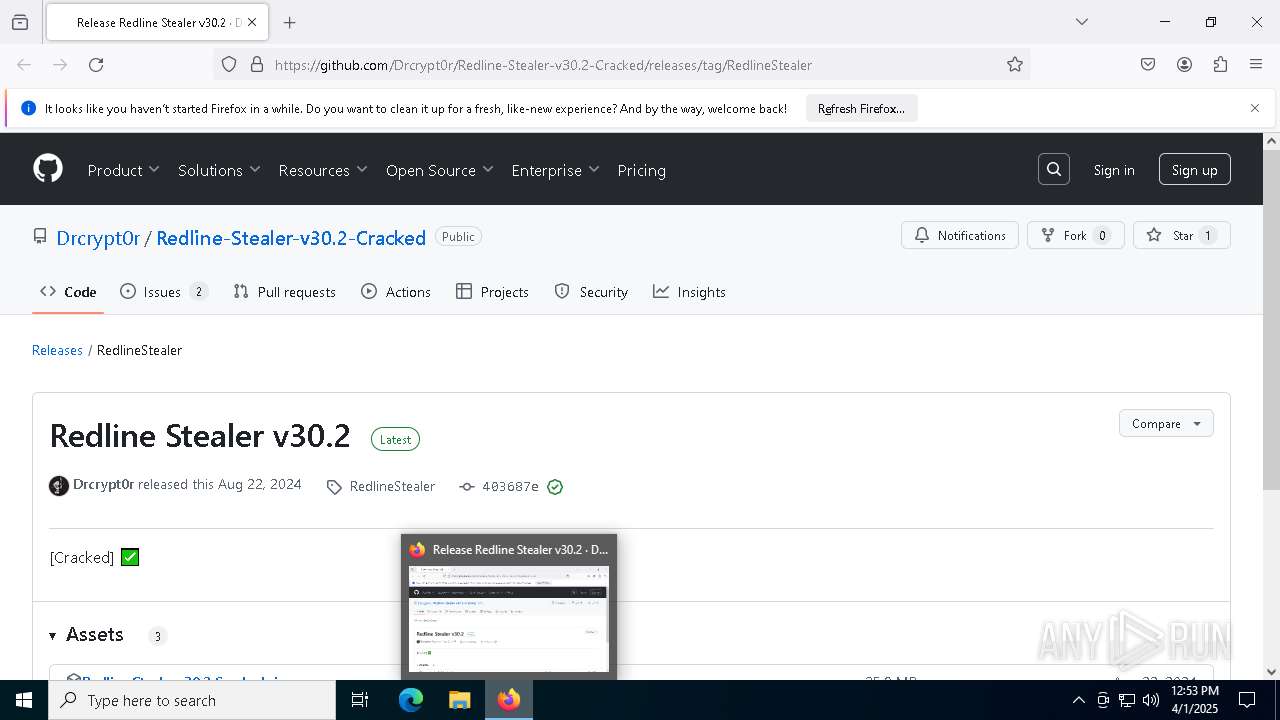
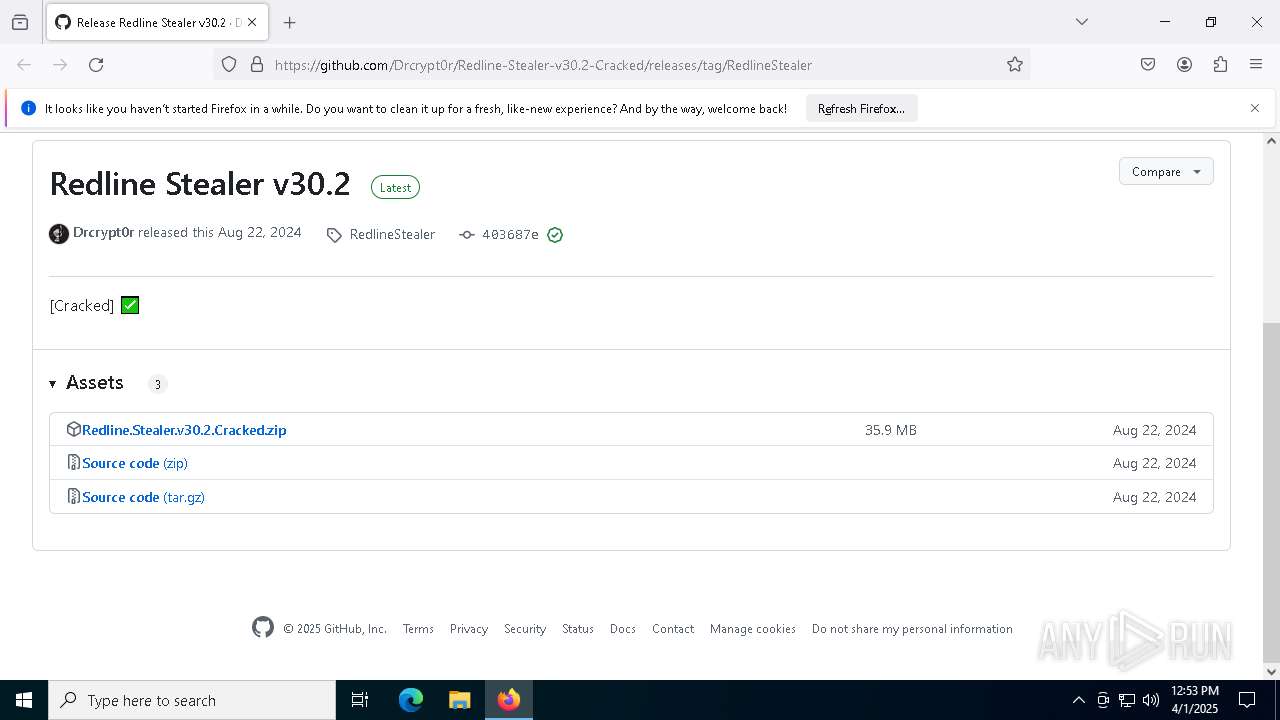
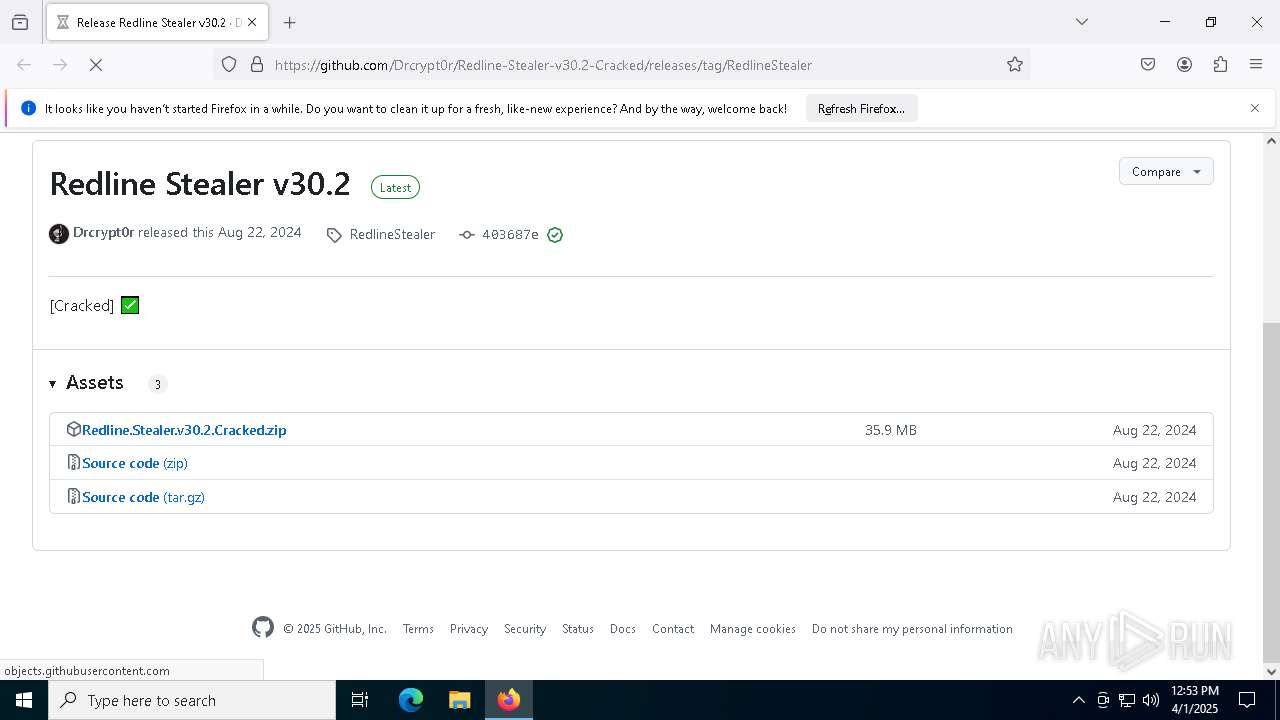
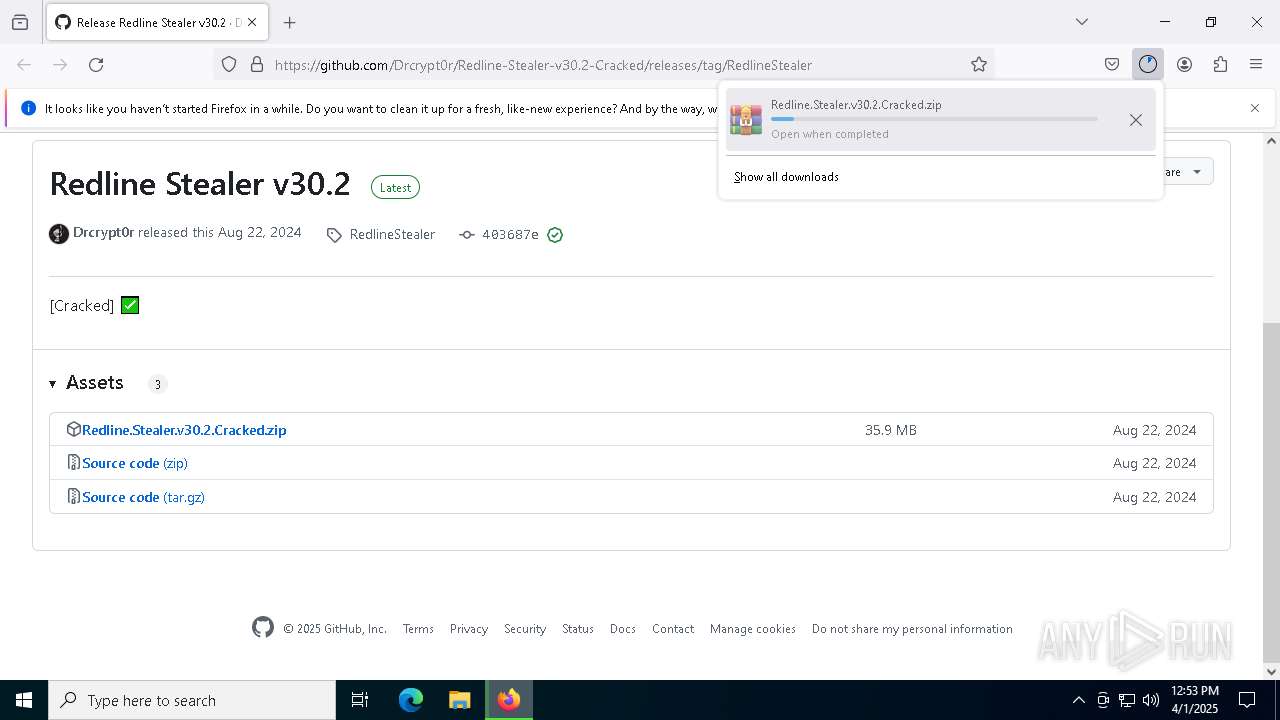
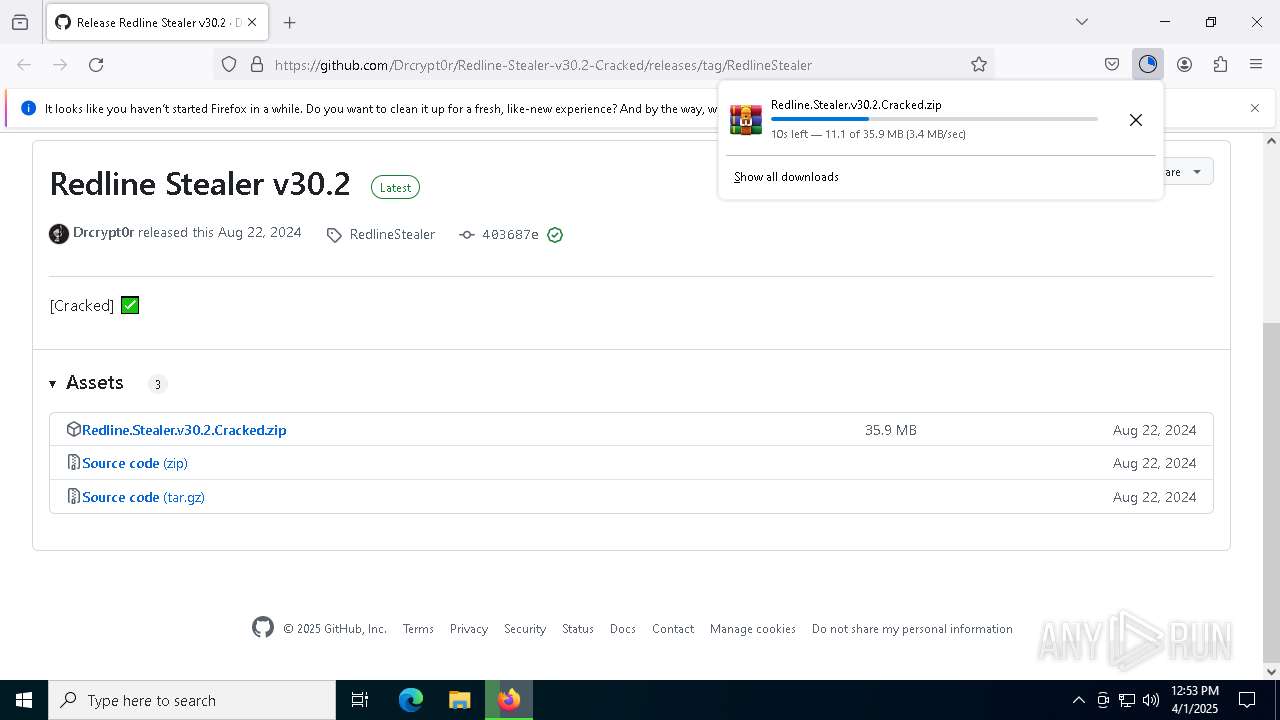
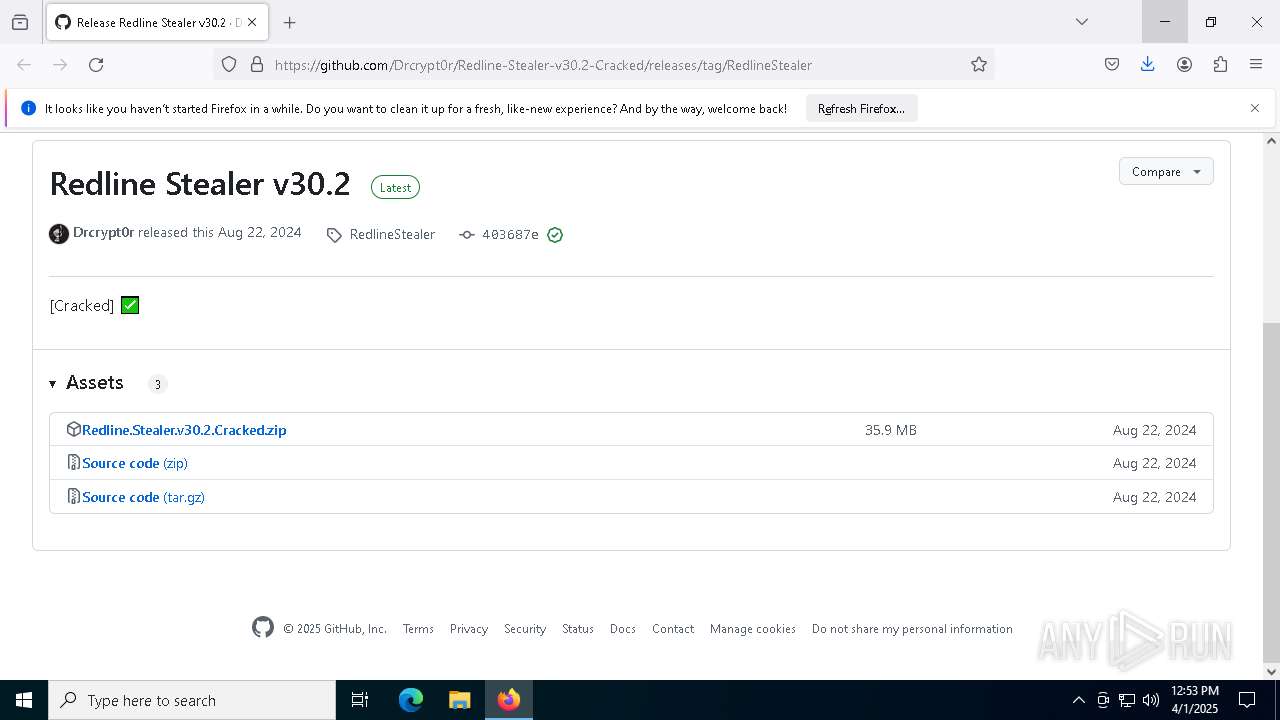
| URL: | https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/tag/RedlineStealer |
| Full analysis: | https://app.any.run/tasks/9ef8691a-0d9c-4a5c-87a9-257130074649 |
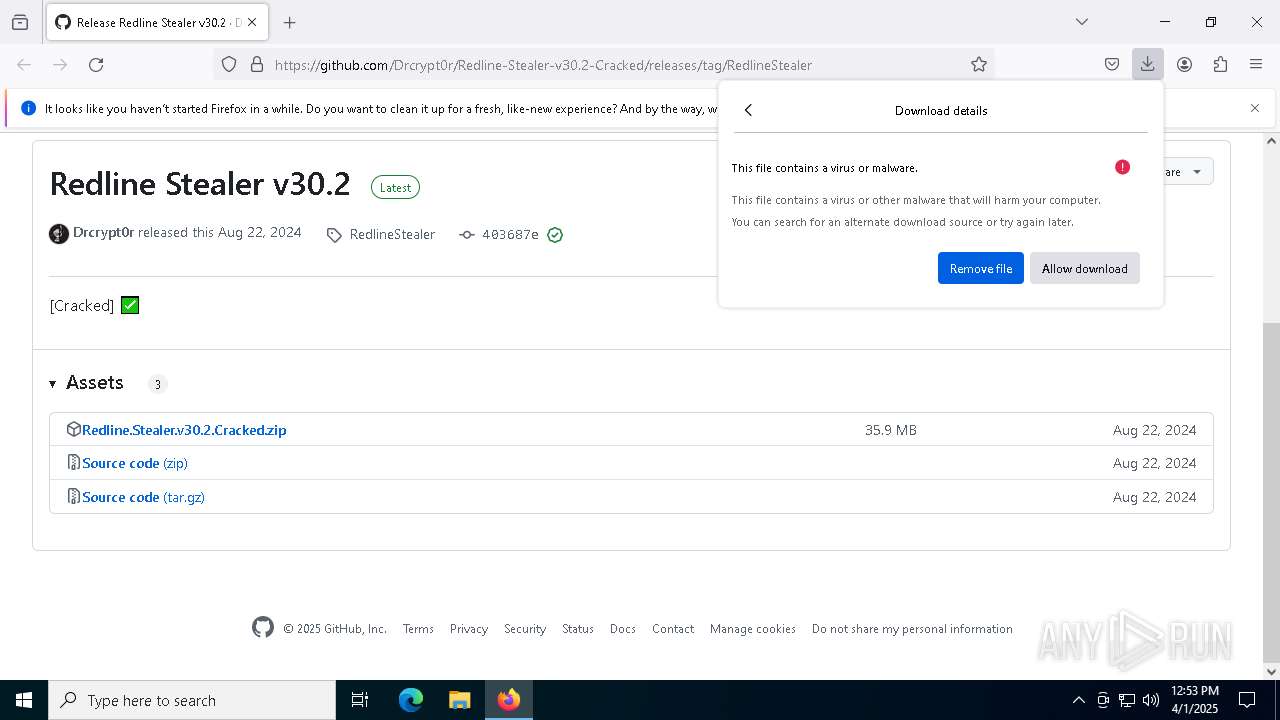
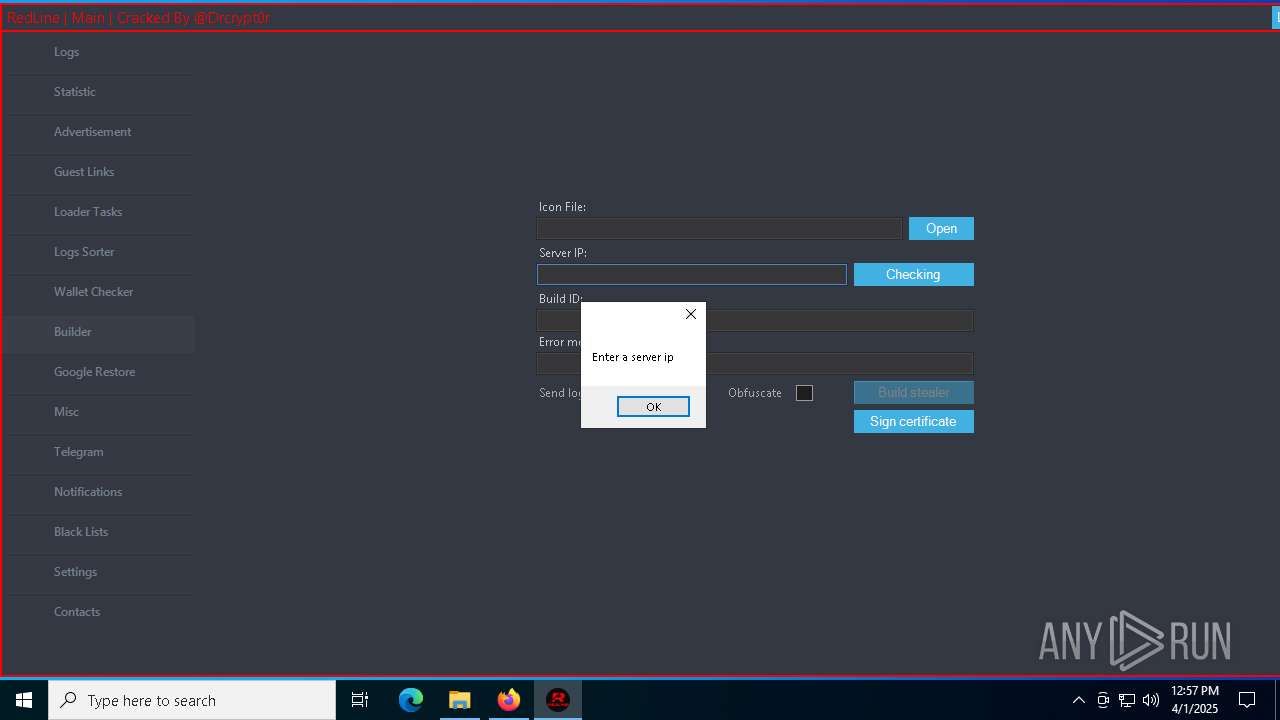
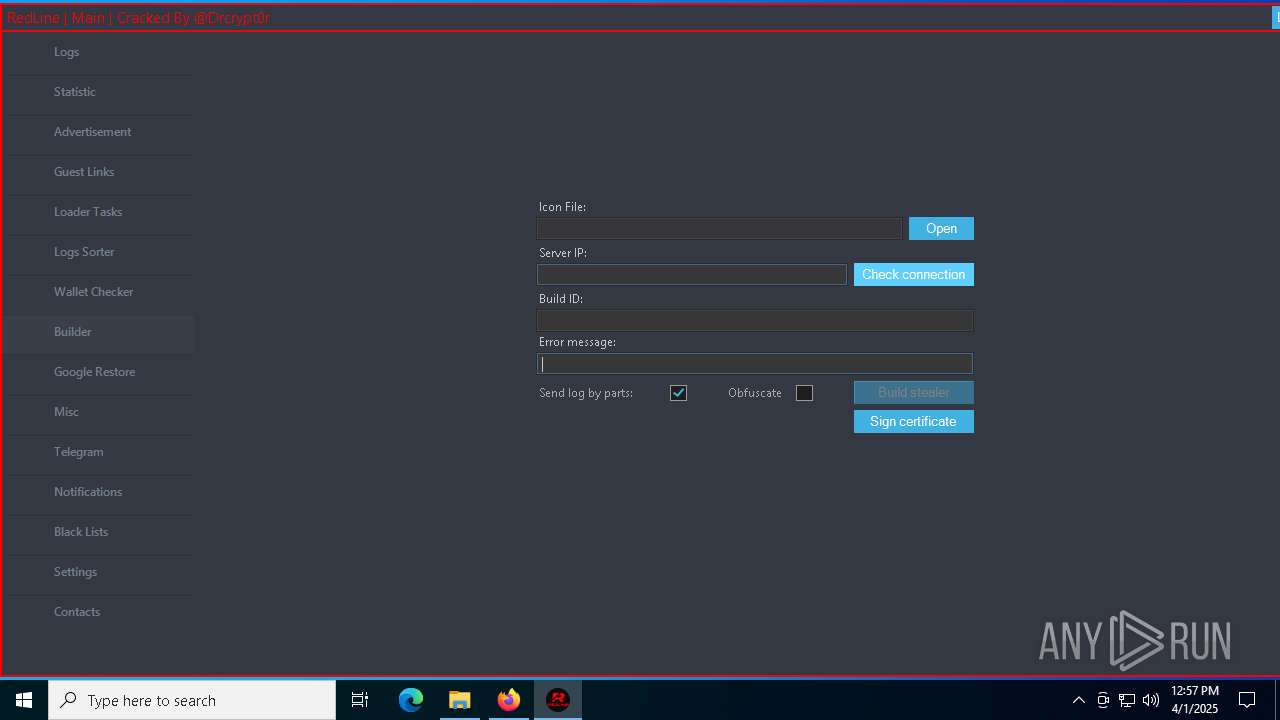
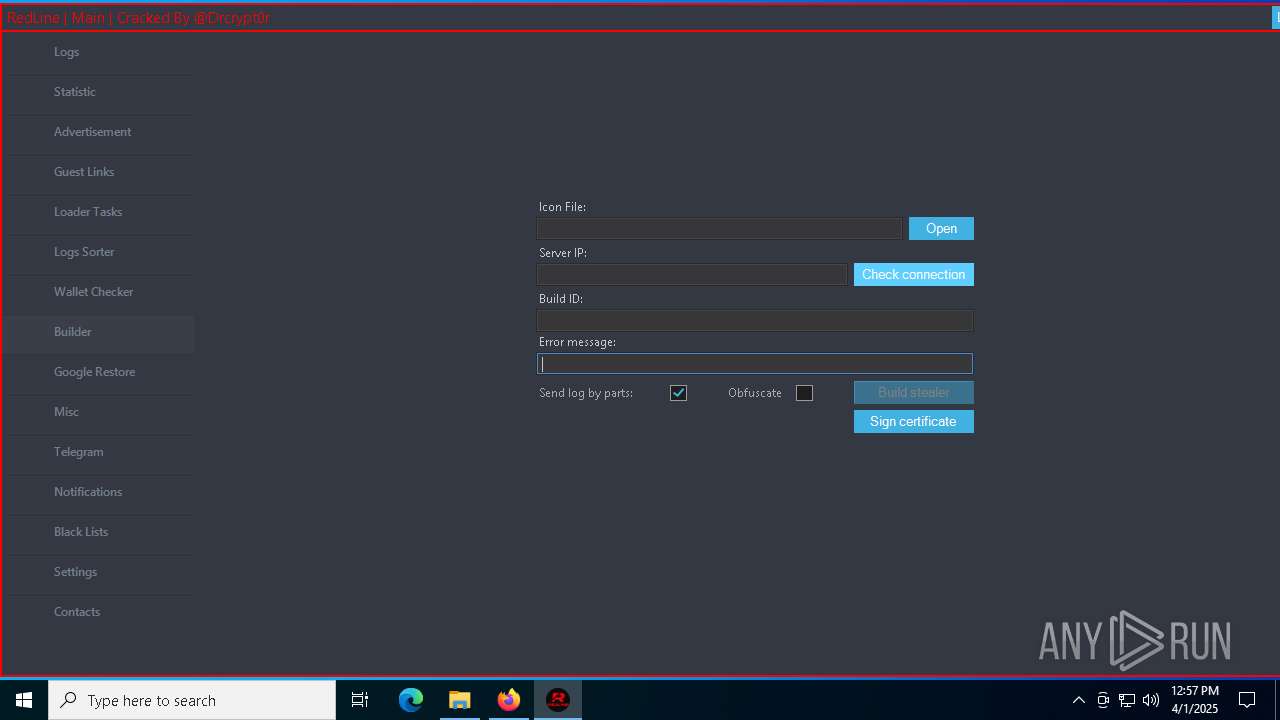
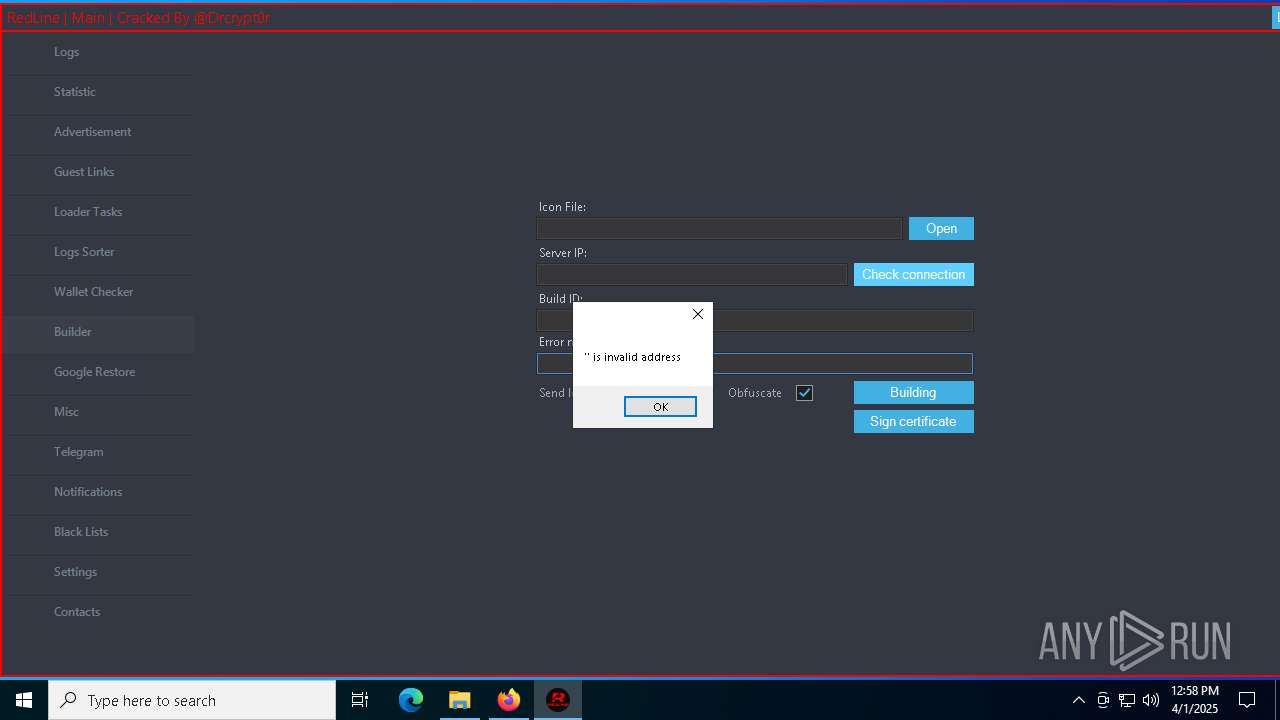
| Verdict: | Malicious activity |
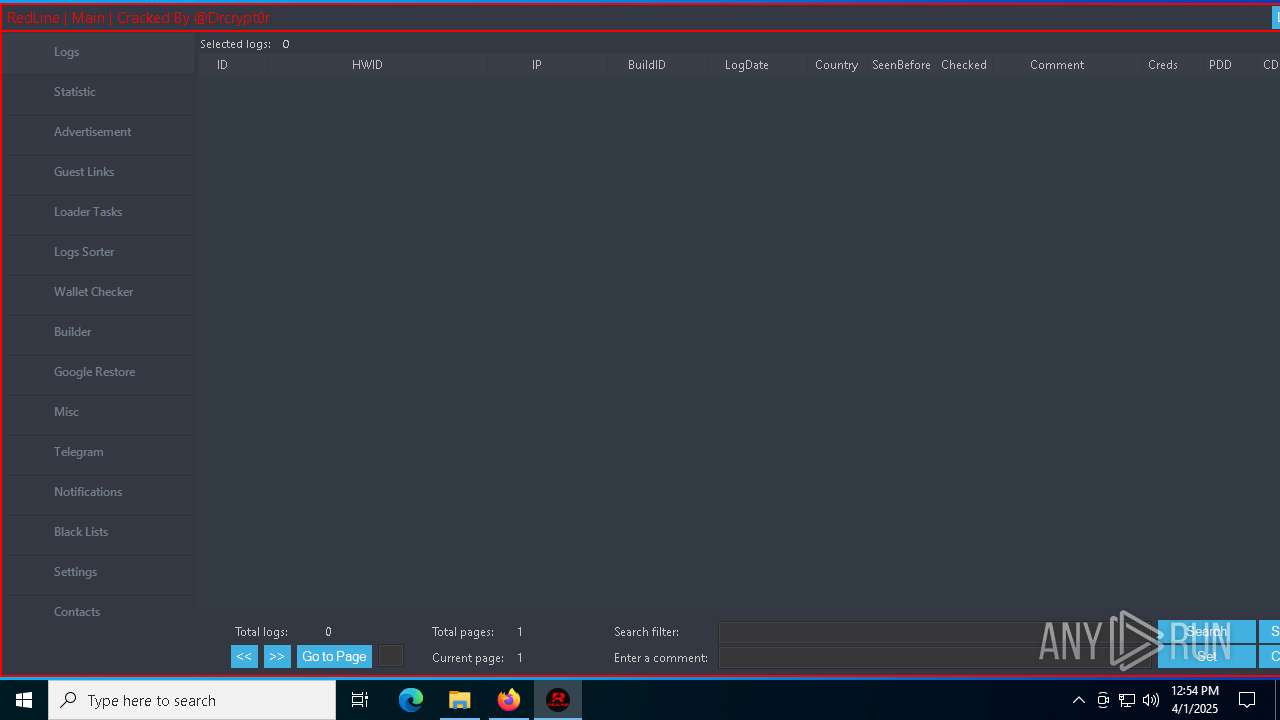
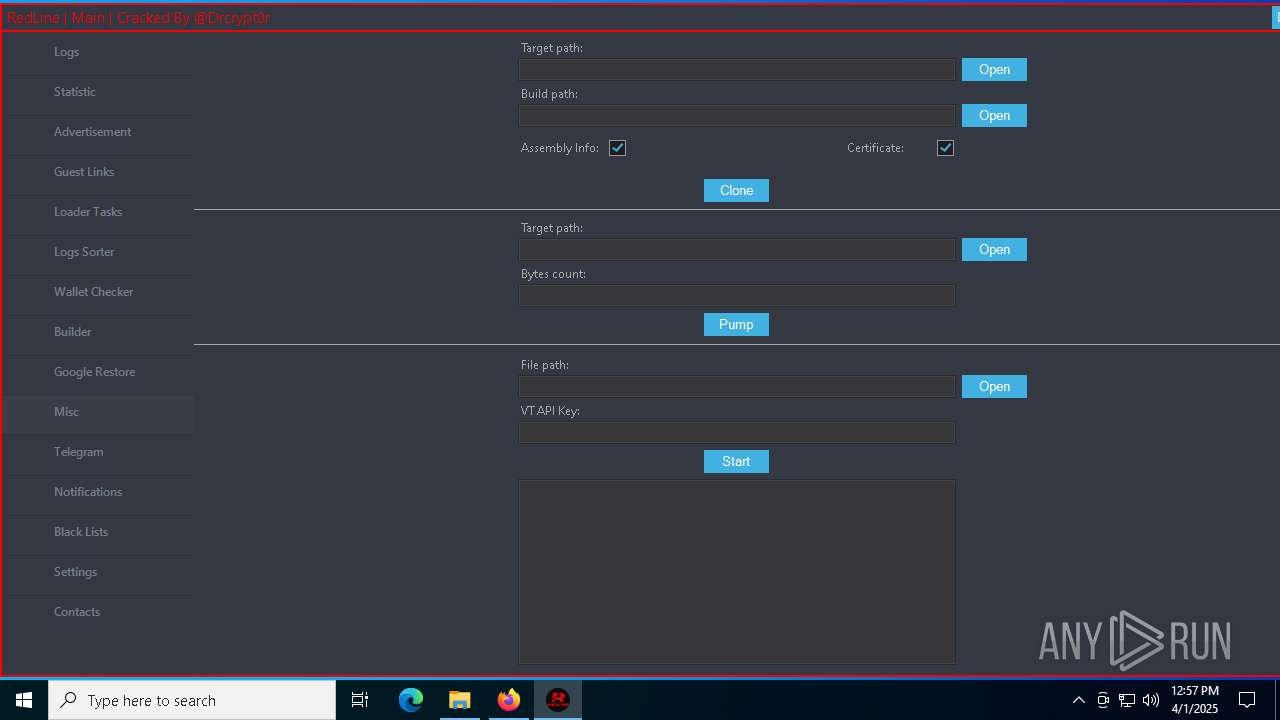
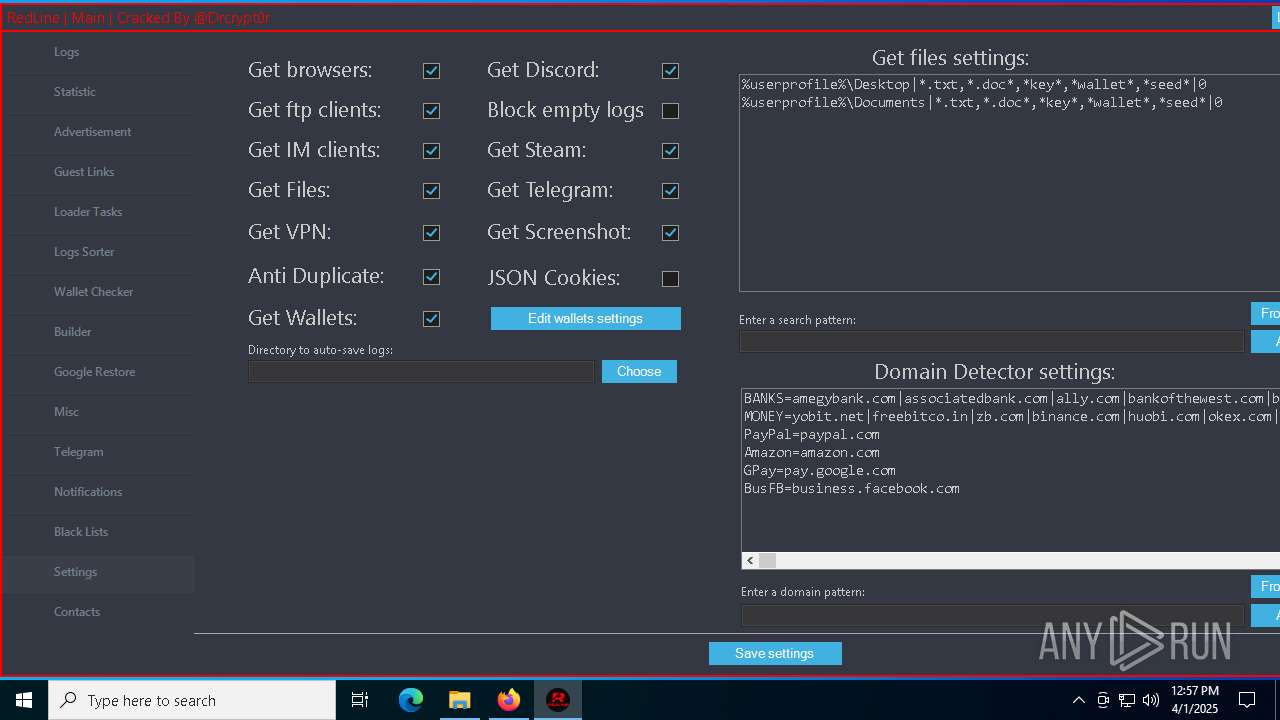
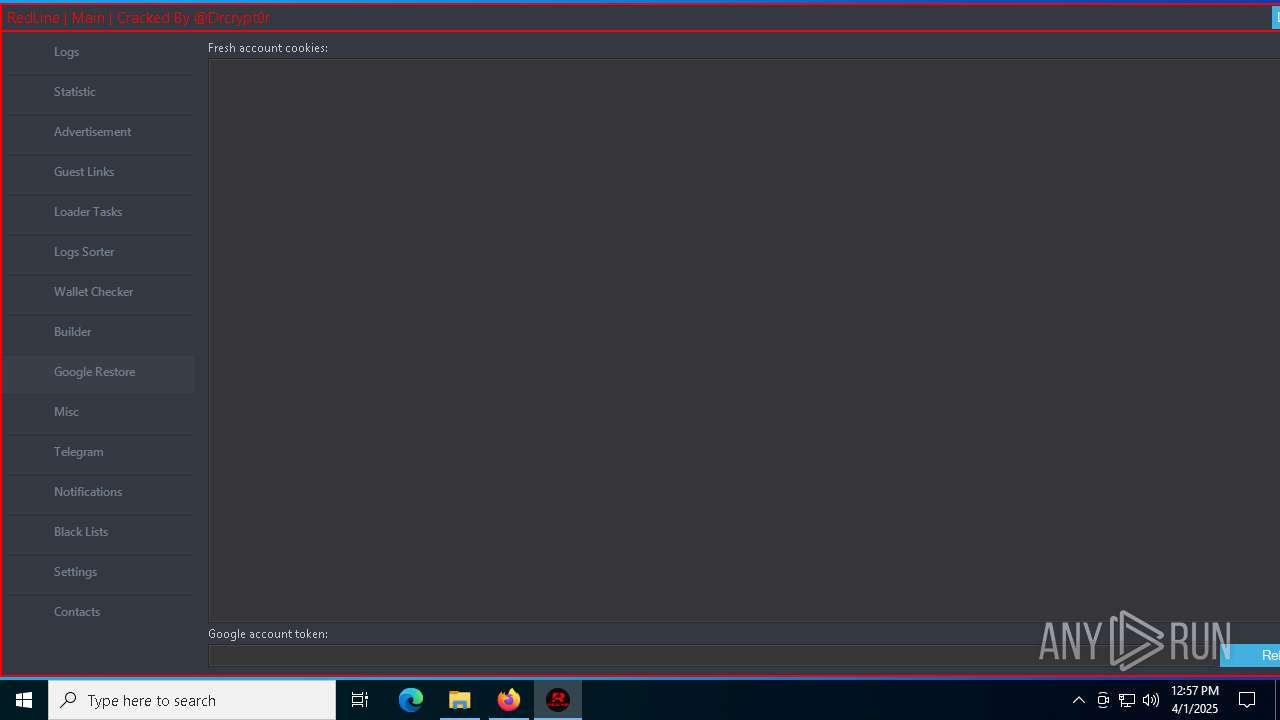
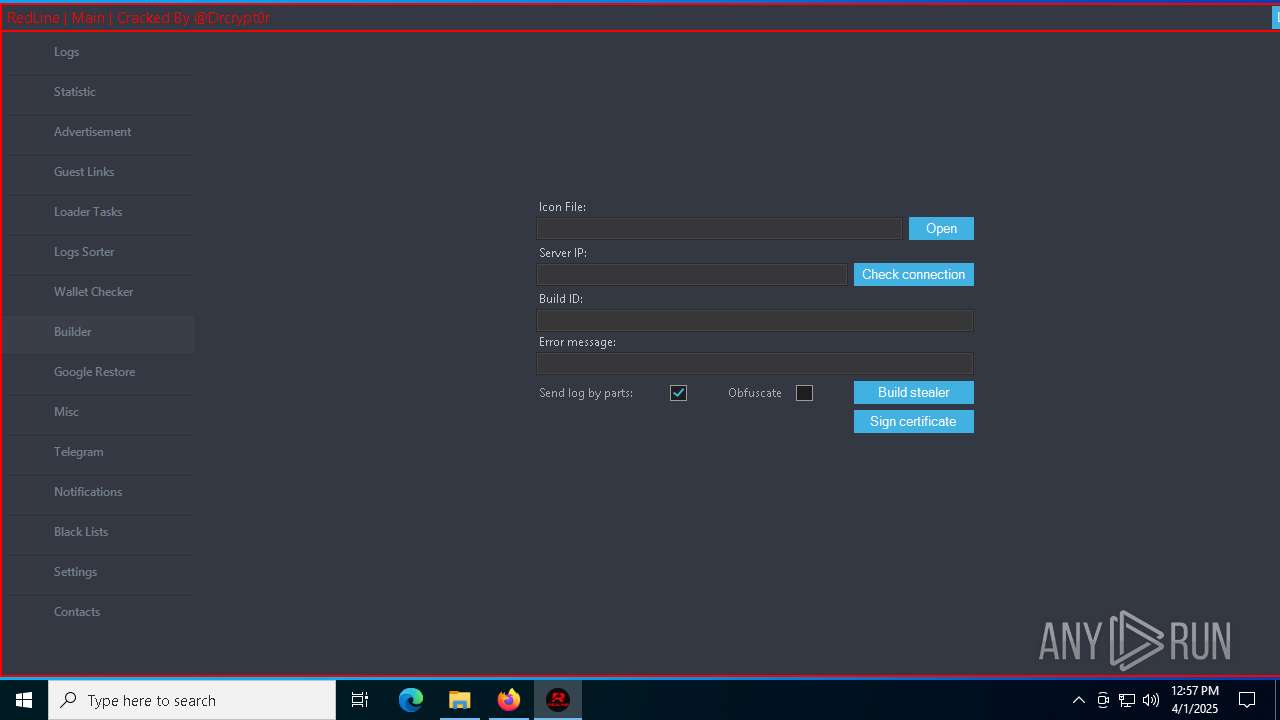
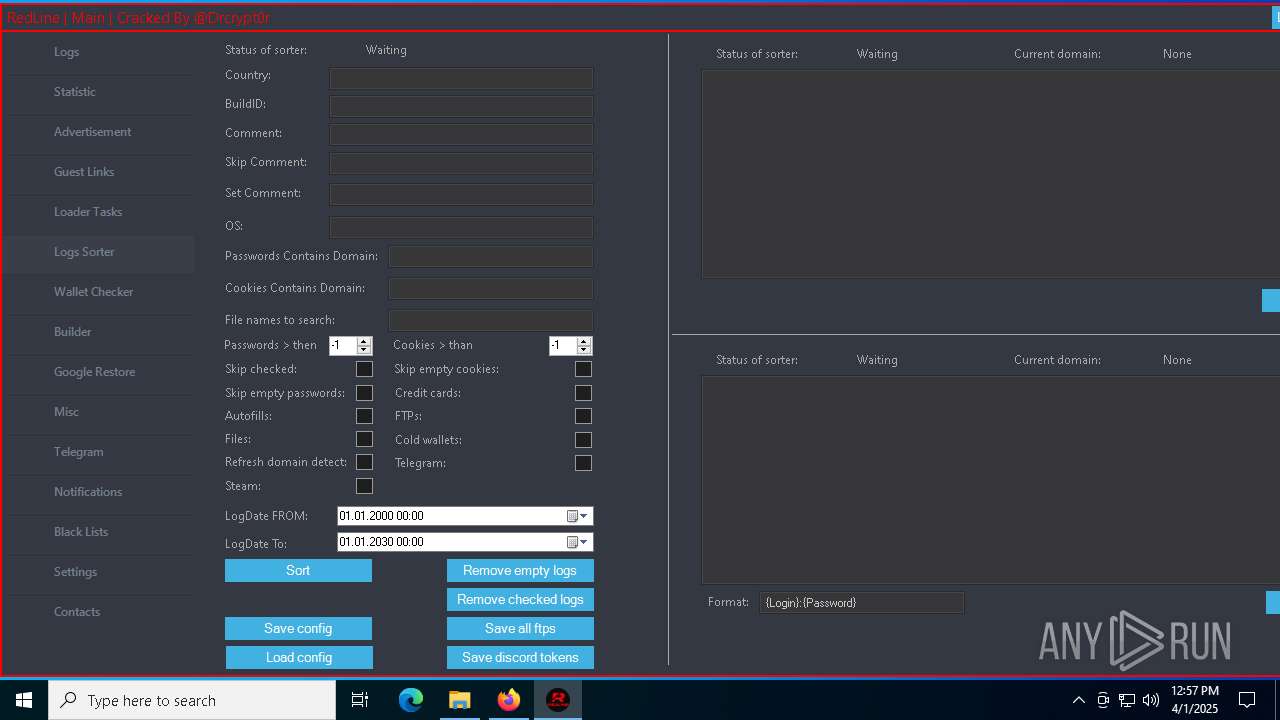
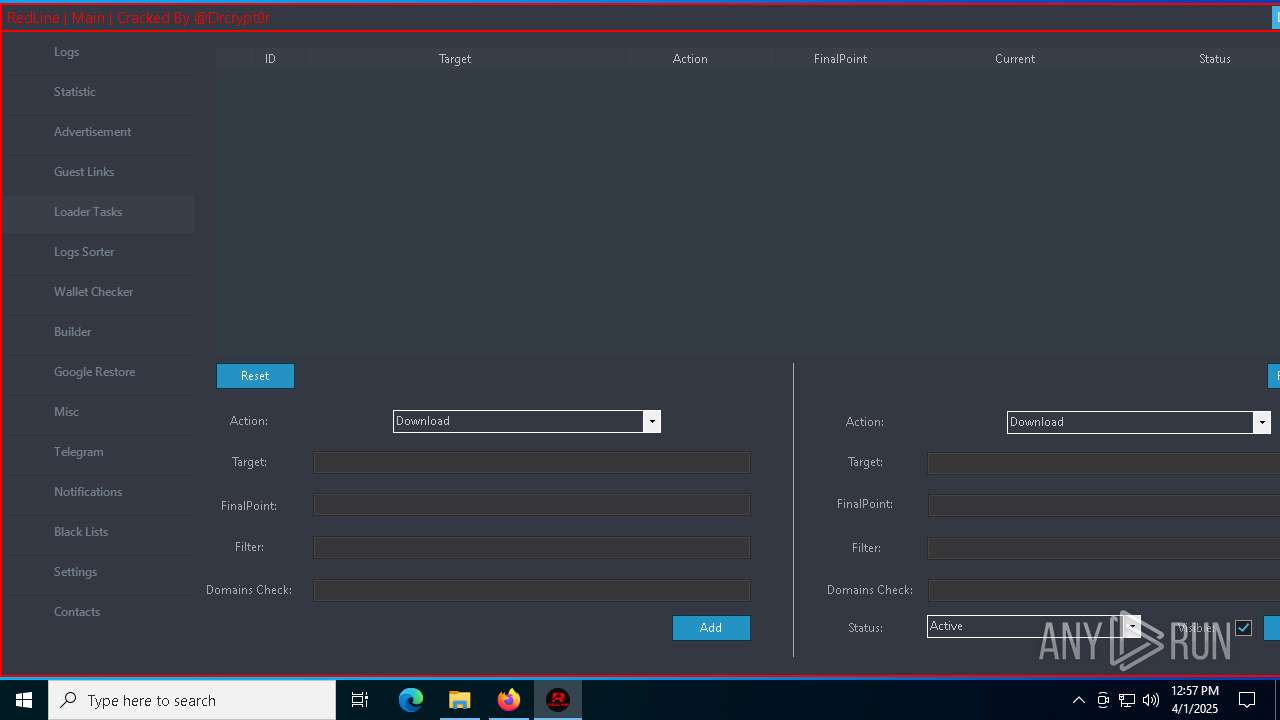
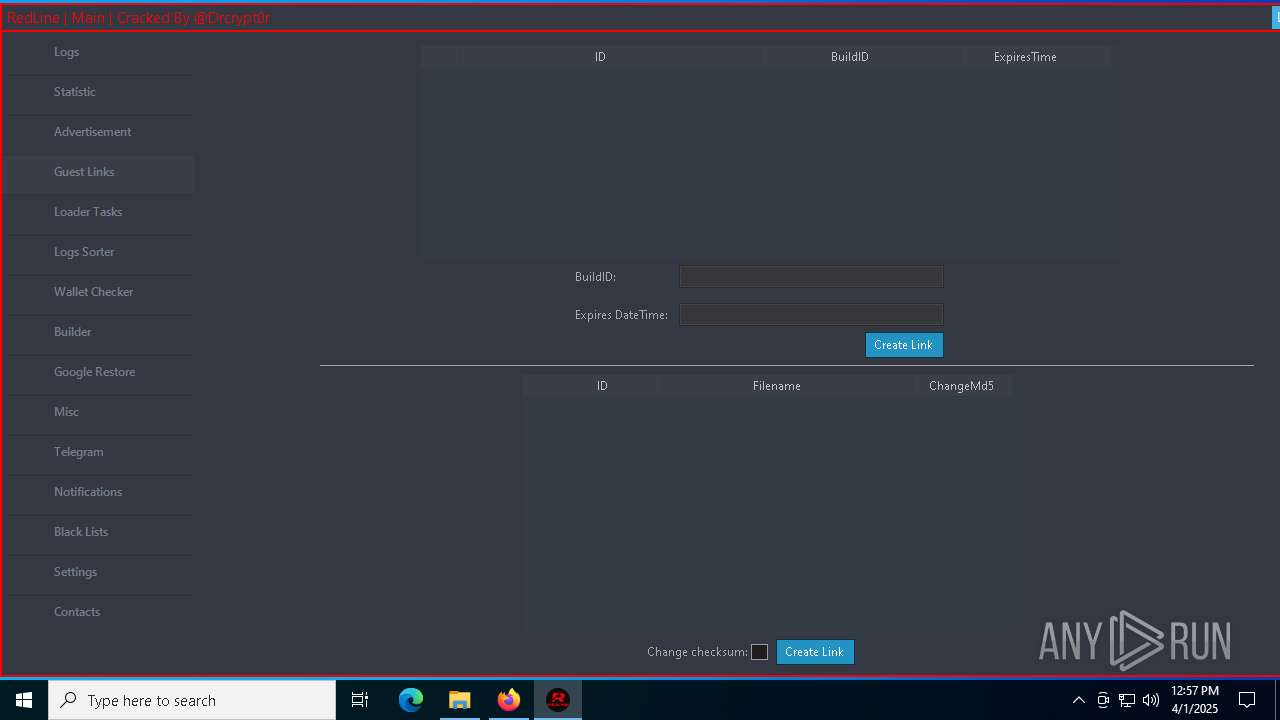
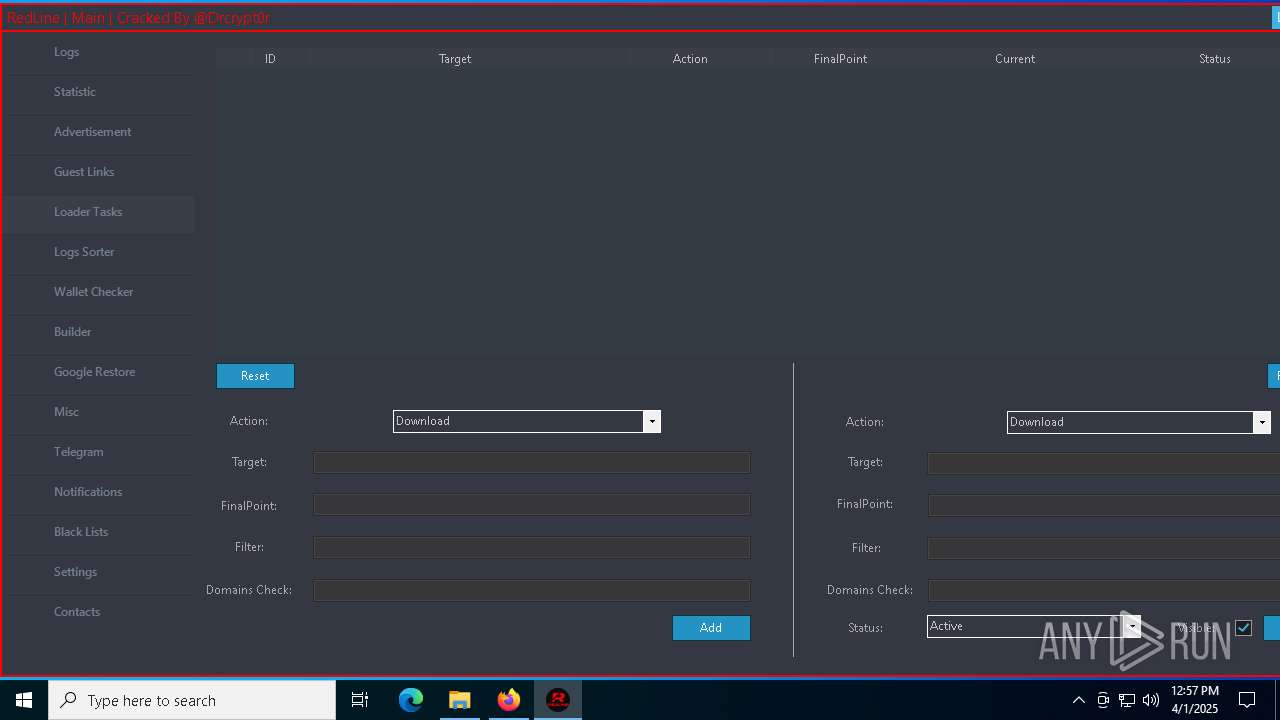
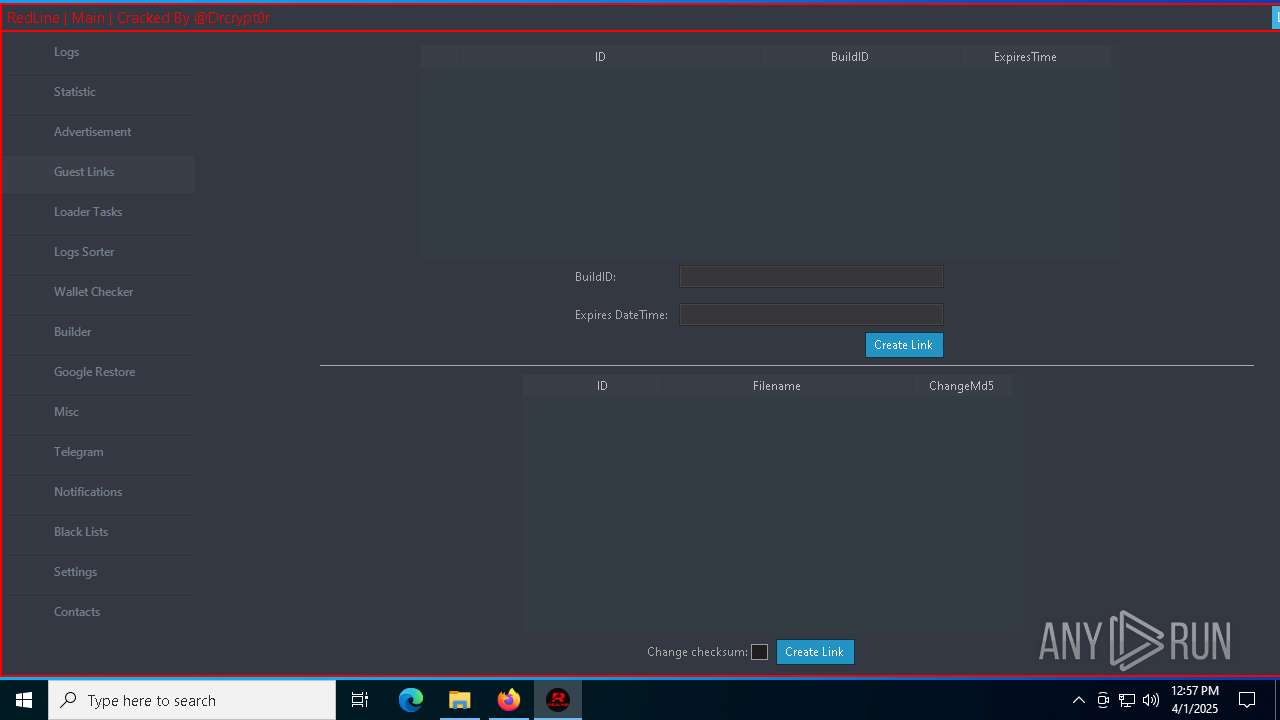
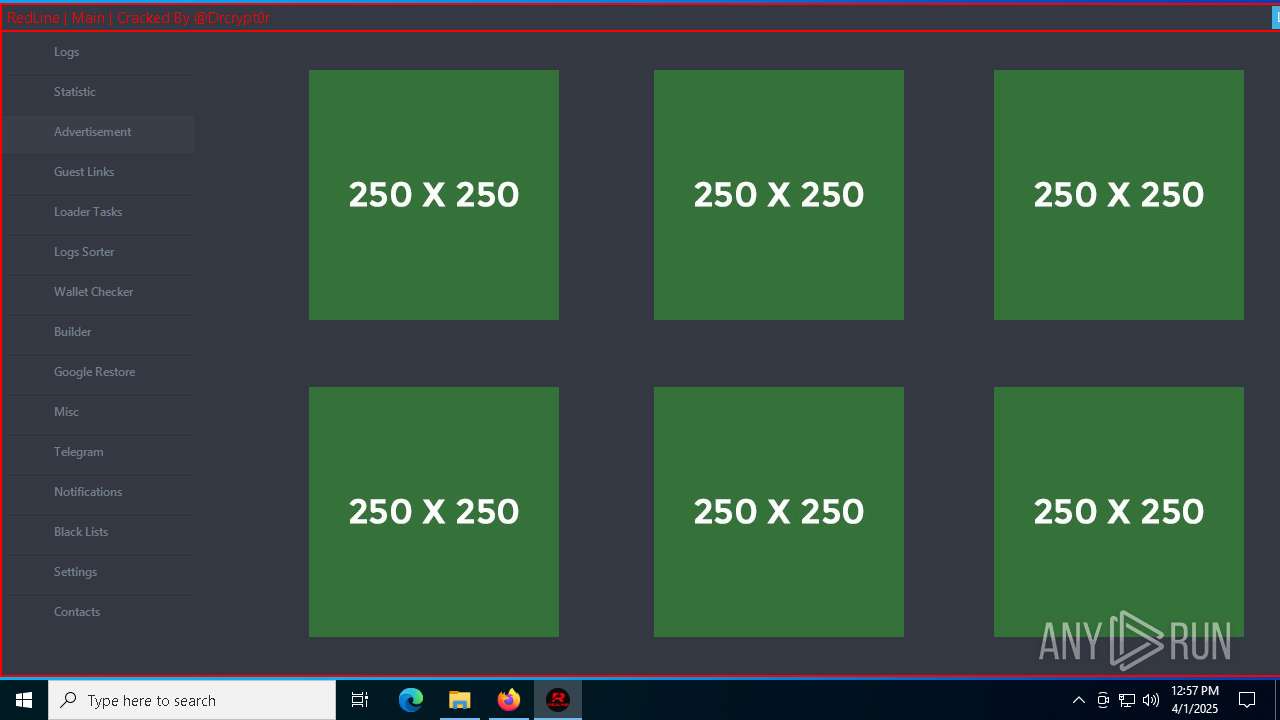
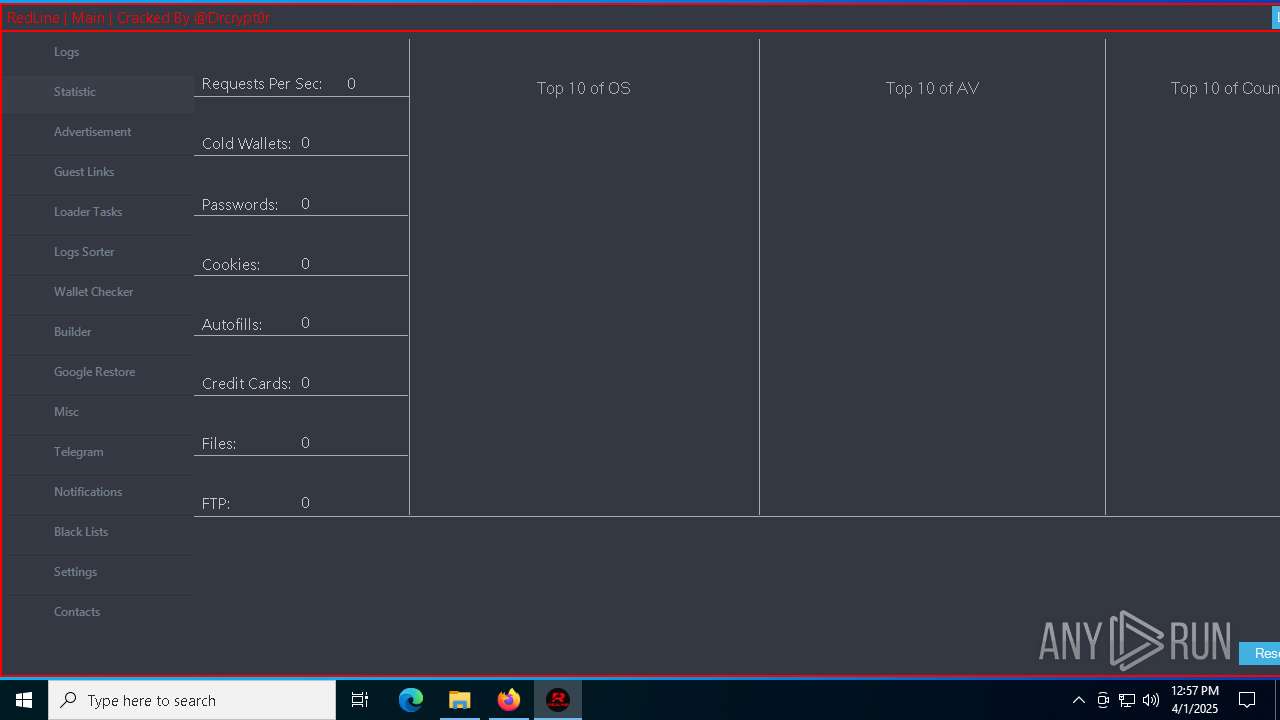
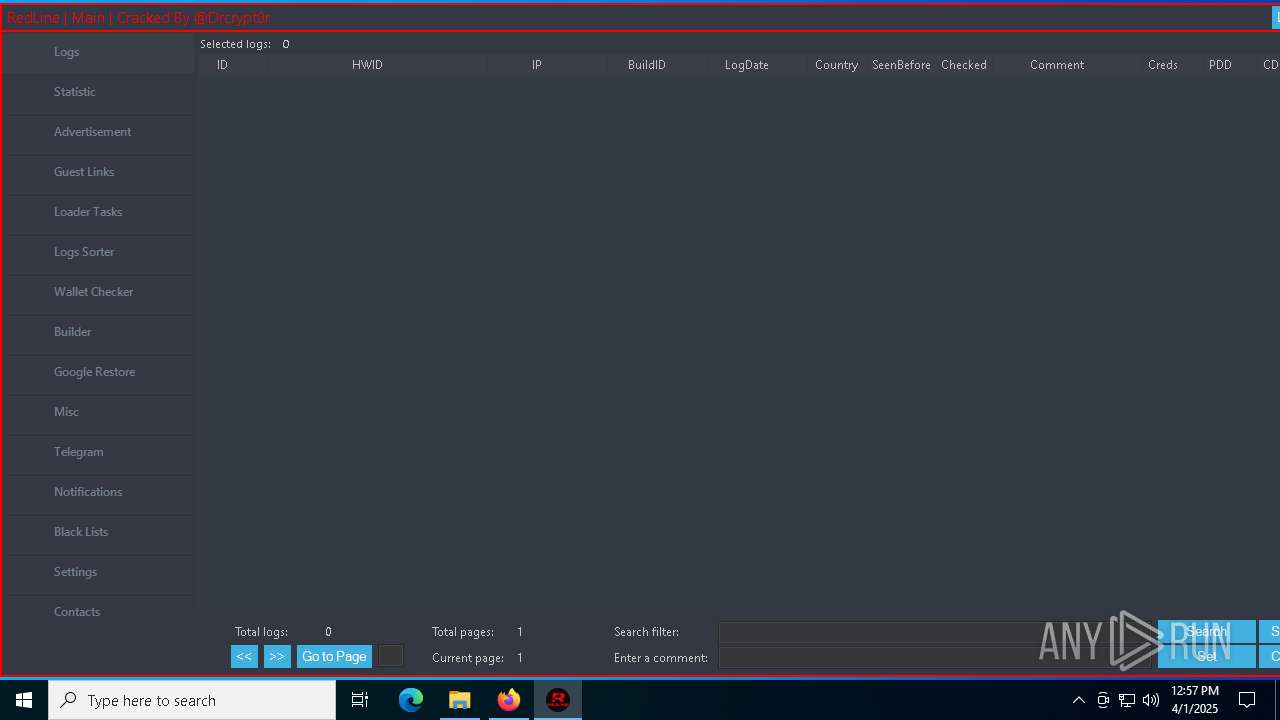
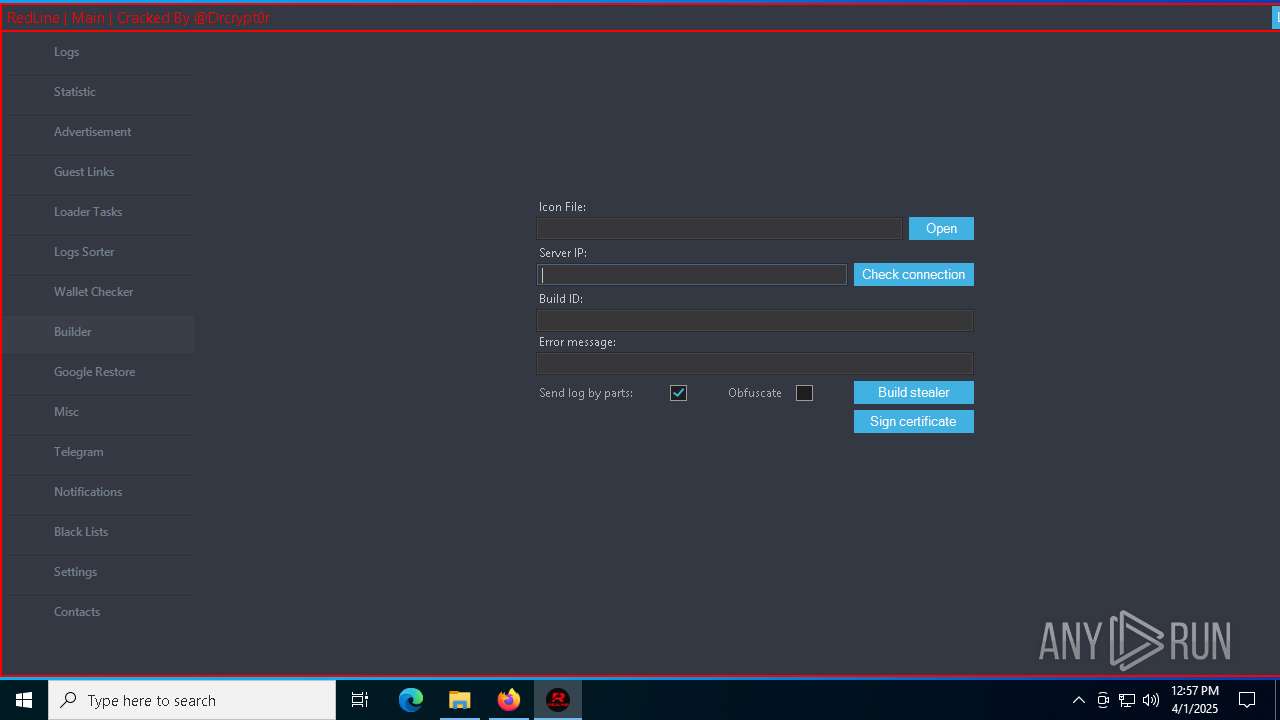
| Threats: | RedLine Stealer is a malicious program that collects users’ confidential data from browsers, systems, and installed software. It also infects operating systems with other malware. |
