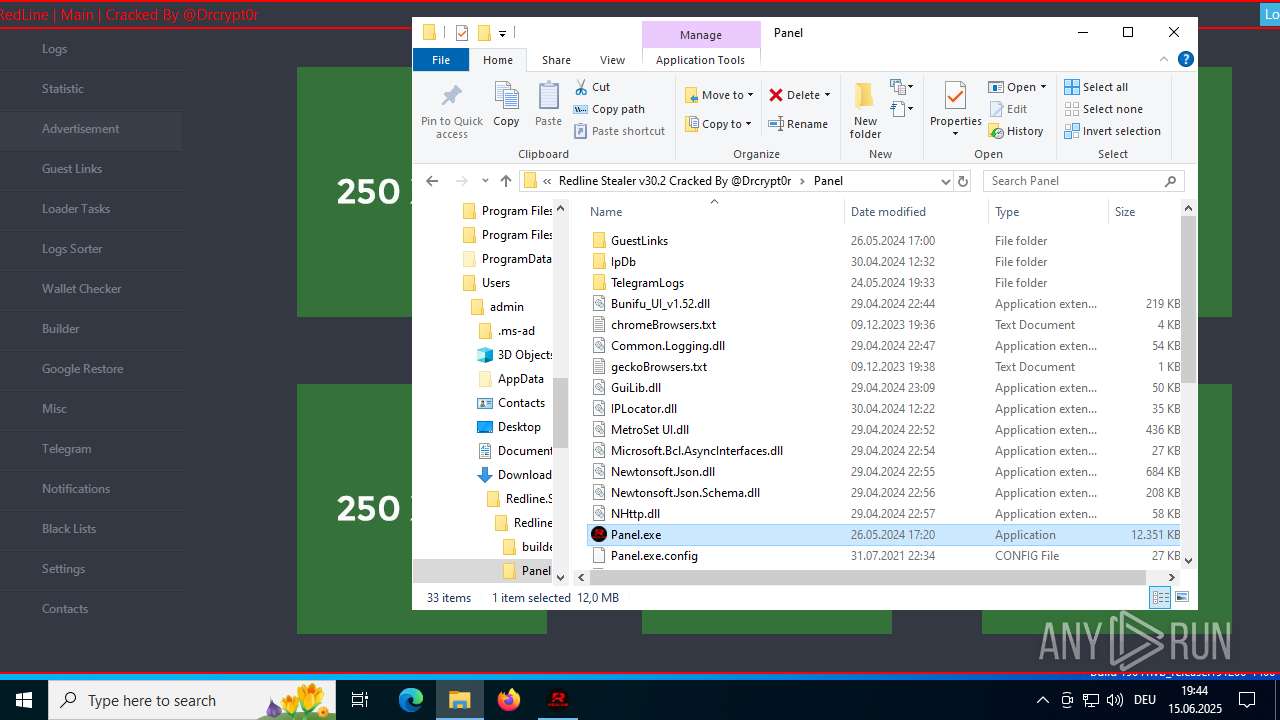
| 1576 | "C:\Users\admin\Downloads\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\builder\RedlineBuilder.exe" | C:\Users\admin\Downloads\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\builder\RedlineBuilder.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: RedlineBuilder Exit code: 4294967295 Version: 1.0.0.0 Modules
| |||||||||||||||
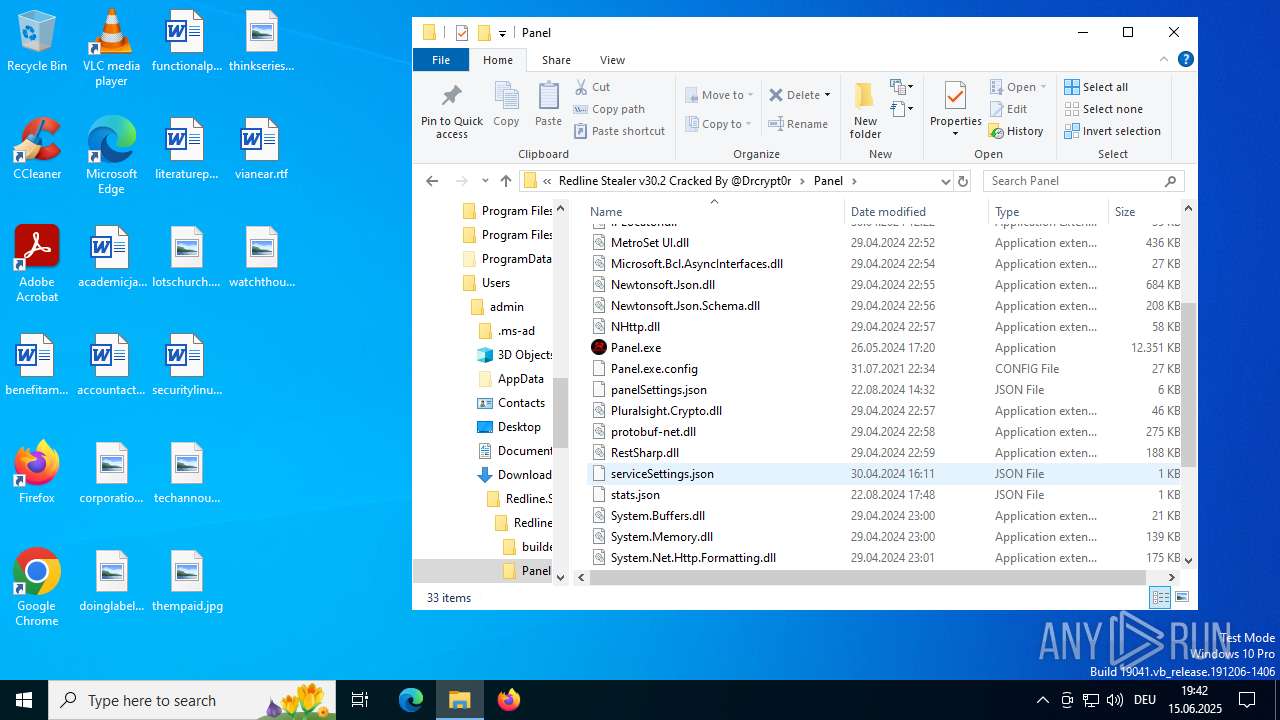
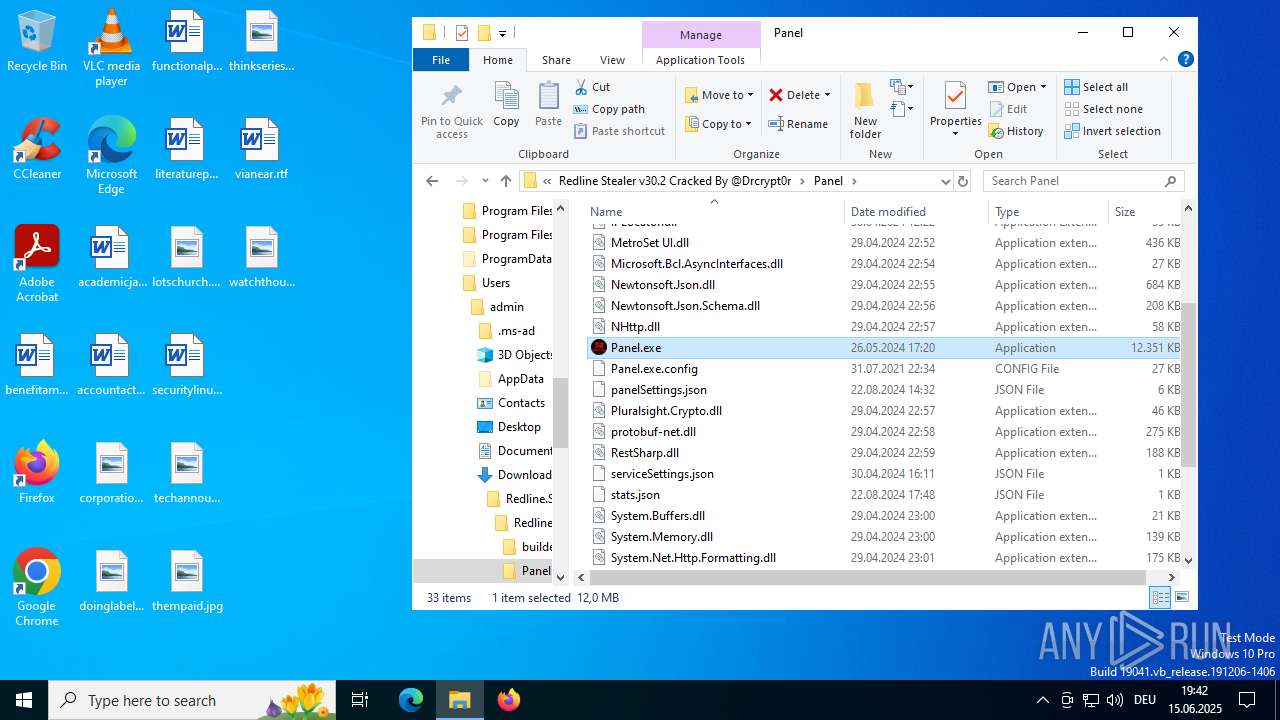
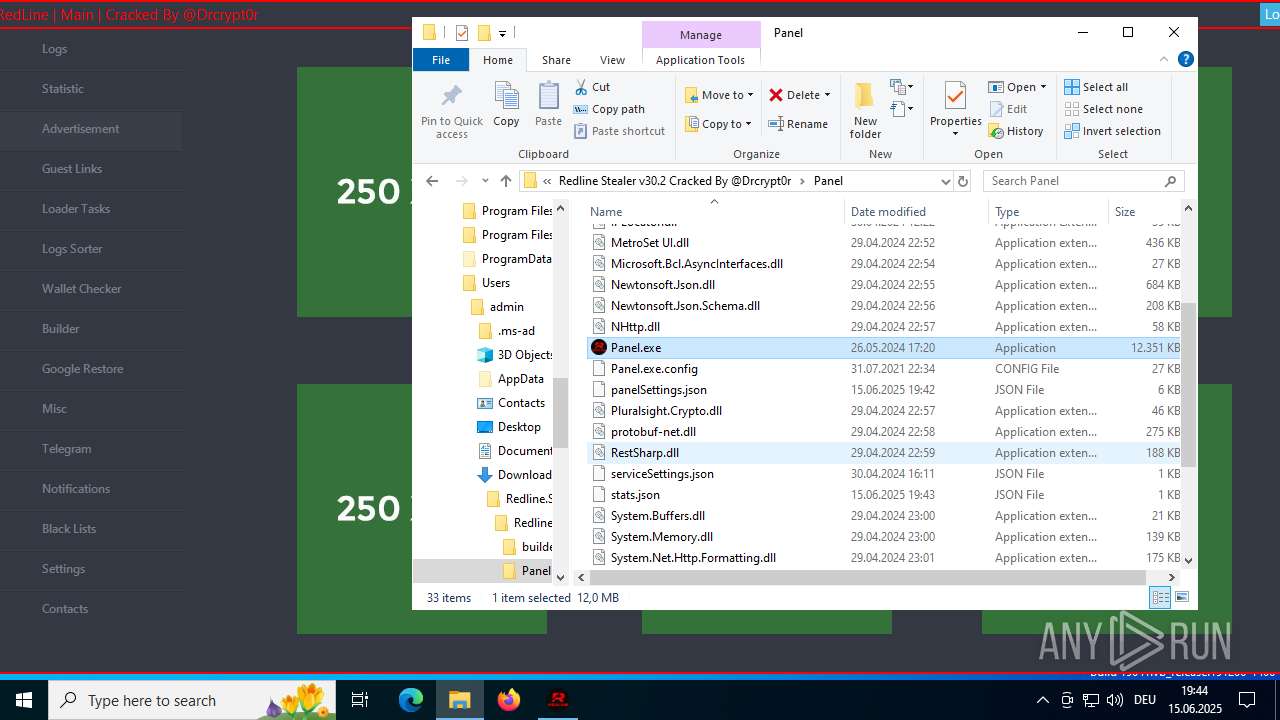
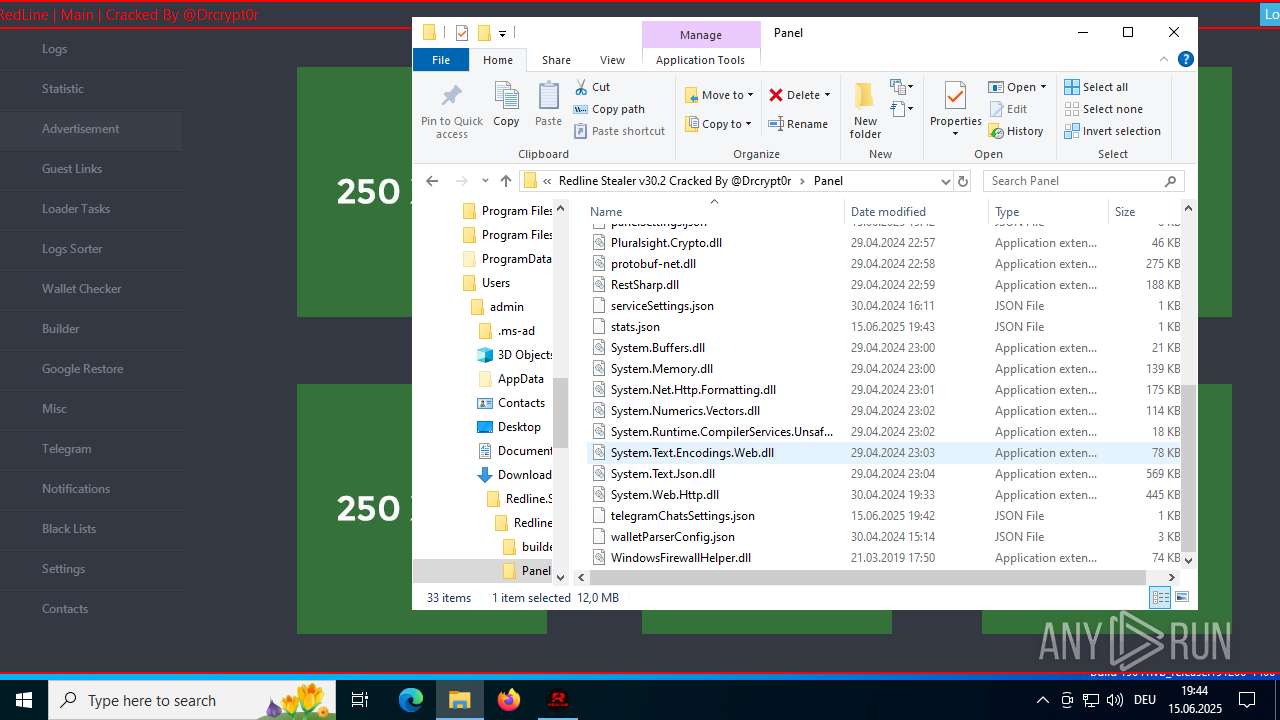