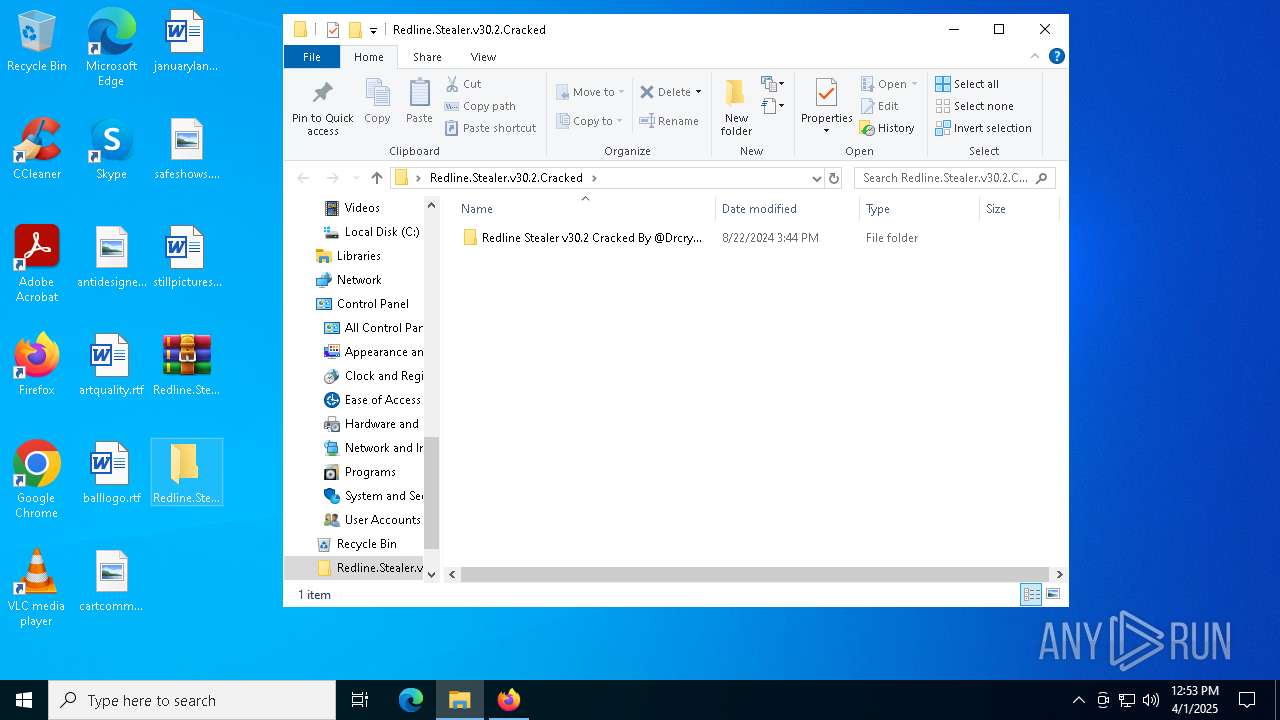
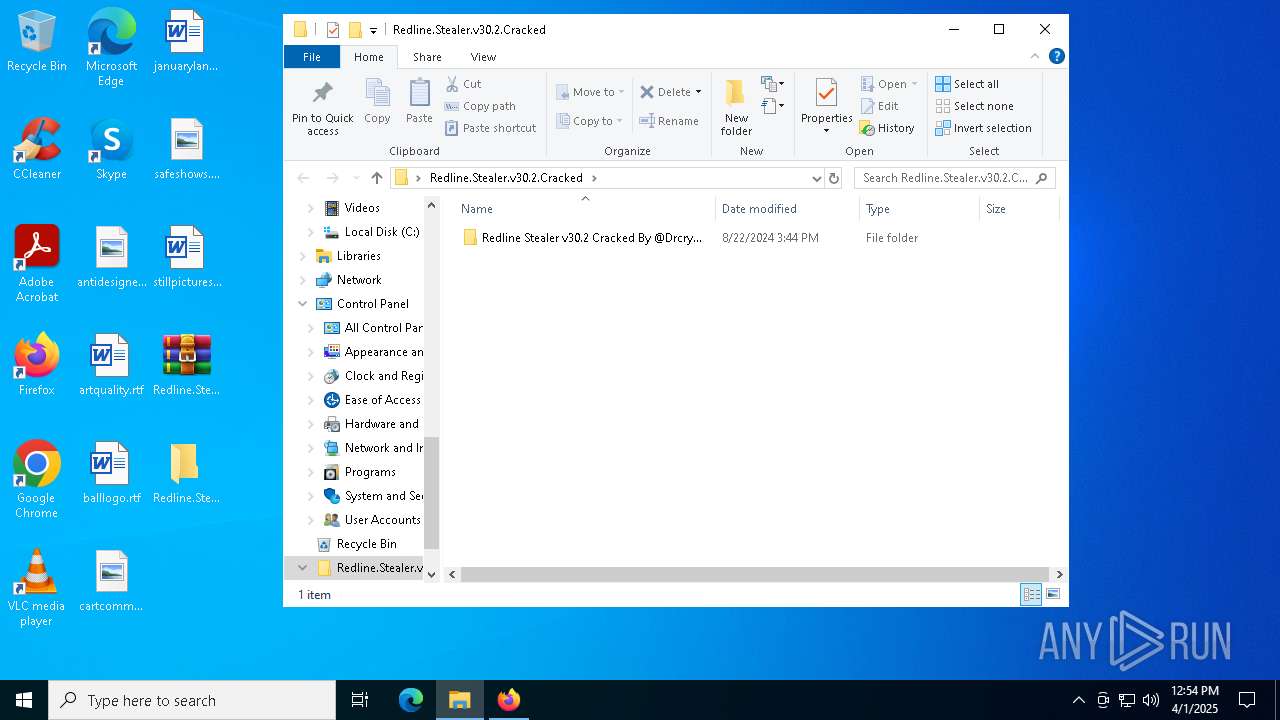
| Analysis date: | April 01, 2025, 12:53:02 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8C58328757A484E69819FFFE150138FD |
| SHA1: | 07979263903946FA8A1AEC02977855062DA026A0 |
| SHA256: | 866C8D2974C8B56D85F4E818D6963B95F588967AB542F159B9707065EEDBC361 |
| SSDEEP: | 3:N8tEdyYqA/KNEJijzEZA72qK3pLTRhJy:2uUAiD/WJx3pLTRh4 |
MALICIOUS
REDLINE has been detected (YARA)
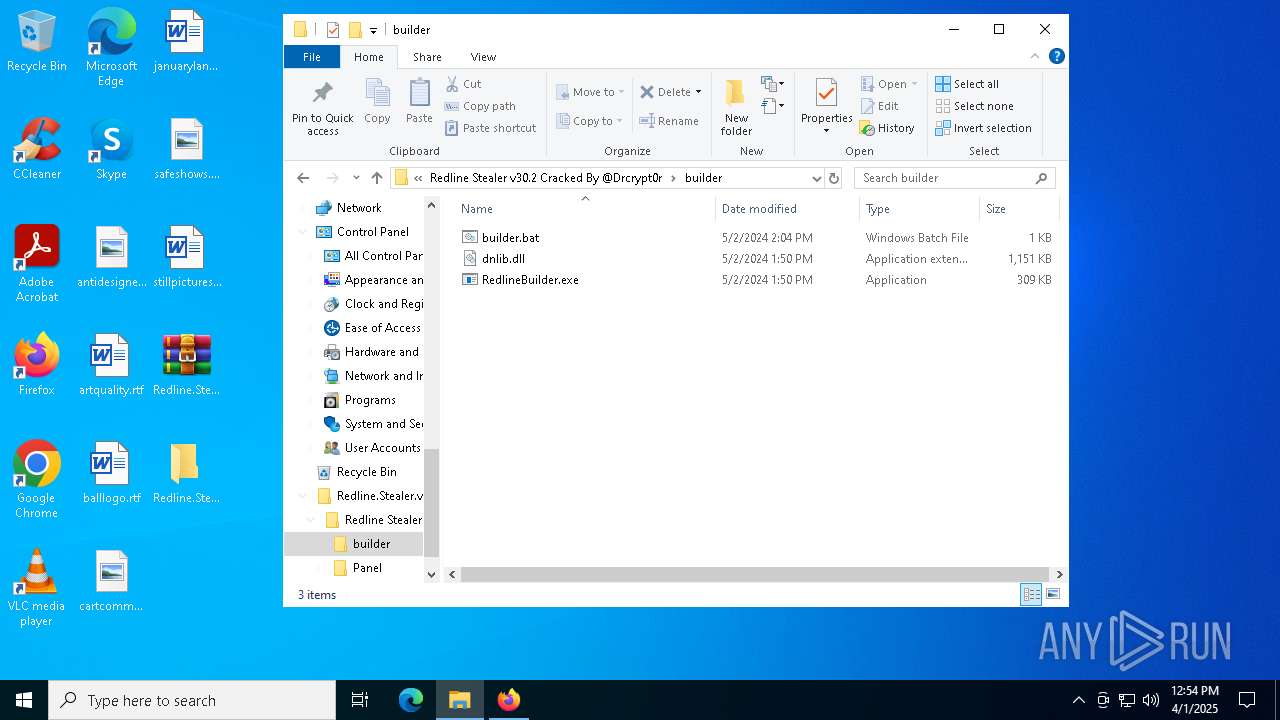
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
XORed URL has been found (YARA)
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
DISCORDGRABBER has been detected (YARA)
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
SUSPICIOUS
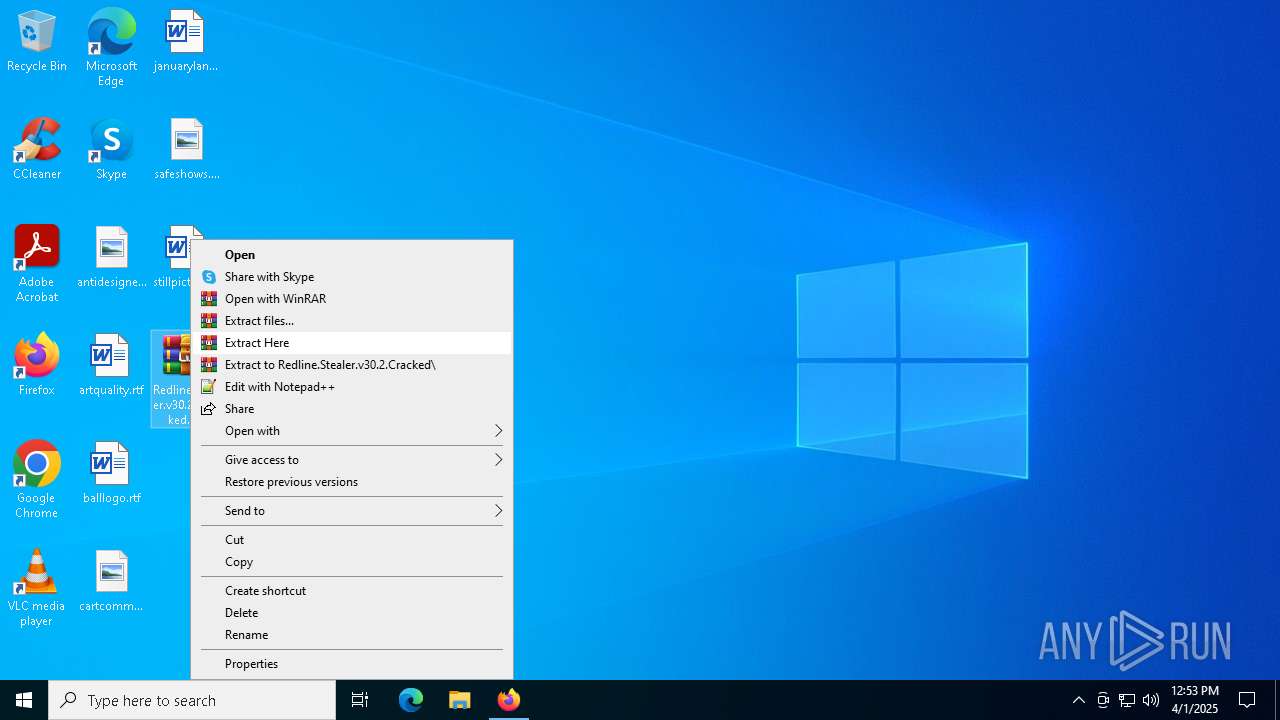
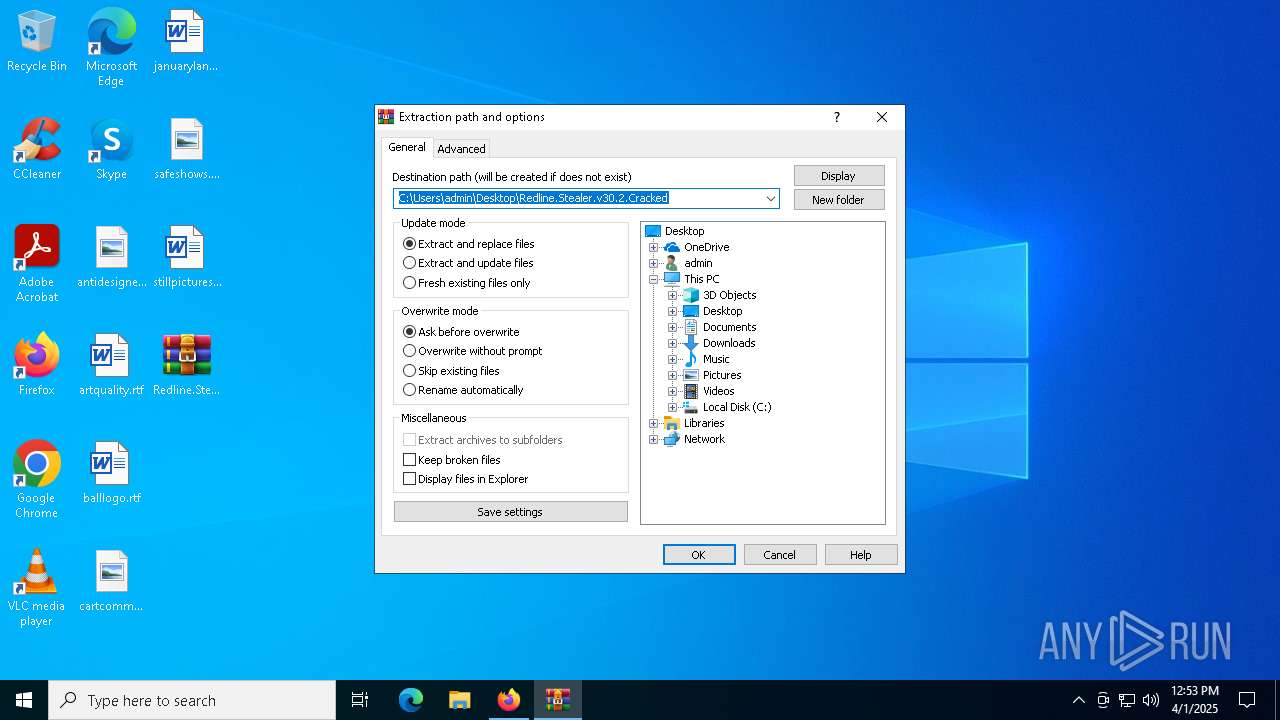
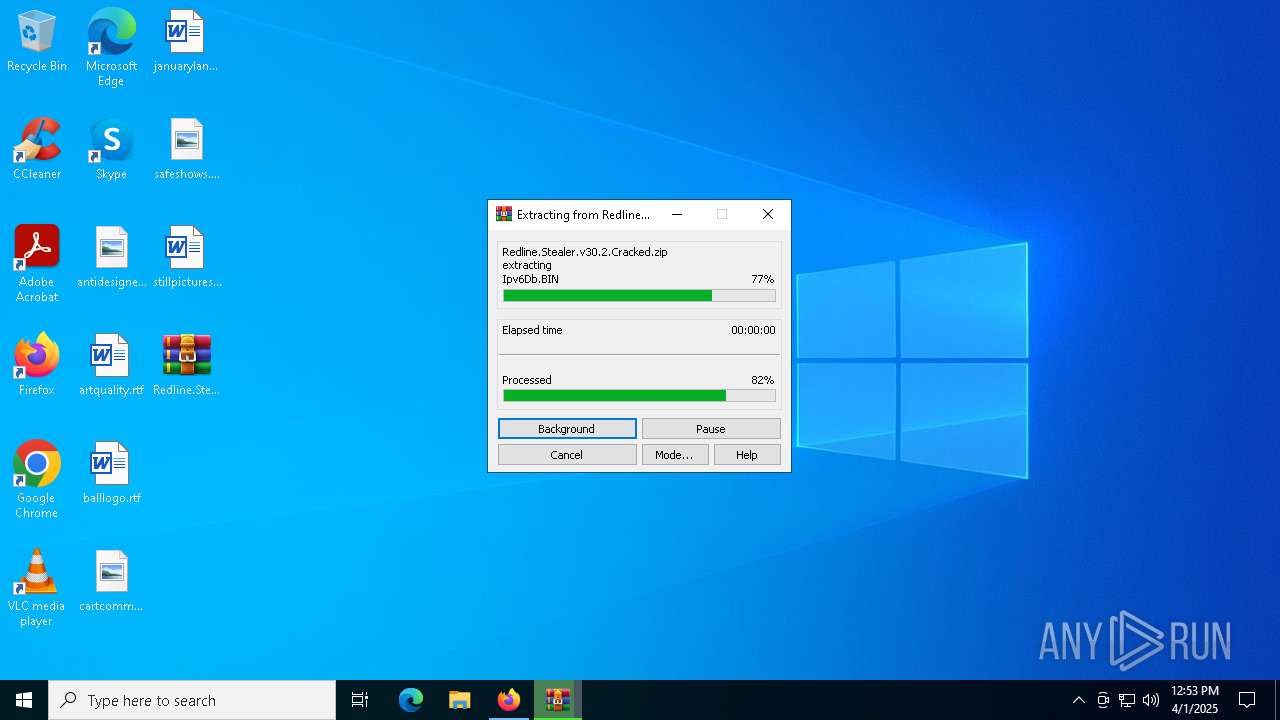
Process drops legitimate windows executable
- WinRAR.exe (PID: 7844)
Reads security settings of Internet Explorer
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
Reads the date of Windows installation
- Panel.exe (PID: 4892)
Application launched itself
- Panel.exe (PID: 4892)
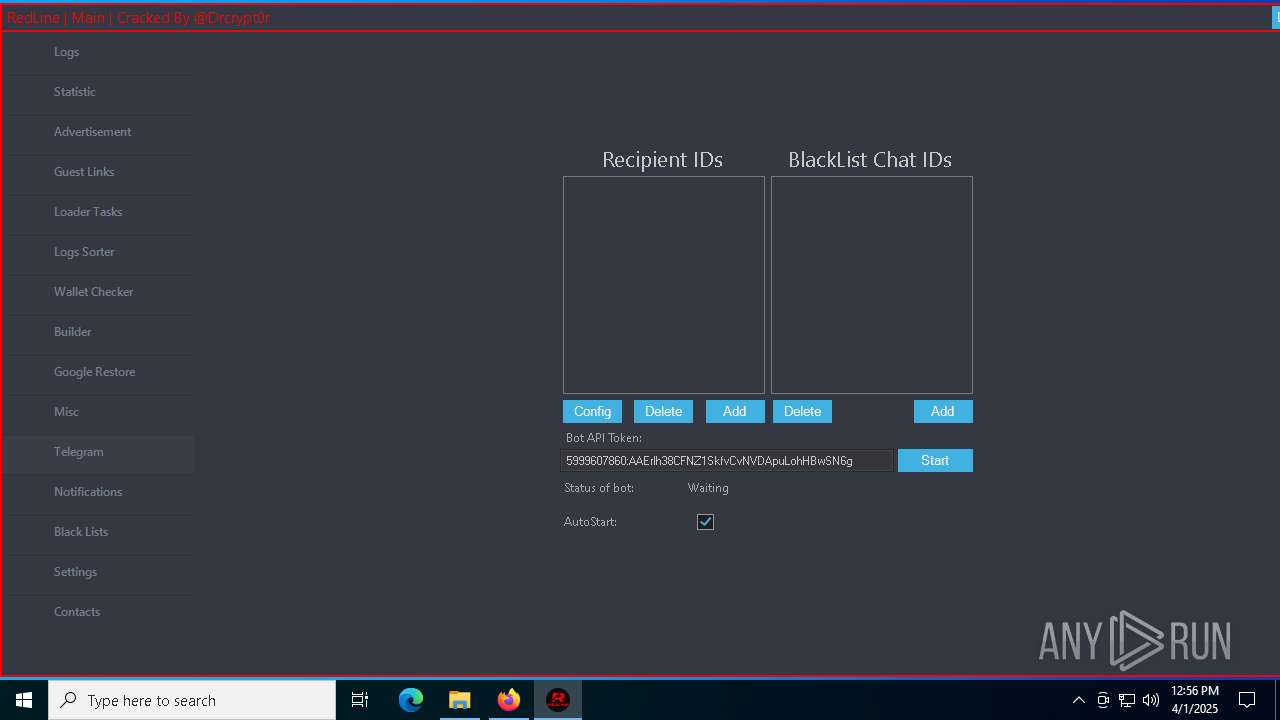
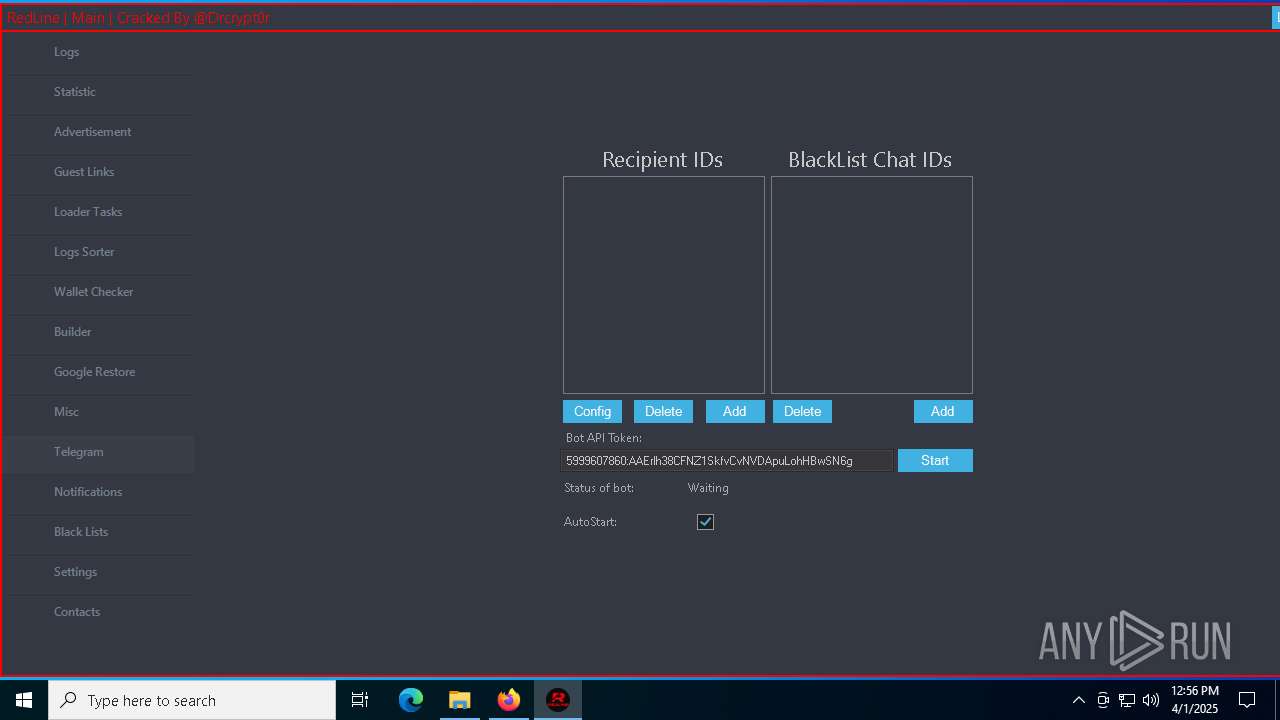
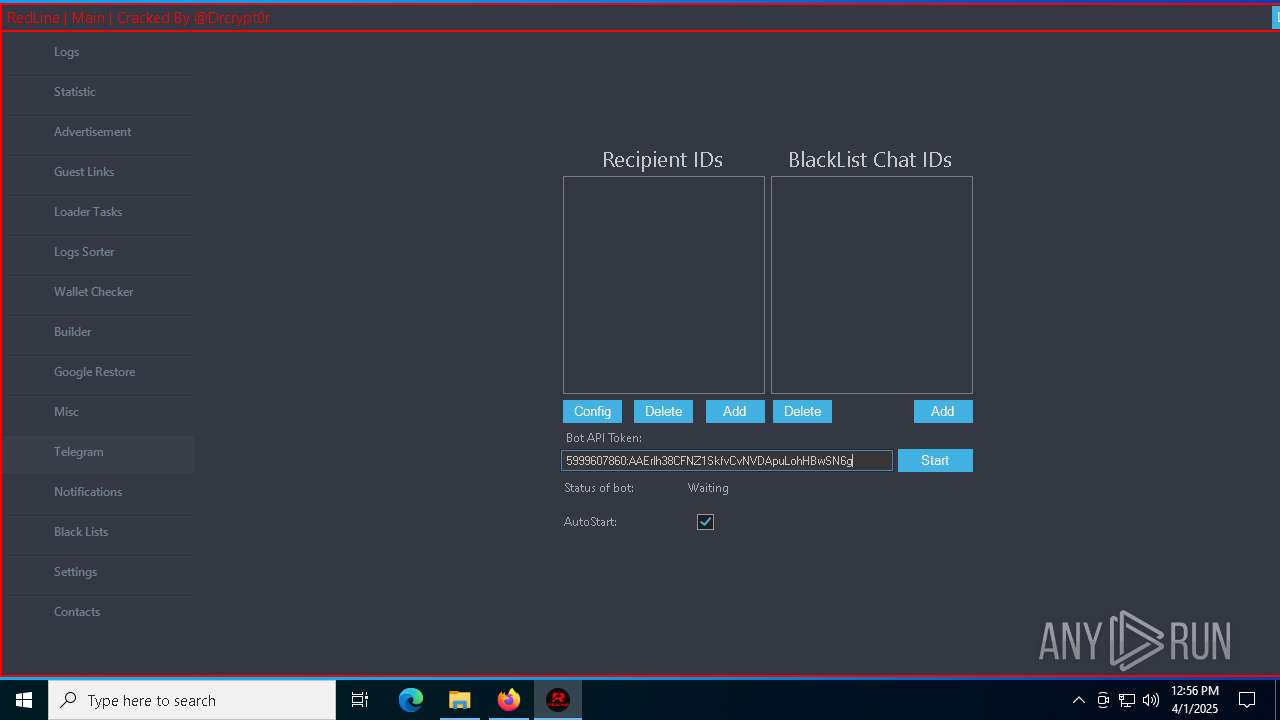
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Panel.exe (PID: 8092)
Found regular expressions for crypto-addresses (YARA)
- Panel.exe (PID: 8092)
- Panel.exe (PID: 4892)
Possible usage of Discord/Telegram API has been detected (YARA)
- Panel.exe (PID: 8092)
INFO
Application launched itself
- firefox.exe (PID: 7440)
- firefox.exe (PID: 7472)
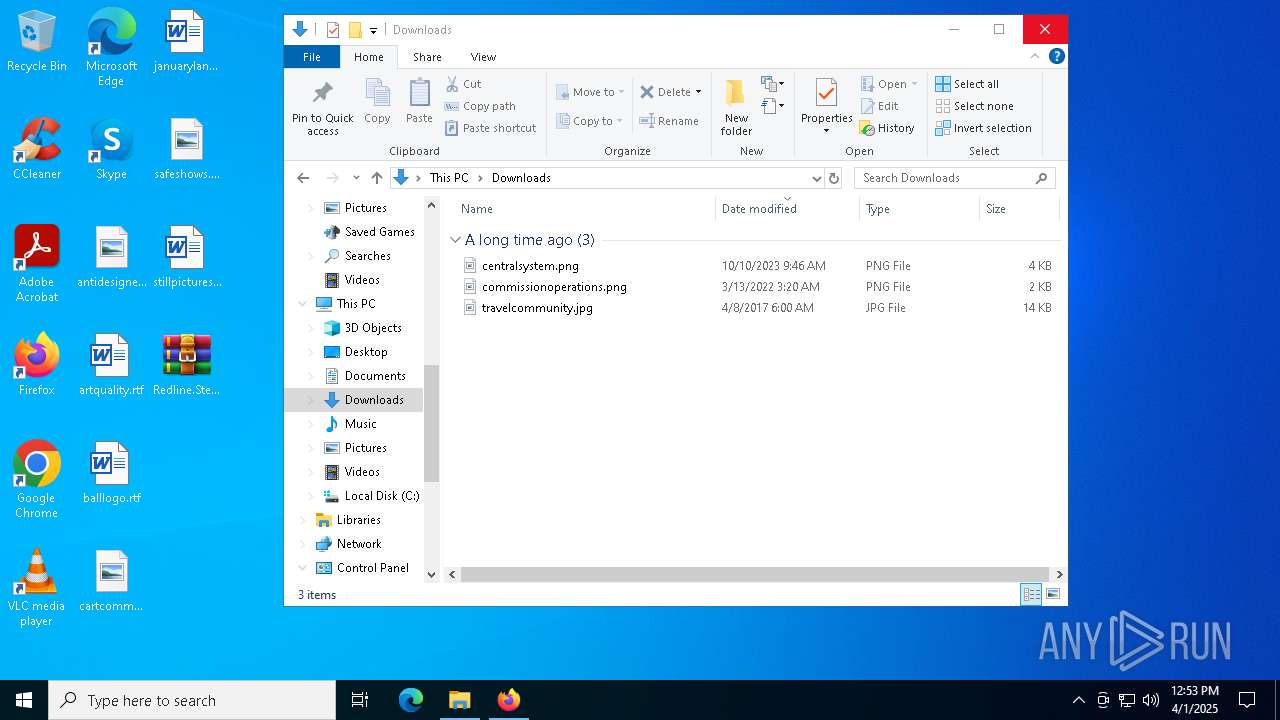
Autorun file from Downloads
- firefox.exe (PID: 7472)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7844)
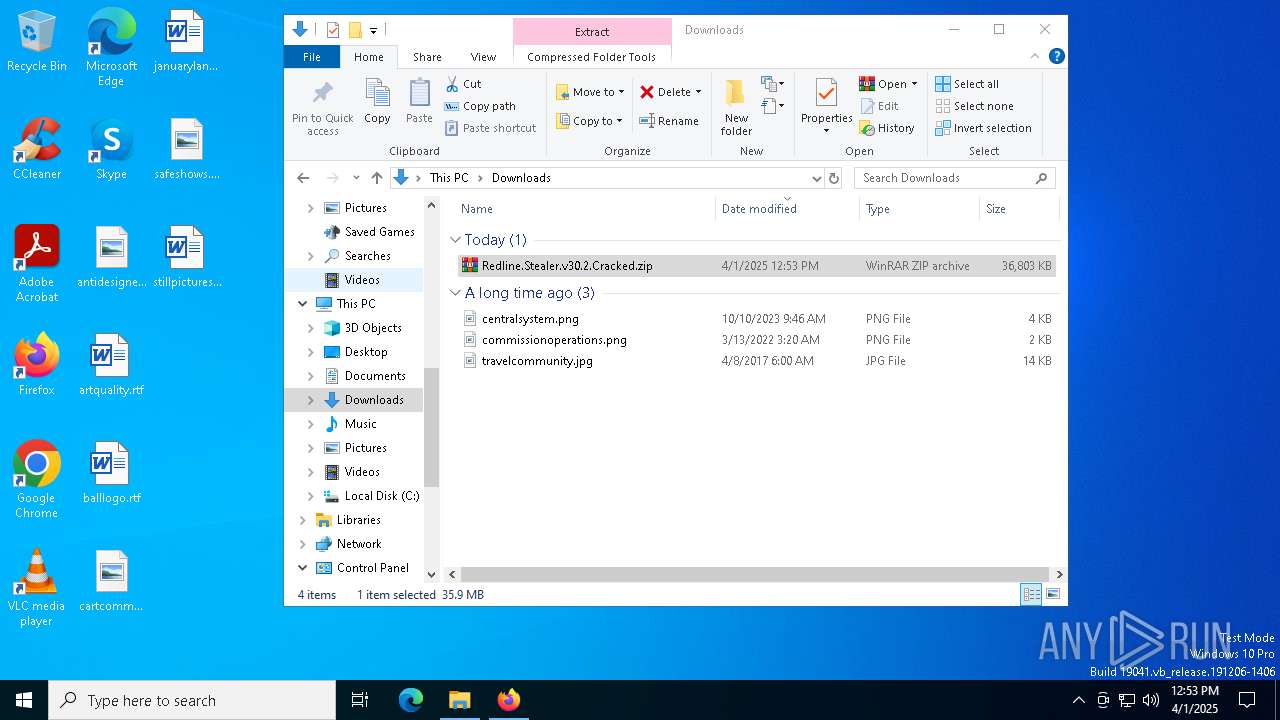
Manual execution by a user
- WinRAR.exe (PID: 7844)
- Panel.exe (PID: 4892)
Checks supported languages
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
Reads the computer name
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
Process checks computer location settings
- Panel.exe (PID: 4892)
Reads the software policy settings
- Panel.exe (PID: 8092)
- slui.exe (PID: 7864)
- slui.exe (PID: 7824)
Confuser has been detected (YARA)
- Panel.exe (PID: 4892)
- Panel.exe (PID: 8092)
Creates files or folders in the user directory
- Panel.exe (PID: 8092)
Reads the machine GUID from the registry
- Panel.exe (PID: 8092)
Reads Environment values
- Panel.exe (PID: 8092)
Disables trace logs
- Panel.exe (PID: 8092)
Checks proxy server information
- Panel.exe (PID: 8092)
- slui.exe (PID: 7824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(4892) Panel.exe
Decrypted-URLs (11)http://ns.adobe.com/xap/1.0/
http://ns.adobe.com/xap/1.0/mm/
http://ns.adobe.com/xap/1.0/sType/ResourceRef#
http://www.w3.org/1999/02/22-rdf-syntax-ns#
https://api.blockcypher.com/v1/btc/main/addrs/
https://api.telegram.org/bot
https://t.me/Drcrypt0r
https://t.me/REDLINESUPPORT
https://t.me/redline_market_bot
https://t.me/reversemesoftware
https://www.virustotal.com/api/v3/files/
(PID) Process(8092) Panel.exe
Decrypted-URLs (11)http://ns.adobe.com/xap/1.0/
http://ns.adobe.com/xap/1.0/mm/
http://ns.adobe.com/xap/1.0/sType/ResourceRef#
http://www.w3.org/1999/02/22-rdf-syntax-ns#
https://api.blockcypher.com/v1/btc/main/addrs/
https://api.telegram.org/bot
https://t.me/Drcrypt0r
https://t.me/REDLINESUPPORT
https://t.me/redline_market_bot
https://t.me/reversemesoftware
https://www.virustotal.com/api/v3/files/
ims-api
(PID) Process(8092) Panel.exe
Telegram-Tokens (1)5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g
Telegram-Info-Links
5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g
Get info about bothttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/getMe
Get incoming updateshttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/getUpdates
Get webhookhttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/getWebhookInfo
Delete webhookhttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/deleteWebhook
Drop incoming updateshttps://api.telegram.org/bot5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g/deleteWebhook?drop_pending_updates=true
Telegram-Requests
Token5999607860:AAErlh38CFNZ1SkfvCvNVDApuLohHBwSN6g
End-PointgetMe
Args
Total processes
147
Monitored processes
18
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 3300 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4876 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4868 -prefMapHandle 4864 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {57e4de19-b928-4905-b3e1-1e3c9236e3d2} 7472 "\\.\pipe\gecko-crash-server-pipe.7472" 245f6b1bf10 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 3896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4988 -childID 4 -isForBrowser -prefsHandle 4792 -prefMapHandle 4648 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {9cfa877c-fa89-47ee-a545-f4b60ac11c9e} 7472 "\\.\pipe\gecko-crash-server-pipe.7472" 245f6d96a10 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
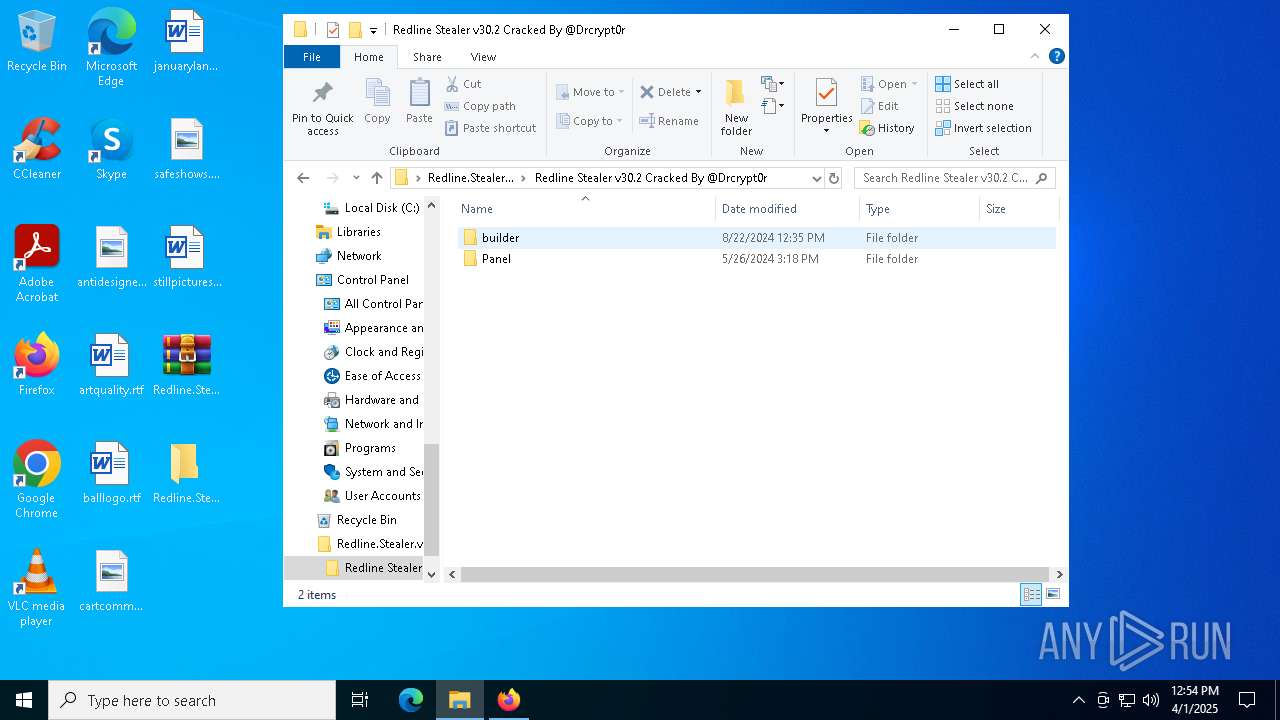
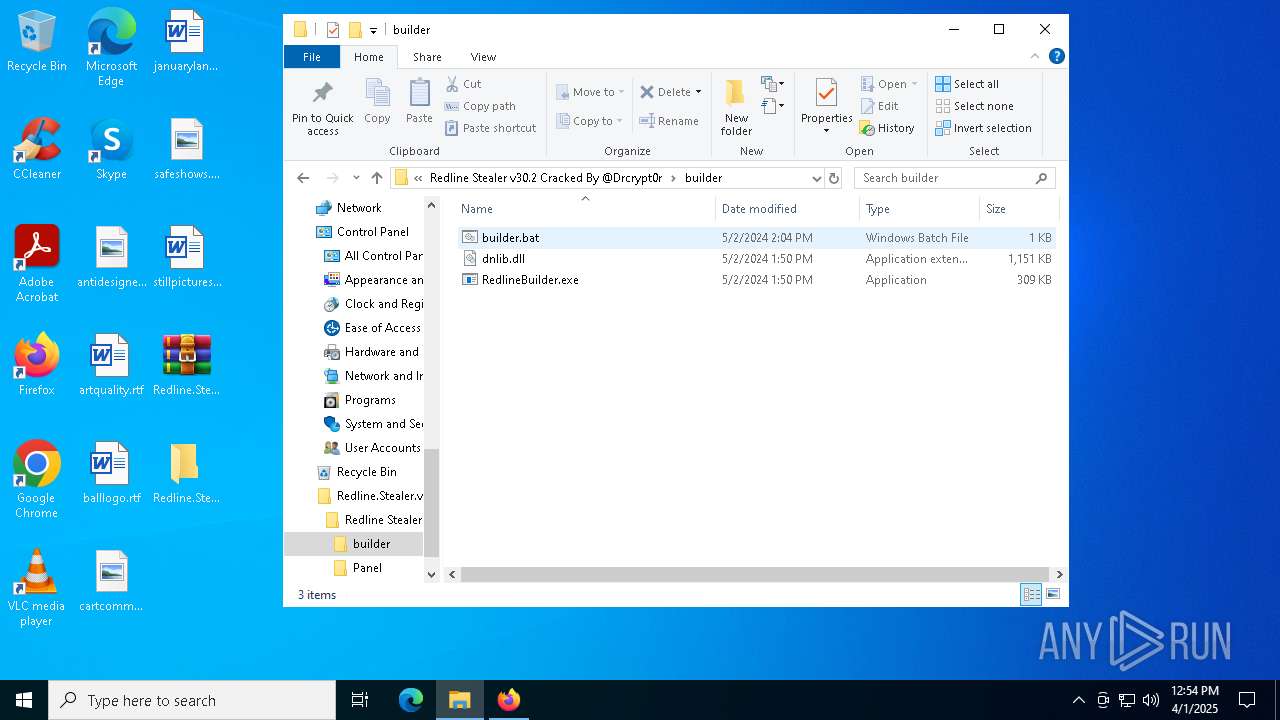
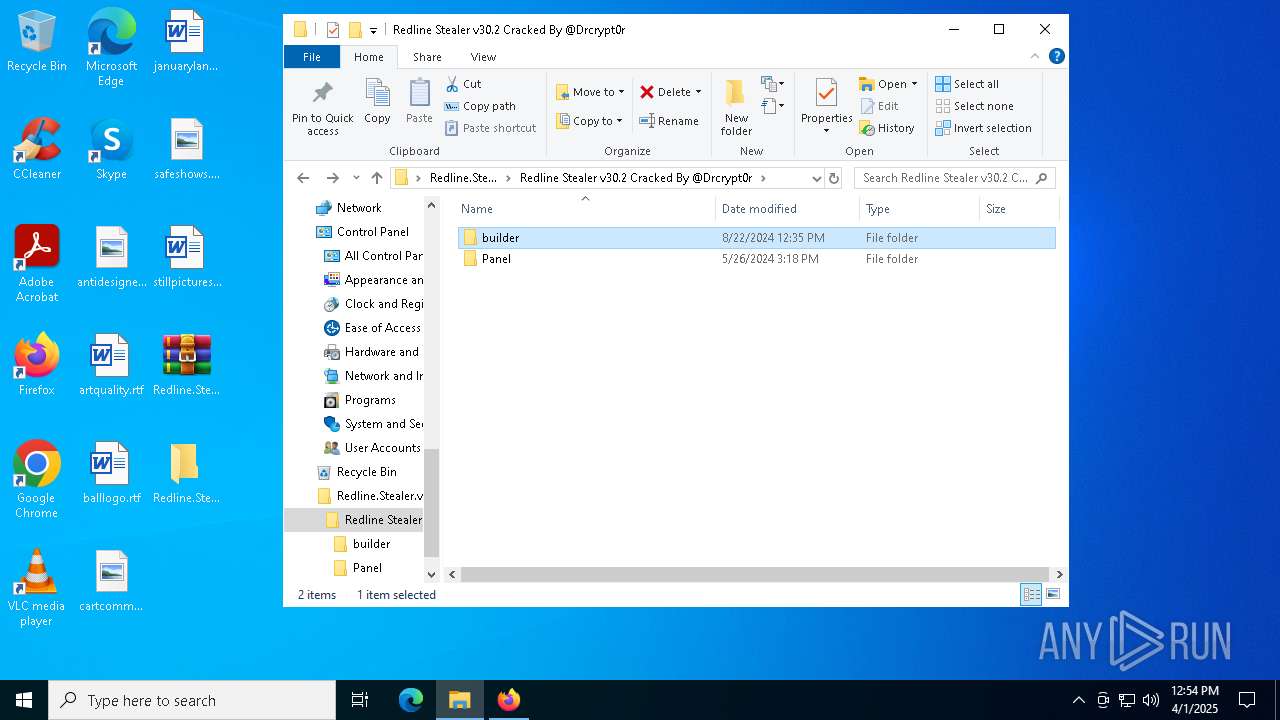
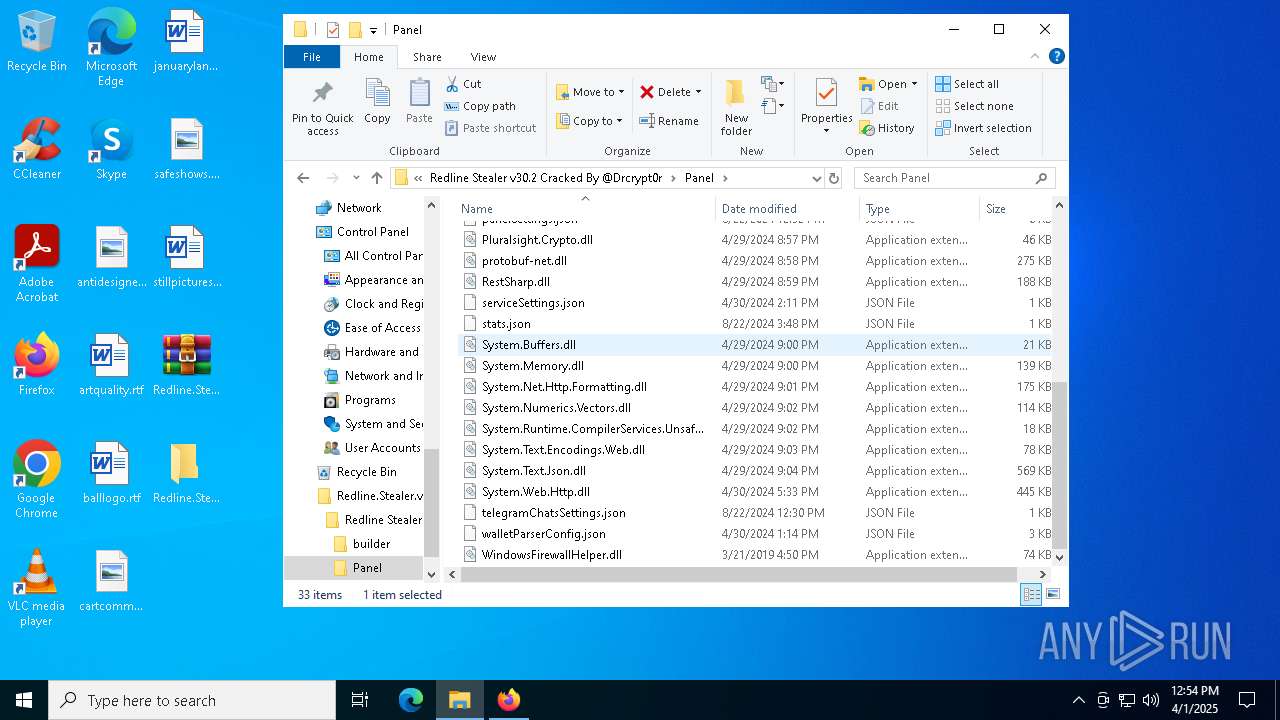
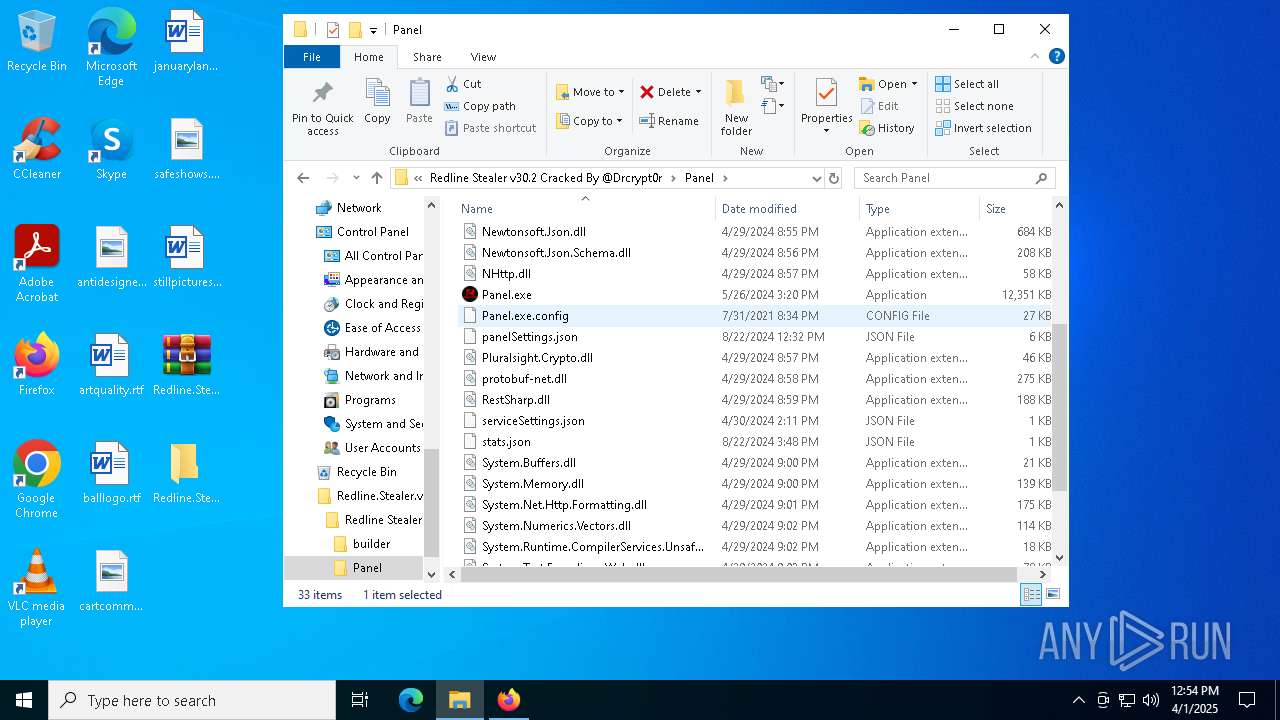
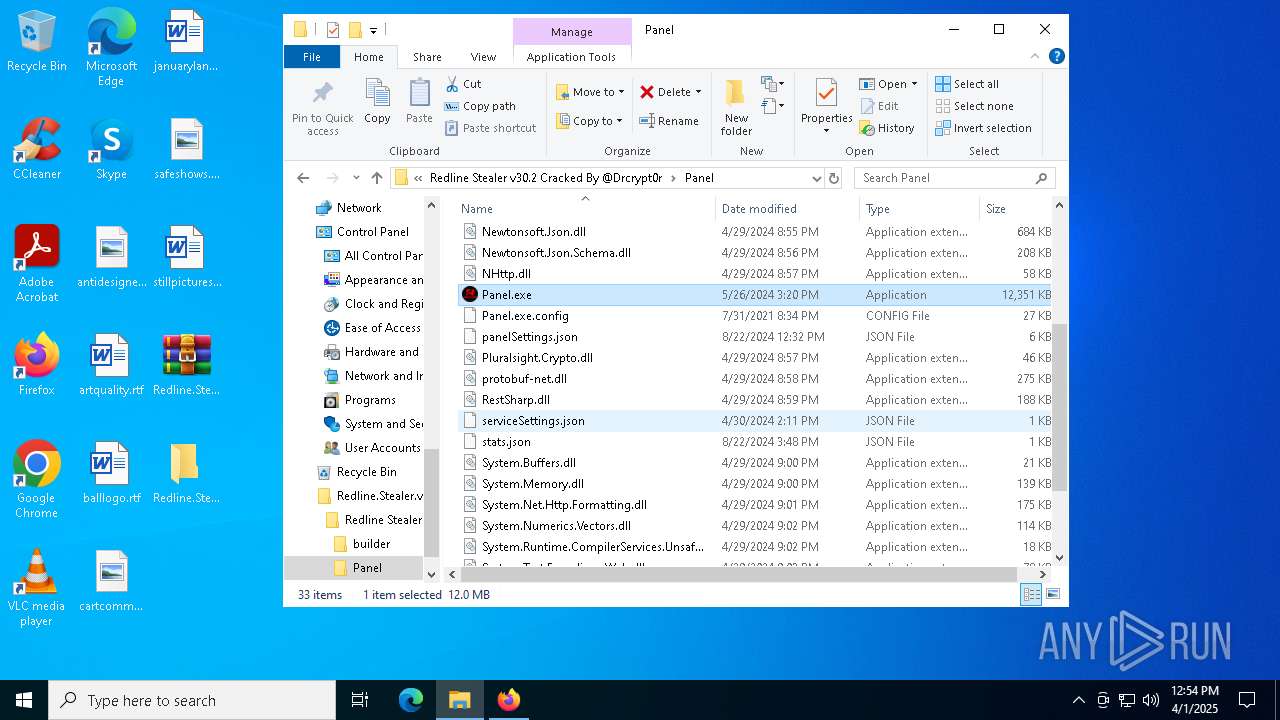
| 4892 | "C:\Users\admin\Desktop\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\Panel\Panel.exe" | C:\Users\admin\Desktop\Redline.Stealer.v30.2.Cracked\Redline Stealer v30.2 Cracked By @Drcrypt0r\Panel\Panel.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
xor-url(PID) Process(4892) Panel.exe Decrypted-URLs (11)http://ns.adobe.com/xap/1.0/ http://ns.adobe.com/xap/1.0/mm/ http://ns.adobe.com/xap/1.0/sType/ResourceRef# http://www.w3.org/1999/02/22-rdf-syntax-ns# https://api.blockcypher.com/v1/btc/main/addrs/ https://api.telegram.org/bot https://t.me/Drcrypt0r https://t.me/REDLINESUPPORT https://t.me/redline_market_bot https://t.me/reversemesoftware https://www.virustotal.com/api/v3/files/ | |||||||||||||||
| 6068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=5088 -childID 5 -isForBrowser -prefsHandle 2292 -prefMapHandle 4852 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {b7c20822-3efd-41aa-ac46-909e8a793817} 7472 "\\.\pipe\gecko-crash-server-pipe.7472" 245f6d96bd0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 6564 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4880 -childID 6 -isForBrowser -prefsHandle 5156 -prefMapHandle 4920 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {857a9c59-d284-4a10-b518-1fc5f2cd5b38} 7472 "\\.\pipe\gecko-crash-server-pipe.7472" 245f6d96f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 6572 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7228 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4656 -childID 3 -isForBrowser -prefsHandle 4892 -prefMapHandle 4880 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1264 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {fdd63a43-99ea-4431-ad42-dcaf429cbee3} 7472 "\\.\pipe\gecko-crash-server-pipe.7472" 245f69fd4d0 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 | |||||||||||||||
| 7440 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/tag/RedlineStealer" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 7472 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/Drcrypt0r/Redline-Stealer-v30.2-Cracked/releases/tag/RedlineStealer | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
Total events
11 040
Read events
11 006
Write events
21
Delete events
13
Modification events
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 11 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 10 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 9 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 8 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 7 |
Value: | |||
| (PID) Process: | (7844) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 6 |
Value: | |||
Executable files
25
Suspicious files
195
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2823318777ntouromlalnodry--naod.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\2918063365piupsah.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:C78F36BF78A74A5C37232FA18305FA6E | SHA256:319C730AC6614FDCE611894E281CBE1B5E1A304DCD812D6B642D3BE978E82EEC | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7472 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
85
DNS requests
133
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.193:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
— | — | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | whitelisted |
— | — | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.67:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.67:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.71:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 184.24.77.71:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
— | — | POST | 200 | 142.250.184.227:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.193:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.172.255.217:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
— | — | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
— | — | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
— | — | 34.117.188.166:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
github.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
content-signature-2.cdn.mozilla.net |
| whitelisted |
prod.content-signature-chains.prod.webservices.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
spocs.getpocket.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
8092 | Panel.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
8092 | Panel.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |
2196 | svchost.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
8092 | Panel.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
8092 | Panel.exe | Misc activity | ET HUNTING Telegram API Certificate Observed |