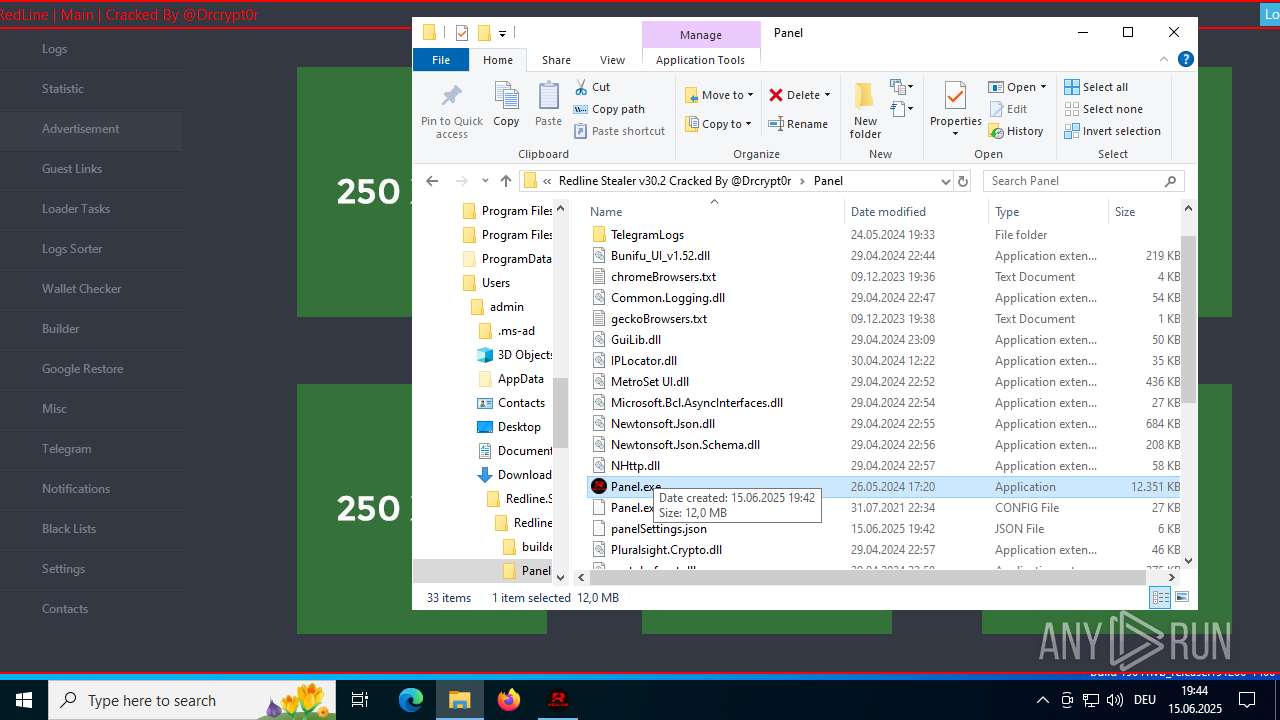
| 1604 | "C:\Users\admin\Downloads\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\Panel\Panel.exe" "--monitor" | C:\Users\admin\Downloads\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\Panel\Panel.exe | Panel.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --field-trial-handle=3064,i,14875652301651836620,2794172887365154018,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x224,0x228,0x22c,0x200,0x230,0x7ffc4512fff8,0x7ffc45130004,0x7ffc45130010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
17 142
Read events
17 096
Write events
39
Delete events
7
Modification events
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (4520) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
Executable files
33
Suspicious files
340
Text files
50
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF17879e.TMP | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1787be.TMP | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF1787be.TMP | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1787be.TMP | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1787cd.TMP | — | |
MD5:— | SHA256:— | |||
| 4520 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
328
TCP/UDP connections
68
DNS requests
56
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
— | — | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 868 b | whitelisted |
— | — | GET | 200 | 172.217.16.202:443 | https://safebrowsingohttpgateway.googleapis.com/v1/ohttp/hpkekeyconfig?key=AIzaSyA2KlwBX3mkFo30om9LUFYQhpqLoa_BNhE | US | binary | 41 b | whitelisted |
— | — | POST | 200 | 66.102.1.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | US | text | 17 b | whitelisted |
— | — | GET | 200 | 140.82.121.4:443 | https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/tag/RedlineStealer | US | html | 184 Kb | whitelisted |
— | — | GET | 200 | 185.199.111.154:443 | https://github.githubassets.com/assets/light-c59dc71e3a4c.css | NL | text | 74.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.253.202:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
avatars.githubusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
1604 | Panel.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
1604 | Panel.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |